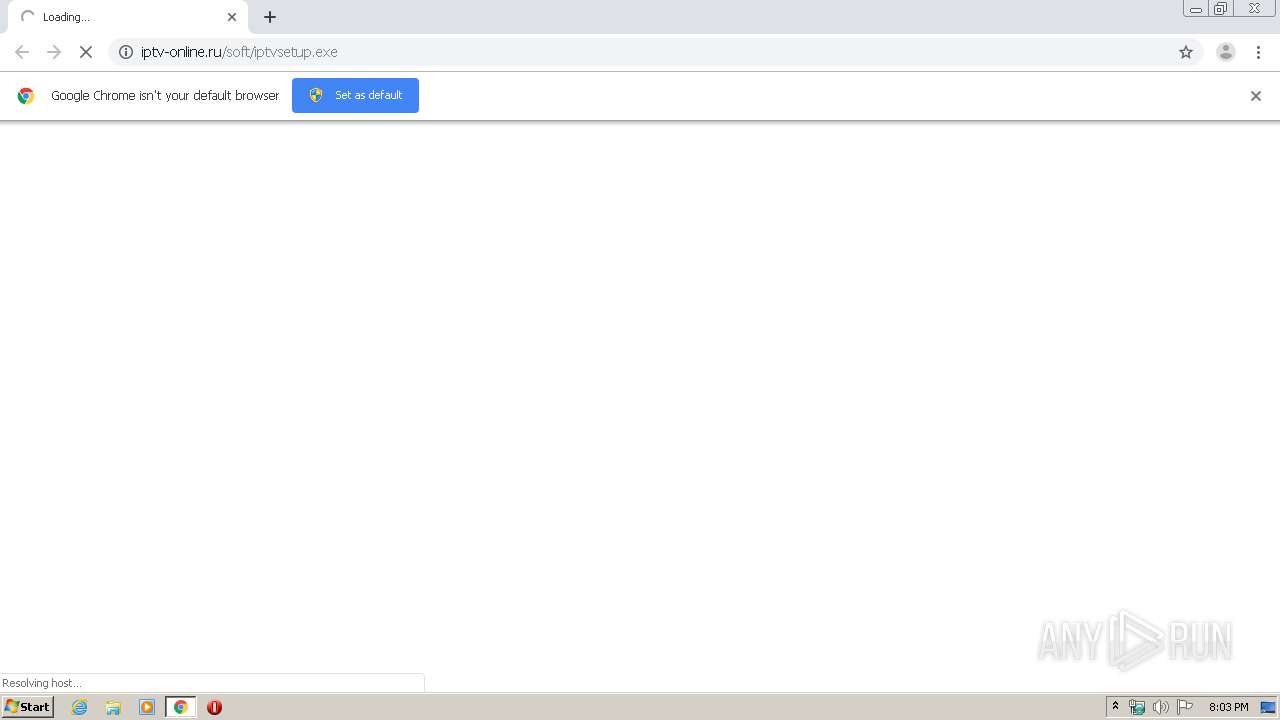
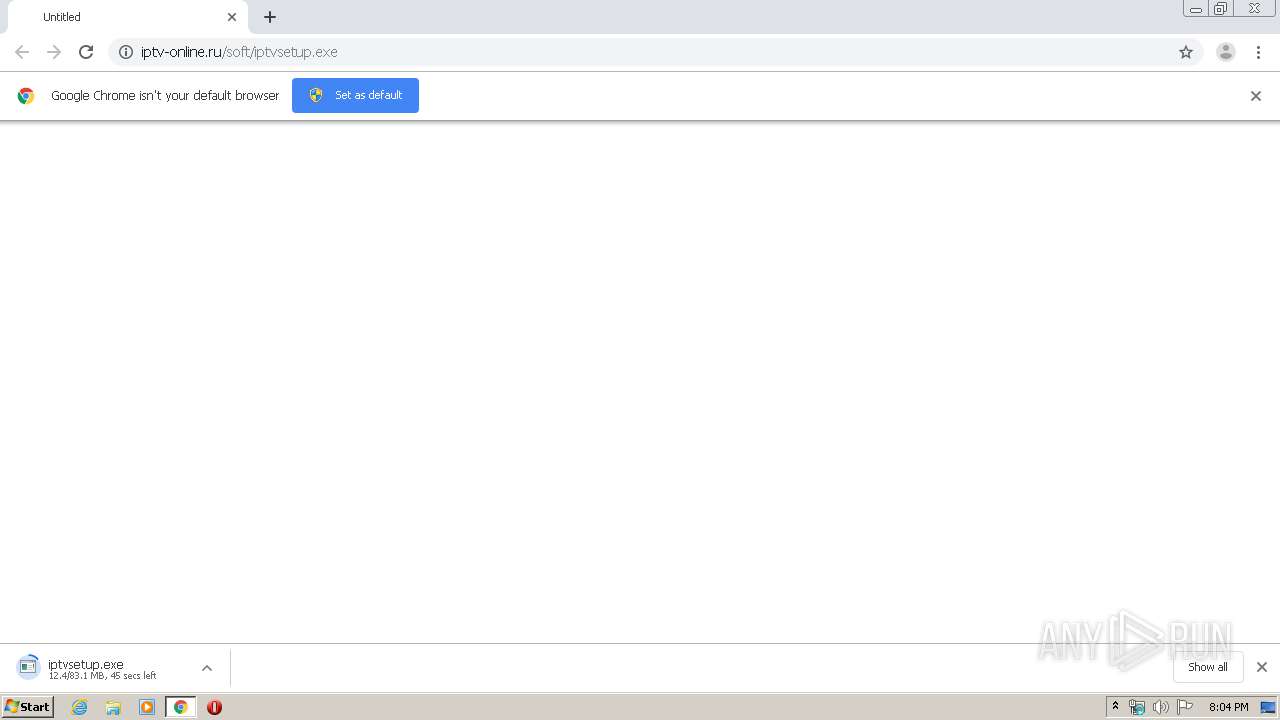
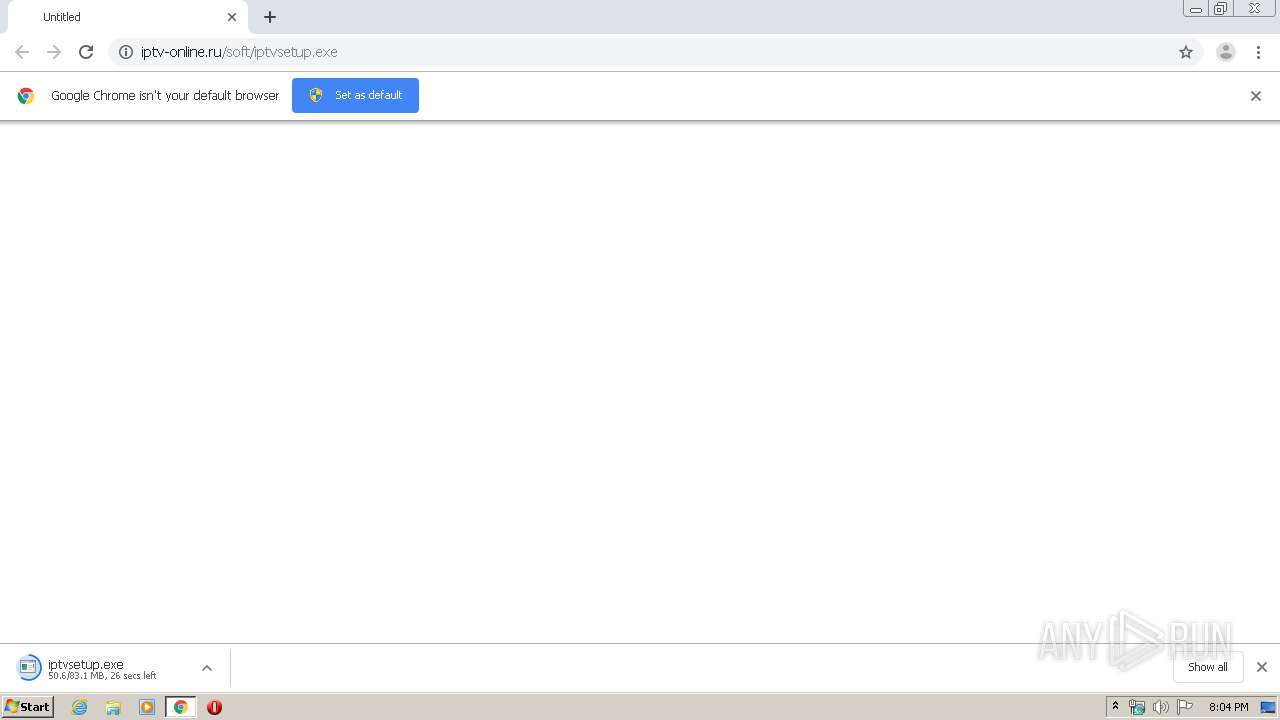
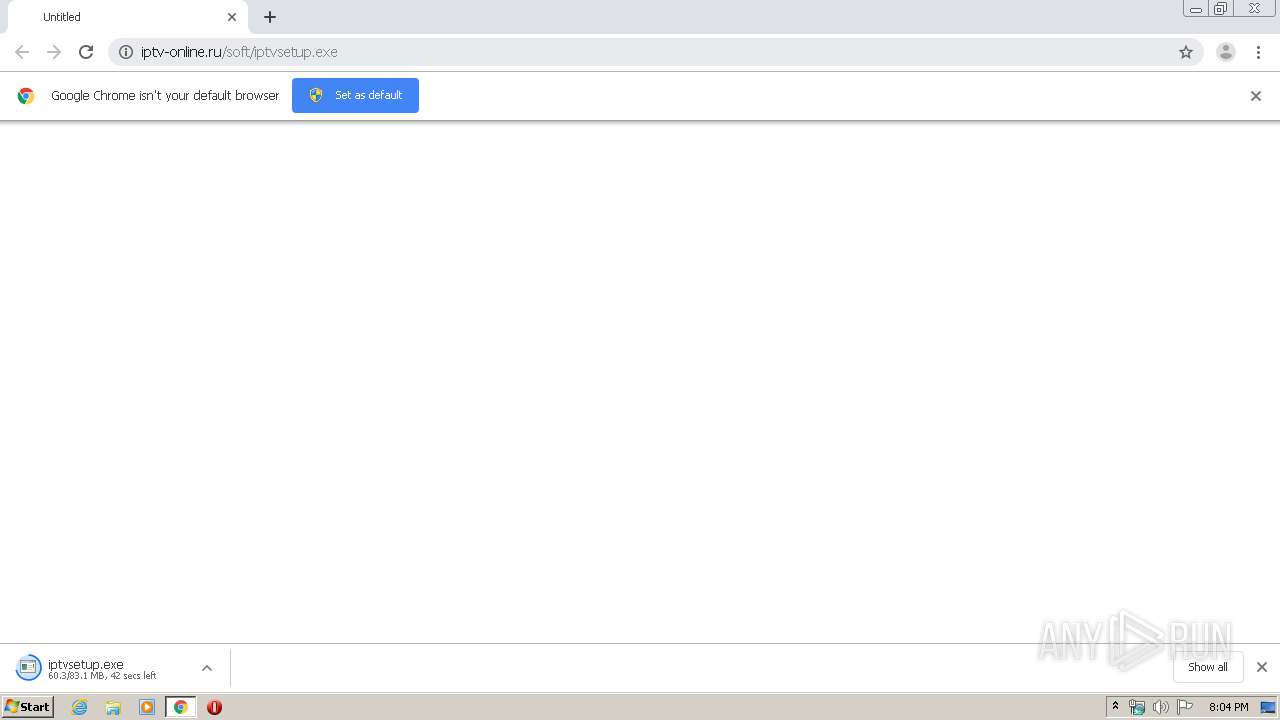
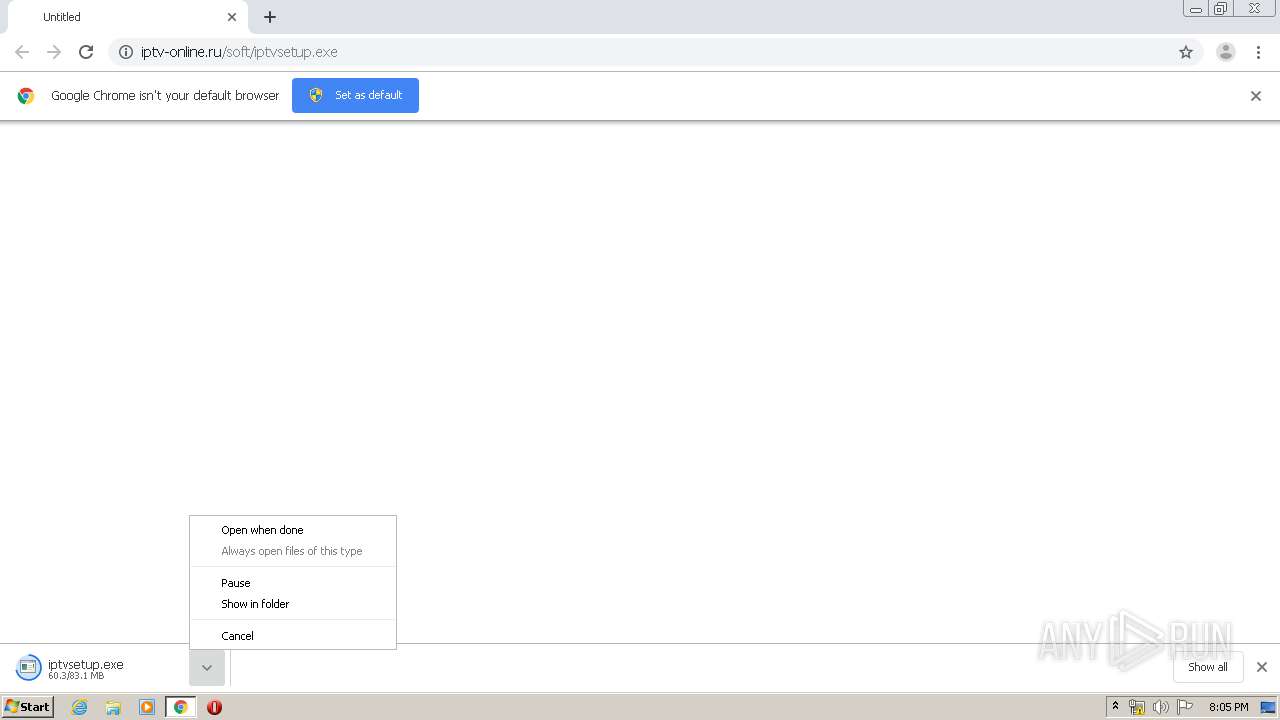
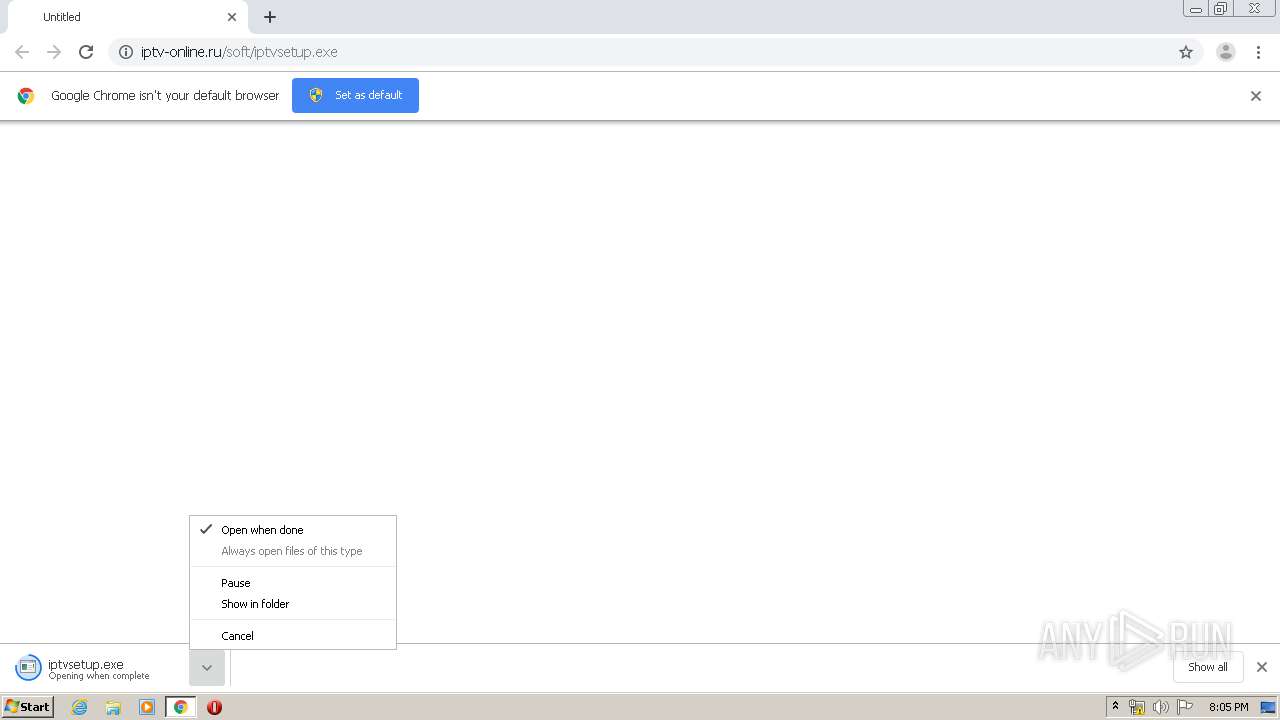
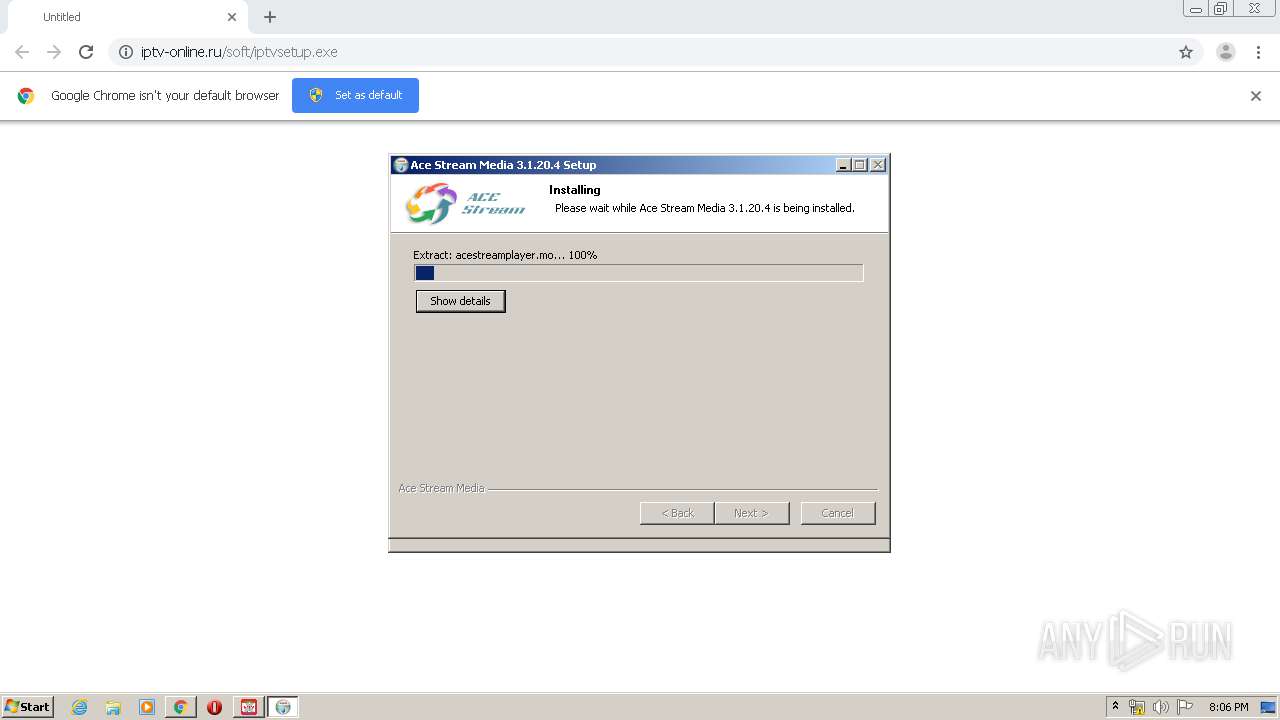
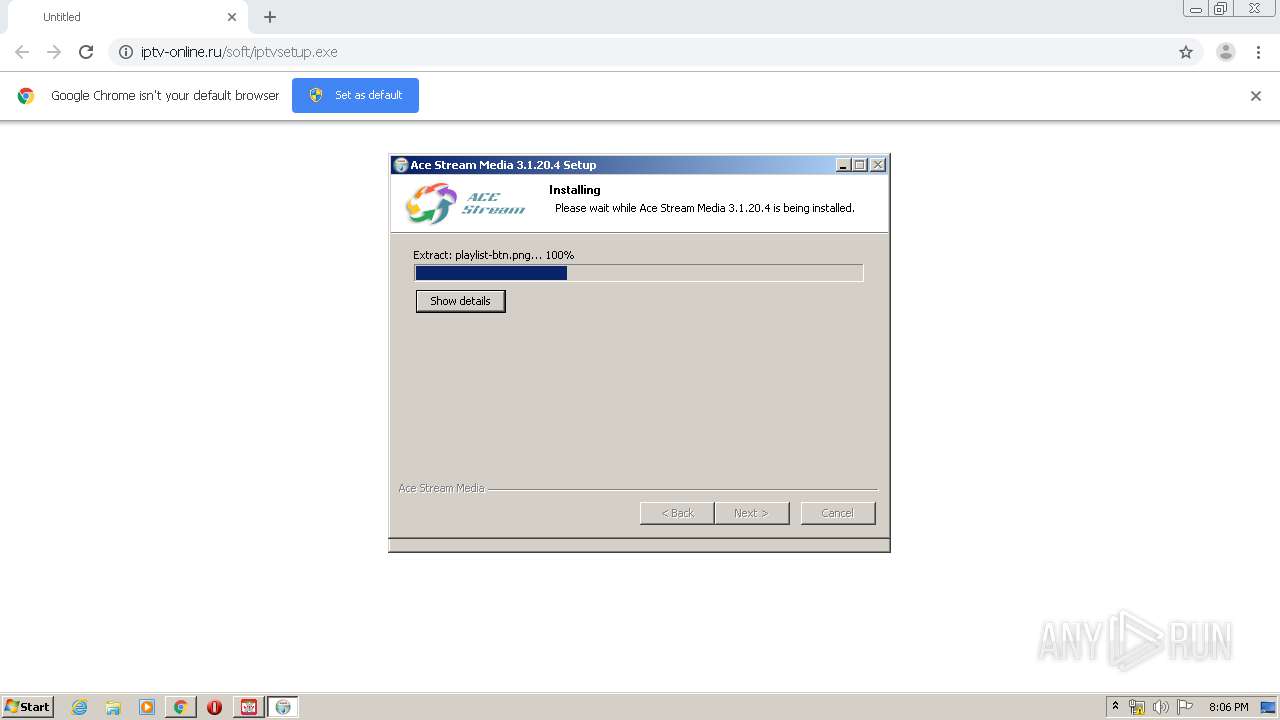
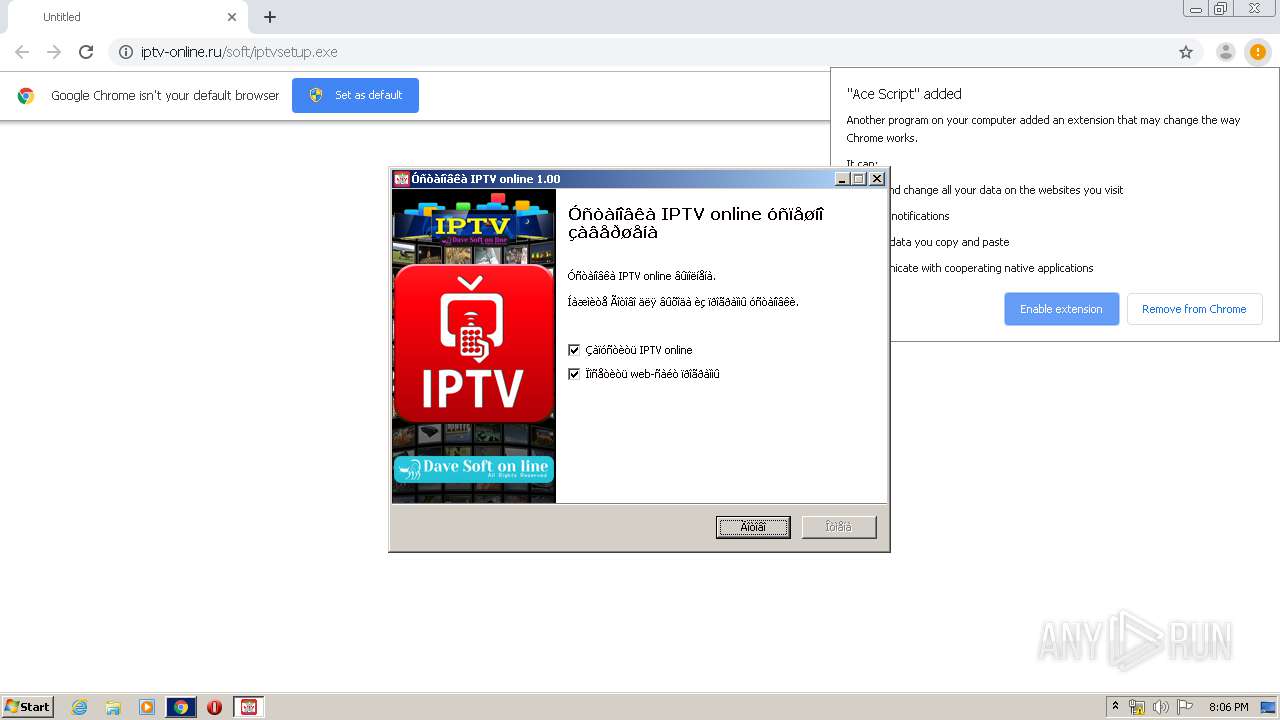
| URL: | http://iptv-online.ru/soft/iptvsetup.exe |
| Full analysis: | https://app.any.run/tasks/09c4d693-1605-4440-8ba1-c890e4c21f65 |
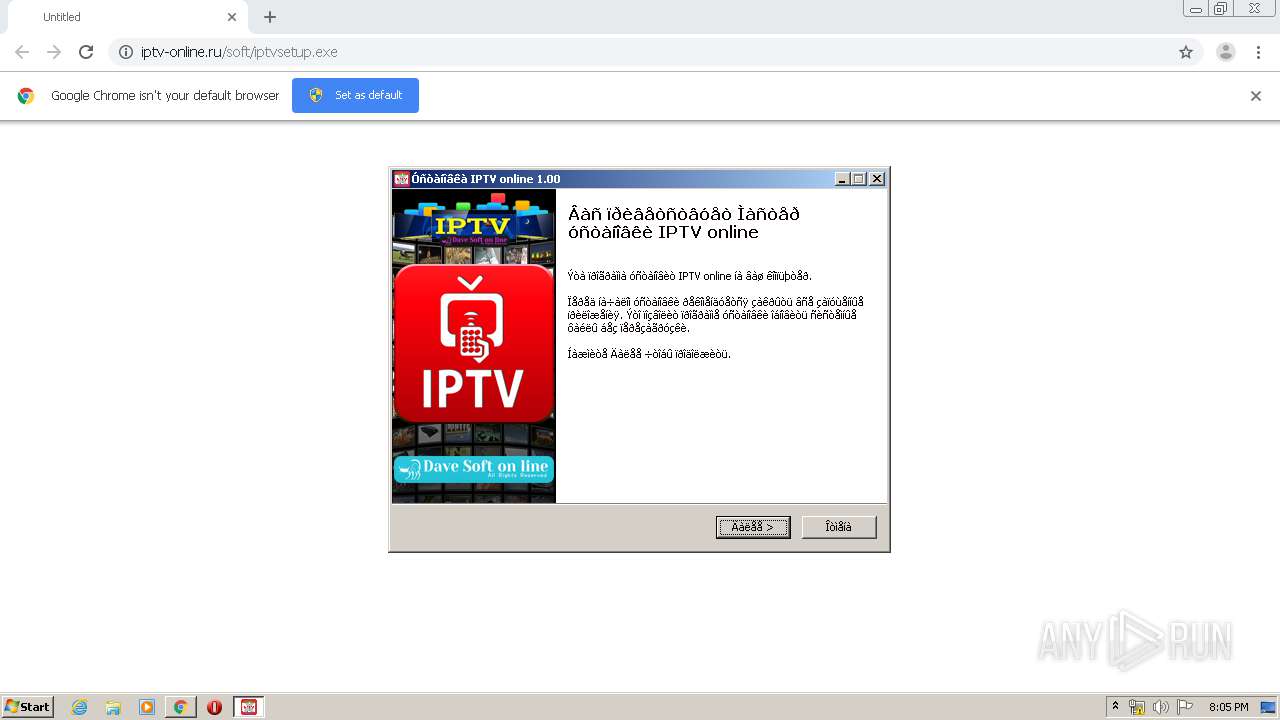
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2020, 19:03:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 15F7CFCCCF666E1A6ED6D43B97E0AD5A |
| SHA1: | 3AA6B12C7EF8355CA1A62AC738CEFE884CC34BBD |
| SHA256: | 59BF7B76FC615C225AE65619FFD1B4DE6712BEEB00CC53DDA2F6B621CBA83729 |
| SSDEEP: | 3:N1KXXNMLLYRKVkA:CtGsTA |
MALICIOUS
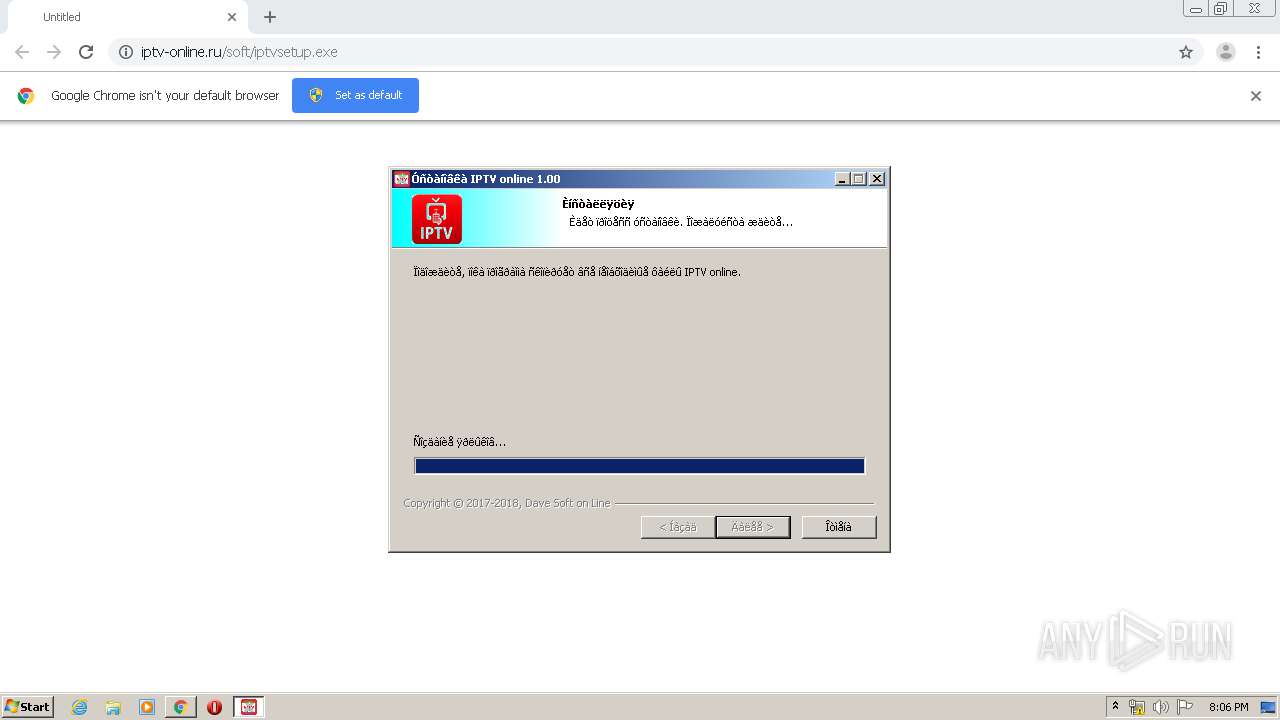
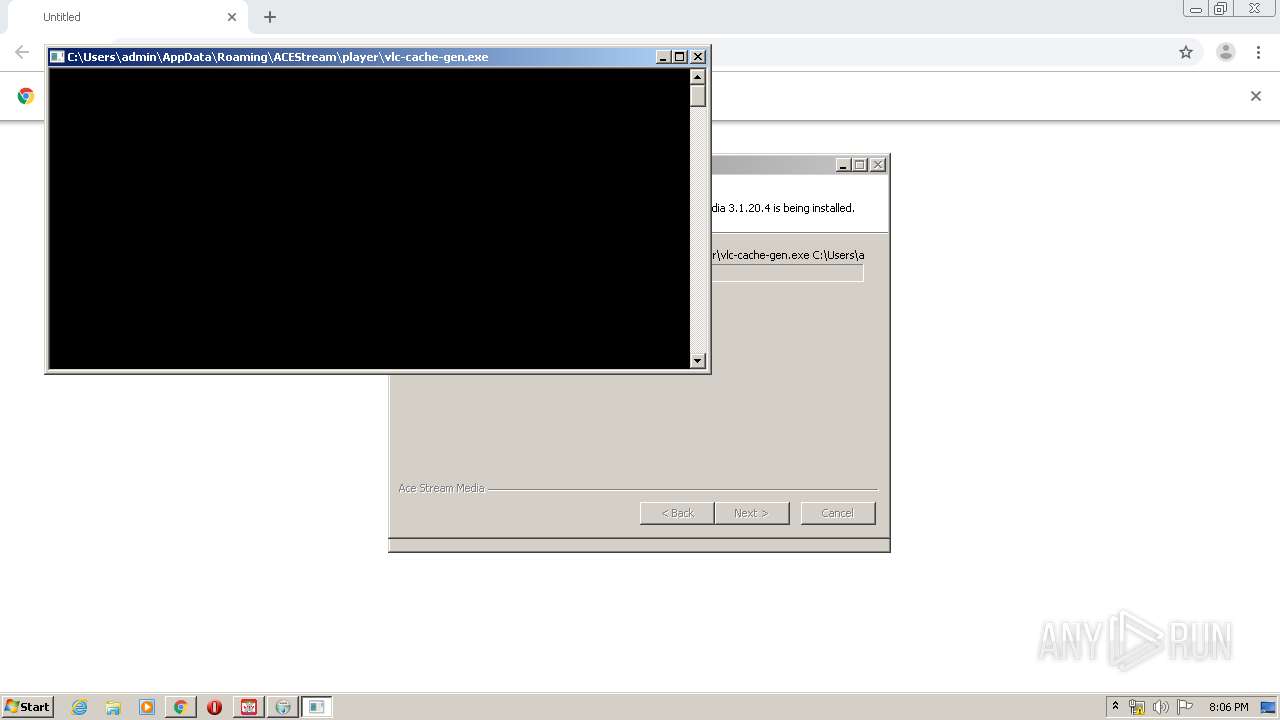
Application was dropped or rewritten from another process
- iptvsetup.exe (PID: 2156)
- iptvsetup.exe (PID: 3904)
- vlc-cache-gen.exe (PID: 2540)
- ace_engine.exe (PID: 3632)
- ace_engine.exe (PID: 4080)
- ace.exe (PID: 3240)
Loads dropped or rewritten executable
- ace.exe (PID: 3240)
- vlc-cache-gen.exe (PID: 2540)
- ace_engine.exe (PID: 3632)
- ace_engine.exe (PID: 4080)
- iexplore.exe (PID: 2440)
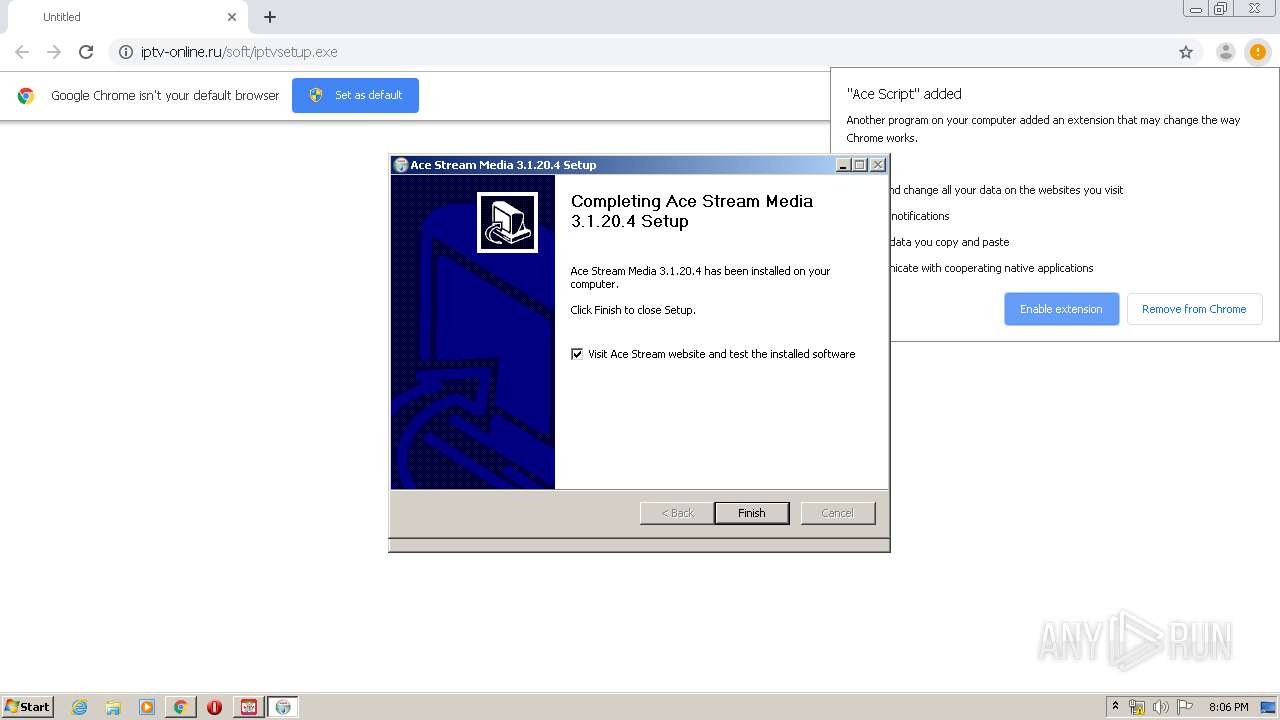
Changes the autorun value in the registry
- ace.exe (PID: 3240)
Actions looks like stealing of personal data
- ace.exe (PID: 3240)
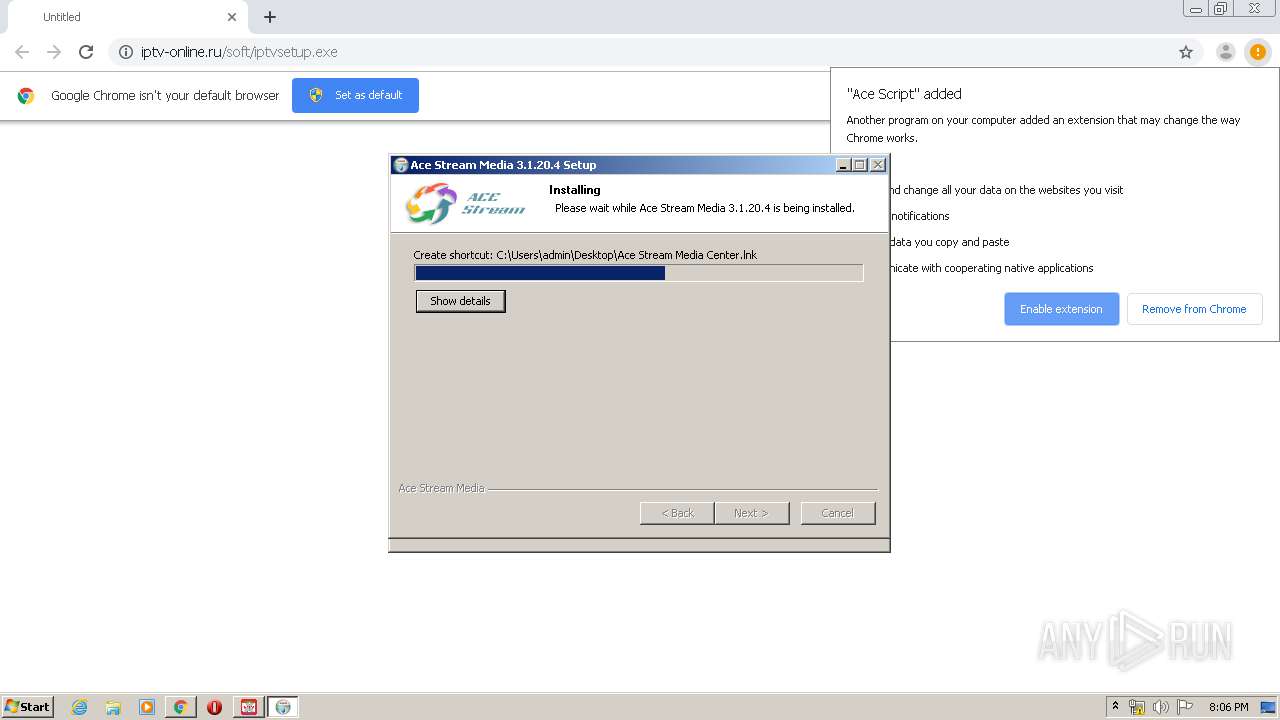
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3968)
- iptvsetup.exe (PID: 3904)
- ace.exe (PID: 3240)
Reads Internet Cache Settings
- ace.exe (PID: 3240)
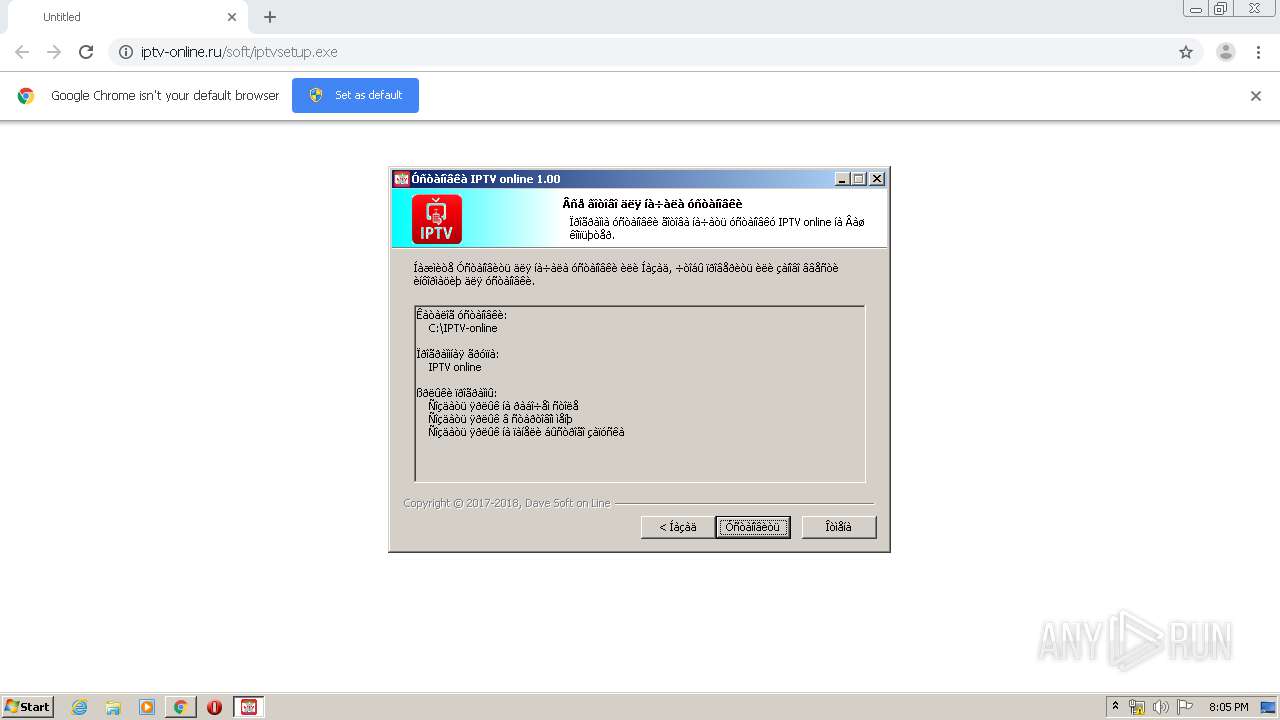
Creates files in the user directory
- iptvsetup.exe (PID: 3904)
- vlc-cache-gen.exe (PID: 2540)
- ace_engine.exe (PID: 3632)
- ace_engine.exe (PID: 4080)
- ace.exe (PID: 3240)
Creates a software uninstall entry
- iptvsetup.exe (PID: 3904)
- ace.exe (PID: 3240)
Creates COM task schedule object
- ace.exe (PID: 3240)
Modifies the open verb of a shell class
- ace.exe (PID: 3240)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3968)
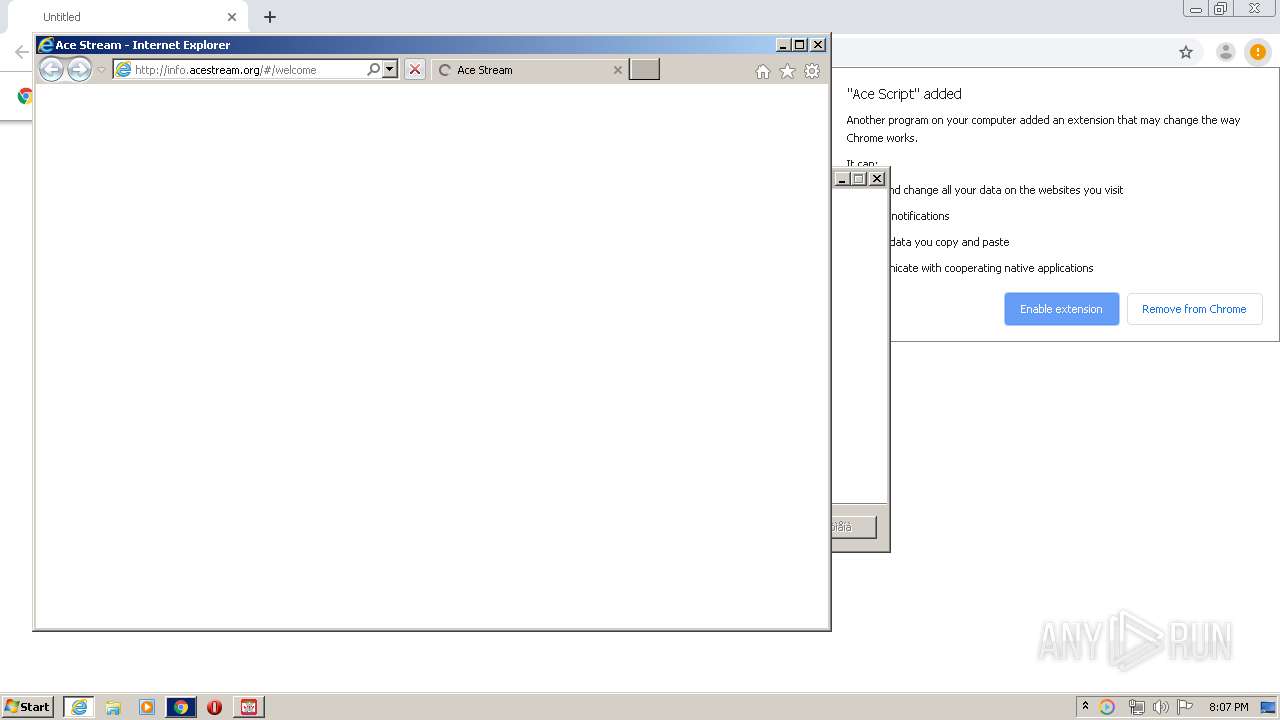
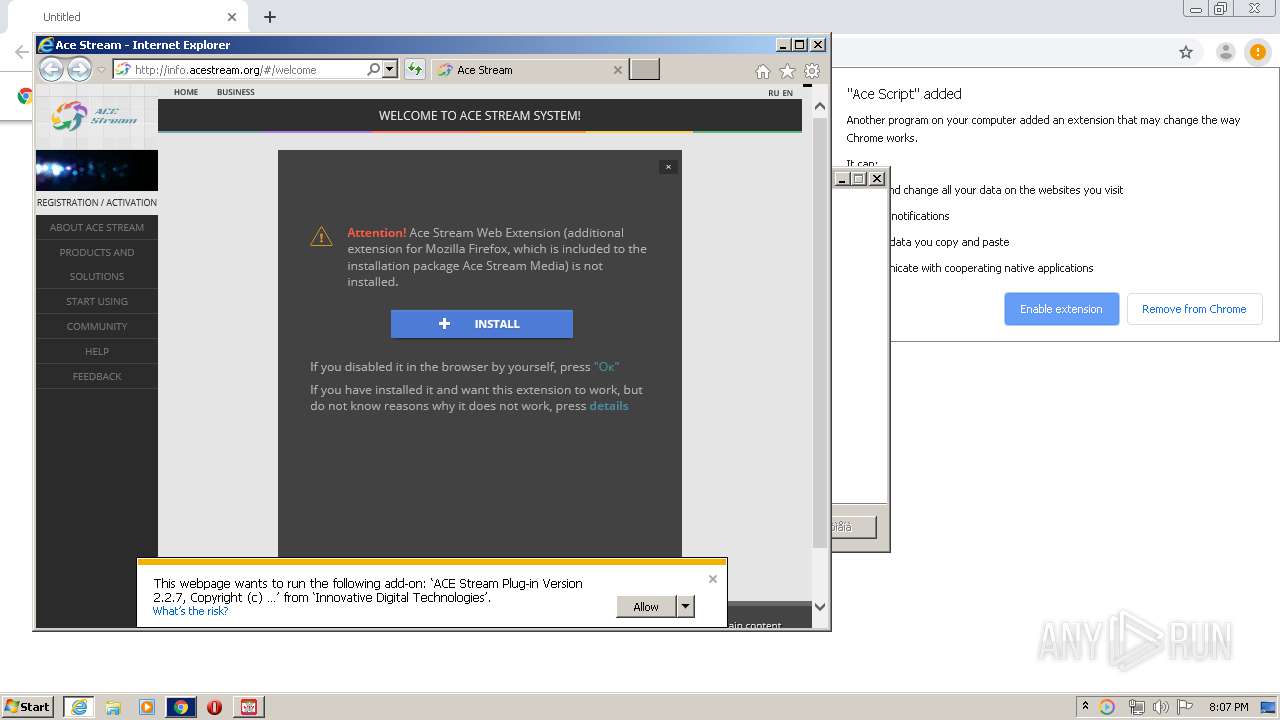
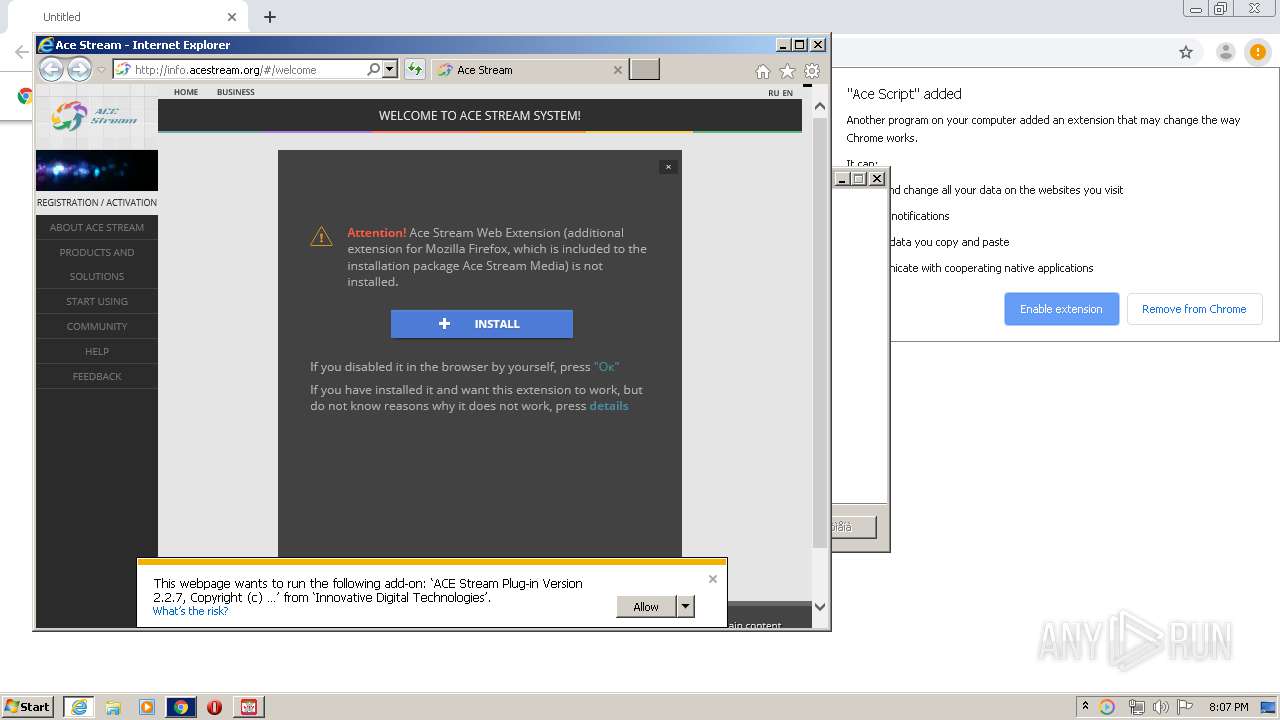
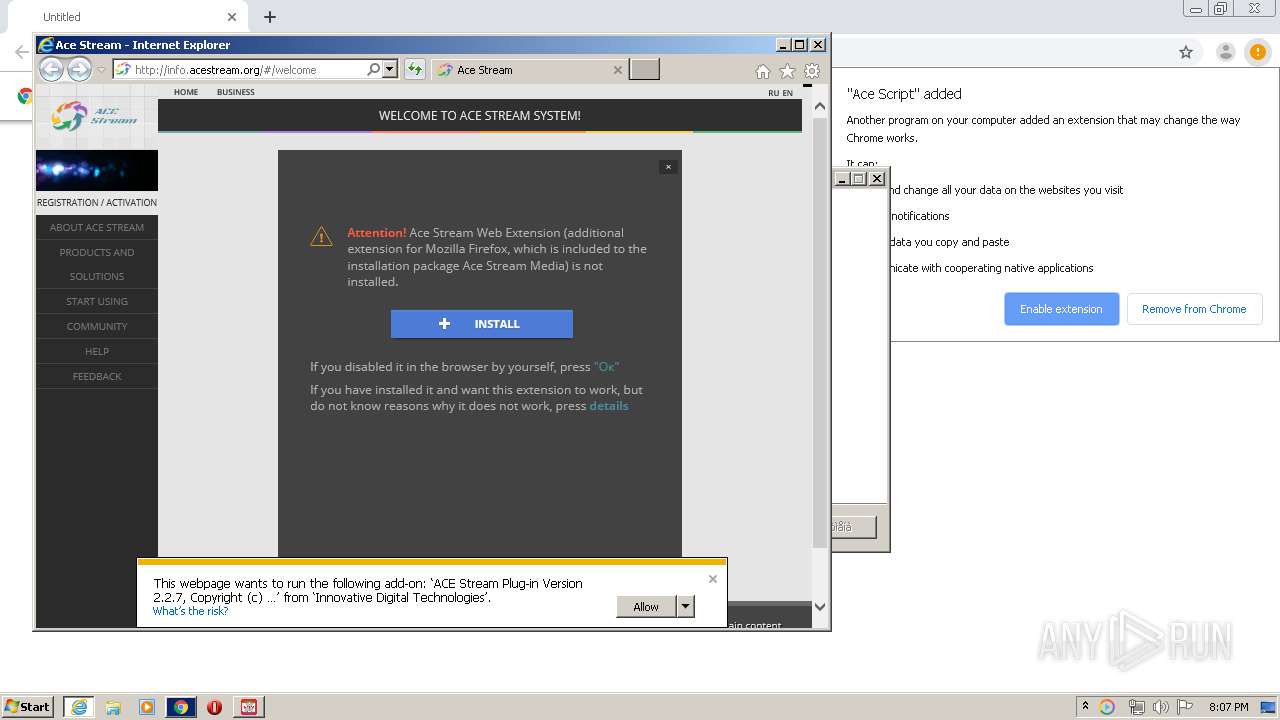
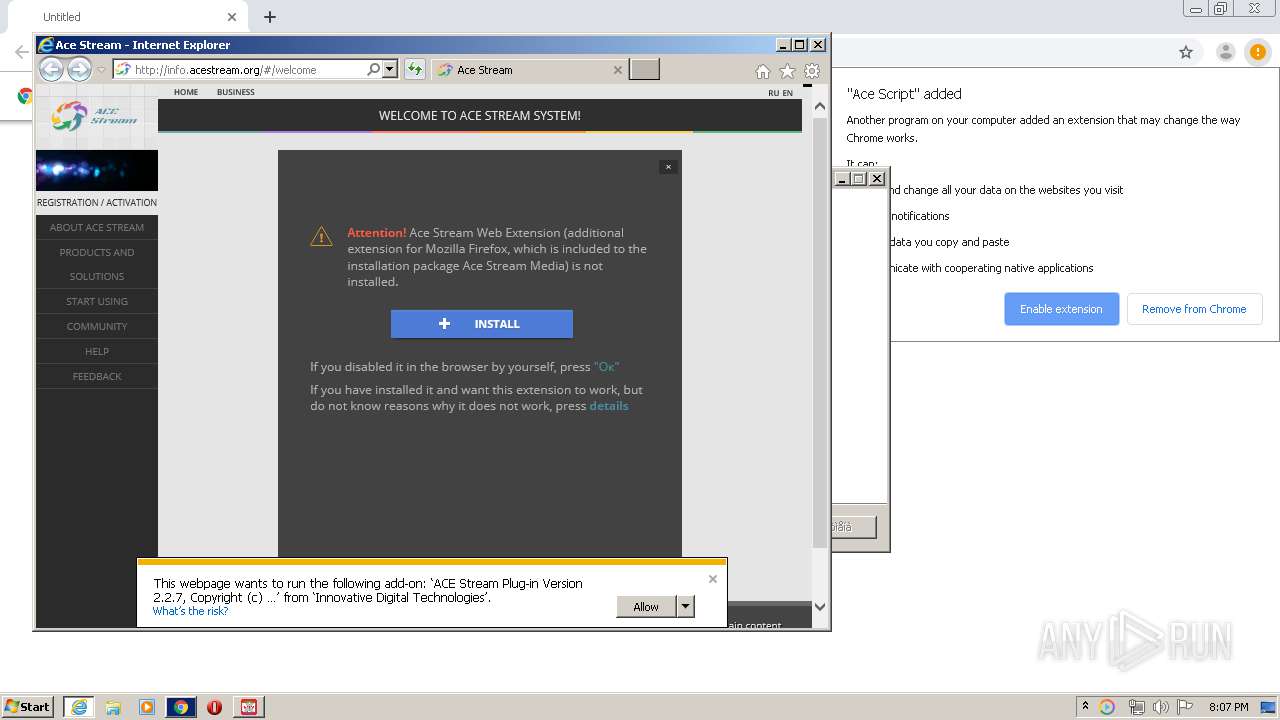
Starts Internet Explorer
- ace.exe (PID: 3240)
Loads Python modules
- ace_engine.exe (PID: 3632)
- ace_engine.exe (PID: 4080)
Starts CMD.EXE for commands execution
- NETSTAT.EXE (PID: 2432)
- ace_engine.exe (PID: 3632)
Uses NETSTAT.EXE to discover network connections
- cmd.exe (PID: 4060)
Uses IPCONFIG.EXE to discover IP address
- cmd.exe (PID: 3236)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 3984)
Application launched itself
- ace_engine.exe (PID: 3632)
INFO
Application launched itself
- chrome.exe (PID: 3968)
- iexplore.exe (PID: 2920)
Reads the hosts file
- chrome.exe (PID: 3968)
- chrome.exe (PID: 3432)
Reads Internet Cache Settings
- chrome.exe (PID: 3968)
- iexplore.exe (PID: 2920)
- iexplore.exe (PID: 2440)
Dropped object may contain Bitcoin addresses
- ace.exe (PID: 3240)
Changes internet zones settings
- iexplore.exe (PID: 2920)
Reads internet explorer settings
- iexplore.exe (PID: 2440)
Reads settings of System Certificates
- chrome.exe (PID: 3432)
- ace_engine.exe (PID: 3632)
- iexplore.exe (PID: 2920)
- iexplore.exe (PID: 2440)
Creates files in the user directory
- iexplore.exe (PID: 2440)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2440)
Changes settings of System certificates
- iexplore.exe (PID: 2440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
94
Monitored processes
48
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,13616854945159213112,12156430379623384036,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5737018267907513930 --mojo-platform-channel-handle=3588 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 604 | C:\Windows\system32\cmd.exe /c "C:\Windows\system32\route.exe" print | C:\Windows\system32\cmd.exe | — | NETSTAT.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,13616854945159213112,12156430379623384036,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=107399411034725121 --mojo-platform-channel-handle=1096 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,13616854945159213112,12156430379623384036,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16870010503793639903 --mojo-platform-channel-handle=2660 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,13616854945159213112,12156430379623384036,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8255146739681366078 --mojo-platform-channel-handle=3476 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,13616854945159213112,12156430379623384036,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5994837803354371651 --mojo-platform-channel-handle=2760 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,13616854945159213112,12156430379623384036,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14099787489150229652 --mojo-platform-channel-handle=3136 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,13616854945159213112,12156430379623384036,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7645672535355669973 --mojo-platform-channel-handle=2052 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,13616854945159213112,12156430379623384036,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4368849875021705725 --mojo-platform-channel-handle=3220 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ebaa9d0,0x6ebaa9e0,0x6ebaa9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
5 353
Read events
2 225
Write events
3 122
Delete events
6
Modification events
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3968-13232142232200375 |
Value: 259 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3968-13232142232200375 |
Value: 259 | |||
Executable files
434
Suspicious files
45
Text files
1 416
Unknown types
292
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5EA1E698-F80.pma | — | |
MD5:— | SHA256:— | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\37d1d3c2-7268-4a32-8d05-050832a90510.tmp | — | |
MD5:— | SHA256:— | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa6e72c.TMP | text | |
MD5:— | SHA256:— | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFa6e75b.TMP | text | |
MD5:— | SHA256:— | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa6e92f.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
161
TCP/UDP connections
101
DNS requests
42
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3432 | chrome.exe | GET | — | 195.64.154.65:80 | http://iptv-online.ru/soft/iptvsetup.exe | UA | — | — | suspicious |
3432 | chrome.exe | GET | 206 | 195.64.154.65:80 | http://iptv-online.ru/soft/iptvsetup.exe | UA | binary | 18.1 Mb | suspicious |
2440 | iexplore.exe | GET | 200 | 77.120.101.26:80 | http://info.acestream.org/ | UA | html | 245 Kb | unknown |
2440 | iexplore.exe | GET | 200 | 77.120.105.71:80 | http://static.acestream.net/sites/acestream/js/jquery.easing.1.3.js | UA | text | 2.12 Kb | suspicious |
2440 | iexplore.exe | GET | 200 | 77.120.101.26:80 | http://info.acestream.org/js/init.js?23 | UA | text | 120 Kb | unknown |
2440 | iexplore.exe | GET | 200 | 148.251.41.163:80 | http://static.torrentstream.org/sites/org/img/social/Facebook.png | DE | image | 1.04 Kb | suspicious |
3432 | chrome.exe | GET | 200 | 74.125.100.10:80 | http://r5---sn-5hnekn7l.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Qx&mip=85.203.44.113&mm=28&mn=sn-5hnekn7l&ms=nvh&mt=1587668716&mv=m&mvi=4&pl=27&shardbypass=yes | US | crx | 816 Kb | whitelisted |
2440 | iexplore.exe | GET | 200 | 77.120.105.71:80 | http://static.acestream.net/sites/acestream/css/jquery.jscrollpane.css | UA | text | 988 b | suspicious |
2440 | iexplore.exe | GET | 200 | 77.120.105.71:80 | http://static.acestream.net/sites/acestream/js/jquery.hashchange-1.0.0.js | UA | text | 1.24 Kb | suspicious |
2440 | iexplore.exe | GET | 200 | 77.120.105.71:80 | http://static.acestream.net/sites/acestream/css/style.css | UA | text | 15.7 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3432 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3432 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
3432 | chrome.exe | 172.217.22.68:443 | www.google.com | Google Inc. | US | whitelisted |
3432 | chrome.exe | 195.64.154.65:80 | iptv-online.ru | Ukrainian Internet Names Center LTD | UA | suspicious |
3432 | chrome.exe | 216.58.208.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3432 | chrome.exe | 216.58.206.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3240 | ace.exe | 148.251.41.163:80 | installer-api.acestream.org | Hetzner Online GmbH | DE | suspicious |
3432 | chrome.exe | 172.217.13.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
3432 | chrome.exe | 172.217.18.14:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3432 | chrome.exe | 216.58.212.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
iptv-online.ru |
| suspicious |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
installer-api.acestream.org |
| suspicious |
clients2.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3432 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3240 | ace.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
3240 | ace.exe | Misc activity | SUSPICIOUS [PTsecurity] HTTP header - Sometimes used by hostile installer |
3240 | ace.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
3240 | ace.exe | Misc activity | SUSPICIOUS [PTsecurity] HTTP header - Sometimes used by hostile installer |
3632 | ace_engine.exe | Potential Corporate Privacy Violation | ET P2P BitTorrent DHT ping request |
3632 | ace_engine.exe | Attempted Information Leak | ET POLICY Python-urllib/ Suspicious User Agent |
3632 | ace_engine.exe | Attempted Information Leak | ET POLICY Python-urllib/ Suspicious User Agent |
3632 | ace_engine.exe | Attempted Information Leak | ET POLICY Python-urllib/ Suspicious User Agent |
3632 | ace_engine.exe | Attempted Information Leak | ET POLICY Python-urllib/ Suspicious User Agent |