| File name: | 3CXDesktopApp-18.12.416.msi |
| Full analysis: | https://app.any.run/tasks/4c8d9e32-c334-42de-ab12-f6ea8e254247 |
| Verdict: | Malicious activity |
| Analysis date: | August 07, 2024, 00:29:29 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: 3CX Desktop App, Author: 3CX Ltd., Keywords: Installer, Comments: Windows Installer Package, Template: x64;1033, Revision Number: {99BD84FA-1803-4DA0-A416-65D94F4D208A}, Create Time/Date: Mon Mar 13 06:33:26 2023, Last Saved Time/Date: Mon Mar 13 06:33:26 2023, Number of Pages: 405, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.11.2.4516), Security: 2 |
| MD5: | 0EEB1C0133EB4D571178B2D9D14CE3E9 |
| SHA1: | BFECB8CE89A312D2EF4AFC64A63847AE11C6F69E |
| SHA256: | 59E1EDF4D82FAE4978E97512B0331B7EB21DD4B838B850BA46794D9C7A2C0983 |
| SSDEEP: | 1572864:xyTUXdwSabTjb4gJeqSgMfDuF5CKib5mG:xyTUXdwFbTjb4gBSPDtZb5mG |
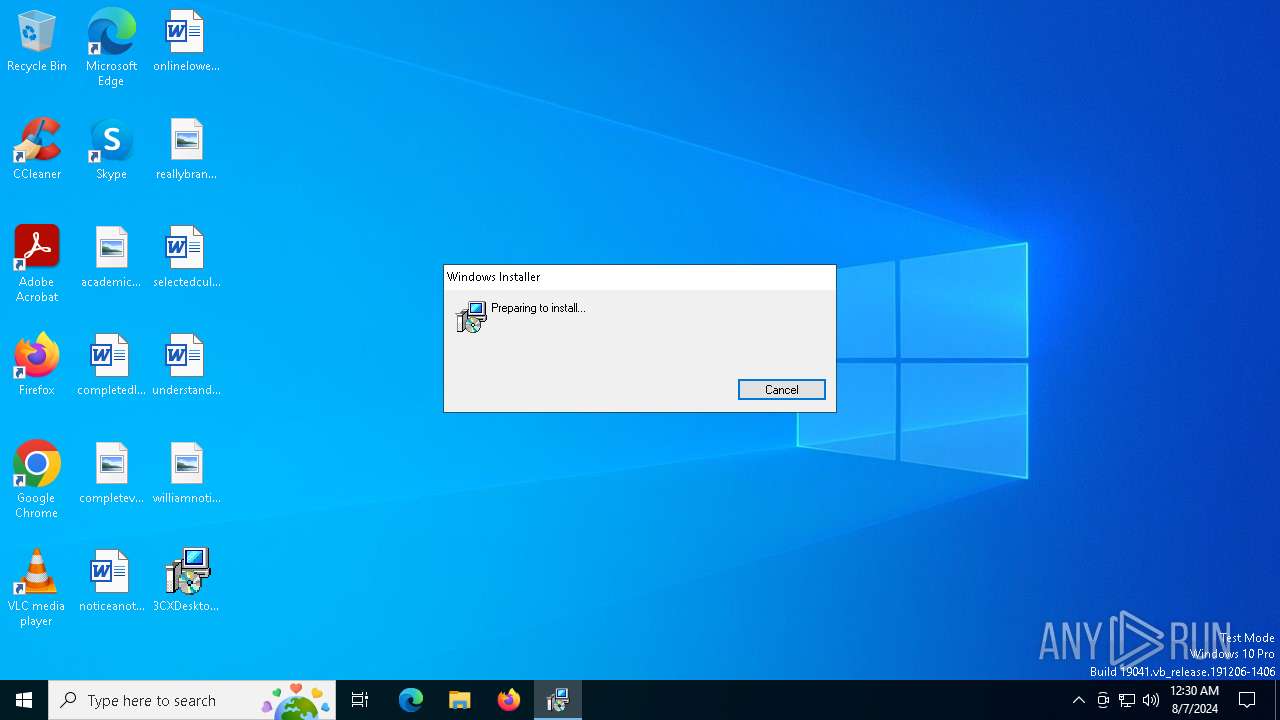
MALICIOUS
Drops the executable file immediately after the start
- msiexec.exe (PID: 6656)
- msiexec.exe (PID: 6828)
Changes the autorun value in the registry
- msiexec.exe (PID: 6828)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 6880)
Checks Windows Trust Settings
- msiexec.exe (PID: 6828)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6828)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 1700)
Reads the date of Windows installation
- msiexec.exe (PID: 1700)
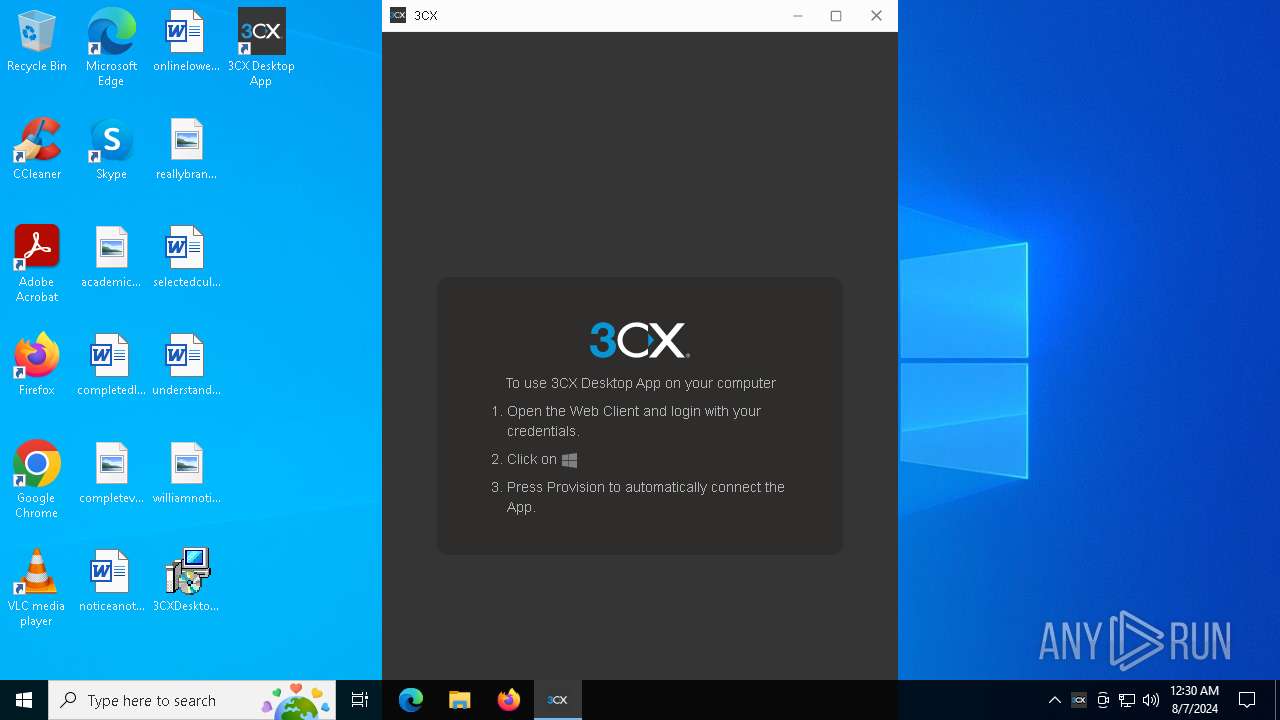
Application launched itself
- 3CXDesktopApp.exe (PID: 6196)
Process drops legitimate windows executable
- msiexec.exe (PID: 6828)
INFO
Reads the software policy settings
- msiexec.exe (PID: 6656)
- msiexec.exe (PID: 6828)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 6656)
Creates files or folders in the user directory
- msiexec.exe (PID: 6656)
- msiexec.exe (PID: 6828)
- 3CXDesktopApp.exe (PID: 6196)
- 3CXDesktopApp.exe (PID: 1664)
- 3CXDesktopApp.exe (PID: 4924)
Checks proxy server information
- msiexec.exe (PID: 6656)
- 3CXDesktopApp.exe (PID: 6196)
Reads the computer name
- msiexec.exe (PID: 6828)
- msiexec.exe (PID: 1700)
- msiexec.exe (PID: 6040)
- 3CXDesktopApp.exe (PID: 6196)
- 3CXDesktopApp.exe (PID: 6224)
- 3CXDesktopApp.exe (PID: 1664)
- 3CXDesktopApp.exe (PID: 3276)
- 3CXDesktopApp.exe (PID: 4924)
- 3CXDesktopApp.exe (PID: 4772)
Checks supported languages
- msiexec.exe (PID: 6828)
- msiexec.exe (PID: 1700)
- msiexec.exe (PID: 6040)
- 3CXDesktopApp.exe (PID: 1664)
- 3CXDesktopApp.exe (PID: 6168)
- 3CXDesktopApp.exe (PID: 6224)
- 3CXDesktopApp.exe (PID: 6196)
- 3CXDesktopApp.exe (PID: 4924)
- 3CXDesktopApp.exe (PID: 3276)
- 3CXDesktopApp.exe (PID: 2456)
- 3CXDesktopApp.exe (PID: 4772)
- 3CXDesktopApp.exe (PID: 5400)
Reads the machine GUID from the registry
- msiexec.exe (PID: 6828)
- 3CXDesktopApp.exe (PID: 4924)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6828)
Application launched itself
- msiexec.exe (PID: 6828)
Creates a software uninstall entry
- msiexec.exe (PID: 6828)
Process checks computer location settings
- msiexec.exe (PID: 1700)
- 3CXDesktopApp.exe (PID: 6196)
- 3CXDesktopApp.exe (PID: 5400)
- 3CXDesktopApp.exe (PID: 2456)
Reads product name
- 3CXDesktopApp.exe (PID: 6196)
Reads Environment values
- 3CXDesktopApp.exe (PID: 6196)
Create files in a temporary directory
- 3CXDesktopApp.exe (PID: 6196)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | 3CX Desktop App |
| Author: | 3CX Ltd. |
| Keywords: | Installer |
| Comments: | Windows Installer Package |
| Template: | x64;1033 |
| RevisionNumber: | {99BD84FA-1803-4DA0-A416-65D94F4D208A} |
| CreateDate: | 2023:03:13 06:33:26 |
| ModifyDate: | 2023:03:13 06:33:26 |
| Pages: | 405 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.11.2.4516) |
| Security: | Read-only recommended |
Total processes
133
Monitored processes
18
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1664 | "C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\app\3CXDesktopApp.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --ignore-certificate-errors=true --ignore-certificate-errors=true --user-data-dir="C:\Users\admin\AppData\Roaming\3CXDesktopApp" --standard-schemes=voipc --enable-sandbox --secure-schemes=voipc --bypasscsp-schemes --cors-schemes=voipc --fetch-schemes=voipc --service-worker-schemes=voipc --streaming-schemes --mojo-platform-channel-handle=1948 --field-trial-handle=1712,i,6772239953607689821,11479508120771243033,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:8 | C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\app\3CXDesktopApp.exe | — | 3CXDesktopApp.exe | |||||||||||
User: admin Company: 3CX Ltd. Integrity Level: MEDIUM Description: 3CX Desktop App Version: 18.12.416 Modules
| |||||||||||||||
| 1700 | C:\Windows\syswow64\MsiExec.exe -Embedding 3E1A01557E4E57B9B6B06A134FC05A46 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2456 | "C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\app\3CXDesktopApp.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\3CXDesktopApp" --standard-schemes=voipc --enable-sandbox --secure-schemes=voipc --bypasscsp-schemes --cors-schemes=voipc --fetch-schemes=voipc --service-worker-schemes=voipc --streaming-schemes --app-user-model-id=9071E5B59CCA4D120EC8D975AF3F02AB --app-path="C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\app\resources\app.asar" --enable-sandbox --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3576 --field-trial-handle=1712,i,6772239953607689821,11479508120771243033,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:1 | C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\app\3CXDesktopApp.exe | — | 3CXDesktopApp.exe | |||||||||||
User: admin Company: 3CX Ltd. Integrity Level: LOW Description: 3CX Desktop App Version: 18.12.416 Modules
| |||||||||||||||
| 3276 | "C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\app\3CXDesktopApp.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --ignore-certificate-errors=true --ignore-certificate-errors=true --user-data-dir="C:\Users\admin\AppData\Roaming\3CXDesktopApp" --standard-schemes=voipc --enable-sandbox --secure-schemes=voipc --bypasscsp-schemes --cors-schemes=voipc --fetch-schemes=voipc --service-worker-schemes=voipc --streaming-schemes --mojo-platform-channel-handle=3780 --field-trial-handle=1712,i,6772239953607689821,11479508120771243033,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:8 | C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\app\3CXDesktopApp.exe | — | 3CXDesktopApp.exe | |||||||||||
User: admin Company: 3CX Ltd. Integrity Level: LOW Description: 3CX Desktop App Version: 18.12.416 Modules
| |||||||||||||||
| 3720 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4316 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4772 | "C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\app\3CXDesktopApp.exe" --type=utility --utility-sub-type=video_capture.mojom.VideoCaptureService --lang=en-US --service-sandbox-type=none --ignore-certificate-errors=true --ignore-certificate-errors=true --user-data-dir="C:\Users\admin\AppData\Roaming\3CXDesktopApp" --standard-schemes=voipc --enable-sandbox --secure-schemes=voipc --bypasscsp-schemes --cors-schemes=voipc --fetch-schemes=voipc --service-worker-schemes=voipc --streaming-schemes --mojo-platform-channel-handle=3744 --field-trial-handle=1712,i,6772239953607689821,11479508120771243033,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:8 | C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\app\3CXDesktopApp.exe | — | 3CXDesktopApp.exe | |||||||||||
User: admin Company: 3CX Ltd. Integrity Level: MEDIUM Description: 3CX Desktop App Exit code: 0 Version: 18.12.416 Modules
| |||||||||||||||
| 4924 | "C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\app\3CXDesktopApp.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --user-data-dir="C:\Users\admin\AppData\Roaming\3CXDesktopApp" --gpu-preferences=UAAAAAAAAADoAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=3540 --field-trial-handle=1712,i,6772239953607689821,11479508120771243033,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:2 | C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\app\3CXDesktopApp.exe | — | 3CXDesktopApp.exe | |||||||||||
User: admin Company: 3CX Ltd. Integrity Level: MEDIUM Description: 3CX Desktop App Exit code: 0 Version: 18.12.416 Modules
| |||||||||||||||
| 5400 | "C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\app\3CXDesktopApp.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\3CXDesktopApp" --standard-schemes=voipc --enable-sandbox --secure-schemes=voipc --bypasscsp-schemes --cors-schemes=voipc --fetch-schemes=voipc --service-worker-schemes=voipc --streaming-schemes --app-user-model-id=9071E5B59CCA4D120EC8D975AF3F02AB --app-path="C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\app\resources\app.asar" --enable-sandbox --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --mojo-platform-channel-handle=2288 --field-trial-handle=1712,i,6772239953607689821,11479508120771243033,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:1 | C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\app\3CXDesktopApp.exe | — | 3CXDesktopApp.exe | |||||||||||
User: admin Company: 3CX Ltd. Integrity Level: LOW Description: 3CX Desktop App Version: 18.12.416 Modules
| |||||||||||||||
| 5760 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
35 316
Read events
34 880
Write events
399
Delete events
37
Modification events
| (PID) Process: | (6828) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 48000000000000004FD7D20161E8DA01AC1A0000D01A0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6828) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 48000000000000004FD7D20161E8DA01AC1A0000D01A0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6828) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000A46E0E0261E8DA01AC1A0000D01A0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6828) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000A46E0E0261E8DA01AC1A0000D01A0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6828) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 48000000000000001DD2100261E8DA01AC1A0000D01A0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6828) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 48000000000000009335130261E8DA01AC1A0000D01A0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6828) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (6828) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000EE6D8A0261E8DA01AC1A0000D01A0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6828) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000EE6D8A0261E8DA01AC1A0000581B0000E803000001000000000000000000000020AE83C44A72954C9F94082E82FE46BC00000000000000000000000000000000 | |||
| (PID) Process: | (6880) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000E460960261E8DA01E01A00007C1B0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
19
Suspicious files
109
Text files
13
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6828 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 6828 | msiexec.exe | C:\Windows\Installer\ed7be.msi | — | |
MD5:— | SHA256:— | |||
| 6828 | msiexec.exe | C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\app-18.12.416\3CXDesktopApp.exe | — | |
MD5:— | SHA256:— | |||
| 6656 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_E6095CD2AECC9011BCD0D7B421356B17 | binary | |
MD5:0745288C6360F4A2060C6A07467F3DFE | SHA256:D9C5BE372FBE307D1B9FF13F6D3FE6943A6510082A0DE3051884C4749A15F112 | |||
| 6828 | msiexec.exe | C:\Windows\Installer\MSIDF44.tmp | executable | |
MD5:93394D2866590FB66759F5F0263453F2 | SHA256:5C29B8255ACE0CD94C066C528C8AD04F0F45EBA12FCF94DA7B9CA1B64AD4288B | |||
| 6828 | msiexec.exe | C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\3CXDesktopApp.VisualElementsManifest.xml | text | |
MD5:5A64EFFD99CEE7AE227BC47EEE578855 | SHA256:ABFCB8AC6CCE1DFC5EEE1D870D794E2CD352D1F5AAA226918B7D3D3024D96507 | |||
| 6656 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\D7833C286363AD25C70511661A83D581_5453925CF1FC5AEA2F776AD35FF4432C | binary | |
MD5:5223C5DE7D5F7B91472BB4AA666905A2 | SHA256:46EE912645F1C35EBB3404A8DAEDD720D50F3731AA7C4542FC037932E122CD5F | |||
| 6828 | msiexec.exe | C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\app-18.12.416\icudtl.dat | — | |
MD5:— | SHA256:— | |||
| 6828 | msiexec.exe | C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\3CXDesktopApp.exe | executable | |
MD5:704DB9184700481A56E5100FB56496CE | SHA256:A60A61BF844BC181D4540C9FAC53203250A982E7C3AD6153869F01E19CC36203 | |||
| 6828 | msiexec.exe | C:\Windows\Installer\MSID9D1.tmp | executable | |
MD5:A3AE5D86ECF38DB9427359EA37A5F646 | SHA256:C8D190D5BE1EFD2D52F72A72AE9DFA3940AB3FACEB626405959349654FE18B74 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
17
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6656 | msiexec.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEB2iSDBvmyYY0ILgln0z02o%3D | unknown | binary | 2.18 Kb | whitelisted |
6656 | msiexec.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ5suEceKjAJbxseAmHFkQ9FrhTWQQUDuE6qFM6MdWKvsG7rWcaA4WtNA4CEBtmEd%2Bcmk1uzI7VDJuReHM%3D | US | binary | 531 b | whitelisted |
— | — | POST | 204 | 95.100.146.8:443 | https://www.bing.com/threshold/xls.aspx | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6656 | msiexec.exe | 104.18.38.233:80 | ocsp.usertrust.com | CLOUDFLARENET | — | shared |
6656 | msiexec.exe | 172.64.149.23:80 | ocsp.usertrust.com | CLOUDFLARENET | US | unknown |
5336 | SearchApp.exe | 2.23.209.179:443 | www.bing.com | Akamai International B.V. | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
www.bing.com |
| whitelisted |