| File name: | 59e1edf4d82fae4978e97512b0331b7eb21dd4b838b850ba46794d9c7a2c0983.msi |
| Full analysis: | https://app.any.run/tasks/2856878d-d3e6-48ab-9691-d3c77fdc1145 |
| Verdict: | Malicious activity |
| Analysis date: | June 17, 2024, 05:19:42 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: 3CX Desktop App, Author: 3CX Ltd., Keywords: Installer, Comments: Windows Installer Package, Template: x64;1033, Revision Number: {99BD84FA-1803-4DA0-A416-65D94F4D208A}, Create Time/Date: Mon Mar 13 06:33:26 2023, Last Saved Time/Date: Mon Mar 13 06:33:26 2023, Number of Pages: 405, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.11.2.4516), Security: 2 |
| MD5: | 0EEB1C0133EB4D571178B2D9D14CE3E9 |
| SHA1: | BFECB8CE89A312D2EF4AFC64A63847AE11C6F69E |
| SHA256: | 59E1EDF4D82FAE4978E97512B0331B7EB21DD4B838B850BA46794D9C7A2C0983 |
| SSDEEP: | 1572864:xyTUXdwSabTjb4gJeqSgMfDuF5CKib5mG:xyTUXdwFbTjb4gBSPDtZb5mG |
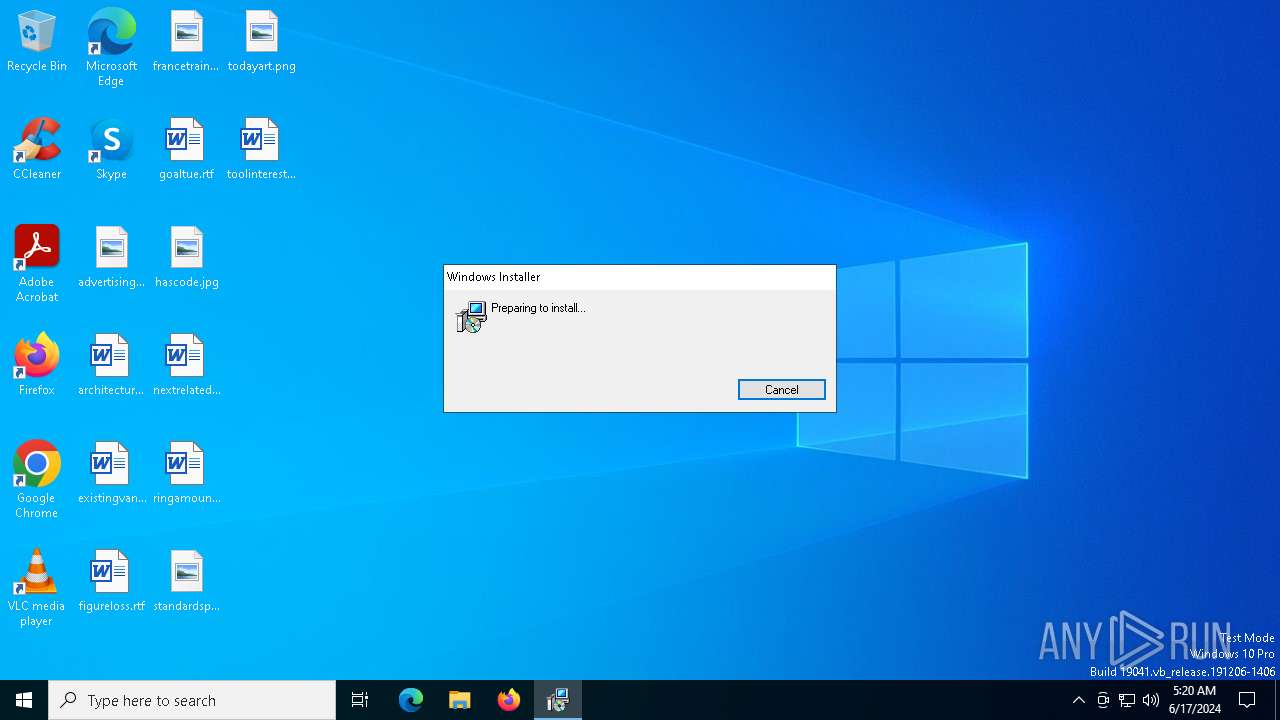
MALICIOUS
Drops the executable file immediately after the start
- msiexec.exe (PID: 7064)
- msiexec.exe (PID: 6364)
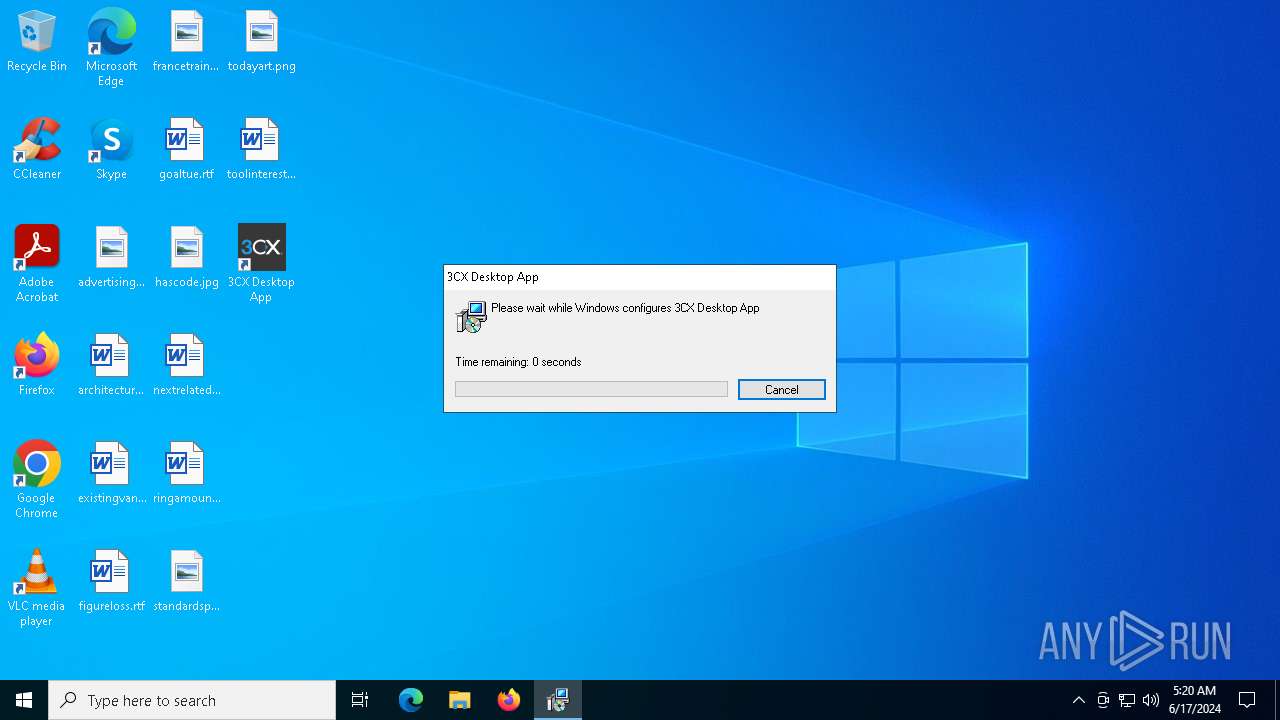
Changes the autorun value in the registry
- msiexec.exe (PID: 6364)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 6320)
Checks Windows Trust Settings
- msiexec.exe (PID: 6364)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6364)
Process drops legitimate windows executable
- msiexec.exe (PID: 6364)
Reads the date of Windows installation
- msiexec.exe (PID: 6192)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 6192)
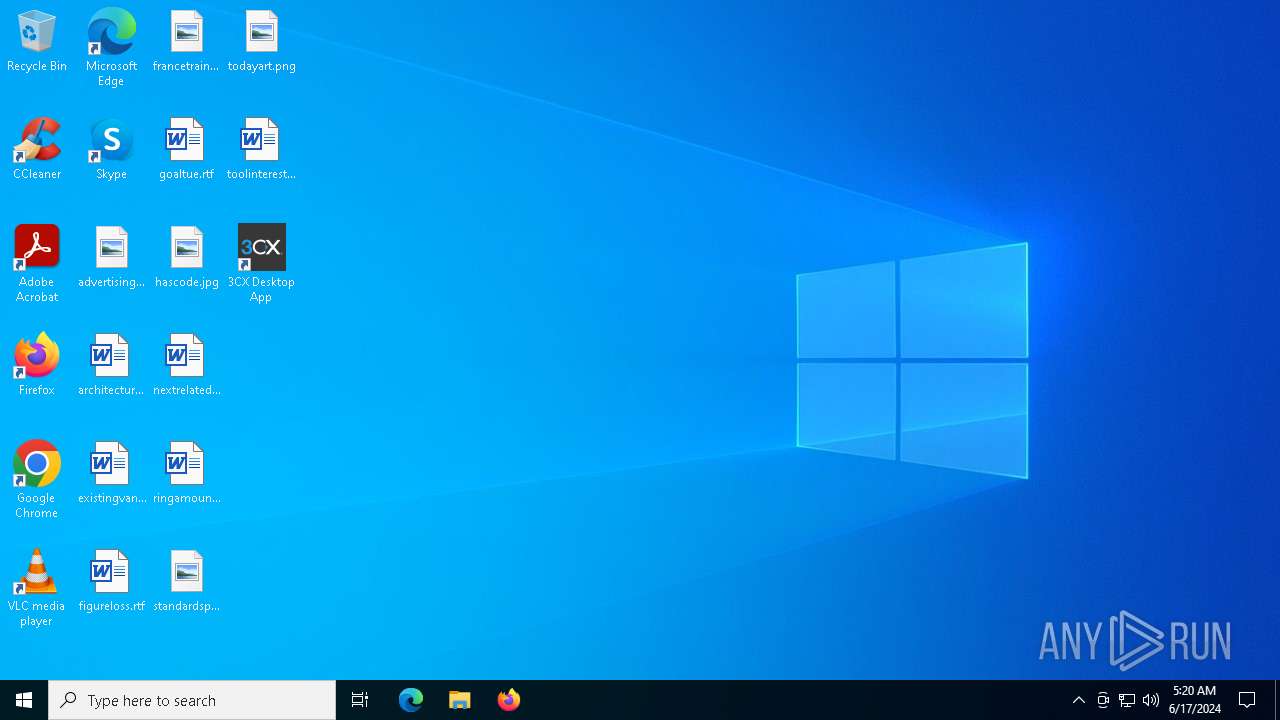
Application launched itself
- 3CXDesktopApp.exe (PID: 780)
INFO
Reads the software policy settings
- msiexec.exe (PID: 7064)
- msiexec.exe (PID: 6364)
- slui.exe (PID: 3724)
Checks proxy server information
- msiexec.exe (PID: 7064)
- 3CXDesktopApp.exe (PID: 780)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 7064)
Creates files or folders in the user directory
- msiexec.exe (PID: 7064)
- msiexec.exe (PID: 6364)
- 3CXDesktopApp.exe (PID: 780)
- 3CXDesktopApp.exe (PID: 5940)
Checks supported languages
- msiexec.exe (PID: 6364)
- msiexec.exe (PID: 6192)
- msiexec.exe (PID: 6456)
- 3CXDesktopApp.exe (PID: 780)
- 3CXDesktopApp.exe (PID: 7012)
- 3CXDesktopApp.exe (PID: 5940)
- 3CXDesktopApp.exe (PID: 5004)
- 3CXDesktopApp.exe (PID: 6564)
- 3CXDesktopApp.exe (PID: 5012)
- 3CXDesktopApp.exe (PID: 1100)
- 3CXDesktopApp.exe (PID: 5592)
Reads the computer name
- msiexec.exe (PID: 6364)
- msiexec.exe (PID: 6192)
- msiexec.exe (PID: 6456)
- 3CXDesktopApp.exe (PID: 780)
- 3CXDesktopApp.exe (PID: 5004)
- 3CXDesktopApp.exe (PID: 5940)
- 3CXDesktopApp.exe (PID: 1100)
- 3CXDesktopApp.exe (PID: 5012)
Reads the machine GUID from the registry
- msiexec.exe (PID: 6364)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6364)
Application launched itself
- msiexec.exe (PID: 6364)
Creates a software uninstall entry
- msiexec.exe (PID: 6364)
Reads Environment values
- 3CXDesktopApp.exe (PID: 780)
Process checks computer location settings
- msiexec.exe (PID: 6192)
- 3CXDesktopApp.exe (PID: 780)
- 3CXDesktopApp.exe (PID: 5592)
- 3CXDesktopApp.exe (PID: 6564)
Reads product name
- 3CXDesktopApp.exe (PID: 780)
Create files in a temporary directory
- 3CXDesktopApp.exe (PID: 780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | 3CX Desktop App |
| Author: | 3CX Ltd. |
| Keywords: | Installer |
| Comments: | Windows Installer Package |
| Template: | x64;1033 |
| RevisionNumber: | {99BD84FA-1803-4DA0-A416-65D94F4D208A} |
| CreateDate: | 2023:03:13 06:33:26 |
| ModifyDate: | 2023:03:13 06:33:26 |
| Pages: | 405 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.11.2.4516) |
| Security: | Read-only recommended |
Total processes
140
Monitored processes
20
Malicious processes
3
Suspicious processes
2
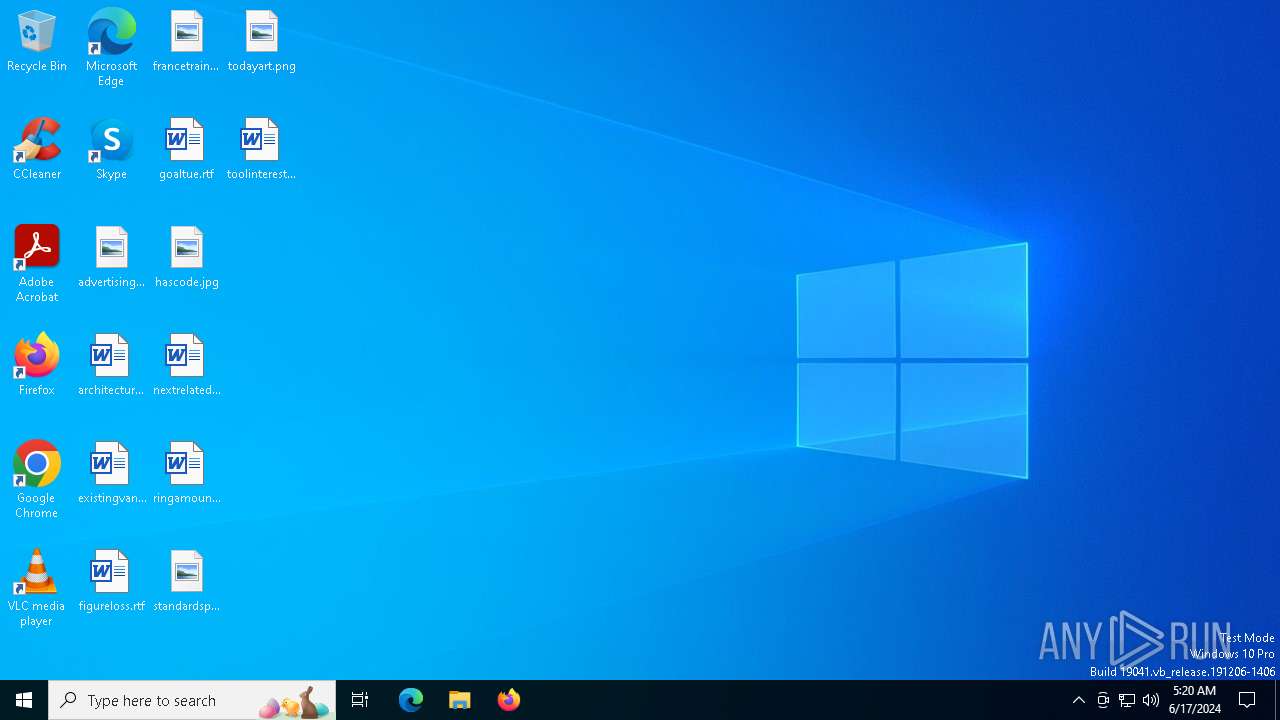
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 780 | "C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\app\3CXDesktopApp.exe" | C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\app\3CXDesktopApp.exe | — | 3CXDesktopApp.exe | |||||||||||
User: admin Company: 3CX Ltd. Integrity Level: MEDIUM Description: 3CX Desktop App Version: 18.12.416 Modules
| |||||||||||||||
| 1100 | "C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\app\3CXDesktopApp.exe" --type=utility --utility-sub-type=video_capture.mojom.VideoCaptureService --lang=en-US --service-sandbox-type=none --ignore-certificate-errors=true --ignore-certificate-errors=true --user-data-dir="C:\Users\admin\AppData\Roaming\3CXDesktopApp" --standard-schemes=voipc --enable-sandbox --secure-schemes=voipc --bypasscsp-schemes --cors-schemes=voipc --fetch-schemes=voipc --service-worker-schemes=voipc --streaming-schemes --mojo-platform-channel-handle=3776 --field-trial-handle=1688,i,7150361765323292352,11679638171082459096,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:8 | C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\app\3CXDesktopApp.exe | — | 3CXDesktopApp.exe | |||||||||||
User: admin Company: 3CX Ltd. Integrity Level: MEDIUM Description: 3CX Desktop App Exit code: 0 Version: 18.12.416 Modules
| |||||||||||||||
| 1724 | C:\WINDOWS\system32\reg.exe QUERY HKCU\Software\Microsoft\Windows\CurrentVersion\Run /v 3CXDeskTopApp | C:\Windows\System32\reg.exe | — | 3CXDesktopApp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1964 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3724 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5004 | "C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\app\3CXDesktopApp.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\3CXDesktopApp" --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1700 --field-trial-handle=1688,i,7150361765323292352,11679638171082459096,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:2 | C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\app\3CXDesktopApp.exe | — | 3CXDesktopApp.exe | |||||||||||
User: admin Company: 3CX Ltd. Integrity Level: LOW Description: 3CX Desktop App Version: 18.12.416 Modules
| |||||||||||||||
| 5012 | "C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\app\3CXDesktopApp.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --ignore-certificate-errors=true --ignore-certificate-errors=true --user-data-dir="C:\Users\admin\AppData\Roaming\3CXDesktopApp" --standard-schemes=voipc --enable-sandbox --secure-schemes=voipc --bypasscsp-schemes --cors-schemes=voipc --fetch-schemes=voipc --service-worker-schemes=voipc --streaming-schemes --mojo-platform-channel-handle=3772 --field-trial-handle=1688,i,7150361765323292352,11679638171082459096,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:8 | C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\app\3CXDesktopApp.exe | — | 3CXDesktopApp.exe | |||||||||||
User: admin Company: 3CX Ltd. Integrity Level: LOW Description: 3CX Desktop App Version: 18.12.416 Modules
| |||||||||||||||
| 5100 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5592 | "C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\app\3CXDesktopApp.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\3CXDesktopApp" --standard-schemes=voipc --enable-sandbox --secure-schemes=voipc --bypasscsp-schemes --cors-schemes=voipc --fetch-schemes=voipc --service-worker-schemes=voipc --streaming-schemes --app-user-model-id=9071E5B59CCA4D120EC8D975AF3F02AB --app-path="C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\app\resources\app.asar" --enable-sandbox --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --mojo-platform-channel-handle=2248 --field-trial-handle=1688,i,7150361765323292352,11679638171082459096,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:1 | C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\app\3CXDesktopApp.exe | — | 3CXDesktopApp.exe | |||||||||||
User: admin Company: 3CX Ltd. Integrity Level: LOW Description: 3CX Desktop App Version: 18.12.416 Modules
| |||||||||||||||
| 5860 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
35 914
Read events
35 477
Write events
400
Delete events
37
Modification events
| (PID) Process: | (6364) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000E9DFB81076C0DA01DC18000008190000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6364) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000E9DFB81076C0DA01DC18000008190000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6364) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000BBED091176C0DA01DC18000008190000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6364) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000BBED091176C0DA01DC18000008190000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6364) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 