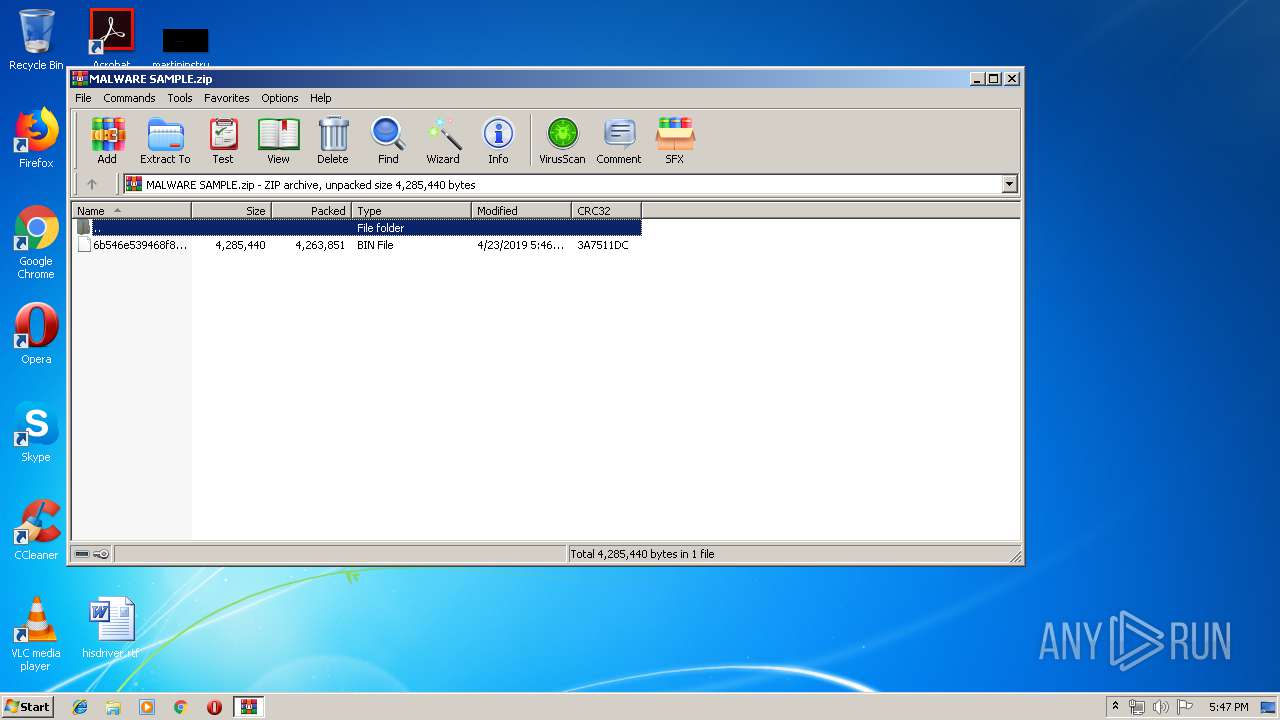
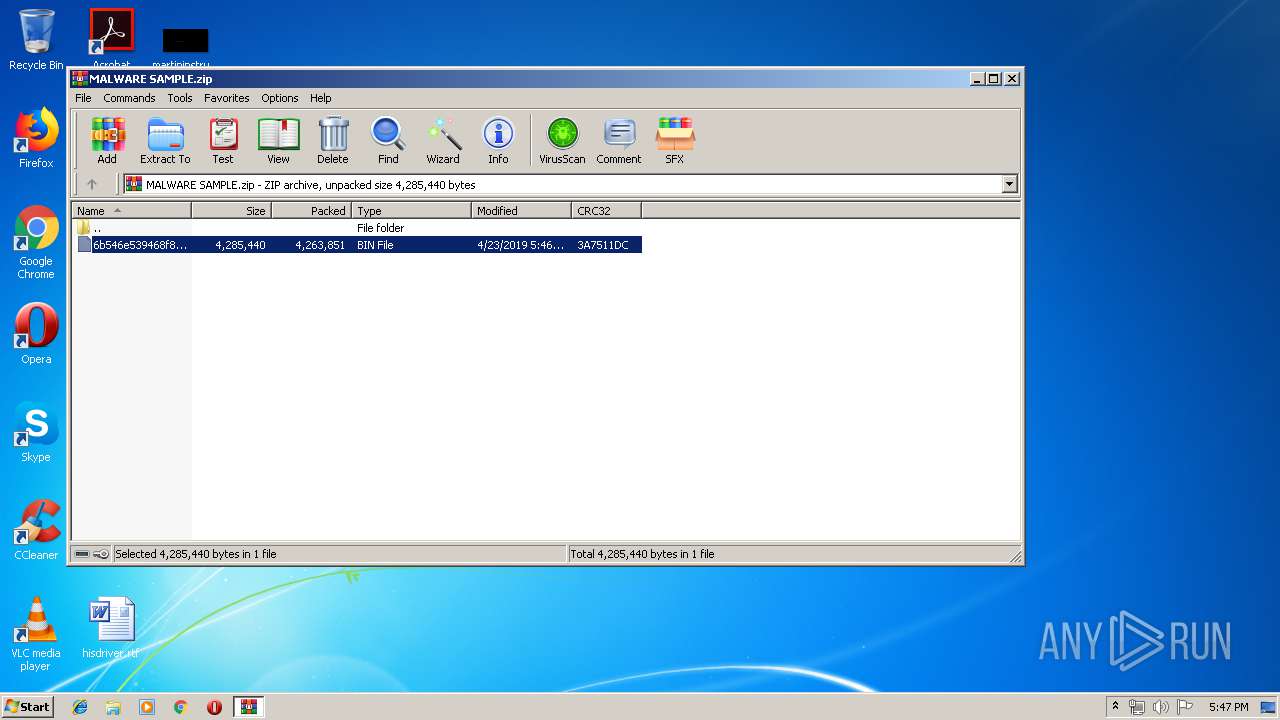
| File name: | MALWARE SAMPLE.zip |
| Full analysis: | https://app.any.run/tasks/e7158e64-4f3b-4f70-b529-00075436fe1d |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 16:46:59 |
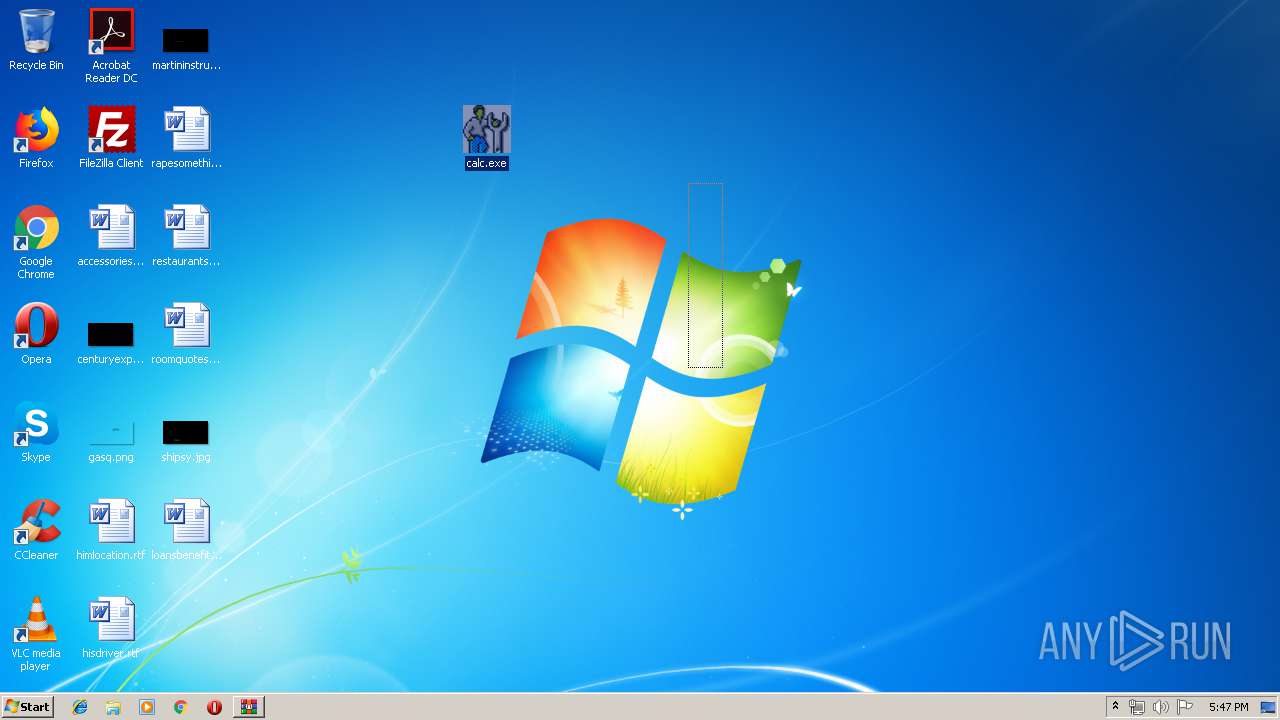
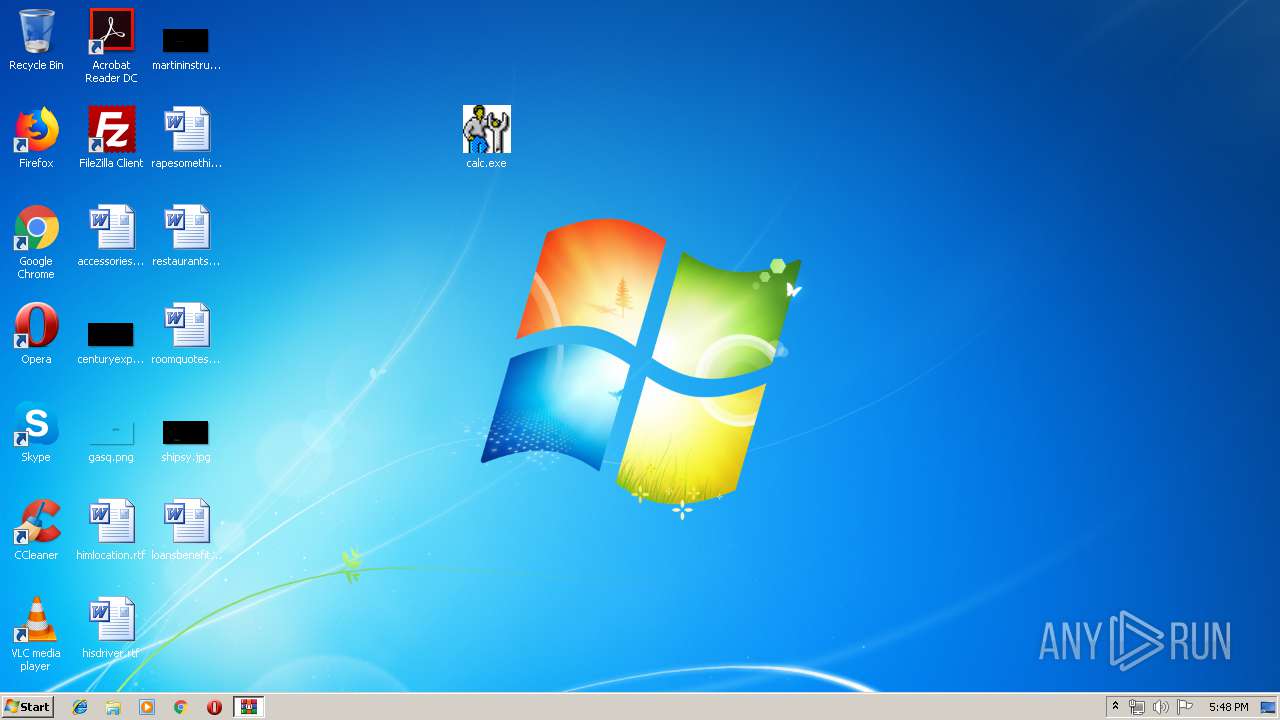
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 2D9DCAE60D6F96E0EE386081E7263D7B |
| SHA1: | A713B85B14D3BDFDF6D8484FB68C8ACCAF4E71F5 |
| SHA256: | 595CA6589D4E322403A42C127D8437010E1B4D137B9EEA014120744E26438654 |
| SSDEEP: | 98304:WkRXkbz0t+3t9JRtiryk0elKRzODqFR4HPXPk4v7:WWkU4h0qe6ODqFW3k4z |
MALICIOUS
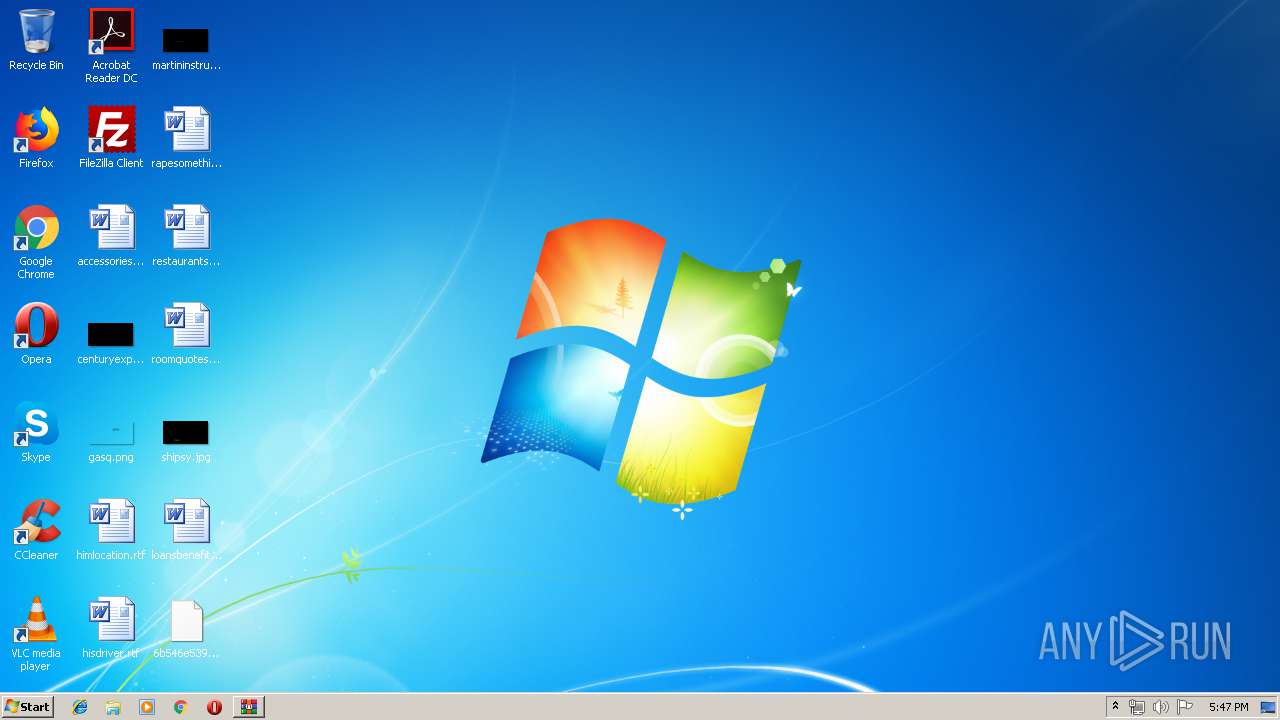
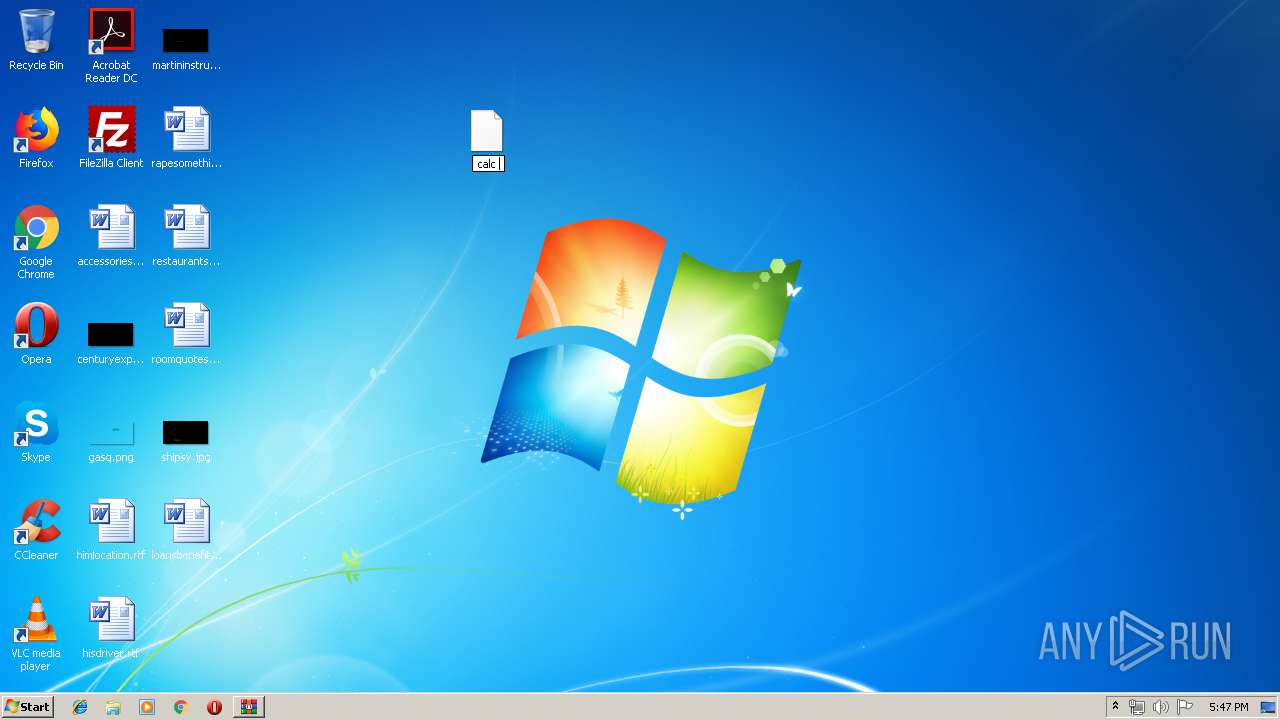
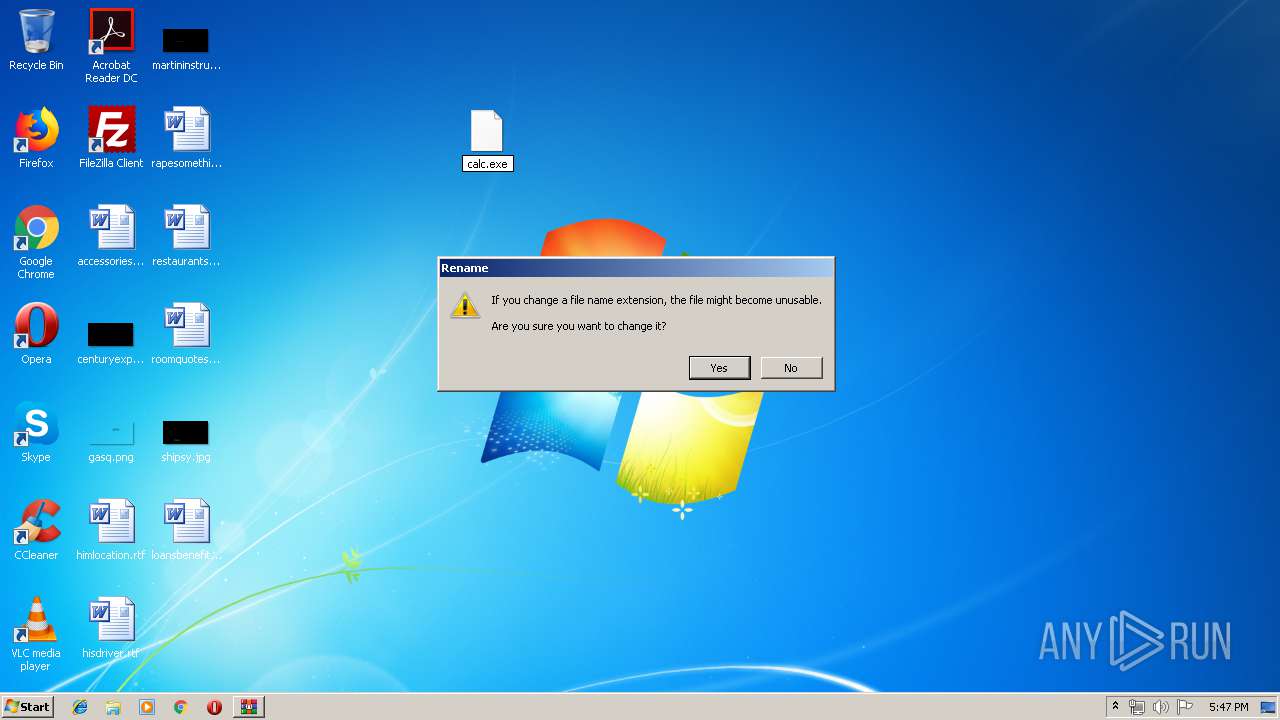
Application was dropped or rewritten from another process
- calc.exe (PID: 1696)
- calc.exe (PID: 1888)
SUSPICIOUS
Creates files in the user directory
- calc.exe (PID: 1888)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1020)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:04:23 16:46:23 |
| ZipCRC: | 0x3a7511dc |
| ZipCompressedSize: | 4263851 |
| ZipUncompressedSize: | 4285440 |
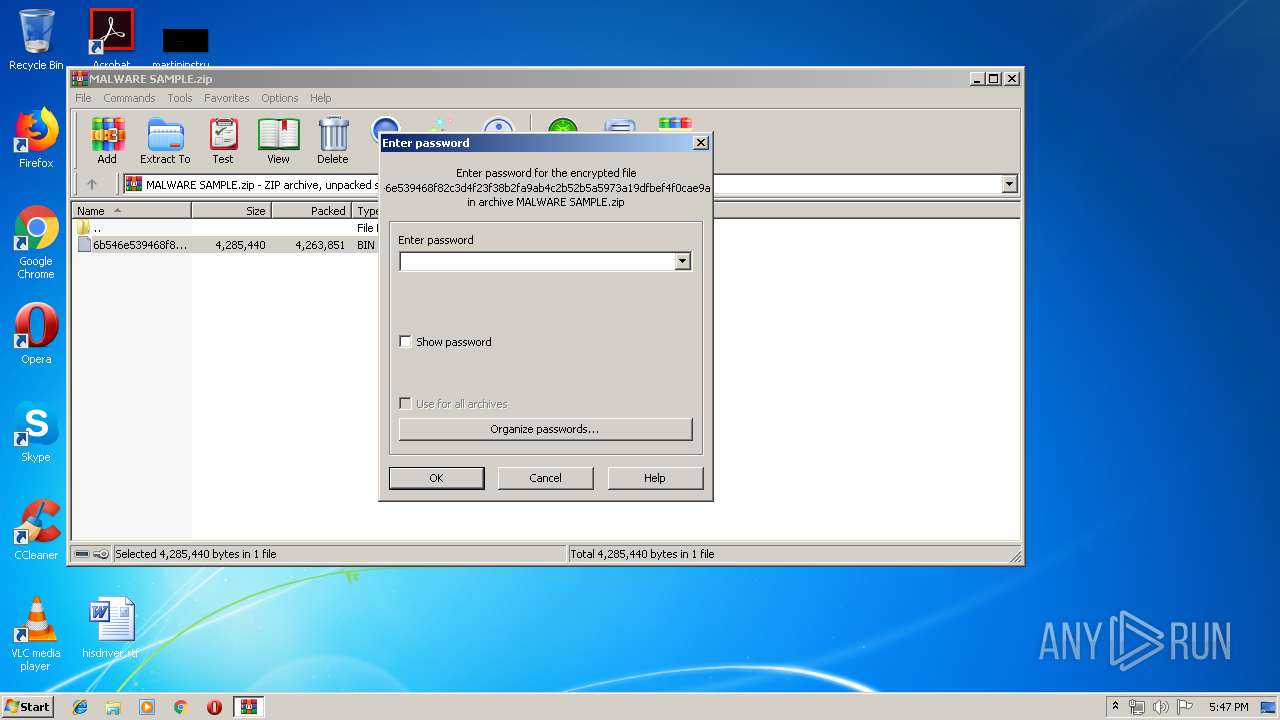
| ZipFileName: | 6b546e539468f82c3d4f23f38b2fa9ab4c2b52b5a5973a19dfbef4f0cae9a923.bin |
Total processes
35
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
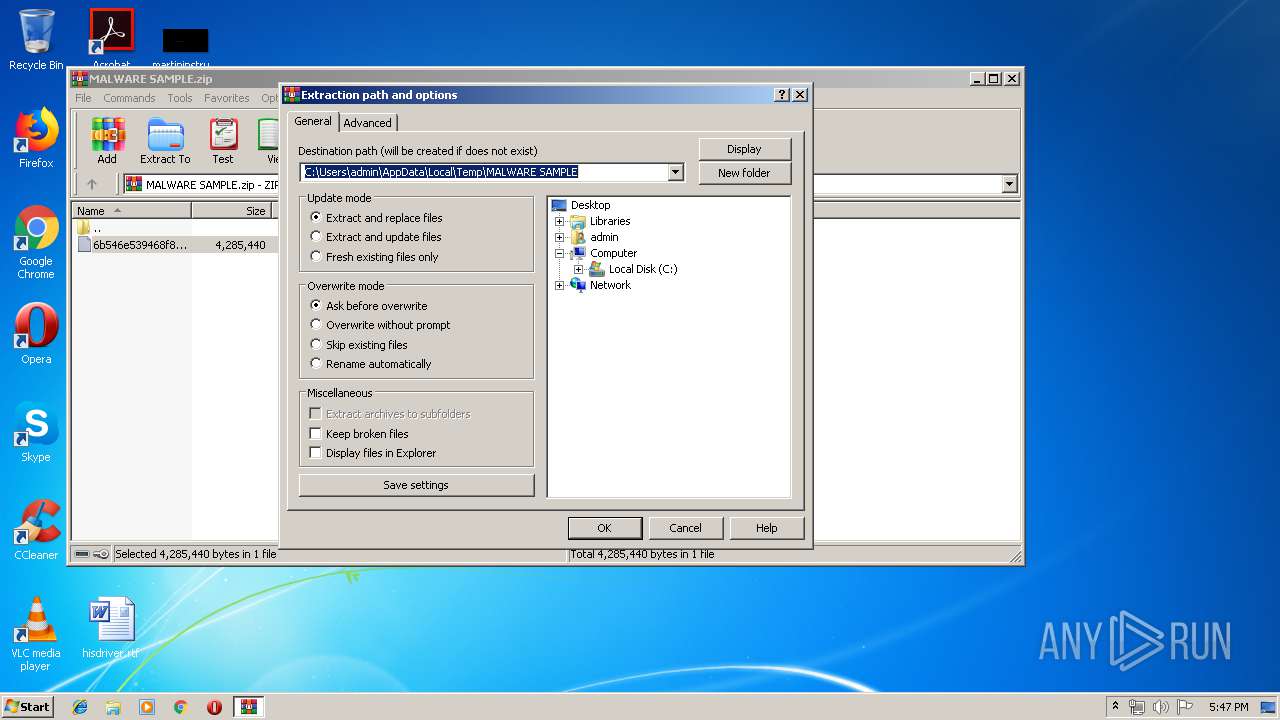
| 1020 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\MALWARE SAMPLE.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1696 | "C:\Users\admin\Desktop\calc.exe" | C:\Users\admin\Desktop\calc.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1888 | "C:\Users\admin\Desktop\calc.exe" | C:\Users\admin\Desktop\calc.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
774
Read events
763
Write events
11
Delete events
0
Modification events
| (PID) Process: | (1020) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1020) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1020) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1020) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\MALWARE SAMPLE.zip | |||
| (PID) Process: | (1020) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1020) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1020) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1020) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1020) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (1020) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
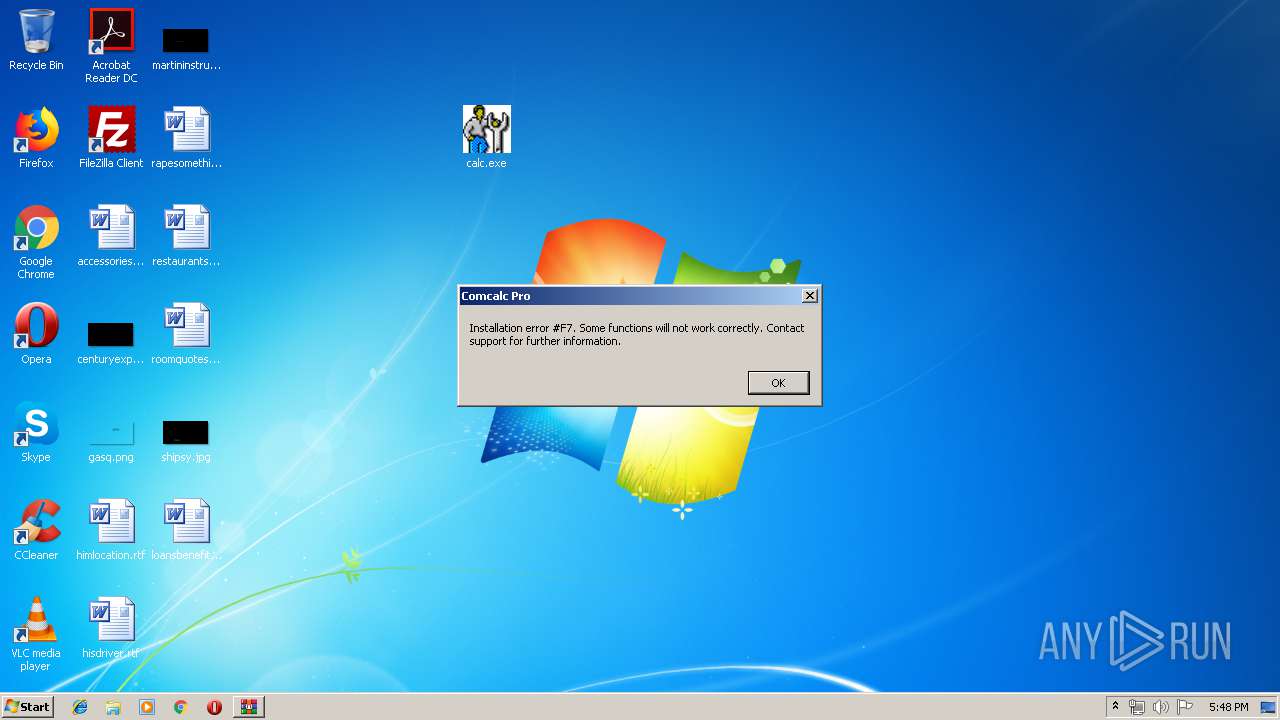
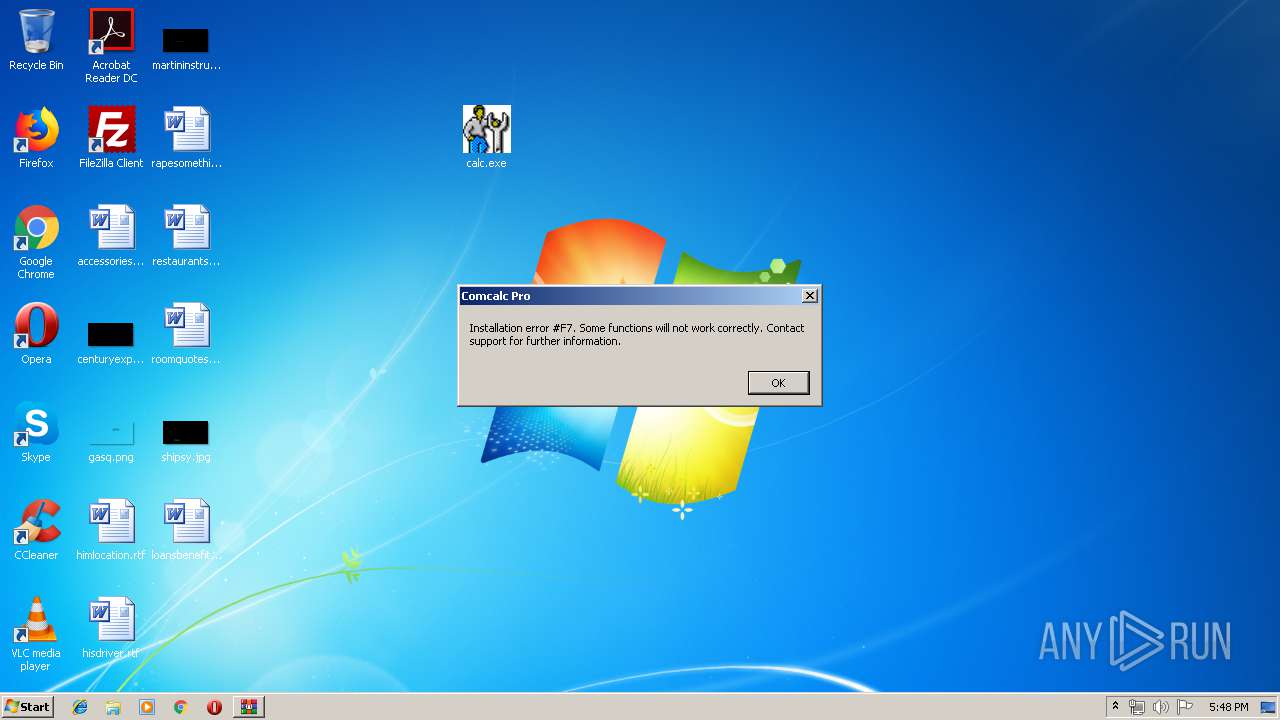
| 1696 | calc.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\SendTo\Comcalc Pro.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1888 | calc.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\SendTo\Comcalc Pro.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1020 | WinRAR.exe | C:\Users\admin\Desktop\6b546e539468f82c3d4f23f38b2fa9ab4c2b52b5a5973a19dfbef4f0cae9a923.bin | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
calc.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
calc.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|