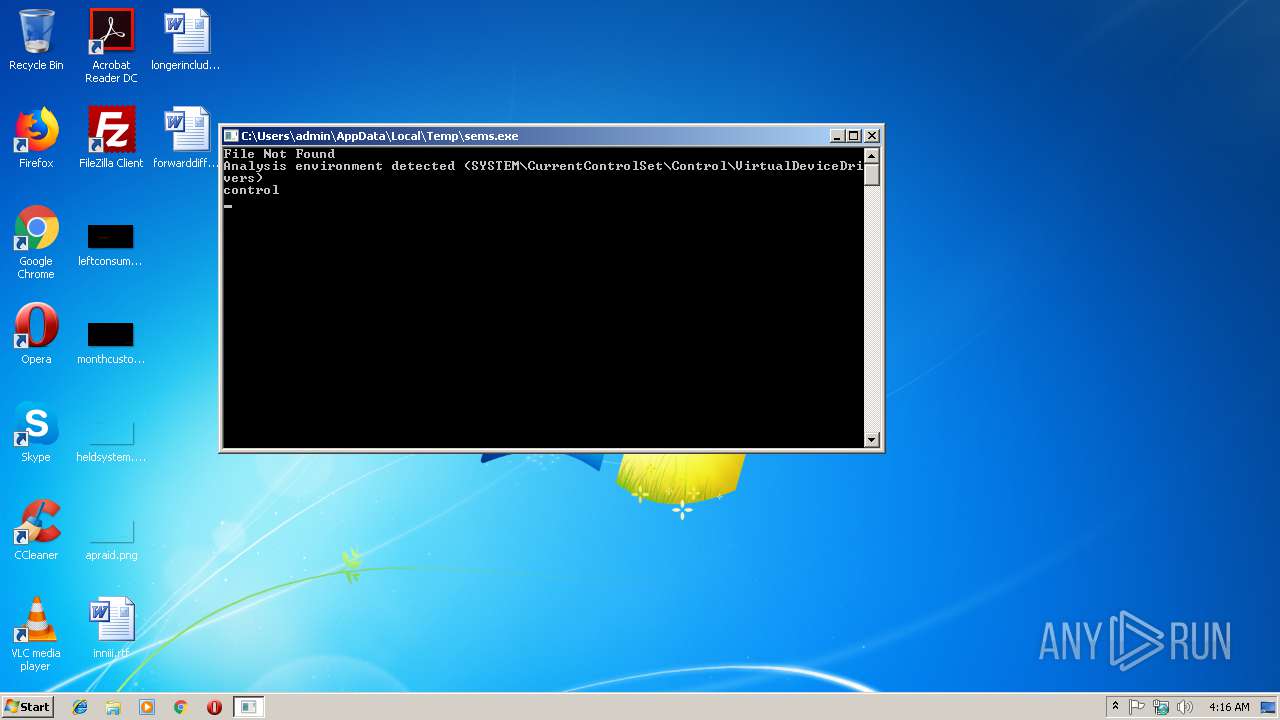
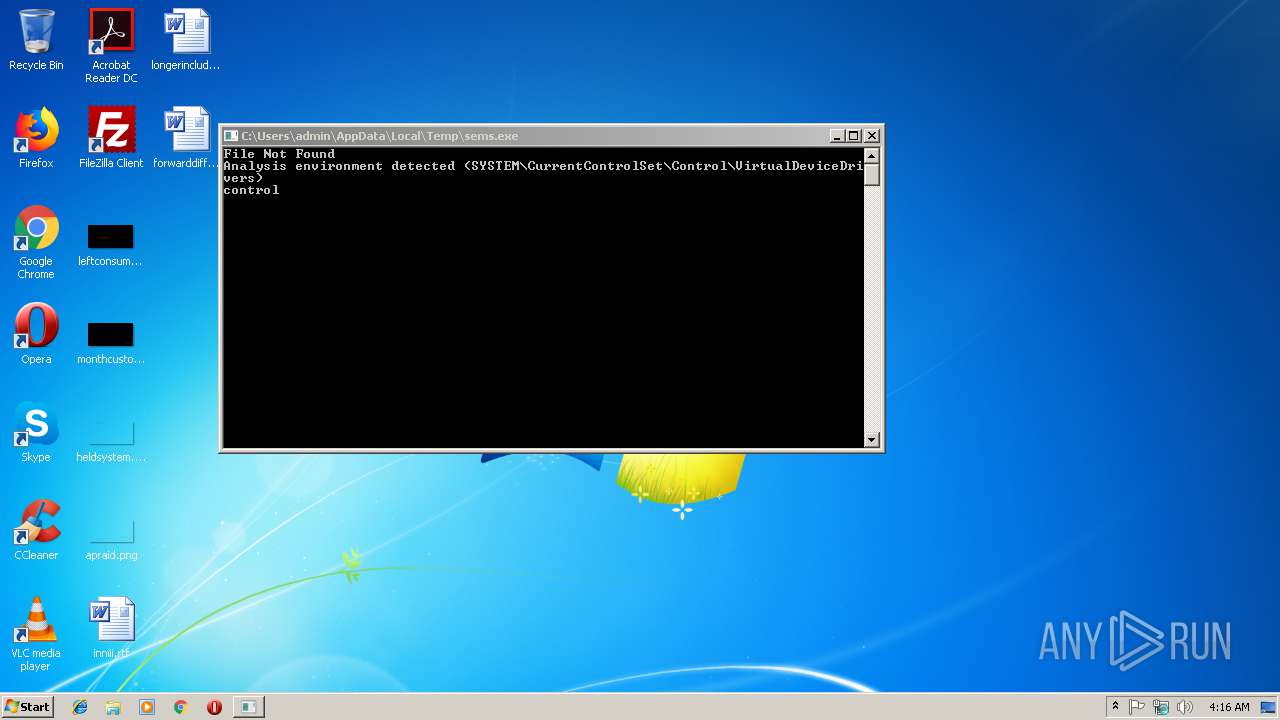
| File name: | sems.exe |
| Full analysis: | https://app.any.run/tasks/1d34c406-bd30-4f35-9595-94957d1a0004 |
| Verdict: | Suspicious activity |
| Analysis date: | November 30, 2018, 04:15:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | B16EEFA3049BB3CB0FCDD35BBDAC5439 |
| SHA1: | 9ED1C415699FC4CD0C74EA9FC1FE97D7AF847CA0 |
| SHA256: | 59BB9D0838882EC12D28EAE3EF9B02AD58CD83DDFFEECEC4B938F7A58BED50EE |
| SSDEEP: | 12288:UOK6QBRpuJv8BgpSazznnfKDuggznQkZpM3BHEcPAF4eWsmug2Ex83dq4+ANiKIt:4WFXZpCC4eWwgf8RJNiKfEYzO |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts CMD.EXE for commands execution
- sems.exe (PID: 2960)
Uses NETSTAT.EXE to discover network connections
- cmd.exe (PID: 2420)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:06:01 08:03:25+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 1013248 |
| InitializedDataSize: | 261120 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x77f5f |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 01-Jun-2016 06:03:25 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 01-Jun-2016 06:03:25 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.textbss9R\x07 | 0x00001000 | 0x00075239 | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.text | 0x00077000 | 0x000F7588 | 0x000F7600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.56399 |
.rdata | 0x0016F000 | 0x0002BFE9 | 0x0002C000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.69776 |
.data | 0x0019B000 | 0x00005B24 | 0x00003200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.6882 |
.idata | 0x001A1000 | 0x0000130F | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.39366 |
.rsrc | 0x001A3000 | 0x0000260C | 0x00002800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.67395 |
.reloc | 0x001A6000 | 0x0000A252 | 0x0000A400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.18488 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
104 | 4.86654 | 2711 | UNKNOWN | Turkish - Turkey | TEXT |
106 | 5.00569 | 4365 | UNKNOWN | Turkish - Turkey | TEXT |
Imports
ADVAPI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MPR.dll |
PSAPI.DLL |
USER32.dll |
WININET.dll |
Total processes
38
Monitored processes
8
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | wmic cpu get NumberOfCores | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2420 | C:\Windows\system32\cmd.exe /c netstat -an | C:\Windows\system32\cmd.exe | — | sems.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2620 | netstat -an | C:\Windows\system32\NETSTAT.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Netstat Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2920 | C:\Windows\system32\cmd.exe /c wmic logicaldisk get size | C:\Windows\system32\cmd.exe | — | sems.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2960 | "C:\Users\admin\AppData\Local\Temp\sems.exe" | C:\Users\admin\AppData\Local\Temp\sems.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3156 | wmic logicaldisk get size | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3468 | C:\Windows\system32\cmd.exe /c cd c:\ & dir *cuckoo* /s /p | C:\Windows\system32\cmd.exe | — | sems.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3916 | C:\Windows\system32\cmd.exe /c wmic cpu get NumberOfCores | C:\Windows\system32\cmd.exe | — | sems.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
113
Read events
99
Write events
14
Delete events
0
Modification events
| (PID) Process: | (2960) sems.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sems_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2960) sems.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sems_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2960) sems.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sems_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2960) sems.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sems_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2960) sems.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sems_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2960) sems.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sems_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2960) sems.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sems_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2960) sems.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sems_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2960) sems.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sems_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2960) sems.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sems_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2960 | sems.exe | C:\Users\admin\AppData\Local\Temp\vmregKey.txt | text | |
MD5:400F552418CA0FBC30AB263B91C53C67 | SHA256:1423C0B22B90582165AC9EE247FCAB67A69A7D1C9455EC3423A24A16B3F96AD1 | |||
| 2960 | sems.exe | C:\Users\admin\AppData\Local\Temp\control.txt | text | |
MD5:400F552418CA0FBC30AB263B91C53C67 | SHA256:1423C0B22B90582165AC9EE247FCAB67A69A7D1C9455EC3423A24A16B3F96AD1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2960 | sems.exe | 172.217.168.3:443 | www.google.com.tr | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com.tr |
| whitelisted |