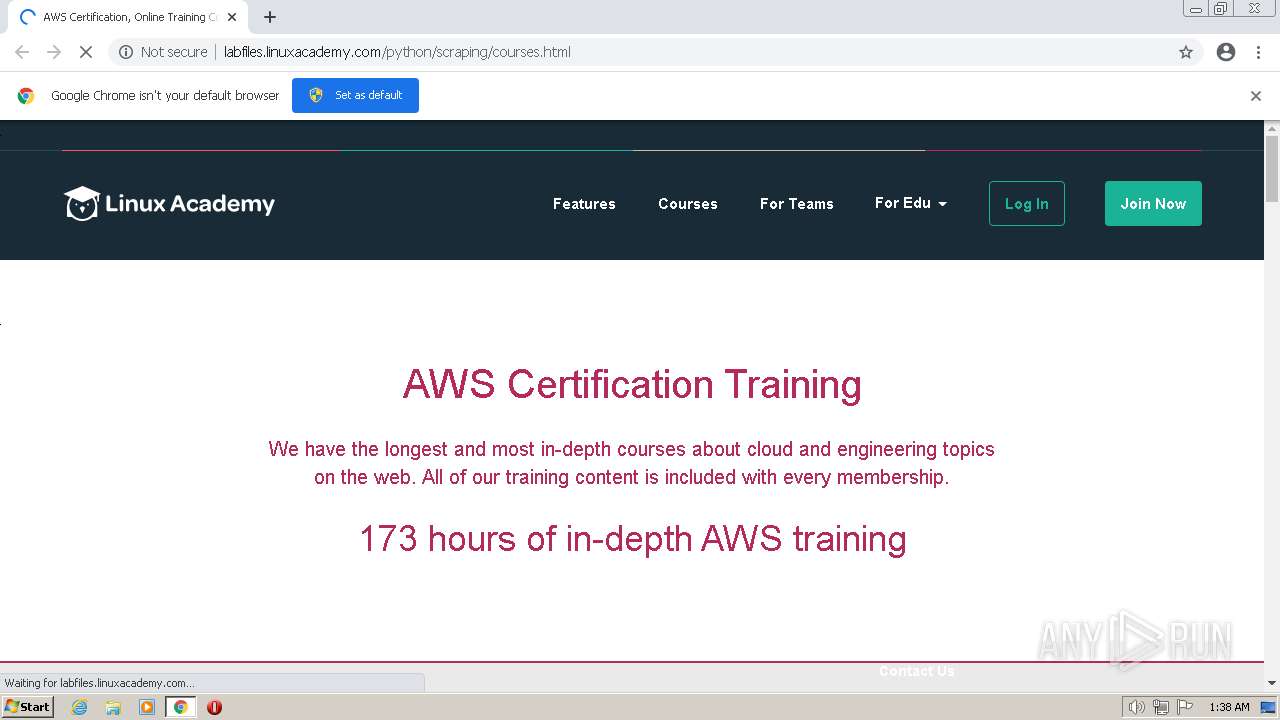
| URL: | http://labfiles.linuxacademy.com/python/scraping/courses.html |
| Full analysis: | https://app.any.run/tasks/c3ce5d06-da5c-47a1-a54d-173e53a14463 |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2022, 01:37:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7C2A3470B1A0036C730B34402ED4ABEC |
| SHA1: | 806DBE6EF44277B6BBAAC1778A543A110A4339CE |
| SHA256: | 59B05A99BB97A61FF599F0A6DF4006ABA5061611B8EFE5607813FA5F56E890CC |
| SSDEEP: | 3:N1KSEjMJvEmGK32RN+AEWP0n:CSMMJcmwRN+A/8 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
43
Monitored processes
10
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1048,6514088662931445458,12024778434633522598,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1256 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "http://labfiles.linuxacademy.com/python/scraping/courses.html" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1048,6514088662931445458,12024778434633522598,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3096 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6e95d988,0x6e95d998,0x6e95d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 3228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1048,6514088662931445458,12024778434633522598,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=2684 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 3232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1048,6514088662931445458,12024778434633522598,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1076 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 3500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,6514088662931445458,12024778434633522598,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 3620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,6514088662931445458,12024778434633522598,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2128 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 3756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,6514088662931445458,12024778434633522598,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1852 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 3896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1048,6514088662931445458,12024778434633522598,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3172 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
8 777
Read events
8 723
Write events
54
Delete events
0
Modification events
| (PID) Process: | (856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (856) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
0
Suspicious files
13
Text files
61
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-638E9CF6-358.pma | — | |
MD5:— | SHA256:— | |||
| 856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c03ca5c6-9100-4b98-8de2-4e05818a392e.tmp | text | |
MD5:— | SHA256:— | |||
| 856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF106f9e6.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF106fa15.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences~RF106fbda.TMP | text | |
MD5:8304B8F42465198890090F52D3F80A4C | SHA256:80C32AC2585E7E81200104B1630F19560A156C4ABF51B5888B0FBF07323FAB34 | |||
| 856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF106fb2e.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1a7cb497-b32e-4167-8b8a-5a46ce4f2666.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
50
TCP/UDP connections
79
DNS requests
23
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
588 | chrome.exe | GET | 200 | 13.32.27.18:80 | http://labfiles.linuxacademy.com/python/scraping/courses_files/ec873c5fbb92e012712dd16d4438fb01_da675d7bda62b7f68062ebe1e20f4c1d_7132c63328c1aec866488d807afd91aa_5a7fa679c5aa33c13eca56c1584d2914_.css | US | text | 182 Kb | malicious |
588 | chrome.exe | GET | 200 | 13.32.27.18:80 | http://labfiles.linuxacademy.com/python/scraping/courses.html | US | html | 87.6 Kb | malicious |
588 | chrome.exe | GET | 200 | 13.32.27.18:80 | http://labfiles.linuxacademy.com/python/scraping/courses_files/j.php | US | text | 672 b | malicious |
588 | chrome.exe | GET | 200 | 13.32.27.23:80 | http://labfiles.linuxacademy.com/python/scraping/courses_files/oct.js | US | text | 13.8 Kb | malicious |
588 | chrome.exe | GET | 200 | 13.32.27.23:80 | http://labfiles.linuxacademy.com/python/scraping/courses_files/bf3bae2cdaede44a4d573035bff796e8_fb32fedafa452a5f0c7cdfe806e39cb3_c5fcd81a7e2d4f93d57b03cc96dfc1a5_0e91c2903715c2a55851608c02d1ff8a_.js | US | text | 67.4 Kb | malicious |
588 | chrome.exe | GET | 200 | 13.32.27.18:80 | http://labfiles.linuxacademy.com/python/scraping/courses_files/saved_resource.html | US | html | 556 b | malicious |
588 | chrome.exe | GET | 200 | 13.32.27.23:80 | http://labfiles.linuxacademy.com/python/scraping/courses_files/dc24c5f64d1f274a9cf0c51f34001b52_d79168bceb42084acc0c35e28363ef35_d79168bceb42084acc0c35e28363ef35_1e7acc518c7bf96420b71bbe3d5ad626_.js | US | text | 204 Kb | malicious |
588 | chrome.exe | GET | 200 | 13.32.27.23:80 | http://labfiles.linuxacademy.com/python/scraping/courses_files/5DZIKWU2NBGHNIYFXDWMUG | US | text | 3.91 Kb | malicious |
588 | chrome.exe | GET | 200 | 13.32.27.18:80 | http://labfiles.linuxacademy.com/python/scraping/courses_files/mc-validate.js | US | text | 147 Kb | malicious |
588 | chrome.exe | GET | 200 | 13.32.27.18:80 | http://labfiles.linuxacademy.com/python/scraping/courses_files/out | US | text | 33.7 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
588 | chrome.exe | 142.250.185.78:443 | clients2.google.com | GOOGLE | US | whitelisted |
588 | chrome.exe | 172.217.18.3:443 | ssl.gstatic.com | GOOGLE | US | whitelisted |
588 | chrome.exe | 13.32.27.23:80 | labfiles.linuxacademy.com | AMAZON-02 | US | suspicious |
588 | chrome.exe | 142.250.186.161:443 | clients2.googleusercontent.com | GOOGLE | US | whitelisted |
588 | chrome.exe | 13.32.27.18:80 | labfiles.linuxacademy.com | AMAZON-02 | US | suspicious |
588 | chrome.exe | 34.96.102.137:80 | dev.visualwebsiteoptimizer.com | GOOGLE | US | suspicious |
588 | chrome.exe | 184.24.77.156:443 | use.typekit.net | Akamai International B.V. | DE | suspicious |
— | — | 13.32.27.23:80 | labfiles.linuxacademy.com | AMAZON-02 | US | suspicious |
588 | chrome.exe | 13.32.27.118:80 | assets.linuxacademy.com | AMAZON-02 | US | unknown |
588 | chrome.exe | 185.60.216.19:80 | connect.facebook.net | FACEBOOK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
labfiles.linuxacademy.com |
| malicious |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
dev.visualwebsiteoptimizer.com |
| whitelisted |
assets.linuxacademy.com |
| malicious |
use.typekit.net |
| whitelisted |
maxcdn.bootstrapcdn.com |
| whitelisted |
linuxacademy.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
588 | chrome.exe | Potentially Bad Traffic | ET INFO Possible Phish - Saved Website Comment Observed |
588 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Possible Injected JS Form Stealer Checking Page Contents M1 |
588 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Possible Injected JS Form Stealer Checking Page Contents M1 |
588 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Possible Injected JS Form Stealer Checking Page Contents M1 |