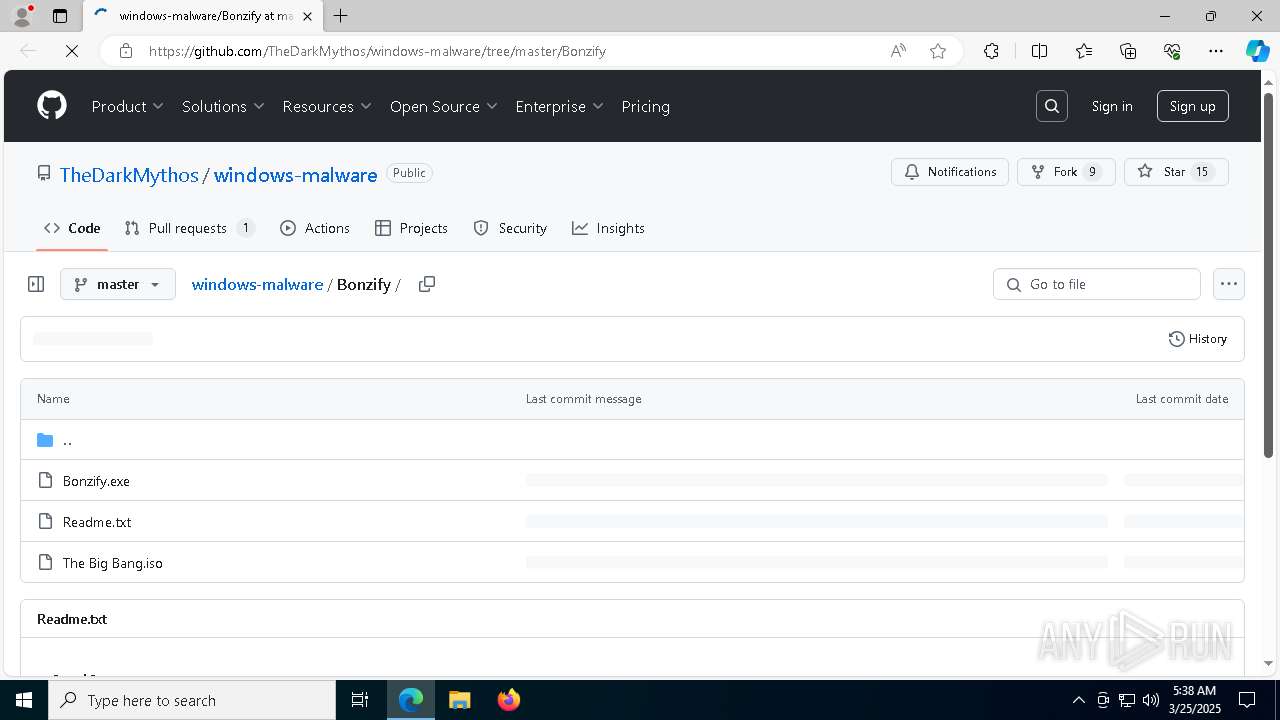
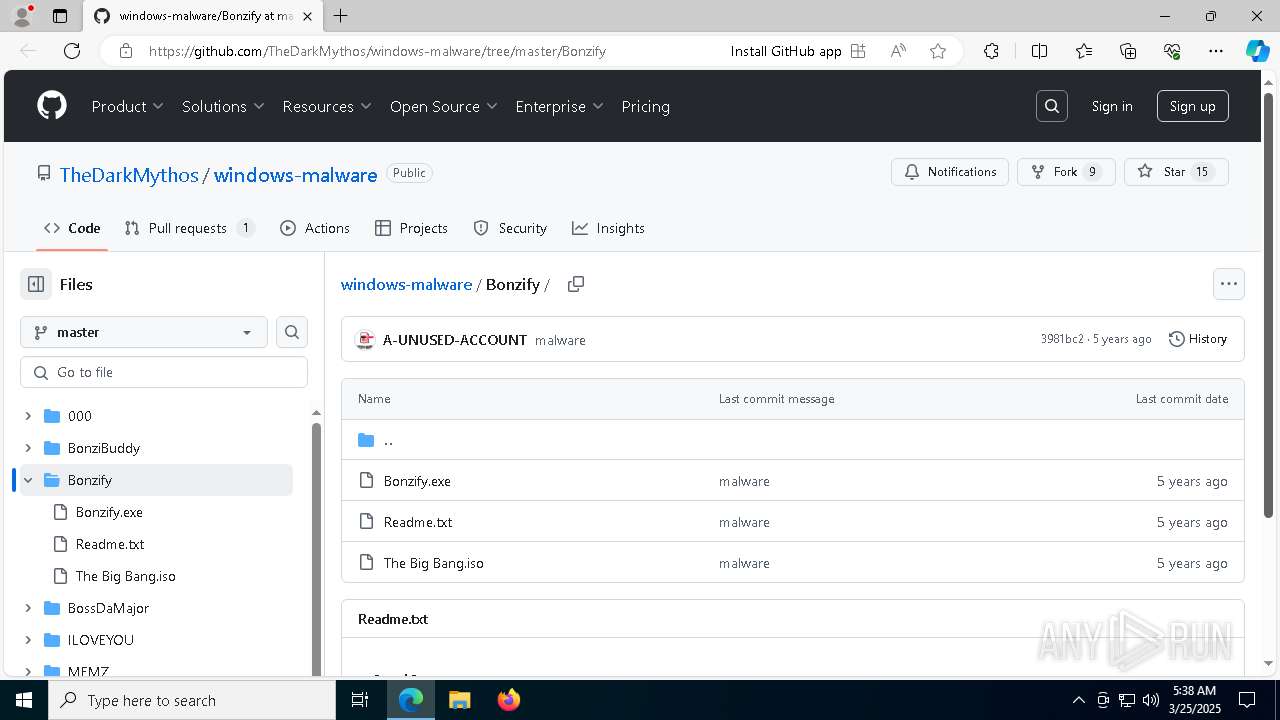
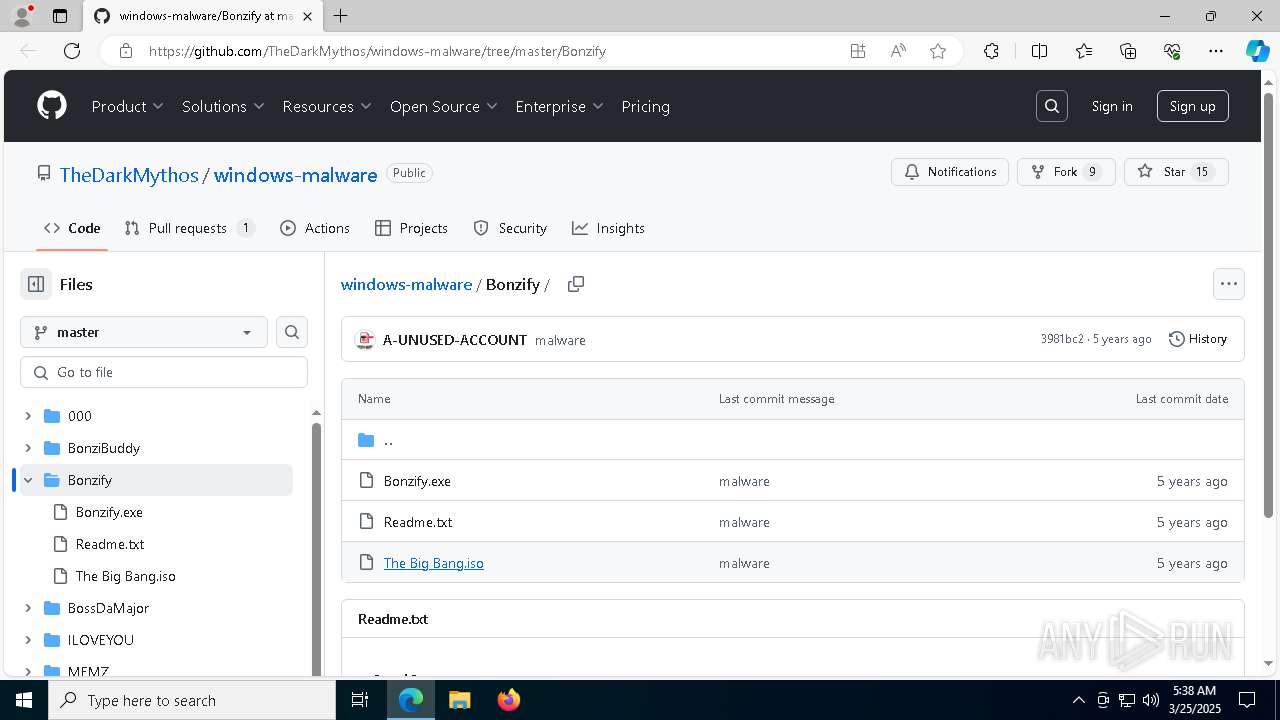
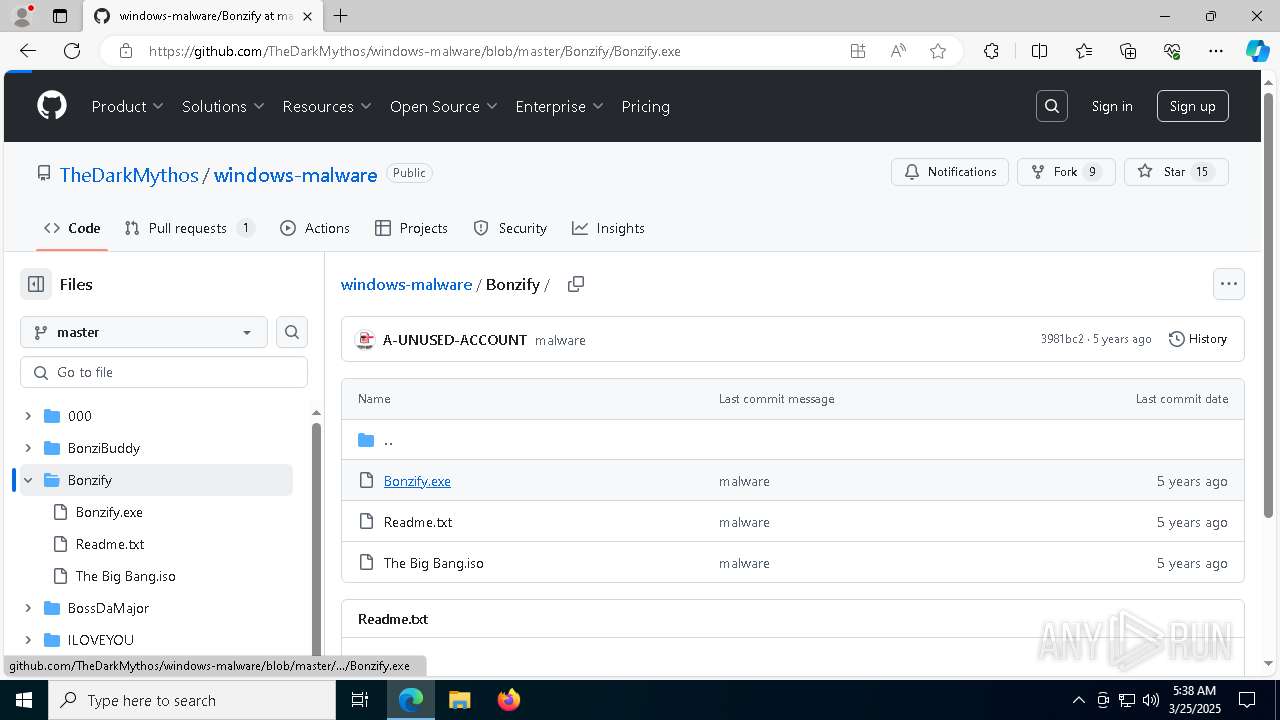
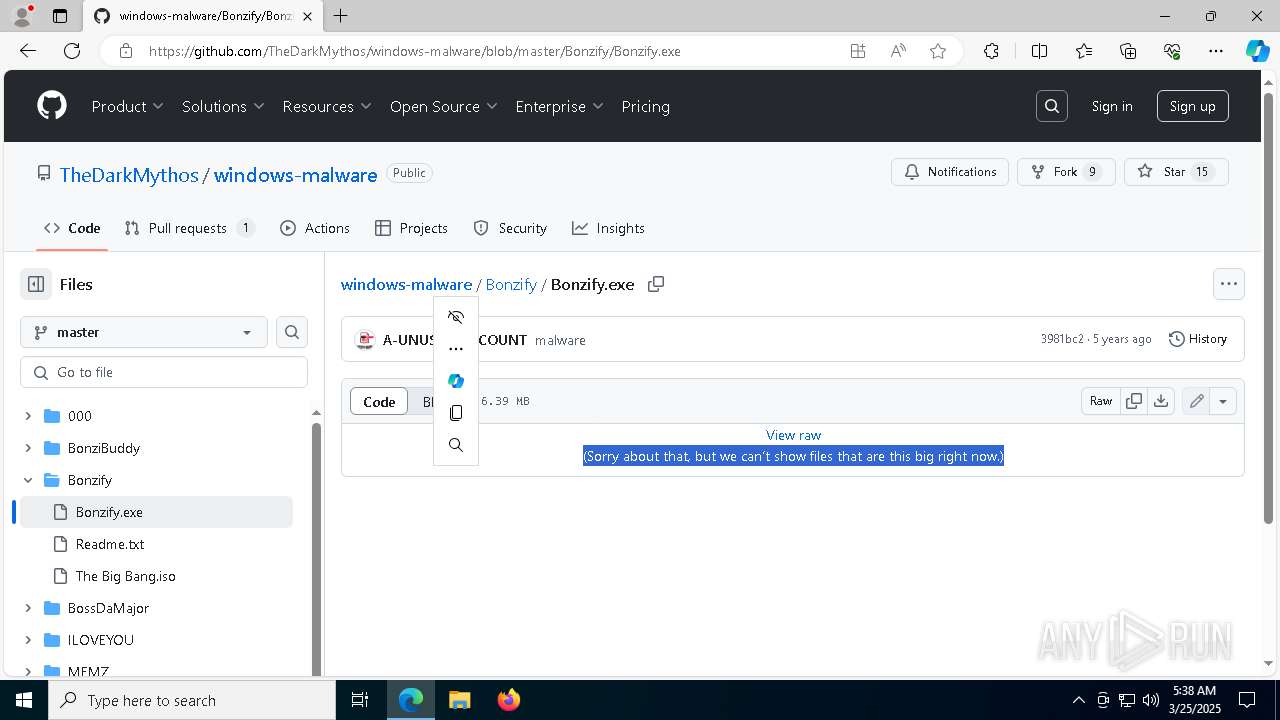
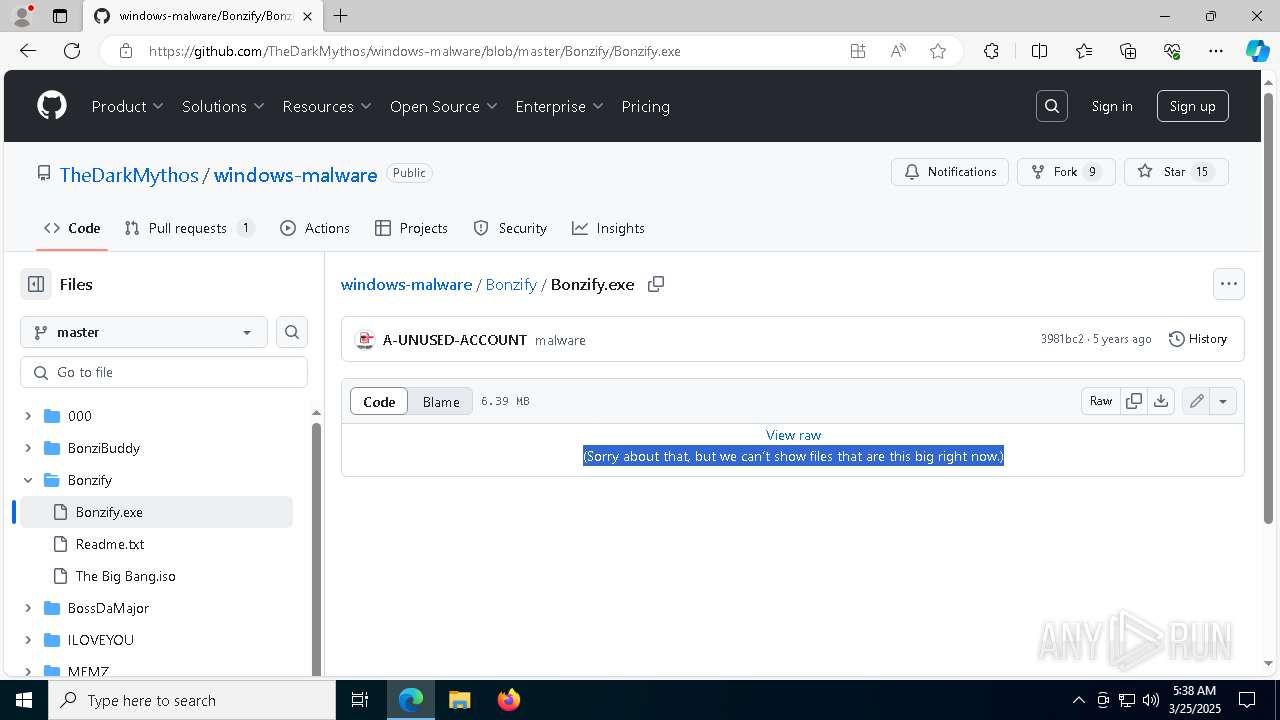
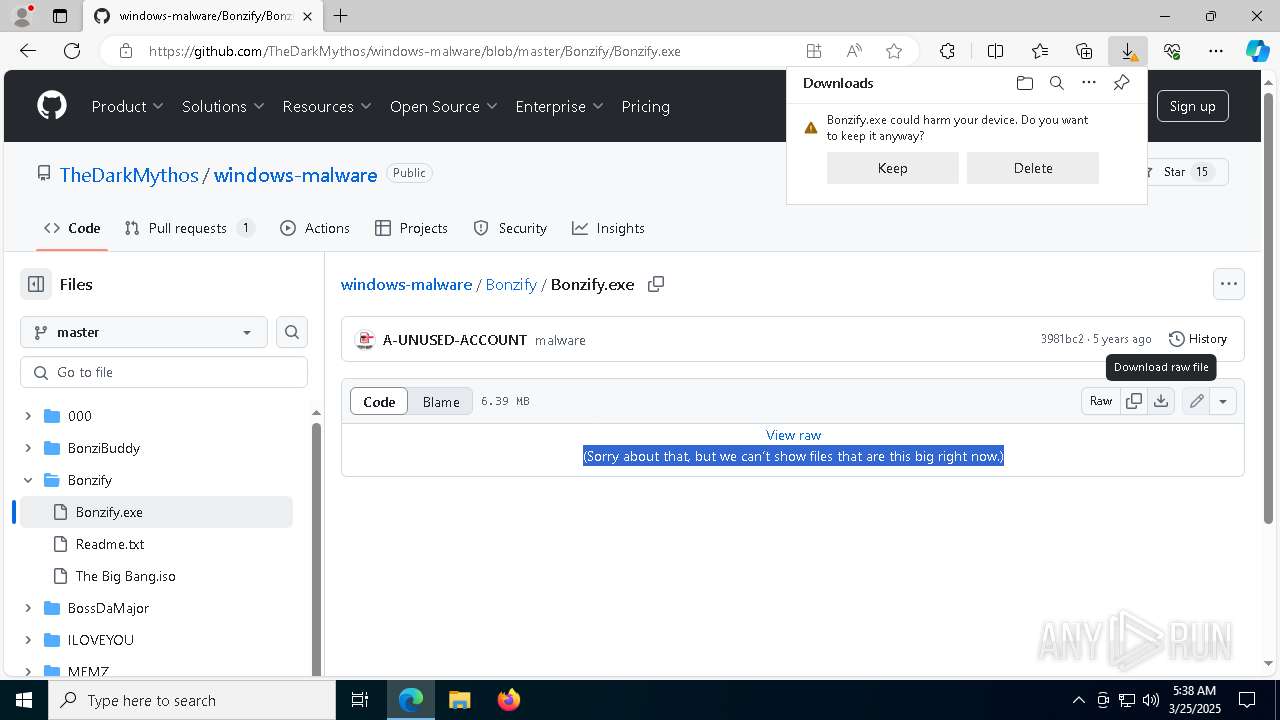
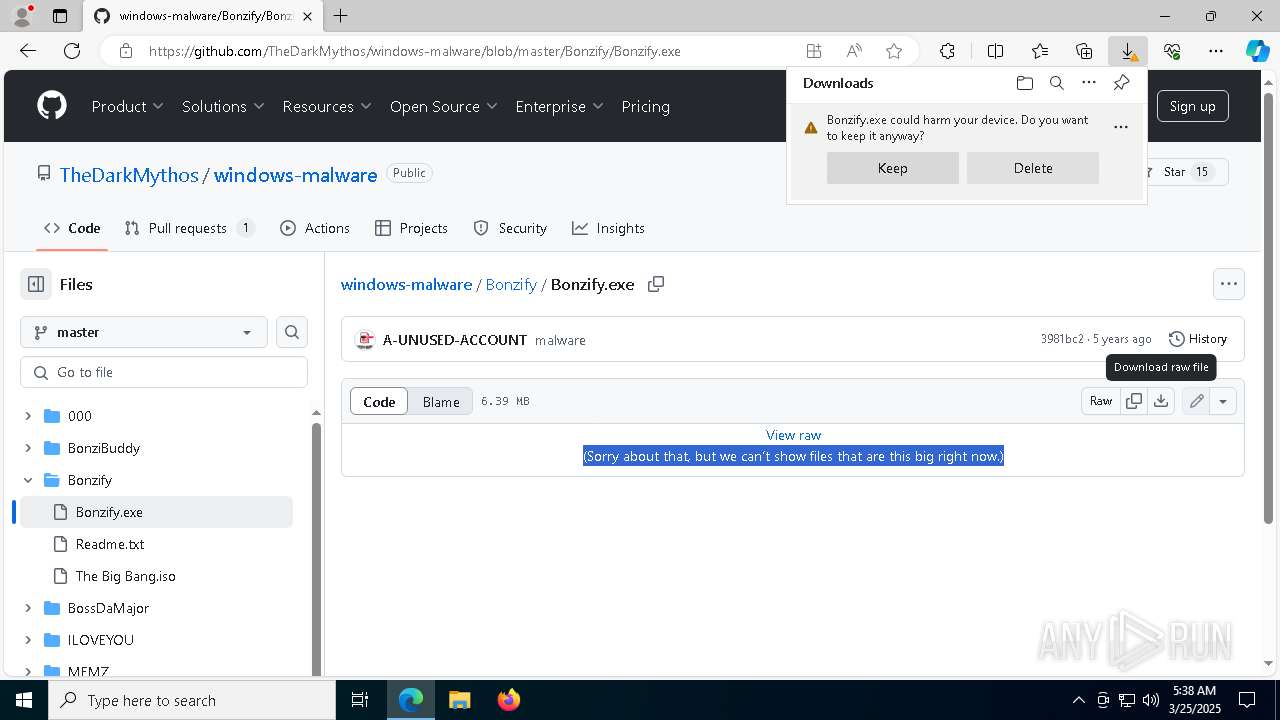
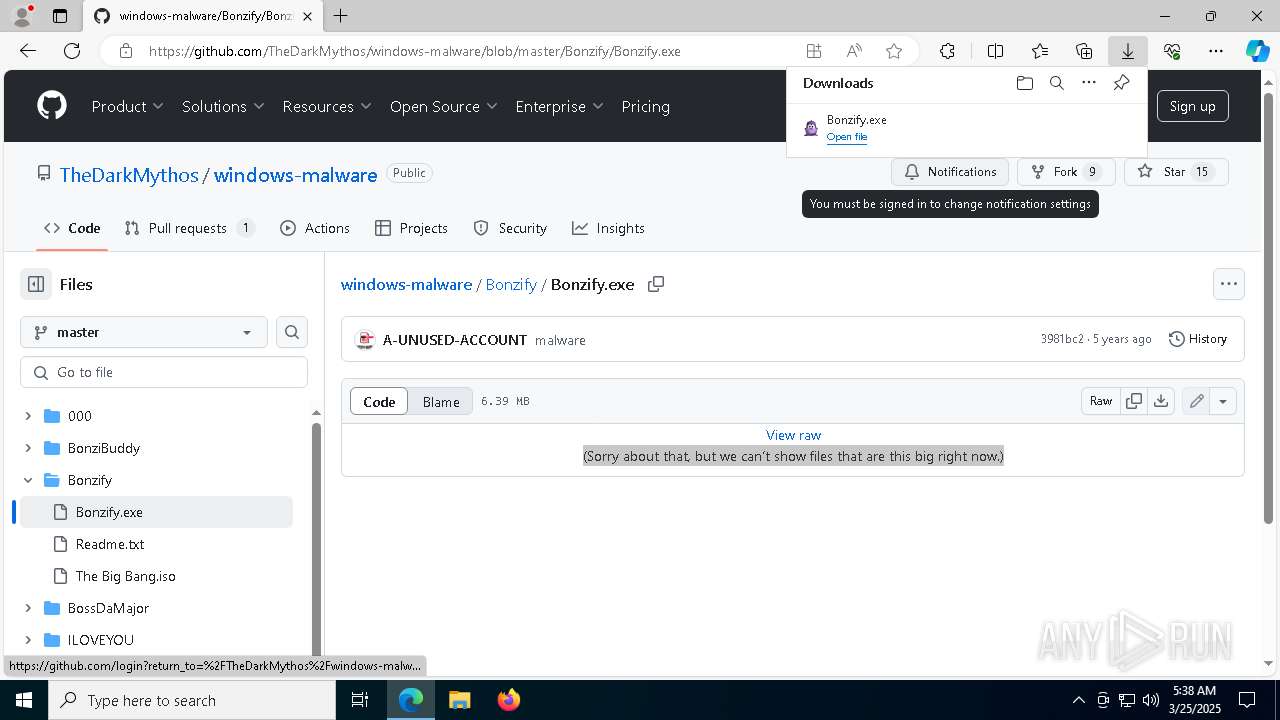
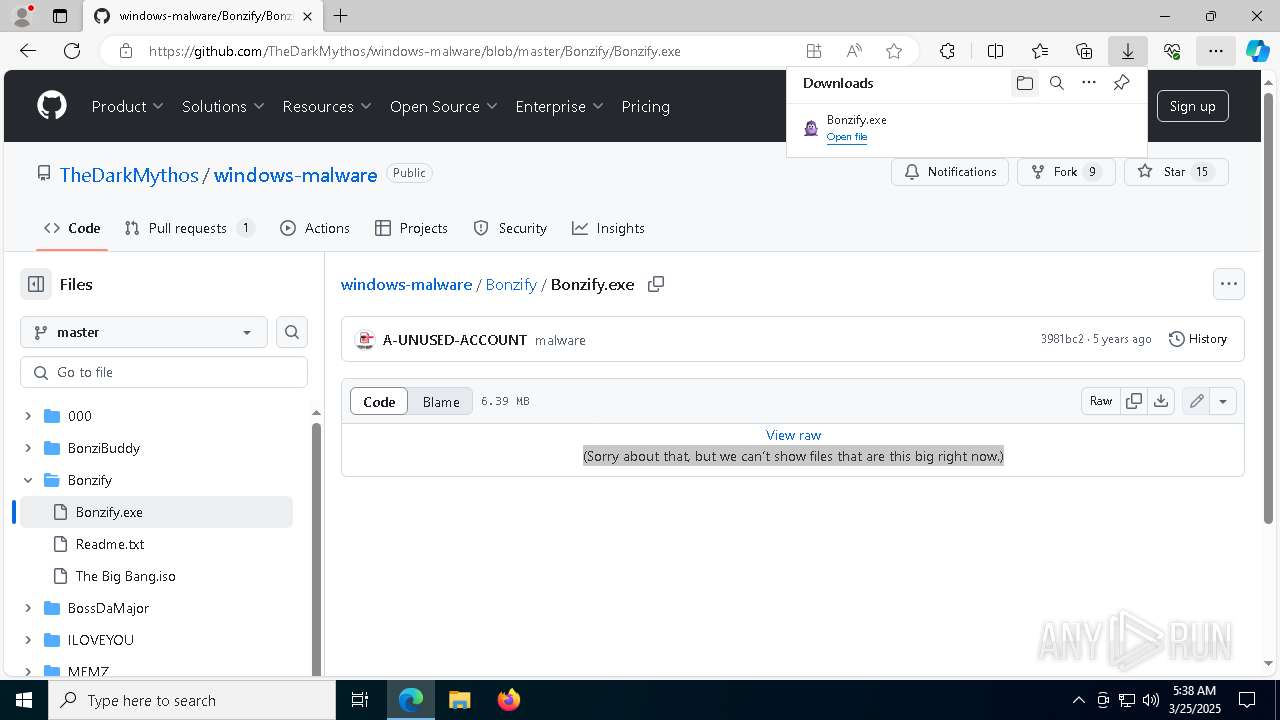
| URL: | https://github.com/TheDarkMythos/windows-malware/tree/master/Bonzify |
| Full analysis: | https://app.any.run/tasks/9fe3cec8-ae5a-4de0-9416-7b92fe8fa6ad |
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2025, 05:37:57 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 045CF0AD8DEC491ECF593A37D061B2F6 |
| SHA1: | A3671A1169FC2A52ADC47E68B1D780FE8B89C691 |
| SHA256: | 597DE7000603935471AC351BE7D512B98A85477EE7C7A88DE11B653E4D4E2CD8 |
| SSDEEP: | 3:N8tEdy/BzE5VKI+3MA:2u4/BzOKI+8A |
MALICIOUS
GENERIC has been found (auto)
- msedge.exe (PID: 7352)
- msedge.exe (PID: 976)
Executing a file with an untrusted certificate
- INSTALLER.exe (PID: 8220)
- INSTALLER.exe (PID: 8700)
Registers / Runs the DLL via REGSVR32.EXE
- INSTALLER.exe (PID: 8220)
- INSTALLER.exe (PID: 8700)
Changes the autorun value in the registry
- INSTALLER.exe (PID: 8700)
SUSPICIOUS
Starts a Microsoft application from unusual location
- INSTALLER.exe (PID: 8220)
- INSTALLER.exe (PID: 8700)
Executable content was dropped or overwritten
- INSTALLER.exe (PID: 8220)
- Bonzify.exe (PID: 8888)
- INSTALLER.exe (PID: 8700)
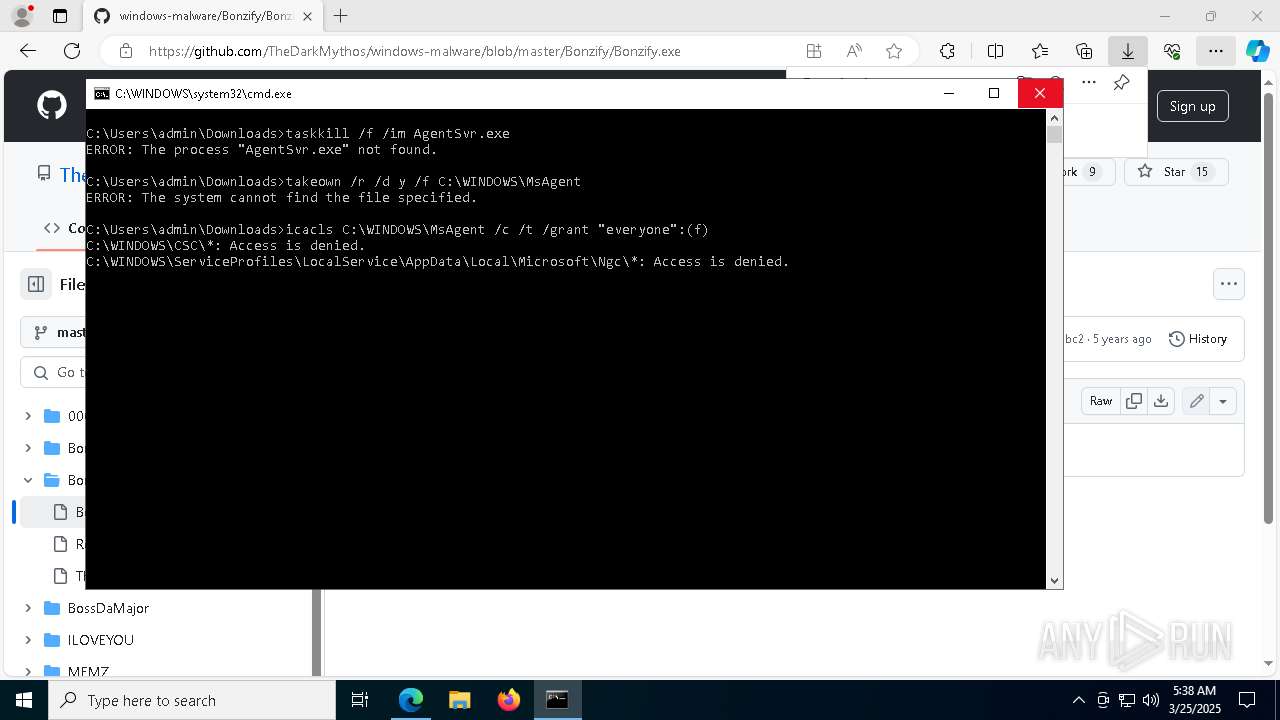
Executing commands from a ".bat" file
- Bonzify.exe (PID: 8888)
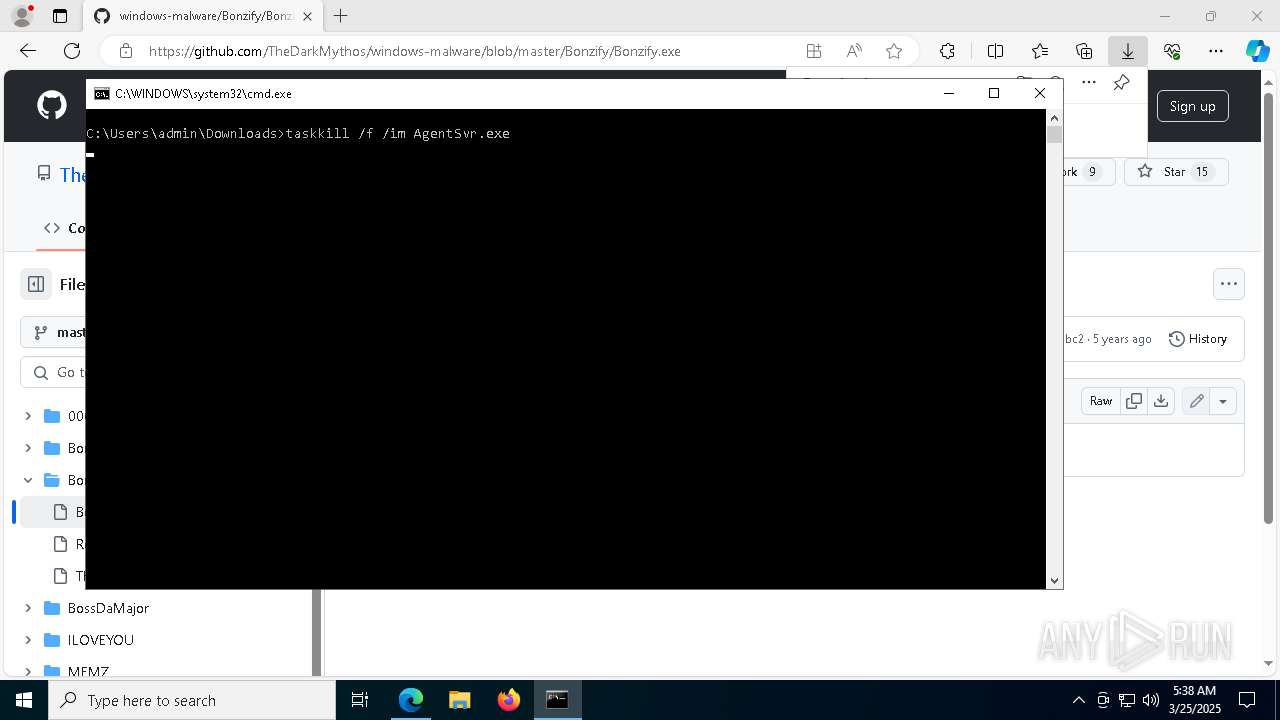
Starts CMD.EXE for commands execution
- Bonzify.exe (PID: 8888)
Takes ownership (TAKEOWN.EXE)
- cmd.exe (PID: 8916)
- cmd.exe (PID: 7856)
- cmd.exe (PID: 8392)
- cmd.exe (PID: 8424)
- cmd.exe (PID: 8308)
- cmd.exe (PID: 3784)
- cmd.exe (PID: 8608)
- cmd.exe (PID: 9196)
- cmd.exe (PID: 9128)
- cmd.exe (PID: 7788)
- cmd.exe (PID: 6872)
- cmd.exe (PID: 7748)
- cmd.exe (PID: 9096)
- cmd.exe (PID: 8280)
- cmd.exe (PID: 3900)
- cmd.exe (PID: 5048)
- cmd.exe (PID: 1116)
- cmd.exe (PID: 4996)
- cmd.exe (PID: 8356)
- cmd.exe (PID: 8600)
- cmd.exe (PID: 5136)
- cmd.exe (PID: 7880)
- cmd.exe (PID: 632)
- cmd.exe (PID: 8564)
- cmd.exe (PID: 5452)
- cmd.exe (PID: 4996)
- cmd.exe (PID: 8176)
- cmd.exe (PID: 7936)
- cmd.exe (PID: 8088)
- cmd.exe (PID: 9000)
- cmd.exe (PID: 7512)
- cmd.exe (PID: 7228)
- cmd.exe (PID: 6640)
- cmd.exe (PID: 7584)
- cmd.exe (PID: 1616)
- cmd.exe (PID: 6972)
- cmd.exe (PID: 8684)
- cmd.exe (PID: 5968)
- cmd.exe (PID: 7768)
- cmd.exe (PID: 7904)
- cmd.exe (PID: 7644)
- cmd.exe (PID: 7648)
- cmd.exe (PID: 9064)
- cmd.exe (PID: 7300)
- cmd.exe (PID: 2344)
- cmd.exe (PID: 7456)
- cmd.exe (PID: 7876)
- cmd.exe (PID: 7804)
- cmd.exe (PID: 7696)
- cmd.exe (PID: 8448)
- cmd.exe (PID: 7596)
- cmd.exe (PID: 5376)
- cmd.exe (PID: 3268)
- cmd.exe (PID: 1056)
- cmd.exe (PID: 6388)
- cmd.exe (PID: 5892)
- cmd.exe (PID: 5756)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 8916)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 8916)
- cmd.exe (PID: 7856)
- cmd.exe (PID: 8392)
- cmd.exe (PID: 8308)
- cmd.exe (PID: 8424)
- cmd.exe (PID: 3784)
- cmd.exe (PID: 8608)
- cmd.exe (PID: 5048)
- cmd.exe (PID: 9128)
- cmd.exe (PID: 9196)
- cmd.exe (PID: 7788)
- cmd.exe (PID: 6872)
- cmd.exe (PID: 7748)
- cmd.exe (PID: 9096)
- cmd.exe (PID: 8280)
- cmd.exe (PID: 3900)
- cmd.exe (PID: 1116)
- cmd.exe (PID: 4996)
- cmd.exe (PID: 8600)
- cmd.exe (PID: 8356)
- cmd.exe (PID: 5136)
- cmd.exe (PID: 632)
- cmd.exe (PID: 4996)
- cmd.exe (PID: 7880)
- cmd.exe (PID: 5452)
- cmd.exe (PID: 8564)
- cmd.exe (PID: 8176)
- cmd.exe (PID: 7936)
- cmd.exe (PID: 8088)
- cmd.exe (PID: 9000)
- cmd.exe (PID: 7512)
- cmd.exe (PID: 6640)
- cmd.exe (PID: 7228)
- cmd.exe (PID: 7584)
- cmd.exe (PID: 6972)
- cmd.exe (PID: 1616)
- cmd.exe (PID: 5968)
- cmd.exe (PID: 8684)
- cmd.exe (PID: 7768)
- cmd.exe (PID: 7696)
- cmd.exe (PID: 7644)
- cmd.exe (PID: 8448)
- cmd.exe (PID: 7648)
- cmd.exe (PID: 9064)
- cmd.exe (PID: 7456)
- cmd.exe (PID: 7904)
- cmd.exe (PID: 7876)
- cmd.exe (PID: 7804)
- cmd.exe (PID: 2344)
- cmd.exe (PID: 7300)
- cmd.exe (PID: 5376)
- cmd.exe (PID: 7596)
- cmd.exe (PID: 1056)
- cmd.exe (PID: 3268)
- cmd.exe (PID: 5892)
- cmd.exe (PID: 5756)
- cmd.exe (PID: 6388)
Process drops legitimate windows executable
- Bonzify.exe (PID: 8888)
- INSTALLER.exe (PID: 8220)
- INSTALLER.exe (PID: 8700)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 8344)
- regsvr32.exe (PID: 4464)
- regsvr32.exe (PID: 5436)
- regsvr32.exe (PID: 856)
- regsvr32.exe (PID: 7560)
- regsvr32.exe (PID: 7868)
- regsvr32.exe (PID: 8384)
- regsvr32.exe (PID: 8936)
- regsvr32.exe (PID: 8996)
Creates a software uninstall entry
- INSTALLER.exe (PID: 8700)
INFO
Application launched itself
- msedge.exe (PID: 976)
- msedge.exe (PID: 8768)
Reads Environment values
- identity_helper.exe (PID: 960)
- identity_helper.exe (PID: 872)
Checks supported languages
- identity_helper.exe (PID: 960)
- INSTALLER.exe (PID: 8220)
- Bonzify.exe (PID: 8888)
- AgentSvr.exe (PID: 728)
- INSTALLER.exe (PID: 8700)
- AgentSvr.exe (PID: 6800)
- identity_helper.exe (PID: 872)
Reads the computer name
- identity_helper.exe (PID: 960)
- INSTALLER.exe (PID: 8220)
- AgentSvr.exe (PID: 728)
- INSTALLER.exe (PID: 8700)
