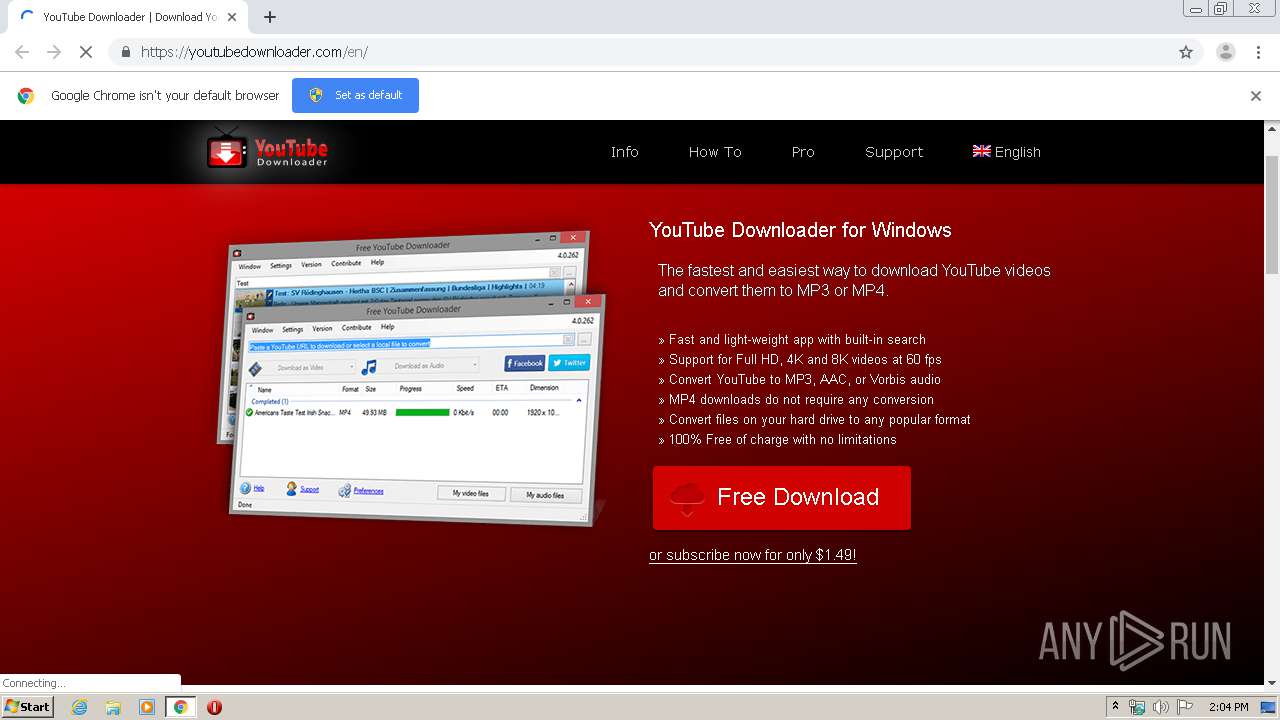
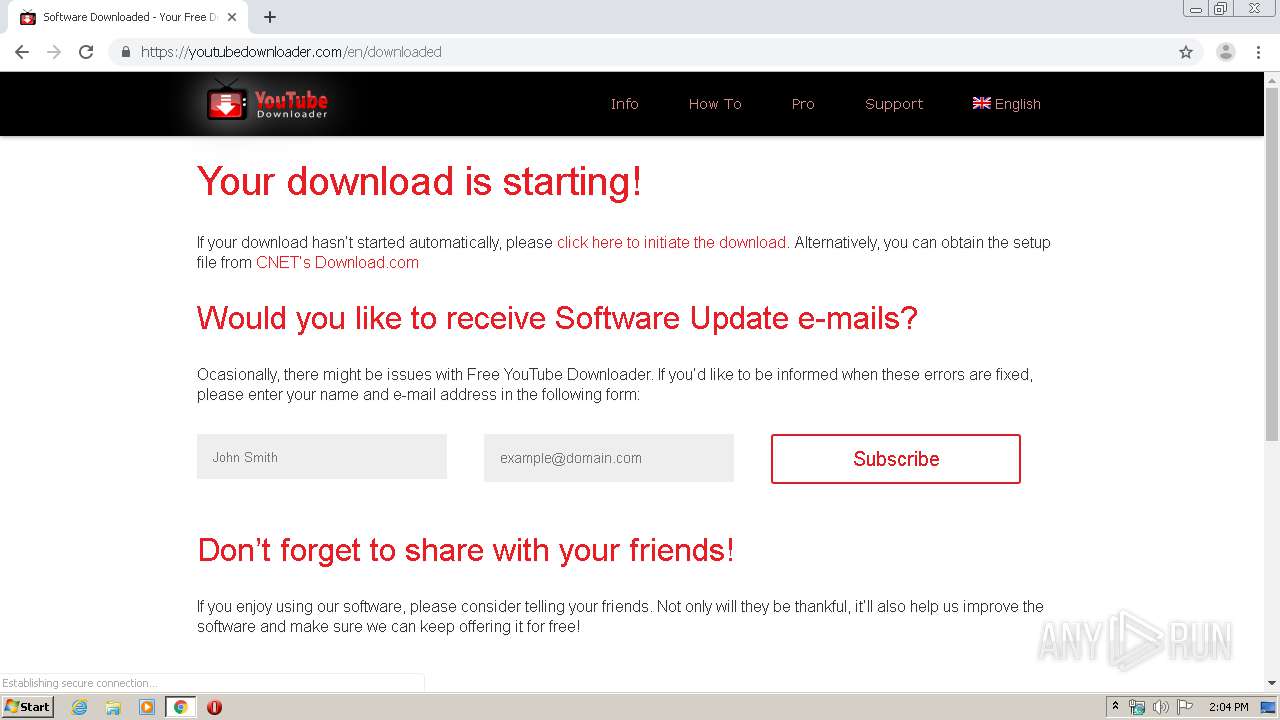
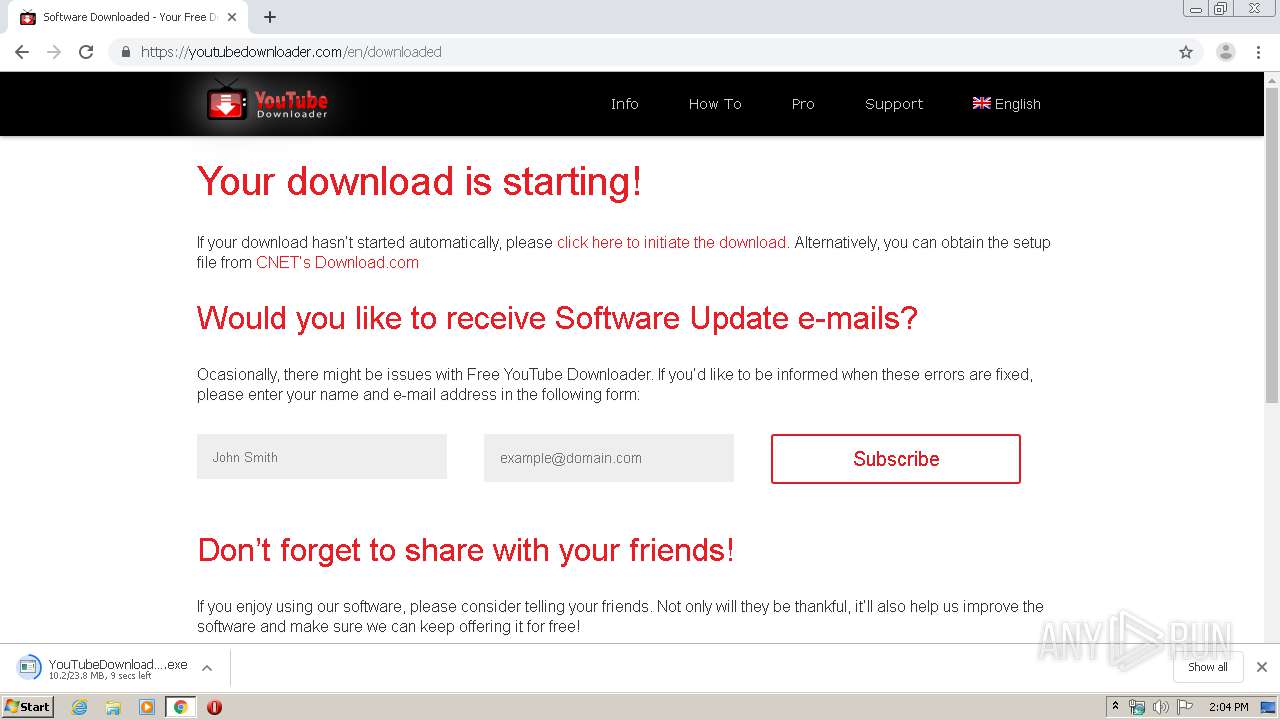
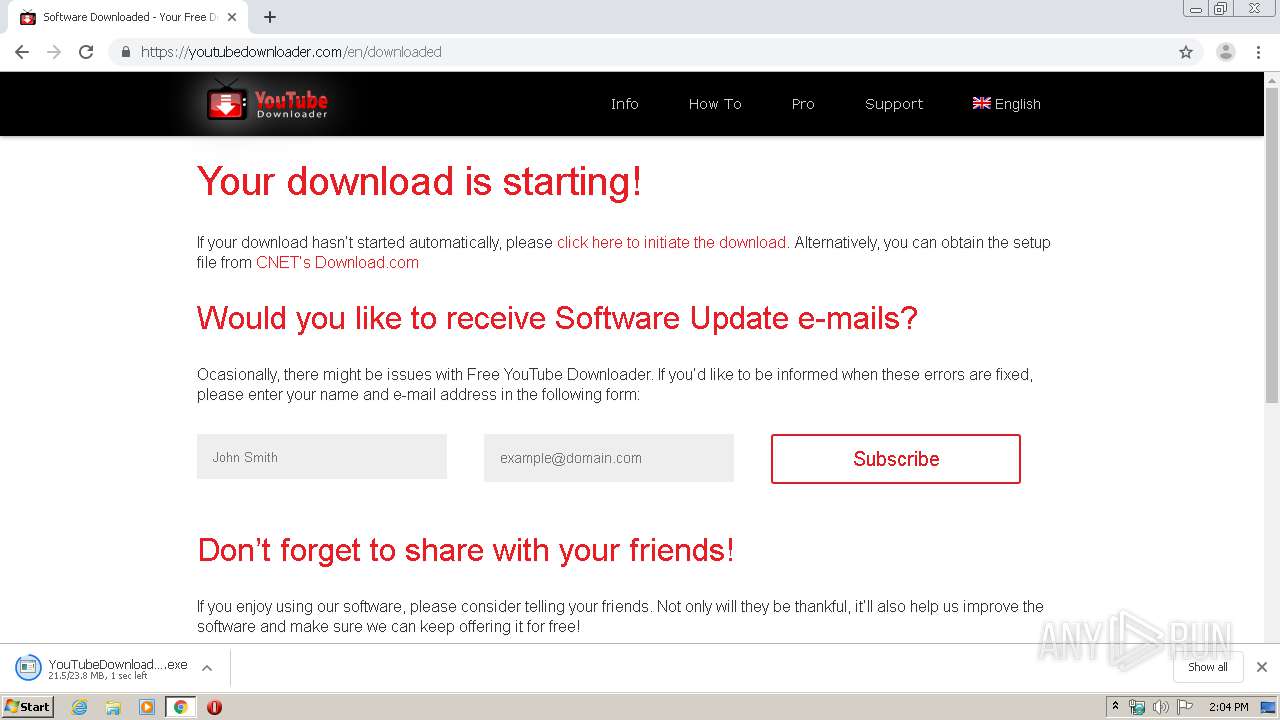
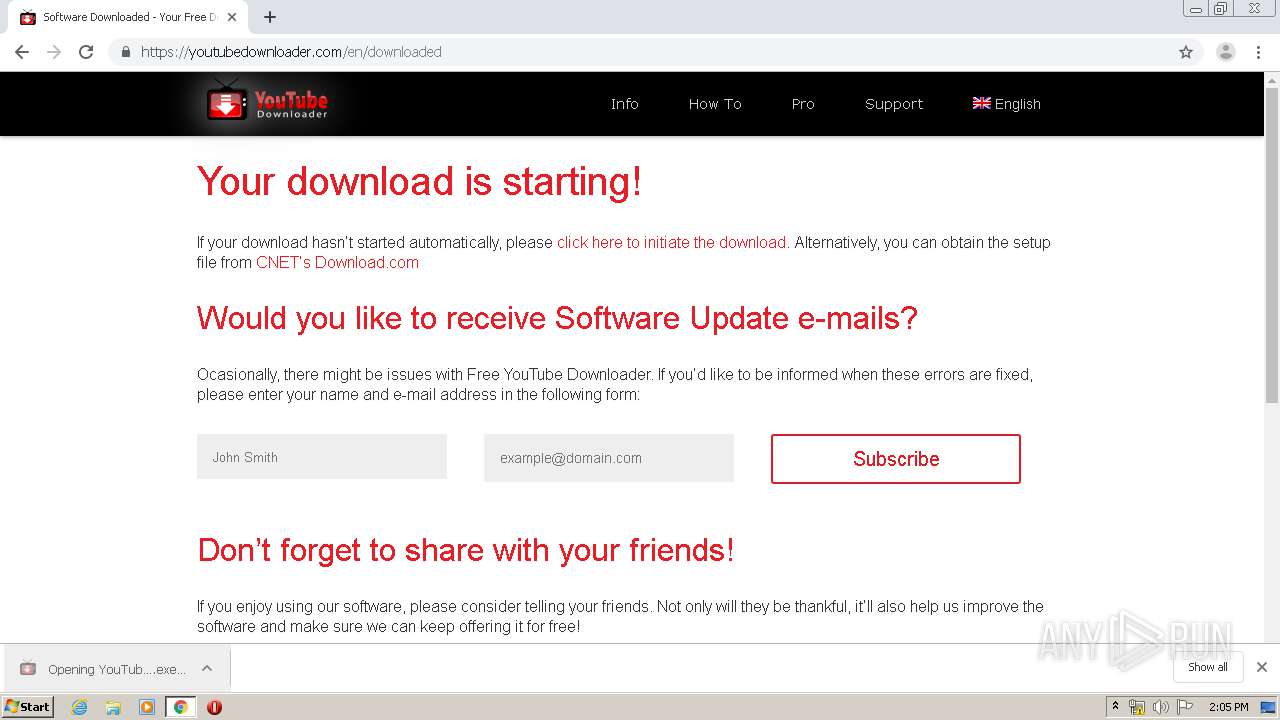
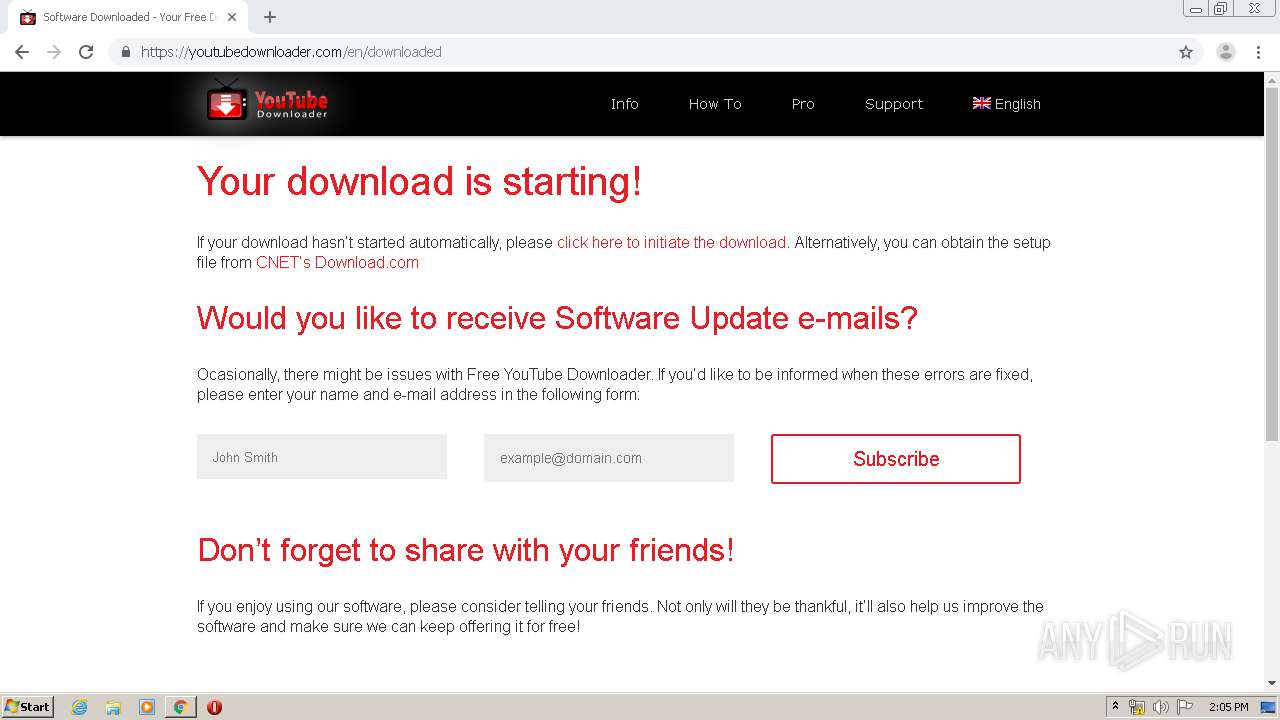
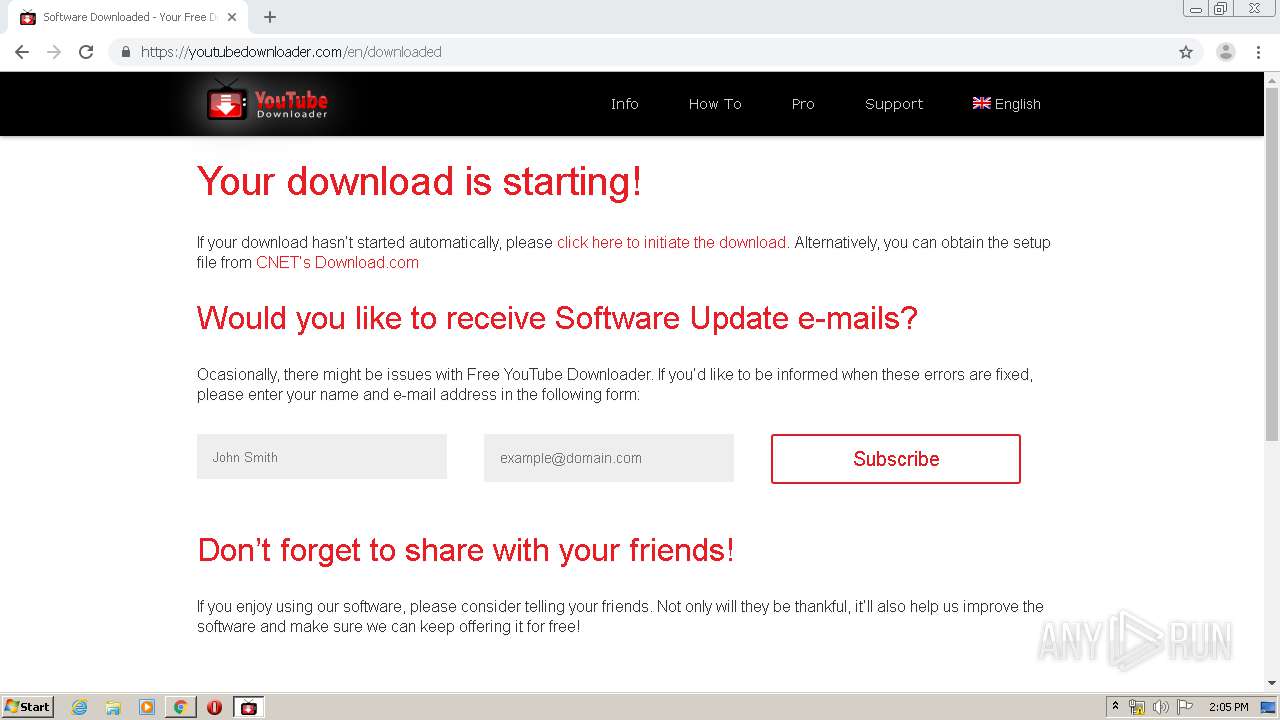
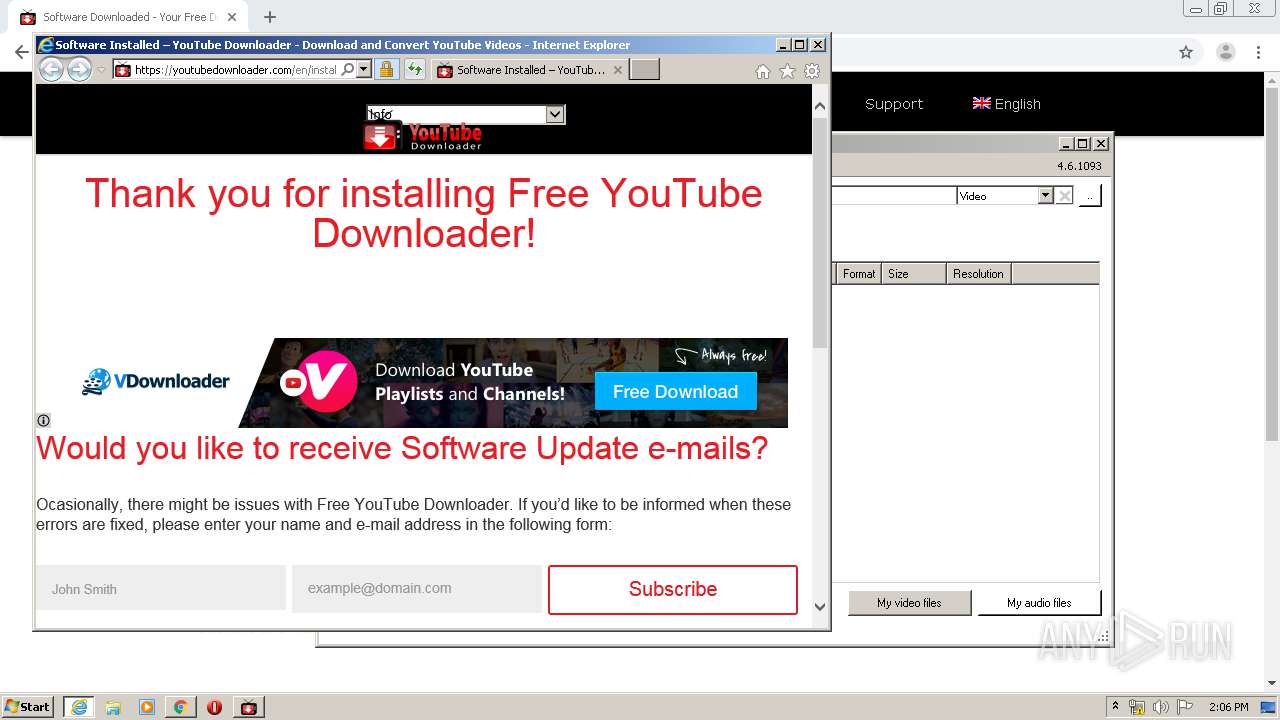
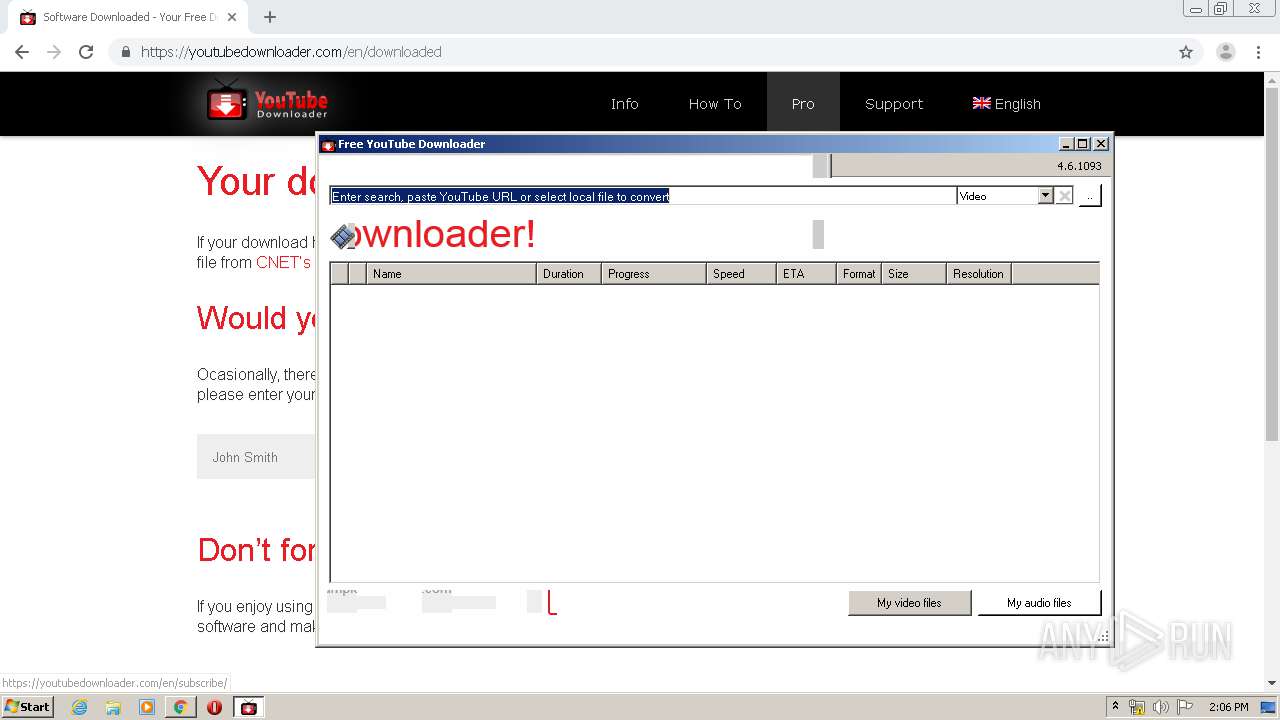
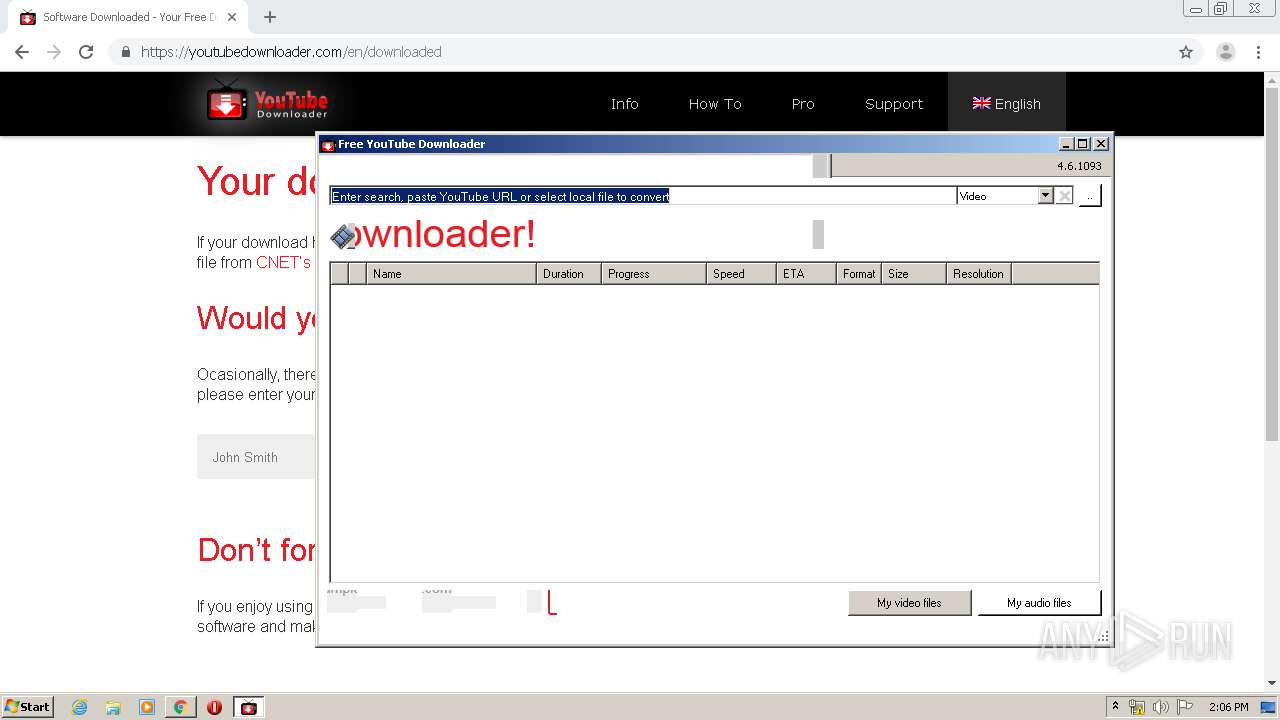
| URL: | https://youtubedownloader.com |
| Full analysis: | https://app.any.run/tasks/78baf230-a9bb-4d01-a6a0-c7a87ce4c981 |
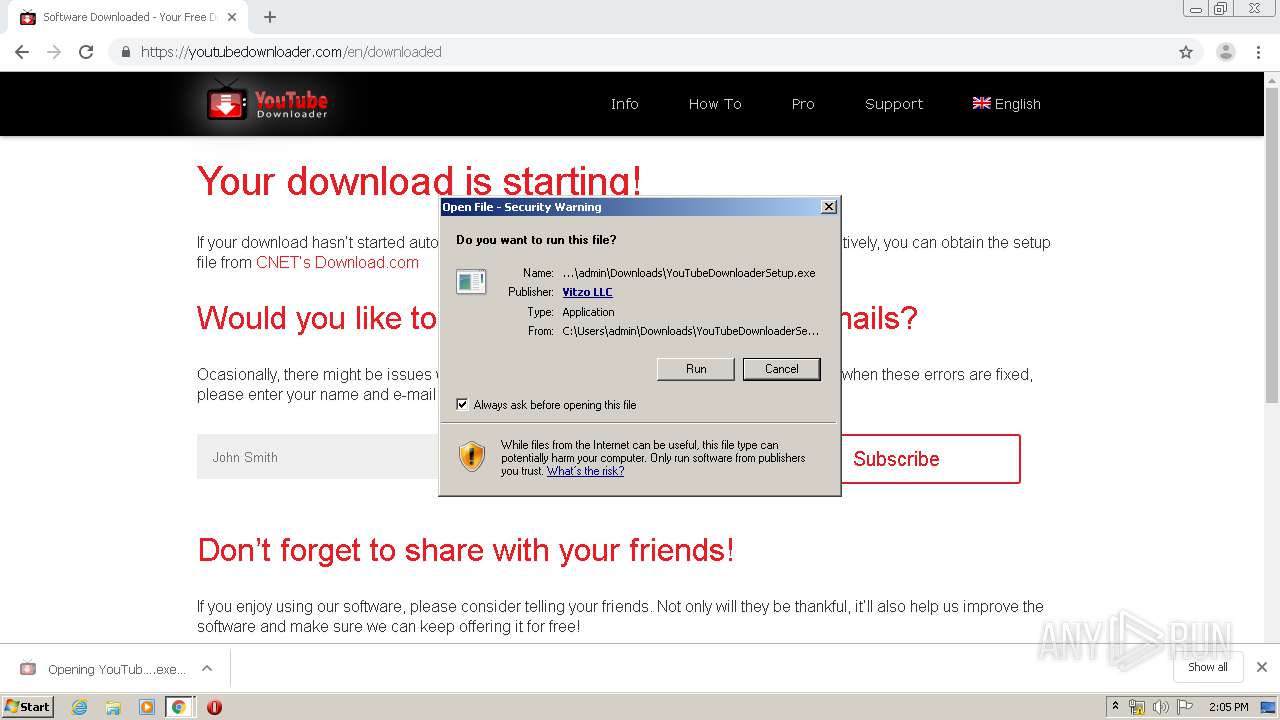
| Verdict: | Malicious activity |
| Analysis date: | March 11, 2020, 14:03:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3D3B84D068B6FBA36AD1E3A6AFE481C7 |
| SHA1: | 50DED02DACD5564D1294D9EAA5A70944FBA3FACD |
| SHA256: | 59C92F1D9E02EC7A52FCA14ECD02F05BA8E10E7C53E9435B27FFBDF613EDFA55 |
| SSDEEP: | 3:N8ugkJodXyKI:2ugklT |
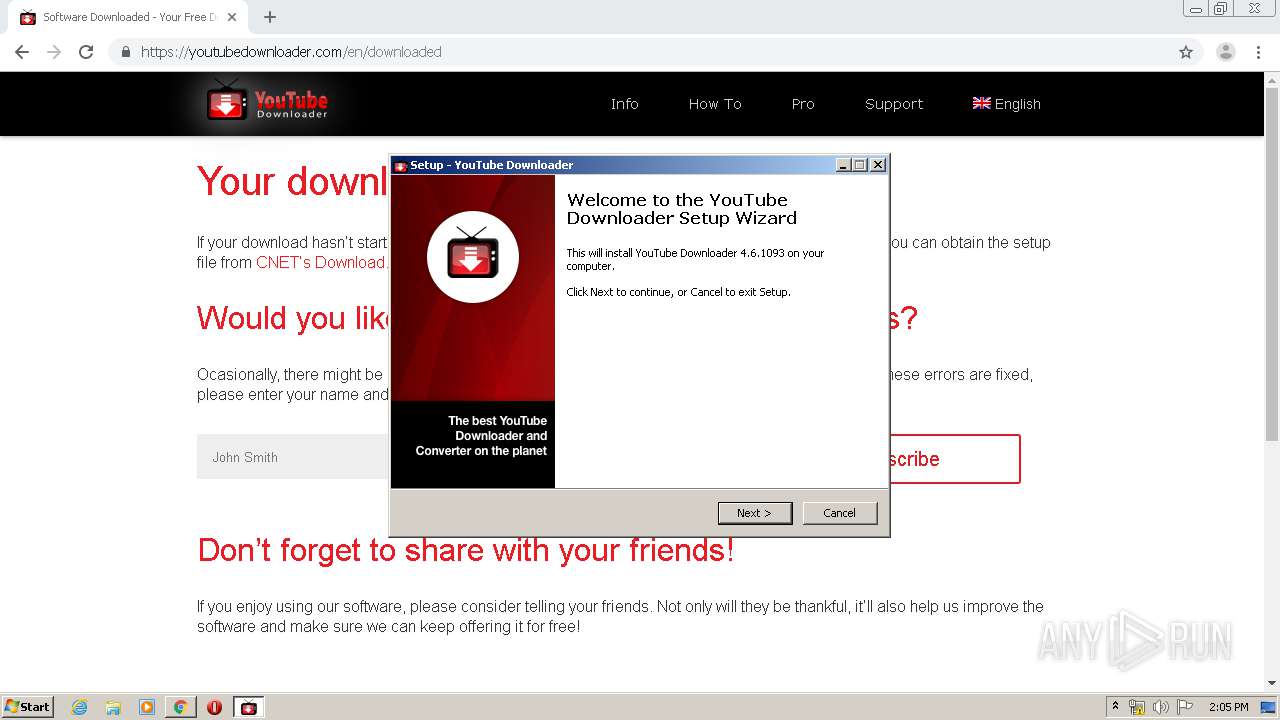
MALICIOUS
Application was dropped or rewritten from another process
- YouTubeDownloaderSetup.exe (PID: 3956)
- YouTubeDownloaderSetup.exe (PID: 3792)
- YouTubeDownloader.exe (PID: 2960)
- YouTubeDownloader.exe (PID: 3708)
Loads dropped or rewritten executable
- YouTubeDownloader.exe (PID: 3708)
- YouTubeDownloader.exe (PID: 2960)
Changes the autorun value in the registry
- YouTubeDownloader.exe (PID: 3708)
SUSPICIOUS
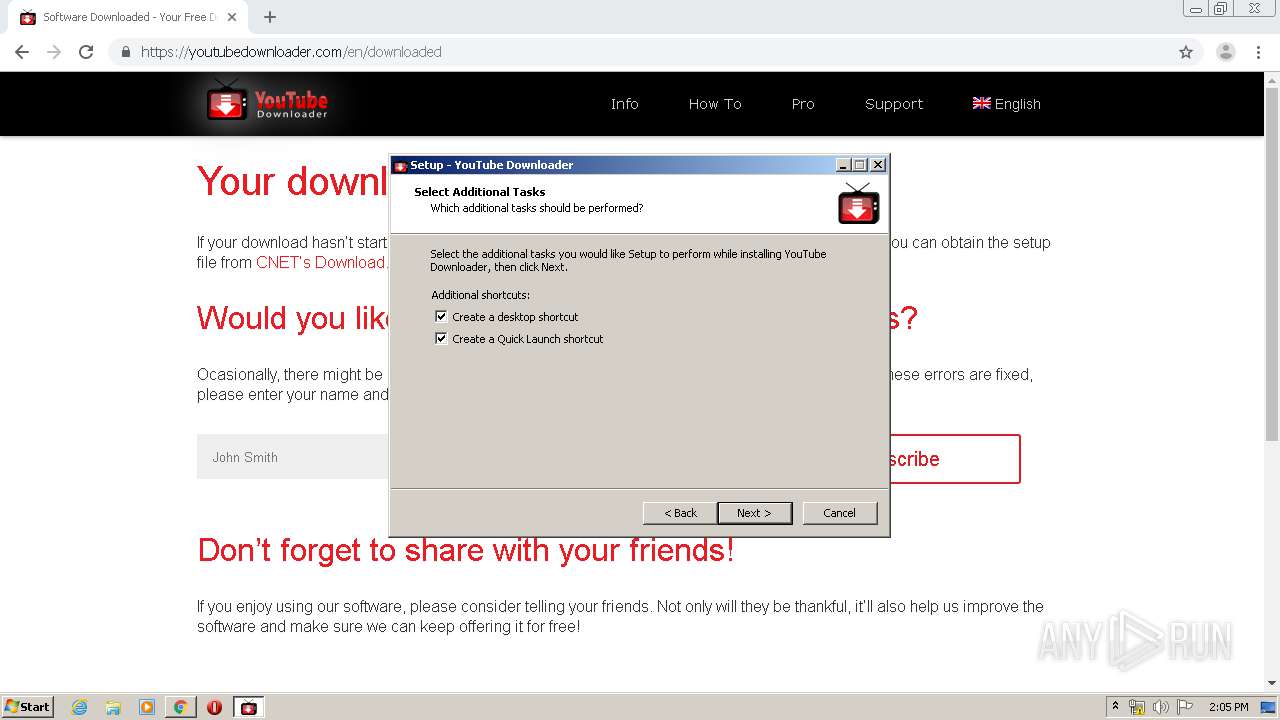
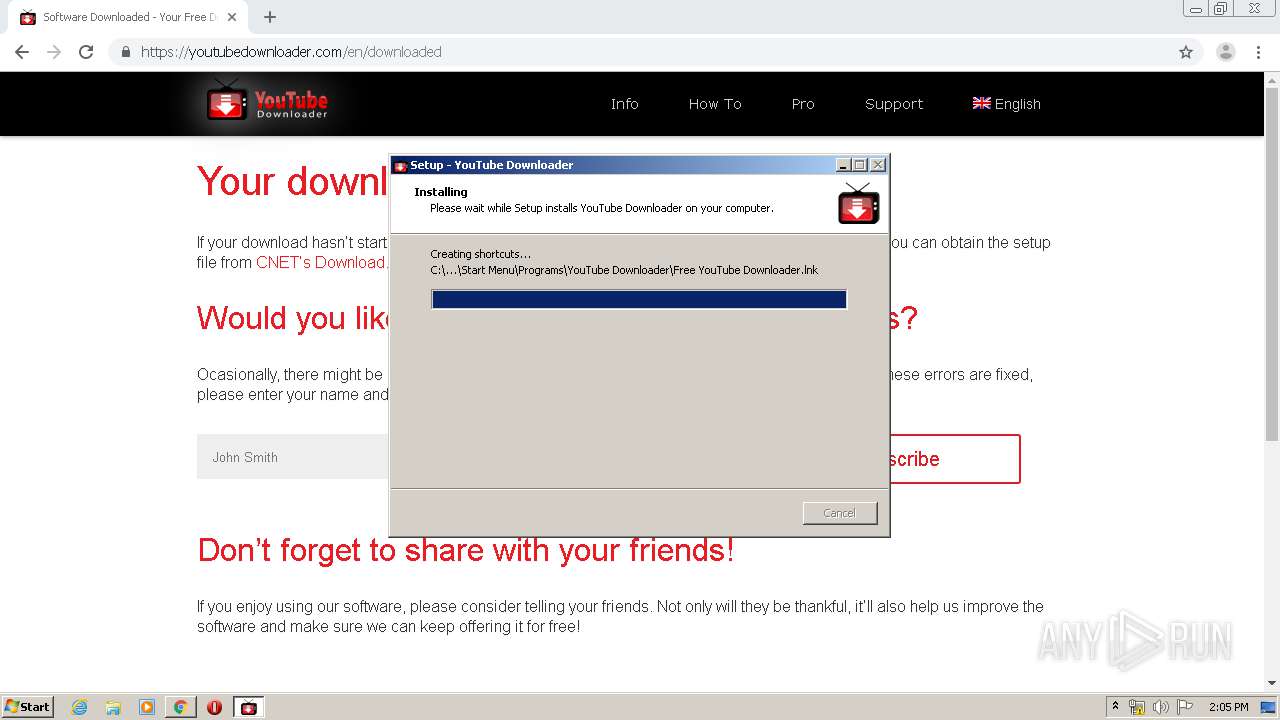
Executable content was dropped or overwritten
- chrome.exe (PID: 3800)
- YouTubeDownloaderSetup.exe (PID: 3792)
- YouTubeDownloaderSetup.exe (PID: 3956)
- chrome.exe (PID: 3928)
- YouTubeDownloaderSetup.tmp (PID: 1200)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3928)
Reads the Windows organization settings
- YouTubeDownloaderSetup.tmp (PID: 1200)
Reads Windows owner or organization settings
- YouTubeDownloaderSetup.tmp (PID: 1200)
Reads the machine GUID from the registry
- YouTubeDownloaderSetup.tmp (PID: 1200)
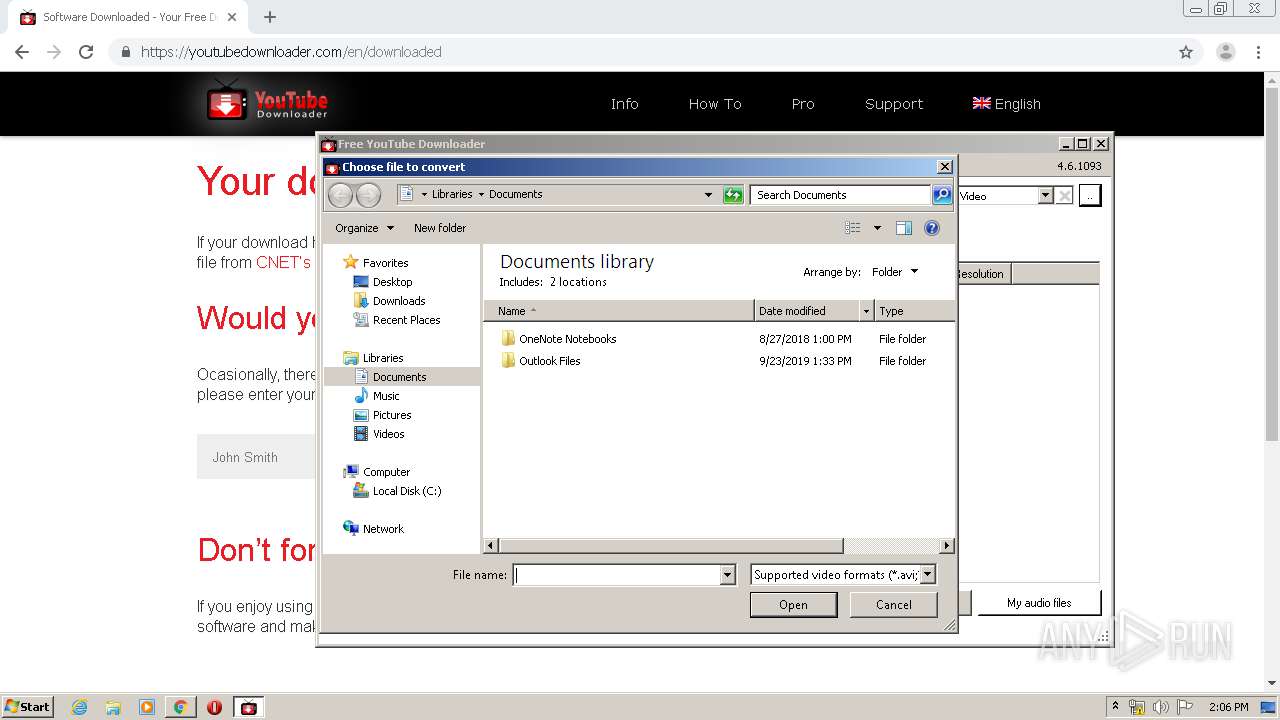
Creates files in the user directory
- YouTubeDownloaderSetup.tmp (PID: 1200)
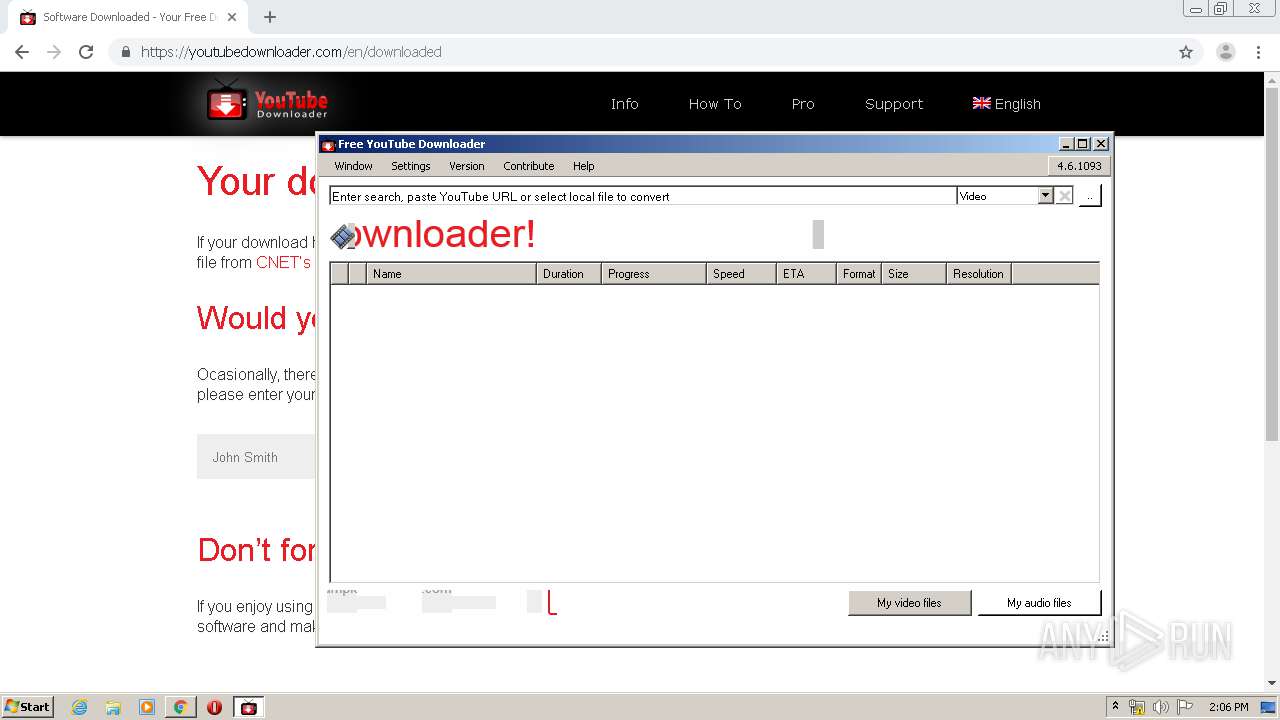
Starts CMD.EXE for commands execution
- YouTubeDownloader.exe (PID: 2960)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 2580)
- cmd.exe (PID: 3060)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 3060)
Reads Environment values
- YouTubeDownloader.exe (PID: 2960)
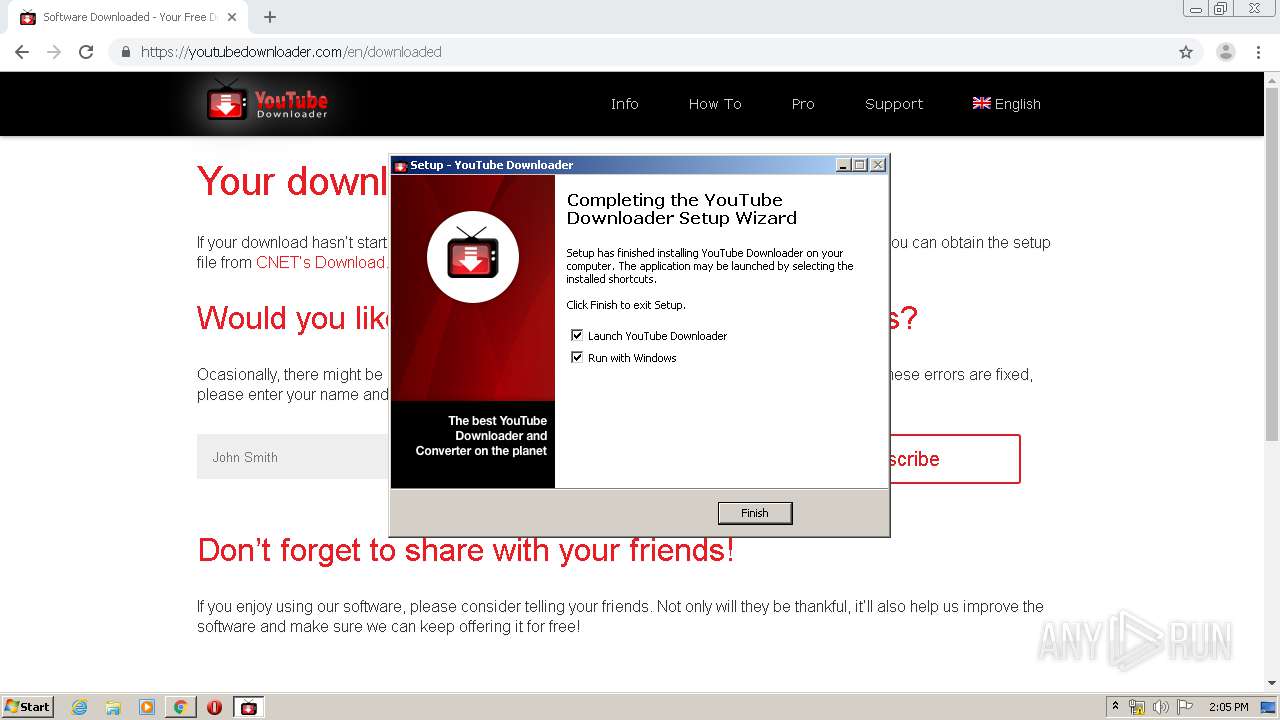
Starts Internet Explorer
- YouTubeDownloaderSetup.tmp (PID: 1200)
Changes IE settings (feature browser emulation)
- YouTubeDownloader.exe (PID: 2960)
INFO
Reads the hosts file
- chrome.exe (PID: 3800)
- chrome.exe (PID: 3928)
Application launched itself
- chrome.exe (PID: 3928)
- iexplore.exe (PID: 3328)
Application was dropped or rewritten from another process
- YouTubeDownloaderSetup.tmp (PID: 2632)
- YouTubeDownloaderSetup.tmp (PID: 1200)
Reads settings of System Certificates
- chrome.exe (PID: 3928)
- iexplore.exe (PID: 3872)
- YouTubeDownloader.exe (PID: 2960)
- iexplore.exe (PID: 3328)
Loads dropped or rewritten executable
- YouTubeDownloaderSetup.tmp (PID: 1200)
Reads Internet Cache Settings
- chrome.exe (PID: 3928)
- iexplore.exe (PID: 3328)
- iexplore.exe (PID: 3872)
Creates files in the program directory
- YouTubeDownloaderSetup.tmp (PID: 1200)
Creates a software uninstall entry
- YouTubeDownloaderSetup.tmp (PID: 1200)
Changes internet zones settings
- iexplore.exe (PID: 3328)
Creates files in the user directory
- iexplore.exe (PID: 3872)
Reads internet explorer settings
- iexplore.exe (PID: 3872)
Dropped object may contain TOR URL's
- iexplore.exe (PID: 3872)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3872)
Changes settings of System certificates
- iexplore.exe (PID: 3872)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
83
Monitored processes
39
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,1942456661840776702,8477033987089859399,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14649775905027370734 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3288 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1200 | "C:\Users\admin\AppData\Local\Temp\is-18OCO.tmp\YouTubeDownloaderSetup.tmp" /SL5="$801D6,24464020,236544,C:\Users\admin\Downloads\YouTubeDownloaderSetup.exe" /SPAWNWND=$501C0 /NOTIFYWND=$9020E | C:\Users\admin\AppData\Local\Temp\is-18OCO.tmp\YouTubeDownloaderSetup.tmp | YouTubeDownloaderSetup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,1942456661840776702,8477033987089859399,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1628933700422666845 --mojo-platform-channel-handle=3840 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,1942456661840776702,8477033987089859399,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1828944324278136730 --mojo-platform-channel-handle=4292 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,1942456661840776702,8477033987089859399,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9716103545944424871 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2240 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2192 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,1942456661840776702,8477033987089859399,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9996561198181292716 --mojo-platform-channel-handle=3884 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa8a9d0,0x6fa8a9e0,0x6fa8a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,1942456661840776702,8477033987089859399,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12615766244567465079 --mojo-platform-channel-handle=3628 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,1942456661840776702,8477033987089859399,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16615353356586558689 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2268 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,1942456661840776702,8477033987089859399,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11601158799325982214 --mojo-platform-channel-handle=4224 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
4 388
Read events
2 941
Write events
1 430
Delete events
17
Modification events
| (PID) Process: | (2636) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3928-13228409042242125 |
Value: 259 | |||
| (PID) Process: | (3928) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3928) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3928) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3928) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3928) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3928) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3928) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3928) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3928) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3928-13228409042242125 |
Value: 259 | |||
Executable files
61
Suspicious files
104
Text files
307
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E68EFD2-F58.pma | — | |
MD5:— | SHA256:— | |||
| 3928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7ffe207a-afd8-4bd4-a59e-f059c682df94.tmp | — | |
MD5:— | SHA256:— | |||
| 3928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa66c01.TMP | text | |
MD5:— | SHA256:— | |||
| 3928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa66bf1.TMP | text | |
MD5:— | SHA256:— | |||
| 3928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66dc6.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
89
DNS requests
51
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3872 | iexplore.exe | GET | 200 | 216.58.208.35:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3872 | iexplore.exe | GET | 200 | 216.58.208.35:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCgdZM8AVzzKAgAAAAALnDU | US | der | 472 b | whitelisted |
— | — | GET | 200 | 143.204.208.79:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEA4dFDwKA4HemjfpvkOaFnY%3D | US | der | 471 b | whitelisted |
3872 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.trust-provider.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEENSAj%2F6qJAfE5%2Fj9OXBRE4%3D | US | der | 471 b | whitelisted |
3872 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.trust-provider.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEENSAj%2F6qJAfE5%2Fj9OXBRE4%3D | US | der | 471 b | whitelisted |
3800 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
3872 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
3872 | iexplore.exe | GET | 200 | 216.58.208.35:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3872 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
3872 | iexplore.exe | GET | 200 | 216.58.208.35:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCv2pgtDmXnZAgAAAAALnDT | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3800 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
3800 | chrome.exe | 104.17.64.4:443 | ajax.cloudflare.com | Cloudflare Inc | US | unknown |
3800 | chrome.exe | 172.217.21.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3800 | chrome.exe | 104.26.3.190:443 | youtubedownloader.com | Cloudflare Inc | US | unknown |
3800 | chrome.exe | 35.190.12.249:443 | fresnel.vimeocdn.com | Google Inc. | US | unknown |
3800 | chrome.exe | 151.101.0.217:443 | player.vimeo.com | Fastly | US | suspicious |
3800 | chrome.exe | 104.17.65.4:443 | ajax.cloudflare.com | Cloudflare Inc | US | unknown |
3800 | chrome.exe | 151.101.114.109:443 | i.vimeocdn.com | Fastly | US | unknown |
3800 | chrome.exe | 172.217.18.174:443 | clients1.google.com | Google Inc. | US | whitelisted |
3800 | chrome.exe | 151.101.64.217:443 | player.vimeo.com | Fastly | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
youtubedownloader.com |
| unknown |
accounts.google.com |
| shared |
s.w.org |
| whitelisted |
player.vimeo.com |
| whitelisted |
ajax.cloudflare.com |
| whitelisted |
clients1.google.com |
| whitelisted |
fresnel.vimeocdn.com |
| whitelisted |
i.vimeocdn.com |
| whitelisted |
f.vimeocdn.com |
| shared |