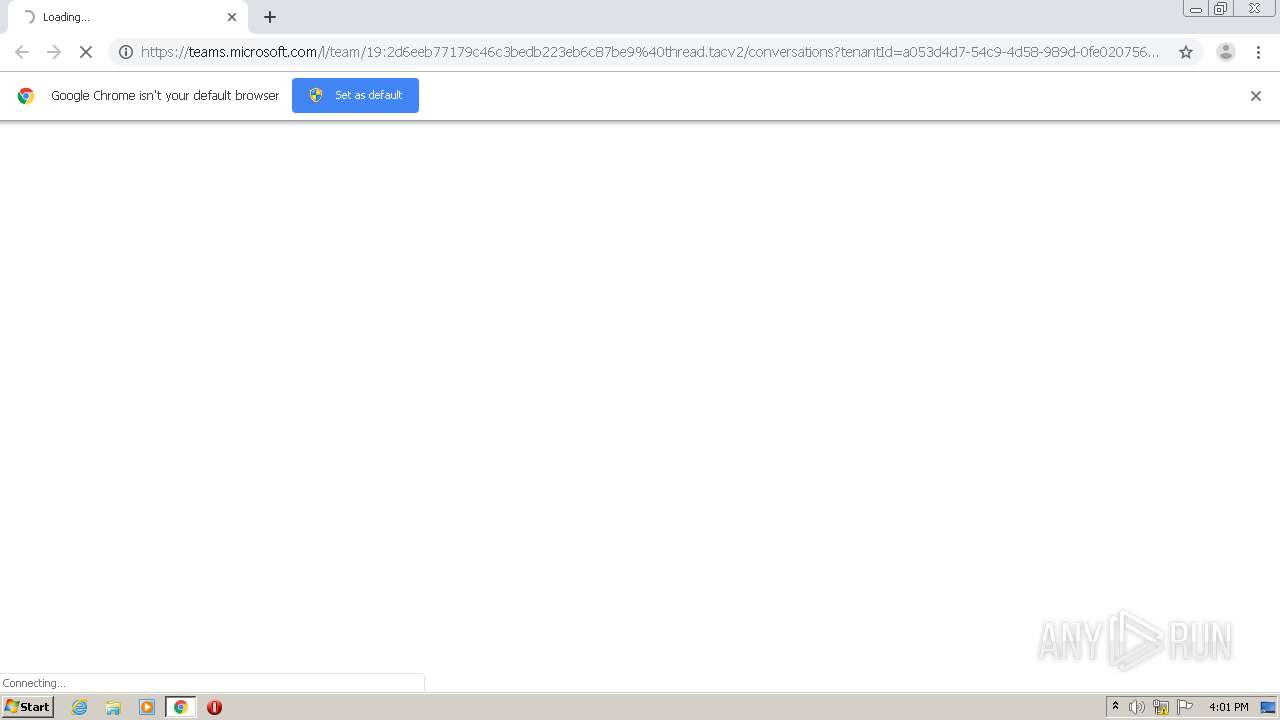
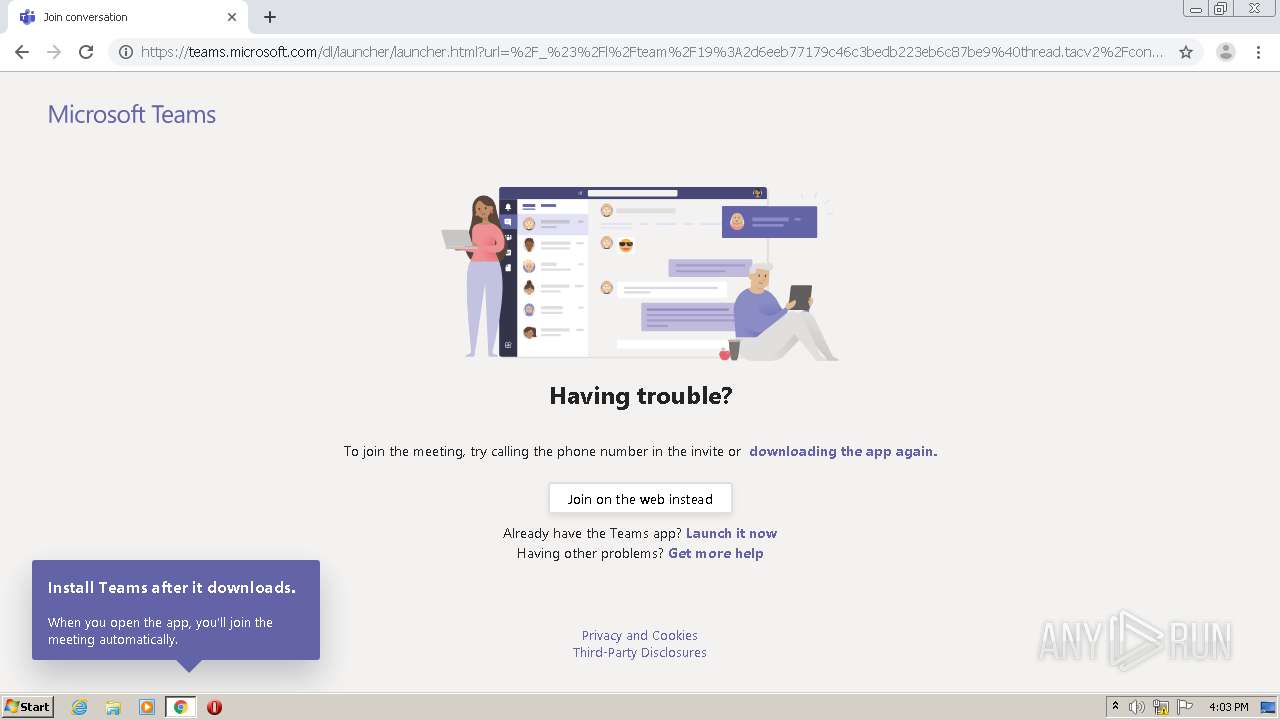
| URL: | https://teams.microsoft.com/l/team/19:2d6eeb77179c46c3bedb223eb6c87be9%40thread.tacv2/conversations?tenantId=a053d4d7-54c9-4d58-989d-0fe020756234 |
| Full analysis: | https://app.any.run/tasks/a071a66d-d4aa-41f2-b626-e11ba81109f5 |
| Verdict: | Malicious activity |
| Analysis date: | September 03, 2020, 15:01:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C82EE026CBC521EC1AB63AD301F86150 |
| SHA1: | 28A53A45E51D1FE74313799BA461C5BB287431C0 |
| SHA256: | 5A1B8720AE24B0730CD5659BCC003B879894F9BBEF8491E6369E6FC4D11868C2 |
| SSDEEP: | 3:N8IuA+tRERhkYBxRcGXHAQiTGdCLoeEaGQyMGA+KhDk3IQdhdwf9VSQTG:2In+DER+G6OkTvotNtMX+KhDDQHds9Ve |
MALICIOUS
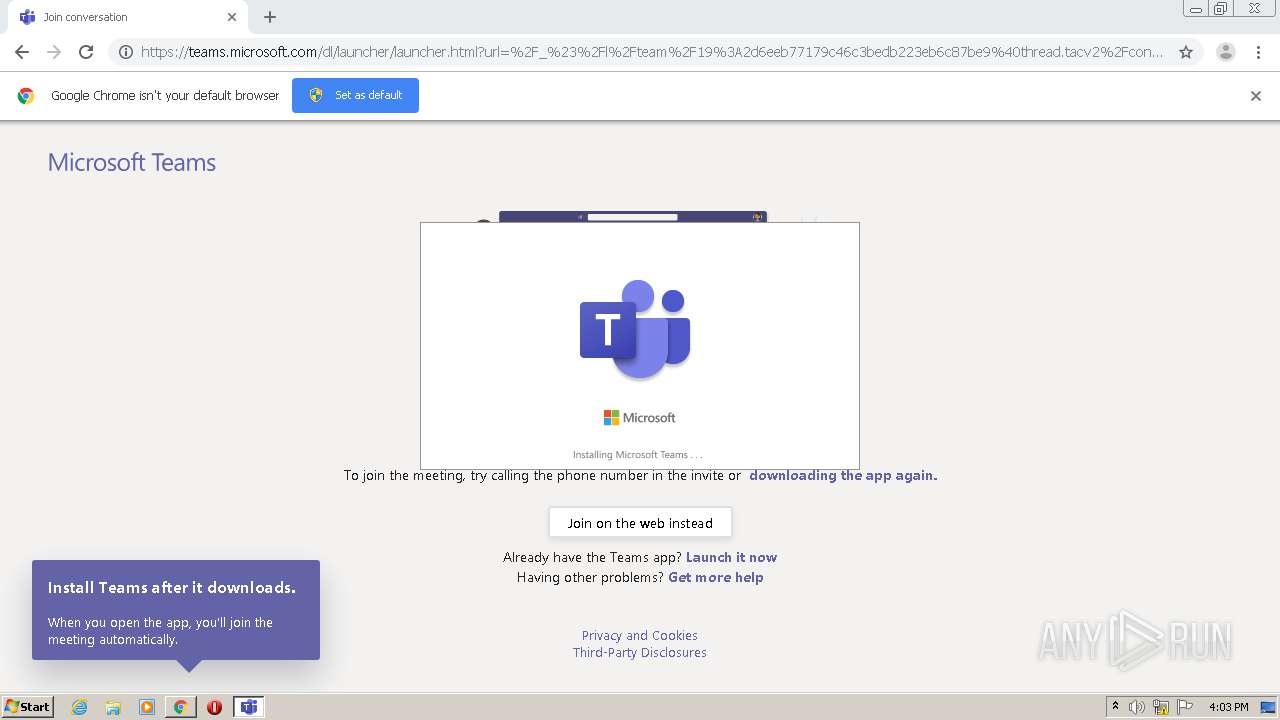
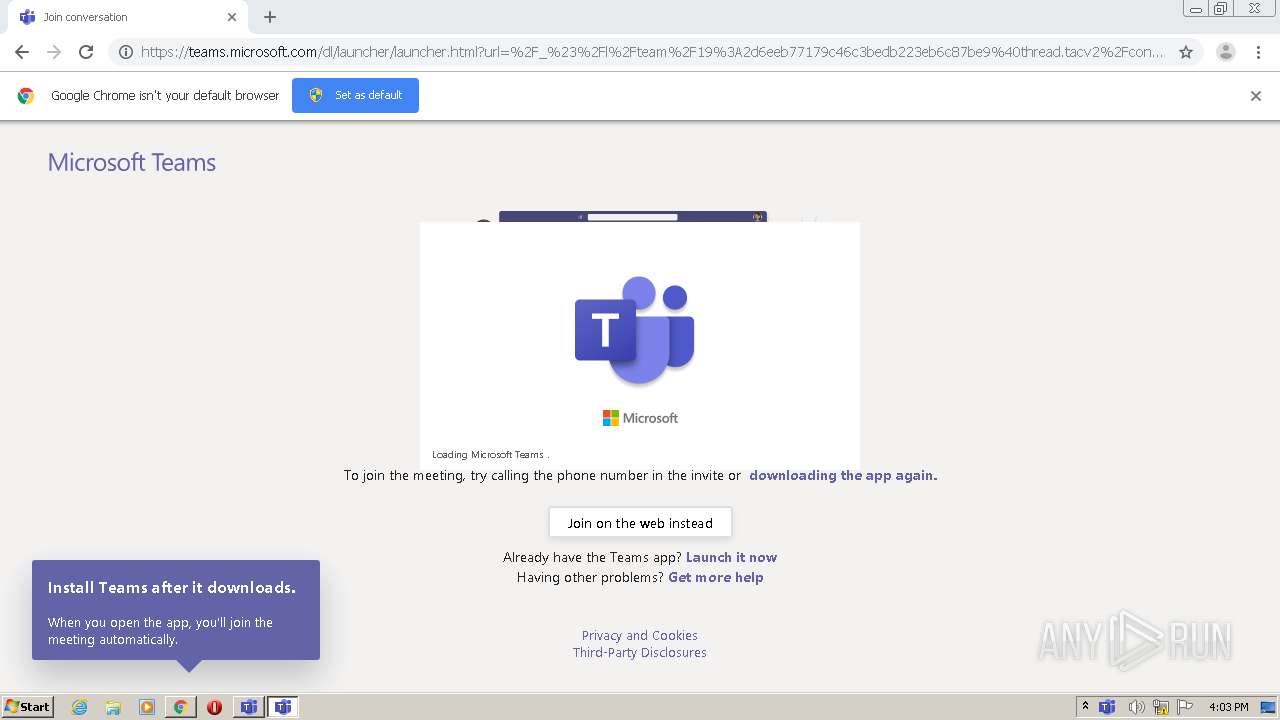
Application was dropped or rewritten from another process
- Teams_windows_s_8D8501A1903AB4B-7-0_.exe (PID: 2488)
- Update.exe (PID: 1668)
- Update.exe (PID: 1856)
- Squirrel.exe (PID: 2844)
Loads dropped or rewritten executable
- Teams.exe (PID: 1572)
- Teams.exe (PID: 1560)
- regsvr32.exe (PID: 3268)
- Teams.exe (PID: 2824)
- Teams.exe (PID: 3044)
- Teams.exe (PID: 3536)
- Teams.exe (PID: 2532)
- Teams.exe (PID: 1528)
Changes the autorun value in the registry
- Teams.exe (PID: 1560)
Registers / Runs the DLL via REGSVR32.EXE
- Update.exe (PID: 1668)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 1340)
- Teams_windows_s_8D8501A1903AB4B-7-0_.exe (PID: 2488)
- Update.exe (PID: 1668)
- Squirrel.exe (PID: 2844)
Creates files in the user directory
- Update.exe (PID: 1668)
- Teams.exe (PID: 1572)
- Teams.exe (PID: 1560)
- Update.exe (PID: 1856)
Reads CPU info
- Teams.exe (PID: 1572)
- Teams.exe (PID: 1560)
Reads Environment values
- Update.exe (PID: 1668)
- Squirrel.exe (PID: 2844)
- Update.exe (PID: 1856)
Application launched itself
- Teams.exe (PID: 1572)
- Teams.exe (PID: 1560)
Modifies the open verb of a shell class
- Teams.exe (PID: 1560)
Creates COM task schedule object
- regsvr32.exe (PID: 3268)
Reads internet explorer settings
- Teams.exe (PID: 1560)
Reads Internet Cache Settings
- Teams.exe (PID: 1560)
Creates a software uninstall entry
- Update.exe (PID: 1668)
INFO
Reads the hosts file
- chrome.exe (PID: 2252)
- chrome.exe (PID: 1340)
- Teams.exe (PID: 1572)
- Teams.exe (PID: 1560)
Reads settings of System Certificates
- chrome.exe (PID: 1340)
- chrome.exe (PID: 2252)
- Update.exe (PID: 1668)
- Teams.exe (PID: 1560)
- Squirrel.exe (PID: 2844)
Application launched itself
- chrome.exe (PID: 1340)
Reads Internet Cache Settings
- chrome.exe (PID: 1340)
- chrome.exe (PID: 2252)
Reads Microsoft Office registry keys
- Update.exe (PID: 1668)
- Update.exe (PID: 1856)
- Squirrel.exe (PID: 2844)
Modifies the open verb of a shell class
- chrome.exe (PID: 1340)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
67
Monitored processes
26
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://teams.microsoft.com/l/team/19:2d6eeb77179c46c3bedb223eb6c87be9%40thread.tacv2/conversations?tenantId=a053d4d7-54c9-4d58-989d-0fe020756234" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1528 | "C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe" --type=gpu-process --enable-features=SharedArrayBuffer --disable-features=SpareRendererForSitePerProcess --no-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --use-gl=swiftshader-webgl --service-request-channel-token=11547660221872069098 --mojo-platform-channel-handle=1660 /prefetch:2 | C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe | — | Teams.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 4 Version: 1.3.00.21759 Modules
| |||||||||||||||
| 1560 | "C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe" --squirrel-firstrun | C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe | Update.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 0 Version: 1.3.00.21759 Modules
| |||||||||||||||
| 1572 | "C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe" --squirrel-install 1.3.00.21759 | C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe | — | Update.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 0 Version: 1.3.00.21759 Modules
| |||||||||||||||
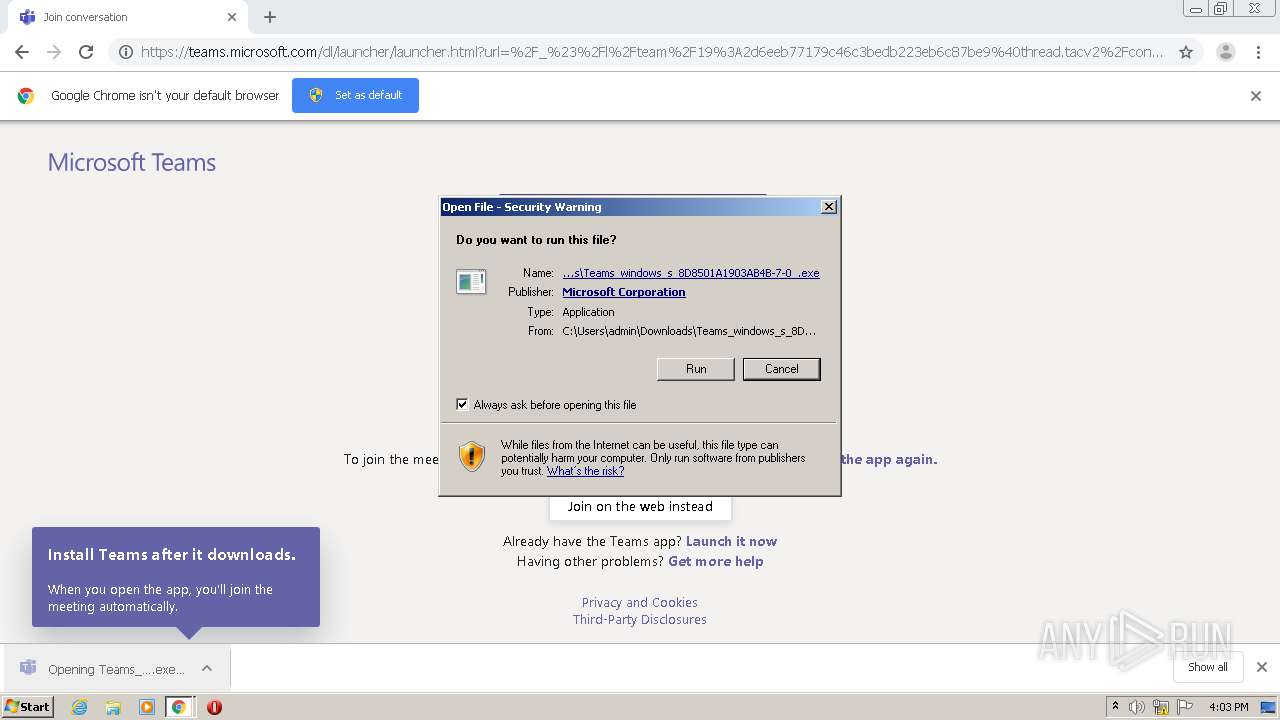
| 1668 | "C:\Users\admin\AppData\Local\SquirrelTemp\Update.exe" --install . --exeName=Teams_windows_s_8D8501A1903AB4B-7-0_.exe | C:\Users\admin\AppData\Local\SquirrelTemp\Update.exe | Teams_windows_s_8D8501A1903AB4B-7-0_.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 0 Version: 1.10.52.0 Modules
| |||||||||||||||
| 1856 | C:\Users\admin\AppData\Local\Microsoft\Teams\Update.exe --createShortcut=Teams.exe -l=StartMenu,Desktop | C:\Users\admin\AppData\Local\Microsoft\Teams\Update.exe | Teams.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 0 Version: 1.10.52.0 Modules
| |||||||||||||||
| 2128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=996,15650354633340513040,3808408301024395834,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12578859807716423909 --mojo-platform-channel-handle=948 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,15650354633340513040,3808408301024395834,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=1951025878416022796 --mojo-platform-channel-handle=1636 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2488 | "C:\Users\admin\Downloads\Teams_windows_s_8D8501A1903AB4B-7-0_.exe" | C:\Users\admin\Downloads\Teams_windows_s_8D8501A1903AB4B-7-0_.exe | chrome.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 0 Version: 1.3.00.21759 Modules
| |||||||||||||||
| 2532 | "C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe" --type=renderer --no-sandbox --autoplay-policy=no-user-gesture-required --enable-features=SharedArrayBuffer --disable-features=SpareRendererForSitePerProcess --service-pipe-token=909784667713478753 --lang=en-US --app-user-model-id=com.squirrel.Teams.Teams --app-path="C:\Users\admin\AppData\Local\Microsoft\Teams\current\resources\app.asar" --user-agent="Mozilla/5.0 (Windows NT 6.1) AppleWebKit/537.36 (KHTML, like Gecko) Teams/1.3.00.21759 Chrome/69.0.3497.128 Electron/4.2.12 Safari/537.36" --node-integration=false --webview-tag=false --no-sandbox --preload="C:\Users\admin\AppData\Local\Microsoft\Teams\current\resources\app.asar\lib\renderer\preload_default.js" --disable-remote-module --background-color=#FFFFFFFF --electron-shared-settings=eyJjci5jb21wYW55IjoiRWxlY3Ryb24iLCJjci5kdW1wcyI6IiIsImNyLmVuYWJsZWQiOmZhbHNlLCJjci5wcm9kdWN0IjoiRWxlY3Ryb24iLCJjci5zZXNzaW9uIjoiIiwiY3IudXJsIjoiIiwiY3IudmVyc2lvbiI6InY0LjIuMTIifQ== --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=909784667713478753 --renderer-client-id=5 --mojo-platform-channel-handle=1460 /prefetch:1 --msteams-process-type=loadingWindow | C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe | — | Teams.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 0 Version: 1.3.00.21759 Modules
| |||||||||||||||
Total events
4 512
Read events
4 120
Write events
383
Delete events
9
Modification events
| (PID) Process: | (1340) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1340) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1340-13243618880070500 |
Value: 259 | |||
| (PID) Process: | (1340) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1340) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1340) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1340) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1340) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1340) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (1340) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
477
Suspicious files
39
Text files
293
Unknown types
77
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1340 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1340 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF15c8b8.TMP | — | |
MD5:— | SHA256:— | |||
| 1340 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ee51475f-5177-4e73-b73e-d0dce72b614e.tmp | — | |
MD5:— | SHA256:— | |||
| 1340 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1340 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1340 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1340 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF15c87a.TMP | text | |
MD5:— | SHA256:— | |||
| 1340 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1340 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF15ca20.TMP | — | |
MD5:— | SHA256:— | |||
| 1340 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
47
DNS requests
34
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1560 | Teams.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQQX6Z6gAidtSefNc6DC0OInqPHDQQUD4BhHIIxYdUvKOeNRji0LOHG2eICEA%2B5ylAxuaJUFGxDNYWKi2s%3D | US | der | 471 b | whitelisted |
1560 | Teams.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
1560 | Teams.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAi4elAbvpzaLRZNPjlRv1U%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
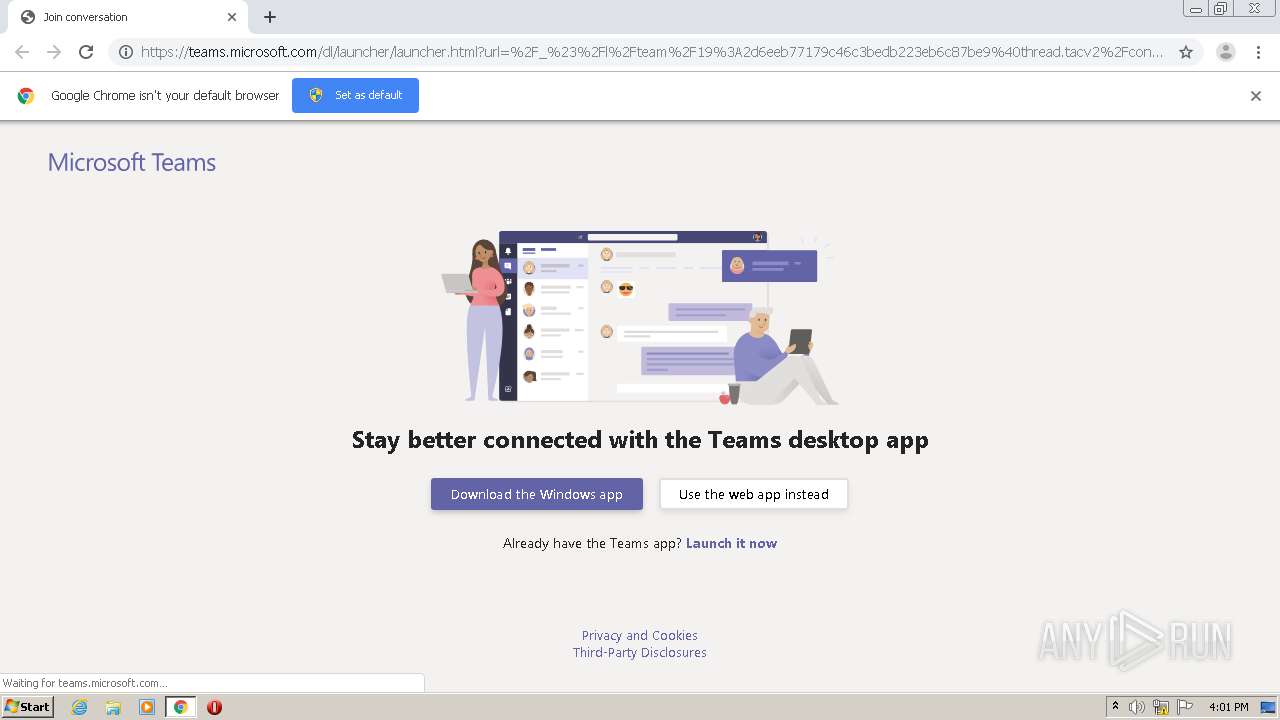
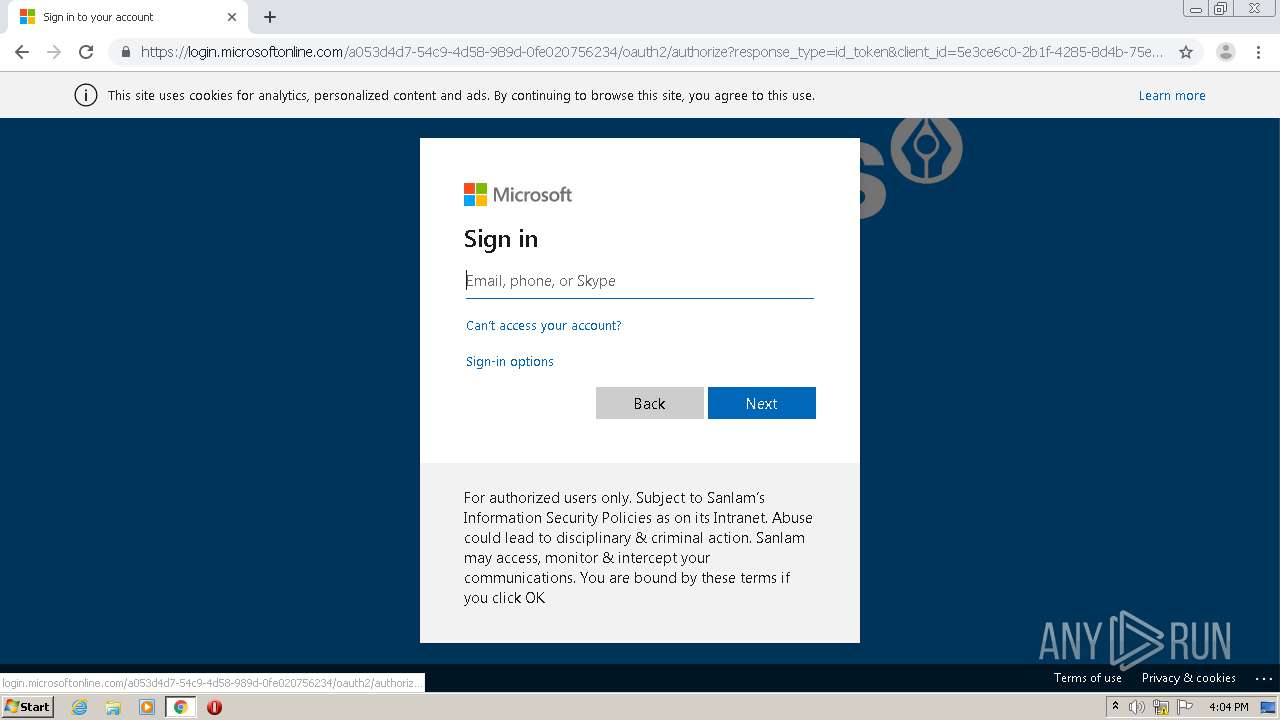
2252 | chrome.exe | 52.113.194.132:443 | teams.microsoft.com | Microsoft Corporation | US | suspicious |
2252 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2252 | chrome.exe | 152.199.19.160:443 | az725175.vo.msecnd.net | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2252 | chrome.exe | 2.16.177.112:443 | statics.teams.cdn.office.net | Akamai International B.V. | — | unknown |
2252 | chrome.exe | 216.58.208.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
2252 | chrome.exe | 40.77.226.250:443 | web.vortex.data.microsoft.com | Microsoft Corporation | IE | whitelisted |
— | — | 172.217.16.174:443 | clients1.google.com | Google Inc. | US | whitelisted |
1856 | Update.exe | 168.62.58.130:443 | mobile.pipe.aria.microsoft.com | Microsoft Corporation | US | unknown |
1560 | Teams.exe | 52.113.194.132:443 | teams.microsoft.com | Microsoft Corporation | US | suspicious |
1560 | Teams.exe | 52.113.194.131:443 | urlshortener.teams.microsoft.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
teams.microsoft.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
statics.teams.microsoft.com |
| whitelisted |
statics.teams.cdn.office.net |
| whitelisted |
az725175.vo.msecnd.net |
| whitelisted |
clients2.google.com |
| whitelisted |
web.vortex.data.microsoft.com |
| whitelisted |
browser.pipe.aria.microsoft.com |
| whitelisted |
www.google.com |
| malicious |
Threats
Process | Message |
|---|---|
Update.exe | Starting TelemetryManager constructor
|
Update.exe | Starting TelemetryManager constructor
|
Update.exe | TelemetryManagerImpl creation started
|
Update.exe | TelemetryManagerImpl creation started
|
Update.exe | Performance counters are disabled. Skipping creation of counters category.
|
Update.exe | Update.exe Information: 0 : |
Update.exe | RecordBatcherTask with ID 4 started.
|
Update.exe | Update.exe Information: 0 : |
Update.exe | DataPackageSender with UserAgent name: AST-exe-C#, version: 1.10.52.0, [Ast_Default_Source]
|
Update.exe | Update.exe Information: 0 : |