- Bonzify.exe (PID: 8888)
- AgentSvr.exe (PID: 6800)
- identity_helper.exe (PID: 872)
Executable content was dropped or overwritten
- msedge.exe (PID: 7352)
- msedge.exe (PID: 976)
Autorun file from Downloads
- msedge.exe (PID: 976)
- msedge.exe (PID: 8600)
Create files in a temporary directory
- Bonzify.exe (PID: 8888)
- INSTALLER.exe (PID: 8220)
- INSTALLER.exe (PID: 8700)
The sample compiled with english language support
- Bonzify.exe (PID: 8888)
- INSTALLER.exe (PID: 8220)
- INSTALLER.exe (PID: 8700)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
431
Monitored processes
296
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 472 | takeown /f "C:\WINDOWS\servicing\LCU\Package_for_RollupFix~31bf3856ad364e35~amd64~~19041.4046.1.11\amd64_microsoft-windows-i..dsetup-rejuvenation_31bf3856ad364e35_10.0.19041.4046_none_c772981ac5de80e4\r\setupplatform.exe" | C:\Windows\SysWOW64\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | takeown /f "C:\WINDOWS\servicing\LCU\Package_for_RollupFix~31bf3856ad364e35~amd64~~19041.4046.1.11\amd64_microsoft-windows-holoshell.appxmain_31bf3856ad364e35_10.0.19041.3636_none_9832009235926692\r\holoshellapp.exe" | C:\Windows\SysWOW64\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | C:\WINDOWS\system32\cmd.exe /c C:\Users\admin\AppData\Local\Temp\TakeOwn.bat "C:\WINDOWS\servicing\LCU\Package_for_RollupFix~31bf3856ad364e35~amd64~~19041.4046.1.11\amd64_microsoft-windows-legacytaskmanager_31bf3856ad364e35_10.0.19041.3636_none_784b037e1892f883\f\taskmgr.exe" | C:\Windows\SysWOW64\cmd.exe | — | Bonzify.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | "C:\WINDOWS\msagent\AgentSvr.exe" /regserver | C:\Windows\msagent\AgentSvr.exe | — | INSTALLER.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Agent Server Exit code: 0 Version: 2.00.0.2202 Modules
| |||||||||||||||
| 856 | regsvr32 /s "C:\WINDOWS\msagent\AgentDP2.dll" | C:\Windows\SysWOW64\regsvr32.exe | — | INSTALLER.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | takeown /f "C:\WINDOWS\servicing\LCU\Package_for_RollupFix~31bf3856ad364e35~amd64~~19041.4046.1.11\amd64_microsoft-windows-ppi-lockdown-configci_31bf3856ad364e35_10.0.19041.3636_none_b7f3b17c35446f94\f\microsoft.ppi.lockdown.configci.exe" | C:\Windows\SysWOW64\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=3436 --field-trial-handle=2344,i,9562796232926113020,5871041198431943090,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
10 774
Read events
10 629
Write events
129
Delete events
16
Modification events
| (PID) Process: | (976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (976) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D62F4368BA8F2F00 | |||
| (PID) Process: | (976) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 16B24C68BA8F2F00 | |||
| (PID) Process: | (976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197230 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3CD91209-71DF-44B7-A115-1A2359C25D24} | |||
| (PID) Process: | (976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197230 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B863BB9E-6C98-4426-B515-7FA4C88E9C75} | |||
| (PID) Process: | (976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197230 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B9FC2799-C367-4767-9D40-57FE6AA66C4A} | |||
| (PID) Process: | (976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197230 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {72991135-0D33-421A-926E-282F2852295E} | |||
Executable files
67
Suspicious files
235
Text files
61
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b306.TMP | — | |
MD5:— | SHA256:— | |||
| 976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b315.TMP | — | |
MD5:— | SHA256:— | |||
| 976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b315.TMP | — | |
MD5:— | SHA256:— | |||
| 976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b325.TMP | — | |
MD5:— | SHA256:— | |||
| 976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b325.TMP | — | |
MD5:— | SHA256:— | |||
| 976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
68
DNS requests
63
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
9112 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
8140 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | unknown |
9112 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | unknown |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 2.16.164.72:80 | crl.microsoft.com | Akamai International B.V. | NL | unknown |
5496 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
976 | msedge.exe | 239.255.255.250:1900 | — | — | — | unknown |
7352 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
7352 | msedge.exe | 140.82.121.3:443 | github.com | GITHUB | US | unknown |
7352 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
7352 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| unknown |
google.com |
| unknown |
crl.microsoft.com |
| unknown |
config.edge.skype.com |
| unknown |
edge.microsoft.com |
| unknown |
github.com |
| unknown |
business.bing.com |
| unknown |
edge-mobile-static.azureedge.net |
| unknown |
bzib.nelreports.net |
| unknown |
github.githubassets.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7352 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7352 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |