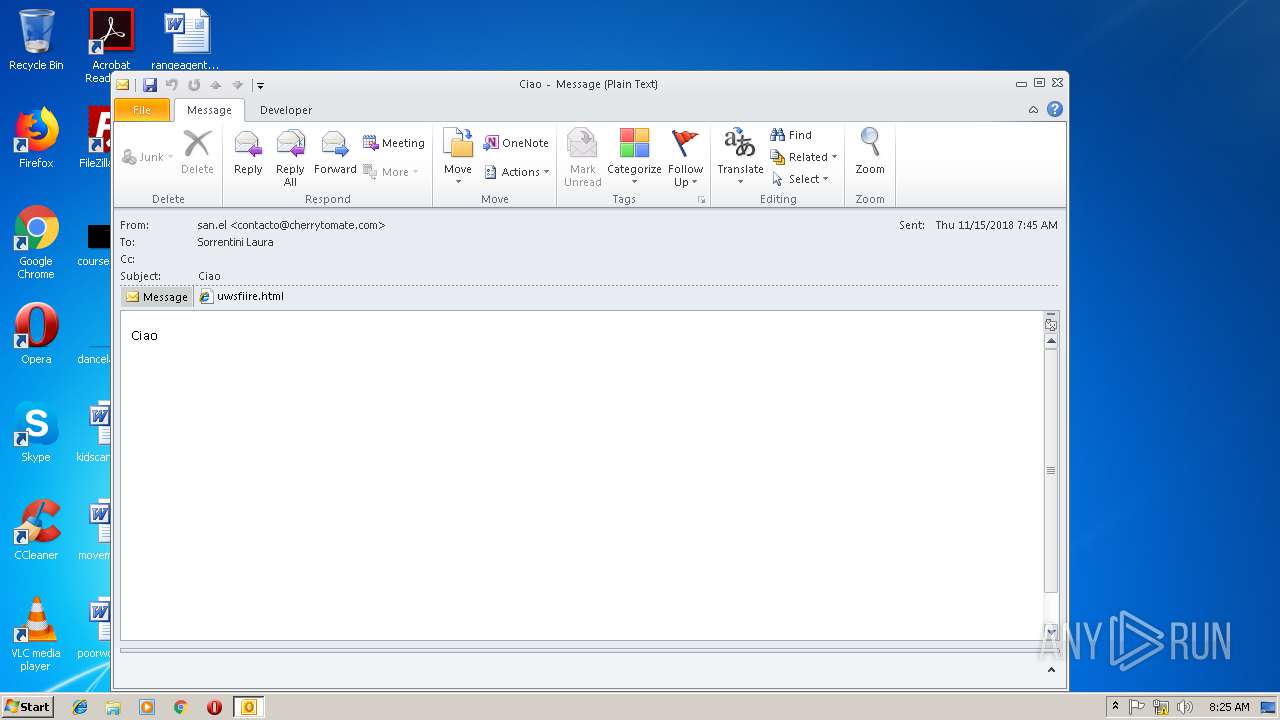
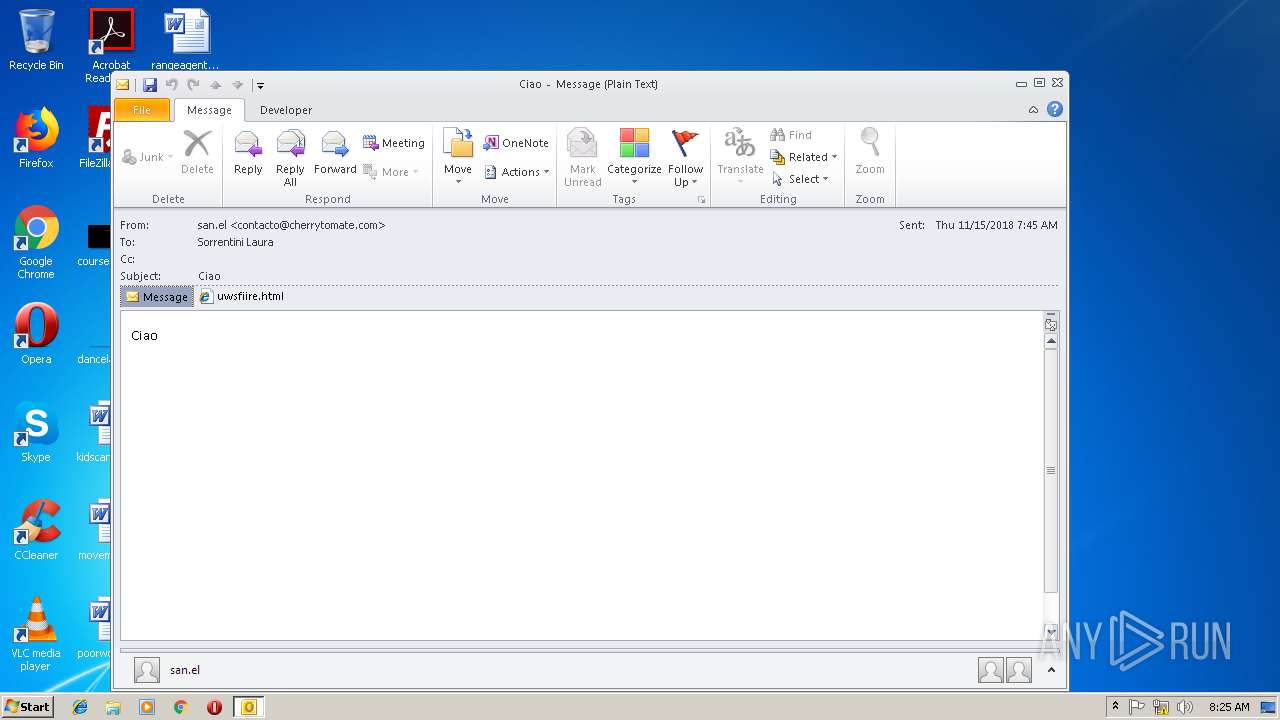
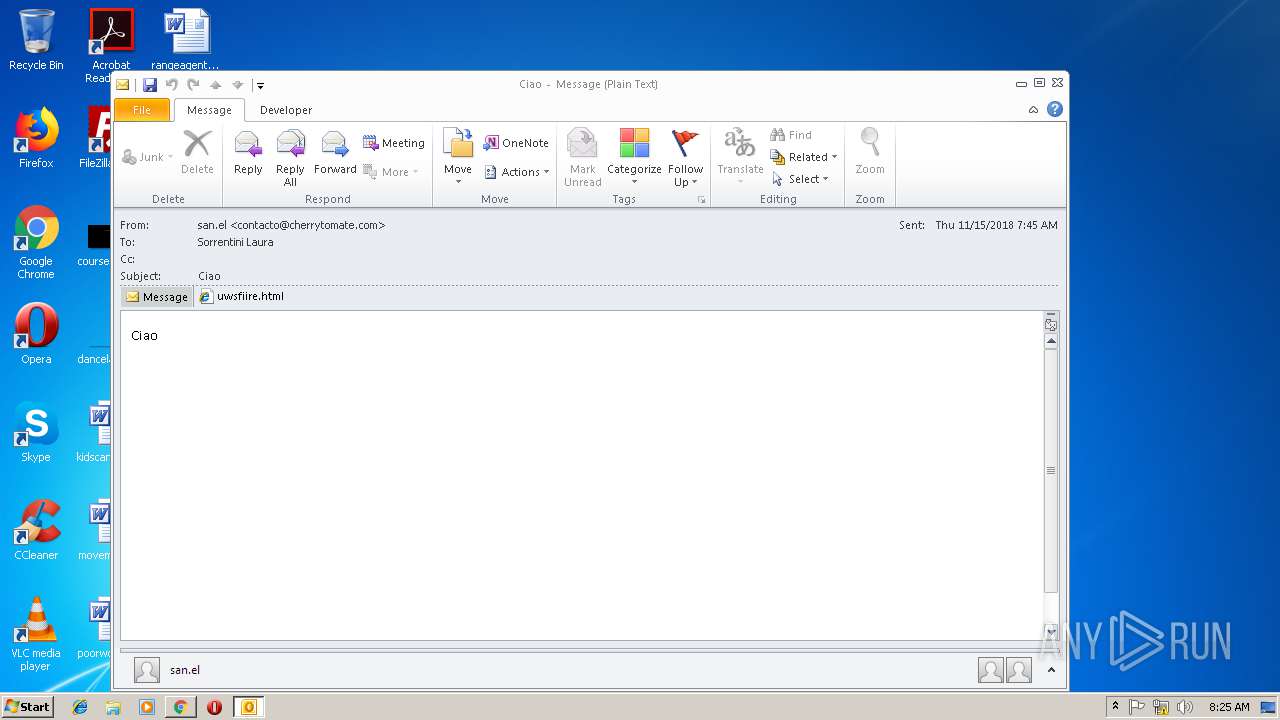
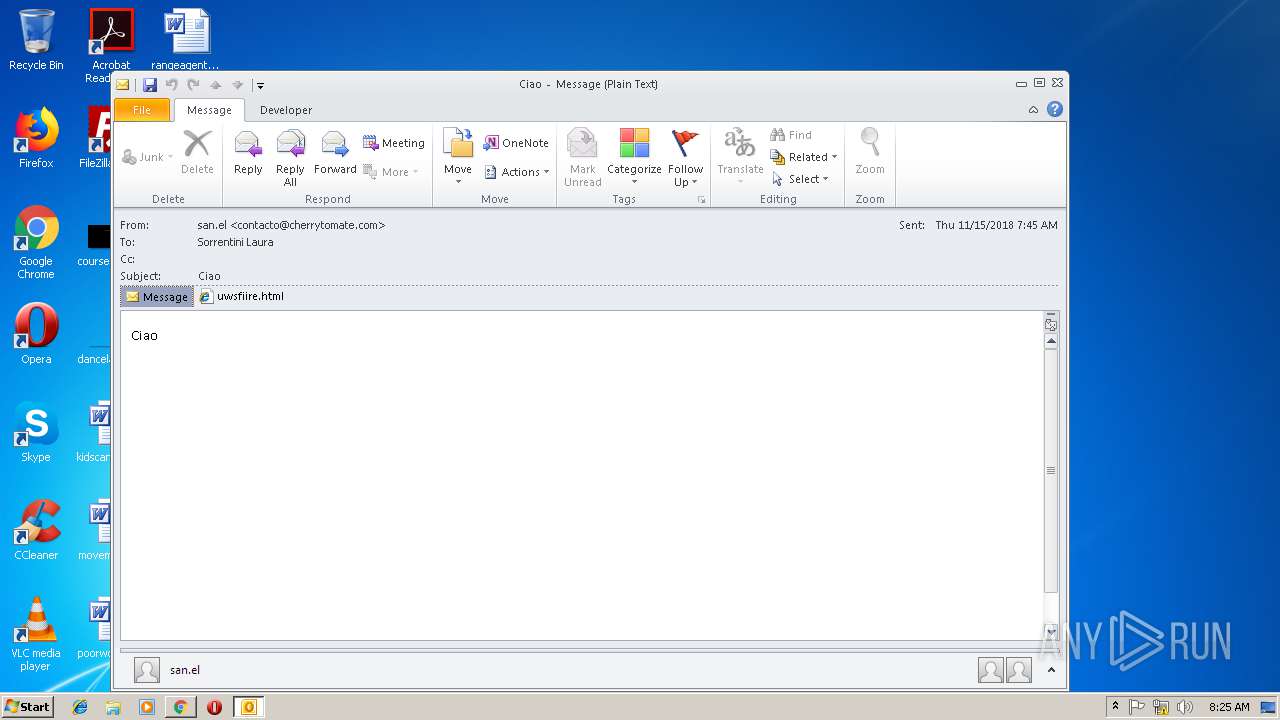
| File name: | Ciao.msg |
| Full analysis: | https://app.any.run/tasks/c360da71-fc26-4fa6-bb10-8d0cc50018cb |
| Verdict: | Malicious activity |
| Analysis date: | November 15, 2018, 08:24:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 2F62B28803131B2C7693FB6DA9C4B527 |
| SHA1: | 09E5F8709D37334A6C5EA93F2130F0A24B641F7E |
| SHA256: | 59B17BF372F3682C125097B088E1DA1A80C9DADA21BF1A3E64DBB440671B838B |
| SSDEEP: | 384:G9uvzvSef8zVAPqVvoYXZpE2kxoSnu34fzdfCc:GAfyAPGo0ryo36fCc |
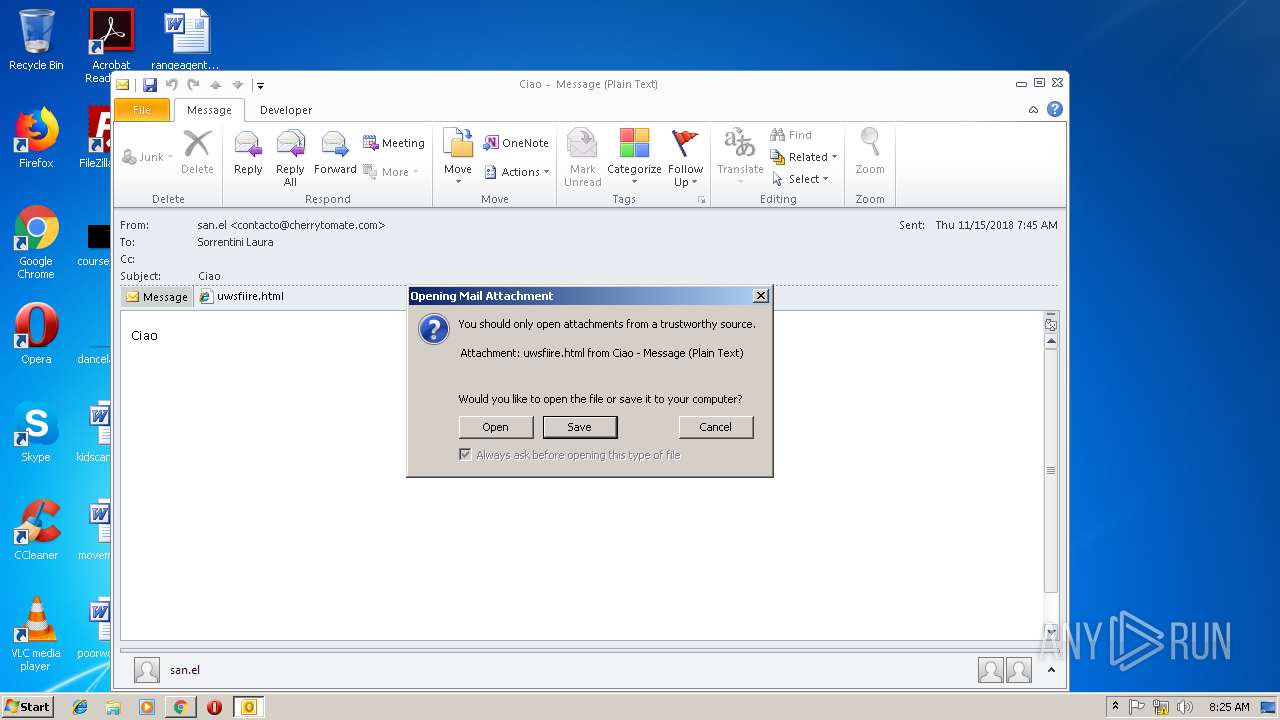
MALICIOUS
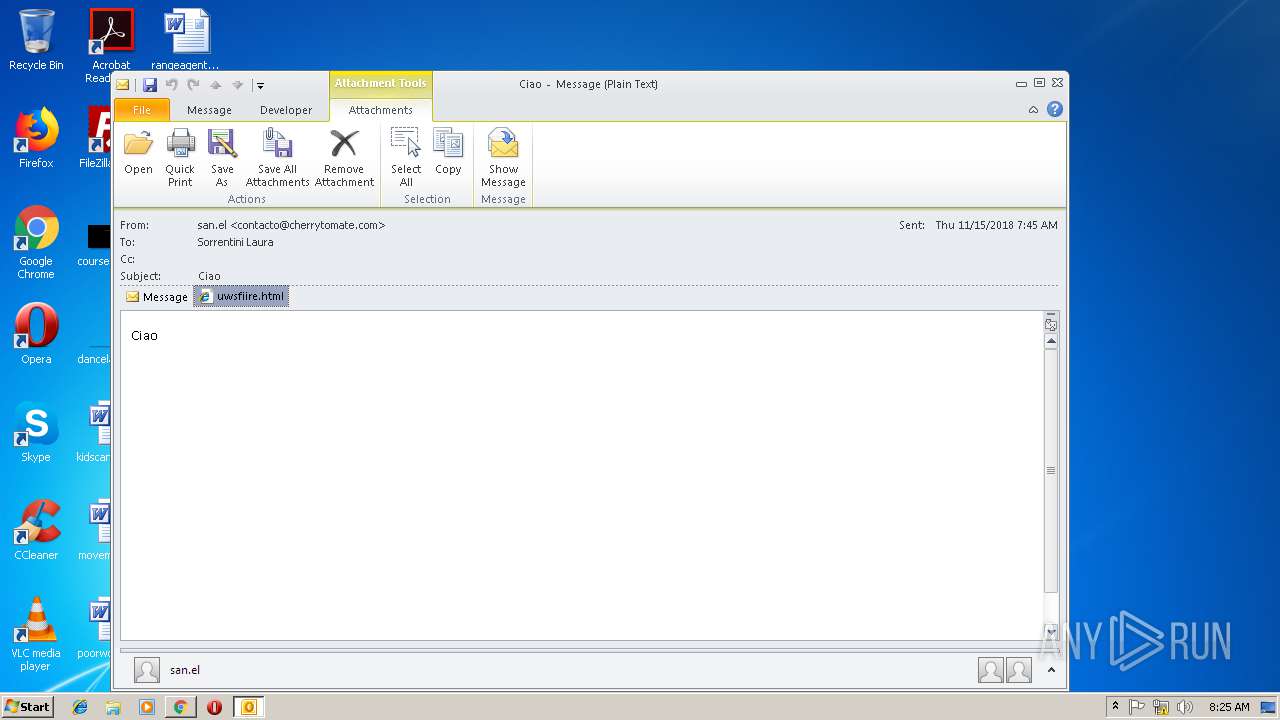
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 3216)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 3216)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3216)
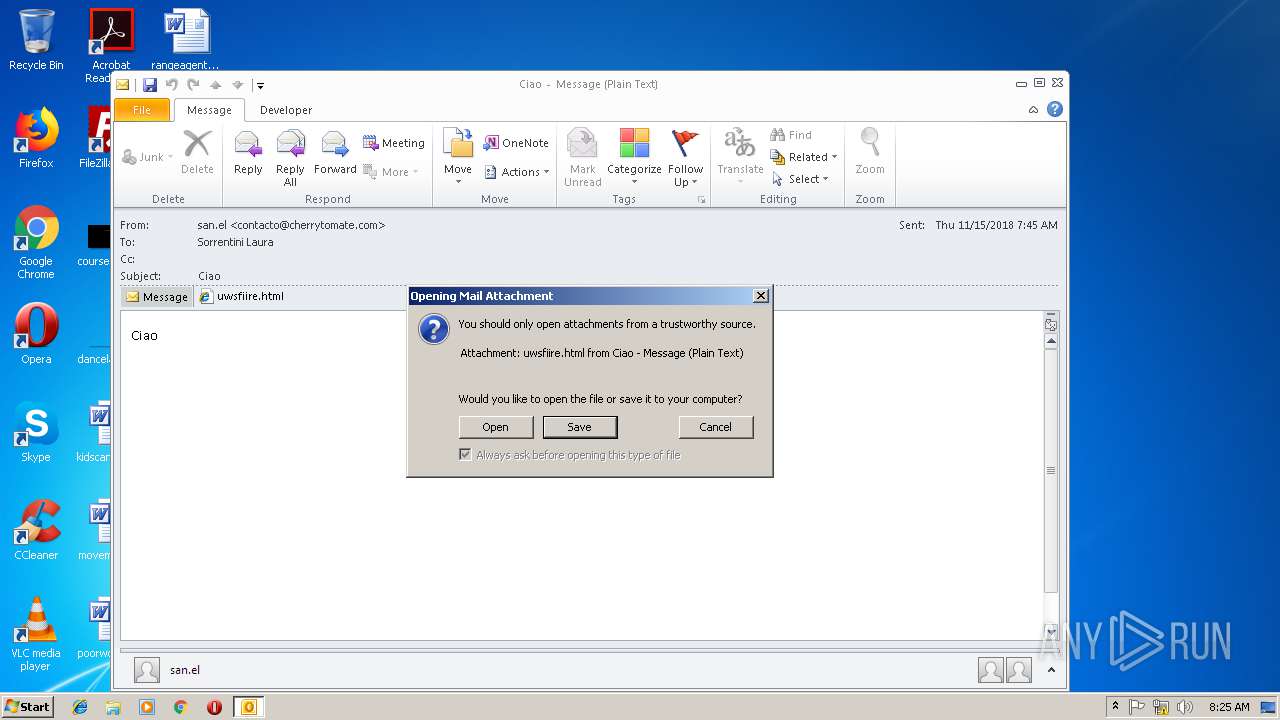
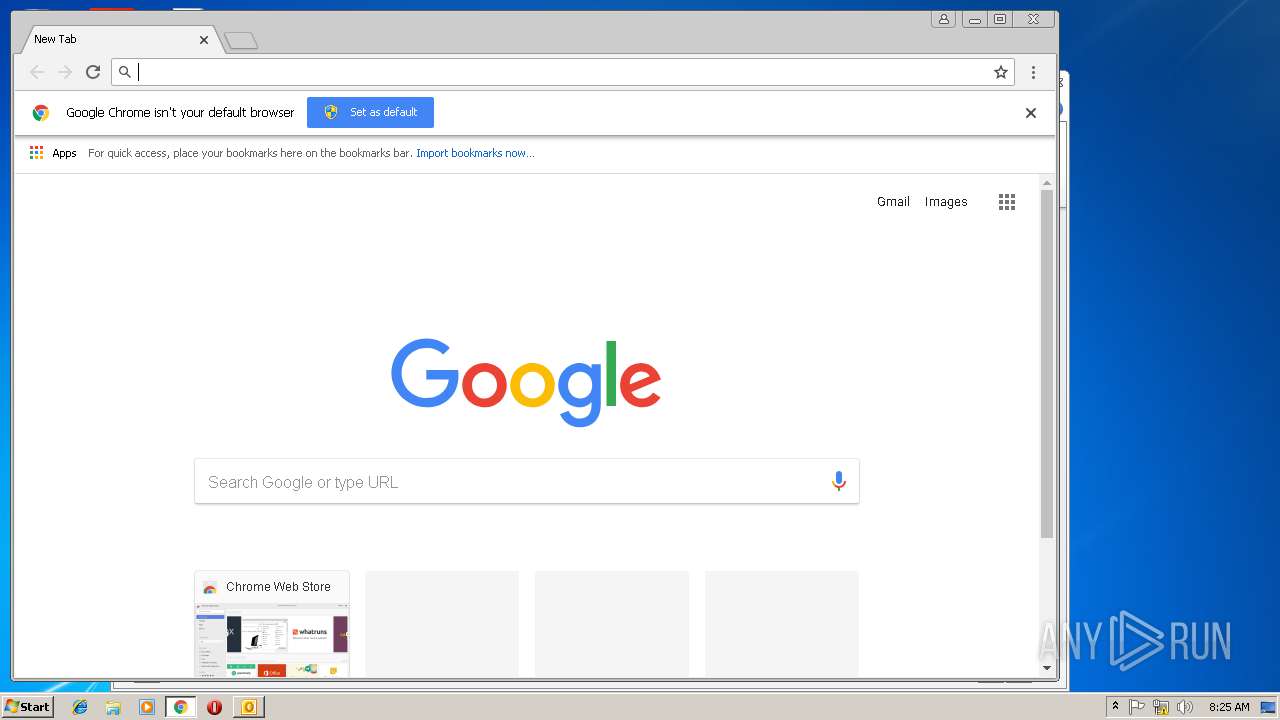
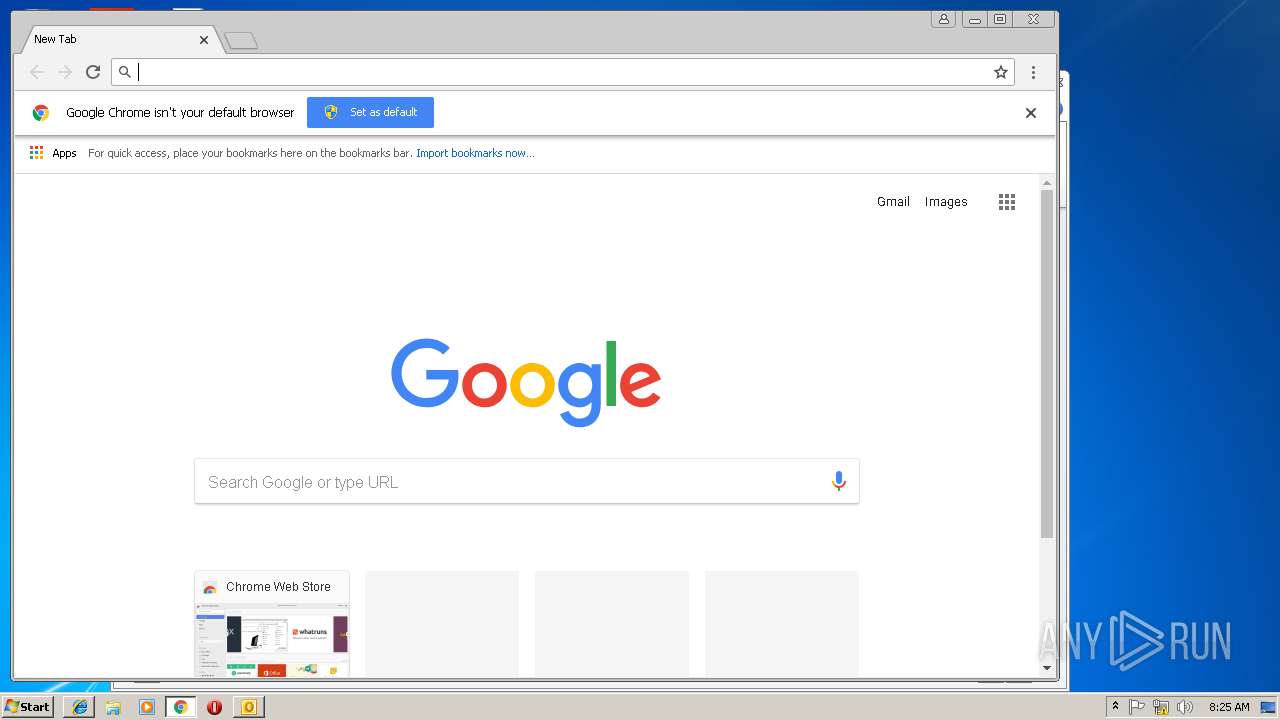
Starts Internet Explorer
- OUTLOOK.EXE (PID: 3216)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3988)
- iexplore.exe (PID: 2096)
Application launched itself
- iexplore.exe (PID: 3988)
- chrome.exe (PID: 2380)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3216)
Reads Internet Cache Settings
- iexplore.exe (PID: 3112)
- iexplore.exe (PID: 3988)
- iexplore.exe (PID: 3144)
Reads internet explorer settings
- iexplore.exe (PID: 3112)
- iexplore.exe (PID: 3144)
Reads settings of System Certificates
- iexplore.exe (PID: 3988)
- chrome.exe (PID: 2380)
Changes settings of System certificates
- chrome.exe (PID: 2380)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
51
Monitored processes
18
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,6181341452207726812,3238412102414240277,131072 --enable-features=PasswordImport --service-pipe-token=B477C705F61FC53C3663DDD21C977B85 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=B477C705F61FC53C3663DDD21C977B85 --renderer-client-id=3 --mojo-platform-channel-handle=2076 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1808 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,6181341452207726812,3238412102414240277,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7FD0E32D1F8695AD48E5891C0F7EAA97 --mojo-platform-channel-handle=1152 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,6181341452207726812,3238412102414240277,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=EB653CD2EFC8C2E91BA70FDCFE0FAD82 --mojo-platform-channel-handle=3916 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
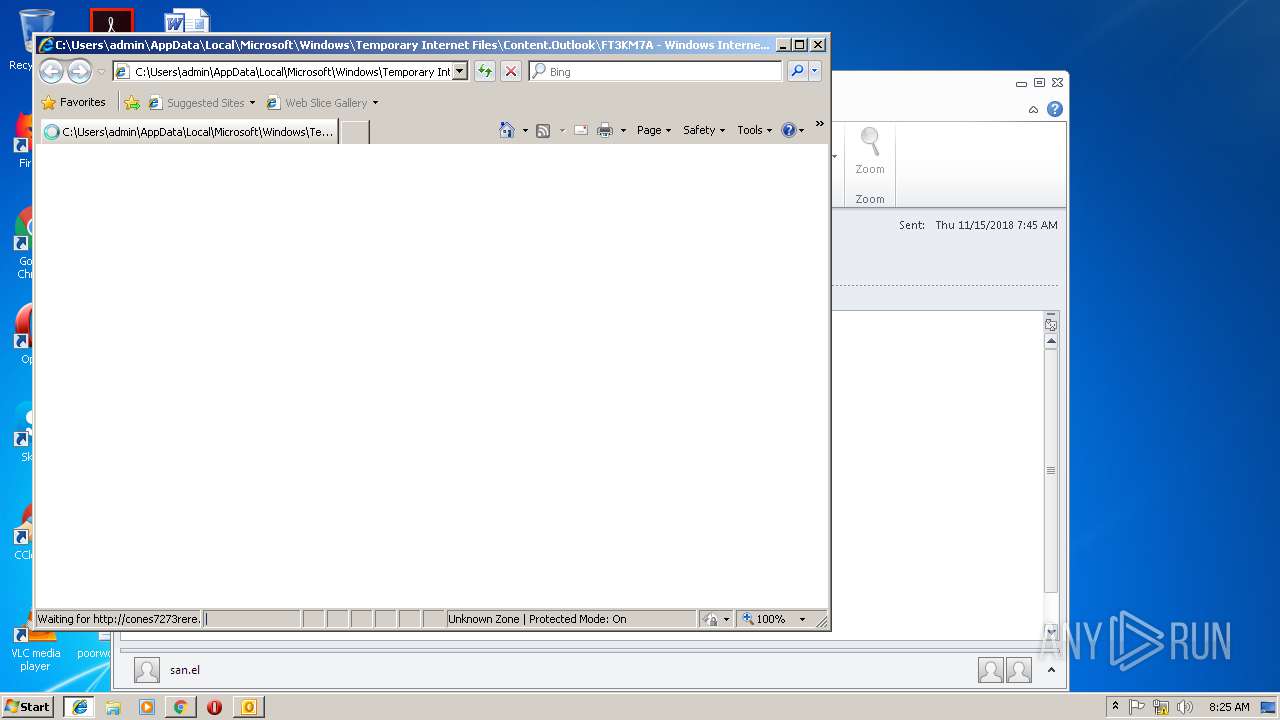
| 2096 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\FT3KM7A8\uwsfiire.html | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,6181341452207726812,3238412102414240277,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=A4361667DBD5251280727A74F0DA9B11 --mojo-platform-channel-handle=3804 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2060 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,6181341452207726812,3238412102414240277,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=BD457E9C7D90D9149326D0723B070E78 --mojo-platform-channel-handle=936 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,6181341452207726812,3238412102414240277,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=C63259C42EDD441FCF1EE3AF31CC6D14 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=C63259C42EDD441FCF1EE3AF31CC6D14 --renderer-client-id=6 --mojo-platform-channel-handle=3580 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3112 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3988 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 968
Read events
2 371
Write events
570
Delete events
27
Modification events
| (PID) Process: | (3216) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3216) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3216) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | =?# |
Value: 3D3F2300900C0000010000000000000000000000 | |||
| (PID) Process: | (3216) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 900C0000D0606CB2BC7CD40100000000 | |||
| (PID) Process: | (3216) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (3216) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 219778560 | |||
| (PID) Process: | (3216) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (3216) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (3216) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (3216) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1299120149 | |||
Executable files
0
Suspicious files
85
Text files
203
Unknown types
25
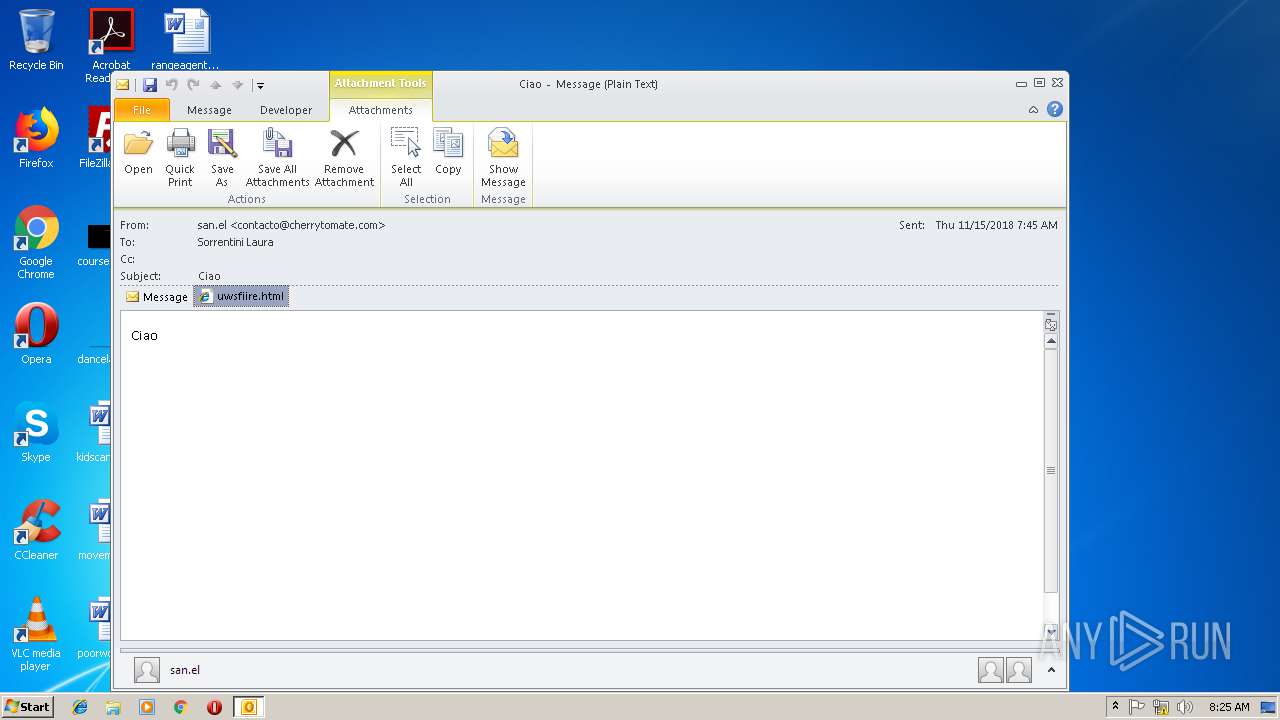
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3216 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR8B3D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3216 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\FT3KM7A8\uwsfiire (2).html\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3988 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3988 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
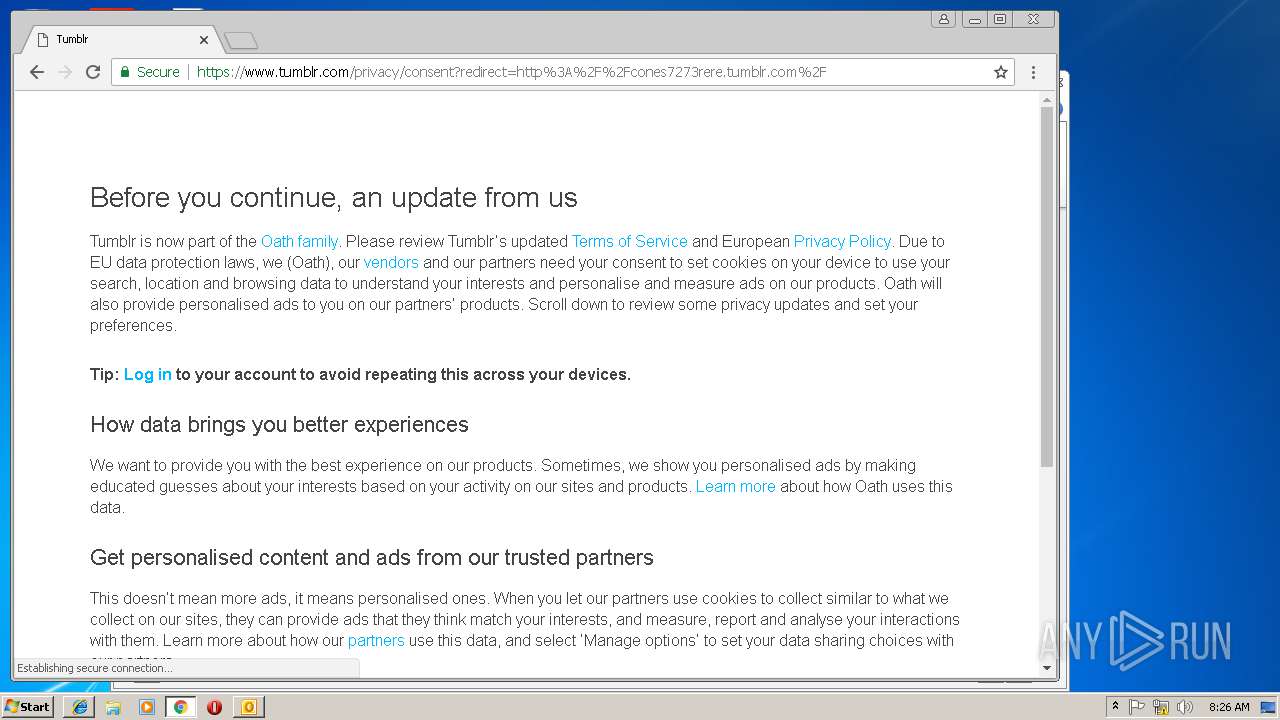
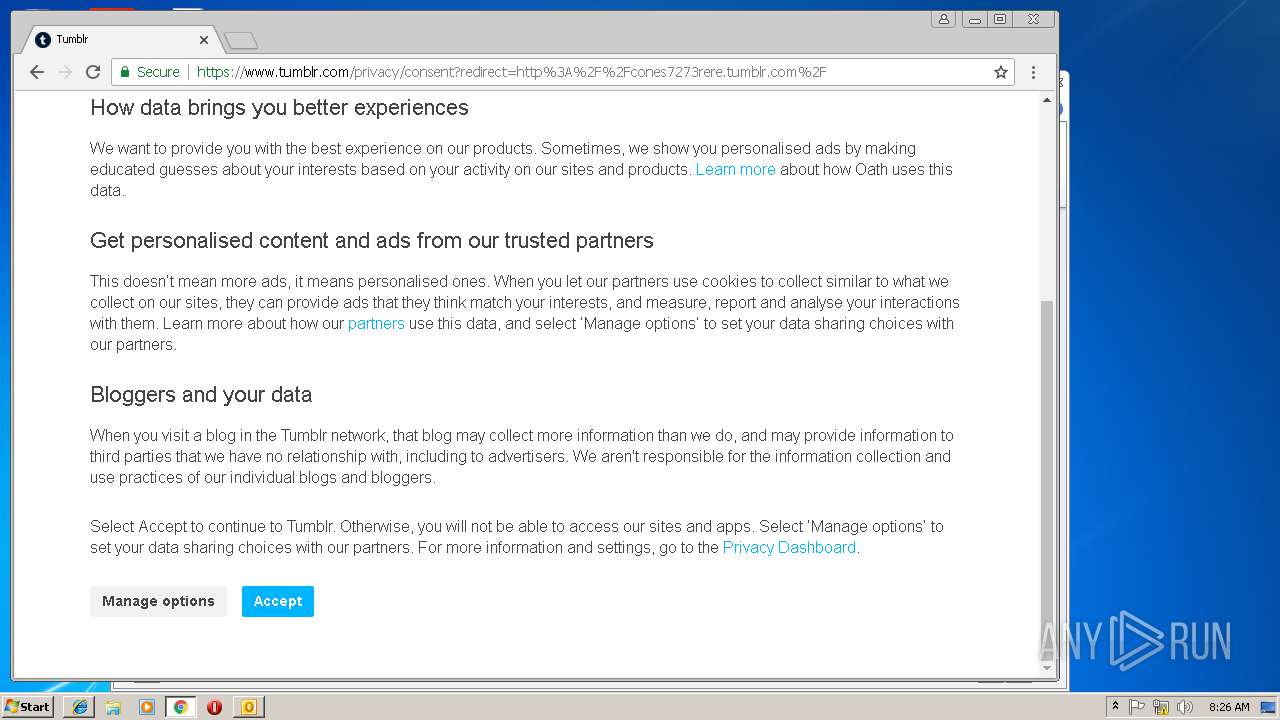
| 3112 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\consent[1].txt | — | |
MD5:— | SHA256:— | |||
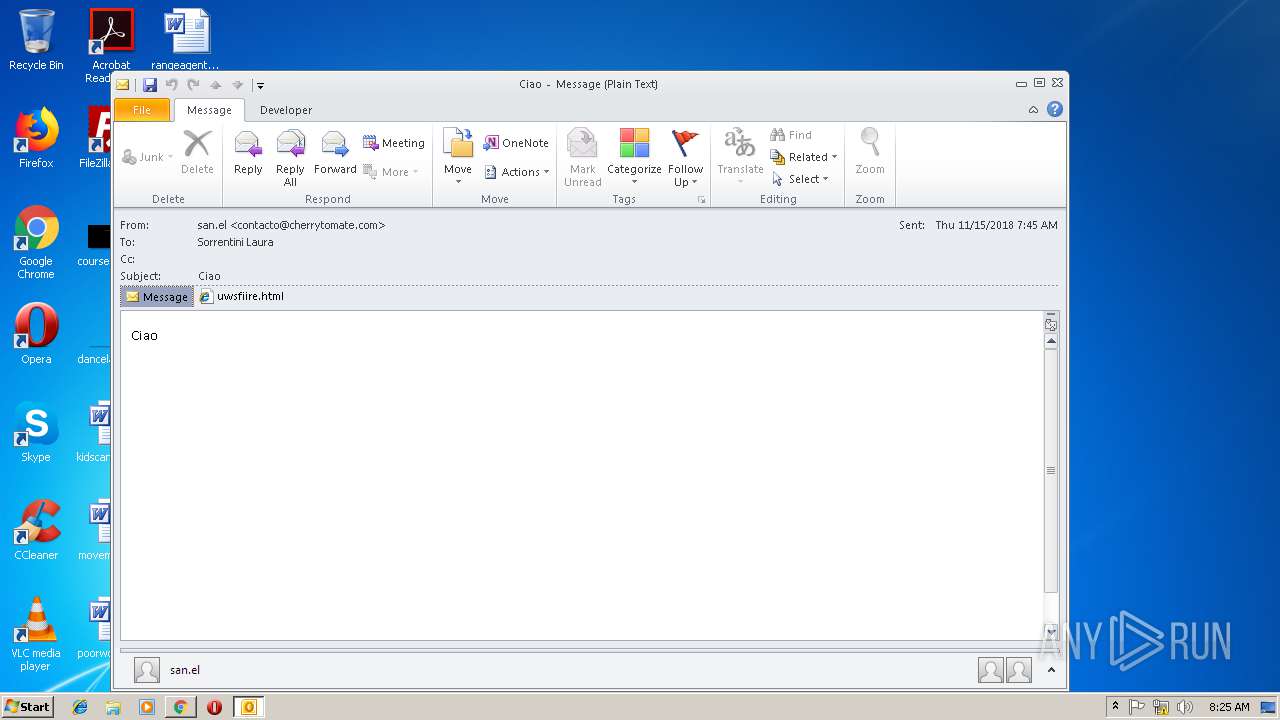
| 3216 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\FT3KM7A8\uwsfiire.html | html | |
MD5:— | SHA256:— | |||
| 3216 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3216 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\FT3KM7A8\uwsfiire (2).html | html | |
MD5:— | SHA256:— | |||
| 3112 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\consent[1].htm | html | |
MD5:— | SHA256:— | |||
| 3112 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\ie[1].css | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
142
TCP/UDP connections
91
DNS requests
43
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3216 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
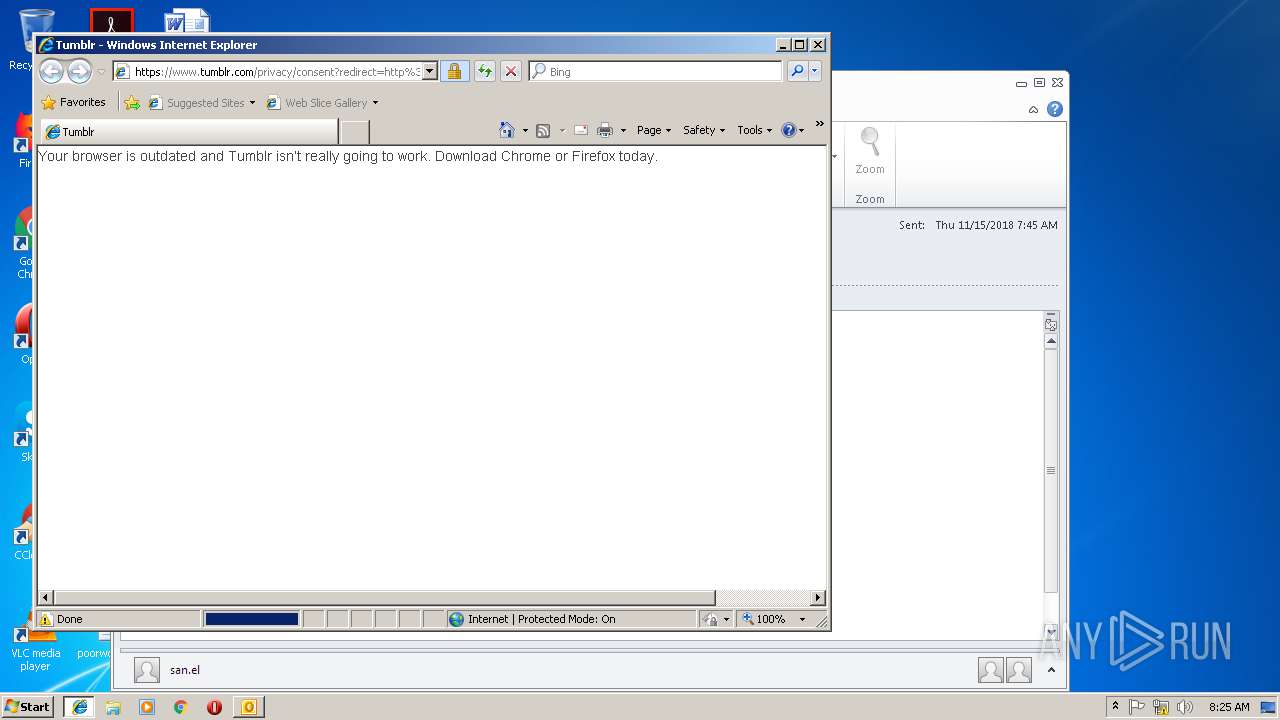
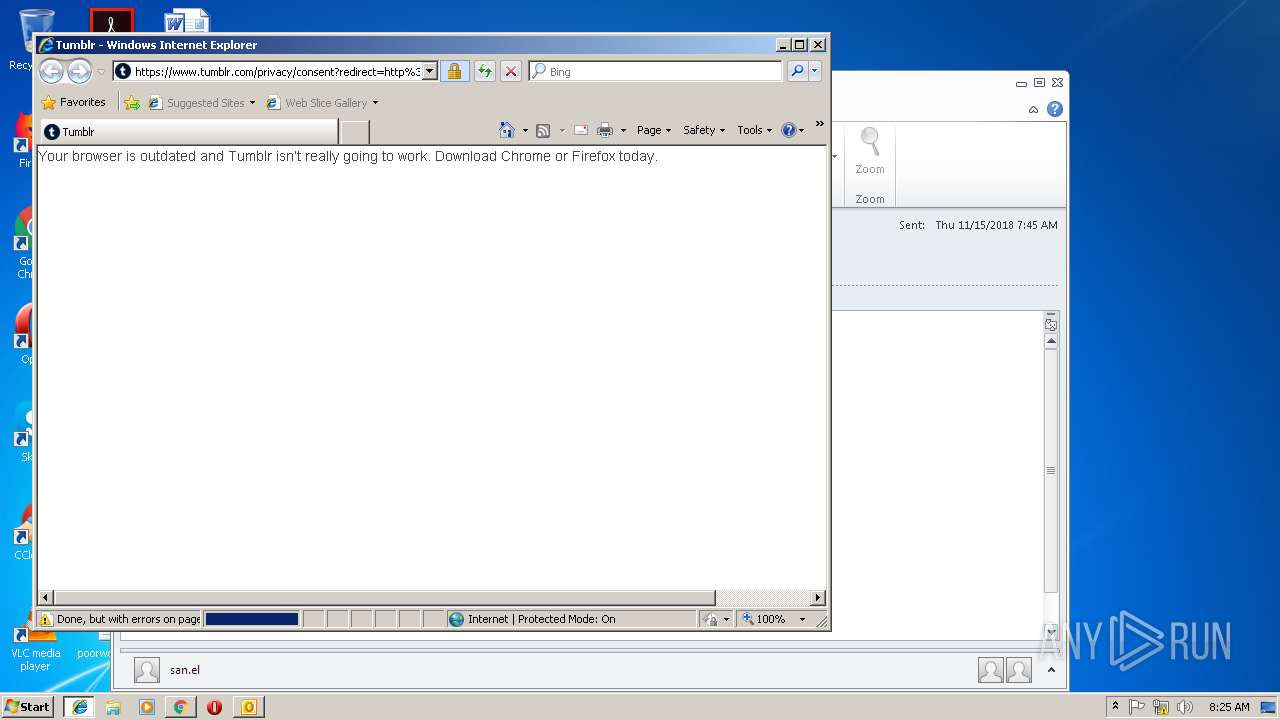
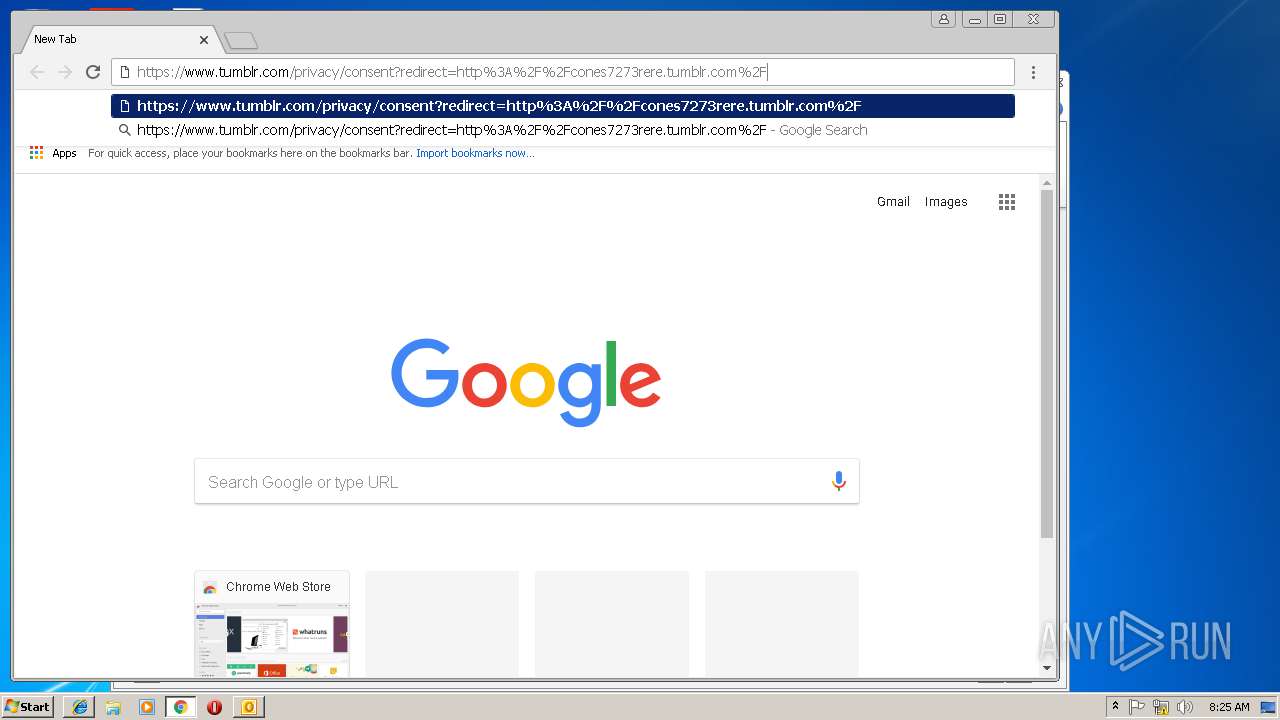
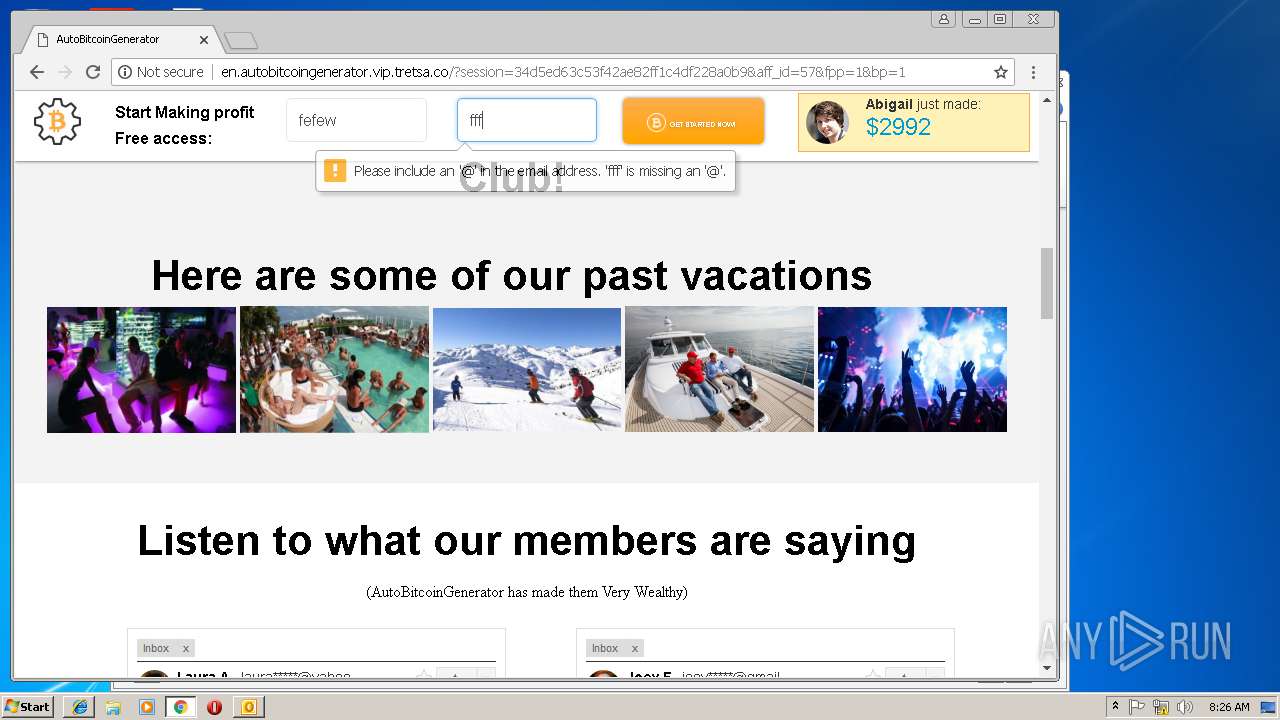
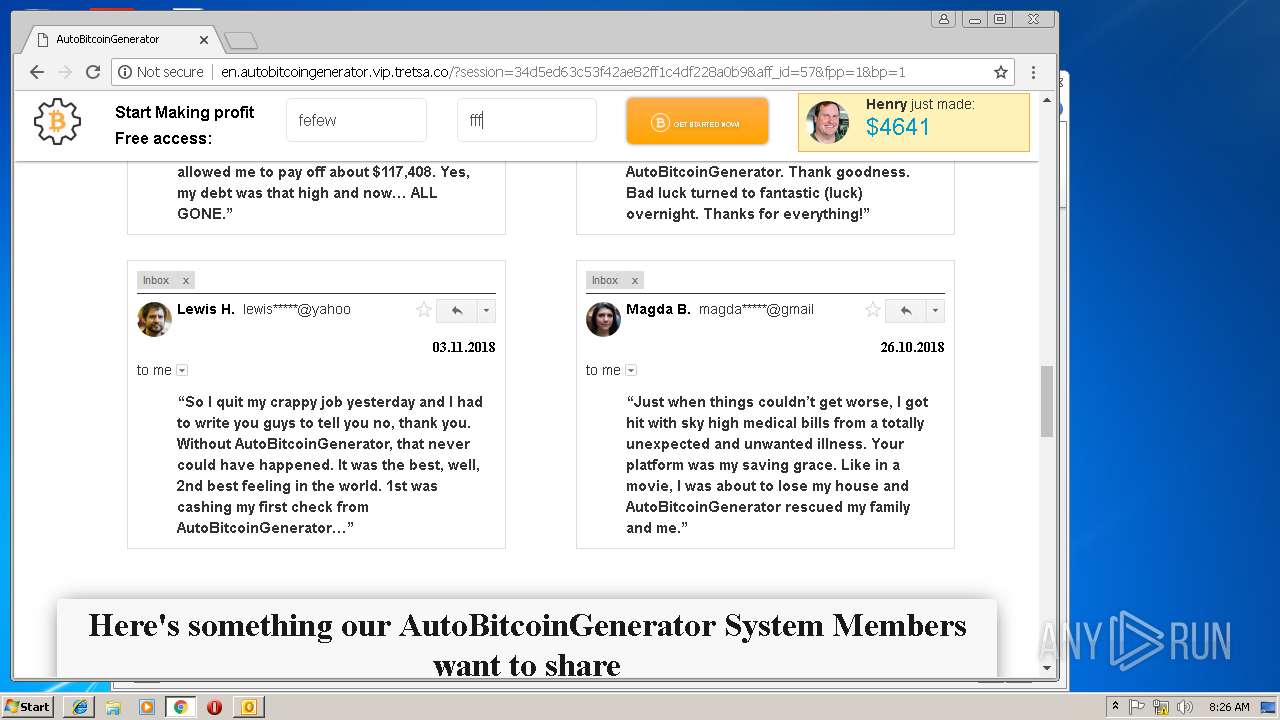
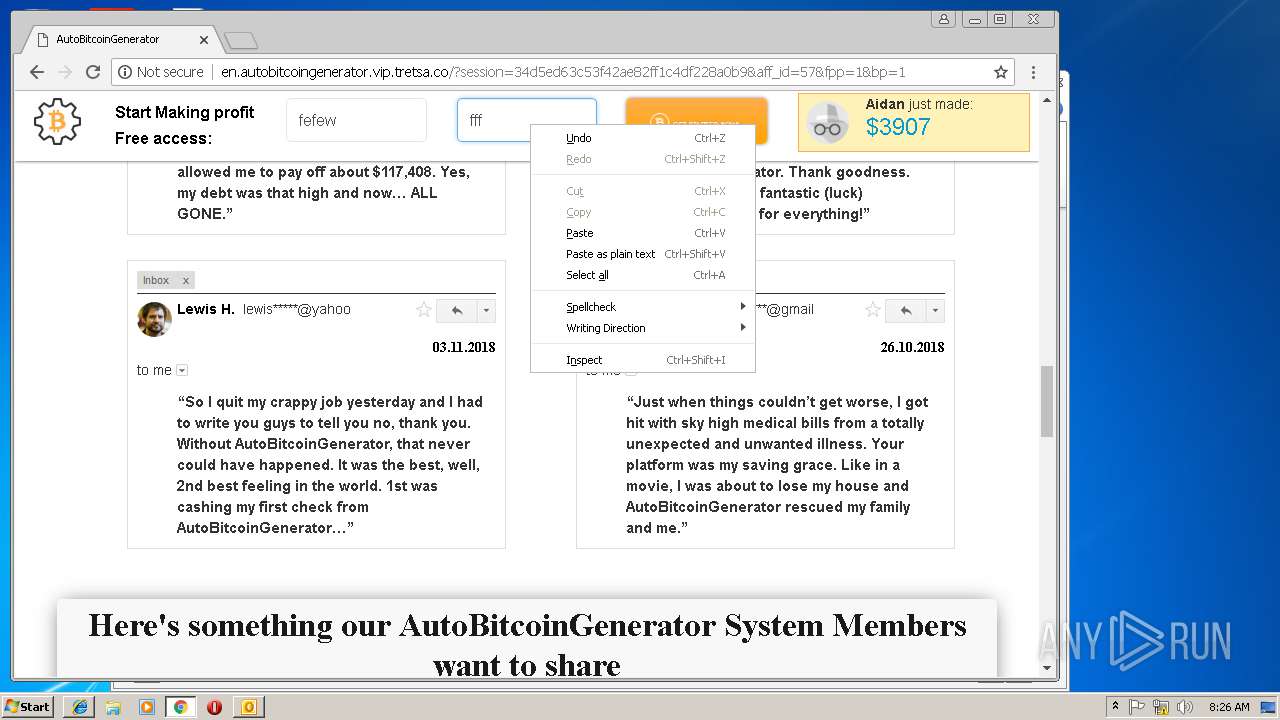
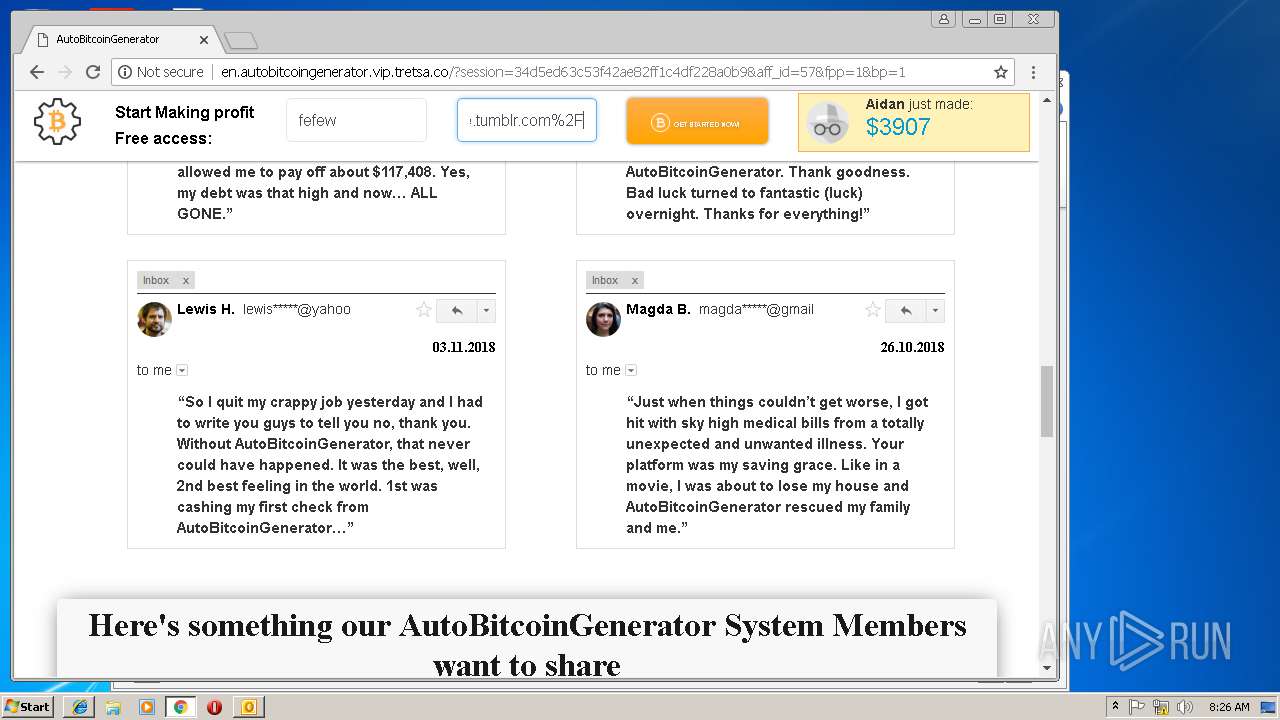
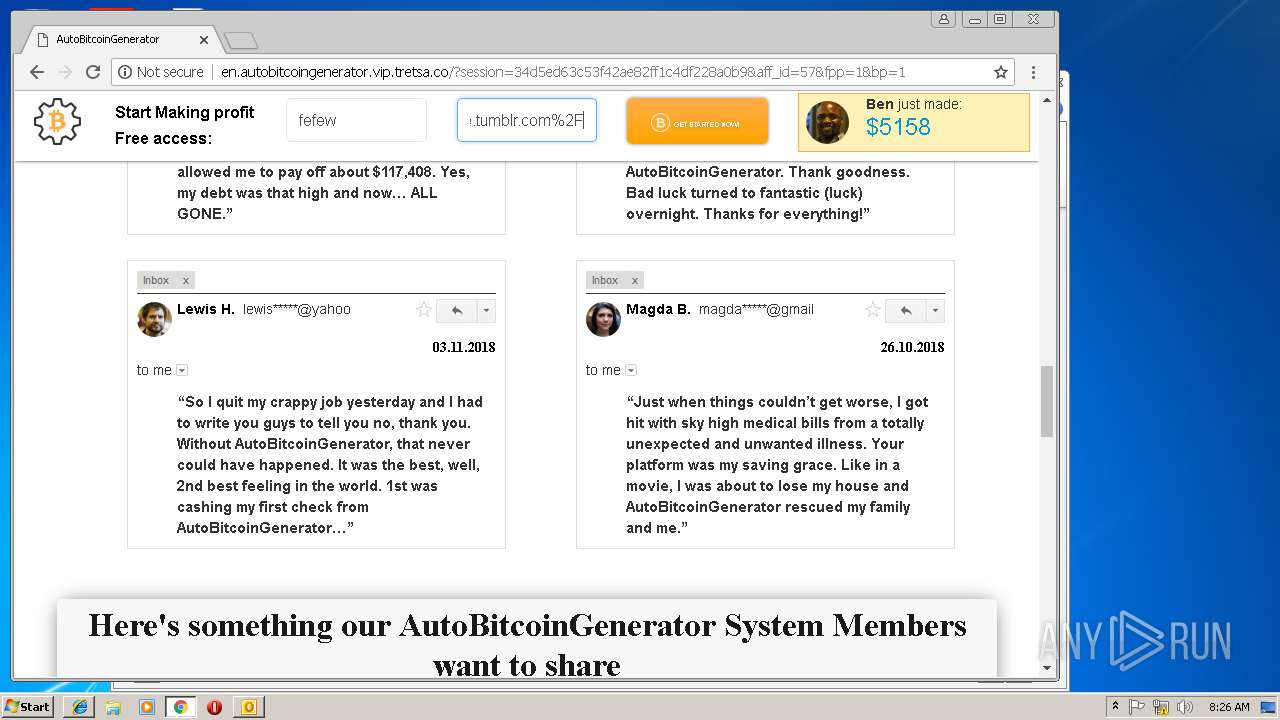
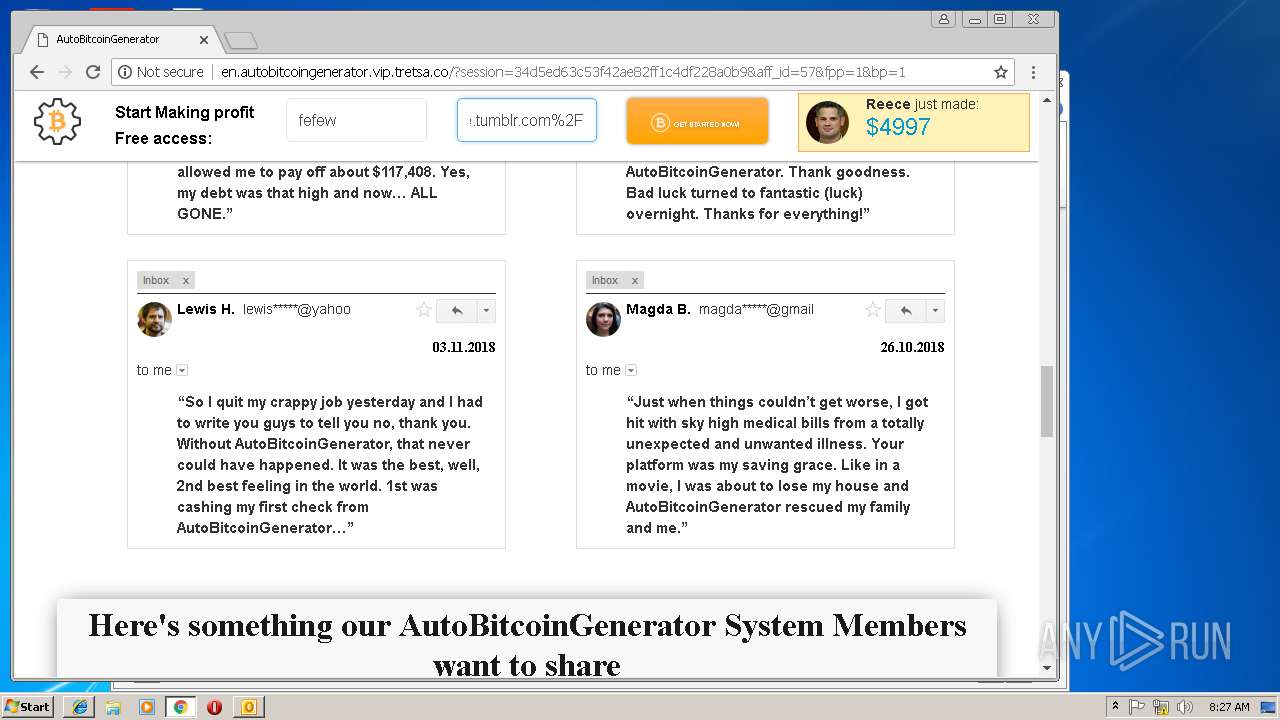
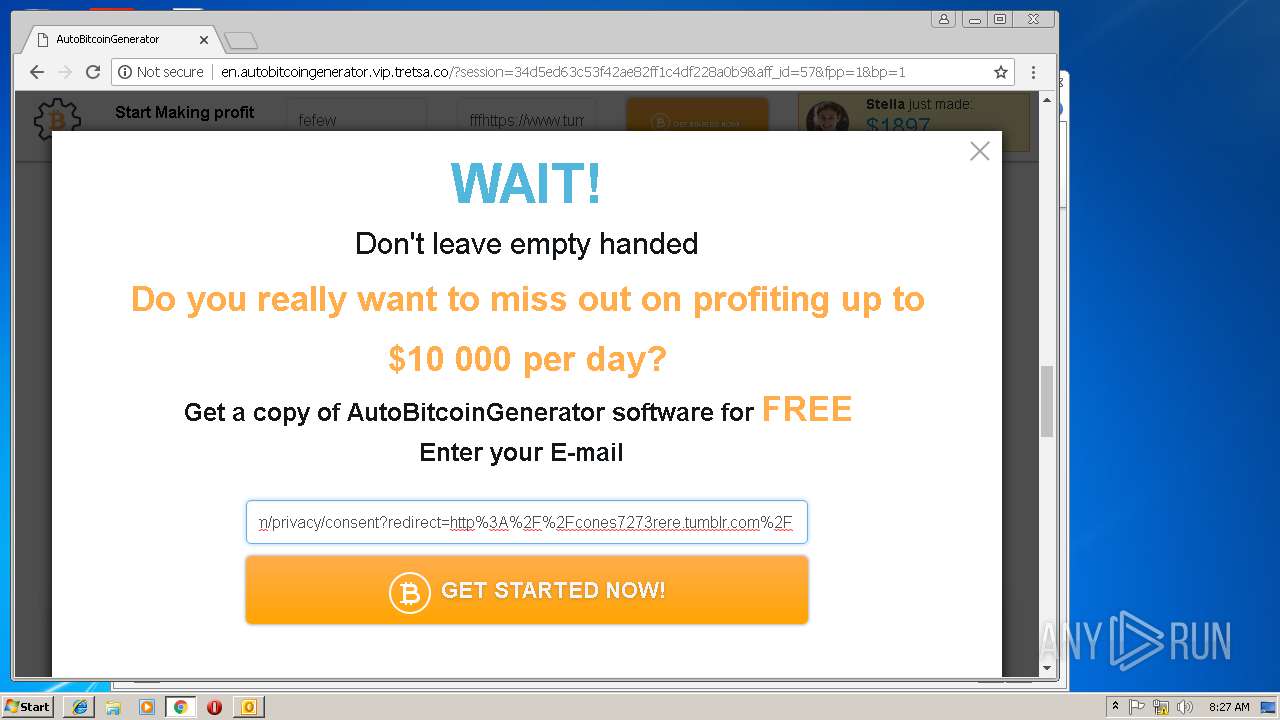
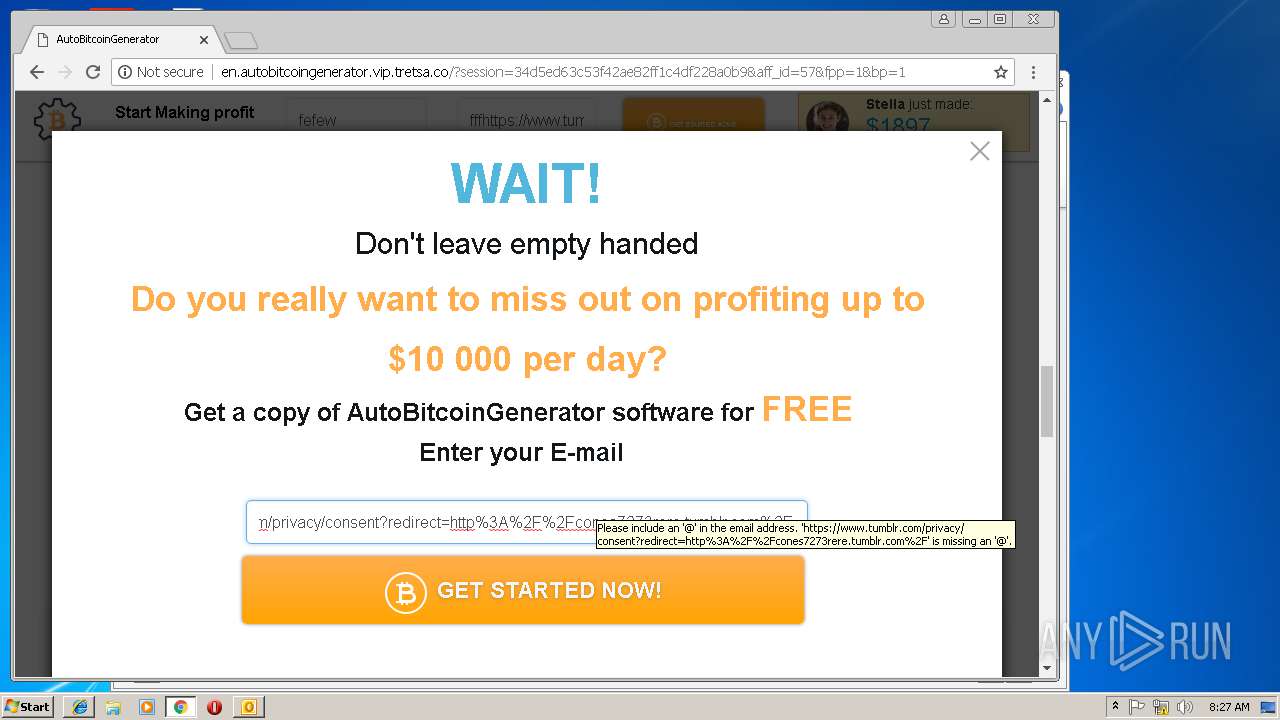
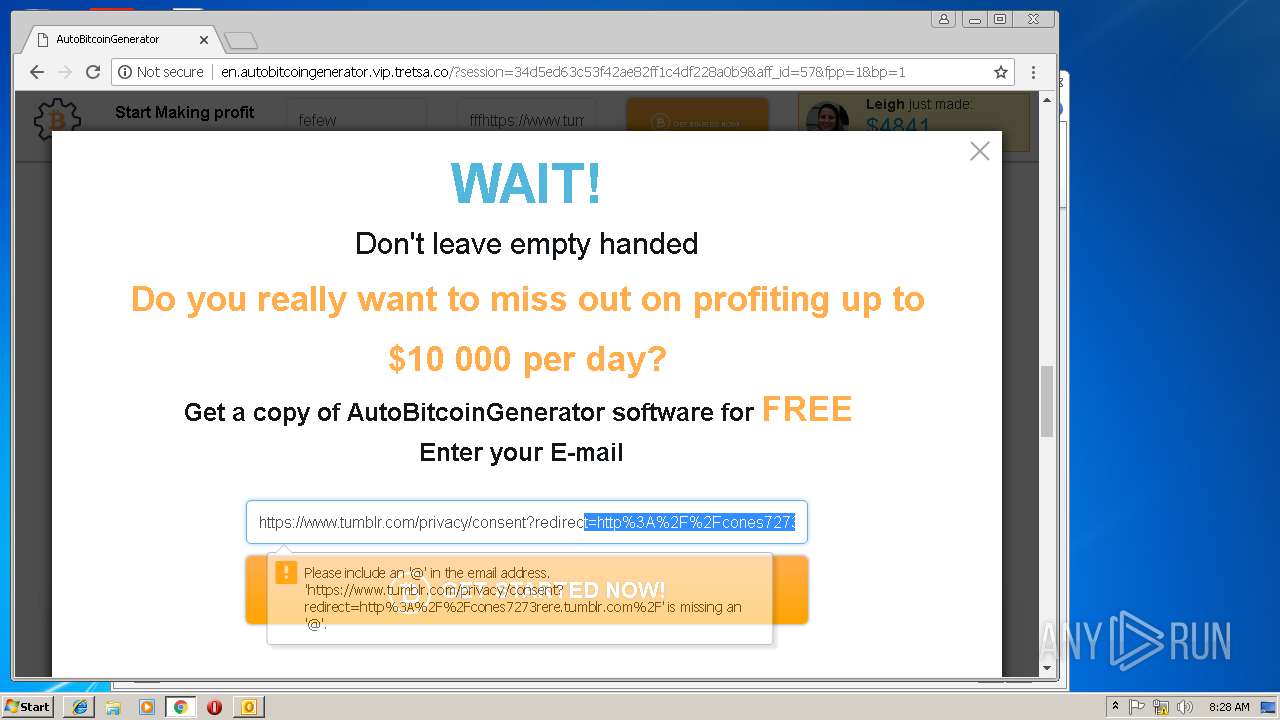
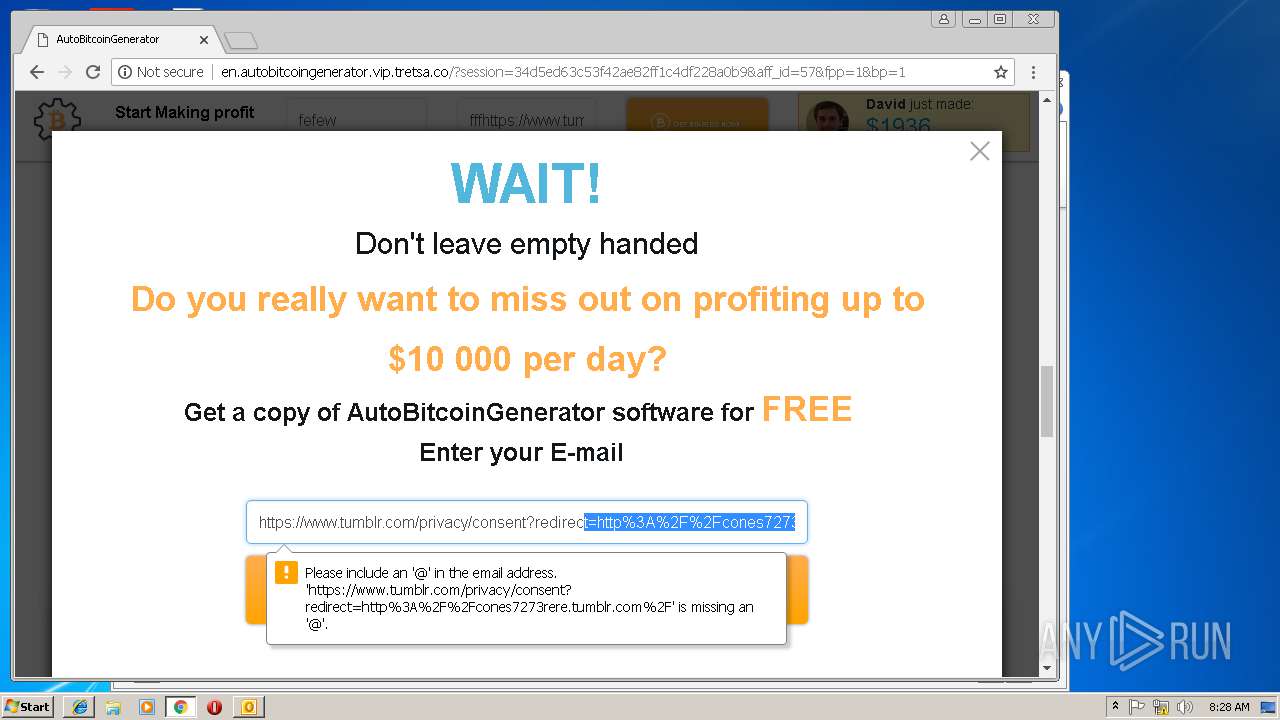
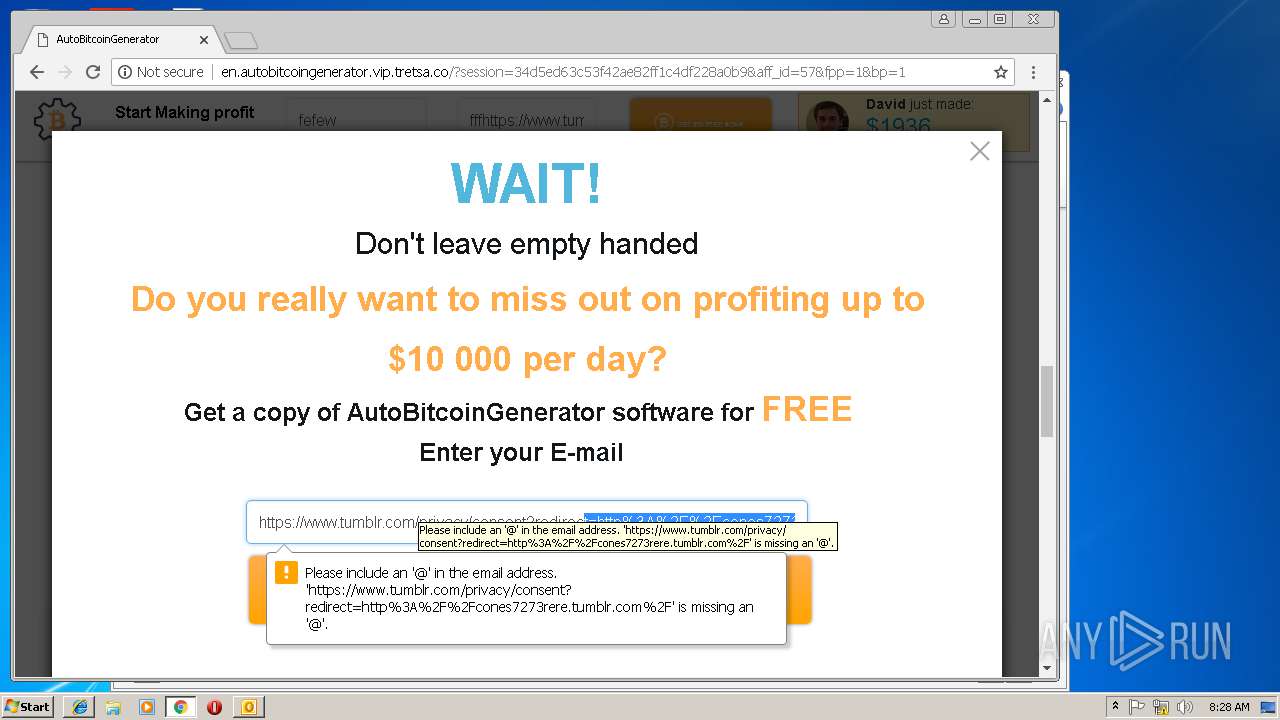
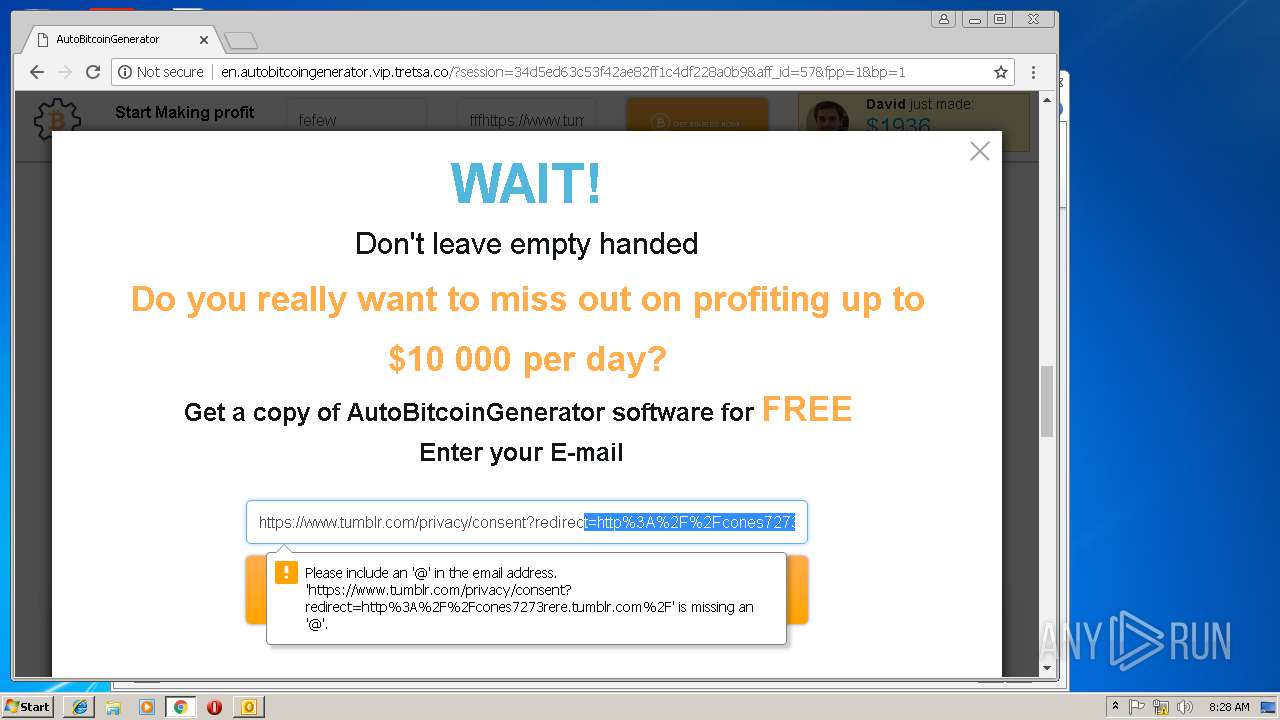
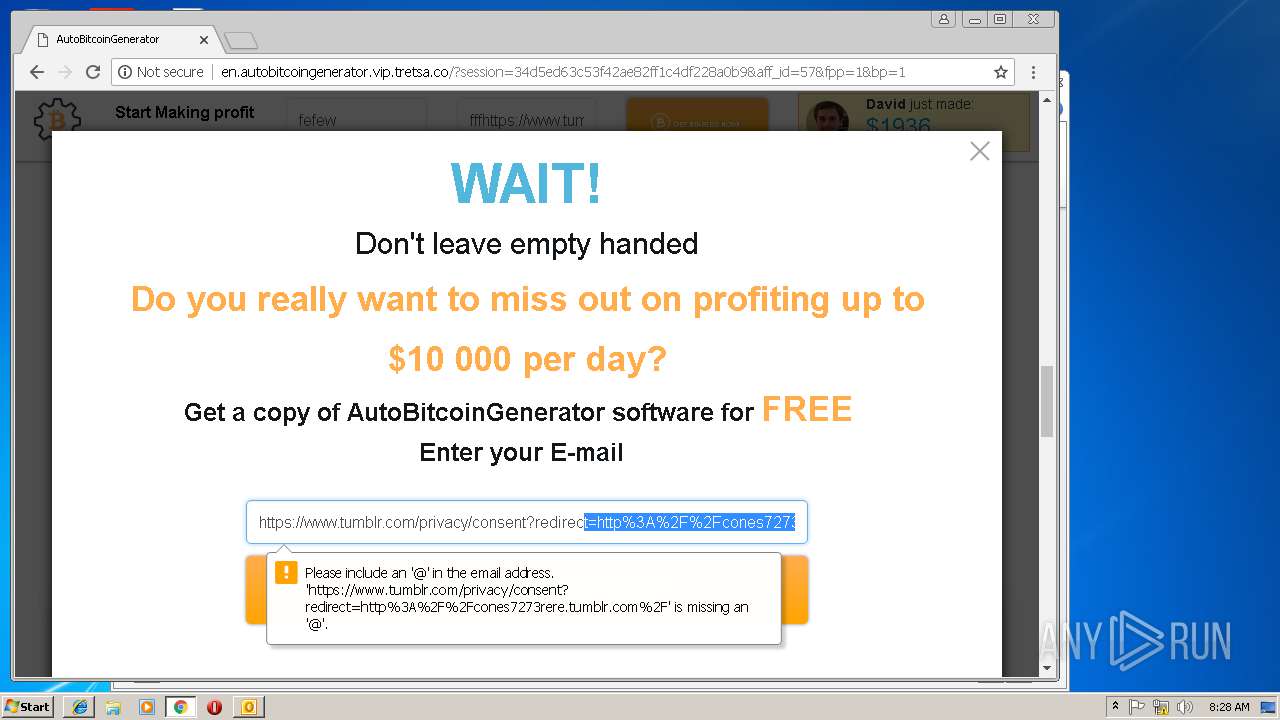
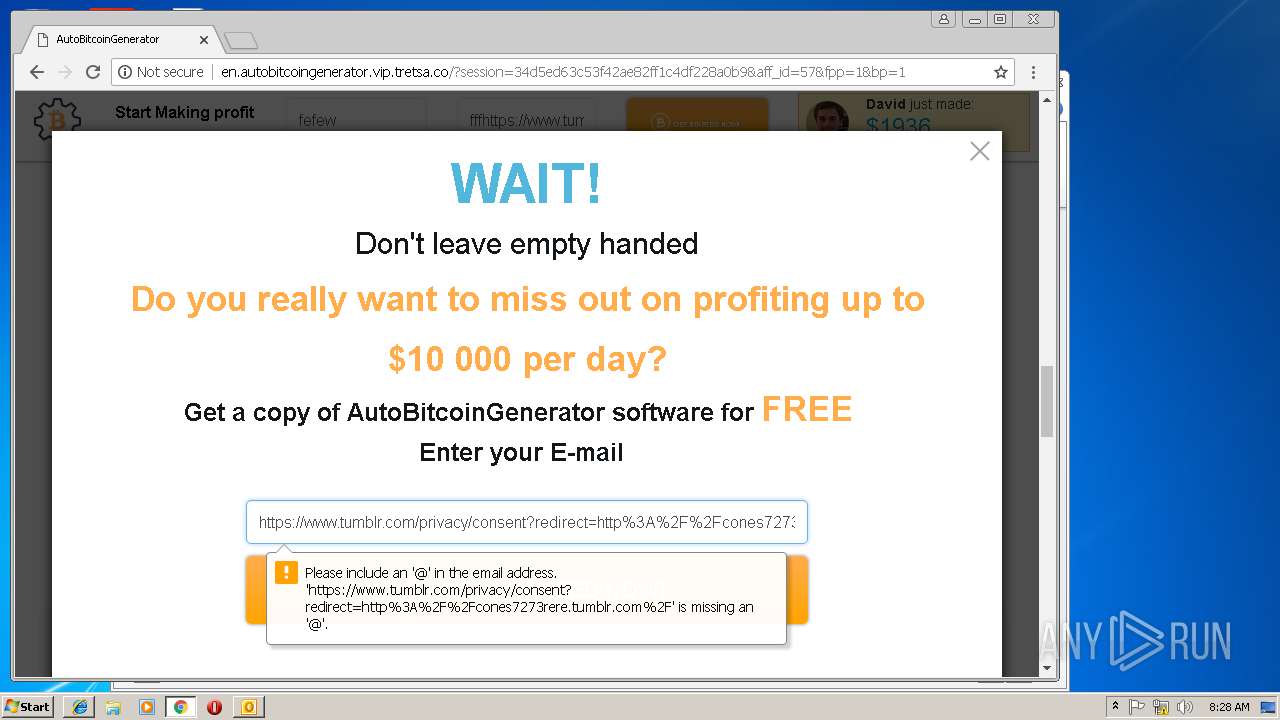
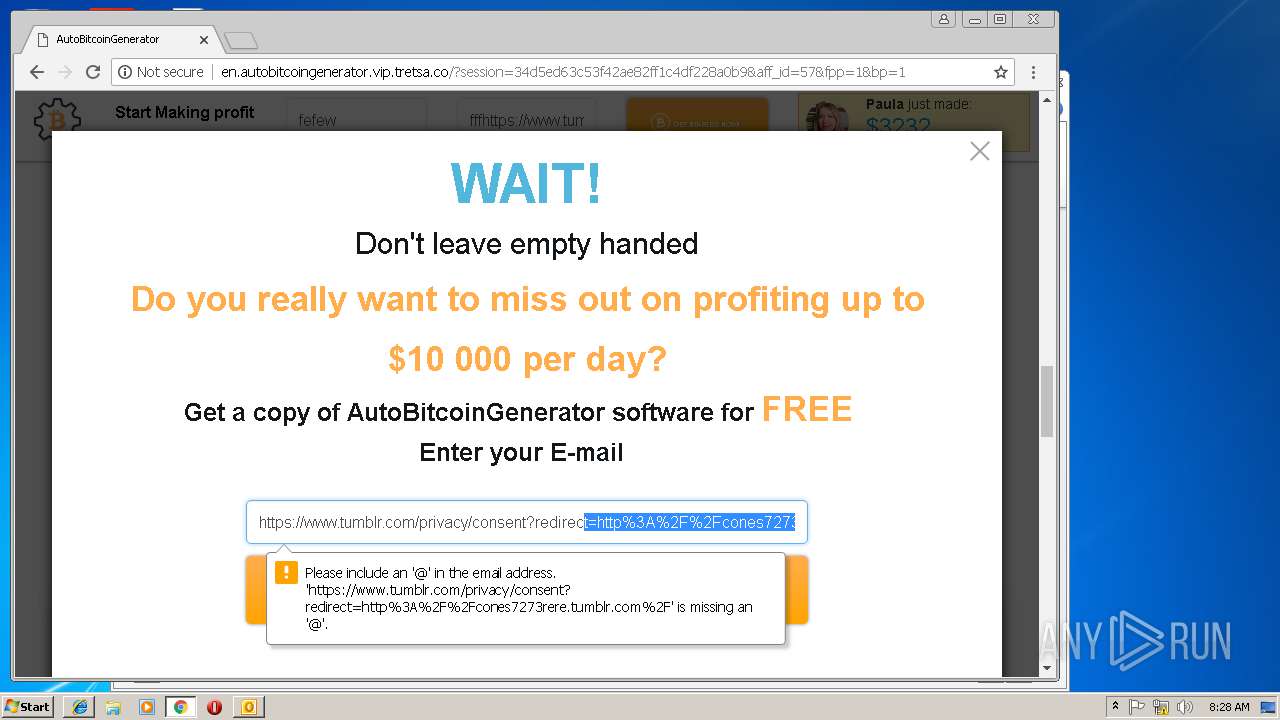
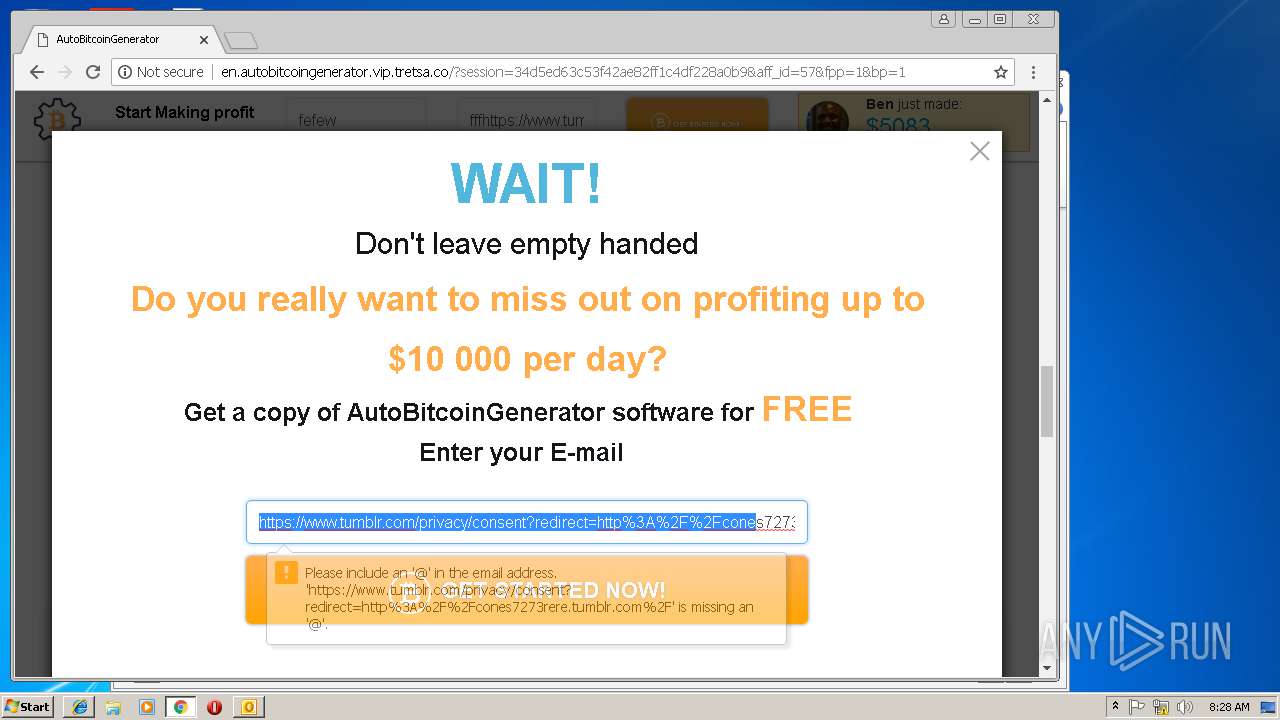
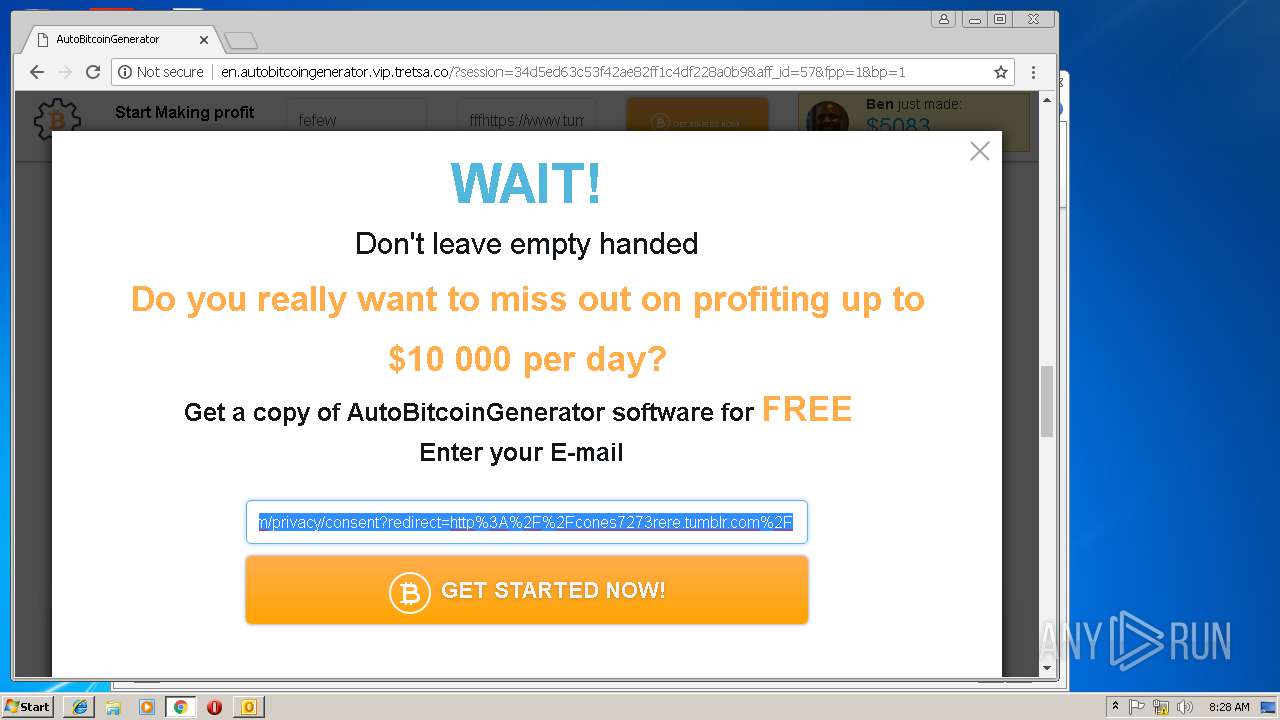
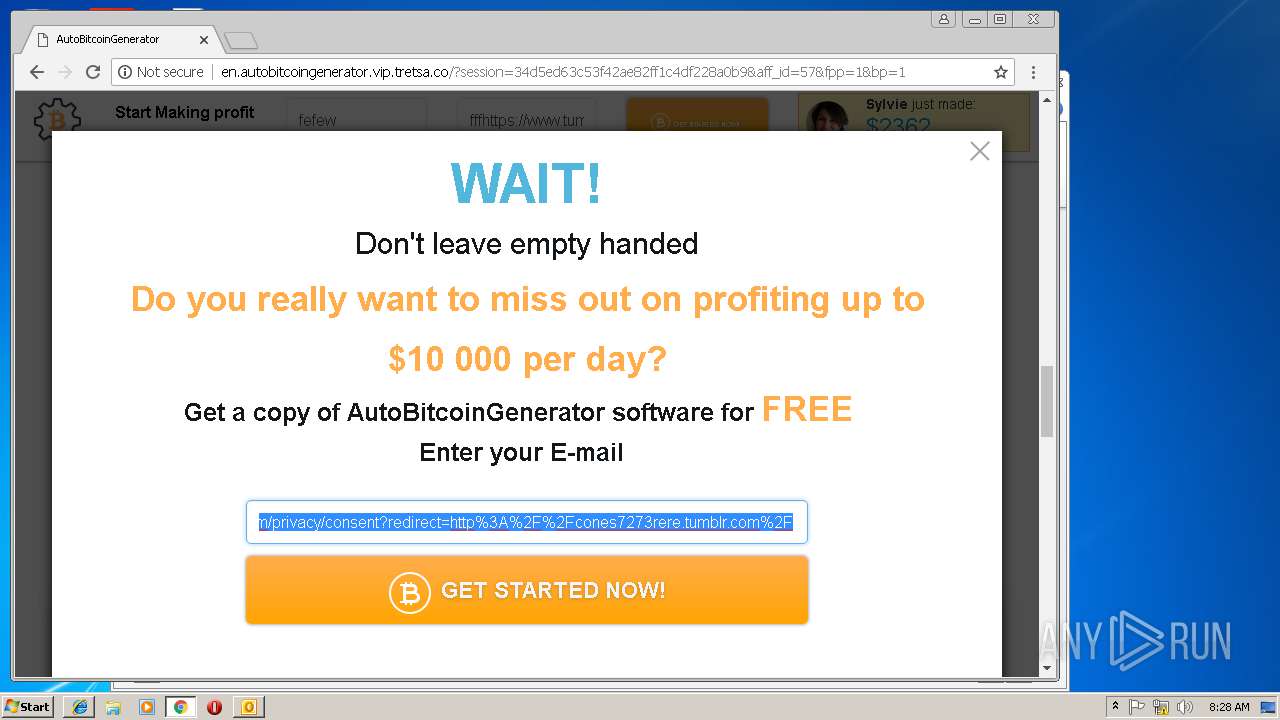
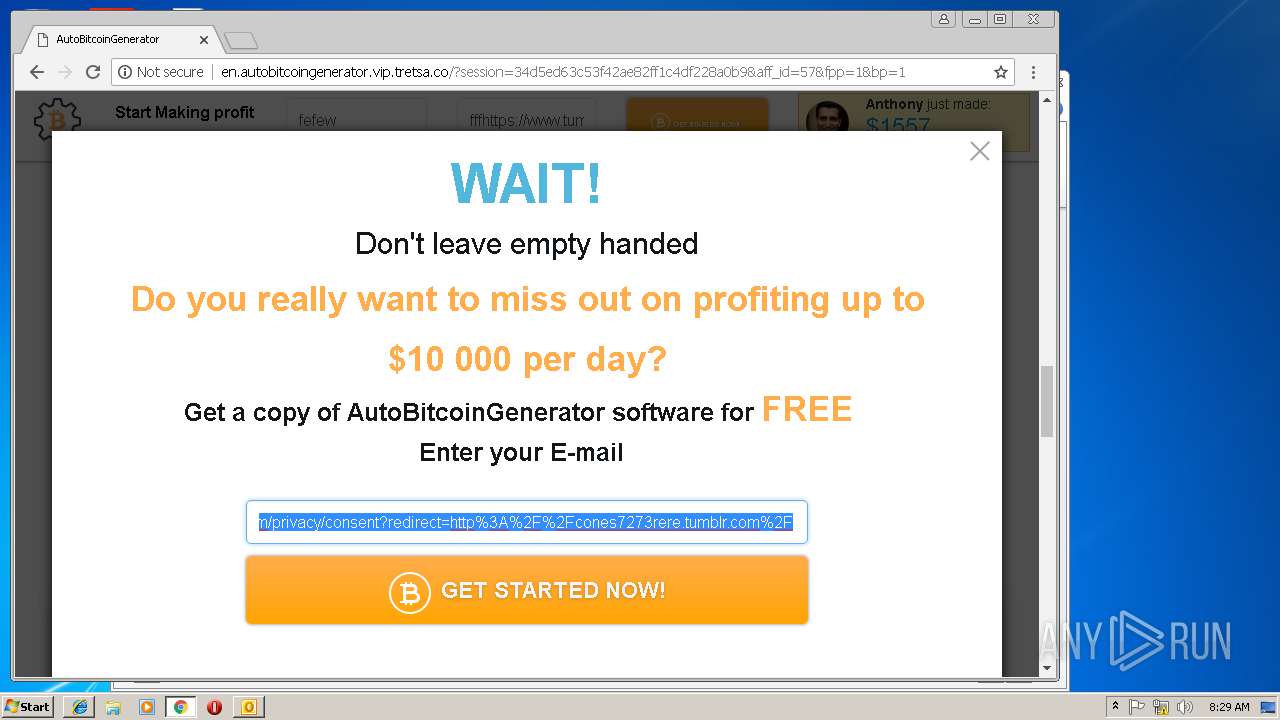
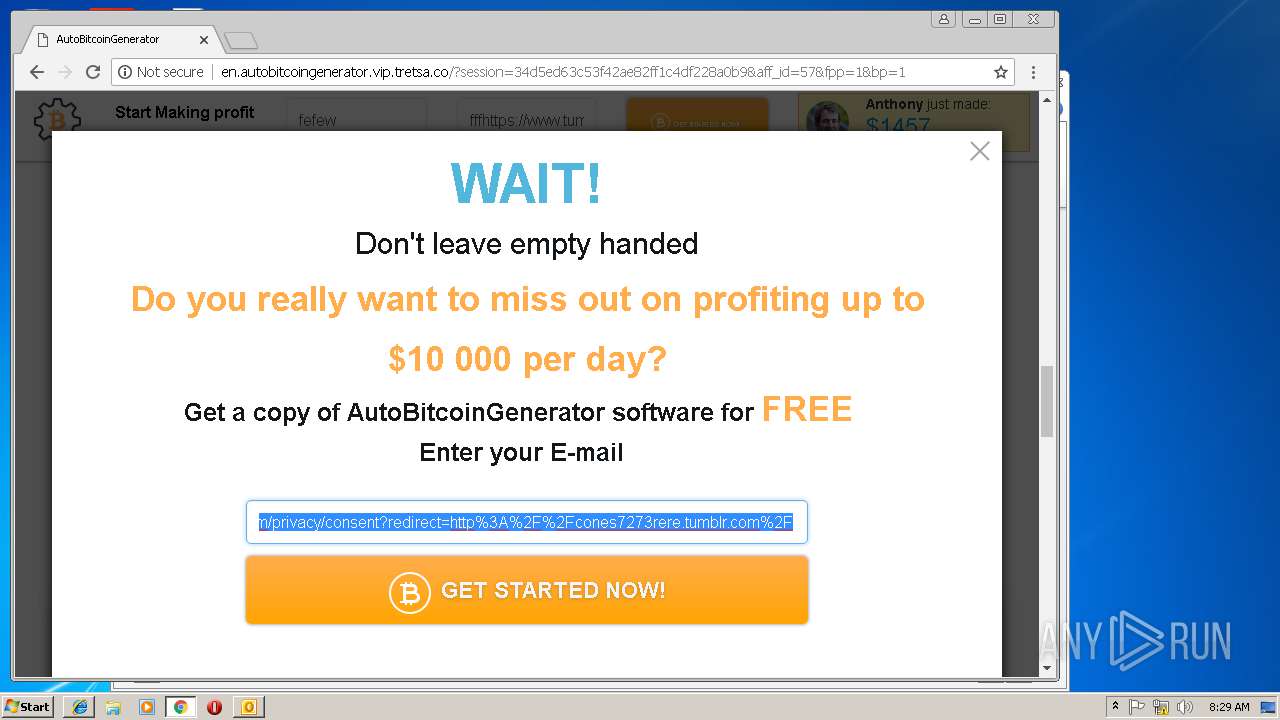
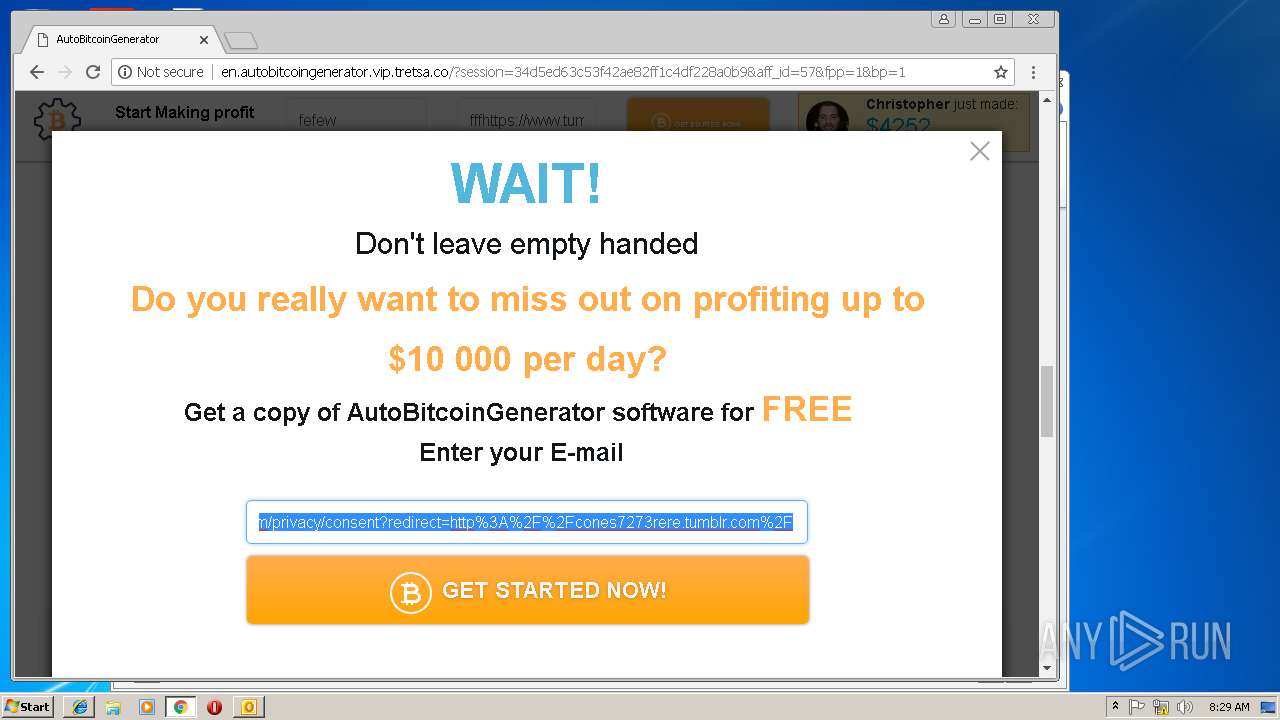
3112 | iexplore.exe | GET | 302 | 66.6.32.21:80 | http://cones7273rere.tumblr.com/ | US | — | — | suspicious |
3144 | iexplore.exe | GET | 302 | 66.6.32.21:80 | http://cones7273rere.tumblr.com/ | US | — | — | suspicious |
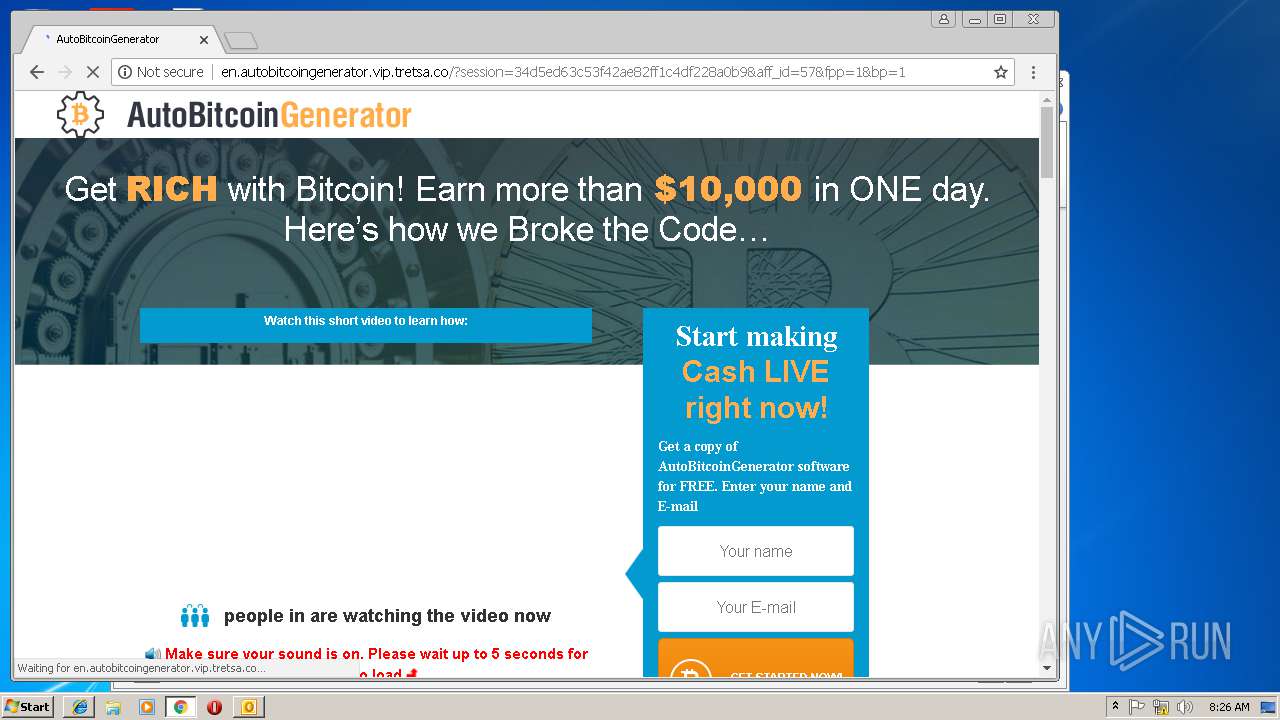
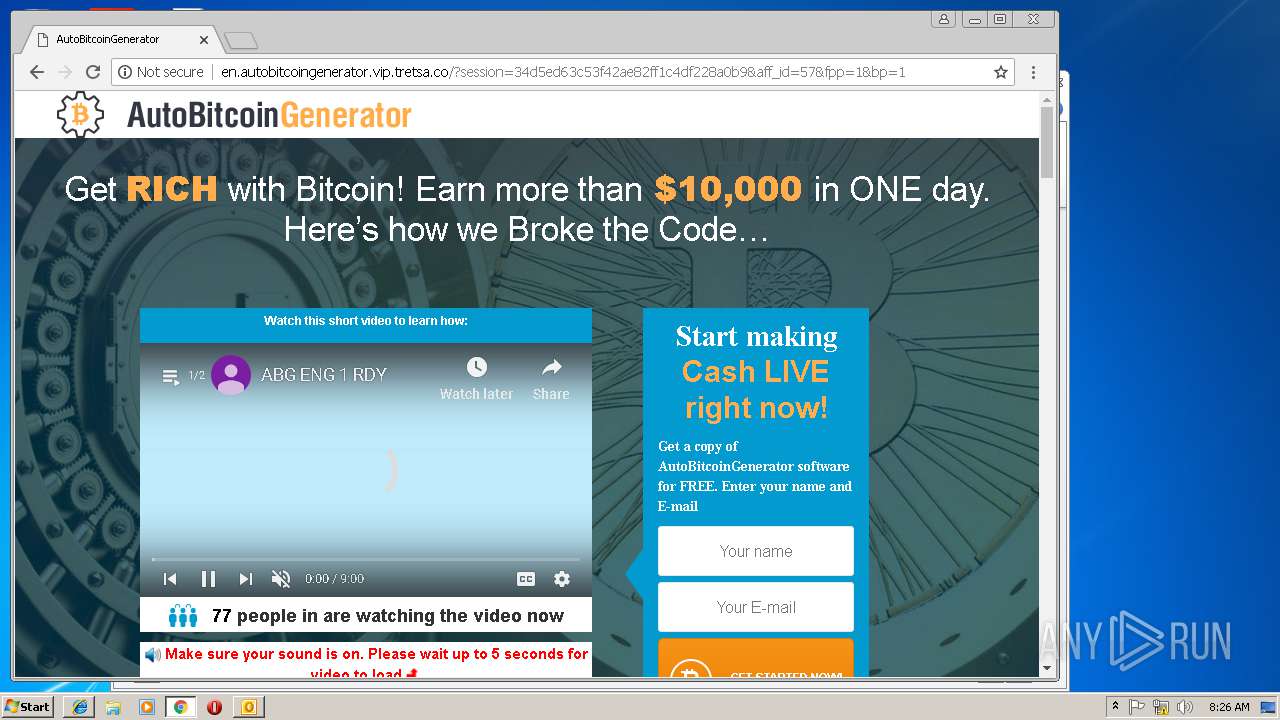
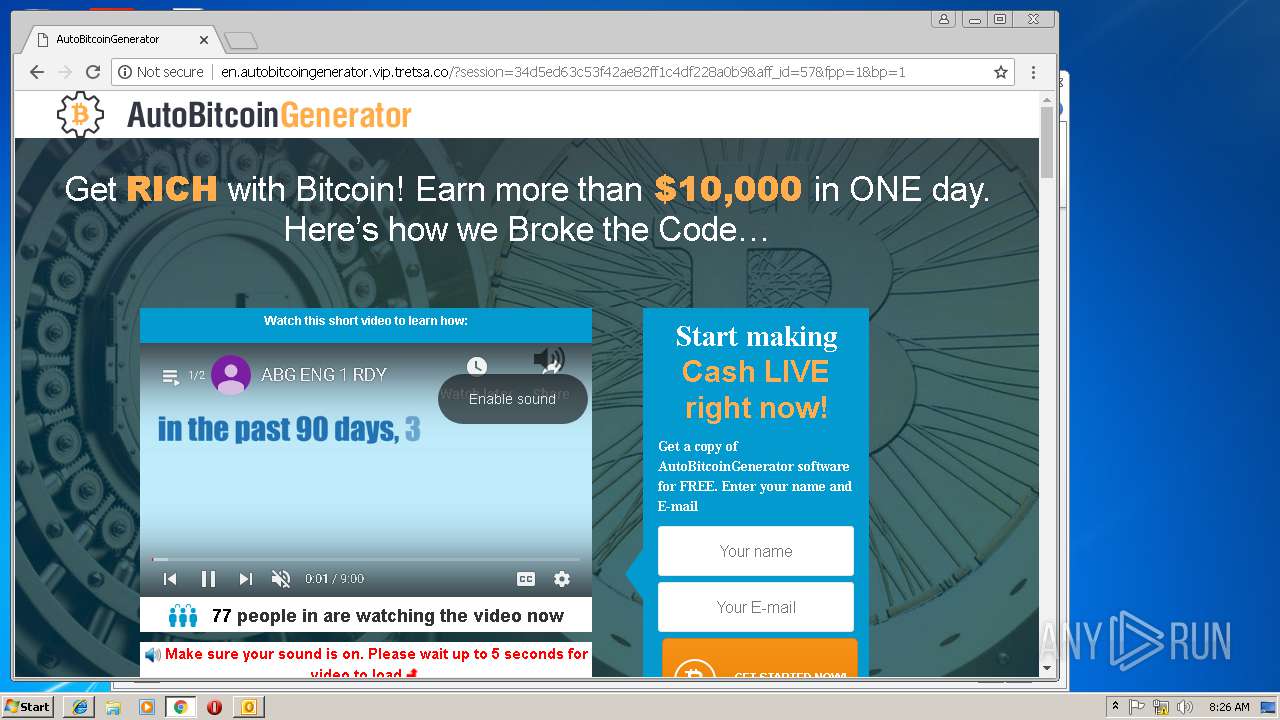
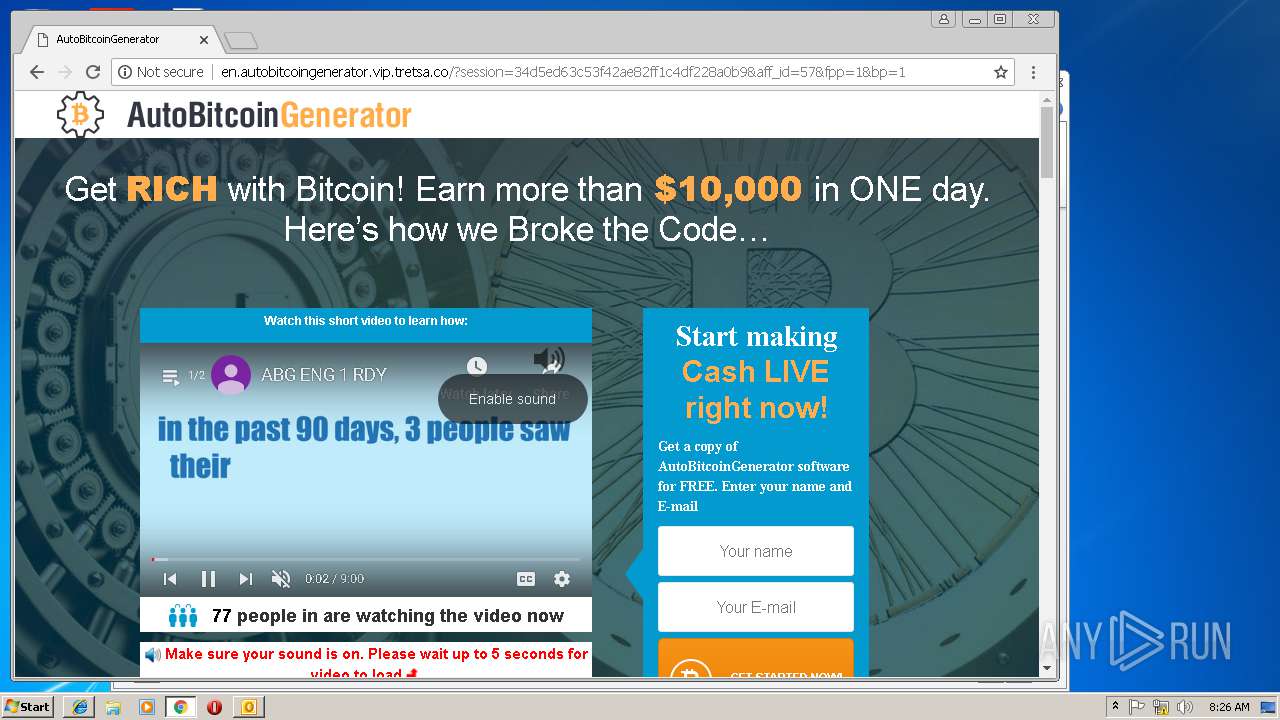
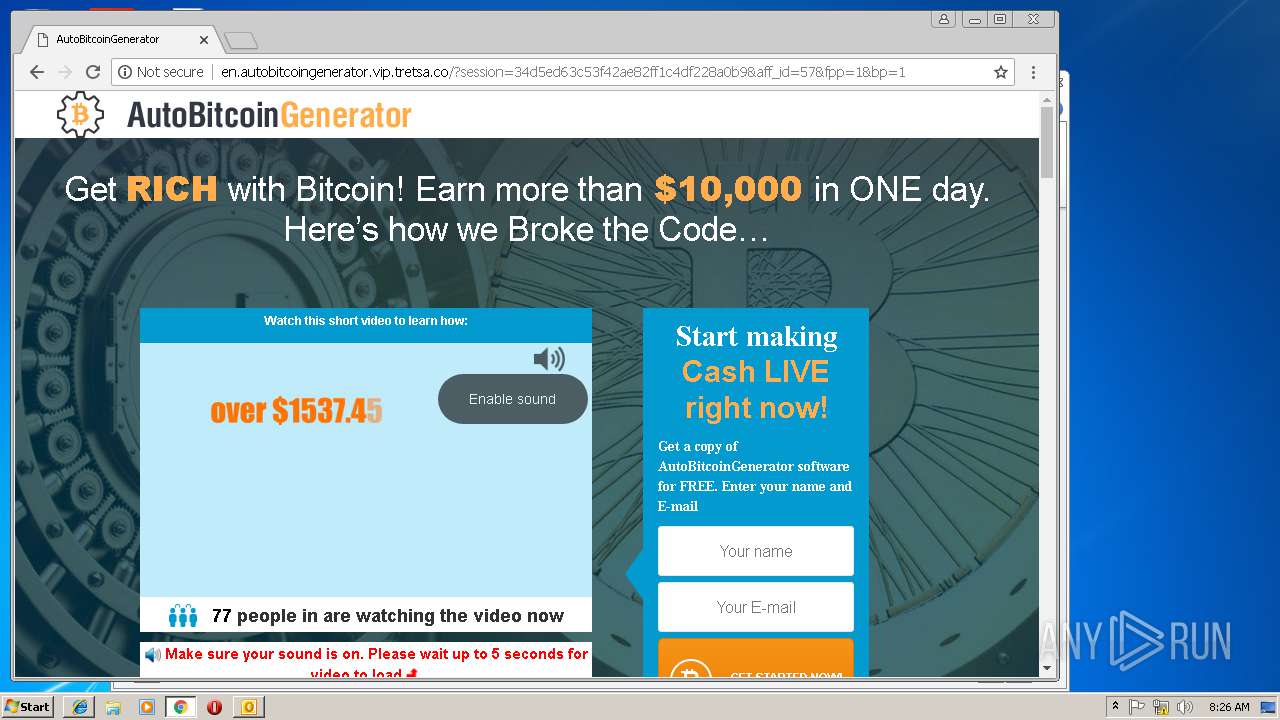
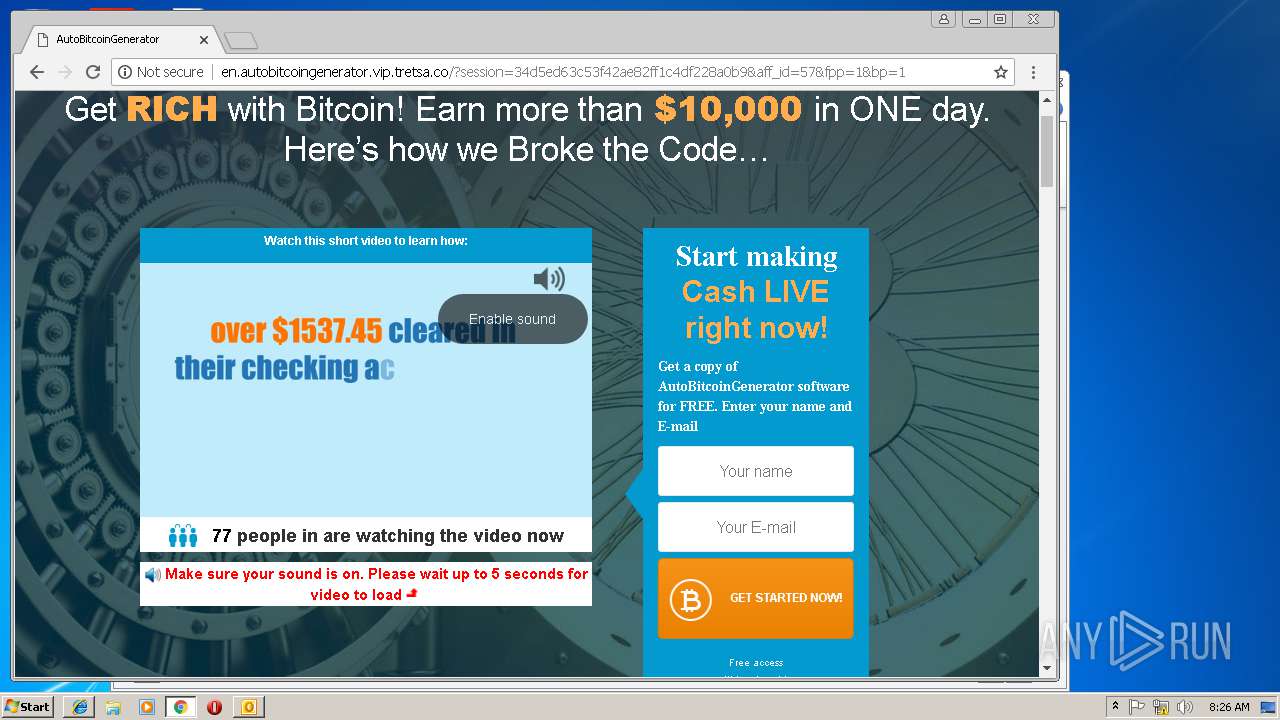
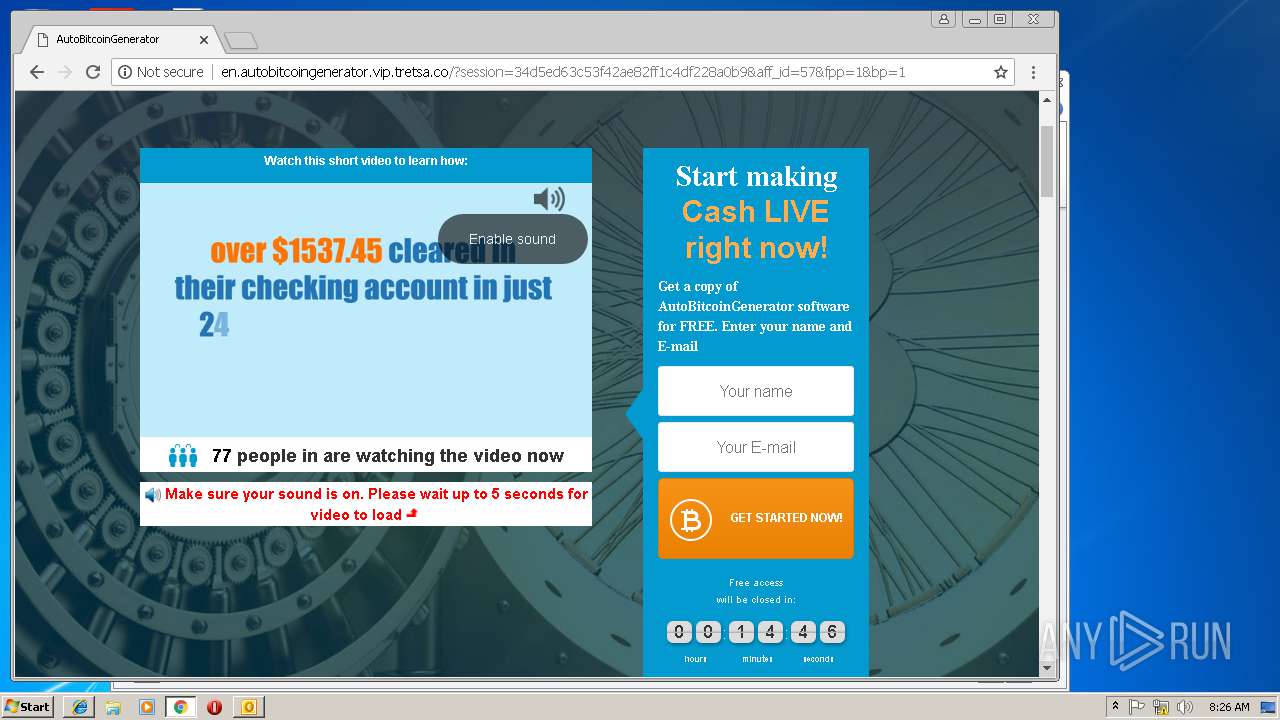
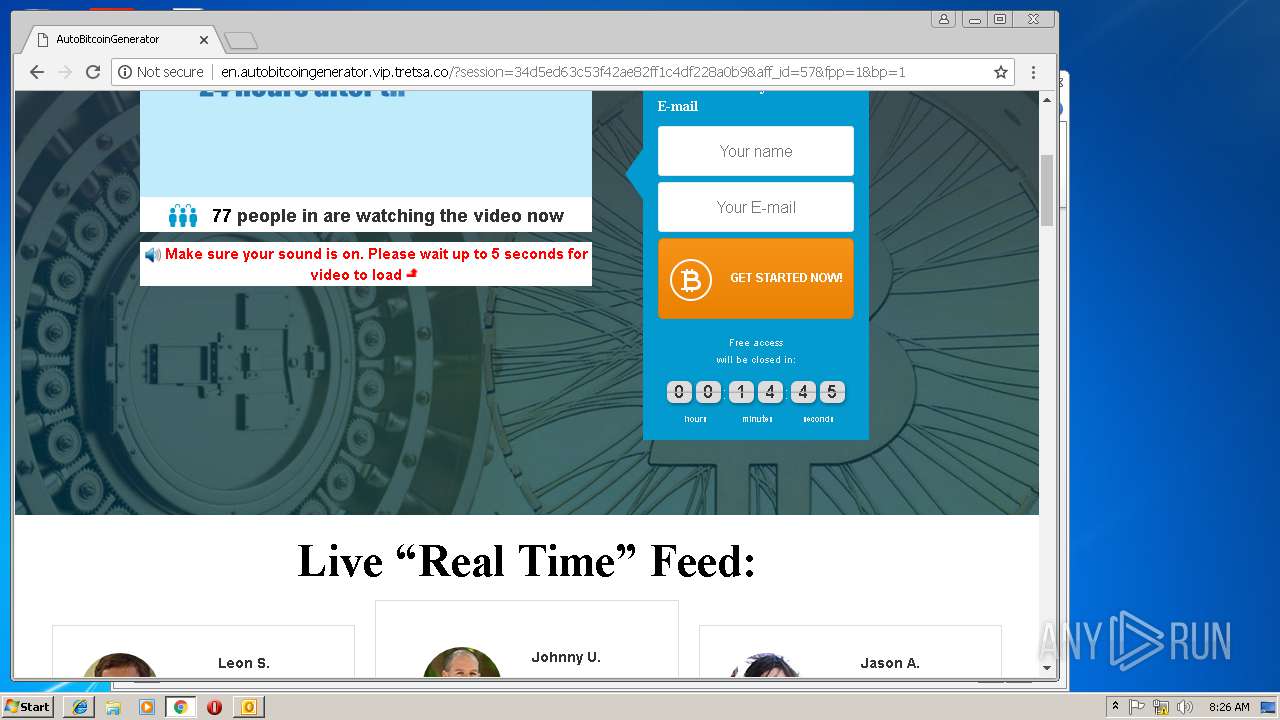
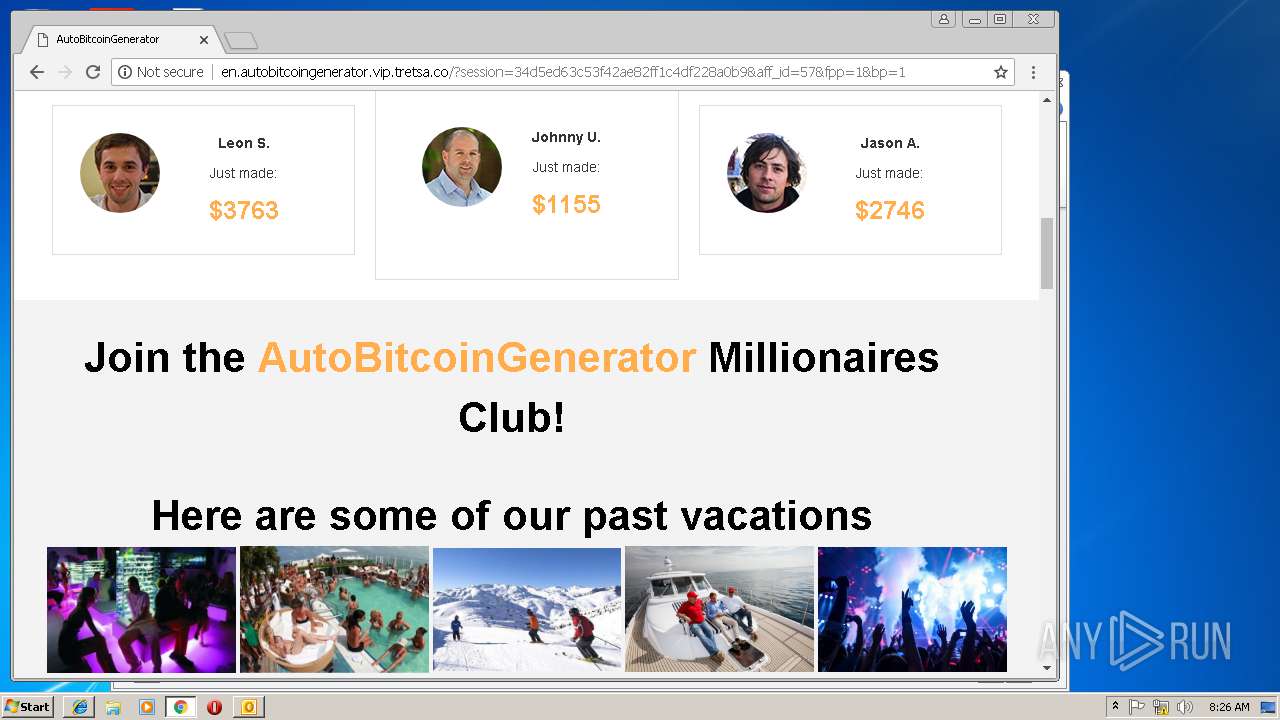
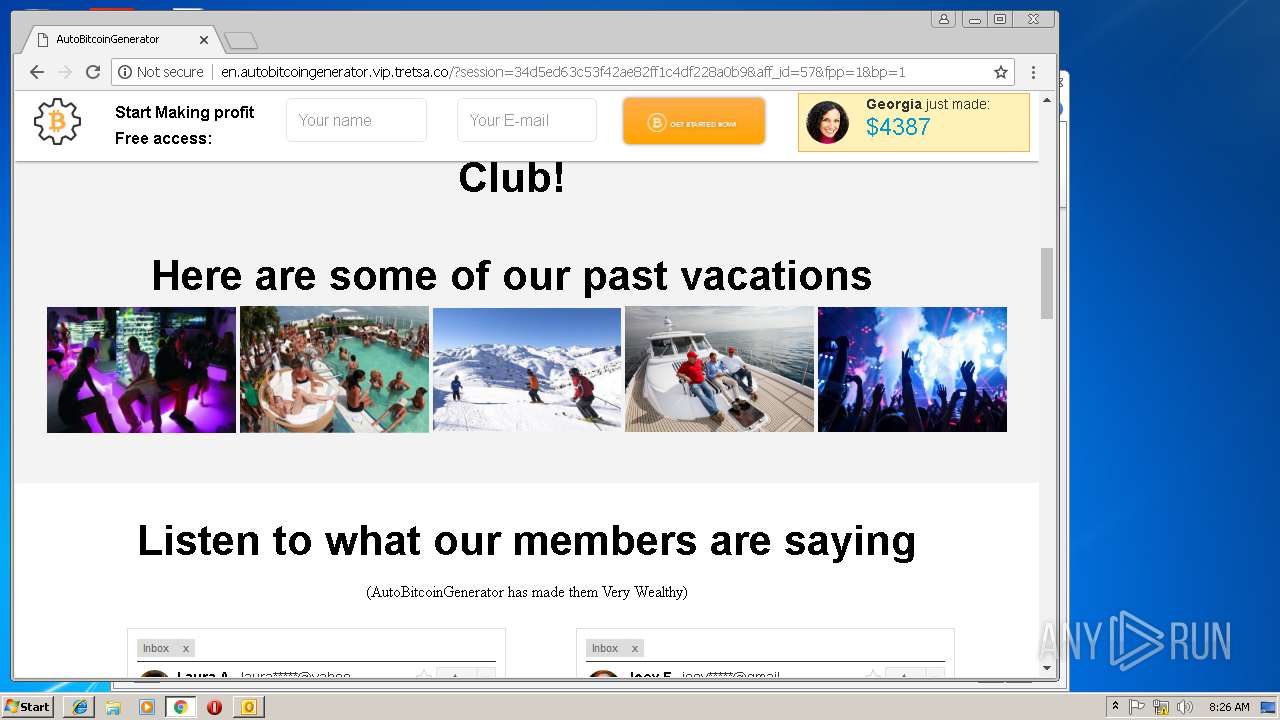
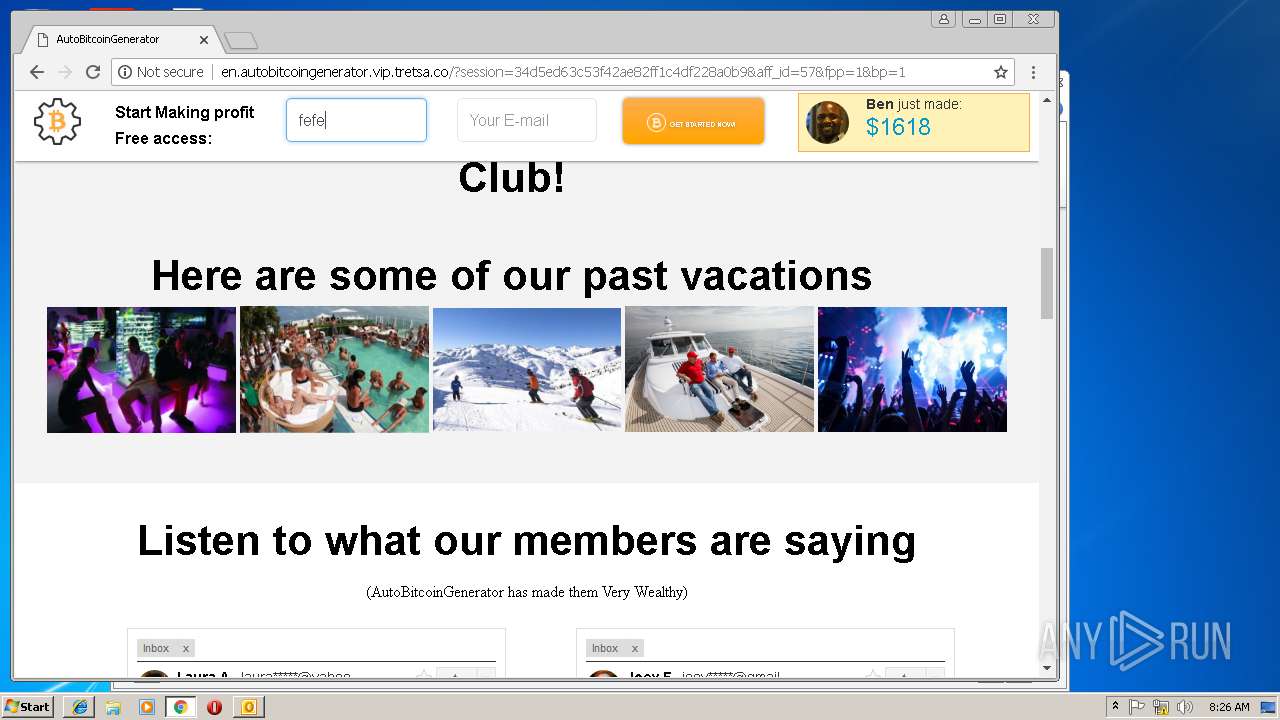
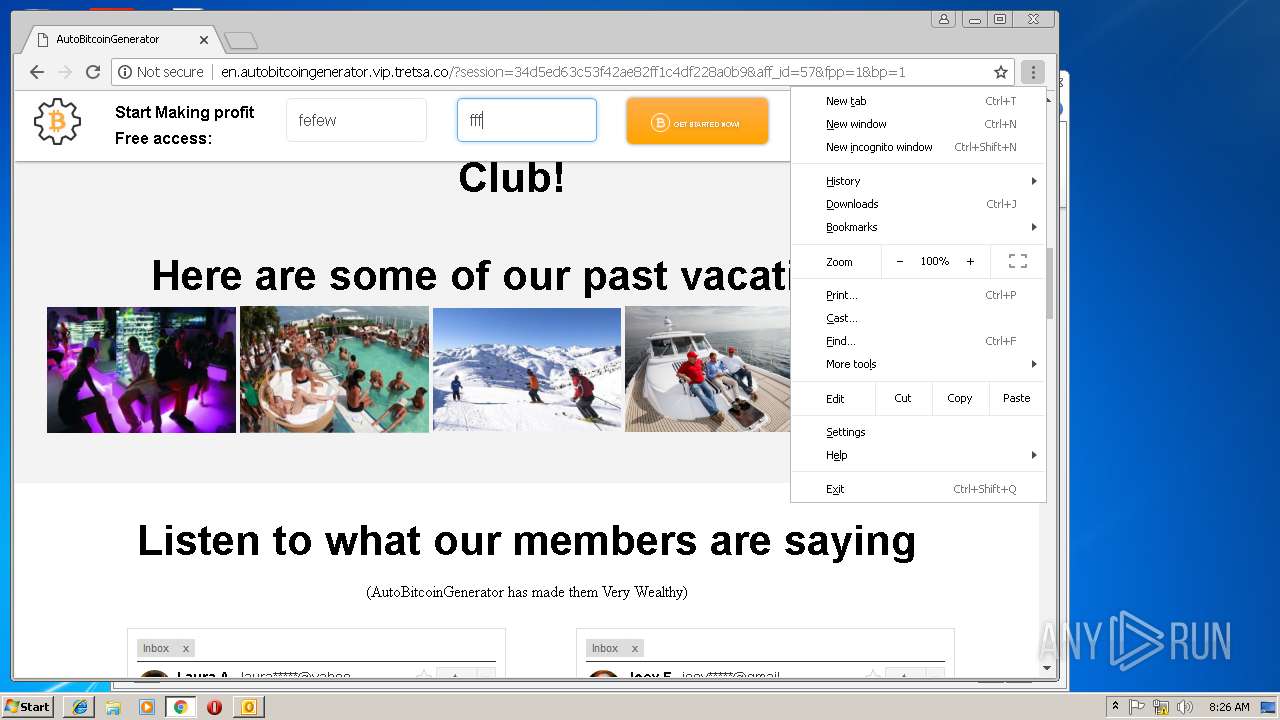
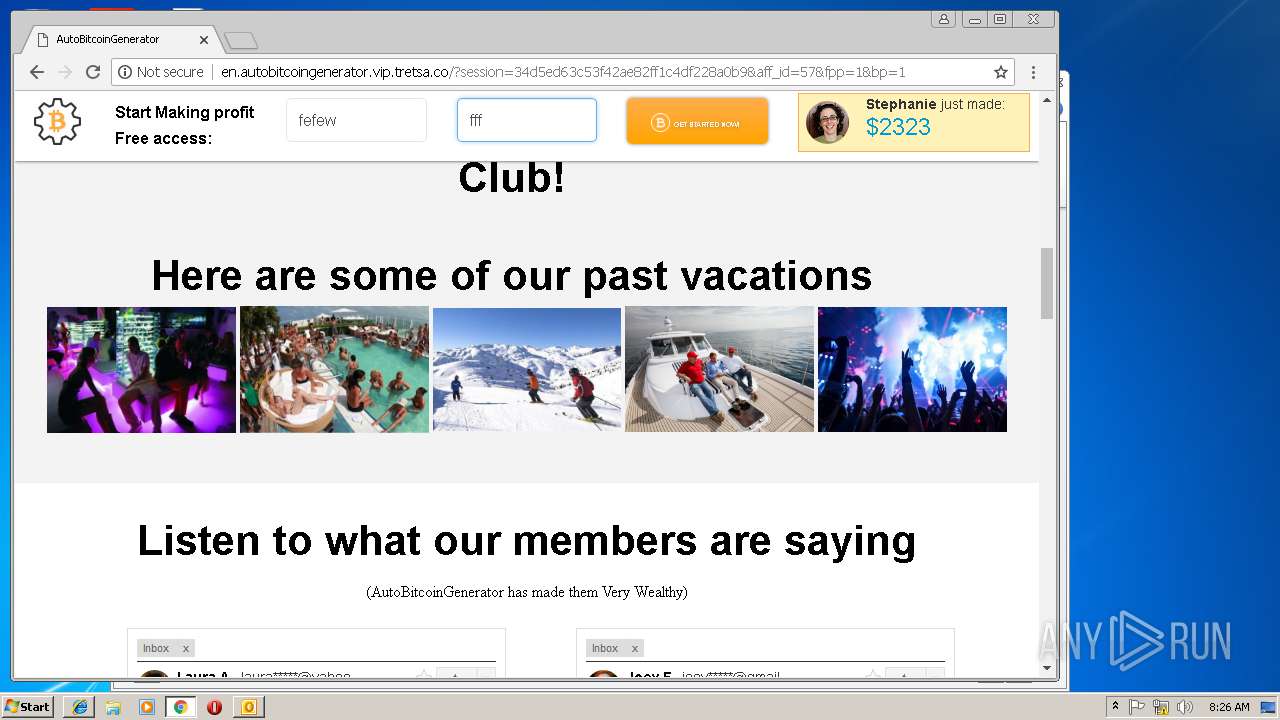
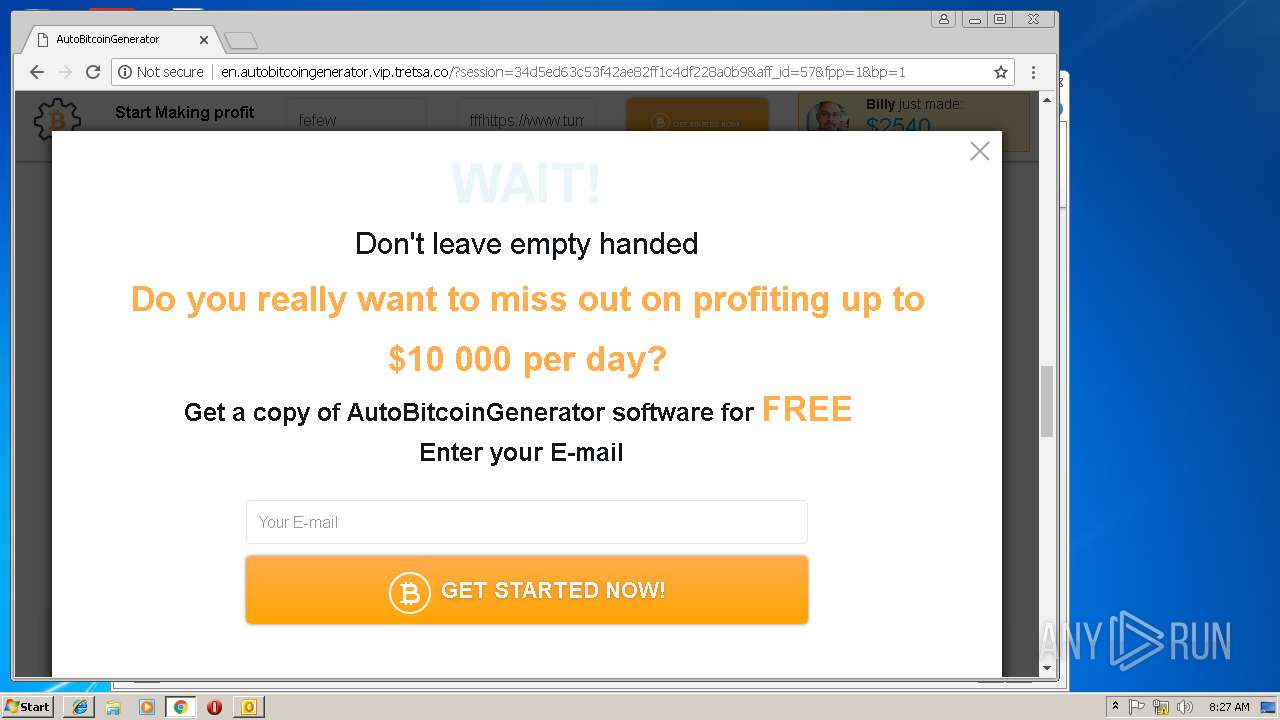
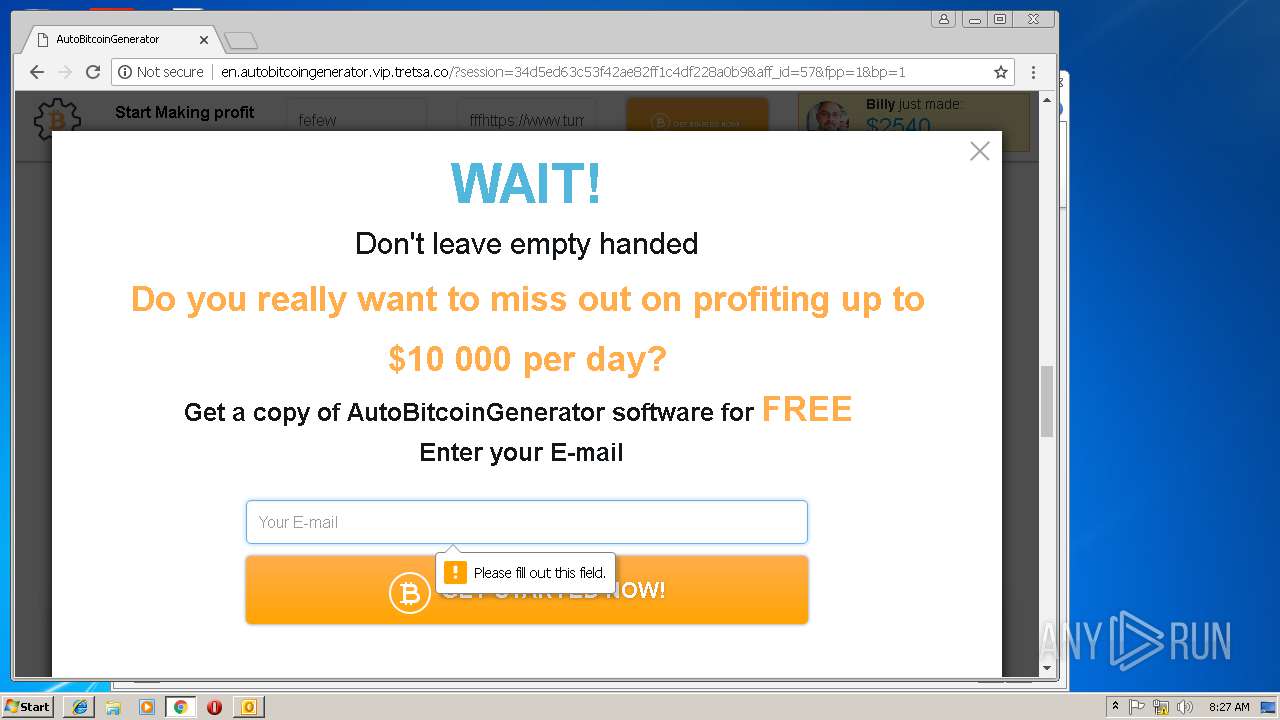
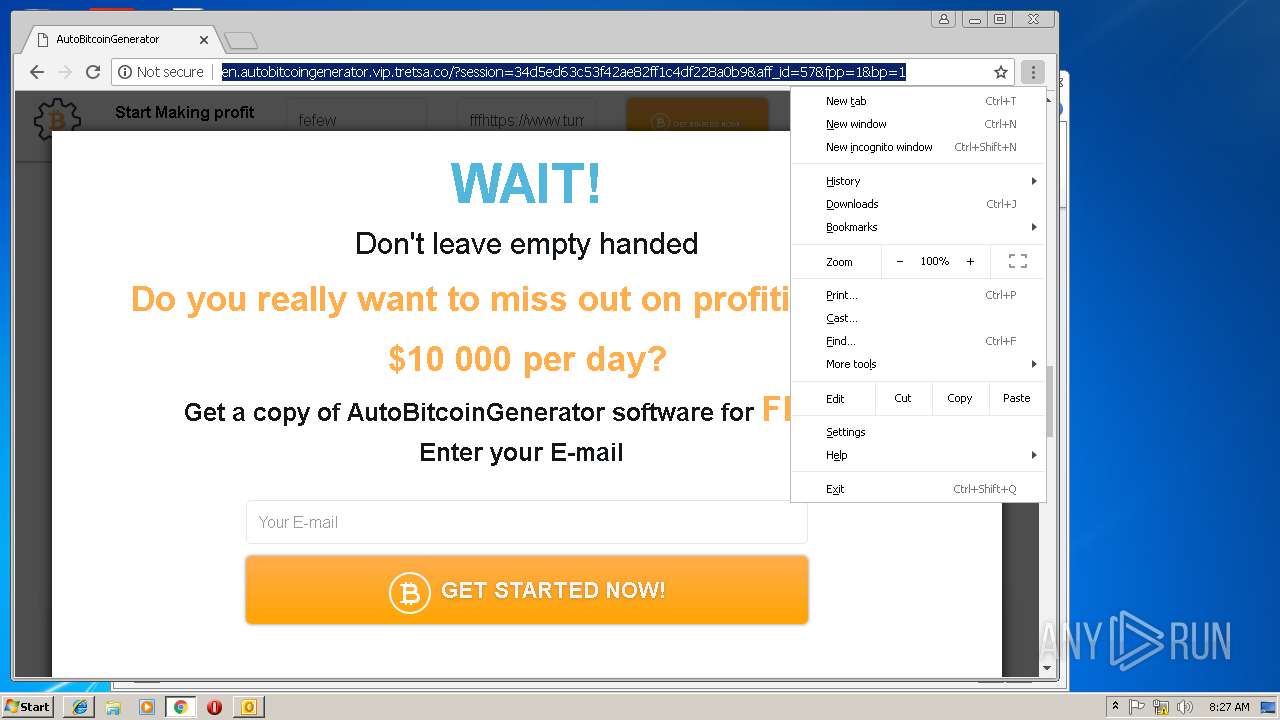
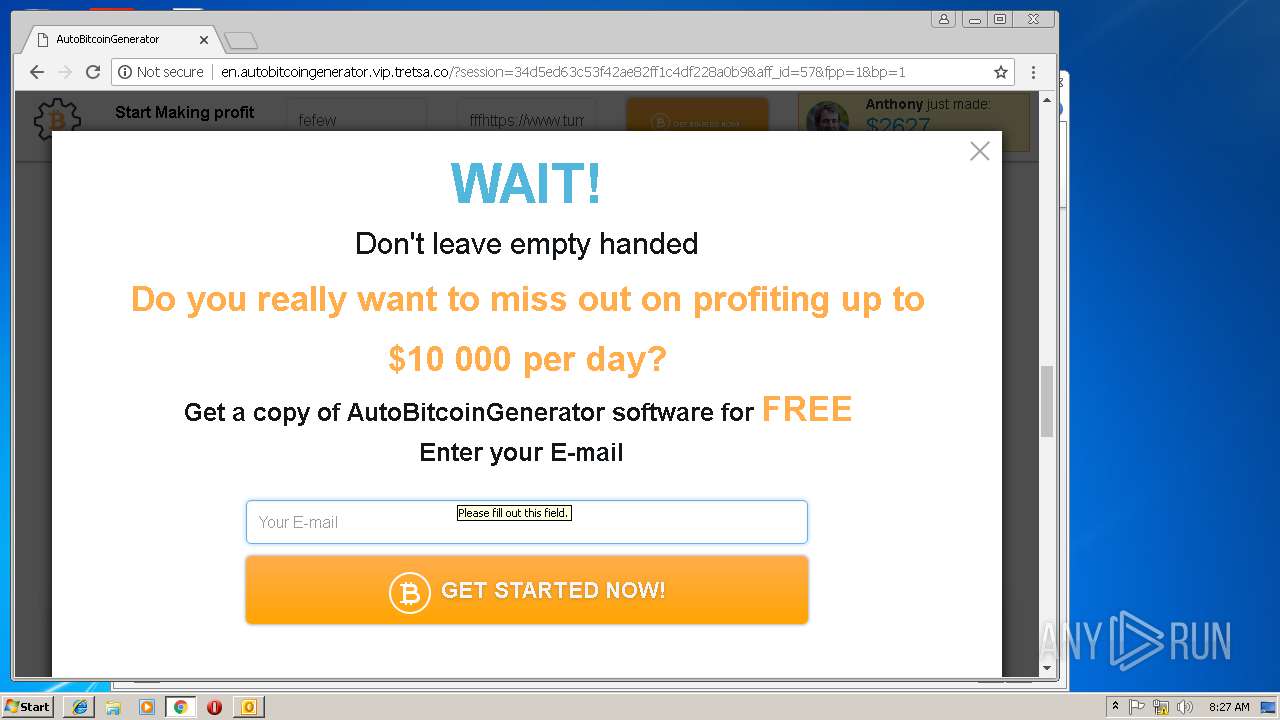
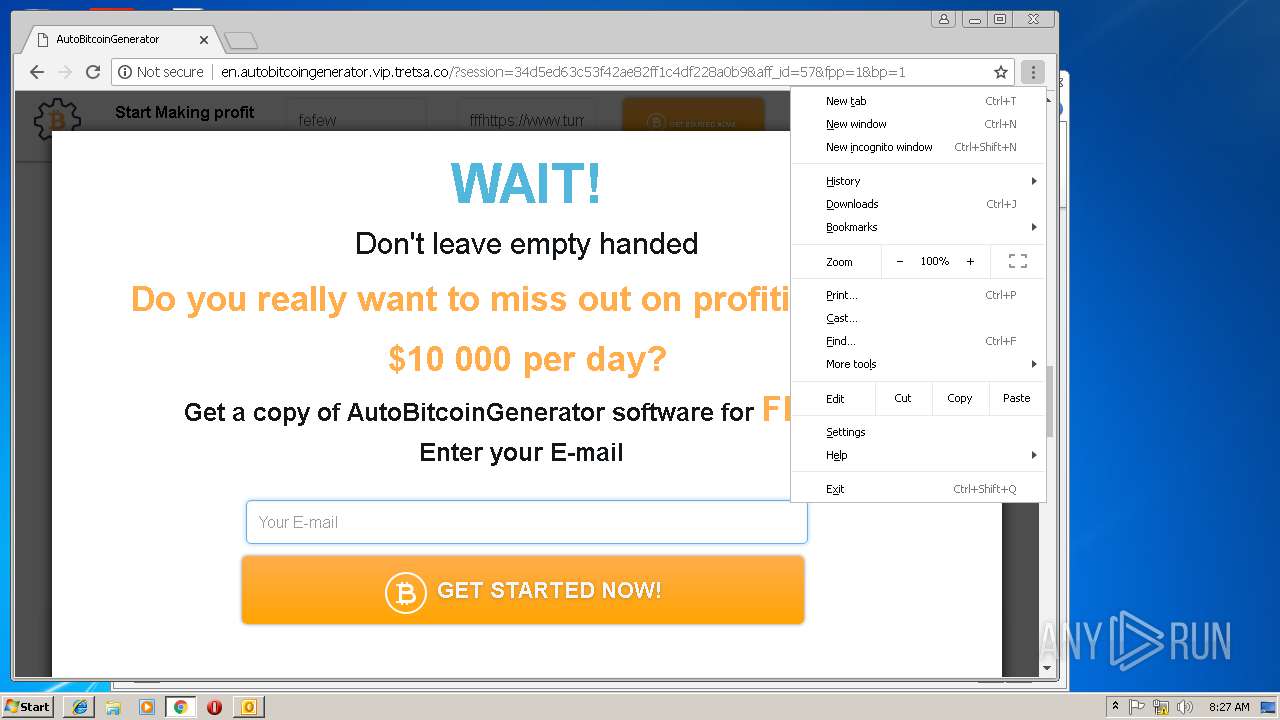
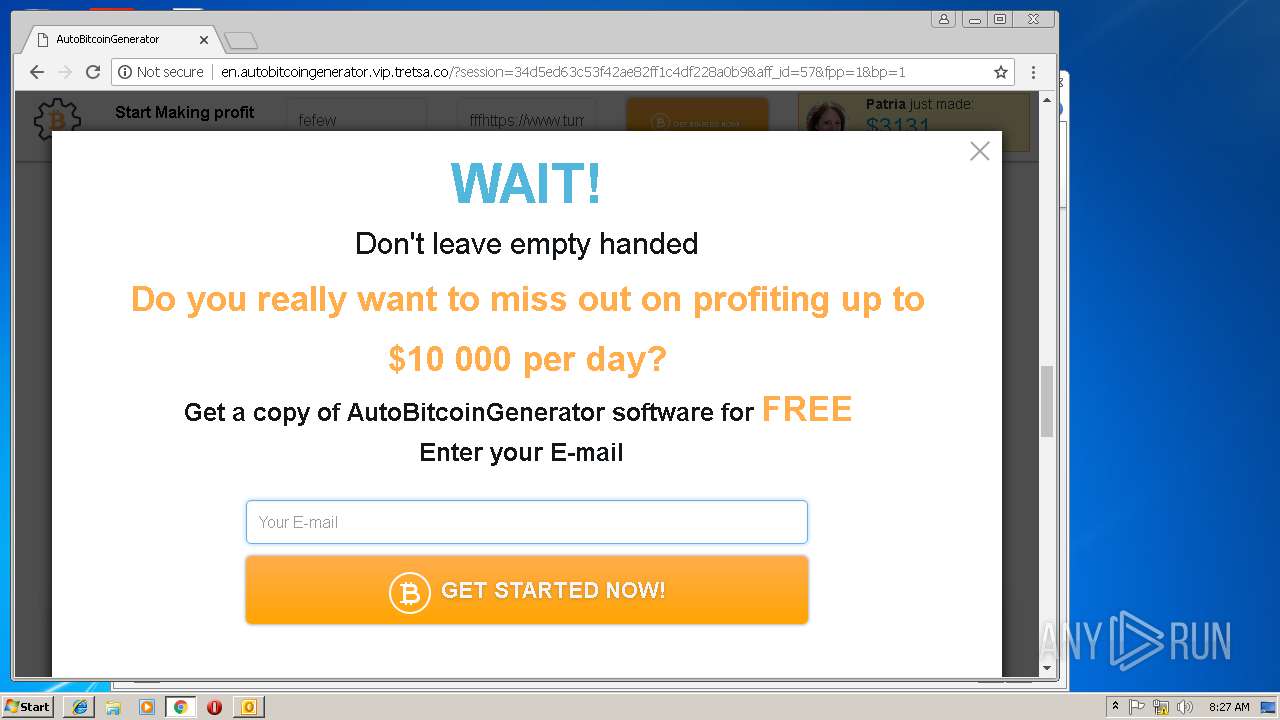
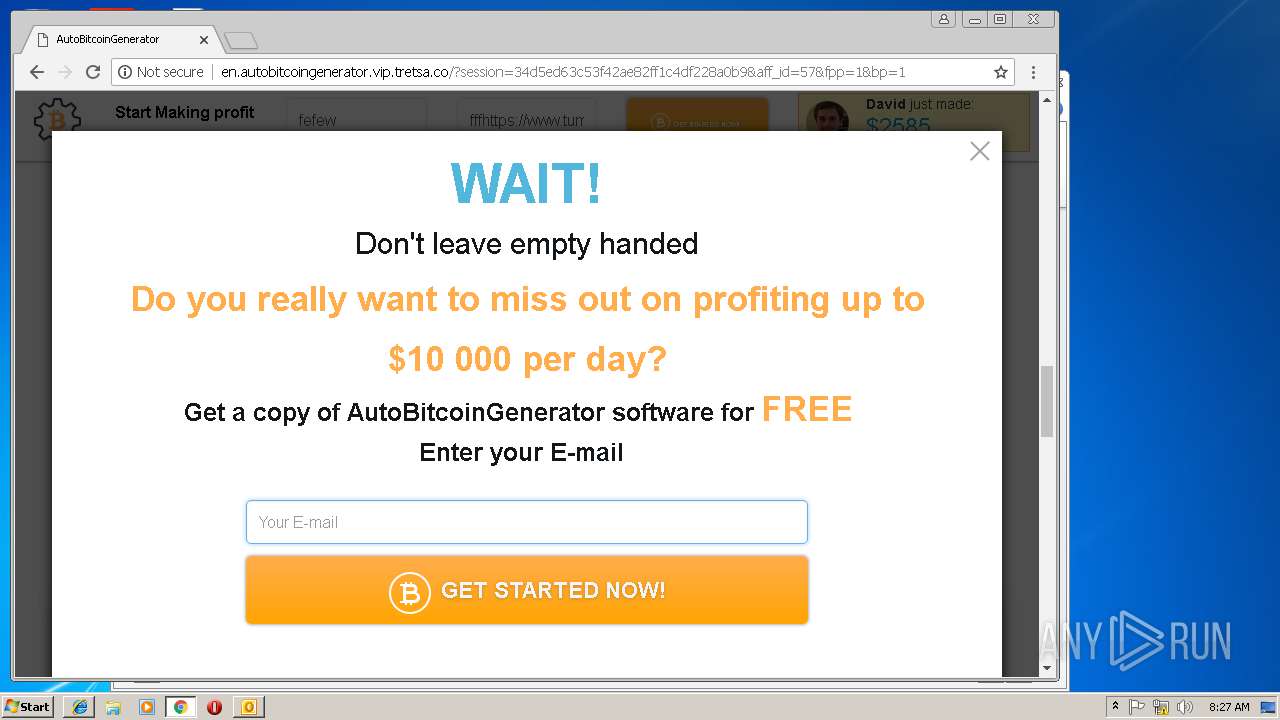
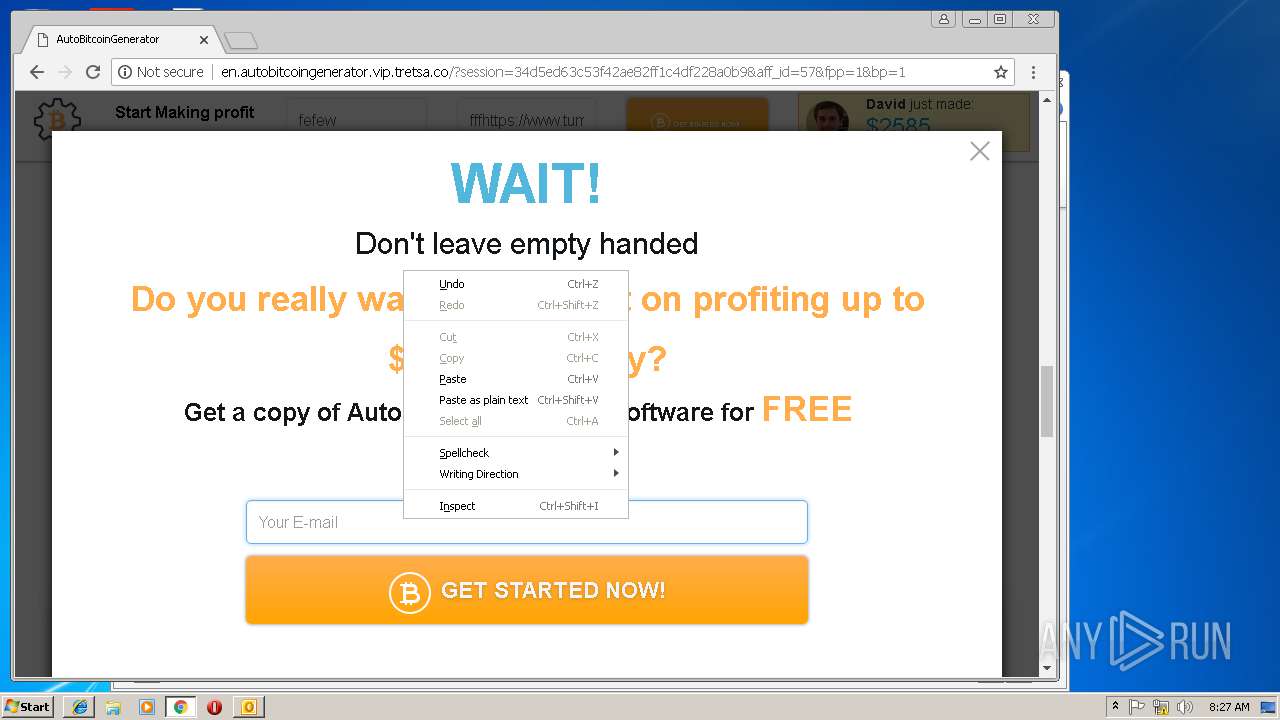
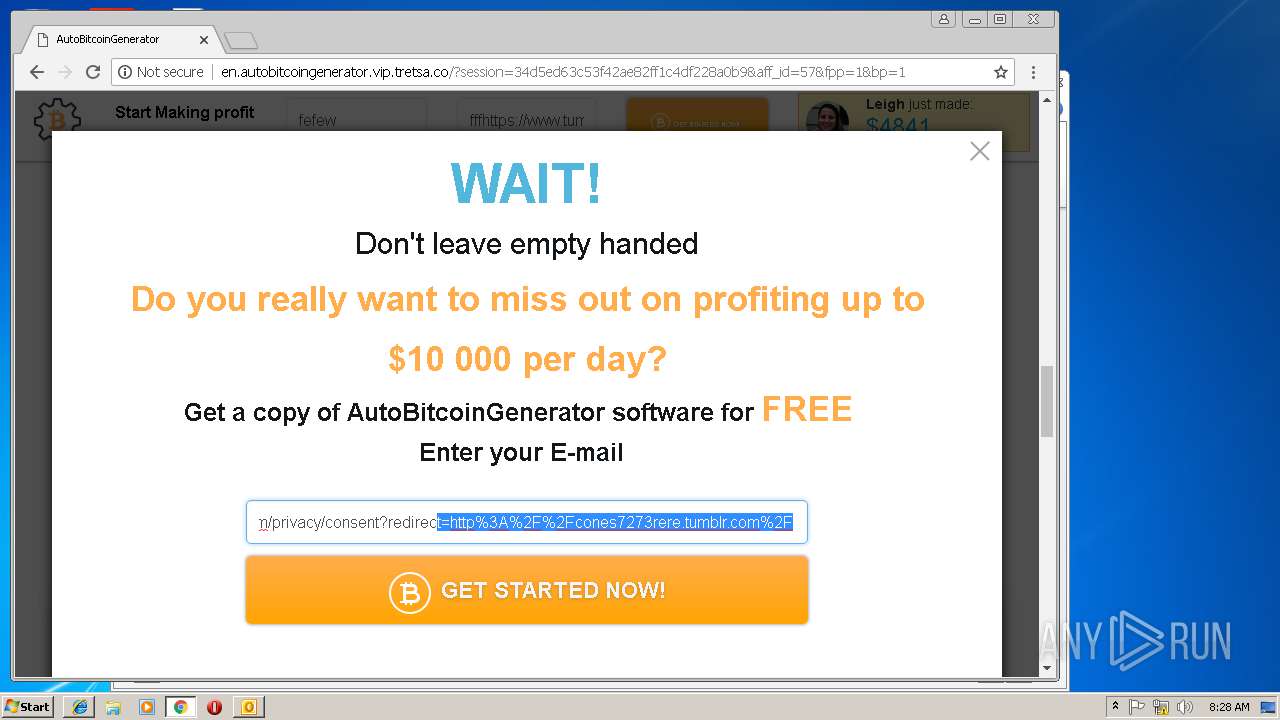
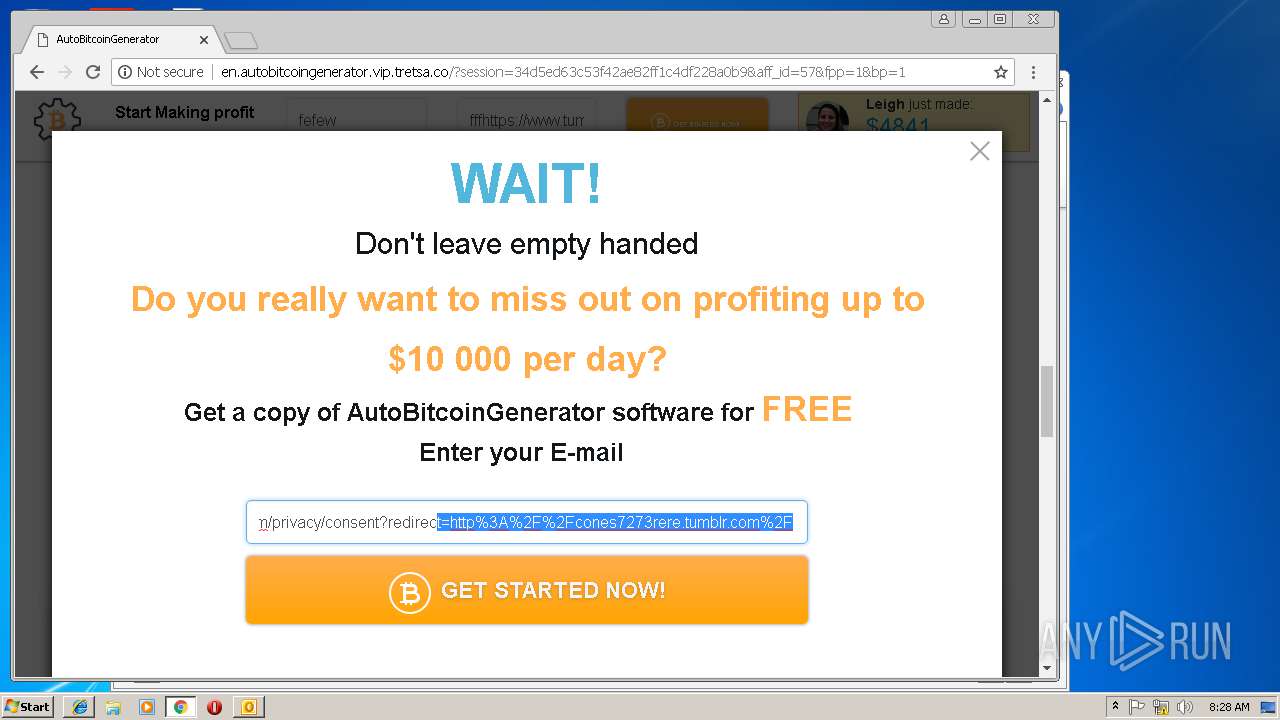
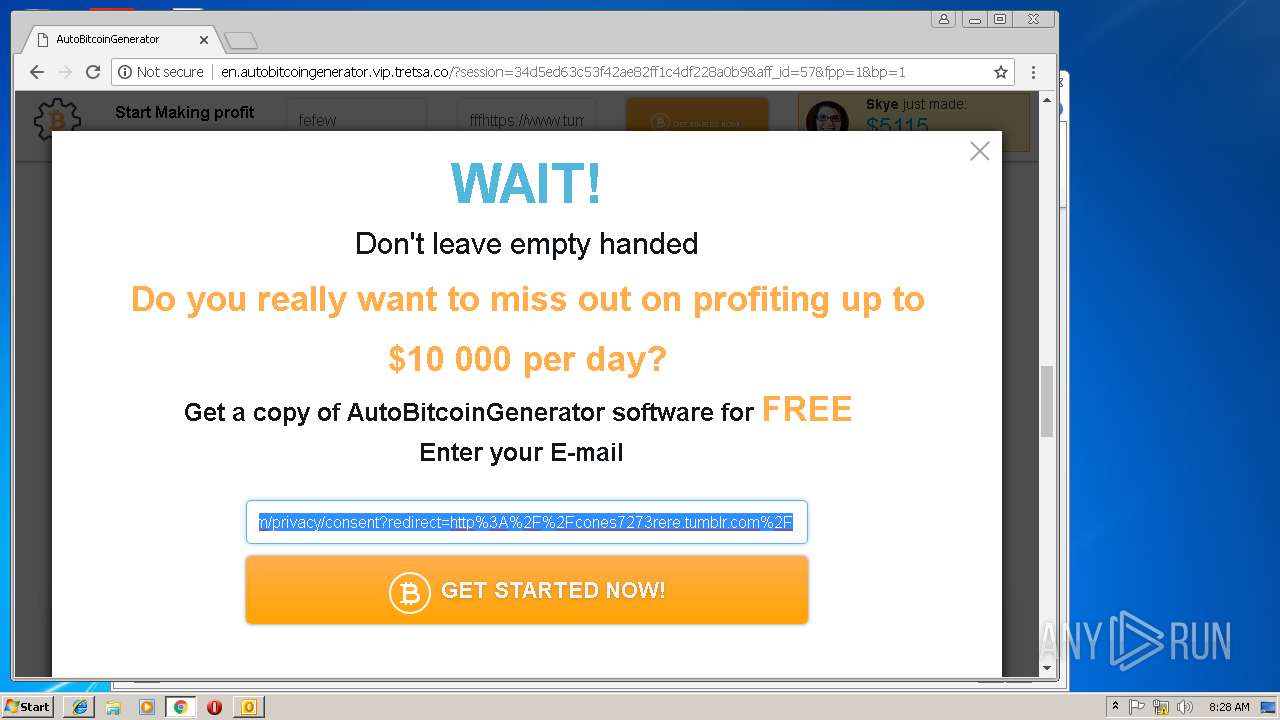
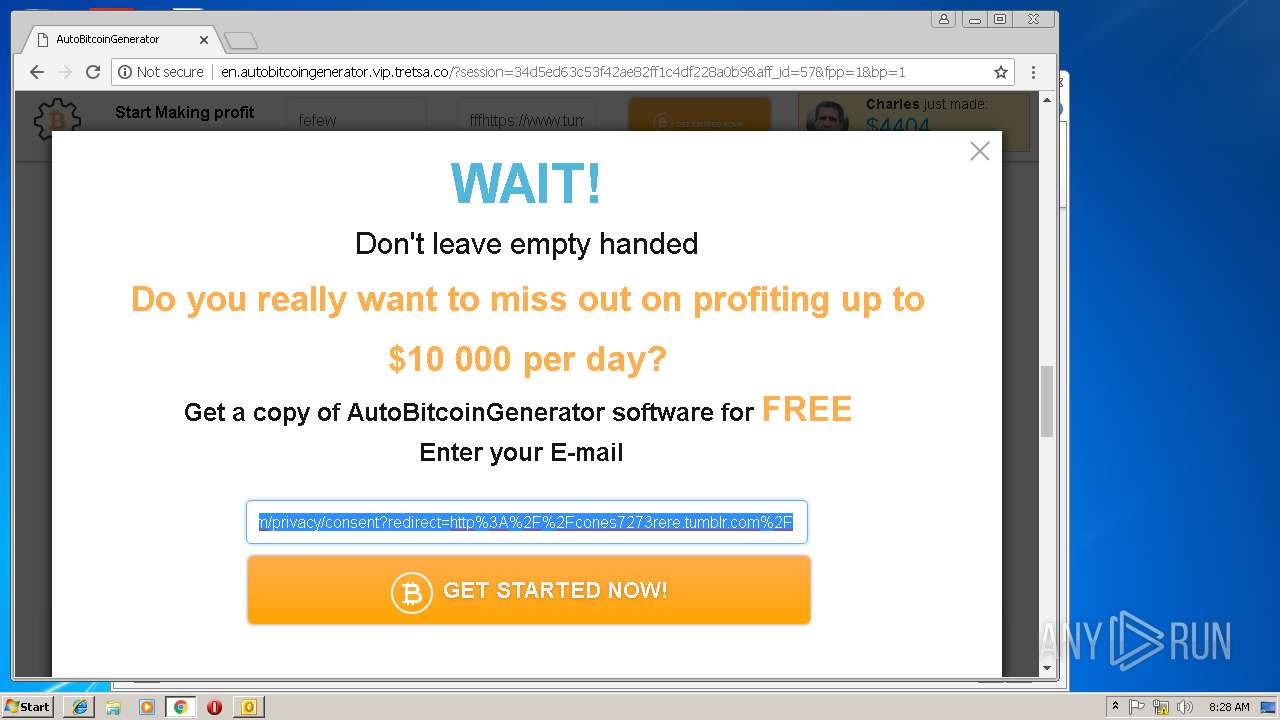
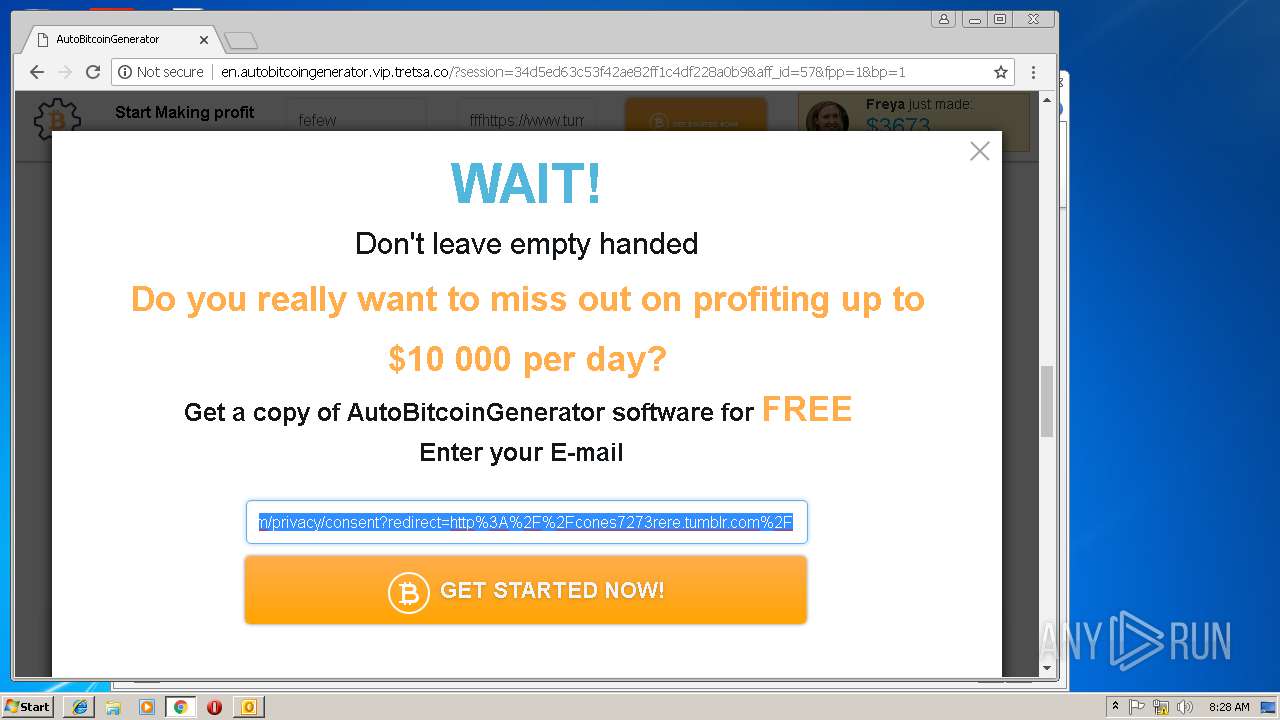
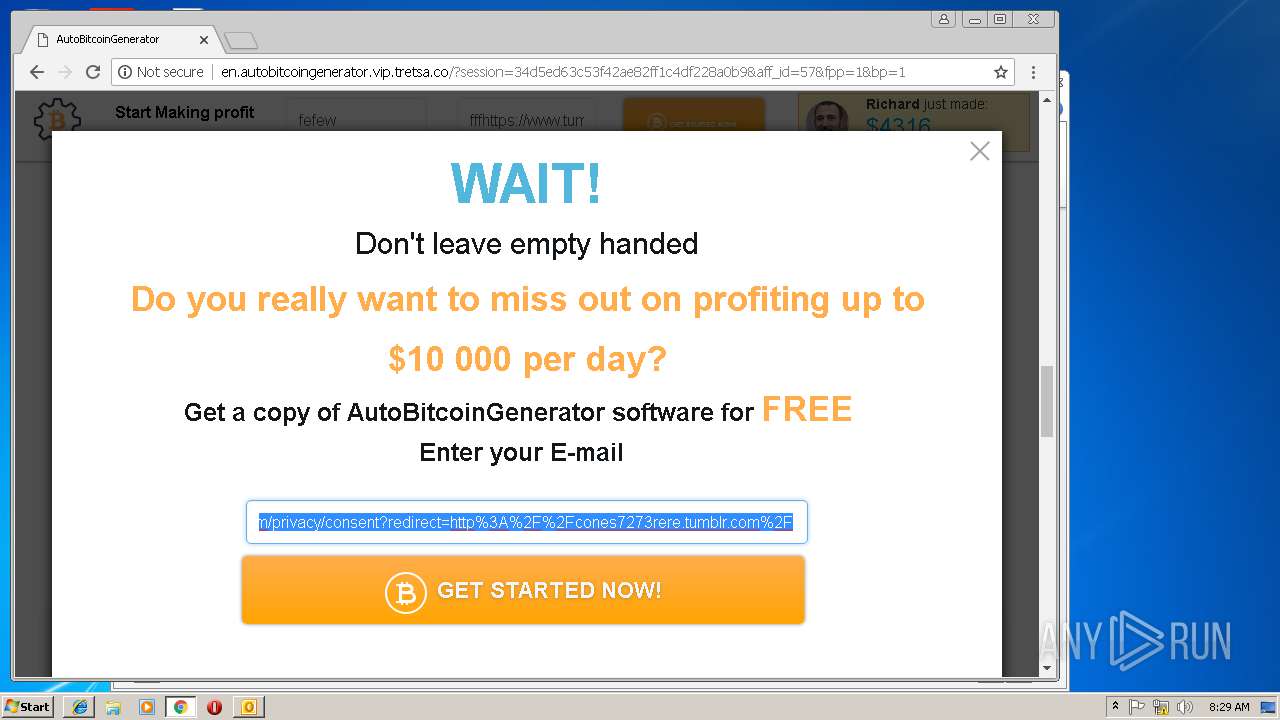
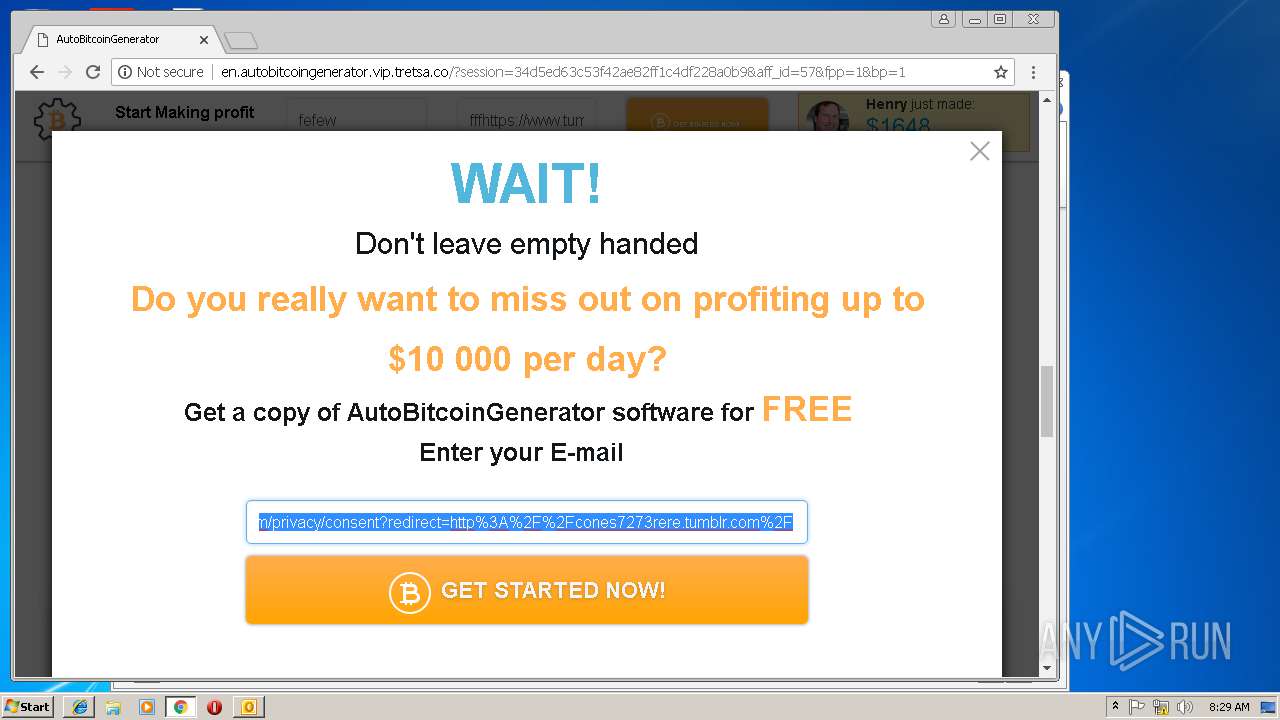
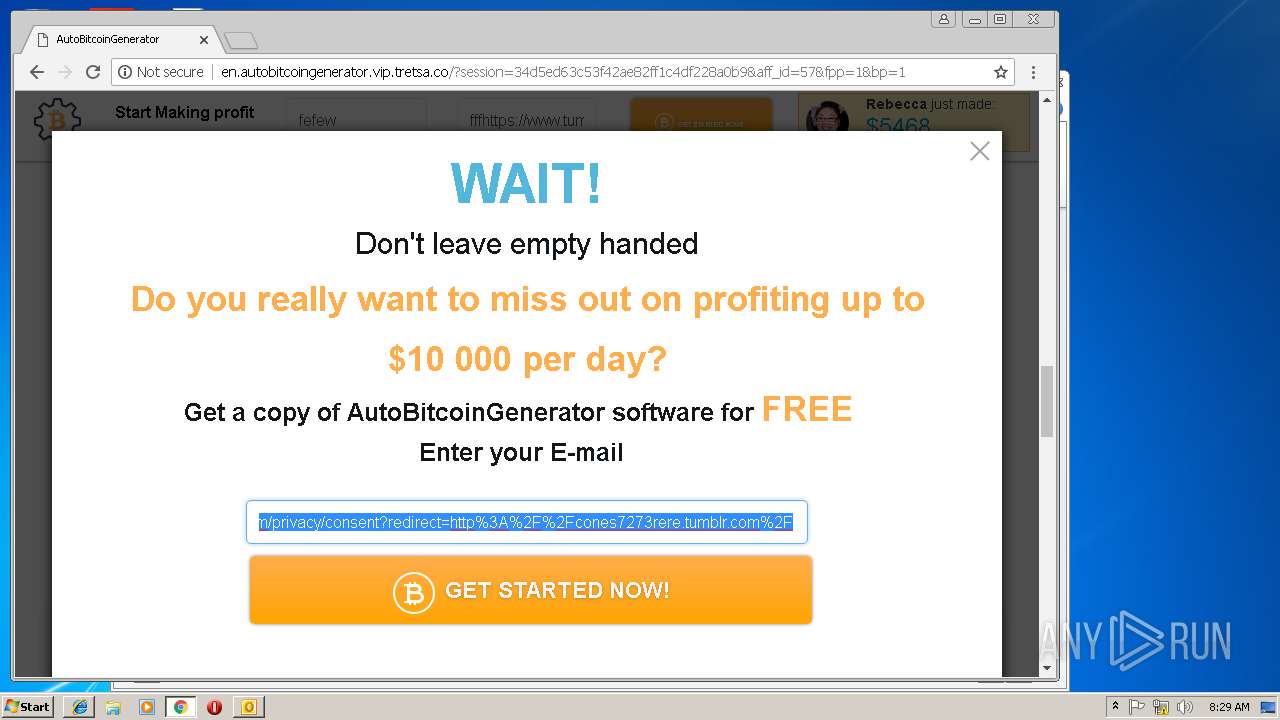
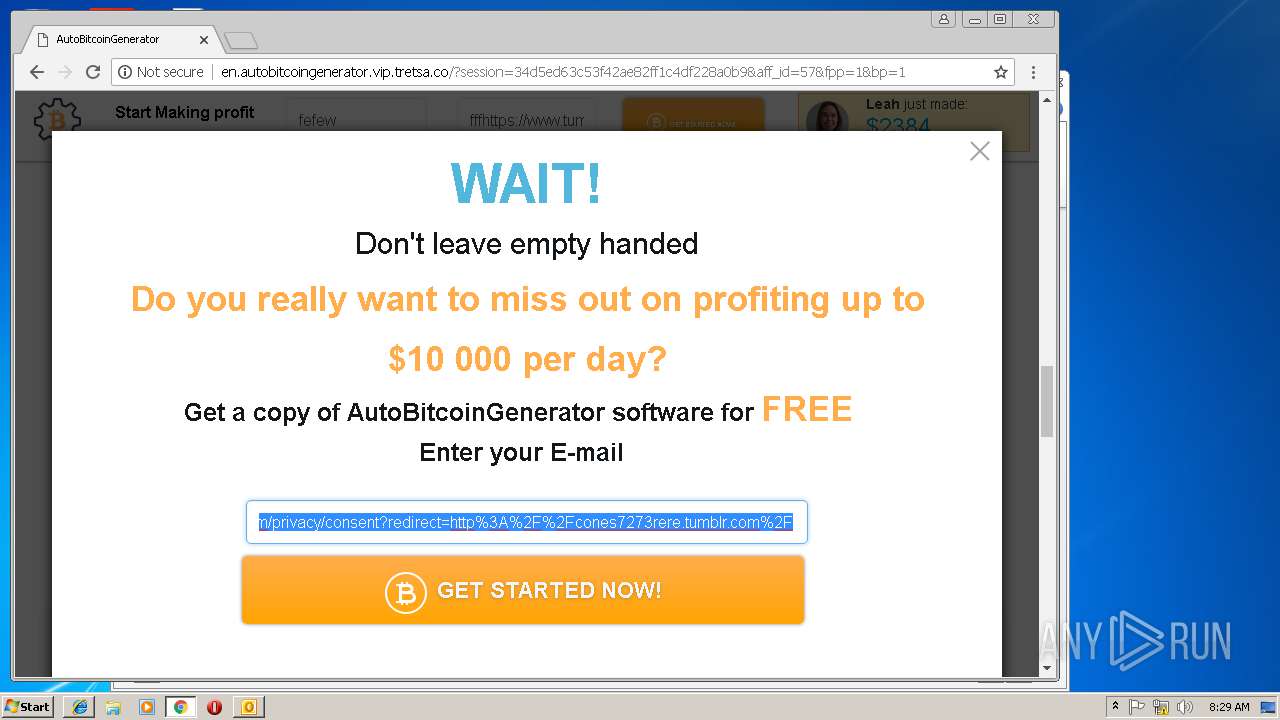
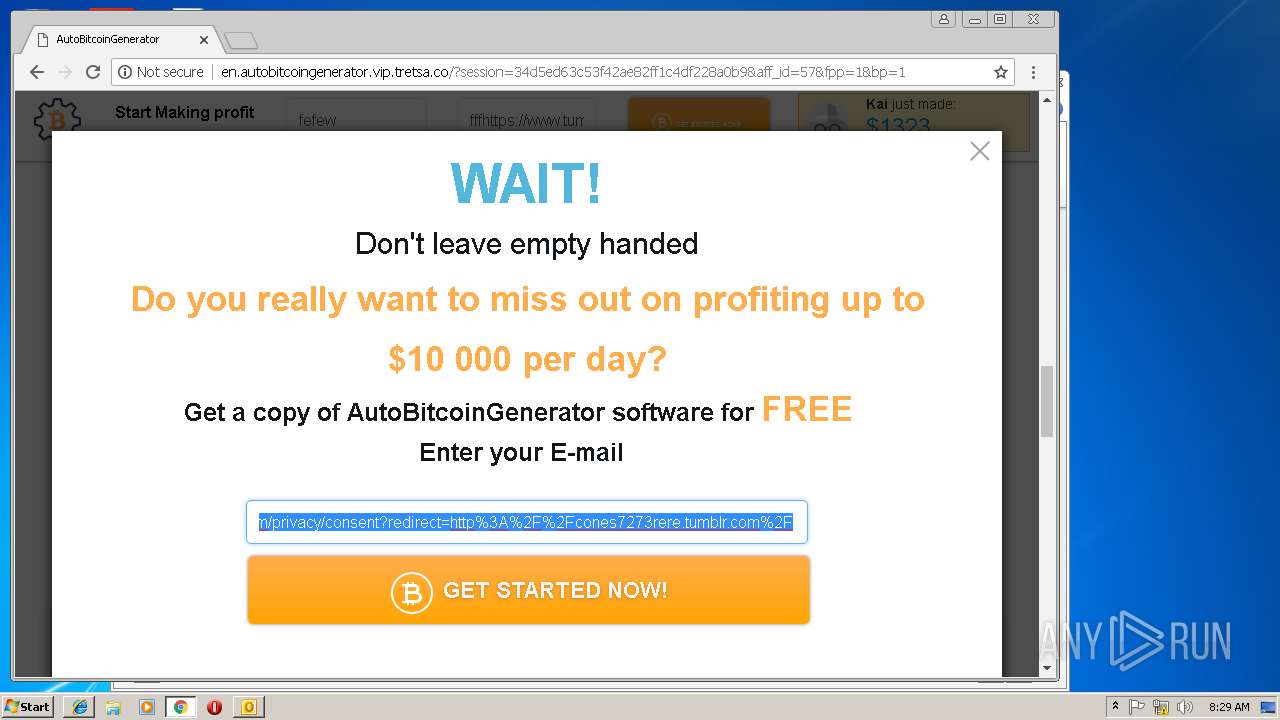
2380 | chrome.exe | GET | 302 | 104.24.108.248:80 | http://vip.tretsa.co/tracker?smart_link_id=60&aff_id=57 | US | — | — | shared |
2380 | chrome.exe | GET | 200 | 66.6.33.149:80 | http://cones7273rere.tumblr.com/ | US | html | 9.42 Kb | suspicious |
2380 | chrome.exe | GET | 200 | 104.24.108.248:80 | http://en.autobitcoingenerator.vip.tretsa.co/css/form-css.css | US | text | 1.55 Kb | shared |
2380 | chrome.exe | GET | 200 | 104.24.108.248:80 | http://en.autobitcoingenerator.vip.tretsa.co/css/reset.css | US | text | 410 b | shared |
2380 | chrome.exe | GET | 200 | 104.24.108.248:80 | http://en.autobitcoingenerator.vip.tretsa.co/?session=34d5ed63c53f42ae82ff1c4df228a0b9&aff_id=57&fpp=1&bp=1 | US | html | 10.7 Kb | shared |
2380 | chrome.exe | GET | 200 | 104.24.108.248:80 | http://en.autobitcoingenerator.vip.tretsa.co/css/bootstrap.min.css | US | text | 20.8 Kb | shared |
2380 | chrome.exe | GET | 200 | 104.24.108.248:80 | http://en.autobitcoingenerator.vip.tretsa.co/css/font-awesome.min.css | US | text | 5.94 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2380 | chrome.exe | 216.58.206.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3216 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3112 | iexplore.exe | 66.6.32.21:80 | cones7273rere.tumblr.com | Yahoo! | US | unknown |
3988 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3112 | iexplore.exe | 87.248.114.14:443 | www.tumblr.com | Yahoo! UK Services Limited | GB | shared |
3112 | iexplore.exe | 152.199.19.43:443 | assets.tumblr.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3988 | iexplore.exe | 152.199.19.43:443 | assets.tumblr.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3144 | iexplore.exe | 66.6.32.21:80 | cones7273rere.tumblr.com | Yahoo! | US | unknown |
2380 | chrome.exe | 216.58.206.4:443 | www.google.com | Google Inc. | US | whitelisted |
3144 | iexplore.exe | 87.248.114.13:443 | www.tumblr.com | Yahoo! UK Services Limited | GB | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
cones7273rere.tumblr.com |
| unknown |
www.bing.com |
| whitelisted |
www.tumblr.com |
| whitelisted |
assets.tumblr.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |