| File name: | atlantis-bootstrapper.exe |
| Full analysis: | https://app.any.run/tasks/793269b0-00de-4af1-9141-7d141bf39716 |
| Verdict: | Malicious activity |
| Analysis date: | November 30, 2024, 09:42:44 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 7 sections |
| MD5: | 25997CBB649406506568C2A4BC3AA2D0 |
| SHA1: | 8F09588159EAAE93FBE61435C6E8D4C896327B24 |
| SHA256: | 5992A6957D67E61CA50A7E76C2C0C05A7094927F63E4EBAD0D806192834F0A73 |
| SSDEEP: | 98304:XySS8M9hMnrOdYiWwGYZLaP1MFvkpOWYs5+aibe7BNdCKo/IYvXWmc/Kz3lQvfnH:Ufo6v5vH |
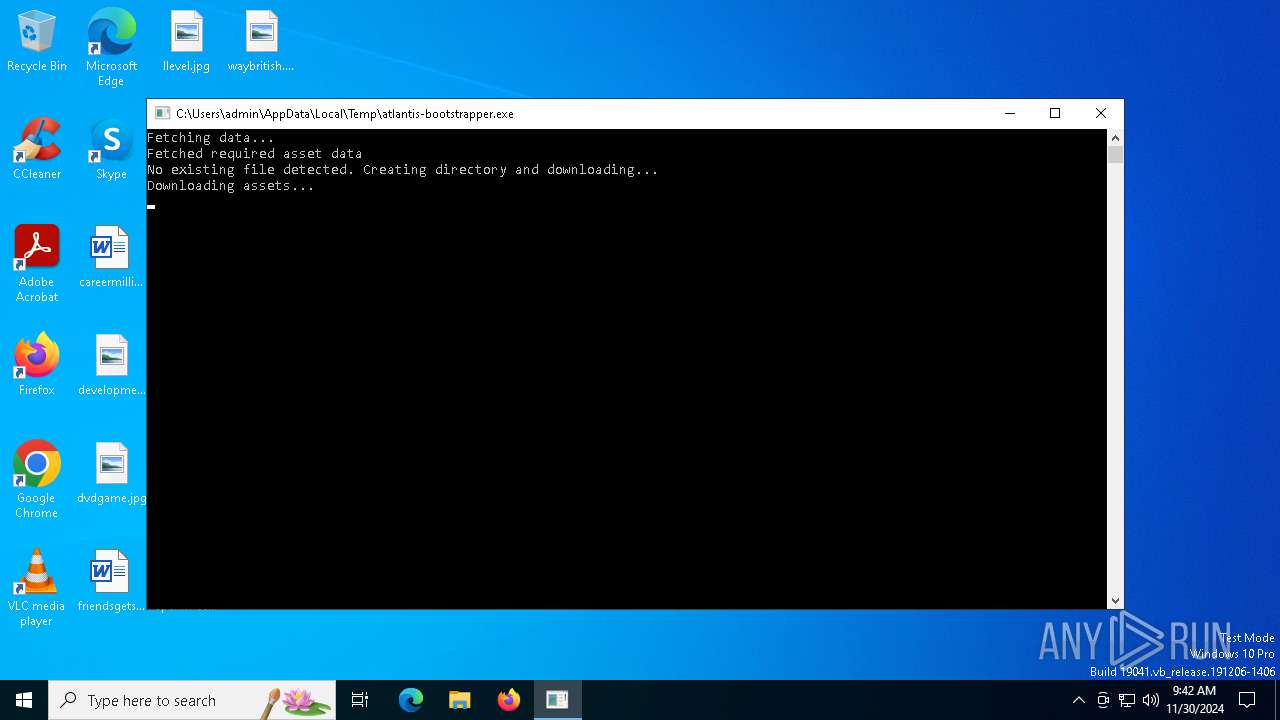
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- atlantis-bootstrapper.exe (PID: 6412)
Process drops legitimate windows executable
- atlantis-bootstrapper.exe (PID: 6412)
INFO
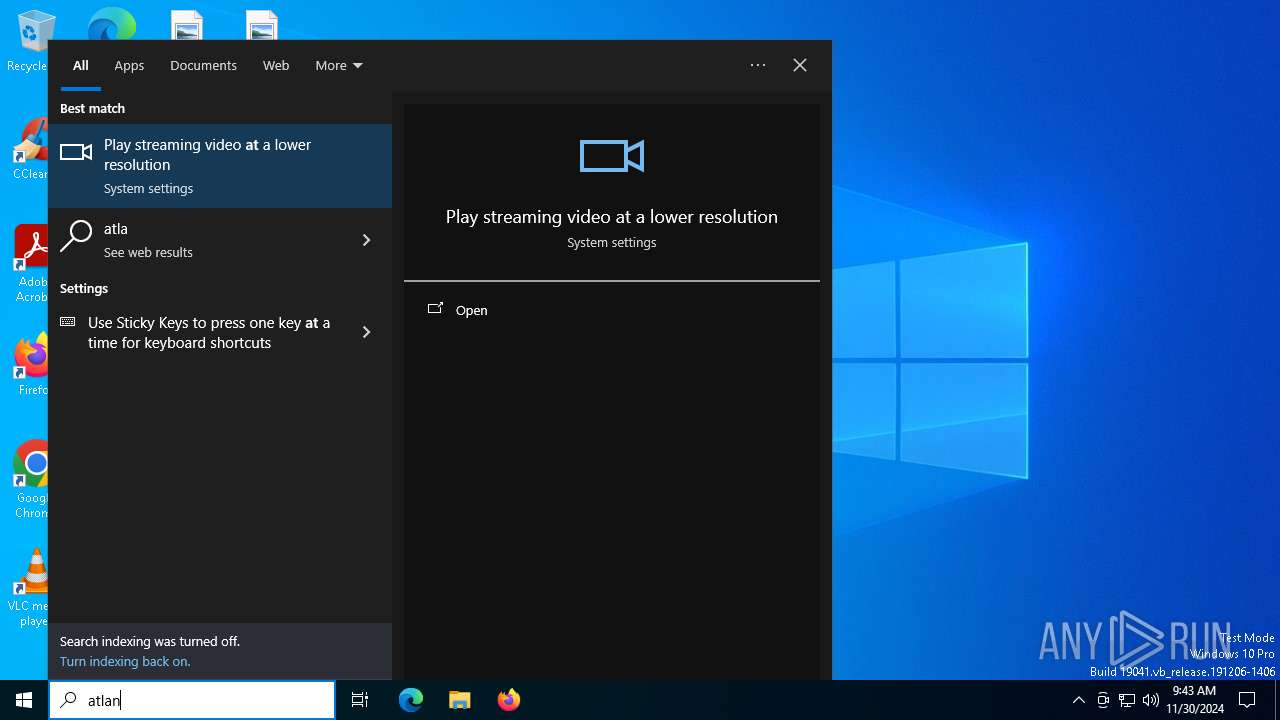
Checks supported languages
- atlantis-bootstrapper.exe (PID: 6412)
Reads the software policy settings
- atlantis-bootstrapper.exe (PID: 6412)
Checks proxy server information
- atlantis-bootstrapper.exe (PID: 6412)
Application based on Rust
- atlantis-bootstrapper.exe (PID: 6412)
Reads the computer name
- atlantis-bootstrapper.exe (PID: 6412)
Create files in a temporary directory
- atlantis-bootstrapper.exe (PID: 6412)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:11:28 16:37:57+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.42 |
| CodeSize: | 2524160 |
| InitializedDataSize: | 1260544 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb141e3 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
132
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
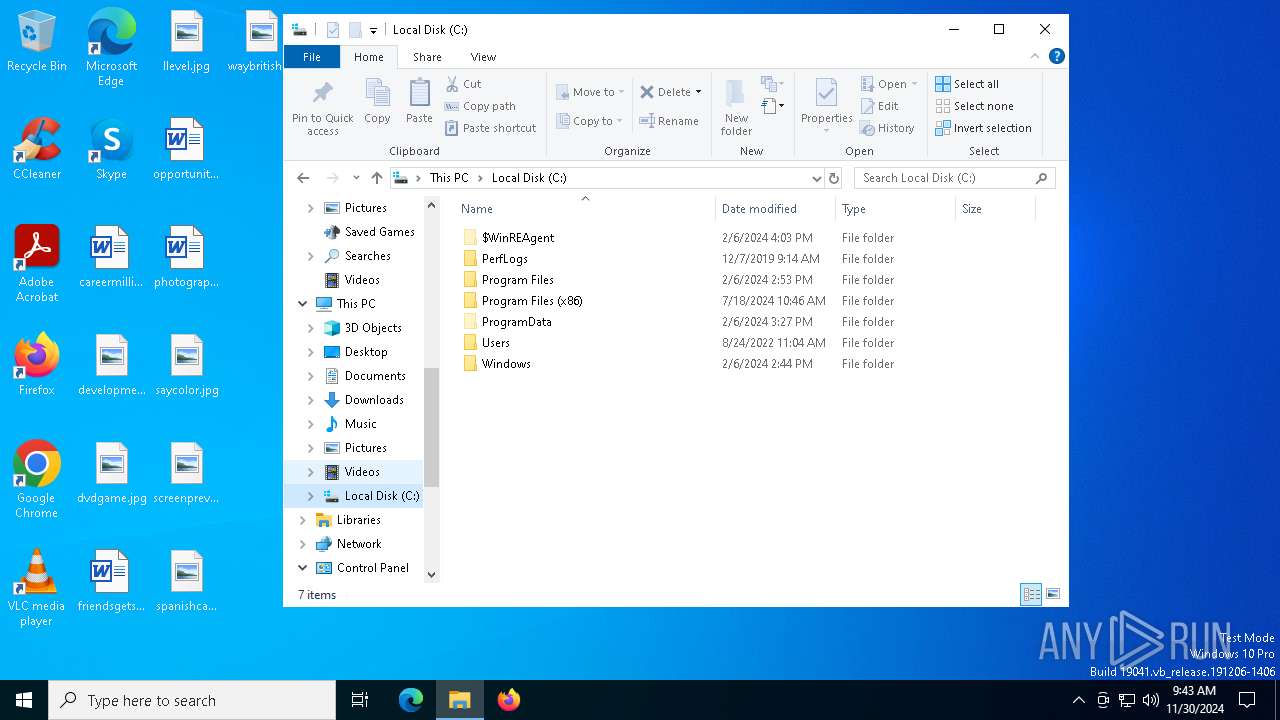
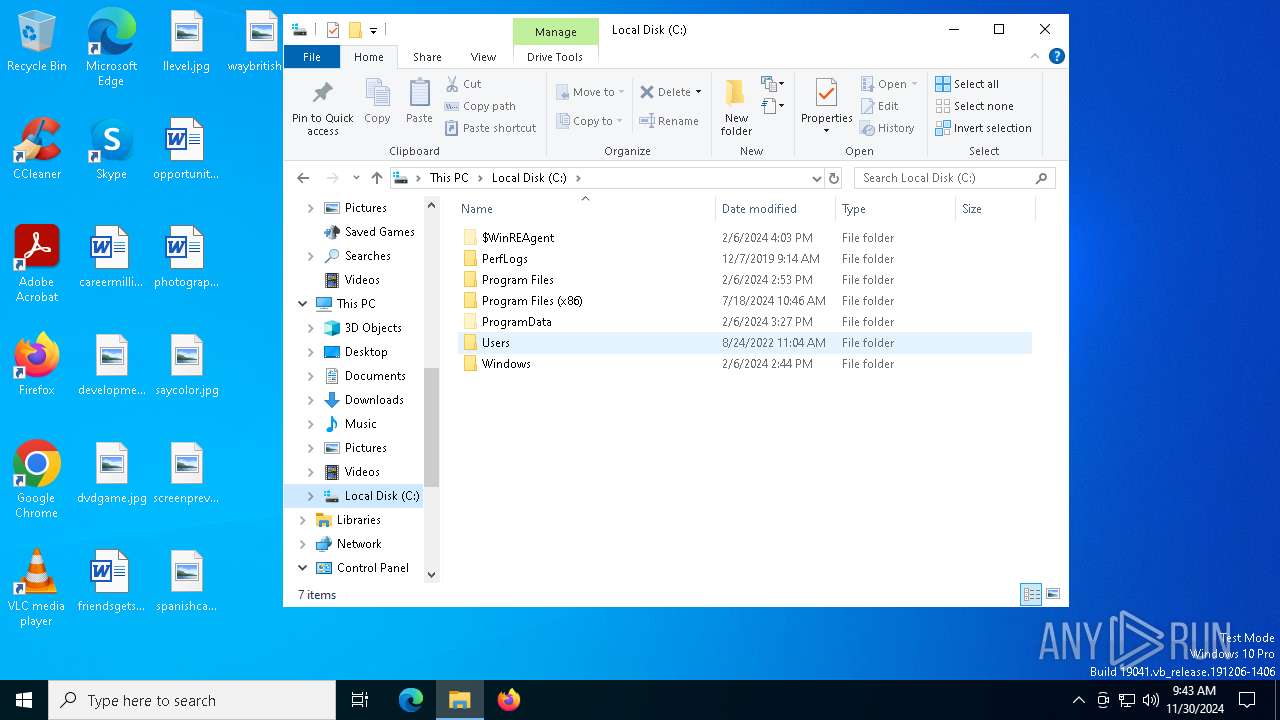
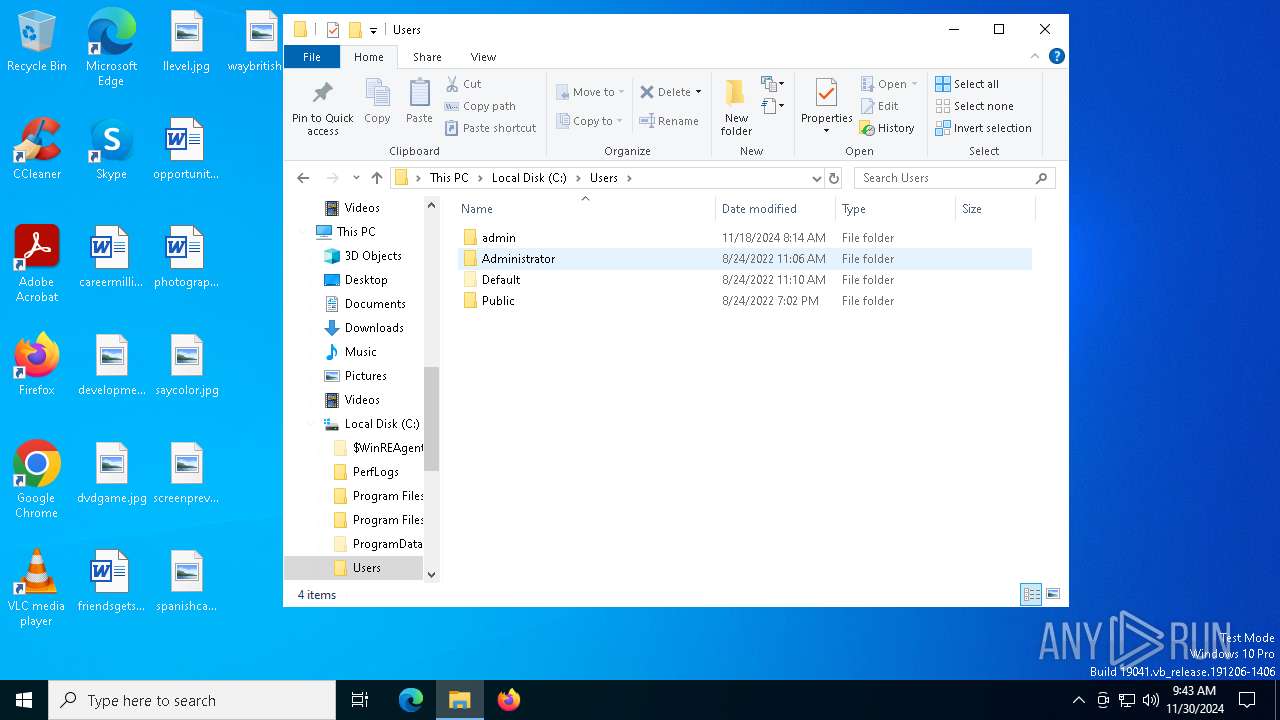
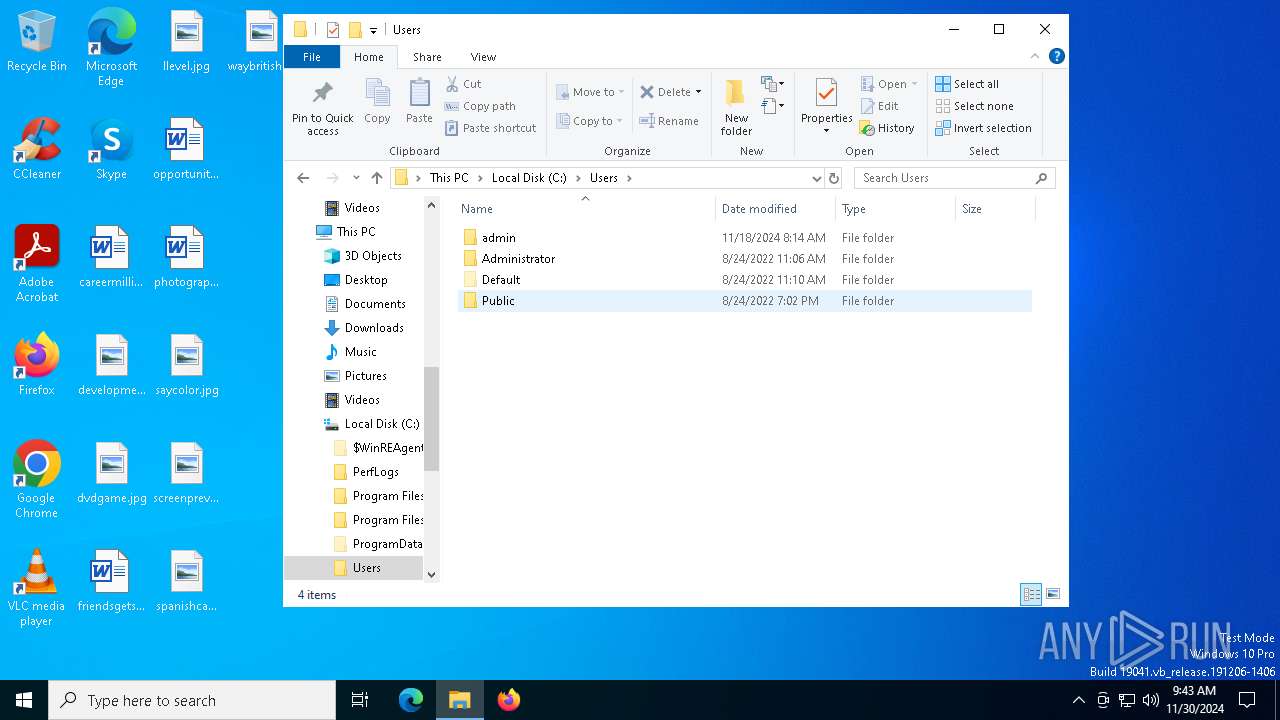
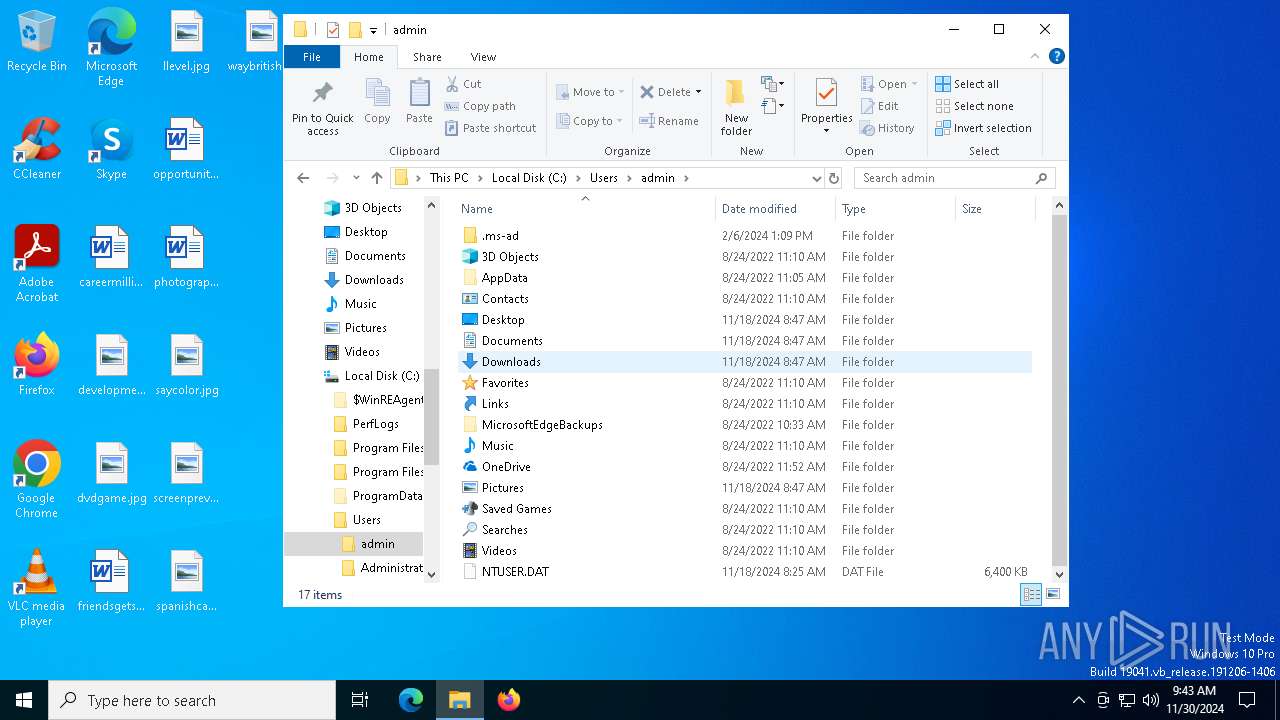
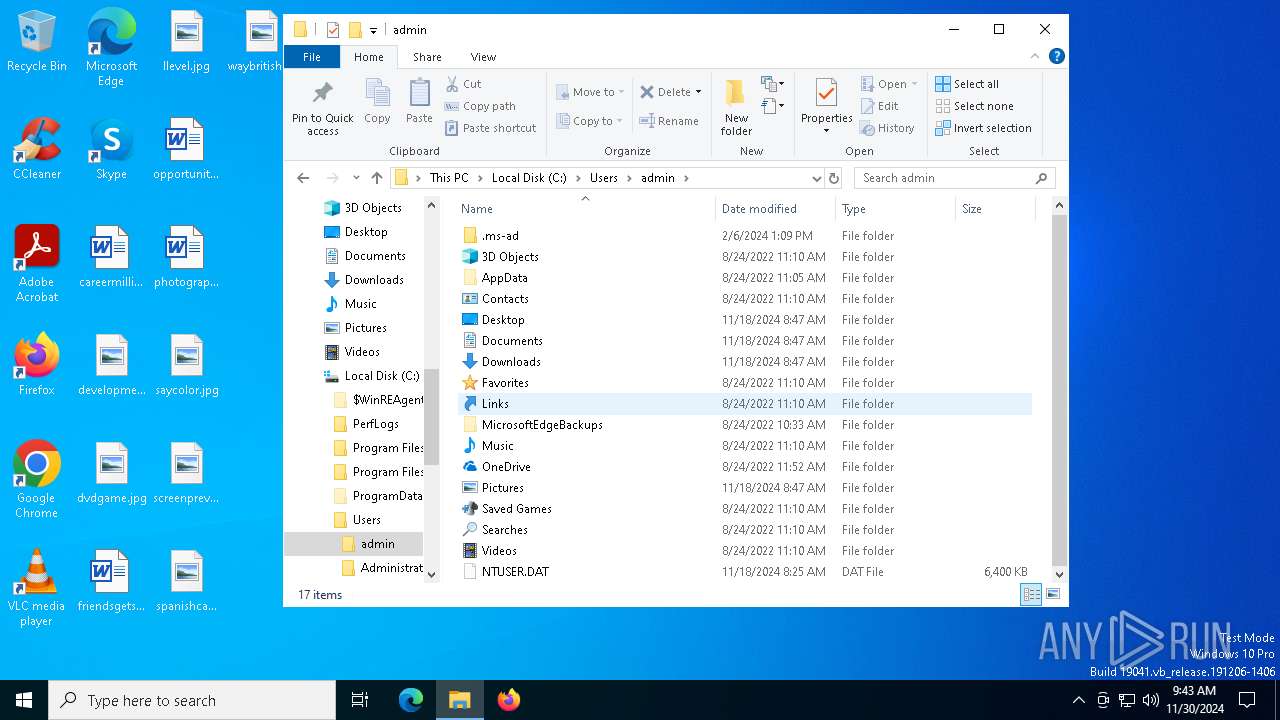
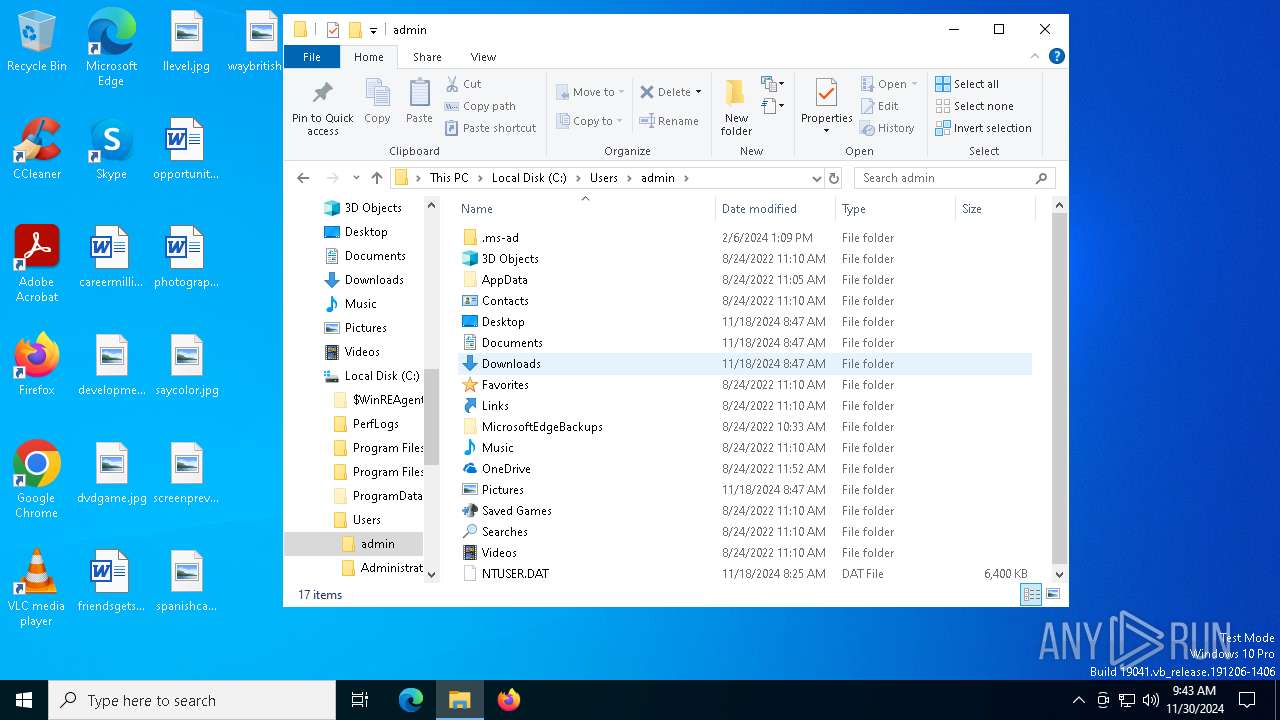
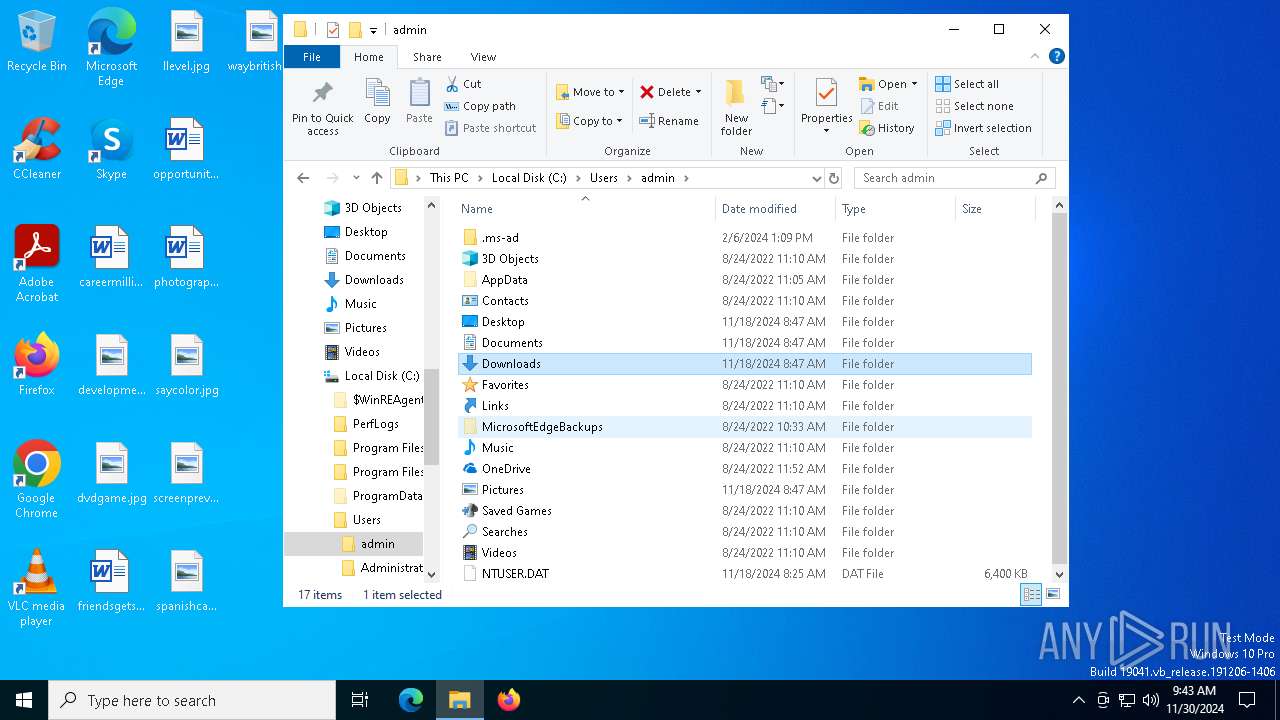
| 6412 | "C:\Users\admin\AppData\Local\Temp\atlantis-bootstrapper.exe" | C:\Users\admin\AppData\Local\Temp\atlantis-bootstrapper.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6420 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | atlantis-bootstrapper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6428 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
591
Read events
591
Write events
0
Delete events
0
Modification events
Executable files
13
Suspicious files
154
Text files
60
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6412 | atlantis-bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Atlantis.zip | compressed | |
MD5:DB969BFA0281B53FCE37509C890B416E | SHA256:1B68DCF143618796106AC9F4788B62CE433F5C3844720EAFFBD35917AF2EA33B | |||
| 6412 | atlantis-bootstrapper.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:3DFCA46E00FFA4795C72A41375F159D3 | SHA256:DCBA1A505396539BAC40A7253C9F5DCCF06CBB79957E21D56305E1FC3AF5F40E | |||
| 6412 | atlantis-bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Atlantis\bin\Monaco\vs\basic-languages\lua\lua.js | binary | |
MD5:8706D861294E09A1F2F7E63D19E5FCB7 | SHA256:FC2D6FB52A524A56CD8AC53BFE4BAD733F246E76DC73CBEC4C61BE32D282AC42 | |||
| 6412 | atlantis-bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Atlantis\bin\key.txt | text | |
MD5:81DCDFC40E71D5028B3BF264F156F79F | SHA256:DEAD8A3815E1A34A80E2A7405E86D1B15A939C9076A2C5114FB6CEB8463CBA12 | |||
| 6412 | atlantis-bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Atlantis\bin\Monaco\vs\editor\editor.main.js | s | |
MD5:9399A8EAA741D04B0AE6566A5EBB8106 | SHA256:93D28520C07FBCA09E20886087F28797BB7BD0E6CF77400153AAB5AE67E3CE18 | |||
| 6412 | atlantis-bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Atlantis\bin\Monaco\vs\editor\editor.main.nls.de.js | text | |
MD5:4D83BC1BCED6F773423BE6F939472CFE | SHA256:0DEE462D5FB231F169F6CBC432465A43FD445C011FE650E29F5FB2BCCC31EAAE | |||
| 6412 | atlantis-bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Atlantis\bin\Monaco\vs\editor\editor.main.nls.es.js | text | |
MD5:B371235F971BAA51F58F123F40C4435A | SHA256:203FF3591E02EB7B55A591E53919CC337F8DEA73E6446FC3493227761C0794BA | |||
| 6412 | atlantis-bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Atlantis\bin\Monaco\vs\editor\editor.main.nls.it.js | text | |
MD5:A8855A662EB4D3A771FDAB7BA6287DEF | SHA256:F67CEC6DBF98C98C834638D20DF53C5A770EDADA7F26EBF6D0B7DFEC60F7A4AB | |||
| 6412 | atlantis-bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Atlantis\bin\Monaco\vs\editor\editor.main.nls.js | text | |
MD5:74DD2381DDBB5AF80CE28AEFED3068FC | SHA256:FDD9D64CE5284373D1541528D15E2AA8AA3A4ADC11B51B3D71D3A3953F8BCC48 | |||
| 6412 | atlantis-bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Atlantis\bin\Monaco\Monaco.html | html | |
MD5:CABDBE1C2D9D0A80E66D9EF6F854345D | SHA256:A2E39847C756841ADF886199EE99DDCB4AAD960B9B08FA40E104B3B1C7622102 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
44
DNS requests
26
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6356 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6356 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6632 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1684 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5064 | SearchApp.exe | 2.16.204.135:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.16.253.202:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
6412 | atlantis-bootstrapper.exe | 185.199.110.133:443 | raw.githubusercontent.com | FASTLY | US | shared |
6412 | atlantis-bootstrapper.exe | 144.126.200.197:443 | getatlantis.xyz | DIGITALOCEAN-ASN | GB | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
raw.githubusercontent.com |
| shared |
getatlantis.xyz |
| unknown |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6412 | atlantis-bootstrapper.exe | Potentially Bad Traffic | ET HUNTING Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |