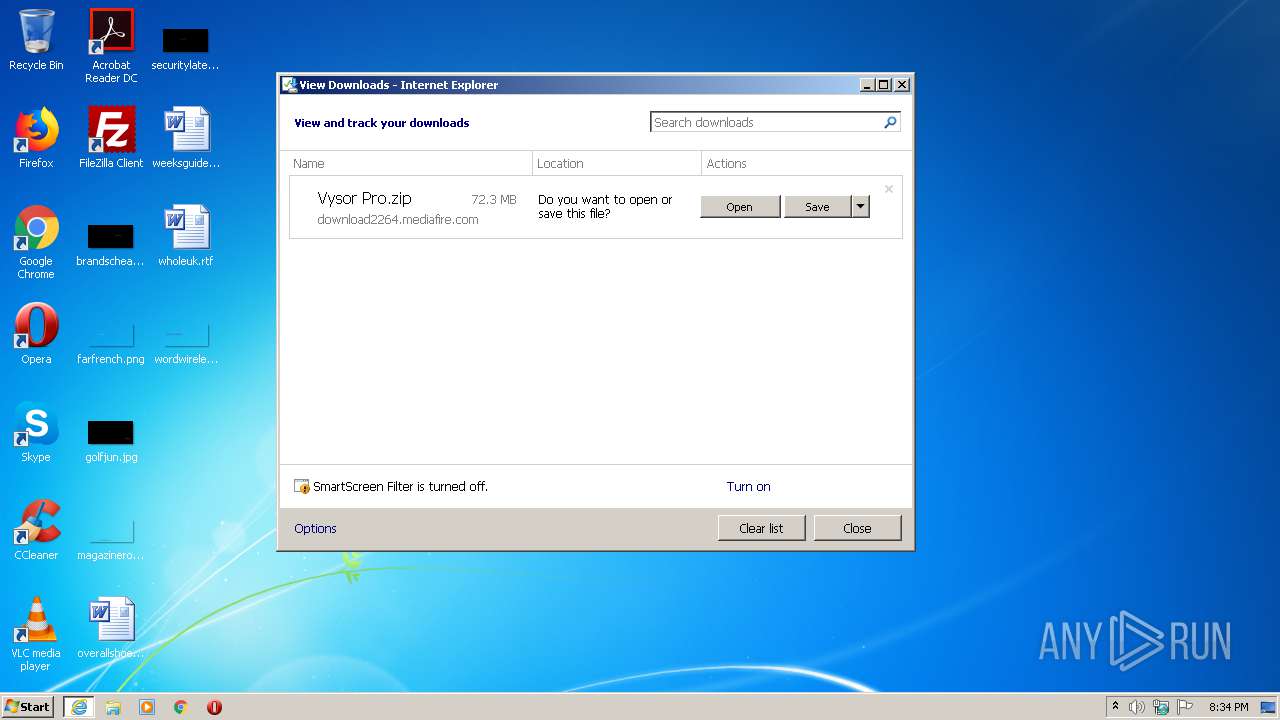
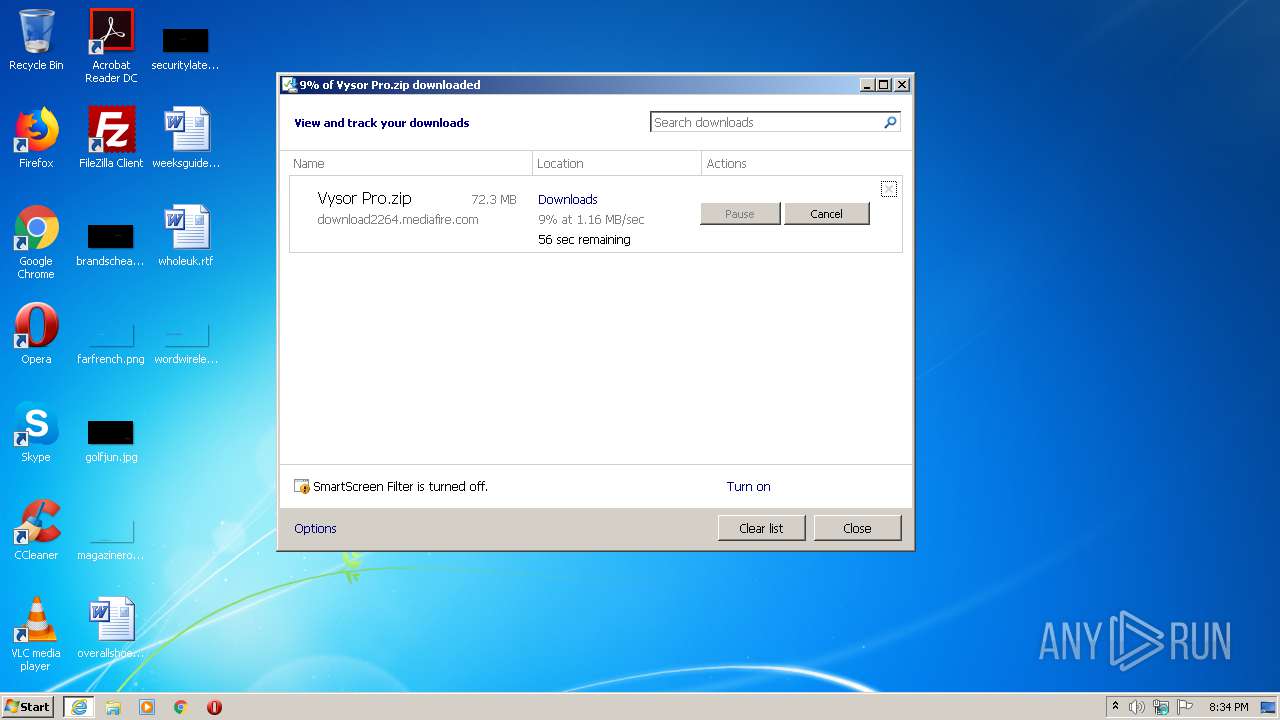
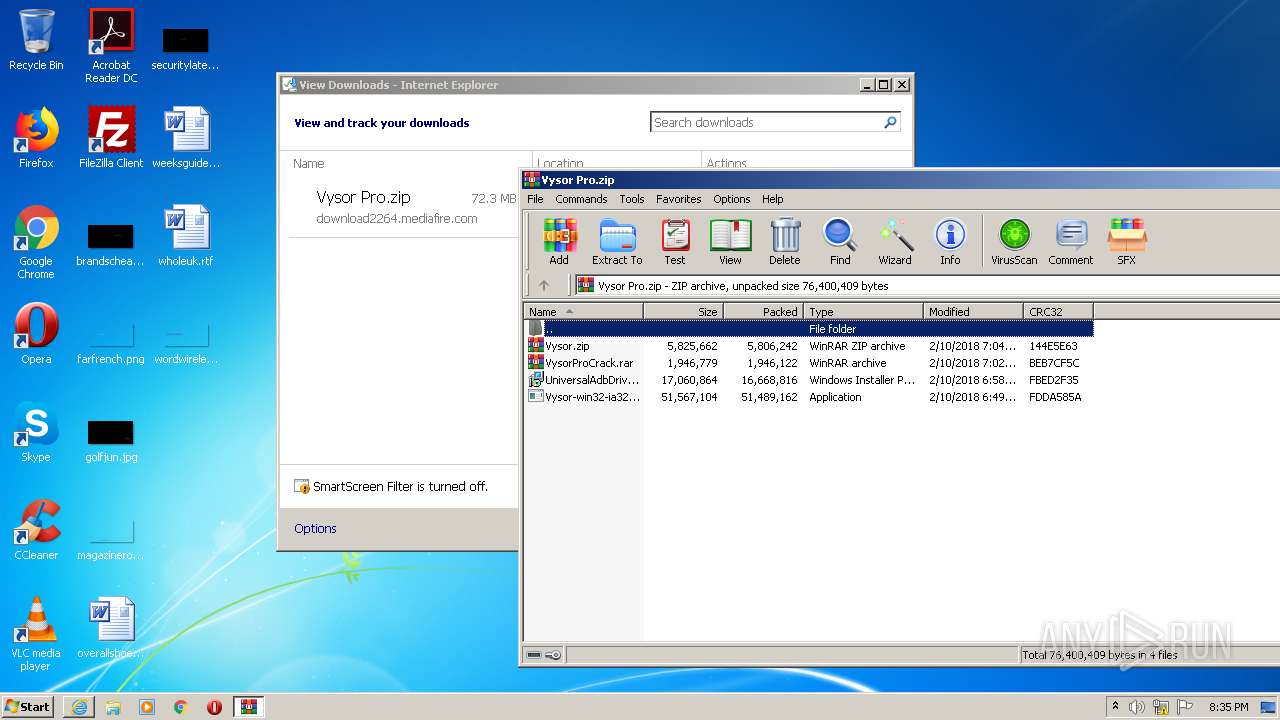
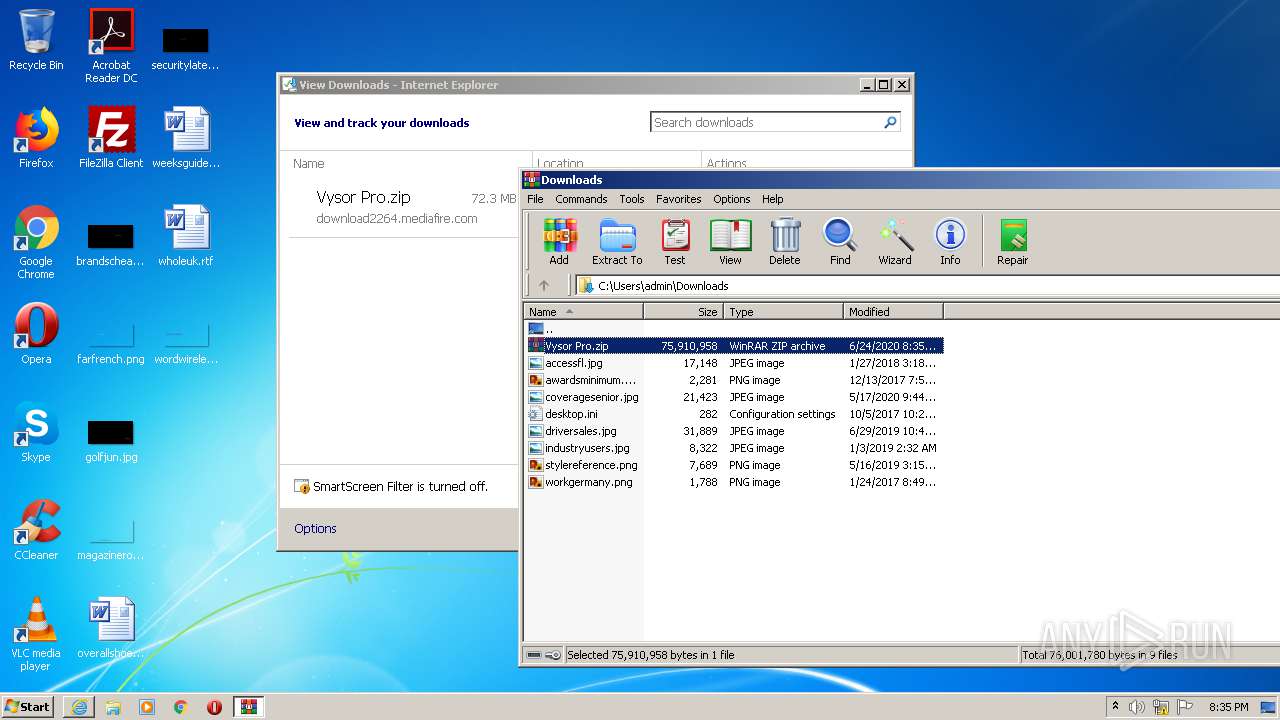
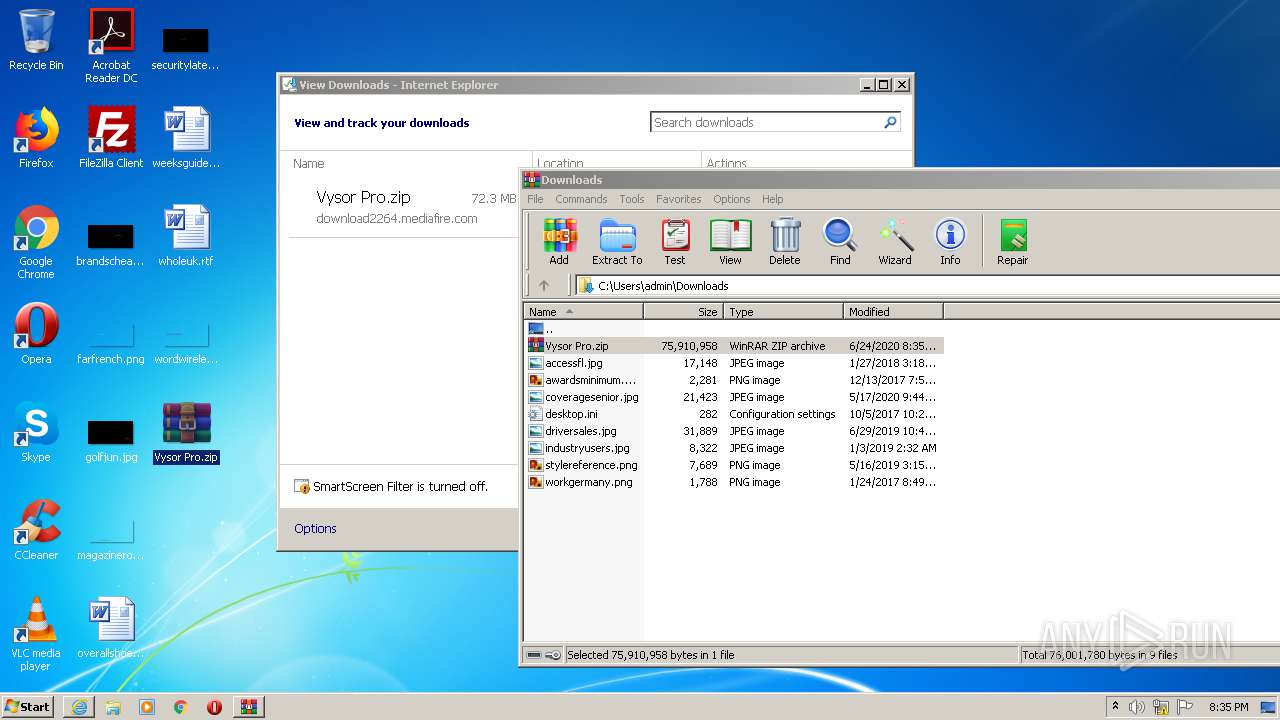
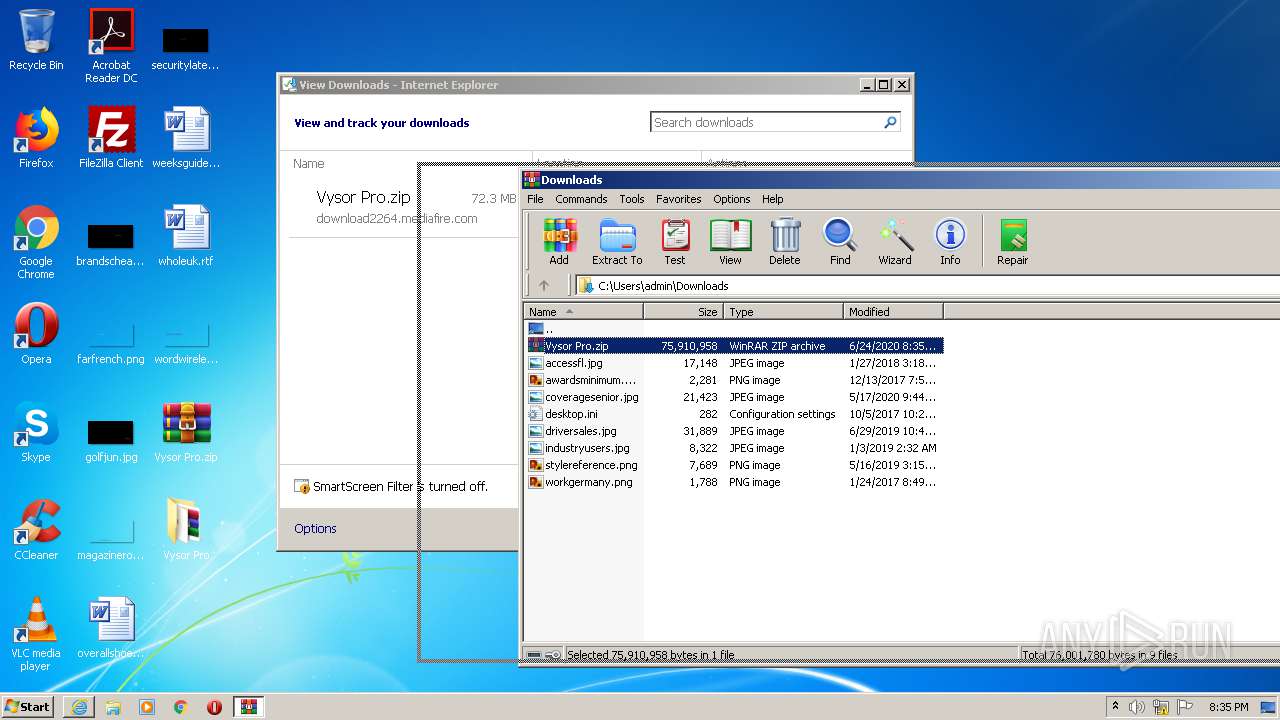
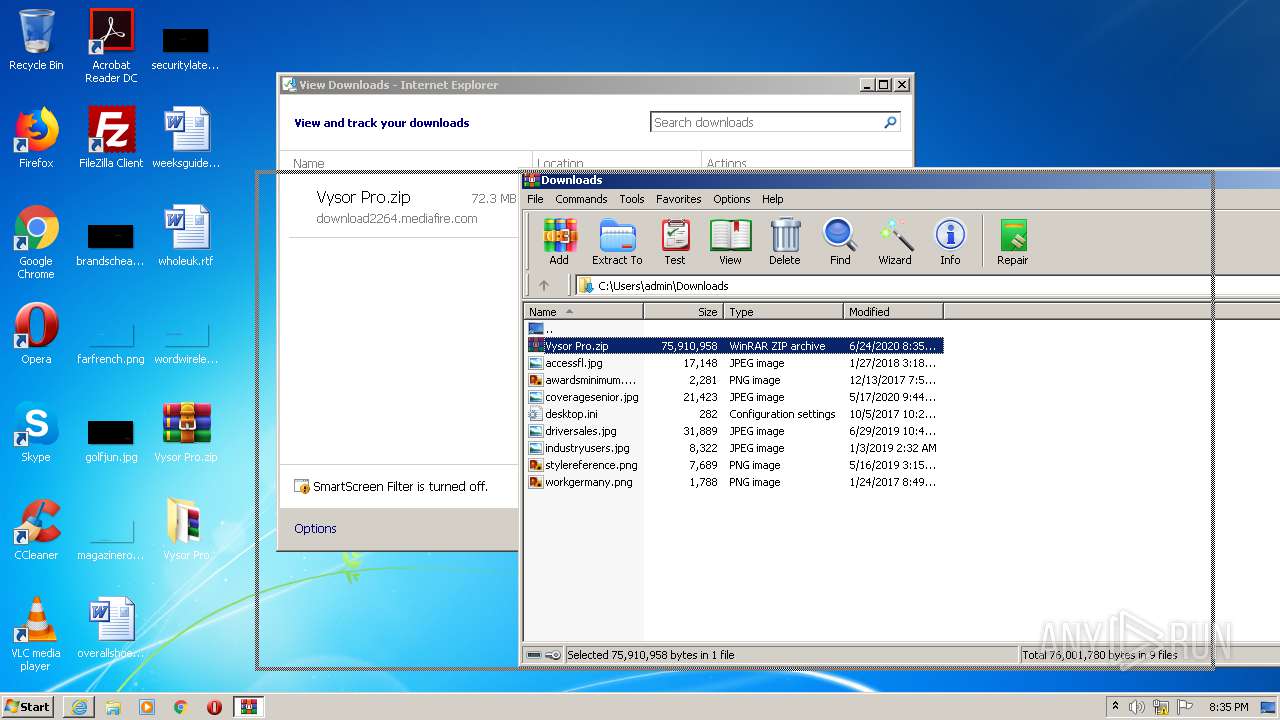
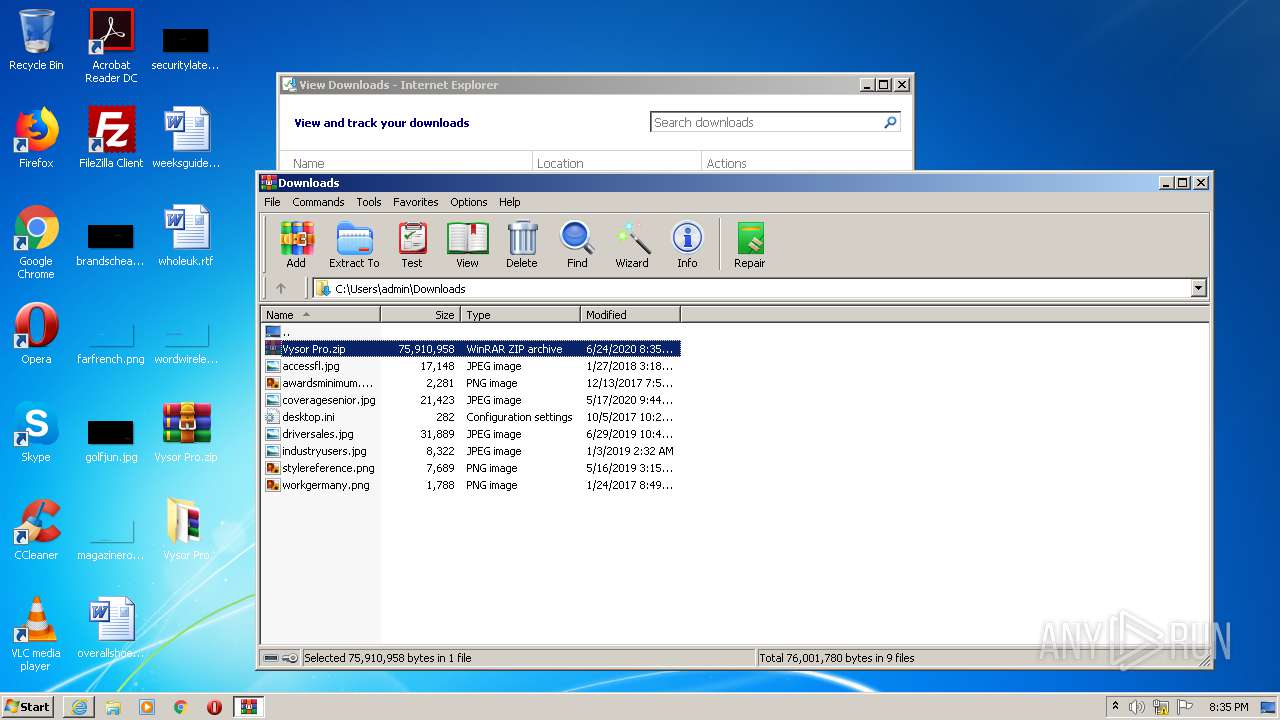
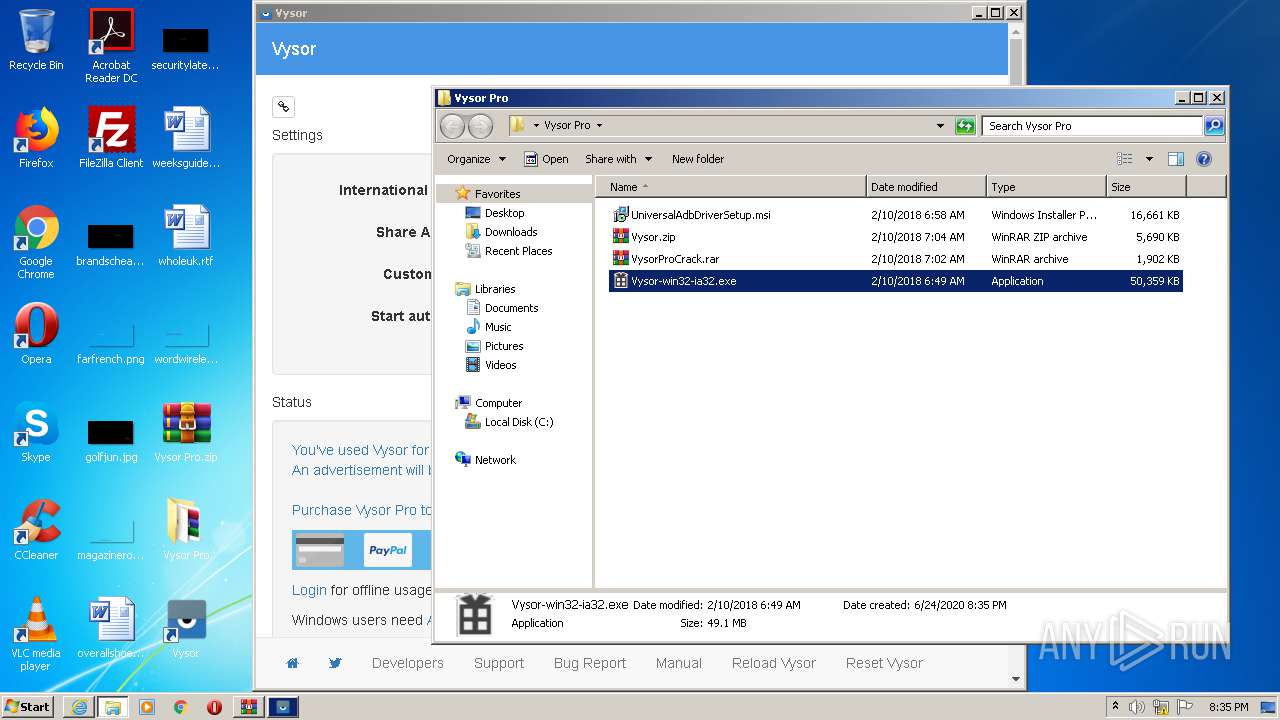
| URL: | http://download2264.mediafire.com/utnfv9sxk9yg/z5767tc18tx5irf/Vysor+Pro.zip |
| Full analysis: | https://app.any.run/tasks/f794aed8-f3ae-4799-b44c-9dbe4c414c42 |
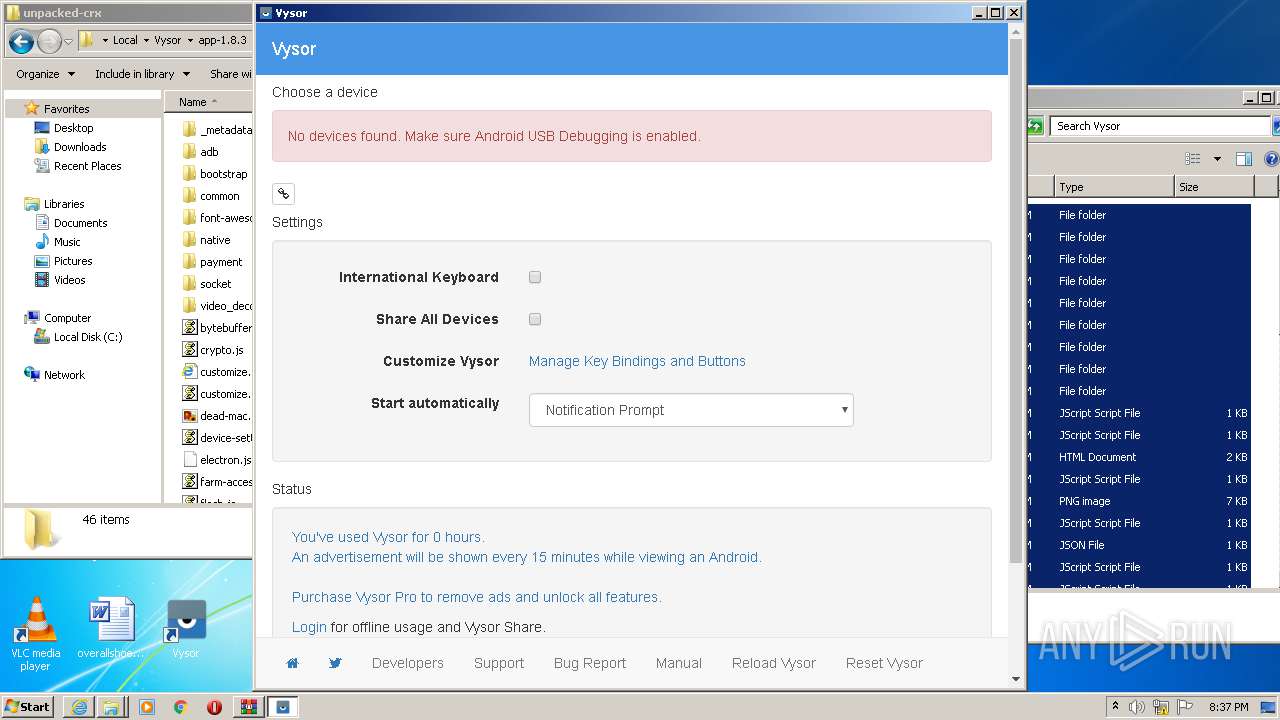
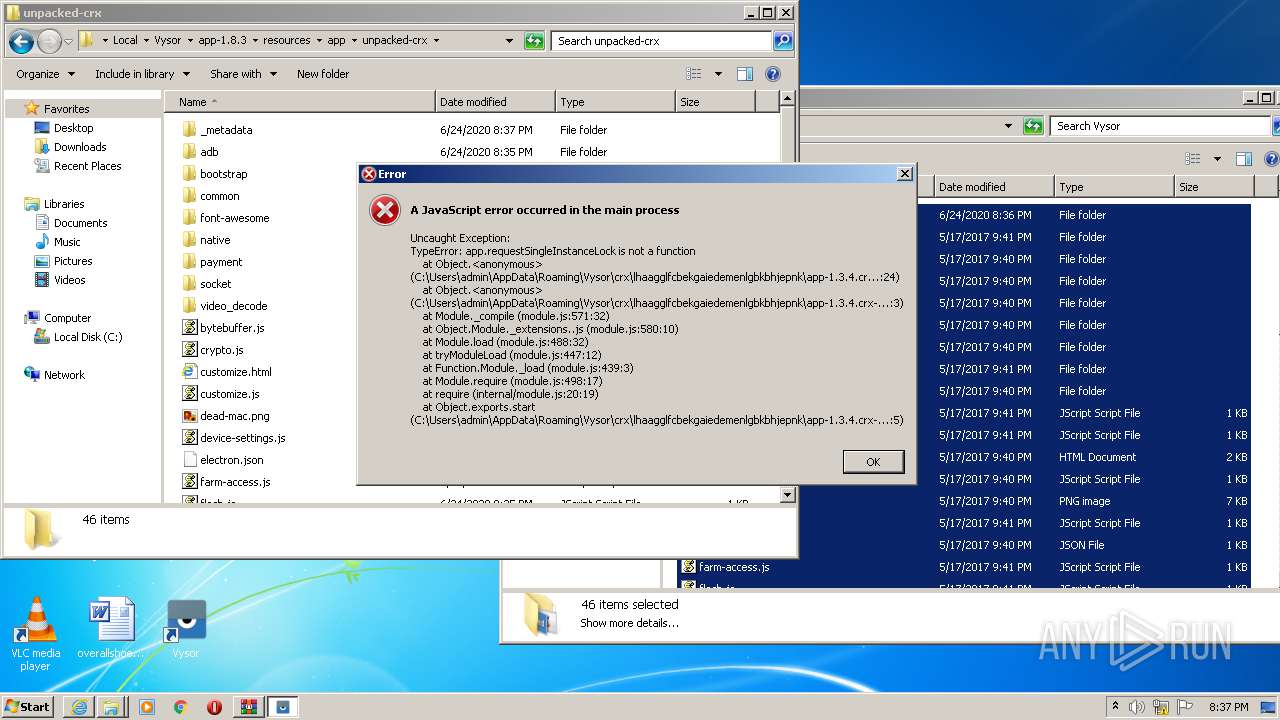
| Verdict: | Malicious activity |
| Analysis date: | June 24, 2020, 19:33:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7CBCDDB602780DCCBB4247CB1E4C9D07 |
| SHA1: | 83CBA2BBC35A768E5159FDDA13A7CDF66710BA16 |
| SHA256: | 5A182A31A53312C997557F53EE0679B4A9D73AF73961BC59260D58A253F9928C |
| SSDEEP: | 3:N1KaKE5BM3eGHqwhZDvUn:CalBSeGH1ZDvUn |
MALICIOUS
Application was dropped or rewritten from another process
- Update.exe (PID: 1536)
- Squirrel.exe (PID: 1288)
- Update.exe (PID: 3132)
- Update.exe (PID: 2924)
- Update.exe (PID: 2536)
- Update.exe (PID: 2780)
- adb.exe (PID: 3008)
- adb.exe (PID: 2084)
- Update.exe (PID: 2808)
- Update.exe (PID: 3264)
- Update.exe (PID: 2392)
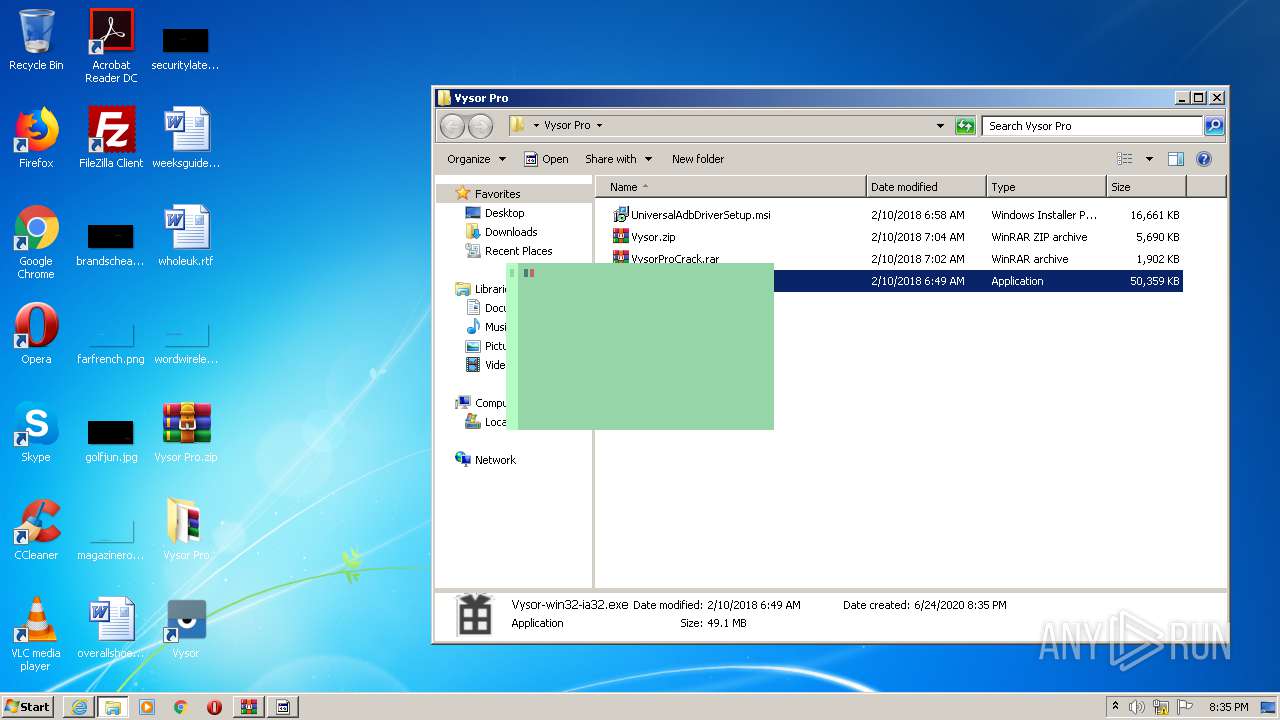
- Vysor.exe (PID: 3100)
- Update.exe (PID: 1844)
Loads dropped or rewritten executable
- Vysor.exe (PID: 1768)
- Vysor.exe (PID: 2372)
- Vysor.exe (PID: 2056)
- Vysor.exe (PID: 500)
- Vysor.exe (PID: 3932)
- adb.exe (PID: 3008)
- adb.exe (PID: 2084)
- Vysor.exe (PID: 1732)
- SearchProtocolHost.exe (PID: 3584)
- Vysor.exe (PID: 3120)
- Vysor.exe (PID: 3388)
- Vysor.exe (PID: 812)
- Vysor.exe (PID: 3004)
- Vysor.exe (PID: 624)
- Vysor.exe (PID: 2672)
- Vysor.exe (PID: 2416)
- Vysor.exe (PID: 3372)
- Vysor.exe (PID: 2100)
- adb.exe (PID: 1928)
- adb.exe (PID: 3364)
- Vysor.exe (PID: 2208)
- Vysor.exe (PID: 2060)
- adb.exe (PID: 2504)
SUSPICIOUS
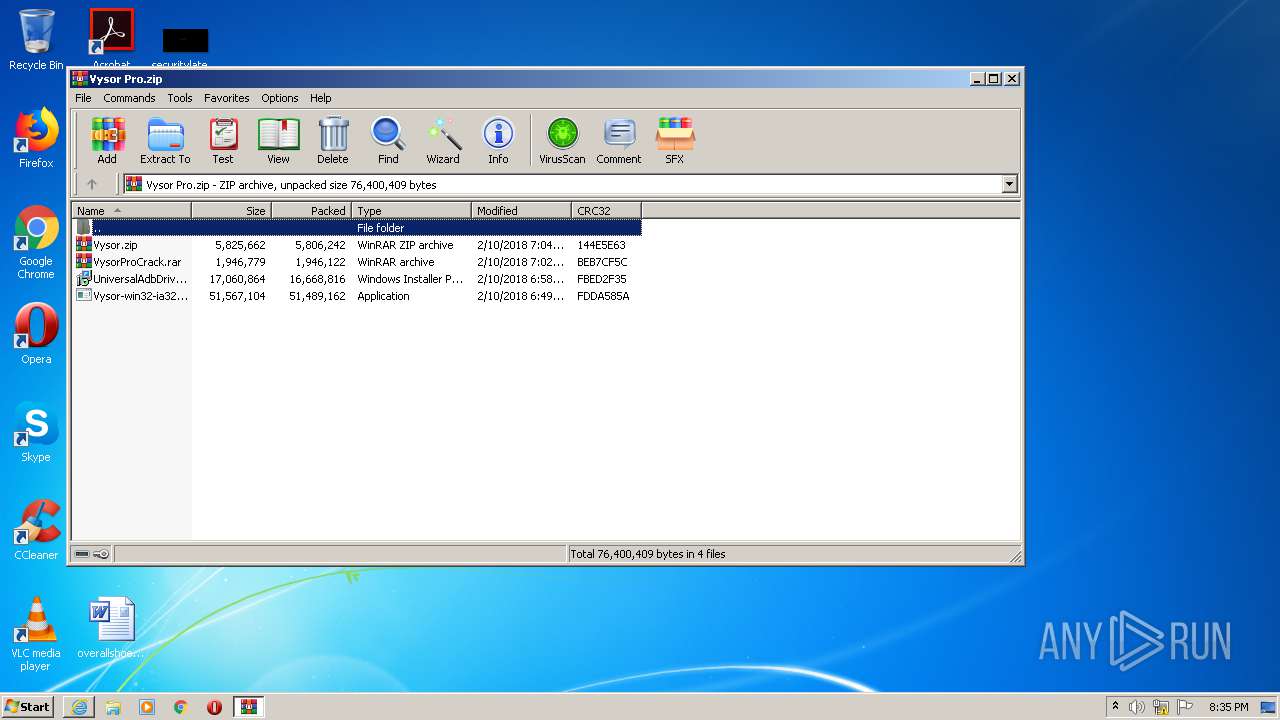
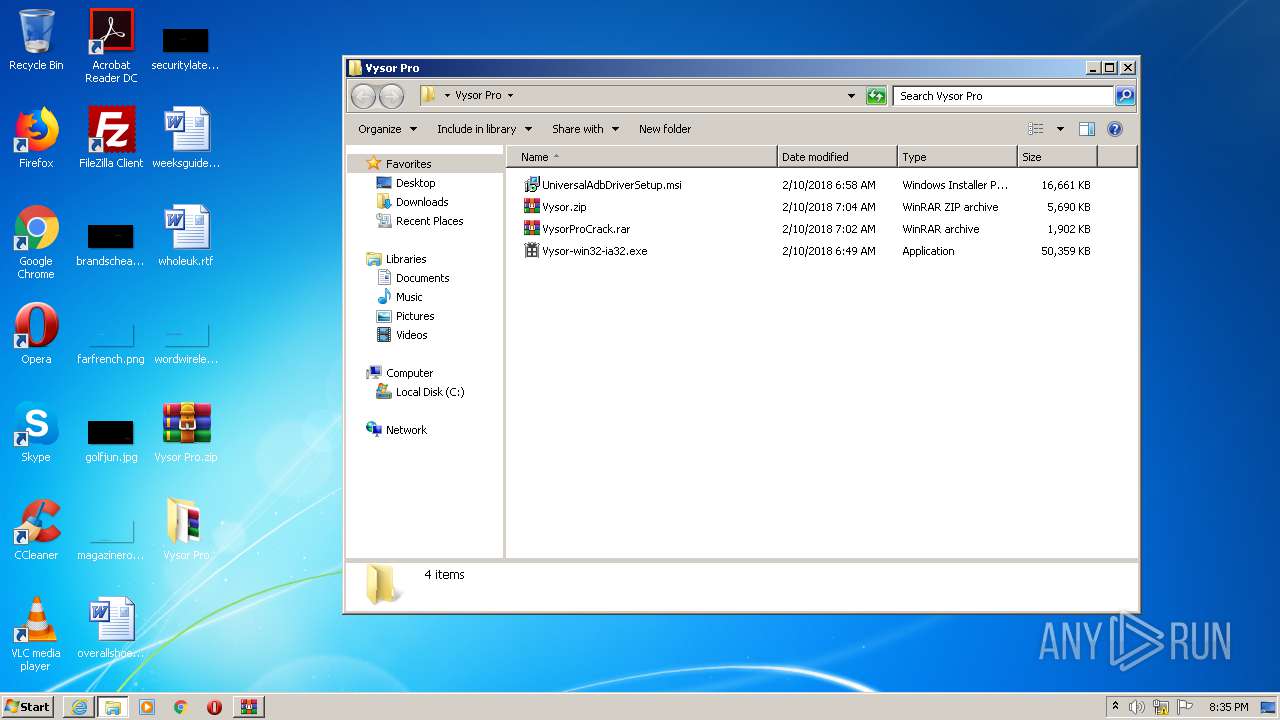
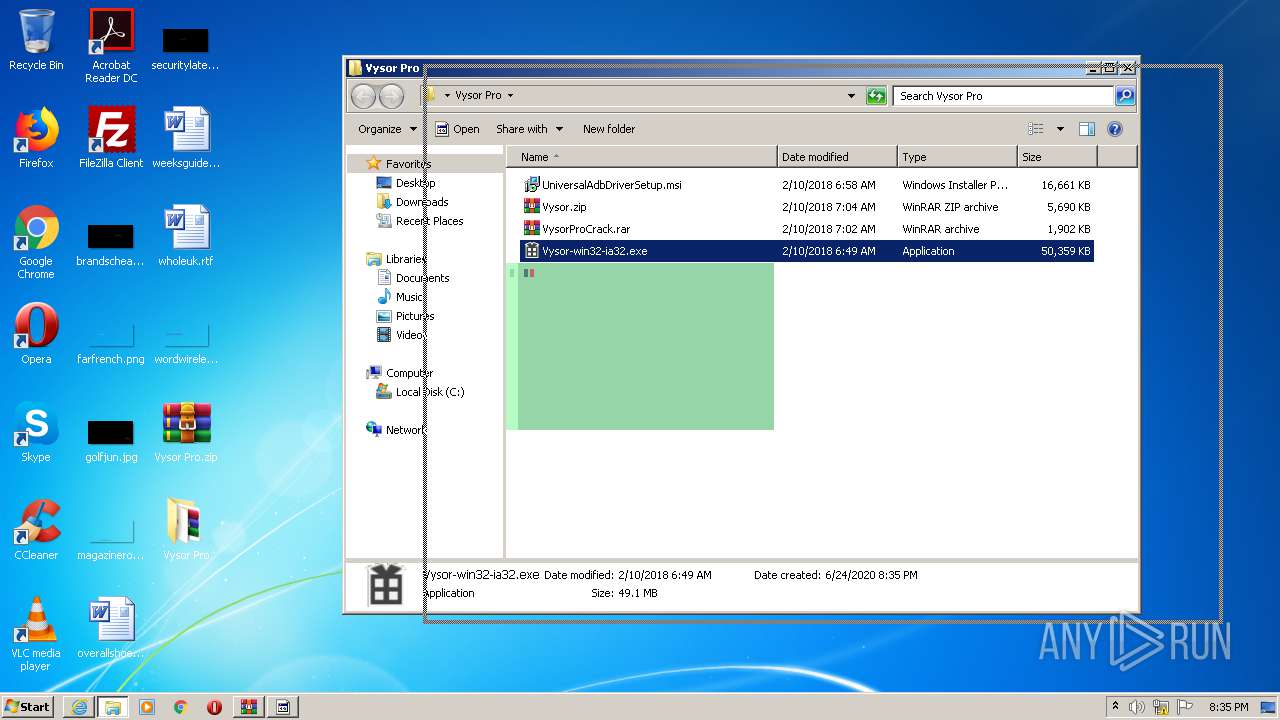
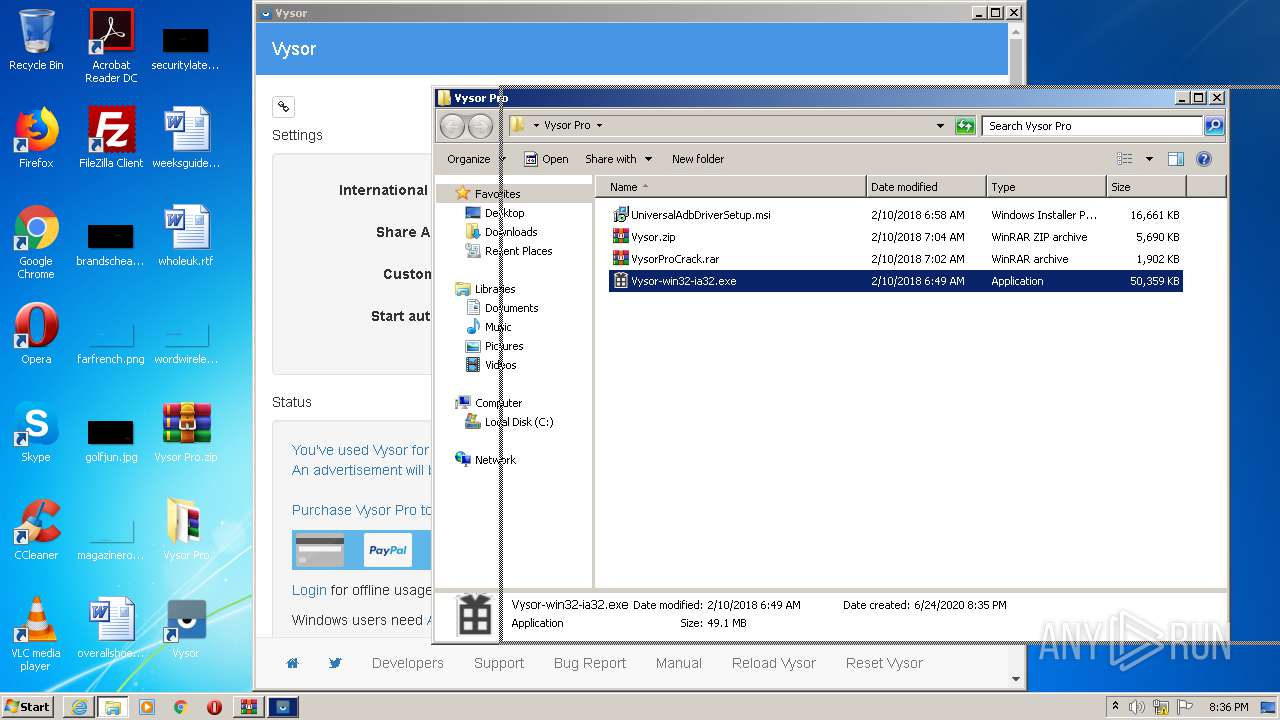
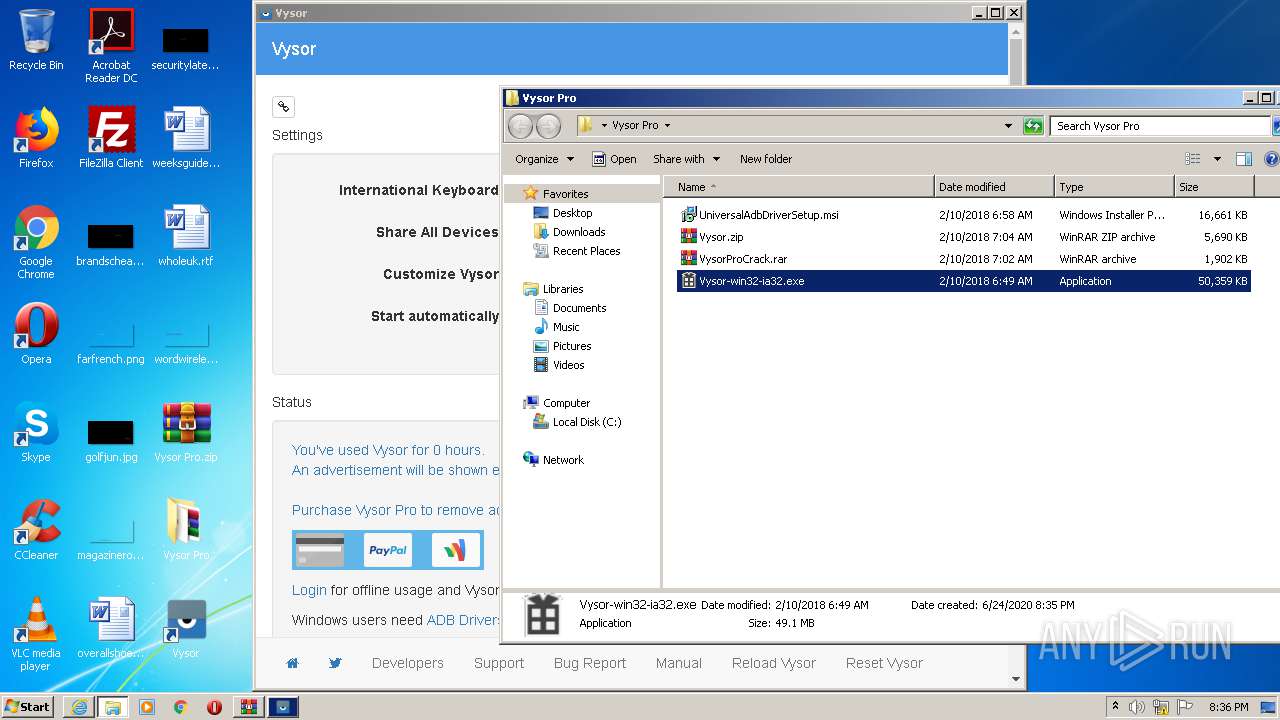
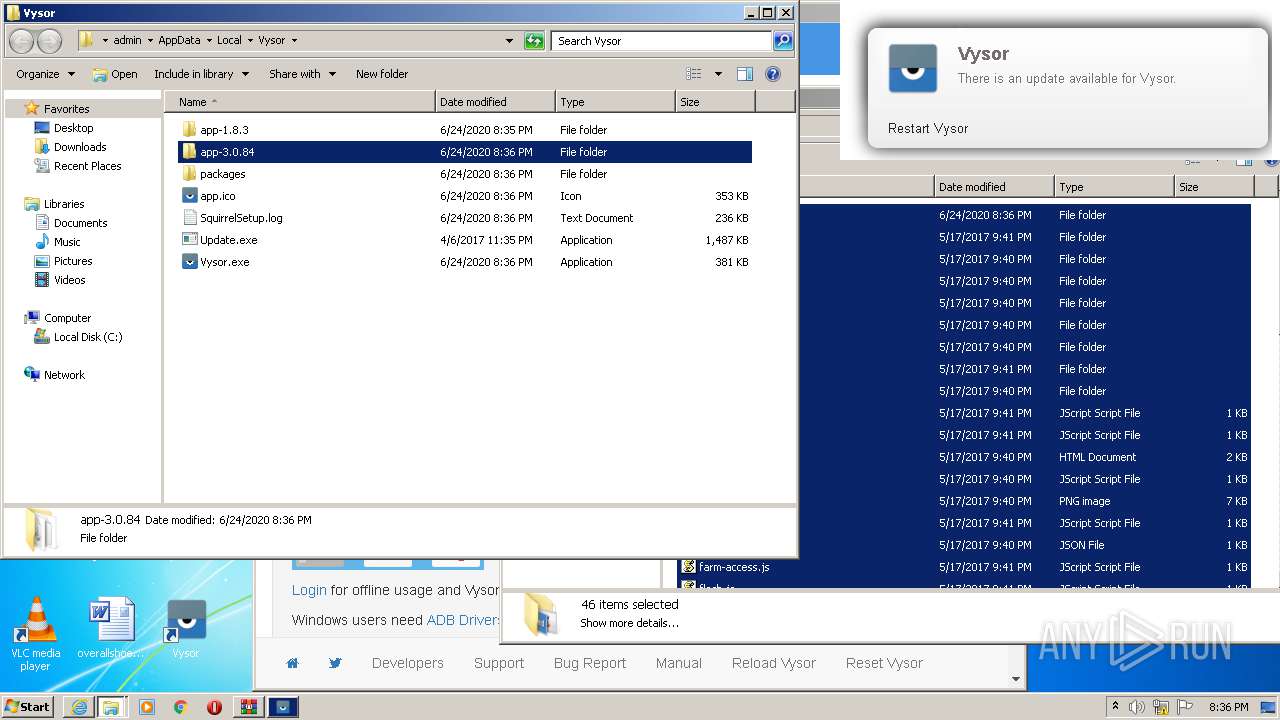
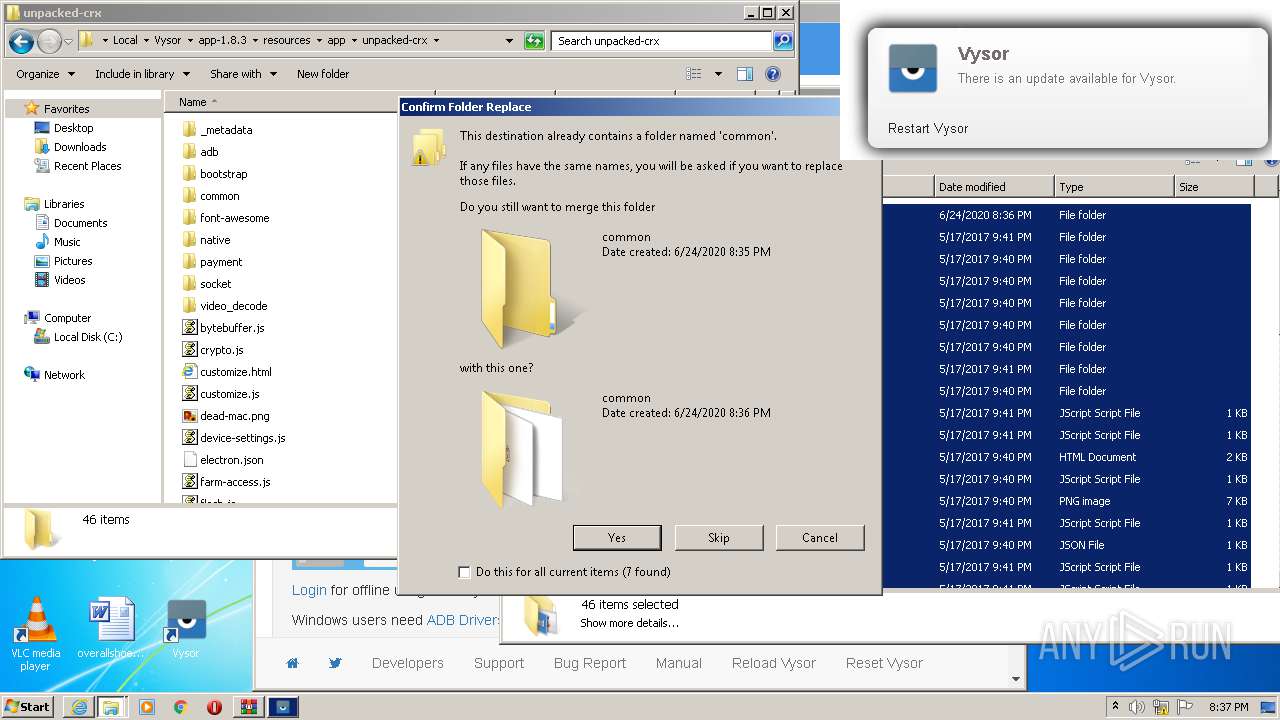
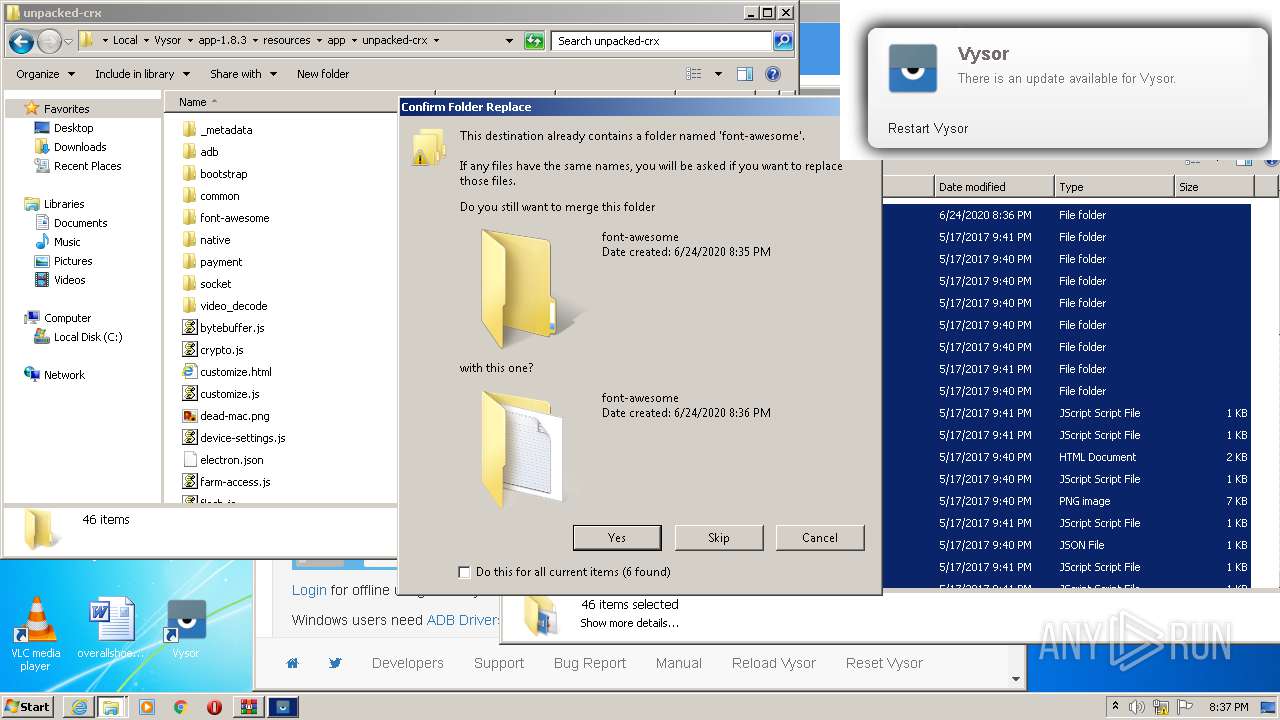
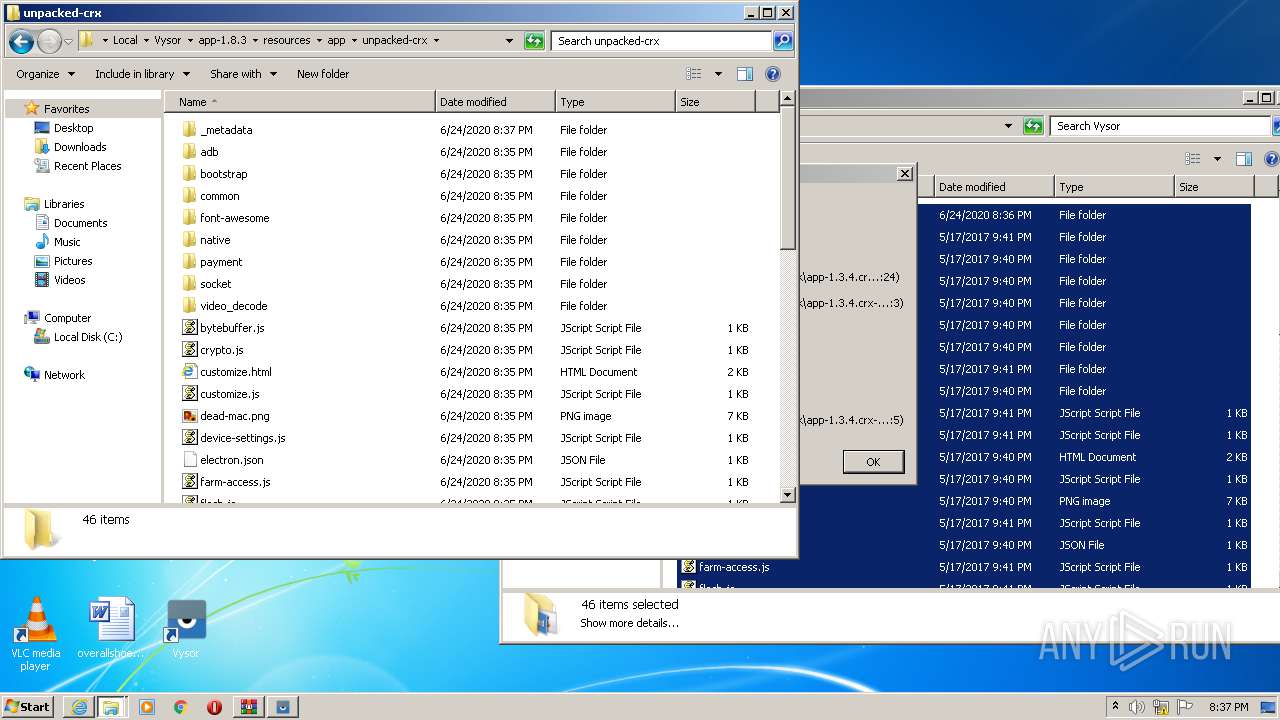
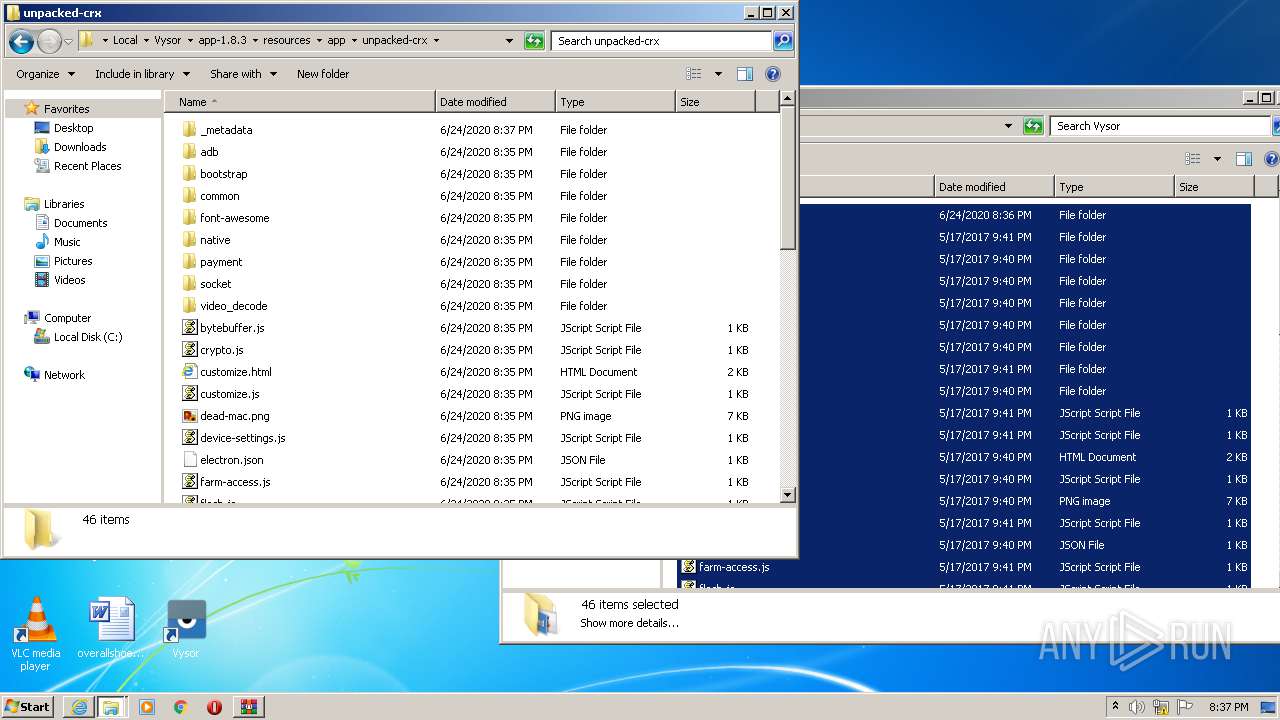
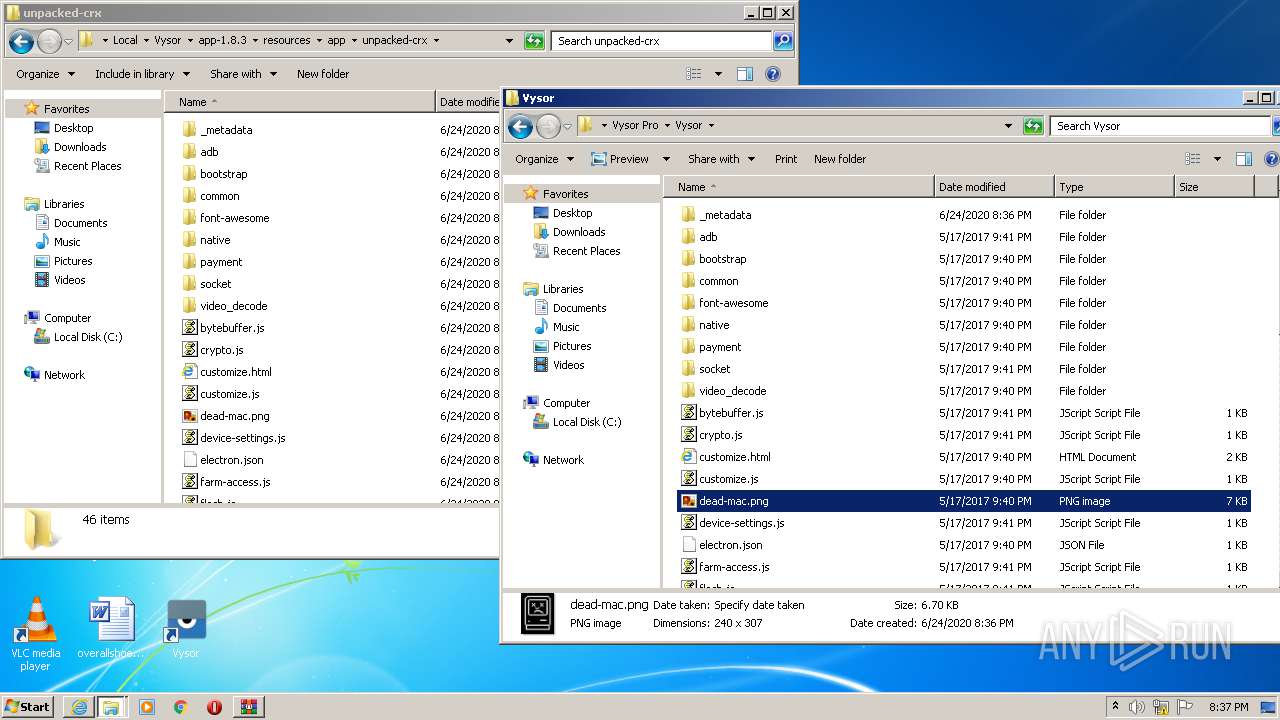
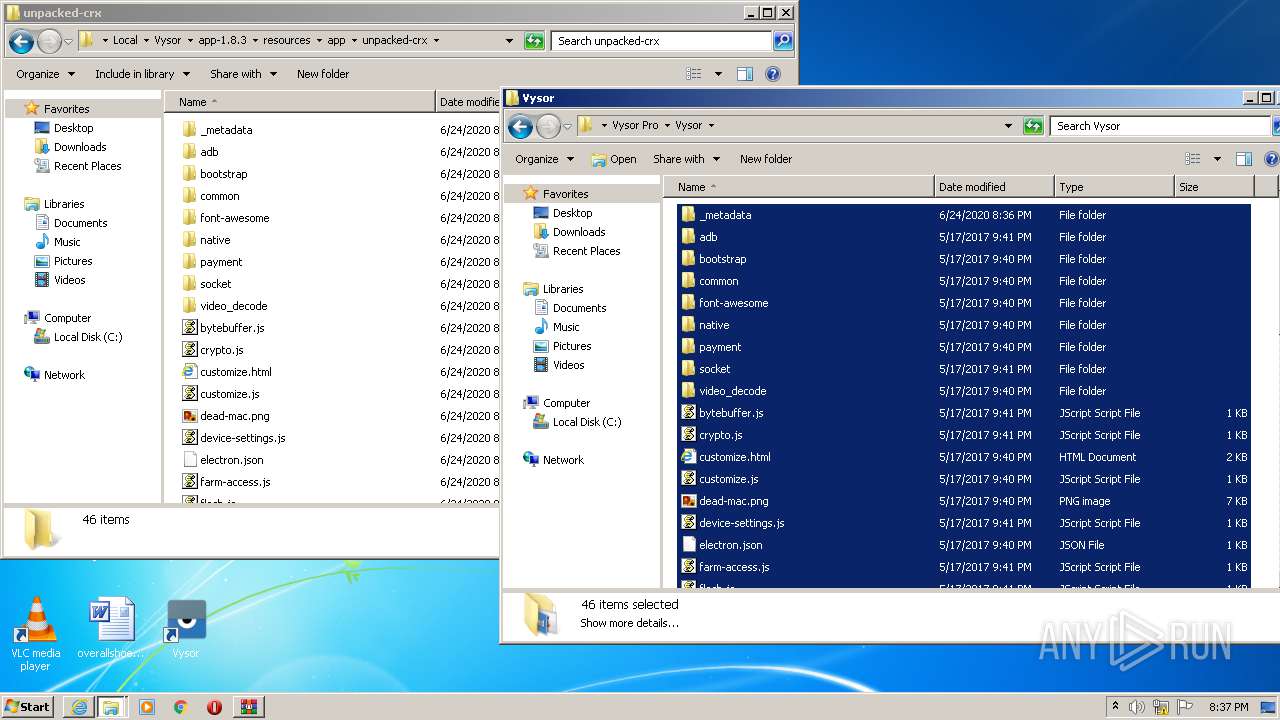
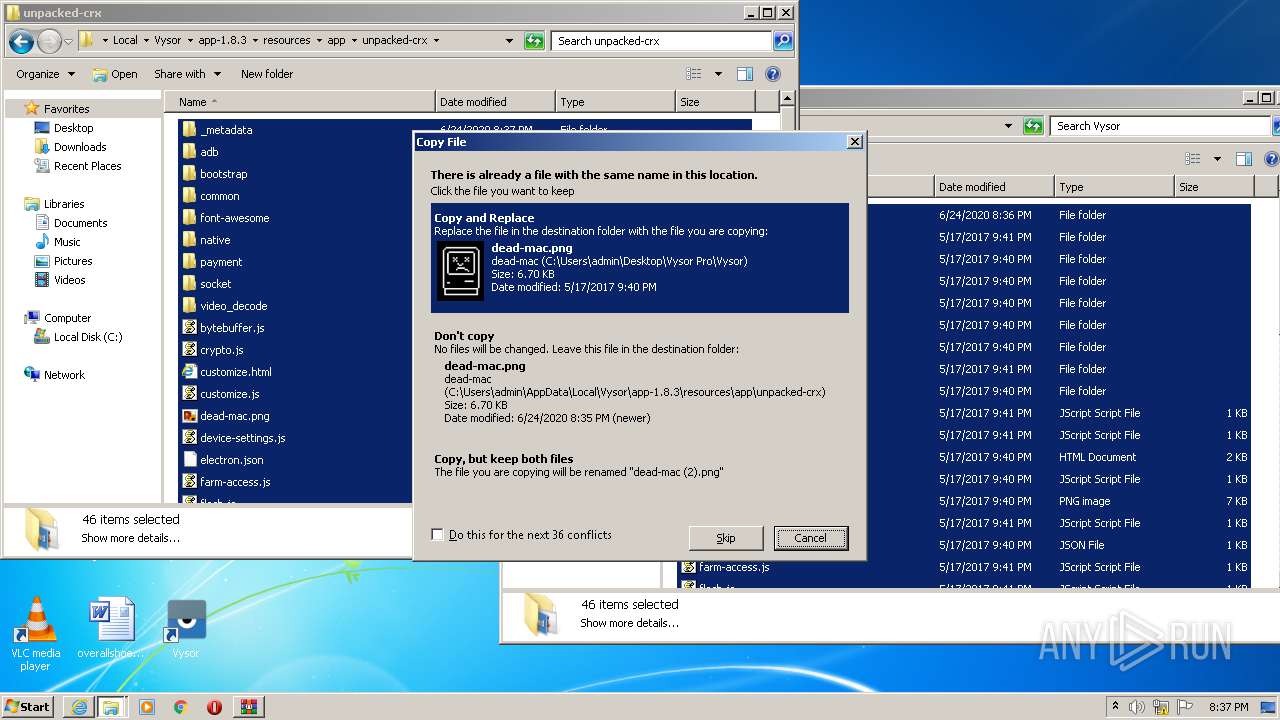
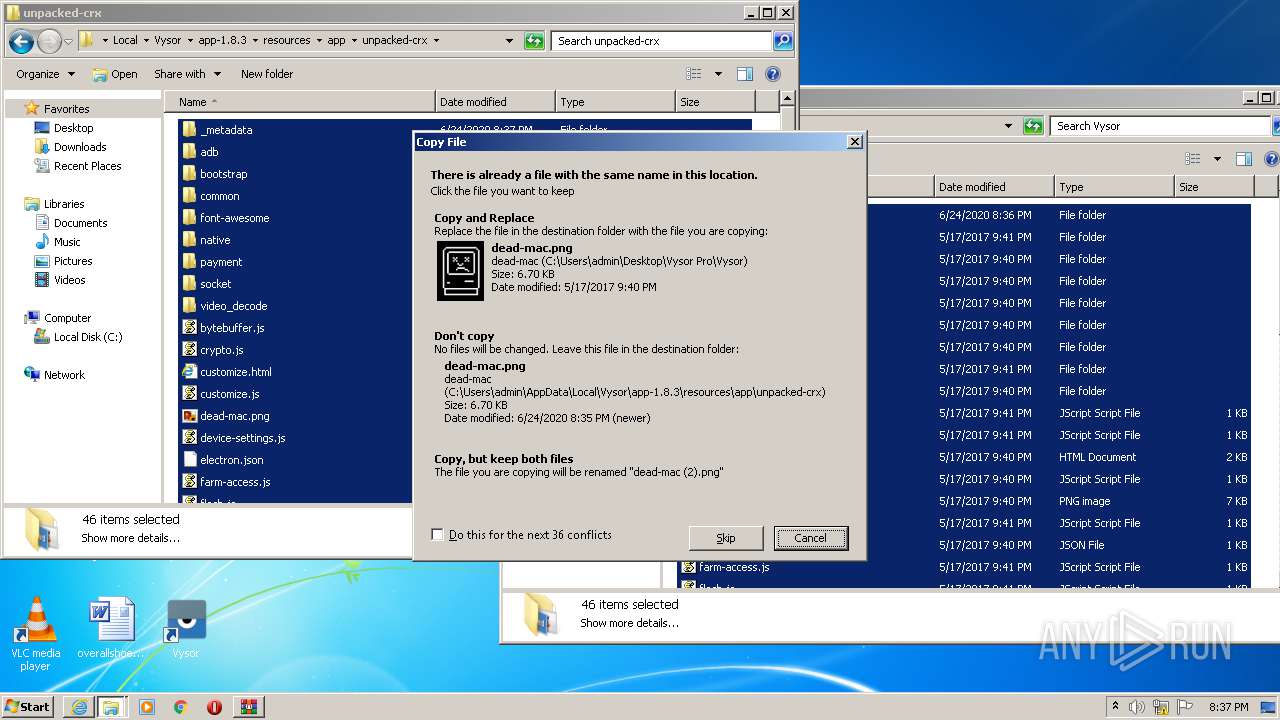
Executable content was dropped or overwritten
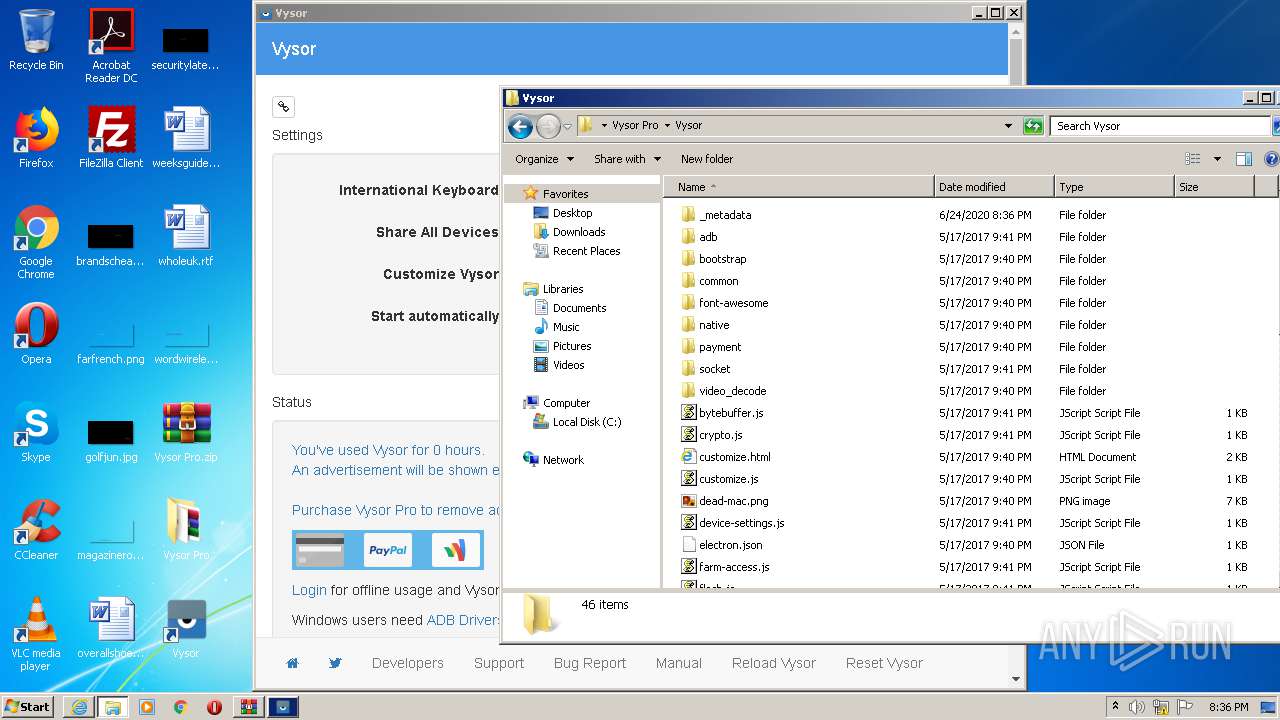
- Vysor-win32-ia32.exe (PID: 2396)
- Update.exe (PID: 1536)
- WinRAR.exe (PID: 2316)
- Update.exe (PID: 2780)
Starts itself from another location
- Update.exe (PID: 1536)
Creates files in the user directory
- Update.exe (PID: 3132)
- Vysor.exe (PID: 2372)
- Vysor.exe (PID: 2056)
Reads Environment values
- Update.exe (PID: 2924)
- Update.exe (PID: 1536)
- Update.exe (PID: 2780)
- Update.exe (PID: 2808)
- Update.exe (PID: 2536)
- Update.exe (PID: 2392)
- Update.exe (PID: 3264)
- Update.exe (PID: 1844)
Application launched itself
- Vysor.exe (PID: 2372)
- adb.exe (PID: 3008)
- Vysor.exe (PID: 812)
- Vysor.exe (PID: 2416)
- Vysor.exe (PID: 3372)
Creates a software uninstall entry
- Update.exe (PID: 1536)
- Update.exe (PID: 2780)
- Update.exe (PID: 2536)
Modifies the open verb of a shell class
- Vysor.exe (PID: 2372)
- Vysor.exe (PID: 812)
- Vysor.exe (PID: 3372)
Searches for installed software
- Update.exe (PID: 2780)
- Update.exe (PID: 2536)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2224)
Reads Internet Cache Settings
- iexplore.exe (PID: 1948)
- iexplore.exe (PID: 2224)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2224)
Application launched itself
- iexplore.exe (PID: 2224)
Creates files in the user directory
- iexplore.exe (PID: 2224)
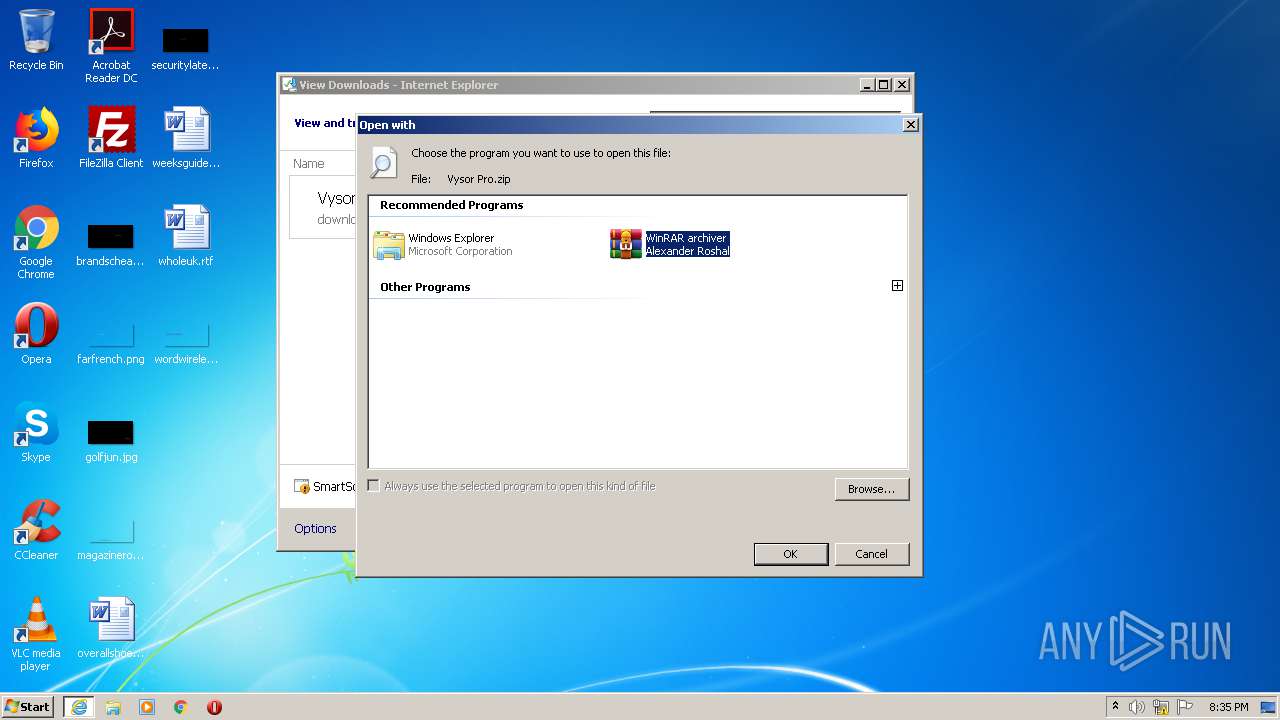
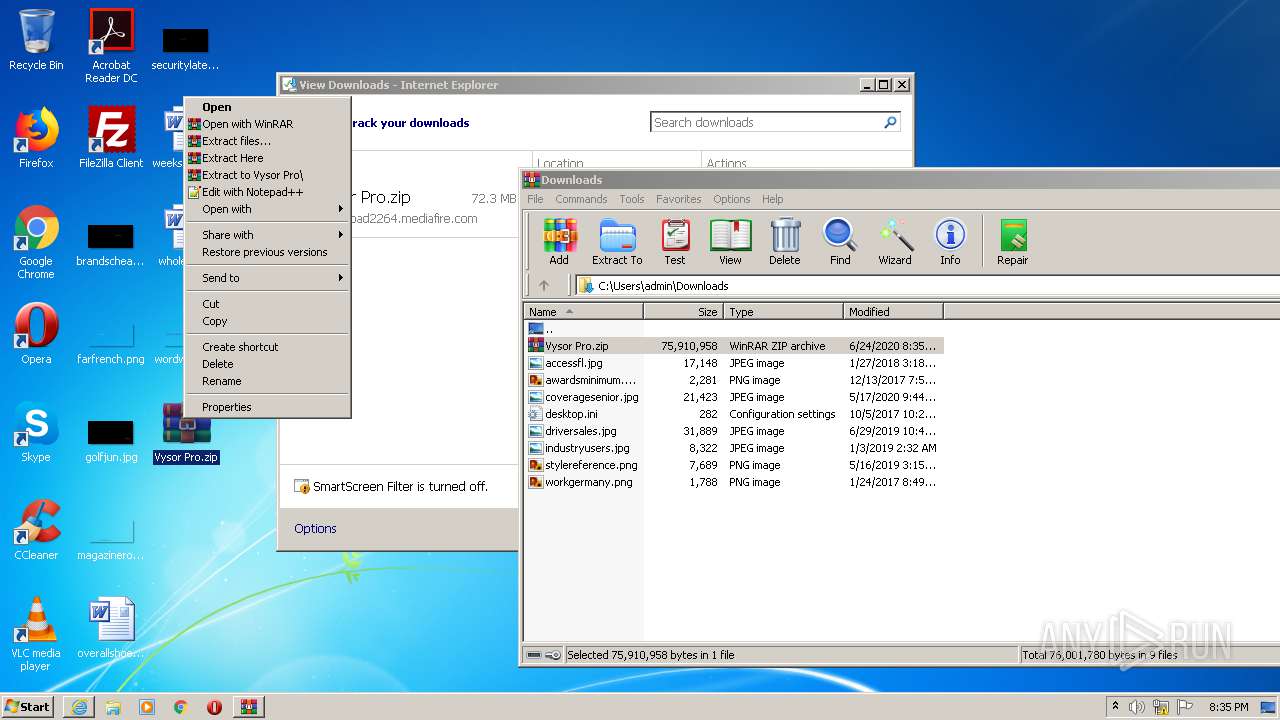
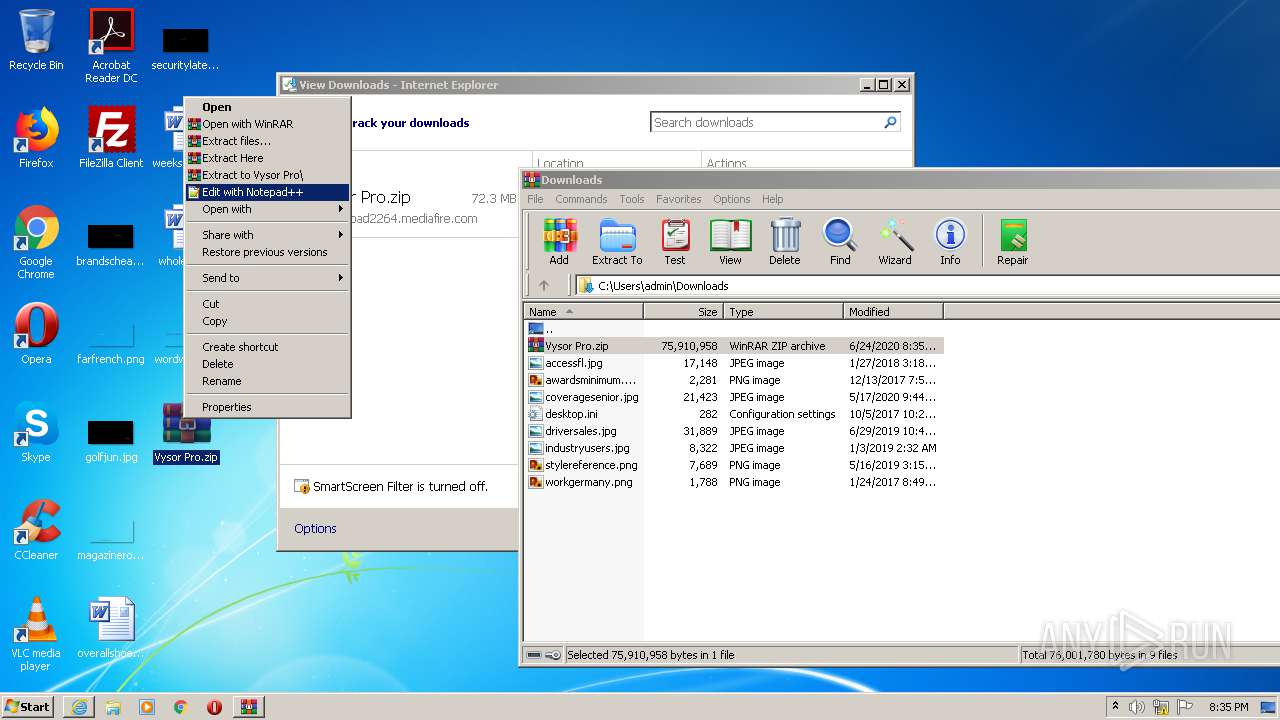
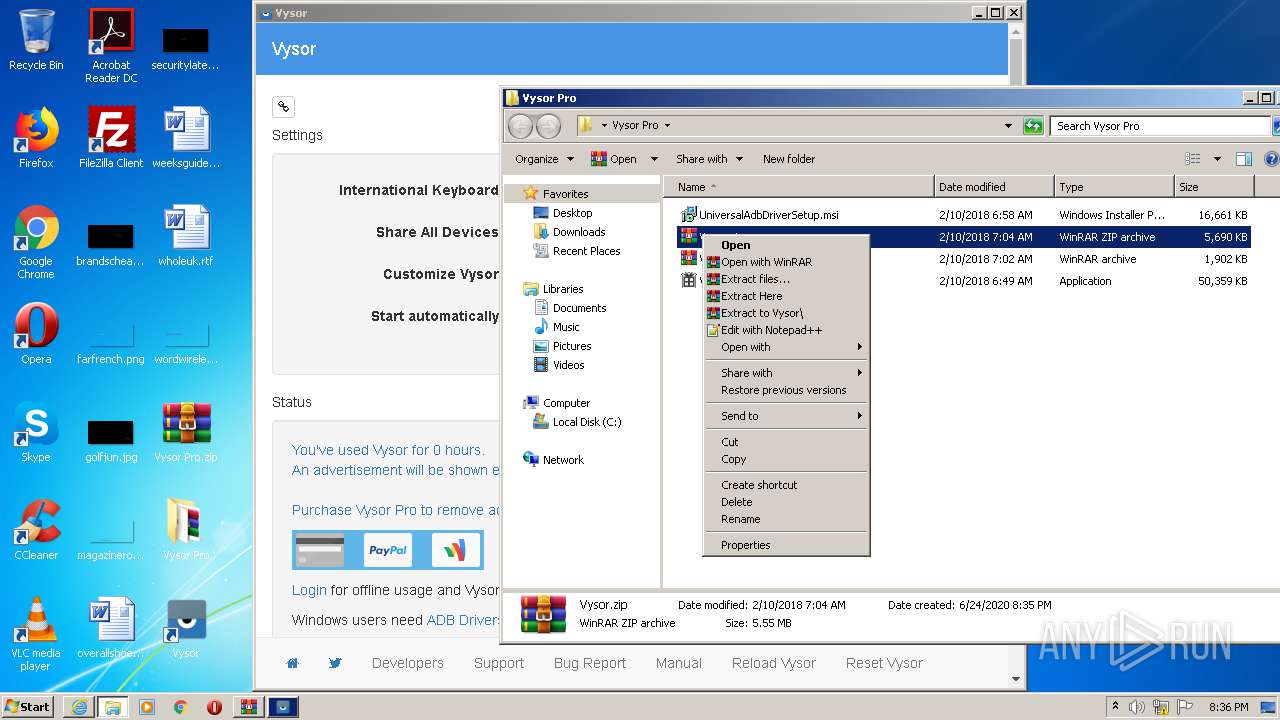
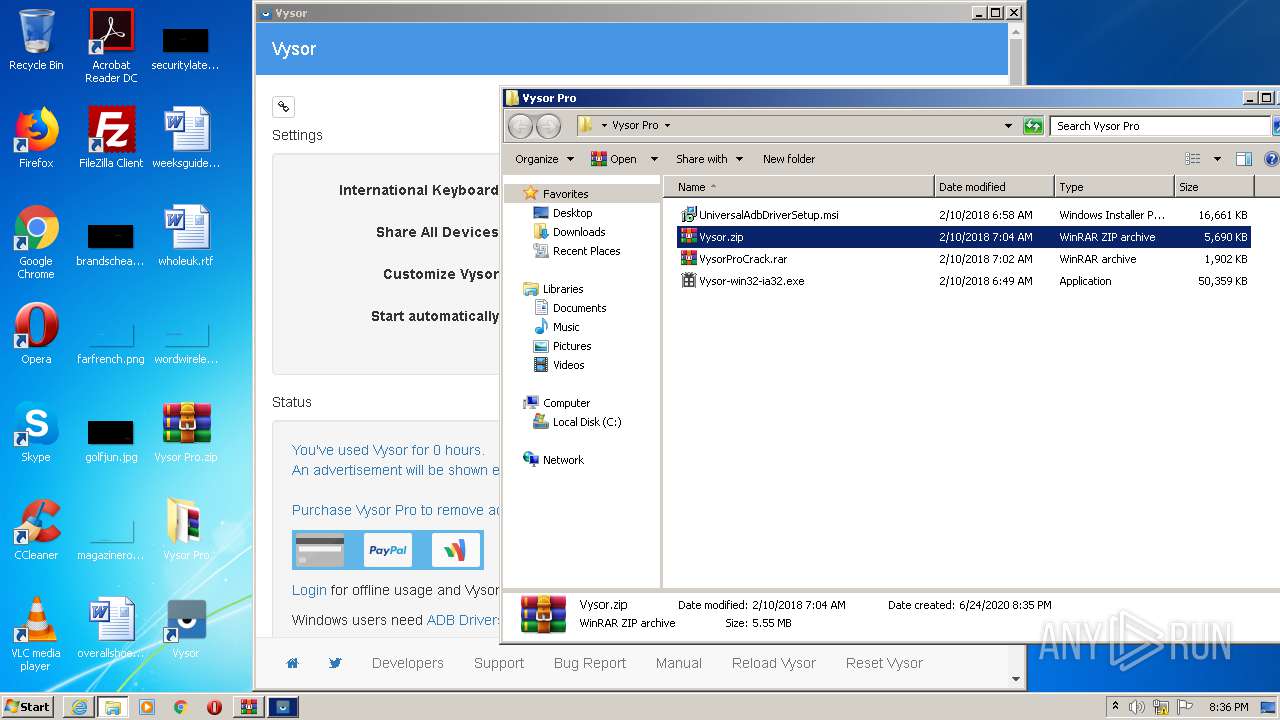
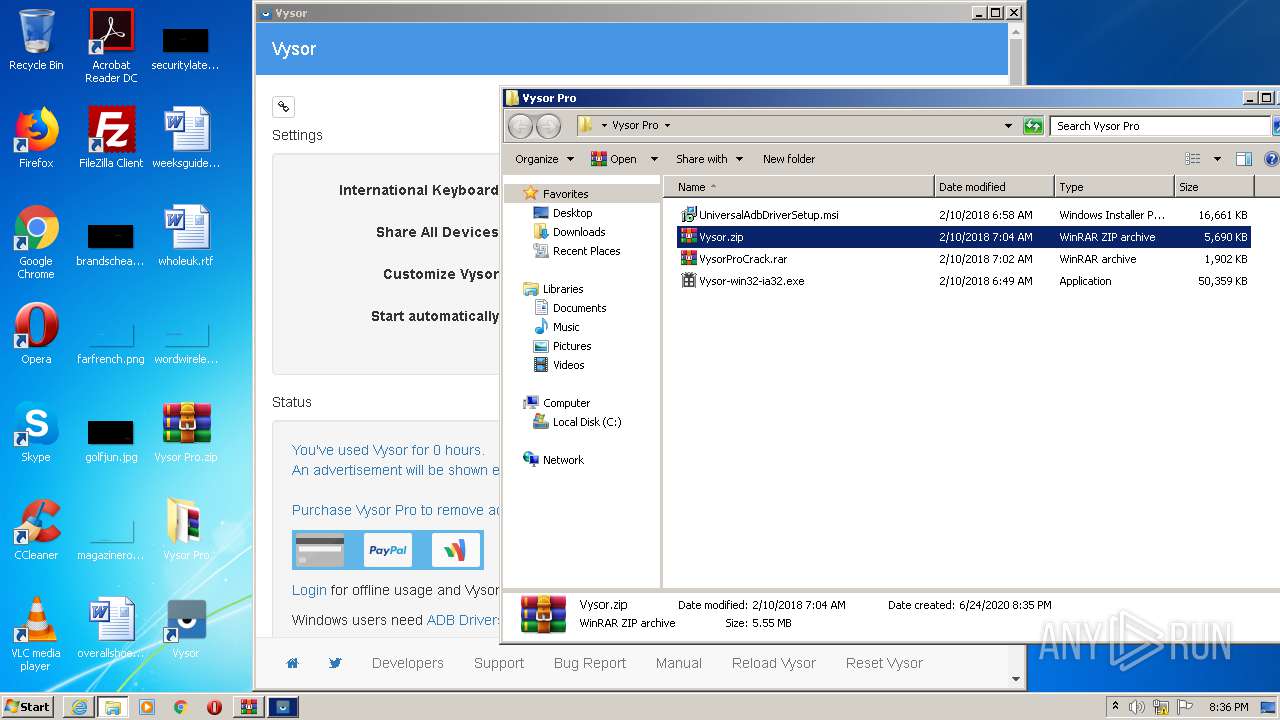
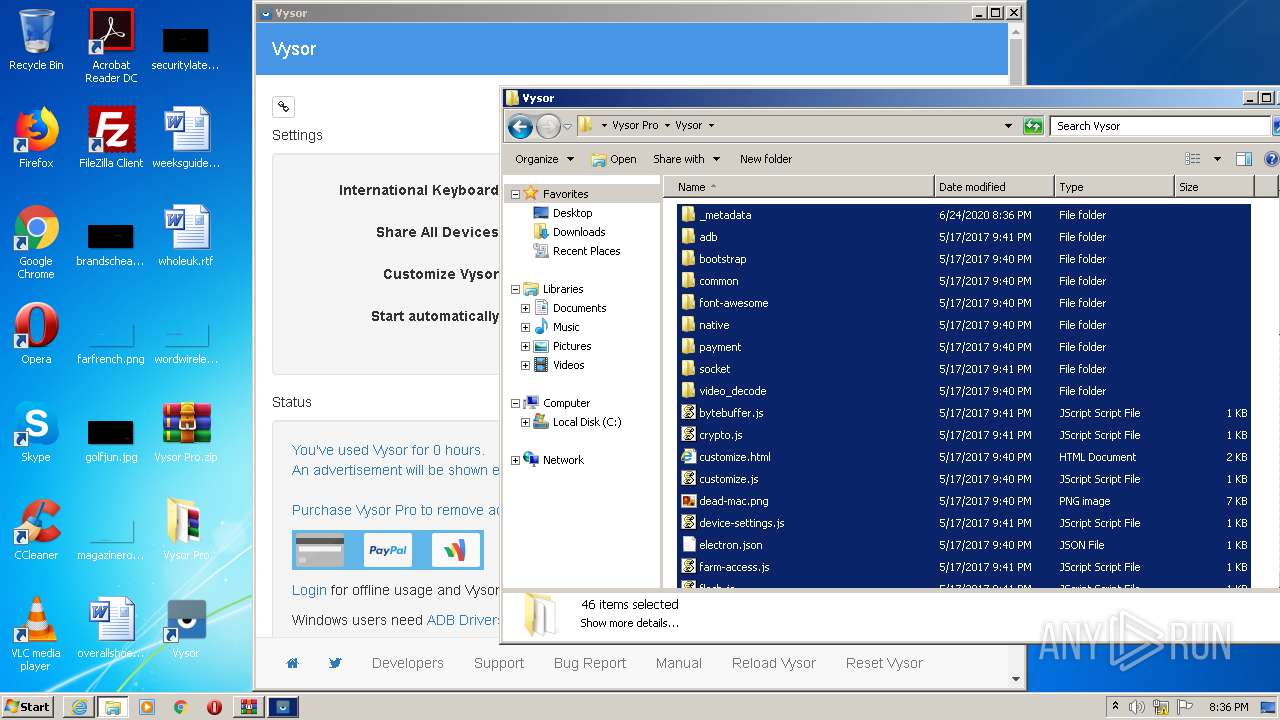
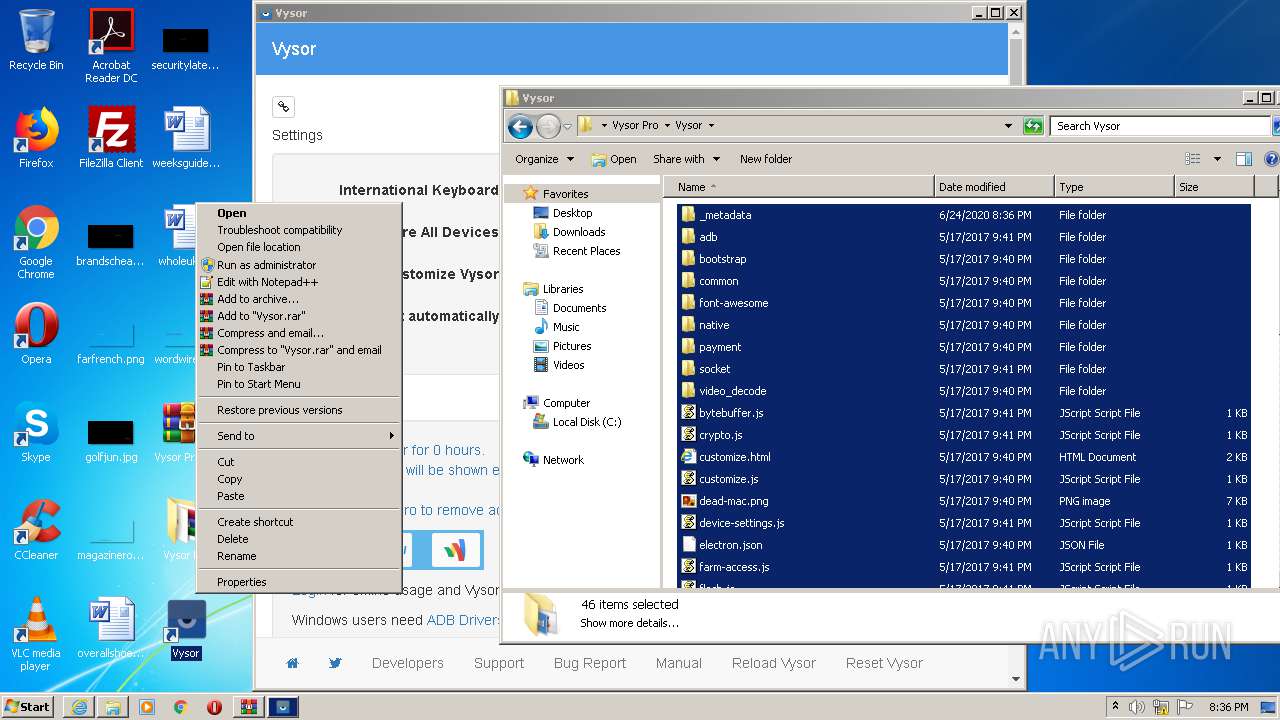
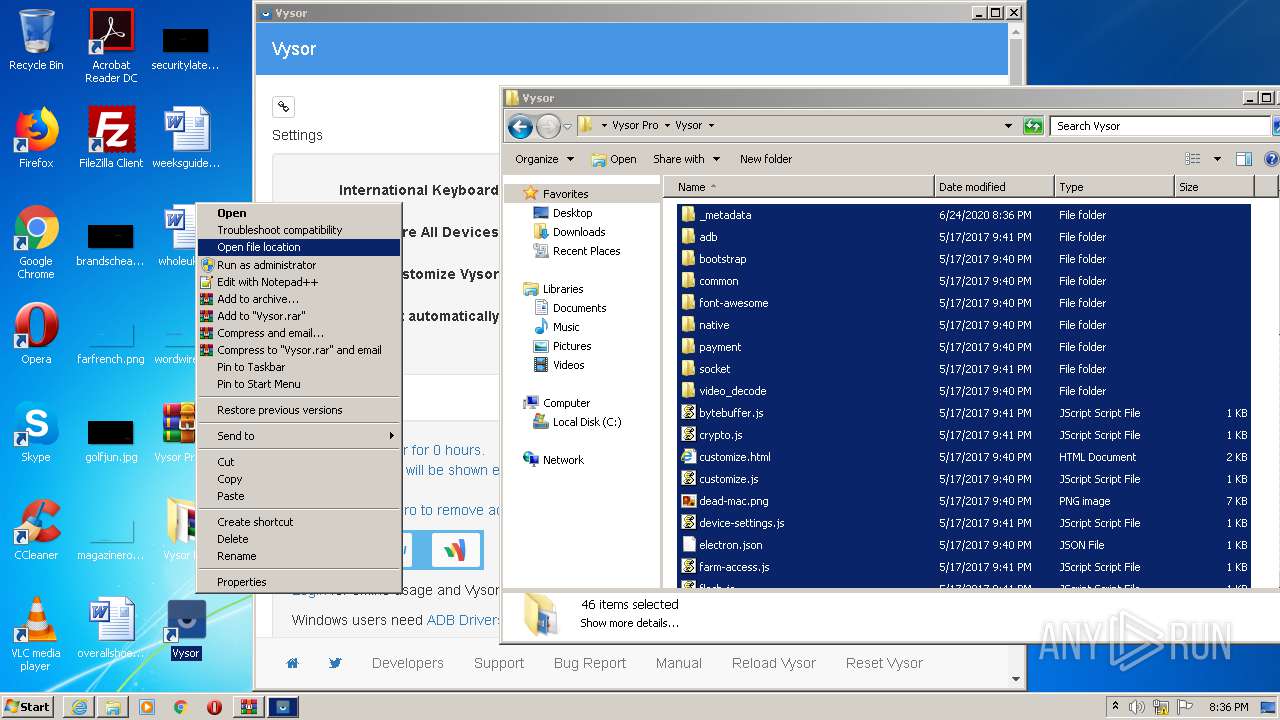
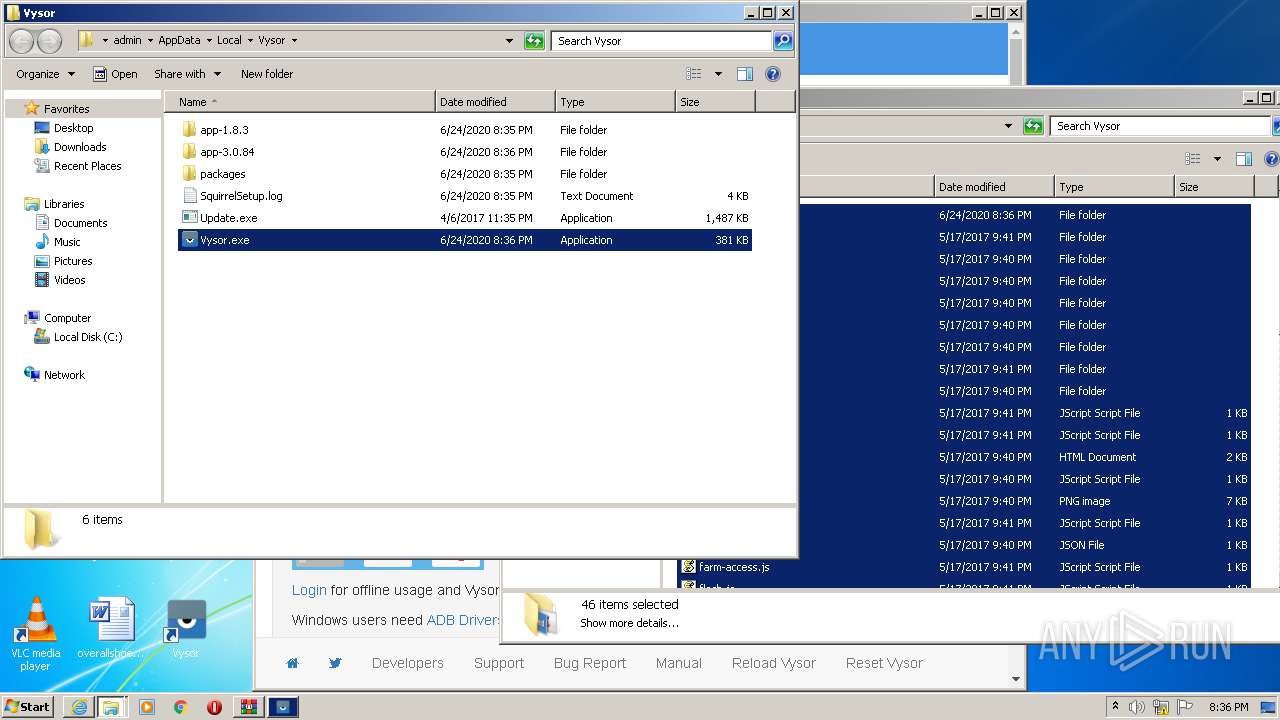
Manual execution by user
- WinRAR.exe (PID: 1584)
- Vysor-win32-ia32.exe (PID: 2396)
- WinRAR.exe (PID: 2316)
- Vysor.exe (PID: 3100)
Reads the hosts file
- Vysor.exe (PID: 1768)
- Vysor.exe (PID: 2372)
- Vysor.exe (PID: 812)
- Vysor.exe (PID: 3372)
Reads settings of System Certificates
- Vysor.exe (PID: 2372)
- Vysor.exe (PID: 812)
- Vysor.exe (PID: 3372)
- iexplore.exe (PID: 2224)
Dropped object may contain Bitcoin addresses
- Vysor.exe (PID: 2056)
- Update.exe (PID: 2780)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2224)
Changes settings of System certificates
- iexplore.exe (PID: 2224)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
90
Monitored processes
40
Malicious processes
24
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
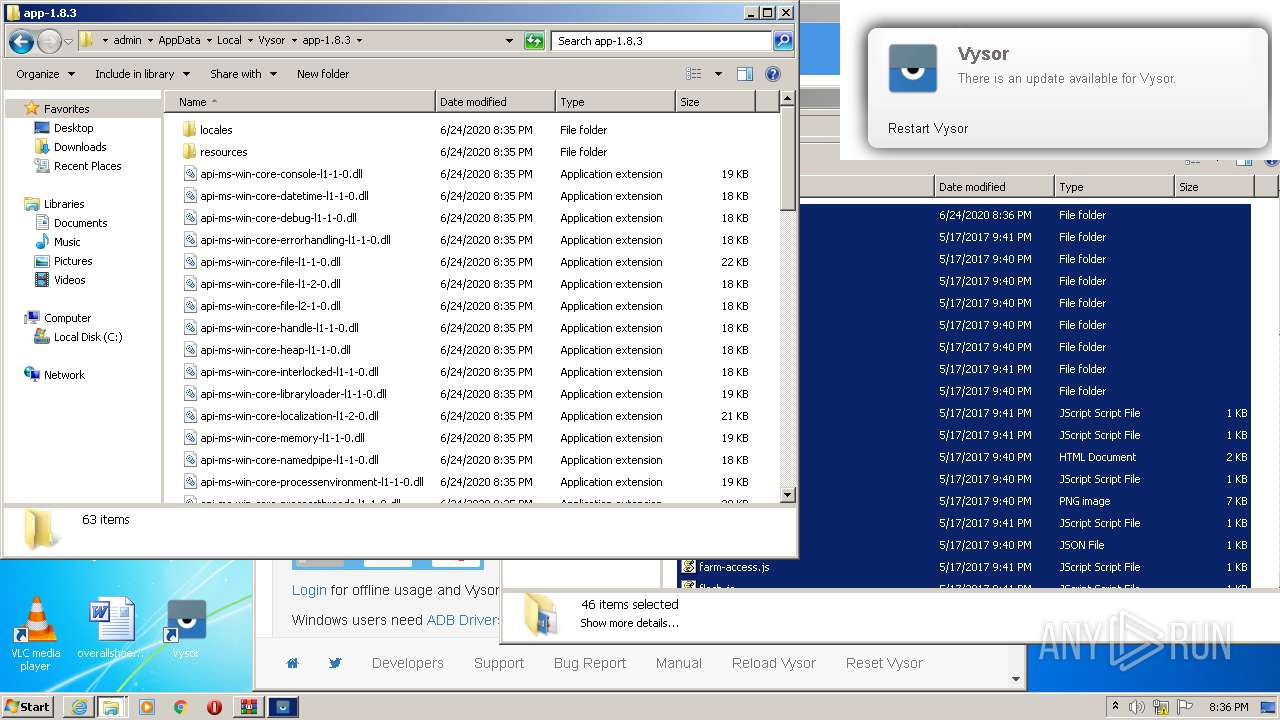
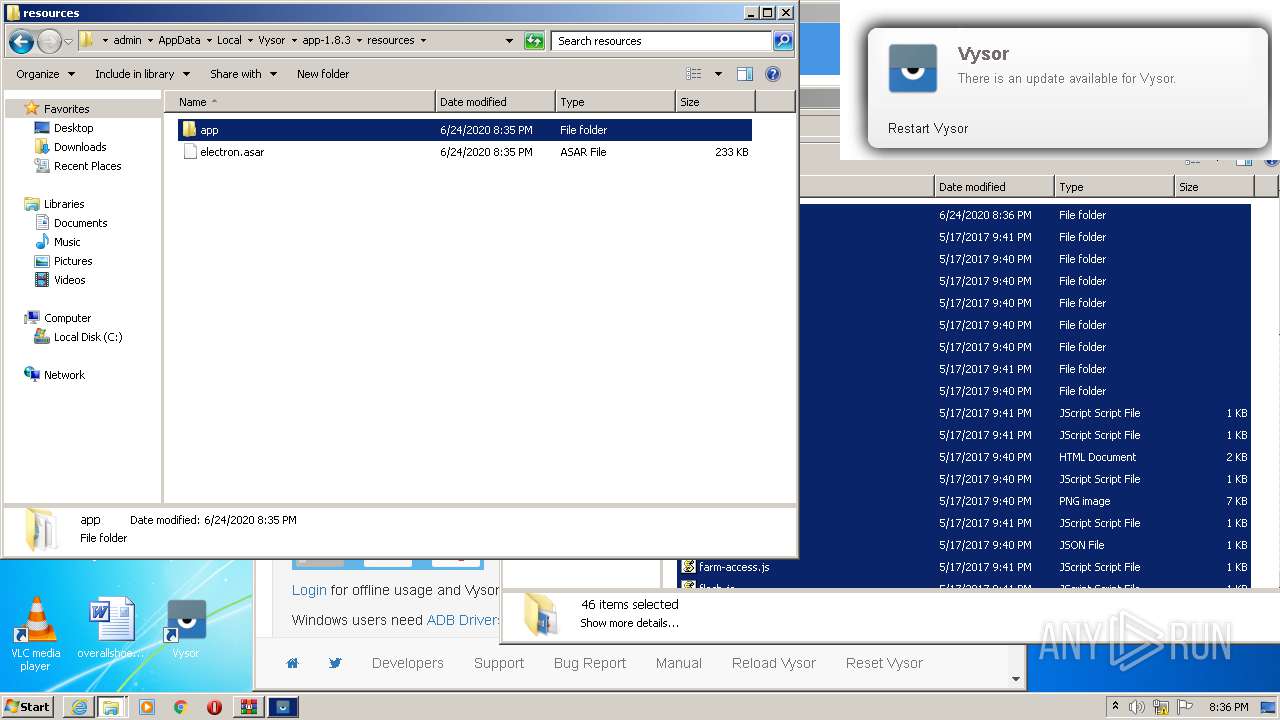
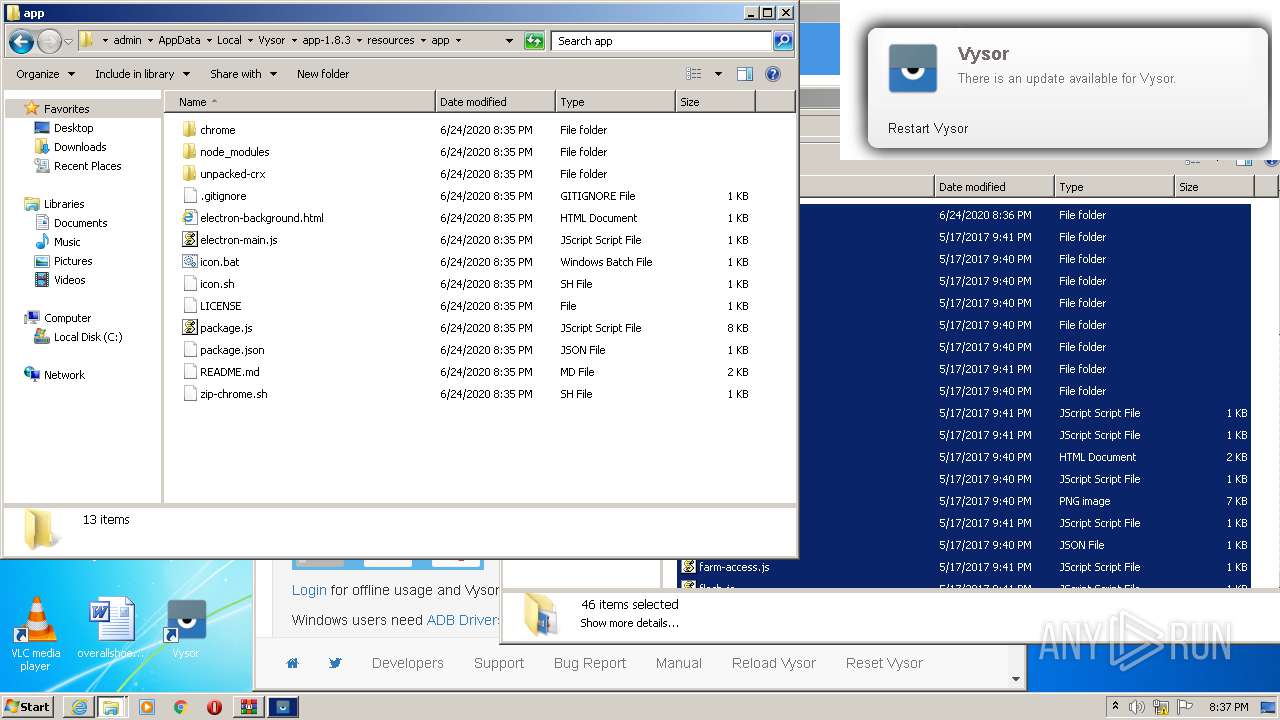
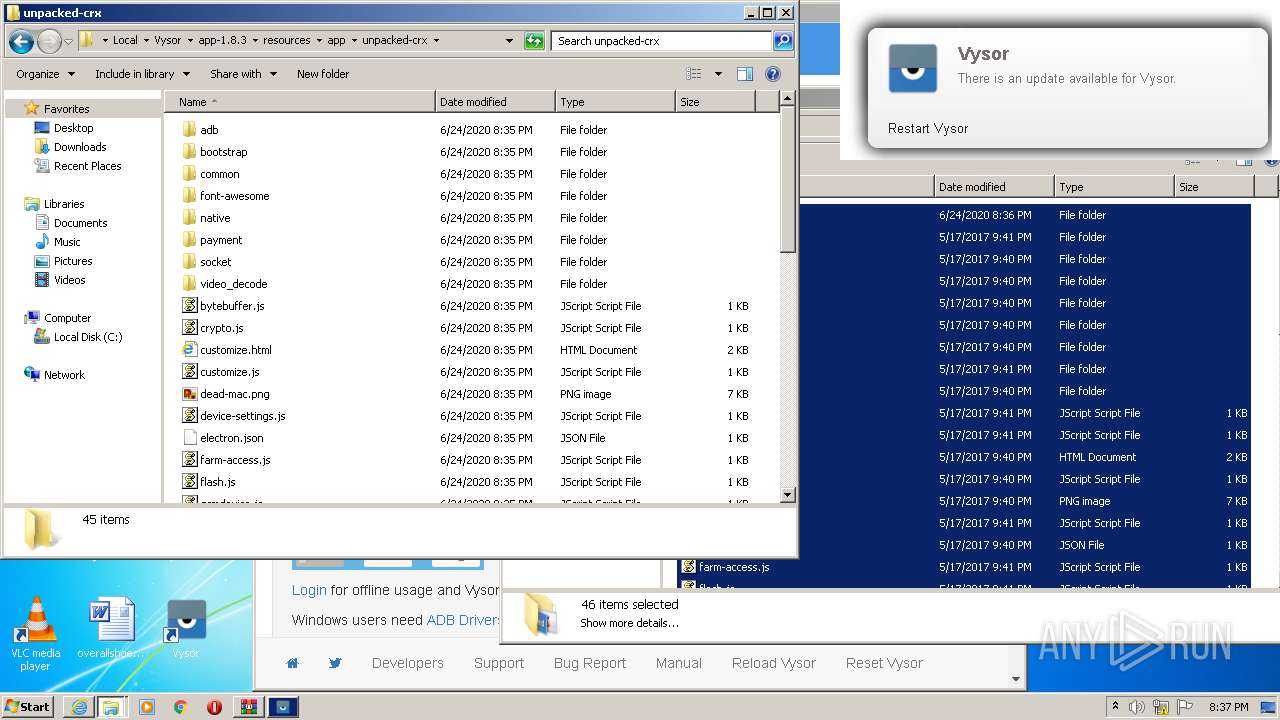
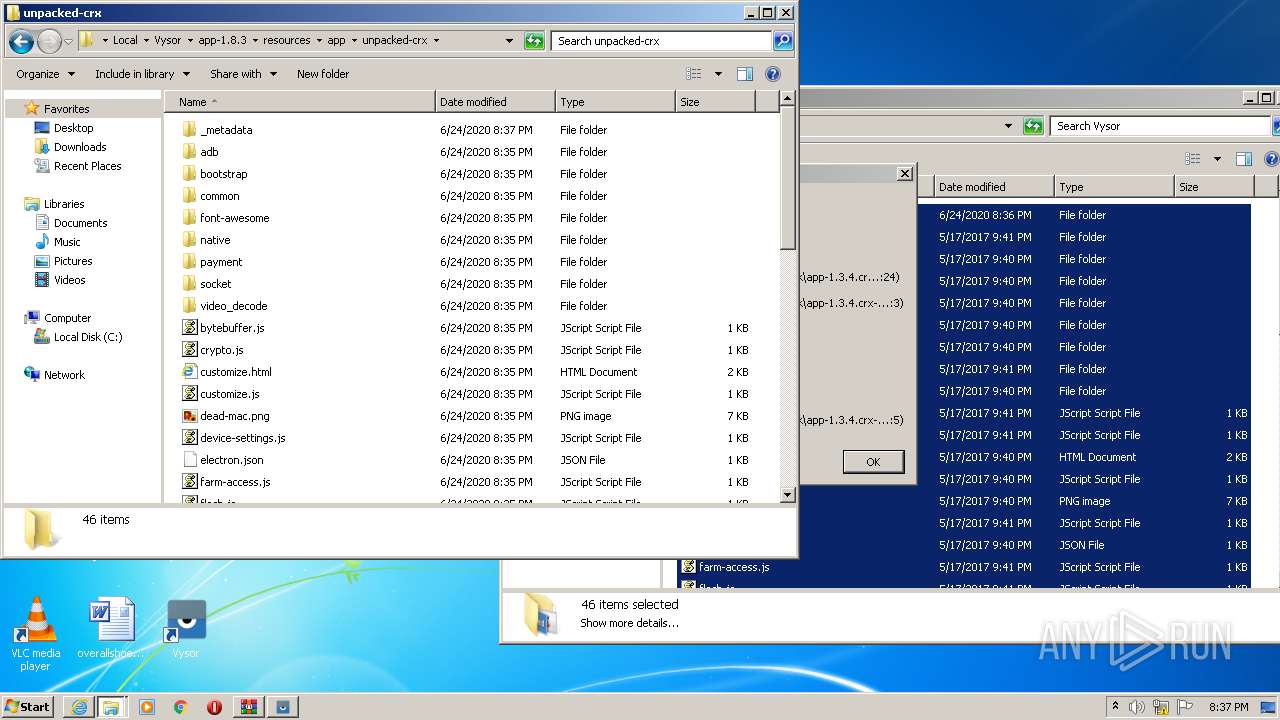
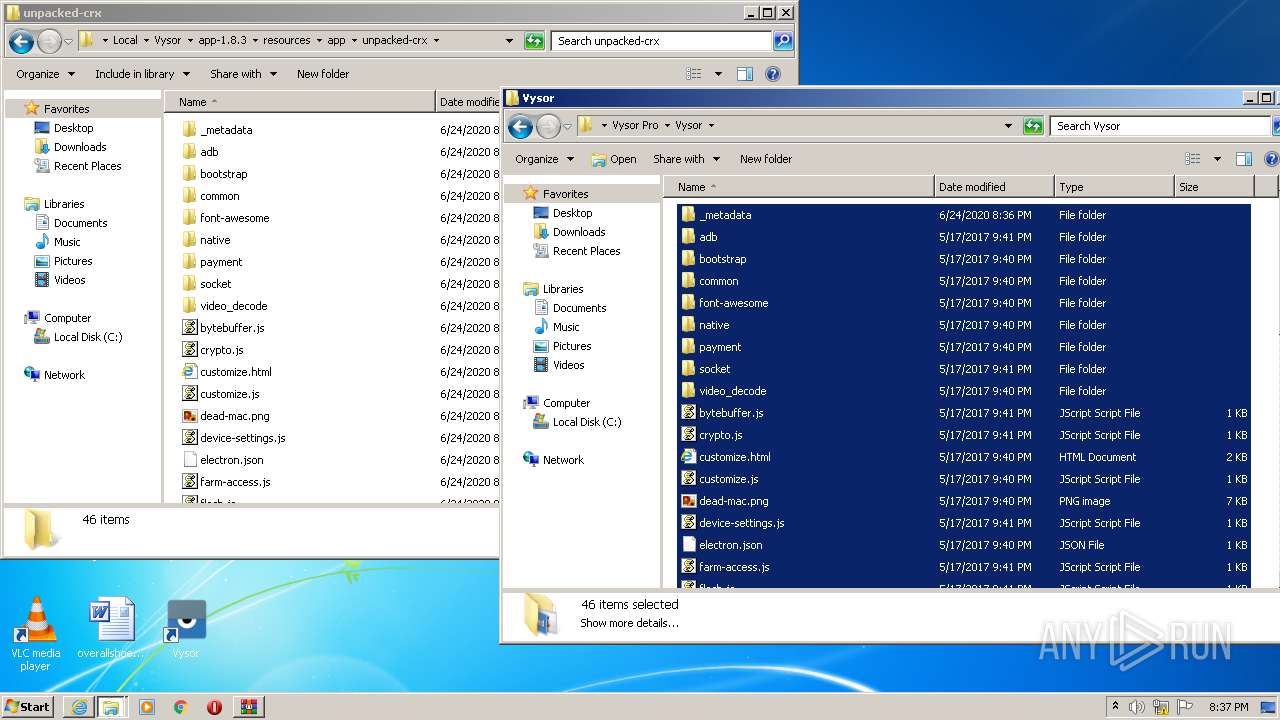
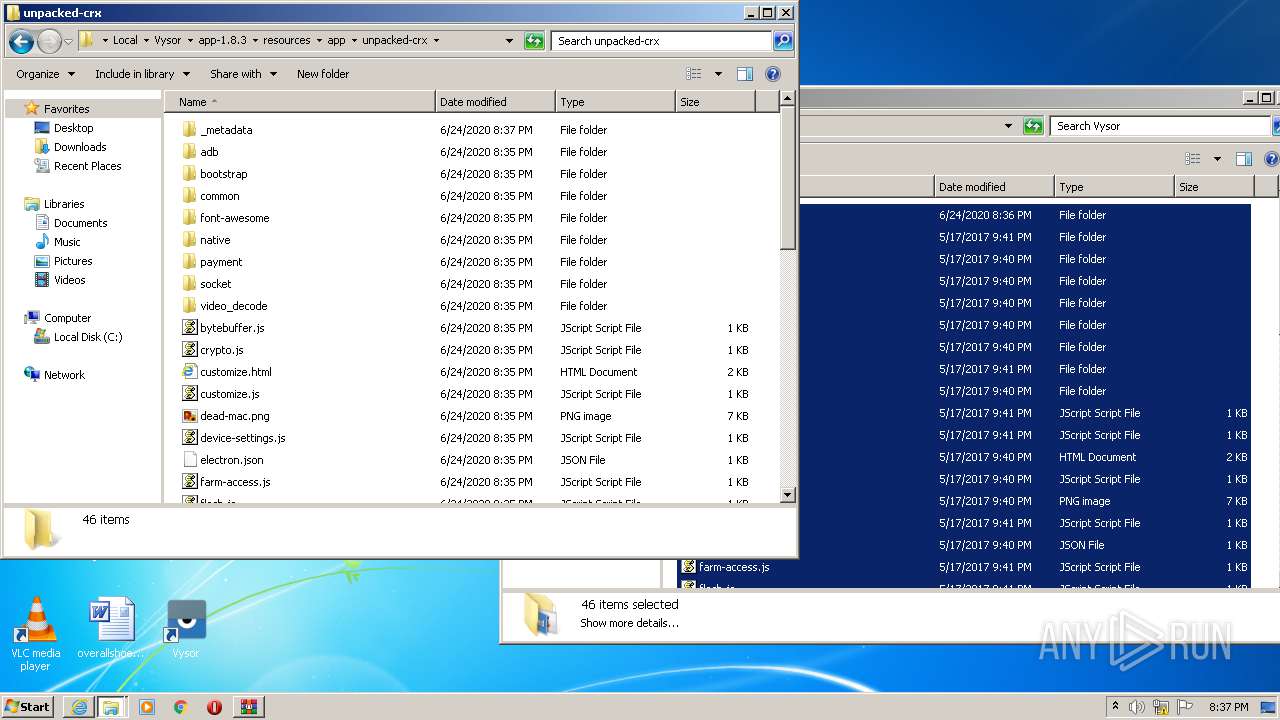
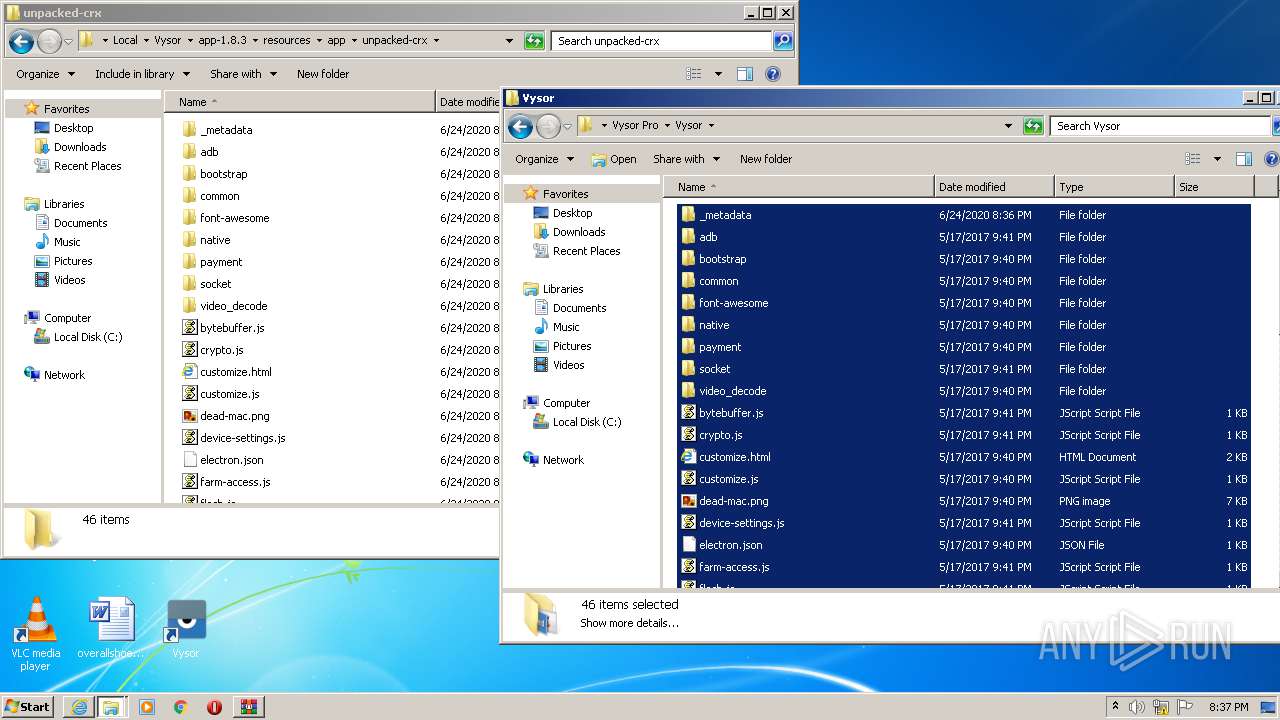
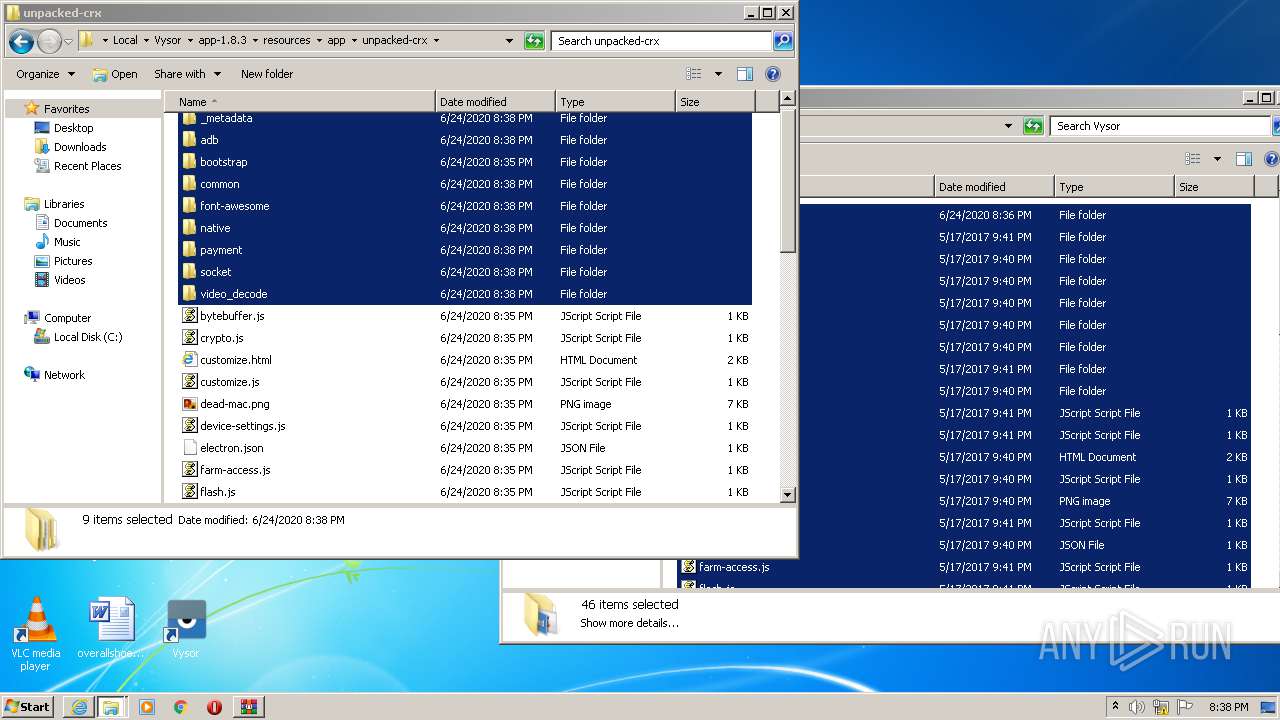
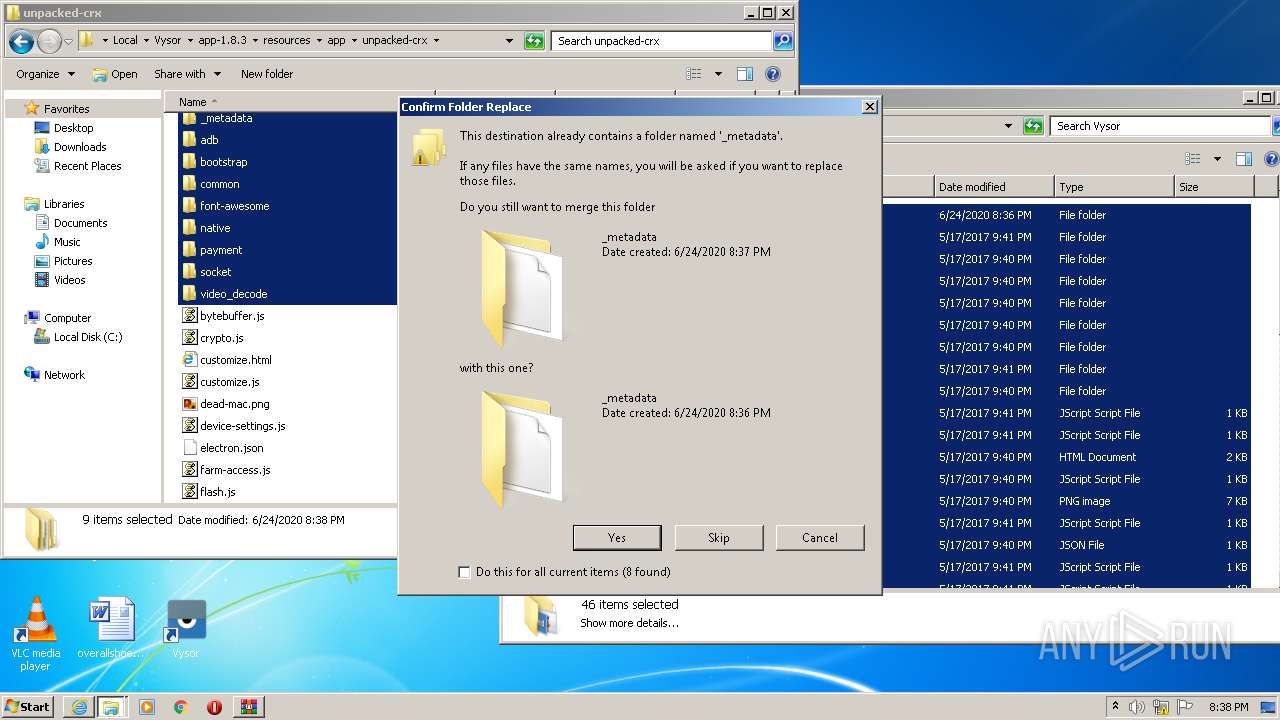
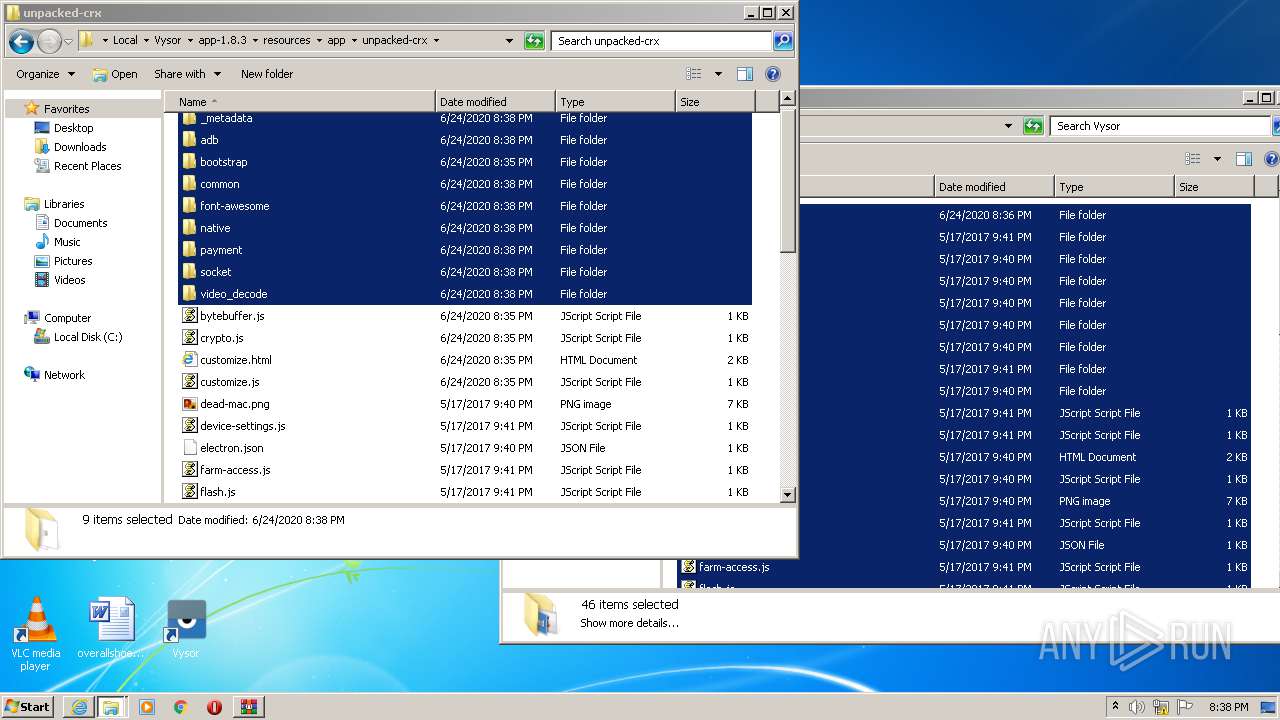
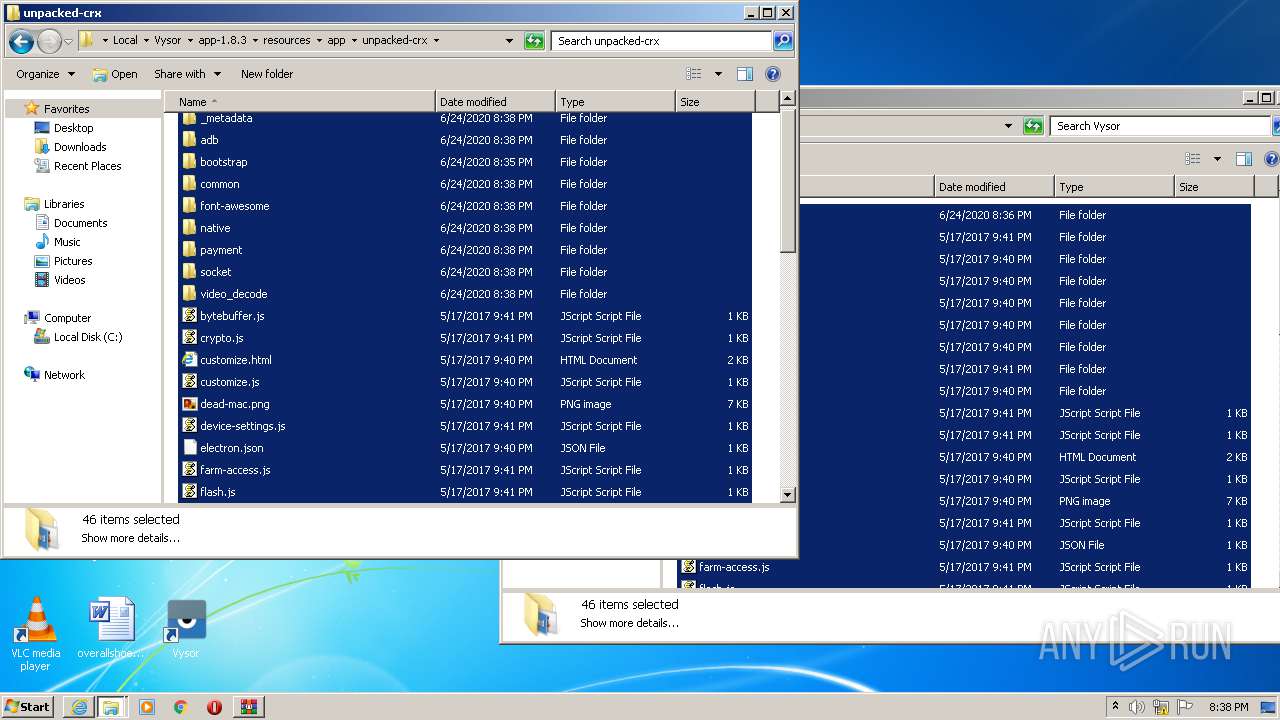
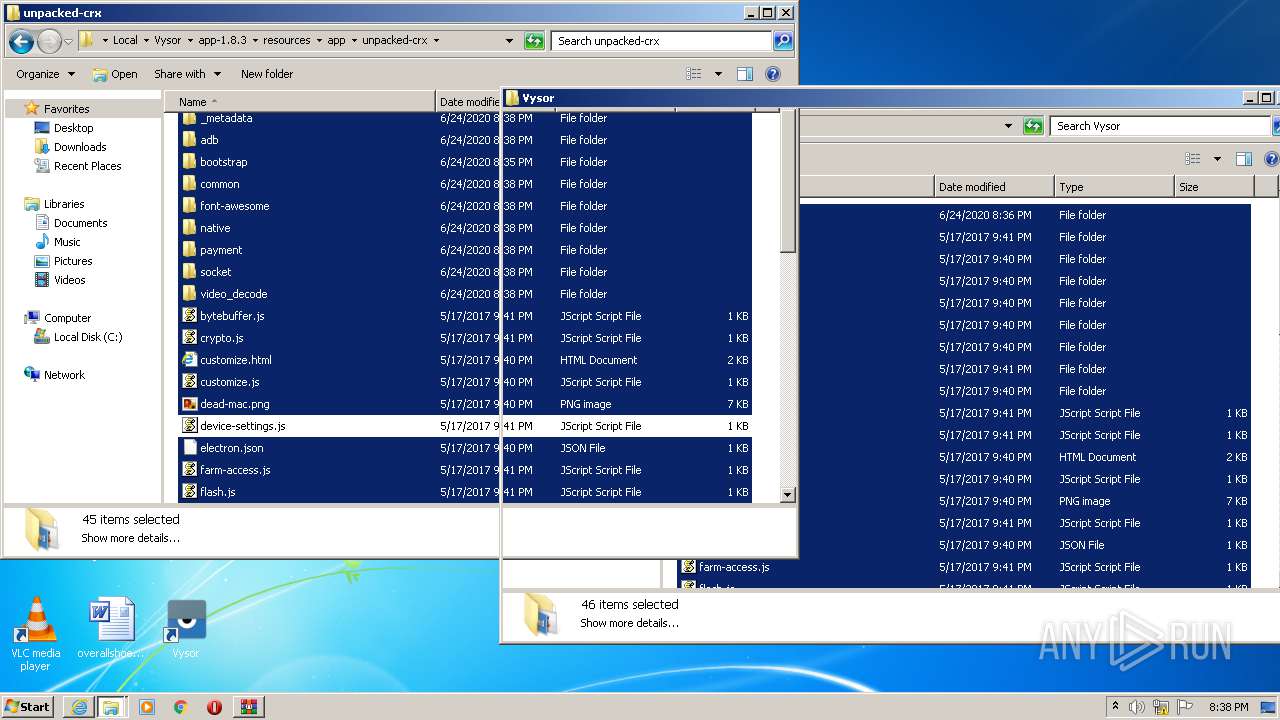
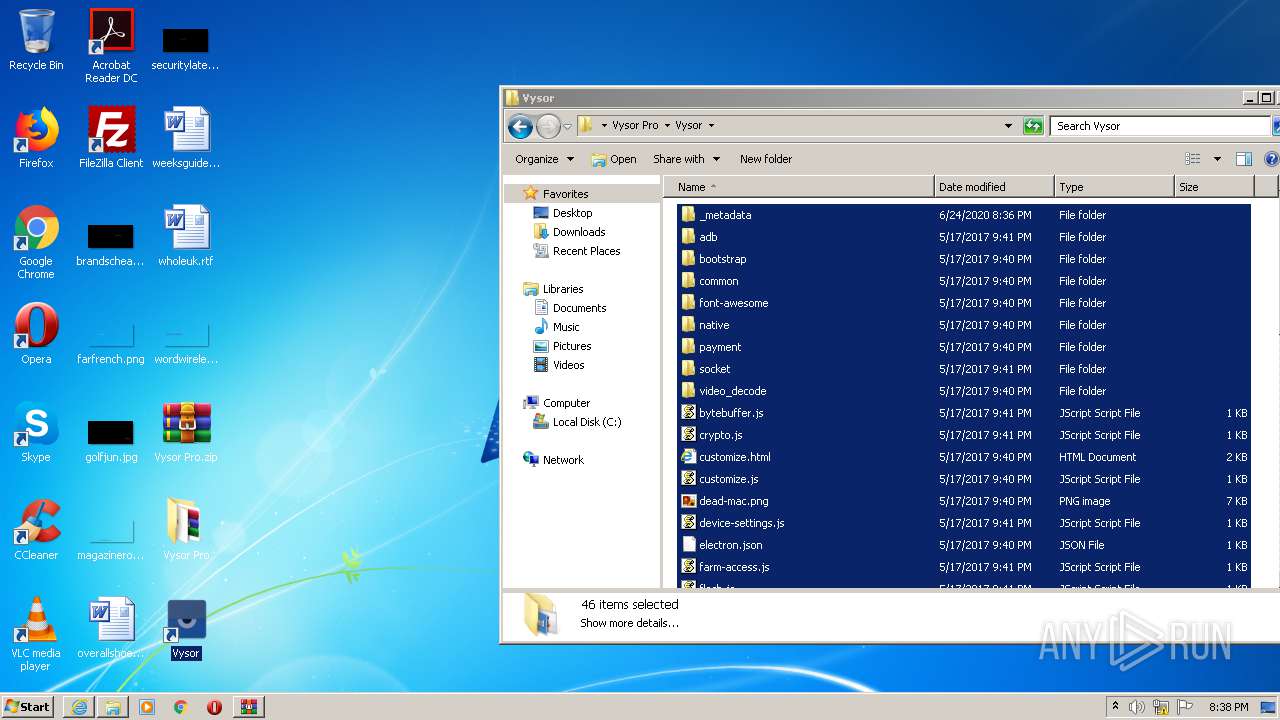
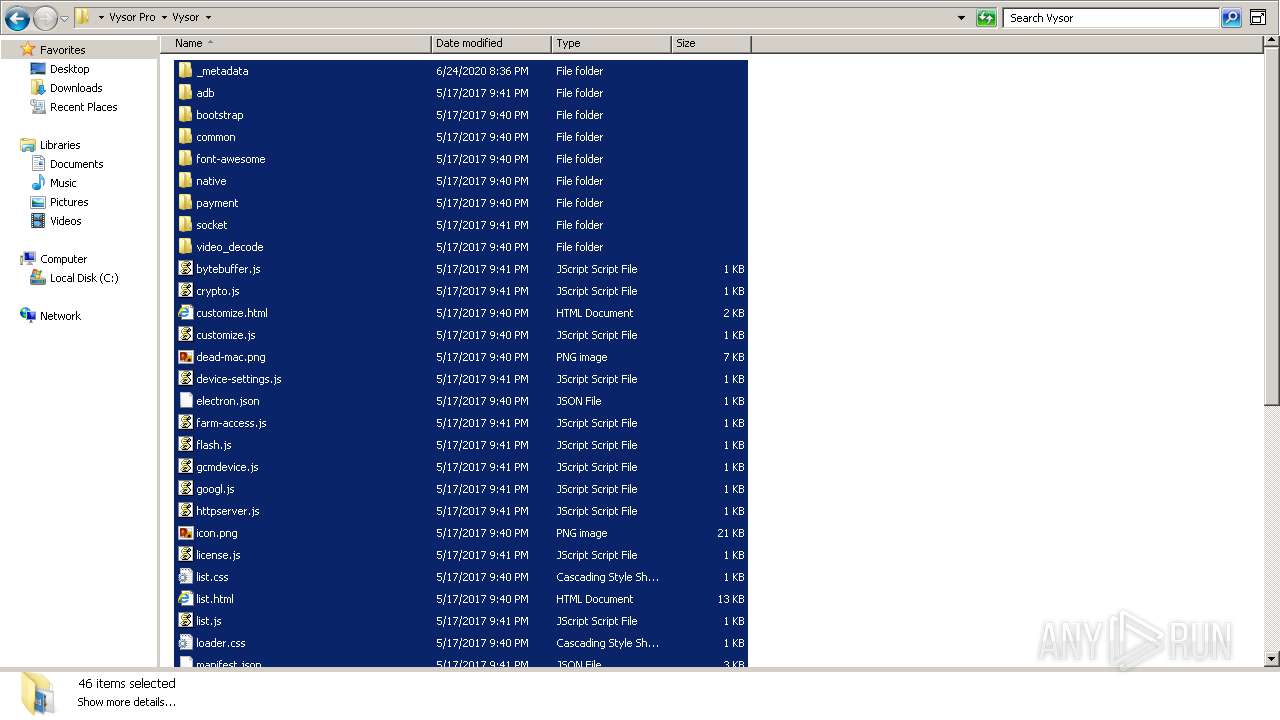
| 500 | "C:\Users\admin\AppData\Local\Vysor\app-1.8.3\Vysor.exe" --type=renderer --no-sandbox --register-pepper-plugins="C:\Users\admin\AppData\Local\Vysor\app-1.8.3\resources\app\unpacked-crx\native\win32\video_decode.dll;application/x-ppapi-vysor" --primordial-pipe-token=F69AAF25BF412AD6021CBCED71E3A629 --lang=en-US --standard-schemes=chrome-extension --app-user-model-id=com.squirrel.Vysor.Vysor --app-path="C:\Users\admin\AppData\Local\Vysor\app-1.8.3\resources\app" --enable-plugins --node-integration=true --webview-tag=true --no-sandbox --preload="C:\Users\admin\AppData\Local\Vysor\app-1.8.3\resources\app\chrome\preload\chrome-preload.js" --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553 --disable-accelerated-video-decode --disable-webrtc-hw-vp8-encoding --disable-gpu-compositing --service-request-channel-token=F69AAF25BF412AD6021CBCED71E3A629 --renderer-client-id=5 --mojo-platform-channel-handle=1532 /prefetch:1 | C:\Users\admin\AppData\Local\Vysor\app-1.8.3\Vysor.exe | Vysor.exe | ||||||||||||
User: admin Company: ClockworkMod Integrity Level: MEDIUM Description: Vysor Exit code: 0 Version: 1.8.3 Modules
| |||||||||||||||
| 544 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Vysor Pro.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 624 | "C:\Users\admin\AppData\Local\Vysor\app-1.8.3\Vysor.exe" --type=renderer --no-sandbox --register-pepper-plugins="C:\Users\admin\AppData\Local\Vysor\app-1.8.3\resources\app\unpacked-crx\native\win32\video_decode.dll;application/x-ppapi-vysor" --primordial-pipe-token=E4ABFF03B88F4BD5528B25D711A5EB8E --lang=en-US --standard-schemes=chrome-extension --app-user-model-id=com.squirrel.Vysor.Vysor --app-path="C:\Users\admin\AppData\Local\Vysor\app-1.8.3\resources\app" --node-integration=true --webview-tag=true --no-sandbox --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553 --disable-accelerated-video-decode --disable-webrtc-hw-vp8-encoding --disable-gpu-compositing --service-request-channel-token=E4ABFF03B88F4BD5528B25D711A5EB8E --renderer-client-id=13 --mojo-platform-channel-handle=1680 /prefetch:1 | C:\Users\admin\AppData\Local\Vysor\app-1.8.3\Vysor.exe | — | Vysor.exe | |||||||||||
User: admin Company: ClockworkMod Integrity Level: MEDIUM Description: Vysor Exit code: 0 Version: 1.8.3 Modules
| |||||||||||||||
| 812 | "C:\Users\admin\AppData\Local\Vysor\app-1.8.3\Vysor.exe" --squirrel-firstrun | C:\Users\admin\AppData\Local\Vysor\app-1.8.3\Vysor.exe | Vysor.exe | ||||||||||||
User: admin Company: ClockworkMod Integrity Level: MEDIUM Description: Vysor Exit code: 0 Version: 1.8.3 Modules
| |||||||||||||||
| 1288 | "C:\Users\admin\AppData\Local\Vysor\app-1.8.3\Squirrel.exe" --updateSelf=C:\Users\admin\AppData\Local\SquirrelTemp\Update.exe | C:\Users\admin\AppData\Local\Vysor\app-1.8.3\Squirrel.exe | — | Update.exe | |||||||||||
User: admin Company: GitHub Integrity Level: MEDIUM Description: Update Exit code: 4294967295 Version: 1.5.2.0 Modules
| |||||||||||||||
| 1536 | "C:\Users\admin\AppData\Local\SquirrelTemp\Update.exe" --install . | C:\Users\admin\AppData\Local\SquirrelTemp\Update.exe | Vysor-win32-ia32.exe | ||||||||||||
User: admin Company: GitHub Integrity Level: MEDIUM Description: Update Exit code: 0 Version: 1.5.2.0 Modules
| |||||||||||||||
| 1584 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\Vysor Pro.zip" "C:\Users\admin\Desktop\Vysor Pro\" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1732 | "C:\Users\admin\AppData\Local\Vysor\app-1.8.3\Vysor.exe" --type=renderer --no-sandbox --register-pepper-plugins="C:\Users\admin\AppData\Local\Vysor\app-1.8.3\resources\app\unpacked-crx\native\win32\video_decode.dll;application/x-ppapi-vysor" --primordial-pipe-token=E02A4539EC4864B0C233F0A47F6F4992 --lang=en-US --standard-schemes=chrome-extension --app-user-model-id=com.squirrel.Vysor.Vysor --app-path="C:\Users\admin\AppData\Local\Vysor\app-1.8.3\resources\app" --node-integration=true --webview-tag=true --no-sandbox --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553 --disable-accelerated-video-decode --disable-webrtc-hw-vp8-encoding --disable-gpu-compositing --service-request-channel-token=E02A4539EC4864B0C233F0A47F6F4992 --renderer-client-id=9 --mojo-platform-channel-handle=2508 /prefetch:1 | C:\Users\admin\AppData\Local\Vysor\app-1.8.3\Vysor.exe | — | Vysor.exe | |||||||||||
User: admin Company: ClockworkMod Integrity Level: MEDIUM Description: Vysor Exit code: 0 Version: 1.8.3 Modules
| |||||||||||||||
| 1768 | "C:\Users\admin\AppData\Local\Vysor\app-1.8.3\Vysor.exe" --squirrel-install 1.8.3 | C:\Users\admin\AppData\Local\Vysor\app-1.8.3\Vysor.exe | — | Update.exe | |||||||||||
User: admin Company: ClockworkMod Integrity Level: MEDIUM Description: Vysor Exit code: 0 Version: 1.8.3 Modules
| |||||||||||||||
| 1844 | C:\Users\admin\AppData\Local\Vysor\Update.exe --checkForUpdate https://vysornuts.clockworkmod.com/update/win32_ia32/1.8.3 | C:\Users\admin\AppData\Local\Vysor\Update.exe | Vysor.exe | ||||||||||||
User: admin Company: GitHub Integrity Level: MEDIUM Description: Update Exit code: 0 Version: 1.5.2.0 Modules
| |||||||||||||||
Total events
10 789
Read events
3 807
Write events
4 752
Delete events
2 230
Modification events
| (PID) Process: | (2224) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2077121682 | |||
| (PID) Process: | (2224) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30820958 | |||
| (PID) Process: | (2224) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2224) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2224) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2224) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2224) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2224) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2224) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2224) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
76
Suspicious files
448
Text files
374
Unknown types
822
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1948 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\Vysor Pro[1].zip | — | |
MD5:— | SHA256:— | |||
| 2224 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab467F.tmp | — | |
MD5:— | SHA256:— | |||
| 2224 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar4680.tmp | — | |
MD5:— | SHA256:— | |||
| 2224 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\ver46BF.tmp | — | |
MD5:— | SHA256:— | |||
| 1948 | iexplore.exe | C:\Users\admin\Downloads\Vysor Pro.zip.jzm6ebm.partial | — | |
MD5:— | SHA256:— | |||
| 2224 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFFA35AE876ED77168.TMP | — | |
MD5:— | SHA256:— | |||
| 2224 | iexplore.exe | C:\Users\admin\Downloads\Vysor Pro.zip.jzm6ebm.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 2224 | iexplore.exe | C:\Users\admin\Downloads\Vysor Pro.zip | — | |
MD5:— | SHA256:— | |||
| 2224 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\OI1BNR63.txt | — | |
MD5:— | SHA256:— | |||
| 2224 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\ZHIAAWHT.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
25
DNS requests
14
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2224 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2224 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2224 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1948 | iexplore.exe | 199.91.155.5:80 | download2264.mediafire.com | MediaFire, LLC | US | suspicious |
2224 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2224 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2224 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2924 | Update.exe | 50.23.163.97:443 | vysornuts.clockworkmod.com | SoftLayer Technologies Inc. | US | unknown |
2372 | Vysor.exe | 172.217.23.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
2372 | Vysor.exe | 216.58.212.161:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2780 | Update.exe | 50.23.163.97:443 | vysornuts.clockworkmod.com | SoftLayer Technologies Inc. | US | unknown |
2372 | Vysor.exe | 172.217.22.110:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2780 | Update.exe | 151.101.0.133:443 | raw.githubusercontent.com | Fastly | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download2264.mediafire.com |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
vysornuts.clockworkmod.com |
| malicious |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1948 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |