| File name: | bewe.exe |
| Full analysis: | https://app.any.run/tasks/6d18584f-a35c-4258-b78b-247ba6c6115d |
| Verdict: | Malicious activity |
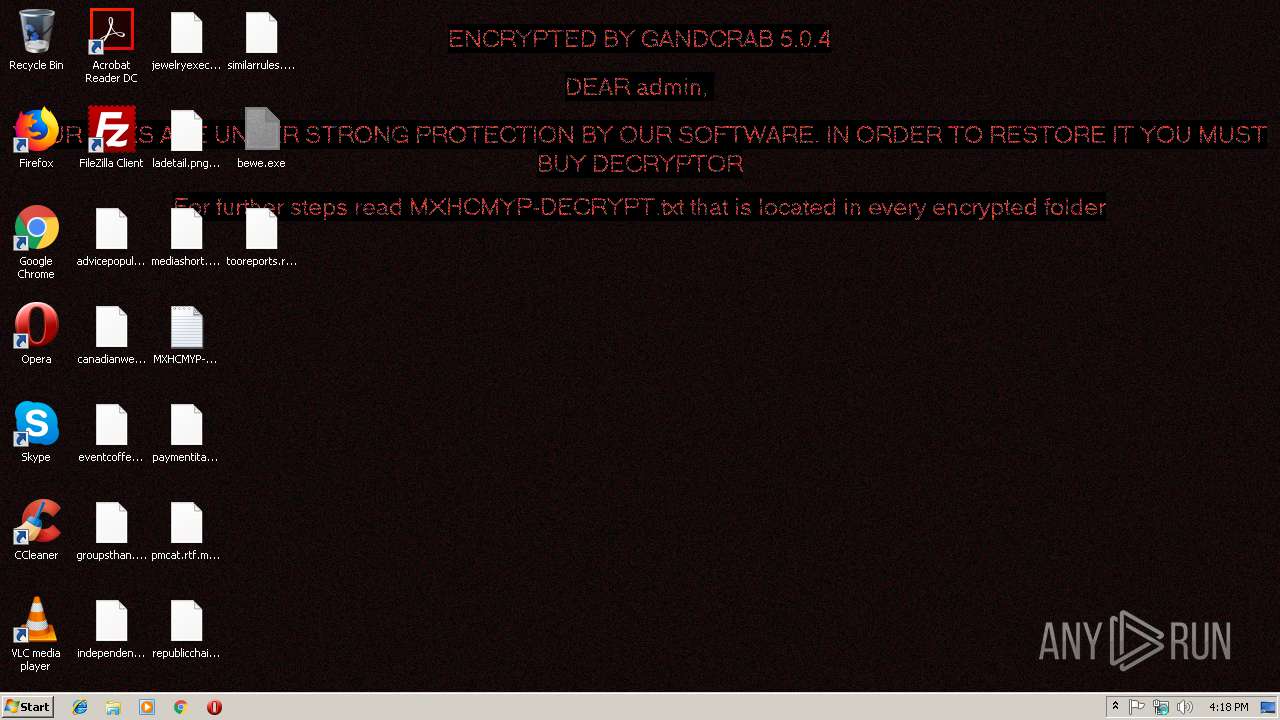
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | December 06, 2018, 16:17:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D75CD2DD6936454325628BB3BDAD04CF |
| SHA1: | 9A8BD9BCDA77A2EF2956F10F27CF92C7AC637146 |
| SHA256: | 5A0AFAC5F26012E4E8BD176AA7A6D696C3875A827AD45A94AA01176E2B9BF584 |
| SSDEEP: | 3072:x6wrHOG1SNhwGPaIZF9b/fZ9mGBT54RM5TzNUkl:Qpoid3x/B9mGBN4R+zNb |
MALICIOUS
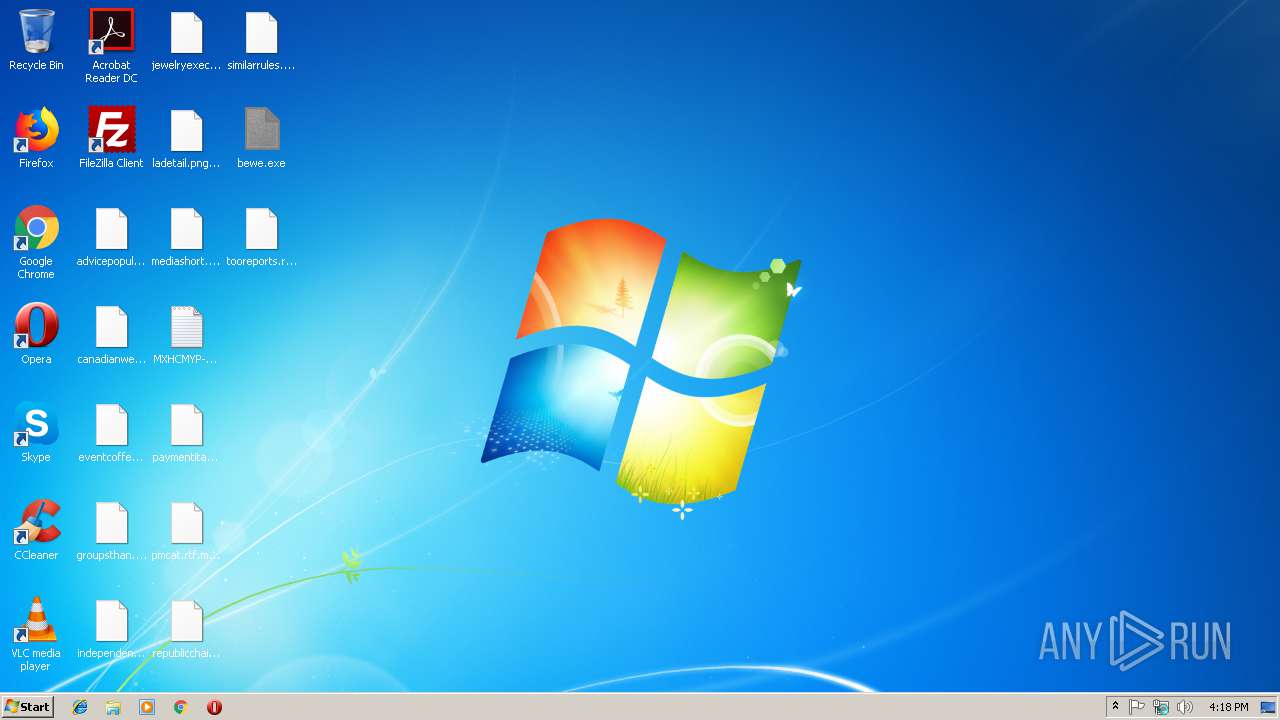
Renames files like Ransomware
- bewe.exe (PID: 3164)
GandCrab keys found
- bewe.exe (PID: 3164)
Connects to CnC server
- bewe.exe (PID: 3164)
Writes file to Word startup folder
- bewe.exe (PID: 3164)
Dropped file may contain instructions of ransomware
- bewe.exe (PID: 3164)
Actions looks like stealing of personal data
- bewe.exe (PID: 3164)
Deletes shadow copies
- bewe.exe (PID: 3164)
SUSPICIOUS
Creates files like Ransomware instruction
- bewe.exe (PID: 3164)
Creates files in the program directory
- bewe.exe (PID: 3164)
Reads the cookies of Mozilla Firefox
- bewe.exe (PID: 3164)
Starts CMD.EXE for commands execution
- bewe.exe (PID: 3164)
Creates files in the user directory
- bewe.exe (PID: 3164)
INFO
Dropped object may contain TOR URL's
- bewe.exe (PID: 3164)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (64.5) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (13.6) |
| .exe | | | Win32 Executable (generic) (9.3) |
| .exe | | | Clipper DOS Executable (4.1) |
| .exe | | | Generic Win/DOS Executable (4.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:12:11 04:38:49+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 161280 |
| InitializedDataSize: | 256000 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1da57 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.0.0.0 |
| ProductVersionNumber: | 3.0.0.0 |
| FileFlagsMask: | 0x004f |
| FileFlags: | (none) |
| FileOS: | Unknown (0x40534) |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Unknown (457A) |
| CharacterSet: | Unknown (A56B) |
| FileVersion: | 5.4.6.60 |
| InternalName: | yayuyivi.exe |
| LegalCopyright: | Copyright (C) 2018, juxiganuwehare |
| ProductVersion: | 5.4.6.60 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Dec-2017 03:38:49 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 11-Dec-2017 03:38:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002754C | 0x00027600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.80616 |
.data | 0x00029000 | 0x000299E8 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.83783 |
.mysec3 | 0x00053000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0.0815394 |
.rsrc | 0x00054000 | 0x00013C20 | 0x00013E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.6959 |
.reloc | 0x00068000 | 0x00001A44 | 0x00001C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.36458 |
Imports
GDI32.dll |
KERNEL32.dll |
USER32.dll |
Total processes
38
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2364 | timeout -c 5 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3128 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | — | bewe.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3164 | "C:\Users\admin\Desktop\bewe.exe" | C:\Users\admin\Desktop\bewe.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3708 | "C:\Windows\System32\cmd.exe" /c timeout -c 5 & del "C:\Users\admin\Desktop\bewe.exe" /f /q | C:\Windows\System32\cmd.exe | — | bewe.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
133
Read events
112
Write events
21
Delete events
0
Modification events
| (PID) Process: | (3164) bewe.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\ex_data\data |
| Operation: | write | Name: | ext |
Value: 2E006D007800680063006D00790070000000 | |||
| (PID) Process: | (3164) bewe.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\keys_data\data |
| Operation: | write | Name: | public |
Value: 0602000000A400005253413100080000010001001F3CBCAE5A87744E274B379DC4B84FA44BCA83795049ABBDF7D05803A07DDD9A46D00F88B0FC47AACB2A18DAB8F702467D1D864288EDD12D45925EA25DAE02236C7A6F6448411EBC920F723BFBA76501766B743B608A16CFDD441AEF98A0A1136EC30A8004198C02C44A6A54CD7E04FE9E3792EF97E6BA4524E37C2C1B9C85ED73D5DF0E05187C4A7F023A7AE0404D5149E3B9BDE10F2B9201469D634B54E0001B5342BF6A02FECA6C0A54FE05AE5DD116C49377B151CD5E65A028AA52783566A006A6B58D787ECB0AB126159ECCE7D7AB568BC2520D2200EB36ADB97E24BDE3BA2A3C449379E2172435774C5A8ED615796C4E3813EEA7265AB6901F30DB66A7 | |||
| (PID) Process: | (3164) bewe.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\keys_data\data |
| Operation: | write | Name: | private |
Value: 94040000262F26615E4DA903872B986323159A382679C32BDAEAD122C396BA71A8E92CDEE79CA60EC75C9D5FDFA8848CDF7E6E9ECC2DED9813B78A6C75FDA074A6A80BAEC0AC3447D4F6CEAFBAC27FFDEBC0F18A19FACA6D3AC24208EC005DFF554248FDB58A90FE44E0D3C520C66BA6B34F2ED6B0F4D807F84B841AA831632C87B55B98DDA45B667EA20D9F2E1FF8924D9990C29088C12A5B13AD6854A4F8C9208A9180F1994AFA886CCBB9D6E6045C367CB87CCB353C21E5E6C6ECF329F04ABDE4B9B5488FB9BF45EEC29C3DBF8B112958B56E6EAF1B601F030755088333803FA4495D40AC5FBBD7411AE0A8C576621FE8138D2E8702F9045F54041CBDFFBC38333E49BFCF64E4A13A65628C3378BD4A525D2637C84744604B7EE8D051CF33B96BAA98EED988B7A3BED9EC536F88F243DEC68004B4CFD7CC56D7EB192F50071076C941F11C6207A6B5223322291731177F3E92DA717B9CF5C1A15650DCFDB49AC6BC55F8BC5E492CE44EE11D2D4BE95FC3B8BB3BEE3C92EA238E9CF971205BF488F02CF03365397F6A3D9EF76485F3F76F0AFE5322B2029BDA2D8F1EDE911820B4674729B9D40B8375C197680A11F75EFAD14988C6C62EED38DDBCA0DF4DA091F539379F155FC63A414B8CB2A78B8705D44BA8F0CC0A6277C951E6AD3E5FC8CB700F639F3EA456554CABC375F0BDE1D7C1030C5BB3CF3D15DD3A0CBAF3A963C3E6B1477674E4A63D6C43375F9361616F3A96F92178E188255E894B3A6B82EE024A67D01074DD40C370D7C005272390B36CB07D7AFEDBBBA531D006A8331FD7B621A92CA3320FCE0CE49DBA3DD188F8A3723FEA3779FF1226633D312EA5AF08F23AEE498403E50474223F711BA9F72CC5AE5EF2448FD01BD3D23DBFA4D2A0CED623E8B72DA5313C0E65ADAB1CE44FE126732756DA8536F7FA2A71A1AB1E778CE8ACCD3E5DCB08FFFCD27C047EEEC5C796F88A102FCC7A3B7142A8249A55A56E47B1C928F5BE407260991DE41A8CEA3FD24DB349984A190521BD2A39268A487FC570C31CF47D1BAF33D94ECA462F67C24AA0CC65118819F0A8A113BE9FA326797408837DB3799603A1E2F6036AA0935475267EB2F803A29EA7DB3E7D16D6005B5403333DC4F5C138E3E756F603C930DBF776ED9043528A481DDCEDC68D1D0E1285BD3C02D9F8D7DDADC83E55341F488AE3D5EAEED13847285BCE44B9EB1F1218E725EB56E63700469BBB38DBDB2E223058785E35D06B6E2B8ECFAB737EF0209EB1DEA275679309DA457FB7C43F12575135FFED29EDA3AF7F874BF001AF75F226EB3E28141C88E1B01158D915A18B7CAE57E6E0D12BD6BE189C7417D015029127C68450BB26F34449738F3DBE754657249C64CAFD35C06D6D7836B05F8A371C2BFF773BE640ADE493E79E893999BEC0F501DDAEA442C26823024F2072048C4BD3A9B98BDD336864A29FCE78EA1A9E4AA23E1AB56A2D3B25C3C8DD535D9F776A10355D98F1A869E3F24E8B2FDC355AB266B498B18FA2E238317DFA62E2E7E43893E97E3AA90821ACE38B427DBCEEB0E46E4A6E90E1196259D7945E7F0675C9BAD688CEEB897E03B812ACDF0A1CBB4F8F852A4CC7191CDE9B29B8CBC8A94E7F350BCB06D440D3A1DF669C91C656D542D1B2E8A785E87DD1F759BD16981BDC1D1EC0F43DD827767410F128A1E93F6D3F9877E8194D5212EF80119966784903026D2D73230BEFF82B5CD4922D73258D587736E738086C5175133FCB02DC1DCF8F71149DF669778D3057C7965F246AB9A34F2806B223619631F007C3B4D9BAA0E3502E60A5B4D4FFF7D4F174EAEF8062F747C5465D3EB393FCCF36F591CC85E7AA1134F4BB0F8493E03DAE105D904A8DD403F67592FCF90AA33D52062536F8584B64A95F908376582A383015E6117EC617A676726B005F1606916DFAAC18076F63DCEEE9A3CC56D3DD1091A759F340C7051FF953C0FA30B7C2ADB6606895BDE062EC3A46D3E9C54B75E6D99E704BCE1871157C6D5368ABDE152422A4D64D205C23623CDA08D5EF9ACC560F10BB66A33CE532BD9B367F6499C61E6CC24C0BCBB11D9D9FD0288F768967D0E6370294E176C102623714D045C01E49F1F33D9D250140A76935BBC1378A28DB8103A459CF1E019F8130040A85F3C77F5859C9BFB69493E6C8B3AB92A08EC9BEACE27B58A3FC174C70DD9A734243E04F99A5351A614690A4931820BB58CC06AAB2633C232C12BC660D42ACDDC5E33215E526736517FE38C43787479A3BD1911436779A5C4E8ED725F6838D85C0862FFDCD1D81D0547D2DB0184980272A232854598BAEDD89CD78049EBF5DD63437944F970B77E8350A5E93B2A57D17DC75E91D8B3A5B596399AD964630B101AC1BDCFBC7 | |||
| (PID) Process: | (3164) bewe.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3164) bewe.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3164) bewe.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bewe_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3164) bewe.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bewe_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3164) bewe.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bewe_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3164) bewe.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bewe_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3164) bewe.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bewe_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
0
Suspicious files
279
Text files
205
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3164 | bewe.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | — | |
MD5:— | SHA256:— | |||
| 3164 | bewe.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobData | — | |
MD5:— | SHA256:— | |||
| 3164 | bewe.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobSettings | — | |
MD5:— | SHA256:— | |||
| 3164 | bewe.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\addressbook.acrodata | — | |
MD5:— | SHA256:— | |||
| 3164 | bewe.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\CRLCache\0FDED5CEB68C302B1CDB2BDDD9D0000E76539CB0.crl | — | |
MD5:— | SHA256:— | |||
| 3164 | bewe.exe | C:\Users\admin\.oracle_jre_usage\MXHCMYP-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 3164 | bewe.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\CRLCache\CE338828149963DCEA4CD26BB86F0363B4CA0BA5.crl | — | |
MD5:— | SHA256:— | |||
| 3164 | bewe.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\MXHCMYP-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 3164 | bewe.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\MXHCMYP-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 3164 | bewe.exe | C:\Users\admin\AppData\Local\VirtualStore\MXHCMYP-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
194
TCP/UDP connections
97
DNS requests
97
Threats
141
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3164 | bewe.exe | GET | 404 | 78.46.77.98:80 | http://www.2mmotorsport.biz/ | DE | xml | 345 b | suspicious |
3164 | bewe.exe | GET | 404 | 136.243.13.215:80 | http://www.holzbock.biz/ | DE | xml | 345 b | suspicious |
3164 | bewe.exe | GET | 404 | 74.220.215.73:80 | http://www.bizziniinfissi.com/ | US | xml | 345 b | malicious |
3164 | bewe.exe | POST | 404 | 78.46.77.98:80 | http://www.2mmotorsport.biz/uploads/graphic/kakasese.bmp | DE | xml | 345 b | suspicious |
3164 | bewe.exe | POST | 404 | 192.185.159.253:80 | http://www.pizcam.com/content/tmp/soruimke.png | US | xml | 345 b | malicious |
3164 | bewe.exe | GET | 404 | 138.201.162.99:80 | http://www.fliptray.biz/ | DE | xml | 345 b | malicious |
3164 | bewe.exe | POST | 404 | 138.201.162.99:80 | http://www.fliptray.biz/uploads/image/imsemo.jpg | DE | xml | 345 b | malicious |
3164 | bewe.exe | POST | 404 | 83.138.82.107:80 | http://www.swisswellness.com/news/images/sosesoim.jpg | DE | xml | 345 b | whitelisted |
3164 | bewe.exe | POST | 404 | 74.220.215.73:80 | http://www.bizziniinfissi.com/content/pics/keth.gif | US | xml | 345 b | malicious |
3164 | bewe.exe | POST | 404 | 136.243.13.215:80 | http://www.holzbock.biz/content/tmp/esruheso.bmp | DE | xml | 345 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3164 | bewe.exe | 78.46.77.98:80 | www.2mmotorsport.biz | Hetzner Online GmbH | DE | suspicious |
3164 | bewe.exe | 74.220.215.73:80 | www.bizziniinfissi.com | Unified Layer | US | malicious |
3164 | bewe.exe | 217.26.53.161:80 | www.haargenau.biz | Hostpoint AG | CH | malicious |
3164 | bewe.exe | 136.243.13.215:80 | www.holzbock.biz | Hetzner Online GmbH | DE | suspicious |
3164 | bewe.exe | 192.185.159.253:80 | www.pizcam.com | CyrusOne LLC | US | malicious |
3164 | bewe.exe | 138.201.162.99:80 | www.fliptray.biz | Hetzner Online GmbH | DE | malicious |
3164 | bewe.exe | 83.138.82.107:80 | www.swisswellness.com | hostNET Medien GmbH | DE | suspicious |
3164 | bewe.exe | 212.59.186.61:80 | www.hotelweisshorn.com | green.ch AG | CH | malicious |
3164 | bewe.exe | 83.166.138.7:80 | www.whitepod.com | Infomaniak Network SA | CH | malicious |
3164 | bewe.exe | 69.16.175.42:80 | www.hardrockhoteldavos.com | Highwinds Network Group, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.2mmotorsport.biz |
| unknown |
www.haargenau.biz |
| unknown |
www.bizziniinfissi.com |
| malicious |
www.holzbock.biz |
| unknown |
www.fliptray.biz |
| malicious |
www.pizcam.com |
| unknown |
www.swisswellness.com |
| whitelisted |
www.hotelweisshorn.com |
| unknown |
www.whitepod.com |
| whitelisted |
www.hardrockhoteldavos.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3164 | bewe.exe | A Network Trojan was detected | ET TROJAN [eSentire] Win32/GandCrab v4/5 Ransomware CnC Activity |
3164 | bewe.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
3164 | bewe.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (gif) |
3164 | bewe.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
3164 | bewe.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (gif) |
3164 | bewe.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
3164 | bewe.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
3164 | bewe.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (jpg) |
3164 | bewe.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
3164 | bewe.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |