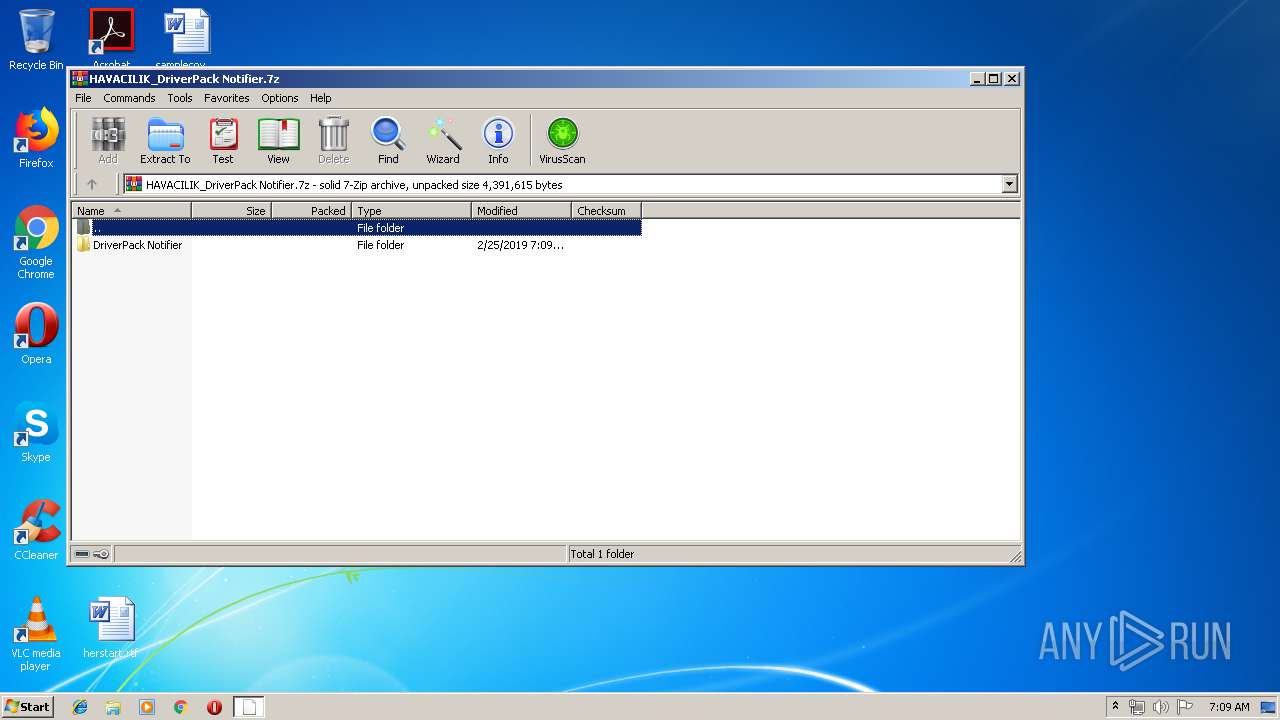
| File name: | HAVACILIK_DriverPack Notifier.7z |
| Full analysis: | https://app.any.run/tasks/ef4c7767-3f39-4d01-9241-4f6a8343f2e7 |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2019, 06:09:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.3 |
| MD5: | 18D5789371B6F06394162BDC8225F4C7 |
| SHA1: | FEBA88C60AAE1C9B2112B13387E7E634A432A54E |
| SHA256: | 5A2935DD88D2CC789F4DF69321CD8E3F237CAA588312C2E1E035E5D87BA0AC81 |
| SSDEEP: | 12288:U7aGZC0zjlDtgS67+dEHwspUetetgvnzkZrOuZKNjeG45lzIhr47tkFU8vbc4A8e:+anMxz67+dk3rgfZS6Rlz+rekFjc4+ |
MALICIOUS
Changes settings of System certificates
- mshta.exe (PID: 2060)
- mshta.exe (PID: 2392)
Application was dropped or rewritten from another process
- wget.exe (PID: 3652)
- DriverPackNotifier.exe (PID: 2784)
Executes PowerShell scripts
- cmd.exe (PID: 3964)
- cmd.exe (PID: 2840)
SUSPICIOUS
Adds / modifies Windows certificates
- mshta.exe (PID: 2060)
- mshta.exe (PID: 2392)
Starts MSHTA.EXE for opening HTA or HTMLS files
- DriverPackNotifier.exe (PID: 2784)
Starts CMD.EXE for commands execution
- mshta.exe (PID: 2060)
- mshta.exe (PID: 2392)
Creates files in the user directory
- mshta.exe (PID: 2060)
- powershell.exe (PID: 1912)
- cmd.exe (PID: 2840)
- cmd.exe (PID: 3964)
- powershell.exe (PID: 2520)
- mshta.exe (PID: 2392)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2136)
Reads Internet Cache Settings
- mshta.exe (PID: 2060)
- mshta.exe (PID: 2392)
INFO
Reads internet explorer settings
- mshta.exe (PID: 2392)
- mshta.exe (PID: 2060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (gen) (100) |
|---|
Total processes
55
Monitored processes
15
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1912 | powershell -NonInteractive -NoLogo -NoProfile -ExecutionPolicy Bypass "Get-Content 'C:\Users\admin\AppData\Roaming\DriverPack Notifier\temp\ps.jvq98n6l.vf0u1.cmd.txt' -Wait | Invoke-Expression" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2060 | "C:\Windows\System32\mshta.exe" "C:\Users\admin\Desktop\DriverPack Notifier\bin\Tools\run.hta" | C:\Windows\System32\mshta.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2136 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\HAVACILIK_DriverPack Notifier.7z" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2172 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\DriverPack Notifier\bin\Tools\main.js" | C:\Windows\System32\WScript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2392 | "C:\Windows\System32\mshta.exe" "C:\Users\admin\Desktop\DriverPack Notifier\bin\Tools\run.hta" | C:\Windows\System32\mshta.exe | DriverPackNotifier.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2520 | powershell -NonInteractive -NoLogo -NoProfile -ExecutionPolicy Bypass "Get-Content 'C:\Users\admin\AppData\Roaming\DriverPack Notifier\temp\ps.jvq98sjj.qalvq.cmd.txt' -Wait | Invoke-Expression" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2552 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\cysnzxdf.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 2696 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESB3B4.tmp" "c:\Users\admin\AppData\Local\Temp\CSCB3B3.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2784 | "C:\Users\admin\Desktop\DriverPack Notifier\DriverPackNotifier.exe" | C:\Users\admin\Desktop\DriverPack Notifier\DriverPackNotifier.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Software and Drivers Exit code: 0 Version: 1.0 Modules
| |||||||||||||||
| 2840 | "C:\Windows\System32\cmd.exe" /C powershell -NonInteractive -NoLogo -NoProfile -ExecutionPolicy Bypass "Get-Content 'C:\Users\admin\AppData\Roaming\DriverPack Notifier\temp\ps.jvq98n6l.vf0u1.cmd.txt' -Wait | Invoke-Expression" > "C:\Users\admin\AppData\Roaming\DriverPack Notifier\temp\ps.jvq98n6l.vf0u1.stdout.log" 2> "C:\Users\admin\AppData\Roaming\DriverPack Notifier\temp\ps.jvq98n6l.vf0u1.stderr.log" | C:\Windows\System32\cmd.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 263
Read events
1 081
Write events
178
Delete events
4
Modification events
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\HAVACILIK_DriverPack Notifier.7z | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
2
Suspicious files
5
Text files
1 041
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2136.49226\DriverPack Notifier\bin\Tools\icons\drp.png | image | |
MD5:1E336F0FD16CDD00664A82ADB2463141 | SHA256:D523EDA626162E20EBC68641E4D06B3C5CBF69C8B6CD973A40256E6BC4D1799D | |||
| 2136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2136.49226\DriverPack Notifier\bin\Tools\icons\loading.gif | image | |
MD5:FA54E1A0B386F83FABB7BC6E62BAFD2C | SHA256:A650F35352617213038CFEF07BF8607960928150F84DF88F6B330ED7D196E61A | |||
| 2136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2136.49226\DriverPack Notifier\bin\Tools\icons\gliph-tool.png | image | |
MD5:B7F7F46D5A993C897DE6B688859DB1DA | SHA256:1F3A59FABCDB8A75FE5BA1FF19FAB743C54D9CB6FDDCC7C85CC5CA933A11AFAA | |||
| 2136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2136.49226\DriverPack Notifier\bin\Tools\icons\gliph-success.png | image | |
MD5:F1C0D26A4E22BAA222484ED6D214BE3C | SHA256:F3FEAAA79AB89192F24513AE7B72464848D8234CD5BE798694C27CD10A9150D7 | |||
| 2136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2136.49226\DriverPack Notifier\bin\Tools\icons\gliph-battery.png | image | |
MD5:CD87BB98E6343597FE6F28D02B4ECD18 | SHA256:C6495D0AEFAB2F75B297415B1F07B2070F21BD9B2BF8D6B7C82C378CD15379CE | |||
| 2136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2136.49226\DriverPack Notifier\bin\Tools\icons\close.png | image | |
MD5:96E15923591FB05F410E06BC7C70B645 | SHA256:22C99D4A95E3ECE9D706E244587F6FA56A2649A98677E53A6DFA6C2A03193080 | |||
| 2136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2136.49226\DriverPack Notifier\bin\Tools\icons\gliph-harddrive.png | image | |
MD5:D23373F5A4C68619E44A17FCAEAF7EFA | SHA256:06C3FFA860DEAF1D3126A82949E78BE7D5A501BF0BF2DC0711FE16F34A45E82B | |||
| 2136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2136.49226\DriverPack Notifier\bin\Tools\icons\gliph-phone.png | image | |
MD5:5FA4D4B112EEE0C3756AE4025126B02D | SHA256:044FD543A650AC2FF91405F45BC798EE2E732625B339AF8F5A74D76E080777D3 | |||
| 2136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2136.49226\DriverPack Notifier\bin\Tools\icons\gliph-chipset.png | image | |
MD5:716103E689EDC4BDC5DE3E040AC59F5C | SHA256:888E741703CBABE2214D5A81D7D85391EC37C2577C4F340DF347D542FA2CF92E | |||
| 2136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2136.49226\DriverPack Notifier\bin\Tools\icons\gliph-cooler.png | image | |
MD5:608386D711A3519179961B6E299D7CF0 | SHA256:F8ABB71E1C13BD14EF3CE6A7B9885F8C674CF294A686270C325B2E432F69C3CA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
8
DNS requests
3
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2392 | mshta.exe | GET | 200 | 216.58.207.78:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
2392 | mshta.exe | GET | 200 | 87.117.235.116:80 | http://update.drp.su/notifier/watcher-check/?t=1557987010044 | GB | text | 171 Kb | malicious |
2060 | mshta.exe | GET | 200 | 216.58.207.78:80 | http://www.google-analytics.com/collect?v=1&tid=UA-68879973-5&cid=460336947.4430484179&t=event&ec=notifier&ea=application%20started&el=17.7.52%2Bpatch.13&ul=en&z=8503664768077694&cd1=460336947.4430484179&cd2=17.7.52%2Bpatch.13&cd3=7%20x86&cd4=SP%201&cd5=Windows%207%20Professional%20&cd6=bad_idea | US | image | 35 b | whitelisted |
2060 | mshta.exe | GET | 200 | 87.117.235.116:80 | http://update.drp.su/notifier/watcher-check/?t=1557987016974 | GB | text | 171 Kb | malicious |
2392 | mshta.exe | GET | 200 | 216.58.207.78:80 | http://www.google-analytics.com/collect?v=1&tid=UA-68879973-5&cid=460336947.4430484179&t=event&ec=notifier&ea=application%20started&el=17.7.52%2Bpatch.13&ul=en&z=6248314455511819&cd1=460336947.4430484179&cd2=17.7.52%2Bpatch.13&cd3=7%20x86&cd4=SP%201&cd5=Windows%207%20Professional%20&cd6=bad_idea | US | image | 35 b | whitelisted |
2060 | mshta.exe | GET | 200 | 216.58.207.78:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2392 | mshta.exe | 87.117.235.116:80 | update.drp.su | iomart Cloud Services Limited. | GB | unknown |
2060 | mshta.exe | 87.117.235.116:80 | update.drp.su | iomart Cloud Services Limited. | GB | unknown |
2392 | mshta.exe | 93.158.134.119:443 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
2392 | mshta.exe | 216.58.207.78:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
2060 | mshta.exe | 216.58.207.78:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
2060 | mshta.exe | 93.158.134.119:443 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
update.drp.su |
| malicious |
mc.yandex.ru |
| whitelisted |
www.google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1068 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
2392 | mshta.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
2392 | mshta.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
2392 | mshta.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
2060 | mshta.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
2060 | mshta.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
2060 | mshta.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|