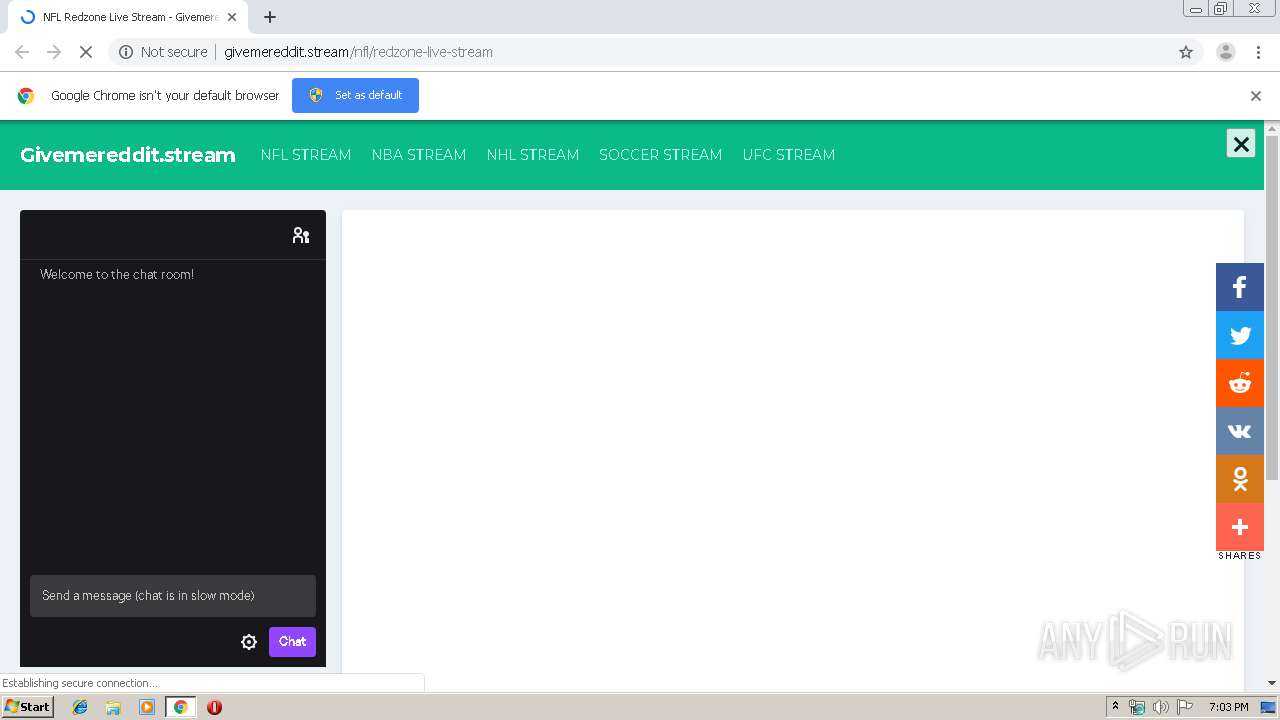
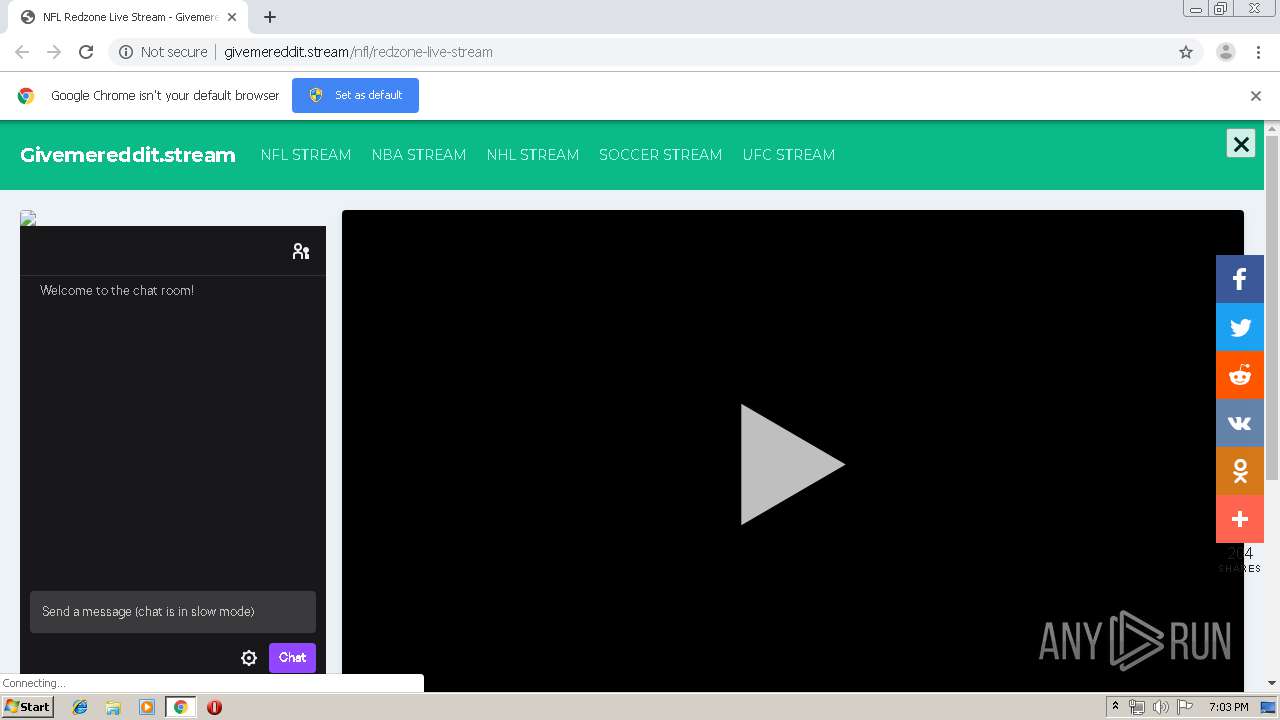
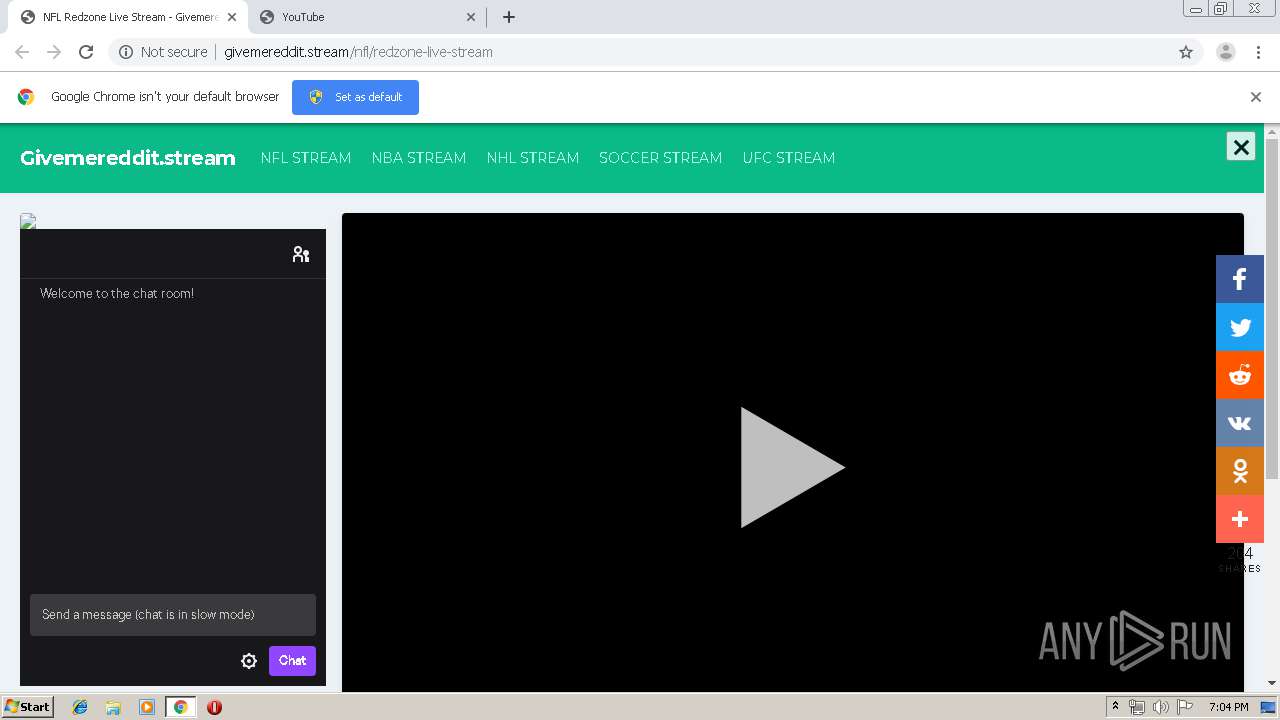
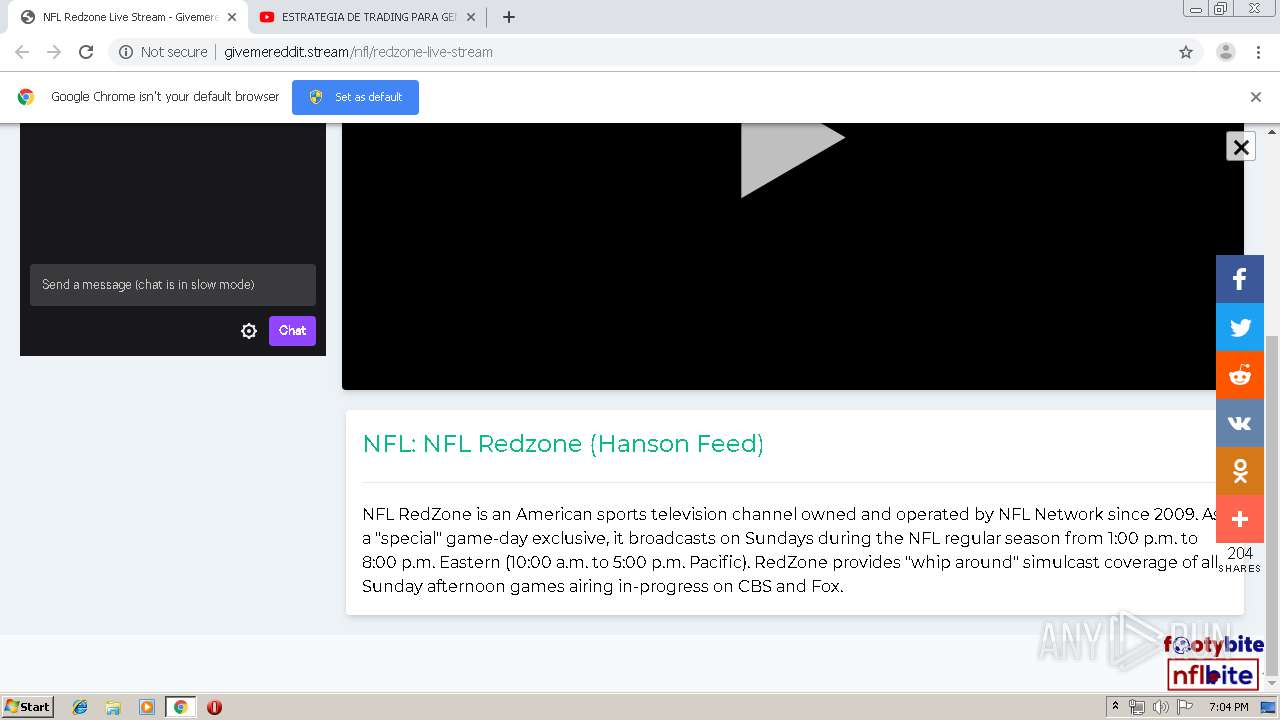
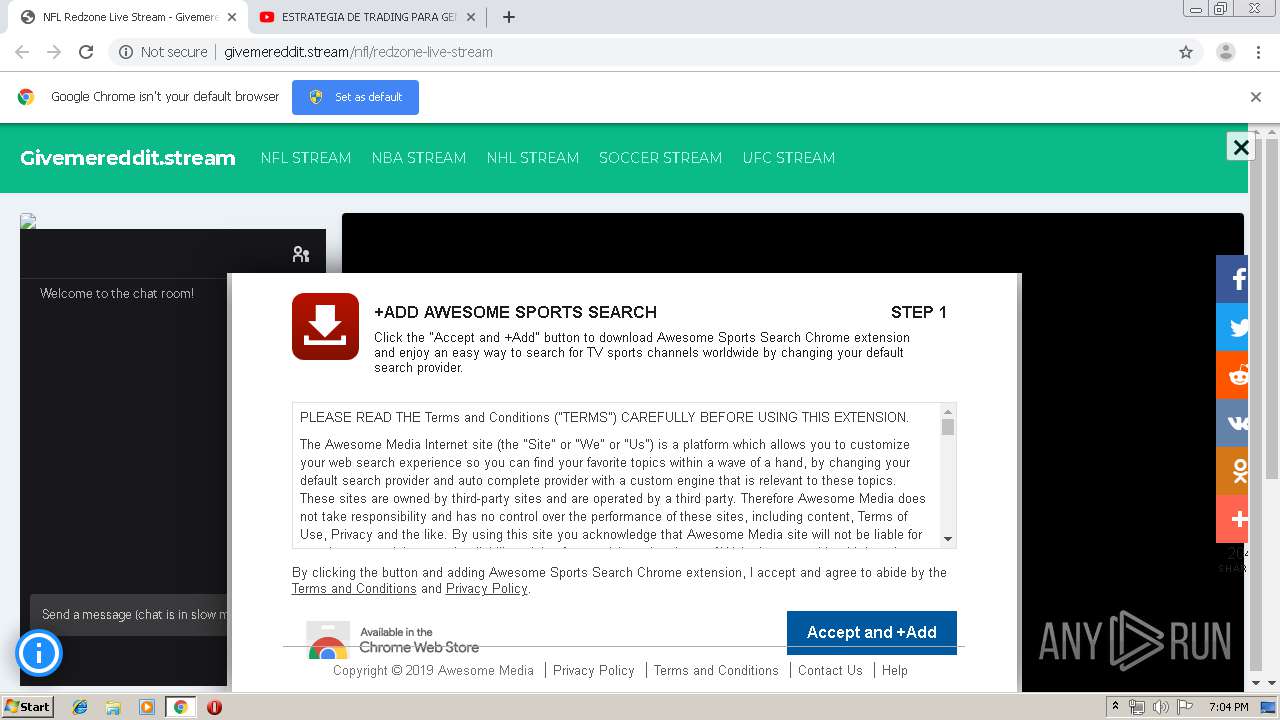
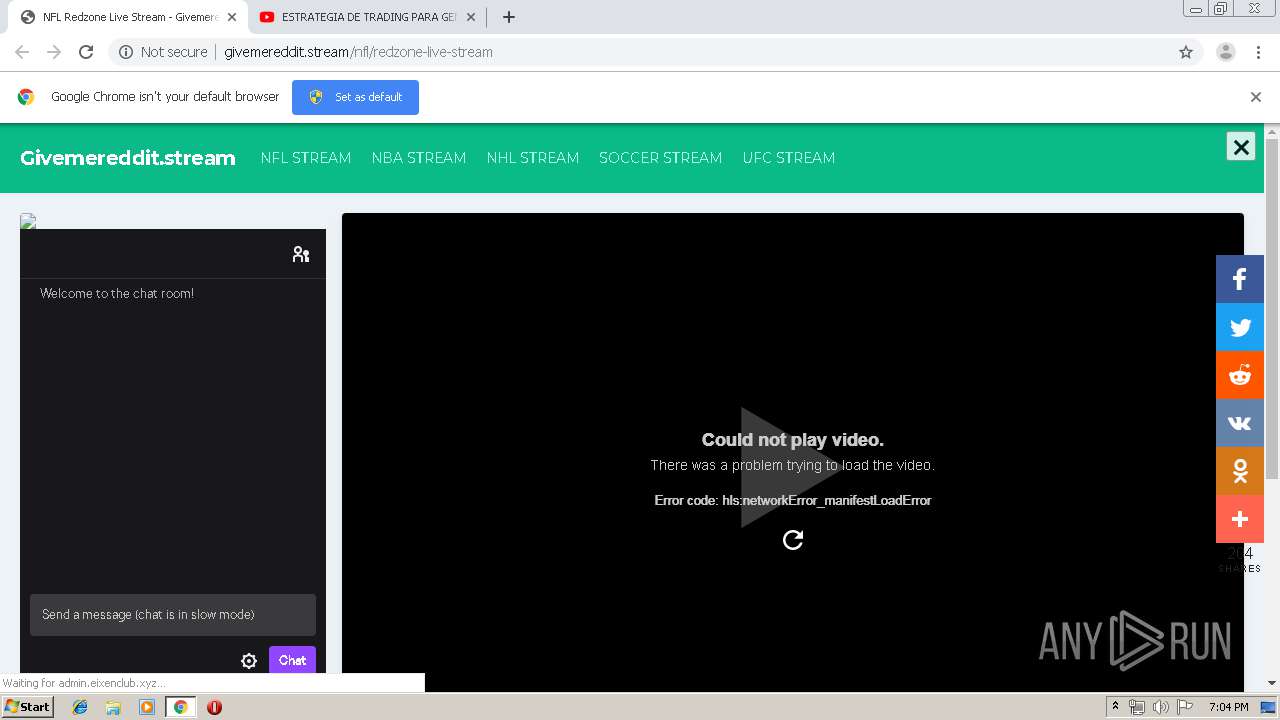
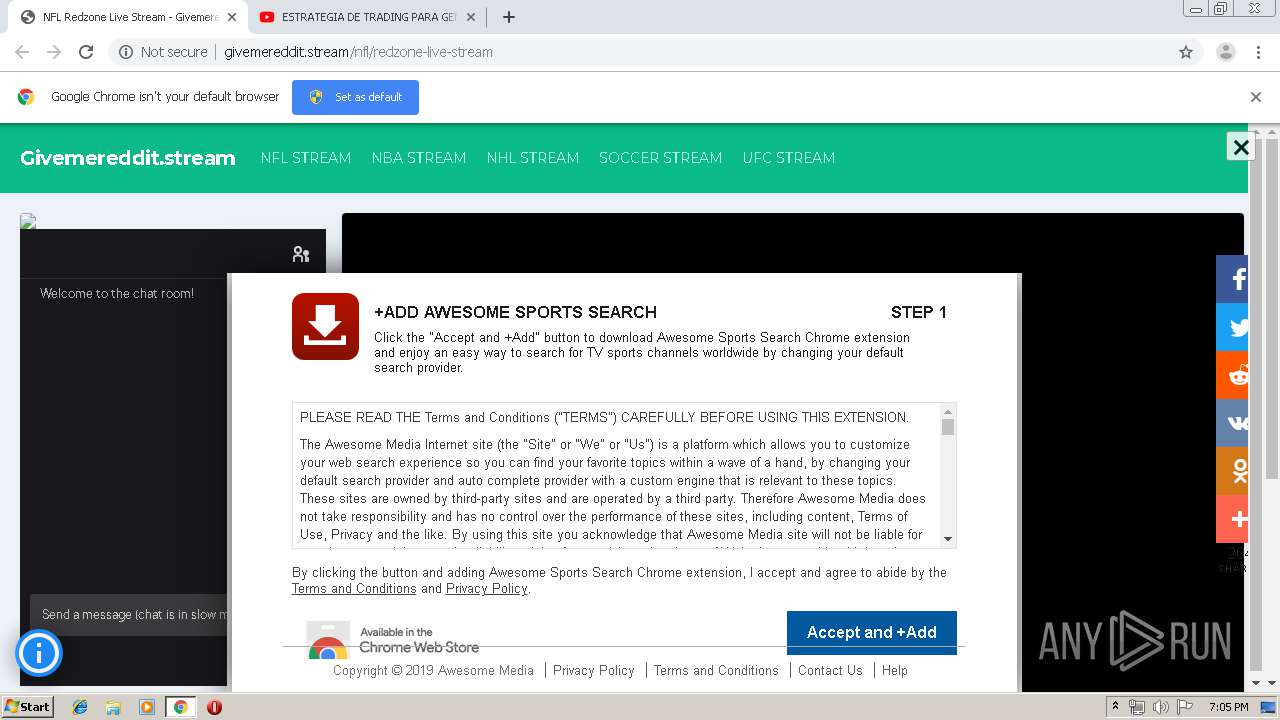
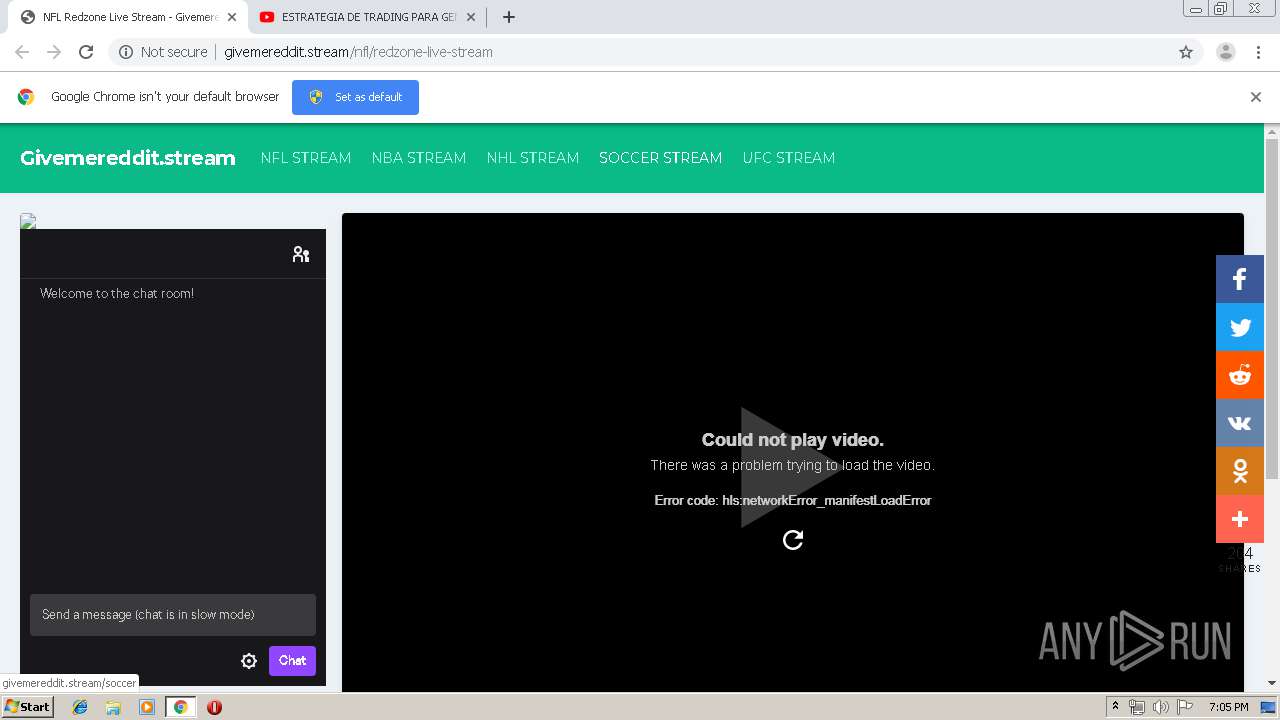
| URL: | http://givemereddit.stream/nfl/redzone-live-stream |
| Full analysis: | https://app.any.run/tasks/0dacc457-79f7-43c3-b97b-0954660fe776 |
| Verdict: | No threats detected |
| Analysis date: | November 18, 2019, 19:02:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E65912351DE3929B761574865D26DBF1 |
| SHA1: | 9D68C66D20400A17880FF2A2F5F416E63EA1EA9E |
| SHA256: | 597C37C5F832B7A2145F6AF729A37F48EEDF2C4385600CB76741211CE20495F4 |
| SSDEEP: | 3:N1KZMTA9QB6tQAUKQUQAFQhn:CyM9U6tQ1UbQhn |
MALICIOUS
No malicious indicators.SUSPICIOUS
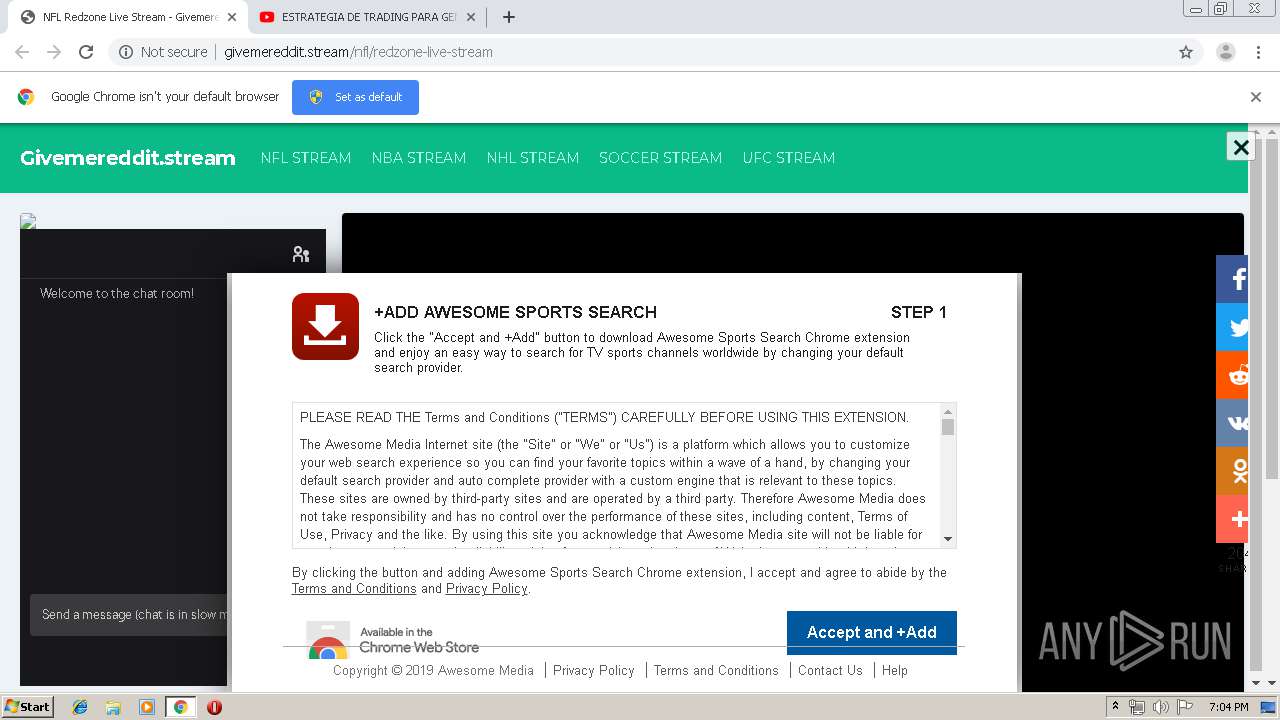
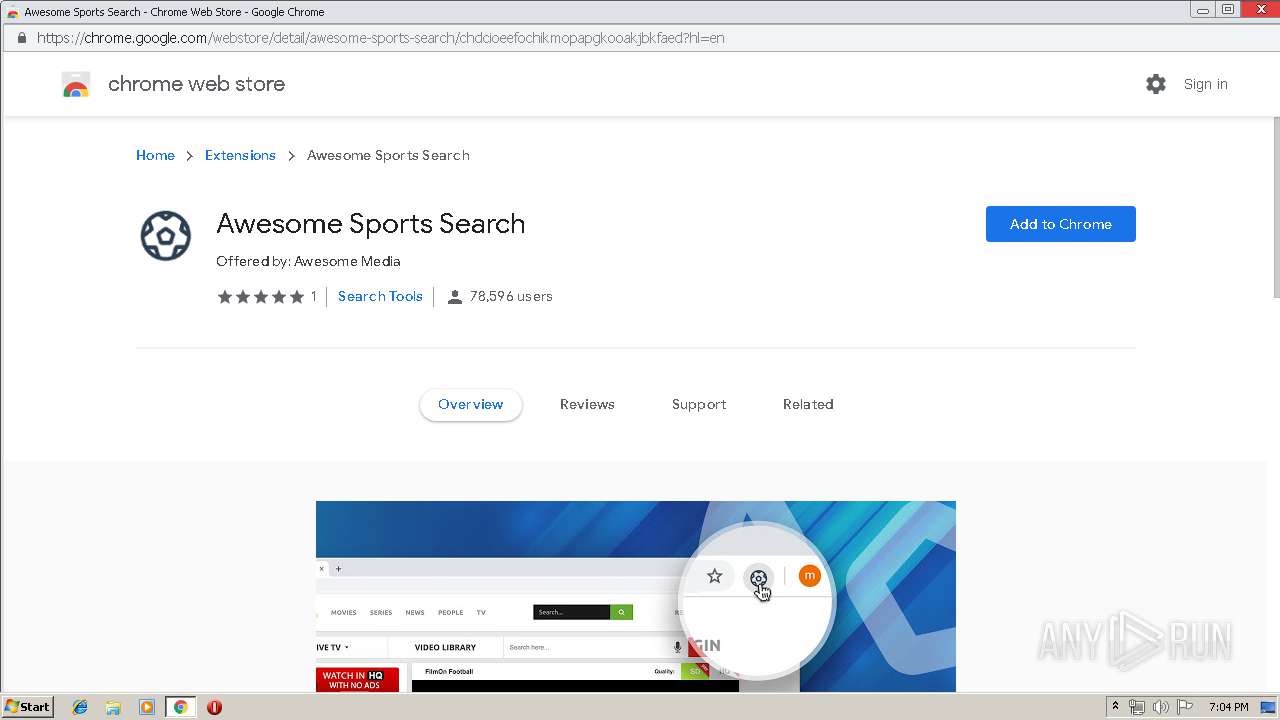
Modifies files in Chrome extension folder
- chrome.exe (PID: 2752)
INFO
Application launched itself
- chrome.exe (PID: 2752)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2752)
Reads the hosts file
- chrome.exe (PID: 2752)
- chrome.exe (PID: 408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
83
Monitored processes
49
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,6641739983538232542,17556077736759167345,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=15430532385901698117 --mojo-platform-channel-handle=1620 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ed2a9d0,0x6ed2a9e0,0x6ed2a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,6641739983538232542,17556077736759167345,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18246957374537696722 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4576 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 716 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,6641739983538232542,17556077736759167345,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=1117861052126543538 --mojo-platform-channel-handle=4192 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,6641739983538232542,17556077736759167345,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10339050201581811725 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3984 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,6641739983538232542,17556077736759167345,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14312174708444038375 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2212 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,6641739983538232542,17556077736759167345,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18237198341275753081 --renderer-client-id=42 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2188 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,6641739983538232542,17556077736759167345,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15680500145798681208 --mojo-platform-channel-handle=4368 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1752 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,6641739983538232542,17556077736759167345,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9310256814829450369 --mojo-platform-channel-handle=4996 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
746
Read events
605
Write events
135
Delete events
6
Modification events
| (PID) Process: | (2752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1528) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2752-13218577399416875 |
Value: 259 | |||
| (PID) Process: | (2752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2752) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
185
Text files
306
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e3b5084f-f99c-440e-acc2-61c010ab2eb0.tmp | — | |
MD5:— | SHA256:— | |||
| 2752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 2752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39c4e1.TMP | text | |
MD5:— | SHA256:— | |||
| 2752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
69
TCP/UDP connections
180
DNS requests
135
Threats
74
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
408 | chrome.exe | GET | 200 | 104.17.167.186:80 | http://6.adsco.re/ | US | — | — | whitelisted |
408 | chrome.exe | GET | 200 | 35.201.74.235:80 | http://theonecdn.com/script/compatibility.js | US | text | 11.8 Kb | malicious |
