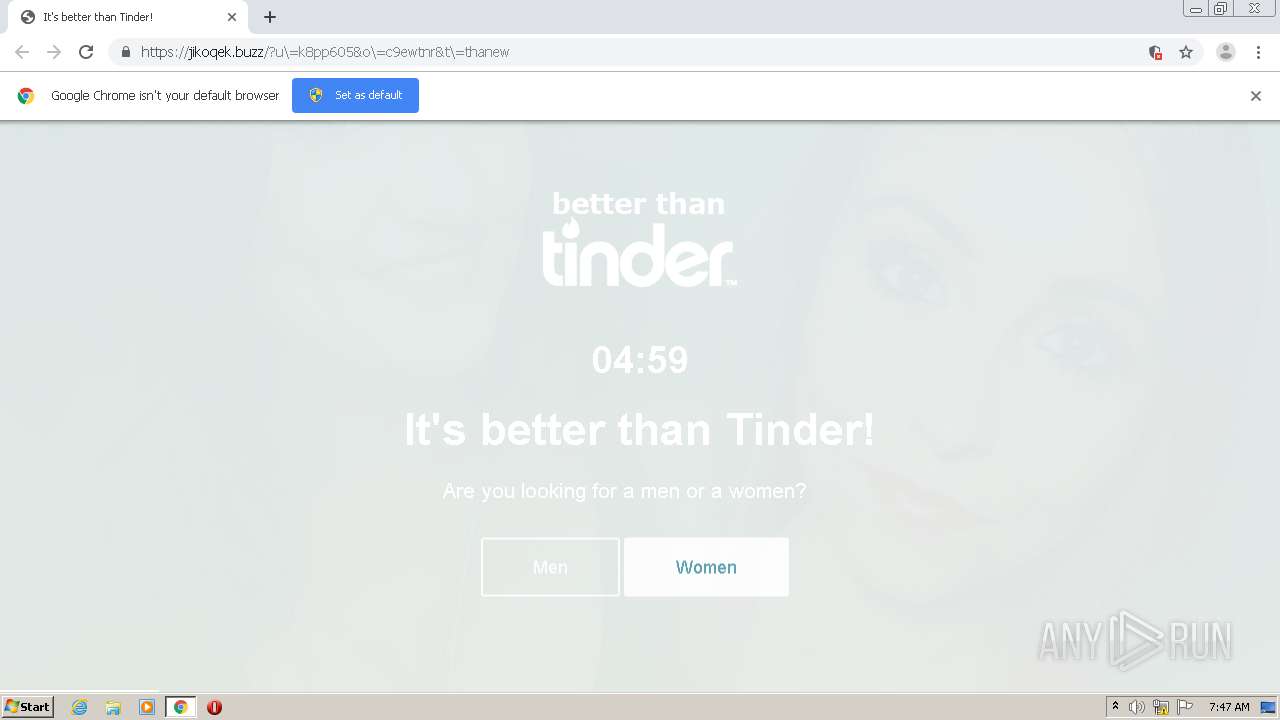
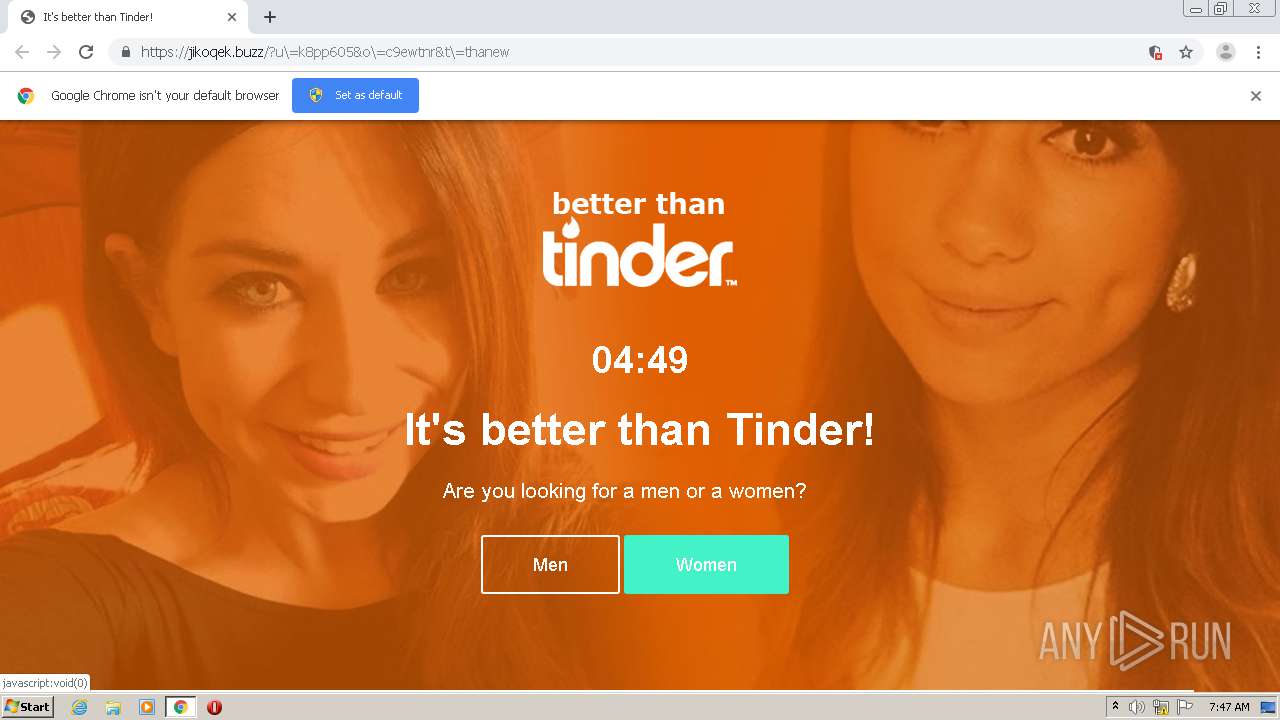
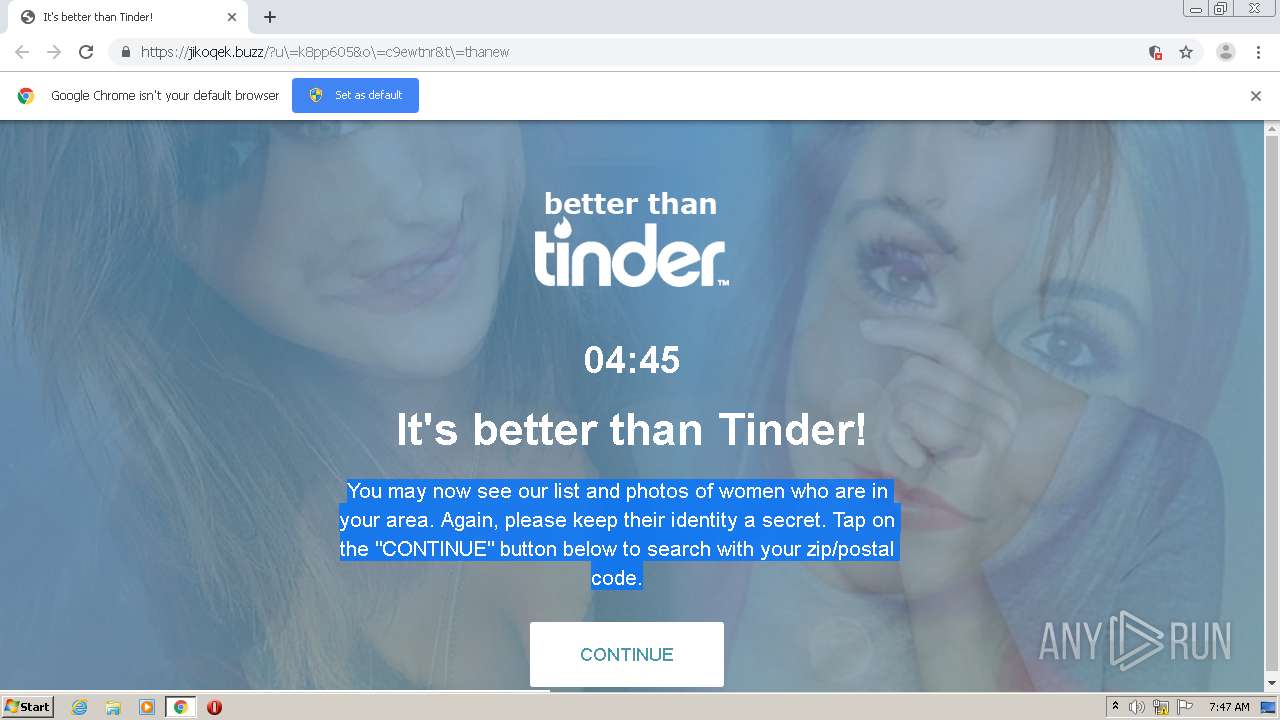
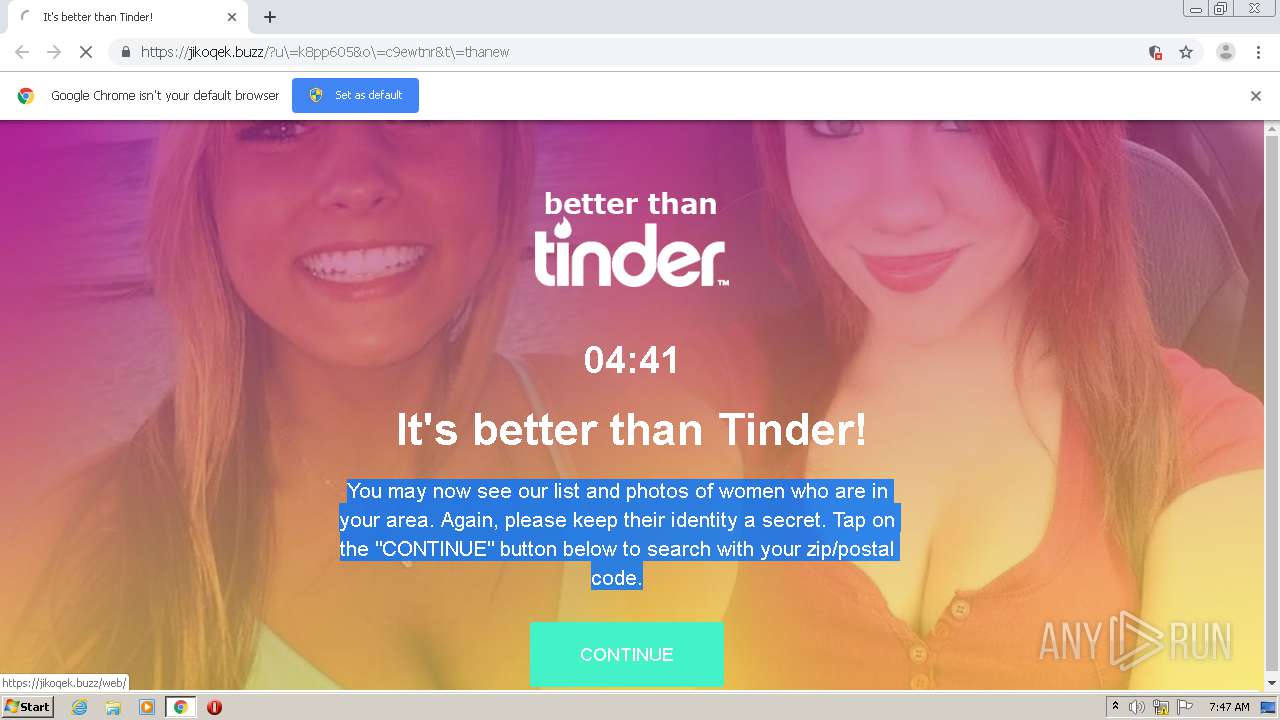
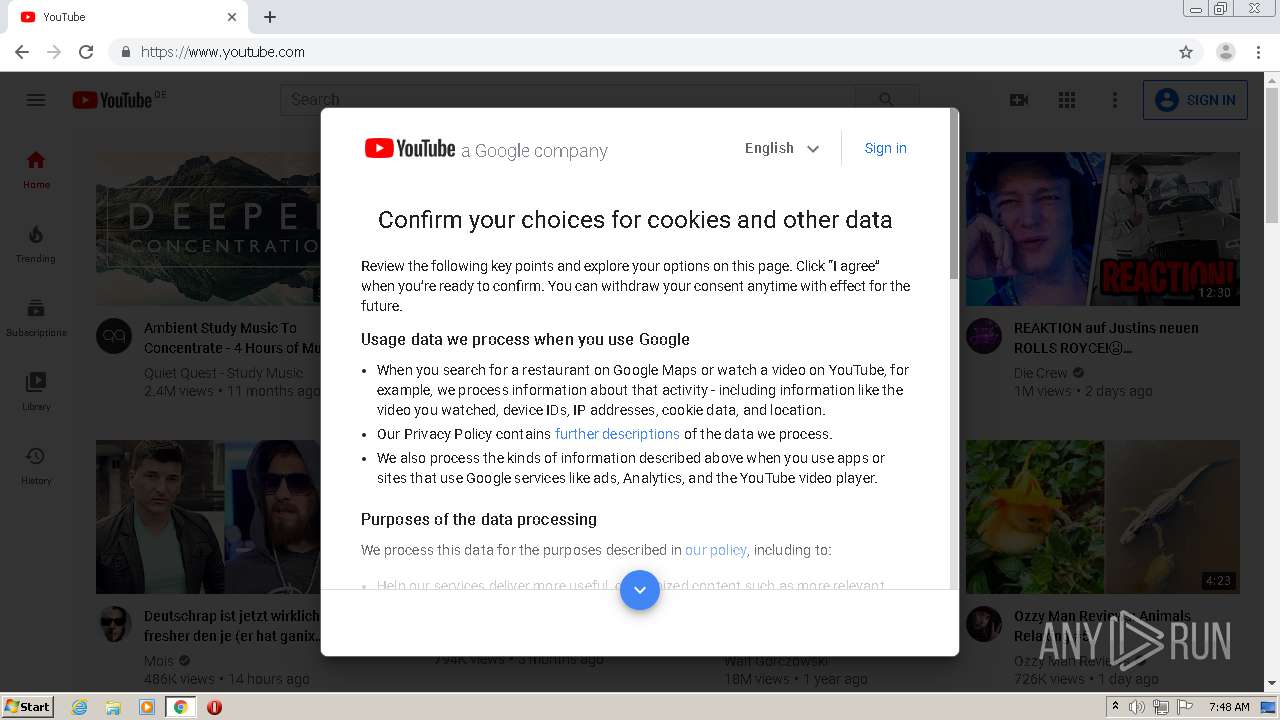
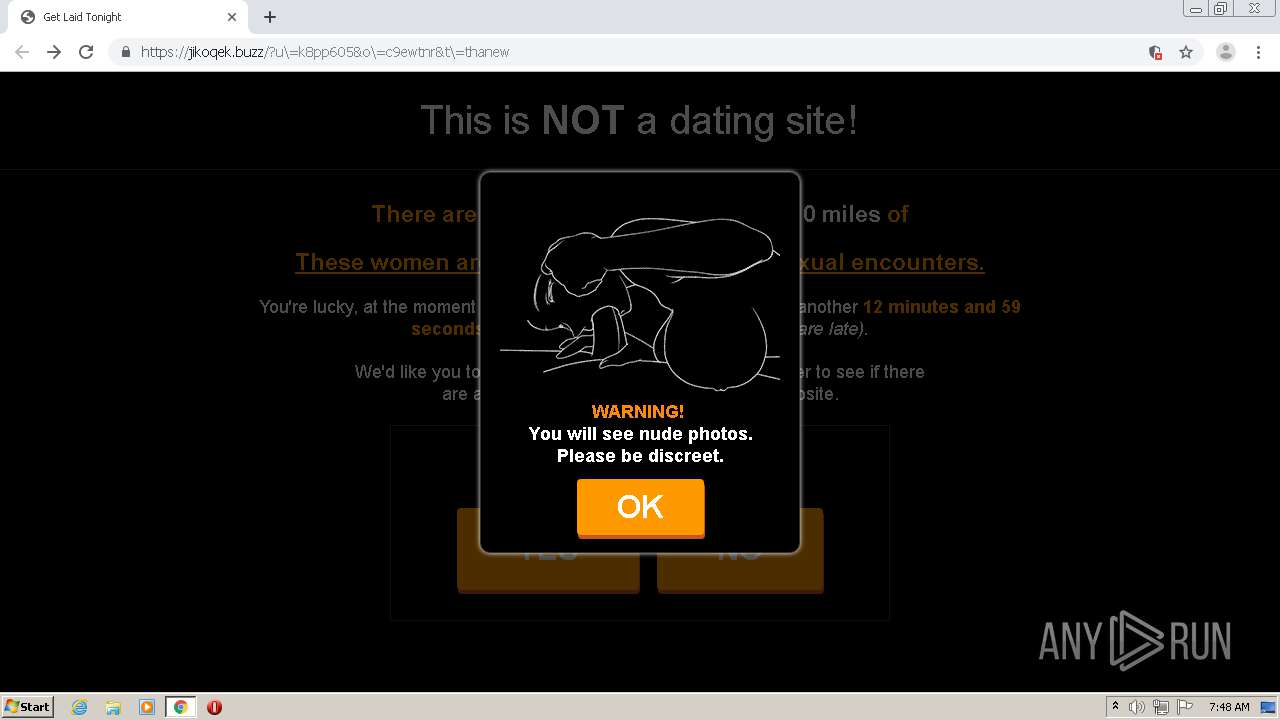
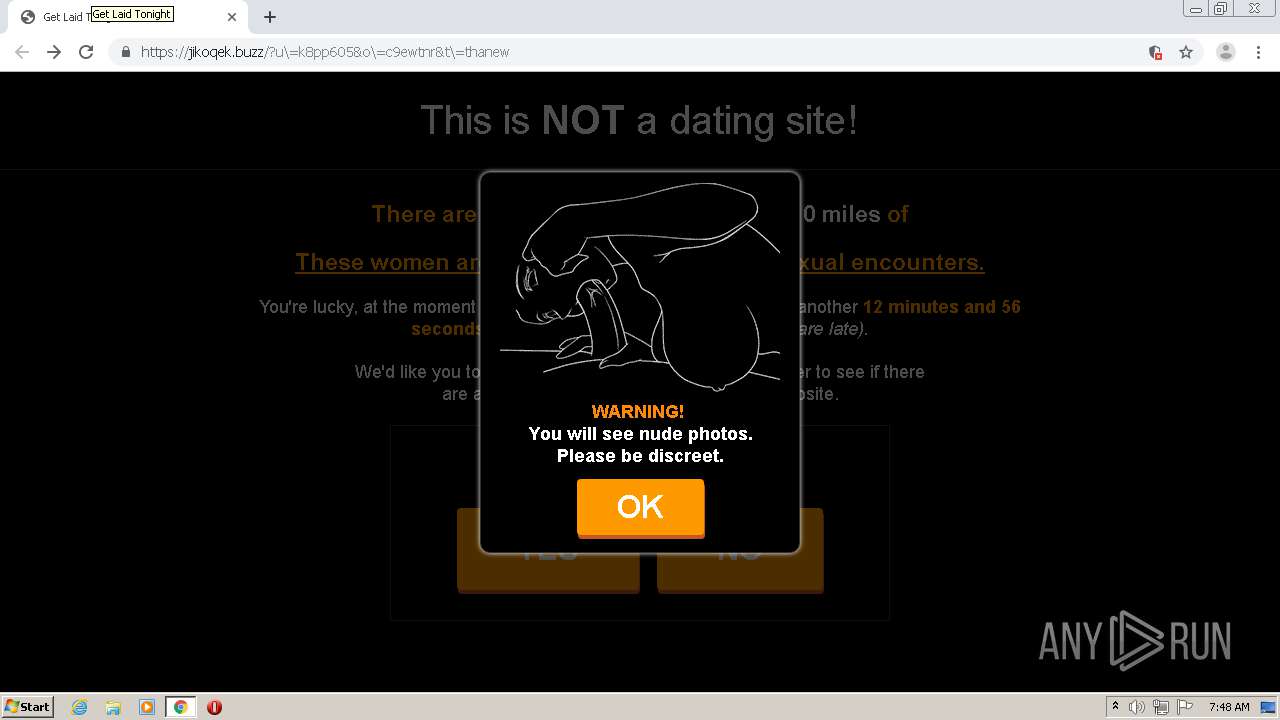
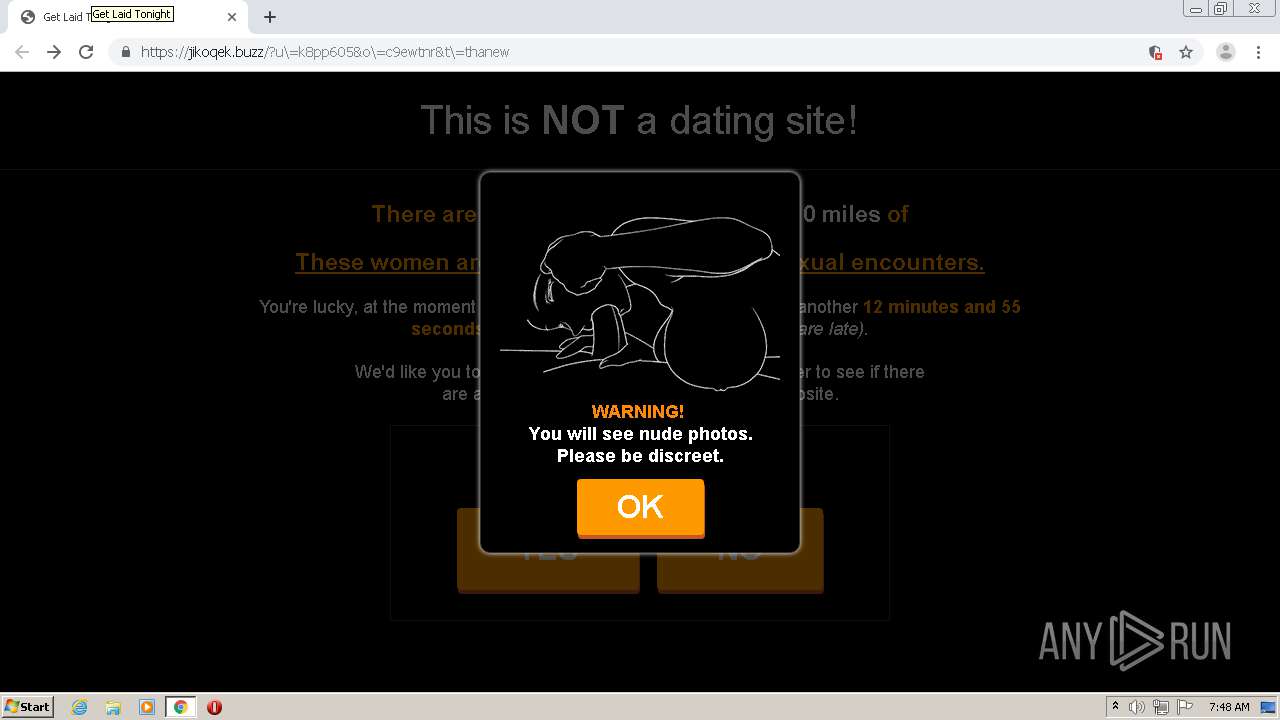
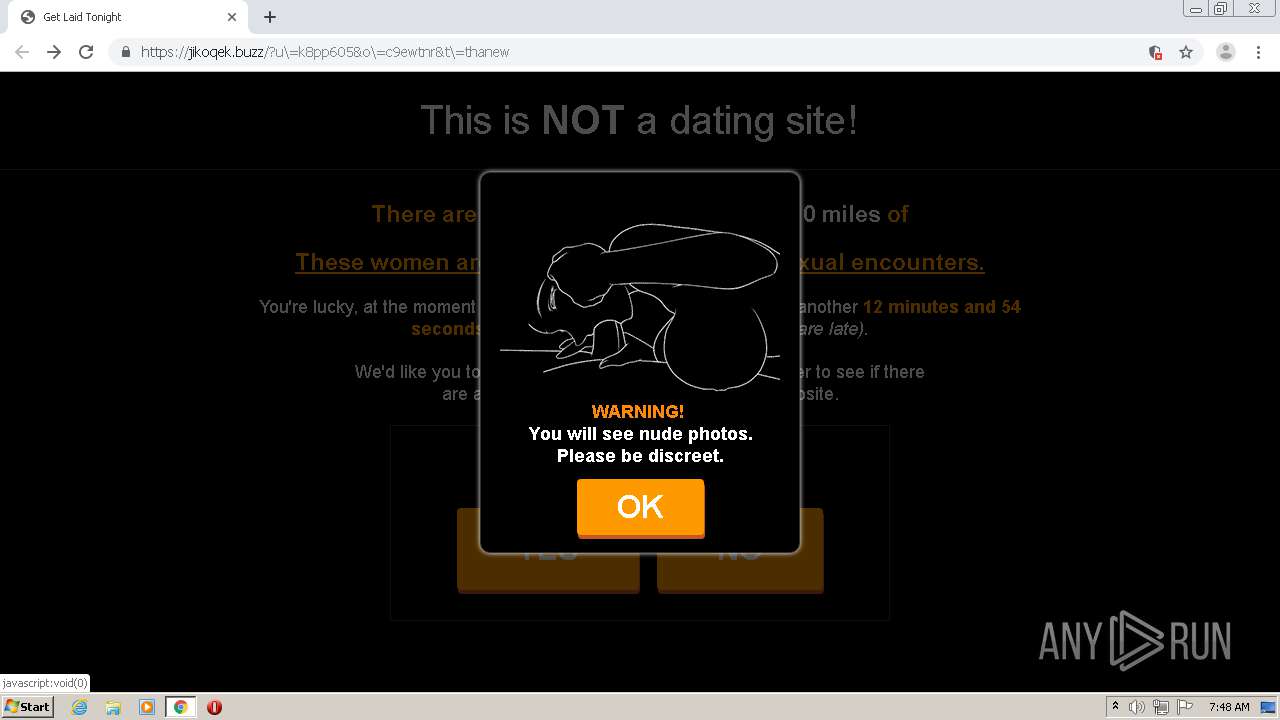
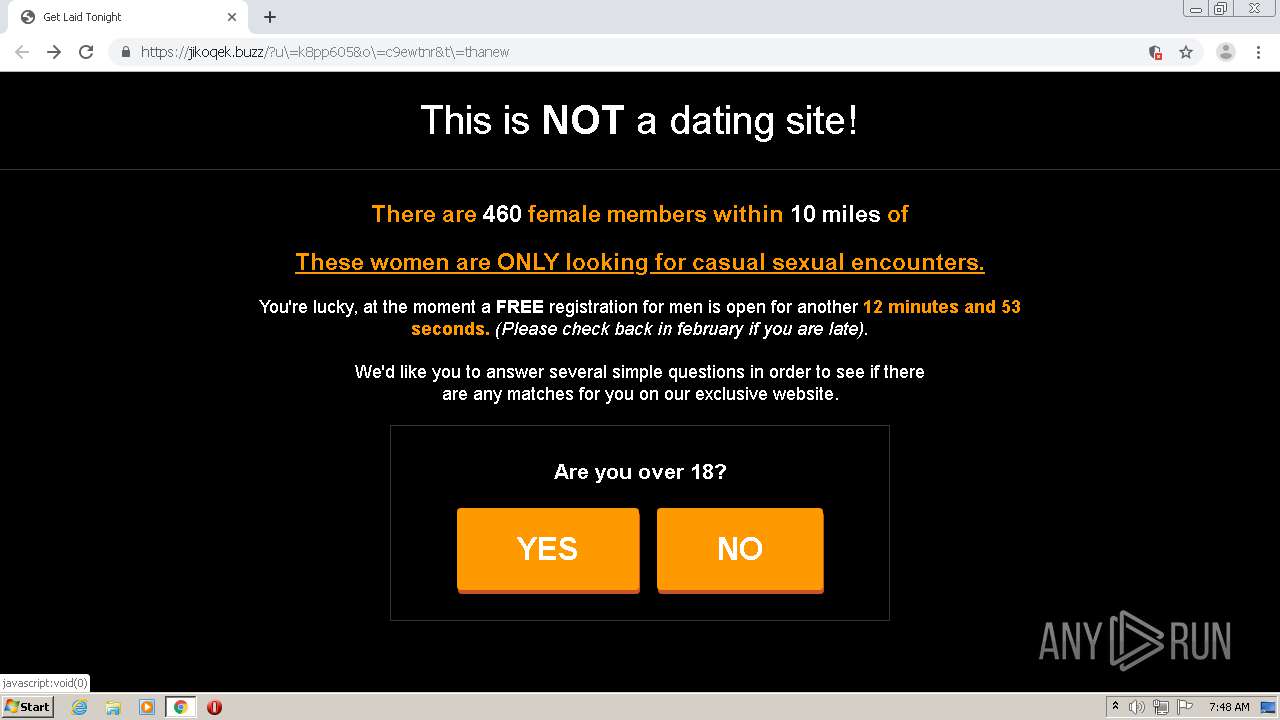
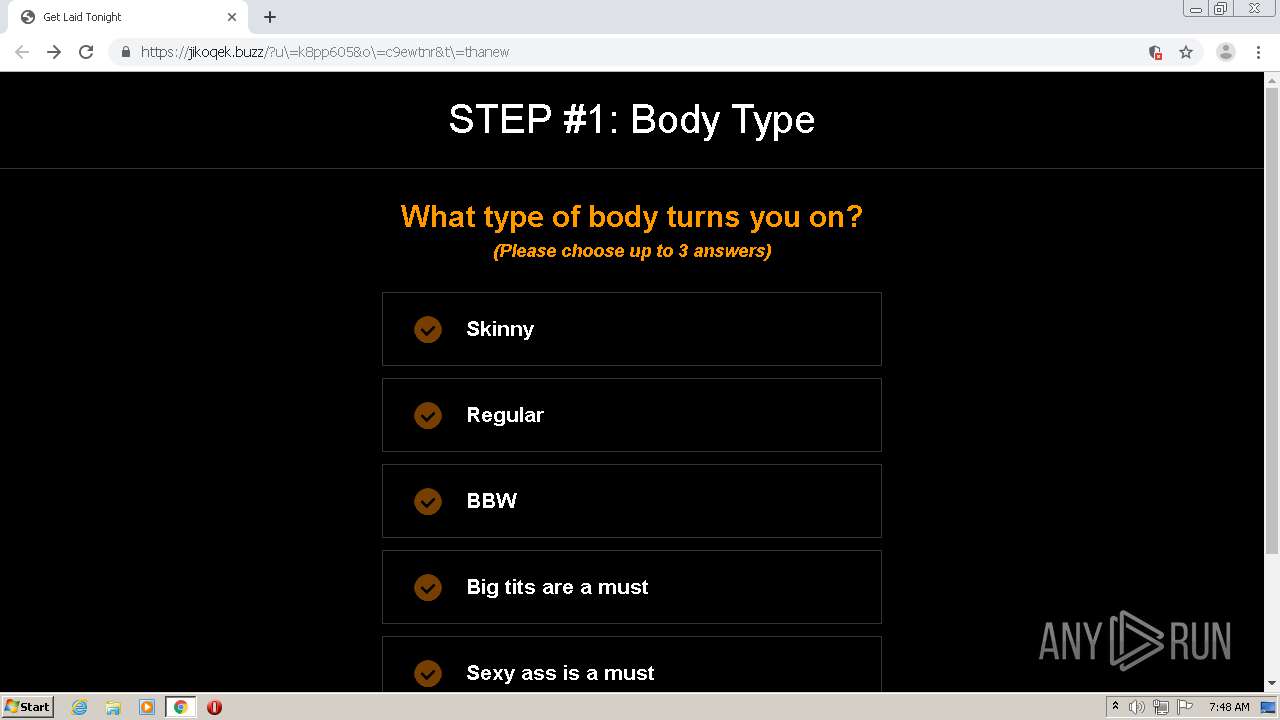
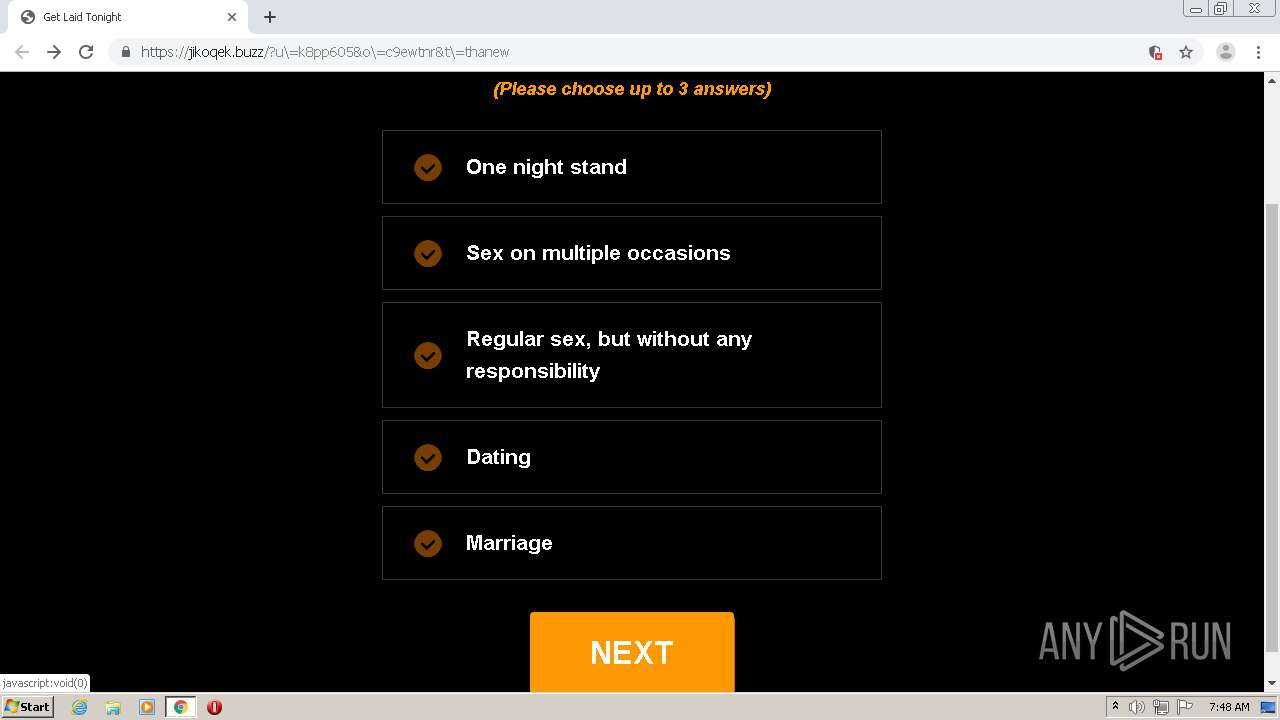
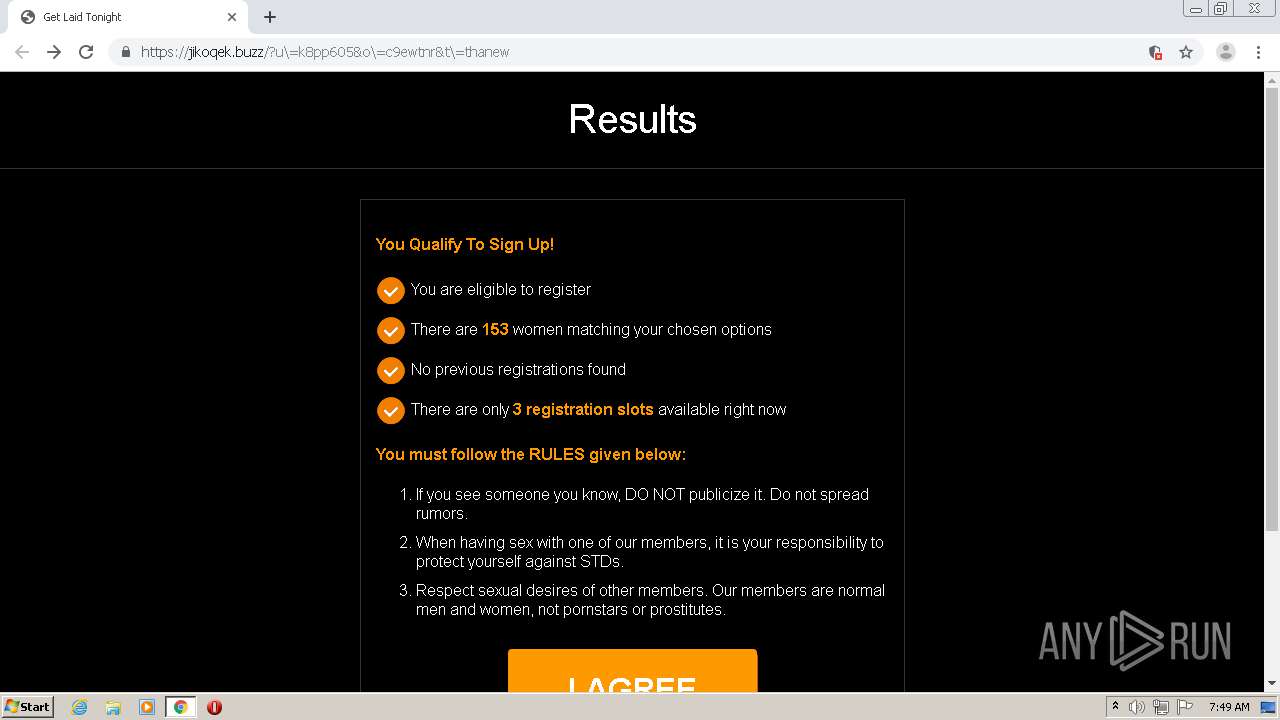
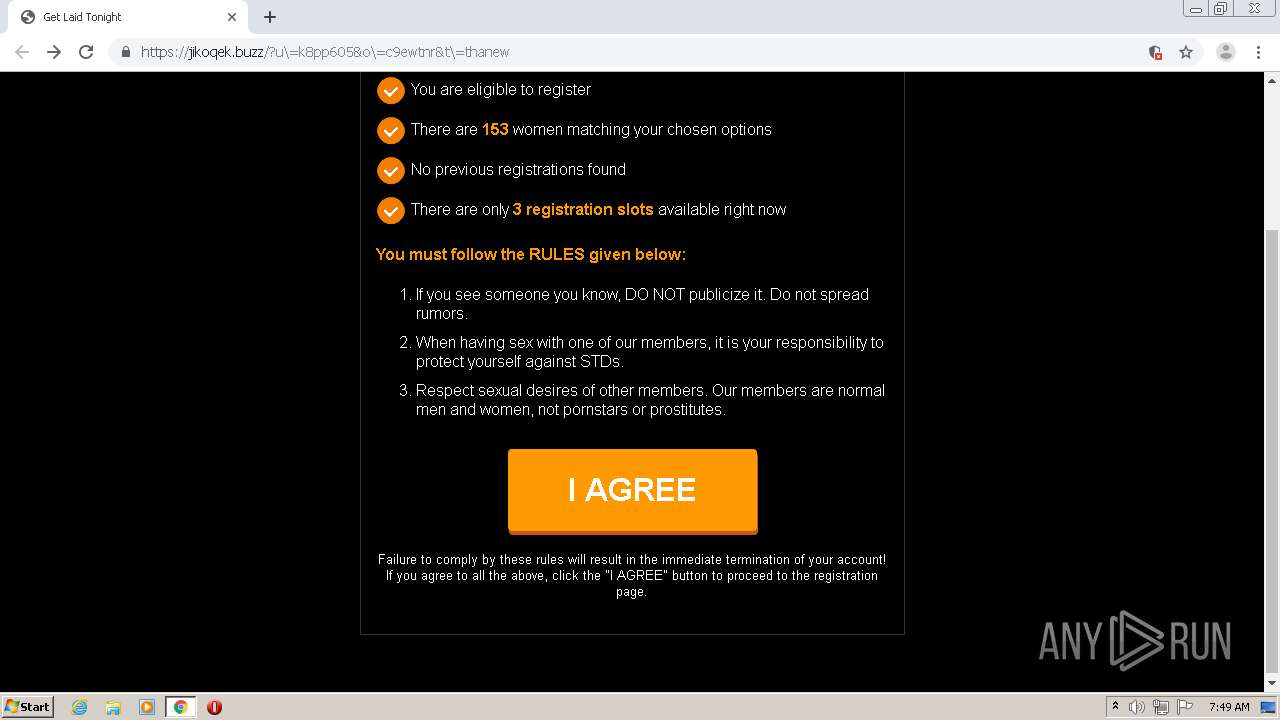
| URL: | http://jikoqek.buzz/?u\=k8pp605&o\=c9ewtnr&t\=thanew |
| Full analysis: | https://app.any.run/tasks/aaace949-f4bf-49b0-8f8c-b4c3ff719814 |
| Verdict: | Malicious activity |
| Analysis date: | January 05, 2021, 07:47:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 568CB036FB99C94B9EF3CB18C7992D2F |
| SHA1: | 1DDAED2F8961CC6C7C0A0255340520F0CB1A5ECD |
| SHA256: | 599F3D562AB6C15A3871B1696BFD3C9192FF452AFEB801BE3CF118B24419E4A0 |
| SSDEEP: | 3:N1KUyUrzjay/L5rUR4RMAS:CUyILGR4RM3 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 1540)
Reads the hosts file
- chrome.exe (PID: 1540)
- chrome.exe (PID: 1756)
Reads settings of System Certificates
- chrome.exe (PID: 1756)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
60
Monitored processes
25
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,16360920075182319709,9993600982492634187,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4167830258203466410 --mojo-platform-channel-handle=1008 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 716 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,16360920075182319709,9993600982492634187,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9833355510921116167 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1628 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,16360920075182319709,9993600982492634187,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16427177388655131420 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2836 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,16360920075182319709,9993600982492634187,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4076738527874192017 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2316 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "http://jikoqek.buzz/?u\=k8pp605&o\=c9ewtnr&t\=thanew" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,16360920075182319709,9993600982492634187,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=3984443633608372008 --mojo-platform-channel-handle=1540 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,16360920075182319709,9993600982492634187,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3177826858168653160 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3044 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,16360920075182319709,9993600982492634187,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14153246877522038818 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3296 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,16360920075182319709,9993600982492634187,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=641050286322888979 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2720 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,16360920075182319709,9993600982492634187,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3440969289342290770 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2424 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
625
Read events
557
Write events
65
Delete events
3
Modification events
| (PID) Process: | (1540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2248) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1540-13254306455486750 |
Value: 259 | |||
| (PID) Process: | (1540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1540) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
Executable files
0
Suspicious files
64
Text files
87
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FF41998-604.pma | — | |
MD5:— | SHA256:— | |||
| 1540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d1ea7263-c62d-442f-a0f3-21611b06401e.tmp | — | |
MD5:— | SHA256:— | |||
| 1540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF127d75.TMP | text | |
MD5:— | SHA256:— | |||
| 1540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF127d75.TMP | text | |
MD5:— | SHA256:— | |||
| 1540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF127d94.TMP | text | |
MD5:— | SHA256:— | |||
| 1540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 1540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF128044.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
187
TCP/UDP connections
88
DNS requests
32
Threats
91
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
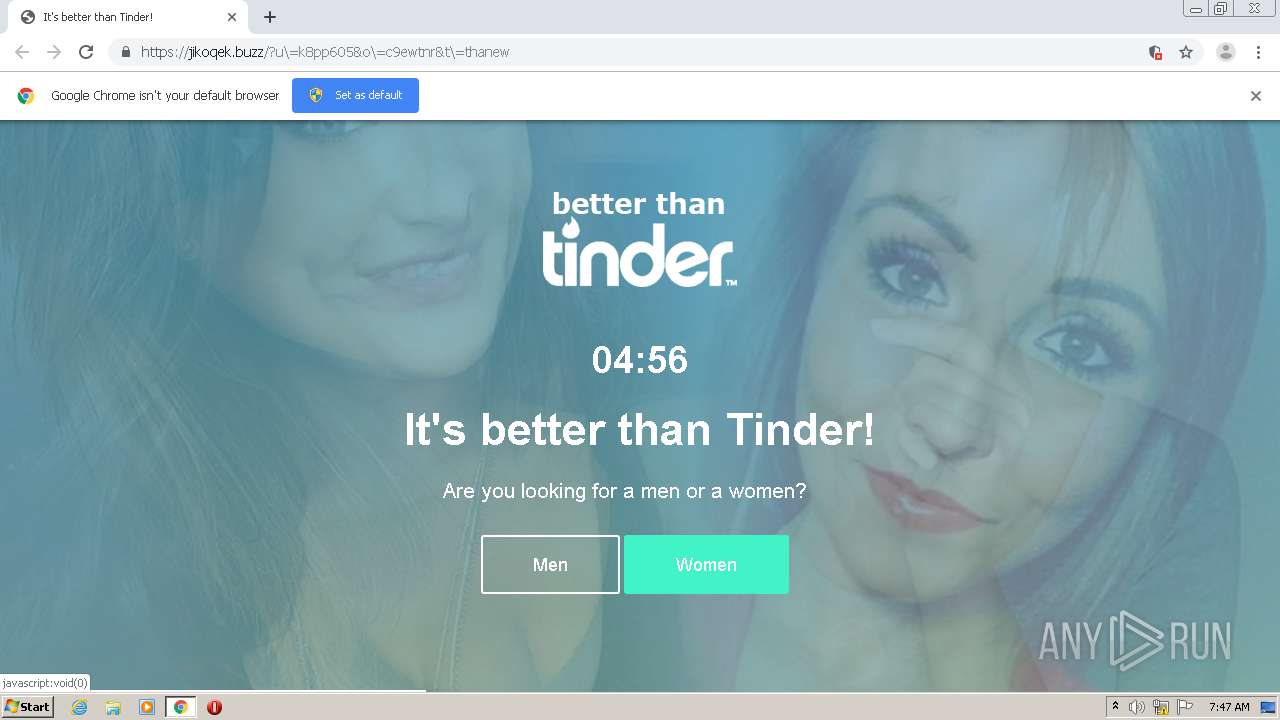
1756 | chrome.exe | POST | 200 | 173.239.5.6:80 | http://megadating2299.com/ | US | html | 158 b | malicious |
1756 | chrome.exe | GET | 301 | 85.25.154.142:80 | http://jikoqek.buzz/?u\=k8pp605&o\=c9ewtnr&t\=thanew | DE | html | 178 b | suspicious |
1756 | chrome.exe | GET | 200 | 173.239.5.6:80 | http://megadating2299.com/ | US | html | 252 b | malicious |
1756 | chrome.exe | GET | 200 | 213.247.47.190:80 | http://dr3.megadating2299.com/ | US | html | 252 b | malicious |
1756 | chrome.exe | POST | 200 | 173.239.5.6:80 | http://megadating2299.com/ | US | html | 158 b | malicious |
1756 | chrome.exe | GET | 200 | 213.247.47.190:80 | http://dr3.megadating2299.com/ | US | html | 252 b | malicious |
1756 | chrome.exe | POST | 200 | 173.239.5.6:80 | http://megadating2299.com/ | US | html | 158 b | malicious |
1756 | chrome.exe | POST | 200 | 173.239.5.6:80 | http://megadating2299.com/ | US | html | 158 b | malicious |
1756 | chrome.exe | GET | 200 | 213.247.47.190:80 | http://dr3.megadating2299.com/ | US | html | 252 b | malicious |
1756 | chrome.exe | GET | 200 | 213.247.47.190:80 | http://dr3.megadating2299.com/ | US | html | 252 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1756 | chrome.exe | 85.25.154.142:80 | jikoqek.buzz | Host Europe GmbH | DE | suspicious |
1756 | chrome.exe | 85.25.154.142:443 | jikoqek.buzz | Host Europe GmbH | DE | suspicious |
— | — | 85.25.154.142:443 | jikoqek.buzz | Host Europe GmbH | DE | suspicious |
1756 | chrome.exe | 216.58.205.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
1756 | chrome.exe | 35.190.80.1:443 | a.nel.cloudflare.com | Google Inc. | US | suspicious |
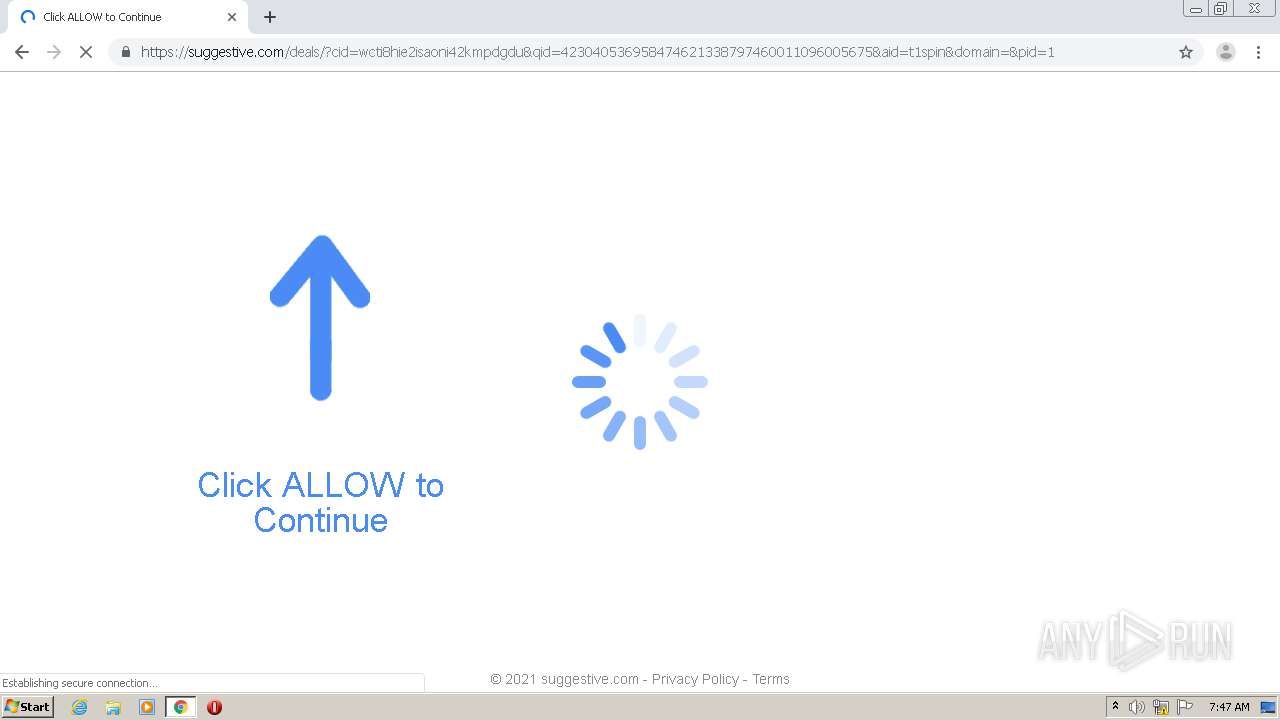
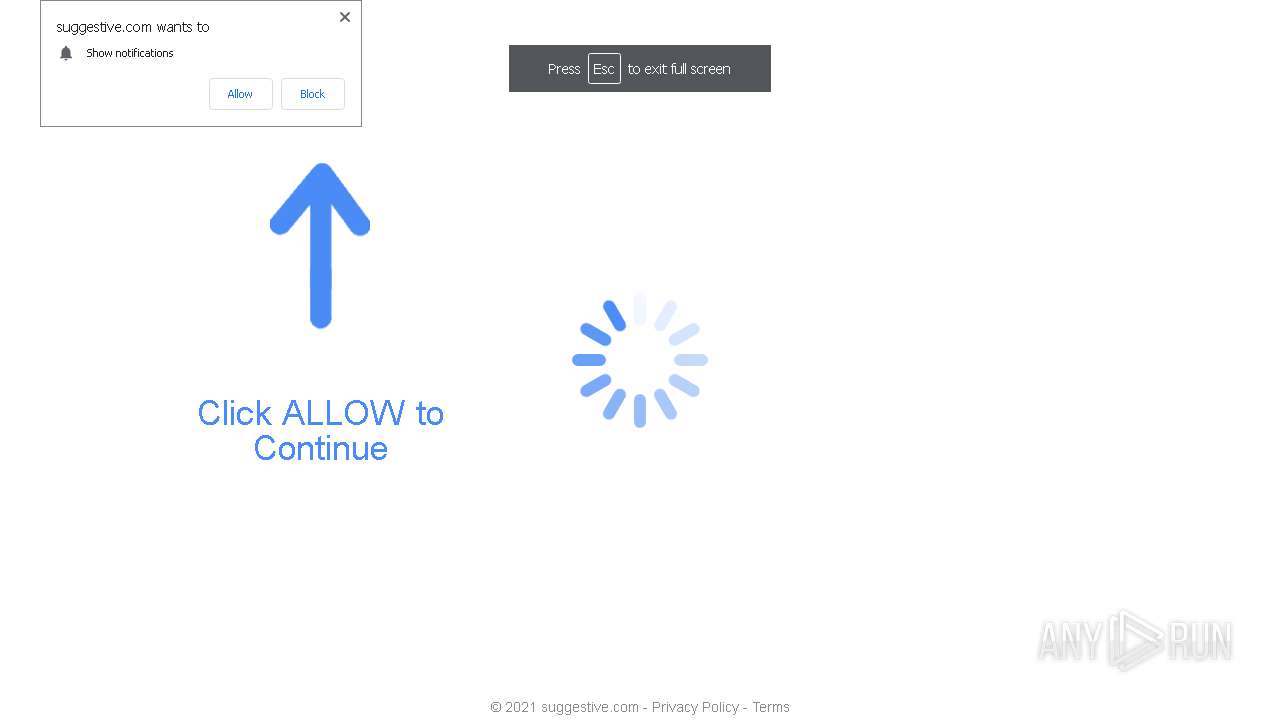
1756 | chrome.exe | 13.224.194.75:443 | cdn.aimtell.com | — | US | malicious |
1756 | chrome.exe | 172.217.23.147:443 | beacon.aimtell.com | Google Inc. | US | whitelisted |
1756 | chrome.exe | 172.217.214.139:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
1756 | chrome.exe | 45.40.140.1:443 | x.co | GoDaddy.com, LLC | US | malicious |
1756 | chrome.exe | 74.125.126.188:5228 | mtalk.google.com | Google Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
jikoqek.buzz |
| suspicious |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
megadating2299.com |
| malicious |
track.traffic.name |
| shared |
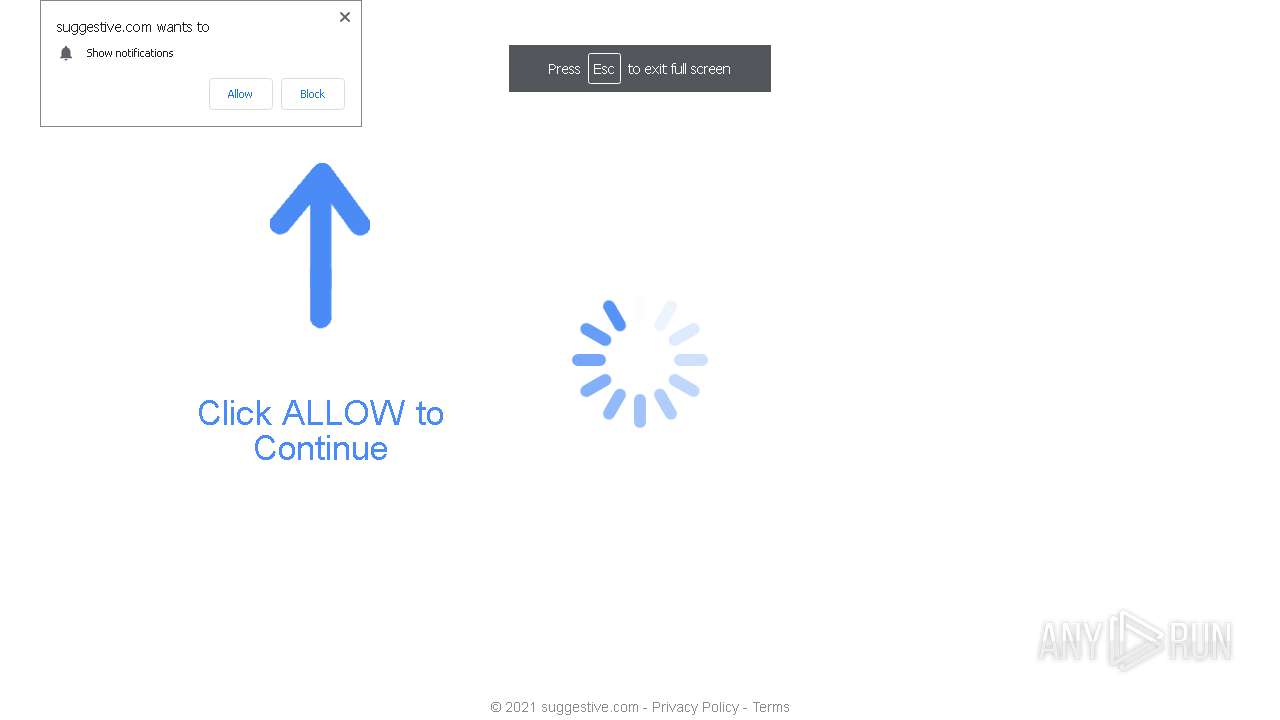
suggestive.com |
| malicious |
www.googletagmanager.com |
| whitelisted |
a.nel.cloudflare.com |
| whitelisted |
s3.amazonaws.com |
| shared |
www.google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1756 | chrome.exe | A Network Trojan was detected | ET MALWARE Win32/Zonebac Traffic Redirect |
1756 | chrome.exe | A Network Trojan was detected | ET MALWARE Win32/Zonebac Traffic Redirect |
1756 | chrome.exe | A Network Trojan was detected | ET MALWARE Win32/Zonebac Traffic Redirect |
1756 | chrome.exe | A Network Trojan was detected | ET MALWARE Win32/Zonebac Traffic Redirect |
1756 | chrome.exe | A Network Trojan was detected | ET MALWARE Win32/Zonebac Traffic Redirect |
1756 | chrome.exe | A Network Trojan was detected | ET MALWARE Win32/Zonebac Traffic Redirect |
1756 | chrome.exe | A Network Trojan was detected | ET MALWARE Win32/Zonebac Traffic Redirect |
1756 | chrome.exe | A Network Trojan was detected | ET MALWARE Win32/Zonebac Traffic Redirect |
1756 | chrome.exe | A Network Trojan was detected | ET MALWARE Win32/Zonebac Traffic Redirect |
1756 | chrome.exe | A Network Trojan was detected | ET MALWARE Win32/Zonebac Traffic Redirect |