| File name: | SIW.2023.v13.4.0424.Technician.exe |
| Full analysis: | https://app.any.run/tasks/ad7a83a7-6627-4b16-815a-990d1a0c9eff |
| Verdict: | Malicious activity |
| Threats: | IcedID is a banking trojan-type malware which allows attackers to utilize it to steal banking credentials of the victims. IcedID aka BokBot mainly targets businesses and steals payment information, it also acts as a loader and can deliver another viruses or download additional modules. |
| Analysis date: | January 12, 2025, 18:55:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | DA11BD40B5FD11BC06FA9520820E0DF8 |
| SHA1: | 687445411560E573D4E659849C2B248478568650 |
| SHA256: | 59641B892D1A2779CBD5EBA95FBBCEC5126E878CEA1463E8DACA601D42BC35CB |
| SSDEEP: | 98304:bAR2yC2SJSSXI/c9jGWWsW7jpMCYlt9MbtuejD0Lr4pke5DxQSFCnU+RbNNL3oM9:ntzbZ5BTESnrH1msfROBN/OSgR8sN/f |
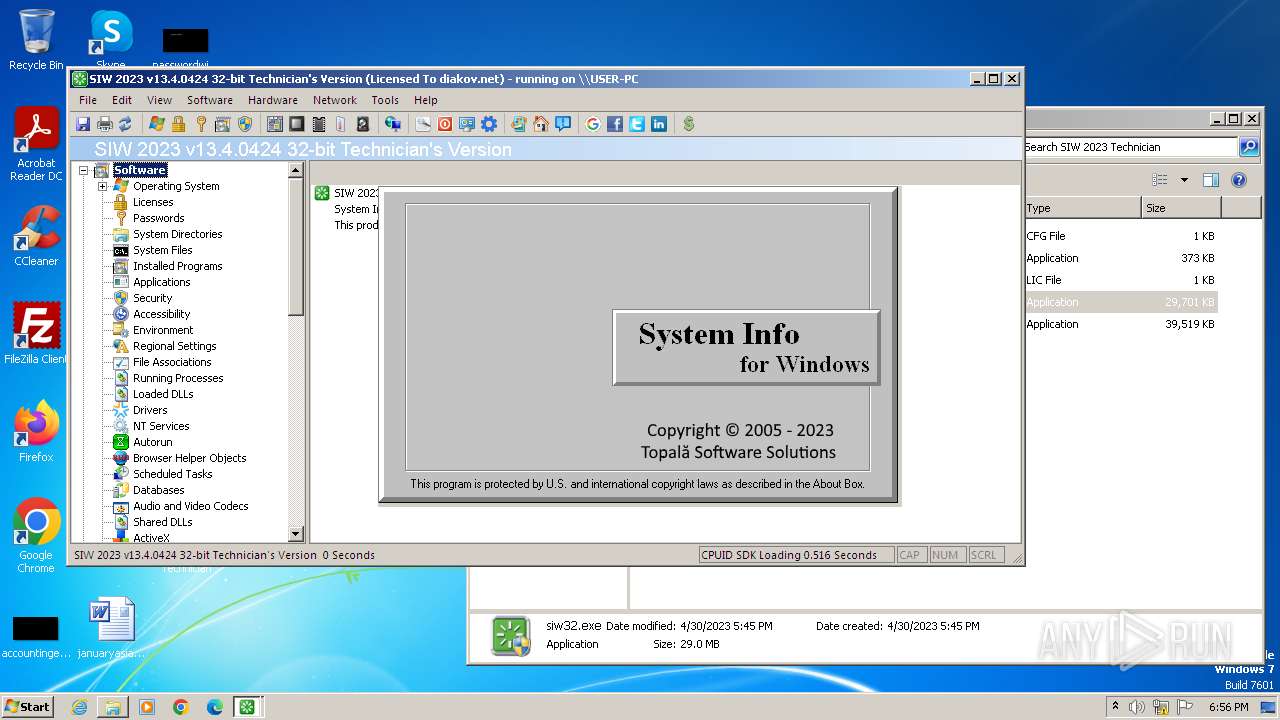
MALICIOUS
Scans artifacts that could help determine the target
- siw32.exe (PID: 3008)
ICEDID has been detected (YARA)
- siw32.exe (PID: 3008)
SPICERAT has been detected (YARA)
- siw32.exe (PID: 3008)
Actions looks like stealing of personal data
- siw32.exe (PID: 3008)
SUSPICIOUS
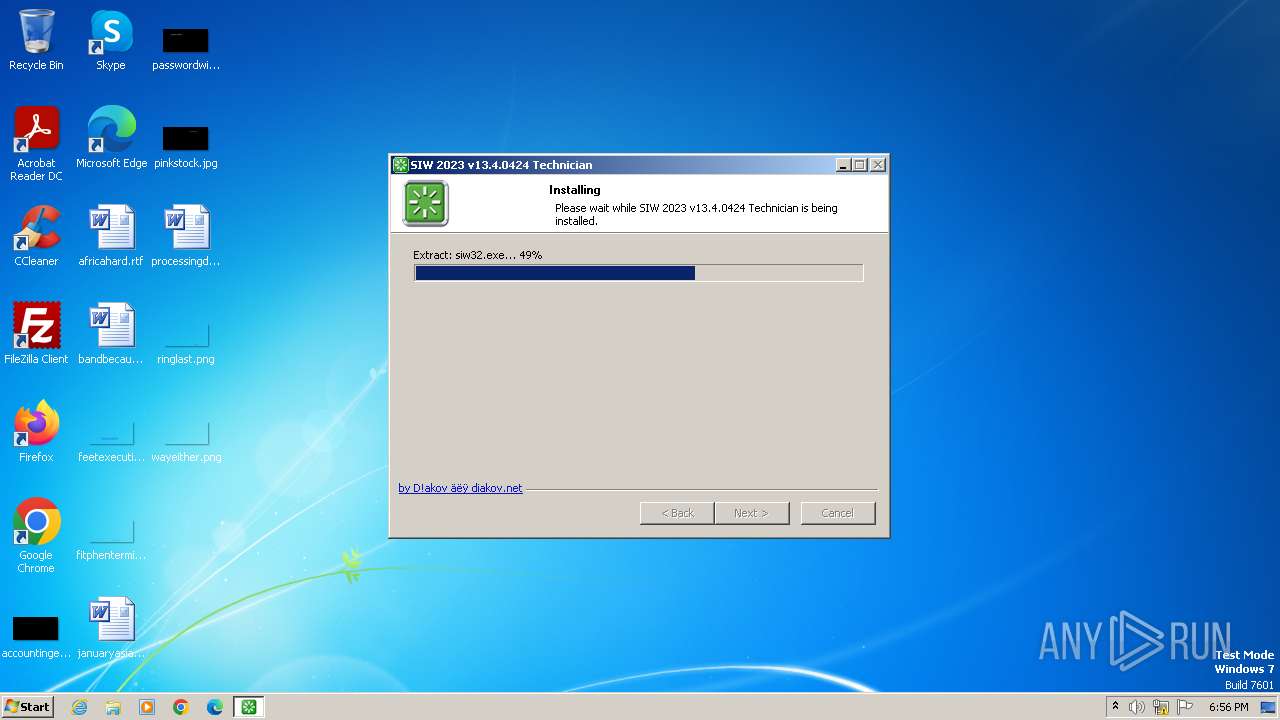
Executable content was dropped or overwritten
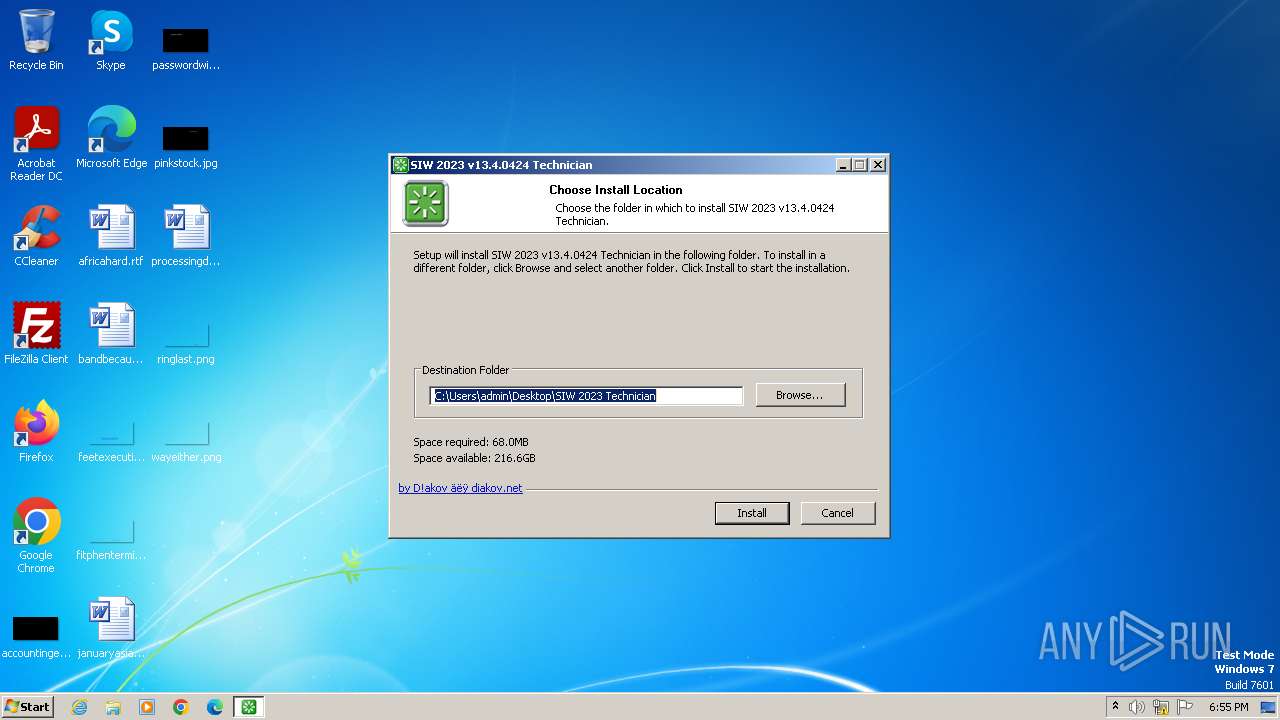
- SIW.2023.v13.4.0424.Technician.exe (PID: 1828)
- siw32.exe (PID: 3008)
Malware-specific behavior (creating "System.dll" in Temp)
- SIW.2023.v13.4.0424.Technician.exe (PID: 1828)
The process creates files with name similar to system file names
- SIW.2023.v13.4.0424.Technician.exe (PID: 1828)
Checks Windows Trust Settings
- siw32.exe (PID: 3008)
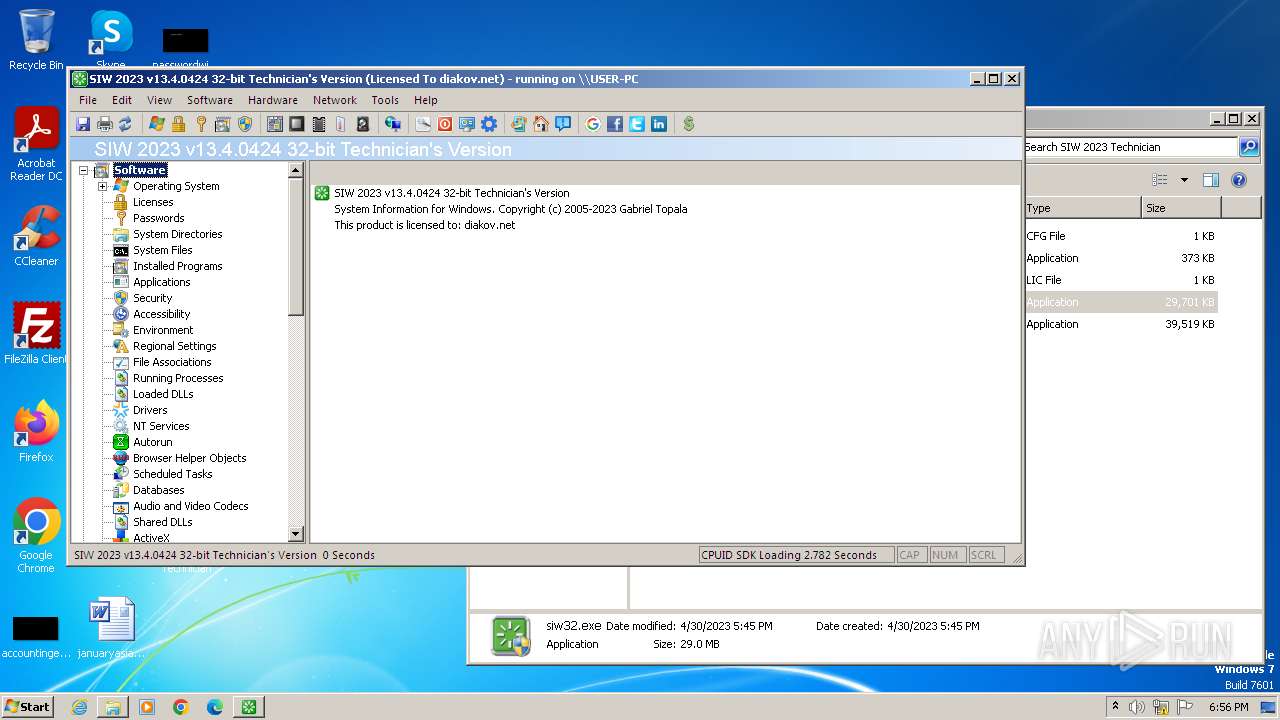
Searches for installed software
- siw32.exe (PID: 3008)
Reads the Internet Settings
- siw32.exe (PID: 3008)
Reads the history of recent RDP connections
- siw32.exe (PID: 3008)
Connects to the server without a host name
- siw32.exe (PID: 3008)
Reads settings of System Certificates
- siw32.exe (PID: 3008)
Reads security settings of Internet Explorer
- siw32.exe (PID: 3008)
Reads the BIOS version
- siw32.exe (PID: 3008)
Checks for Java to be installed
- siw32.exe (PID: 3008)
There is functionality for VM detection antiVM strings (YARA)
- siw32.exe (PID: 3008)
There is functionality for VM detection Parallels (YARA)
- siw32.exe (PID: 3008)
There is functionality for VM detection VirtualBox (YARA)
- siw32.exe (PID: 3008)
There is functionality for VM detection VMWare (YARA)
- siw32.exe (PID: 3008)
The process verifies whether the antivirus software is installed
- siw32.exe (PID: 3008)
The process checks if it is being run in the virtual environment
- siw32.exe (PID: 3008)
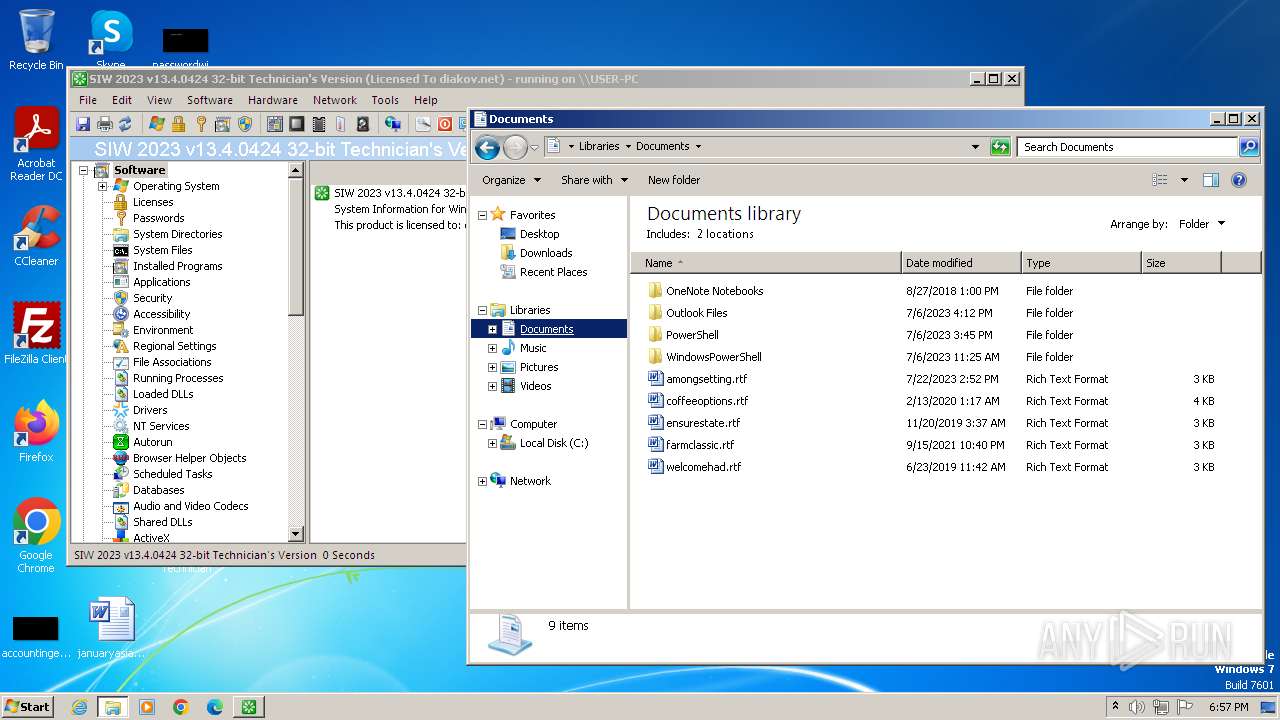
Accesses Microsoft Outlook profiles
- siw32.exe (PID: 3008)
INFO
The sample compiled with english language support
- SIW.2023.v13.4.0424.Technician.exe (PID: 1828)
- siw32.exe (PID: 3008)
Create files in a temporary directory
- SIW.2023.v13.4.0424.Technician.exe (PID: 1828)
- siw32.exe (PID: 3008)
The sample compiled with russian language support
- SIW.2023.v13.4.0424.Technician.exe (PID: 1828)
Reads the computer name
- SIW.2023.v13.4.0424.Technician.exe (PID: 1828)
- siw32.exe (PID: 3008)
- wmpnscfg.exe (PID: 1736)
Checks supported languages
- SIW.2023.v13.4.0424.Technician.exe (PID: 1828)
- siw.exe (PID: 2052)
- siw32.exe (PID: 3008)
- wmpnscfg.exe (PID: 1736)
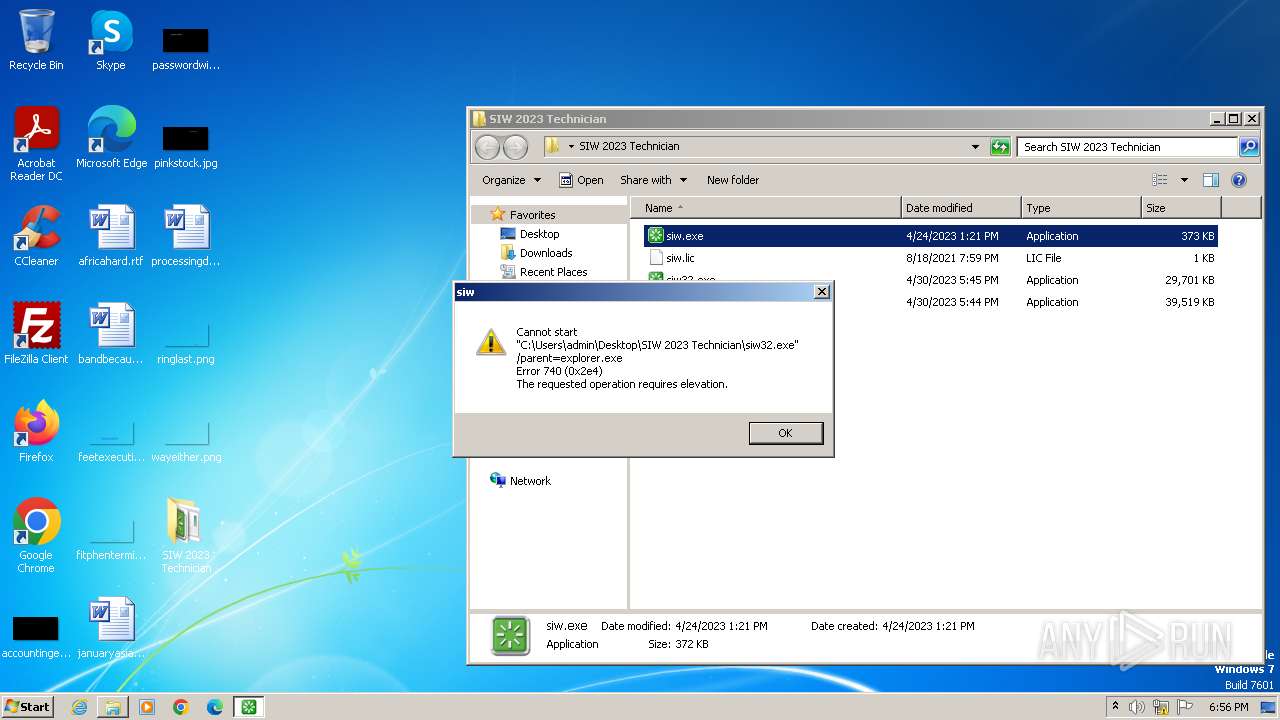
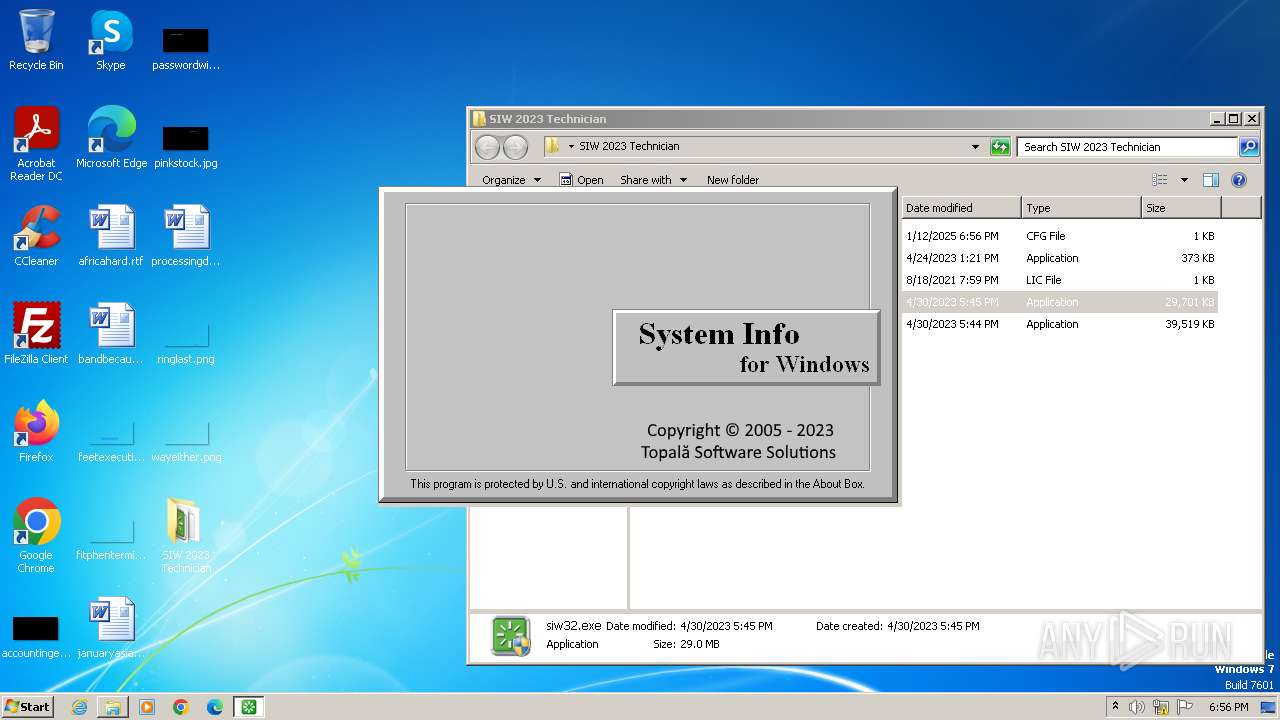
Manual execution by a user
- siw.exe (PID: 2052)
- siw32.exe (PID: 3176)
- siw32.exe (PID: 3008)
- wmpnscfg.exe (PID: 1736)
Reads Environment values
- siw32.exe (PID: 3008)
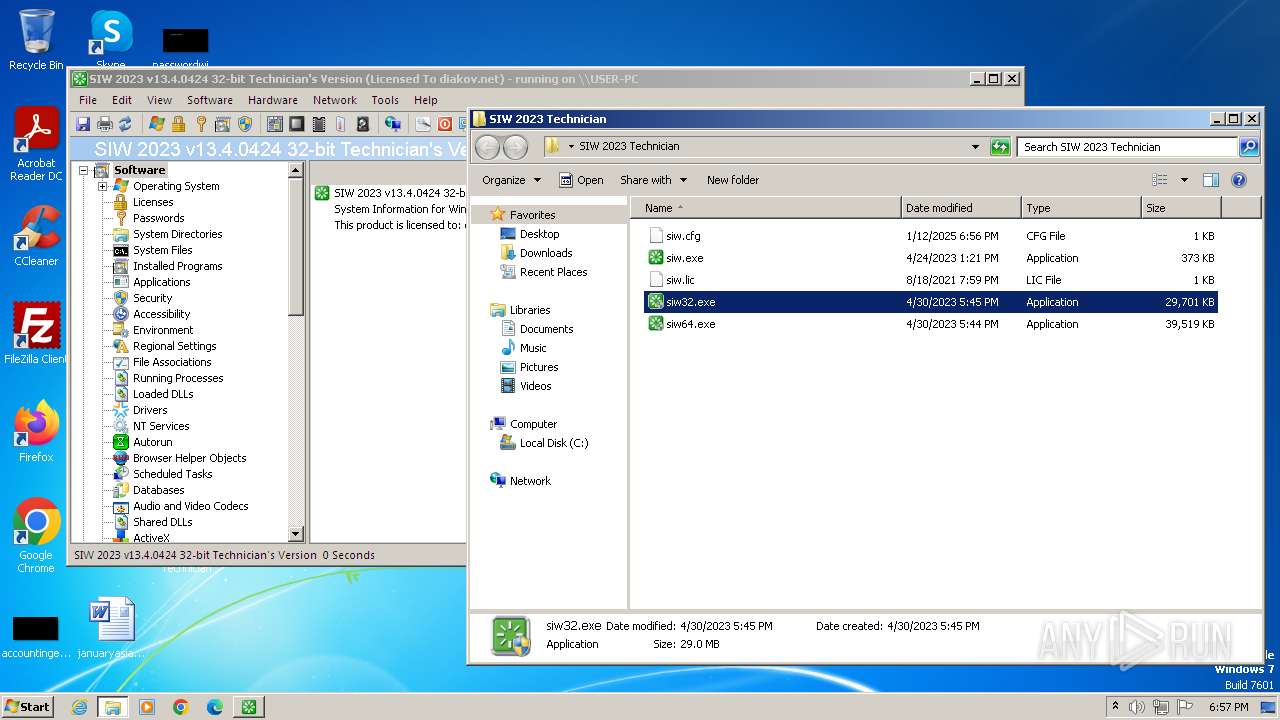
Creates files in the program directory
- siw32.exe (PID: 3008)
Process checks whether UAC notifications are on
- siw32.exe (PID: 3008)
Reads the machine GUID from the registry
- siw32.exe (PID: 3008)
Reads Windows Product ID
- siw32.exe (PID: 3008)
Reads product name
- siw32.exe (PID: 3008)
Reads Microsoft Office registry keys
- siw32.exe (PID: 3008)
The sample compiled with french language support
- siw32.exe (PID: 3008)
Reads CPU info
- siw32.exe (PID: 3008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 22:50:46+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x323c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2023.13.4.424 |
| ProductVersionNumber: | 2023.13.4.424 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Russian |
| CharacterSet: | Windows, Cyrillic |
| CompanyName: | diakov.net |
| FileDescription: | SIW 2023 v13.4.0424 Technician |
| FileVersion: | 2023.13.4.0424 |
Total processes
49
Monitored processes
7
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
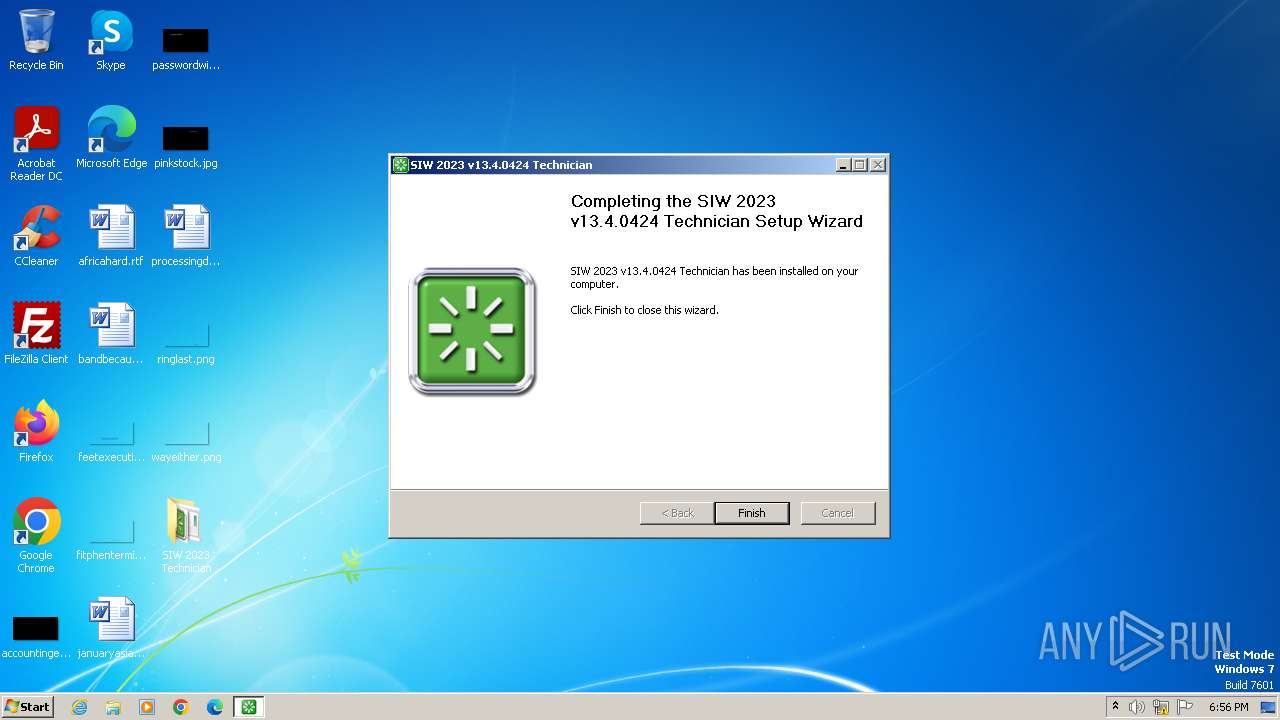
| 1560 | "C:\Users\admin\Downloads\SIW.2023.v13.4.0424.Technician.exe" | C:\Users\admin\Downloads\SIW.2023.v13.4.0424.Technician.exe | — | explorer.exe | |||||||||||
User: admin Company: diakov.net Integrity Level: MEDIUM Description: SIW 2023 v13.4.0424 Technician Exit code: 3221226540 Version: 2023.13.4.0424 Modules
| |||||||||||||||
| 1736 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1828 | "C:\Users\admin\Downloads\SIW.2023.v13.4.0424.Technician.exe" | C:\Users\admin\Downloads\SIW.2023.v13.4.0424.Technician.exe | explorer.exe | ||||||||||||
User: admin Company: diakov.net Integrity Level: HIGH Description: SIW 2023 v13.4.0424 Technician Exit code: 0 Version: 2023.13.4.0424 Modules
| |||||||||||||||
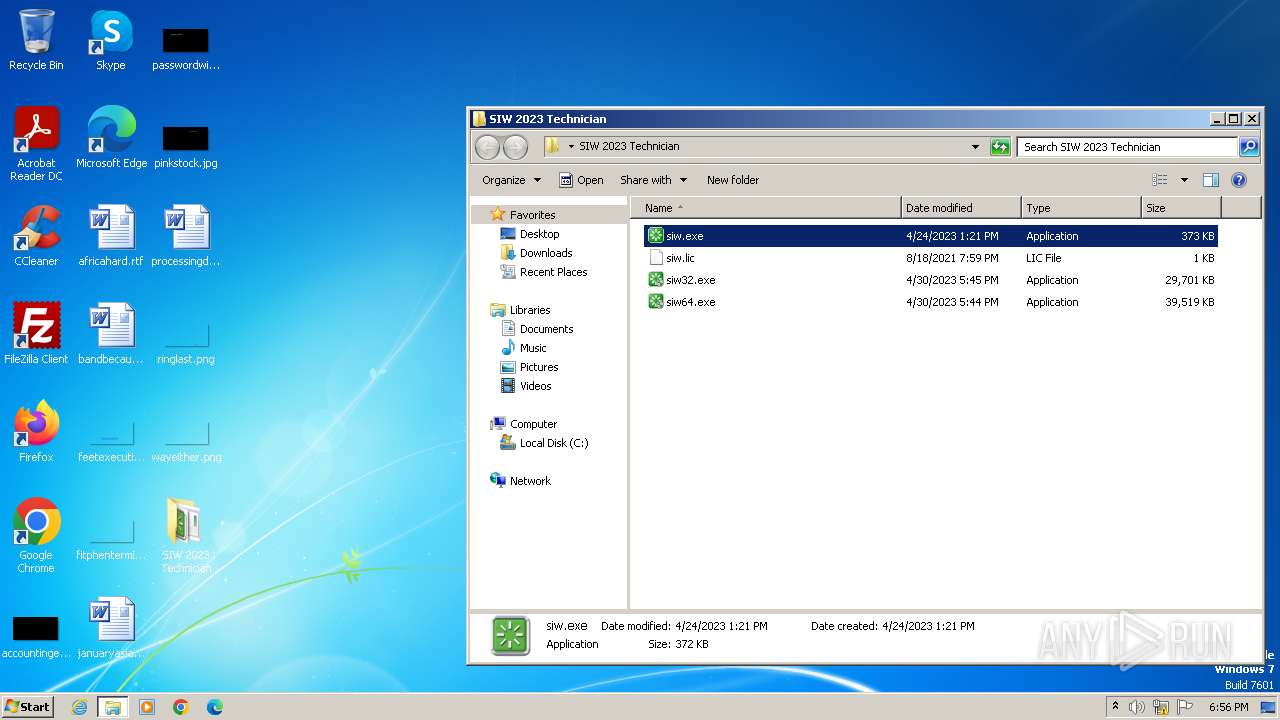
| 2052 | "C:\Users\admin\Desktop\SIW 2023 Technician\siw.exe" | C:\Users\admin\Desktop\SIW 2023 Technician\siw.exe | — | explorer.exe | |||||||||||
User: admin Company: Topala Software Solutions Integrity Level: MEDIUM Description: SIW Launcher Exit code: 0 Version: 2,5,0,0 Modules
| |||||||||||||||
| 2108 | "C:\Users\admin\Desktop\SIW 2023 Technician\siw32.exe" /parent=explorer.exe | C:\Users\admin\Desktop\SIW 2023 Technician\siw32.exe | — | siw.exe | |||||||||||
User: admin Company: Topala Software Solutions Integrity Level: MEDIUM Description: SIW - System Information for Windows Exit code: 3221226540 Version: 13,4,0,0 Modules
| |||||||||||||||
| 3008 | "C:\Users\admin\Desktop\SIW 2023 Technician\siw32.exe" | C:\Users\admin\Desktop\SIW 2023 Technician\siw32.exe | explorer.exe | ||||||||||||
User: admin Company: Topala Software Solutions Integrity Level: HIGH Description: SIW - System Information for Windows Version: 13,4,0,0 Modules
| |||||||||||||||
| 3176 | "C:\Users\admin\Desktop\SIW 2023 Technician\siw32.exe" | C:\Users\admin\Desktop\SIW 2023 Technician\siw32.exe | — | explorer.exe | |||||||||||
User: admin Company: Topala Software Solutions Integrity Level: MEDIUM Description: SIW - System Information for Windows Exit code: 3221226540 Version: 13,4,0,0 Modules
| |||||||||||||||
Total events
35 460
Read events
35 378
Write events
82
Delete events
0
Modification events
| (PID) Process: | (3008) siw32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\sud.dll,-10 |
Value: Choose which programs you want Windows to use for activities like web browsing, editing photos, sending e-mail, and playing music. | |||
| (PID) Process: | (3008) siw32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3008) siw32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | @%windir%\system32\displayswitch.exe,-321 |
Value: Connect your computer to a projector by display cable. | |||
| (PID) Process: | (3008) siw32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | @%windir%\system32\mblctr.exe,-1004 |
Value: Opens the Windows Mobility Center so you can adjust display brightness, volume, power options, and other mobile PC settings. | |||
| (PID) Process: | (3008) siw32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | @%systemroot%\system32\Msinfo32.exe,-130 |
Value: Display detailed information about your computer. | |||
| (PID) Process: | (3008) siw32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | @%systemroot%\system32\dfrgui.exe,-172 |
Value: Defragments your disks so that your computer runs faster and more efficiently. | |||
| (PID) Process: | (3008) siw32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | @%systemroot%\system32\wdc.dll,-10031 |
Value: Monitor the usage and performance of the following resources in real time: CPU, Disk, Network and Memory. | |||
| (PID) Process: | (3008) siw32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | @%windir%\system32\migwiz\wet.dll,-601 |
Value: View reports from transfers you've performed | |||
| (PID) Process: | (3008) siw32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | @%windir%\system32\odbcint.dll,-1312 |
Value: Maintains ODBC data sources and drivers. | |||
| (PID) Process: | (3008) siw32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | @%windir%\system32\iscsicpl.dll,-5002 |
Value: Connect to remote iSCSI targets and configure connection settings. | |||
Executable files
11
Suspicious files
5
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
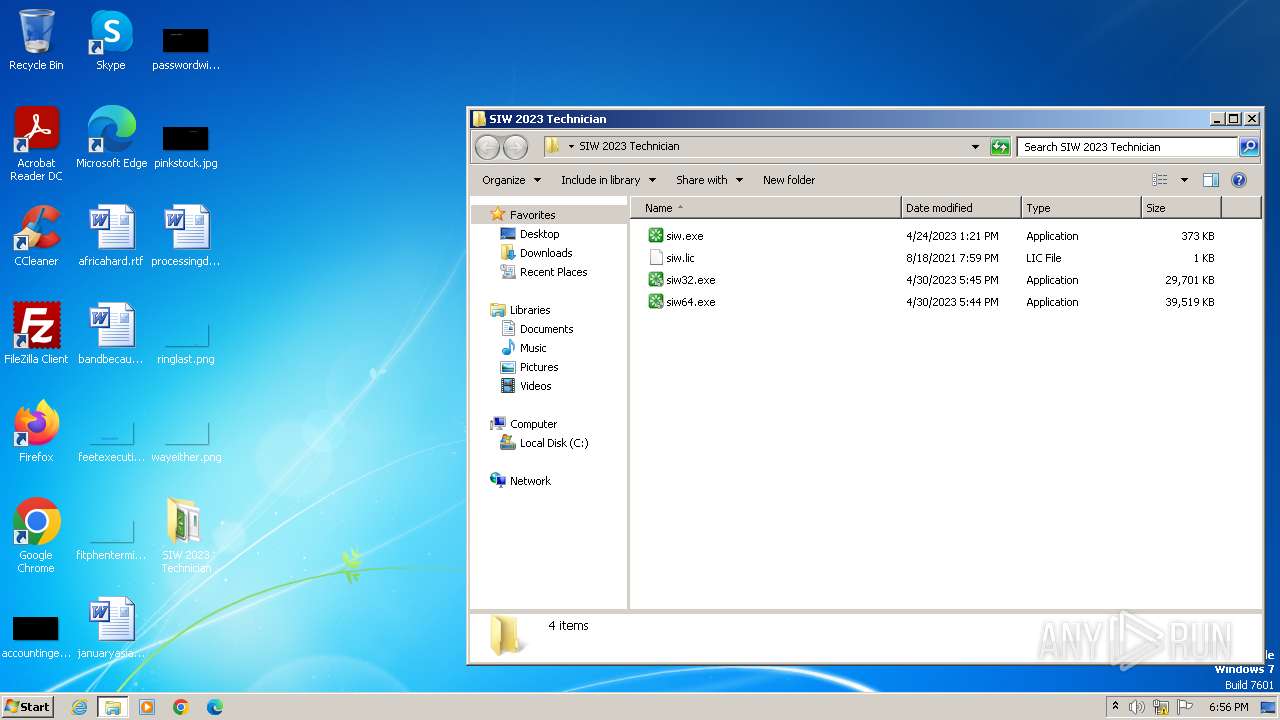
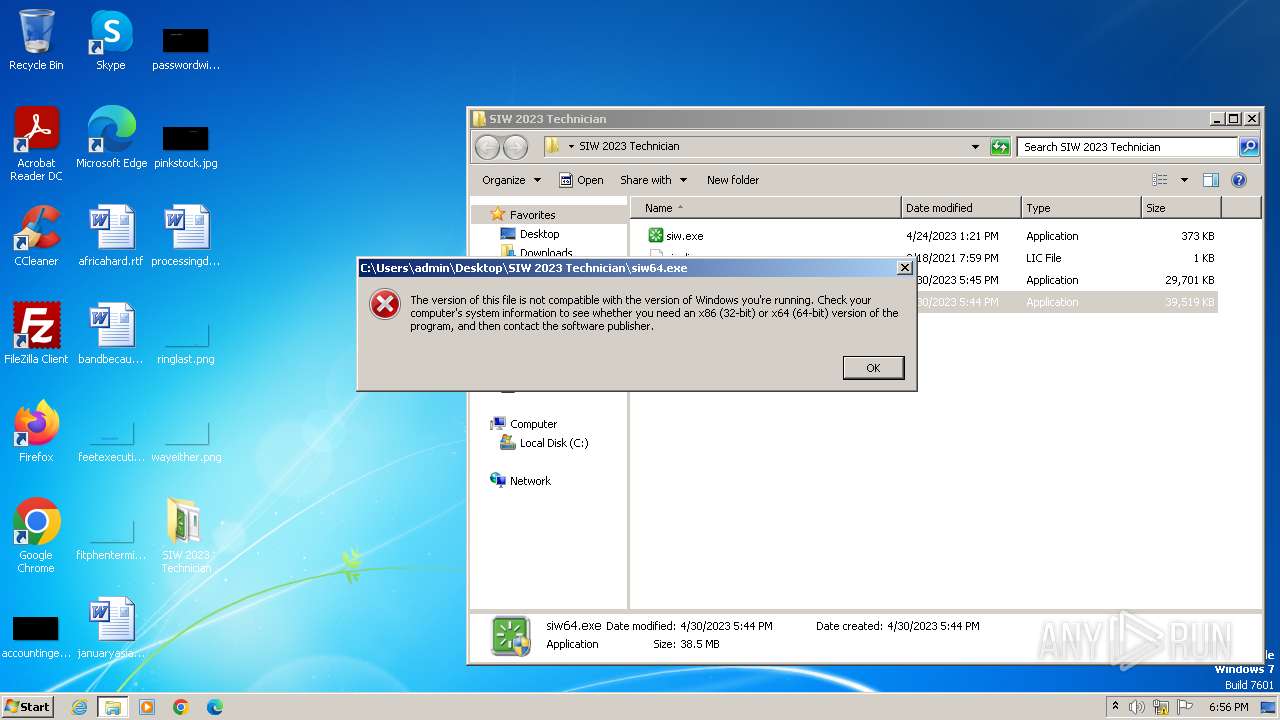
| 1828 | SIW.2023.v13.4.0424.Technician.exe | C:\Users\admin\Desktop\SIW 2023 Technician\siw64.exe | — | |
MD5:— | SHA256:— | |||
| 1828 | SIW.2023.v13.4.0424.Technician.exe | C:\Users\admin\AppData\Local\Temp\nsq790B.tmp | — | |
MD5:— | SHA256:— | |||
| 3008 | siw32.exe | C:\ProgramData\siw_tmp\CrashSender1500-x32.exe | executable | |
MD5:85CE87D2454CE18A1DC836B6D871A45C | SHA256:BA8698D1794F54D4011453566DB476EFA285C1FA957720979DEEB996FBB6D2AC | |||
| 1828 | SIW.2023.v13.4.0424.Technician.exe | C:\Users\admin\AppData\Local\Temp\nsg791C.tmp\modern-header.bmp | image | |
MD5:8B7F221F4F99825F95FA81FE120B208D | SHA256:5BCA33351ABADDD2C7F52B482D9D5C3A7DE80CB42FEA83A811E0FB1C09EC0601 | |||
| 1828 | SIW.2023.v13.4.0424.Technician.exe | C:\Users\admin\Desktop\SIW 2023 Technician\siw32.exe | executable | |
MD5:4E9FC35E8A00CA89D7176074F42F1987 | SHA256:C1EE4029EAAF7BAFF8ED090FA6B6569E1D9CFAC04480A50F5B12BA34F91B68B3 | |||
| 3008 | siw32.exe | C:\Users\admin\Desktop\SIW 2023 Technician\siw.cfg.tmp | binary | |
MD5:AE7A7E2B8828015249A56A41422C08E6 | SHA256:05D3A9ACB3D293ABD13B580301AD402F799E91E121EF4C629350025A6BFBA9AF | |||
| 3008 | siw32.exe | C:\ProgramData\siw_tmp\CrashRpt1500-x32.dll | executable | |
MD5:C601DAE73657BDA77B1CD8B546A79A77 | SHA256:24EE10317EA898F59E86830BFF092BA221111EA40ABA9EC1A4987B40A83257FE | |||
| 1828 | SIW.2023.v13.4.0424.Technician.exe | C:\Users\admin\AppData\Local\Temp\nsg791C.tmp\System.dll | executable | |
MD5:F4E3FA5C852D2BDC41756E58124B21D3 | SHA256:E457505B7648838185FD971E19DAF6FD626824D7935A2701342DF7099315E62C | |||
| 1828 | SIW.2023.v13.4.0424.Technician.exe | C:\Users\admin\AppData\Local\Temp\nsg791C.tmp\modern-wizard.bmp | image | |
MD5:DB698EB88D39B3833C1662DFF0772E75 | SHA256:3FD40951BD82CF0B7068FD5BEA6F65ED3EE101DB224CD122E76A32425010DAF5 | |||
| 1828 | SIW.2023.v13.4.0424.Technician.exe | C:\Users\admin\AppData\Local\Temp\nsg791C.tmp\BrandingURL.dll | executable | |
MD5:71C46B663BAA92AD941388D082AF97E7 | SHA256:BB2B9C272B8B66BC1B414675C2ACBA7AFAD03FFF66A63BABEE3EE57ED163D19E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
7
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3008 | siw32.exe | GET | 200 | 13.92.242.18:80 | http://13.92.242.18/scripts/date.php | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | unknown |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1108 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
3008 | siw32.exe | 13.92.242.18:80 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| unknown |