480000000000000036510C1176C0DA01DC18000008190000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6364) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000A86F131176C0DA01DC18000008190000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6364) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (6364) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 48000000000000001D96961176C0DA01DC18000008190000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6364) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000006DFA981176C0DA01DC18000094090000E80300000100000000000000000000006595EEF714C4DA4885FCC483AD0F1A8B00000000000000000000000000000000 | |||
| (PID) Process: | (6320) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000062C49D1176C0DA01B0180000D0180000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
19
Suspicious files
64
Text files
13
Unknown types
46
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6364 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 6364 | msiexec.exe | C:\WINDOWS\Installer\11a6dc.msi | — | |
MD5:— | SHA256:— | |||
| 6364 | msiexec.exe | C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\app-18.12.416\3CXDesktopApp.exe | — | |
MD5:— | SHA256:— | |||
| 7064 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\D7833C286363AD25C70511661A83D581_5453925CF1FC5AEA2F776AD35FF4432C | der | |
MD5:6C62C850771B39ACC29AAD9AA0F899F5 | SHA256:6F0A98348814DED9C5A64DBAF64B99E3FCE836EBE7E49C11C29BB6F8E0893BB2 | |||
| 6364 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:DFC07E0B06E8276AA884AA70C60E4024 | SHA256:B4E5A0AA2F84E6BC069E5AE5F20984B37DE13EFE65407B3DC573AA2E6EDA2F50 | |||
| 6364 | msiexec.exe | C:\WINDOWS\Installer\MSIAEFD.tmp | executable | |
MD5:93394D2866590FB66759F5F0263453F2 | SHA256:5C29B8255ACE0CD94C066C528C8AD04F0F45EBA12FCF94DA7B9CA1B64AD4288B | |||
| 6364 | msiexec.exe | C:\WINDOWS\Installer\MSIAEAE.tmp | executable | |
MD5:B2E2C24EBCE4F188CF28B9E1470227F5 | SHA256:233F5E43325615710CA1AA580250530E06339DEF861811073912E8A16B058C69 | |||
| 6364 | msiexec.exe | C:\Users\admin\AppData\Local\Programs\3CXDesktopApp\app-18.12.416\icudtl.dat | — | |
MD5:— | SHA256:— | |||
| 7064 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_E6095CD2AECC9011BCD0D7B421356B17 | der | |
MD5:D523FDFC0B3B03D346FA47540FB7D196 | SHA256:AA4758EC284F40A156FB745B79632A20F42F6FE0775E4C292DA07262F6305221 | |||
| 6364 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{f7ee9565-c414-48da-85fc-c483ad0f1a8b}_OnDiskSnapshotProp | binary | |
MD5:DFC07E0B06E8276AA884AA70C60E4024 | SHA256:B4E5A0AA2F84E6BC069E5AE5F20984B37DE13EFE65407B3DC573AA2E6EDA2F50 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
56
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5632 | svchost.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
5260 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
5632 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
4936 | SIHClient.exe | GET | 200 | 88.221.125.143:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
7064 | msiexec.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEB2iSDBvmyYY0ILgln0z02o%3D | unknown | — | — | unknown |
4936 | SIHClient.exe | GET | 200 | 88.221.125.143:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
7064 | msiexec.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ5suEceKjAJbxseAmHFkQ9FrhTWQQUDuE6qFM6MdWKvsG7rWcaA4WtNA4CEBtmEd%2Bcmk1uzI7VDJuReHM%3D | unknown | — | — | unknown |
4680 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | — | — | unknown |
2908 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 239.255.255.250:1900 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
5632 | svchost.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | unknown |
5632 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
4680 | SearchApp.exe | 2.19.96.25:443 | — | Akamai International B.V. | DE | unknown |
4680 | SearchApp.exe | 2.19.96.10:443 | — | Akamai International B.V. | DE | unknown |
4680 | SearchApp.exe | 2.19.96.27:443 | — | Akamai International B.V. | DE | unknown |
— | — | 2.19.96.27:443 | — | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |