| File name: | TLauncher.exe |
| Full analysis: | https://app.any.run/tasks/c18083a0-25c5-4fb0-8dd6-1822c8659813 |
| Verdict: | Malicious activity |
| Analysis date: | February 08, 2021, 18:54:21 |
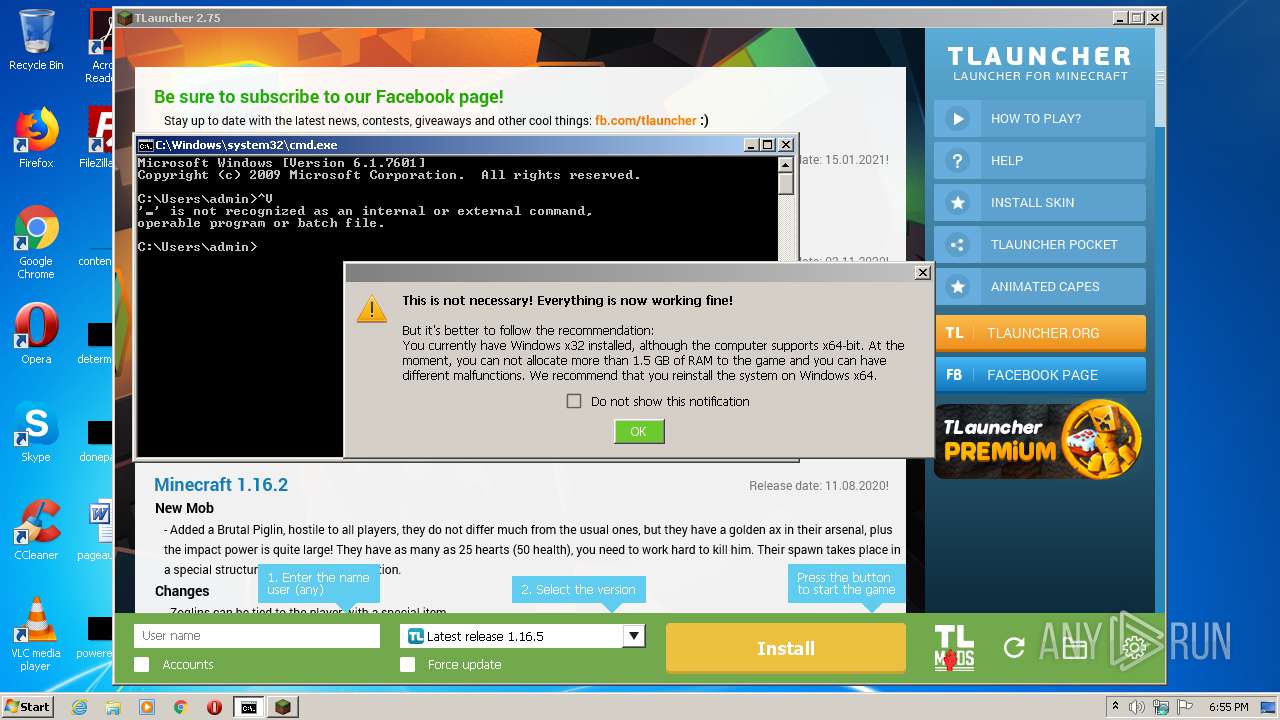
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | F592E97F080AE5D323CC0CE2A329A949 |
| SHA1: | FE998BF6F2F5321AF9F756A7A06A01290A97C55A |
| SHA256: | 5A00AFA820039B55D570D5CBDAE0CE1167272D314592AD9E951257755EA5BAC7 |
| SSDEEP: | 49152:hoQlo2tuEXgq23ttxCpG7szUMS2h07cNF+zNCkweZQT/nmDHYkmMhOq2zSxxAy:hoh20Jq23ttxH7szY2y7G+zszcv7oy |
MALICIOUS
No malicious indicators.SUSPICIOUS
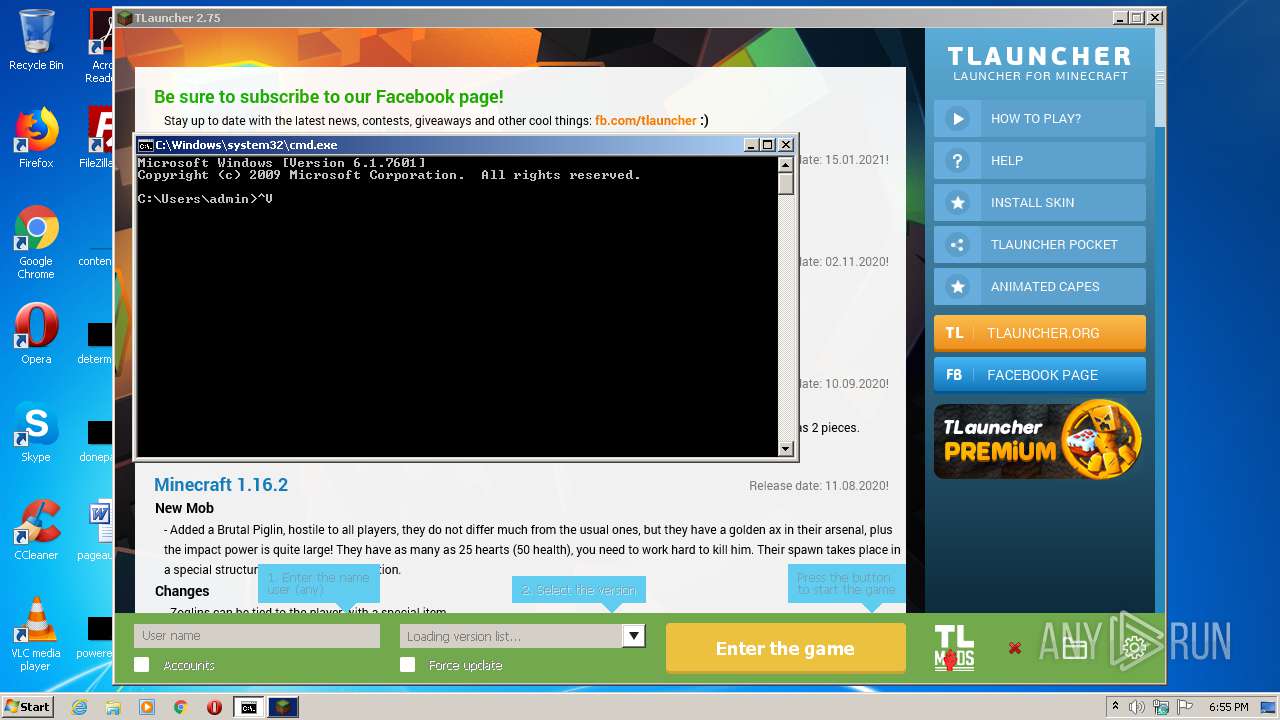
Starts application with an unusual extension
- cmd.exe (PID: 2140)
- cmd.exe (PID: 3956)
- cmd.exe (PID: 3796)
- cmd.exe (PID: 2520)
- cmd.exe (PID: 2712)
- cmd.exe (PID: 3112)
- cmd.exe (PID: 2436)
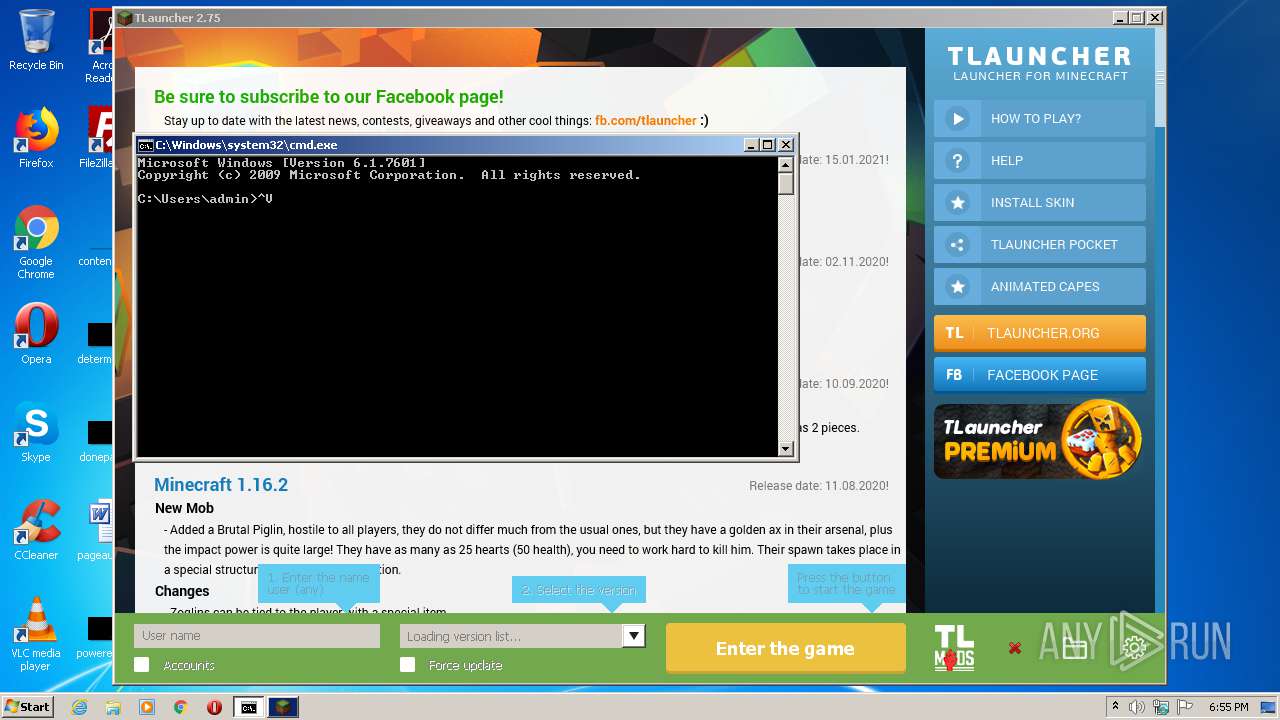
Starts CMD.EXE for commands execution
- javaw.exe (PID: 4008)
- javaw.exe (PID: 2980)
Executes JAVA applets
- TLauncher.exe (PID: 3312)
- javaw.exe (PID: 4008)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 3956)
- cmd.exe (PID: 2140)
- cmd.exe (PID: 2520)
- cmd.exe (PID: 2712)
- cmd.exe (PID: 2436)
Creates files in the user directory
- javaw.exe (PID: 4008)
- dxdiag.exe (PID: 2816)
- javaw.exe (PID: 2980)
Application launched itself
- javaw.exe (PID: 4008)
Uses SYSTEMINFO.EXE to read environment
- cmd.exe (PID: 3112)
INFO
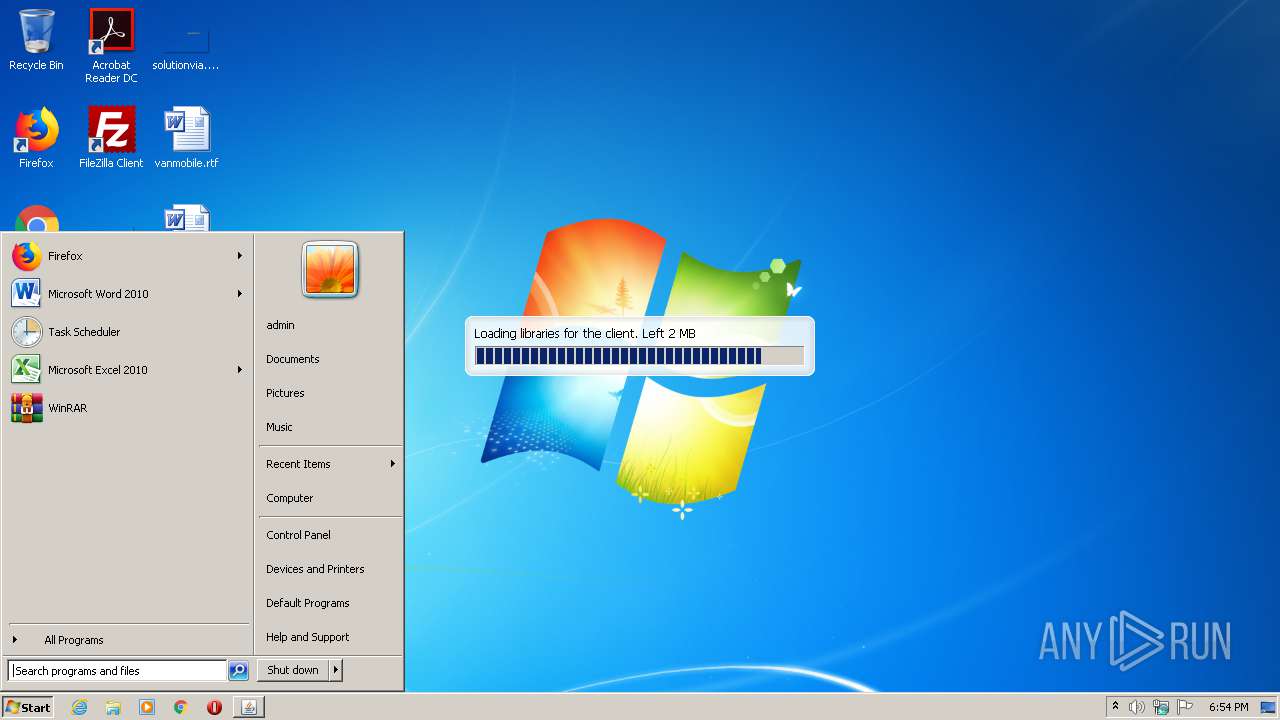
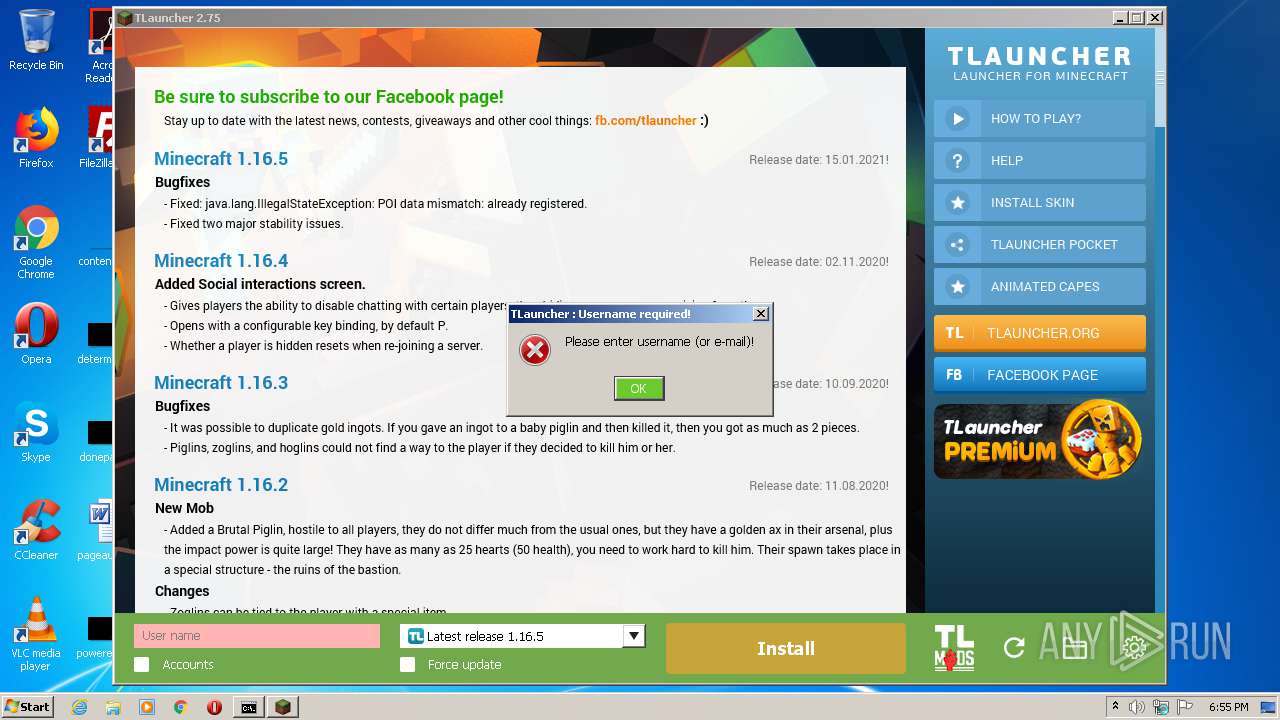
Manual execution by user
- cmd.exe (PID: 2652)
Reads settings of System Certificates
- dxdiag.exe (PID: 2816)
Dropped object may contain Bitcoin addresses
- javaw.exe (PID: 2980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:12:20 12:16:34+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.56 |
| CodeSize: | 25088 |
| InitializedDataSize: | 16896 |
| UninitializedDataSize: | 36864 |
| EntryPoint: | 0x1290 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.75.0.0 |
| ProductVersionNumber: | 2.75.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Windows NT |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | TLauncher Inc. |
| FileDescription: | TLauncher |
| FileVersion: | 2.75 |
| InternalName: | TLauncher |
| LegalCopyright: | TLauncher Inc. |
| LegalTrademarks: | - |
| OriginalFileName: | TLauncher.exe |
| ProductName: | TLauncher |
| ProductVersion: | 2.75.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Dec-2020 11:16:34 |
| Detected languages: |
|
| CompanyName: | TLauncher Inc. |
| FileDescription: | TLauncher |
| FileVersion: | 2.75 |
| InternalName: | TLauncher |
| LegalCopyright: | TLauncher Inc. |
| LegalTrademarks: | - |
| OriginalFilename: | TLauncher.exe |
| ProductName: | TLauncher |
| ProductVersion: | 2.75.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 20-Dec-2020 11:16:34 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006080 | 0x00006200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.98243 |
.data | 0x00008000 | 0x00000040 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.163808 |
.rdata | 0x00009000 | 0x00000510 | 0x00000600 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.01355 |
.bss | 0x0000A000 | 0x00008E30 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00013000 | 0x00000AA8 | 0x00000C00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.65264 |
.rsrc | 0x00014000 | 0x00002D9C | 0x00002E00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.52393 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.26212 | 728 | UNKNOWN | Process Default Language | RT_VERSION |
2 | 2.25163 | 6 | UNKNOWN | Process Default Language | RT_RCDATA |
10 | 3.39275 | 13 | UNKNOWN | Process Default Language | RT_RCDATA |
17 | 2.32193 | 5 | UNKNOWN | Process Default Language | RT_RCDATA |
18 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
20 | 1.58496 | 3 | UNKNOWN | Process Default Language | RT_RCDATA |
21 | 4.10695 | 31 | UNKNOWN | Process Default Language | RT_RCDATA |
30 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
101 | 4.04307 | 50 | UNKNOWN | Process Default Language | RT_RCDATA |
102 | 4.26779 | 115 | UNKNOWN | Process Default Language | RT_RCDATA |
Imports
ADVAPI32.DLL |
KERNEL32.dll |
SHELL32.DLL |
USER32.dll |
msvcrt.dll |
Total processes
70
Monitored processes
25
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2140 | cmd.exe /C chcp 437 & wmic os get osarchitecture | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2208 | chcp 437 | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2304 | chcp 437 | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2392 | chcp 437 | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2436 | cmd.exe /C chcp 437 & wmic qfe get HotFixID | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2520 | cmd.exe /C chcp 437 & wmic os get osarchitecture | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2652 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2684 | chcp 437 | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2712 | cmd.exe /C chcp 437 & wmic CPU get NAME | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2752 | wmic os get osarchitecture | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
889
Read events
722
Write events
151
Delete events
16
Modification events
| (PID) Process: | (4008) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
| (PID) Process: | (2980) javaw.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2980) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
| (PID) Process: | (3784) systeminfo.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3784) systeminfo.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\mlang.dll,-4386 |
Value: English (United States) | |||
| (PID) Process: | (2816) dxdiag.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectX Diagnostic Tool |
| Operation: | write | Name: | DxDiag In SystemInfo |
Value: 1 | |||
| (PID) Process: | (2816) dxdiag.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectX Diagnostic Tool |
| Operation: | delete value | Name: | DxDiag In SystemInfo |
Value: 1 | |||
| (PID) Process: | (2816) dxdiag.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectX Diagnostic Tool |
| Operation: | write | Name: | DxDiag In DirectDraw |
Value: 1 | |||
| (PID) Process: | (2816) dxdiag.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectX Diagnostic Tool |
| Operation: | delete value | Name: | DxDiag In DirectDraw |
Value: 1 | |||
| (PID) Process: | (2816) dxdiag.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectX Diagnostic Tool |
| Operation: | write | Name: | DxDiag In DirectSound |
Value: 1 | |||
Executable files
6
Suspicious files
20
Text files
55
Unknown types
160
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4008 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\javax\inject\javax.inject\1\javax.inject-1.jar.tlauncherdownload | — | |
MD5:— | SHA256:— | |||
| 4008 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\aopalliance\aopalliance\1.0\aopalliance-1.0.jar.tlauncherdownload | — | |
MD5:— | SHA256:— | |||
| 4008 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\com\google\inject\guice\4.1.0\guice-4.1.0.jar.tlauncherdownload | — | |
MD5:— | SHA256:— | |||
| 4008 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\net\sf\jopt-simple\jopt-simple\4.9\jopt-simple-4.9.jar.tlauncherdownload | — | |
MD5:— | SHA256:— | |||
| 4008 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\com\google\inject\extentions\guice-assistedinject\4.1.0\guice-assistedinject-4.1.0.jar.tlauncherdownload | — | |
MD5:— | SHA256:— | |||
| 4008 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\log4j\log4j\1.2.17\log4j-1.2.17.jar.tlauncherdownload | — | |
MD5:— | SHA256:— | |||
| 4008 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\com\google\guava\guava\19.0\guava-19.0.jar.tlauncherdownload | — | |
MD5:— | SHA256:— | |||
| 4008 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\org\apache\commons\commons-lang3\3.4\commons-lang3-3.4.jar.tlauncherdownload | — | |
MD5:— | SHA256:— | |||
| 4008 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\org\tukaani\xz\1.5\xz-1.5.jar.tlauncherdownload | — | |
MD5:— | SHA256:— | |||
| 4008 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\org\tlauncher\tlauncher-resource\1.4\tlauncher-resource-1.4.jar.tlauncherdownload | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
202
TCP/UDP connections
28
DNS requests
12
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2980 | javaw.exe | HEAD | 200 | 104.20.235.70:80 | http://page.tlauncher.org/ | US | — | — | malicious |
2980 | javaw.exe | GET | 200 | 104.20.234.70:80 | http://repo.tlauncher.org/update/downloads/libraries/org/tlauncher/authlib/libraries-1.7.json | US | text | 143 Kb | whitelisted |
2980 | javaw.exe | GET | 200 | 104.20.234.70:80 | http://repo.tlauncher.org/update/downloads/configs/inner_servers.json | US | text | 3.78 Kb | whitelisted |
2980 | javaw.exe | GET | 200 | 104.20.235.70:80 | http://img.tlauncher.org/update/downloads/configs/client/style_new_bes_fontov.css | US | text | 5.76 Kb | malicious |
2980 | javaw.exe | GET | 200 | 104.20.235.70:80 | http://img.tlauncher.org/update/downloads/configs/client/images/icons/btn4.png | US | image | 205 b | malicious |
2980 | javaw.exe | GET | 200 | 104.20.235.70:80 | http://img.tlauncher.org/update/downloads/configs/client/images/icons/btn2.png | US | image | 193 b | malicious |
4008 | javaw.exe | GET | 200 | 46.4.112.226:80 | http://advancedrepository.com/update/downloads/libraries/com/google/inject/guice/4.1.0/guice-4.1.0.jar | DE | java | 658 Kb | malicious |
4008 | javaw.exe | GET | 200 | 104.20.235.70:80 | http://repo.tlauncher.org/update/downloads/libraries/com/google/inject/extentions/guice-assistedinject/4.1.0/guice-assistedinject-4.1.0.jar | US | compressed | 41.8 Kb | whitelisted |
4008 | javaw.exe | GET | 200 | 46.4.112.226:80 | http://advancedrepository.com/update/downloads/libraries/dnsjava/dnsjava/2.1.8/dnsjava-2.1.8.jar | DE | compressed | 307 Kb | malicious |
4008 | javaw.exe | GET | 200 | 104.20.235.70:80 | http://repo.tlauncher.org/update/downloads/libraries/org/tlauncher/picture-bundle/3.0/picture-bundle-3.0.jar | US | compressed | 2.08 Mb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4008 | javaw.exe | 46.4.112.226:443 | securerepository.net | Hetzner Online GmbH | DE | malicious |
4008 | javaw.exe | 46.4.112.226:80 | securerepository.net | Hetzner Online GmbH | DE | malicious |
4008 | javaw.exe | 104.20.235.70:80 | repo.tlauncher.org | Cloudflare Inc | US | malicious |
2980 | javaw.exe | 104.20.234.70:80 | repo.tlauncher.org | Cloudflare Inc | US | suspicious |
2980 | javaw.exe | 104.20.235.70:80 | repo.tlauncher.org | Cloudflare Inc | US | malicious |
2980 | javaw.exe | 104.16.167.35:443 | ajax.cloudflare.com | Cloudflare Inc | US | unknown |
2980 | javaw.exe | 65.9.68.20:443 | launchermeta.mojang.com | AT&T Services, Inc. | US | unknown |
2980 | javaw.exe | 176.9.83.82:8092 | stat.tlrepo.com | Hetzner Online GmbH | DE | suspicious |
2980 | javaw.exe | 104.20.156.70:443 | dl2.tlrepo.com | Cloudflare Inc | US | unknown |
2980 | javaw.exe | 65.9.58.11:80 | resources.download.minecraft.net | AT&T Services, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
securerepository.net |
| whitelisted |
advancedrepository.com |
| unknown |
repo.tlauncher.org |
| whitelisted |
page.tlauncher.org |
| malicious |
img.tlauncher.org |
| malicious |
ajax.cloudflare.com |
| whitelisted |
launchermeta.mojang.com |
| whitelisted |
stat.tlrepo.com |
| suspicious |
tlauncher.org |
| malicious |
dl2.tlrepo.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4008 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
4008 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
4008 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
4008 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
4008 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
4008 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |