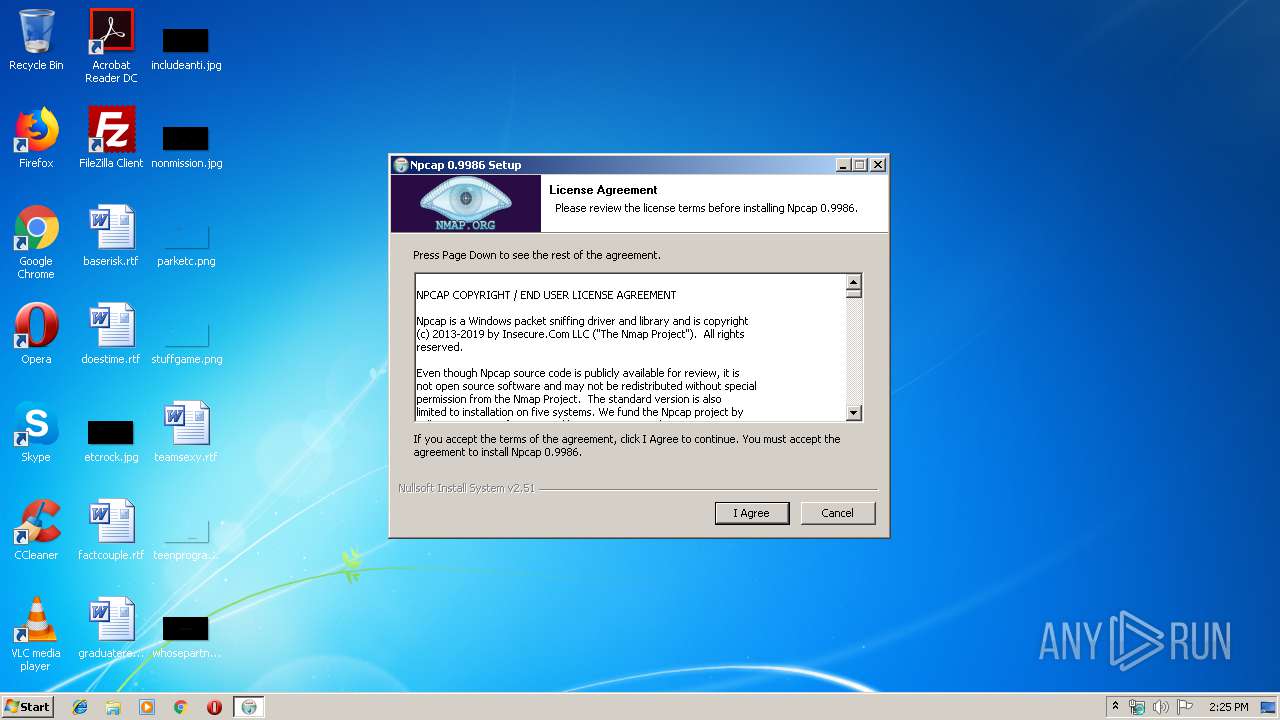
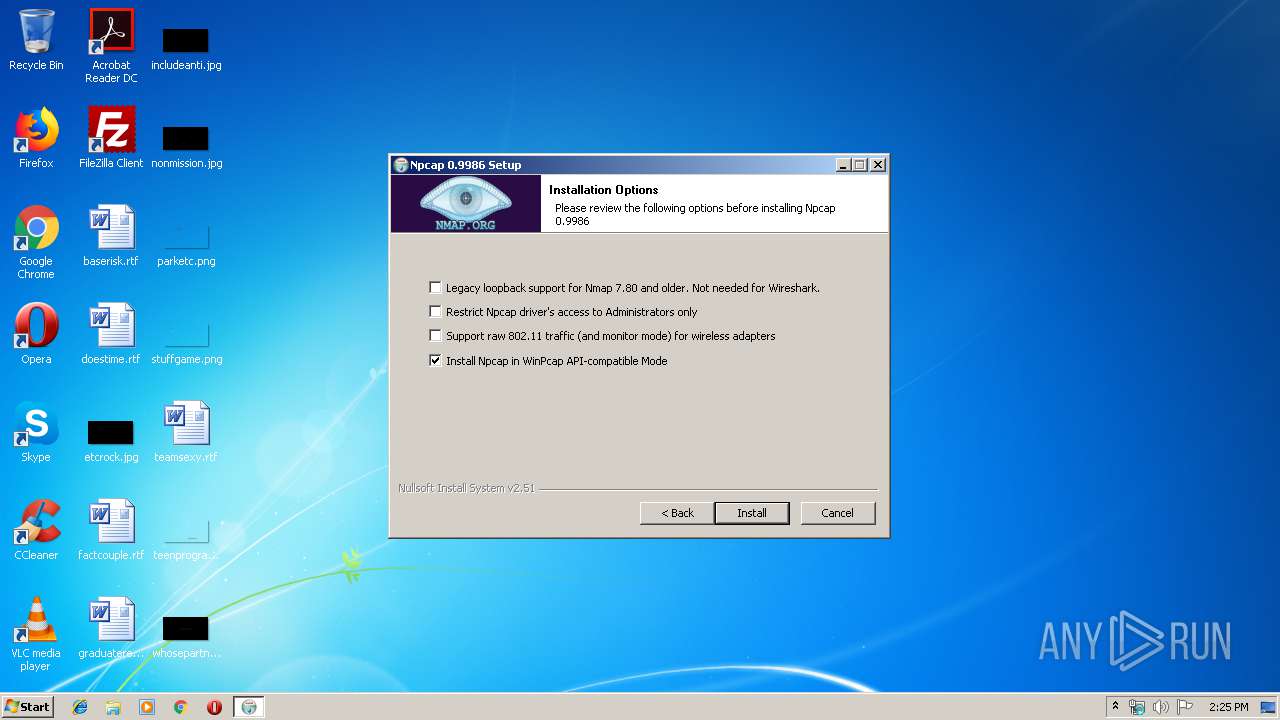
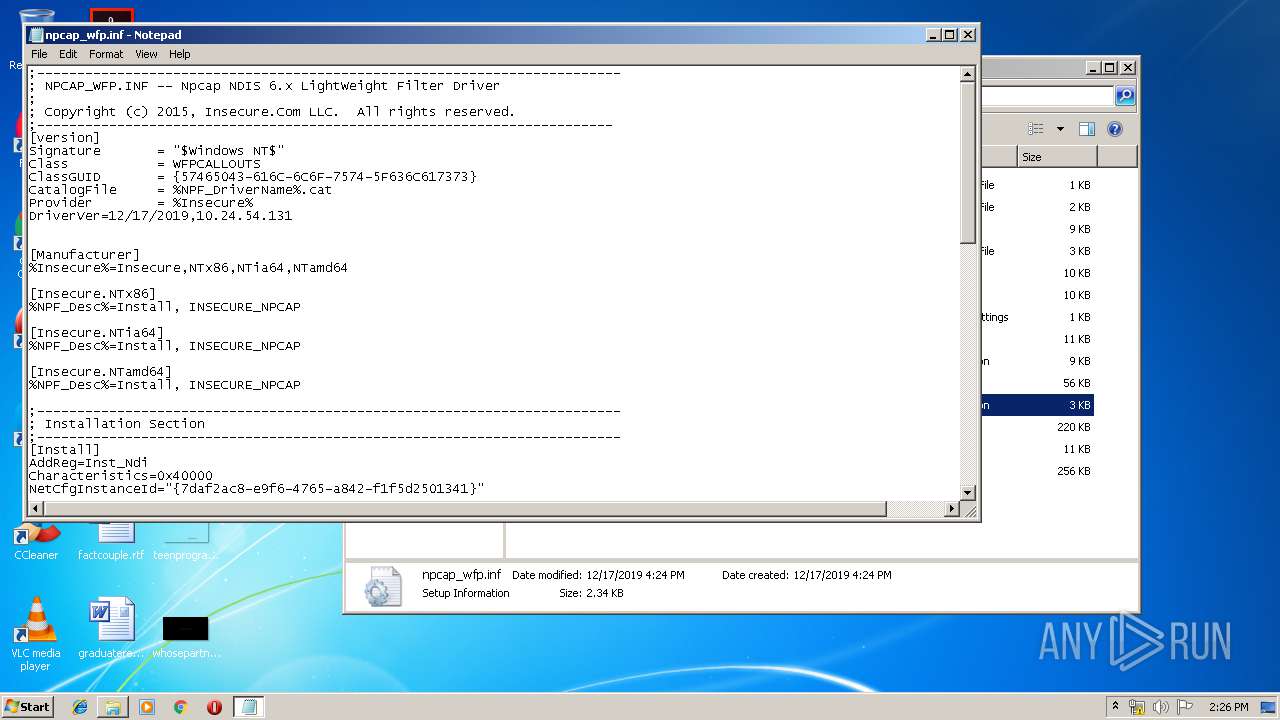
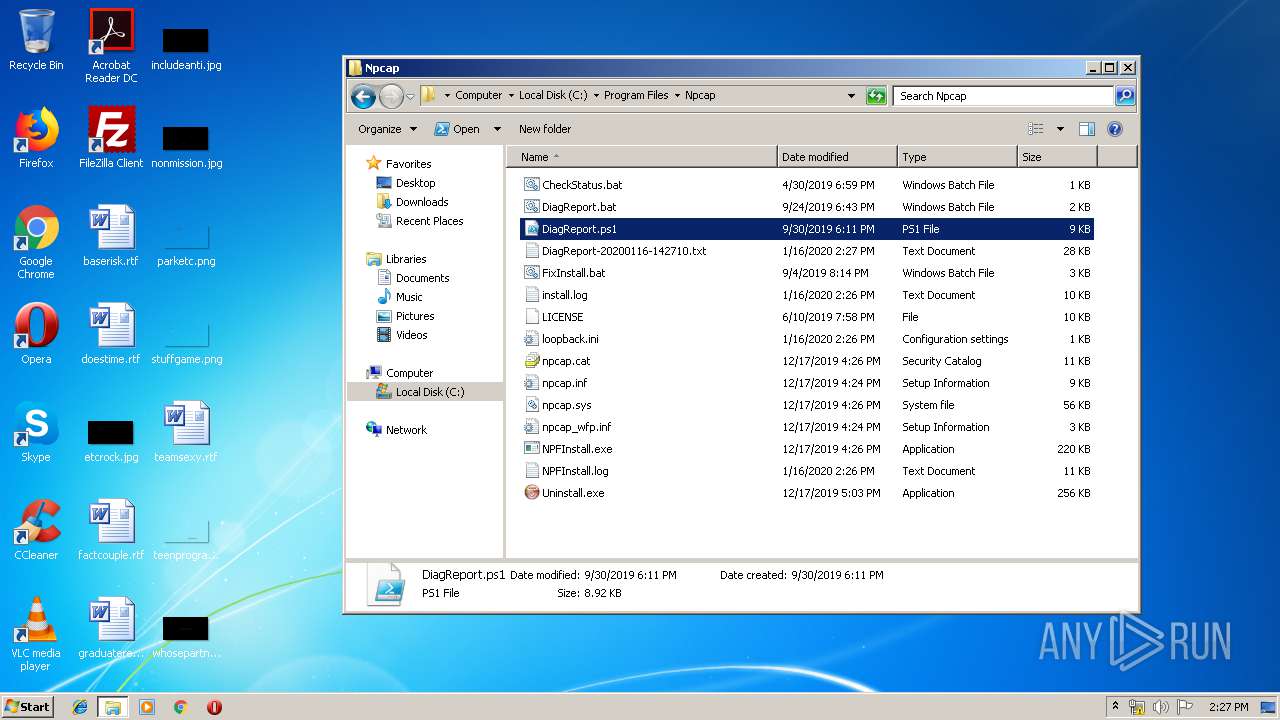
| File name: | npcap-0.9986.exe |
| Full analysis: | https://app.any.run/tasks/32847298-ebd8-4db2-b6ca-4b595b9b399f |
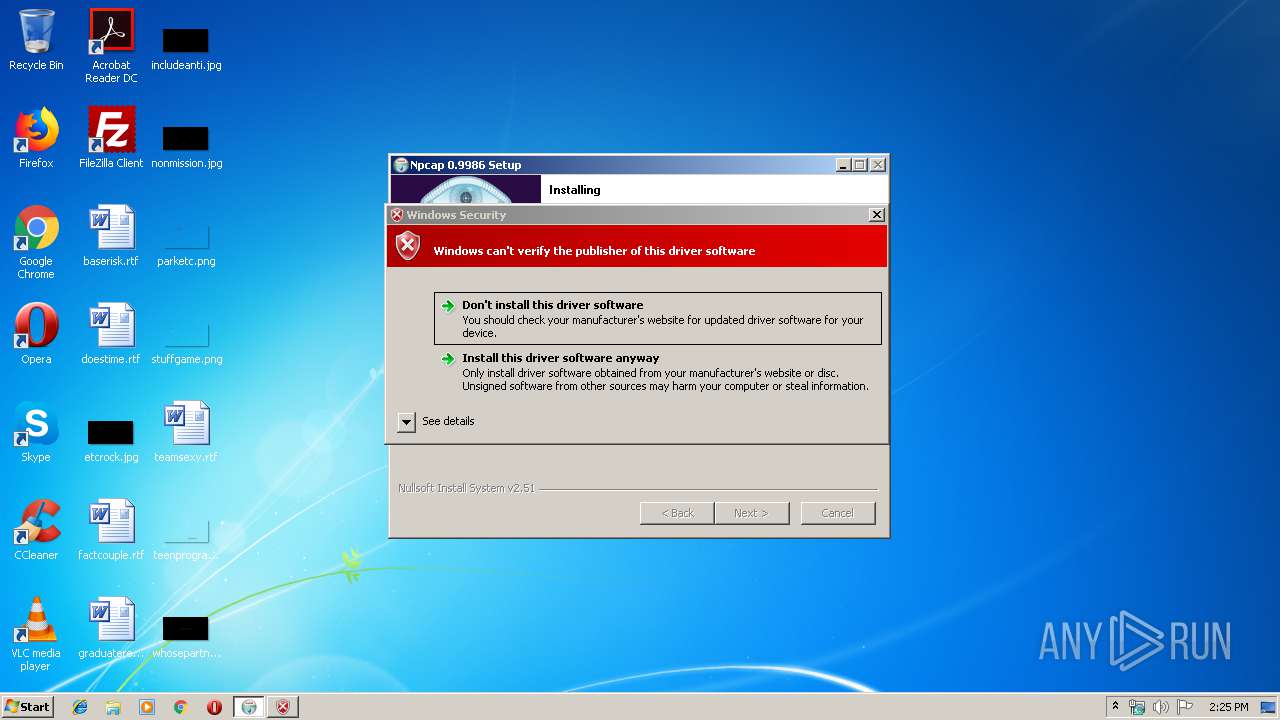
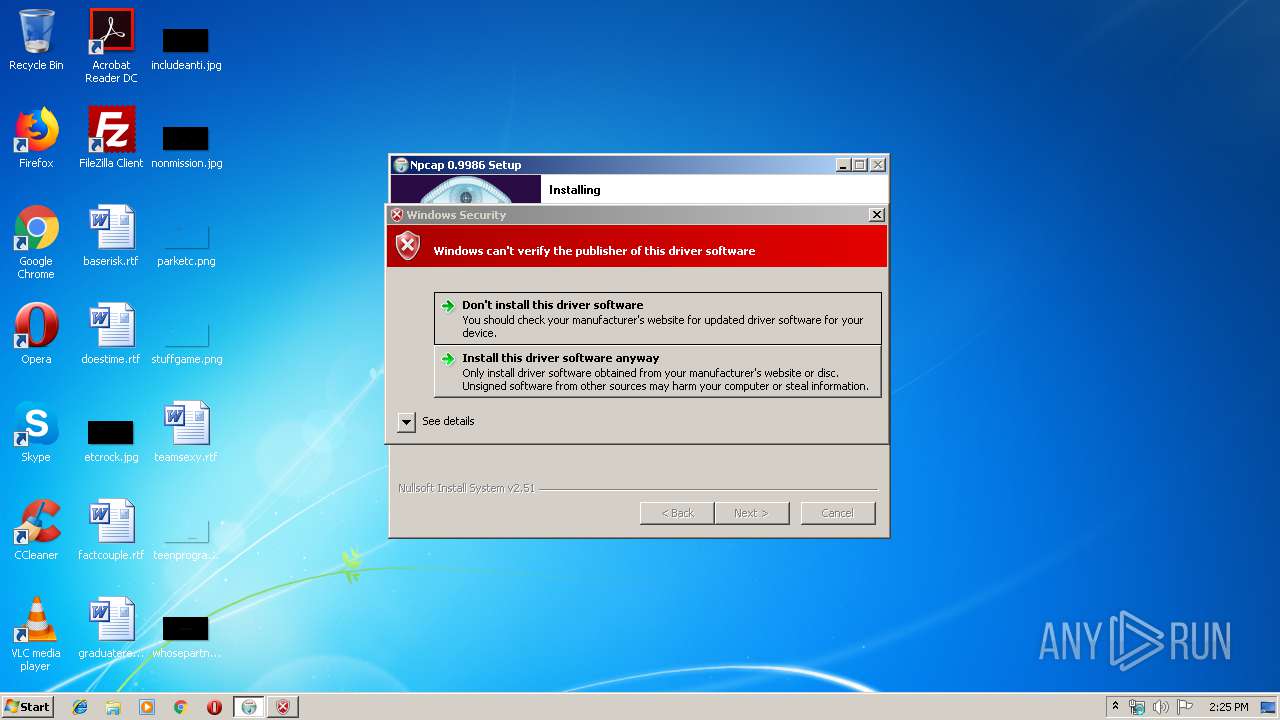
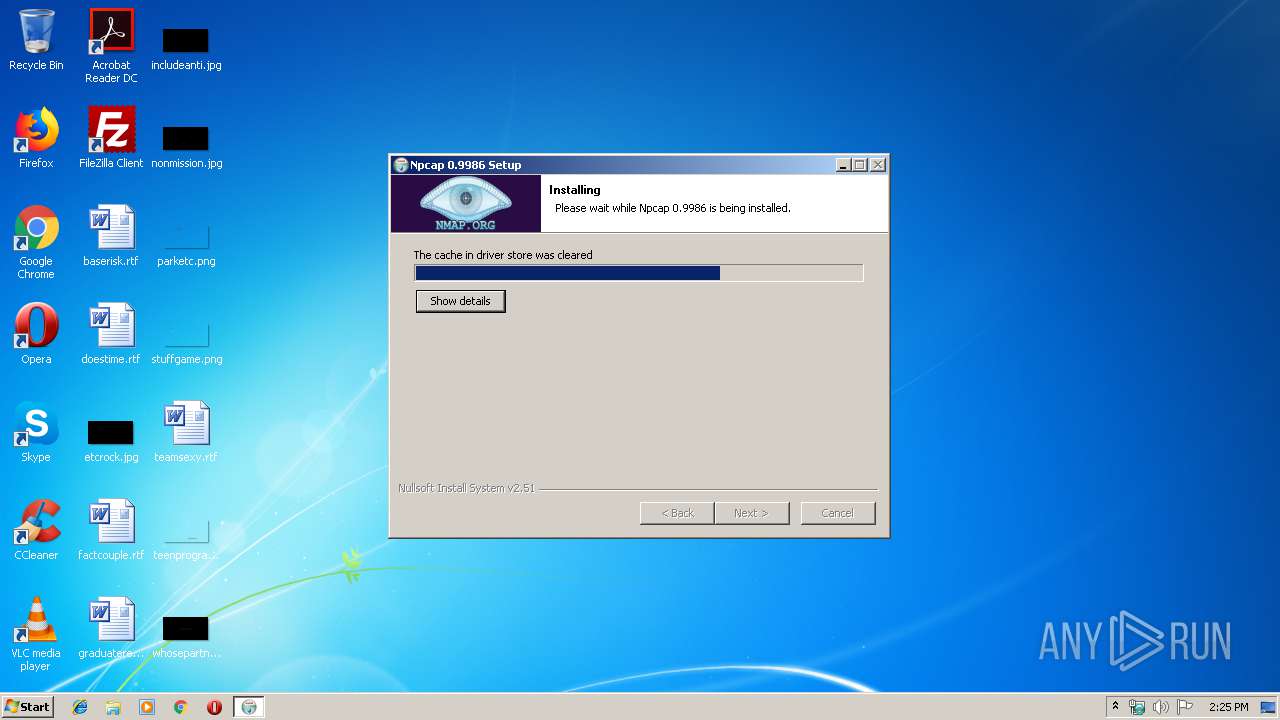
| Verdict: | Malicious activity |
| Analysis date: | January 16, 2020, 14:25:18 |
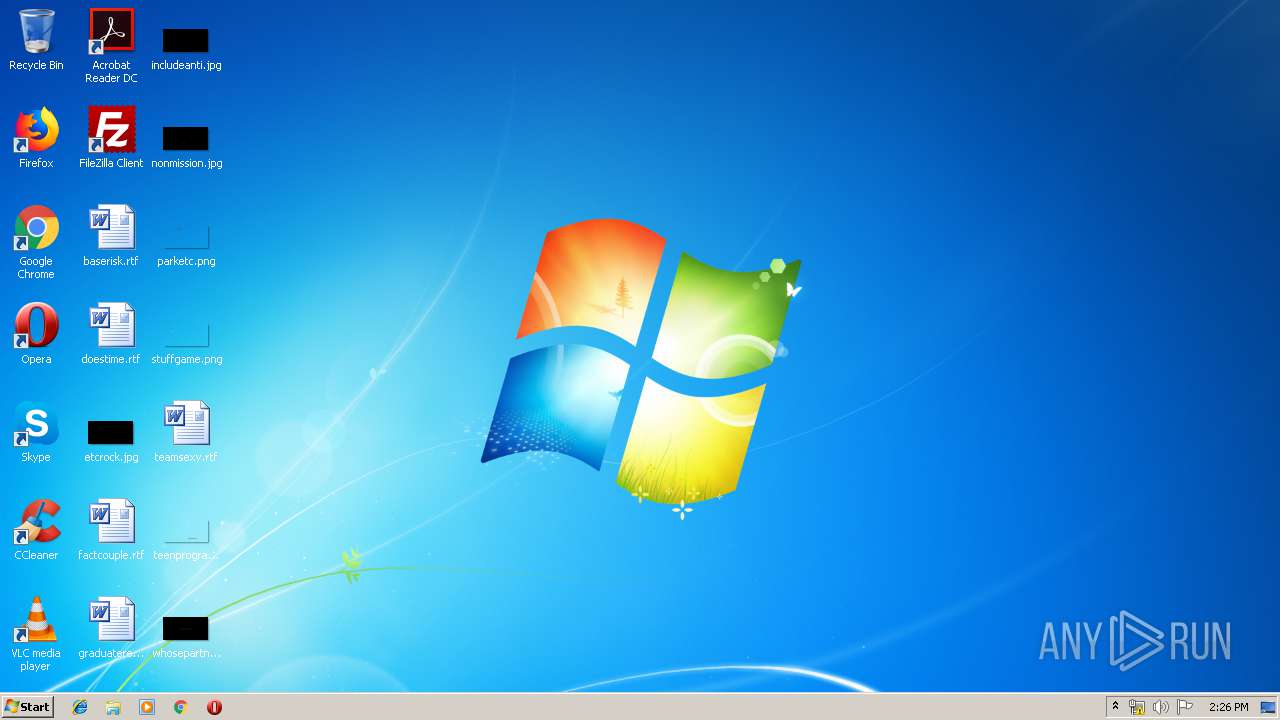
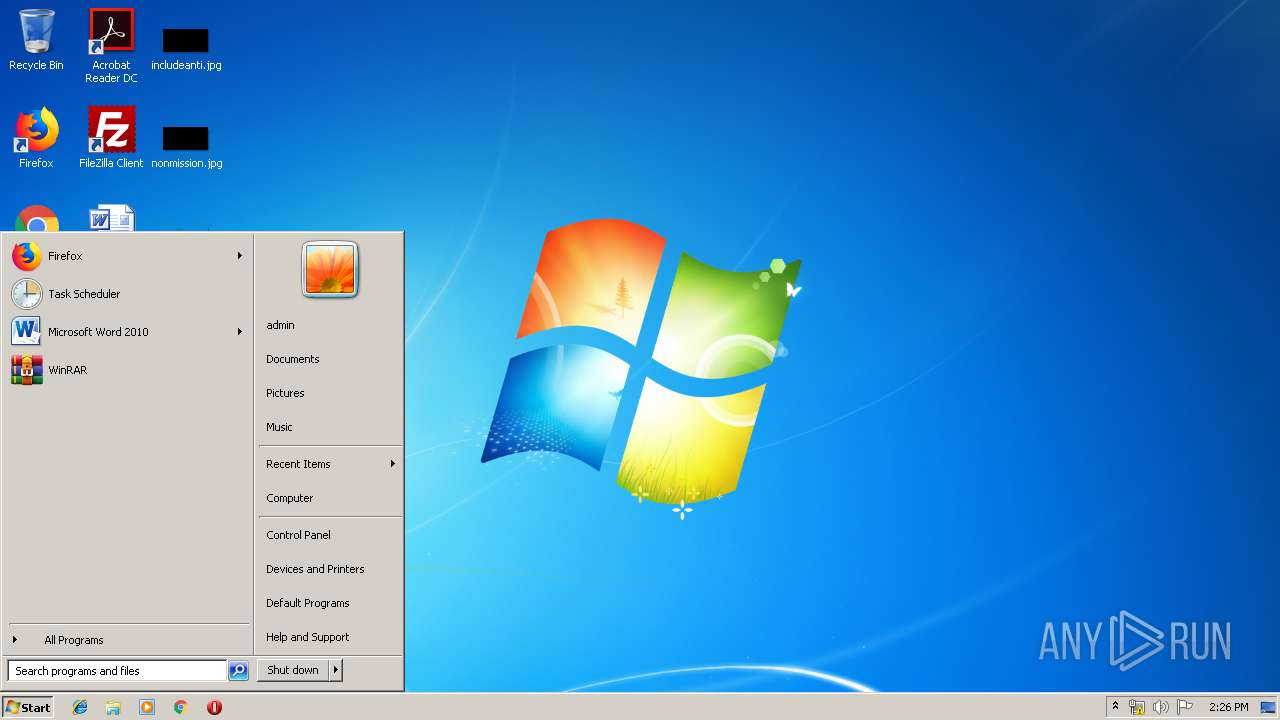
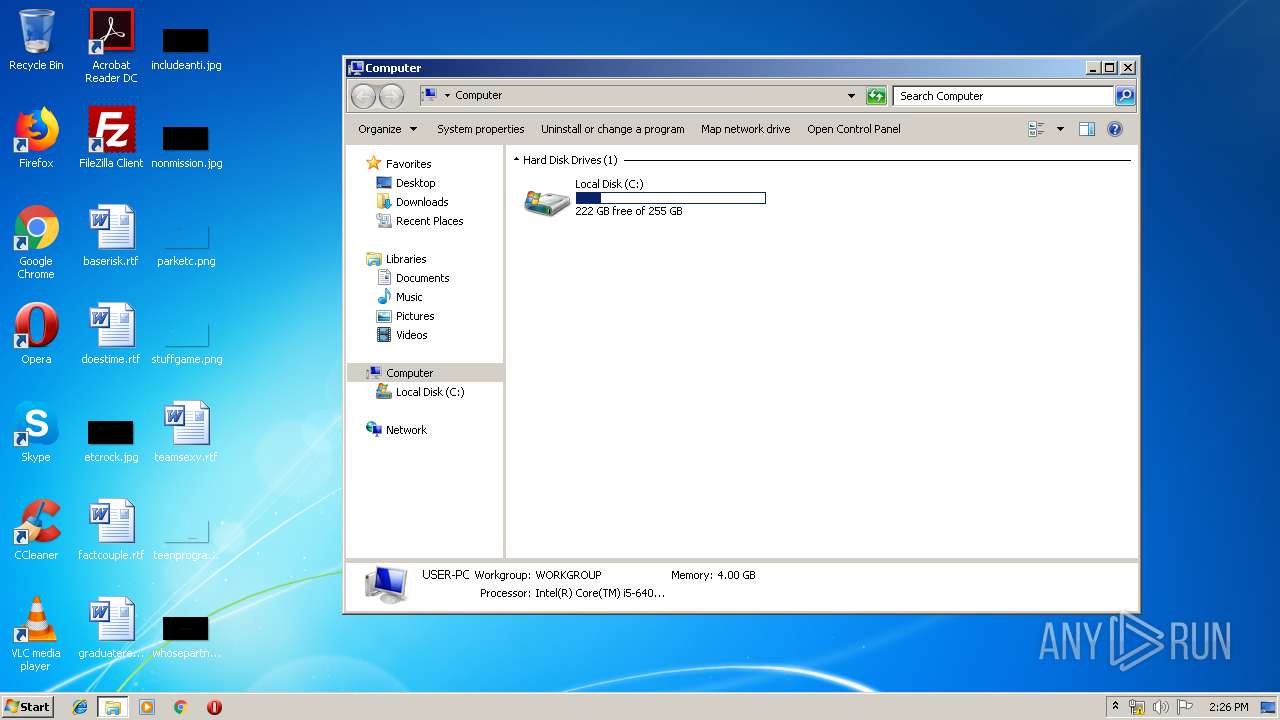
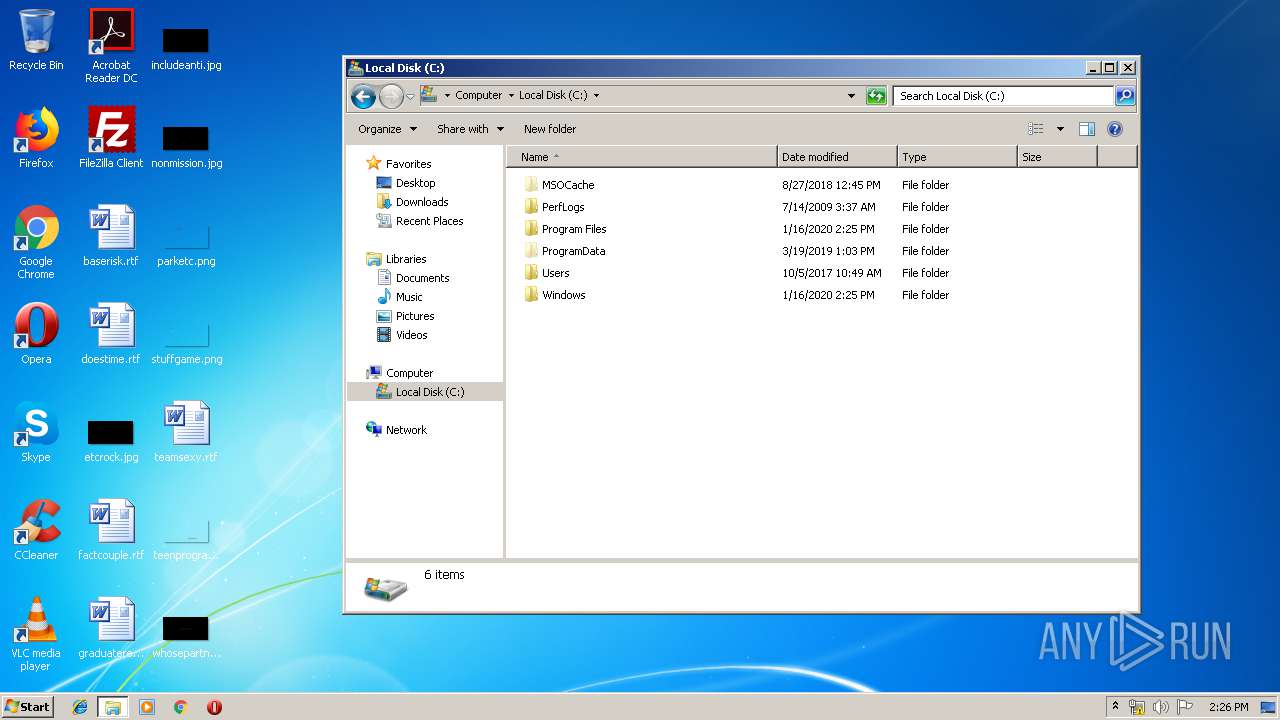
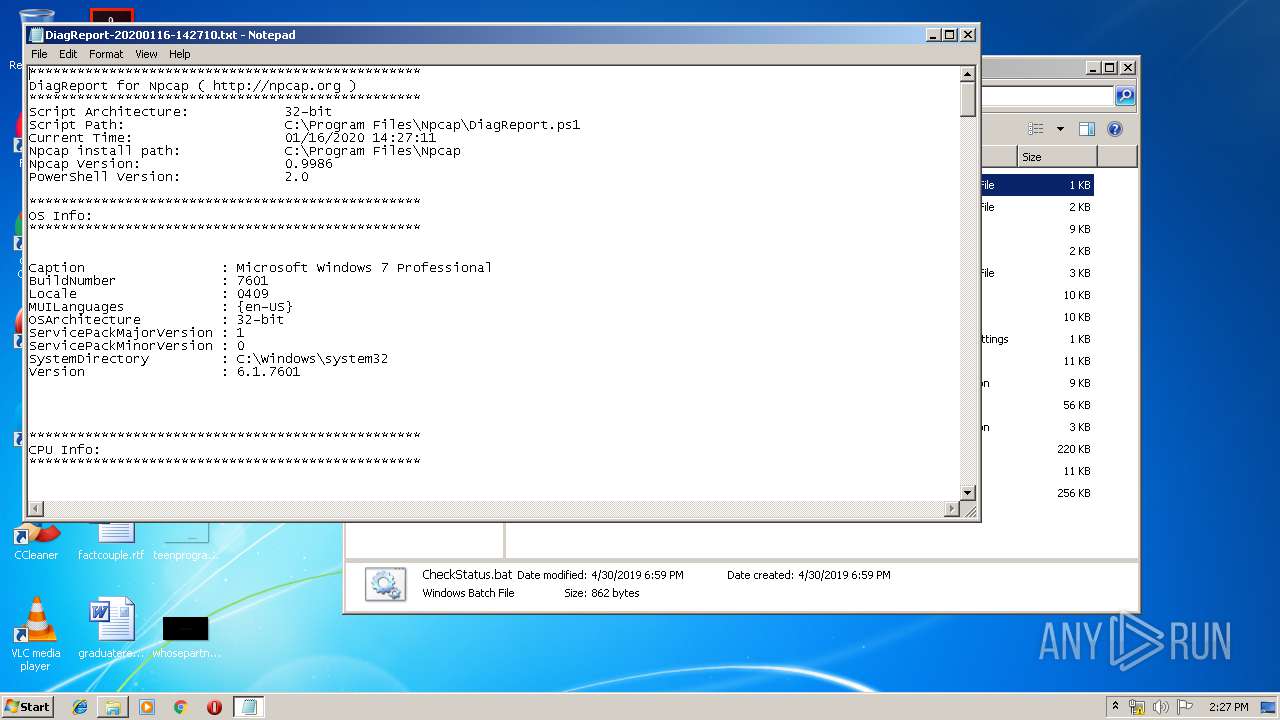
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | A31CB0DEC3F3A59DA83C549B384C5844 |
| SHA1: | 38919ED321DA0121232FFB8B148918482E831C6D |
| SHA256: | 59E7EDD7C98D076CA508F7AA536008A065E2F61366499476DB4C87FBC82FD2E3 |
| SSDEEP: | 24576:MElgi/FYxF20iawOh+DBXvrRfyQ/d7/hcne5lpjfc:bgiS20xYB/rRKQ/l/hOeNE |
MALICIOUS
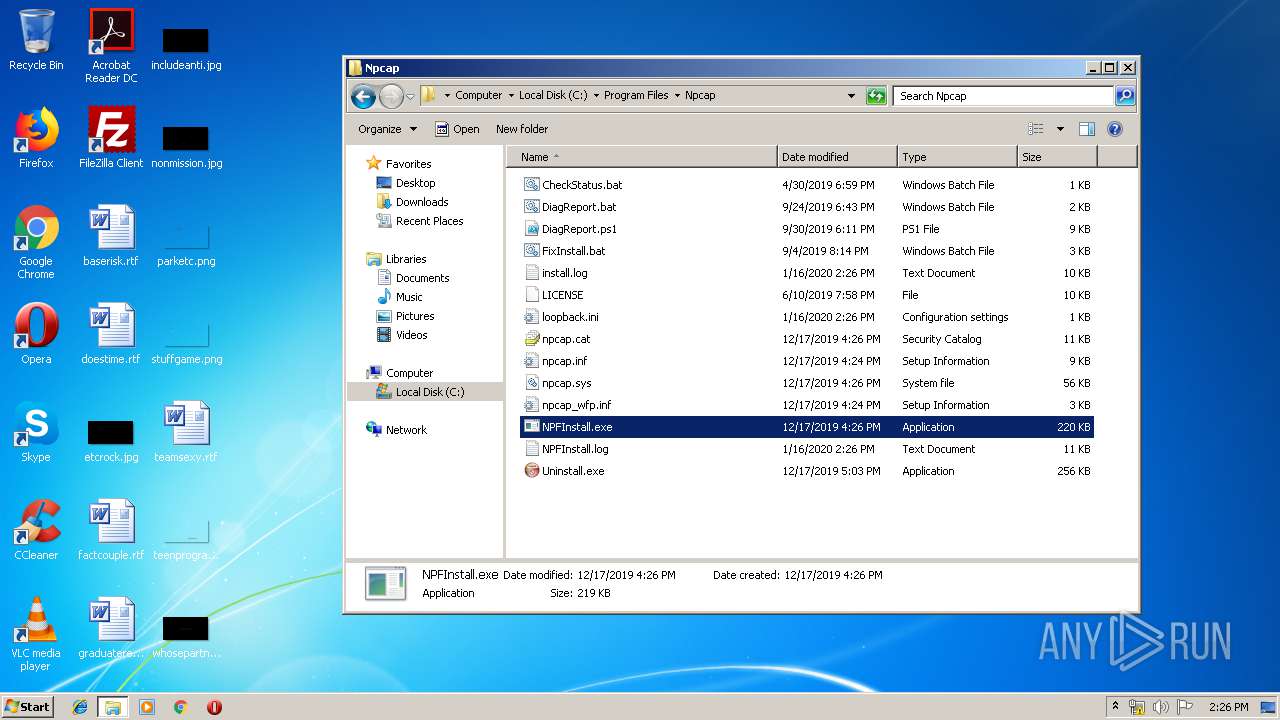
Application was dropped or rewritten from another process
- NPFInstall.exe (PID: 3796)
- NPFInstall.exe (PID: 2892)
- nsCC69.tmp (PID: 960)
- nsC929.tmp (PID: 3032)
- NPFInstall.exe (PID: 2856)
- nsCB8D.tmp (PID: 3872)
- nsCA15.tmp (PID: 2104)
- NPFInstall.exe (PID: 3836)
- nsE46.tmp (PID: 2184)
- NPFInstall.exe (PID: 2332)
- ns2401.tmp (PID: 1488)
- nsDD8.tmp (PID: 3136)
- NPFInstall.exe (PID: 2348)
- NPFInstall.exe (PID: 1764)
- NPFInstall.exe (PID: 1880)
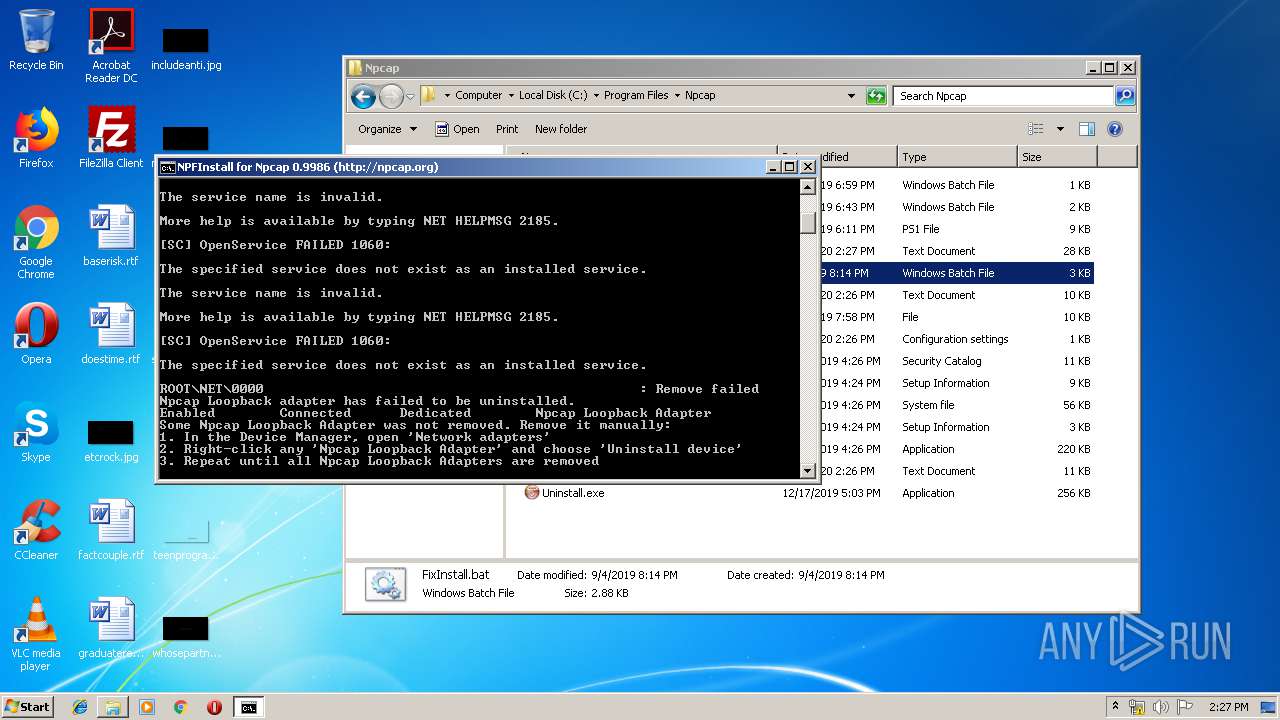
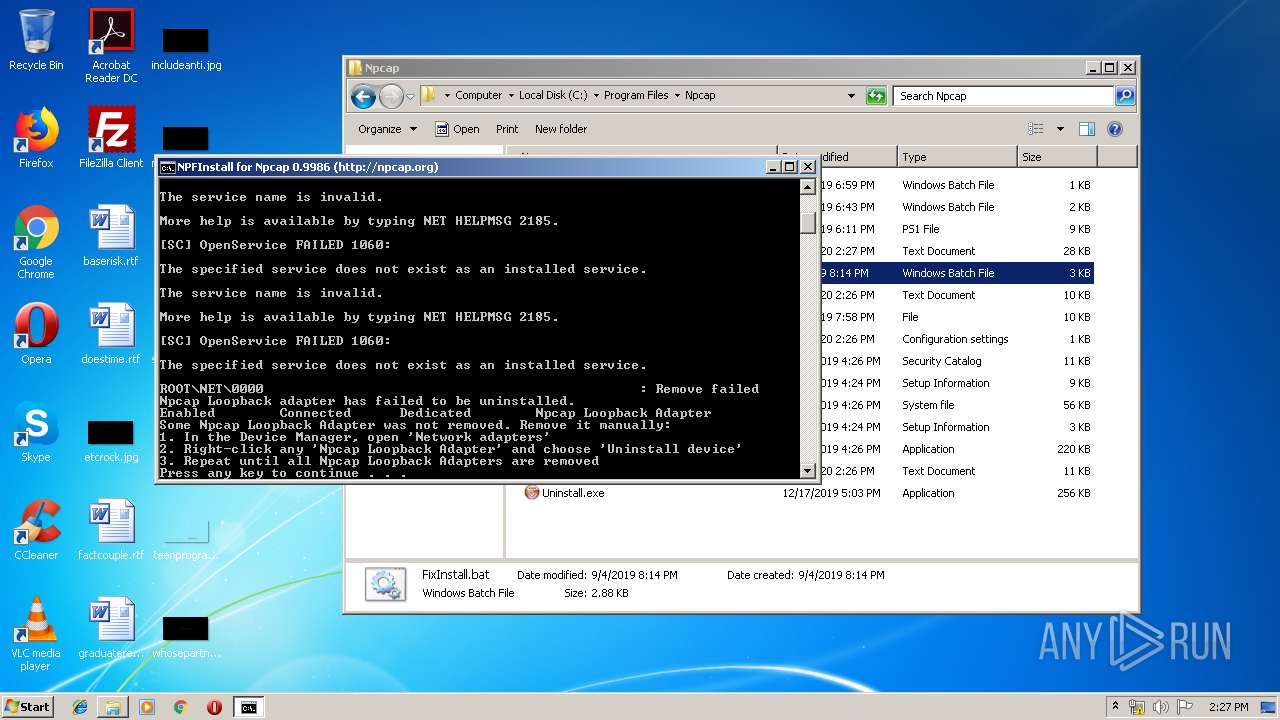
Loads dropped or rewritten executable
- npcap-0.9986.exe (PID: 928)
Changes settings of System certificates
- certutil.exe (PID: 3948)
Uses Task Scheduler to run other applications
- ns2401.tmp (PID: 1488)
Loads the Task Scheduler COM API
- SCHTASKS.EXE (PID: 3576)
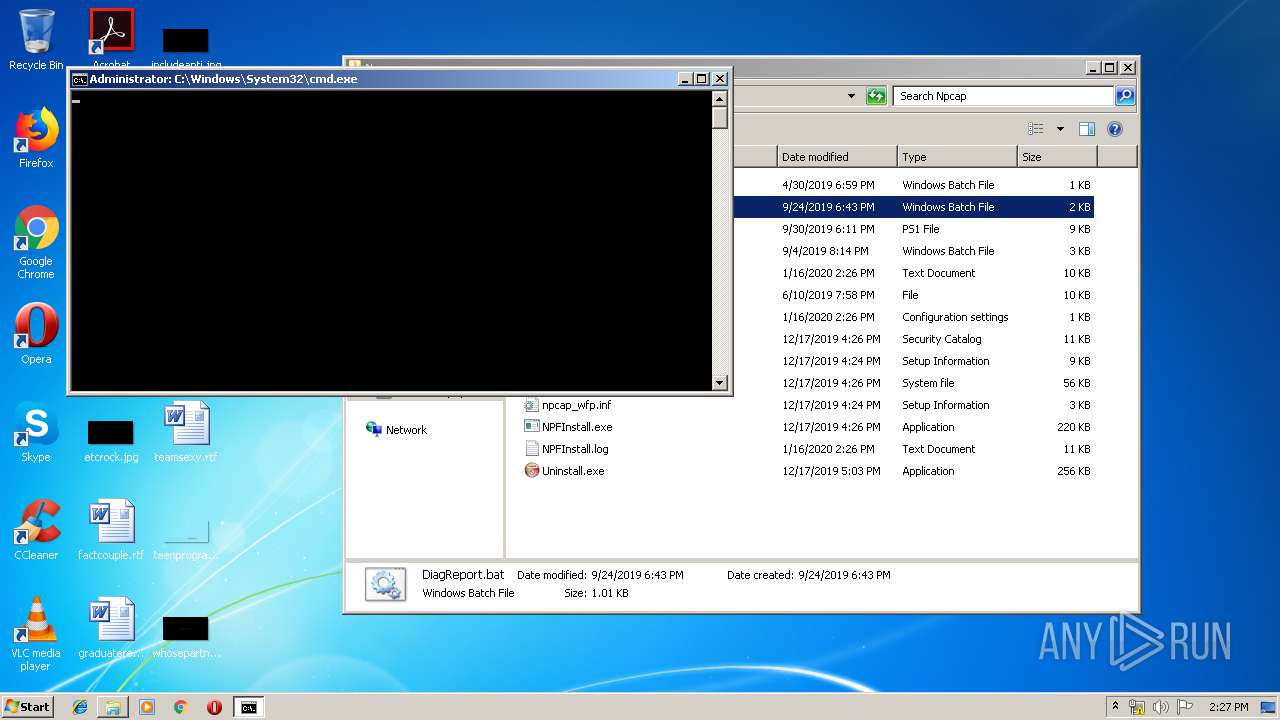
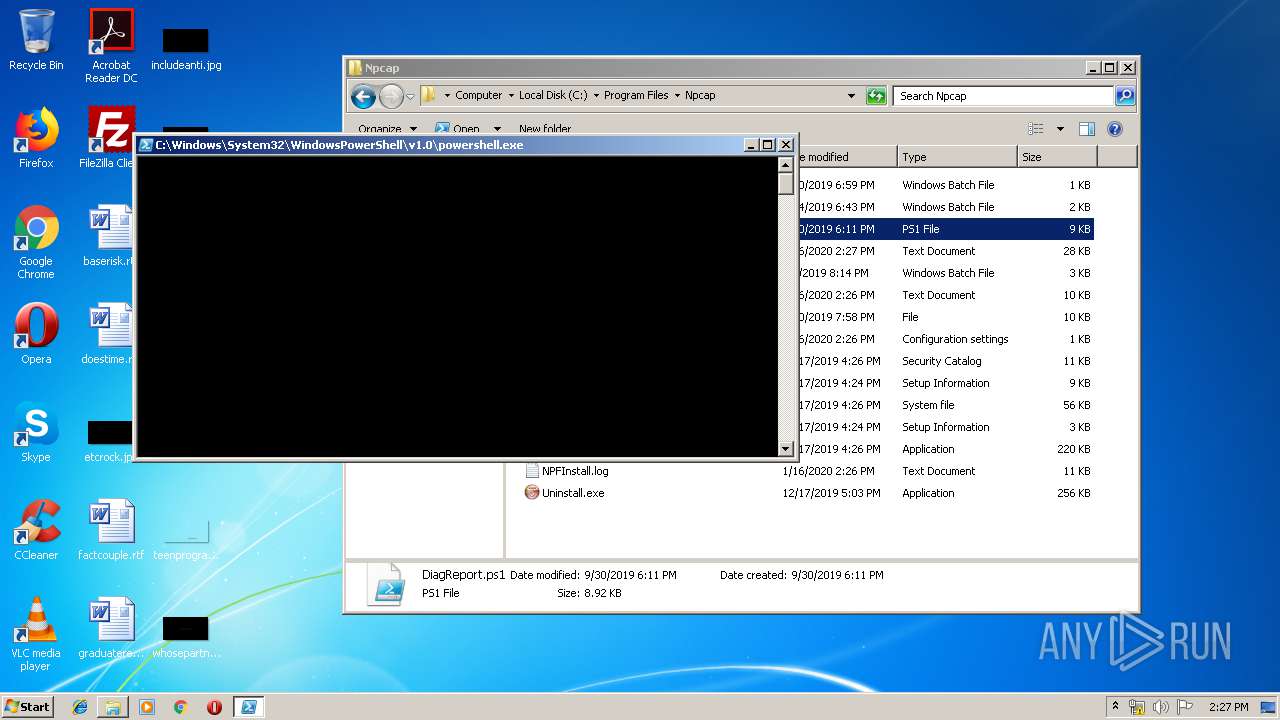
Executes PowerShell scripts
- cmd.exe (PID: 2992)
- cmd.exe (PID: 2824)
Starts NET.EXE for service management
- cmd.exe (PID: 2084)
SUSPICIOUS
Executable content was dropped or overwritten
- npcap-0.9986.exe (PID: 928)
- DrvInst.exe (PID: 444)
- NPFInstall.exe (PID: 3796)
- DrvInst.exe (PID: 1600)
Creates files in the Windows directory
- npcap-0.9986.exe (PID: 928)
- certutil.exe (PID: 3948)
- pnputil.exe (PID: 2264)
- DrvInst.exe (PID: 444)
- DrvInst.exe (PID: 1600)
- NPFInstall.exe (PID: 3796)
Removes files from Windows directory
- certutil.exe (PID: 3948)
- DrvInst.exe (PID: 444)
- NPFInstall.exe (PID: 3796)
- DrvInst.exe (PID: 1600)
Executed via COM
- DrvInst.exe (PID: 444)
- DrvInst.exe (PID: 1600)
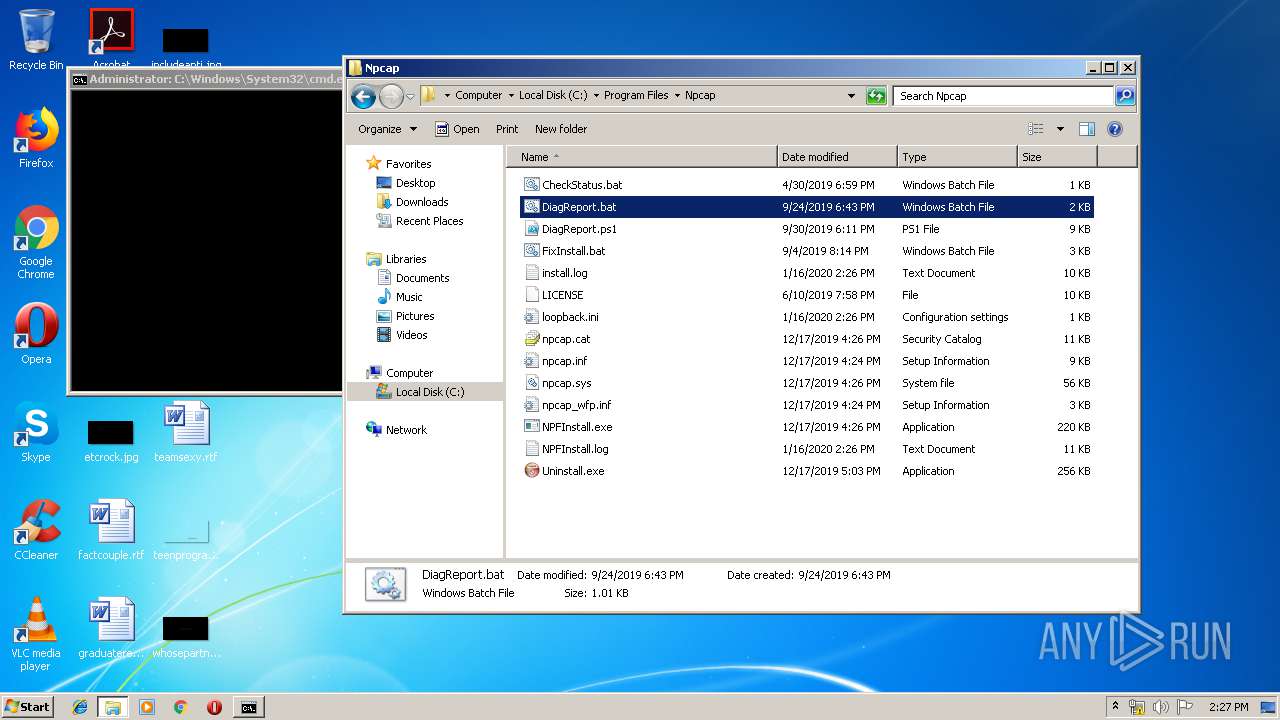
Creates a software uninstall entry
- npcap-0.9986.exe (PID: 928)
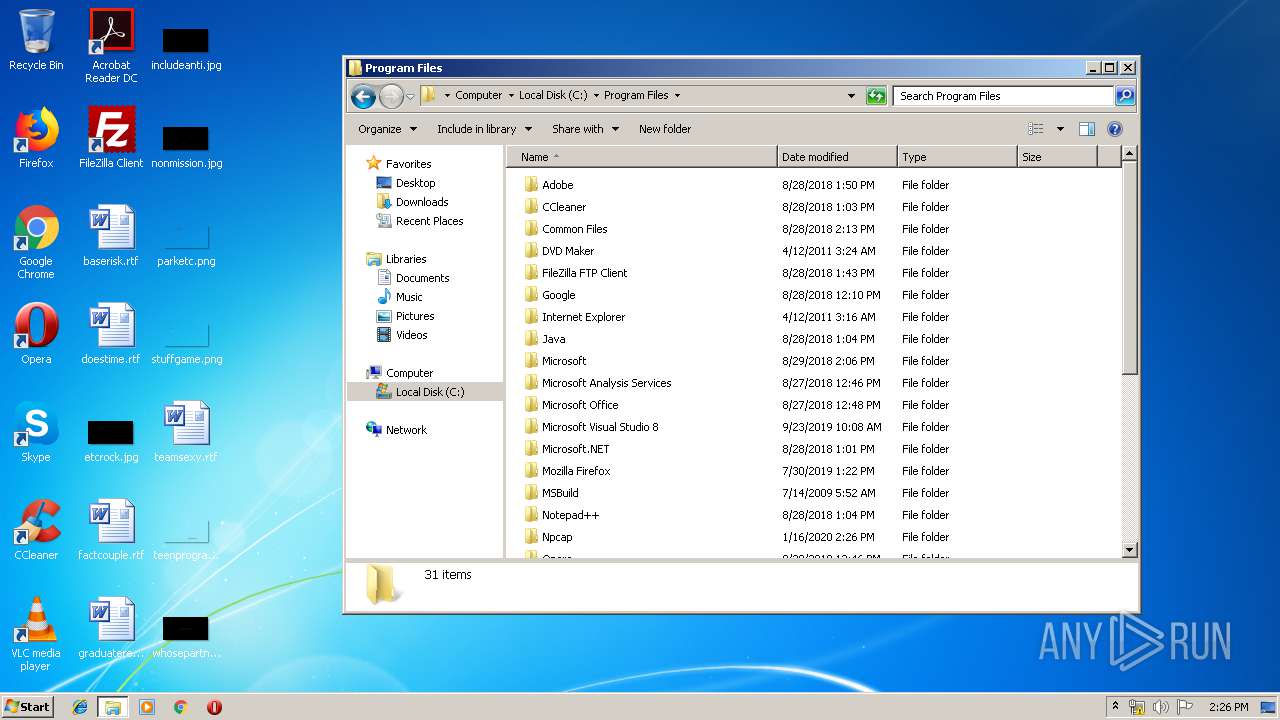
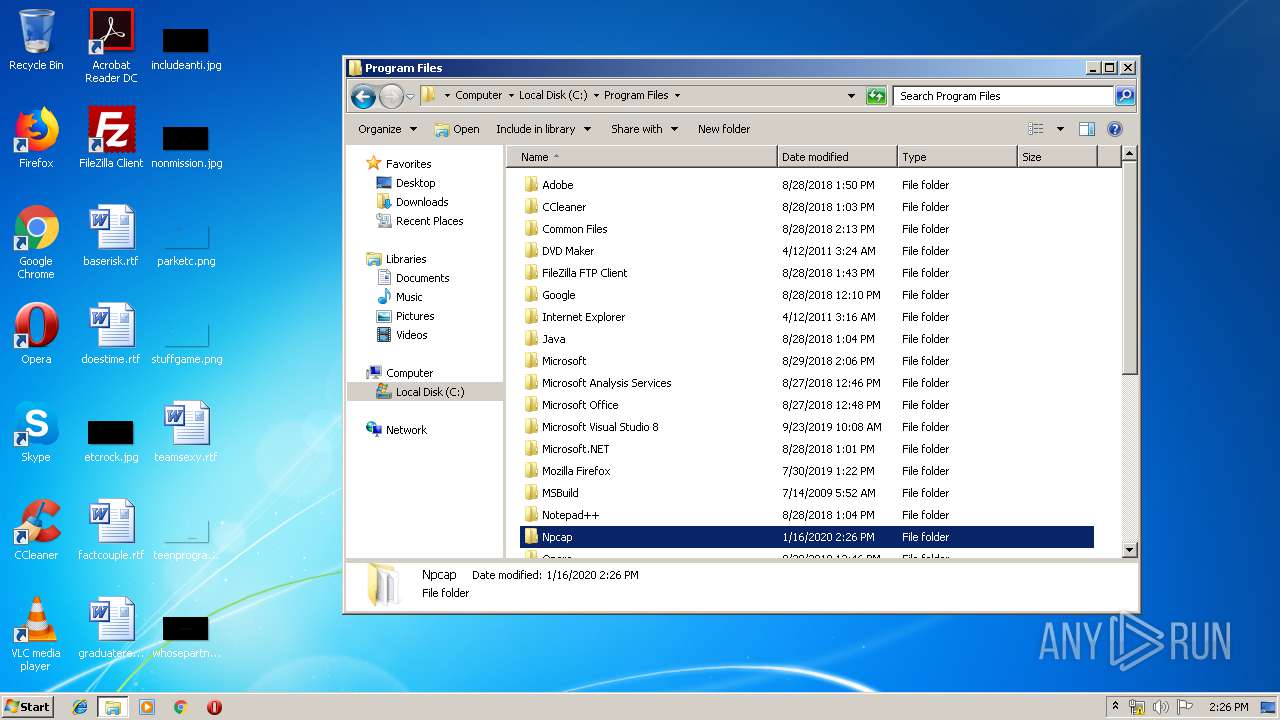
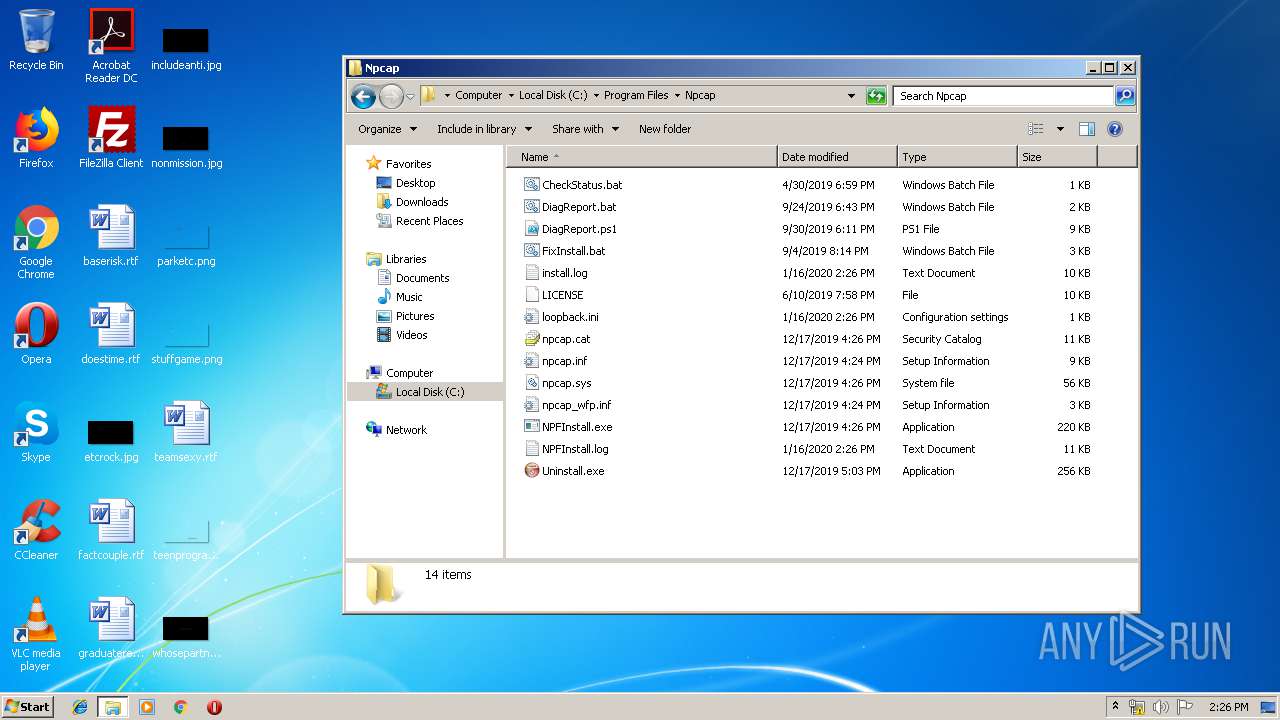
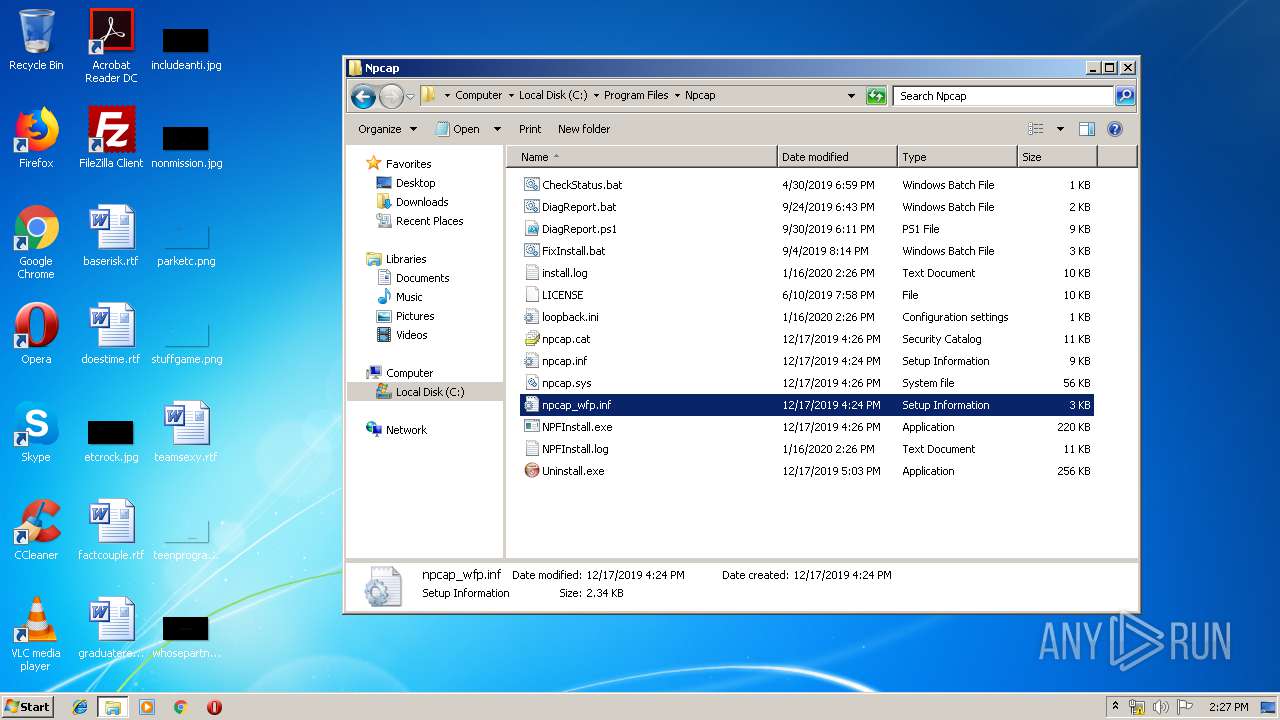
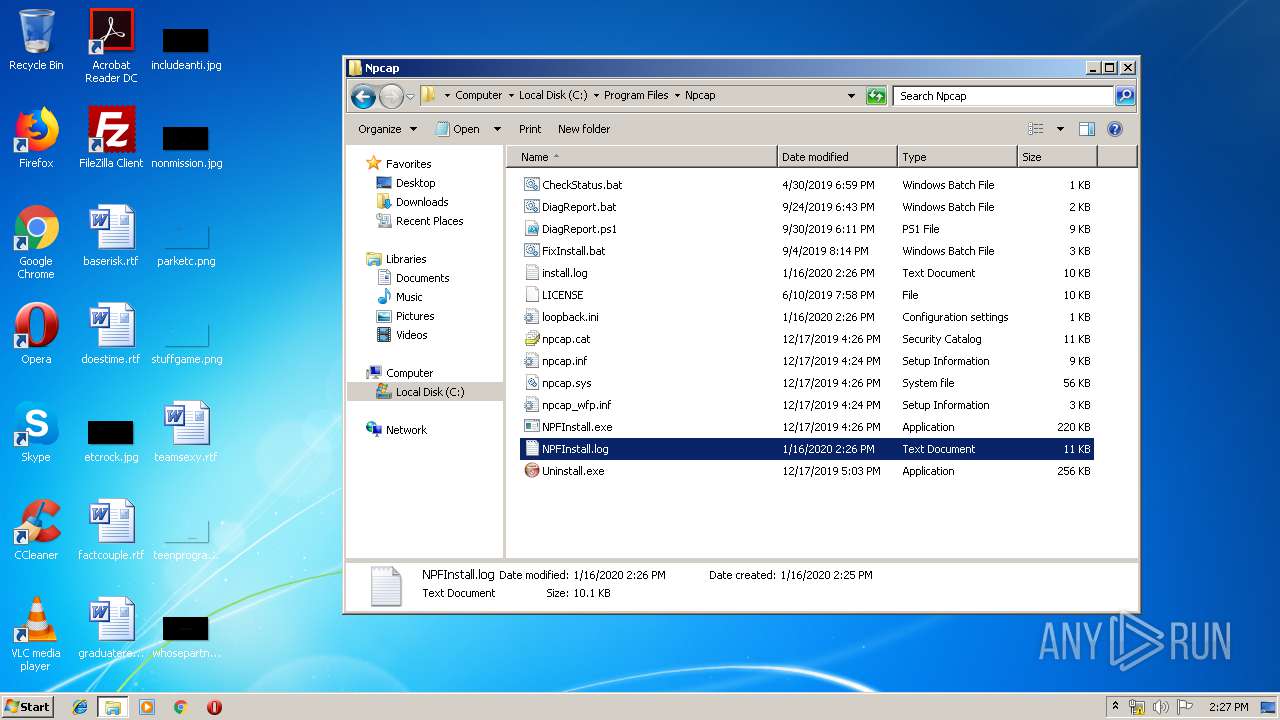
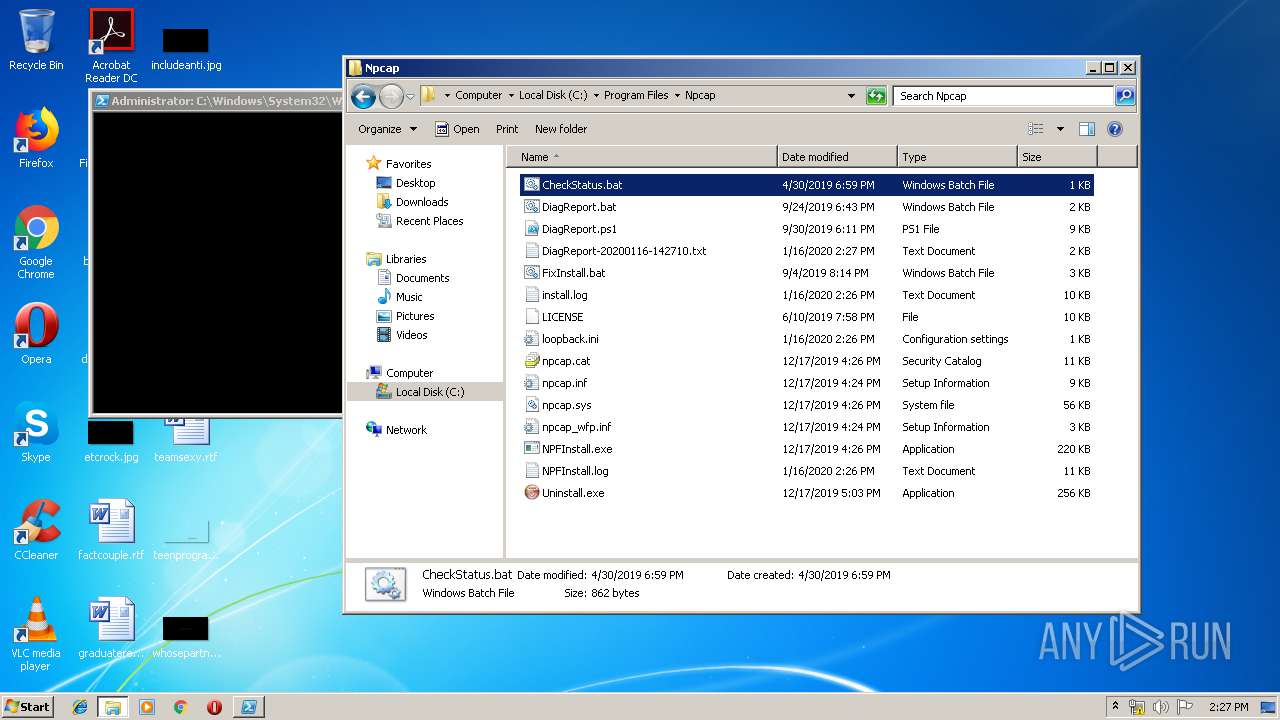
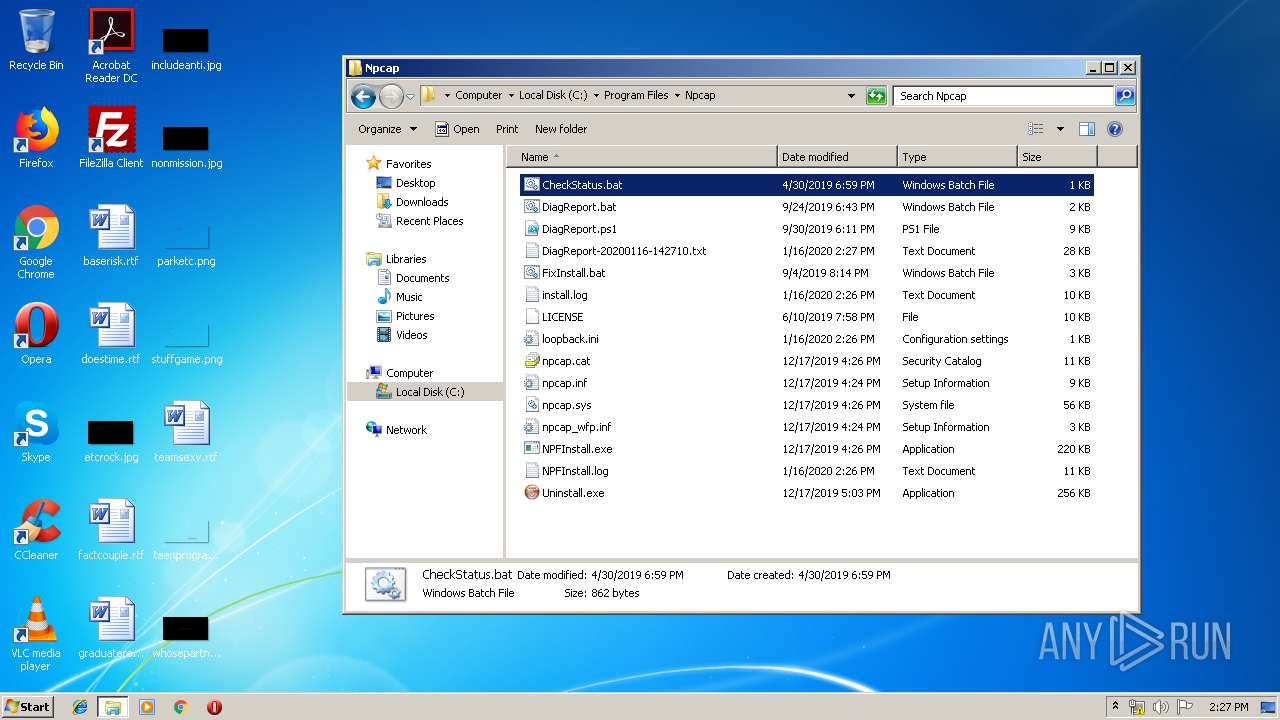
Creates files in the program directory
- npcap-0.9986.exe (PID: 928)
- NPFInstall.exe (PID: 2856)
- NPFInstall.exe (PID: 2332)
- powershell.exe (PID: 856)
Starts application with an unusual extension
- npcap-0.9986.exe (PID: 928)
Creates files in the driver directory
- DrvInst.exe (PID: 444)
- DrvInst.exe (PID: 1600)
- NPFInstall.exe (PID: 3796)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 444)
Executed as Windows Service
- vssvc.exe (PID: 1956)
Creates or modifies windows services
- DrvInst.exe (PID: 1600)
- npcap-0.9986.exe (PID: 928)
Executes scripts
- cmd.exe (PID: 1904)
Uses WHOAMI.EXE to obtaining logged on user information
- cmd.exe (PID: 1904)
- cmd.exe (PID: 2824)
Starts CMD.EXE for commands execution
- WScript.exe (PID: 3200)
- cmd.exe (PID: 2824)
- cmd.exe (PID: 3812)
- cmd.exe (PID: 2084)
Creates files in the user directory
- powershell.exe (PID: 3952)
- powershell.exe (PID: 4076)
- powershell.exe (PID: 236)
- powershell.exe (PID: 3676)
- powershell.exe (PID: 856)
- powershell.exe (PID: 3340)
Executes PowerShell scripts
- powershell.exe (PID: 4076)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 320)
- cmd.exe (PID: 736)
- cmd.exe (PID: 3044)
- cmd.exe (PID: 4008)
- cmd.exe (PID: 2416)
- cmd.exe (PID: 3400)
- cmd.exe (PID: 1764)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 3812)
PowerShell script executed
- powershell.exe (PID: 3340)
Application launched itself
- powershell.exe (PID: 4076)
- cmd.exe (PID: 2084)
Starts SC.EXE for service management
- cmd.exe (PID: 2084)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 2084)
INFO
Searches for installed software
- DrvInst.exe (PID: 444)
Low-level read access rights to disk partition
- vssvc.exe (PID: 1956)
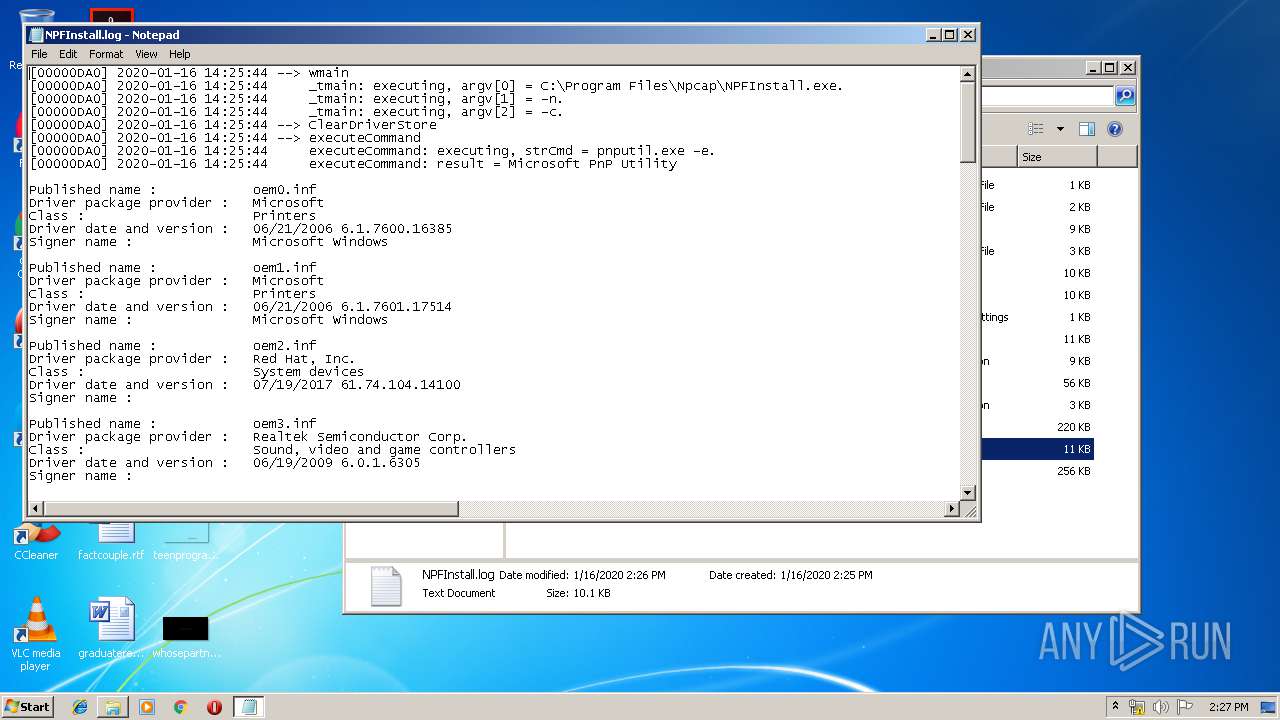
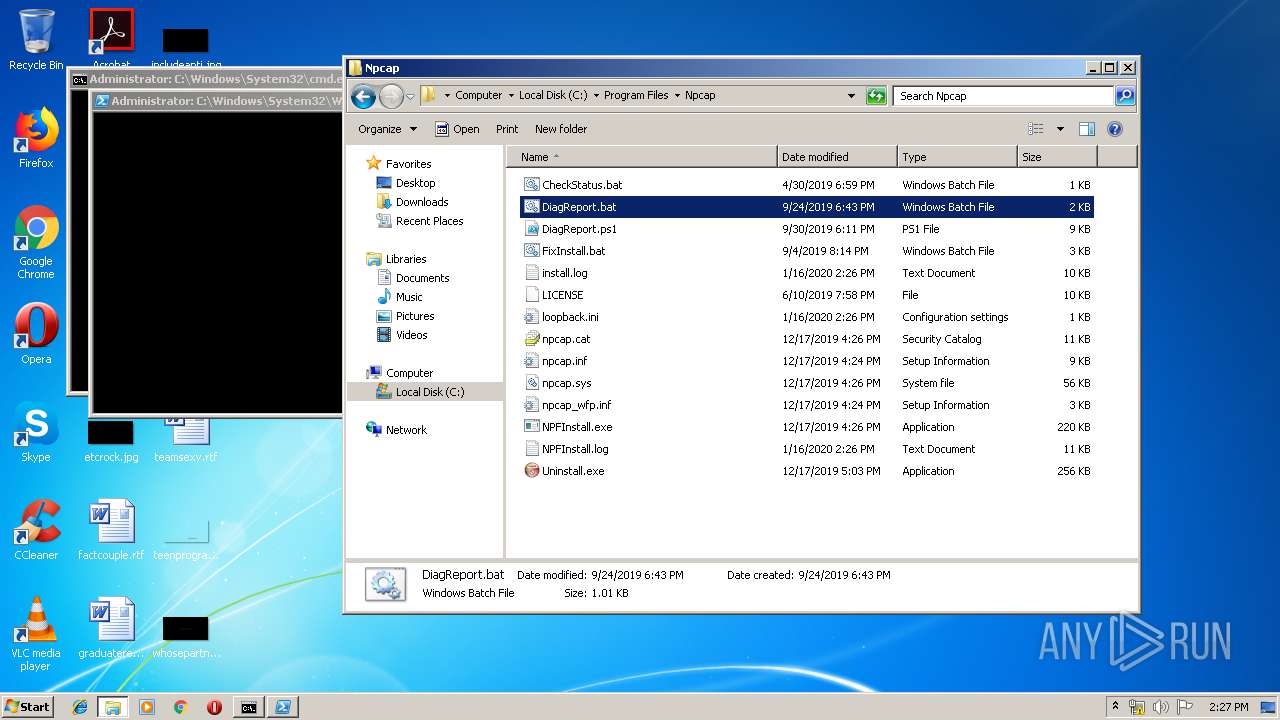
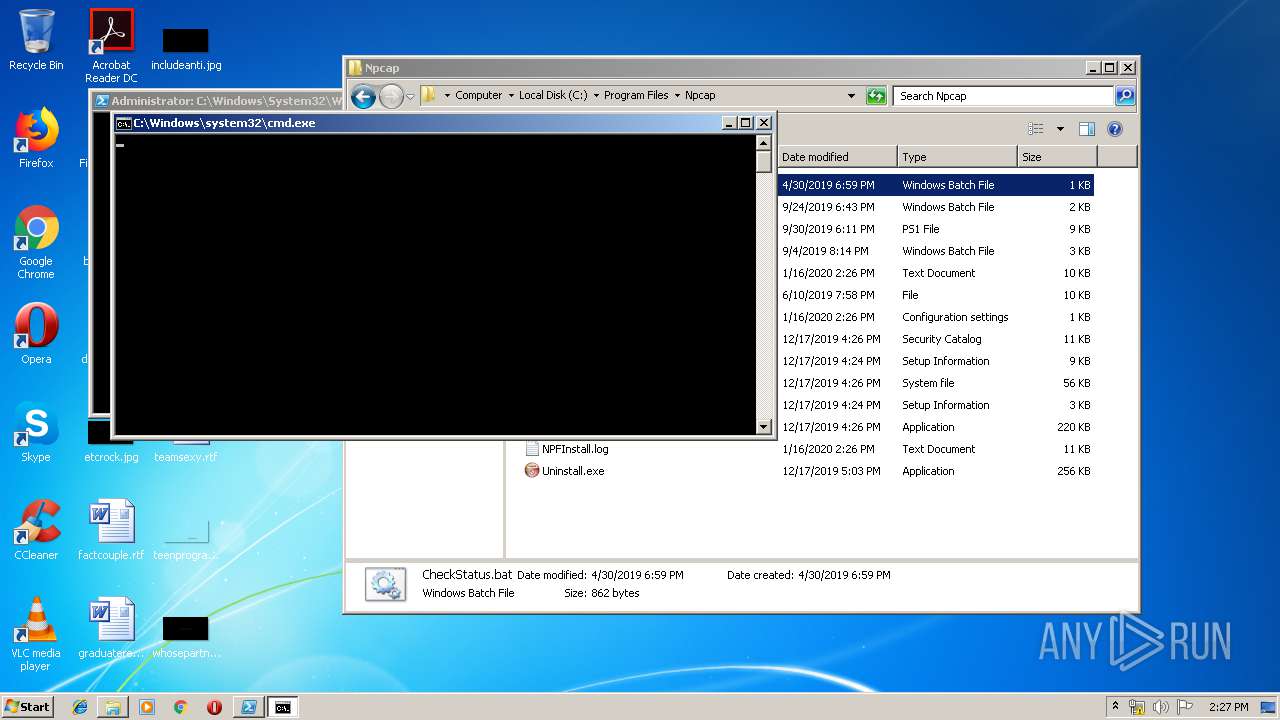
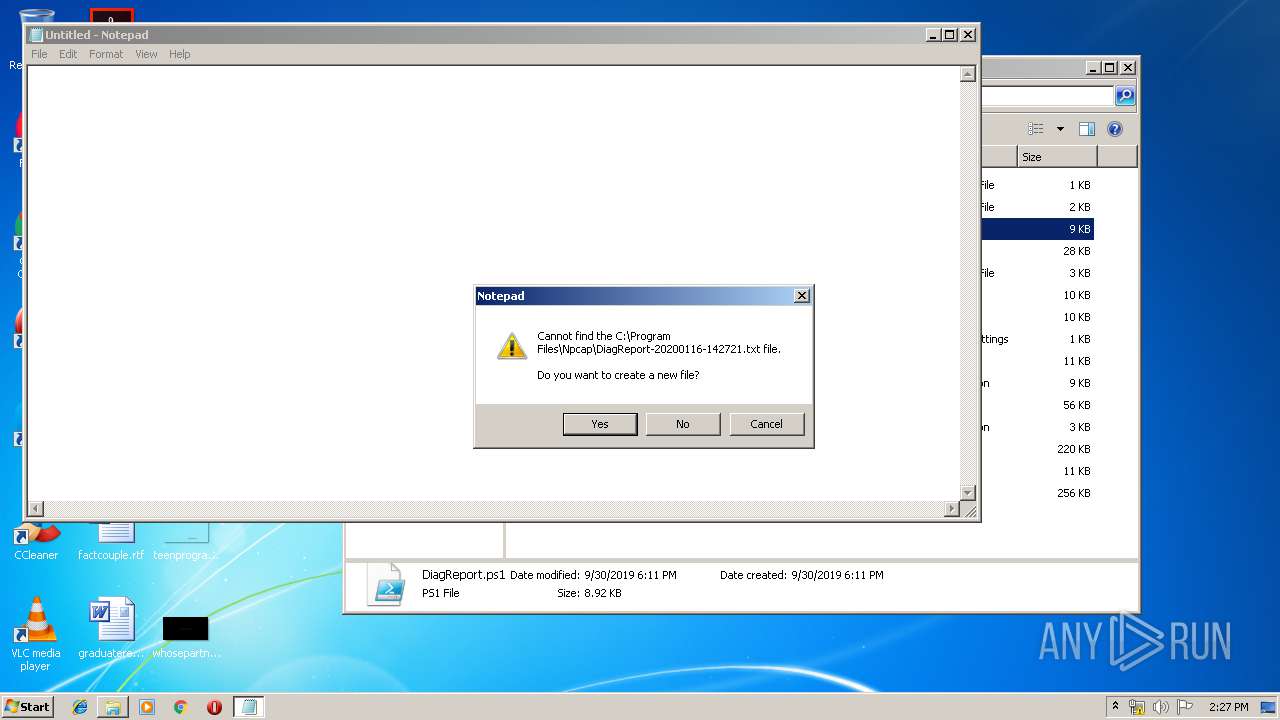
Manual execution by user
- NPFInstall.exe (PID: 1764)
- NOTEPAD.EXE (PID: 1972)
- NOTEPAD.EXE (PID: 1796)
- cmd.exe (PID: 1904)
- NPFInstall.exe (PID: 2348)
- cmd.exe (PID: 3812)
- powershell.exe (PID: 3340)
- cmd.exe (PID: 2084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:02 05:21:39+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25600 |
| InitializedDataSize: | 125440 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x36e7 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.0.9986.1217 |
| ProductVersionNumber: | 5.0.9986.1217 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| FileDescription: | Npcap 0.9986 installer |
| FileVersion: | 0.9986 |
| LegalCopyright: | Copyright 2019 Insecure.Com LLC ("The Nmap Project") |
| ProductName: | Npcap |
| ProductVersion: | 0.9986 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Apr-2016 03:21:39 |
| Detected languages: |
|
| FileDescription: | Npcap 0.9986 installer |
| FileVersion: | 0.9986 |
| LegalCopyright: | Copyright 2019 Insecure.Com LLC ("The Nmap Project") |
| ProductName: | Npcap |
| ProductVersion: | 0.9986 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 02-Apr-2016 03:21:39 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000063CD | 0x00006400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4551 |
.rdata | 0x00008000 | 0x000011E2 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.30938 |
.data | 0x0000A000 | 0x0001C4F8 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.96324 |
.ndata | 0x00027000 | 0x00010000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00037000 | 0x000044F0 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.87159 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21417 | 958 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.9993 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 6.24459 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 5.01502 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 6.16057 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 3.34146 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 3.04232 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.6691 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.67385 | 512 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
148
Monitored processes
83
Malicious processes
9
Suspicious processes
4
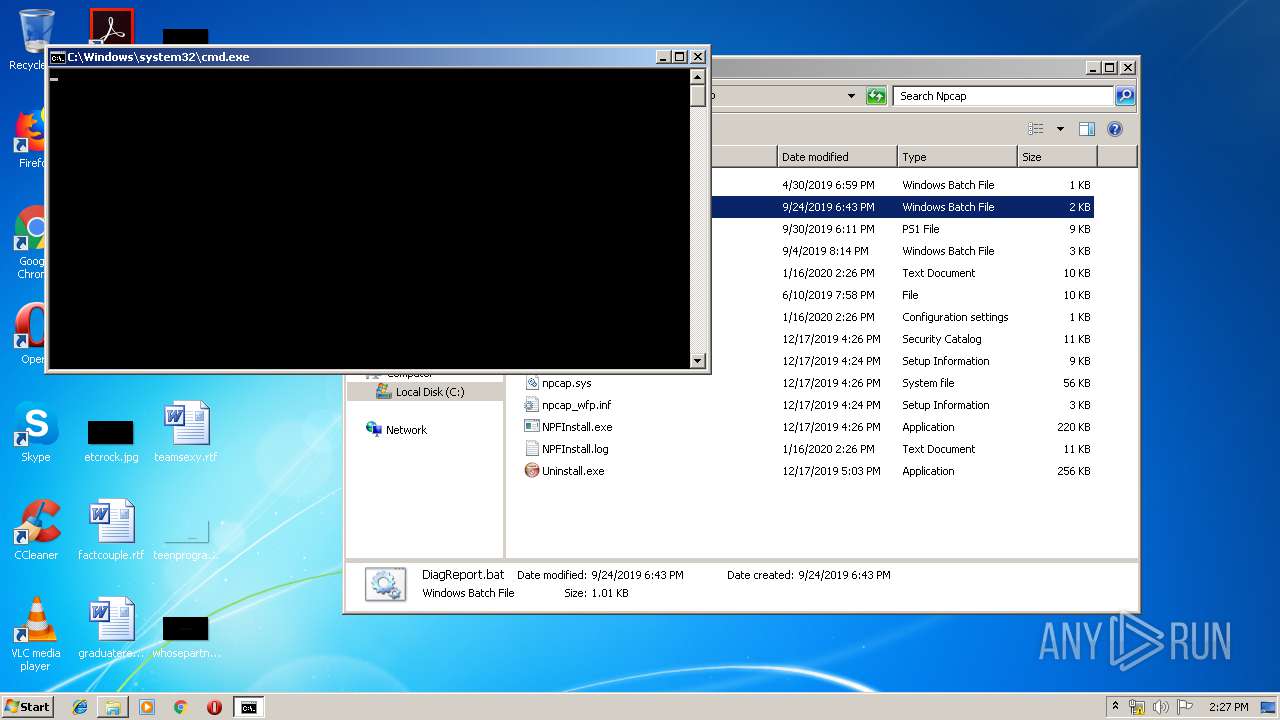
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | powershell Set-ExecutionPolicy 0 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 320 | C:\Windows\system32\cmd.exe /c reg query "HKLM\Software\WOW6432Node\Npcap" /ve 2>nul | find "REG_SZ" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 320 | reg query "HKLM\Software\WOW6432Node\Npcap" /ve | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 328 | reg query "HKLM\SYSTEM\CurrentControlSet\Services\npcap\Parameters" /v "WinPcapCompatible" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 444 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{3e7766ff-b327-2e4e-25f2-d435f8bcc267}\NPCAP.inf" "0" "605306be3" "00000320" "WinSta0\Default" "0000055C" "208" "C:\Program Files\Npcap" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 616 | net stop npcap | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 736 | C:\Windows\system32\cmd.exe /c reg query "HKLM\Software\Npcap" /ve 2>nul | find "REG_SZ" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 748 | wmic.exe nic GET Name,NetConnectionID | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 776 | find "REG_SZ" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 816 | "C:\Windows\system32\notepad.exe" "C:\Program Files\Npcap\DiagReport-20200116-142710.txt" | C:\Windows\system32\notepad.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 838
Read events
2 699
Write events
1 091
Delete events
48
Modification events
| (PID) Process: | (928) npcap-0.9986.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Npcap |
| Operation: | write | Name: | AdminOnly |
Value: 1 | |||
| (PID) Process: | (928) npcap-0.9986.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Npcap |
| Operation: | write | Name: | WinPcapCompatible |
Value: 1 | |||
| (PID) Process: | (928) npcap-0.9986.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Npcap |
| Operation: | write | Name: | |
Value: C:\Program Files\Npcap | |||
| (PID) Process: | (928) npcap-0.9986.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NpcapInst |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\Npcap\uninstall.exe" | |||
| (PID) Process: | (928) npcap-0.9986.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NpcapInst |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Program Files\Npcap\uninstall.exe" /S | |||
| (PID) Process: | (928) npcap-0.9986.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NpcapInst |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\Npcap\uninstall.exe | |||
| (PID) Process: | (928) npcap-0.9986.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NpcapInst |
| Operation: | write | Name: | UninstallPath |
Value: C:\Program Files\Npcap | |||
| (PID) Process: | (3948) certutil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\TrustedPublisher\Certificates\1C58BD08D220F81B21FB2837E3AB65AEE5EFD727 |
| Operation: | write | Name: | Blob |
Value: 0300000001000000140000001C58BD08D220F81B21FB2837E3AB65AEE5EFD72720000000010000001E0600003082061A30820502A003020102021100EE6DF2FCB54A8B580C72AF81B464471A300D06092A864886F70D01010B0500308191310B3009060355040613024742311B30190603550408131247726561746572204D616E636865737465723110300E0603550407130753616C666F7264311A3018060355040A1311434F4D4F444F204341204C696D69746564313730350603550403132E434F4D4F444F2052534120457874656E6465642056616C69646174696F6E20436F6465205369676E696E67204341301E170D3139313130363030303030305A170D3232313130353233353935395A30820105311530130603550405130C32303030313033313030313331133011060B2B0601040182373C02010313025553311B3019060B2B0601040182373C020102130A43616C69666F726E6961311D301B060355040F131450726976617465204F7267616E697A6174696F6E310B30090603550406130255533113301106035504110C0A39383130342D323230353113301106035504080C0A57617368696E67746F6E3110300E06035504070C0753656174746C65311C301A06035504090C133131332043686572727920537420233133333731193017060355040A0C10496E7365637572652E436F6D204C4C433119301706035504030C10496E7365637572652E436F6D204C4C4330820122300D06092A864886F70D01010105000382010F003082010A0282010100C17B640E83B48EC2354C7E47C8D92D1D43D68AB1F2E8FAA10ADA99A9C0E667E91358A639FDE188AE13C0FA6E3275A9B99273A5B698B84C883410FB5DF5CD01BB8433891FB803C21B14146E8C51C955A73FE34FBF34B8023717DF569C53C70DBD06FD678BAAF186F93637DC0FB64D3D156C2BCE70E5F85D53B10141537DE04F398F95A53F095077BC408A92A56E8A7C62C79F0471BD9ED60DC41439910D26D44ADFB69E758D3F80A71281553041DE95350C34FC4BBE8133CCEF81F1EE598450E72A3A2351BDD288232BB89940B7DF8B6FC974EE377C92C985C9B98BFF318AAB167CDC3BABCFB2E2AEC51C65D7FE2BFE0AD86D02481B5CB59C7EF0ED399A3807AF0203010001A38201F4308201F0301F0603551D23041830168014DF8FF3200CE9CAA604D85B58372A3DAB46DC8349301D0603551D0E0416041409EA7D43258DF05BAFB73EF75B605C89030EDA0A300E0603551D0F0101FF040403020780300C0603551D130101FF0402300030130603551D25040C300A06082B06010505070303301106096086480186F842010104040302041030400603551D20043930373035060C2B06010401B23101020106013025302306082B06010505070201161768747470733A2F2F7365637469676F2E636F6D2F43505330550603551D1F044E304C304AA048A0468644687474703A2F2F63726C2E636F6D6F646F63612E636F6D2F434F4D4F444F525341457874656E64656456616C69646174696F6E436F64655369676E696E6743412E63726C30818606082B06010505070101047A3078305006082B060105050730028644687474703A2F2F6372742E636F6D6F646F63612E636F6D2F434F4D4F444F525341457874656E64656456616C69646174696F6E436F64655369676E696E6743412E637274302406082B060105050730018618687474703A2F2F6F6373702E636F6D6F646F63612E636F6D30460603551D11043F303DA02A06082B06010505070803A01E301C0C1A55532D43414C49464F524E49412D323030303130333130303133810F676F72646F6E406E6D61702E636F6D300D06092A864886F70D01010B05000382010100237298D99FF2E84203C1FD45FE61C1F99B29028C2373EAB0F23C1D12F36F4477CE54E15285F0544DB6DFAFE83DD00F98CD373F29C147F00BD93E6985F404D545608A0F3C39A025A75B99625CBA02DBFBADCC0E6D220E45D8508DCC3AD6EB5F99514671BFD2BB1AE0DFEAD63DC061F7D6D4CCF43F28D749D6238B1D7F0D3813294F787E42206D7B075CB975CBE373B23497B9CC531C6E081A3A9D120A3350B2D56885806927FAD1E1B6D58C79D06A9A30AA9015C97AF80A16E0BE1D687D30A164AE5A7AE6395421309A919AC8CF9C520FFB4532C7AE655D04587DFCF5D50D9A1834BA244A60FEBF0789E1186733E5EEF94A997420EFF79D9084C8C530D7D8043B | |||
| (PID) Process: | (3948) certutil.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3796) NPFInstall.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Network\NetCfgLockHolder |
| Operation: | write | Name: | |
Value: NPCAP | |||
Executable files
23
Suspicious files
33
Text files
228
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 928 | npcap-0.9986.exe | C:\Users\admin\AppData\Local\Temp\nspAC1B.tmp\final.ini | text | |
MD5:— | SHA256:— | |||
| 928 | npcap-0.9986.exe | C:\Users\admin\AppData\Local\Temp\nspAC1B.tmp\options.ini | text | |
MD5:— | SHA256:— | |||
| 928 | npcap-0.9986.exe | C:\Users\admin\AppData\Local\Temp\nspAC1B.tmp\System.dll | executable | |
MD5:6A2F80ED640B6C2458329C2D3F8D9E3F | SHA256:1E981423FDA8F74E9A7079675C1A6FE55C716D4C0D50FB03EA482FF7500DB14B | |||
| 928 | npcap-0.9986.exe | C:\Users\admin\AppData\Local\Temp\nspAC1B.tmp\SimpleSC.dll | executable | |
MD5:4A2B58BD7CAB29463D9E53FCB9A252B6 | SHA256:18B17999996D73FE911A8EB676C231CB0BF002174954B552F880BDABF4C78124 | |||
| 928 | npcap-0.9986.exe | C:\Program Files\Npcap\LICENSE | text | |
MD5:043E3F337A269643FA4A6BCB5C17EA55 | SHA256:8ED32F19CFB6A16C595965DF6293A4711D171B616916D87CE4B2DEDED911CE88 | |||
| 928 | npcap-0.9986.exe | C:\Users\admin\AppData\Local\Temp\nspAC1B.tmp\Insecure-EV.cer | — | |
MD5:— | SHA256:— | |||
| 928 | npcap-0.9986.exe | C:\Program Files\Npcap\npcap.cat | cat | |
MD5:— | SHA256:— | |||
| 928 | npcap-0.9986.exe | C:\Users\admin\AppData\Local\Temp\nspAC1B.tmp\nsC929.tmp | — | |
MD5:— | SHA256:— | |||
| 928 | npcap-0.9986.exe | C:\Program Files\Npcap\npcap.sys | executable | |
MD5:— | SHA256:— | |||
| 928 | npcap-0.9986.exe | C:\Windows\system32\wpcap.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report