408 | chrome.exe | GET | 200 | 104.17.167.186:80 | http://c.adsco.re/ | US | html | 10.9 Kb | whitelisted |
408 | chrome.exe | GET | 200 | 195.181.174.6:80 | http://c1.popads.net/pop.js | DE | html | 9.23 Kb | whitelisted |
408 | chrome.exe | GET | 200 | 46.105.201.240:80 | http://s10.histats.com/js15_as.js | FR | html | 4.42 Kb | whitelisted |
408 | chrome.exe | GET | 200 | 104.27.153.218:80 | http://scienceandtechnology.xyz/wp-content/uploads/2019/09/Screen-Shot-2019-09-08-at-11.22.27-PM.png | US | image | 50.8 Kb | malicious |
408 | chrome.exe | GET | 200 | 35.201.74.235:80 | http://theonecdn.com/script/chrome.js | US | text | 18.3 Kb | malicious |
408 | chrome.exe | GET | 403 | 173.192.101.24:80 | http://mybestdc.com/adServe/banners?tid=UMARIMTIAZ3_17528_11&pause=5 | US | html | 426 b | malicious |
408 | chrome.exe | GET | 304 | 104.17.167.186:80 | http://c.adsco.re/ | US | compressed | 10.9 Kb | whitelisted |
408 | chrome.exe | GET | 200 | 94.31.29.128:80 | http://p12995.mycdn.co/banners/script/di_tag_90-0.js | GB | text | 55.0 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
408 | chrome.exe | 2.18.232.15:443 | s7.addthis.com | Akamai International B.V. | — | whitelisted |
408 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
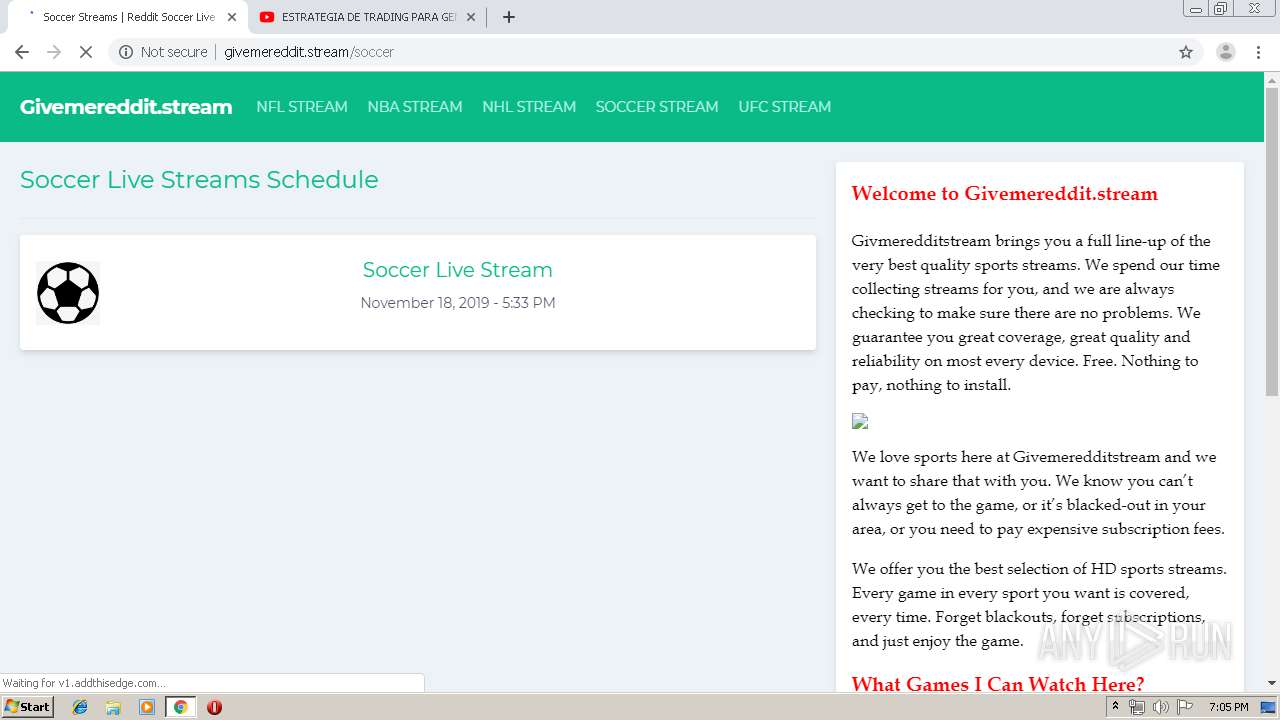
408 | chrome.exe | 103.194.171.187:80 | givemereddit.stream | Host Palace Internet Services | NL | suspicious |
408 | chrome.exe | 216.58.208.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
408 | chrome.exe | 172.217.18.4:443 | www.google.com | Google Inc. | US | whitelisted |
408 | chrome.exe | 172.217.22.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
408 | chrome.exe | 198.134.112.242:80 | 6ped2nd3yp.com | Webair Internet Development Company Inc. | US | suspicious |
408 | chrome.exe | 35.201.115.74:80 | moneymakercdn.com | Google Inc. | US | whitelisted |
408 | chrome.exe | 172.217.16.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
408 | chrome.exe | 35.201.74.235:80 | theonecdn.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
givemereddit.stream |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
6ped2nd3yp.com |
| malicious |
fonts.gstatic.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
s7.addthis.com |
| whitelisted |
crewofthieves.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
408 | chrome.exe | Potential Corporate Privacy Violation | ET INFO Suspicious Darkwave Popads Pop Under Redirect |
408 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
408 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
408 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
408 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |