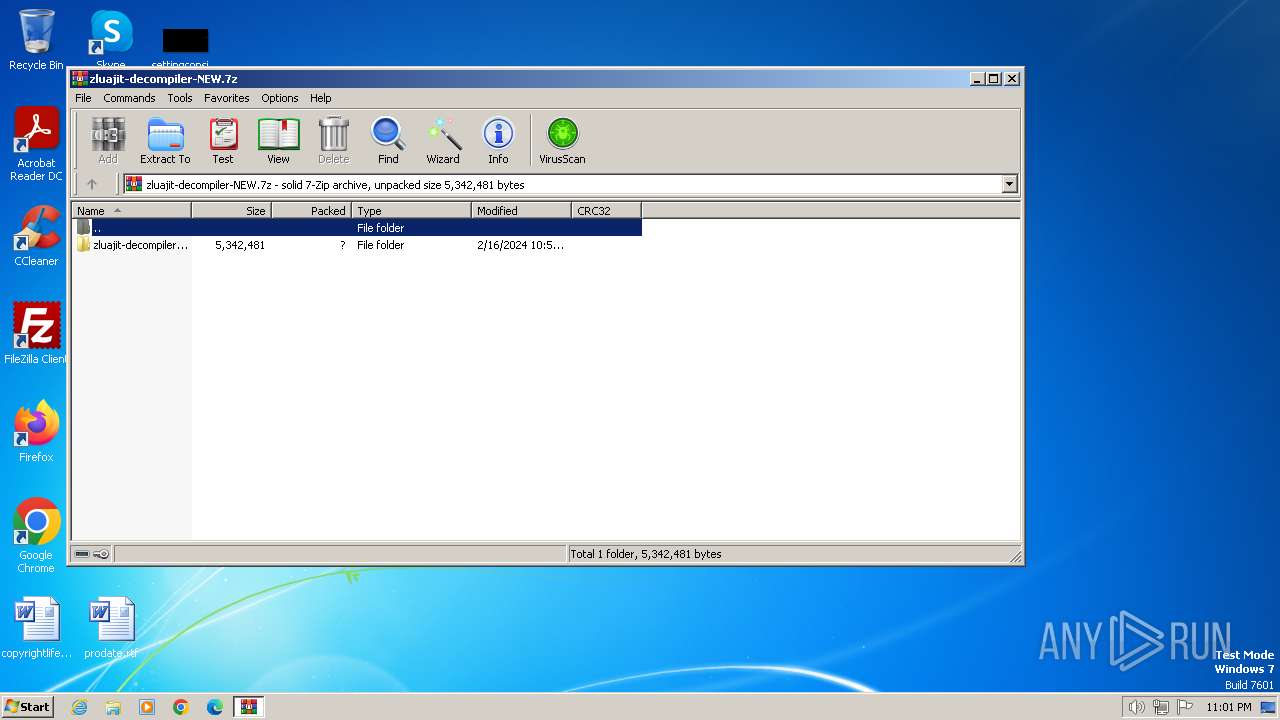
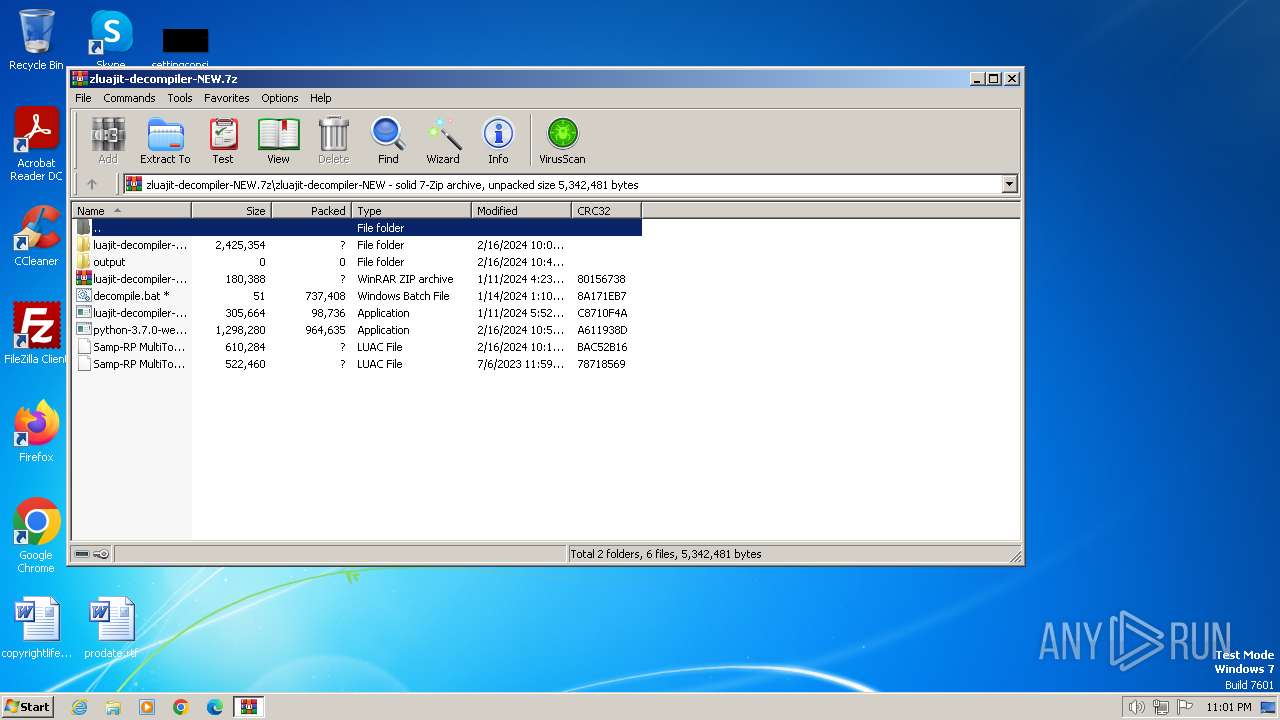
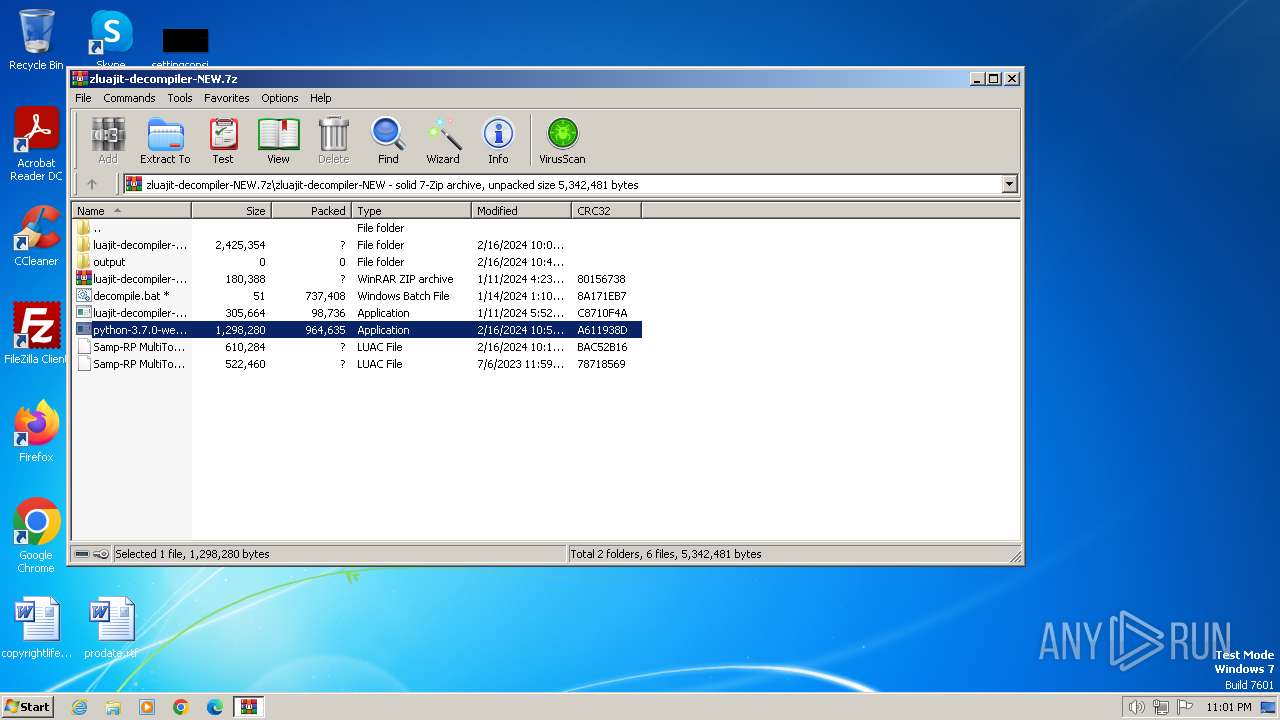
| File name: | zluajit-decompiler-NEW.7z |
| Full analysis: | https://app.any.run/tasks/d595d87c-ad9c-47b8-845d-3e7fe44a24fa |
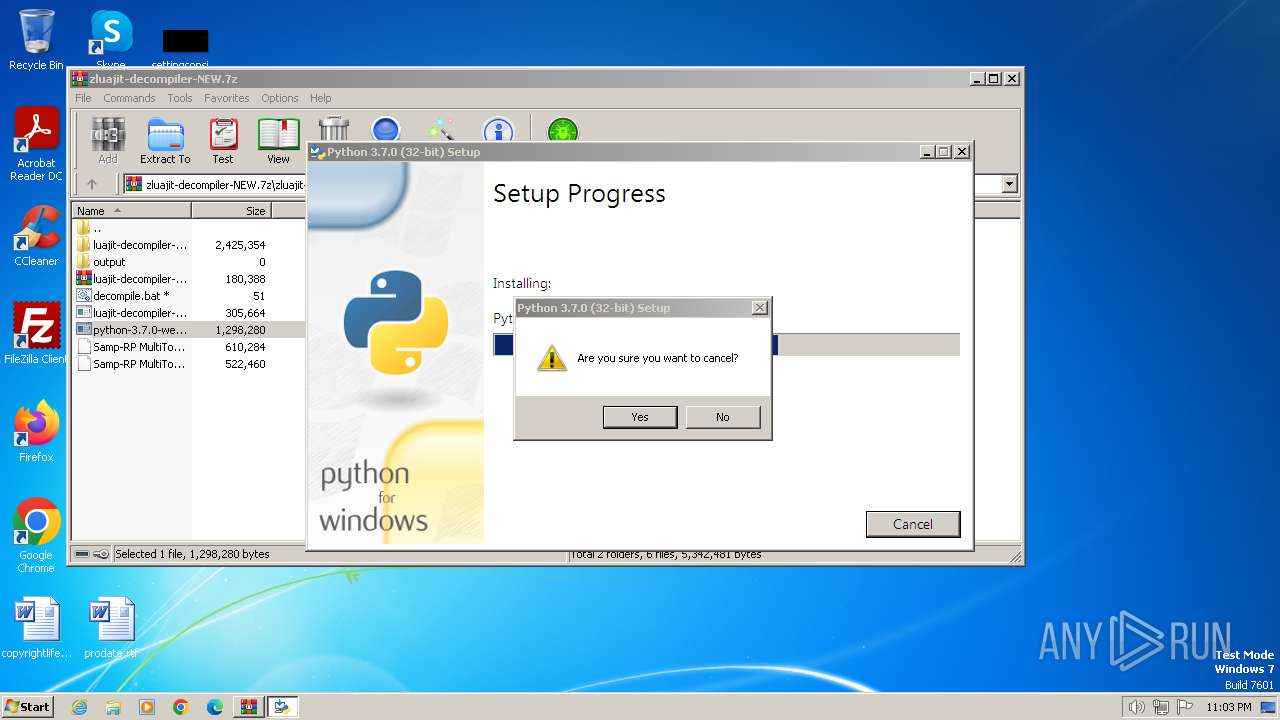
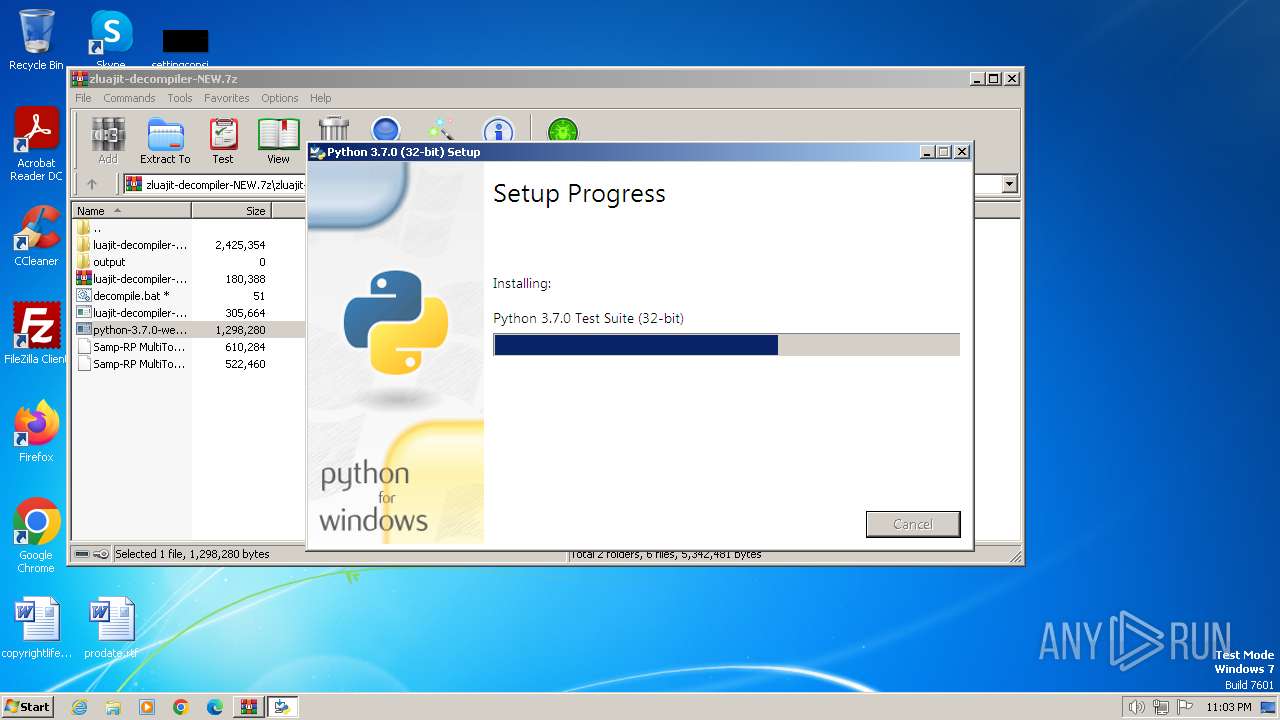
| Verdict: | Malicious activity |
| Analysis date: | February 16, 2024, 23:01:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | A4551ABDBCE45C17EFE02F6F289BF357 |
| SHA1: | D9DEB5CA5EBF63F5420952B541340BCA00E919B8 |
| SHA256: | 596AD976FD125B14CB037C07A37CB8541801DC1D8FD51FE71111C35517CDAC48 |
| SSDEEP: | 98304:VRquWHlTYLfuhdI0o2X/HWagrXo9rXYWdthggu18+J48ZBazurtax6lrSs52:Bw |
MALICIOUS
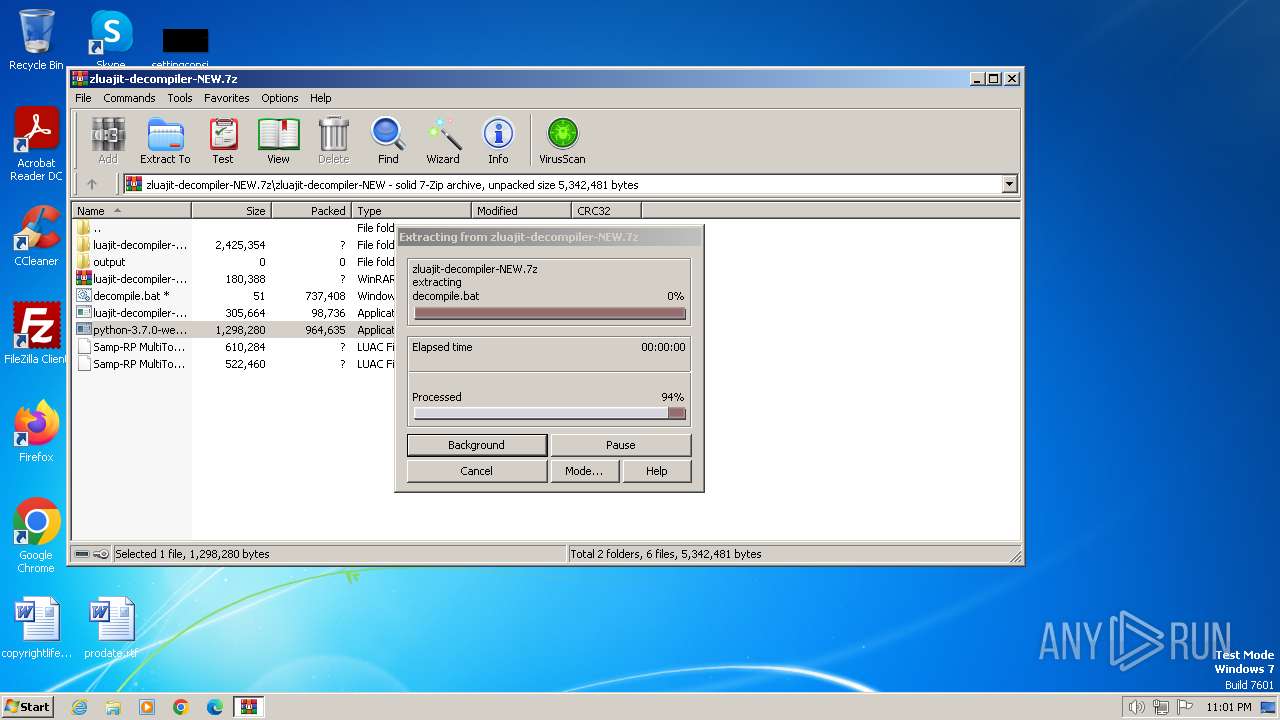
Drops the executable file immediately after the start
- WinRAR.exe (PID: 1384)
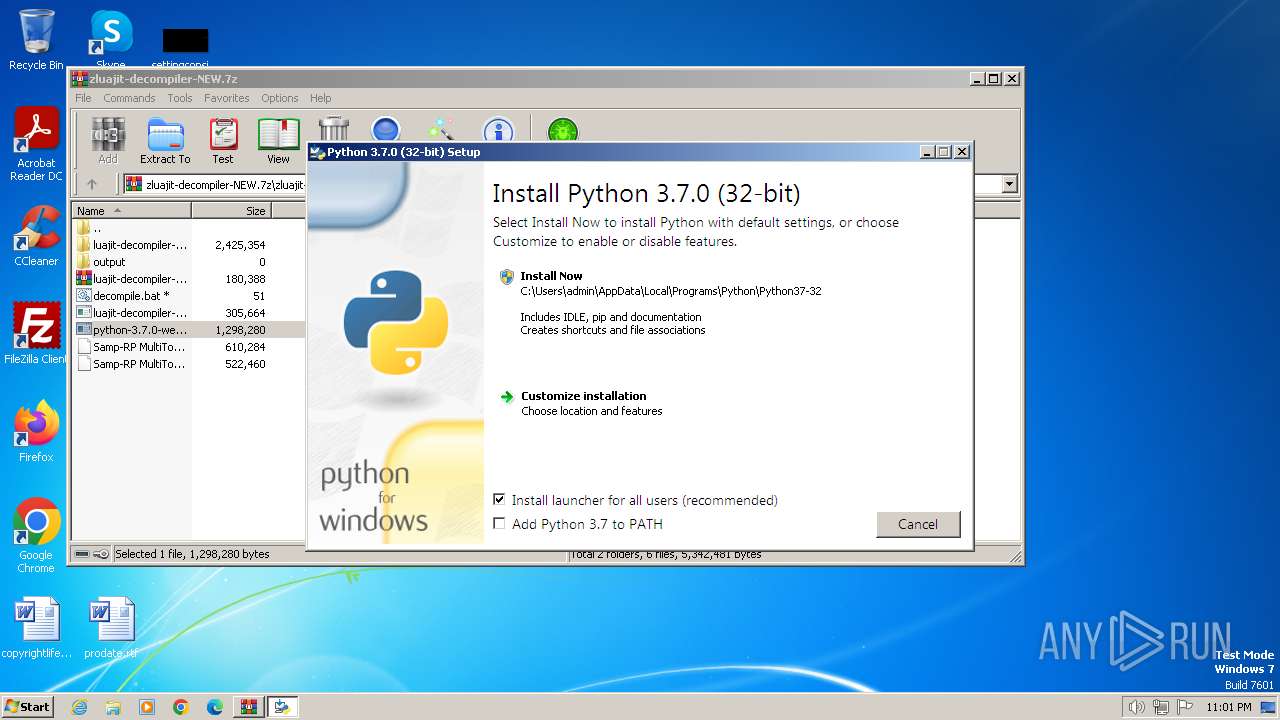
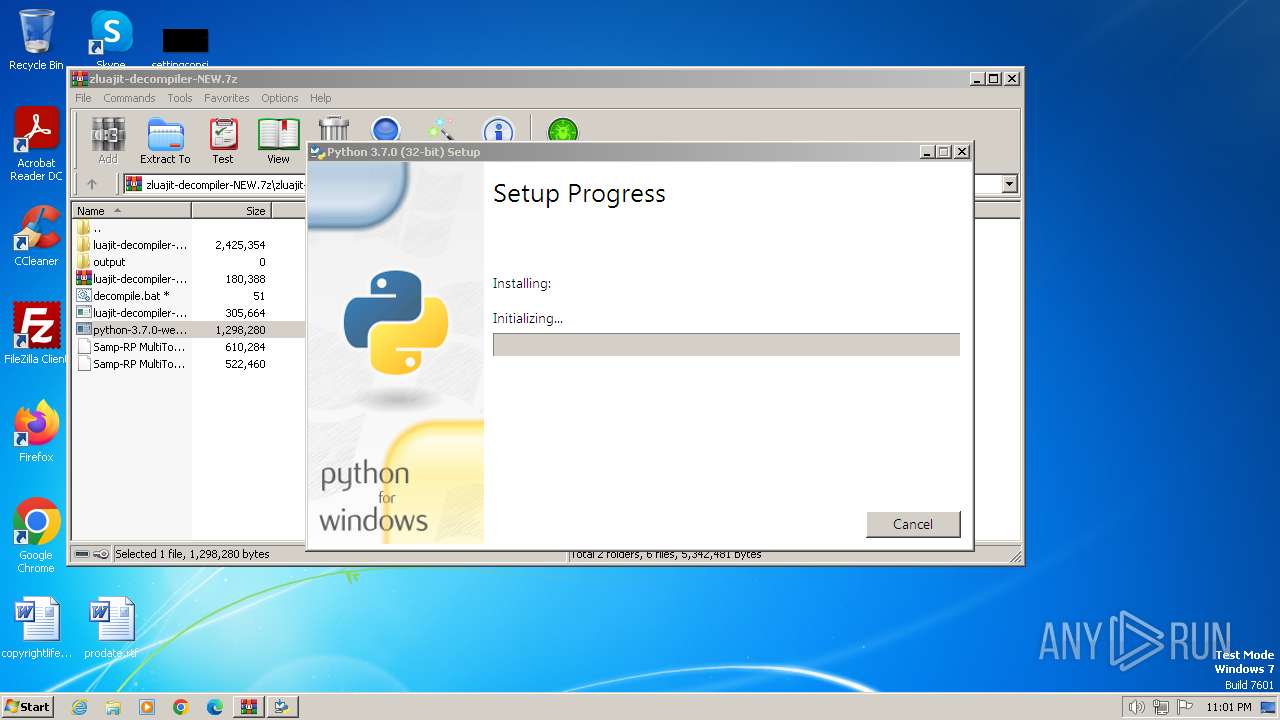
- python-3.7.0-webinstall.exe (PID: 3952)
- python-3.7.0-webinstall.exe (PID: 3664)
Changes the autorun value in the registry
- python-3.7.0-webinstall.exe (PID: 3664)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 1384)
- python-3.7.0-webinstall.exe (PID: 3664)
Executable content was dropped or overwritten
- python-3.7.0-webinstall.exe (PID: 3664)
- python-3.7.0-webinstall.exe (PID: 3952)
- python-3.7.0-webinstall.exe (PID: 864)
Reads the Internet Settings
- python-3.7.0-webinstall.exe (PID: 3664)
Searches for installed software
- python-3.7.0-webinstall.exe (PID: 3664)
- python-3.7.0-webinstall.exe (PID: 864)
Starts itself from another location
- python-3.7.0-webinstall.exe (PID: 3664)
Executes as Windows Service
- VSSVC.exe (PID: 1696)
Creates a software uninstall entry
- python-3.7.0-webinstall.exe (PID: 3664)
Reads settings of System Certificates
- python-3.7.0-webinstall.exe (PID: 3664)
Checks Windows Trust Settings
- python-3.7.0-webinstall.exe (PID: 3664)
Write to the desktop.ini file (may be used to cloak folders)
- WinRAR.exe (PID: 1384)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1384)
Create files in a temporary directory
- python-3.7.0-webinstall.exe (PID: 3664)
- python-3.7.0-webinstall.exe (PID: 3952)
Checks supported languages
- python-3.7.0-webinstall.exe (PID: 3664)
- python-3.7.0-webinstall.exe (PID: 864)
- python-3.7.0-webinstall.exe (PID: 3952)
Reads the computer name
- python-3.7.0-webinstall.exe (PID: 3664)
- python-3.7.0-webinstall.exe (PID: 864)
Reads the machine GUID from the registry
- python-3.7.0-webinstall.exe (PID: 3664)
- python-3.7.0-webinstall.exe (PID: 864)
Creates files or folders in the user directory
- python-3.7.0-webinstall.exe (PID: 3664)
Checks proxy server information
- python-3.7.0-webinstall.exe (PID: 3664)
Reads the software policy settings
- python-3.7.0-webinstall.exe (PID: 3664)
Creates files in the program directory
- python-3.7.0-webinstall.exe (PID: 864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
44
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
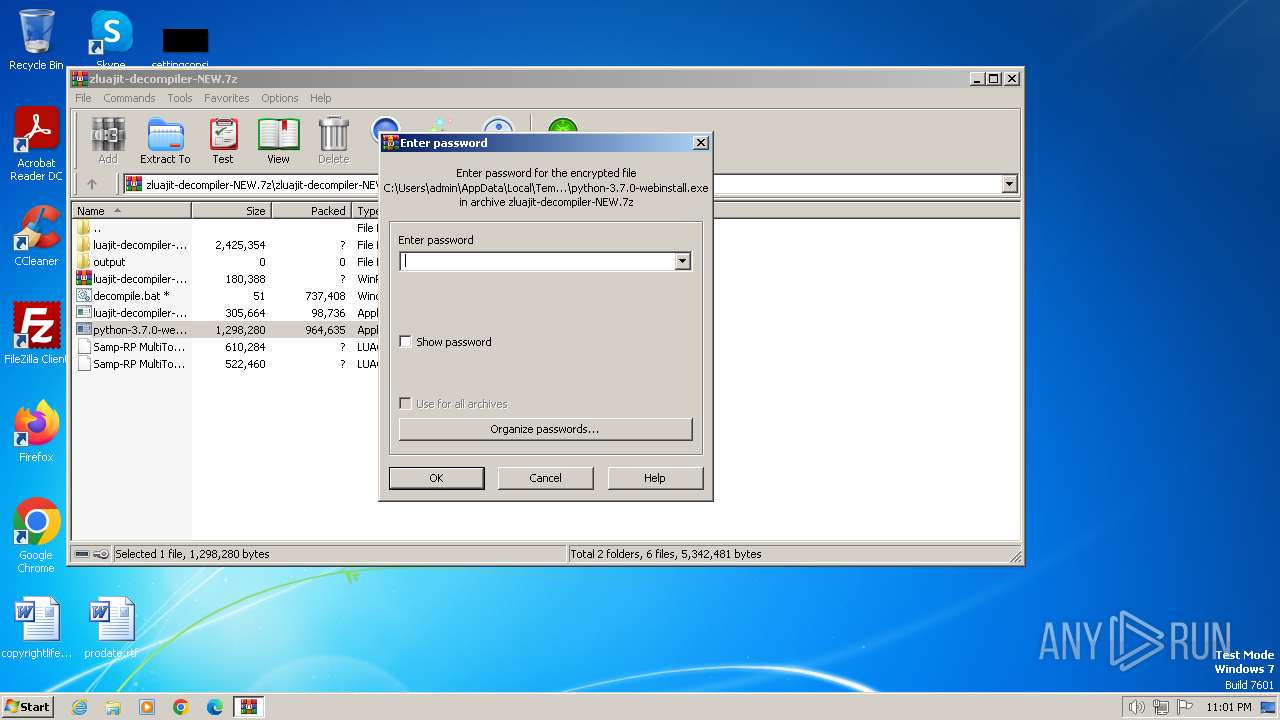
| 864 | "C:\Users\admin\AppData\Local\Temp\{B494D657-A5AC-46A9-AC99-680DBBCD582F}\.be\python-3.7.0-webinstall.exe" -q -burn.elevated BurnPipe.{B459BBAD-2415-433F-881A-B7C14D0A1E24} {77BB8234-E6F6-45E8-8AB2-B282E943BD98} 3664 | C:\Users\admin\AppData\Local\Temp\{B494D657-A5AC-46A9-AC99-680DBBCD582F}\.be\python-3.7.0-webinstall.exe | python-3.7.0-webinstall.exe | ||||||||||||
User: admin Company: Python Software Foundation Integrity Level: HIGH Description: Python 3.7.0 (32-bit) Exit code: 0 Version: 3.7.150.0 Modules
| |||||||||||||||
| 1384 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\zluajit-decompiler-NEW.7z" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1696 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3664 | "C:\Users\admin\AppData\Local\Temp\{90D9A52C-56B2-4AB9-9209-1905758A90E9}\.cr\python-3.7.0-webinstall.exe" -burn.clean.room="C:\Users\admin\AppData\Local\Temp\Rar$EXb1384.46884\zluajit-decompiler-NEW\python-3.7.0-webinstall.exe" -burn.filehandle.attached=152 -burn.filehandle.self=160 | C:\Users\admin\AppData\Local\Temp\{90D9A52C-56B2-4AB9-9209-1905758A90E9}\.cr\python-3.7.0-webinstall.exe | python-3.7.0-webinstall.exe | ||||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python 3.7.0 (32-bit) Exit code: 0 Version: 3.7.150.0 Modules
| |||||||||||||||
| 3952 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb1384.46884\zluajit-decompiler-NEW\python-3.7.0-webinstall.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb1384.46884\zluajit-decompiler-NEW\python-3.7.0-webinstall.exe | WinRAR.exe | ||||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python 3.7.0 (32-bit) Exit code: 0 Version: 3.7.150.0 Modules
| |||||||||||||||
Total events
13 001
Read events
12 739
Write events
243
Delete events
19
Modification events
| (PID) Process: | (1384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1384) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (1384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (1384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\zluajit-decompiler-NEW.7z | |||
| (PID) Process: | (1384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1384) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
33
Suspicious files
66
Text files
108
Unknown types
149
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb1384.46884\zluajit-decompiler-NEW\luajit-decompiler-masterOLD\aPrevious\decompile.py | text | |
MD5:4F1DD71EEDFD2B8D11FFFE643436B5D0 | SHA256:9E69D161235195EE69D42345E72A25FECE3AC65625C0CE6824C4EAB663B64ED1 | |||
| 1384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb1384.46884\zluajit-decompiler-NEW\luajit-decompiler-masterOLD\aPrevious\ljd\ast\locals.py | text | |
MD5:93AA17BCC31FD219DCBC807B320B3723 | SHA256:4DE42EC1CF7233484430E7150ECCCACB291A1826D0AACDDF67275653294072CC | |||
| 1384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb1384.46884\zluajit-decompiler-NEW\decompile.bat | text | |
MD5:EA8081DB8FBD5DC703BEB4CFA7383D54 | SHA256:AC6031A3C1FB69D2971C3622180F10D91812E4CFED106332D28F5829415CAF44 | |||
| 1384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb1384.46884\zluajit-decompiler-NEW\luajit-decompiler-masterOLD\aPrevious\ljd\ast\helpers.py | text | |
MD5:6892B3D30AC46AF6B141B6BE92AFB3DC | SHA256:DD2F43078B729362B828AC112482CAB9C8309BABF1280DE5014B6EFBB5003A37 | |||
| 1384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb1384.46884\zluajit-decompiler-NEW\luajit-decompiler-masterOLD\aPrevious\ljd\ast\unwarper.py | text | |
MD5:59A5328B5FAB8827557011E5D67B9994 | SHA256:AB809D19C1180552C29925D010C319FB5C066A76A1EAF032C6FF37D9328D8622 | |||
| 1384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb1384.46884\zluajit-decompiler-NEW\luajit-decompiler-masterOLD\aPrevious\ljd\ast\validator.py | text | |
MD5:8A09F8D5C5BE22B28E40A426B2ECA6AF | SHA256:9926CBFEA538052D8E9C50362F164D5BC10344FE557AF1D4F629C92D1911142C | |||
| 1384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb1384.46884\zluajit-decompiler-NEW\luajit-decompiler-masterOLD\aPrevious\ljd\ast\__init__.py | text | |
MD5:FB6B8ED25057C388AFBEE42BCCD39928 | SHA256:860A998F28B35A3DCFABF44D9C7B23157431BAEB904F1A2893401753BBA2F291 | |||
| 1384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb1384.46884\zluajit-decompiler-NEW\luajit-decompiler-masterOLD\aPrevious\ljd\ast\traverse.py | text | |
MD5:735F255360618FC63317B1823FCC76DF | SHA256:0F7082D3EAD0E3681391E78A47725290213380293AF0A0B514FE0C66557D36A9 | |||
| 1384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb1384.46884\zluajit-decompiler-NEW\luajit-decompiler-masterOLD\aPrevious\ljd\ast\nodes.py | text | |
MD5:47A98A9A2D20E3D4B84F405363730505 | SHA256:2AD903702D4A93DDC42832B159B44F16D56E0302A8E0D1ED7FDE69D1255E4CB2 | |||
| 1384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb1384.46884\zluajit-decompiler-NEW\luajit-decompiler-masterOLD\aPrevious\ljd\ast\__pycache__\helpers.cpython-37.pyc | binary | |
MD5:6FCFB10AF83945D172EC77AEC9253740 | SHA256:ED7E662075DEF480783174FDDAFDBEFF5235A6150CB1BE548B670D804E34B641 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
8
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3664 | python-3.7.0-webinstall.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?99fa285759fbe781 | unknown | — | — | unknown |
3664 | python-3.7.0-webinstall.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEH3wUWDKXSh7Z3b6AuDWurw%3D | unknown | binary | 1.40 Kb | unknown |
1080 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c503292d7802e201 | unknown | compressed | 65.2 Kb | unknown |
1080 | svchost.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?89bca2e7018c82c0 | unknown | compressed | 65.2 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3664 | python-3.7.0-webinstall.exe | 146.75.116.223:443 | www.python.org | FASTLY | US | unknown |
3664 | python-3.7.0-webinstall.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3664 | python-3.7.0-webinstall.exe | 104.18.20.226:80 | ocsp2.globalsign.com | CLOUDFLARENET | — | shared |
1080 | svchost.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.python.org |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |