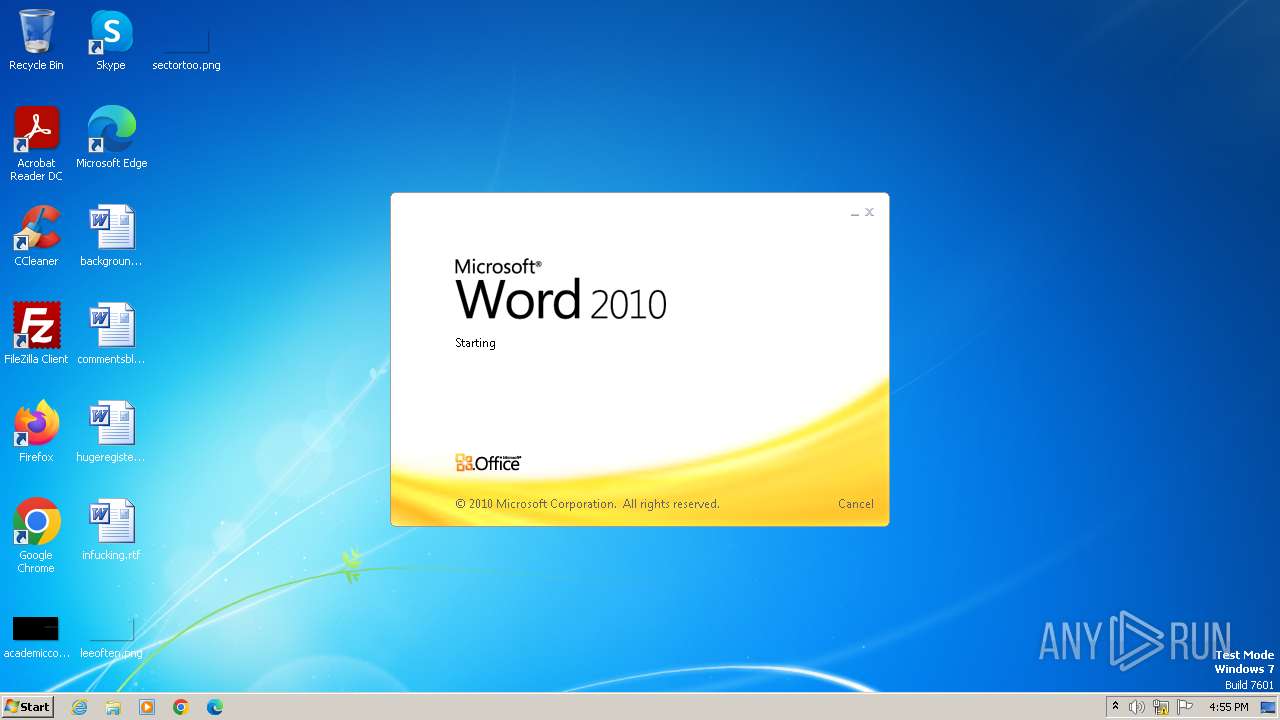
| File name: | factura.doc |
| Full analysis: | https://app.any.run/tasks/5411cd48-931c-4f79-a398-9ea6e857dd54 |
| Verdict: | Malicious activity |
| Analysis date: | January 31, 2025, 16:55:28 |
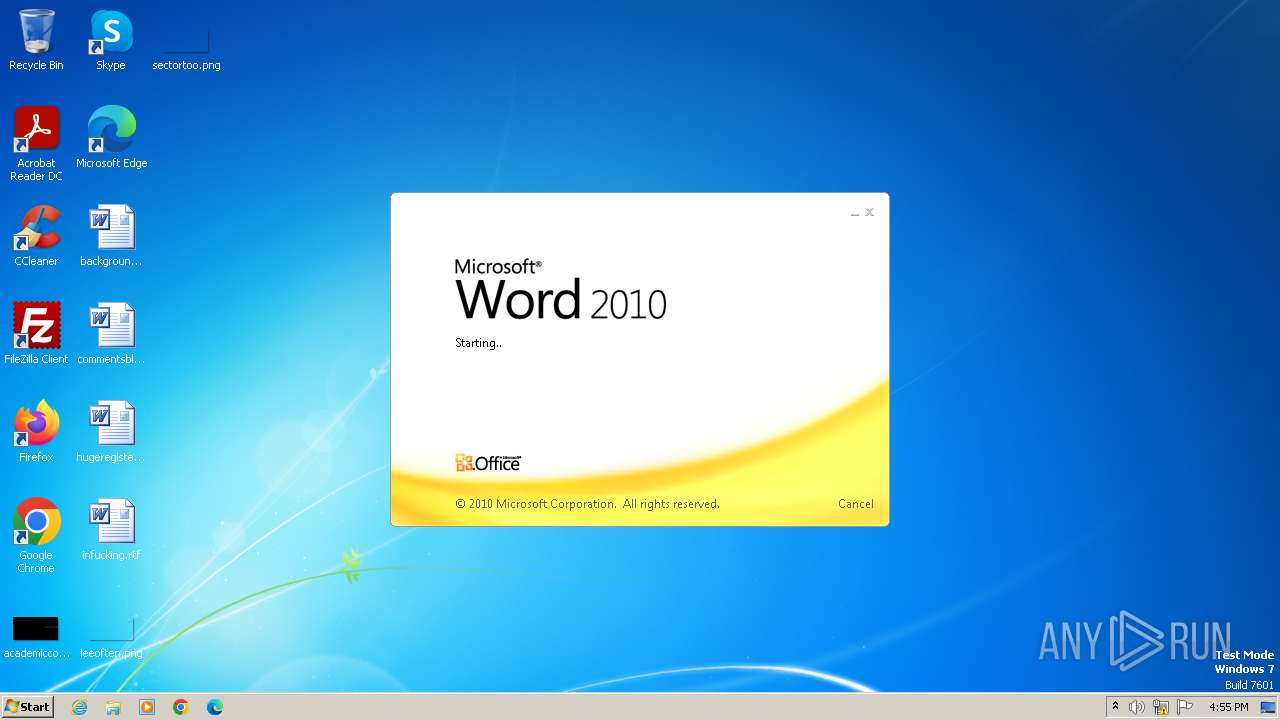
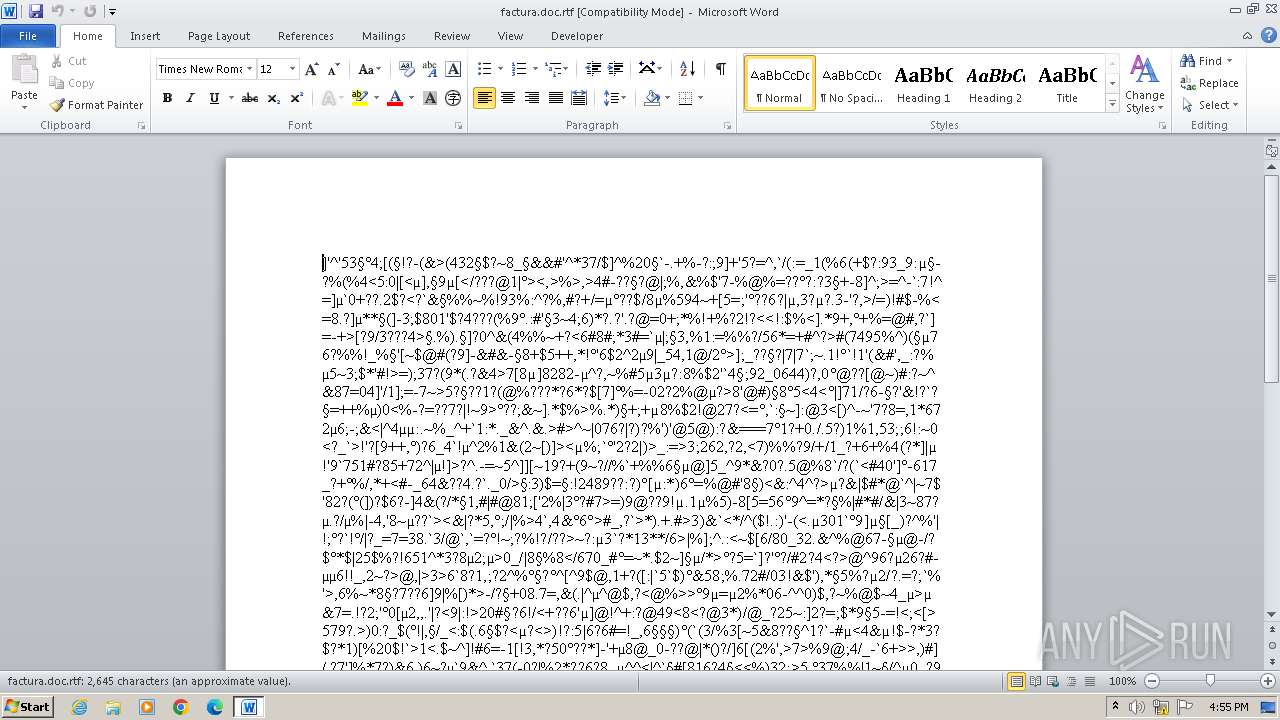
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 7 |
| MD5: | 05C137D8E79CE59ED6E4B7CD78E5B8A2 |
| SHA1: | 3A41DE3774B6A17A34A8BEDF1A0881A3F08D492D |
| SHA256: | 5A31C77293AF2920D7020D5D0236691ADCEA2C57C2716658CE118A5CBA9D4913 |
| SSDEEP: | 192:TMv9/nrxOgNIVk04Pre4VqPuc+17rf14g/gjXKSDxX8VxrdPJH:Yv9/rsok+Prz1dZKXDsjtJH |
MALICIOUS
Equation Editor starts application (likely CVE-2017-11882)
- EQNEDT32.EXE (PID: 1068)
SUSPICIOUS
Reads the Internet Settings
- EQNEDT32.EXE (PID: 1068)
Reads security settings of Internet Explorer
- EQNEDT32.EXE (PID: 1068)
INFO
Reads the computer name
- EQNEDT32.EXE (PID: 1068)
Checks supported languages
- EQNEDT32.EXE (PID: 1068)
Reads the machine GUID from the registry
- EQNEDT32.EXE (PID: 1068)
Checks proxy server information
- EQNEDT32.EXE (PID: 1068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
Total processes
36
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1068 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\microsoft shared\EQUATION\EQNEDT32.EXE | — | svchost.exe | |||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 1108 | C:\Windows\system32\svchost.exe -k NetworkService | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1848 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n C:\Users\admin\Downloads\factura.doc.rtf | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
4 243
Read events
3 355
Write events
572
Delete events
316
Modification events
| (PID) Process: | (1848) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | {,7 |
Value: 7B2C370038070000010000000000000000000000 | |||
| (PID) Process: | (1848) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1848) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1848) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1848) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1848) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1848) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1848) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1848) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1848) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
1
Suspicious files
4
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1848 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR904B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1848 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | binary | |
MD5:317111332CCDEA357438AB13381C13FD | SHA256:2294612CB8BE07B503874FFB33555FD36C4B6F87B84E4707052557A5604750BA | |||
| 1848 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:6530EFBAC9FAC6A6EA01DA704257AF79 | SHA256:526A61BFFF34F876B2B5E605C4E0BB762BE0C70AC31579716C4F90F2DE0A7CCF | |||
| 1848 | WINWORD.EXE | C:\Users\admin\Downloads\~$ctura.doc.rtf | binary | |
MD5:278346EB517EC98F2174ADE8B40E06EF | SHA256:48FF7A8C86069848E709E40437AA23267883884565F93FAC4A327E6AC2F4D16C | |||
| 1848 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\factura.doc.rtf.LNK | binary | |
MD5:F3101DECACF8E66B3BB9E44CC545783D | SHA256:A43CD53968A4B469CCA93862A858F2A9F176EBE39872529DF4320C1273A4E9FD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
4
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1108 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
seed-bc.com |
| malicious |