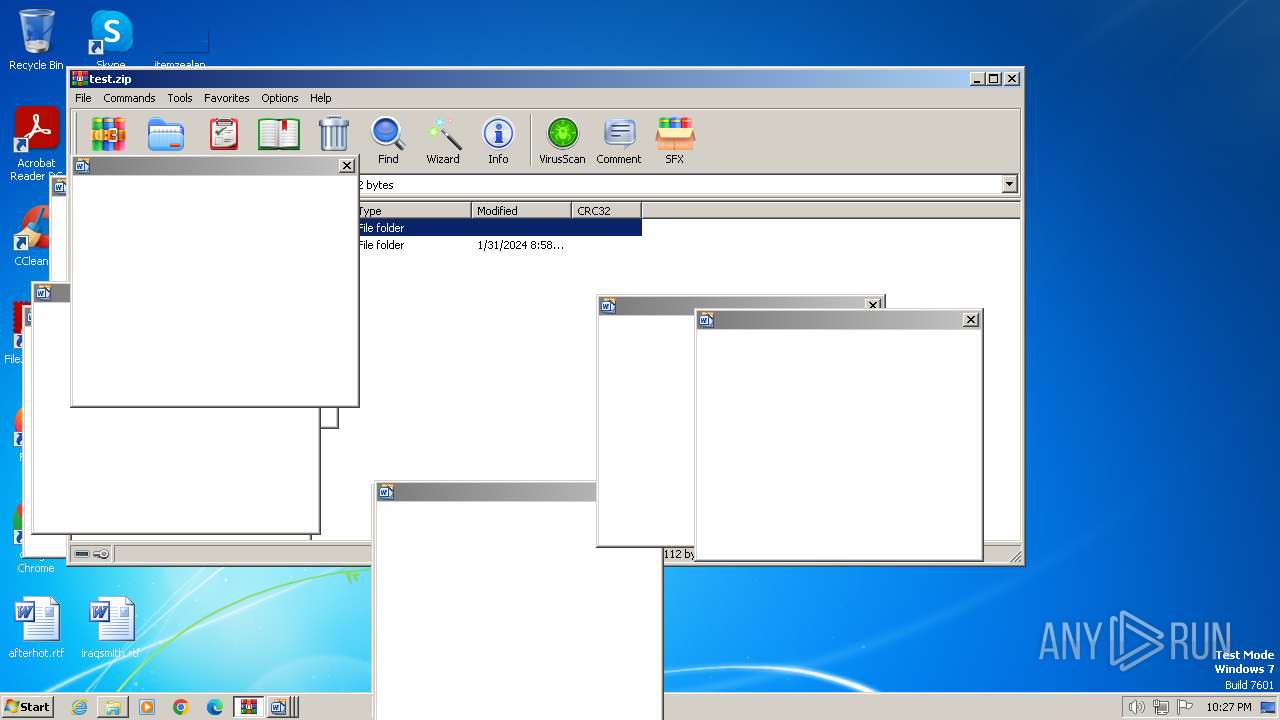
| File name: | test.zip |
| Full analysis: | https://app.any.run/tasks/6ed16bba-b345-4aca-bc6c-76ef10c33078 |
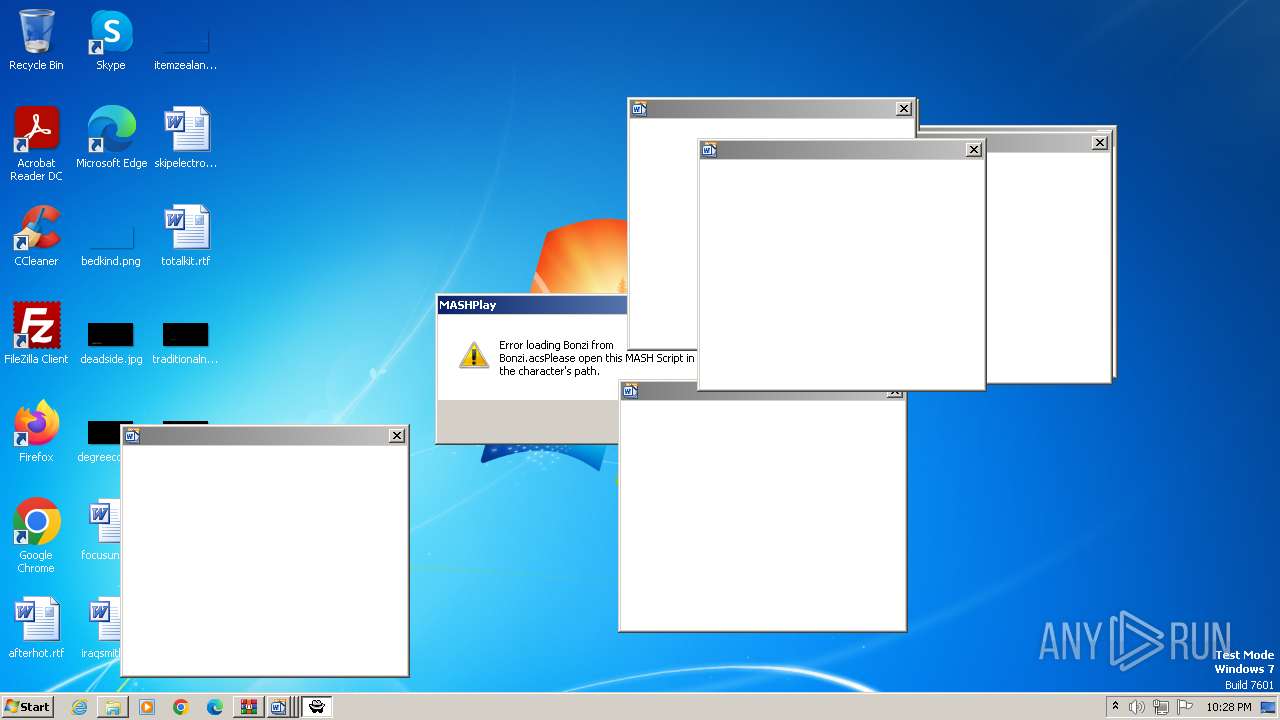
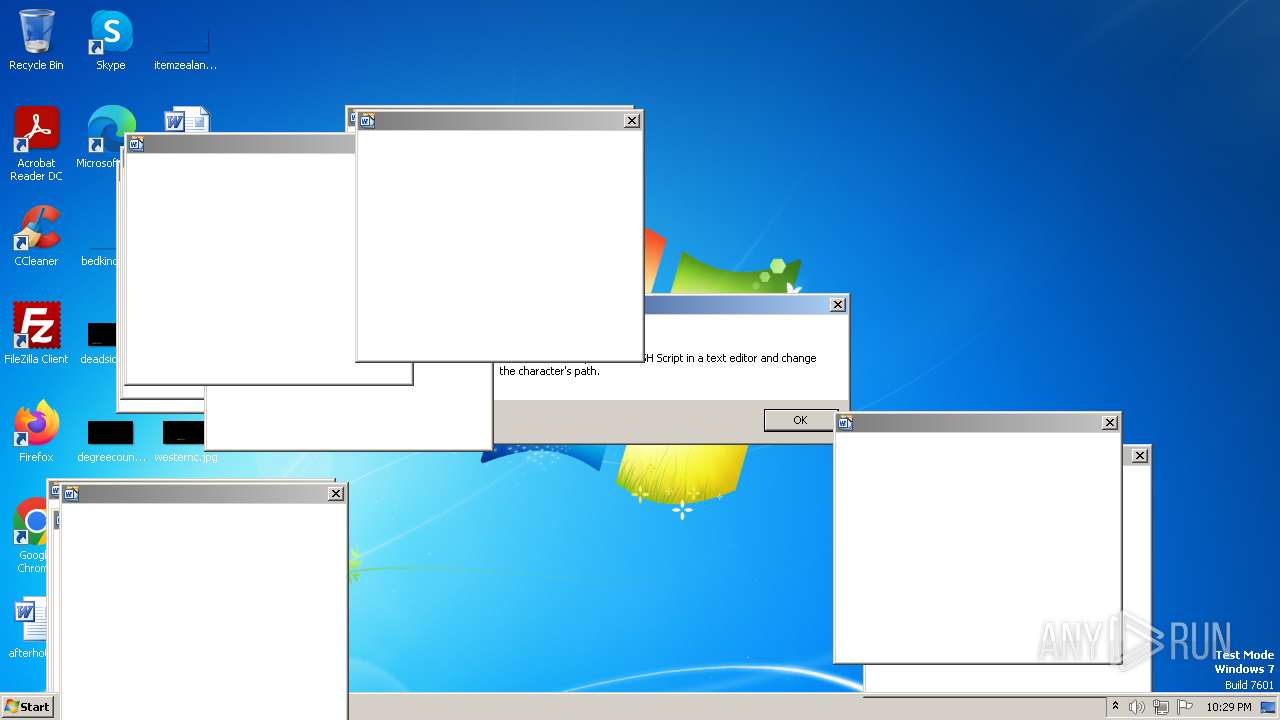
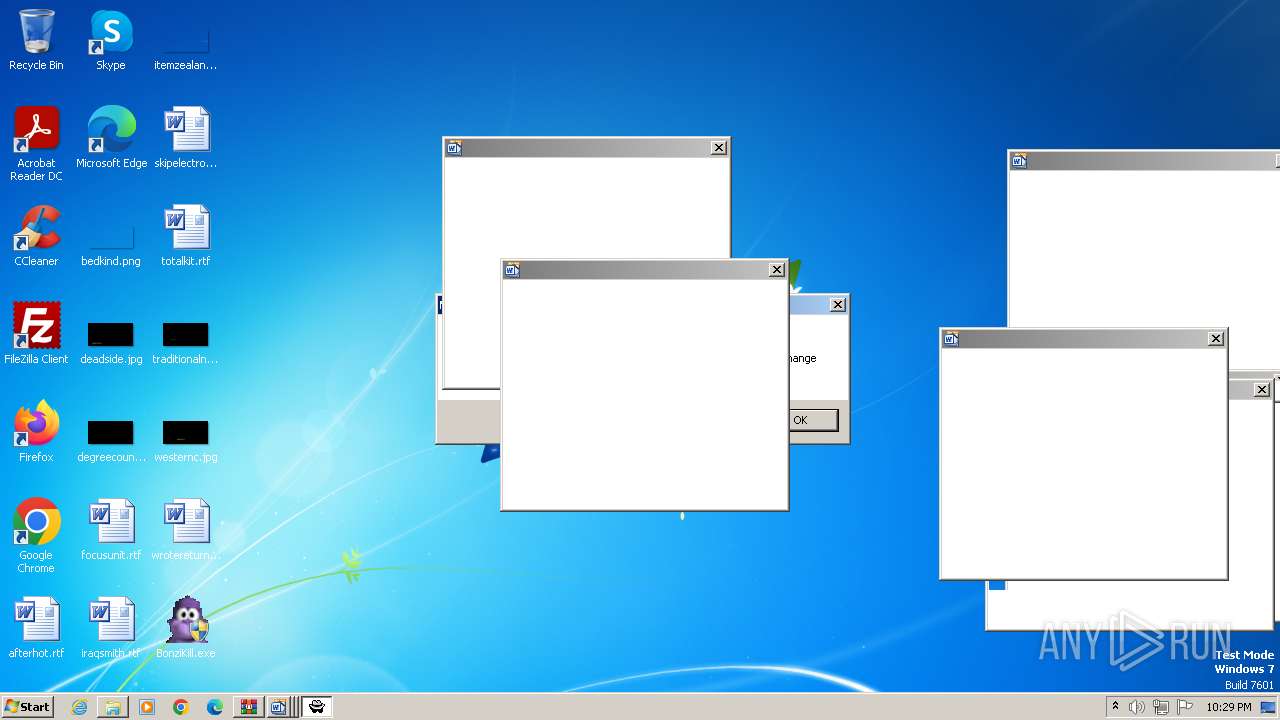
| Verdict: | Malicious activity |
| Analysis date: | January 31, 2024, 22:26:49 |
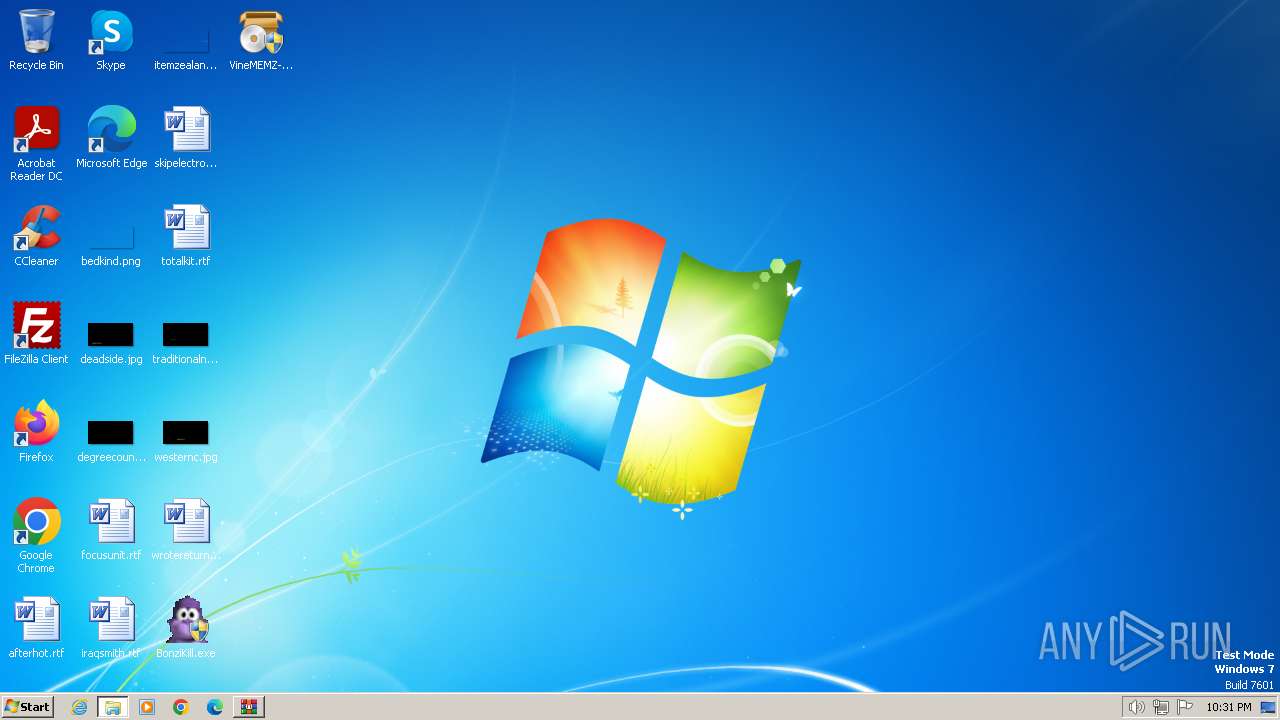
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v4.5 to extract |
| MD5: | 0D28DD96DF2F54848DE627D81BF3404D |
| SHA1: | 66E9B0E1D0F33FB8690774E019F63E66BDB31757 |
| SHA256: | 59423795B41F8E42B60B6B4CA3703EA60A4593E4F15513419F48416ED4EF6092 |
| SSDEEP: | 3072:8nP8SvGoatO8tCO93PGfGE9+eVBwap9ElnZKokCFb1bio9DVpl46CezJbsaR38M+:kkSvGo4O84Q3uNM0BZ9Eln8o/1plC8dq |
MALICIOUS
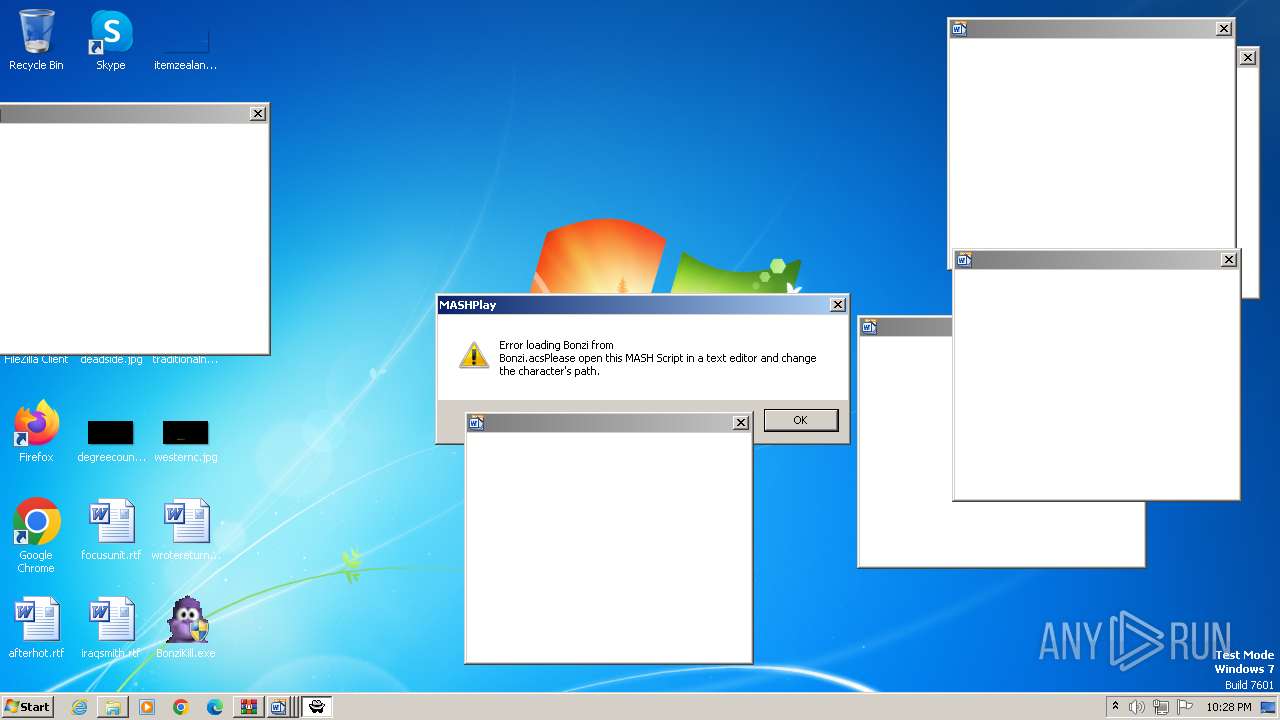
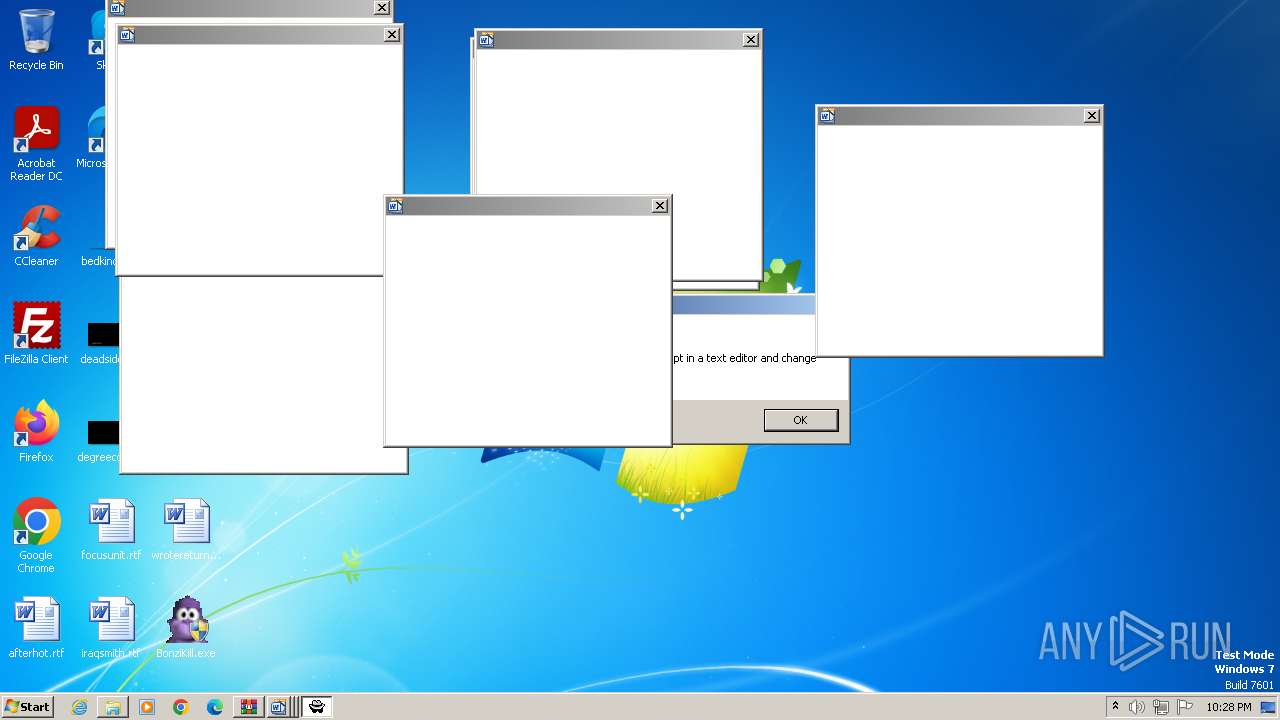
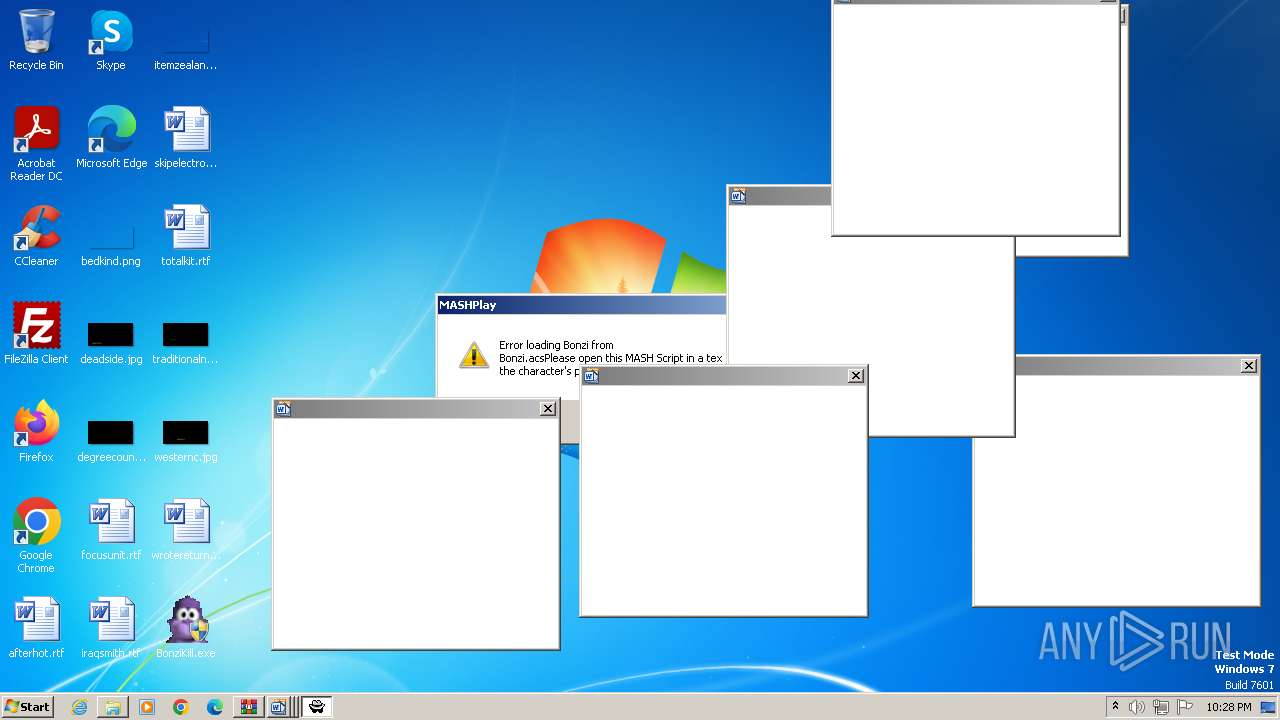
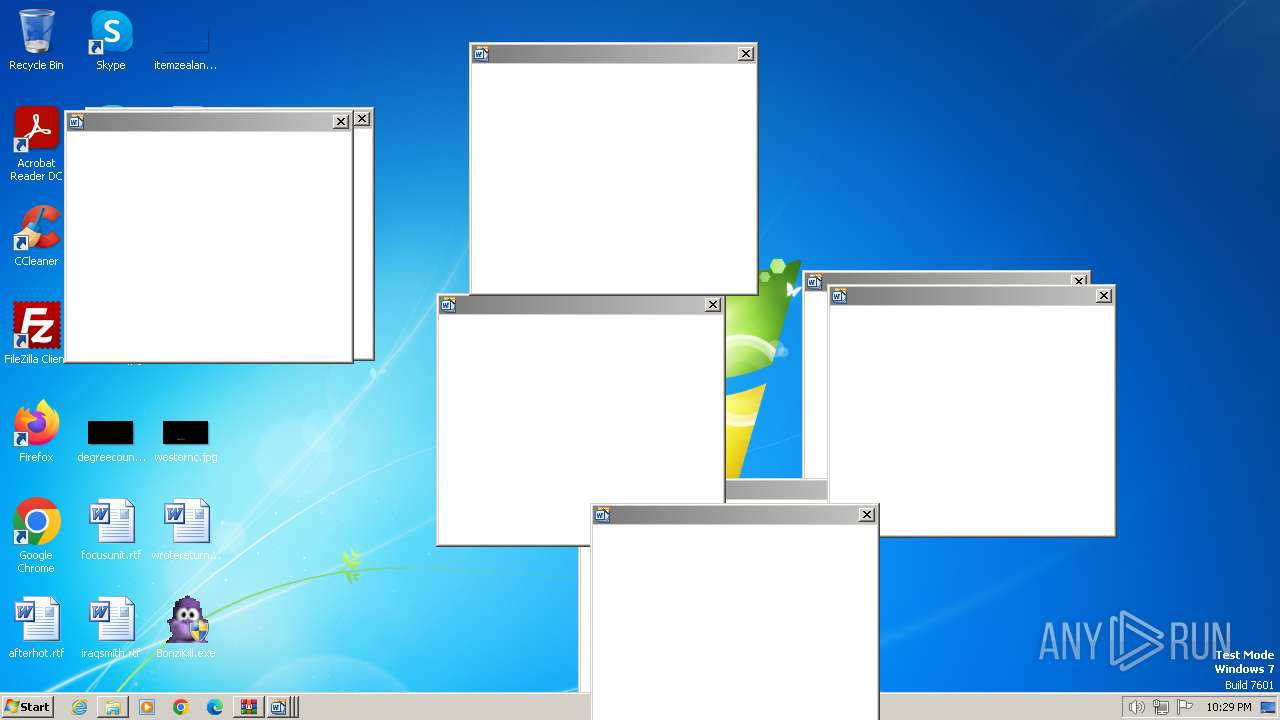
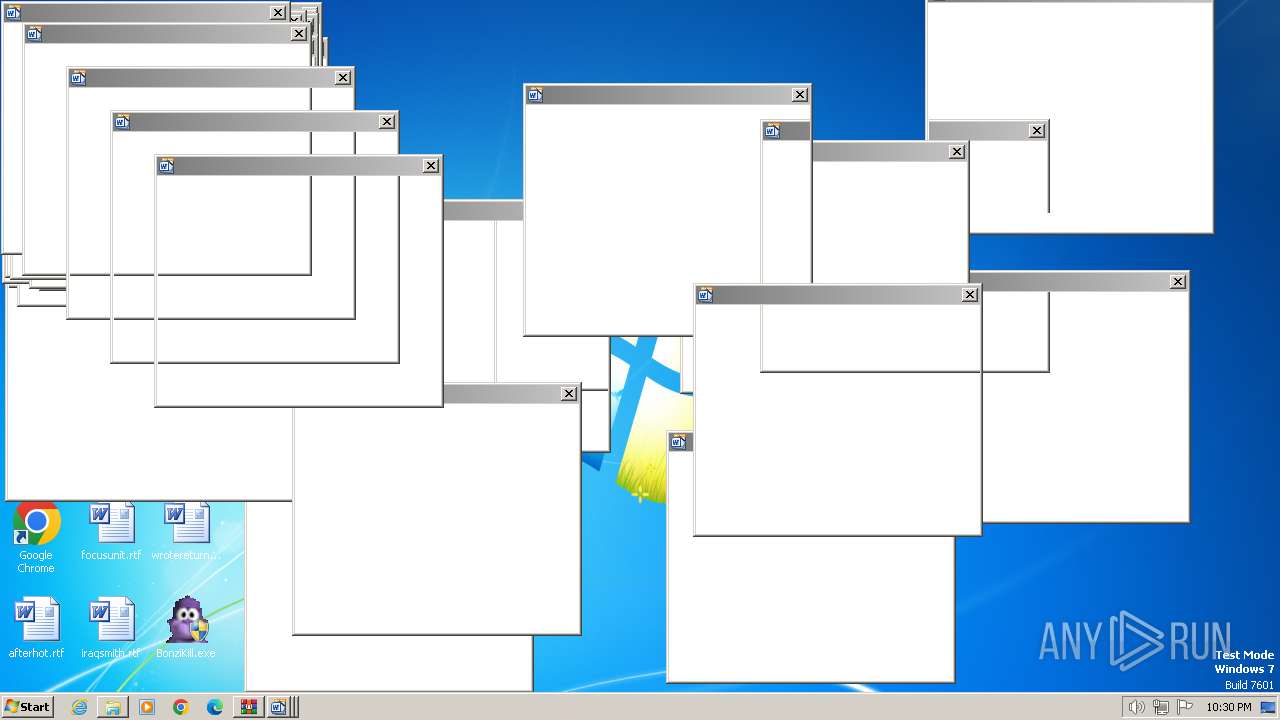
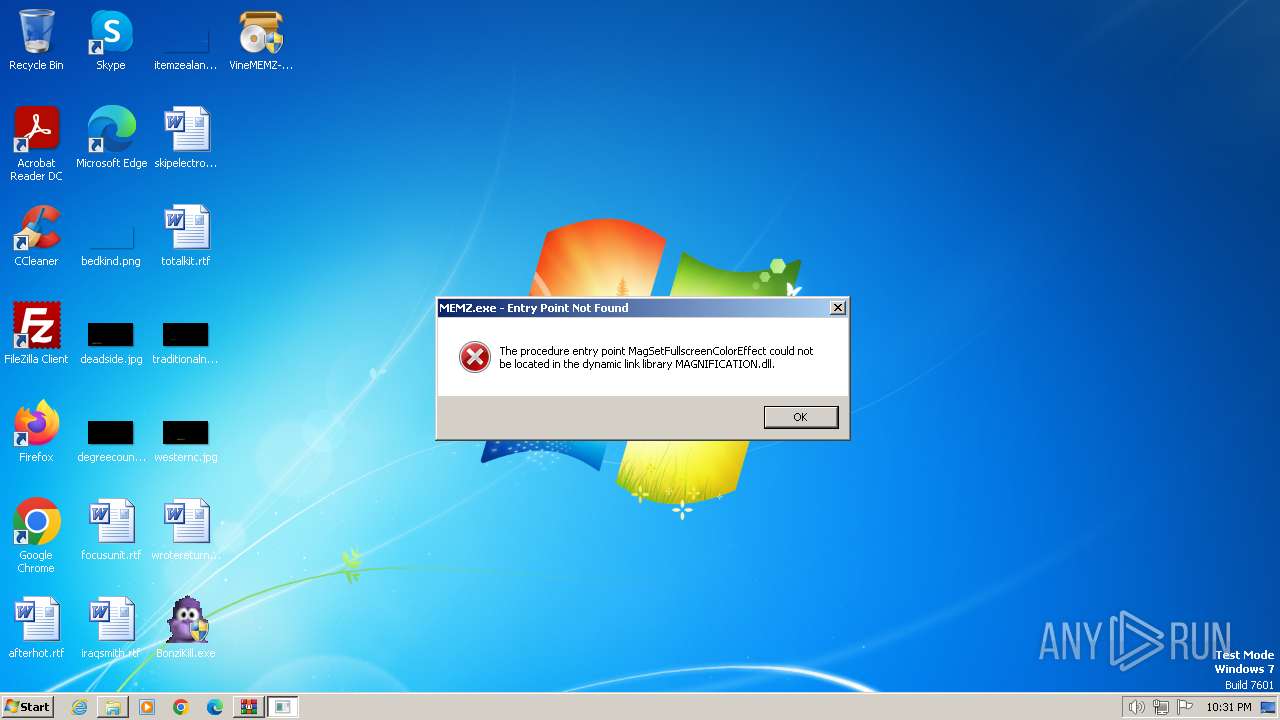
Drops the executable file immediately after the start
- WinRAR.exe (PID: 1380)
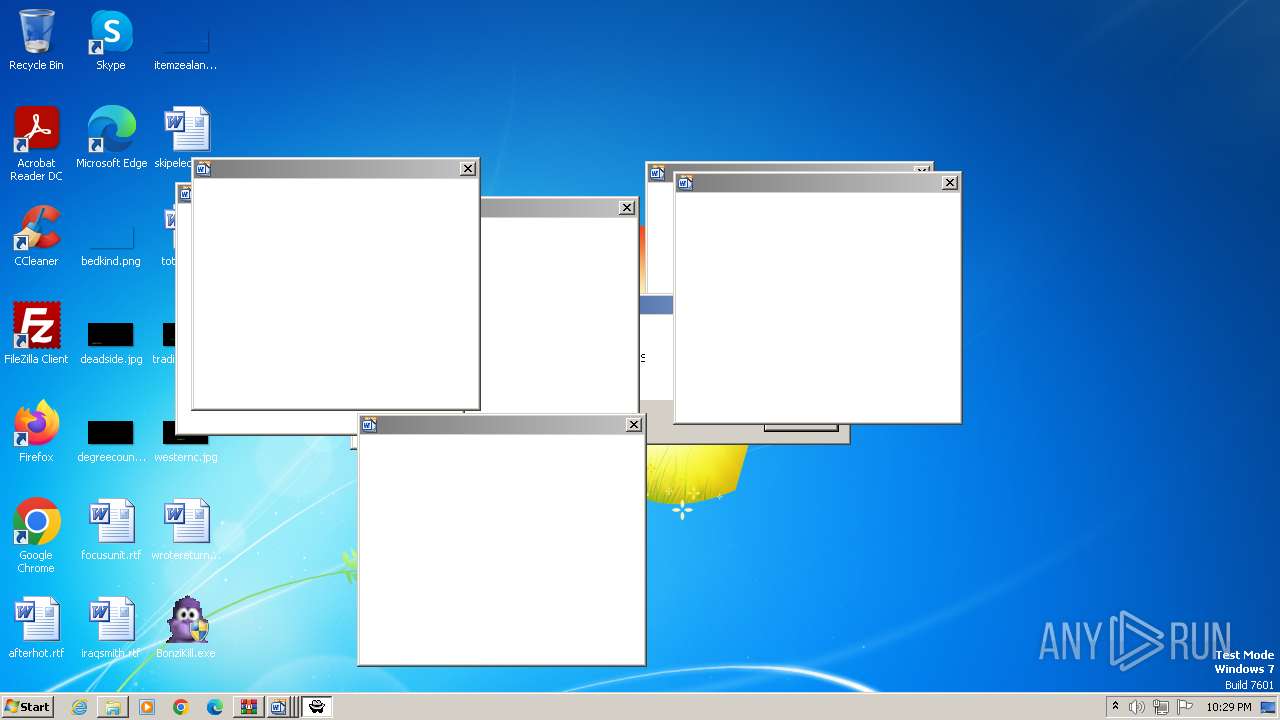
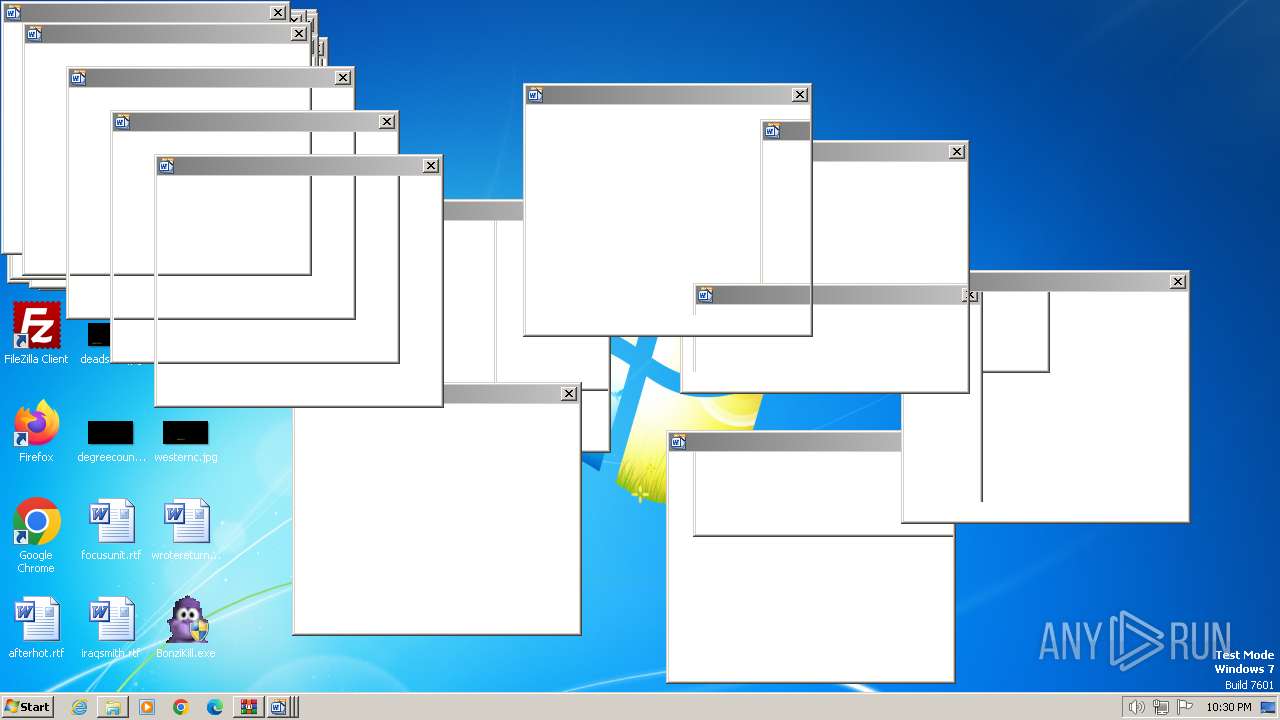
- BonziKill.exe (PID: 4032)
- BonziKill.exe (PID: 3008)
- BonziKill.exe (PID: 3500)
- BonziKill.exe (PID: 4668)
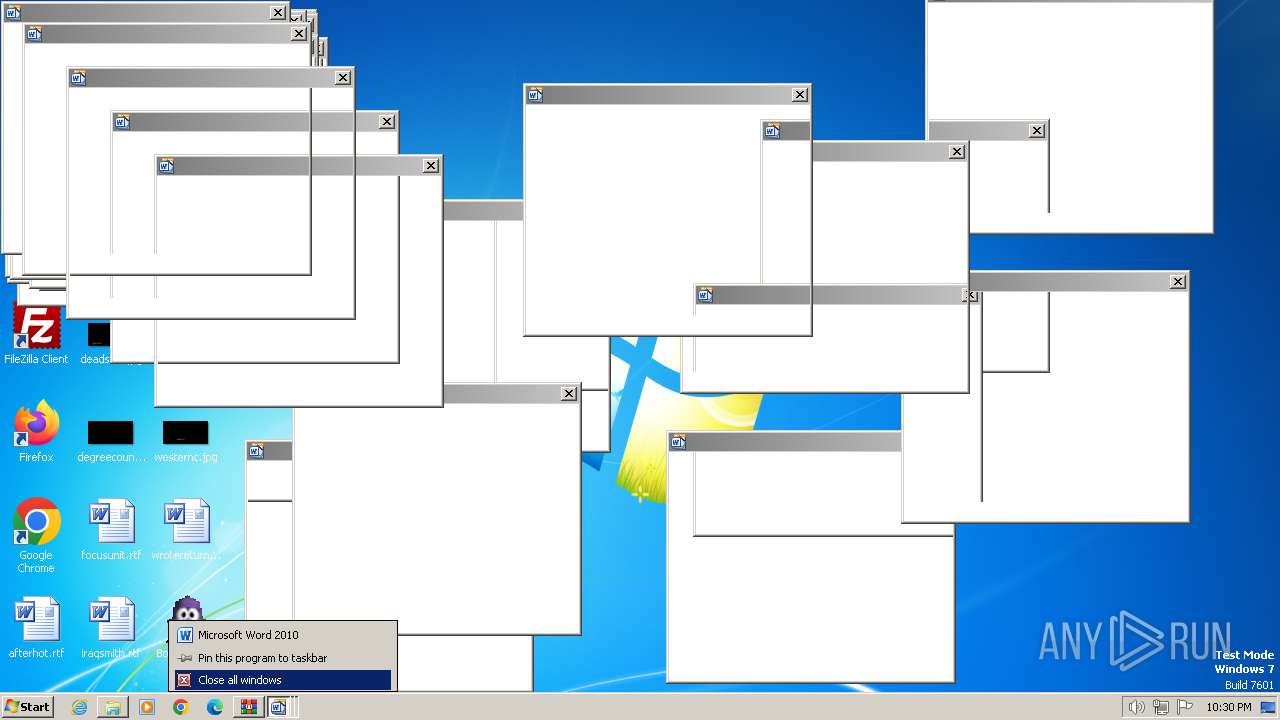
- VineMEMZ-Original.exe (PID: 4964)
SUSPICIOUS
Reads settings of System Certificates
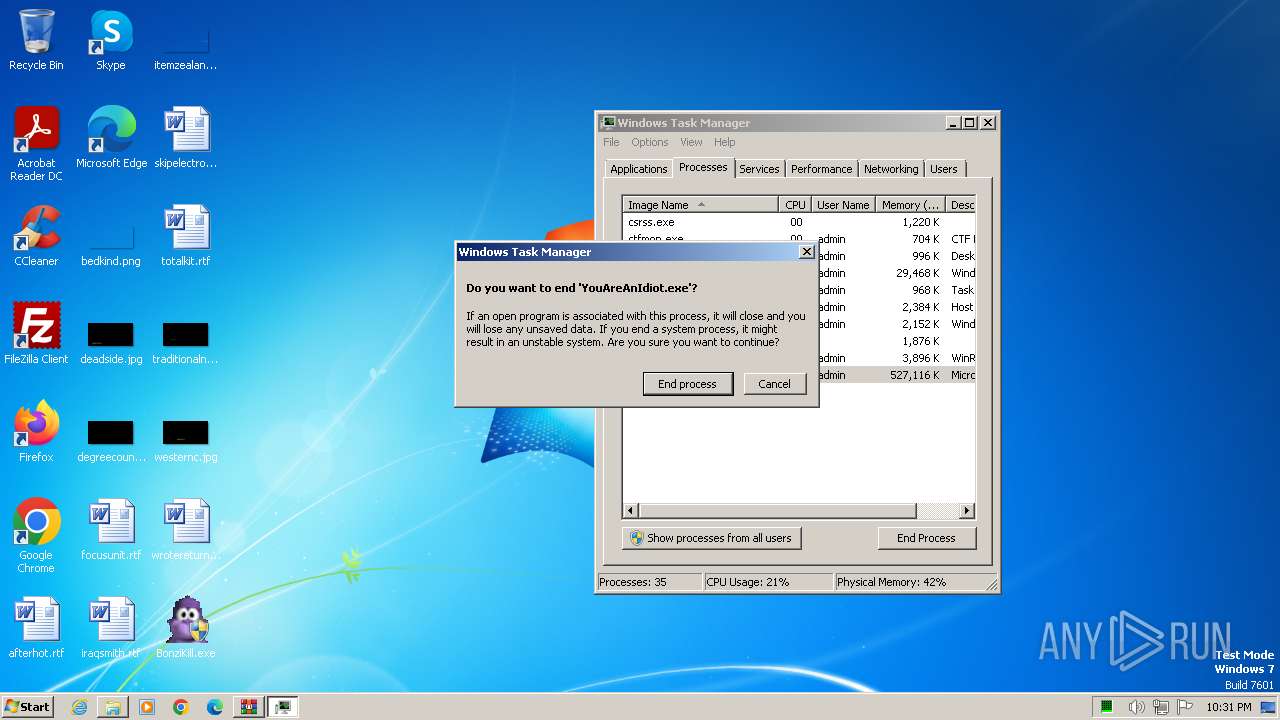
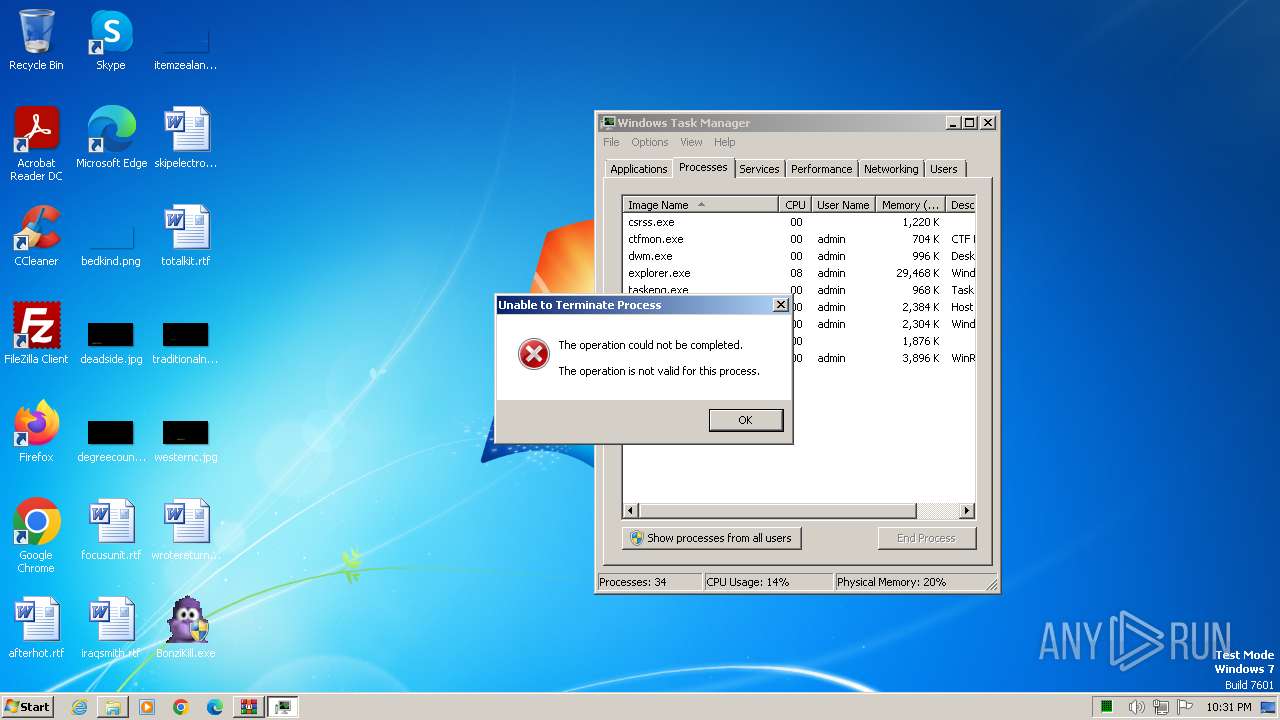
- YouAreAnIdiot.exe (PID: 3248)
Executable content was dropped or overwritten
- BonziKill.exe (PID: 4032)
- BonziKill.exe (PID: 3008)
- BonziKill.exe (PID: 3500)
- BonziKill.exe (PID: 4668)
- VineMEMZ-Original.exe (PID: 4964)
The process drops C-runtime libraries
- BonziKill.exe (PID: 4032)
- BonziKill.exe (PID: 3008)
- BonziKill.exe (PID: 3500)
- BonziKill.exe (PID: 4668)
Process drops legitimate windows executable
- BonziKill.exe (PID: 4032)
- BonziKill.exe (PID: 3008)
- BonziKill.exe (PID: 3500)
- BonziKill.exe (PID: 4668)
Reads the Internet Settings
- BonziKill.exe (PID: 4032)
- BonziKill.exe (PID: 3008)
- BonziKill.exe (PID: 3500)
INFO
Checks supported languages
- YouAreAnIdiot.exe (PID: 3248)
- BonziKill.exe (PID: 4032)
- BonziBuddy_original.exe (PID: 3876)
- BonziKill.exe (PID: 3008)
- BonziBuddy_original.exe (PID: 3796)
- BonziKill.exe (PID: 3500)
- BonziBuddy_original.exe (PID: 3936)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1380)
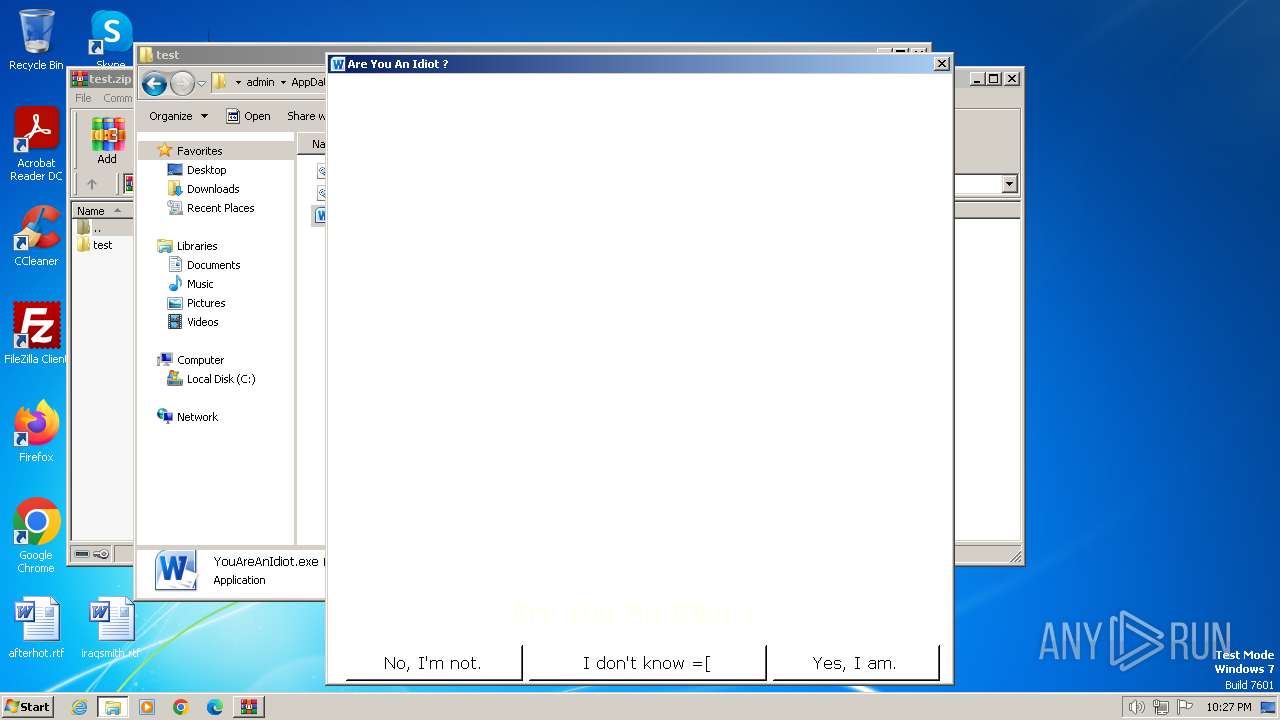
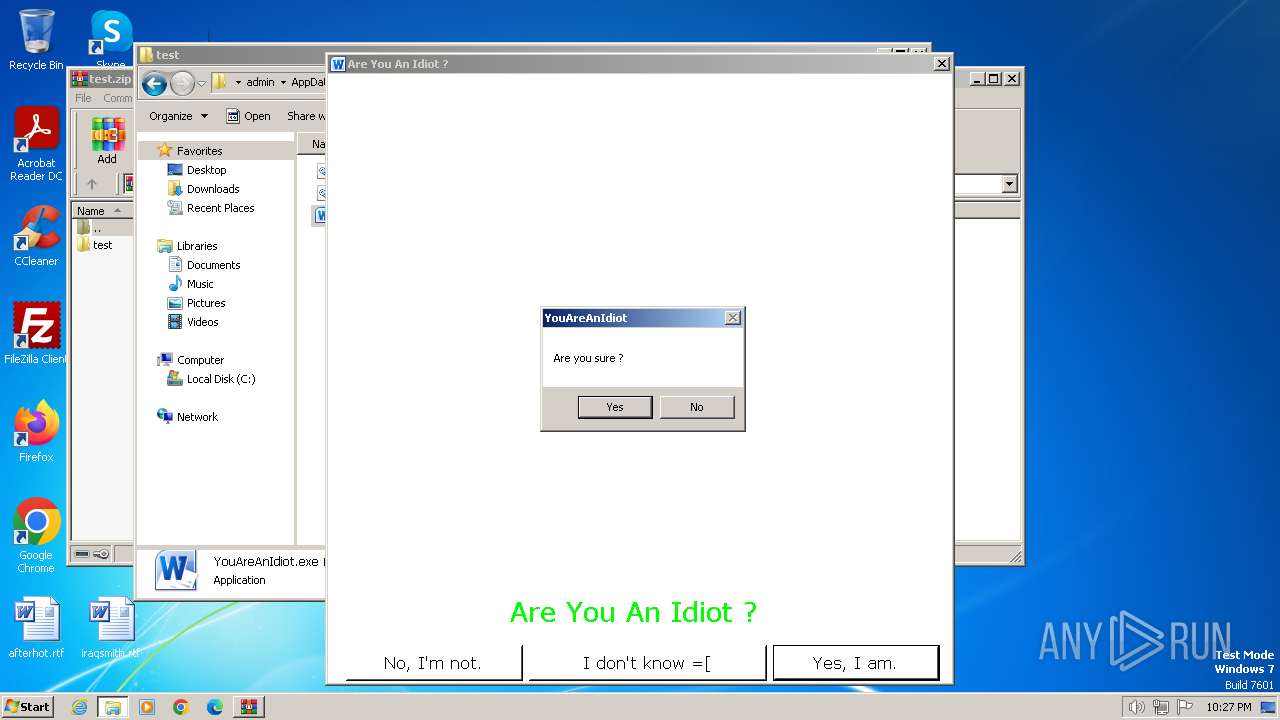
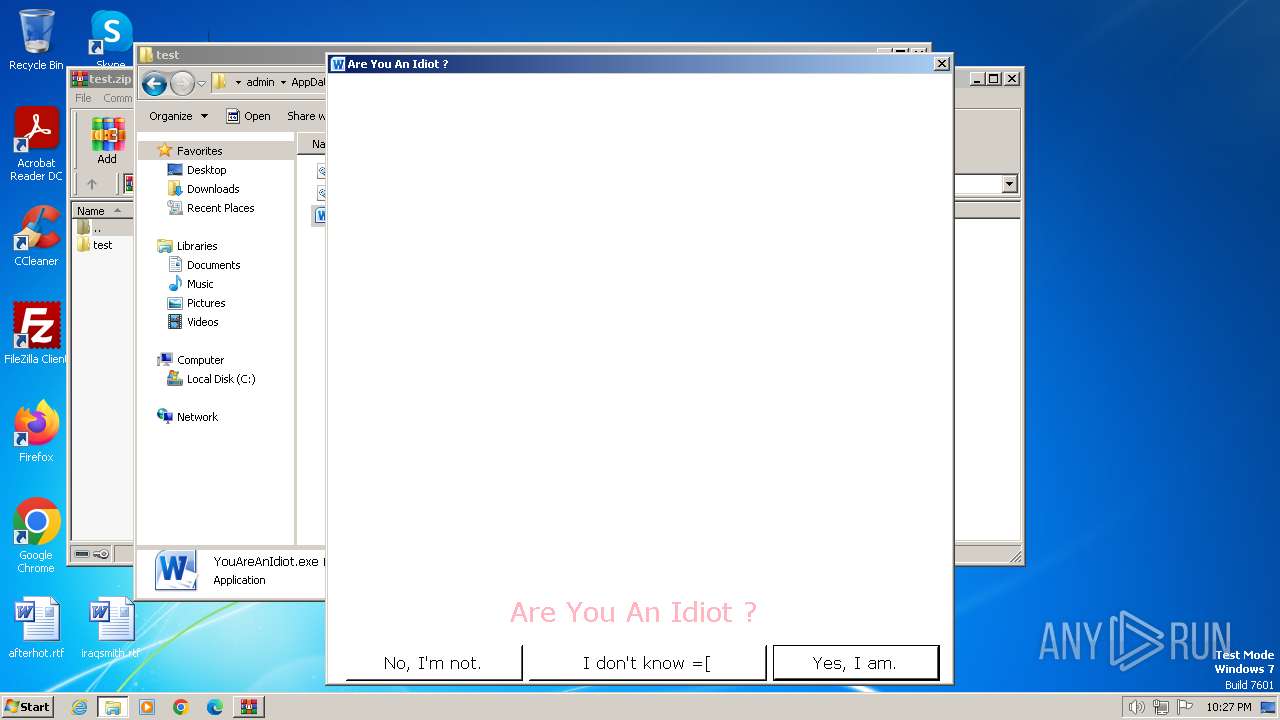
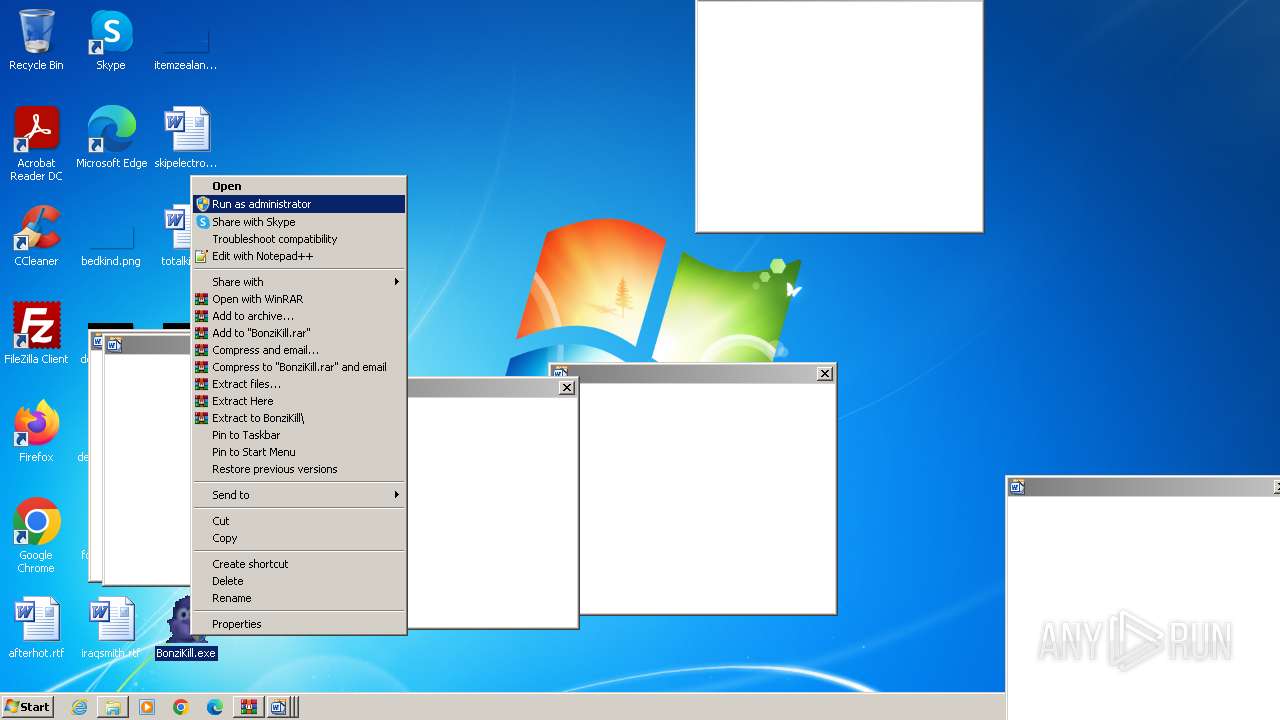
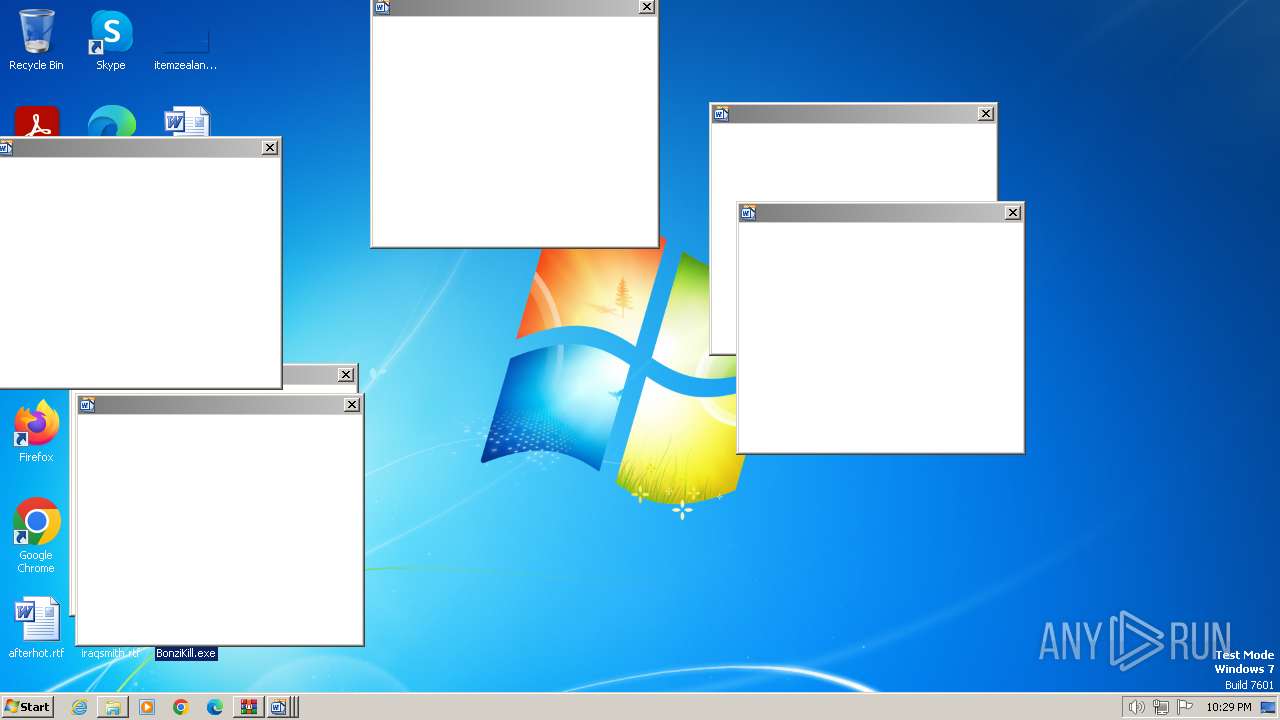
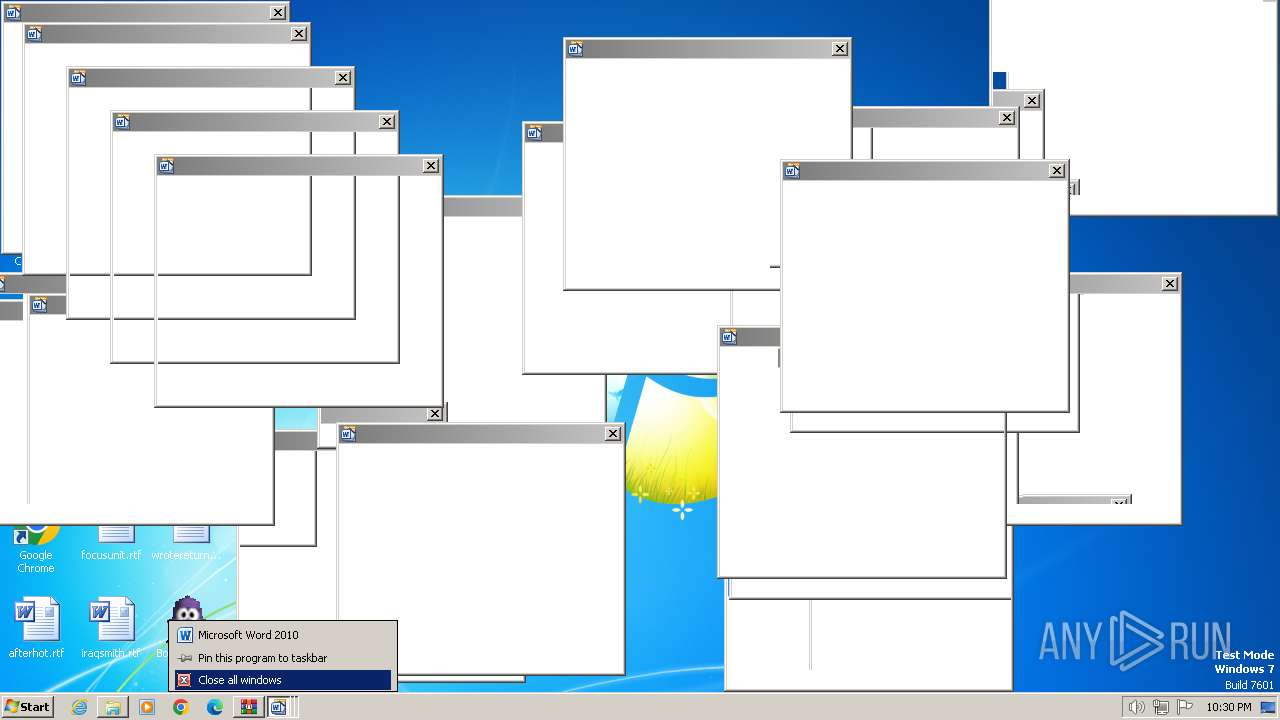
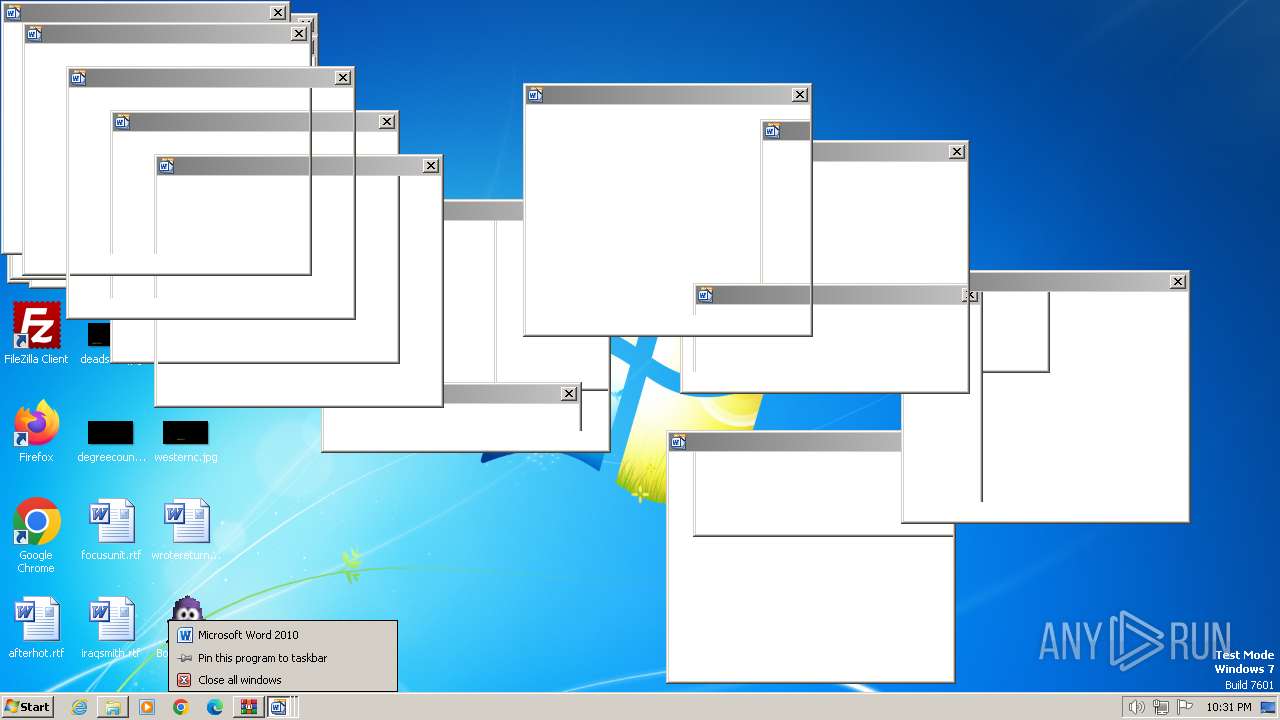
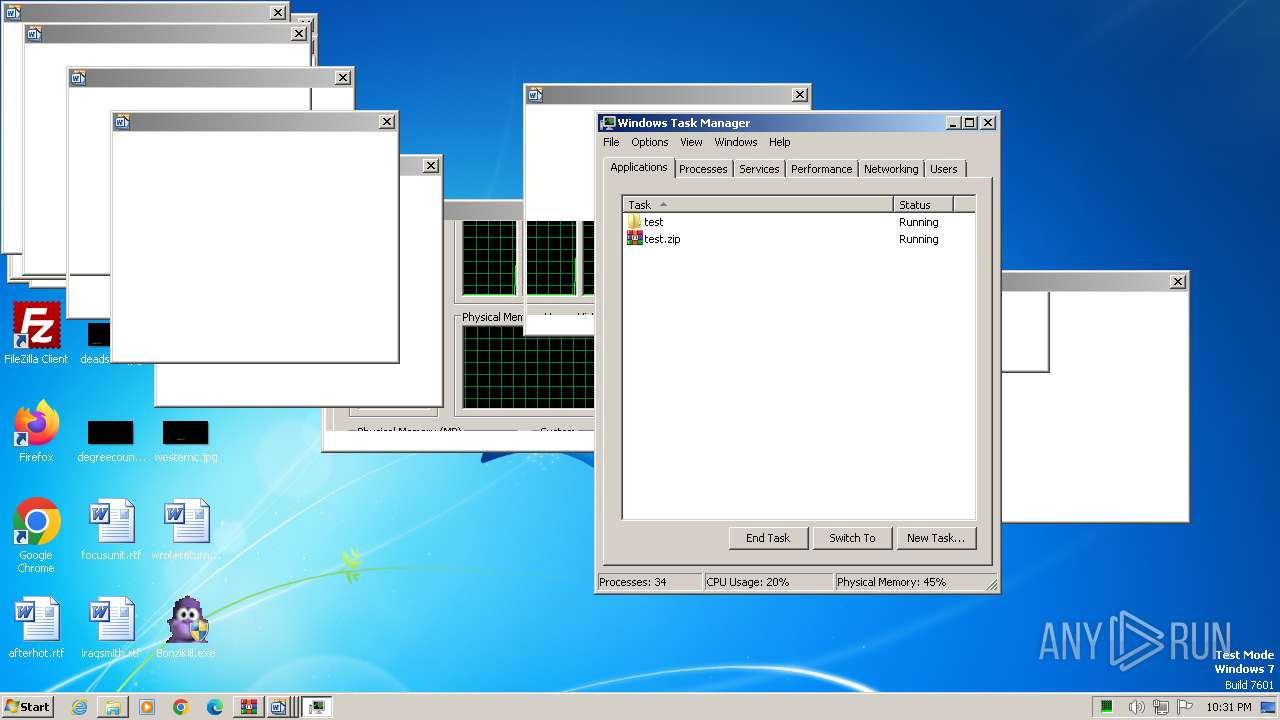
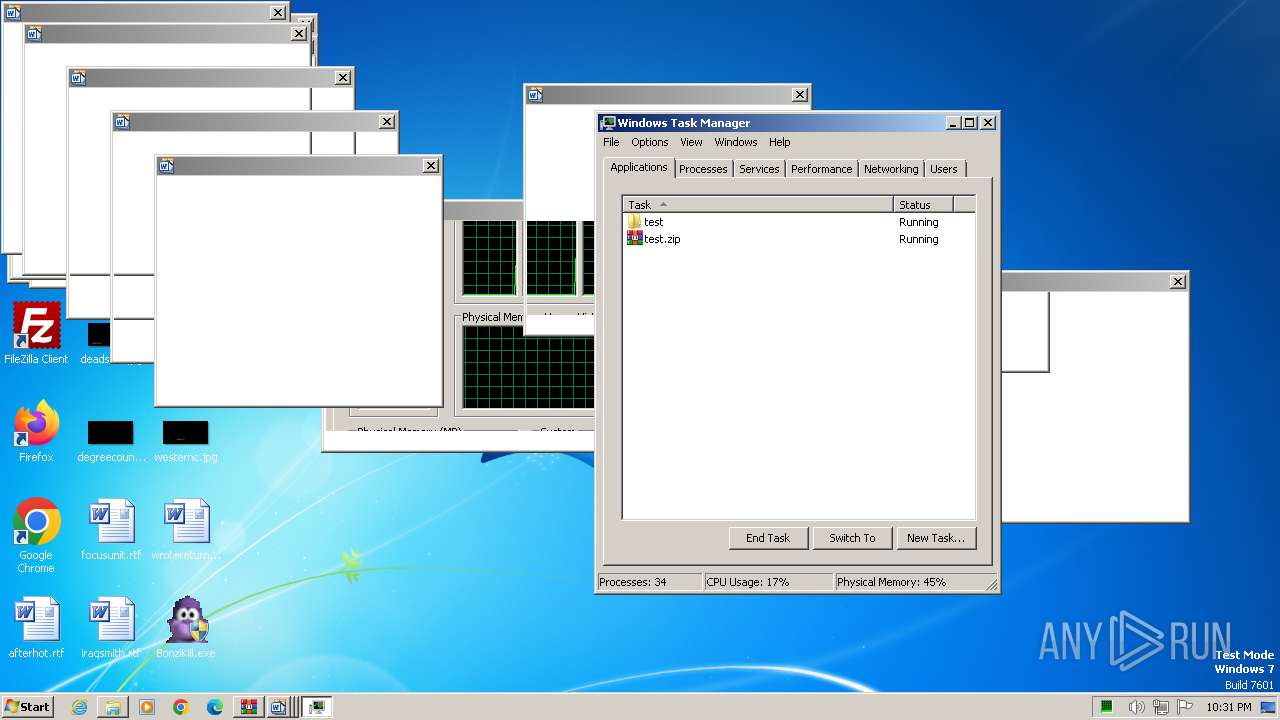
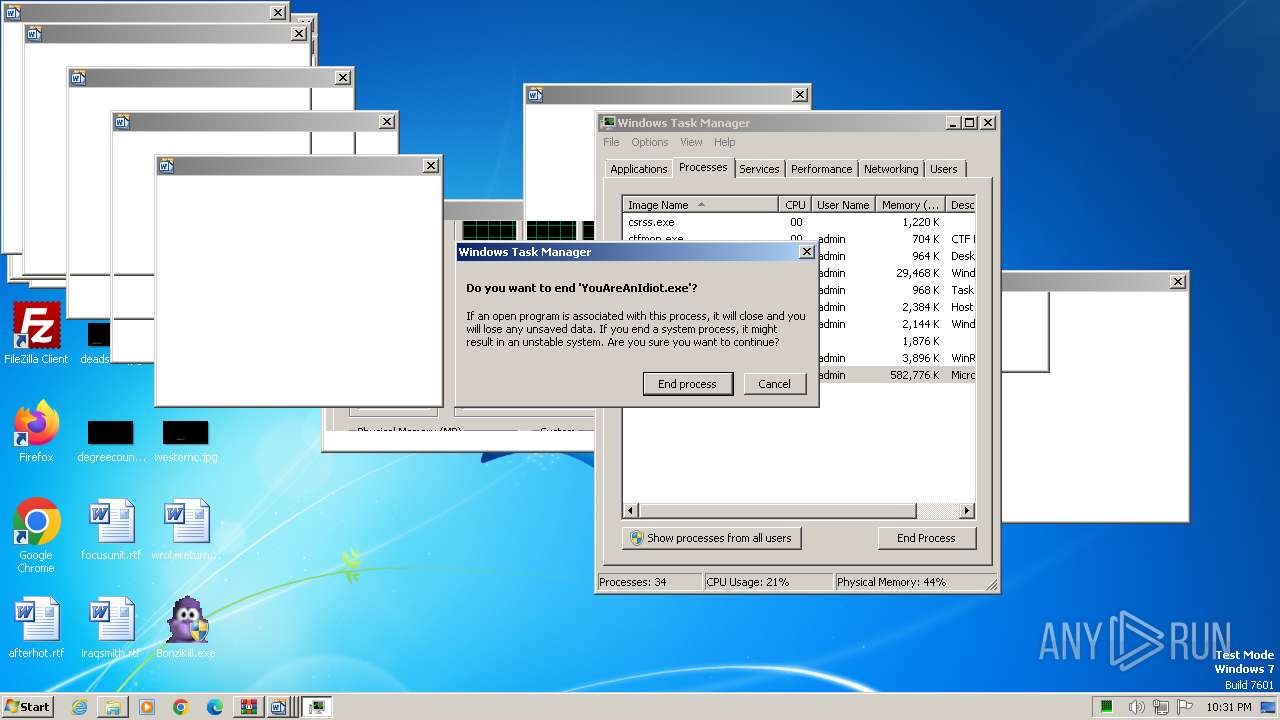
Manual execution by a user
- YouAreAnIdiot.exe (PID: 3248)
- BonziKill.exe (PID: 3632)
- BonziKill.exe (PID: 4032)
- BonziKill.exe (PID: 3008)
- BonziKill.exe (PID: 3500)
- BonziKill.exe (PID: 4552)
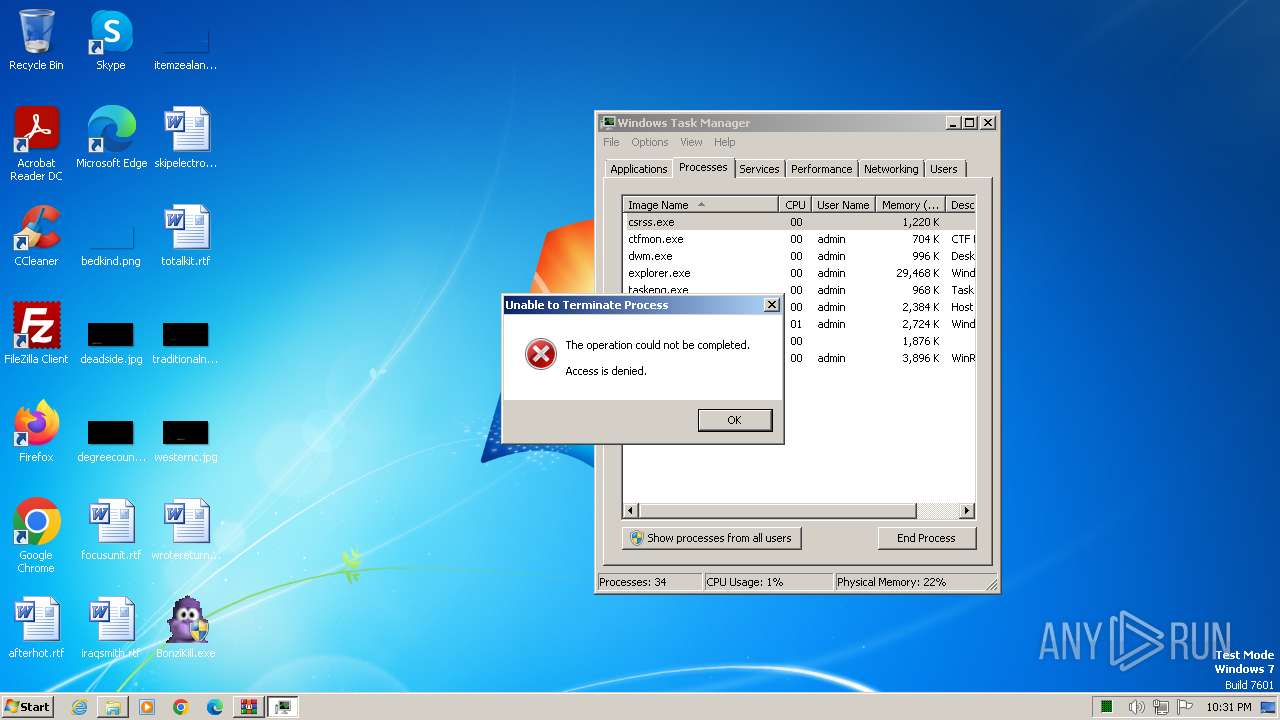
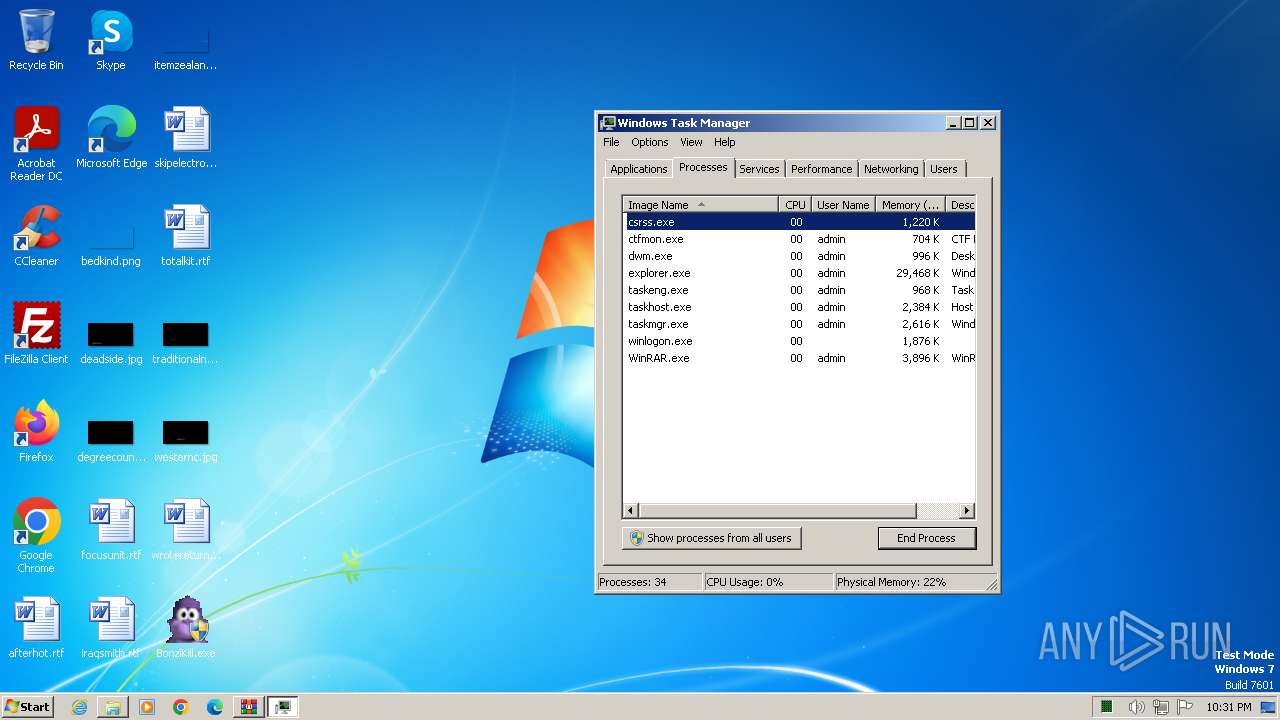
- taskmgr.exe (PID: 4196)
- BonziKill.exe (PID: 4668)
- VineMEMZ-Original.exe (PID: 4964)
- VineMEMZ-Original.exe (PID: 4864)
Reads the computer name
- YouAreAnIdiot.exe (PID: 3248)
- BonziKill.exe (PID: 4032)
- BonziBuddy_original.exe (PID: 3876)
- BonziKill.exe (PID: 3008)
- BonziBuddy_original.exe (PID: 3796)
- BonziKill.exe (PID: 3500)
- BonziBuddy_original.exe (PID: 3936)
Reads CPU info
- YouAreAnIdiot.exe (PID: 3248)
Reads the machine GUID from the registry
- YouAreAnIdiot.exe (PID: 3248)
- BonziBuddy_original.exe (PID: 3876)
- BonziBuddy_original.exe (PID: 3796)
- BonziBuddy_original.exe (PID: 3936)
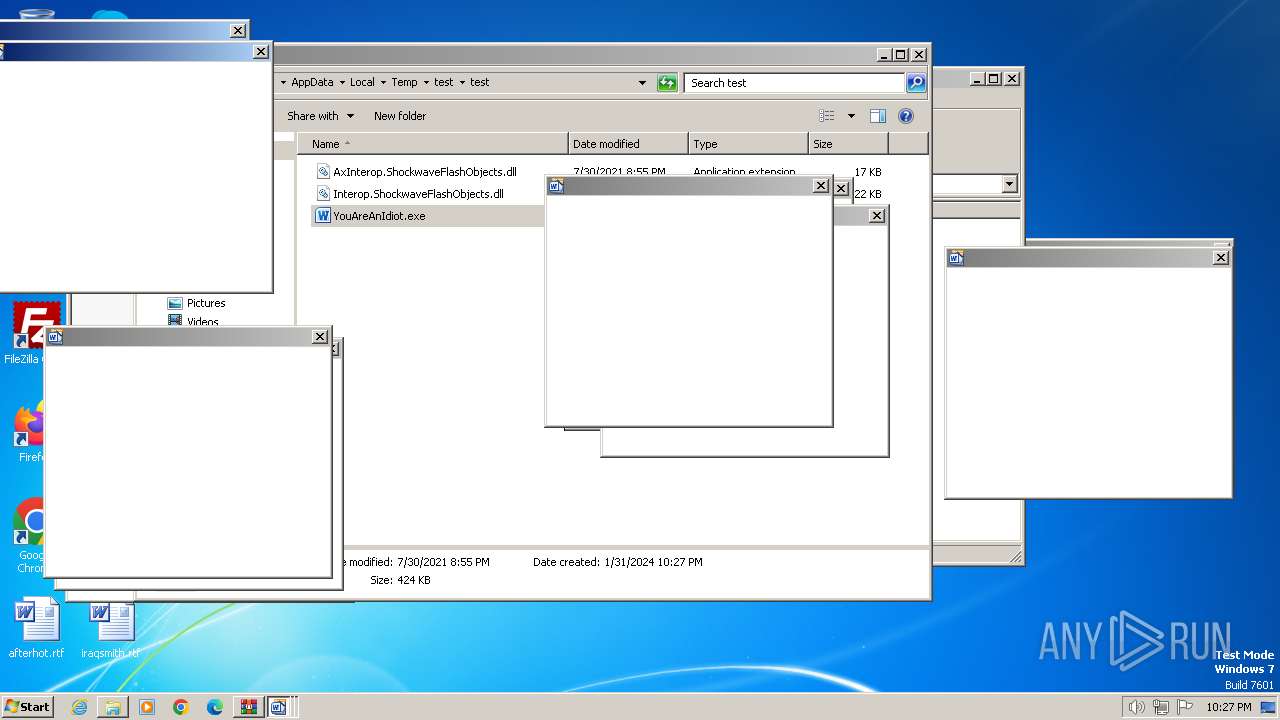
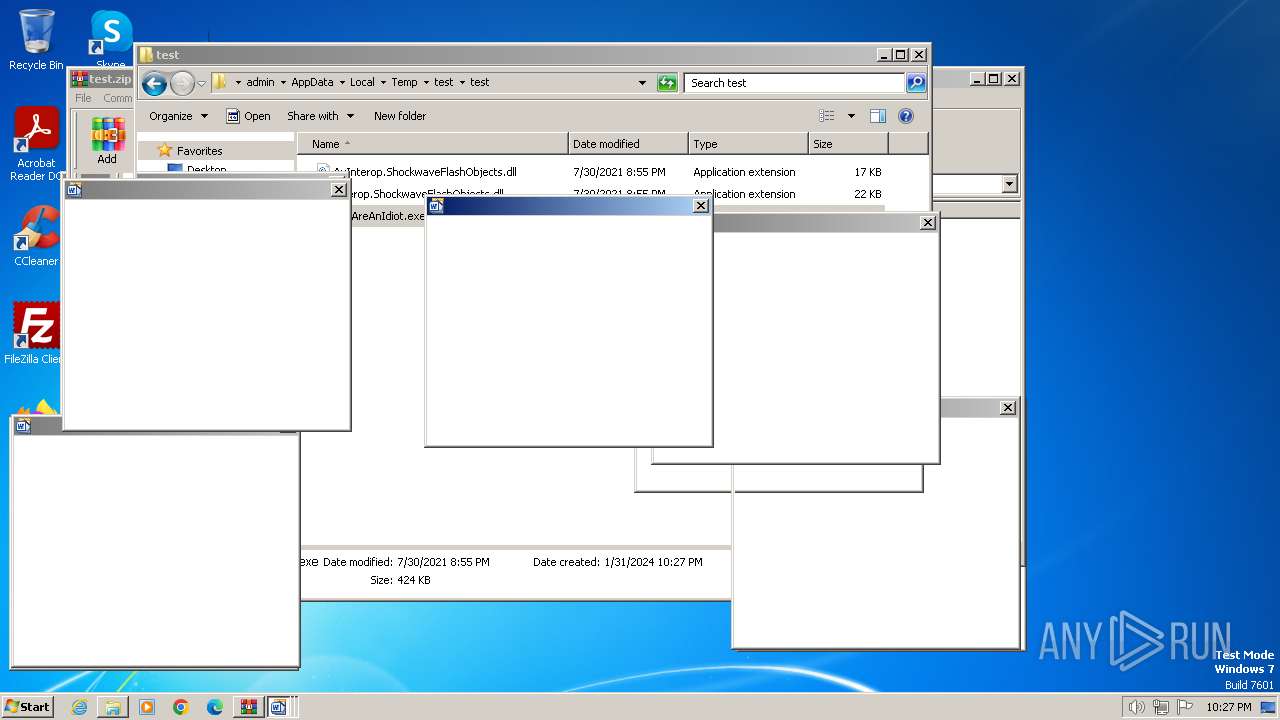
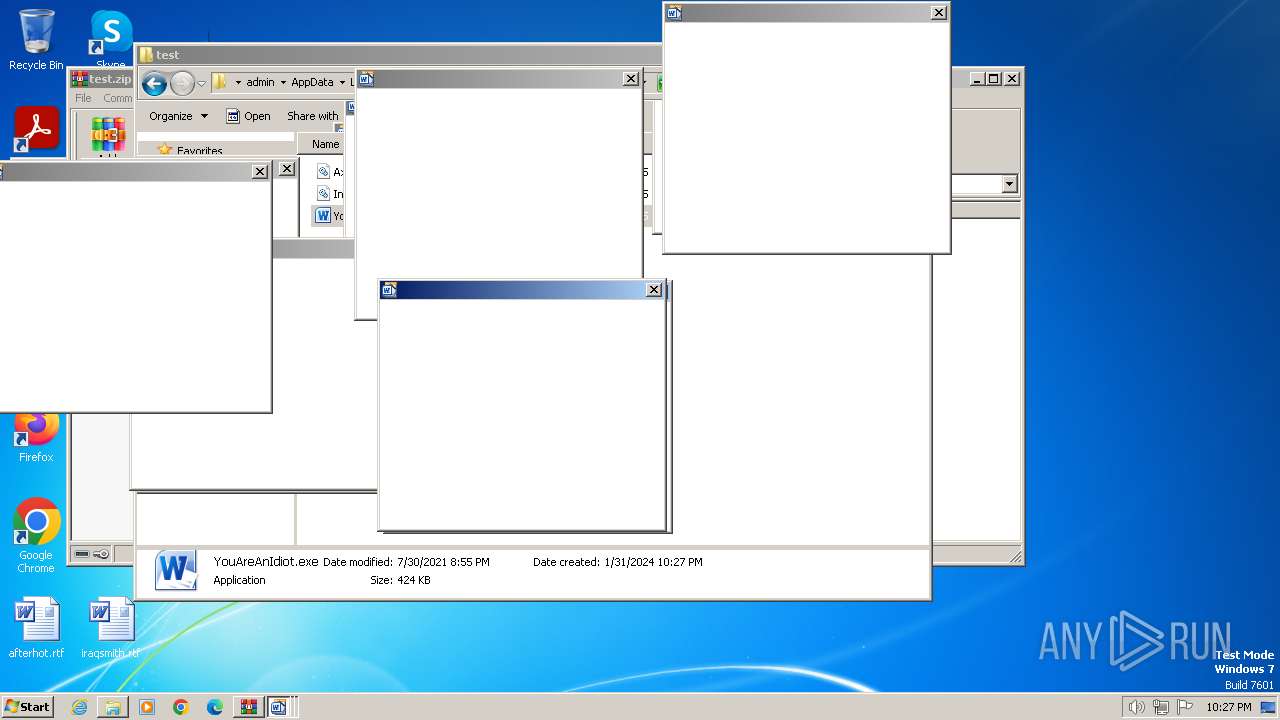
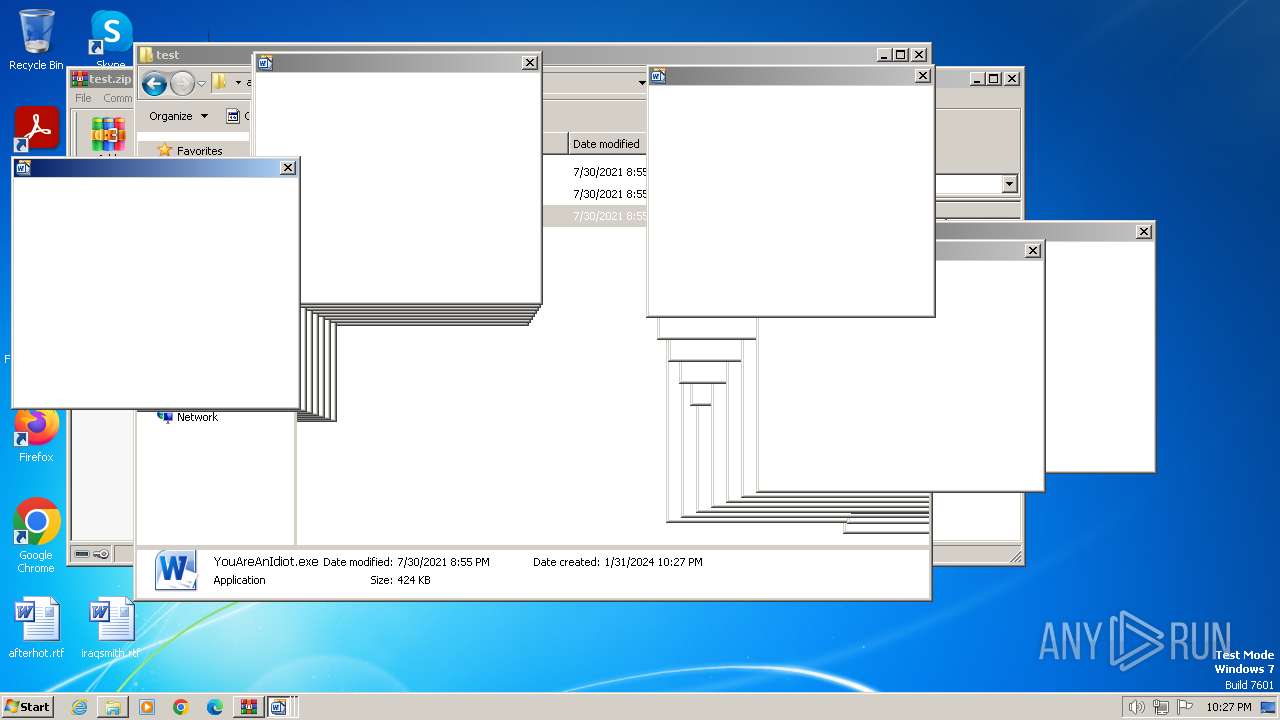
Creates files or folders in the user directory
- YouAreAnIdiot.exe (PID: 3248)
Create files in a temporary directory
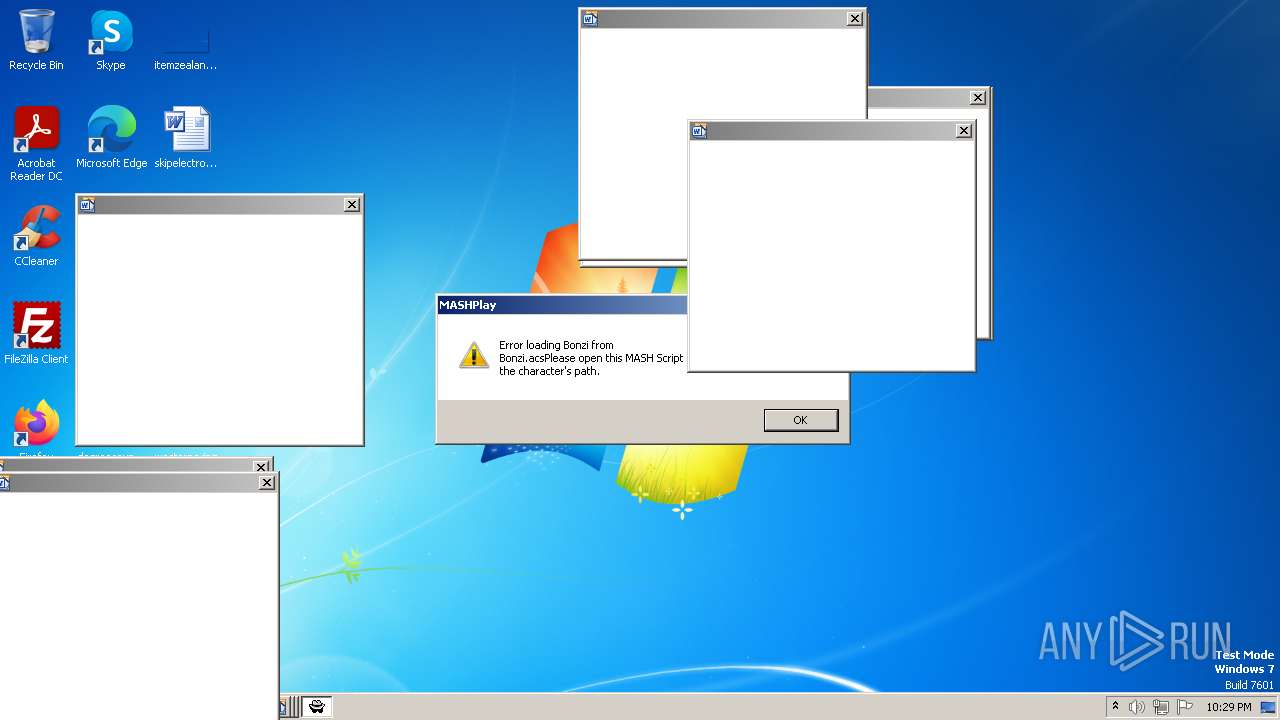
- BonziBuddy_original.exe (PID: 3876)
- BonziBuddy_original.exe (PID: 3796)
- BonziBuddy_original.exe (PID: 3936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 45 |
|---|---|
| ZipBitFlag: | 0x0800 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:01:31 20:58:12 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 2 |
| ZipUncompressedSize: | - |
| ZipFileName: | test/ |
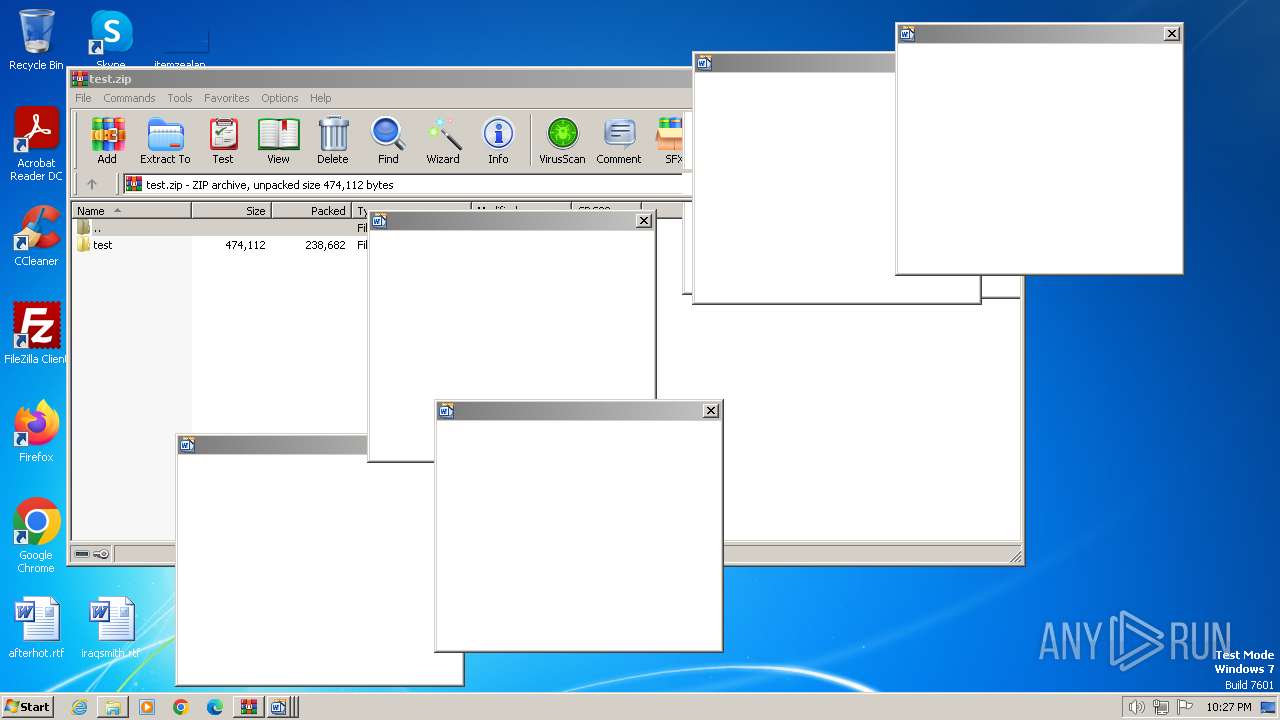
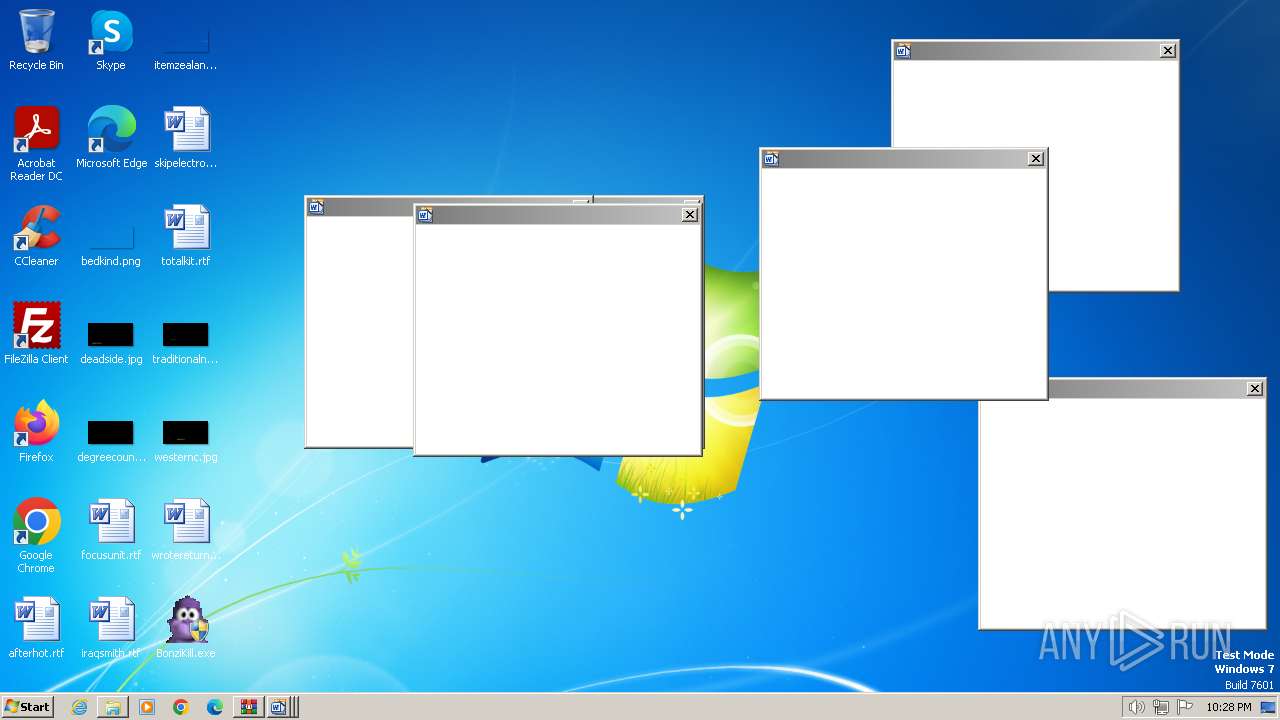
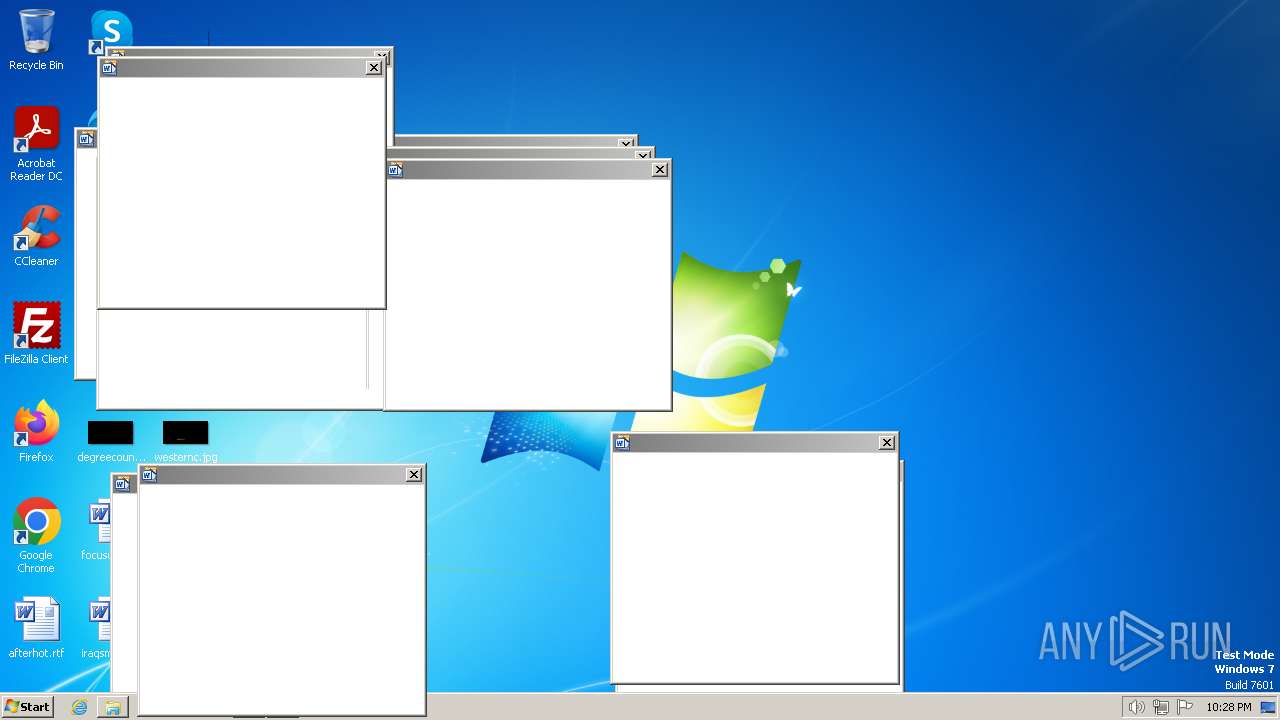
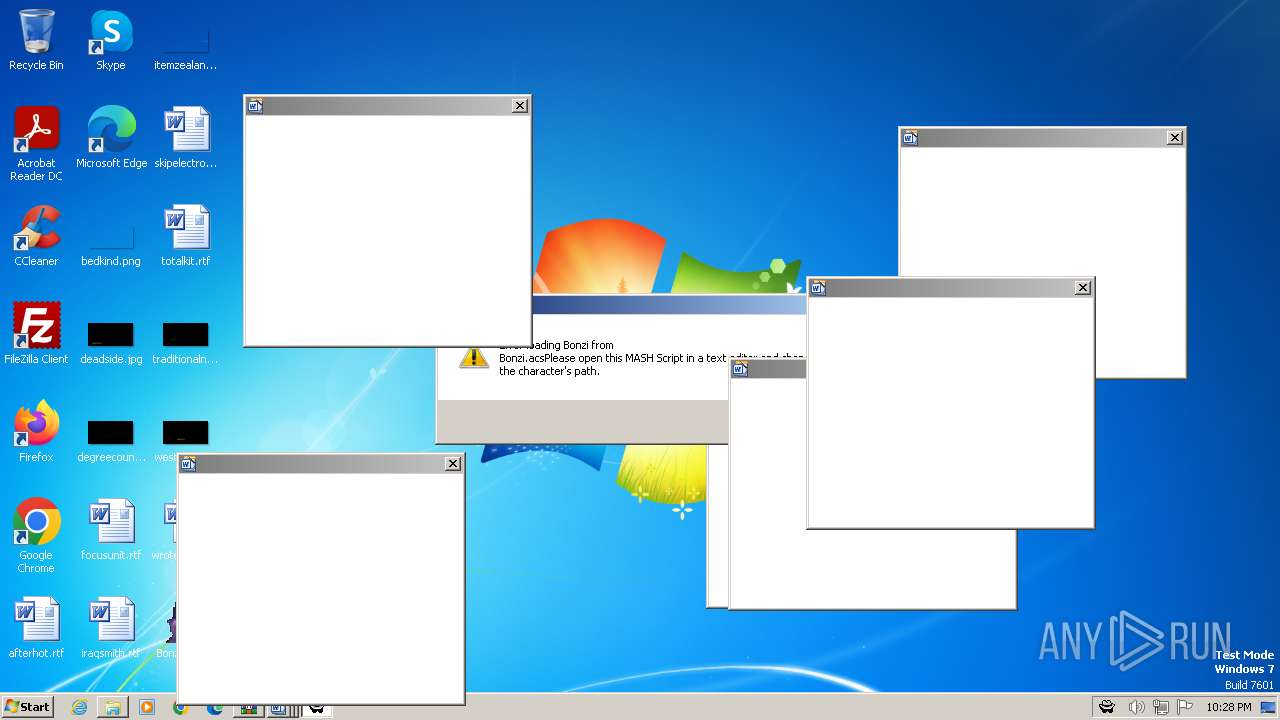
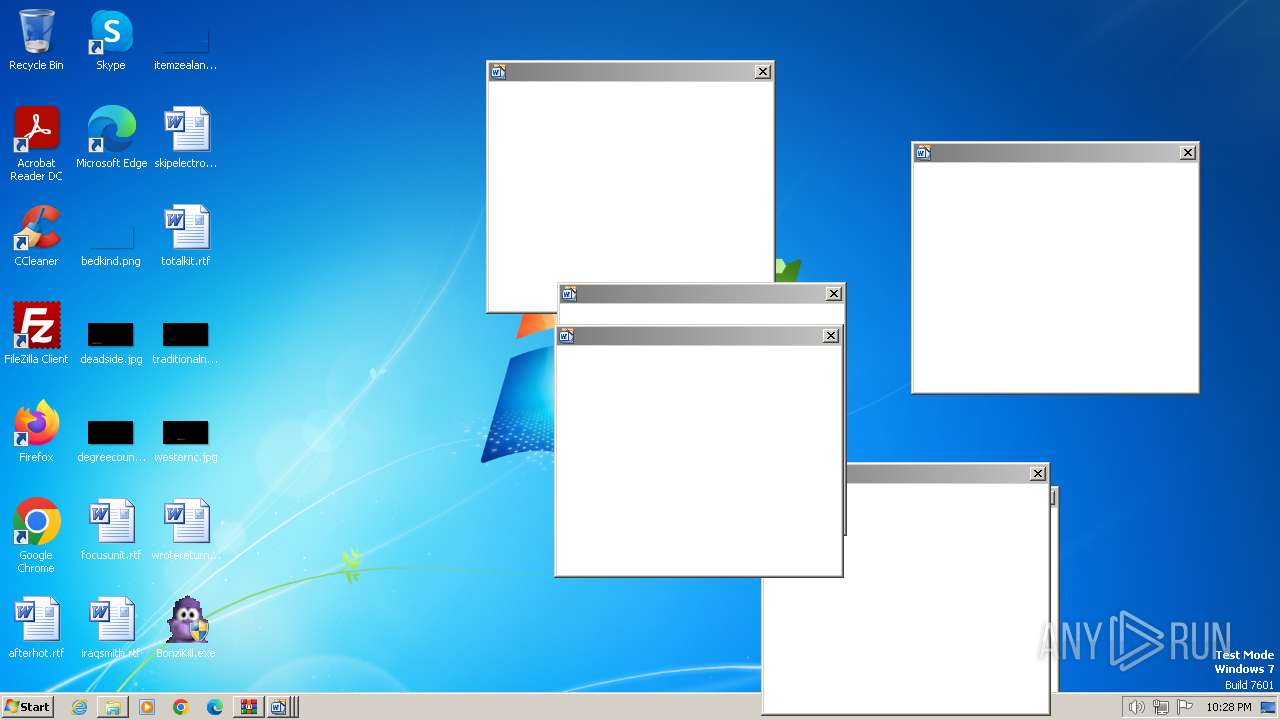
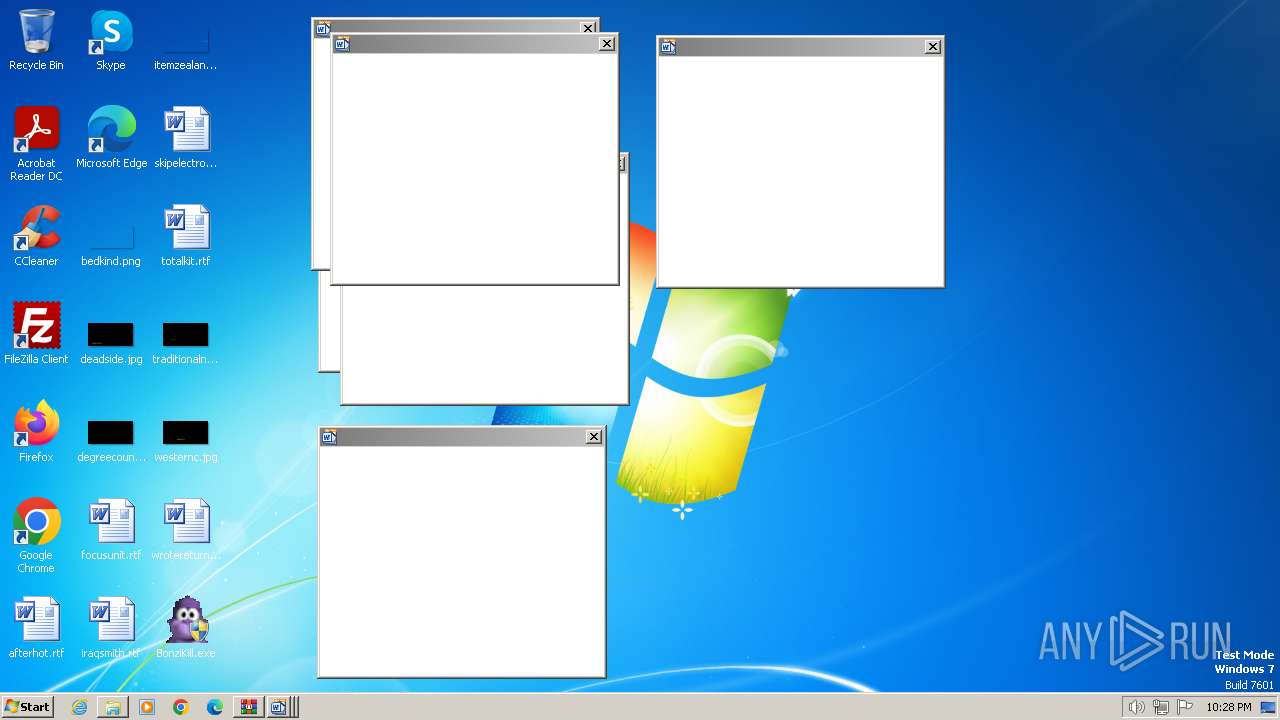
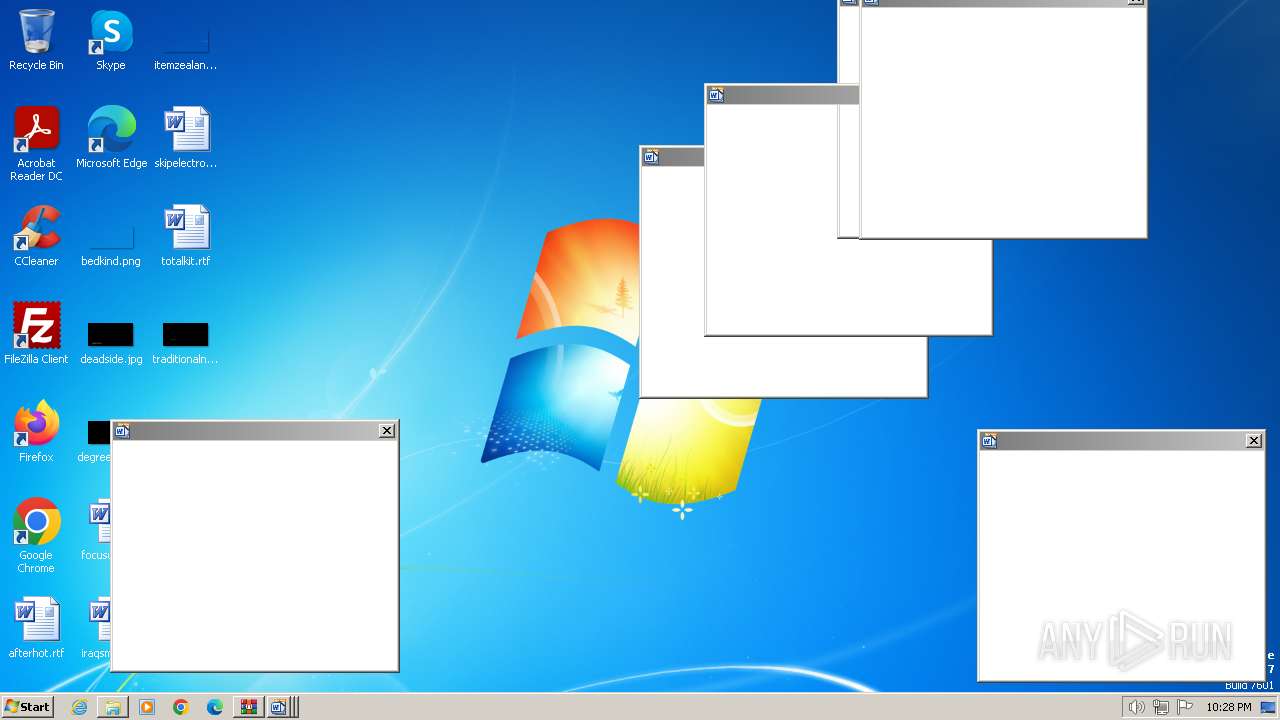
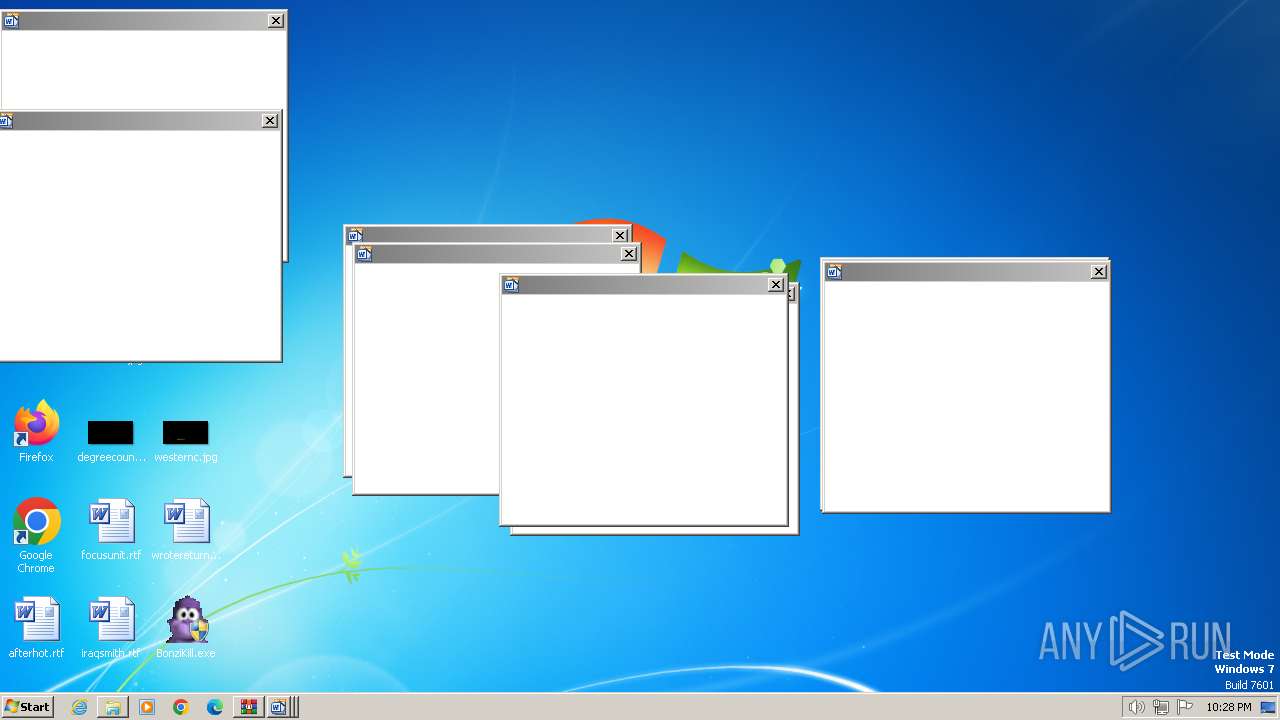
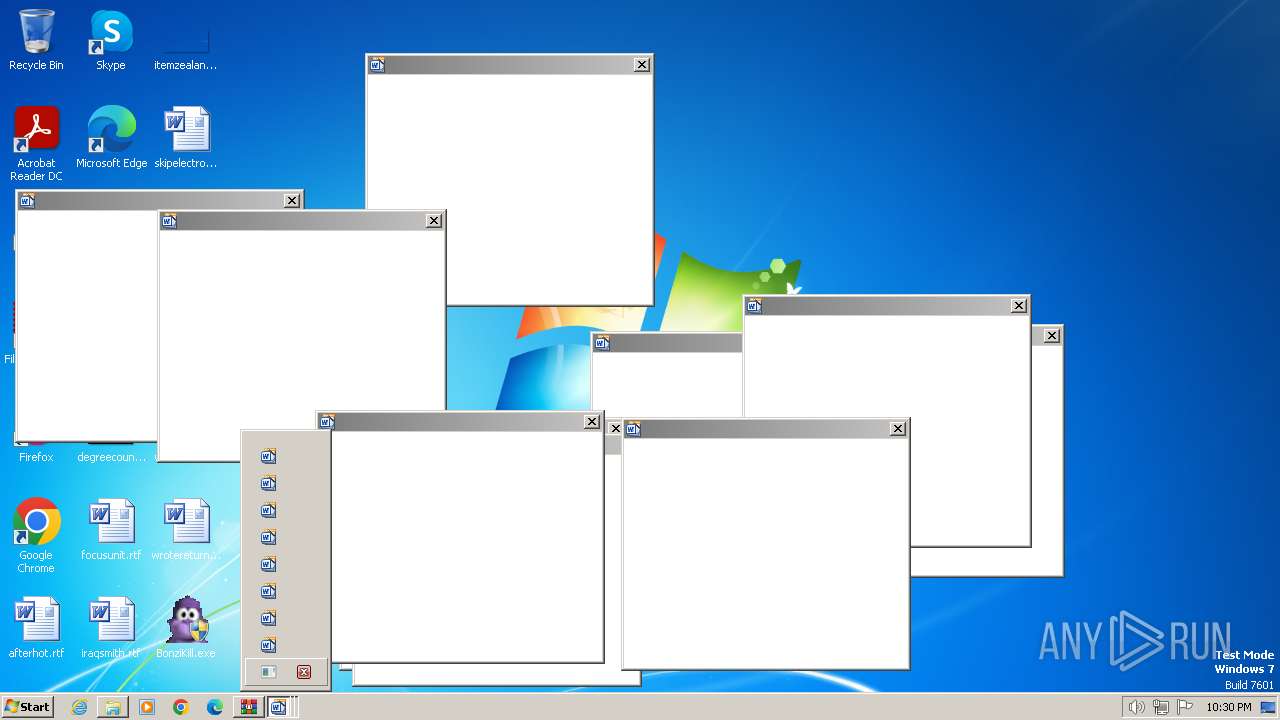
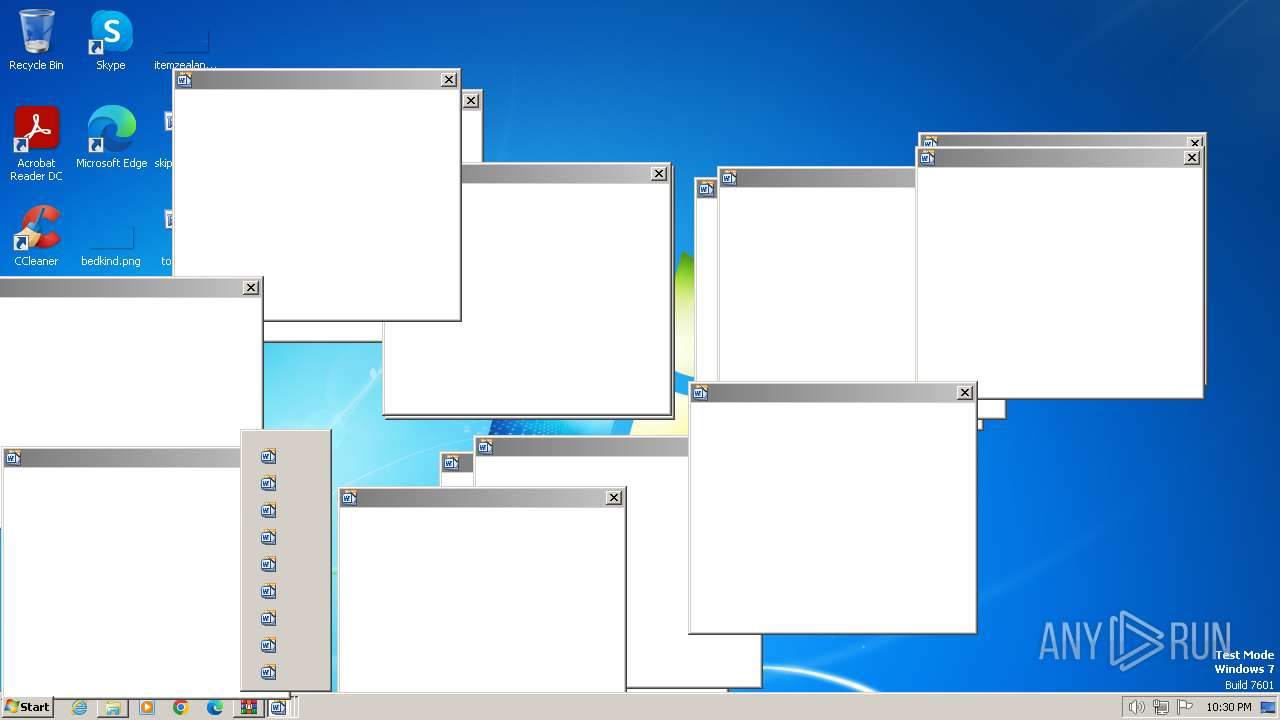
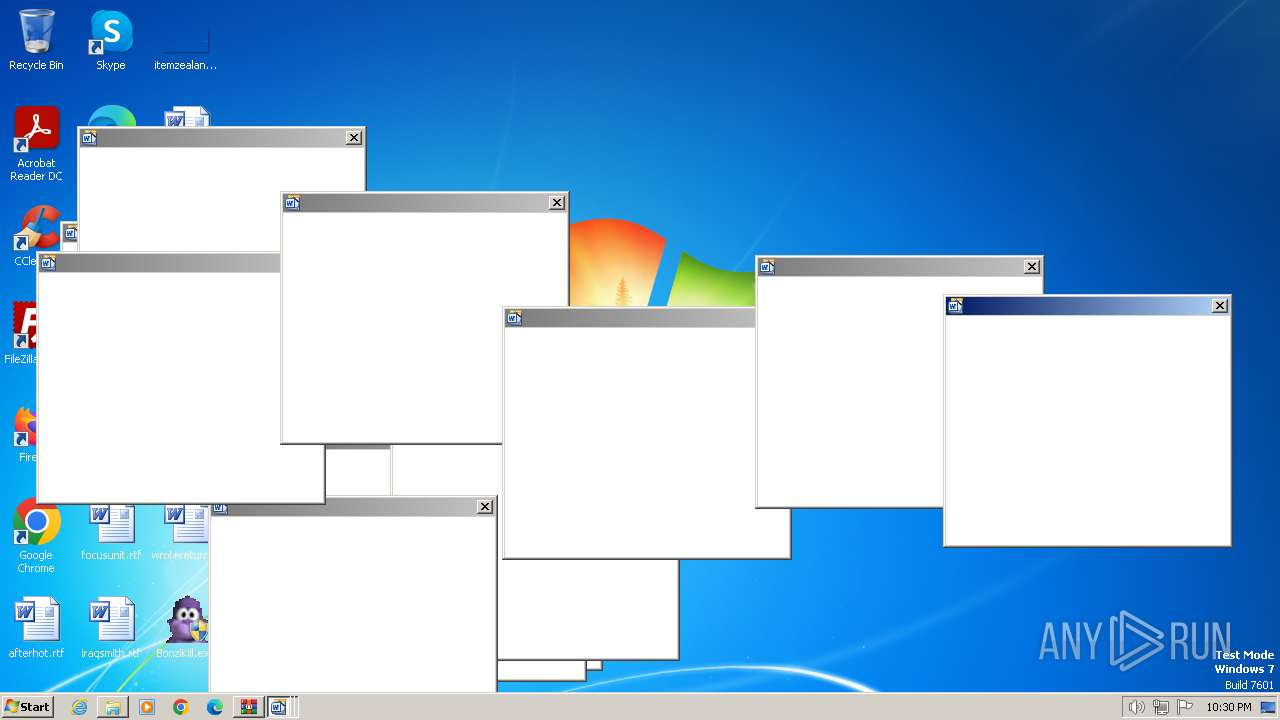
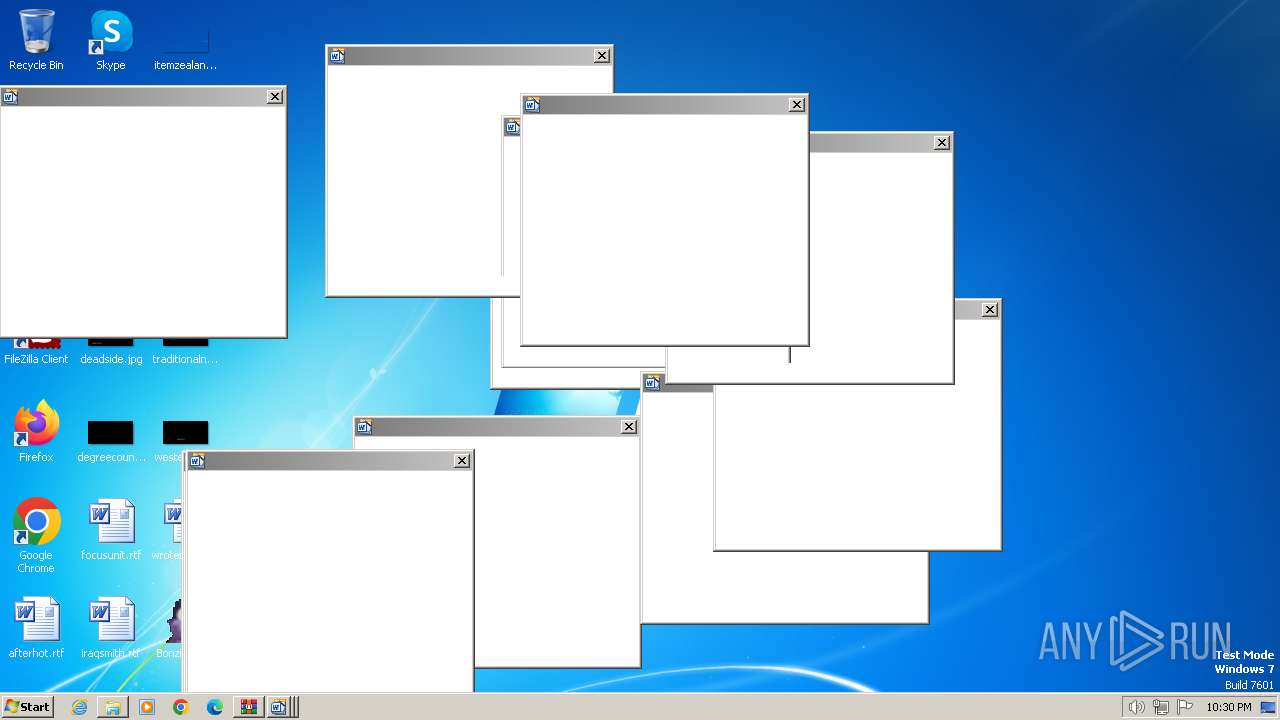
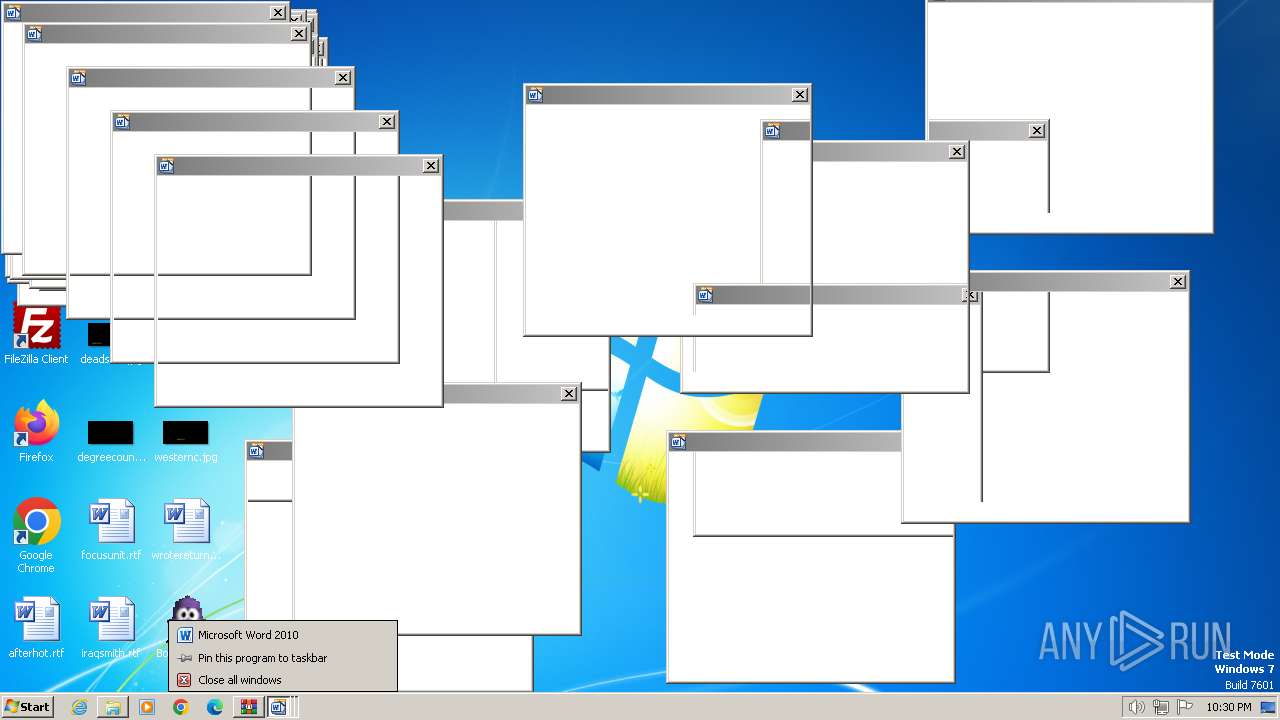
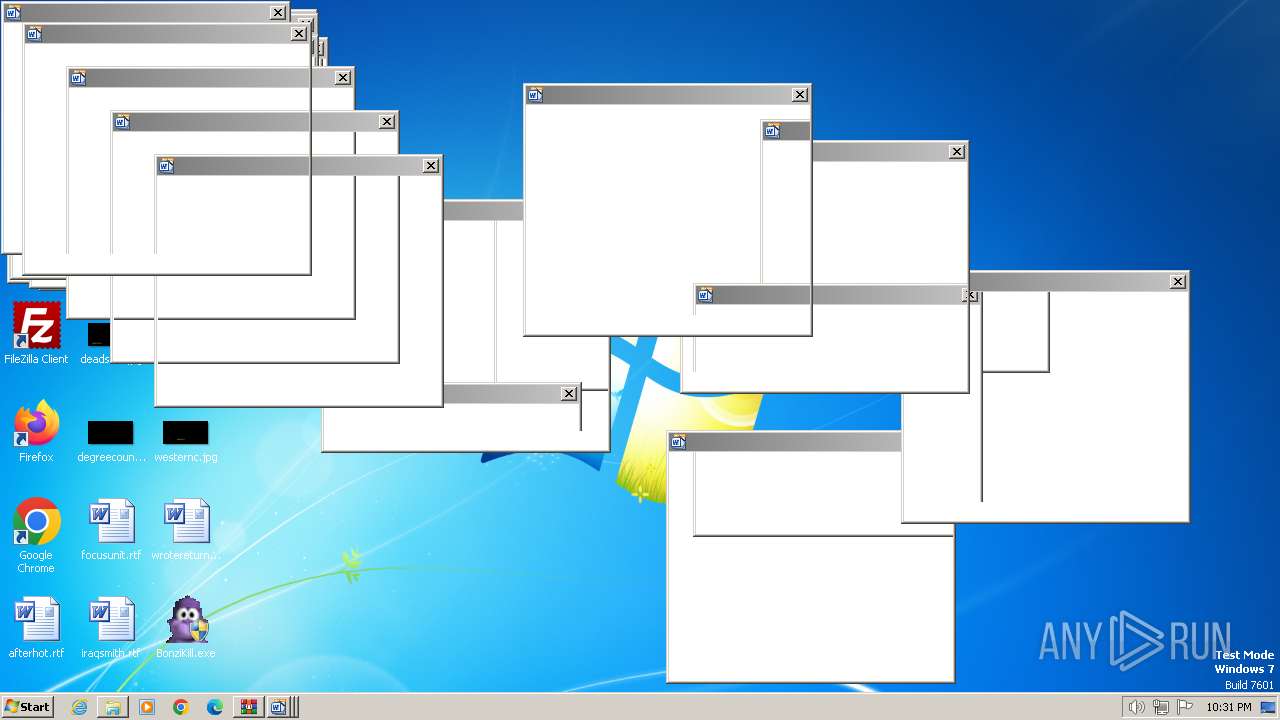
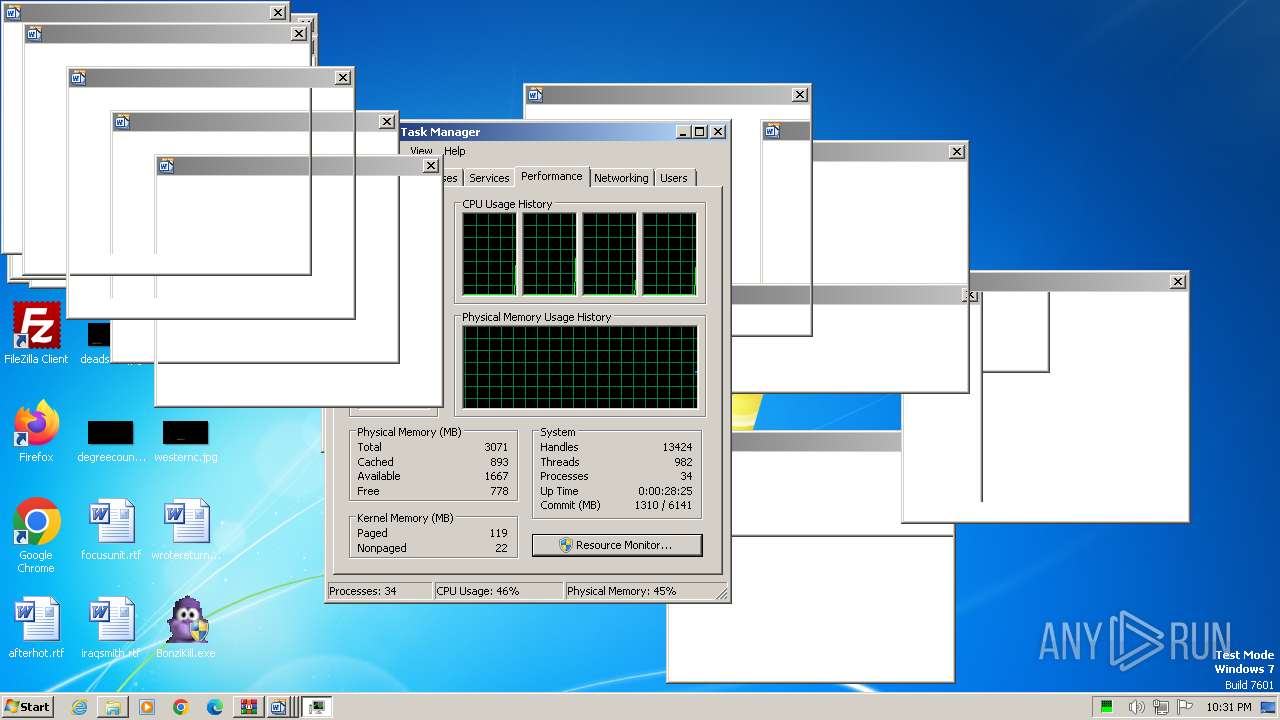
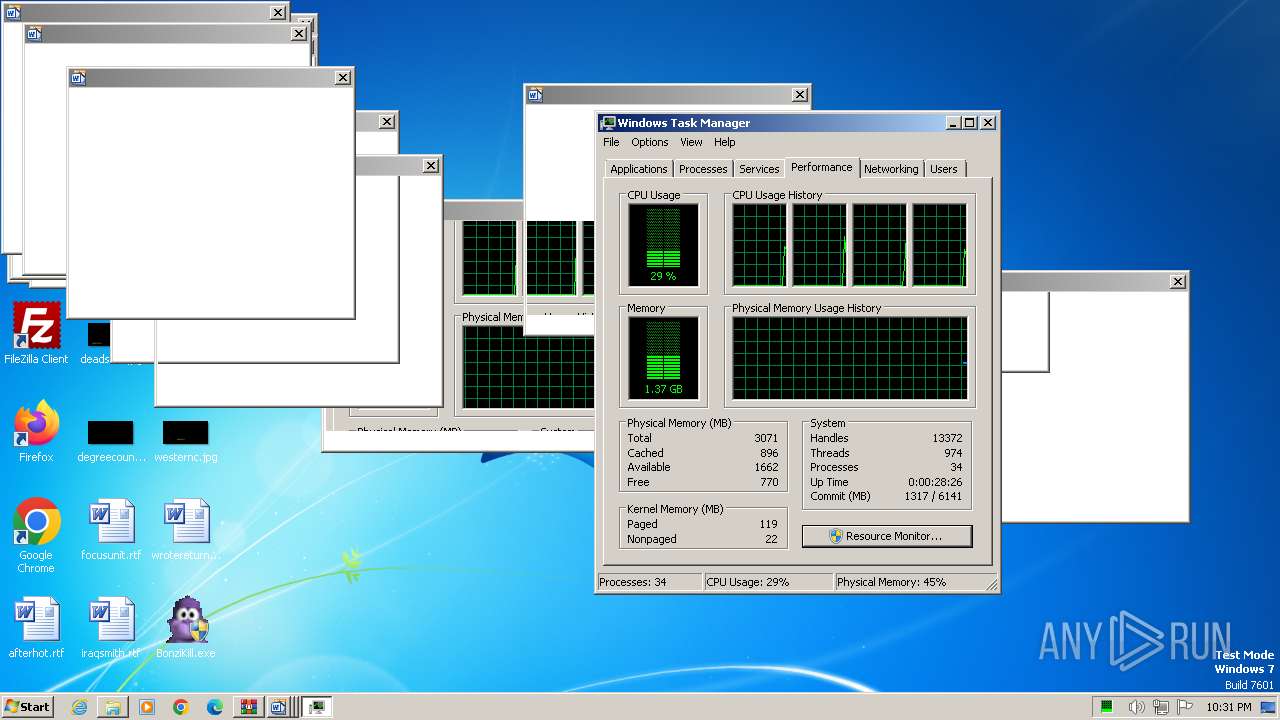
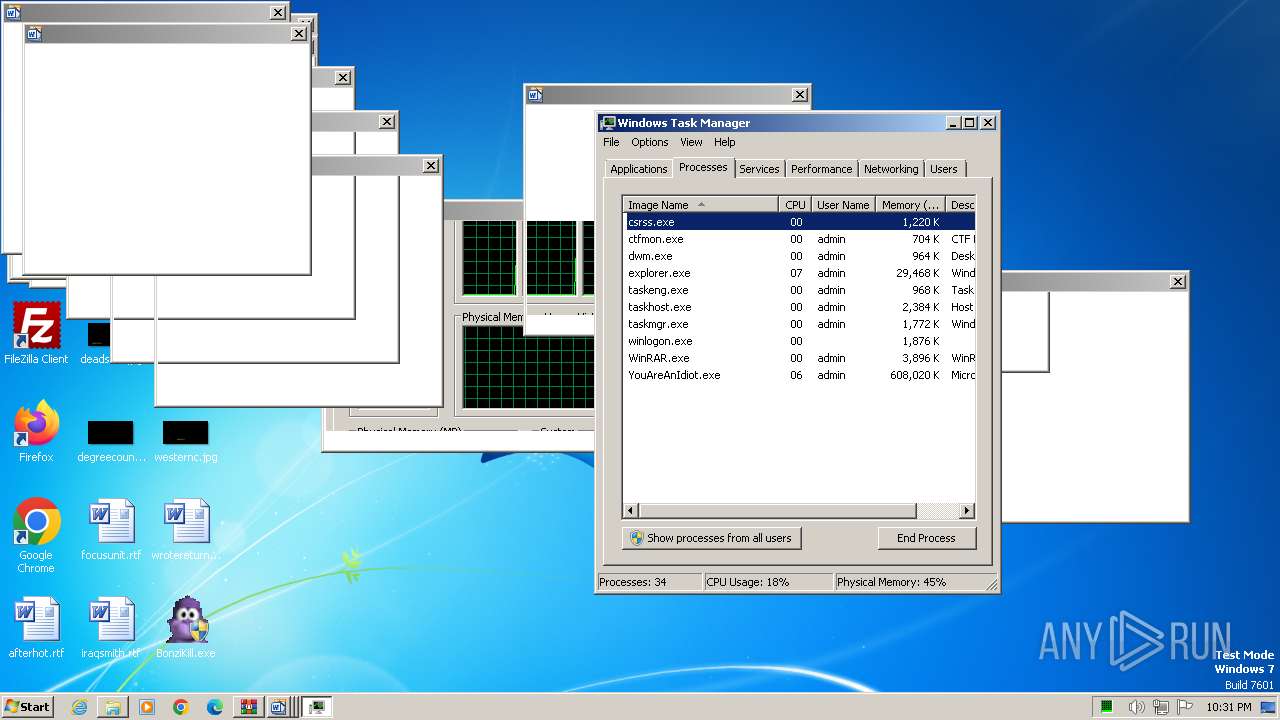
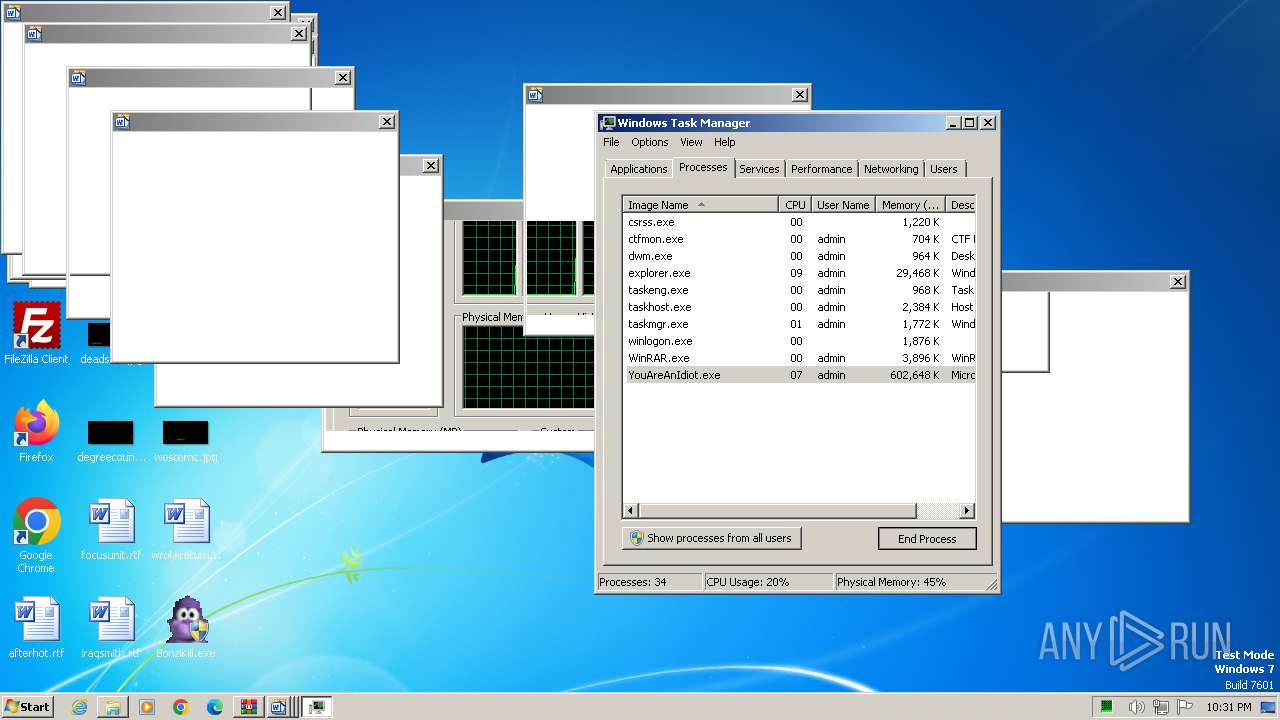
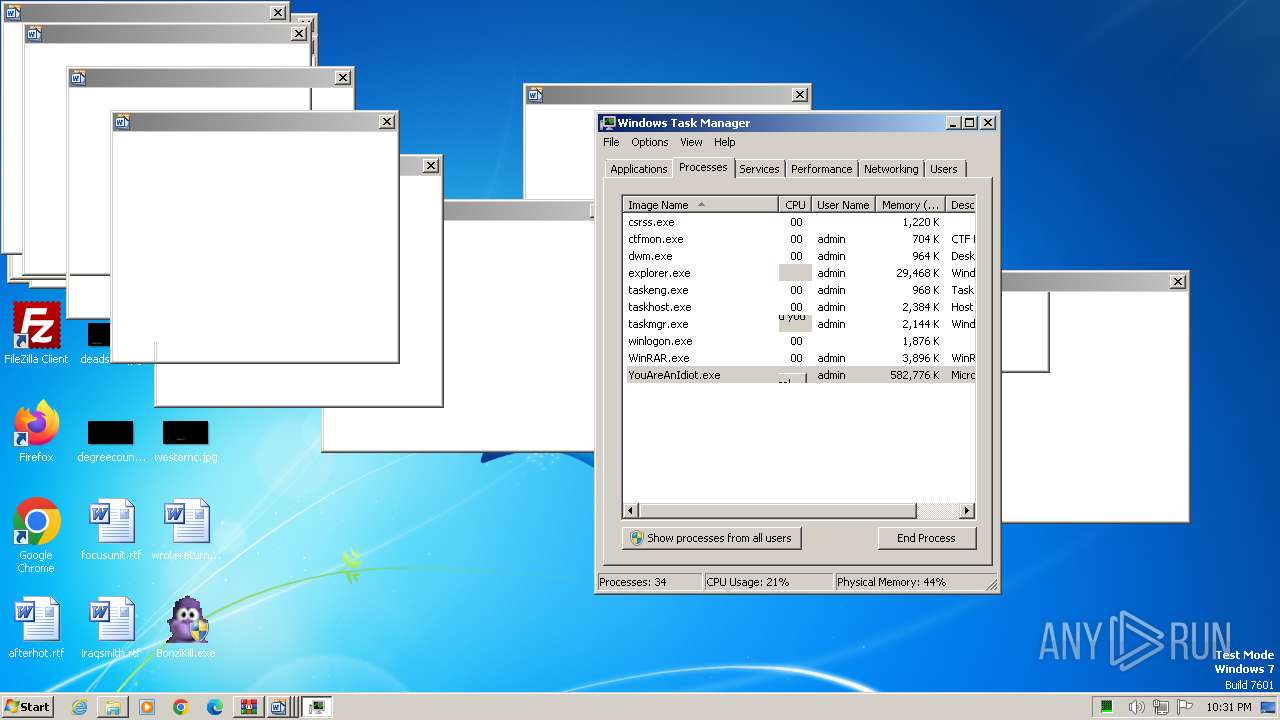
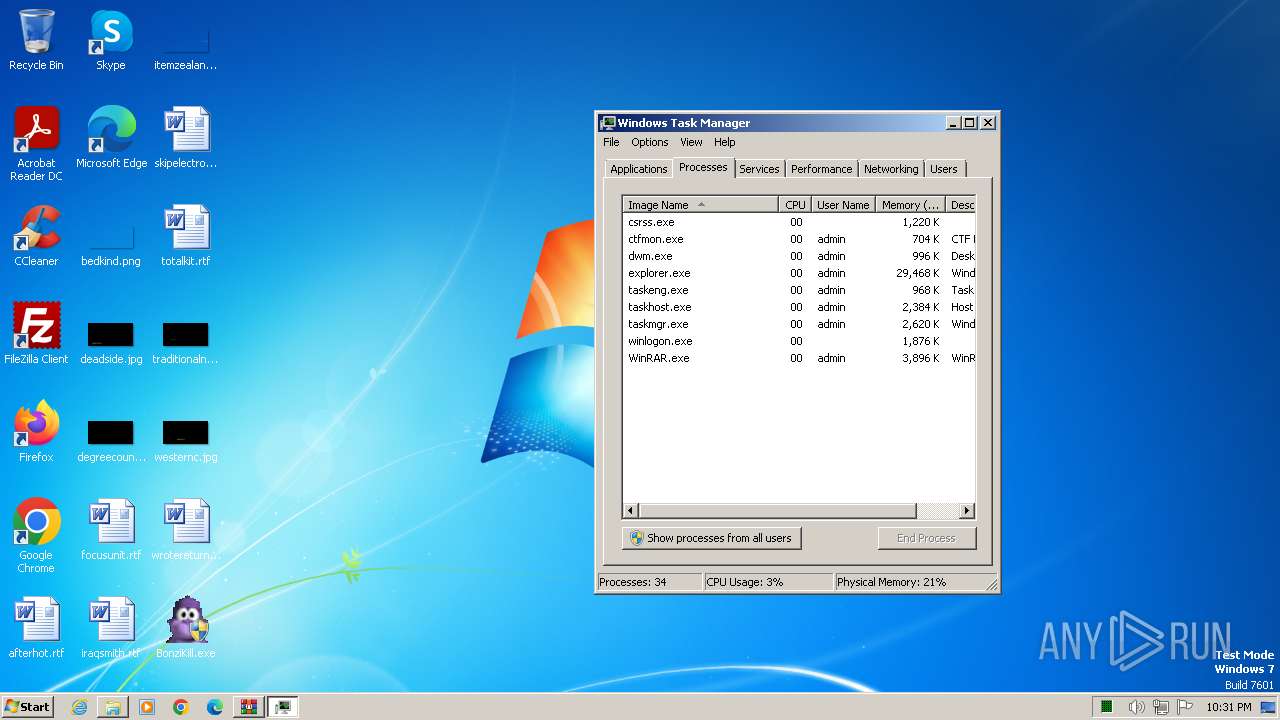
Total processes
72
Monitored processes
16
Malicious processes
5
Suspicious processes
1
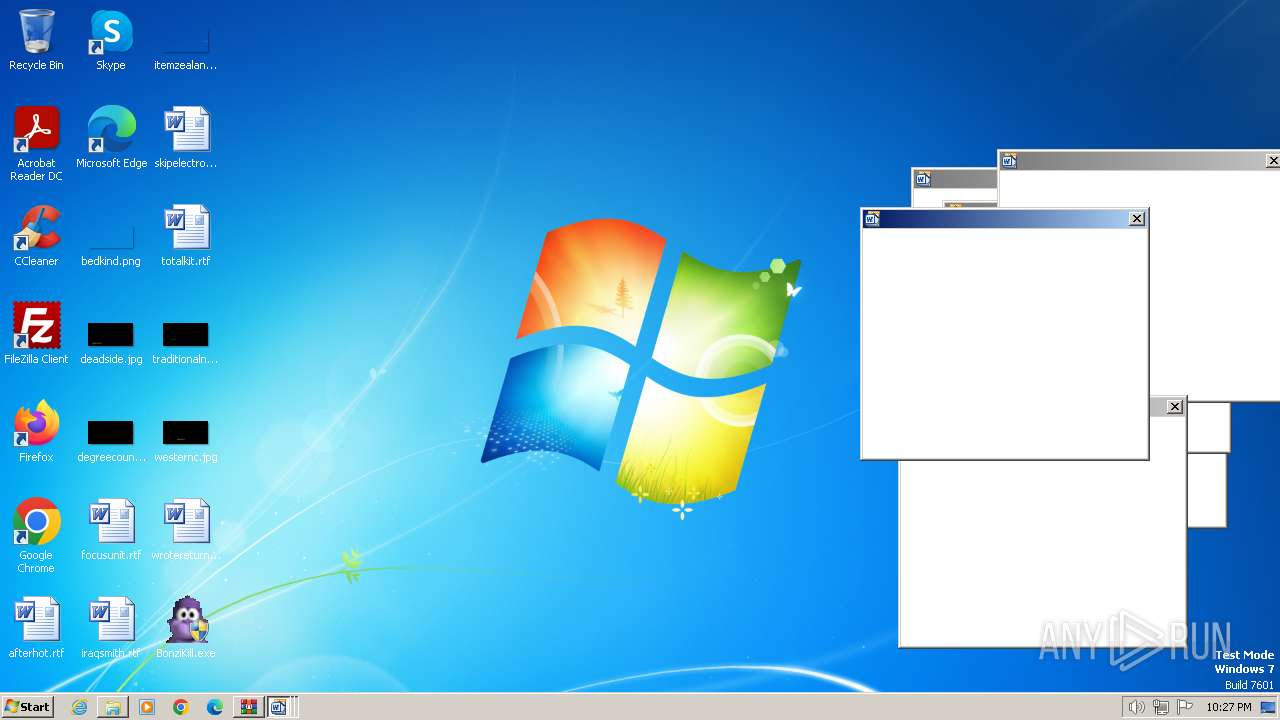
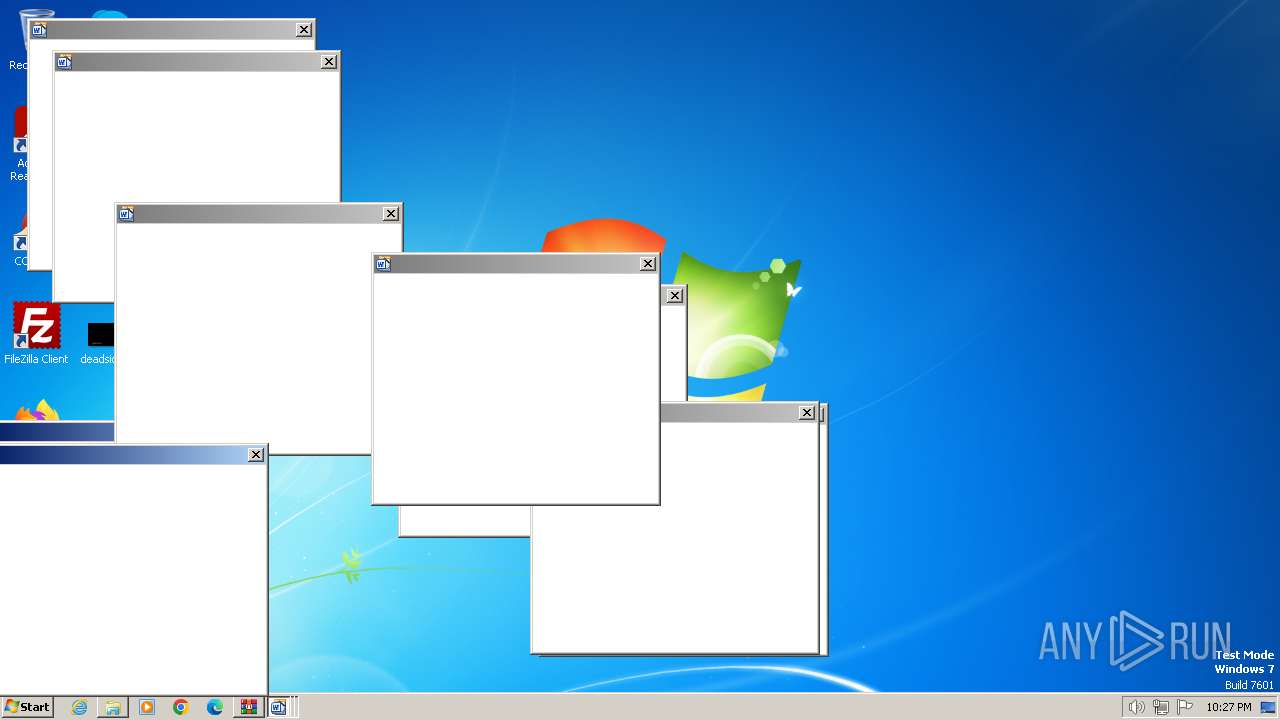
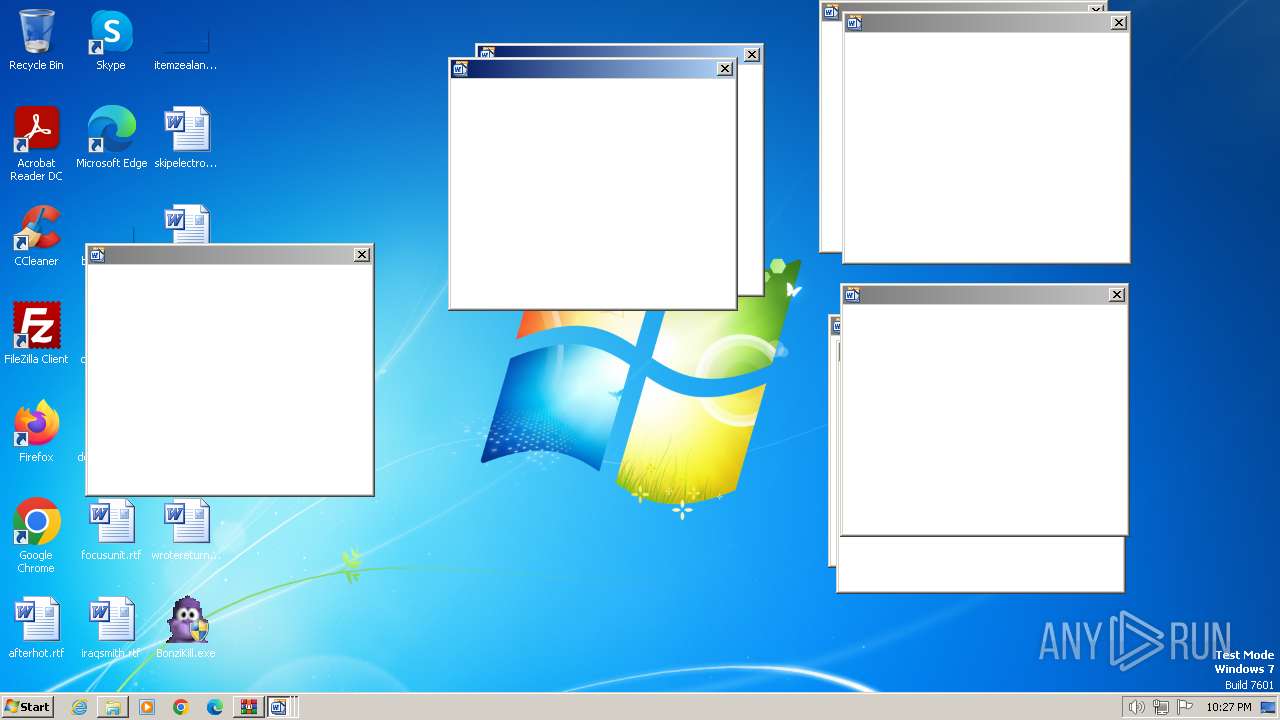
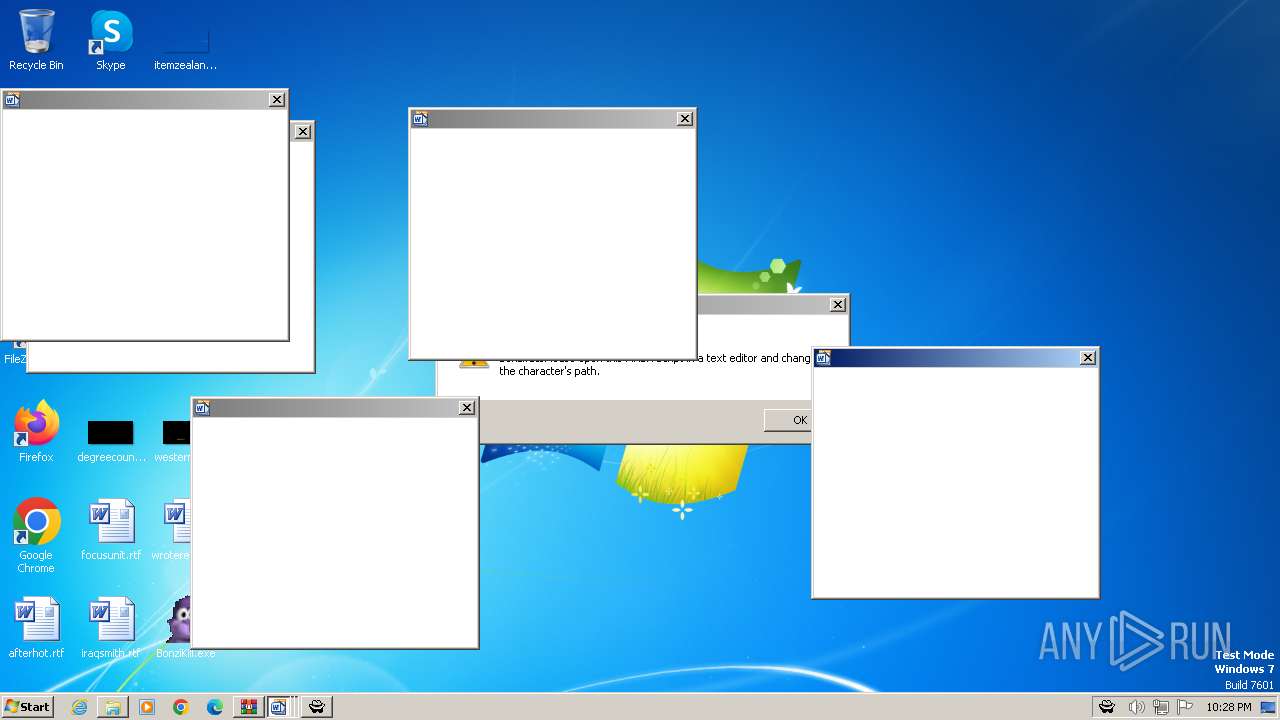
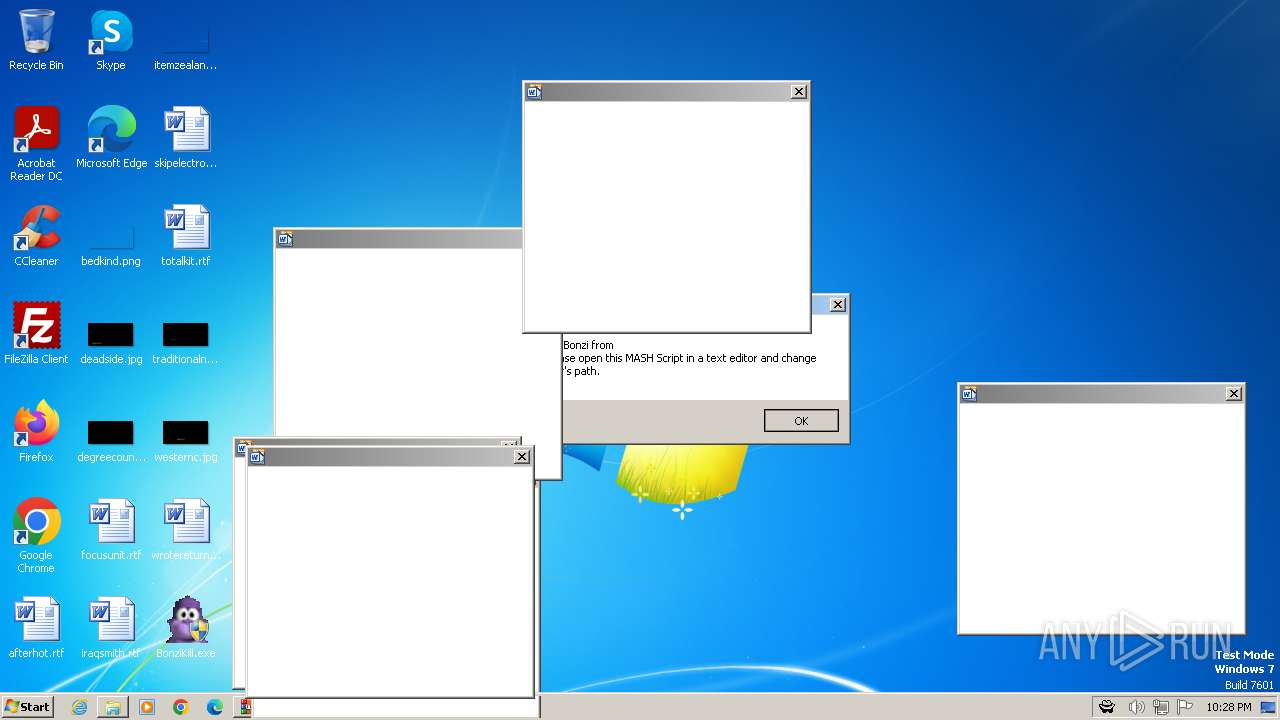
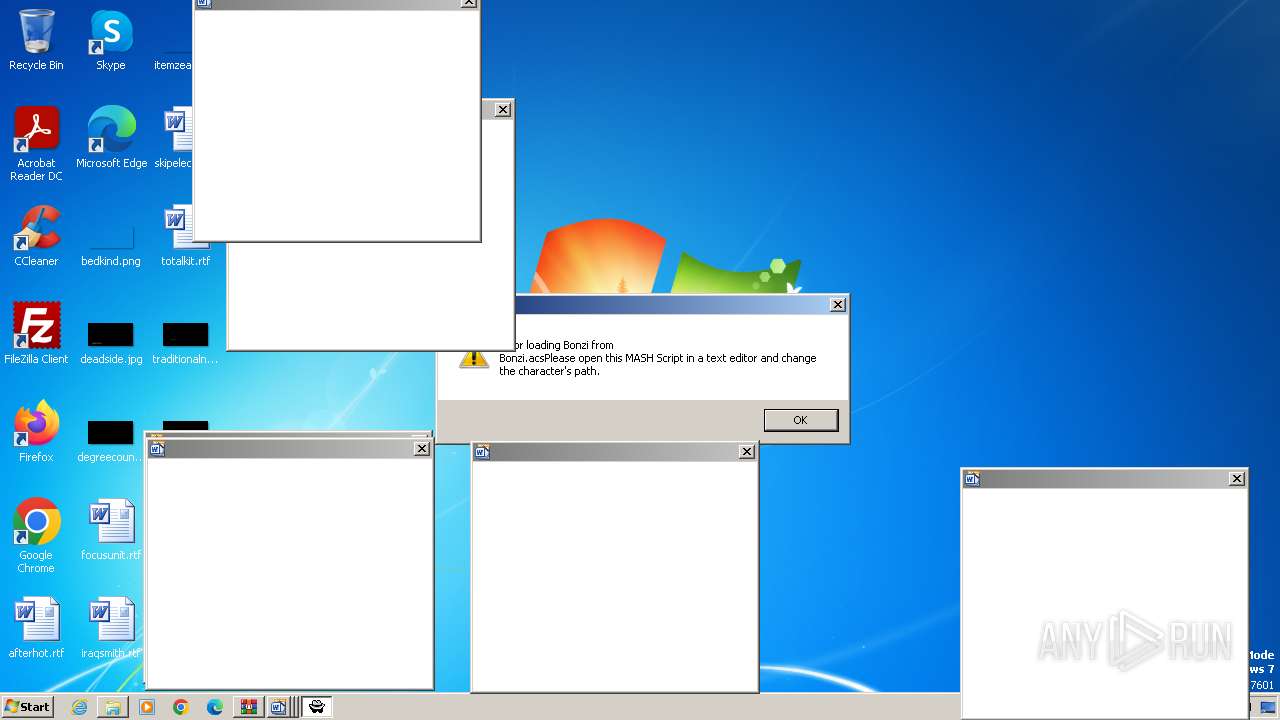
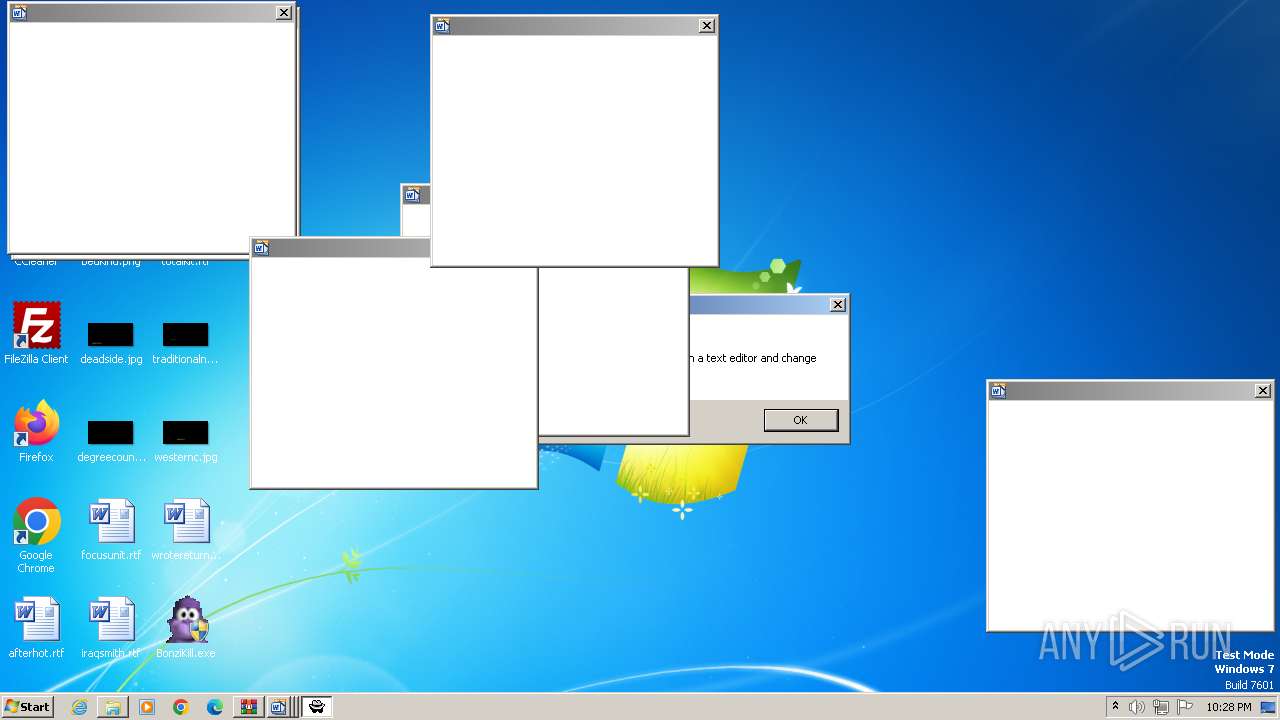
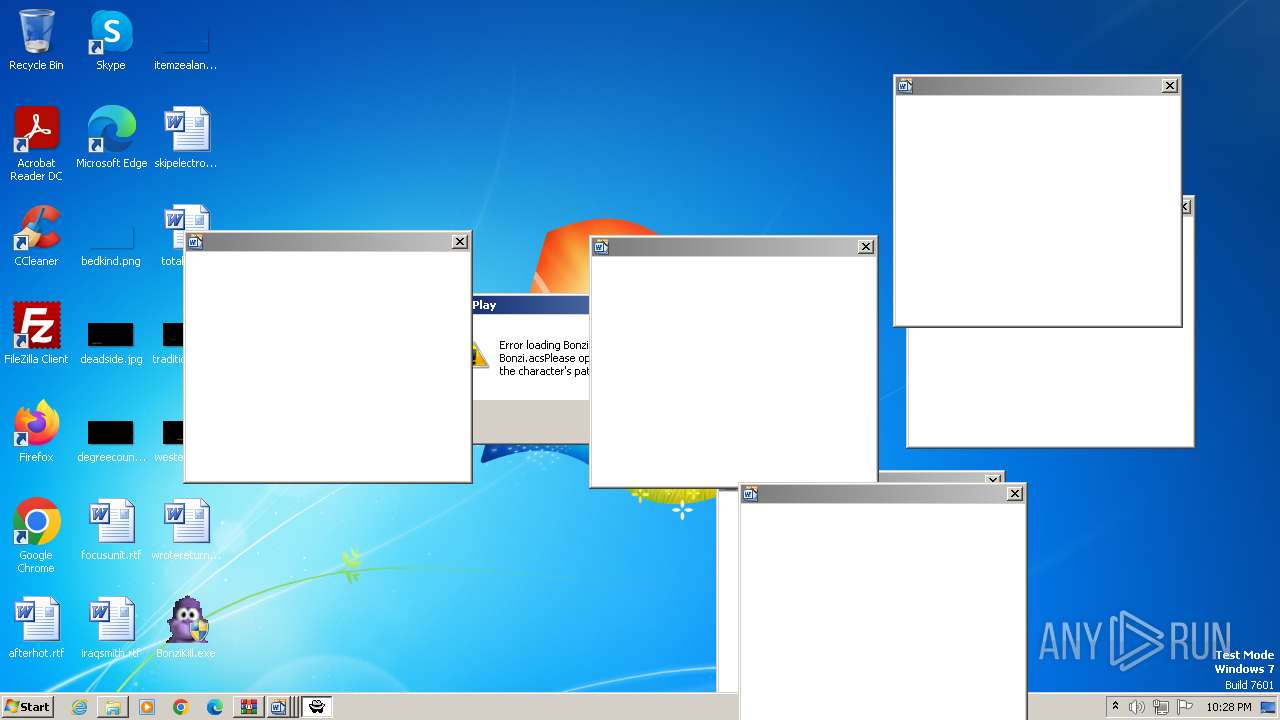
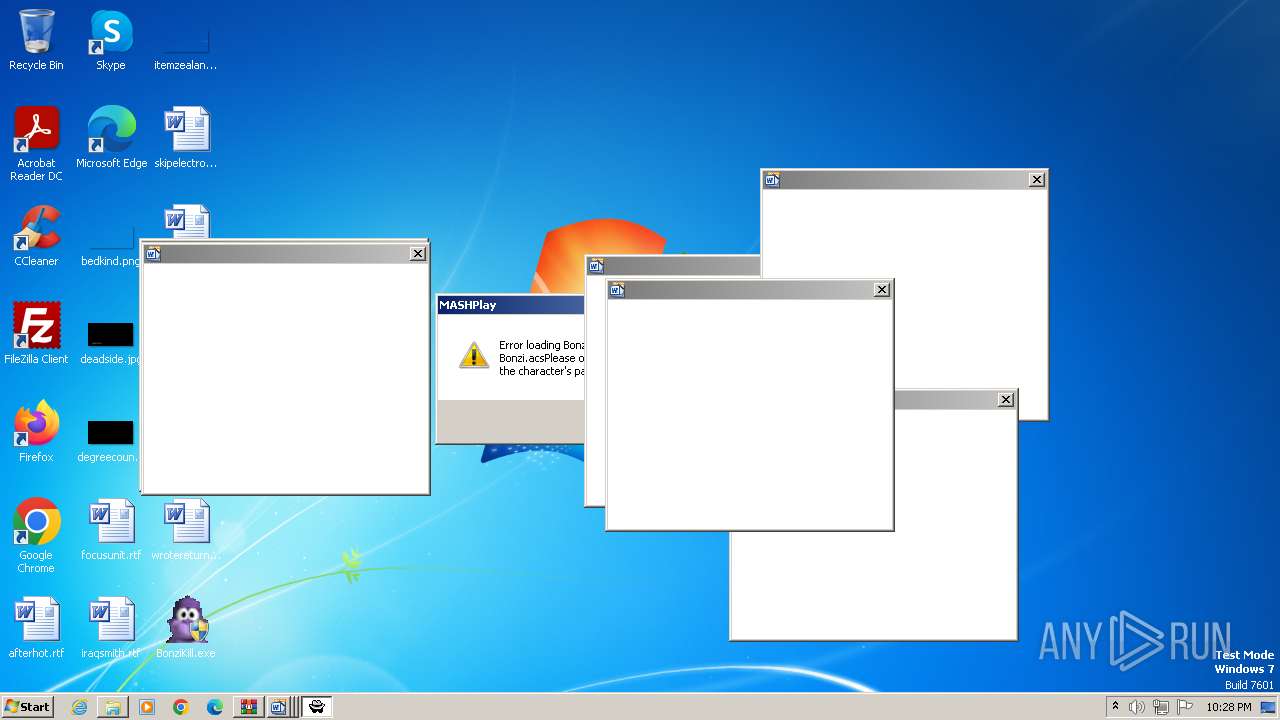
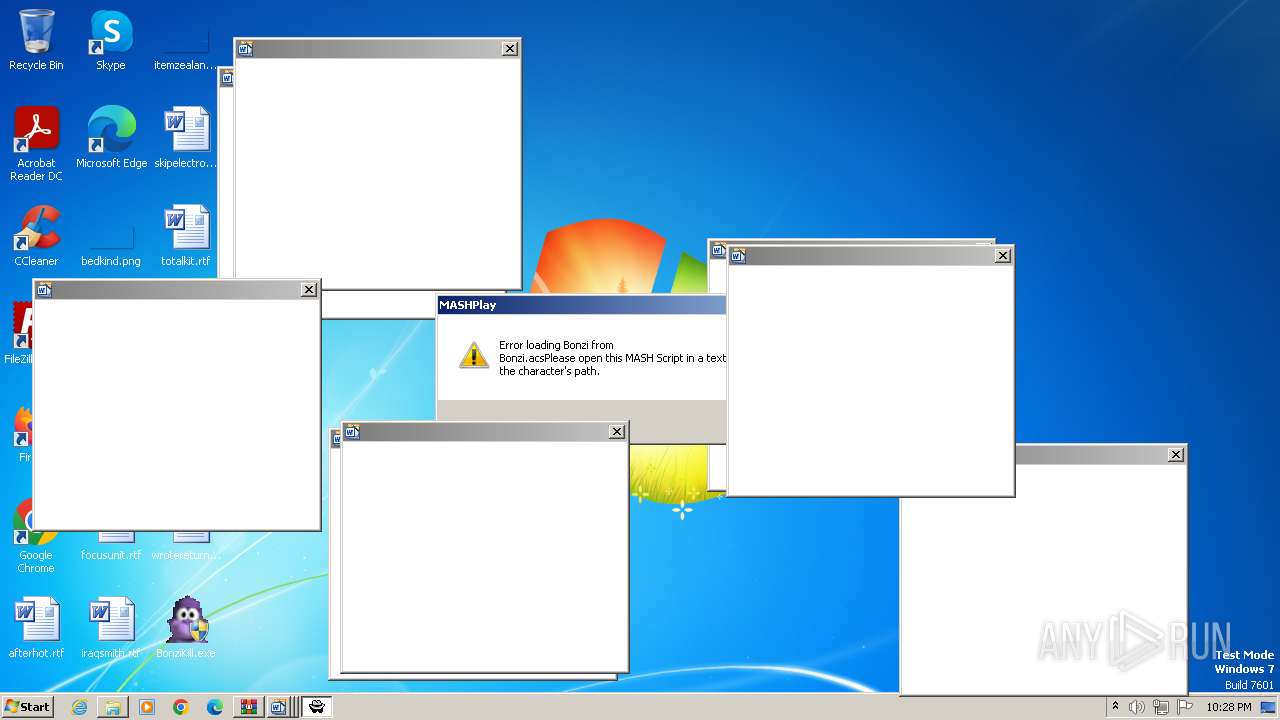
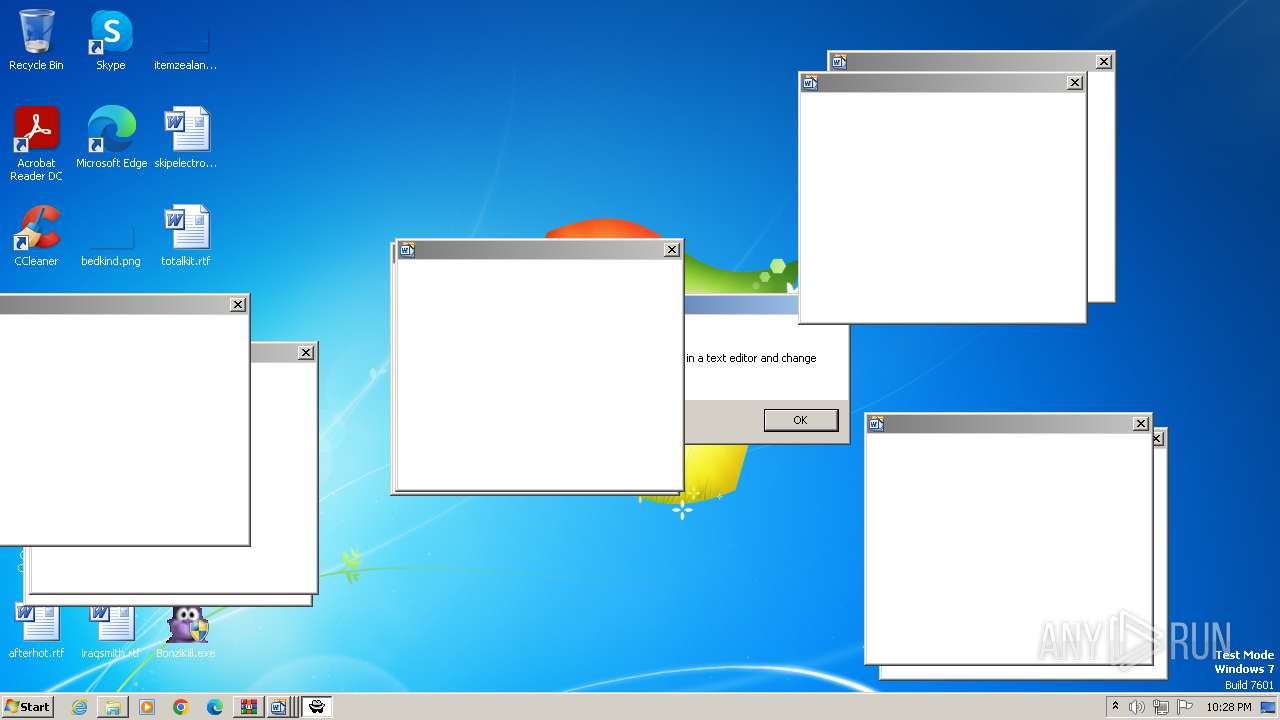
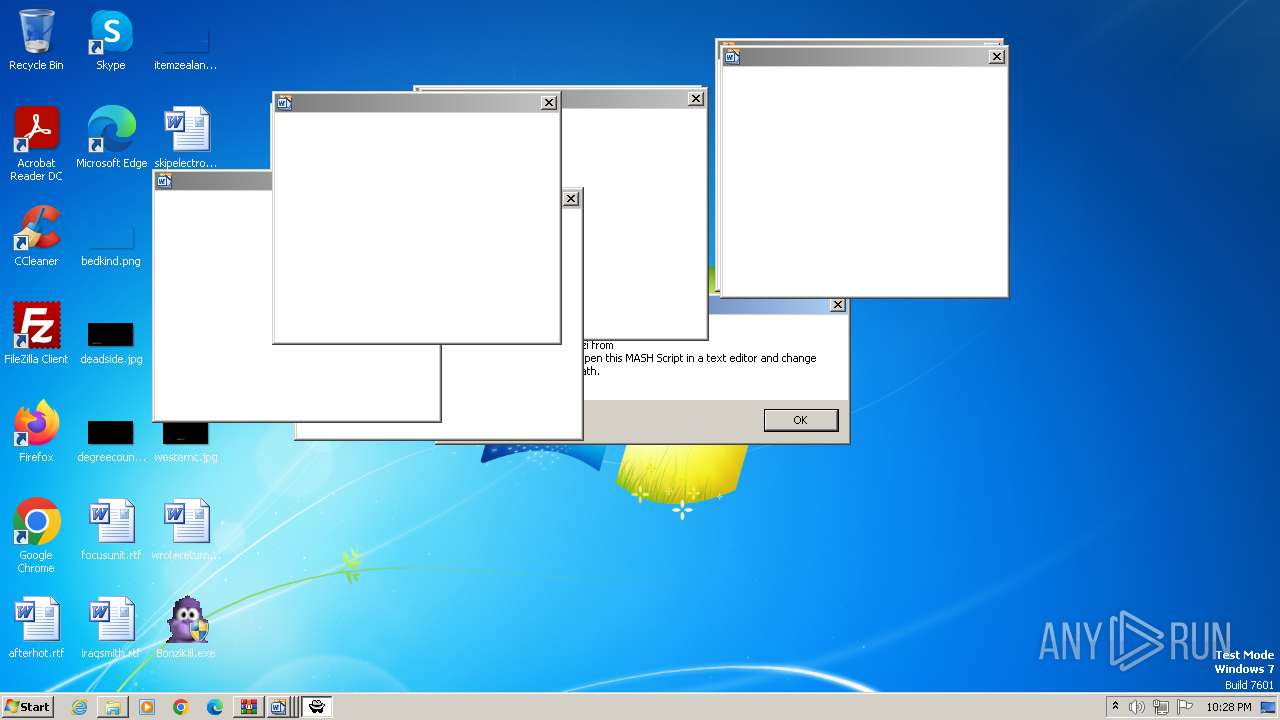
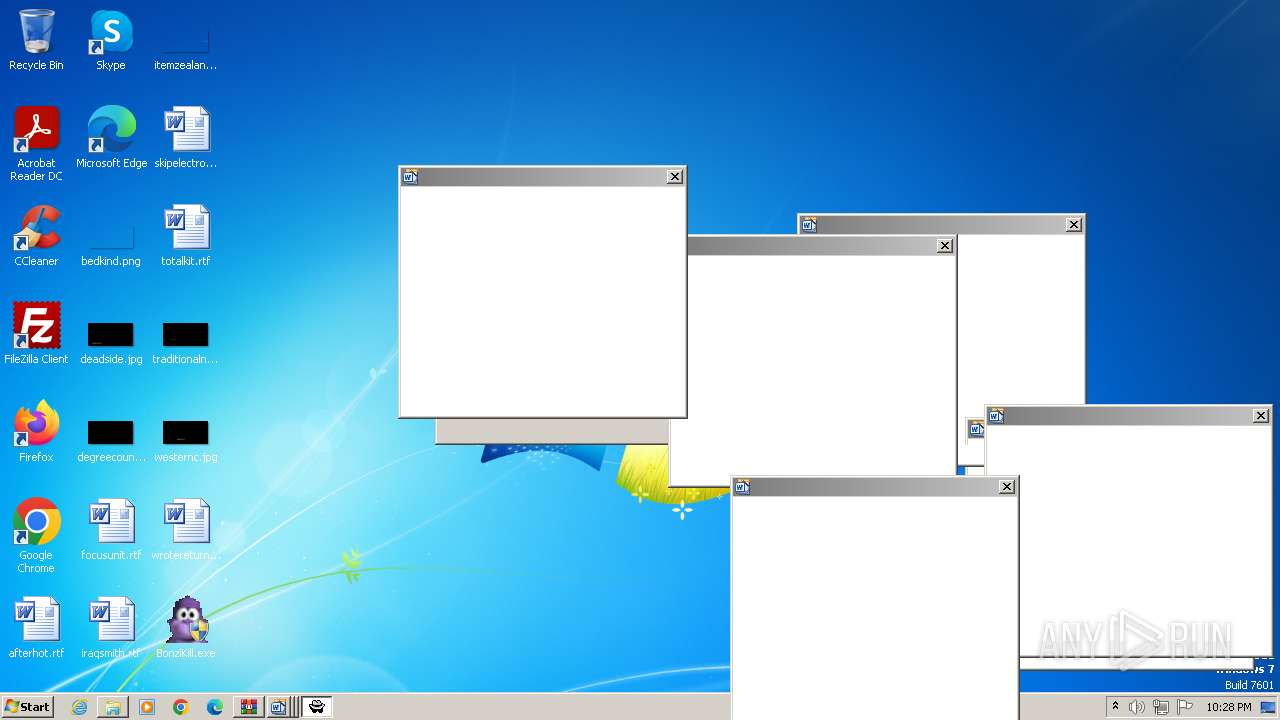
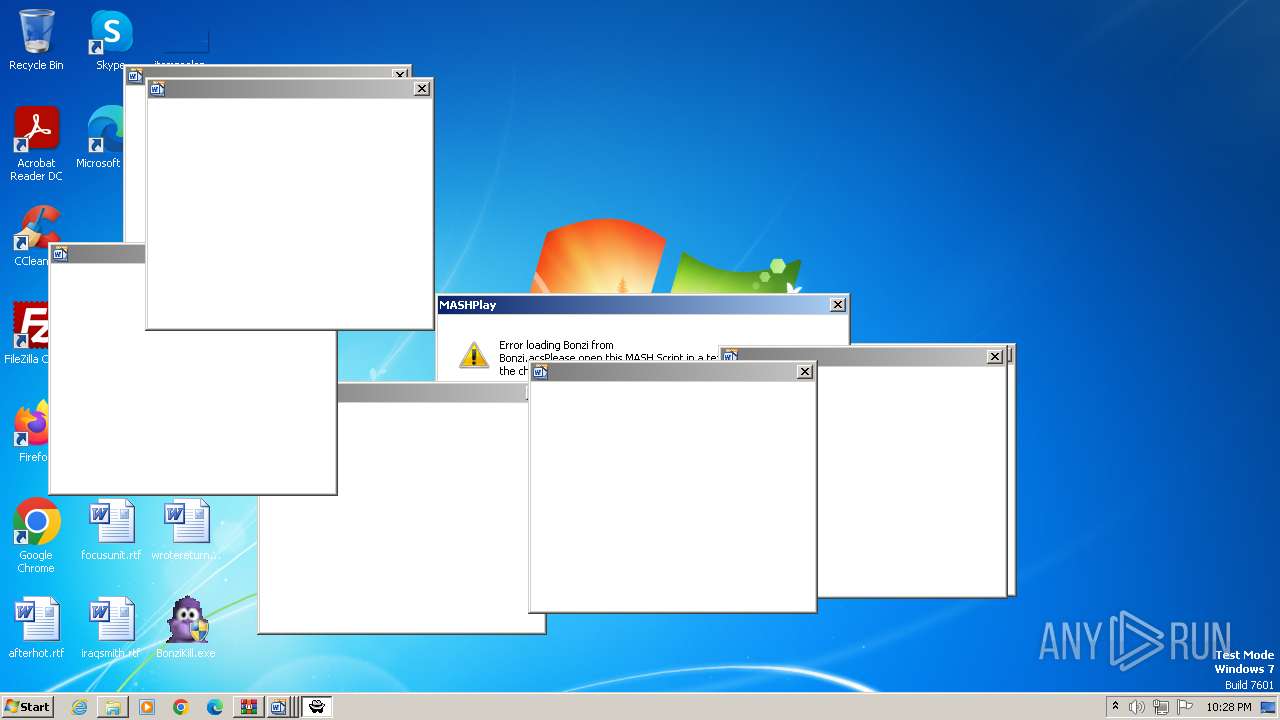
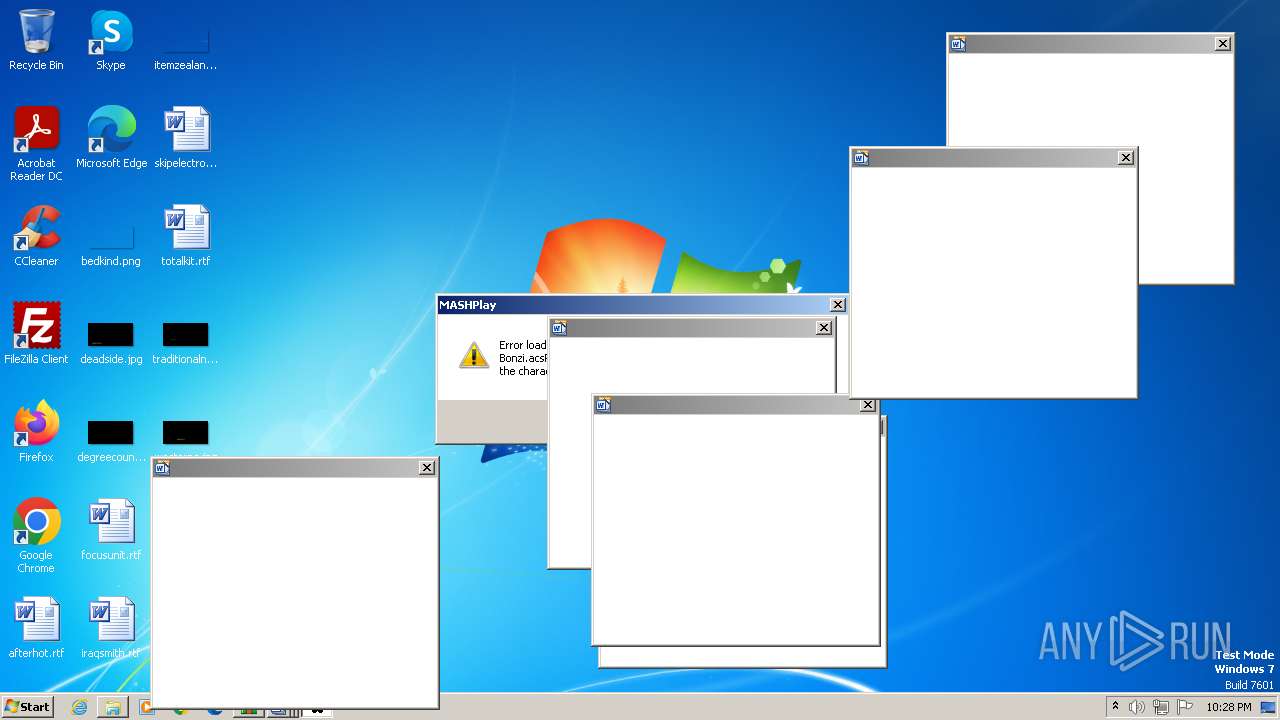
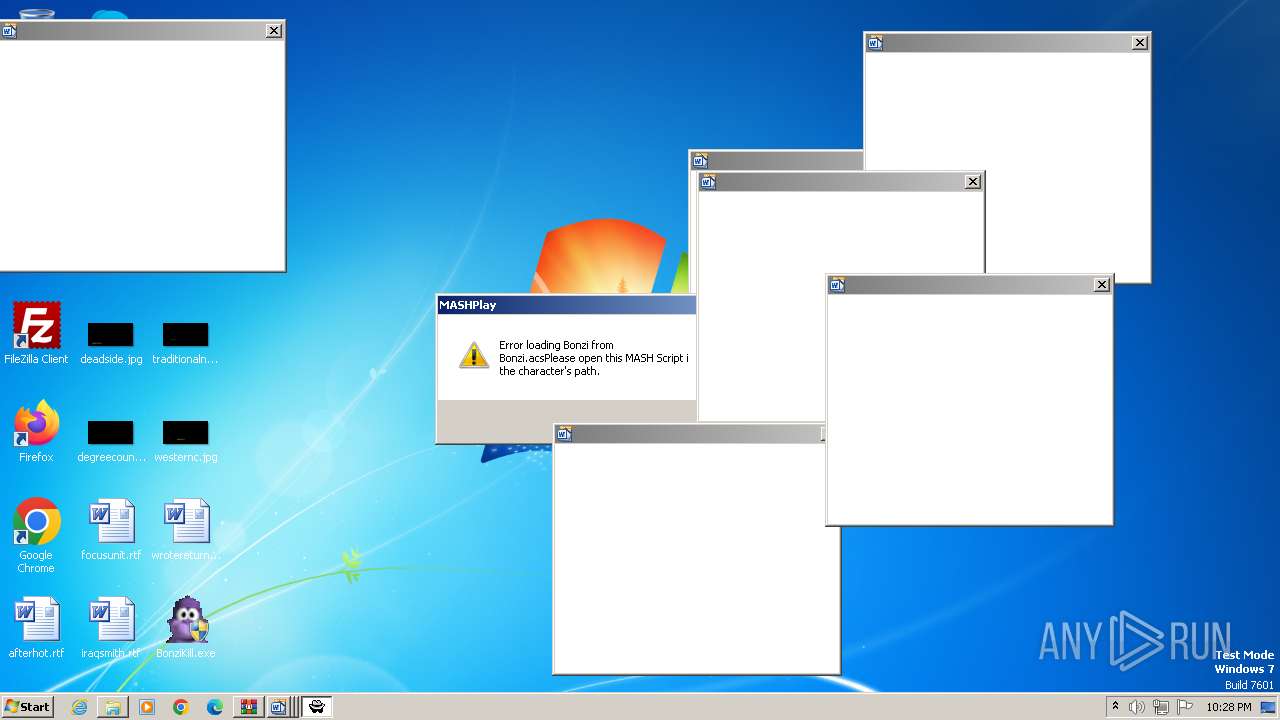
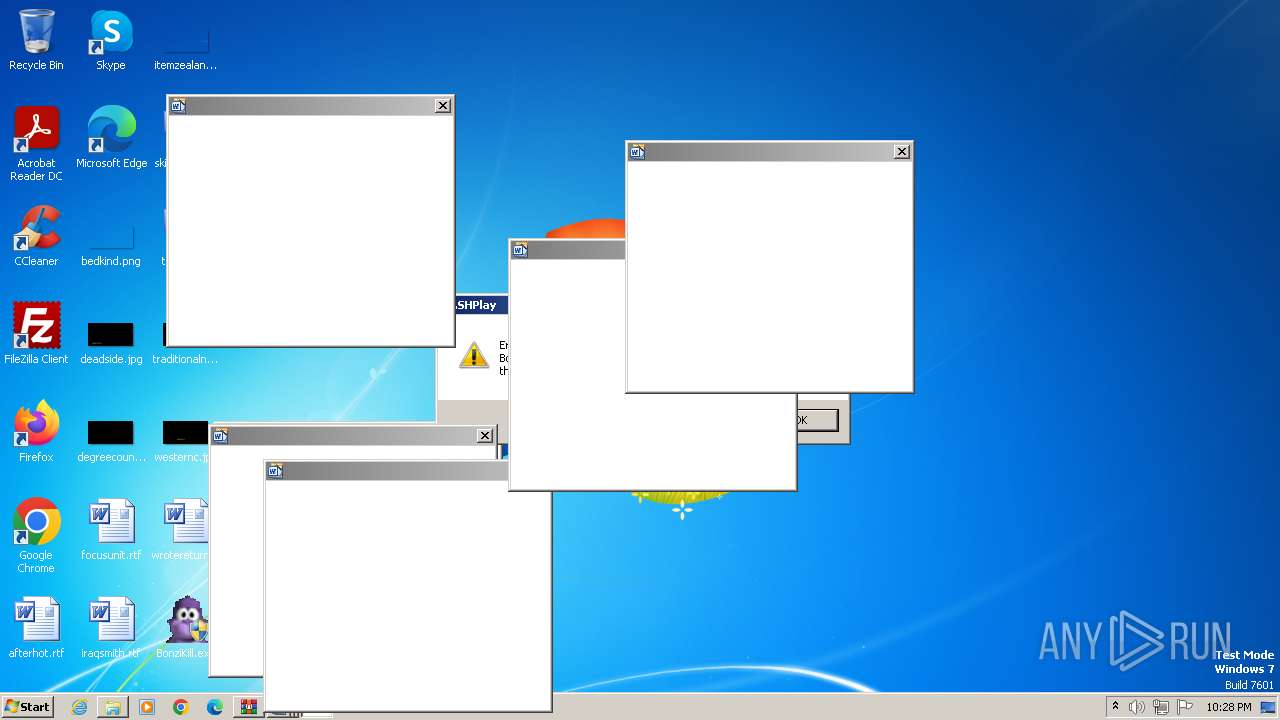
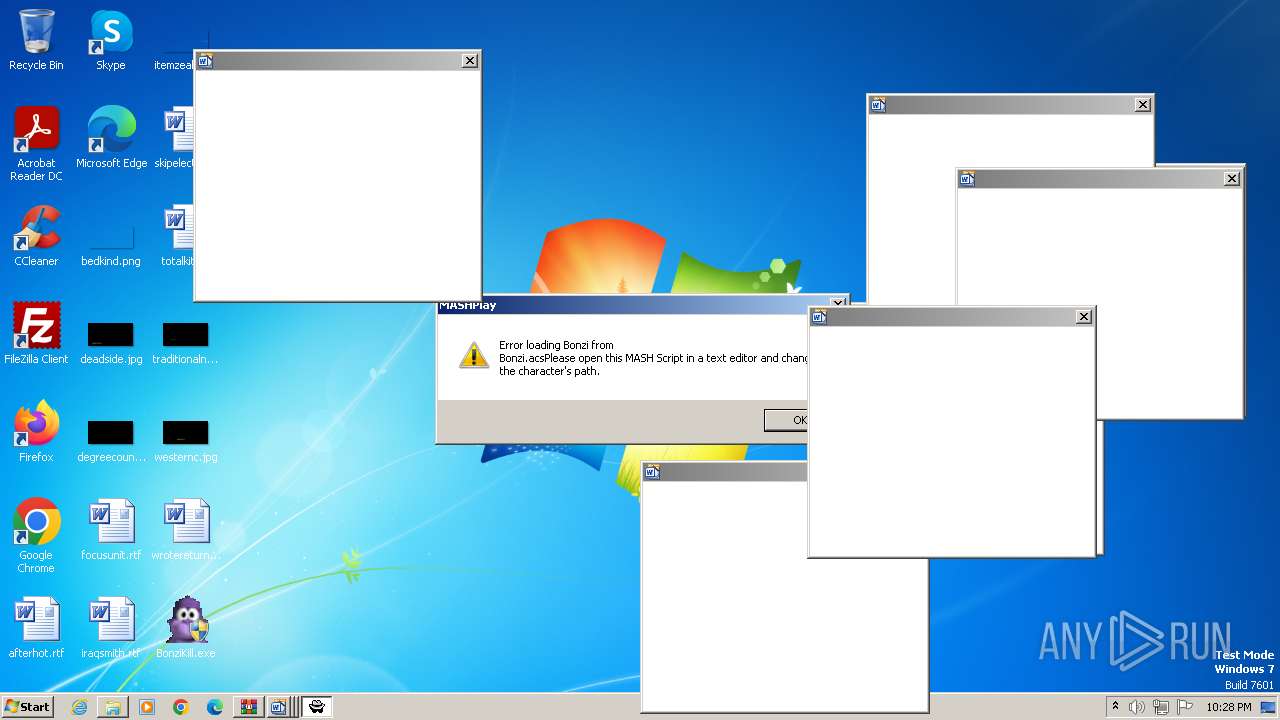
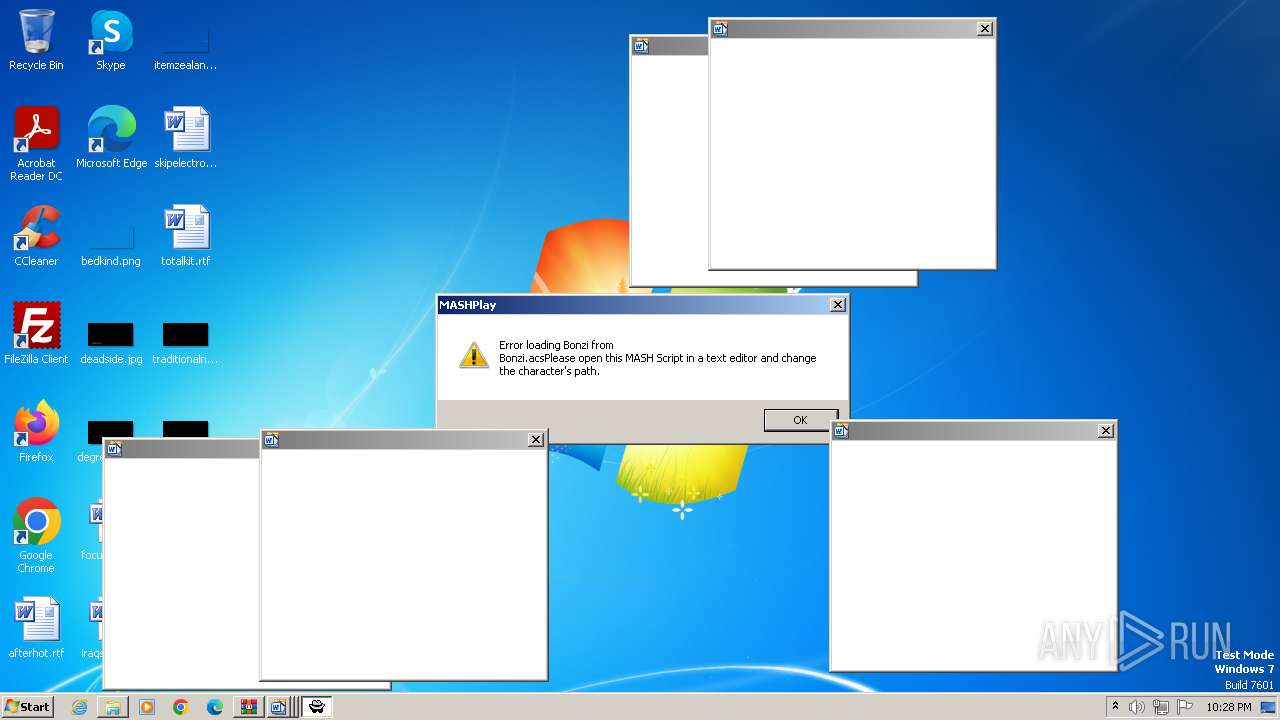
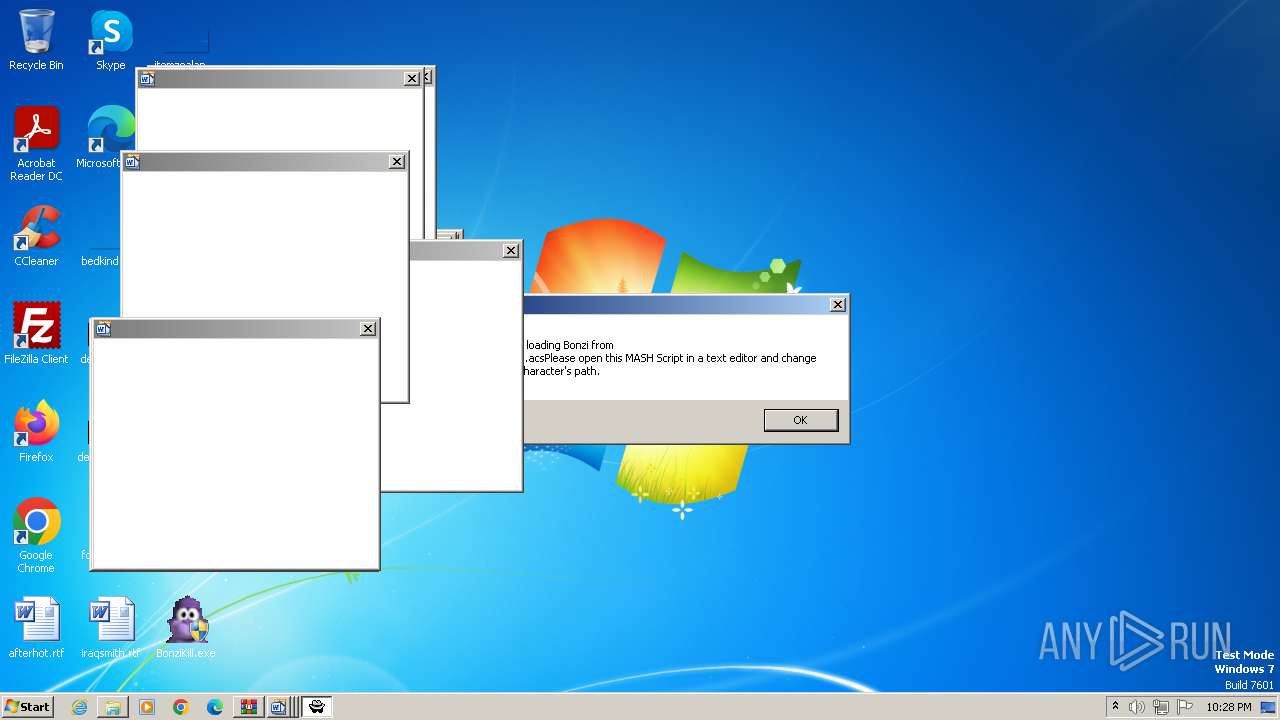
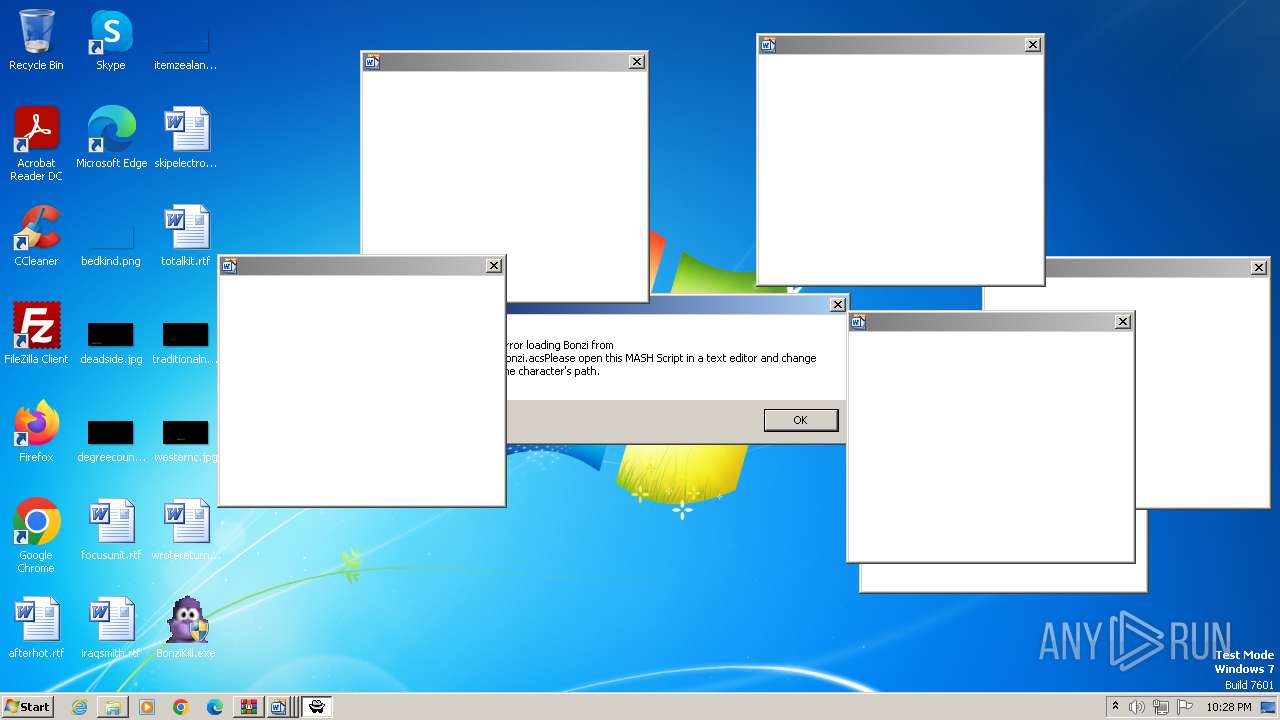
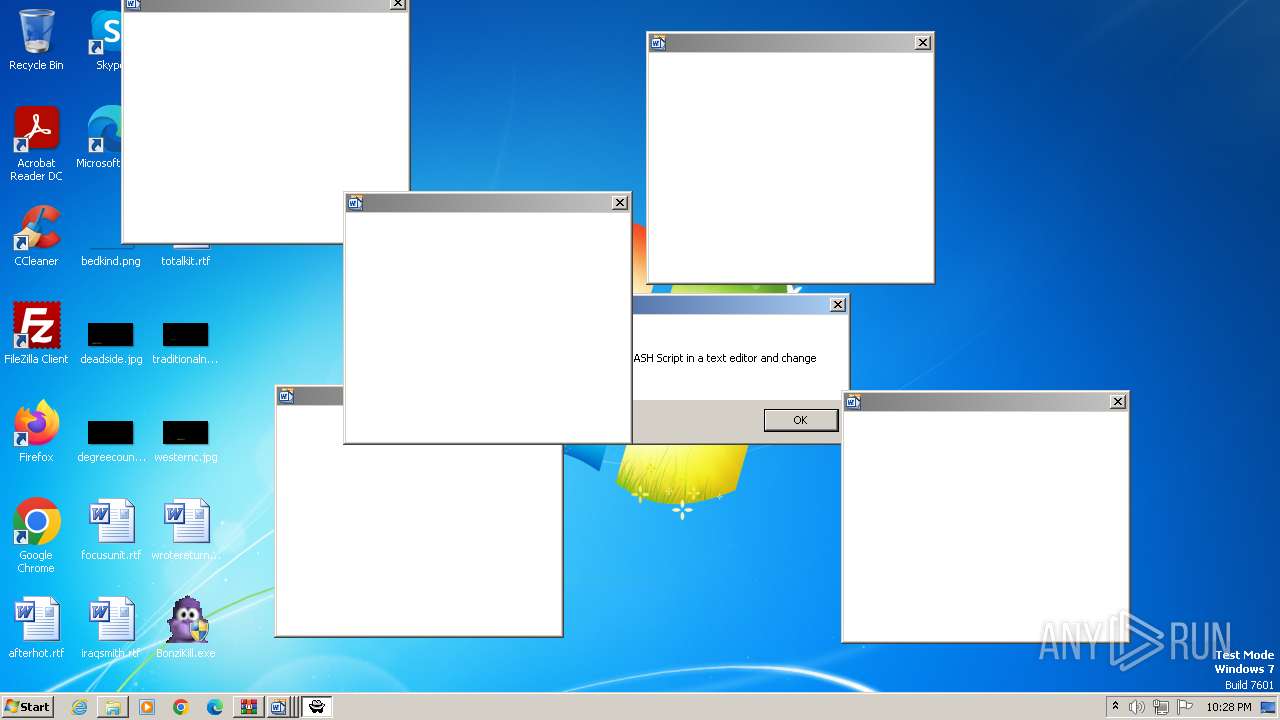
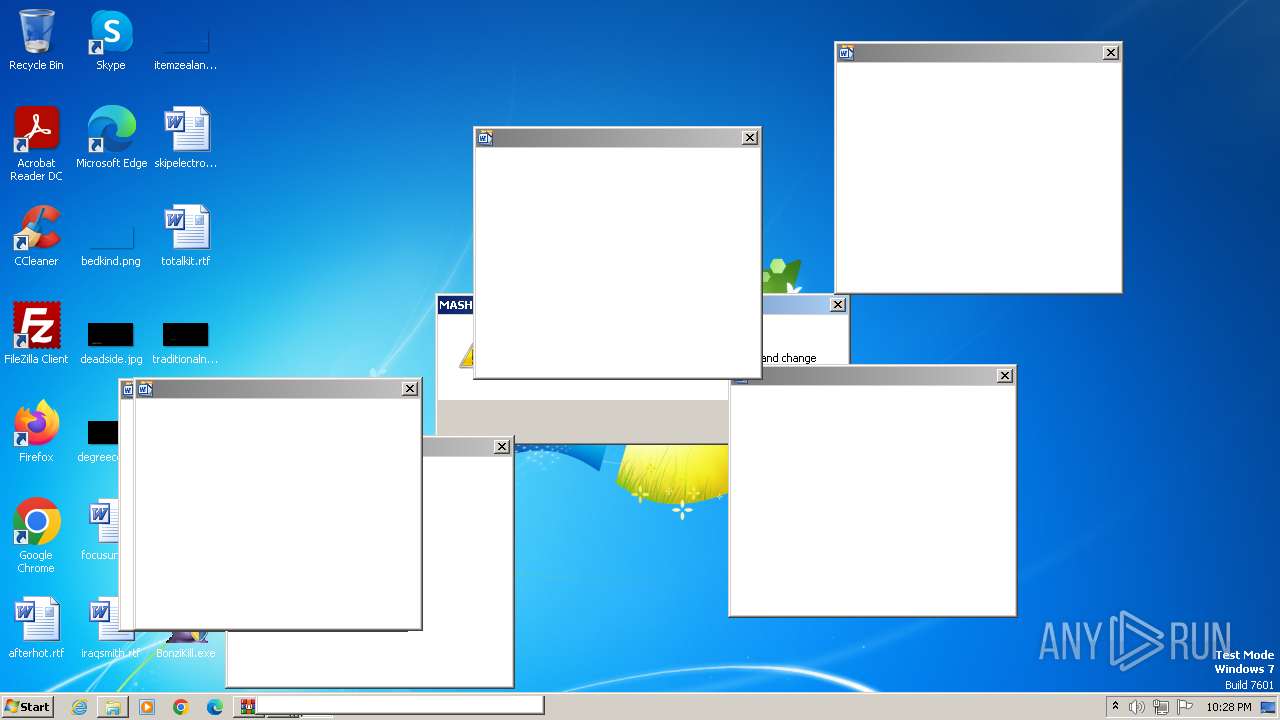
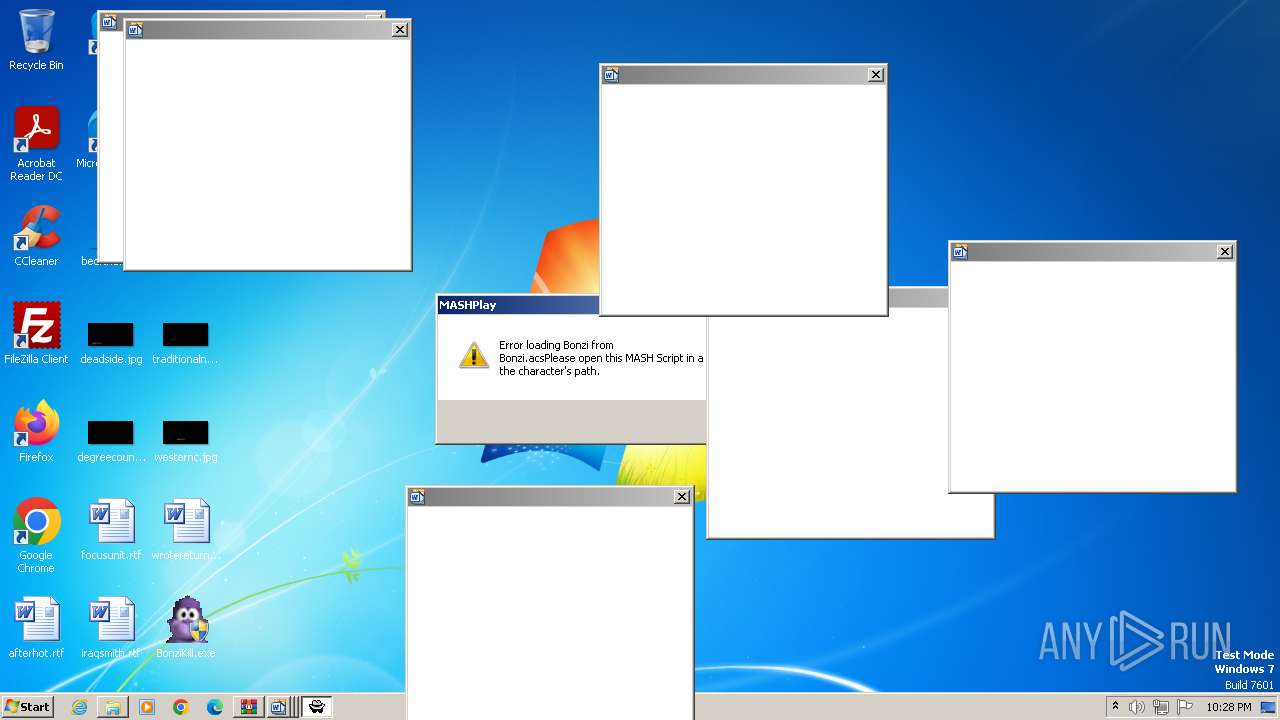
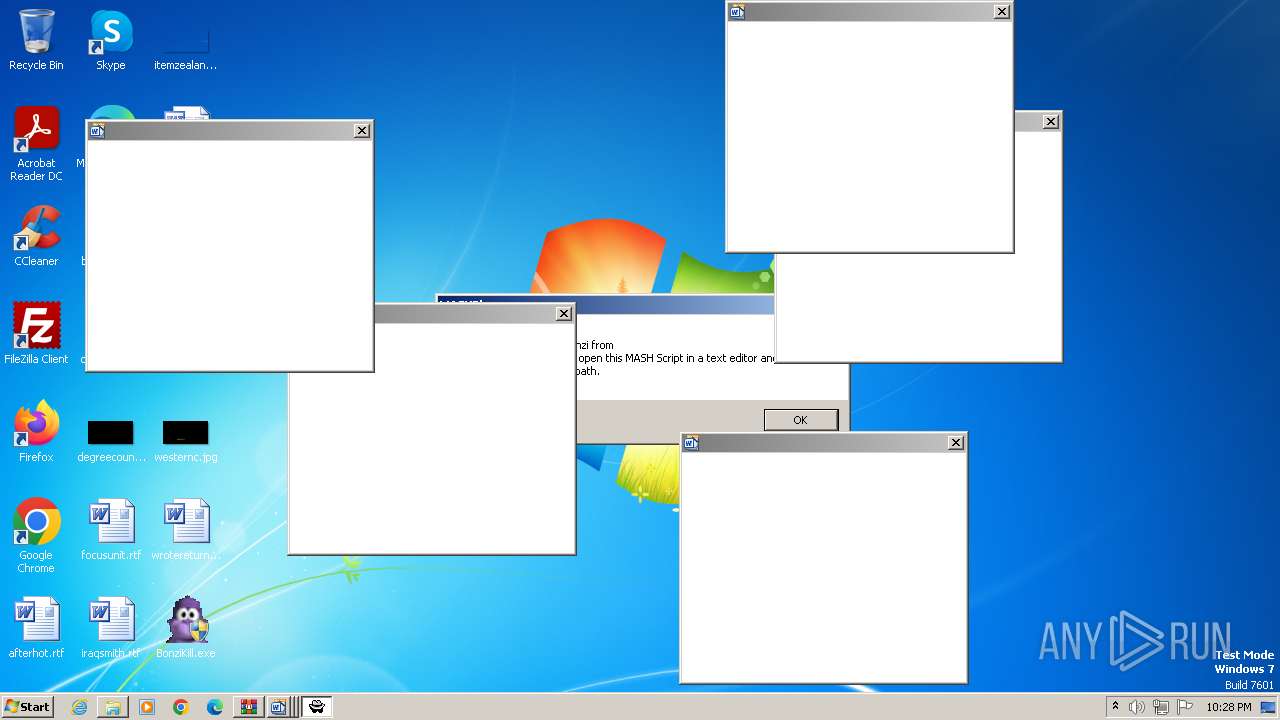
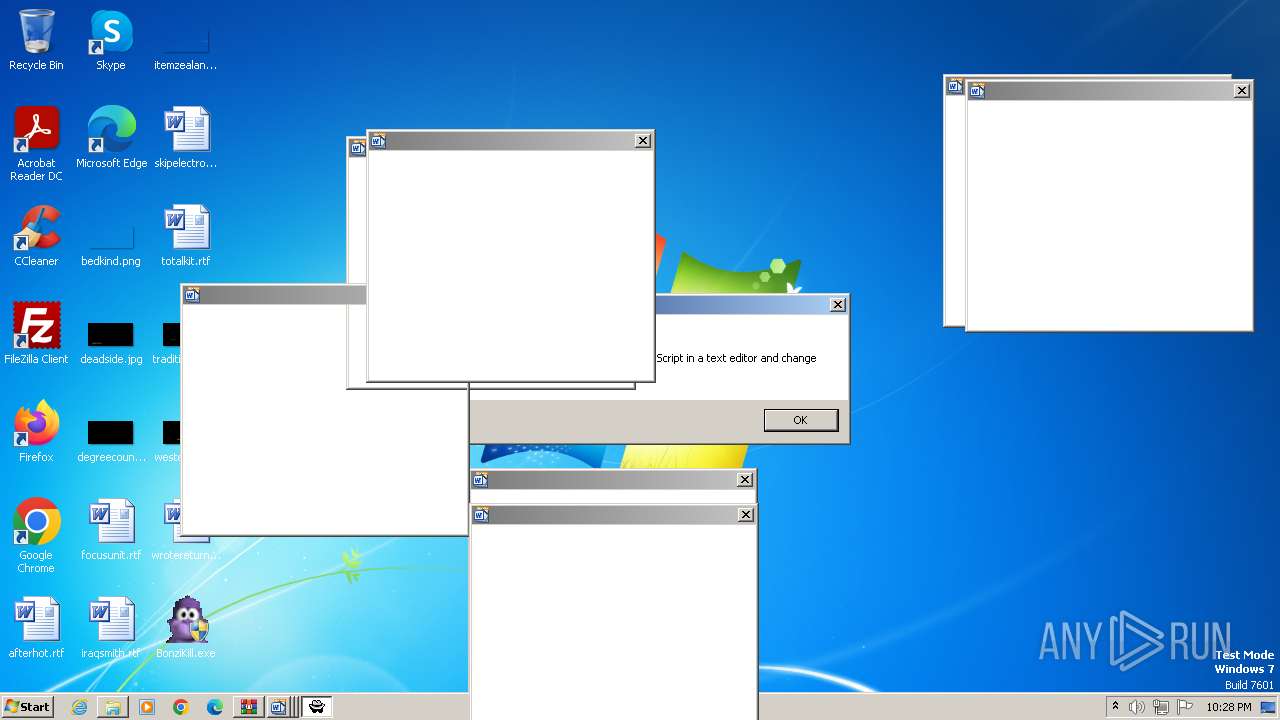
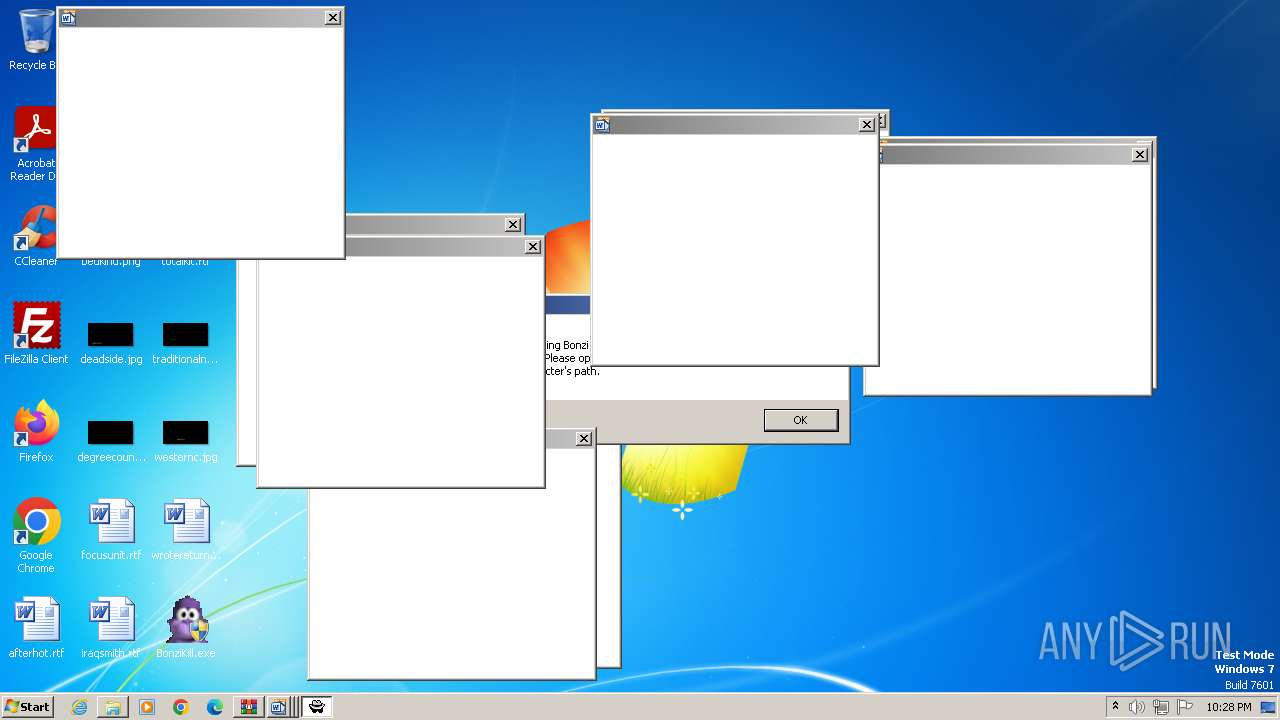
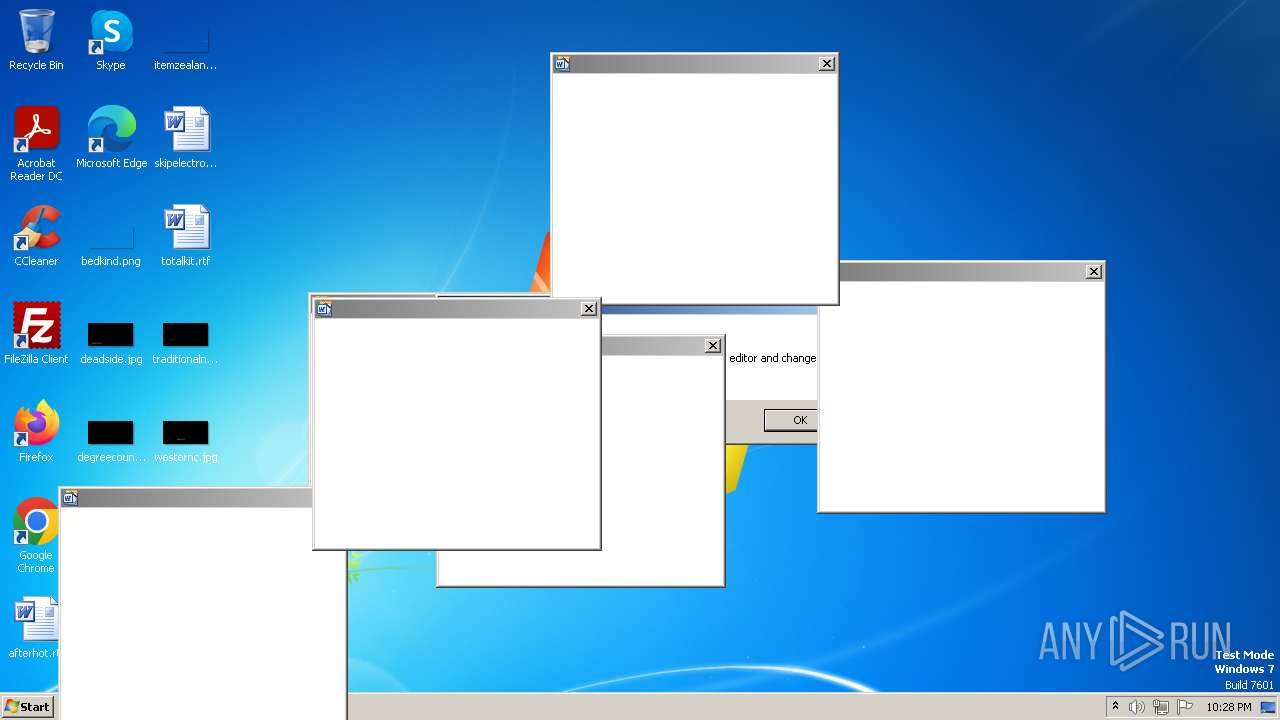
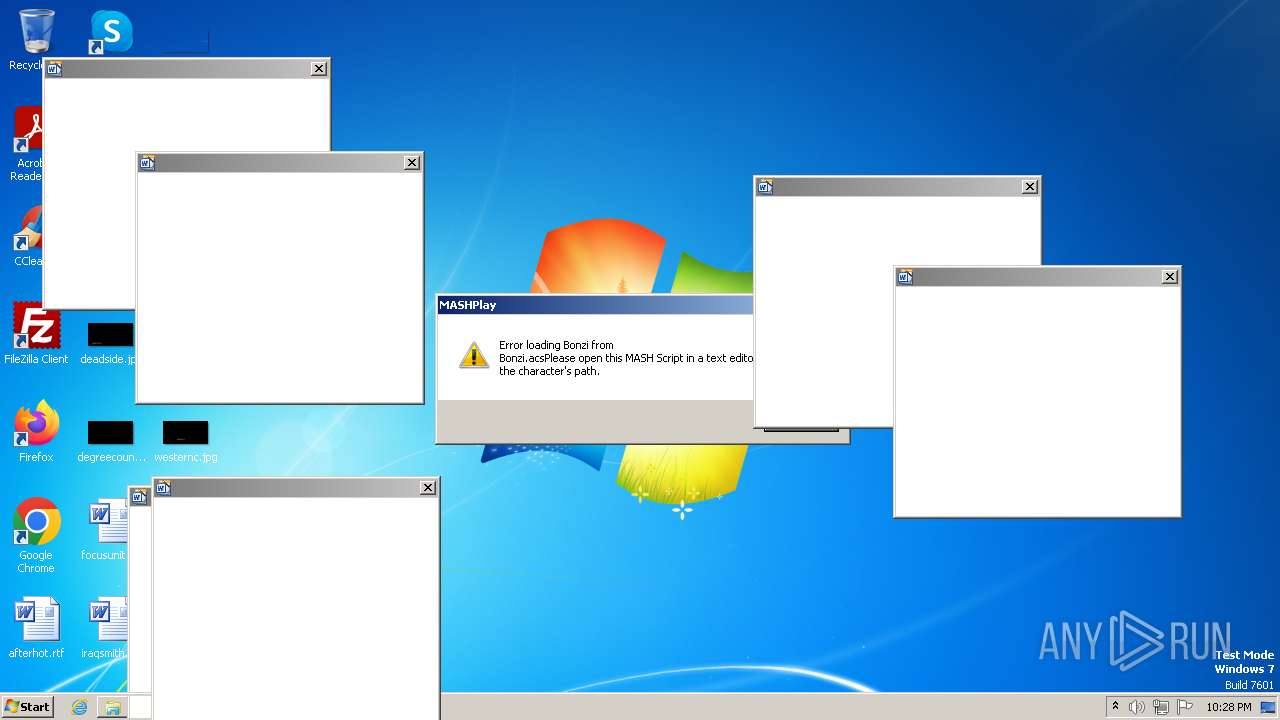
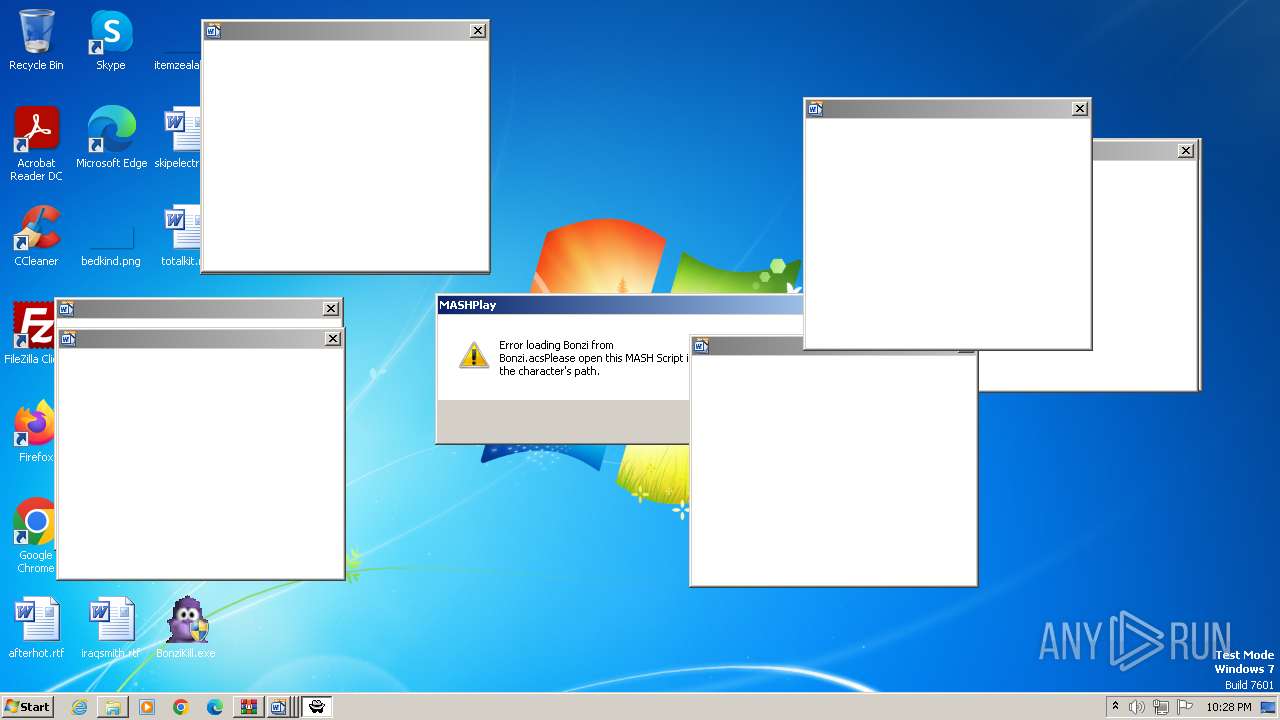
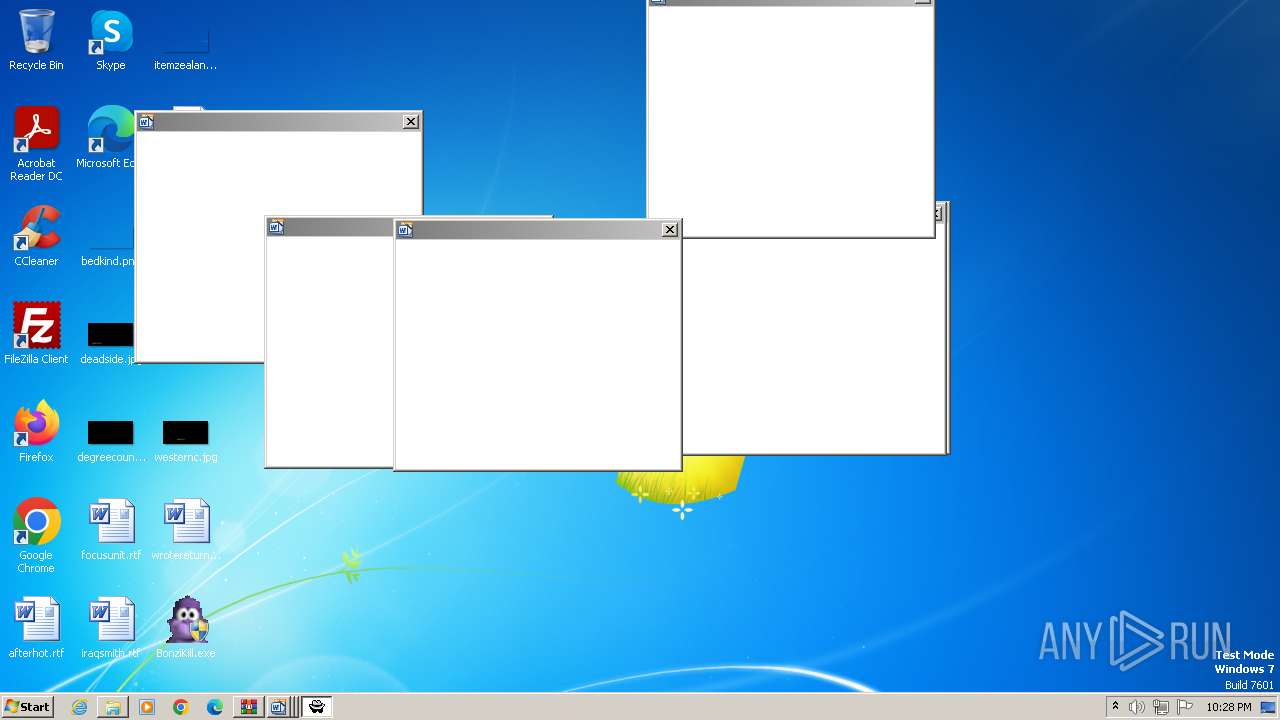
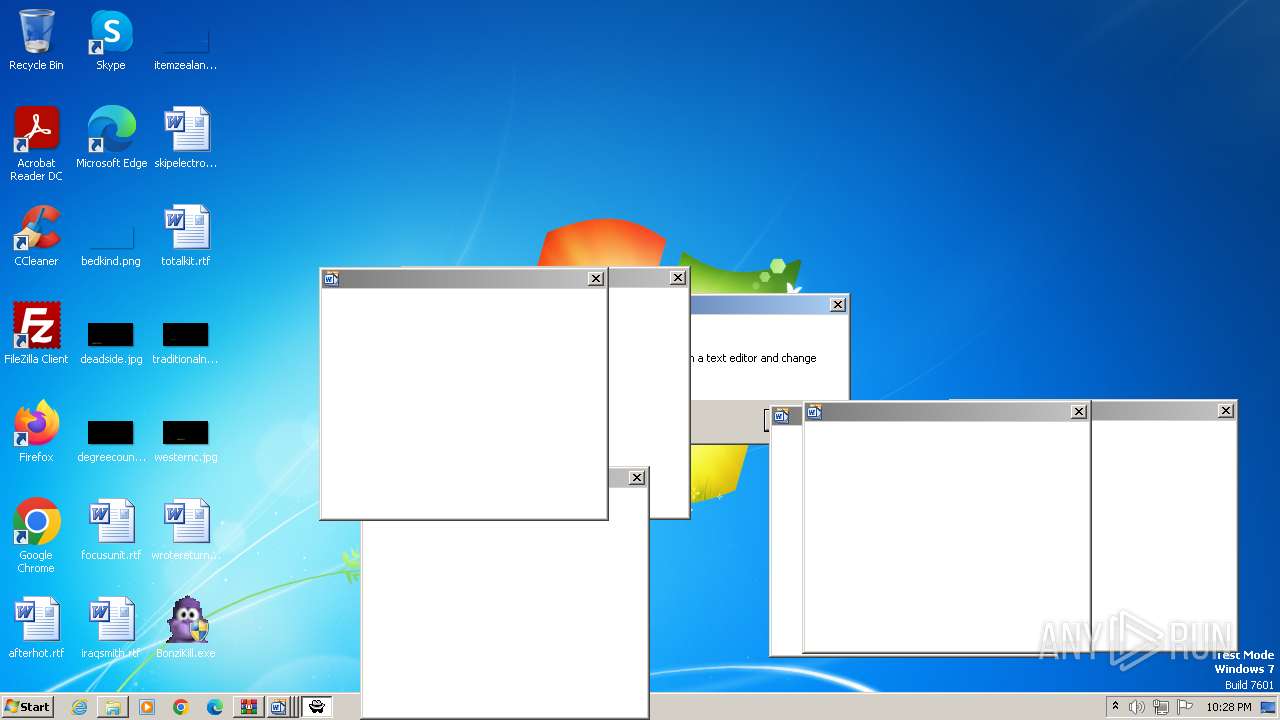
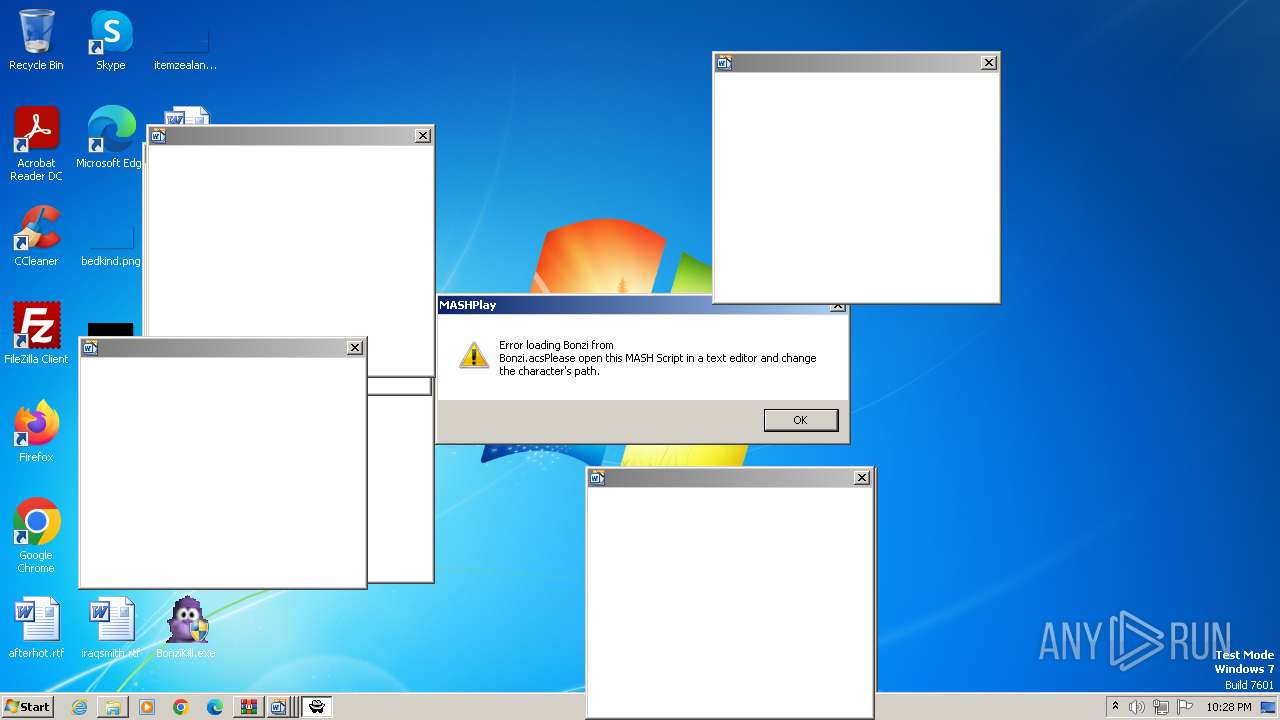
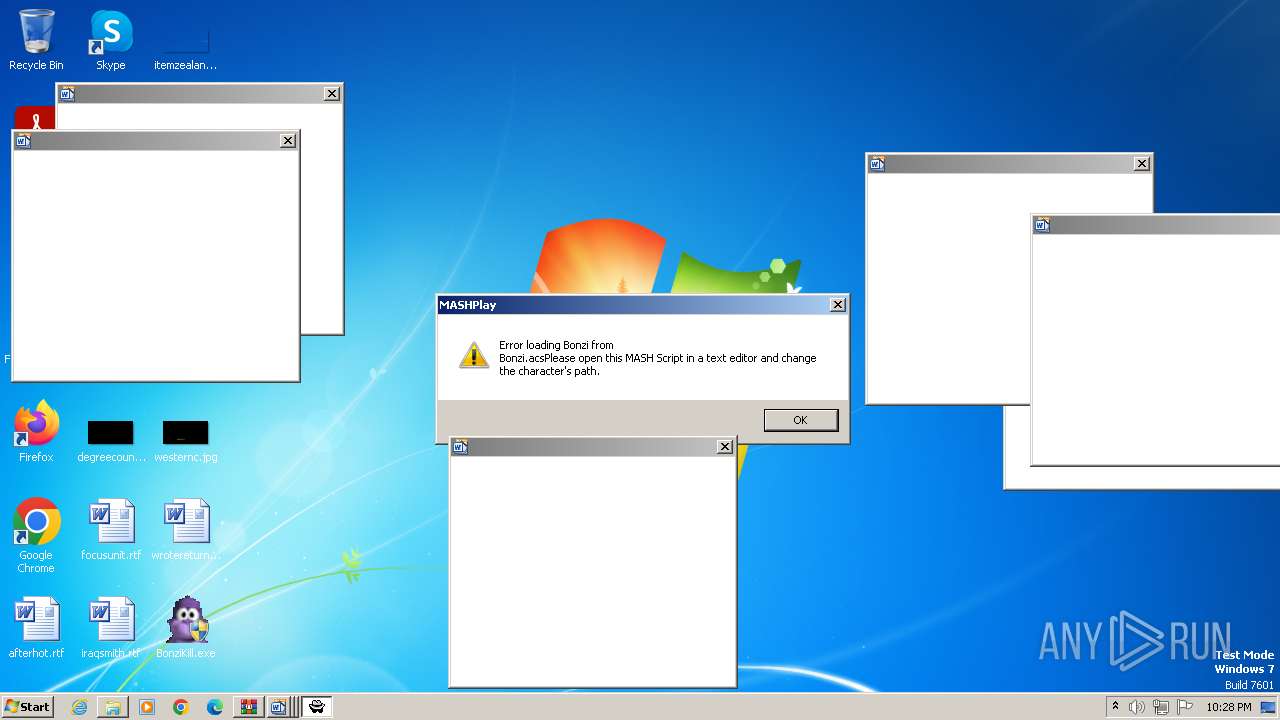
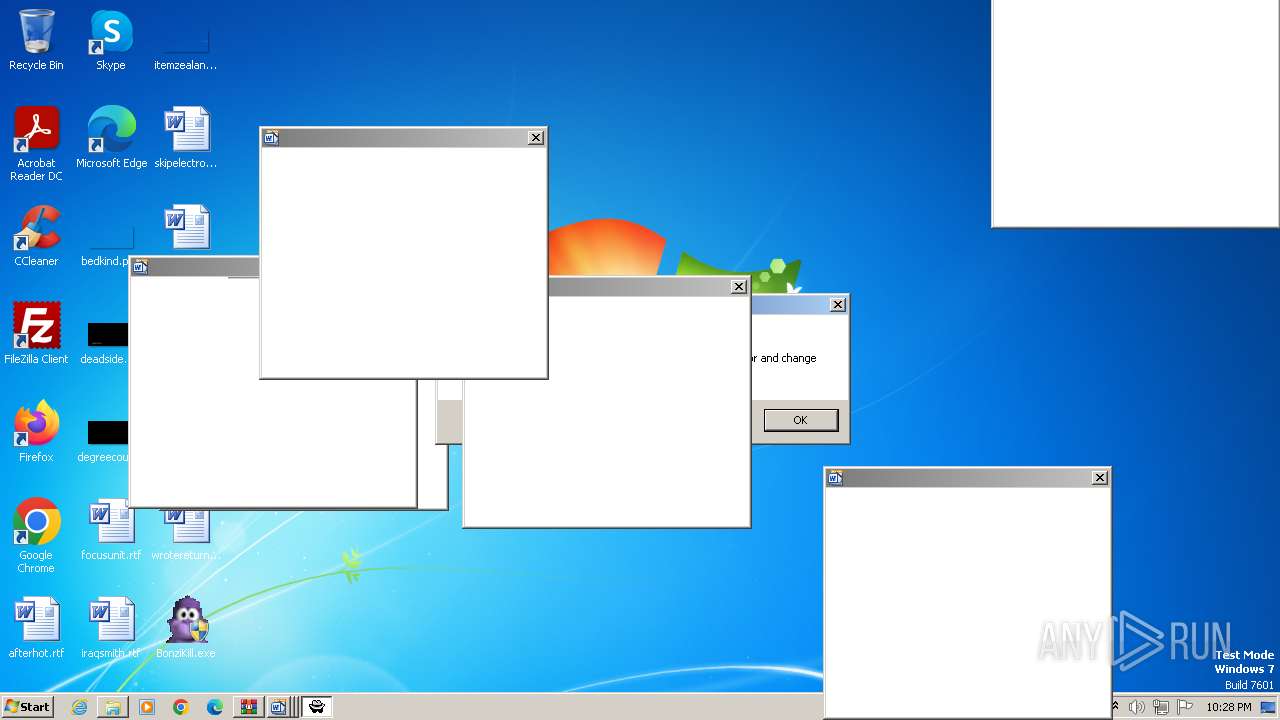
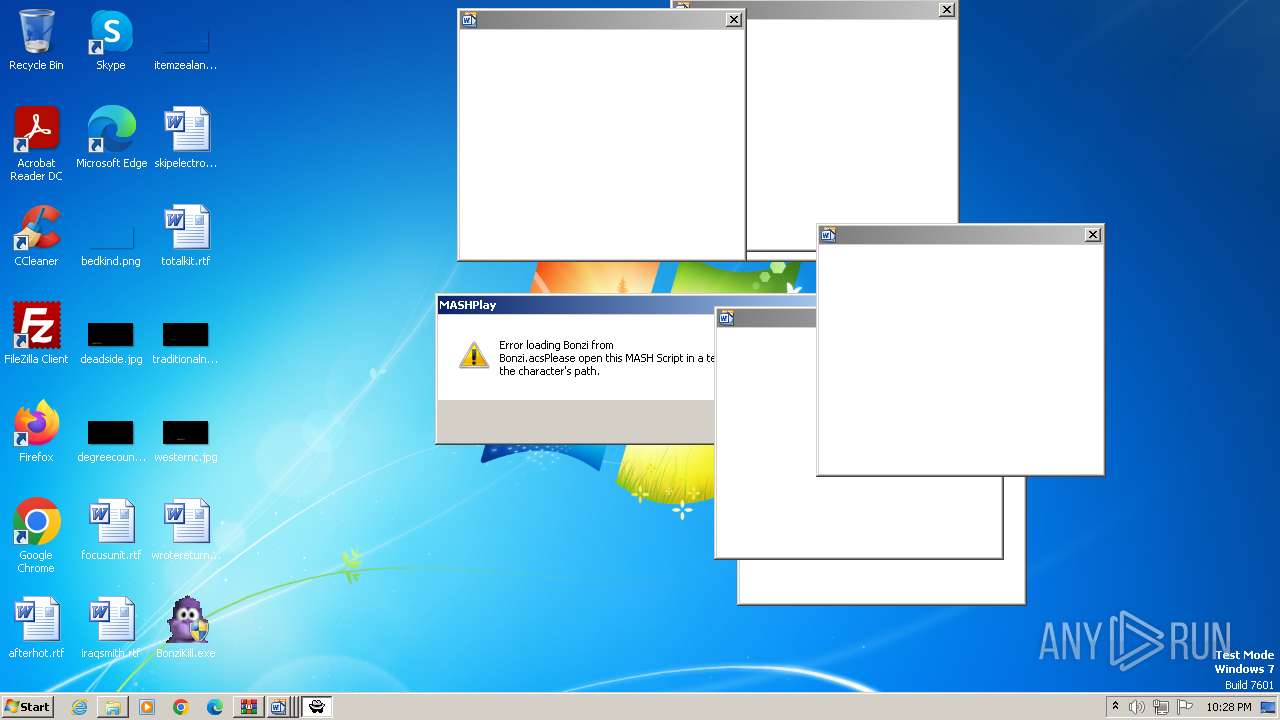
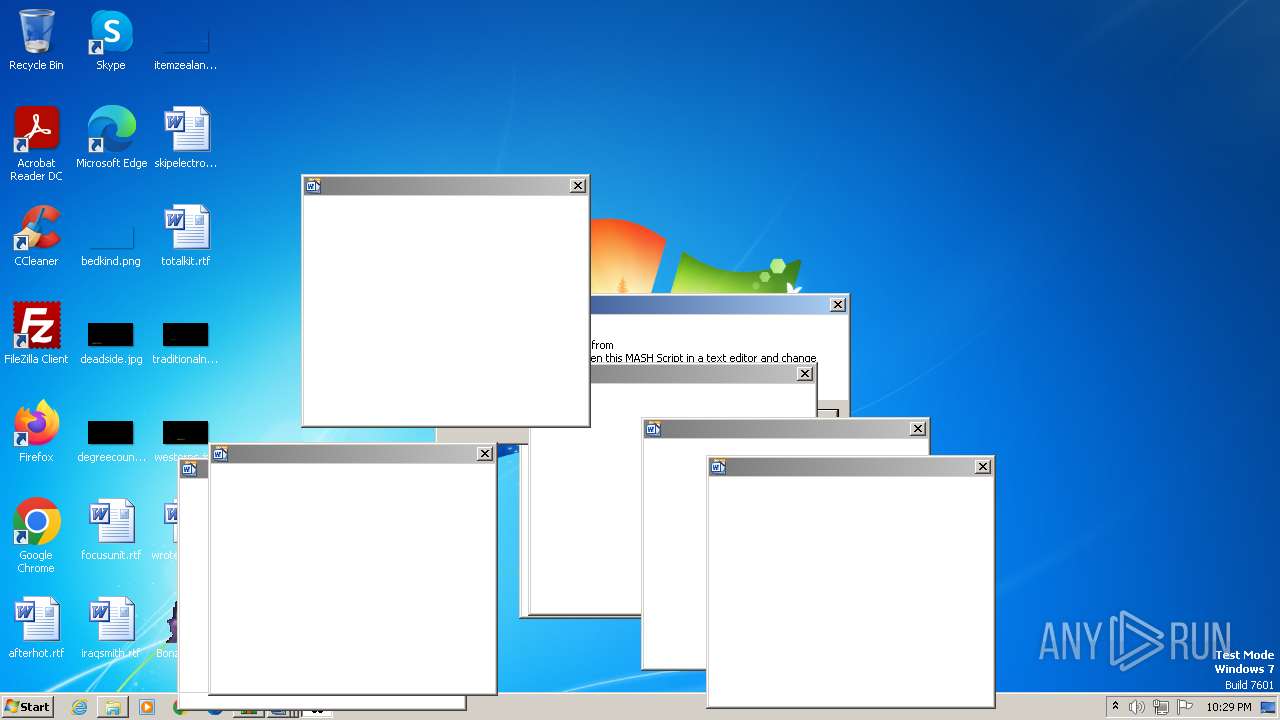
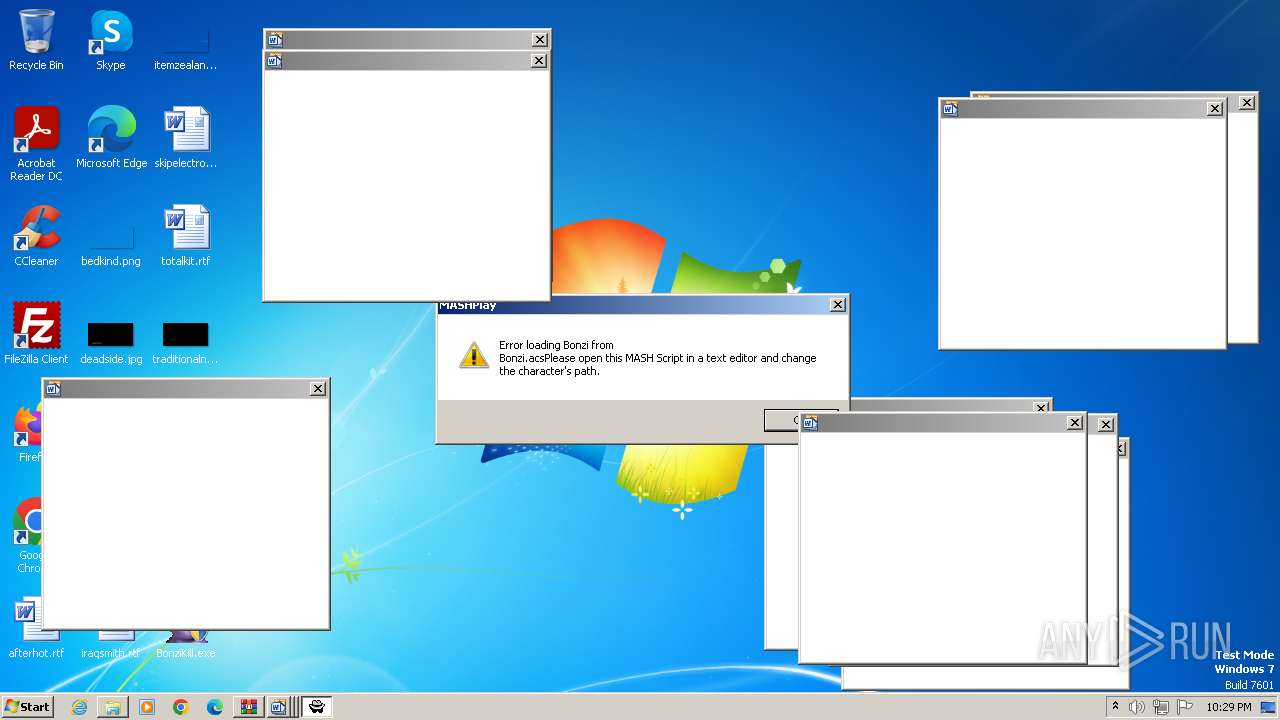
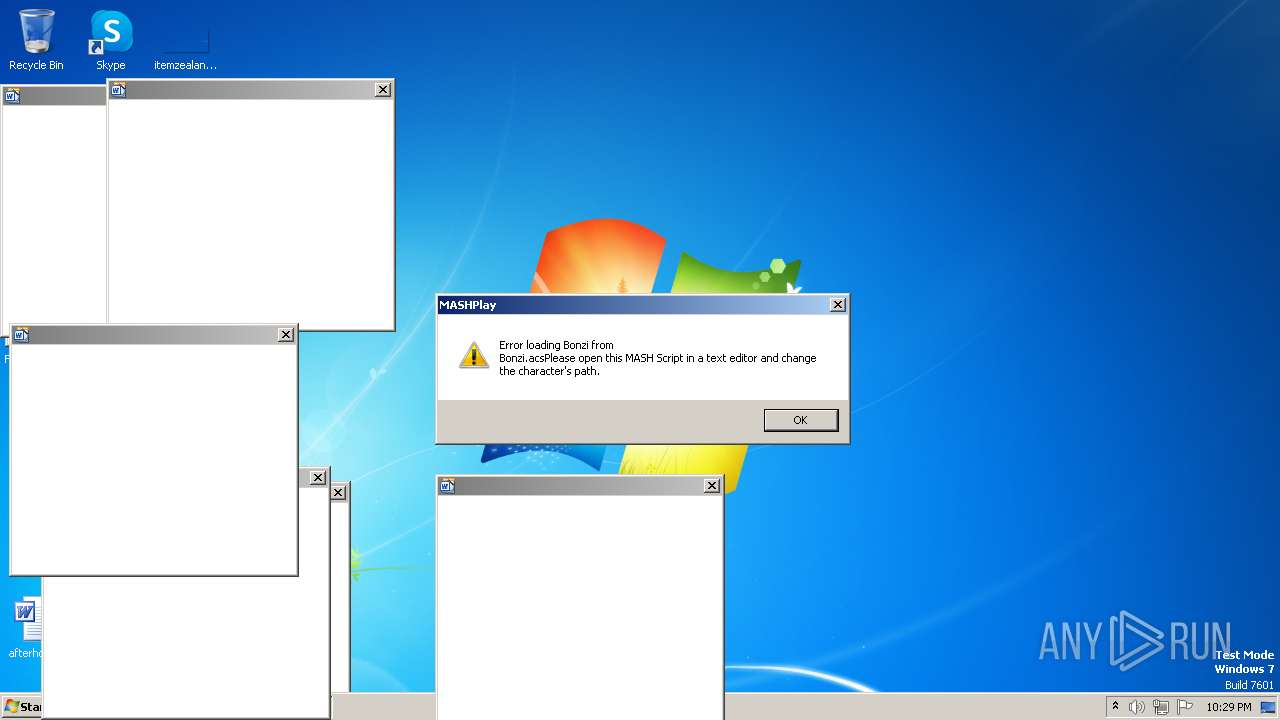
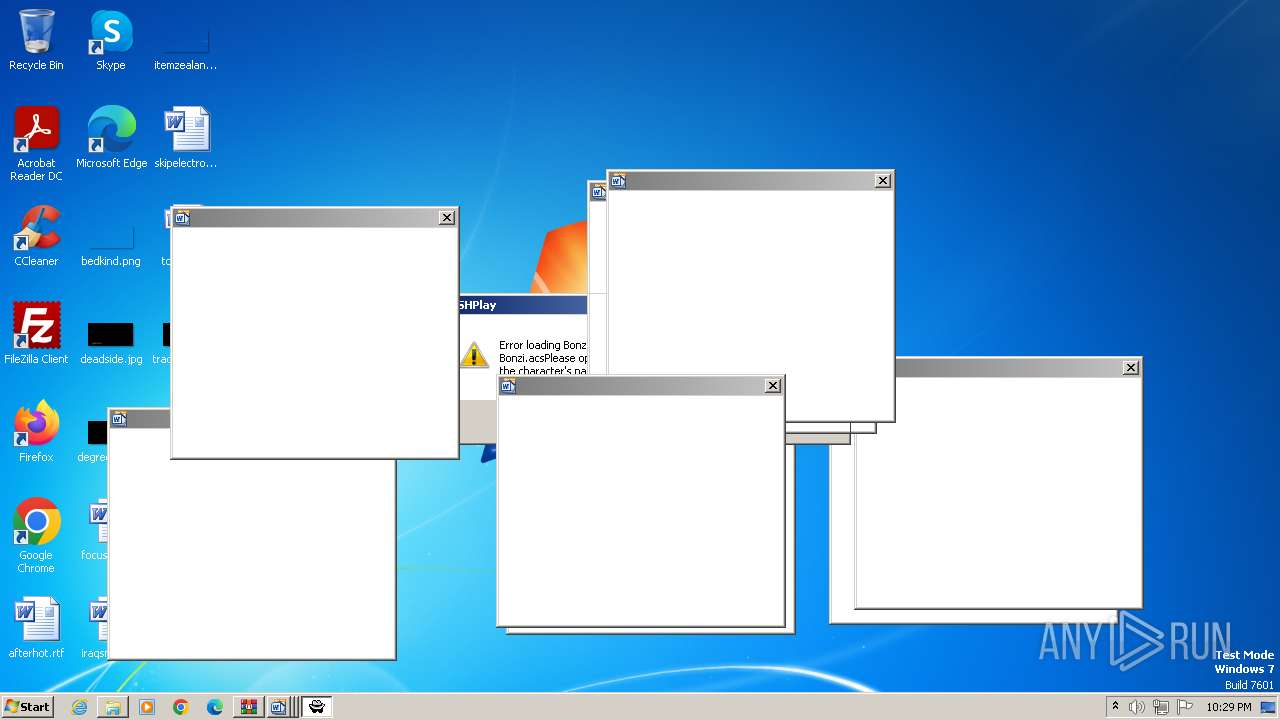
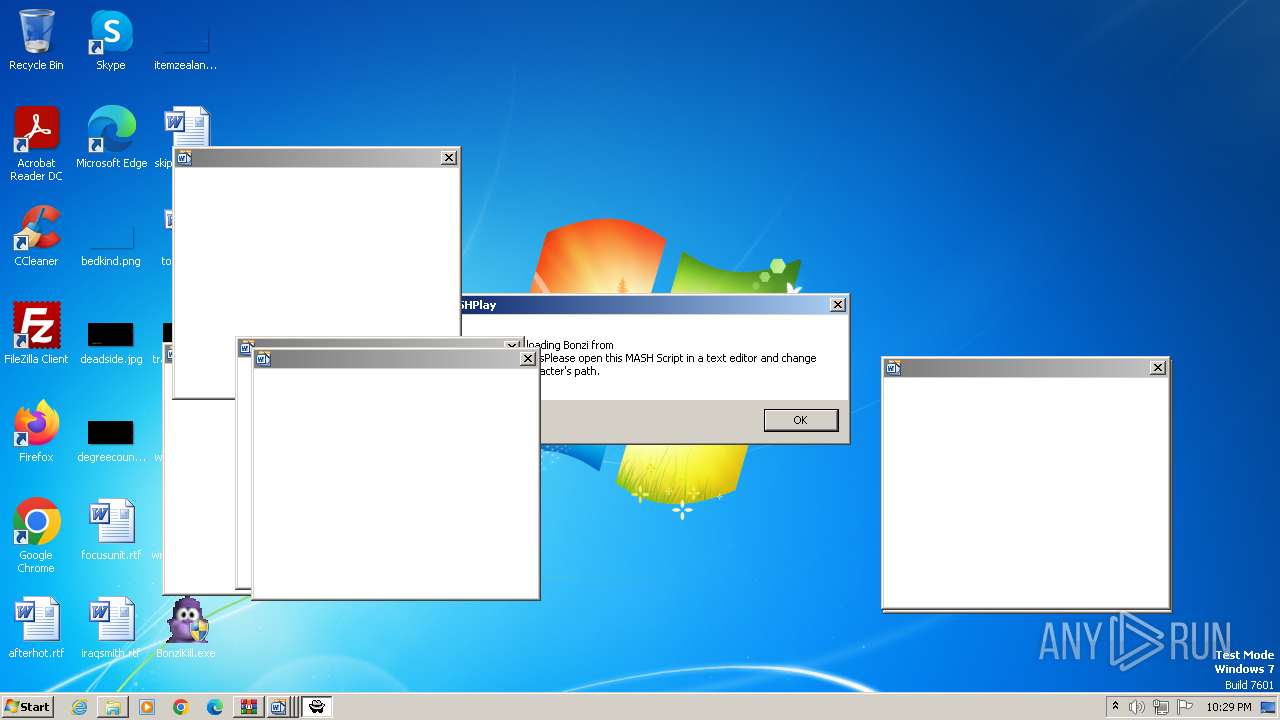
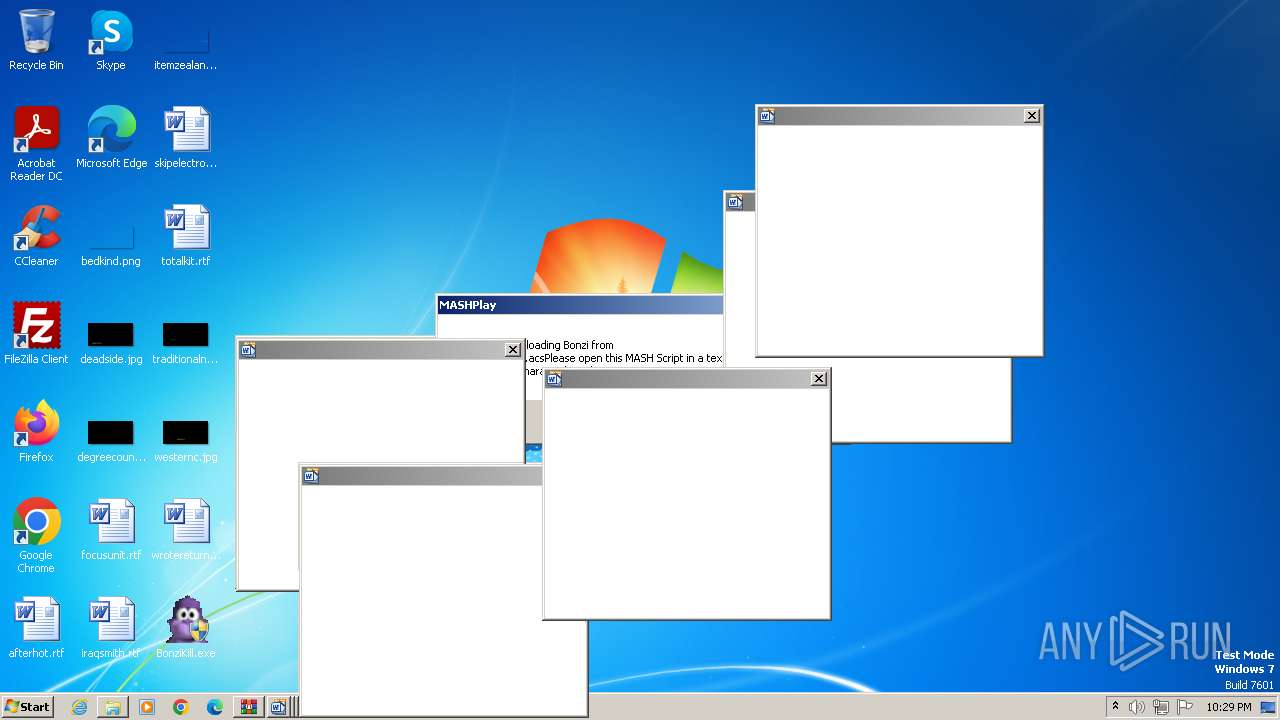
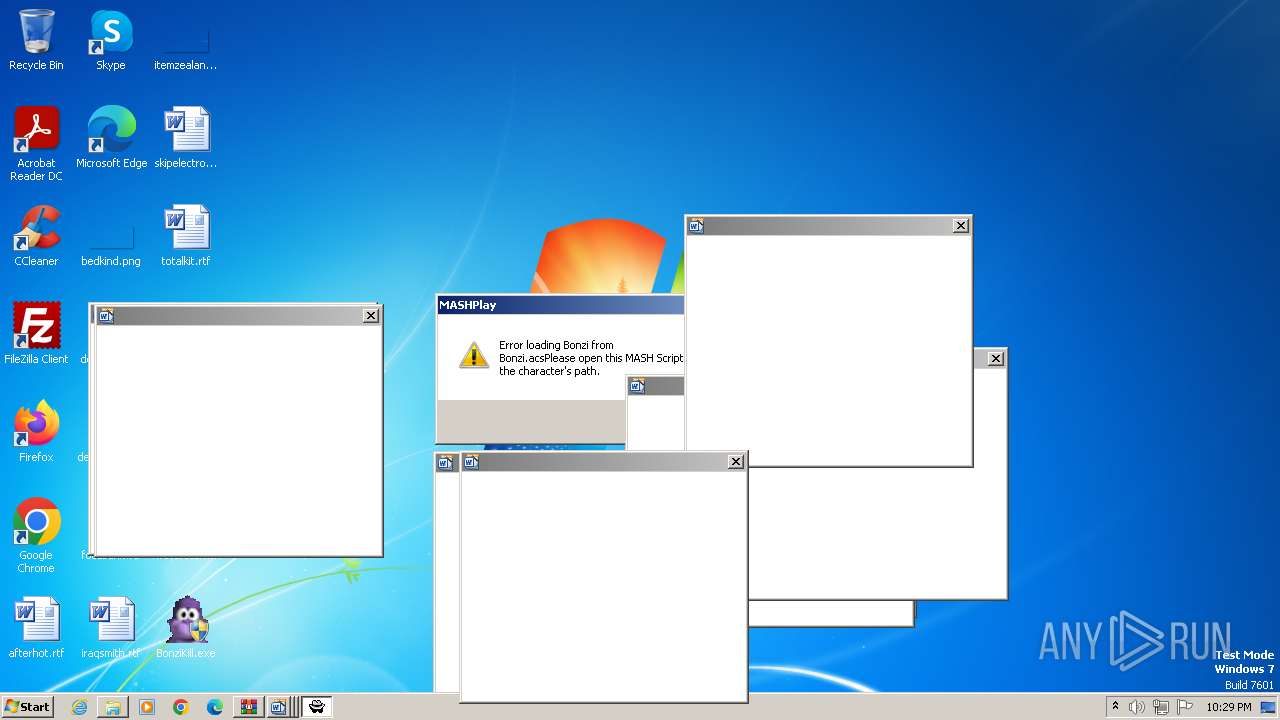
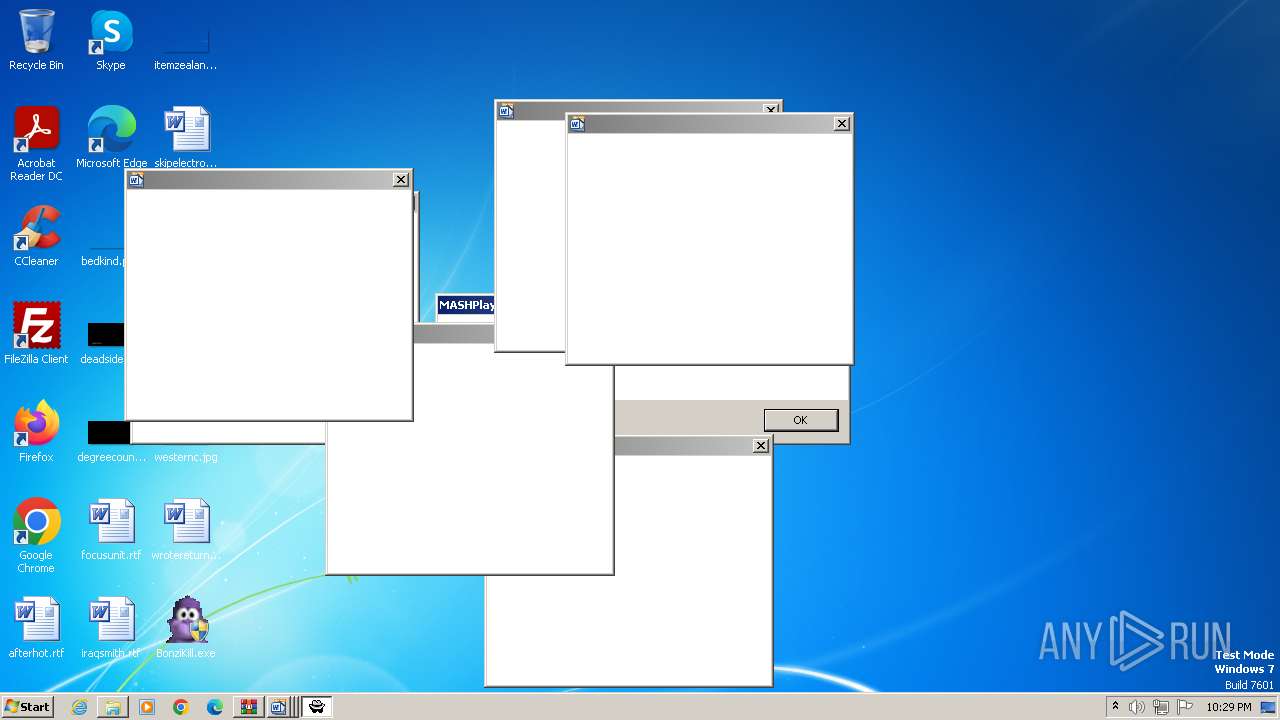
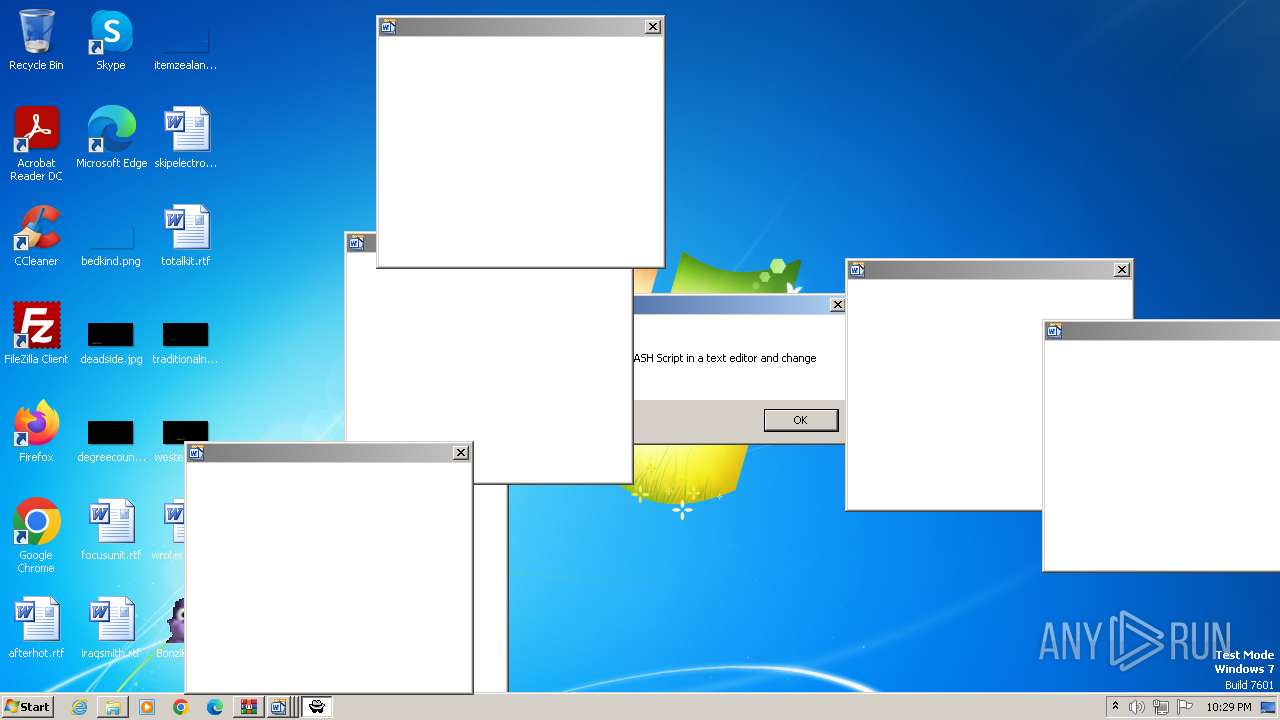
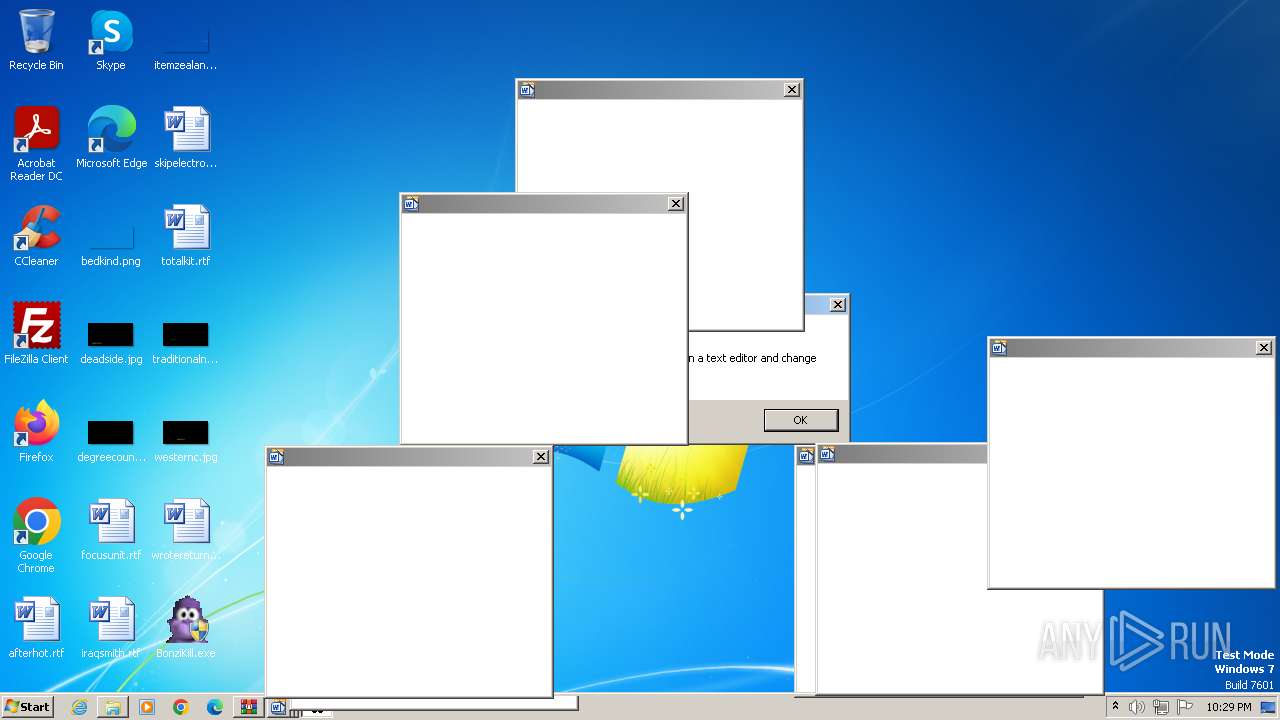
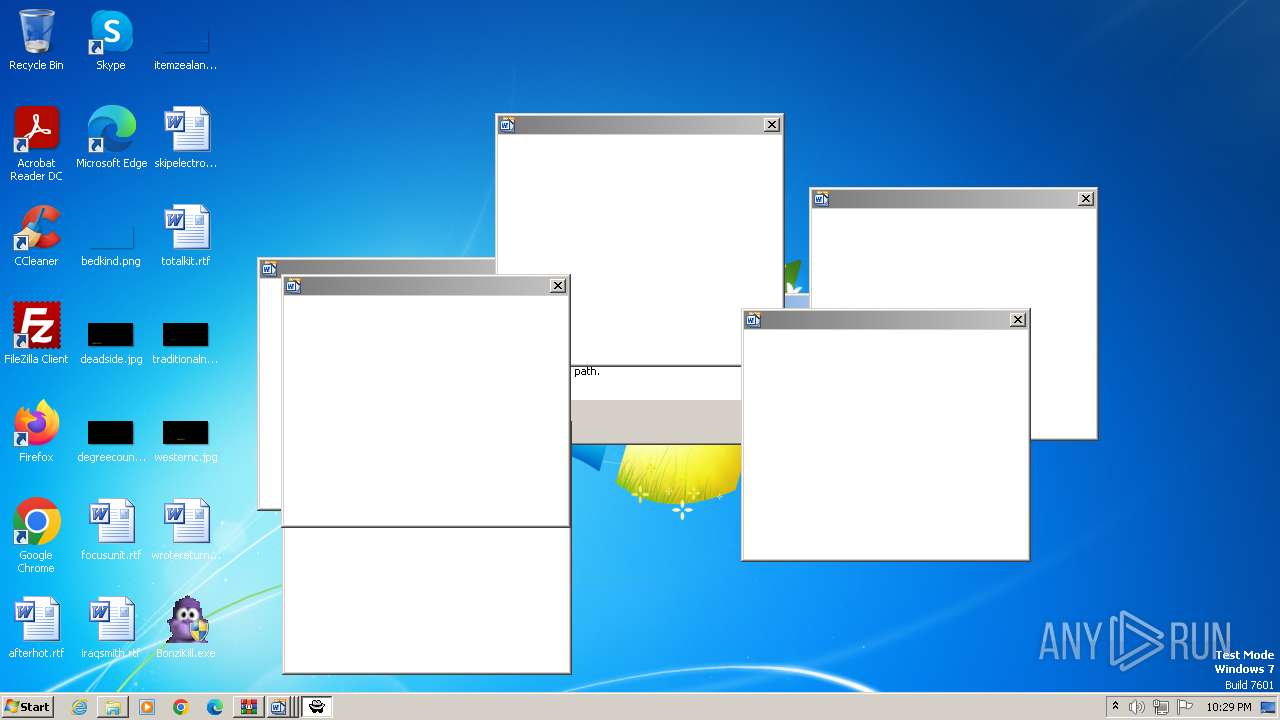
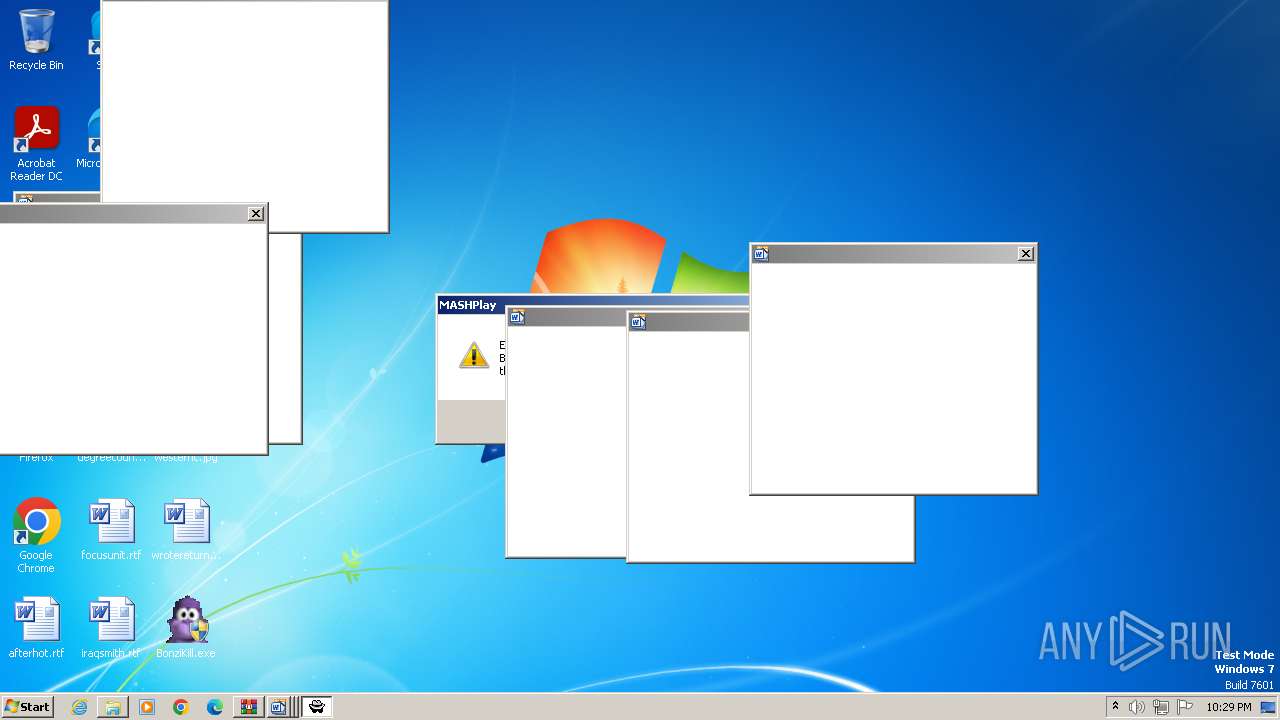
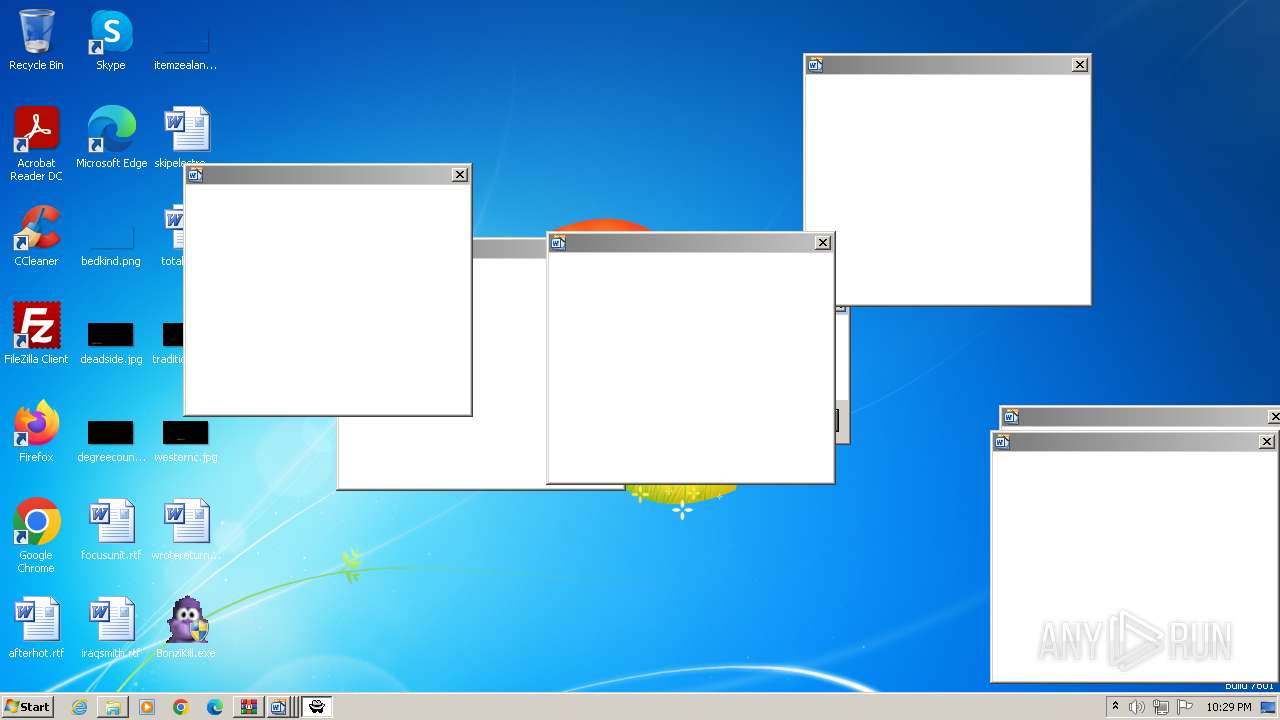
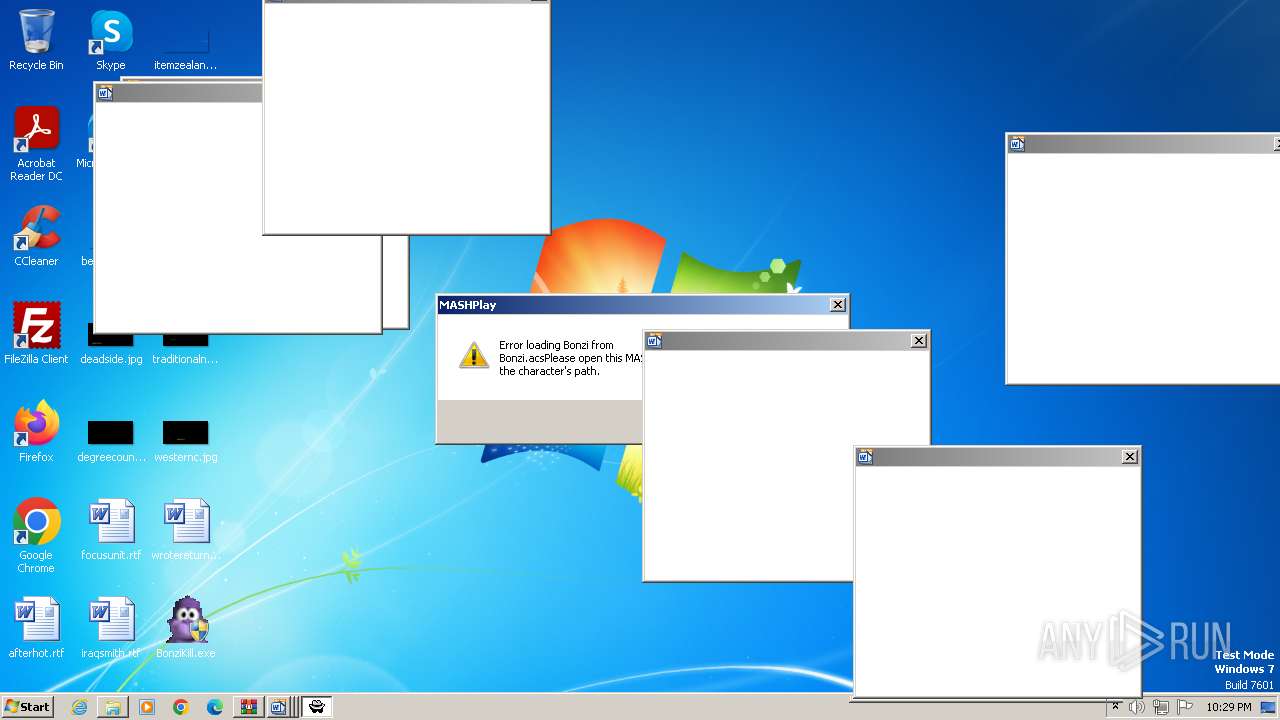
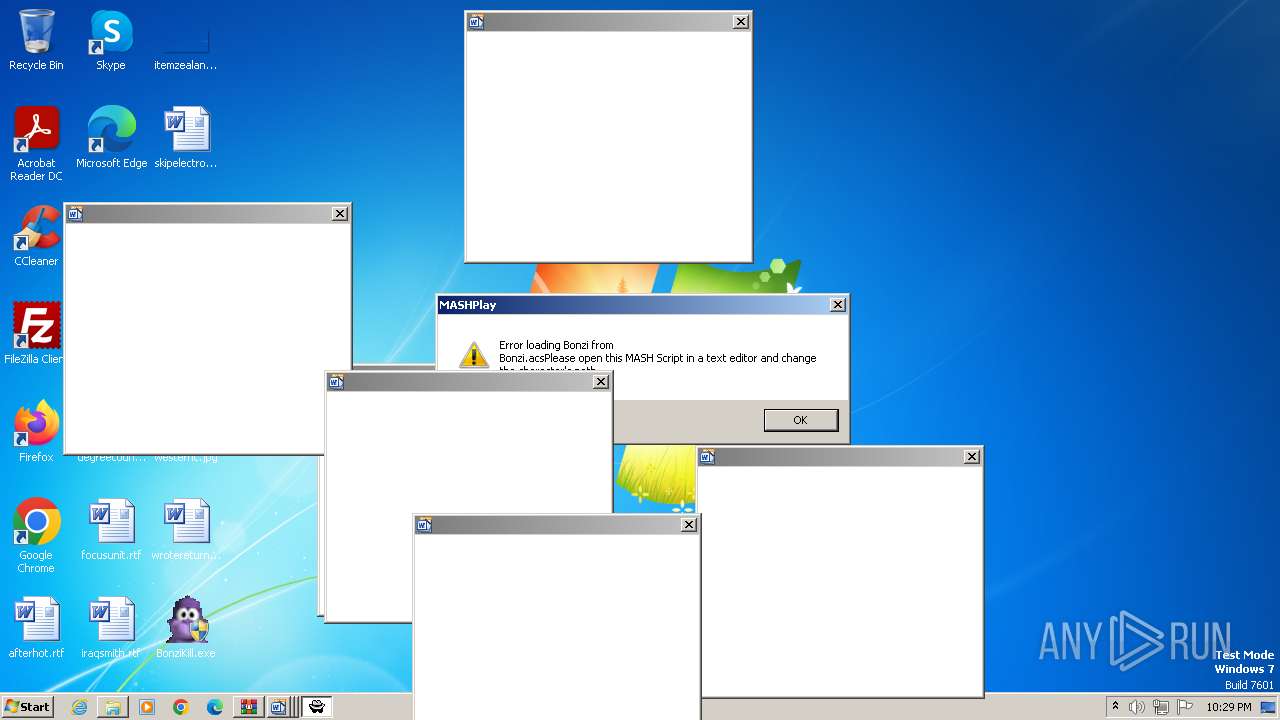
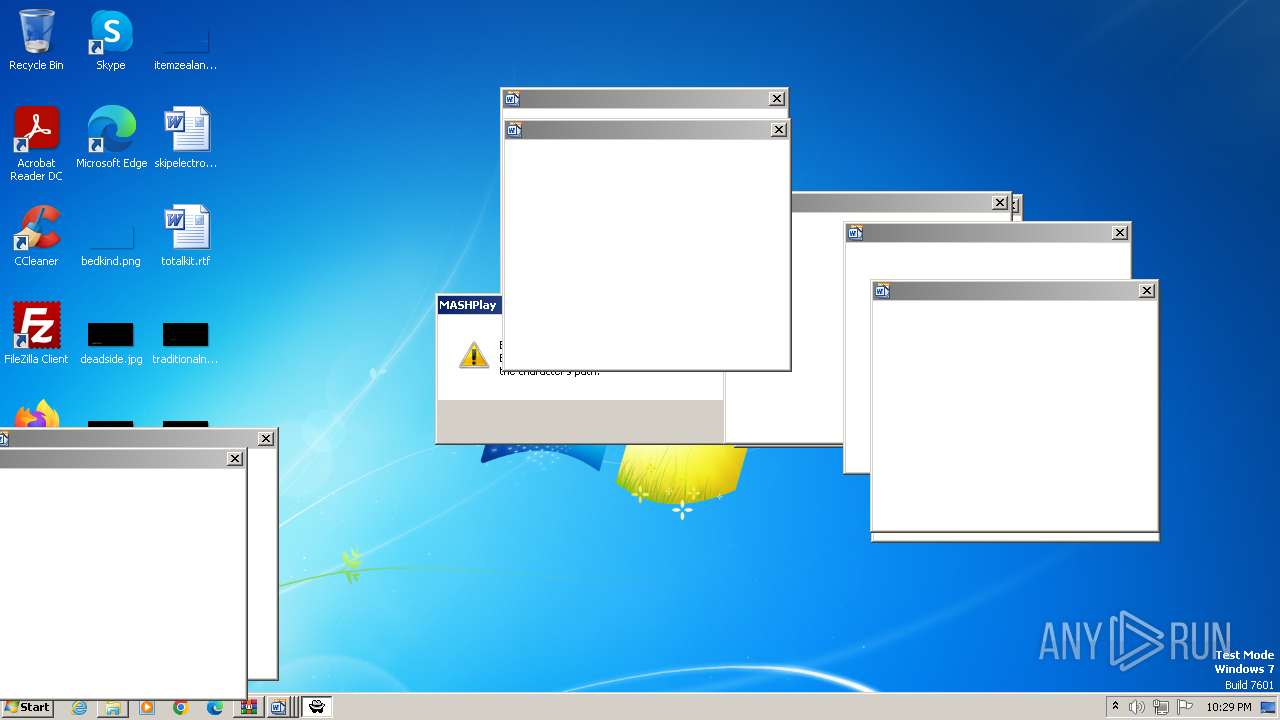
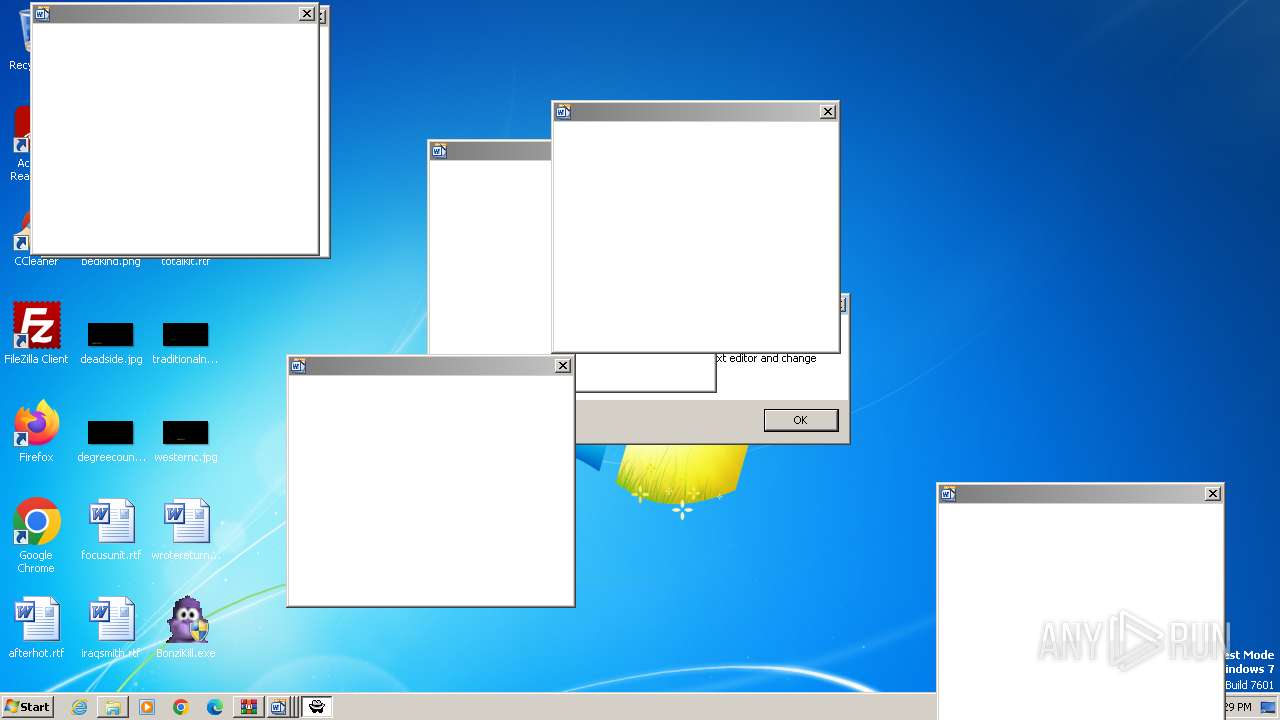
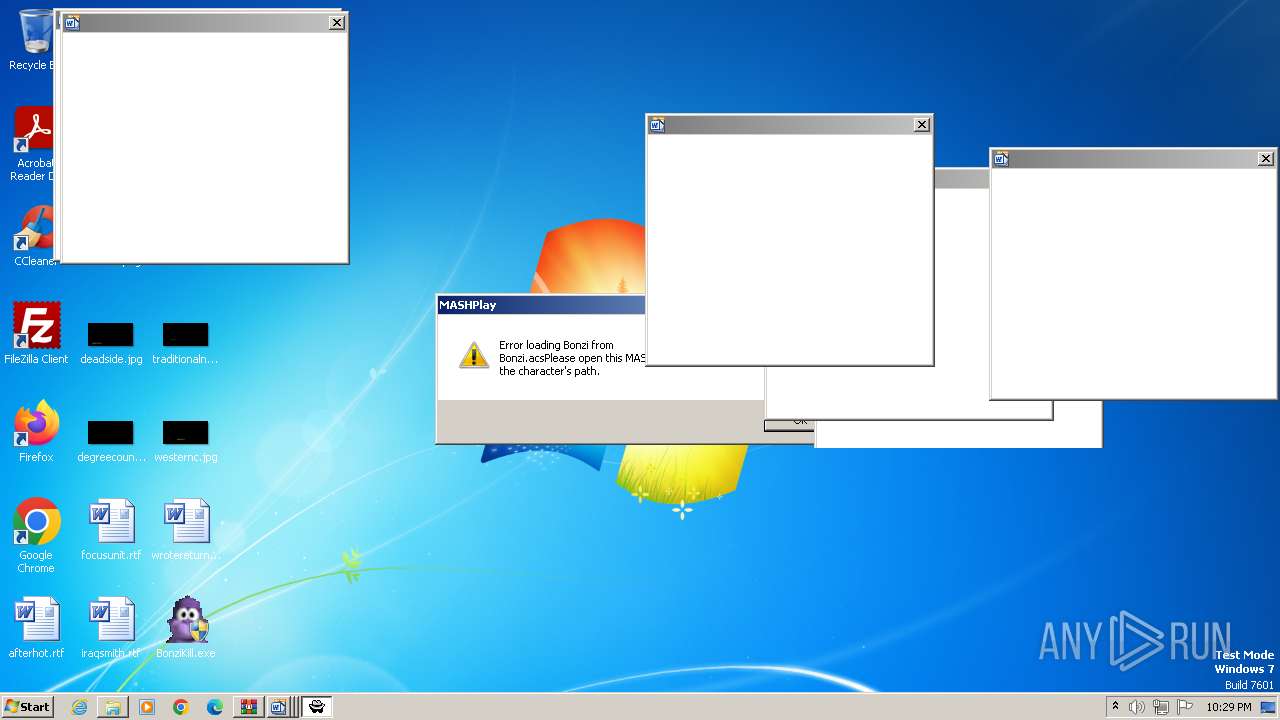
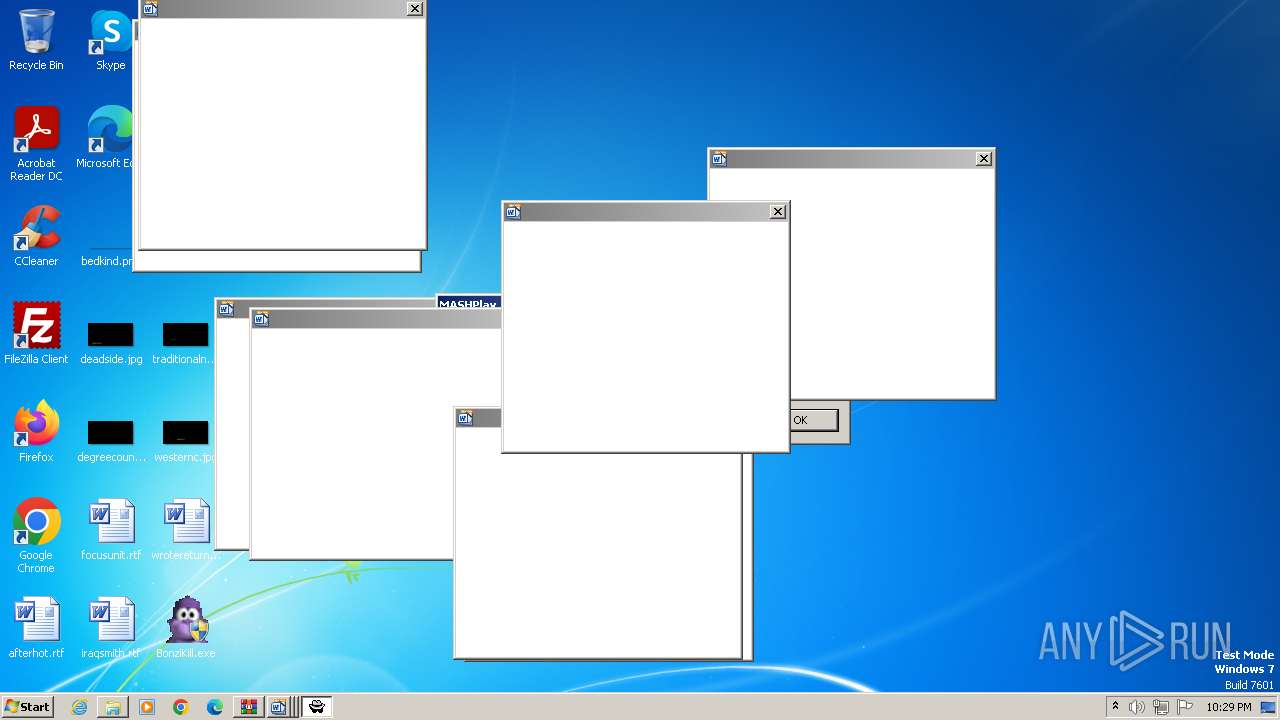
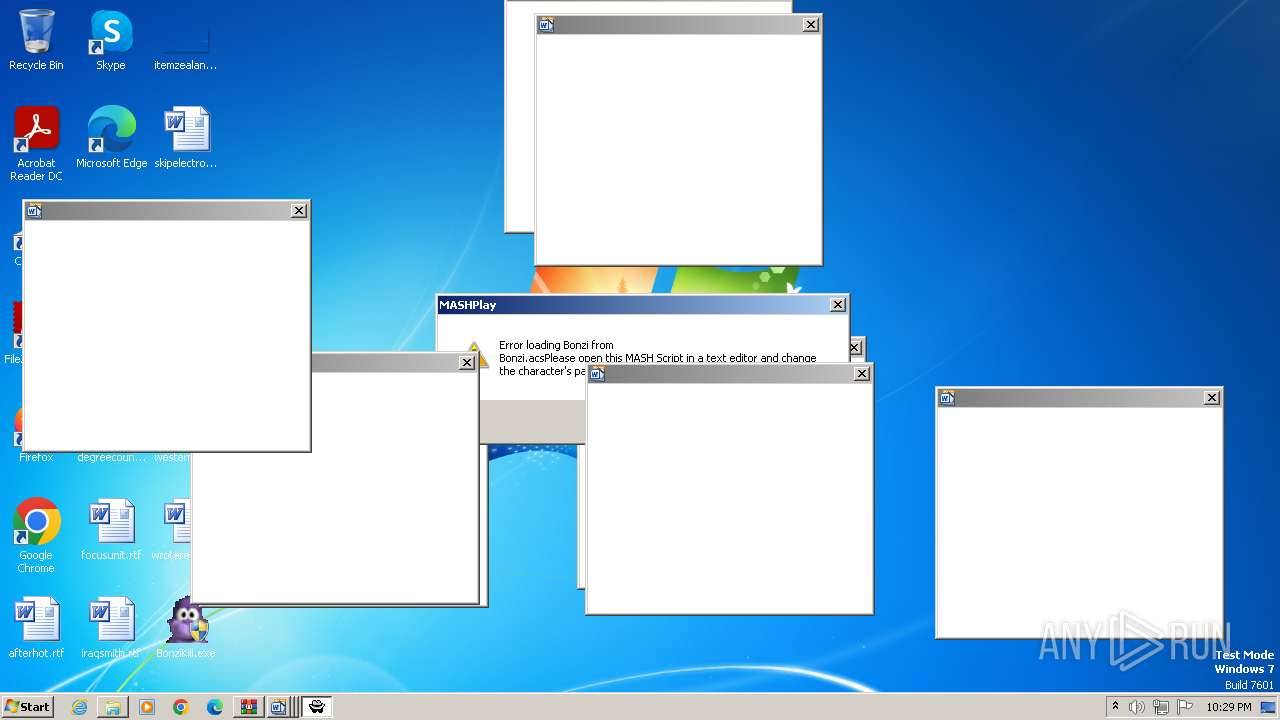
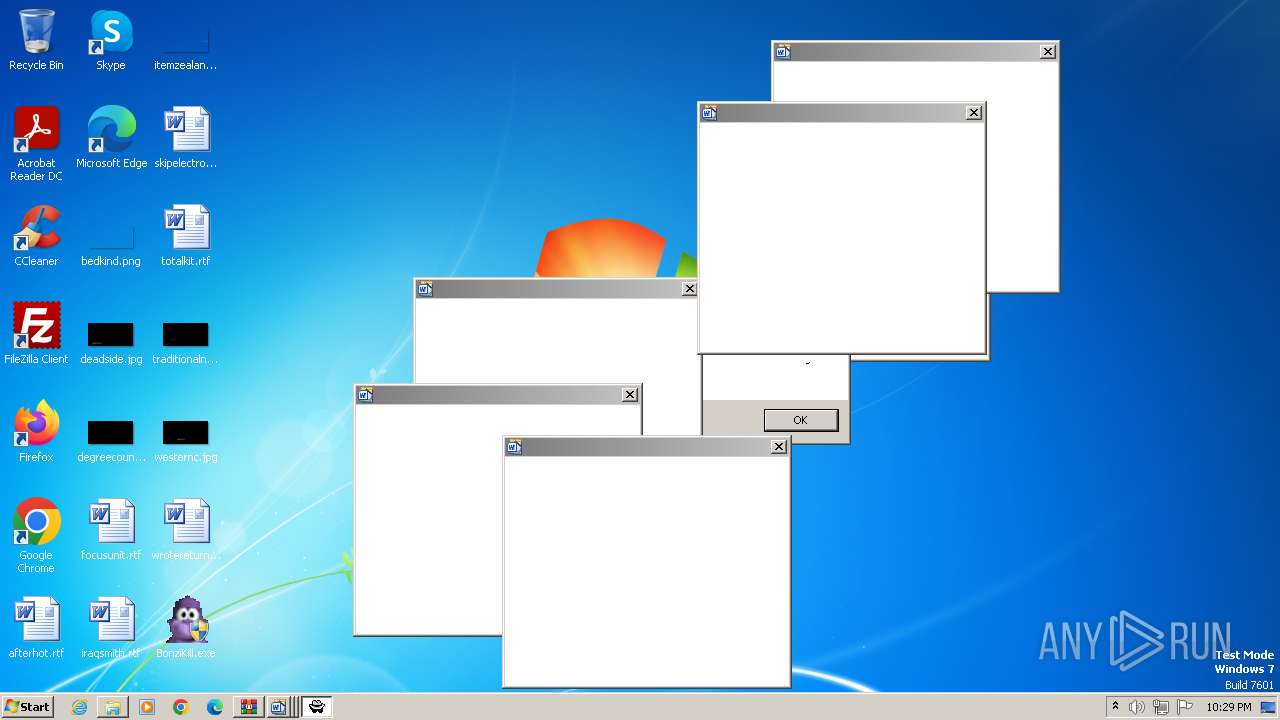
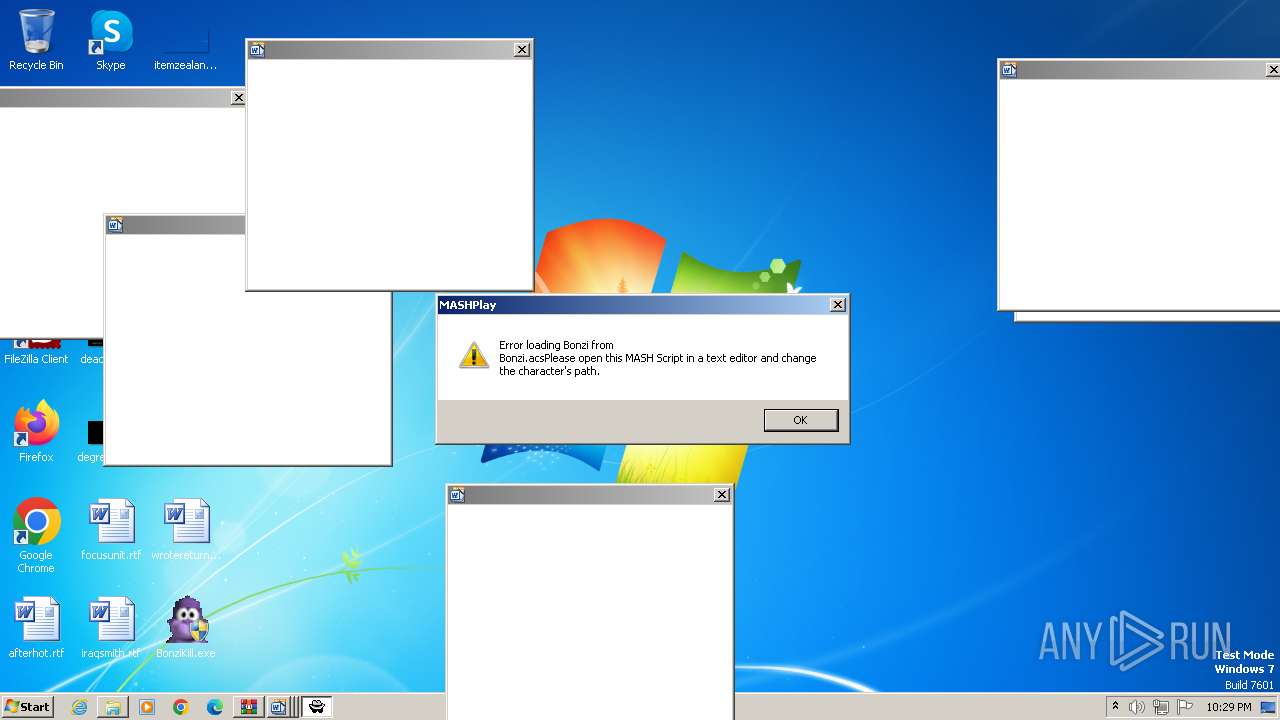
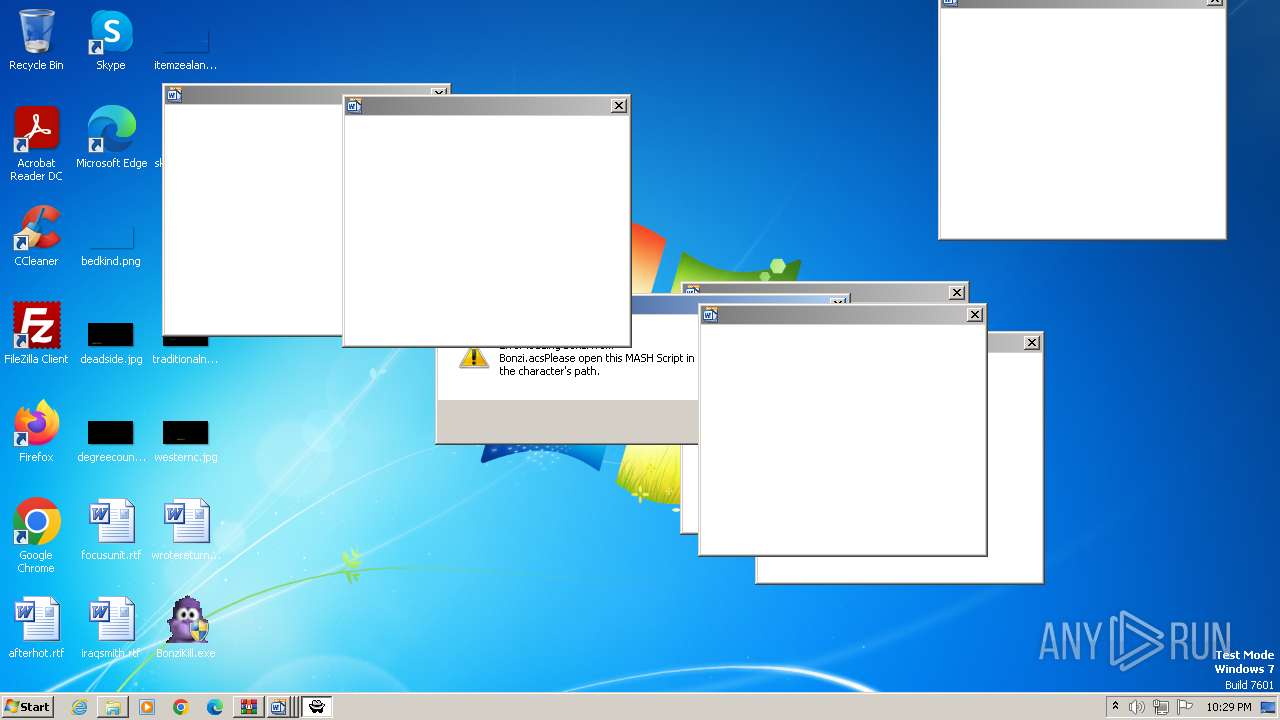
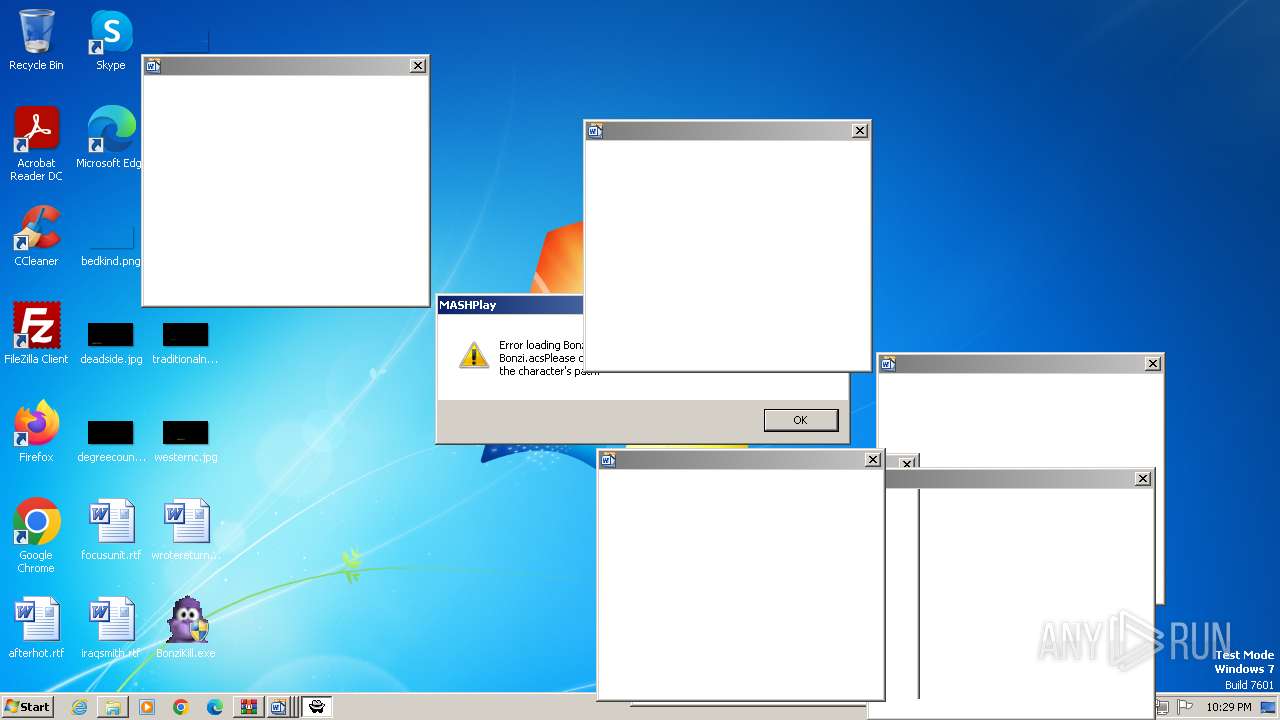
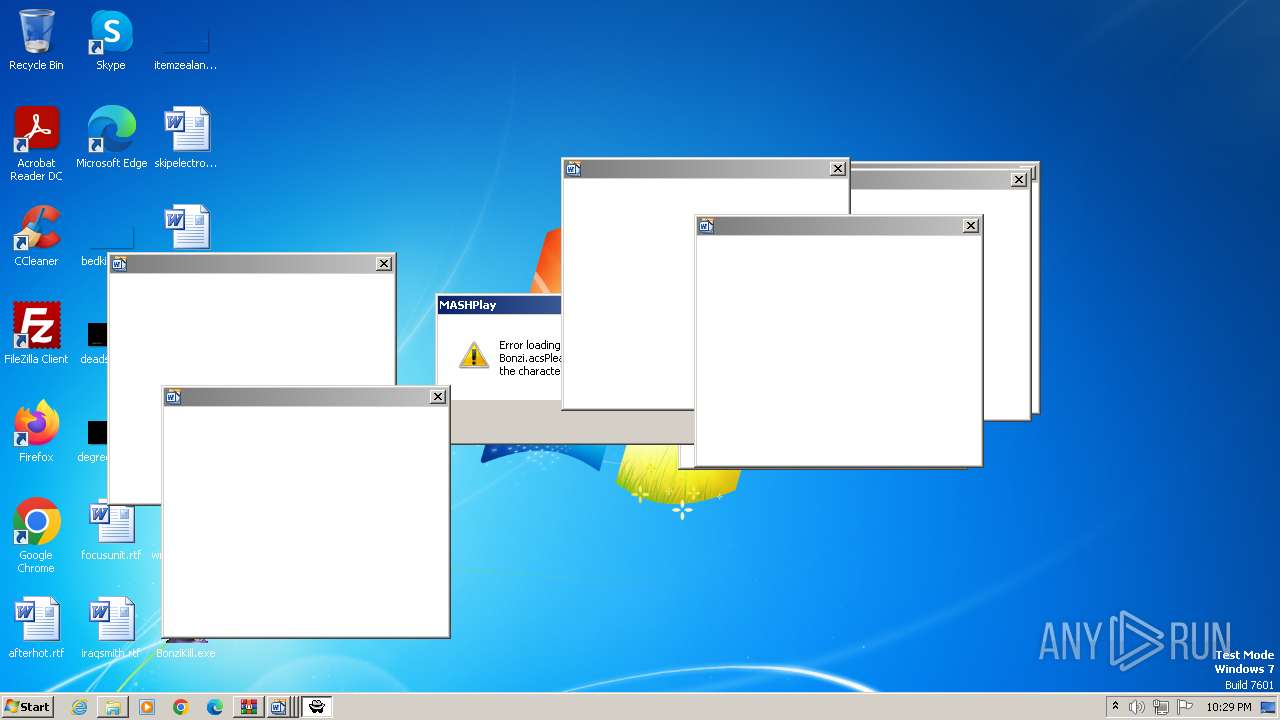
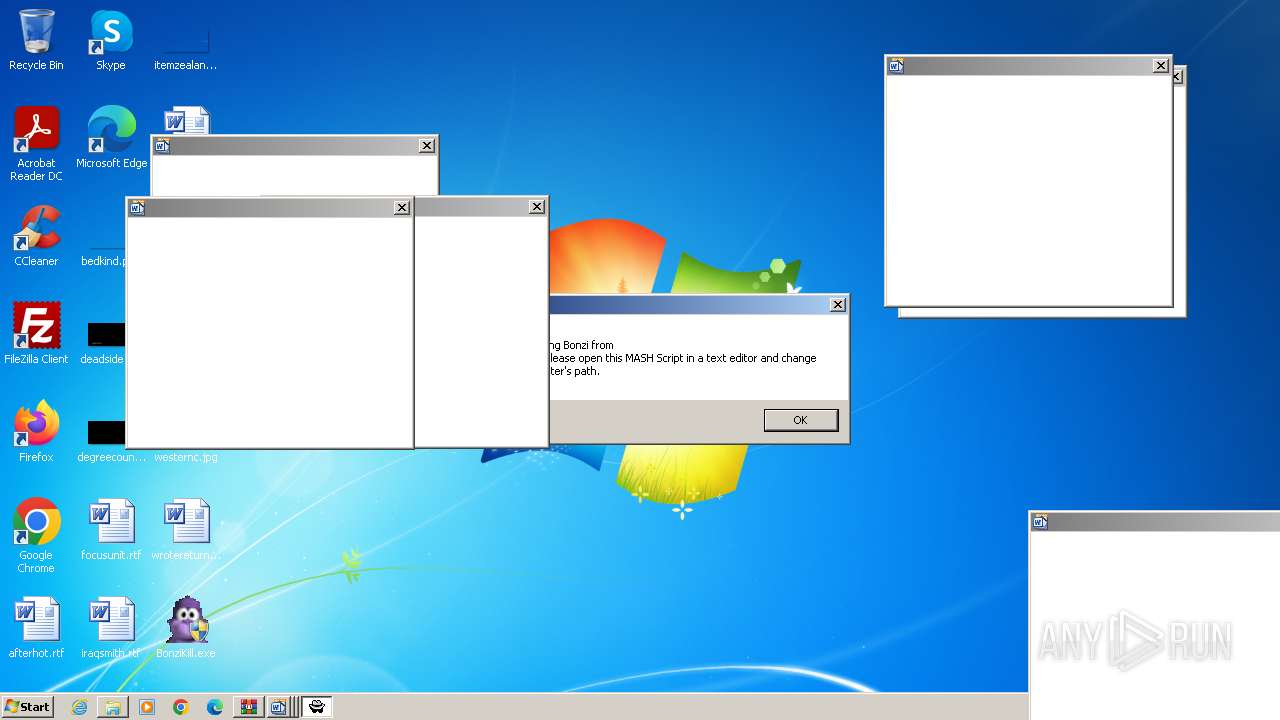
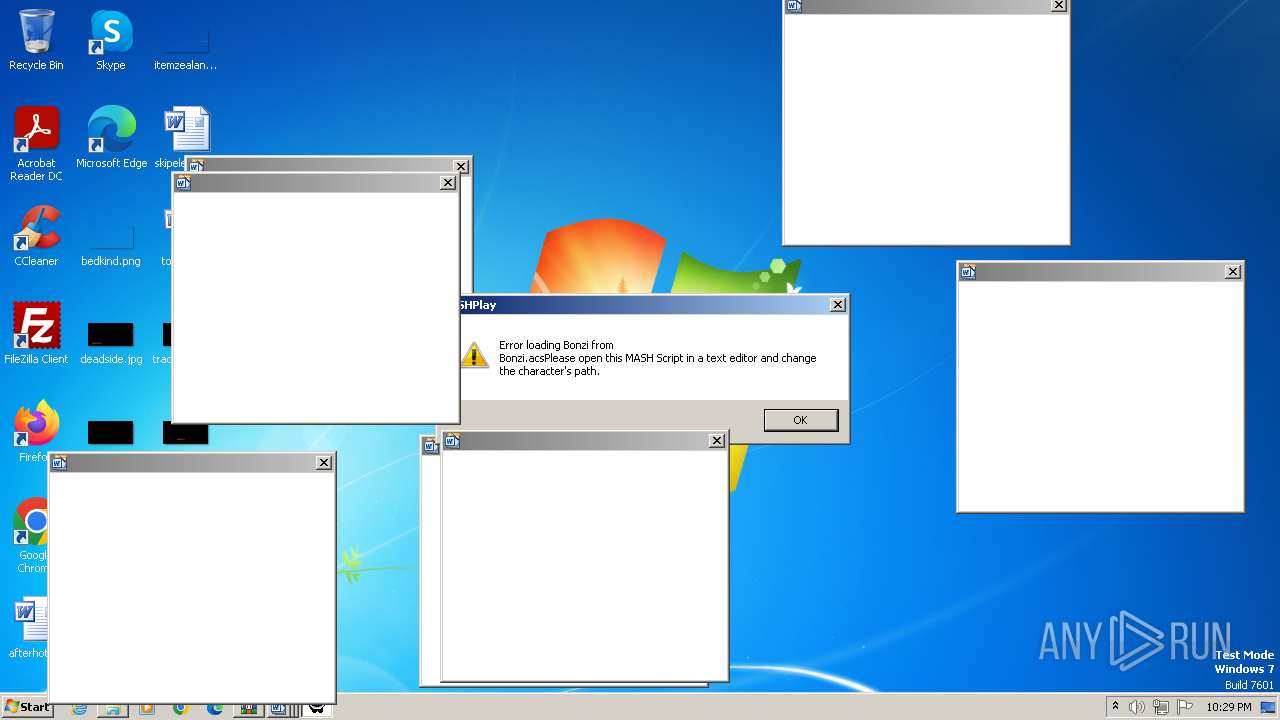
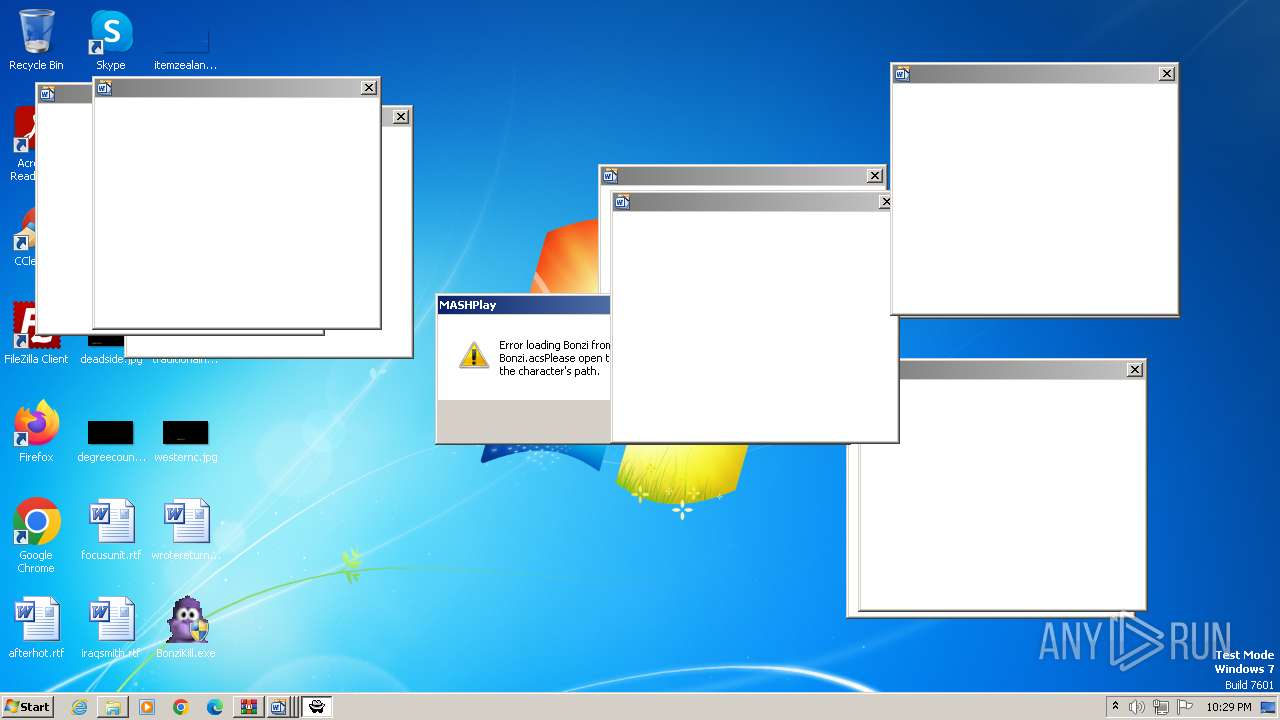
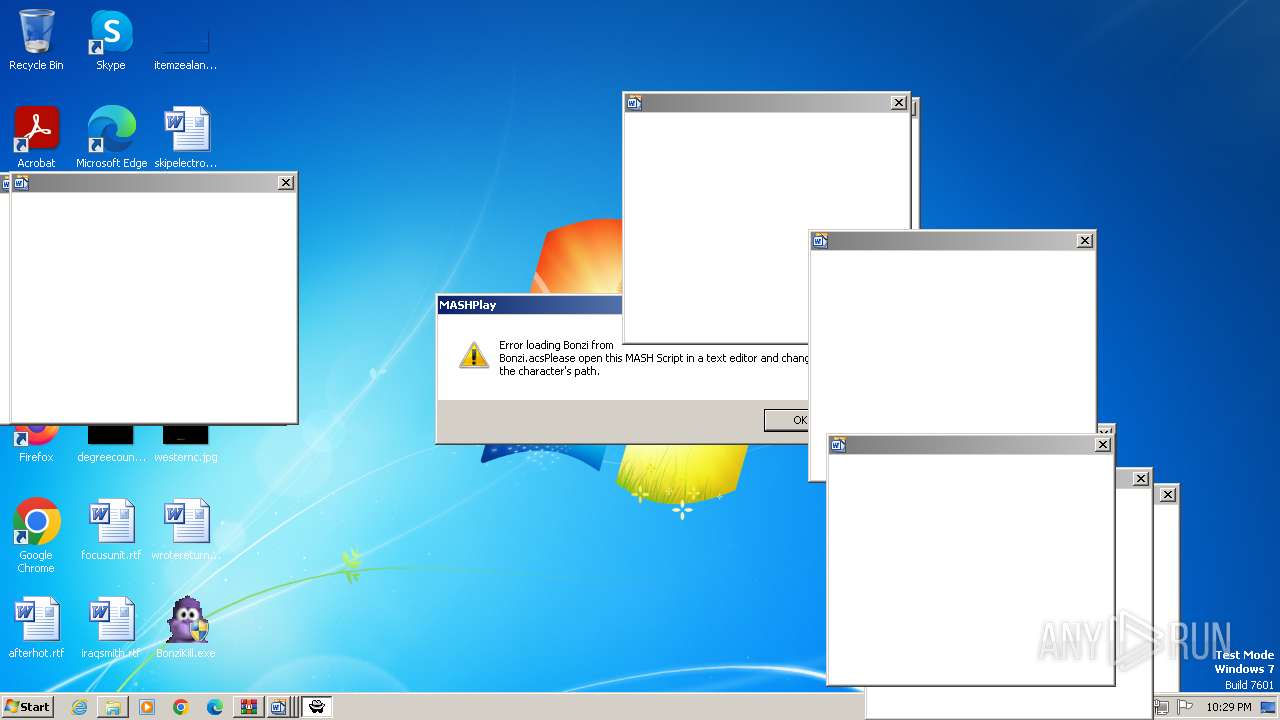
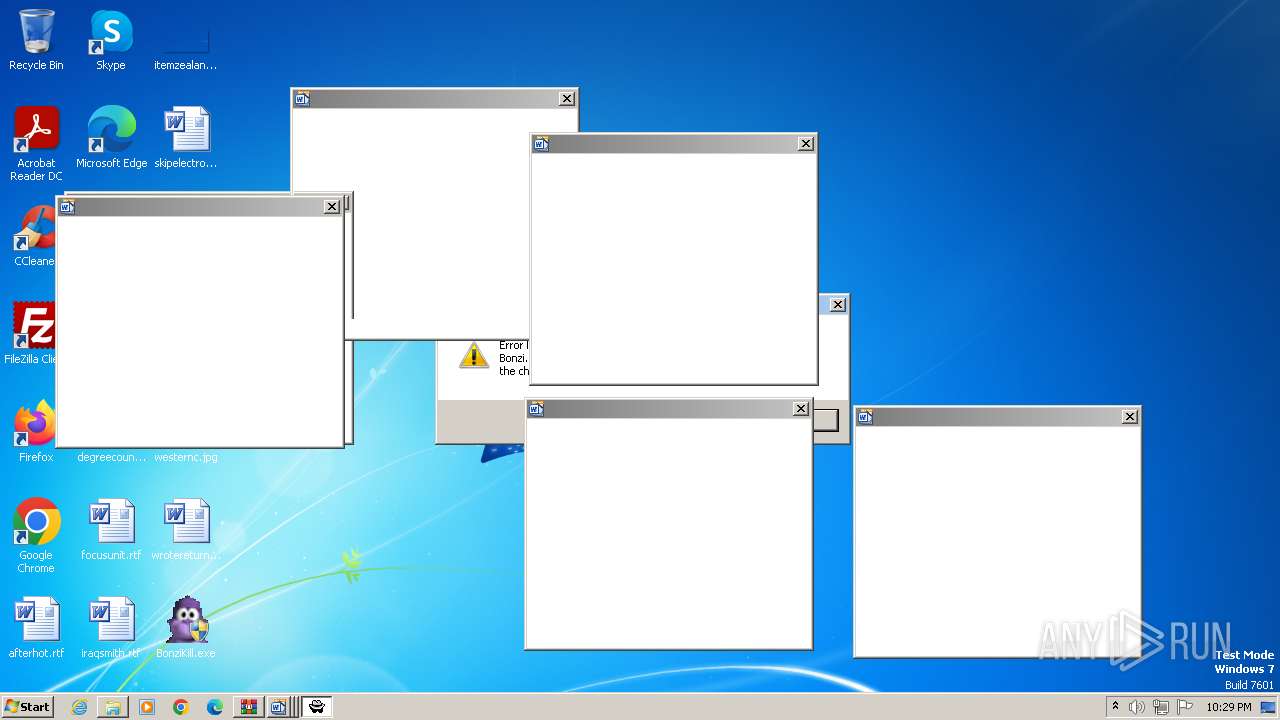
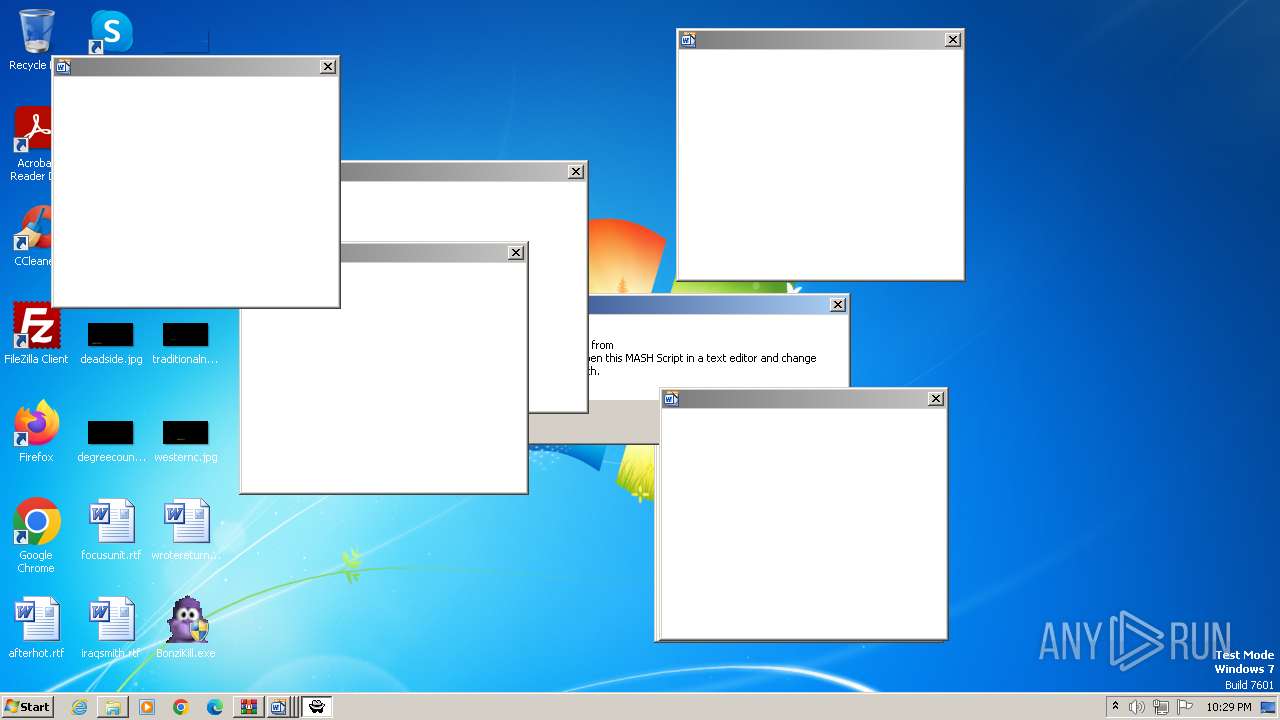
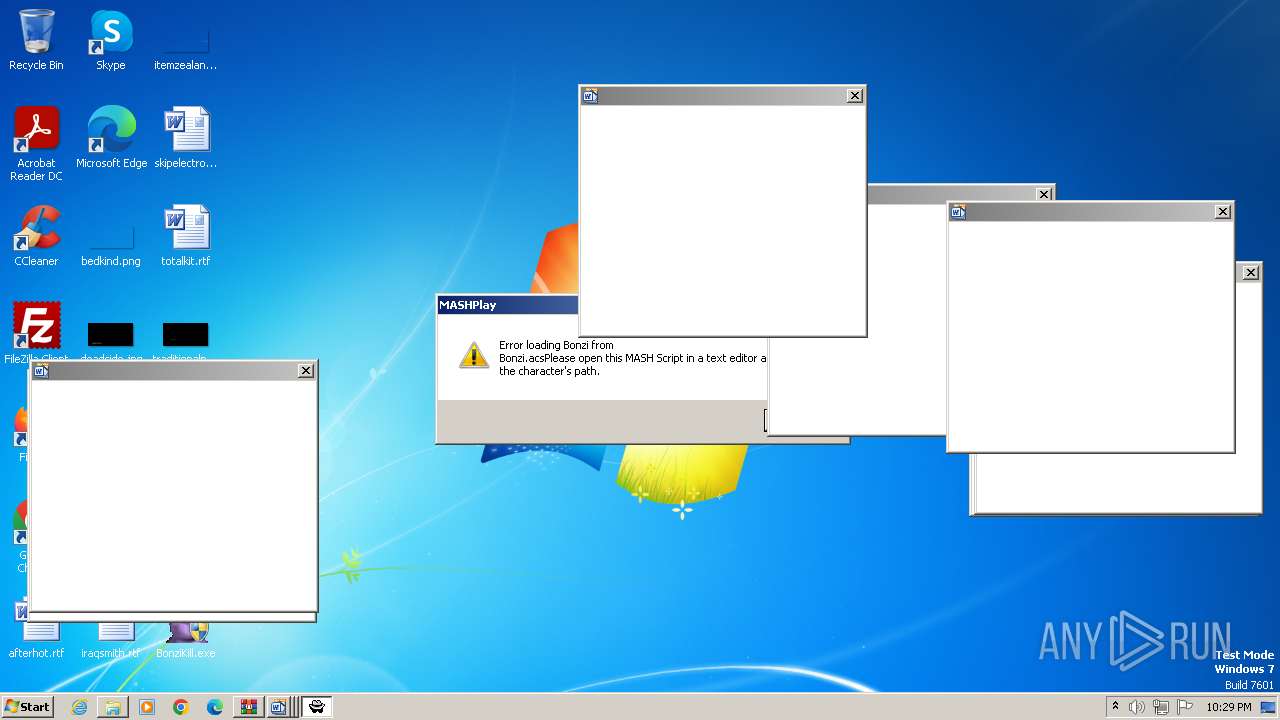
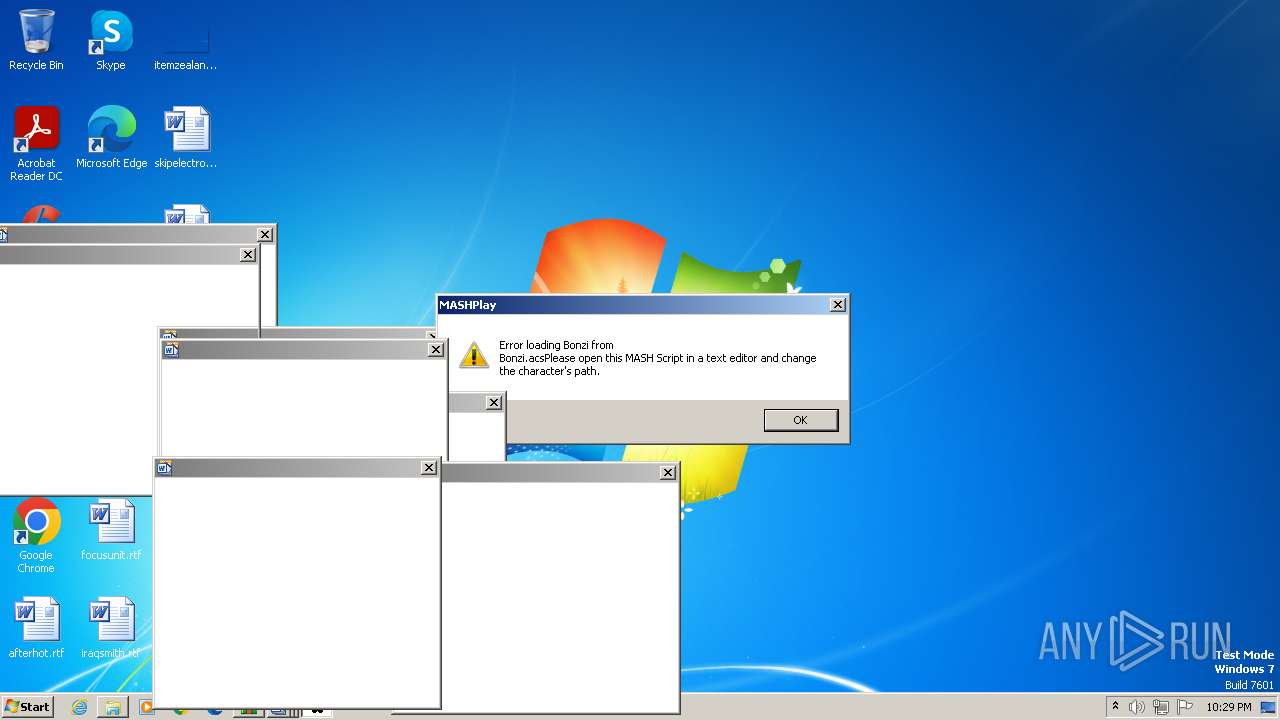
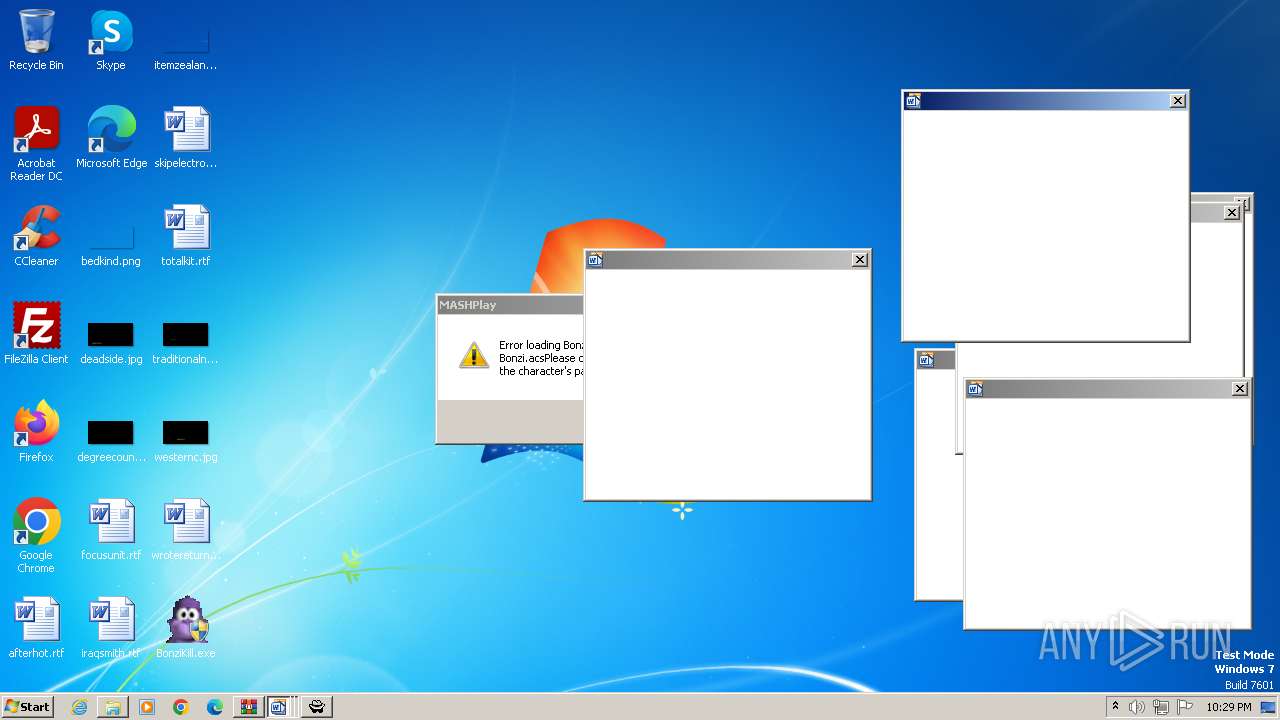
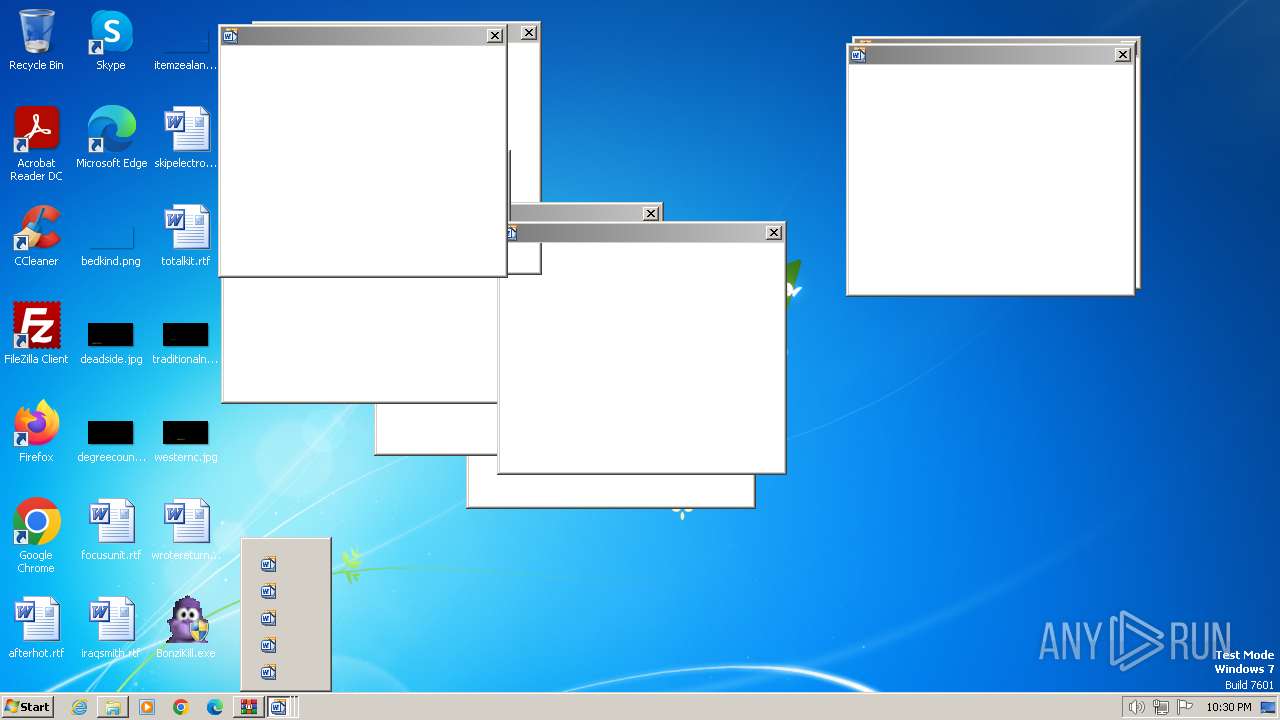
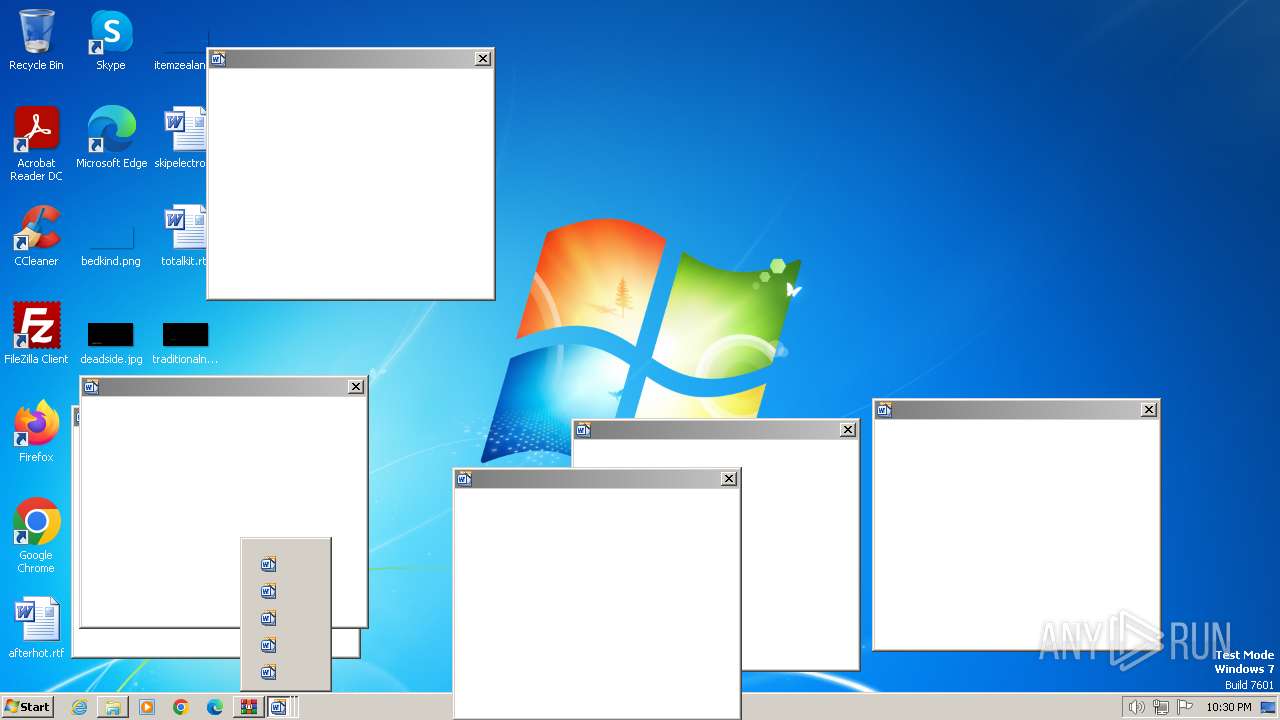
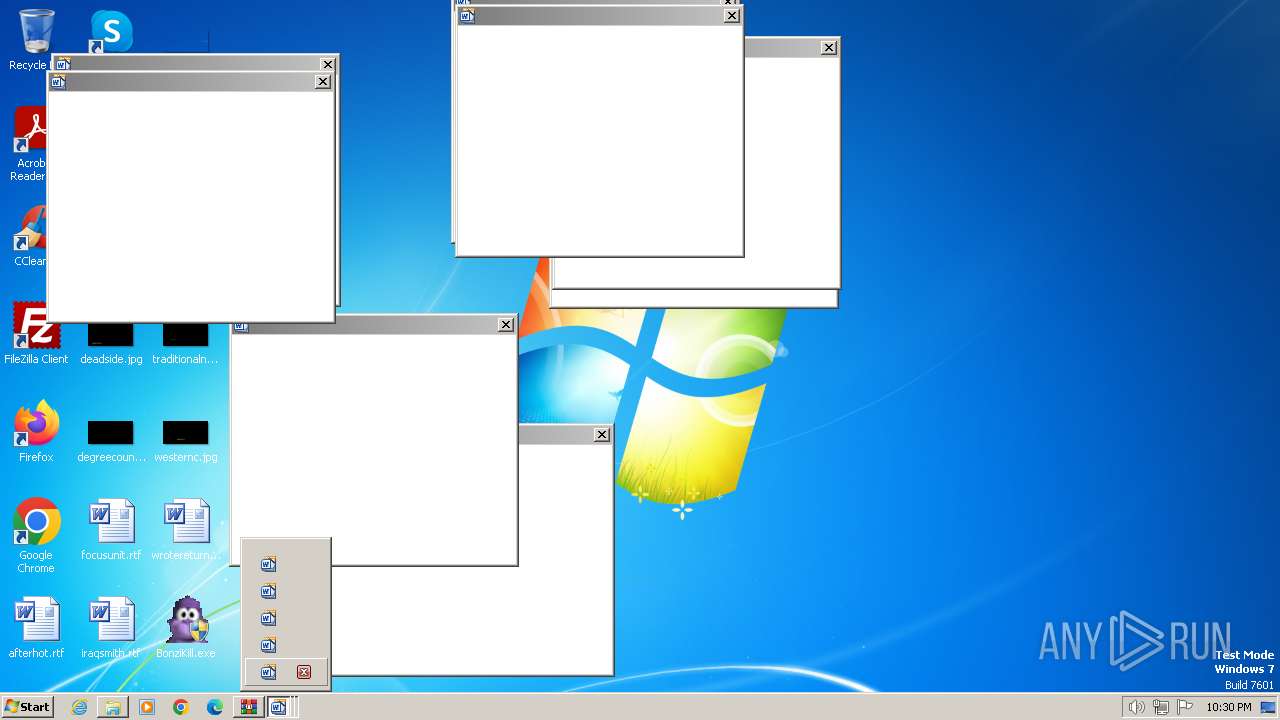
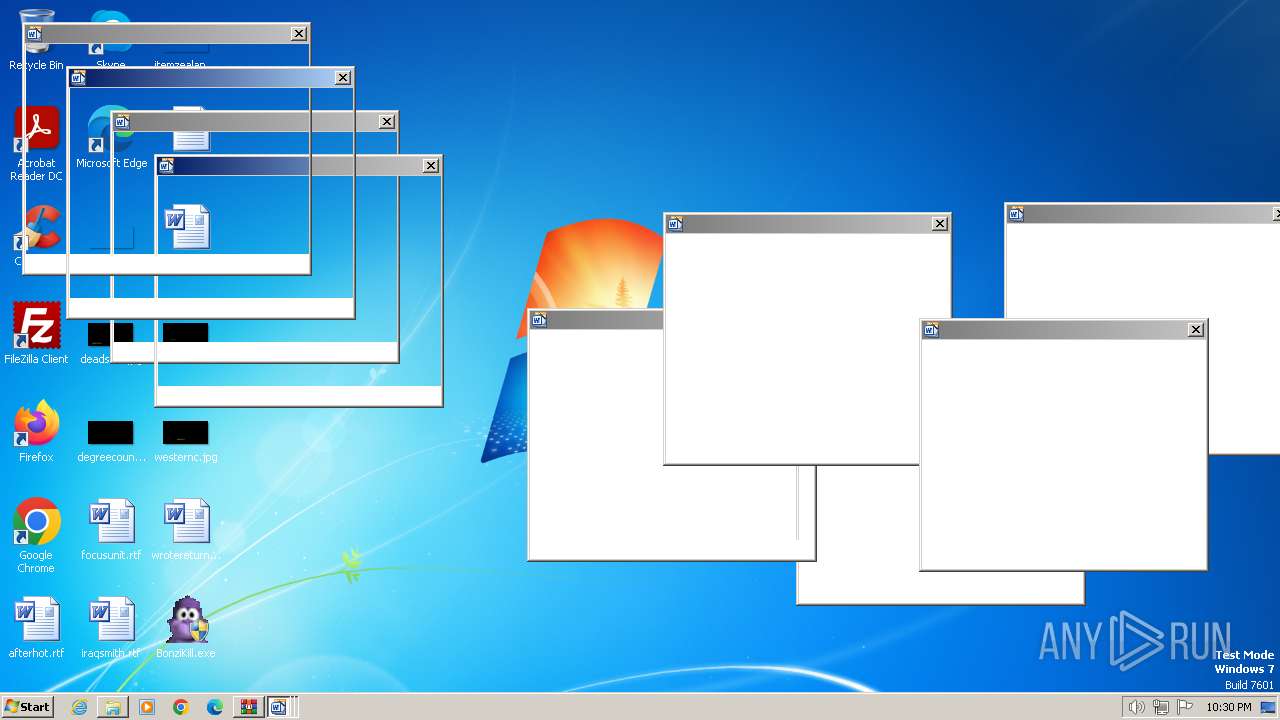
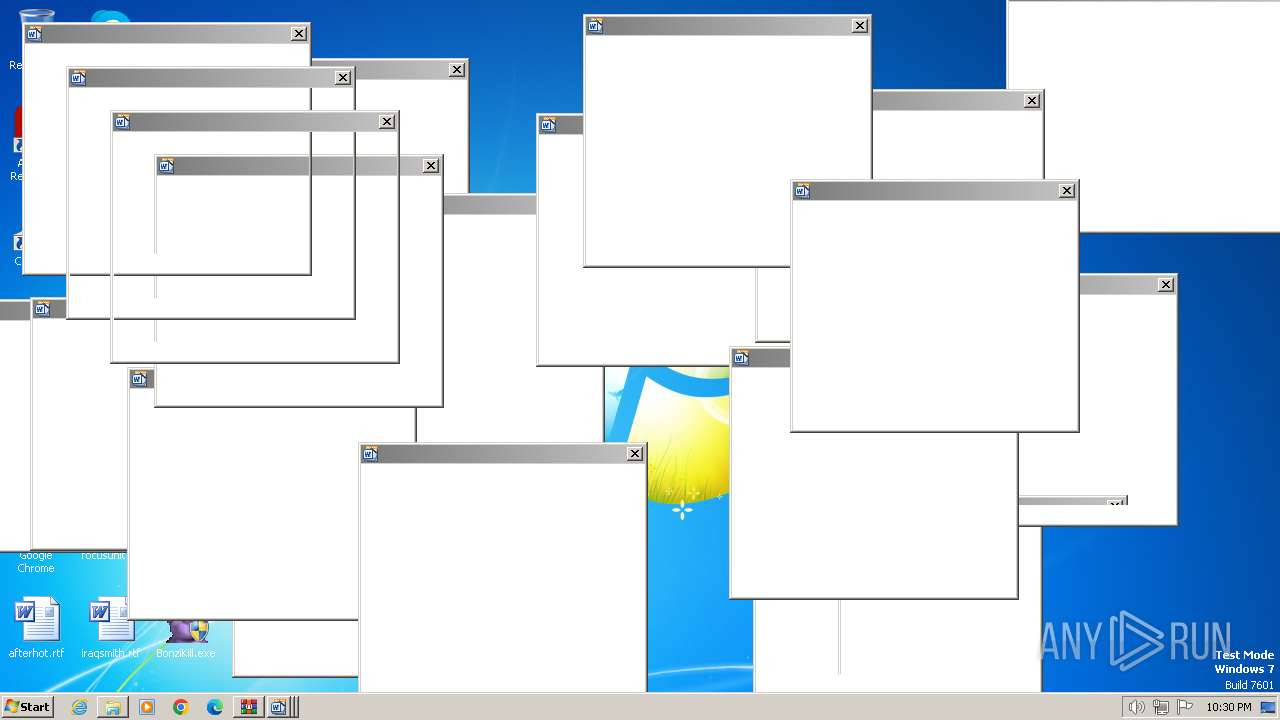
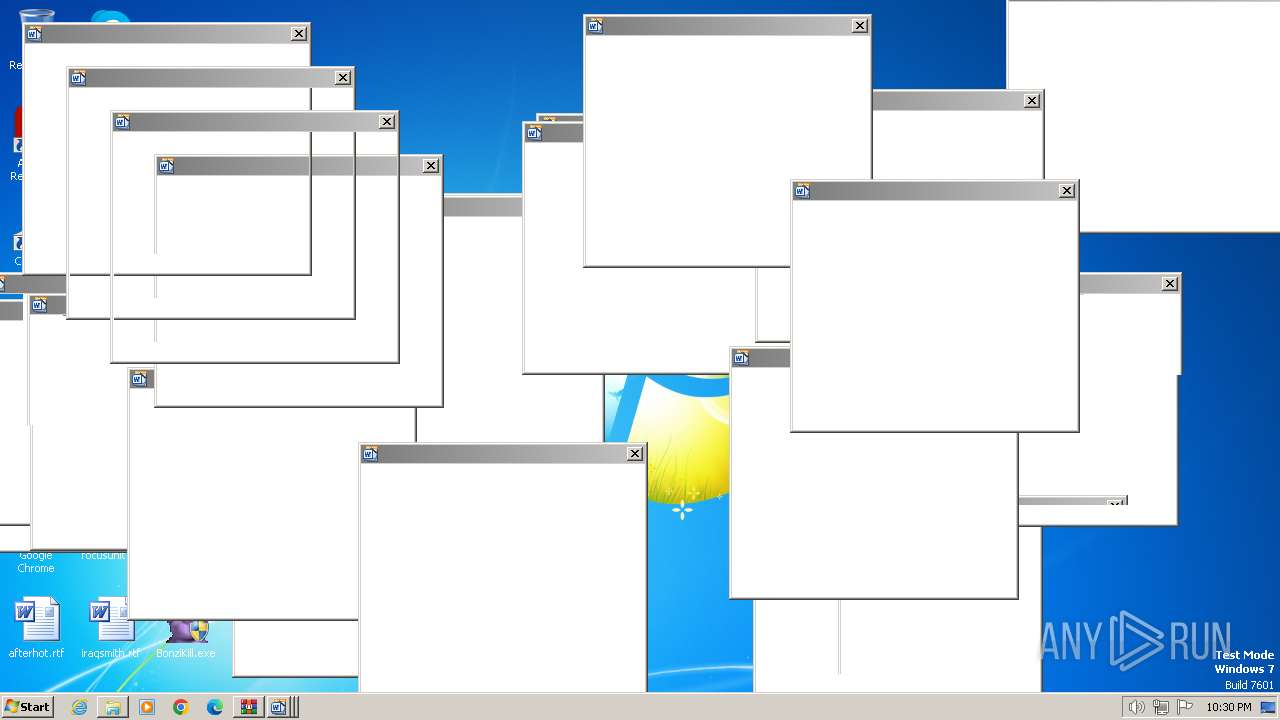
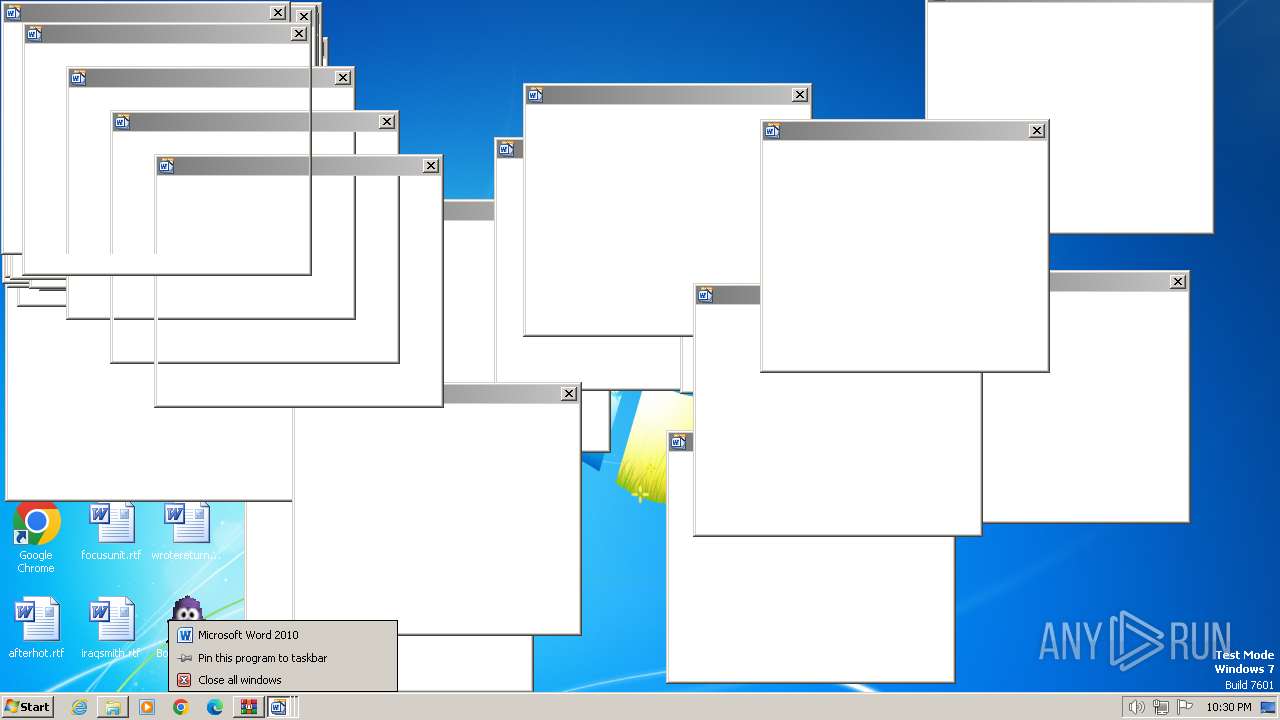
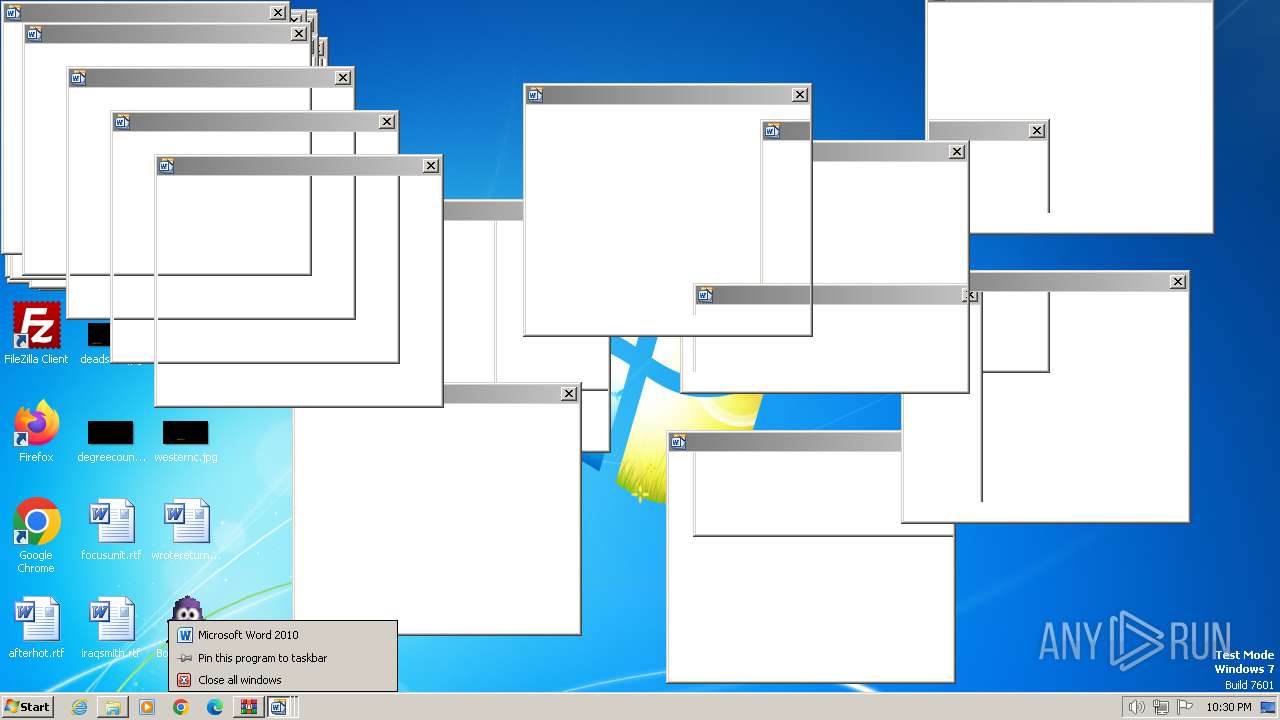
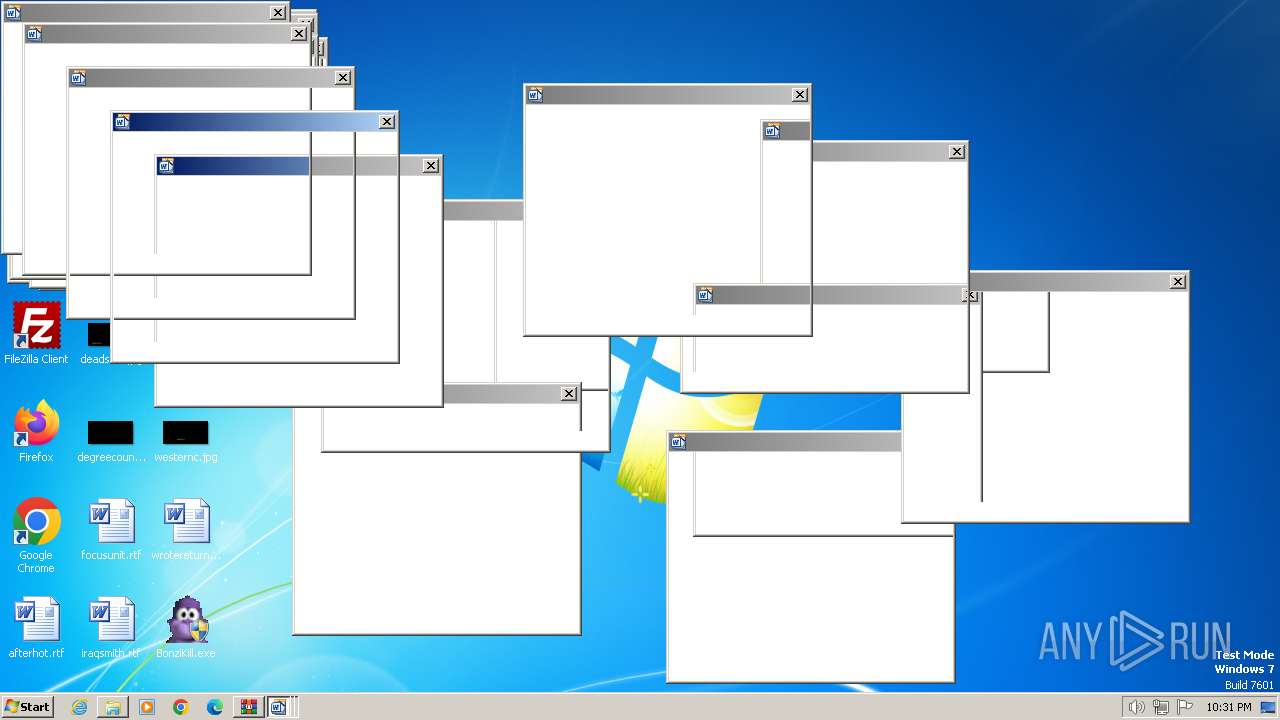
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
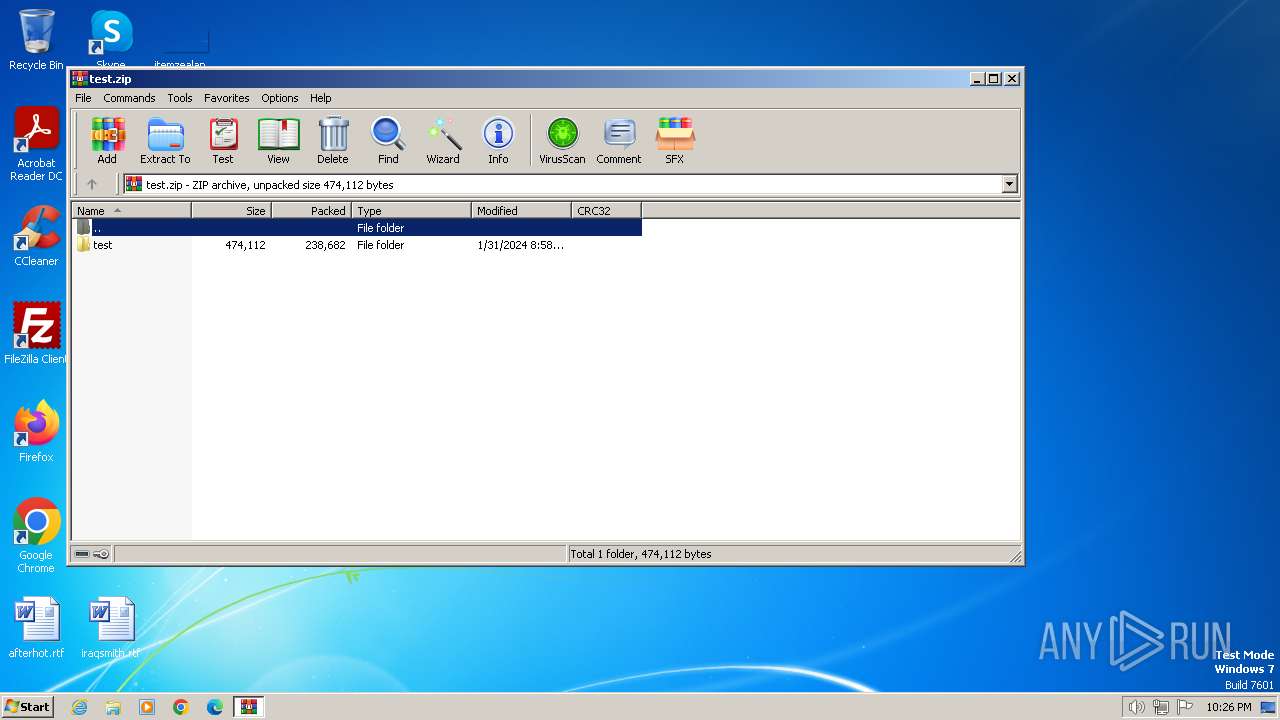
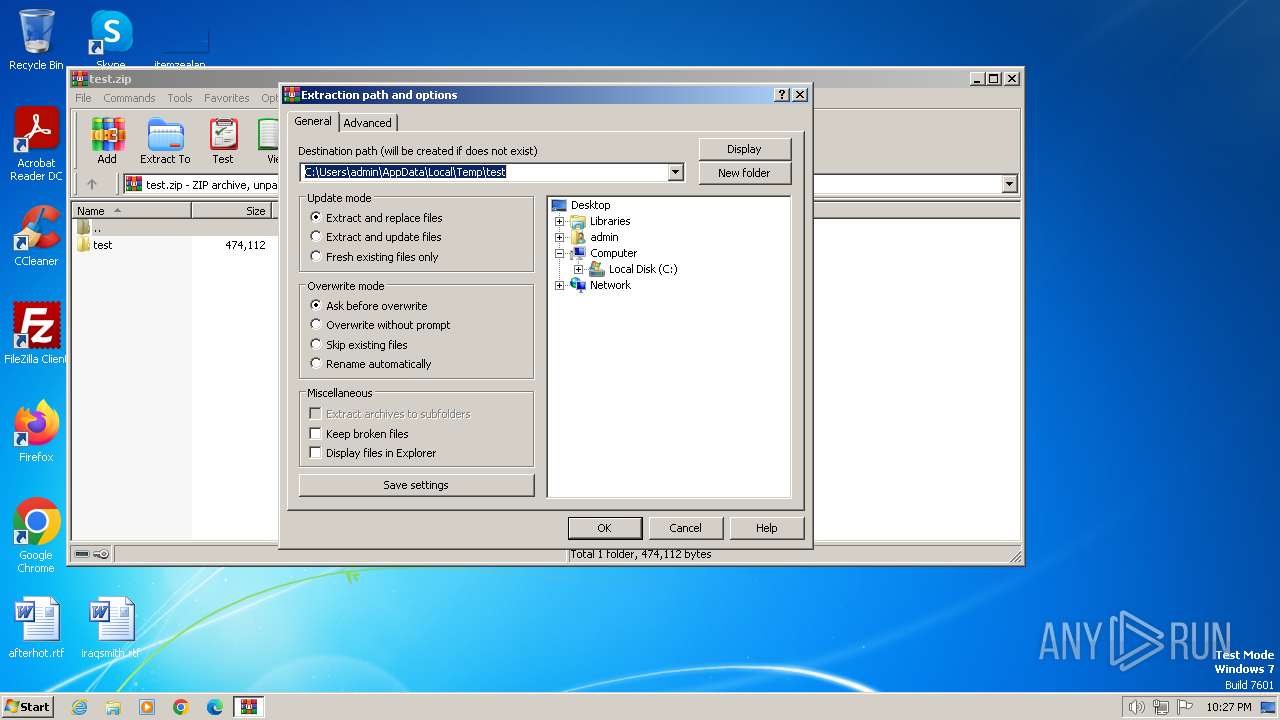
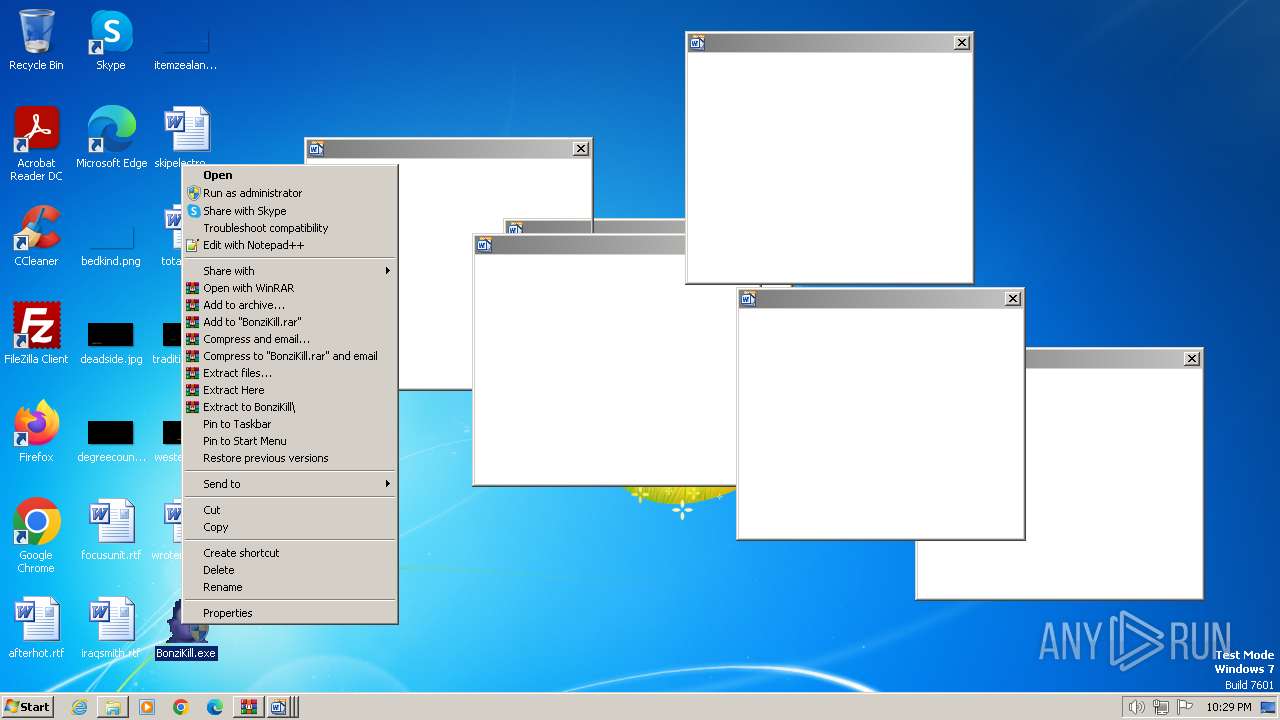
| 1380 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\test.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
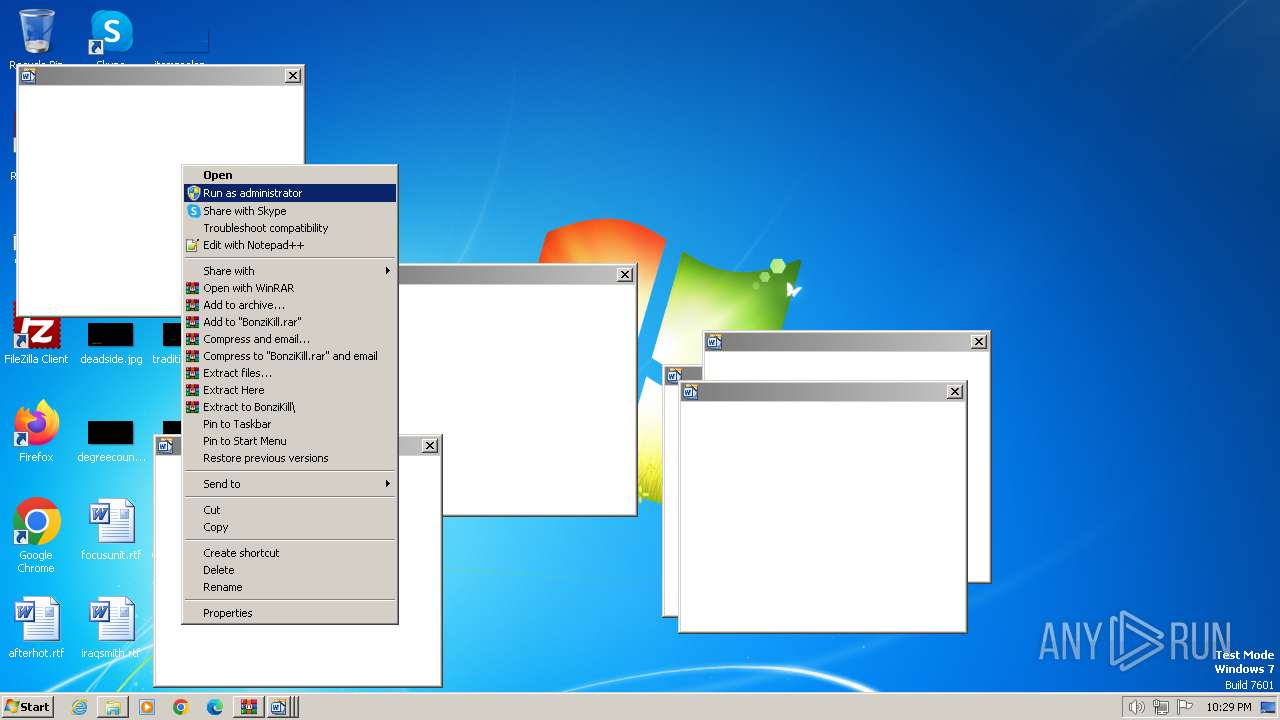
| 3008 | "C:\Users\admin\Desktop\BonziKill.exe" | C:\Users\admin\Desktop\BonziKill.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1000 Modules
| |||||||||||||||
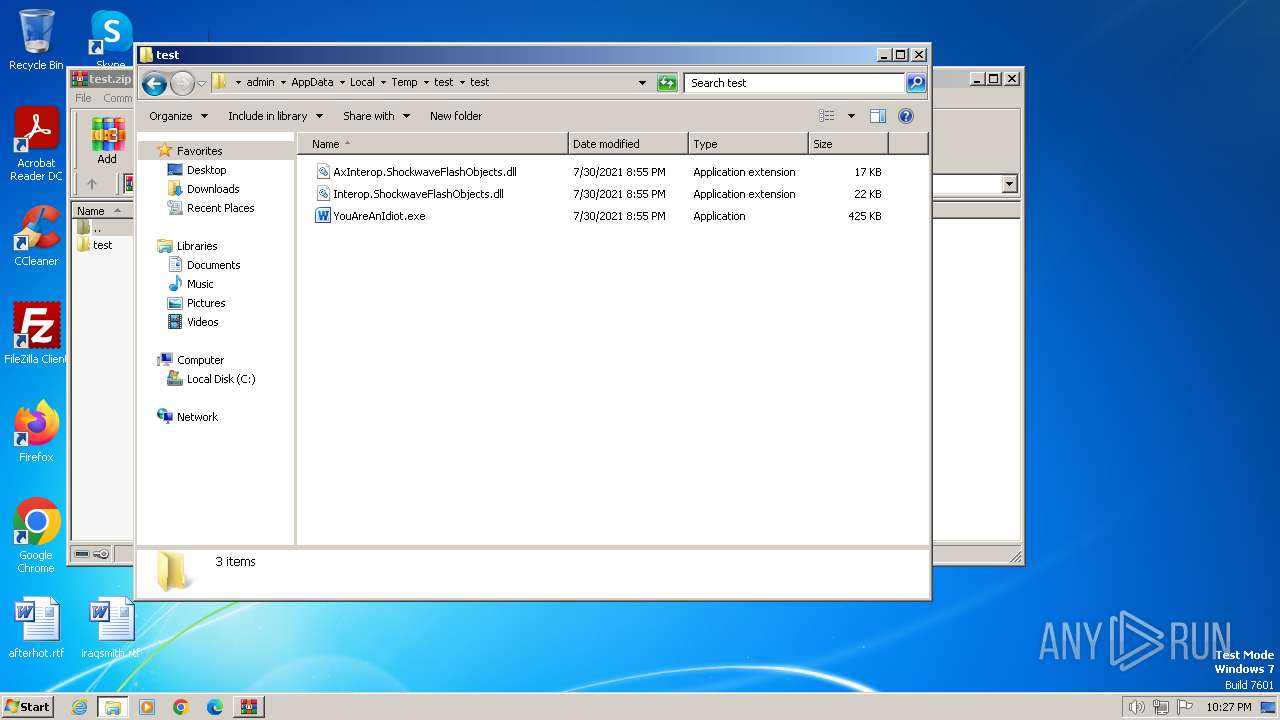
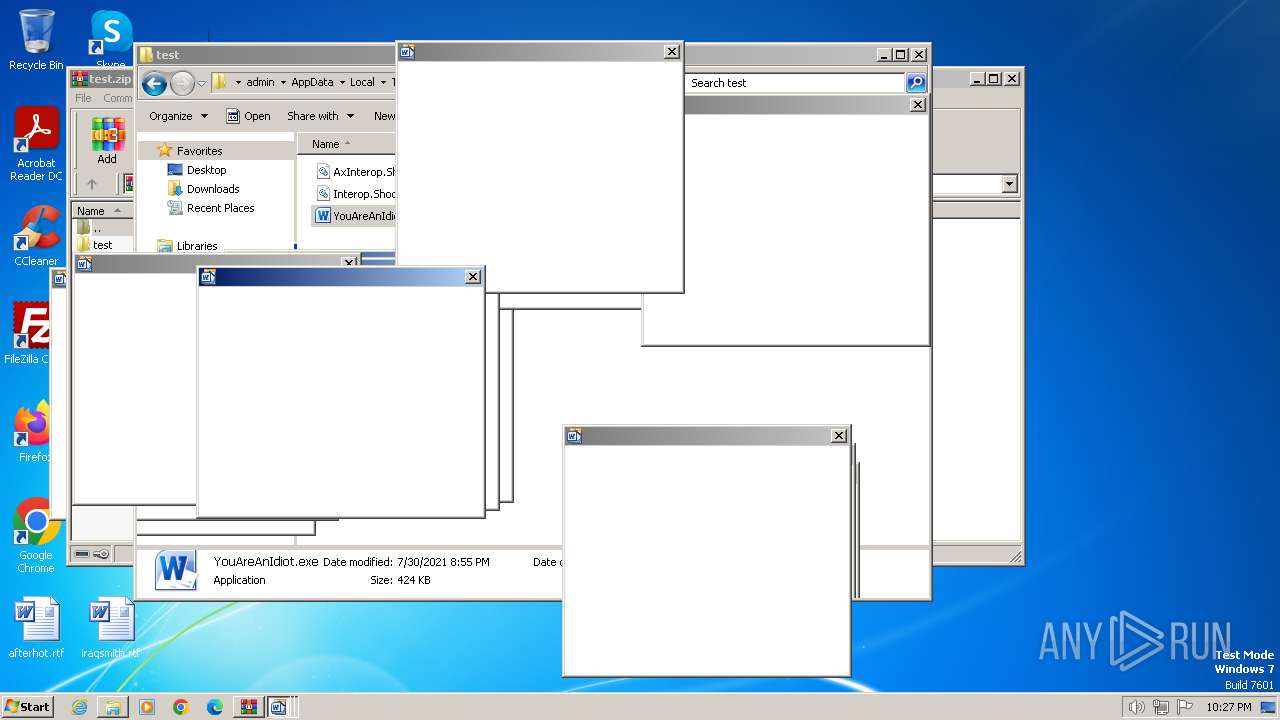
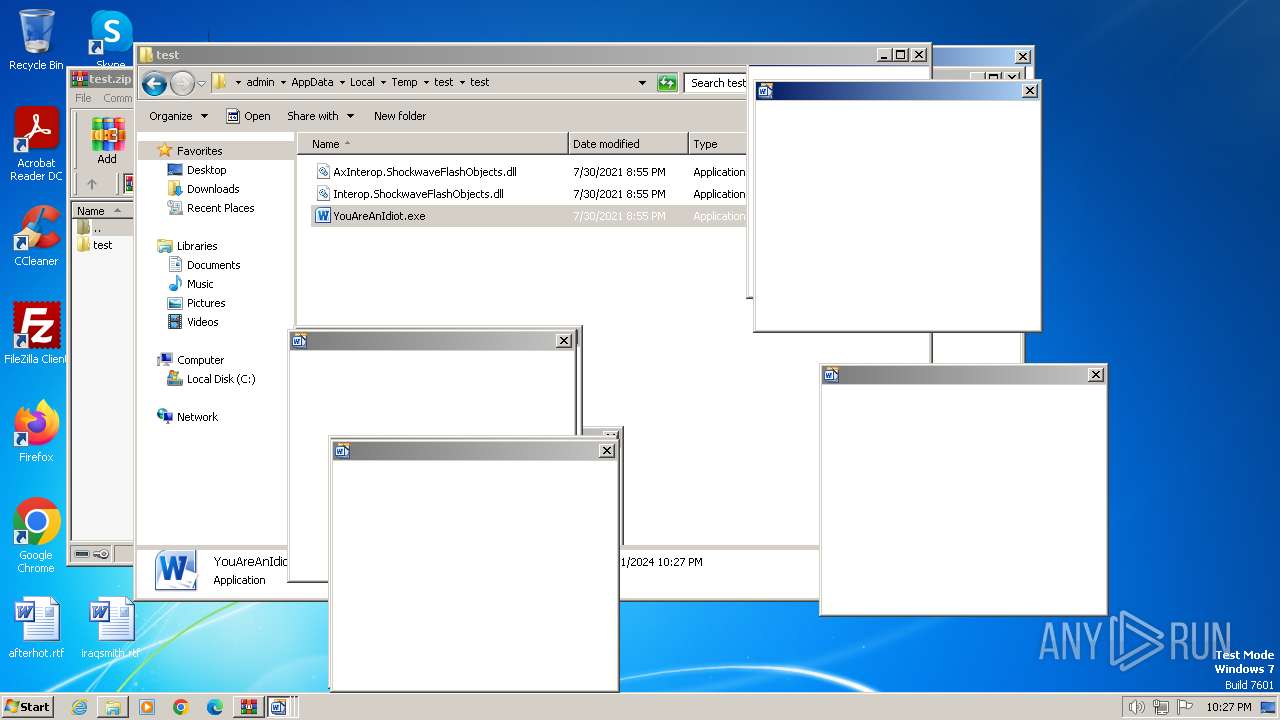
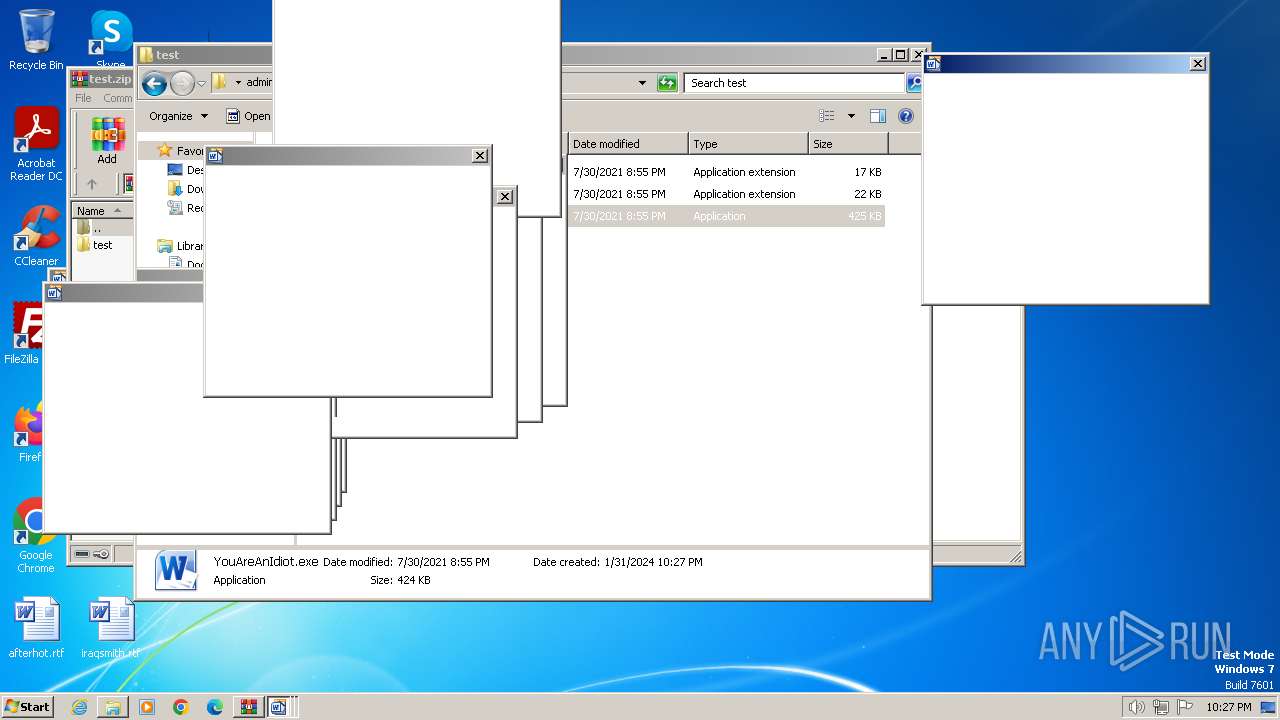
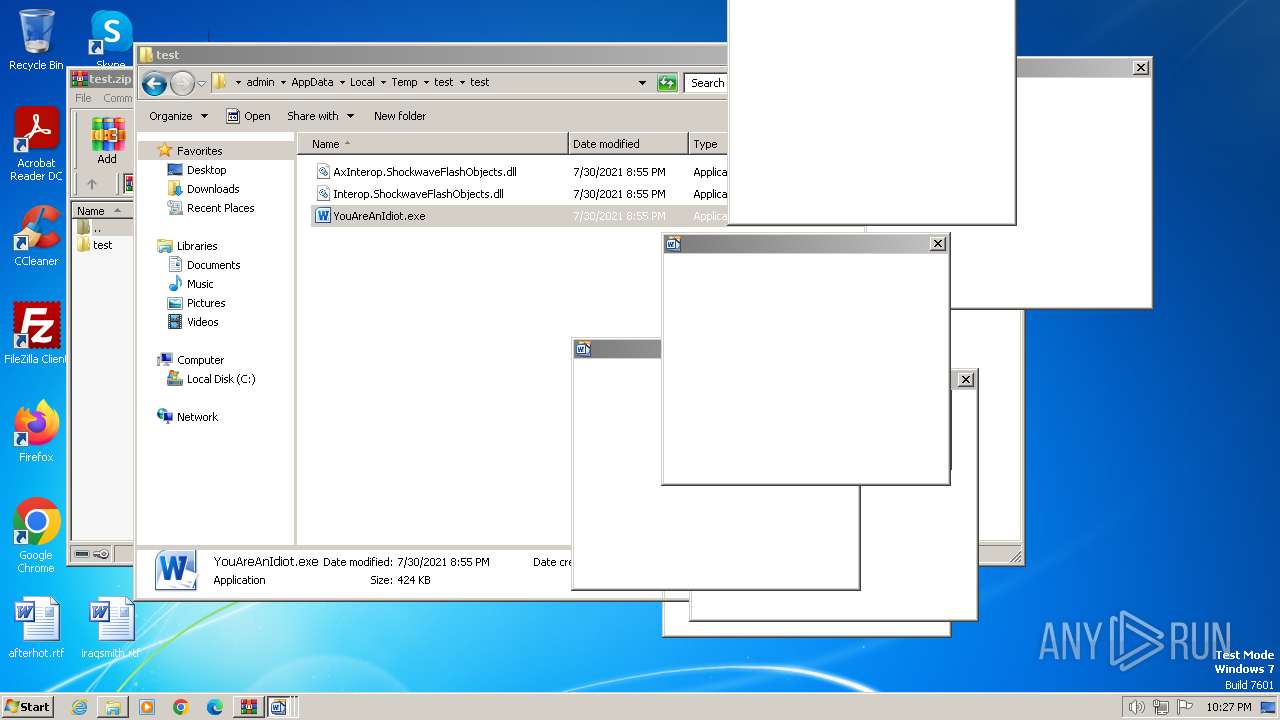
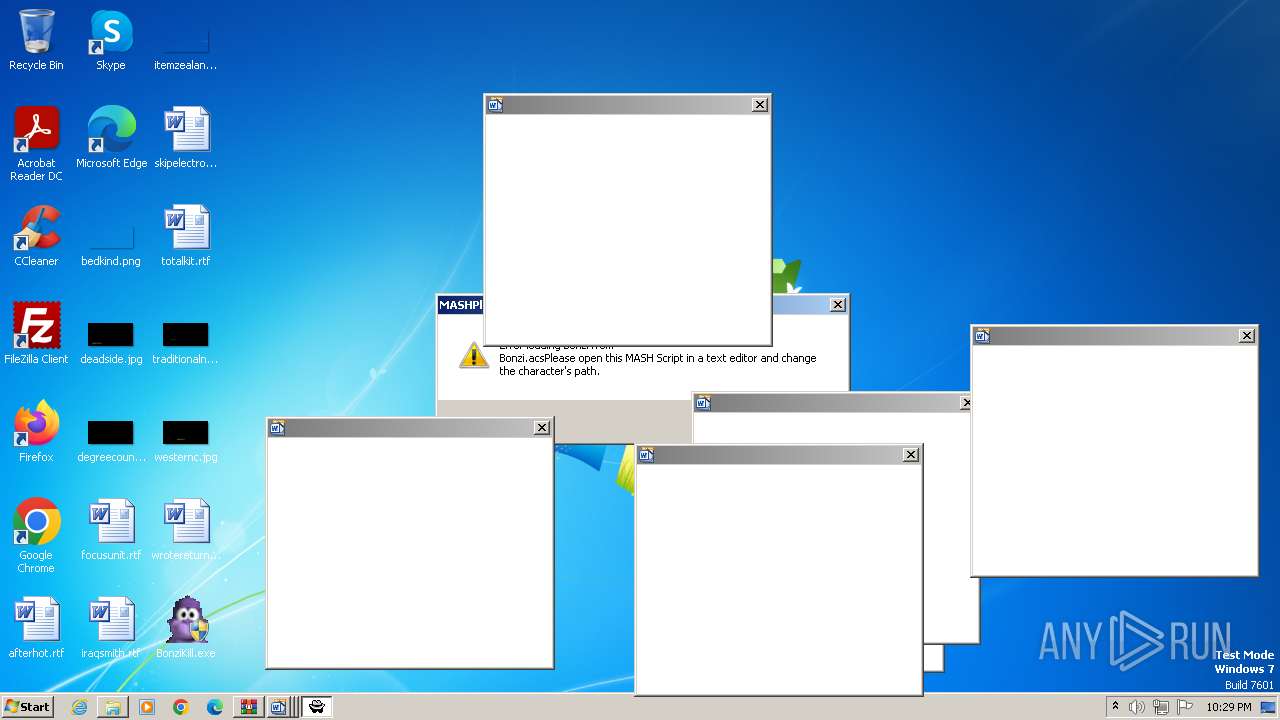
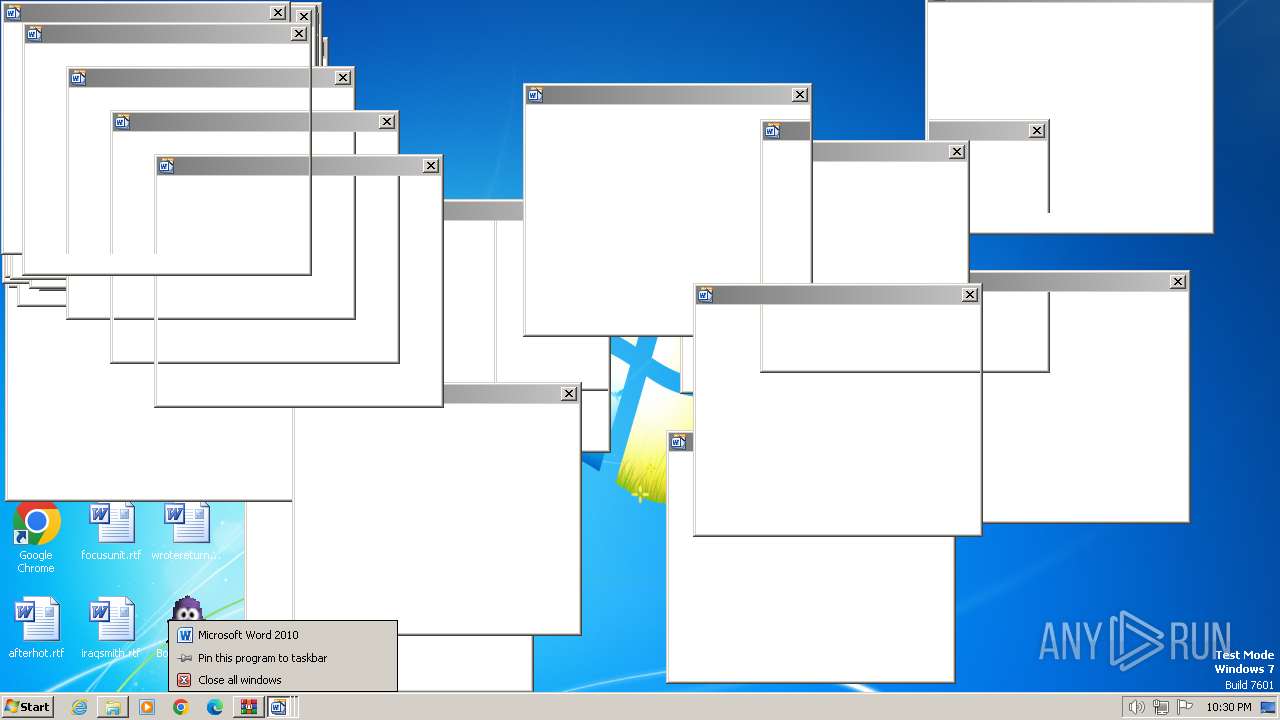
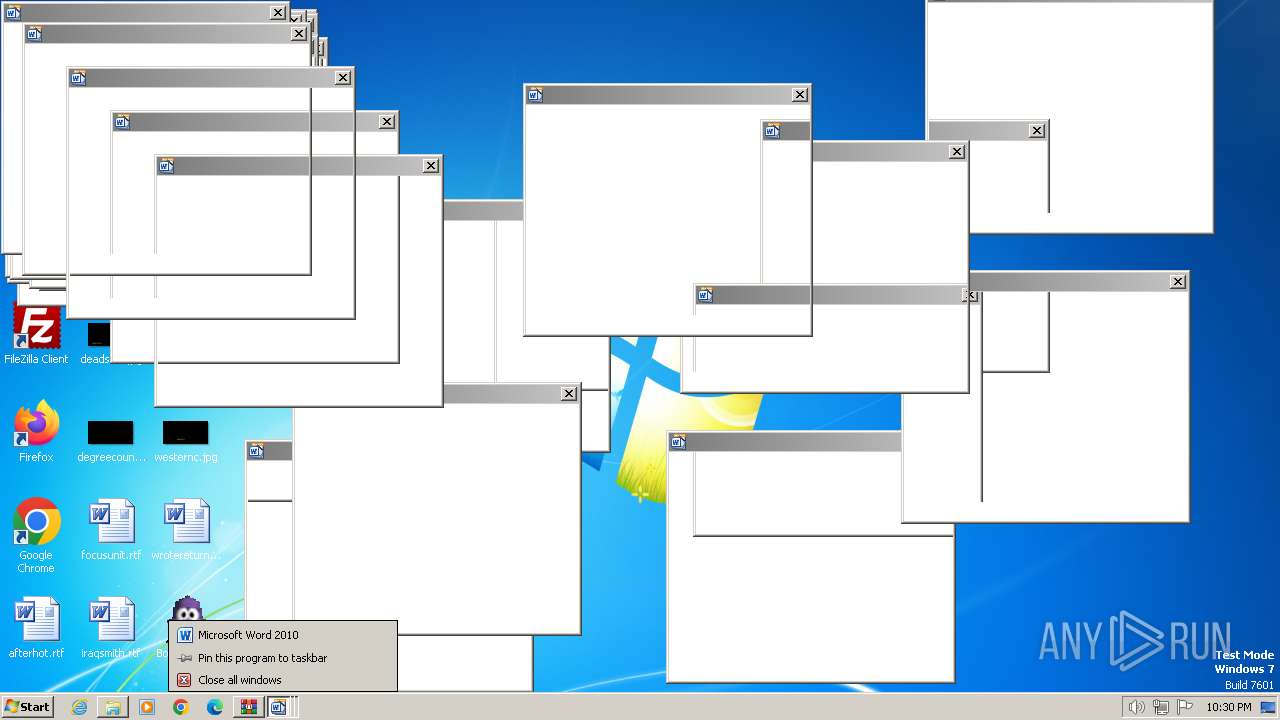
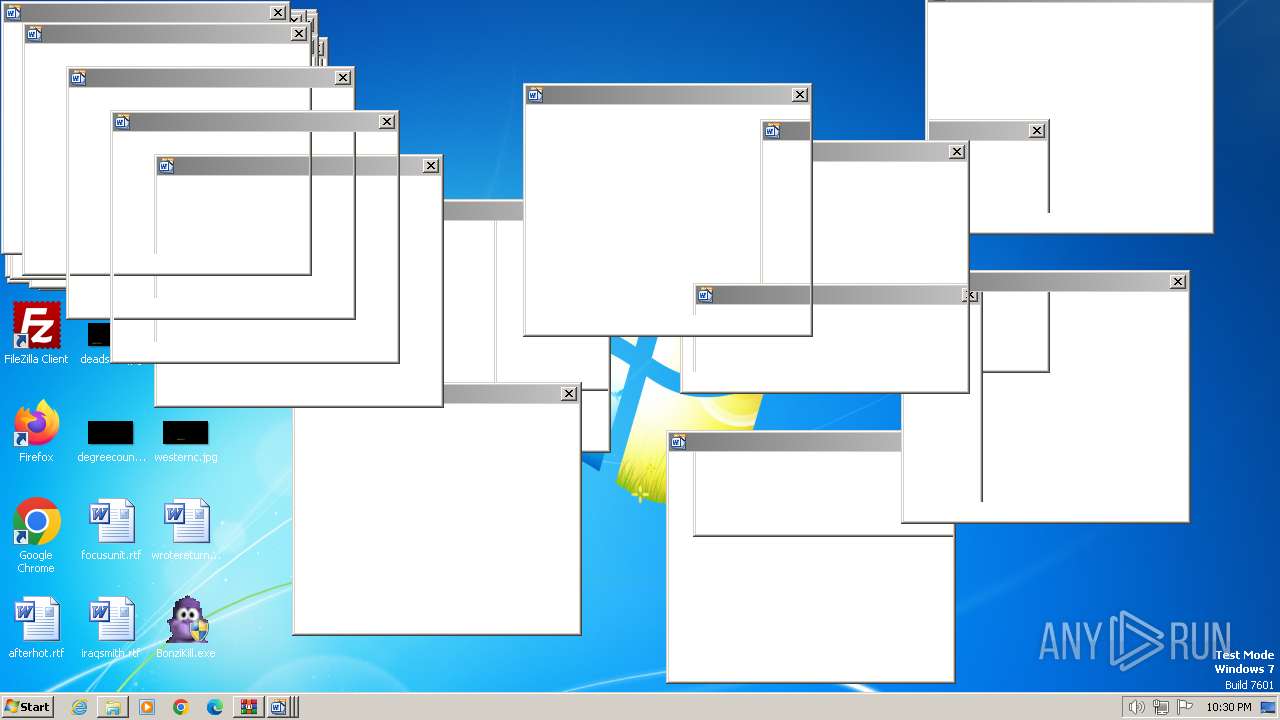
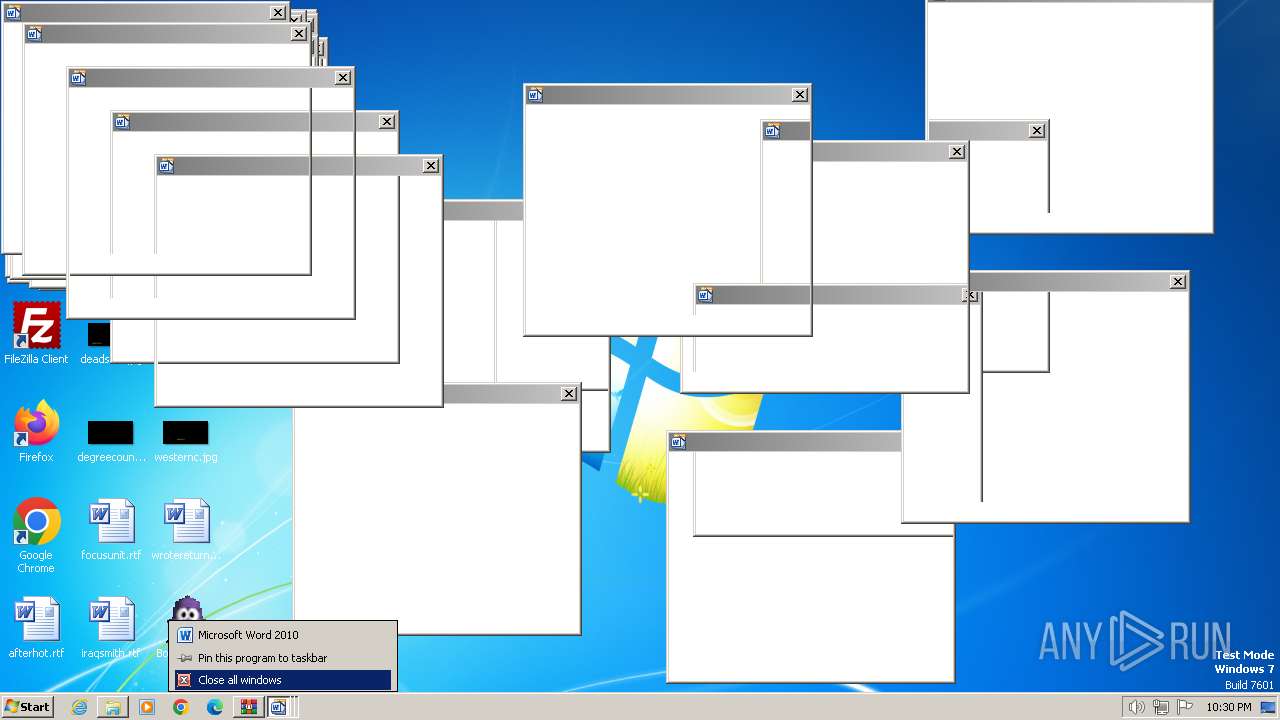
| 3248 | "C:\Users\admin\AppData\Local\Temp\test\test\YouAreAnIdiot.exe" | C:\Users\admin\AppData\Local\Temp\test\test\YouAreAnIdiot.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: Microsoft Word 2010 Exit code: 1 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3500 | "C:\Users\admin\Desktop\BonziKill.exe" | C:\Users\admin\Desktop\BonziKill.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1000 Modules
| |||||||||||||||
| 3632 | "C:\Users\admin\Desktop\BonziKill.exe" | C:\Users\admin\Desktop\BonziKill.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
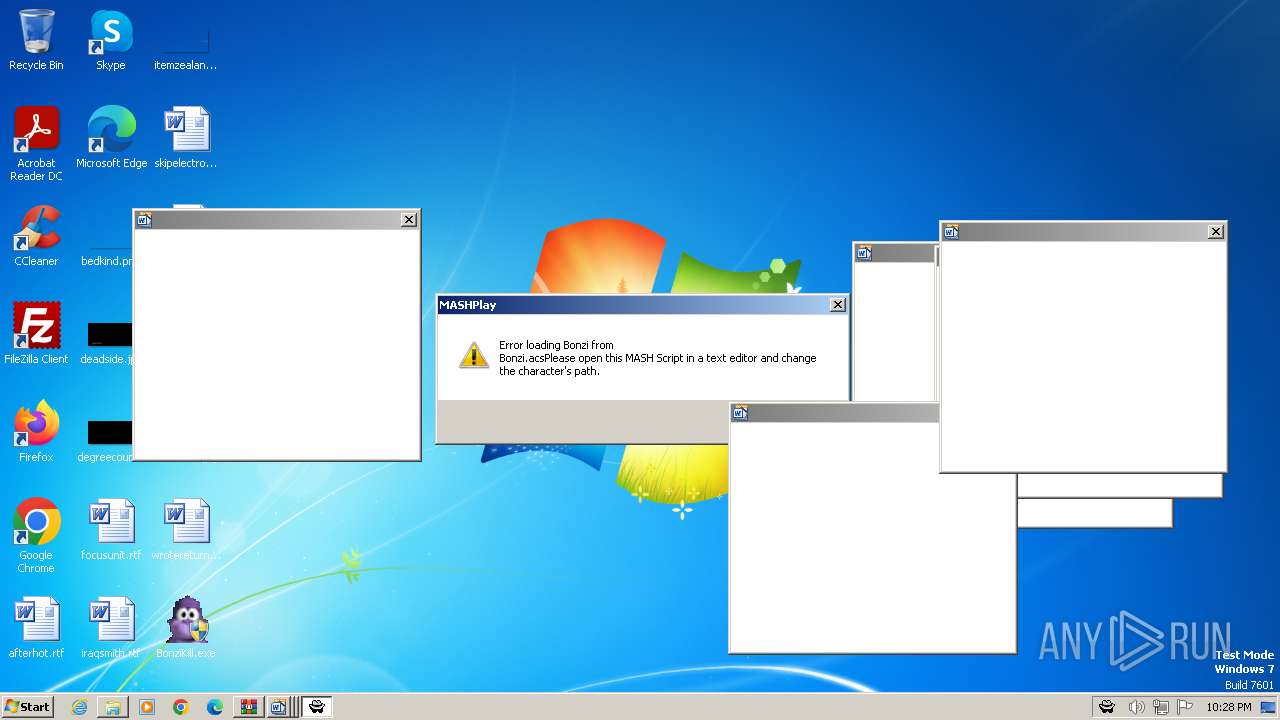
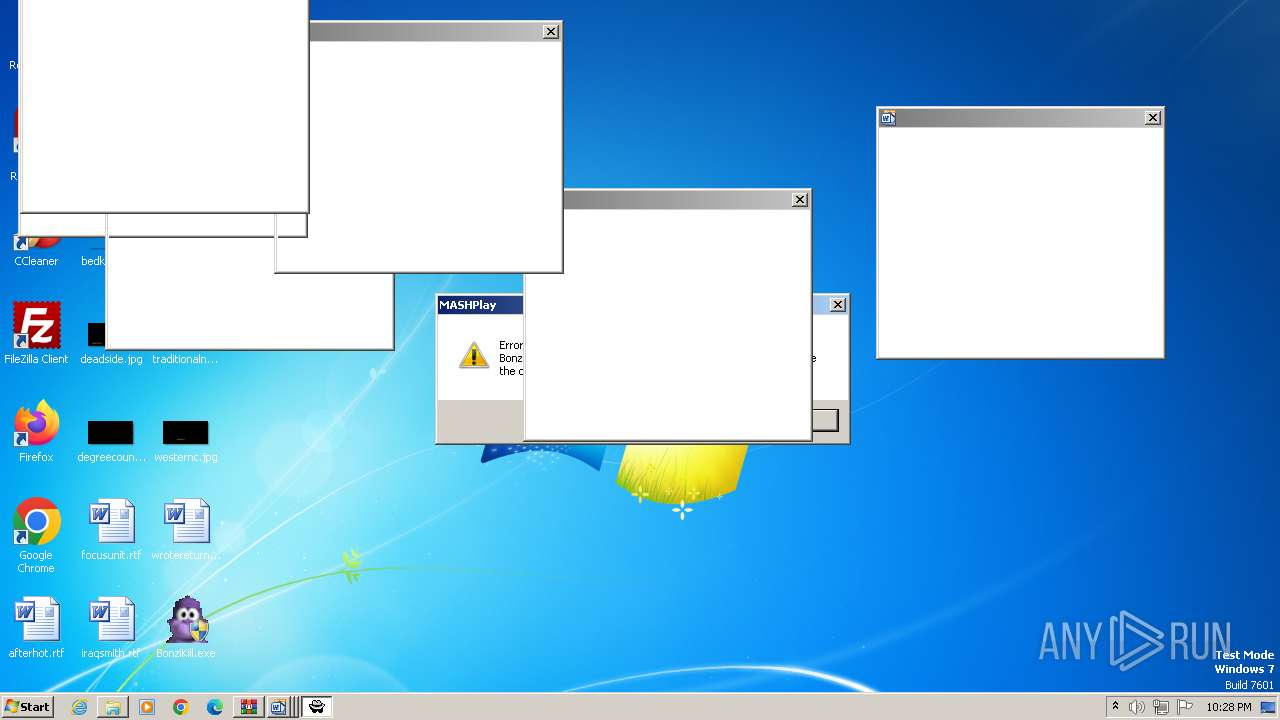
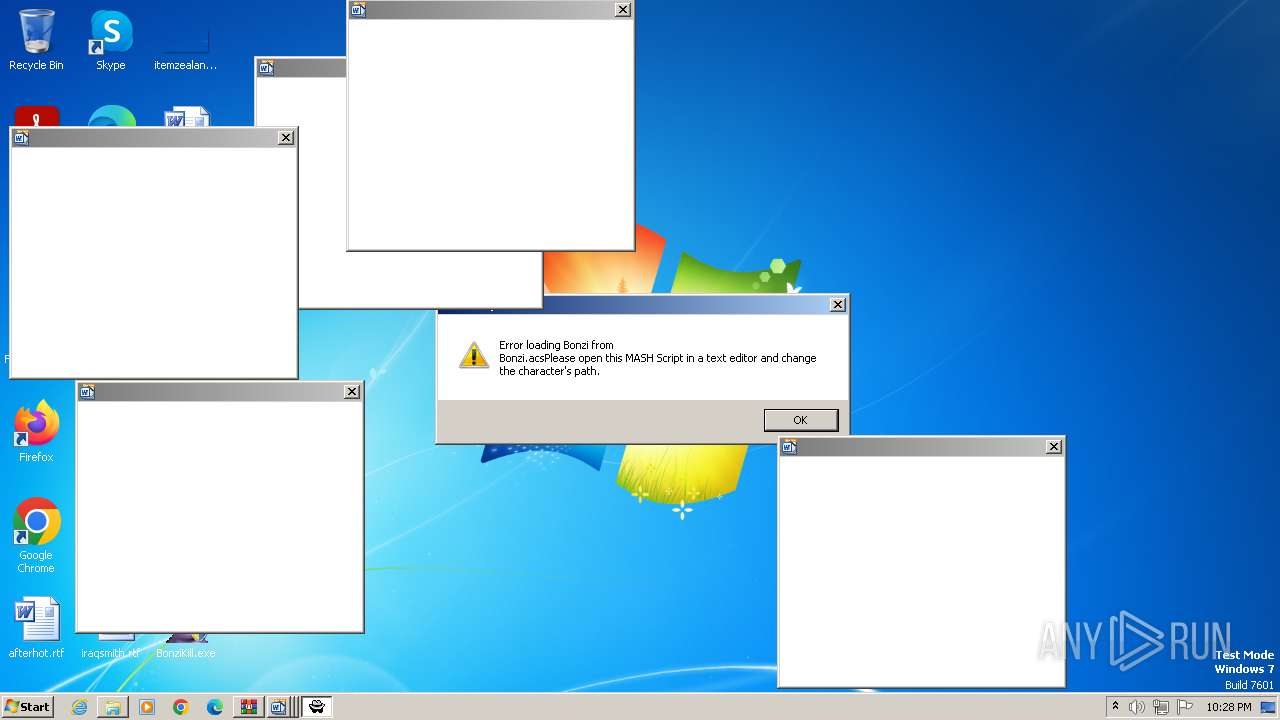
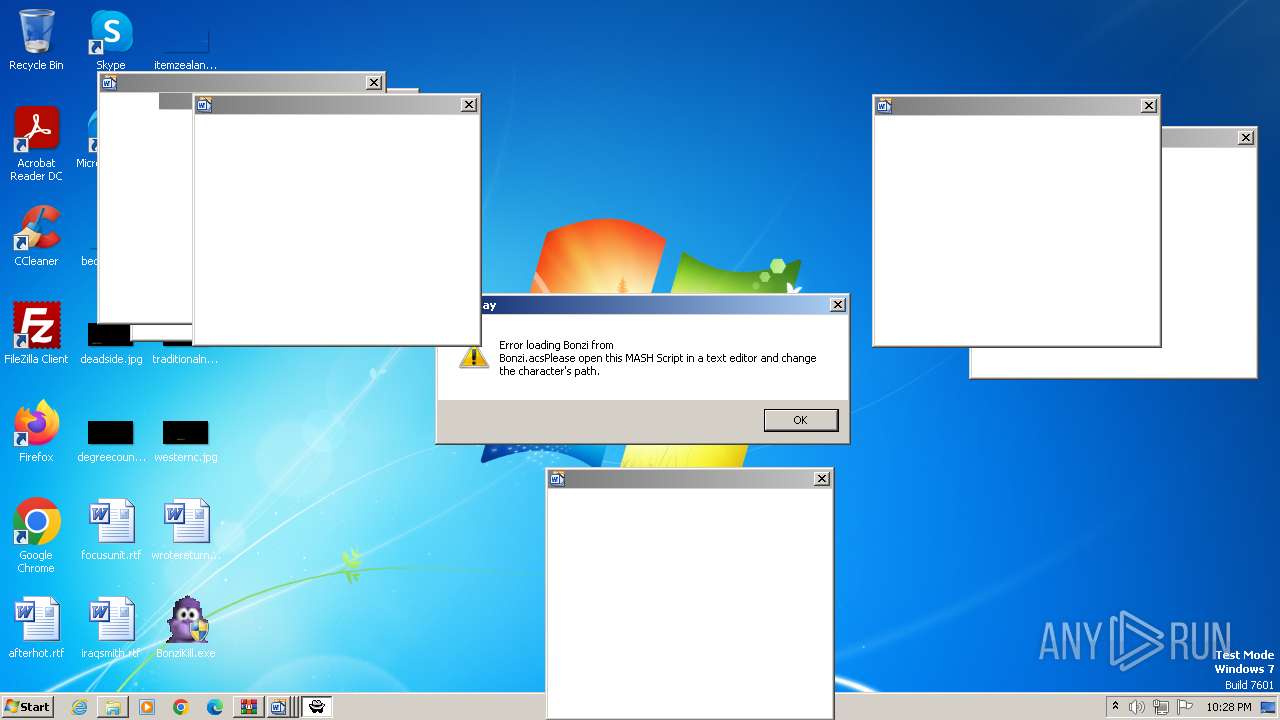
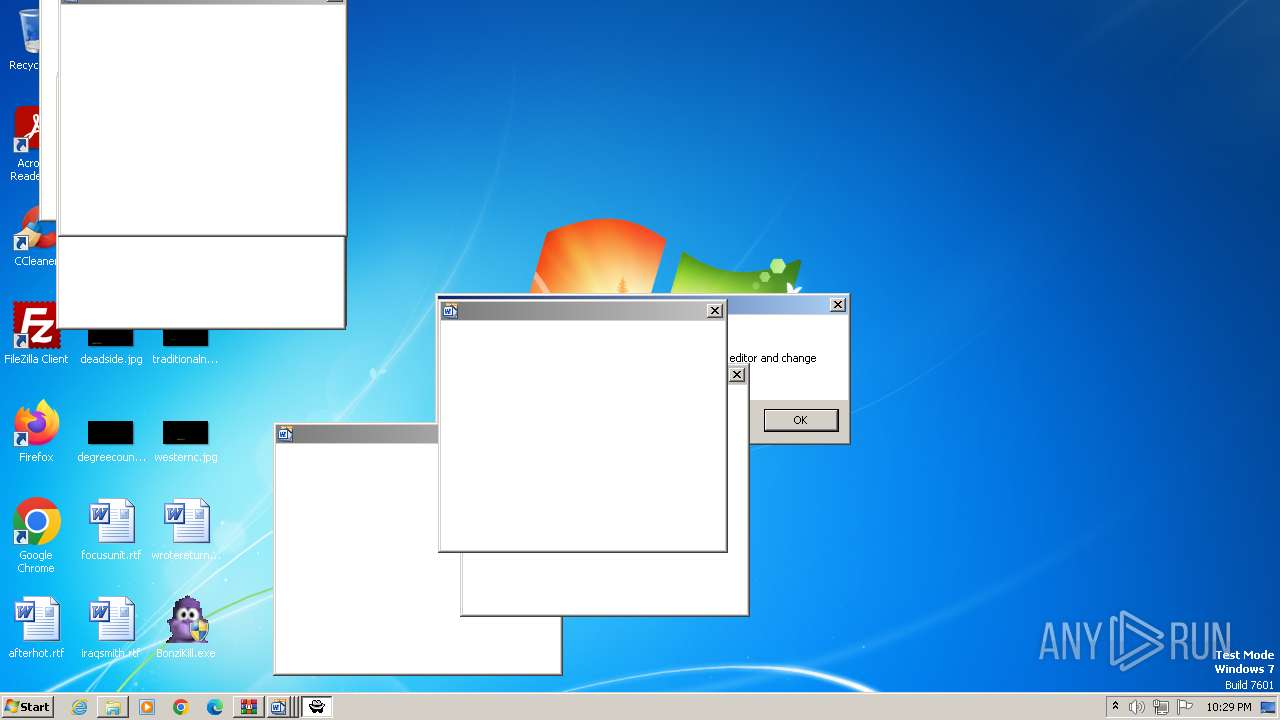
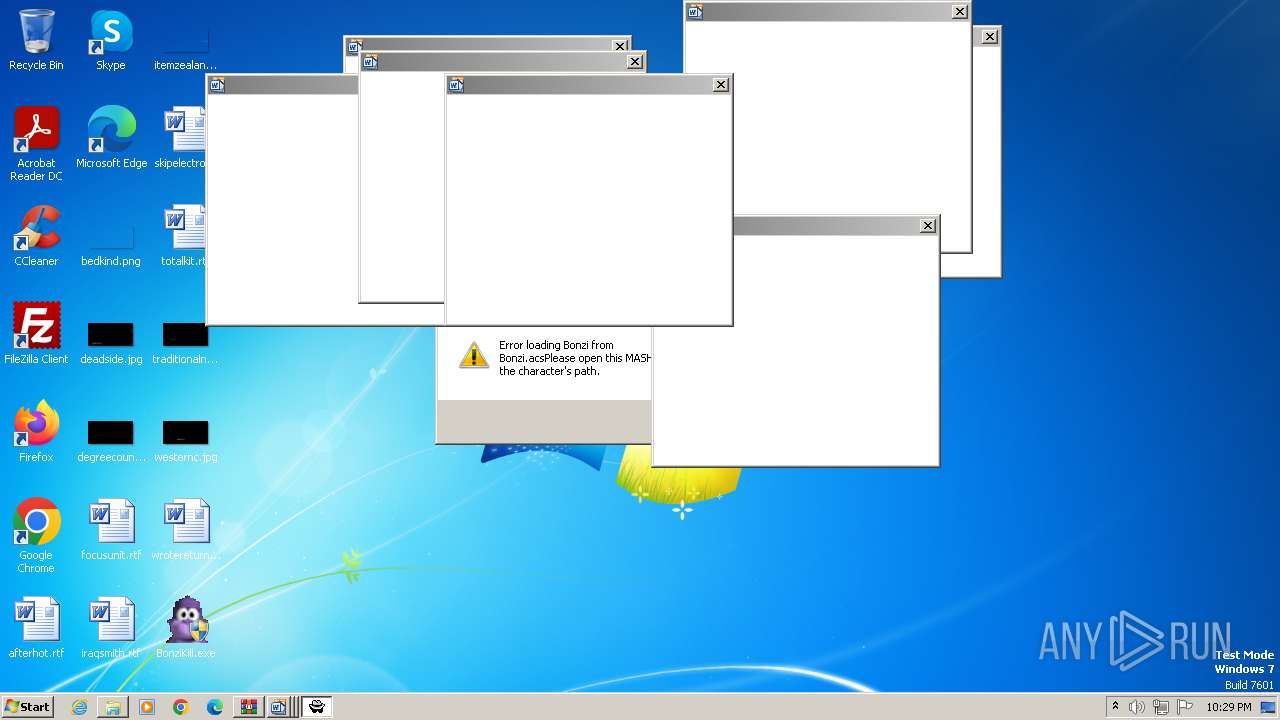
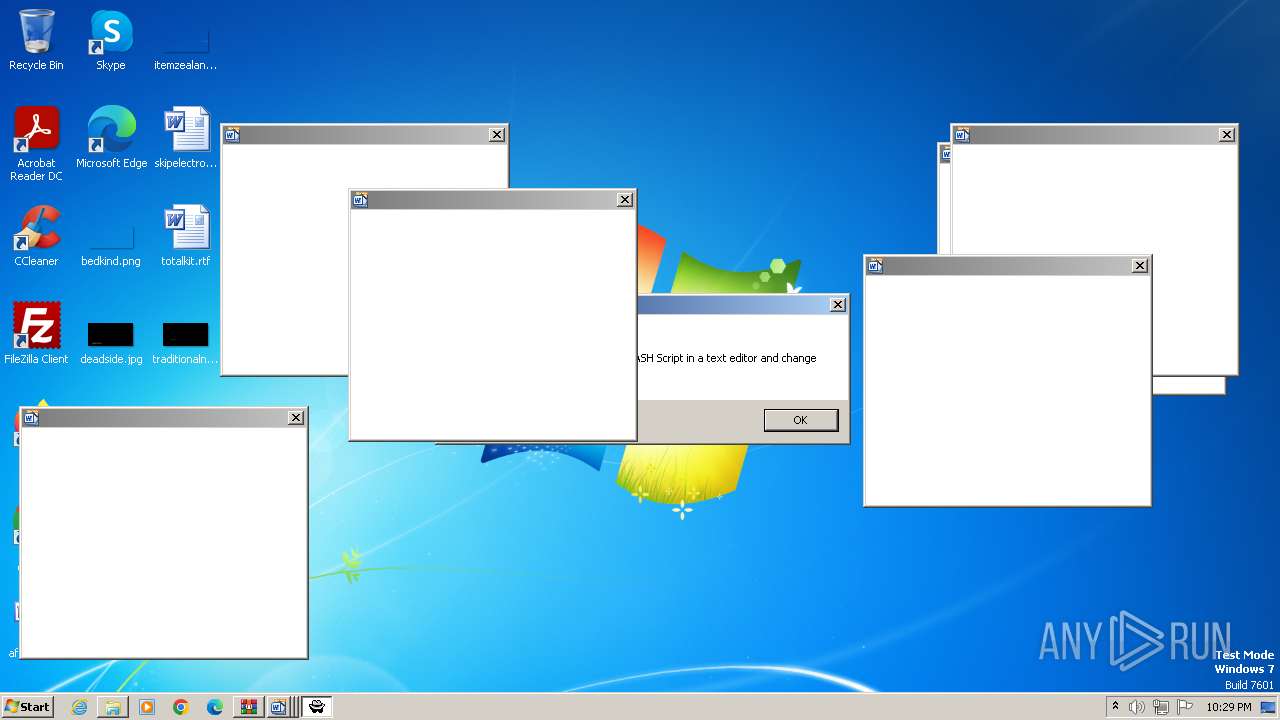
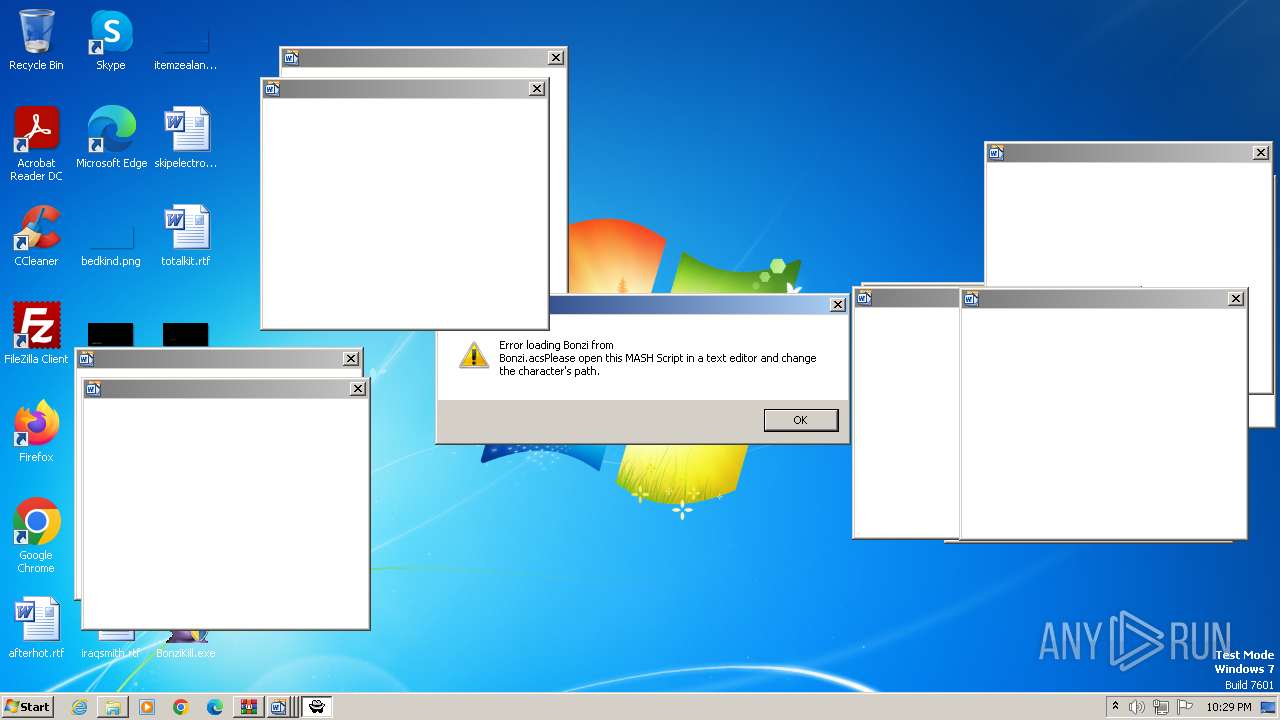
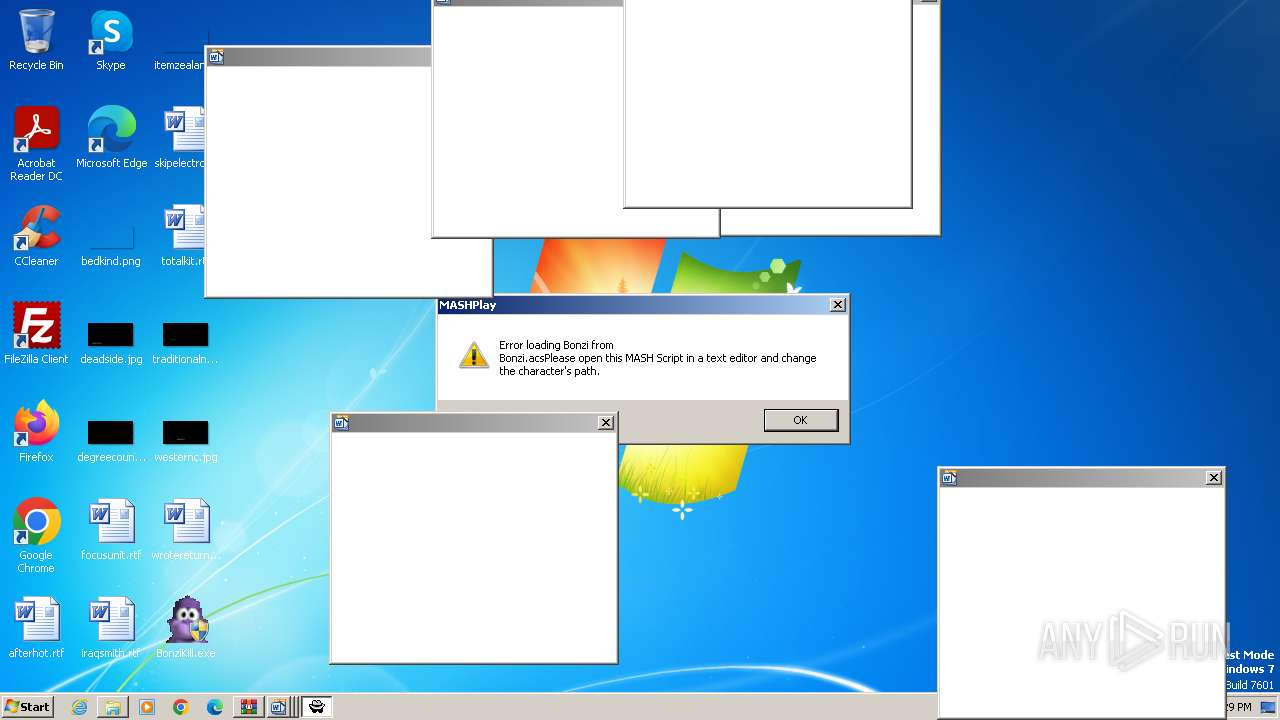
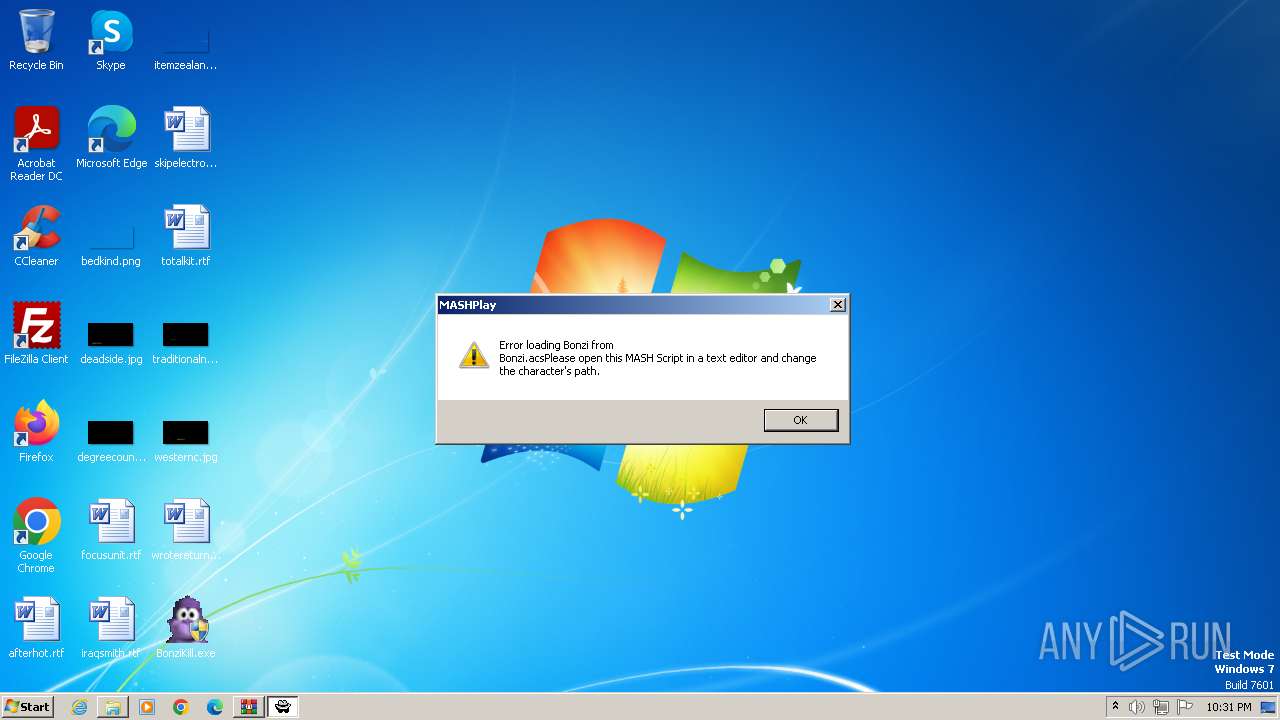
| 3796 | "C:\bonzi\BonziBuddy_original.exe" | C:\bonzi\BonziBuddy_original.exe | — | BonziKill.exe | |||||||||||
User: admin Company: BellCraft Technologies Integrity Level: HIGH Exit code: 0 Version: 7.05 Modules
| |||||||||||||||
| 3876 | "C:\bonzi\BonziBuddy_original.exe" | C:\bonzi\BonziBuddy_original.exe | — | BonziKill.exe | |||||||||||
User: admin Company: BellCraft Technologies Integrity Level: HIGH Exit code: 3221225547 Version: 7.05 Modules
| |||||||||||||||
| 3936 | "C:\bonzi\BonziBuddy_original.exe" | C:\bonzi\BonziBuddy_original.exe | — | BonziKill.exe | |||||||||||
User: admin Company: BellCraft Technologies Integrity Level: HIGH Exit code: 3221225547 Version: 7.05 Modules
| |||||||||||||||
| 4032 | "C:\Users\admin\Desktop\BonziKill.exe" | C:\Users\admin\Desktop\BonziKill.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1000 Modules
| |||||||||||||||
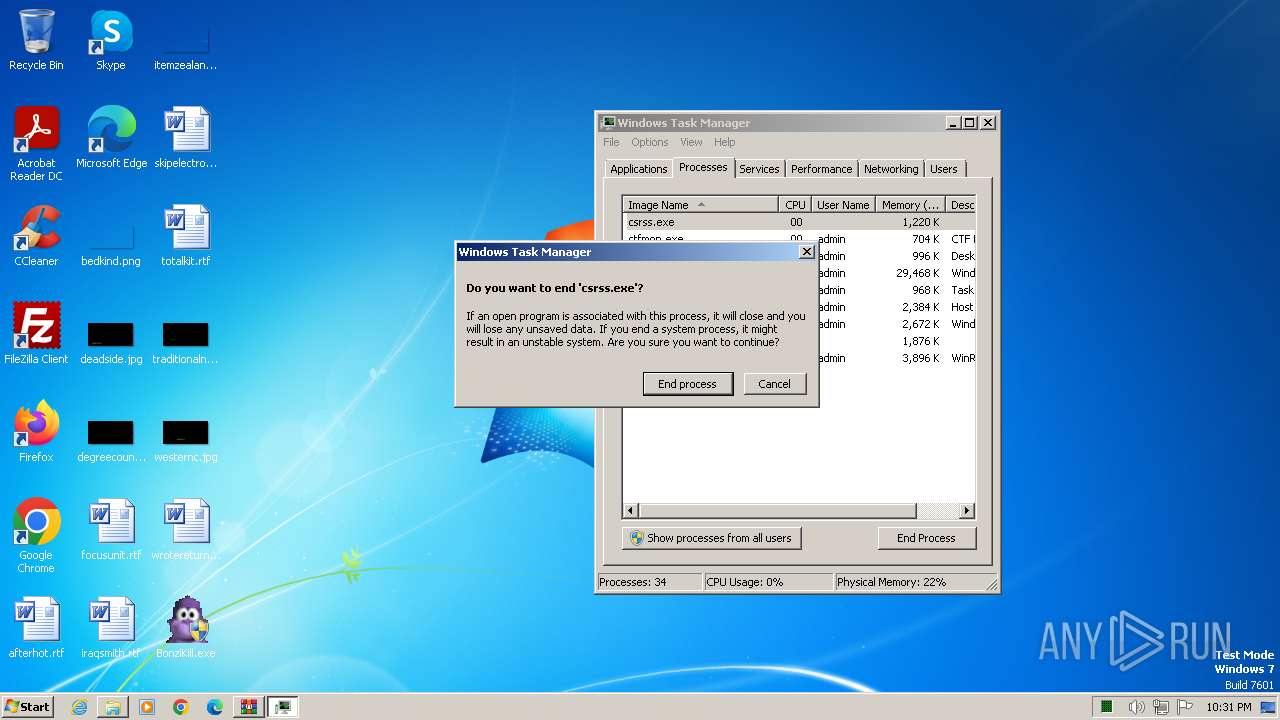
| 4196 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\System32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
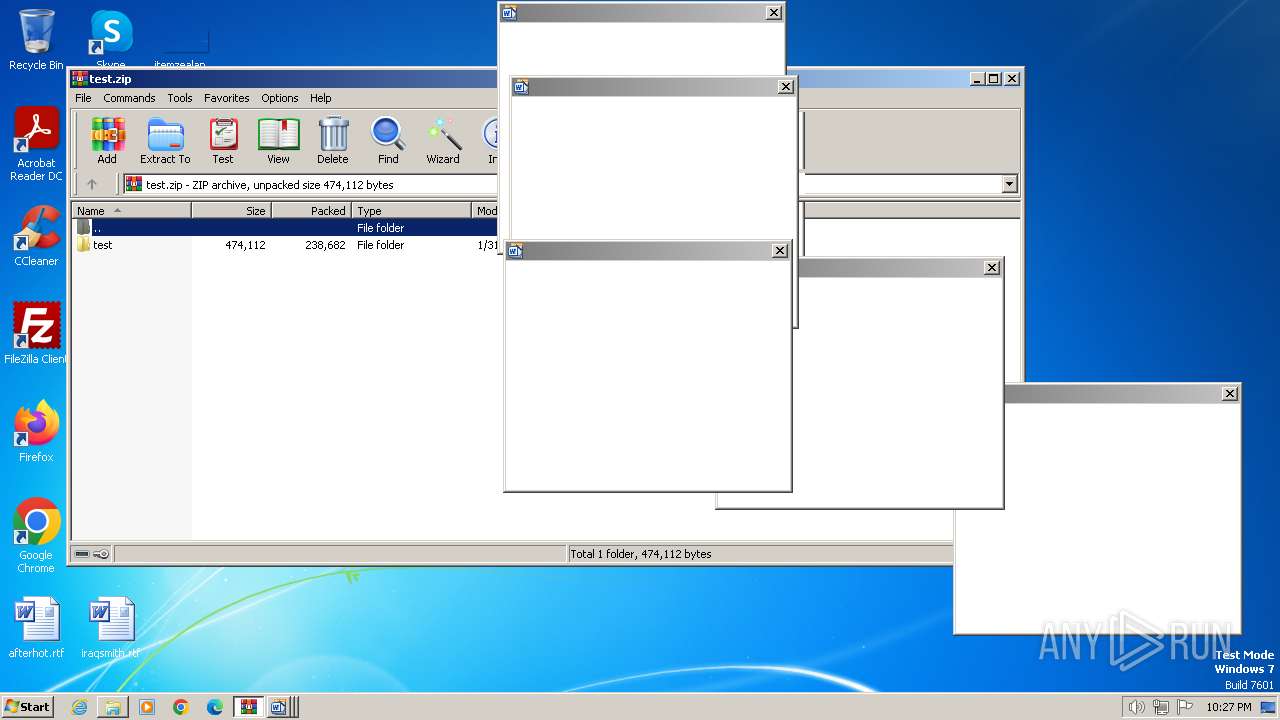
Total events
3 597
Read events
3 561
Write events
36
Delete events
0
Modification events
| (PID) Process: | (1380) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1380) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (1380) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (1380) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1380) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (1380) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1380) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1380) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1380) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4032) BonziKill.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
261
Suspicious files
364
Text files
611
Unknown types
0
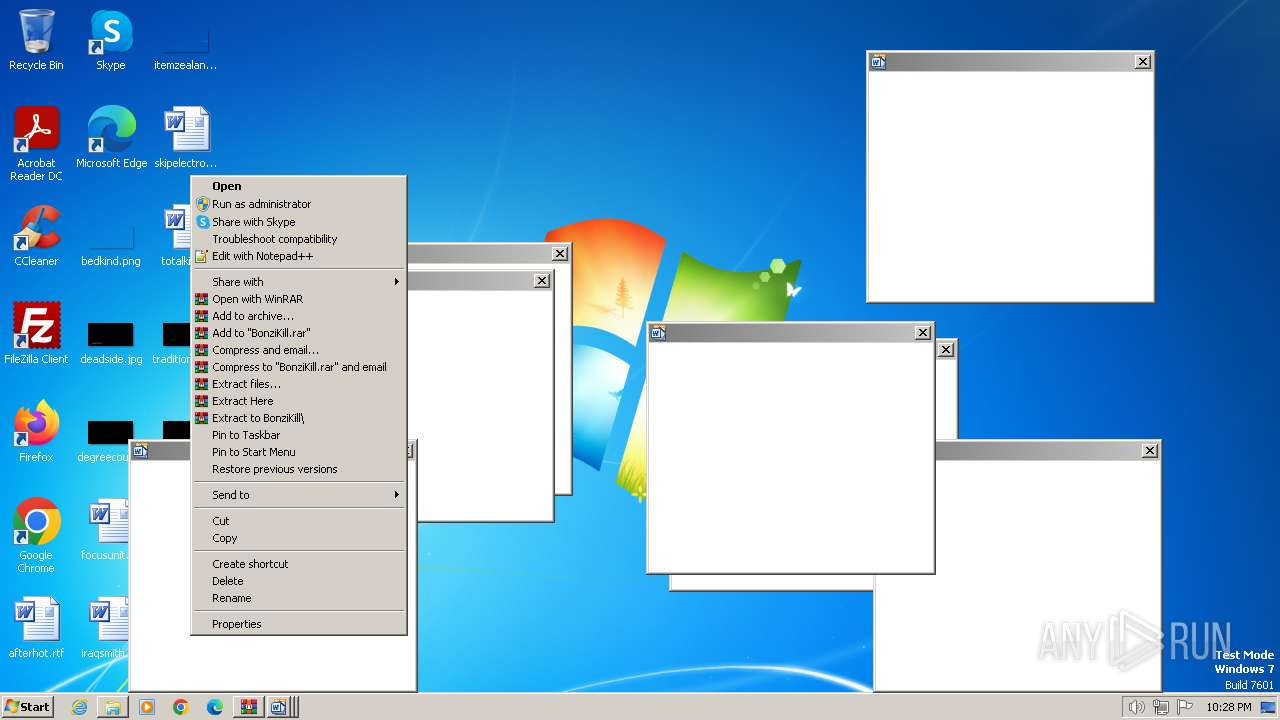
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4032 | BonziKill.exe | C:\bonzi\bob.exe | — | |
MD5:— | SHA256:— | |||
| 4032 | BonziKill.exe | C:\bonzi\dicks.wav | — | |
MD5:— | SHA256:— | |||
| 4032 | BonziKill.exe | C:\bonzi\boi.bat | text | |
MD5:E3FB07DBA9803C1F174B725D2A05EA51 | SHA256:A7A14AFE50AC26962F92BAFBCADEAD48CA2E8FCB546CB259819BACD8156FAE84 | |||
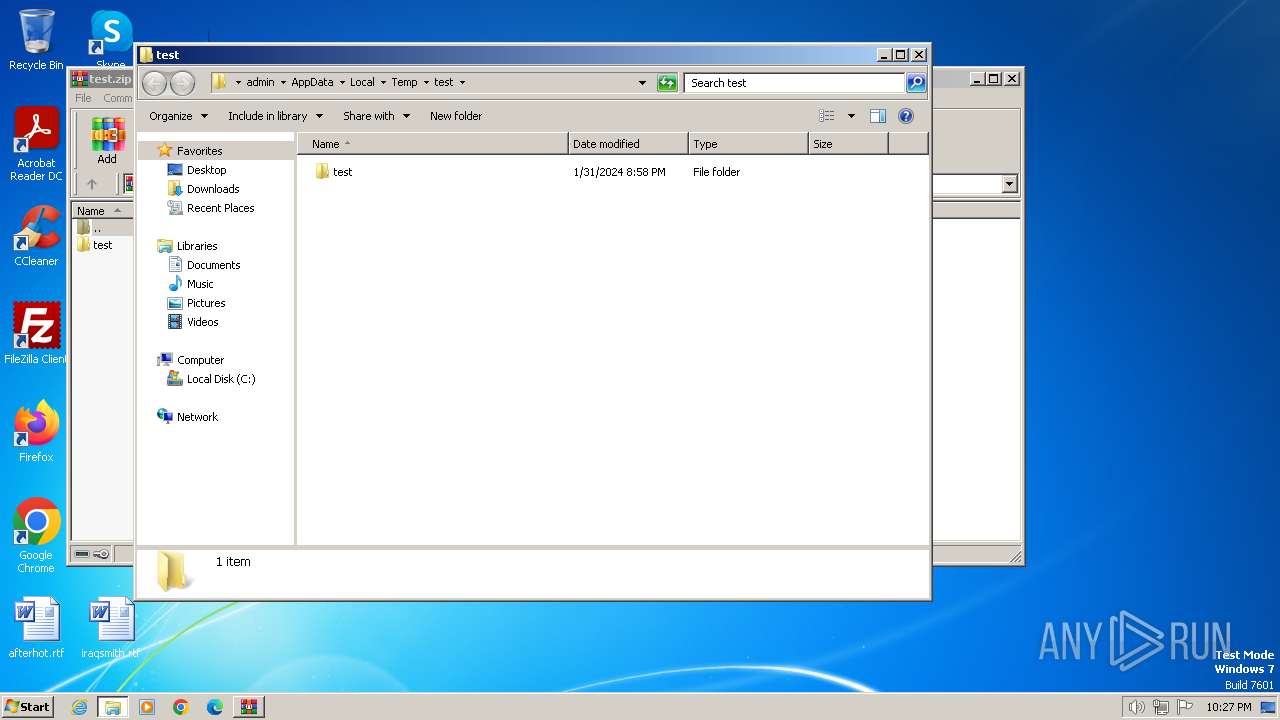
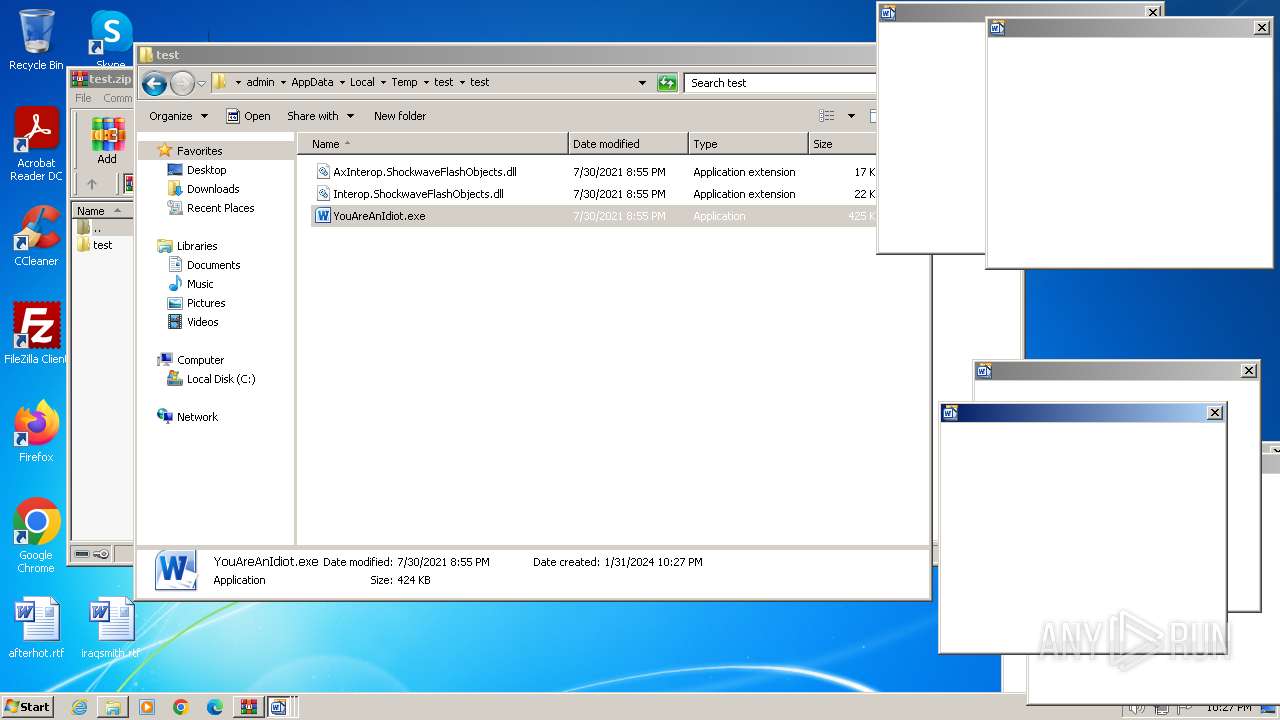
| 1380 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\test\test\Interop.ShockwaveFlashObjects.dll | executable | |
MD5:E869D1D4545C212D9068A090A370DED3 | SHA256:63AF704211A03F6FF6530EBFCA095B6C97636AB66E5A6DE80D167B19C3C30C66 | |||
| 1380 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\test\test\AxInterop.ShockwaveFlashObjects.dll | executable | |
MD5:451112D955AF4FE3C0D00F303D811D20 | SHA256:0D57A706D4E10CCA3AED49B341A651F29046F5EF1328878D616BE93C3B4CBCE9 | |||
| 4032 | BonziKill.exe | C:\bonzi\midi.bat | text | |
MD5:27D92EBFADFABCE5AB3FA8F842E6A2E8 | SHA256:2ACB21881A9C9625C653DCF43A79C6F5FB81D65BEC36D290F12E1F2A6A7763C7 | |||
| 4032 | BonziKill.exe | C:\bonzi\BonziBuddy_original.exe | executable | |
MD5:FF8E3BEF2B1C444E59D21D5291C81D96 | SHA256:50A65FFCB48CB6BA99CCF79D855696CFDFB28FF21D0F71666C8FAE9DFEDF878E | |||
| 4032 | BonziKill.exe | C:\bonzi\blue.exe | executable | |
MD5:C3C1F4FF433DF26B896DEDDACB5817F0 | SHA256:BC8F7334495C673DD646D092AFDABBFB84EDB5282A25D9D8B1D3CEADC019478B | |||
| 4032 | BonziKill.exe | C:\bonzi\BonzVir.msh | text | |
MD5:0CF59661F4B25D7BCE496B51264CF6EF | SHA256:14ED561155EF917214695A958392FE53295E1B972BD247DA7672E7D38CC4EAB2 | |||
| 3248 | YouAreAnIdiot.exe | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\openssl\cache\RevocationCacheFile.dat | binary | |
MD5:0F343B0931126A20F133D67C2B018A3B | SHA256:5F70BF18A086007016E948B04AED3B82103A36BEA41755B6CDDFAF10ACE3C6EF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
10
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3248 | YouAreAnIdiot.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | unknown | binary | 471 b | unknown |
3248 | YouAreAnIdiot.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | unknown | binary | 471 b | unknown |
3248 | YouAreAnIdiot.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | unknown | binary | 471 b | unknown |
3248 | YouAreAnIdiot.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3248 | YouAreAnIdiot.exe | 2.19.105.74:443 | geo2.adobe.com | AKAMAI-AS | DE | whitelisted |
3248 | YouAreAnIdiot.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3248 | YouAreAnIdiot.exe | 23.192.254.115:443 | fpdownload.macromedia.com | AKAMAI-AS | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
geo2.adobe.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fpdownload.macromedia.com |
| whitelisted |