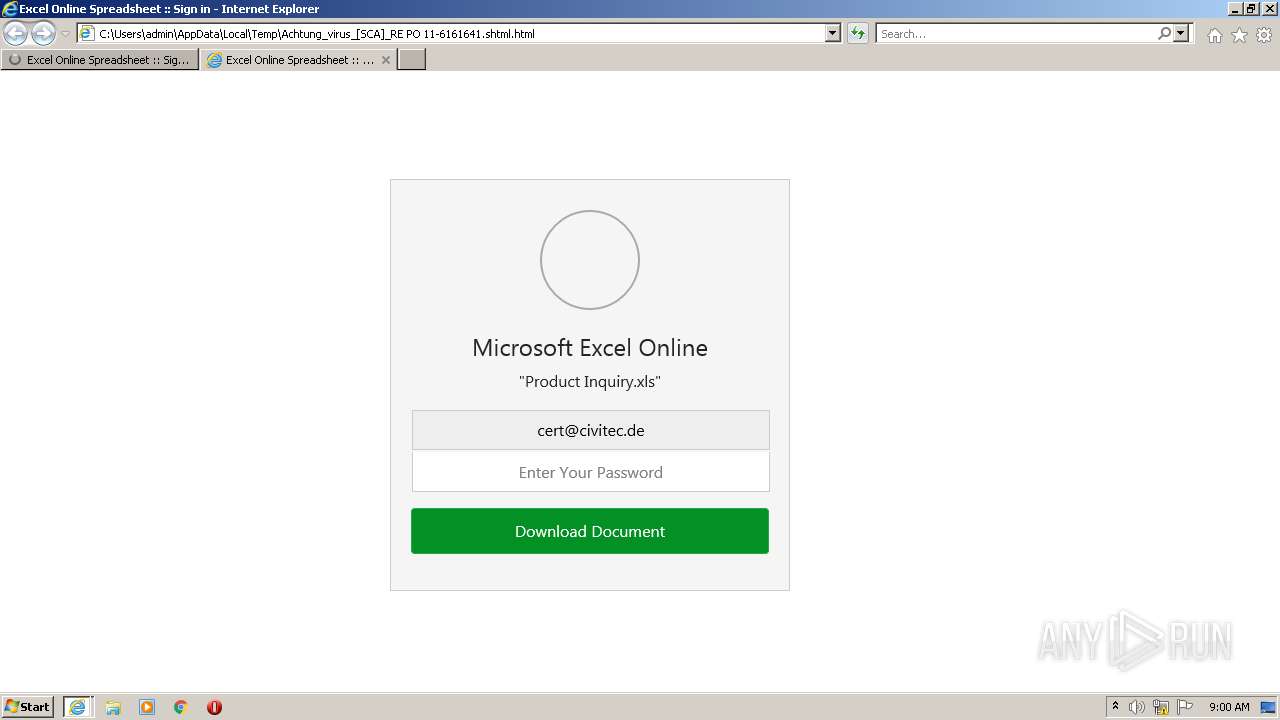
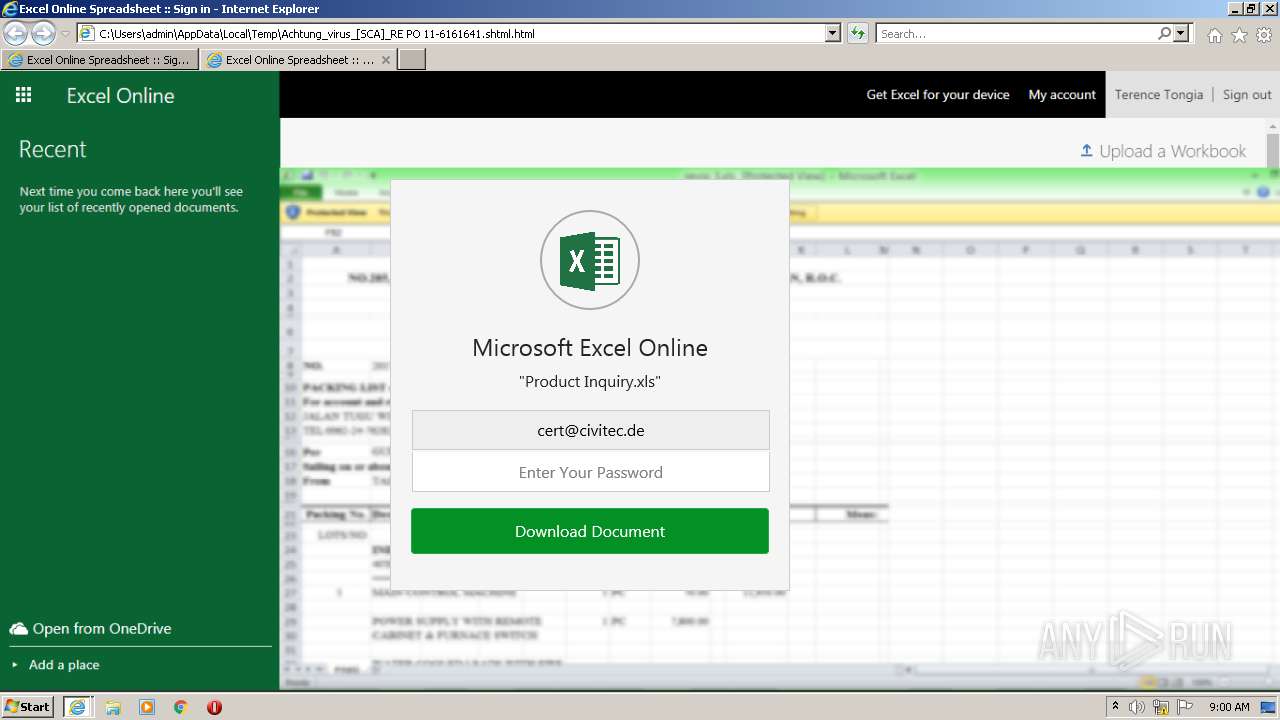
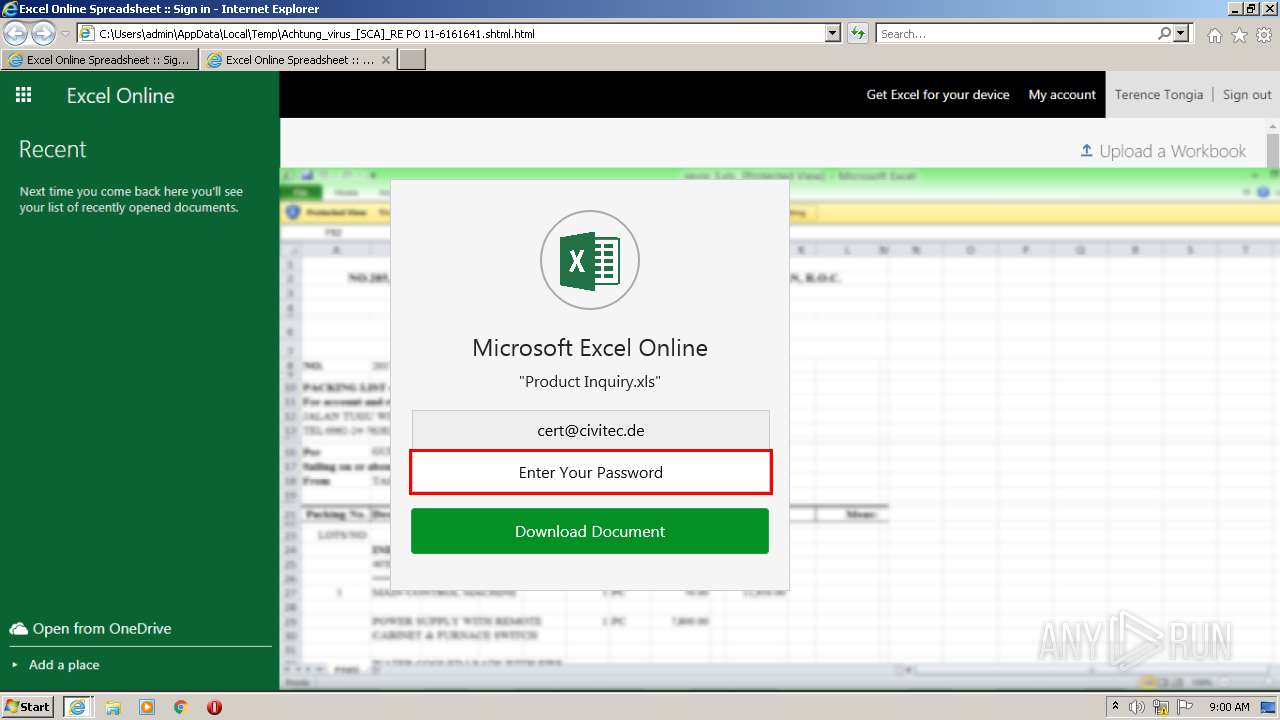
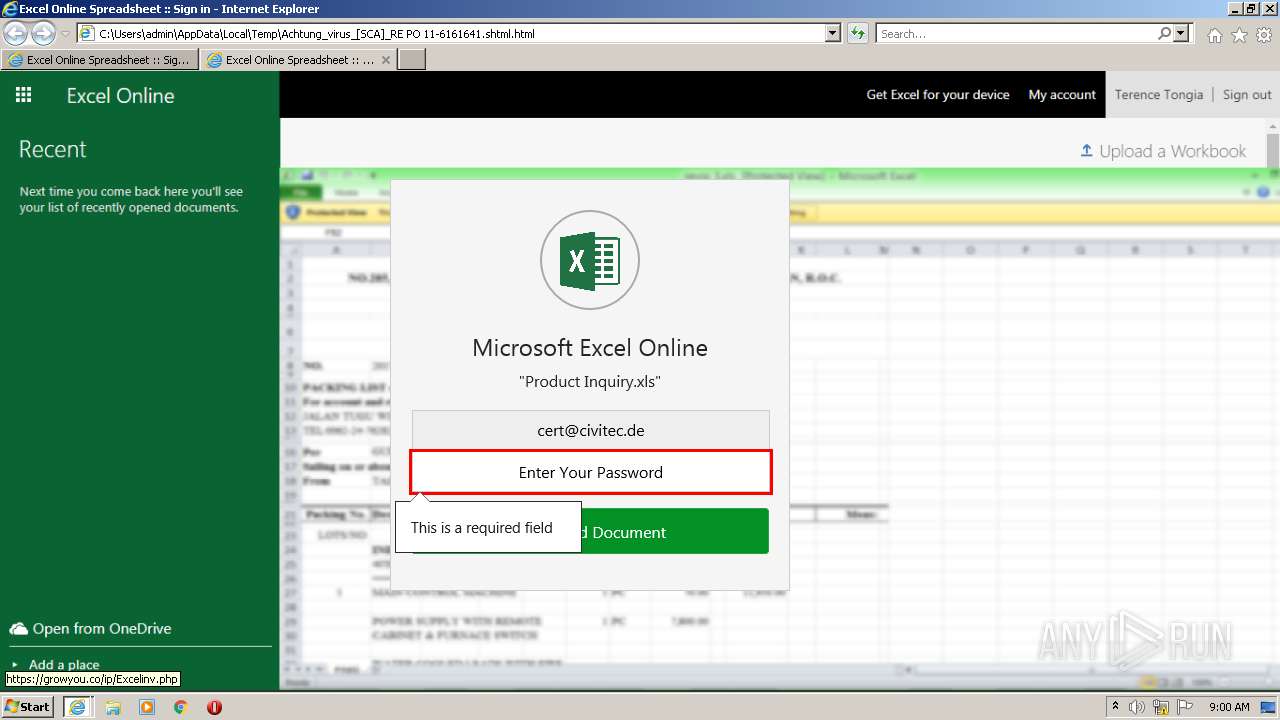
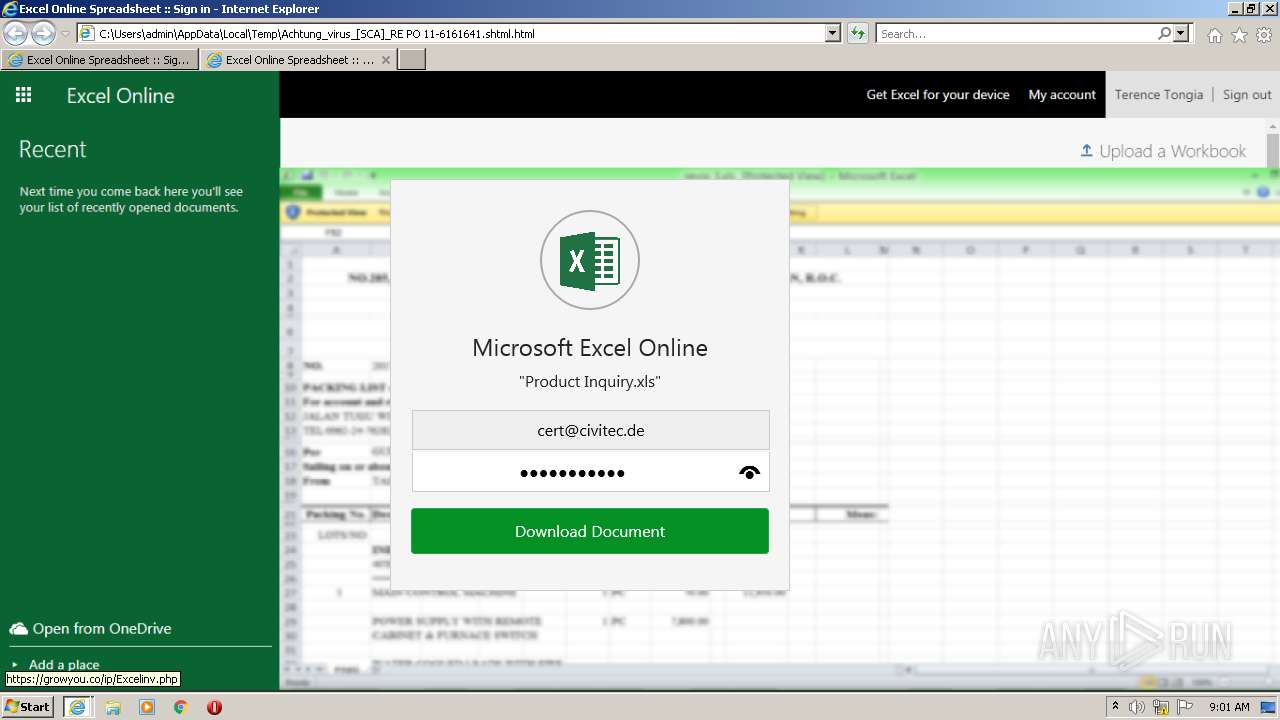
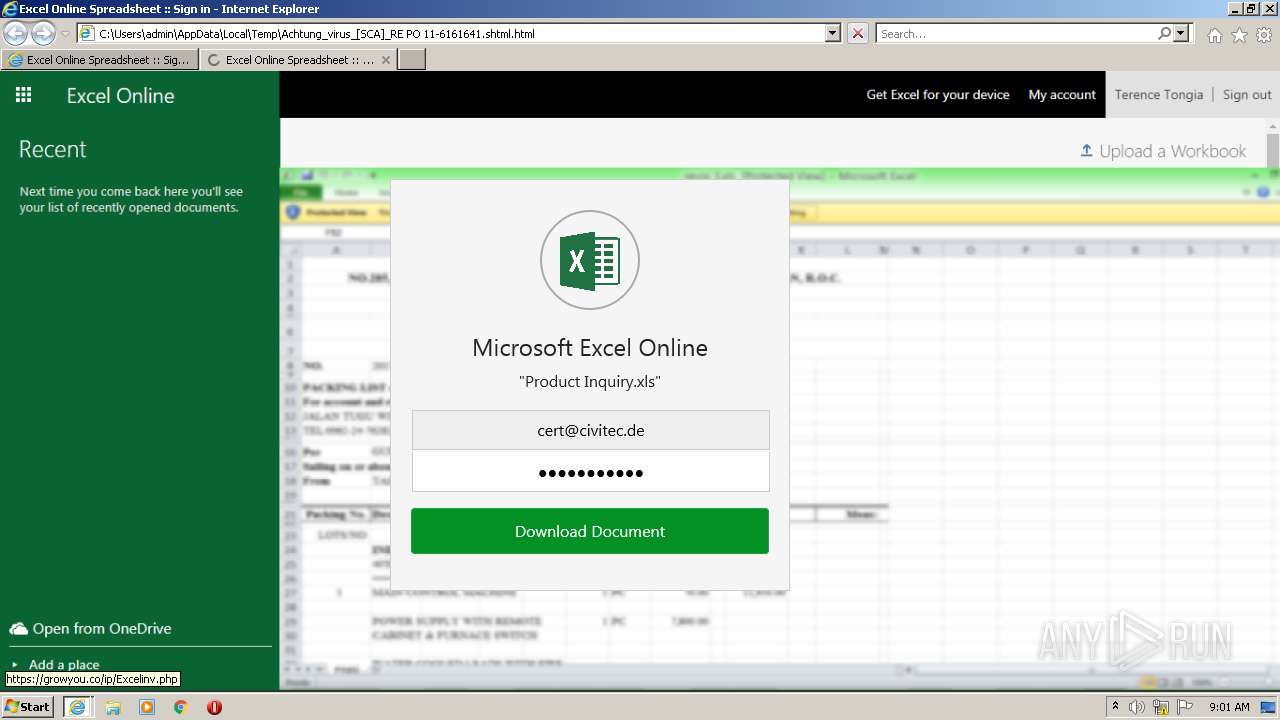
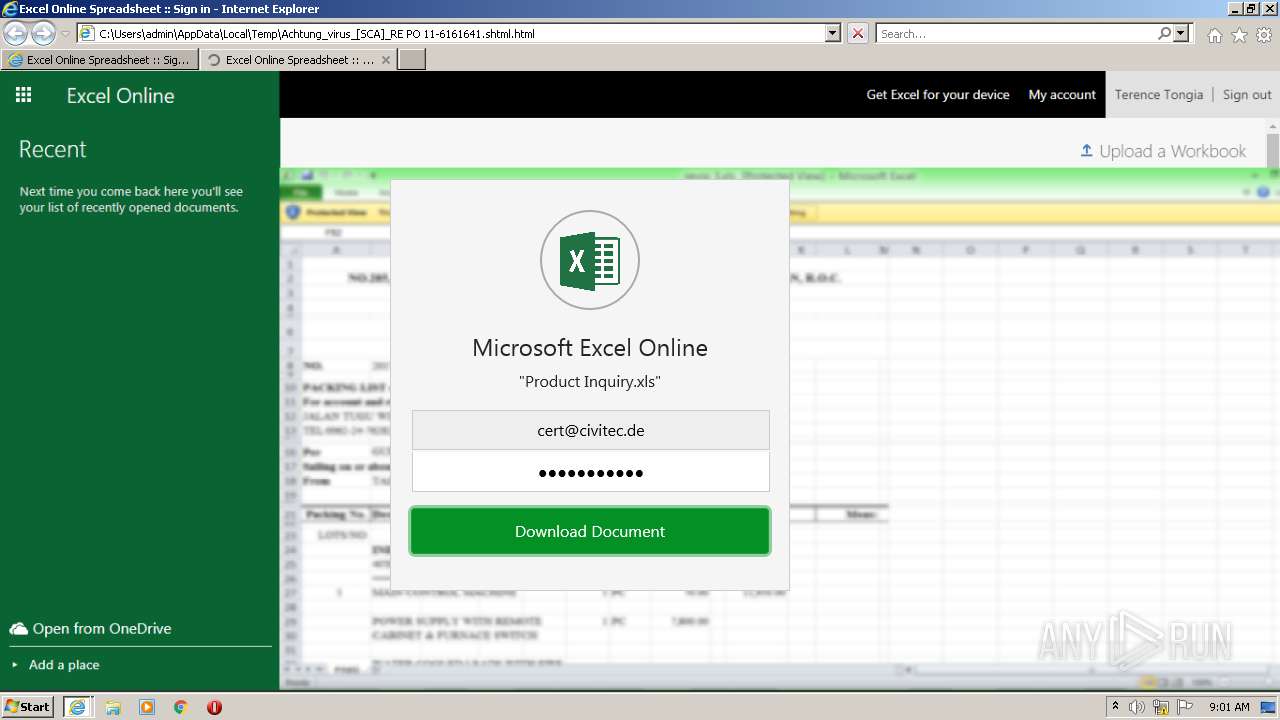
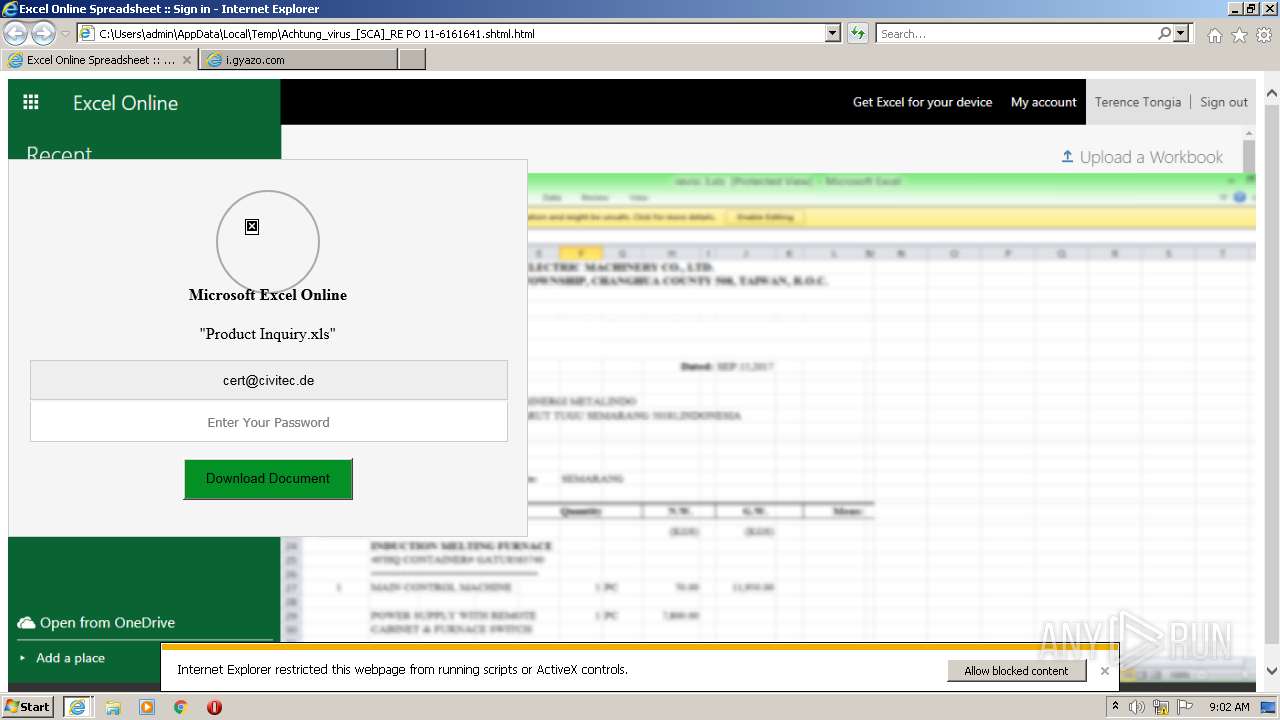
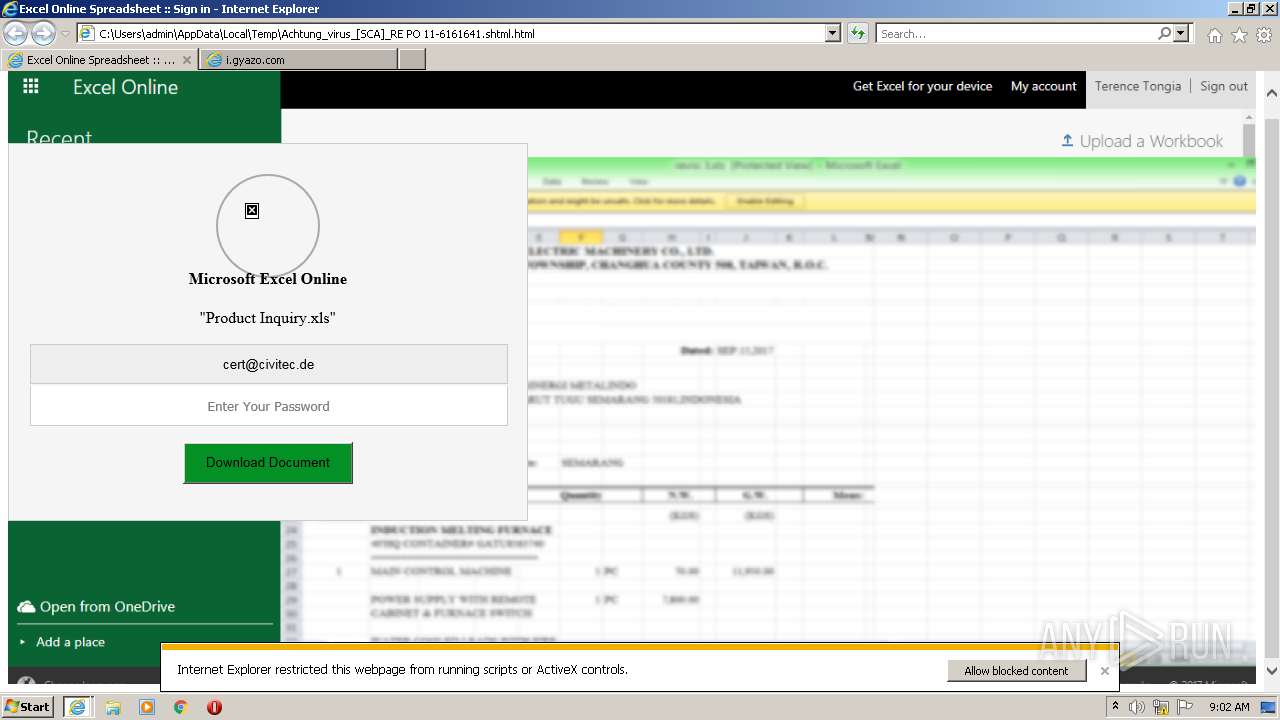
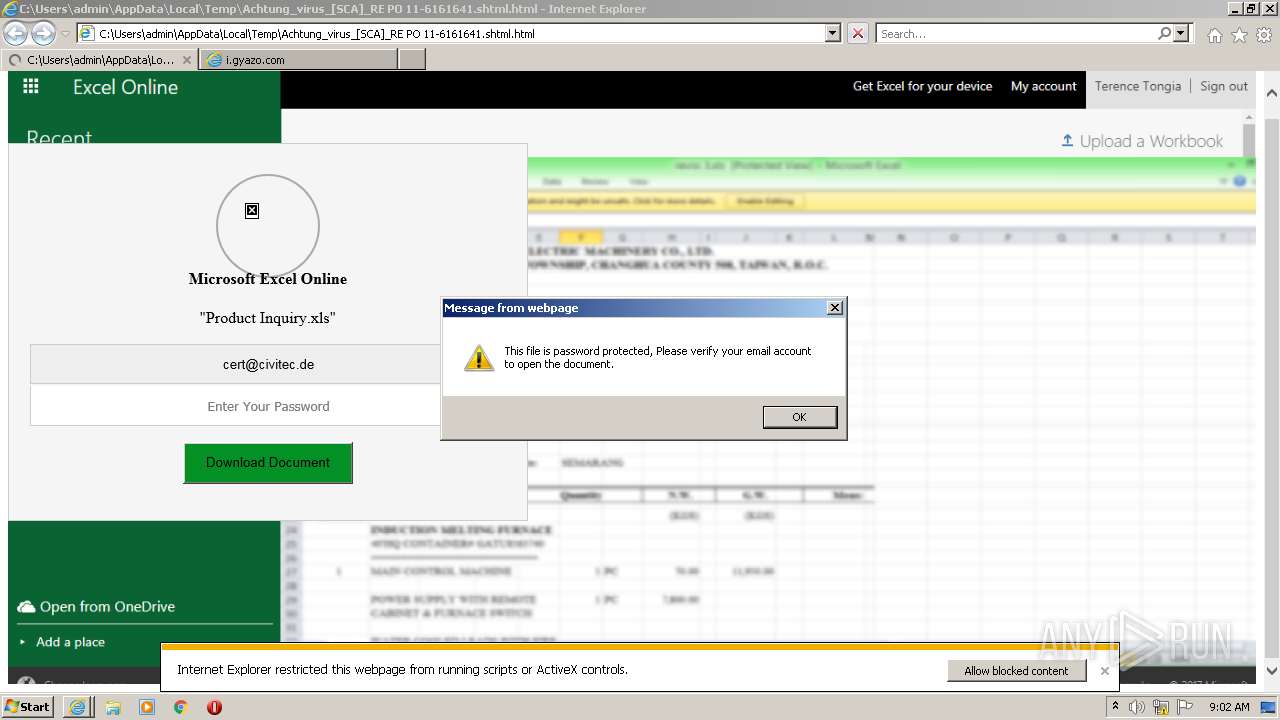
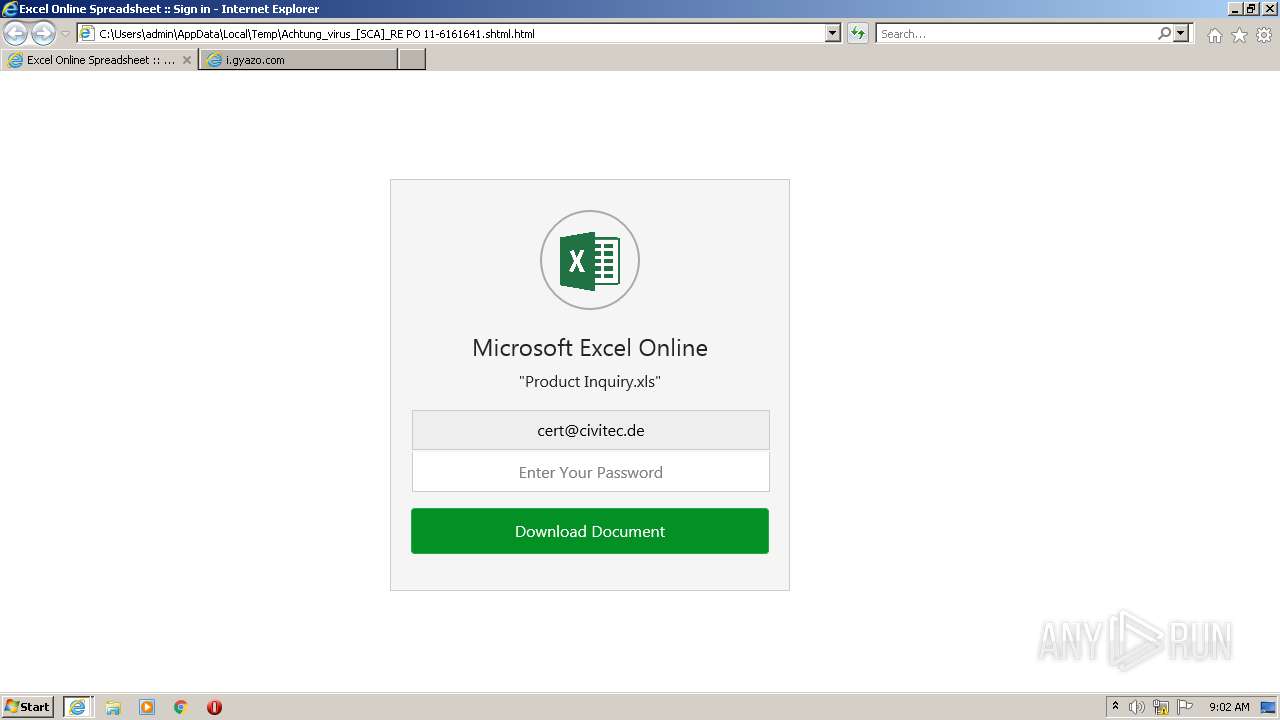
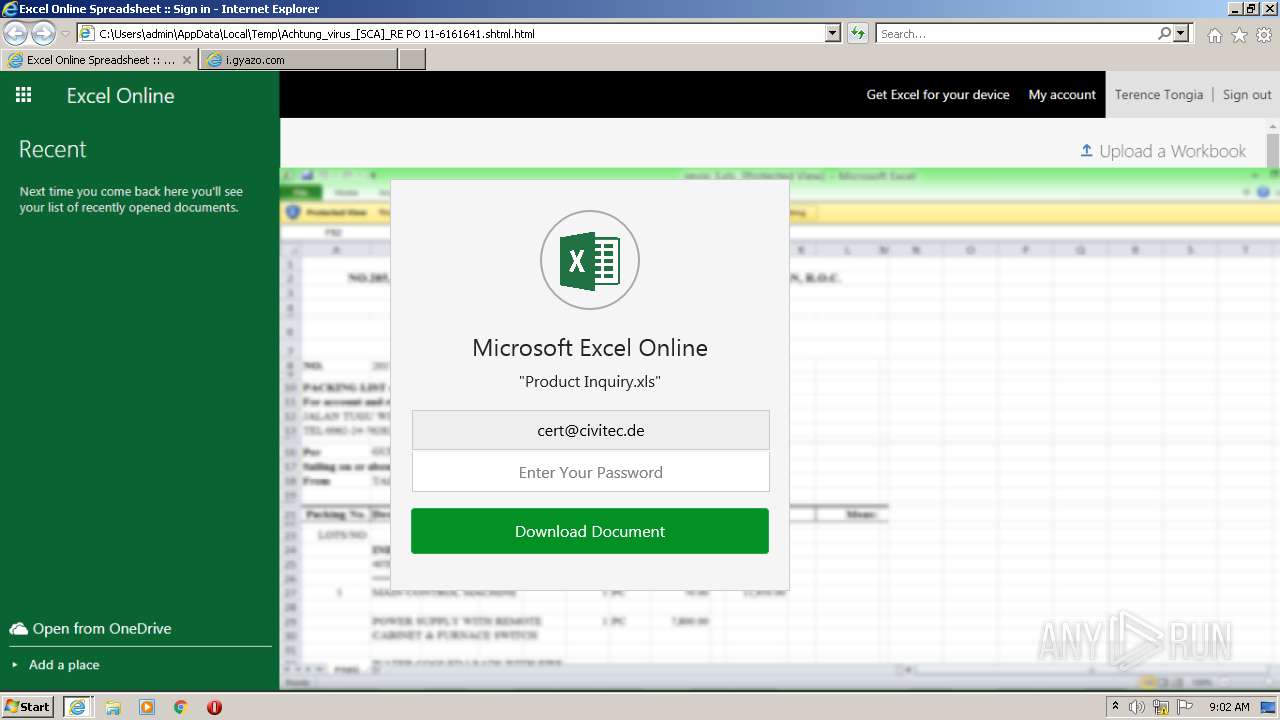
| File name: | Achtung_virus_[SCA]_RE PO 11-6161641.shtml |
| Full analysis: | https://app.any.run/tasks/eb3e10d0-33da-4802-b4e9-882fa057570e |
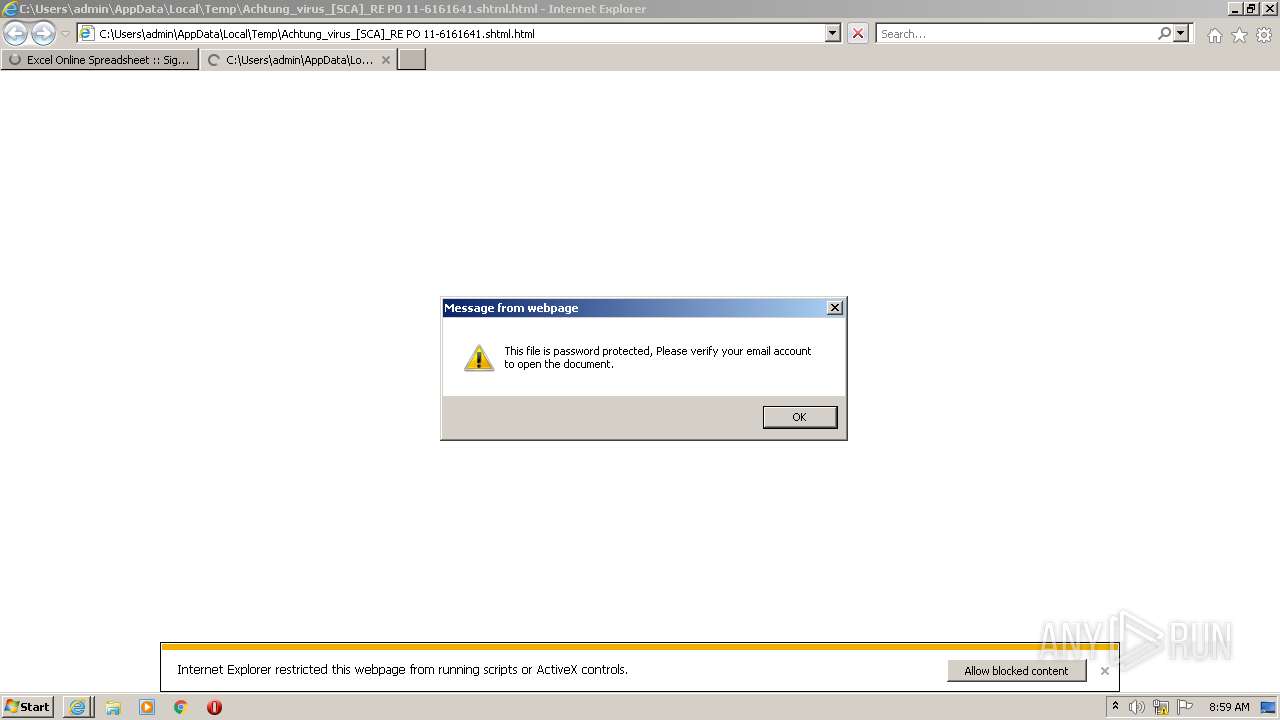
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2022, 07:59:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with CRLF line terminators |
| MD5: | 1DCB2B45A3FC5C585C4ED4836C86B5C2 |
| SHA1: | 8134492640406A0A23B90EC6776016BFA40CBDC3 |
| SHA256: | 59E7CFD5C4E093F35ABE52A0747C7FF4EAECBBCAF1DAE59C02CC2F7F4B4E429C |
| SSDEEP: | 96:SAiIJjb7a0jtKokMxPqaLT4/rVqcyh/XrL4E0W:S/IJDaetKokMxPLLT4xDyhfr0E1 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1204)
- iexplore.exe (PID: 4052)
- iexplore.exe (PID: 956)
- iexplore.exe (PID: 3504)
- iexplore.exe (PID: 2548)
INFO
Application launched itself
- iexplore.exe (PID: 956)
- iexplore.exe (PID: 4052)
Checks supported languages
- iexplore.exe (PID: 1204)
- iexplore.exe (PID: 956)
- iexplore.exe (PID: 4052)
- iexplore.exe (PID: 3504)
- iexplore.exe (PID: 2548)
Reads the computer name
- iexplore.exe (PID: 956)
- iexplore.exe (PID: 1204)
- iexplore.exe (PID: 4052)
- iexplore.exe (PID: 3504)
- iexplore.exe (PID: 2548)
Changes internet zones settings
- iexplore.exe (PID: 956)
Checks Windows Trust Settings
- iexplore.exe (PID: 4052)
- iexplore.exe (PID: 1204)
- iexplore.exe (PID: 956)
- iexplore.exe (PID: 3504)
- iexplore.exe (PID: 2548)
Reads internet explorer settings
- iexplore.exe (PID: 1204)
- iexplore.exe (PID: 4052)
- iexplore.exe (PID: 3504)
- iexplore.exe (PID: 2548)
Changes settings of System certificates
- iexplore.exe (PID: 4052)
- iexplore.exe (PID: 1204)
- iexplore.exe (PID: 956)
Adds / modifies Windows certificates
- iexplore.exe (PID: 4052)
- iexplore.exe (PID: 1204)
- iexplore.exe (PID: 956)
Reads settings of System Certificates
- iexplore.exe (PID: 1204)
- iexplore.exe (PID: 4052)
- iexplore.exe (PID: 956)
- iexplore.exe (PID: 3504)
- iexplore.exe (PID: 2548)
Creates files in the user directory
- iexplore.exe (PID: 956)
- iexplore.exe (PID: 2548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
Total processes
42
Monitored processes
5
Malicious processes
0
Suspicious processes
0
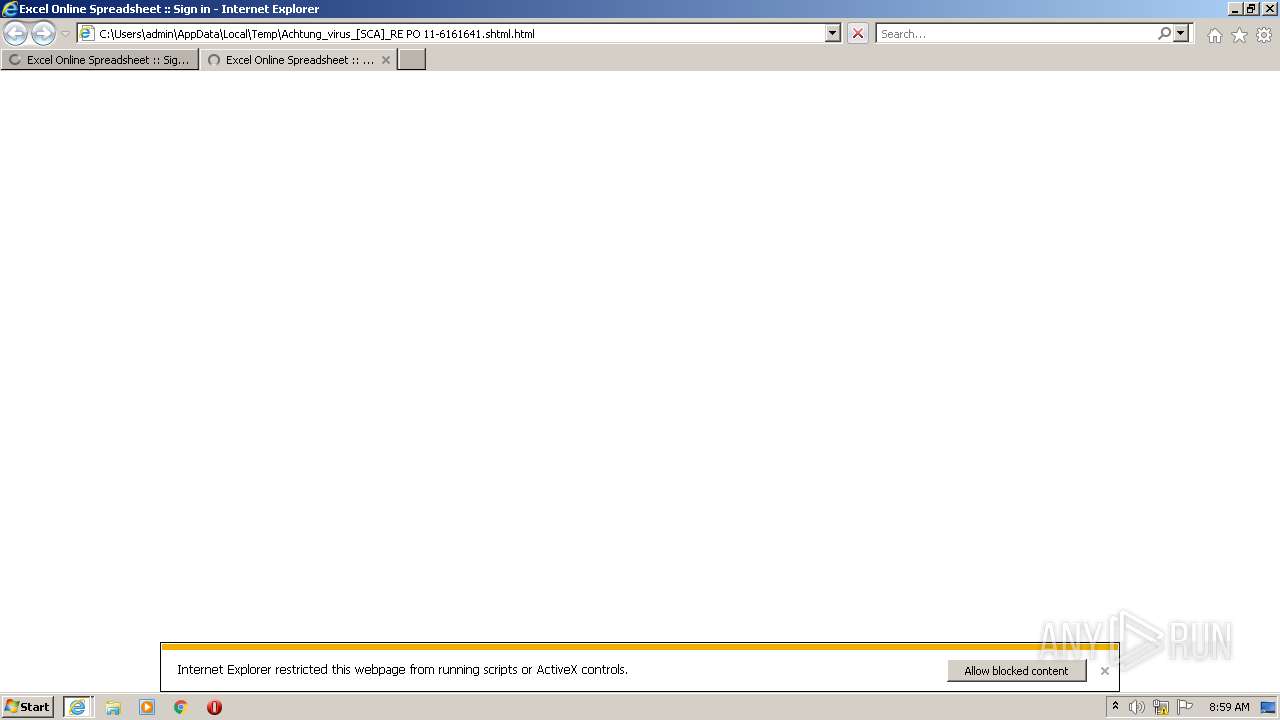
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 956 | "C:\Program Files\Internet Explorer\iexplore.exe" "C:\Users\admin\AppData\Local\Temp\Achtung_virus_[SCA]_RE PO 11-6161641.shtml.html" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1204 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:956 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2548 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:956 CREDAT:2037004 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3504 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:956 CREDAT:464129 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 4052 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:956 CREDAT:275461 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
48 613
Read events
48 248
Write events
344
Delete events
21
Modification events
| (PID) Process: | (956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30968315 | |||
| (PID) Process: | (956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30968315 | |||
| (PID) Process: | (956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
28
Text files
28
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1204 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 4052 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab9E79.tmp | compressed | |
MD5:— | SHA256:— | |||
| 4052 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab9E8B.tmp | compressed | |
MD5:— | SHA256:— | |||
| 4052 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:— | SHA256:— | |||
| 4052 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar9E7A.tmp | cat | |
MD5:— | SHA256:— | |||
| 1204 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:— | SHA256:— | |||
| 1204 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_45E3C223BCF135987E4038FB6B0DBA13 | der | |
MD5:— | SHA256:— | |||
| 4052 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 1204 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_45E3C223BCF135987E4038FB6B0DBA13 | binary | |
MD5:— | SHA256:— | |||
| 956 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
116
DNS requests
27
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4052 | iexplore.exe | GET | 200 | 8.248.91.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?6f5451784d8e8e78 | US | compressed | 60.0 Kb | whitelisted |
4052 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
4052 | iexplore.exe | GET | 200 | 8.248.91.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?844a6579254a164d | US | compressed | 60.0 Kb | whitelisted |
4052 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
1204 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIAjrICMzZli2TN25s%3D | US | der | 724 b | whitelisted |
956 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
1204 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://crl.usertrust.com/USERTrustRSACertificationAuthority.crl | US | der | 978 b | whitelisted |
1204 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
1204 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
4052 | iexplore.exe | GET | 200 | 8.248.91.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?bfd2a261415bbe34 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
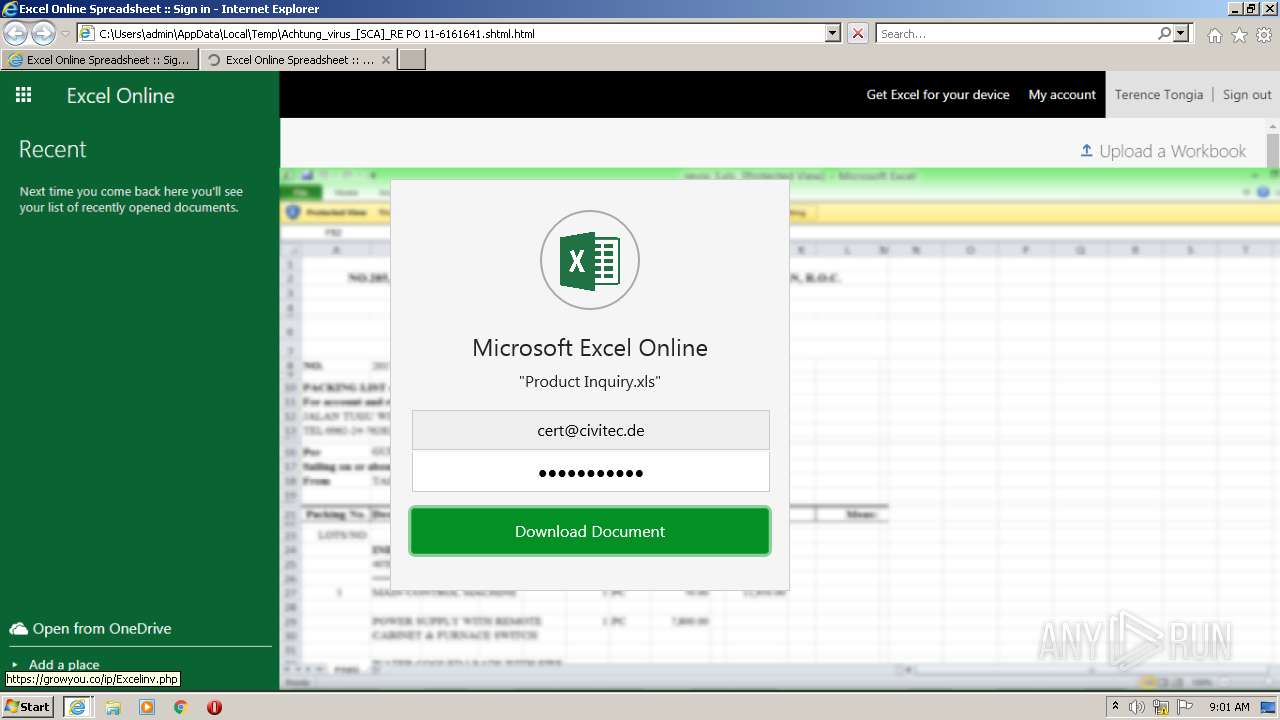
1204 | iexplore.exe | 23.48.23.12:443 | ucarecdn.com | TRUE INTERNET Co.,Ltd. | US | suspicious |
1204 | iexplore.exe | 199.36.158.100:443 | klxszs.web.app | — | US | malicious |
1204 | iexplore.exe | 104.18.10.207:443 | maxcdn.bootstrapcdn.com | Cloudflare Inc | US | suspicious |
1204 | iexplore.exe | 8.248.91.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | unknown |
1204 | iexplore.exe | 69.16.175.10:443 | code.jquery.com | Highwinds Network Group, Inc. | US | malicious |
4052 | iexplore.exe | 199.36.158.100:443 | klxszs.web.app | — | US | malicious |
4052 | iexplore.exe | 23.48.23.12:443 | ucarecdn.com | TRUE INTERNET Co.,Ltd. | US | suspicious |
1204 | iexplore.exe | 142.250.184.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
4052 | iexplore.exe | 23.45.105.185:80 | x1.c.lencr.org | Akamai International B.V. | NL | unknown |
1204 | iexplore.exe | 172.64.155.188:80 | ocsp.comodoca.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
klxszs.web.app |
| malicious |
ucarecdn.com |
| whitelisted |
maxcdn.bootstrapcdn.com |
| whitelisted |
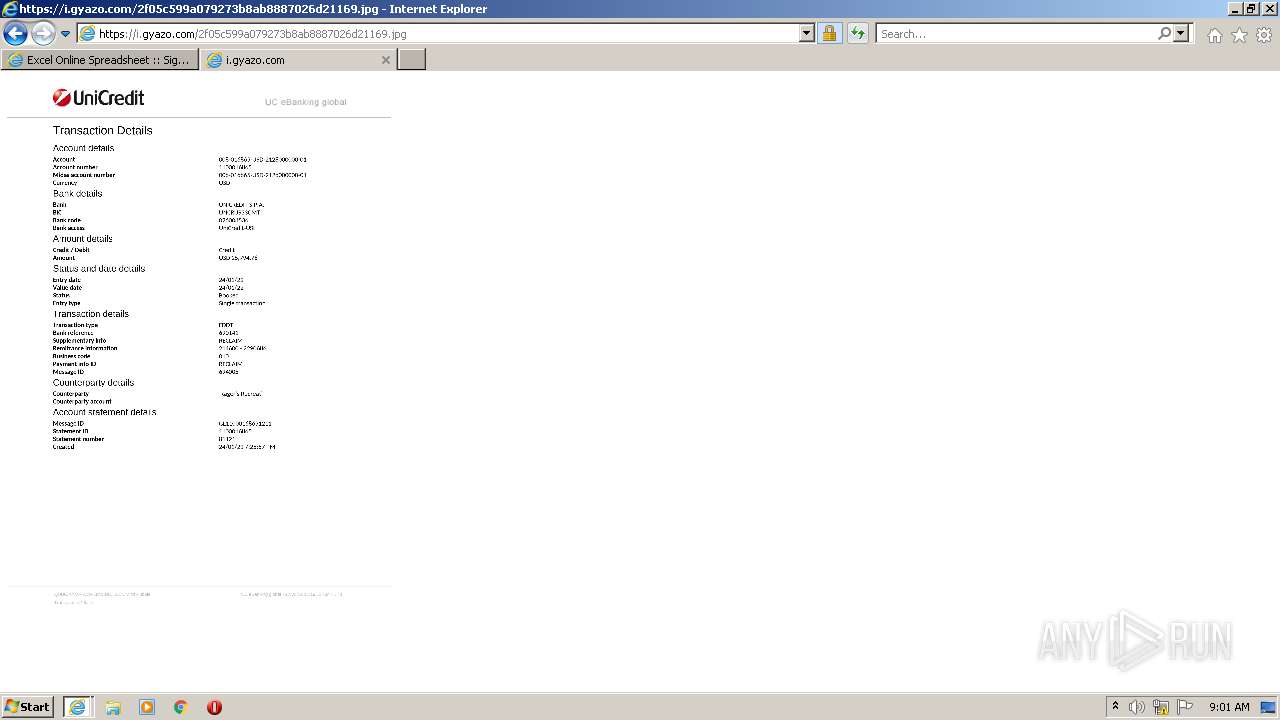
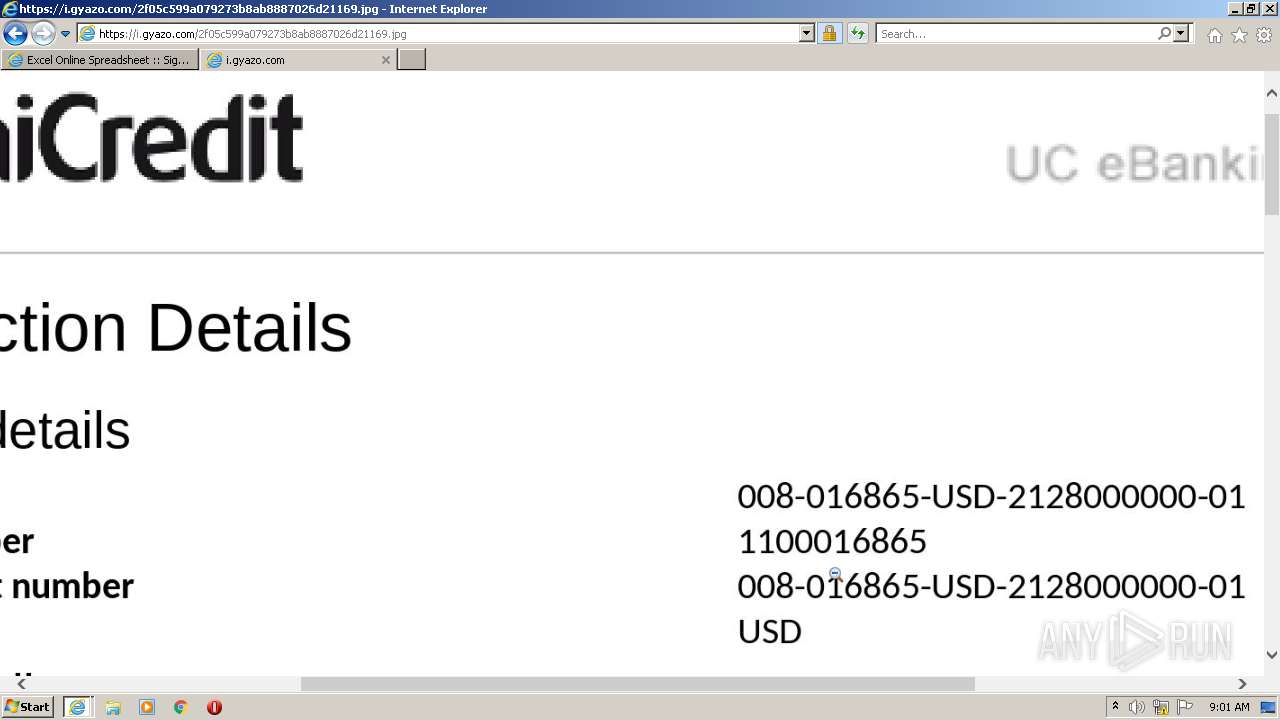
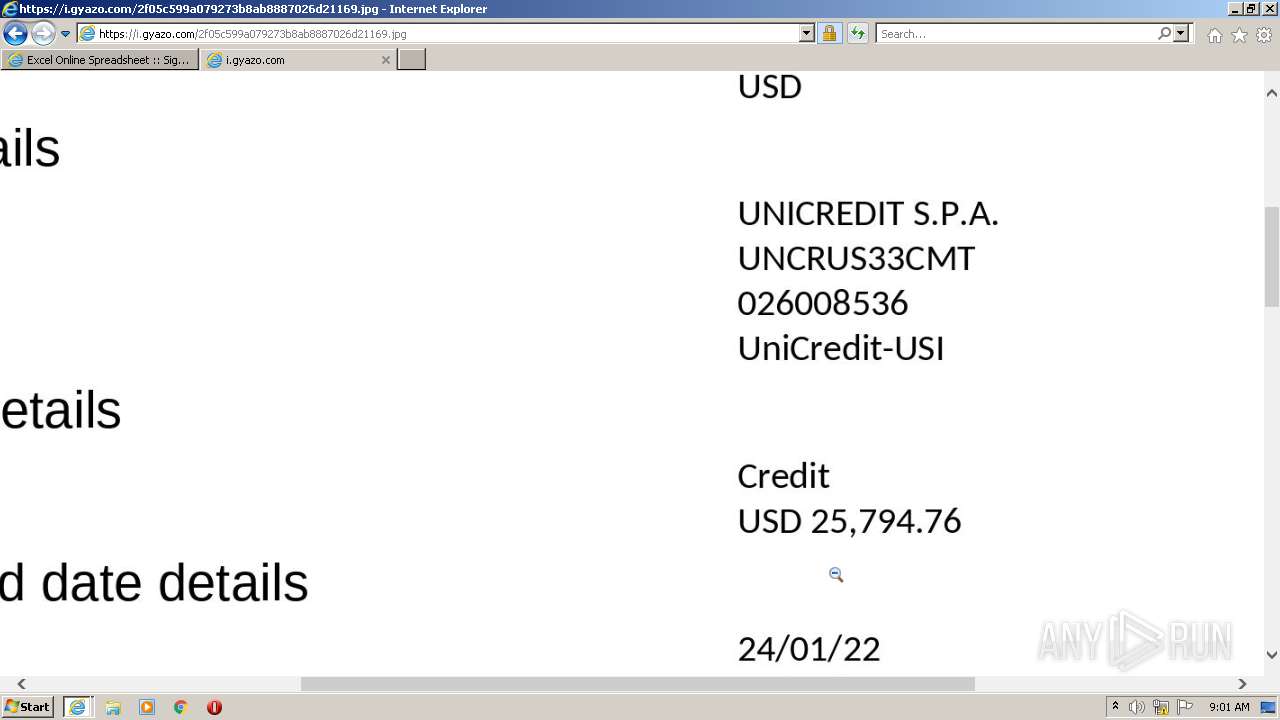
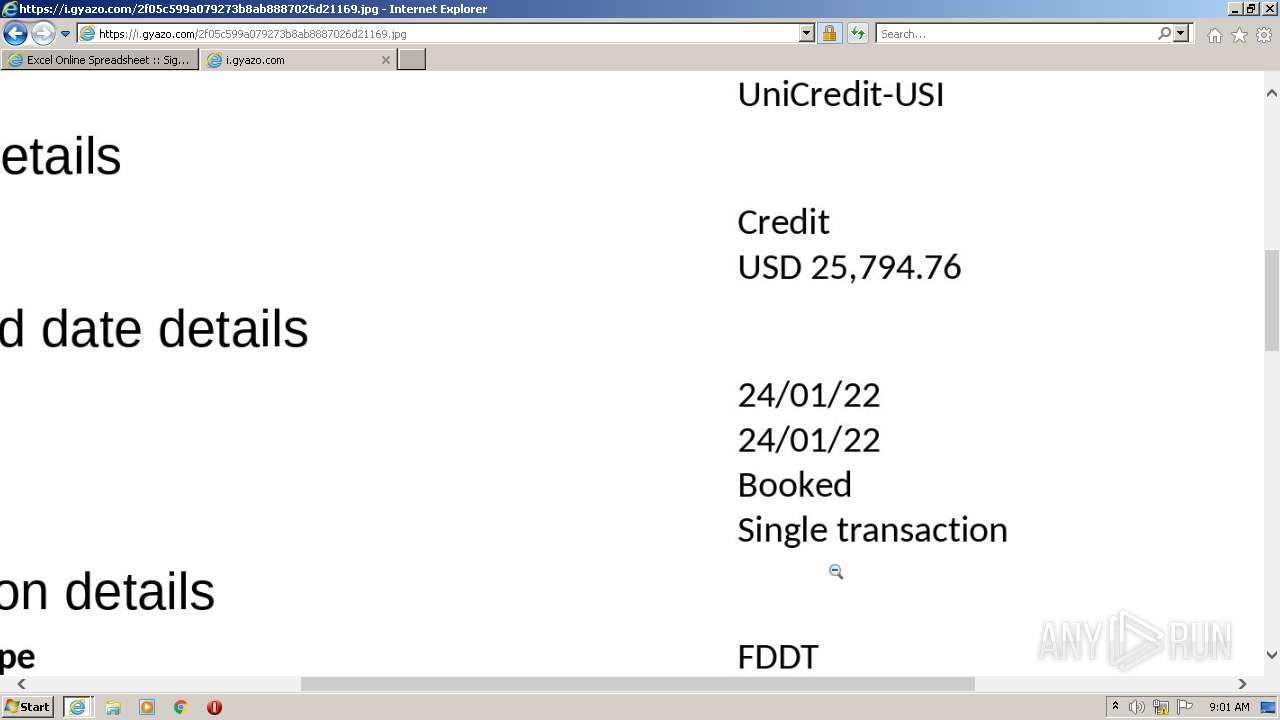
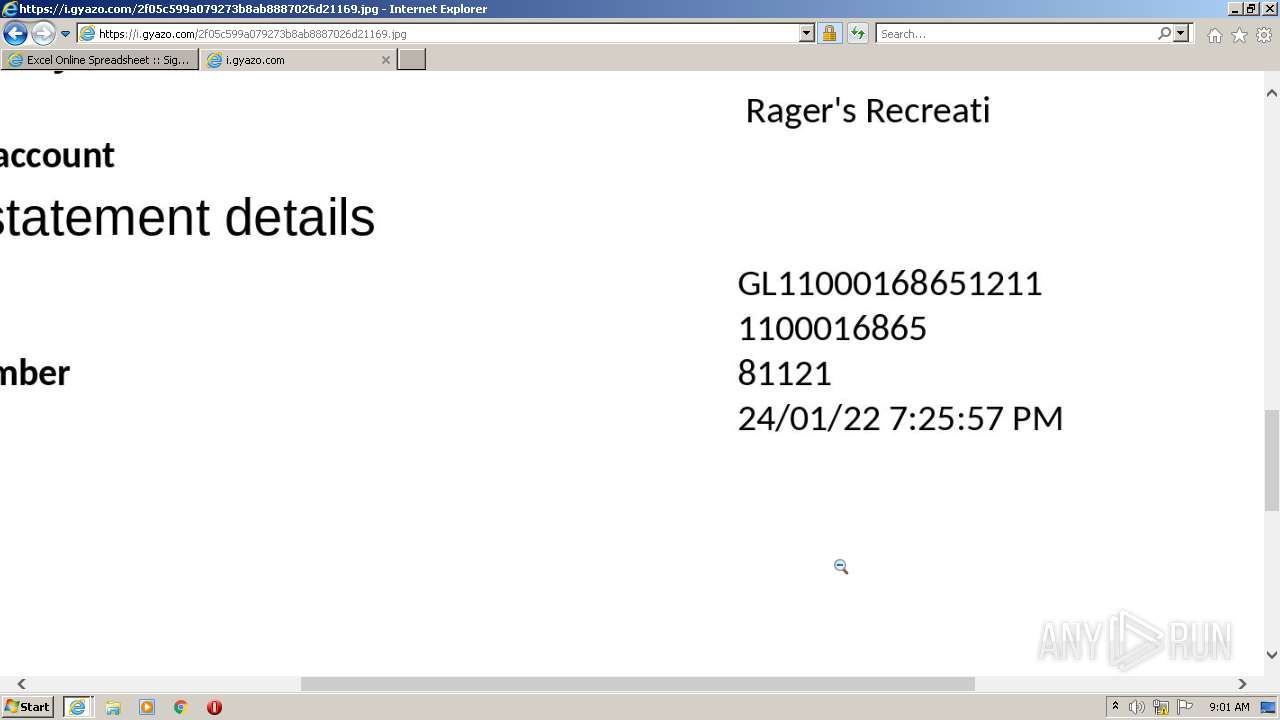
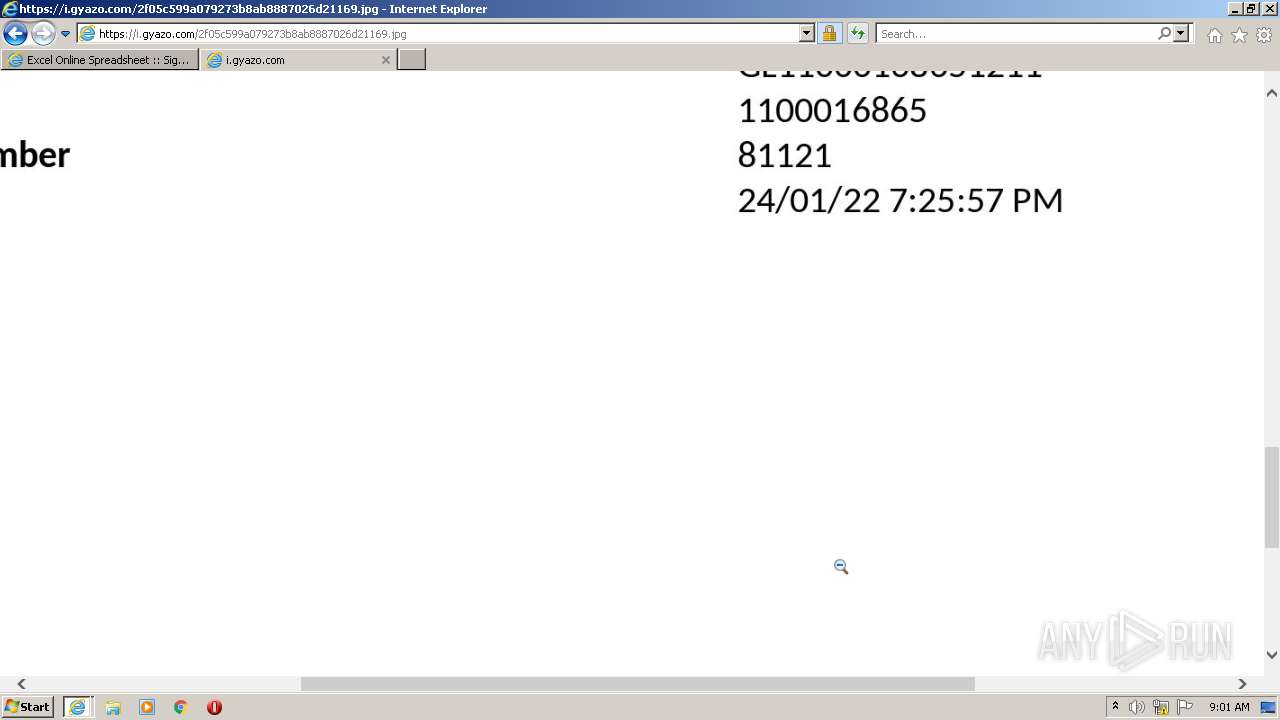
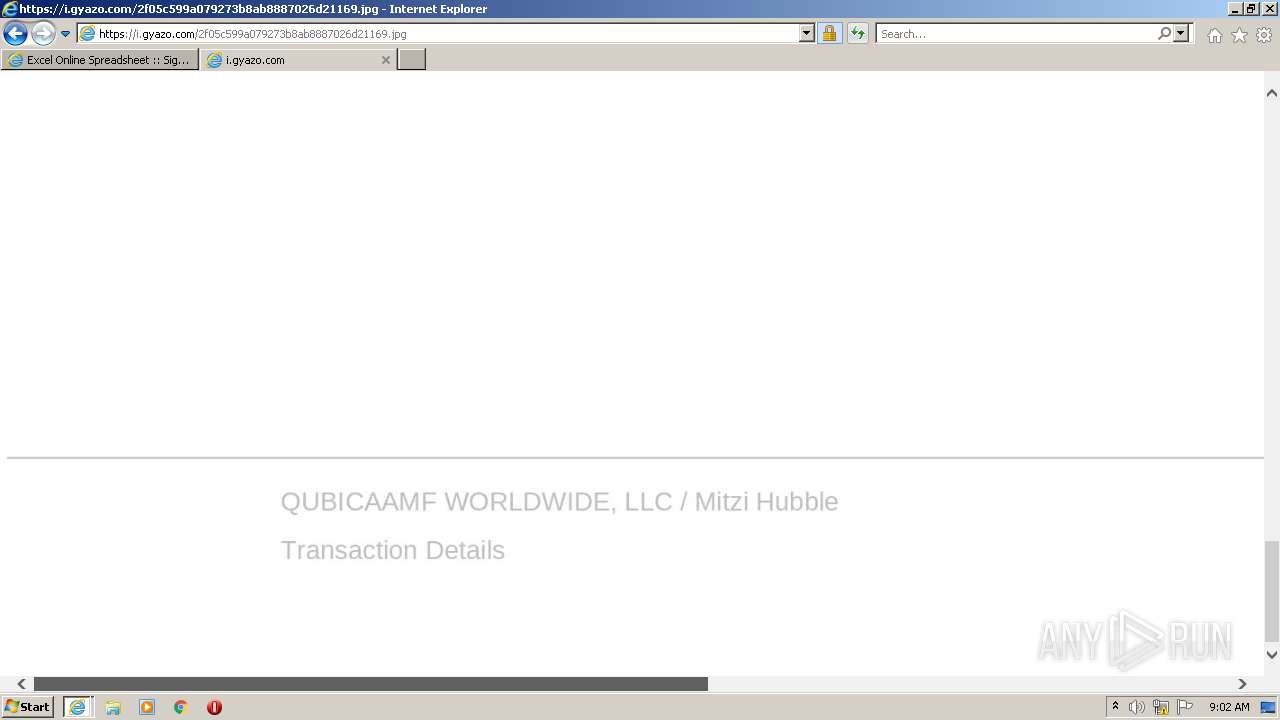
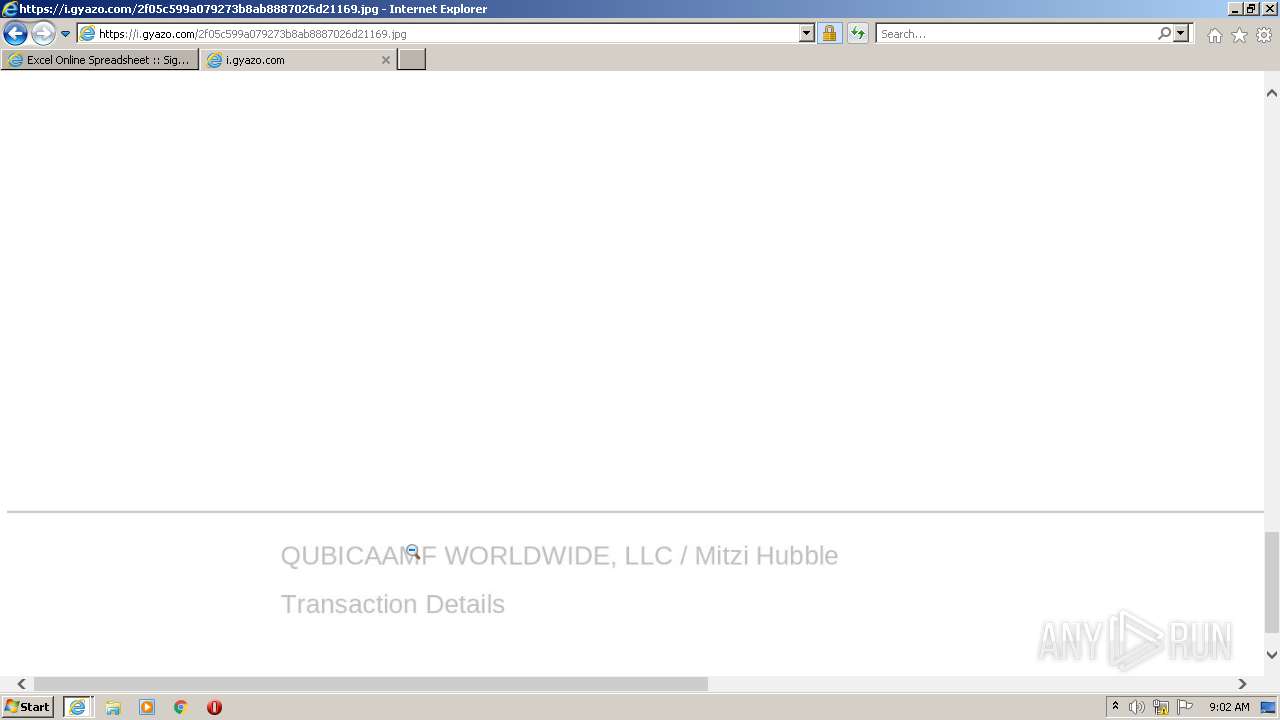
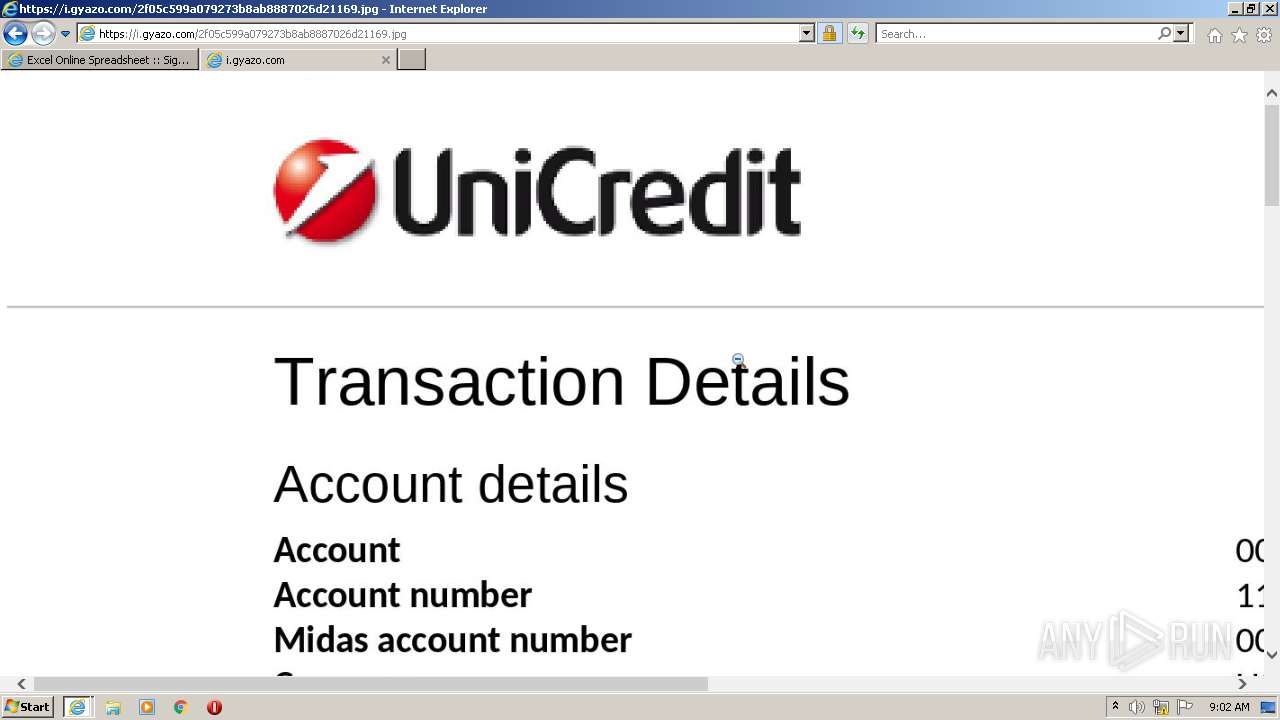
i.gyazo.com |
| whitelisted |
code.jquery.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |