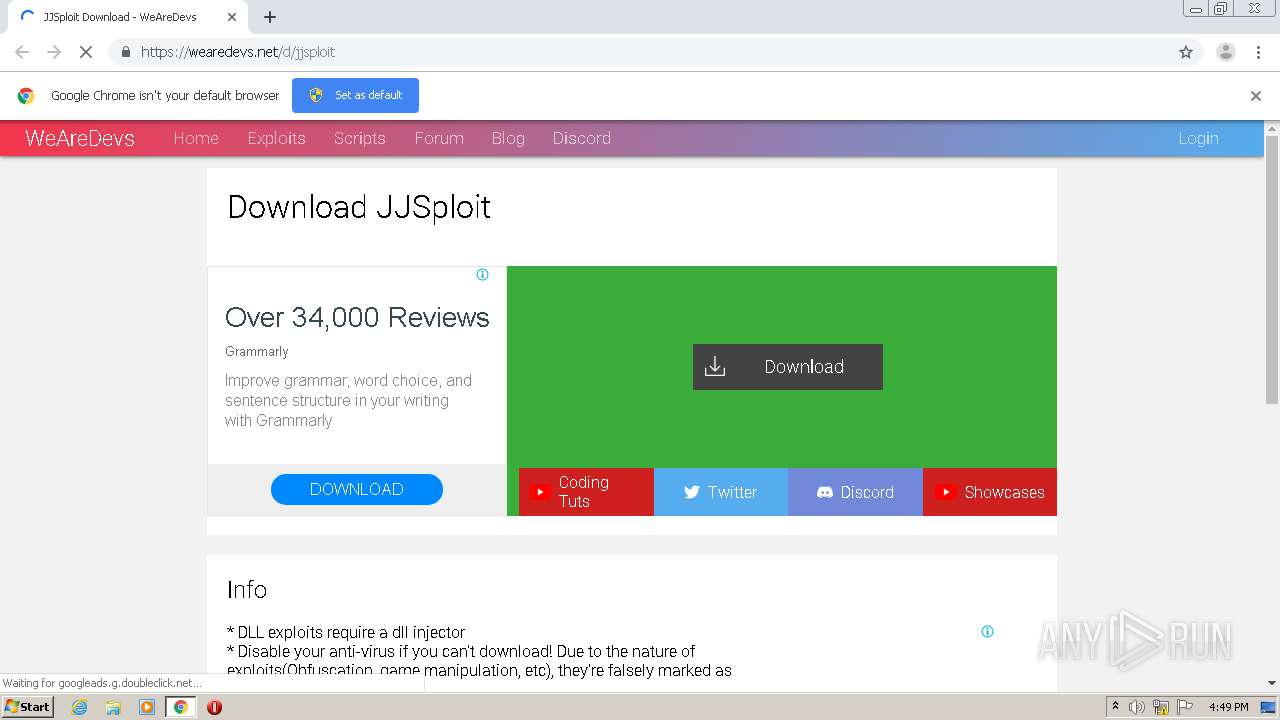
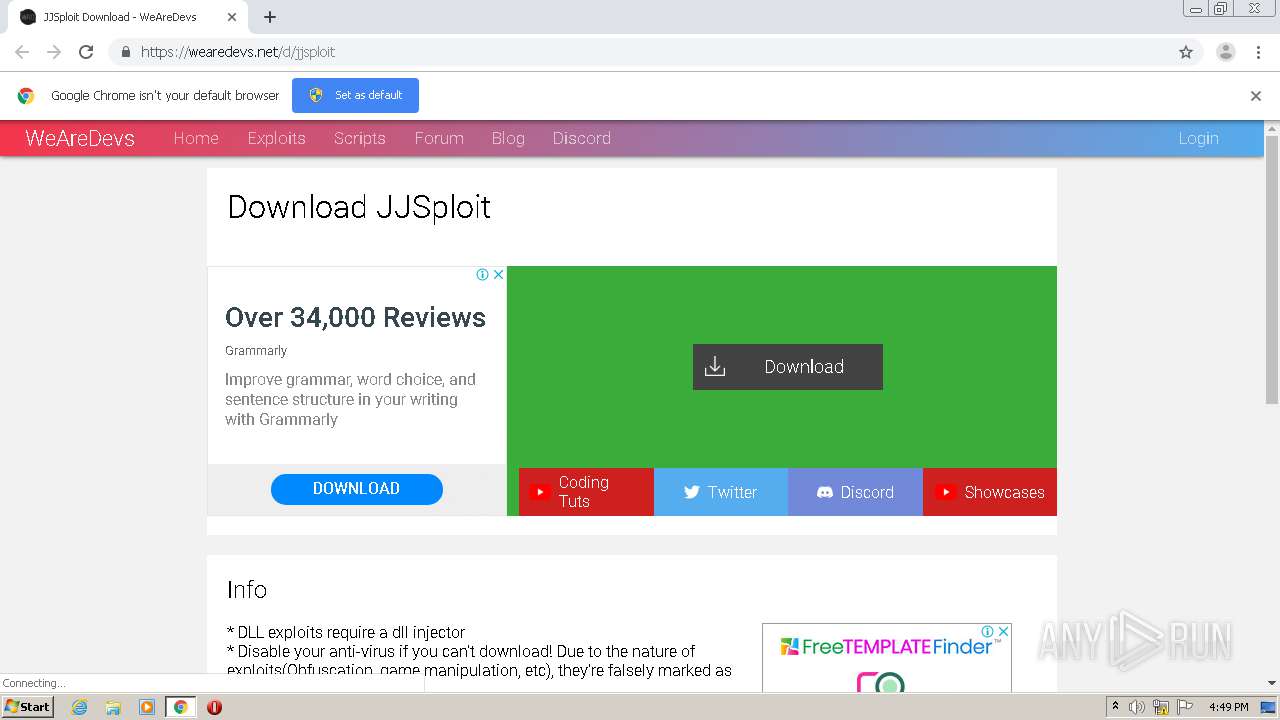
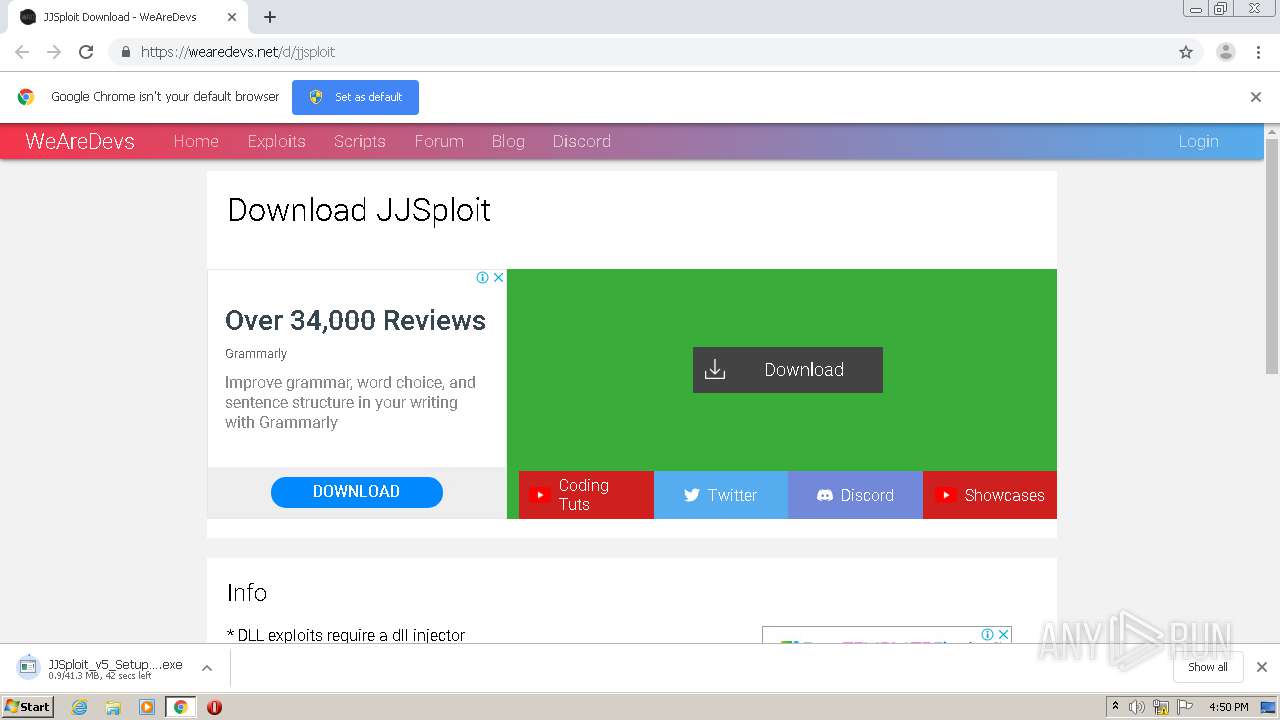
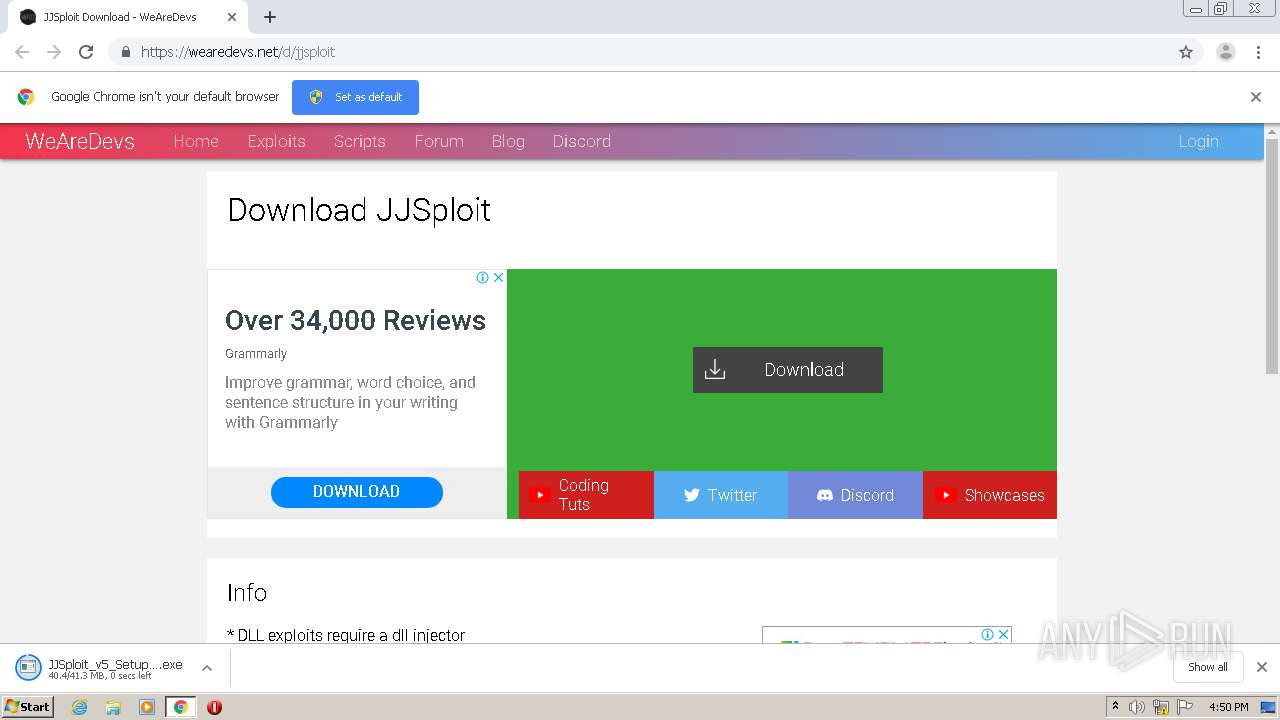
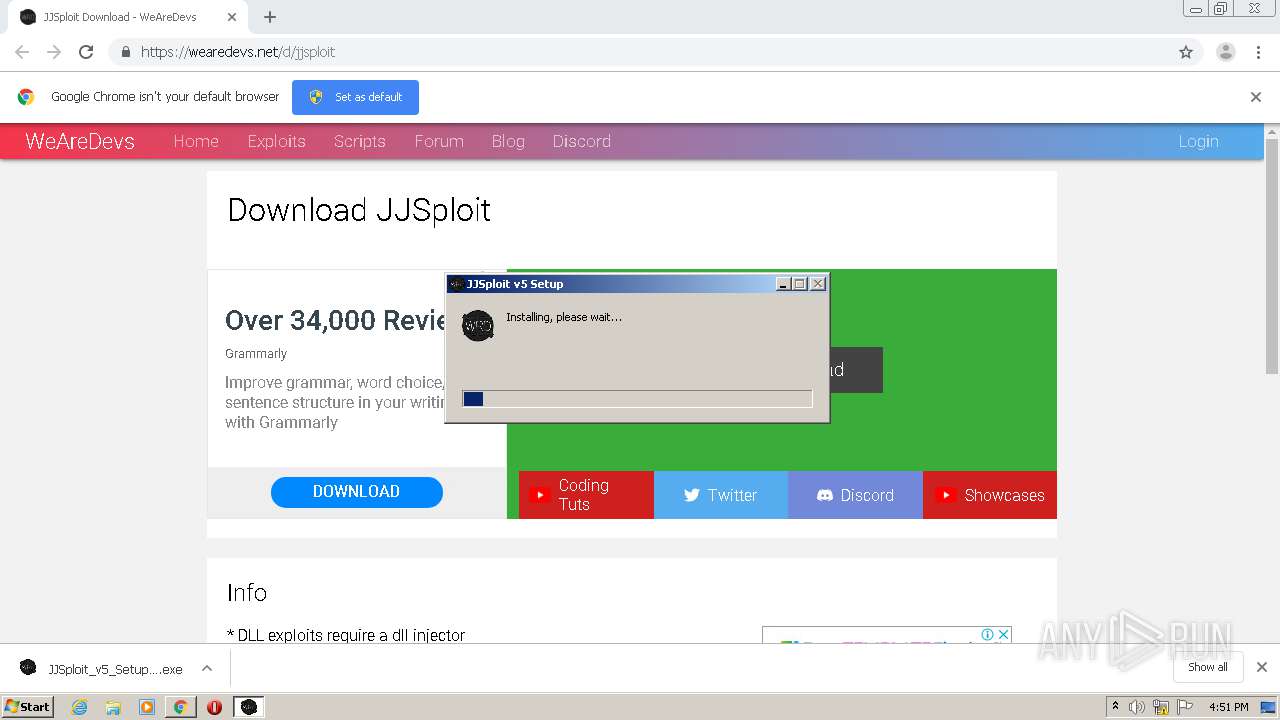
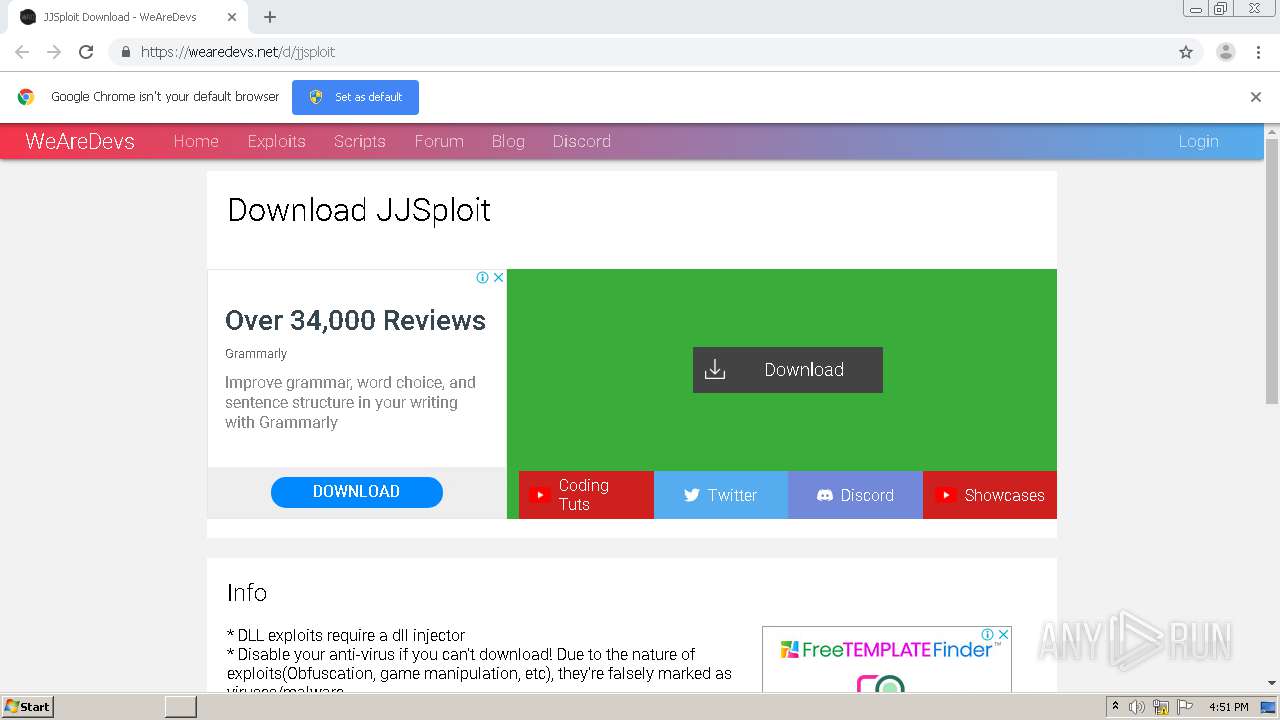
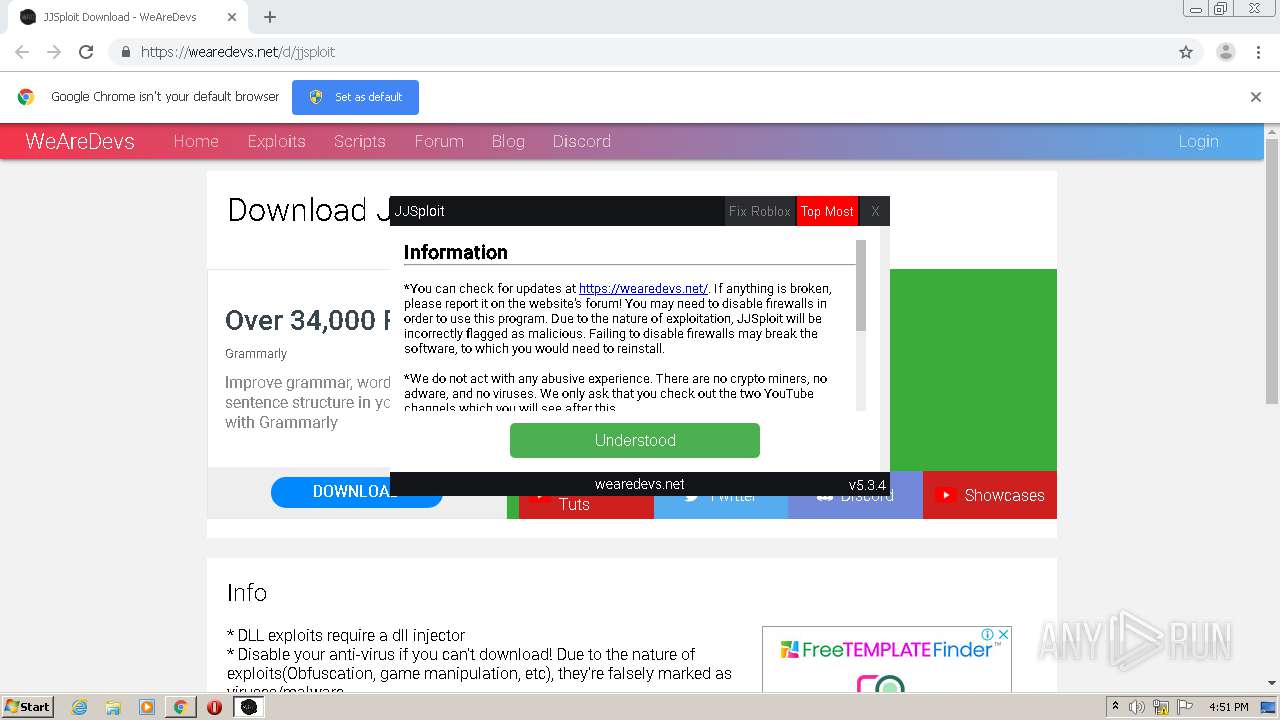
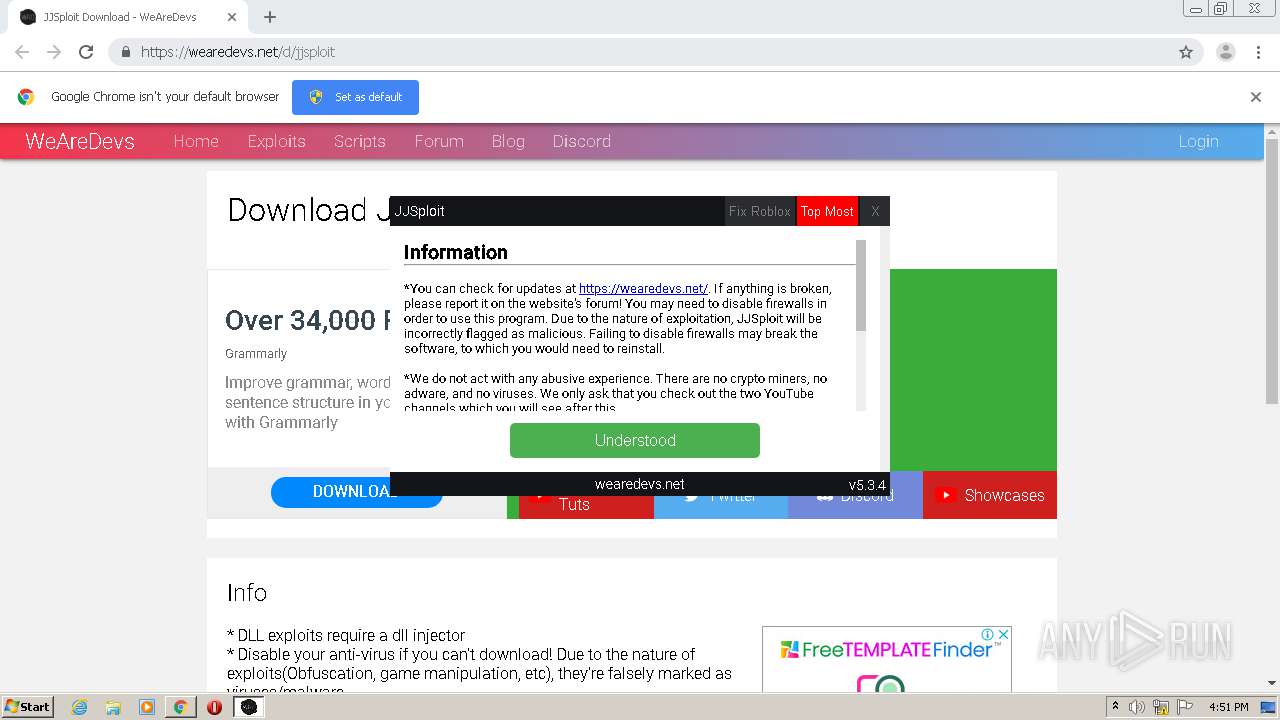
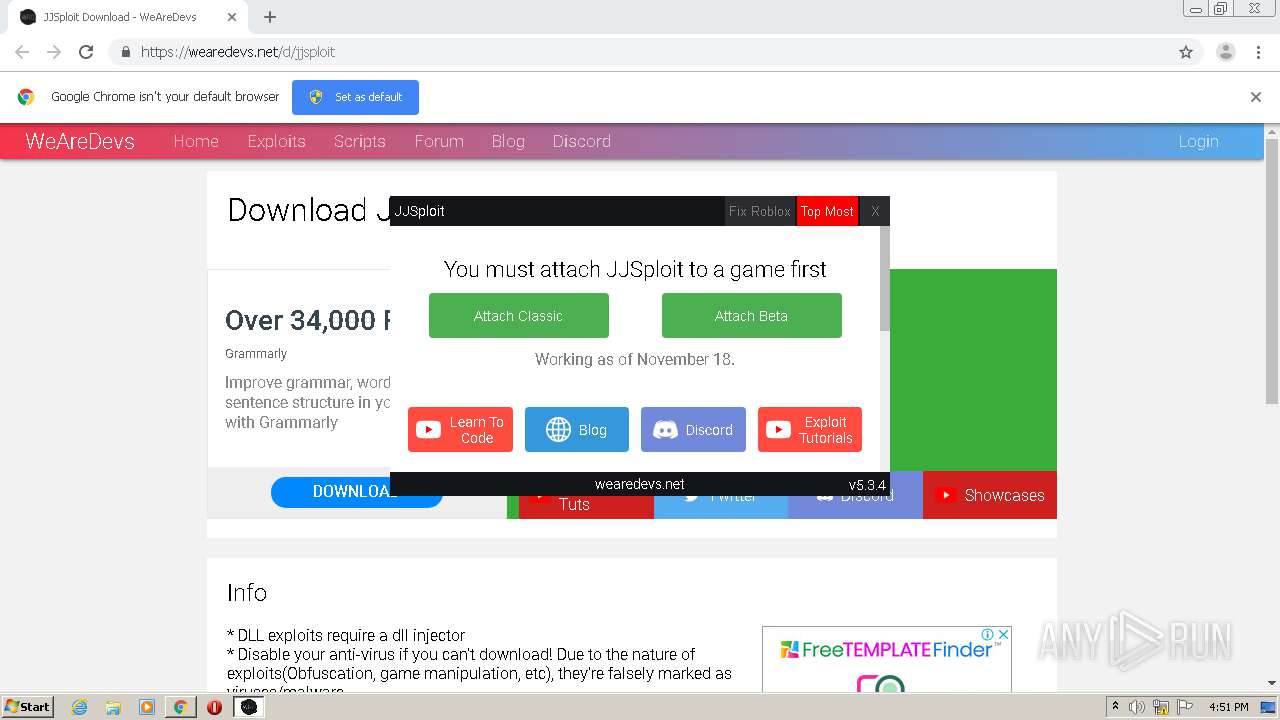
| URL: | https://wearedevs.net/d/jjsploit |
| Full analysis: | https://app.any.run/tasks/0594a802-40ab-4f1d-b557-71a123960598 |
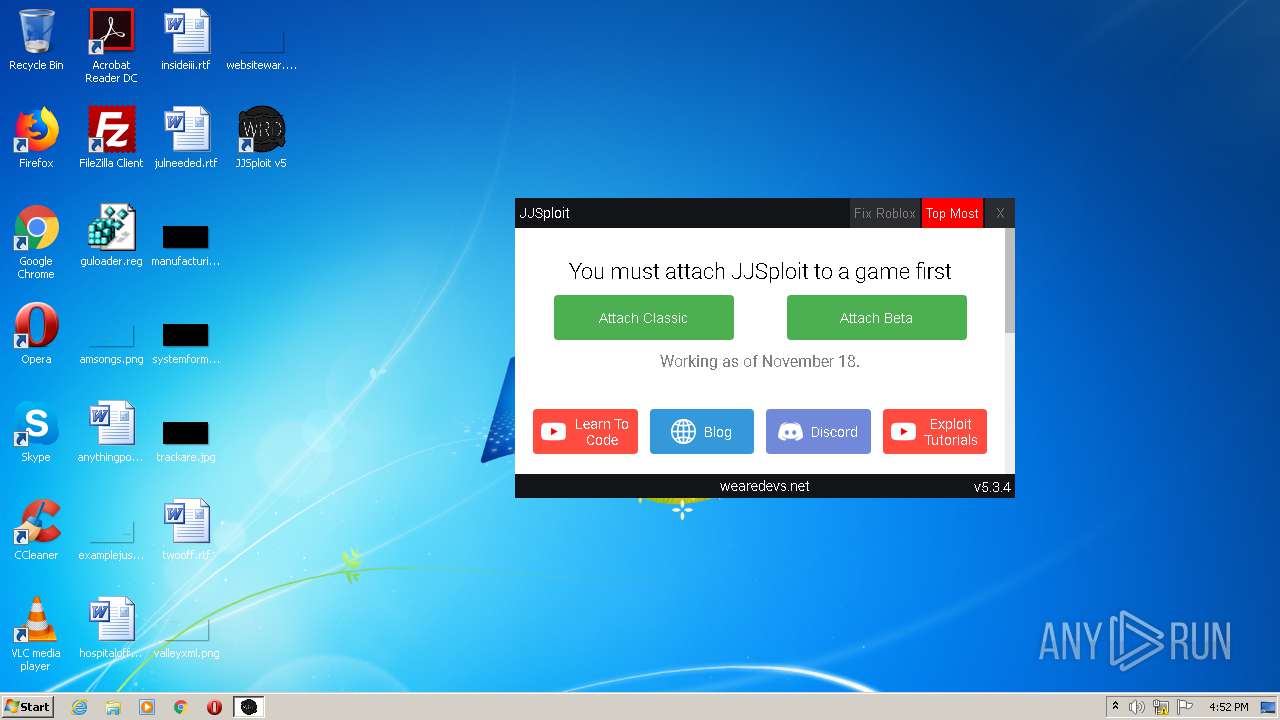
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2020, 16:49:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C3ED6403FEA9F2F9DC8E86C412CB3334 |
| SHA1: | A3CB61C057D39E1CC76B888C3CADAB5E275C065C |
| SHA256: | 59C4ED340EE1B0F9A7136E9680FF6DD4512E5EE4324112DB9BC744ADAF24A069 |
| SSDEEP: | 3:N8R/BApK8K:25BuBK |
MALICIOUS
Loads dropped or rewritten executable
- JJSploit_v5_Setup_5.3.4.exe (PID: 2928)
- JJSploit v5.exe (PID: 2672)
- JJSploit v5.exe (PID: 4072)
- JJSploit v5.exe (PID: 1068)
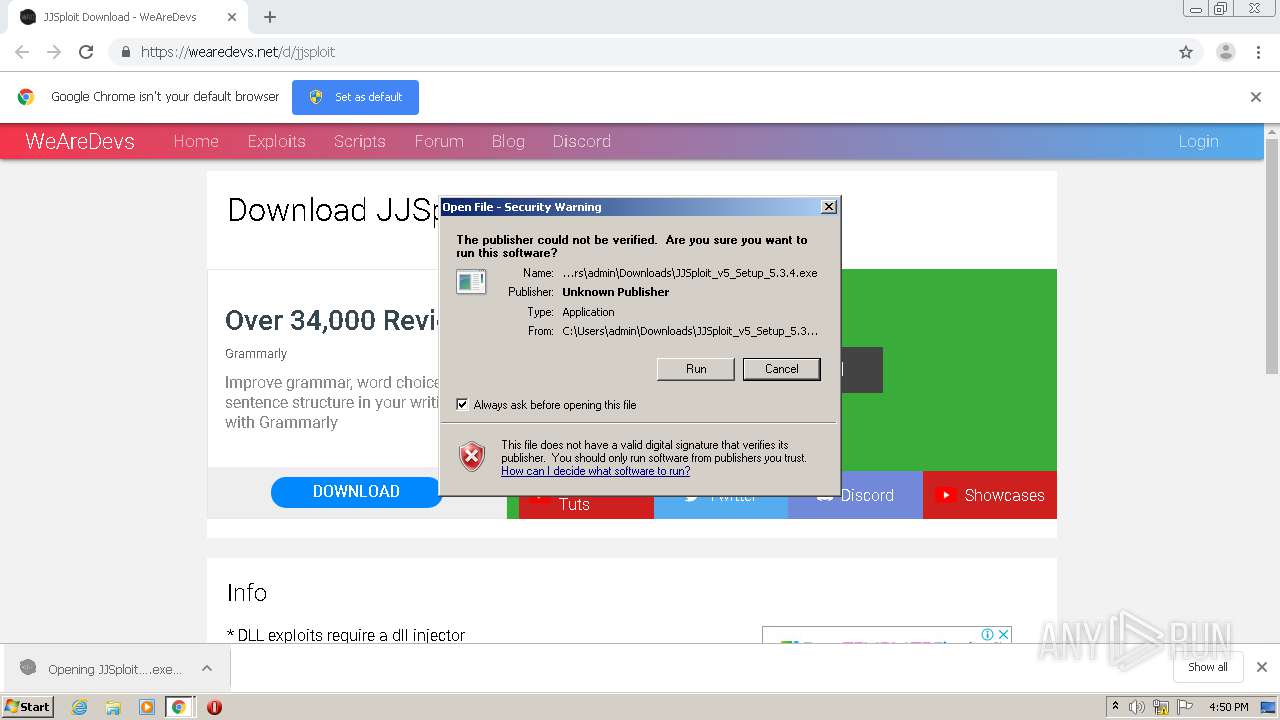
Application was dropped or rewritten from another process
- JJSploit_v5_Setup_5.3.4.exe (PID: 2928)
SUSPICIOUS
Executable content was dropped or overwritten
- JJSploit_v5_Setup_5.3.4.exe (PID: 2928)
- chrome.exe (PID: 2472)
- JJSploit v5.exe (PID: 2672)
Drops a file with too old compile date
- JJSploit_v5_Setup_5.3.4.exe (PID: 2928)
Drops a file that was compiled in debug mode
- JJSploit_v5_Setup_5.3.4.exe (PID: 2928)
- JJSploit v5.exe (PID: 2672)
Drops a file with a compile date too recent
- chrome.exe (PID: 2472)
- JJSploit v5.exe (PID: 2672)
Creates a software uninstall entry
- JJSploit_v5_Setup_5.3.4.exe (PID: 2928)
Creates files in the user directory
- JJSploit_v5_Setup_5.3.4.exe (PID: 2928)
- JJSploit v5.exe (PID: 2672)
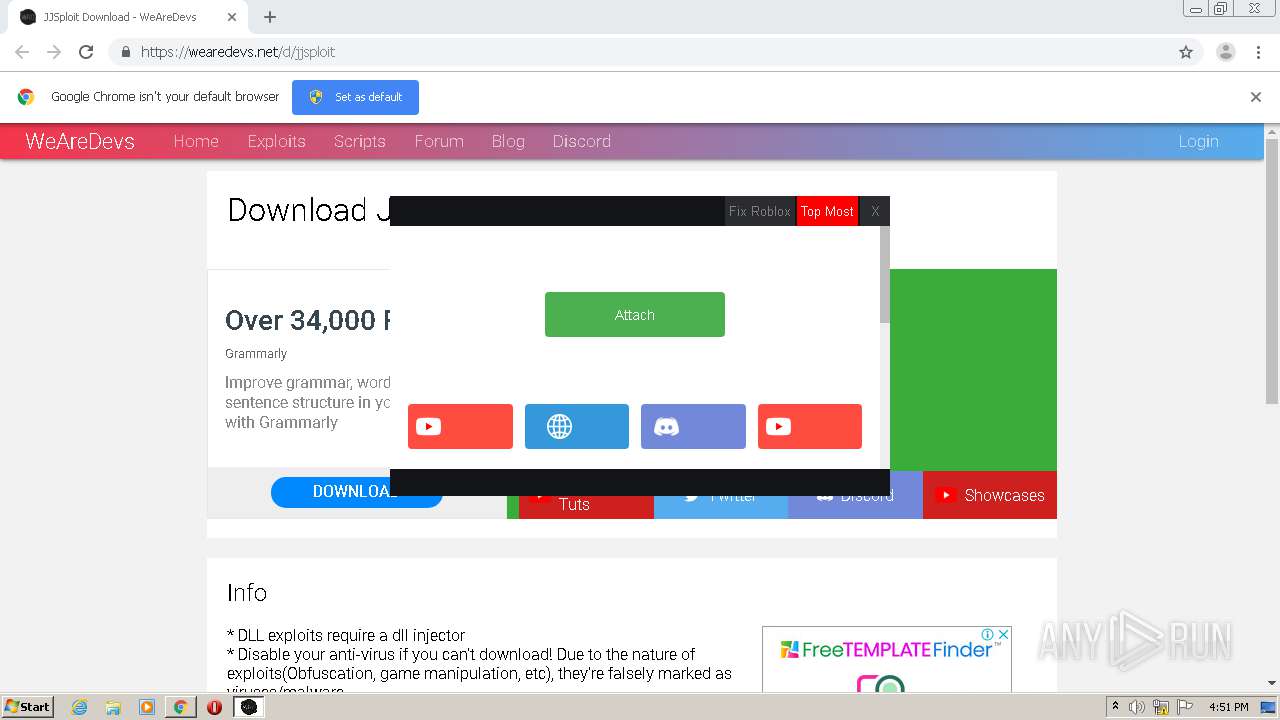
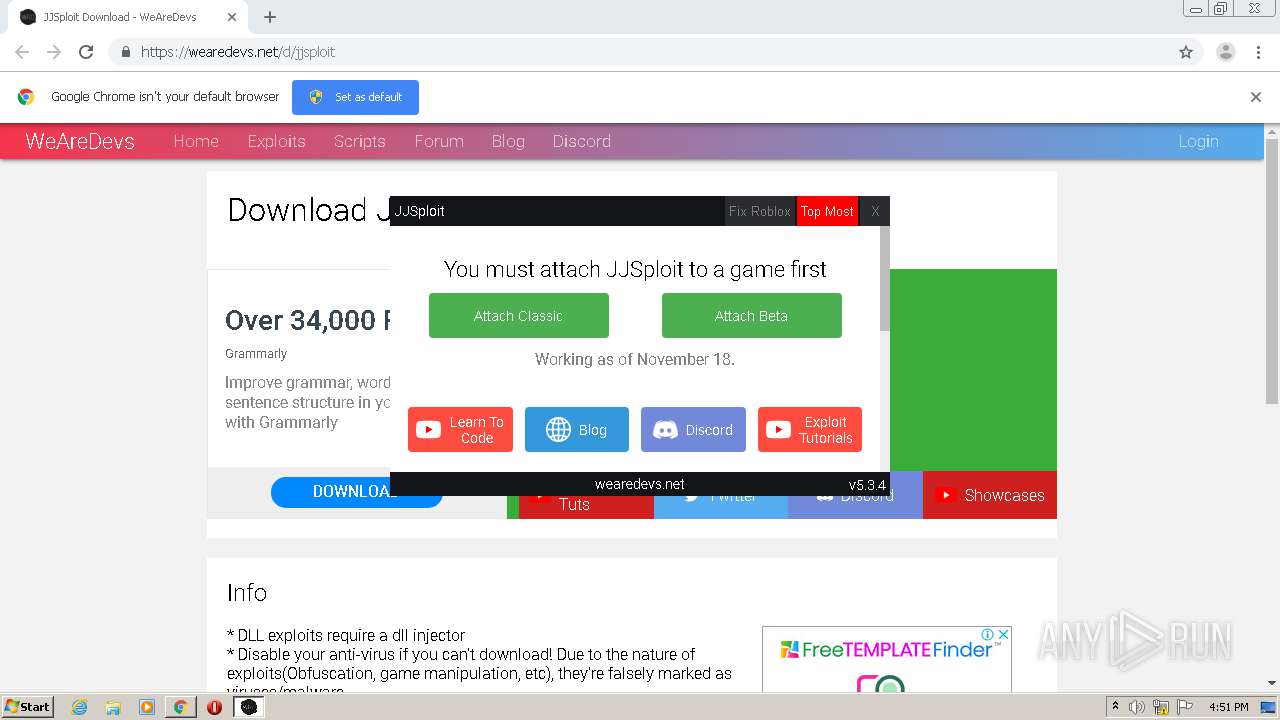
Application launched itself
- JJSploit v5.exe (PID: 2672)
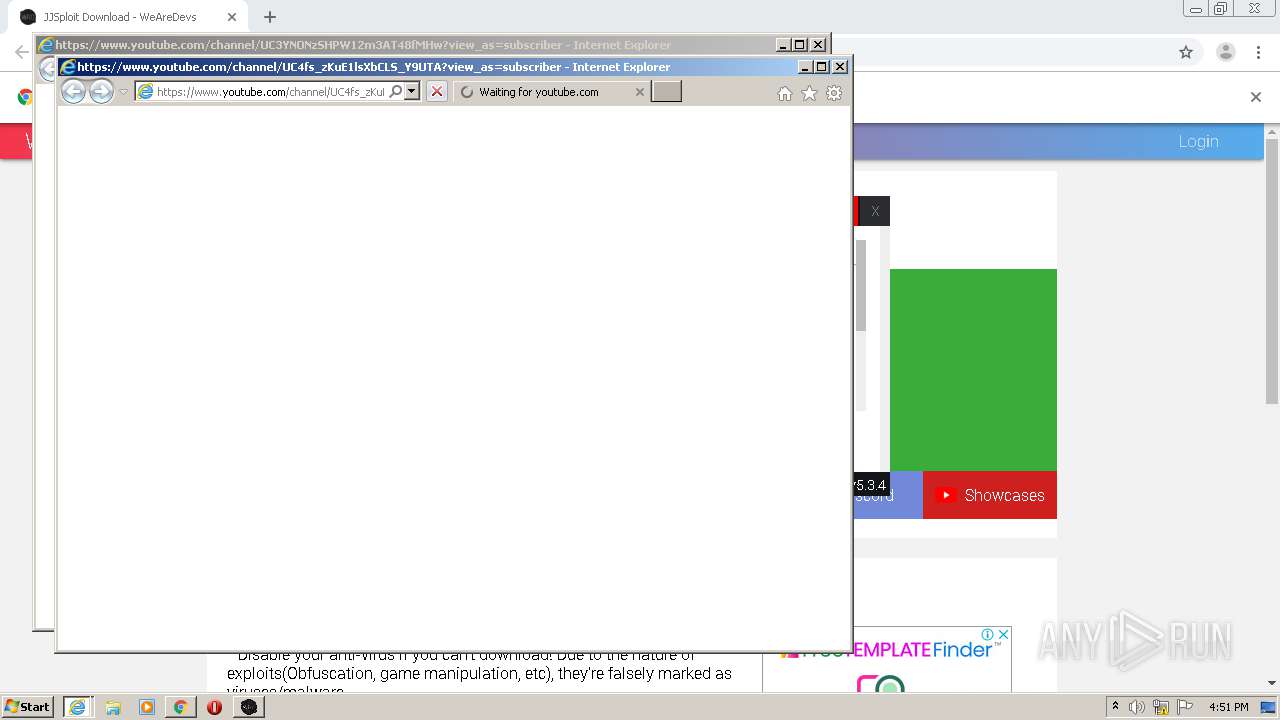
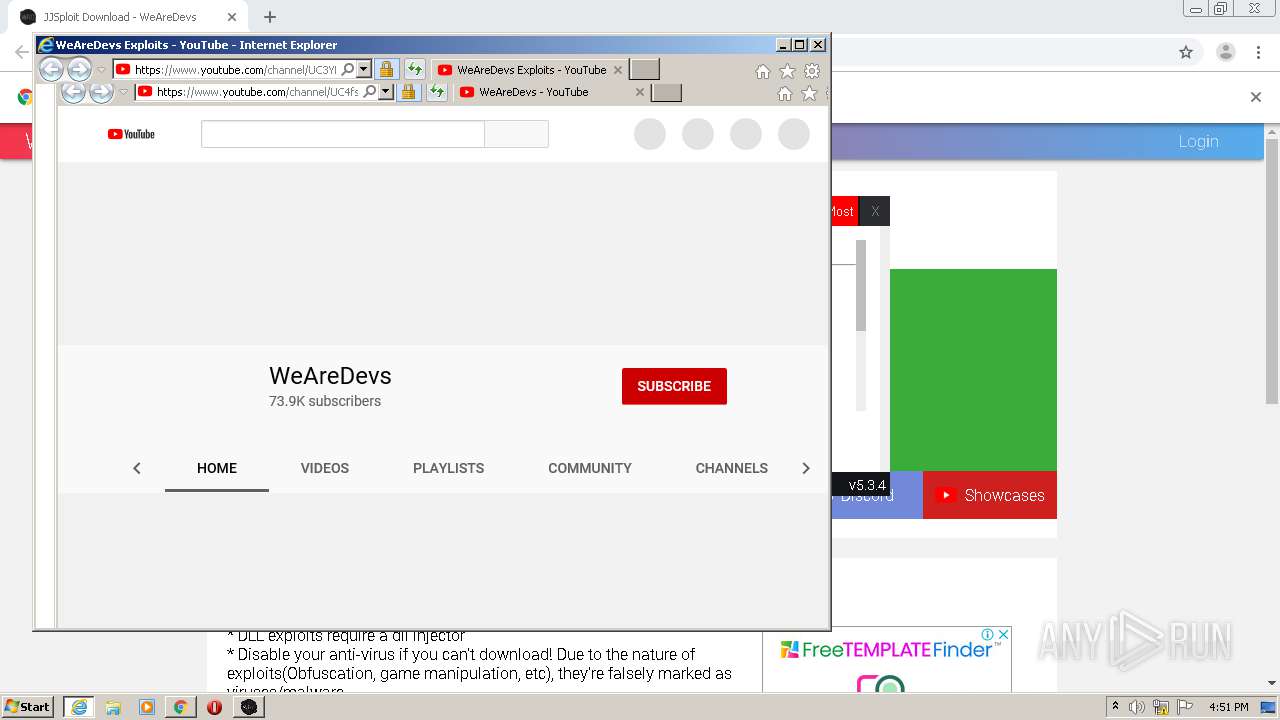
Starts Internet Explorer
- JJSploit v5.exe (PID: 2672)
INFO
Application launched itself
- chrome.exe (PID: 2472)
- iexplore.exe (PID: 1864)
- iexplore.exe (PID: 2560)
Reads the hosts file
- chrome.exe (PID: 1532)
- chrome.exe (PID: 2472)
- JJSploit v5.exe (PID: 2672)
Manual execution by user
- JJSploit v5.exe (PID: 2672)
Changes internet zones settings
- iexplore.exe (PID: 2560)
- iexplore.exe (PID: 1864)
Creates files in the user directory
- iexplore.exe (PID: 4052)
- iexplore.exe (PID: 1452)
Reads settings of System Certificates
- iexplore.exe (PID: 1452)
- iexplore.exe (PID: 1864)
- iexplore.exe (PID: 4052)
- iexplore.exe (PID: 2560)
Reads internet explorer settings
- iexplore.exe (PID: 4052)
- iexplore.exe (PID: 1452)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1864)
- iexplore.exe (PID: 2560)
Changes settings of System certificates
- iexplore.exe (PID: 1864)
- iexplore.exe (PID: 2560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
61
Monitored processes
23
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1068,18314383001733395140,15904812678788623149,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11269450768363805193 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2052 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1068,18314383001733395140,15904812678788623149,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18280019088174711856 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3224 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1068 | "C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe" --type=renderer --disable-features=SpareRendererForSitePerProcess --service-pipe-token=10624882930826704842 --lang=en-US --app-path="C:\Users\admin\AppData\Local\Programs\jjsploitv5\resources\app.asar" --no-sandbox --no-zygote --preload="C:\Users\admin\AppData\Local\Programs\jjsploitv5\resources\app.asar\build\preload.js" --background-color=#fff --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10624882930826704842 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1580 /prefetch:1 | C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe | — | JJSploit v5.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: JJSploit v5 Exit code: 0 Version: 5.3.4 Modules
| |||||||||||||||
| 1172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1068,18314383001733395140,15904812678788623149,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7144818324350581073 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3336 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1452 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1864 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1068,18314383001733395140,15904812678788623149,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=11985850185085913366 --mojo-platform-channel-handle=1428 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1068,18314383001733395140,15904812678788623149,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10465598089751871375 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2284 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1864 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.youtube.com/channel/UC4fs_zKuE1lsXbCLS_Y9UTA?view_as=subscriber | C:\Program Files\Internet Explorer\iexplore.exe | JJSploit v5.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2176 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1068,18314383001733395140,15904812678788623149,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5307017476359803502 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2168 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1068,18314383001733395140,15904812678788623149,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6243138425152896156 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3444 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 862
Read events
2 549
Write events
308
Delete events
5
Modification events
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2244) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2472-13251401373205750 |
Value: 259 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
20
Suspicious files
126
Text files
138
Unknown types
108
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FC7C59D-9A8.pma | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\687aab2b-957e-4bb9-b2fd-c5af83fd1ee7.tmp | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF13eef7.TMP | text | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF13f020.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
109
DNS requests
51
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4052 | iexplore.exe | GET | 200 | 216.58.207.67:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQD76E8xQFZstgIAAAAAgFWS | US | — | 472 b | whitelisted |
4052 | iexplore.exe | GET | 200 | 216.58.207.67:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQD76E8xQFZstgIAAAAAgFWS | US | — | 472 b | whitelisted |
4052 | iexplore.exe | GET | 200 | 216.58.207.67:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | — | 468 b | whitelisted |
1452 | iexplore.exe | GET | 200 | 216.58.207.67:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | — | 468 b | whitelisted |
1452 | iexplore.exe | GET | 200 | 216.58.207.67:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | — | 468 b | whitelisted |
1452 | iexplore.exe | GET | 200 | 216.58.207.67:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDa2MTpyZrzlQgAAAAAYth4 | US | — | 472 b | whitelisted |
1452 | iexplore.exe | GET | 200 | 216.58.207.67:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQD76E8xQFZstgIAAAAAgFWS | US | — | 472 b | whitelisted |
1452 | iexplore.exe | GET | 200 | 216.58.207.67:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQD76E8xQFZstgIAAAAAgFWS | US | — | 472 b | whitelisted |
4052 | iexplore.exe | GET | 200 | 216.58.207.67:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | — | 468 b | whitelisted |
4052 | iexplore.exe | GET | 200 | 216.58.207.67:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDDCp%2BiAKlAlQIAAAAAgFRY | US | — | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1532 | chrome.exe | 172.217.22.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
1532 | chrome.exe | 142.250.74.194:443 | pagead2.googlesyndication.com | Google Inc. | US | suspicious |
1532 | chrome.exe | 172.217.16.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1532 | chrome.exe | 142.250.74.202:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1532 | chrome.exe | 104.16.19.94:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
1532 | chrome.exe | 216.58.210.8:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
1532 | chrome.exe | 216.58.206.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1532 | chrome.exe | 172.217.23.162:443 | adservice.google.com | Google Inc. | US | whitelisted |
1532 | chrome.exe | 104.26.6.147:443 | wearedevs.net | Cloudflare Inc | US | suspicious |
1532 | chrome.exe | 172.217.22.34:443 | adservice.google.ae | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wearedevs.net |
| whitelisted |
accounts.google.com |
| shared |
pagead2.googlesyndication.com |
| whitelisted |
cdn.wearedevs.net |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |