| URL: | https://link.sbstck.com/redirect/cc7c5b35-0421-431a-ada0-ff4f1c517d6d?j=eyJ1IjoiNG9na2ZoIn0.GfcJYrQ3bnal_X7-wzmgAbk8Z7xmBsIcJlcVoVwUntc |
| Full analysis: | https://app.any.run/tasks/9200cd85-f89e-40df-80cc-9adf0d7ea907 |
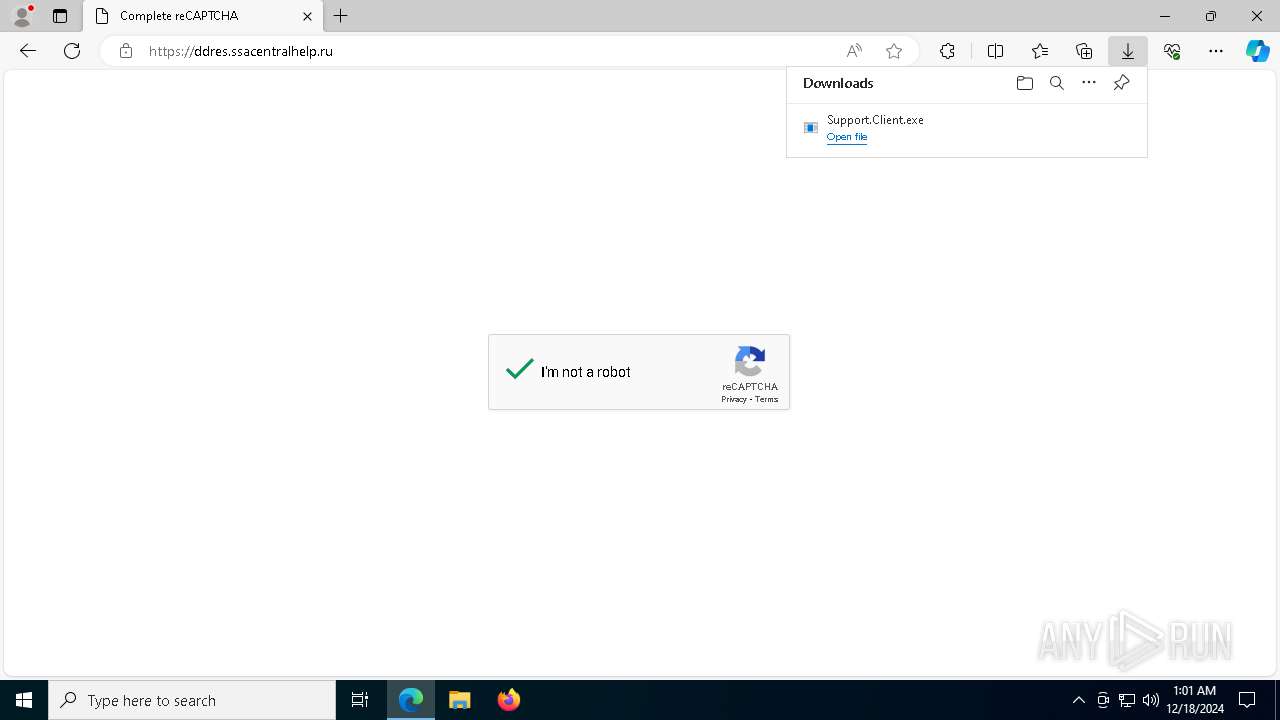
| Verdict: | Malicious activity |
| Analysis date: | December 18, 2024, 01:00:47 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 83197D4DB3A8A2D6FC02A24E95CD5580 |
| SHA1: | 45D9D7F9404695238B4FF31DEC6484B73B262D4F |
| SHA256: | 593F16963A2B97E8F1ADE55BAA97299BE92979B34C2EC0FEC3A5749FD035C623 |
| SSDEEP: | 3:N8MLk9GO2GySY3hQOuc9rwv7VW1kA8Hmy+sEkKkn:2Mg9GbGyt3M0wvRMkA8Hmy+RY |
MALICIOUS
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 6732)
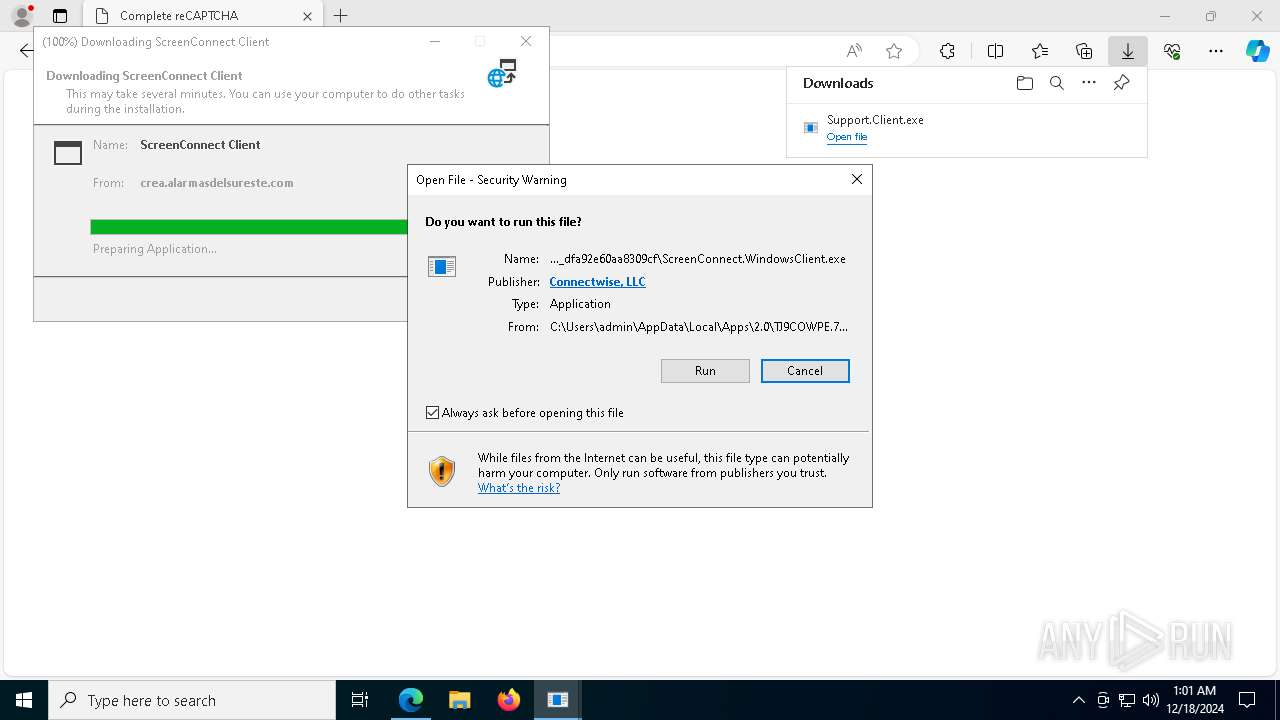
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 4076)
SUSPICIOUS
Reads security settings of Internet Explorer
- dfsvc.exe (PID: 7664)
- ScreenConnect.WindowsClient.exe (PID: 3364)
- ScreenConnect.ClientService.exe (PID: 188)
- ScreenConnect.ClientService.exe (PID: 4076)
- ScreenConnect.WindowsClient.exe (PID: 2008)
- ScreenConnect.WindowsClient.exe (PID: 2280)
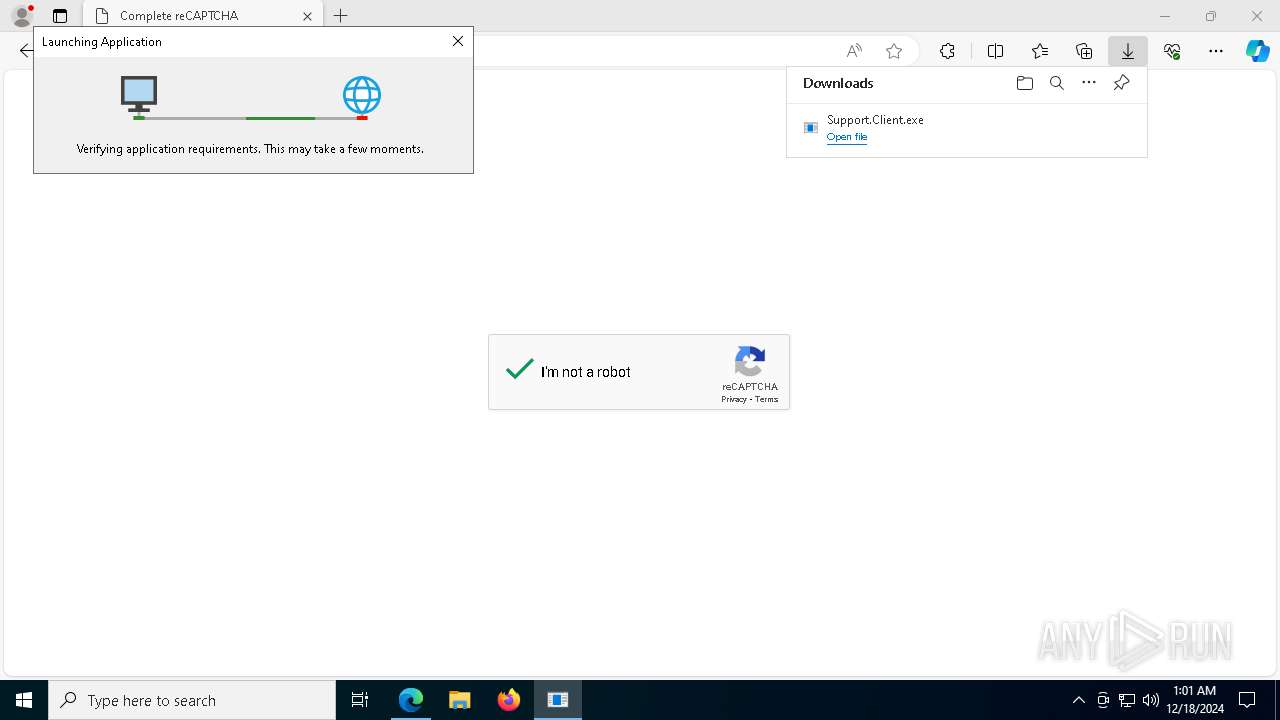
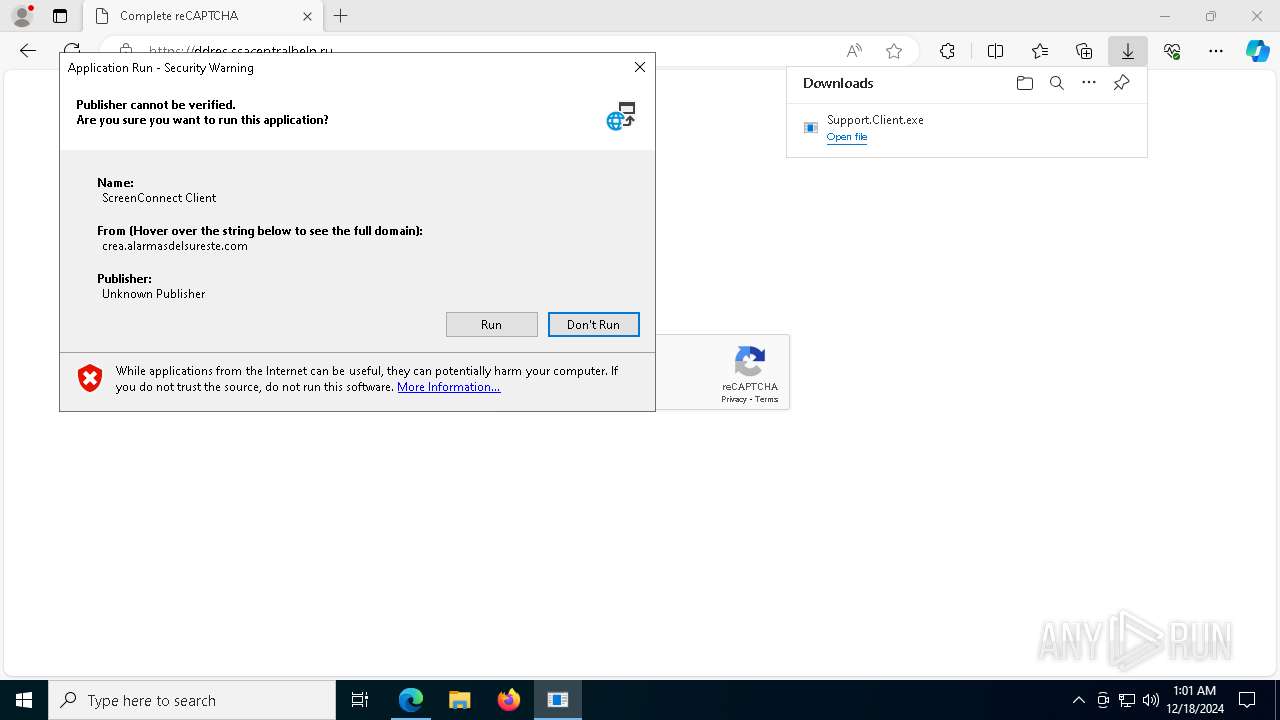
Checks Windows Trust Settings
- dfsvc.exe (PID: 7664)
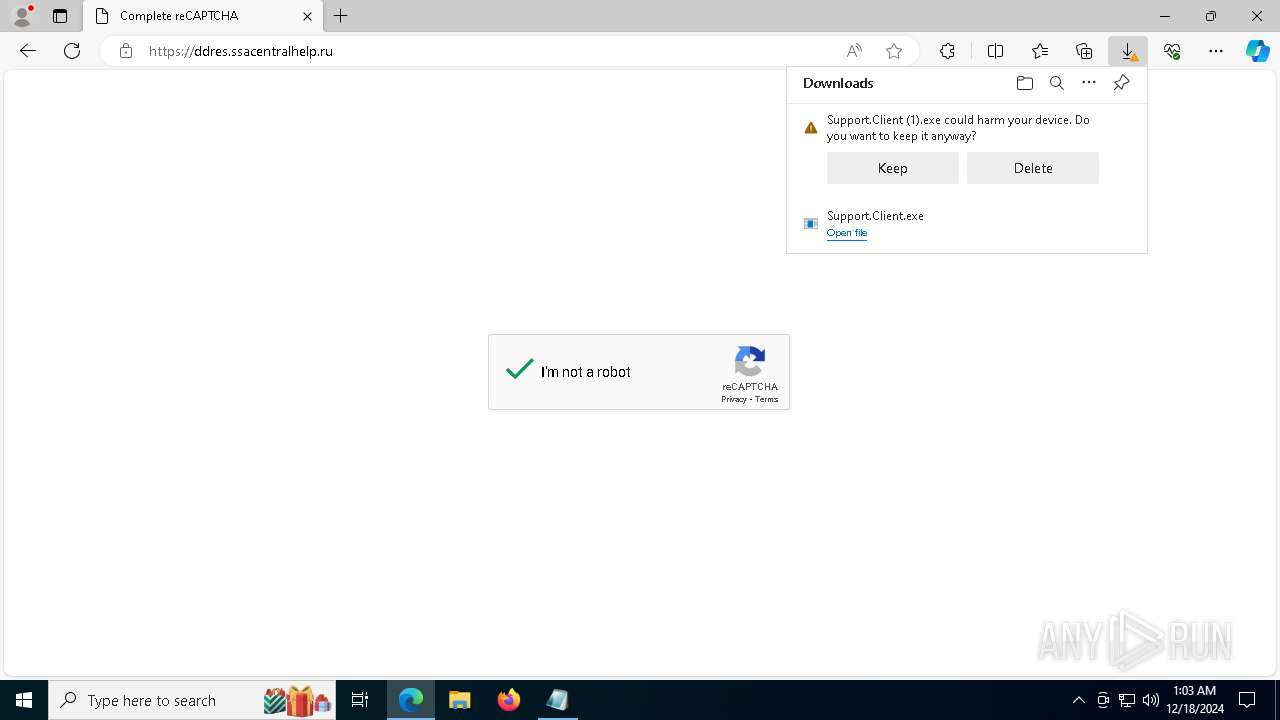
Executable content was dropped or overwritten
- dfsvc.exe (PID: 7664)
The process creates files with name similar to system file names
- dfsvc.exe (PID: 7664)
Reads Internet Explorer settings
- dfsvc.exe (PID: 7664)
Adds/modifies Windows certificates
- dfsvc.exe (PID: 7664)
- Support.Client.exe (PID: 1488)
Reads the date of Windows installation
- dfsvc.exe (PID: 7664)
- ScreenConnect.WindowsClient.exe (PID: 3364)
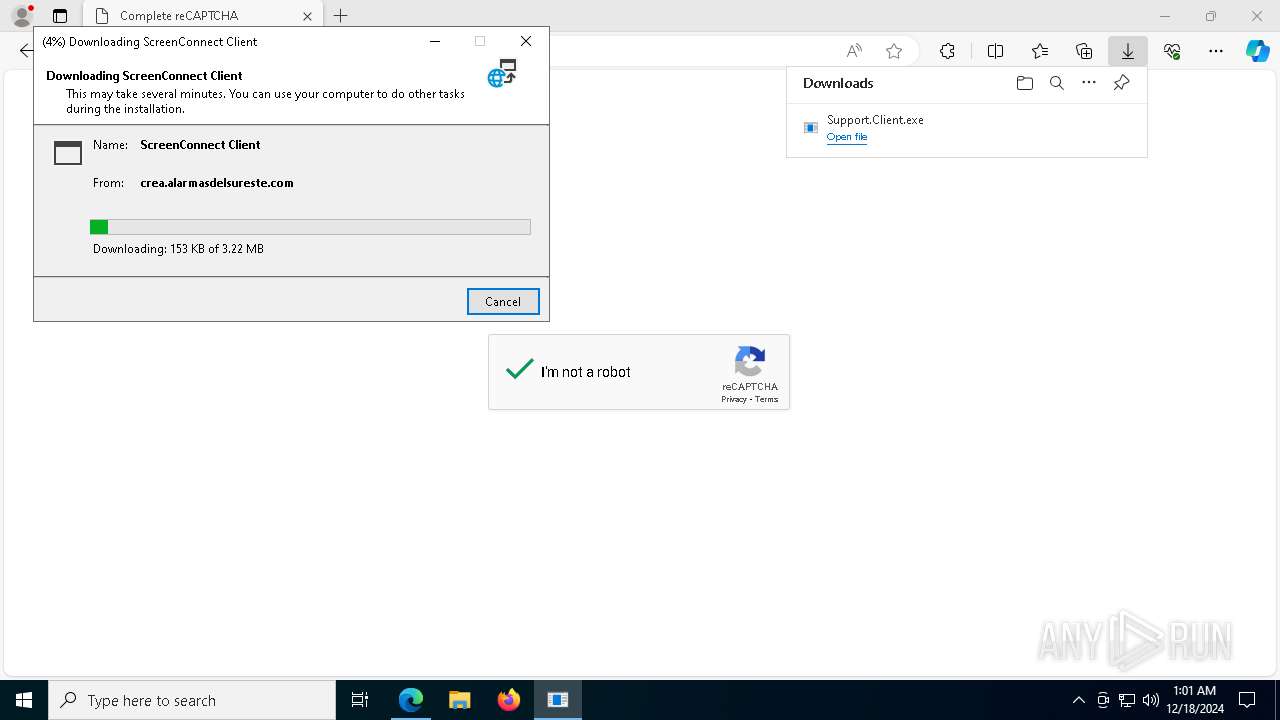
Creates or modifies Windows services
- ScreenConnect.ClientService.exe (PID: 4076)
Executes as Windows Service
- ScreenConnect.ClientService.exe (PID: 4076)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 4076)
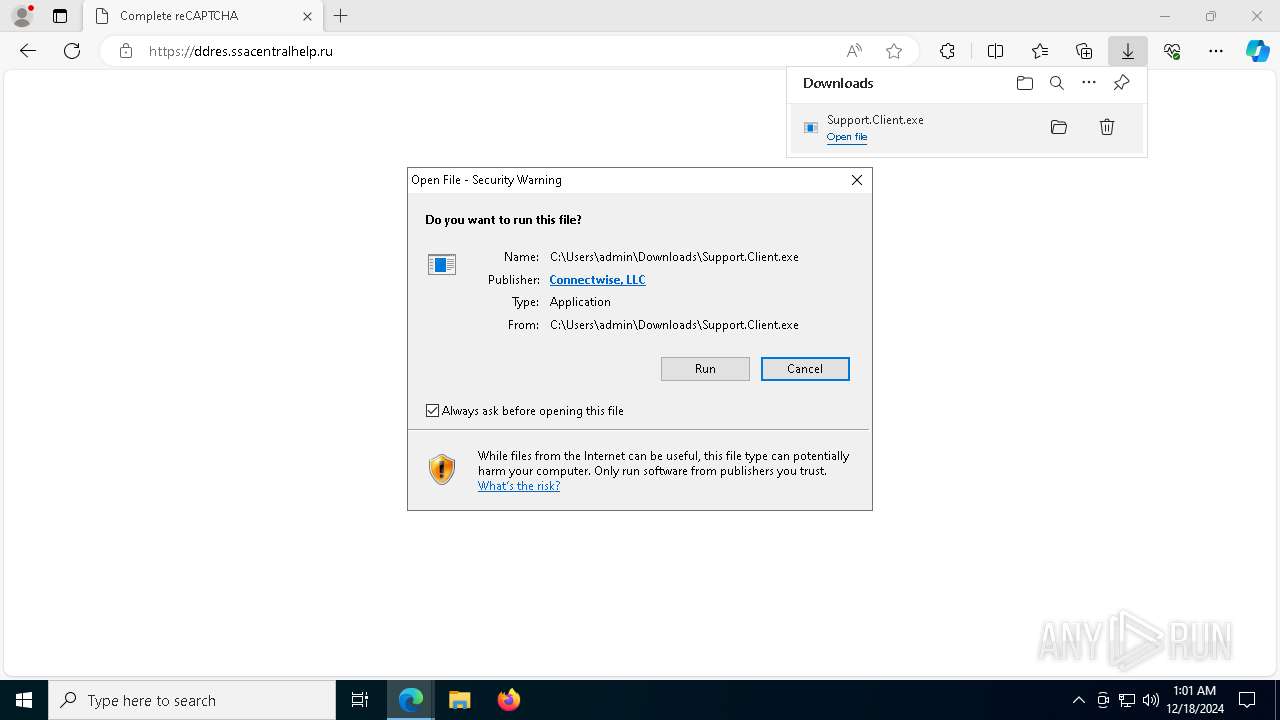
Executes application which crashes
- Support.Client.exe (PID: 1488)
There is functionality for taking screenshot (YARA)
- ScreenConnect.WindowsClient.exe (PID: 2008)
- ScreenConnect.ClientService.exe (PID: 4076)
Connects to unusual port
- ScreenConnect.ClientService.exe (PID: 4076)
INFO
Checks supported languages
- identity_helper.exe (PID: 7564)
- dfsvc.exe (PID: 7664)
- Support.Client.exe (PID: 1488)
- ScreenConnect.WindowsClient.exe (PID: 3364)
- ScreenConnect.ClientService.exe (PID: 188)
- ScreenConnect.ClientService.exe (PID: 4076)
- ScreenConnect.WindowsClient.exe (PID: 2008)
- ScreenConnect.WindowsClient.exe (PID: 2280)
Reads Environment values
- identity_helper.exe (PID: 7564)
- dfsvc.exe (PID: 7664)
Reads the computer name
- identity_helper.exe (PID: 7564)
- dfsvc.exe (PID: 7664)
- Support.Client.exe (PID: 1488)
- ScreenConnect.WindowsClient.exe (PID: 3364)
- ScreenConnect.ClientService.exe (PID: 188)
- ScreenConnect.WindowsClient.exe (PID: 2008)
- ScreenConnect.ClientService.exe (PID: 4076)
- ScreenConnect.WindowsClient.exe (PID: 2280)
Executable content was dropped or overwritten
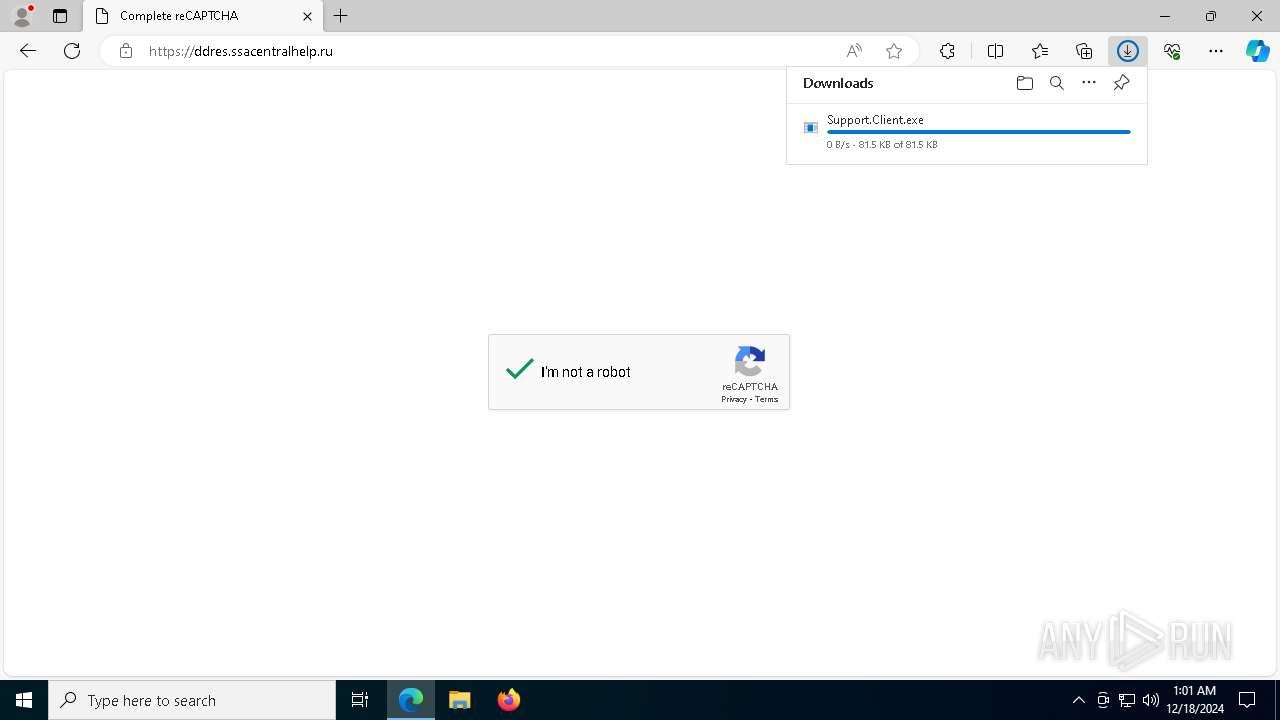
- msedge.exe (PID: 6420)
- msedge.exe (PID: 6732)
- msedge.exe (PID: 5544)
The process uses the downloaded file
- msedge.exe (PID: 6420)
- msedge.exe (PID: 6188)
- dfsvc.exe (PID: 7664)
- ScreenConnect.WindowsClient.exe (PID: 3364)
- ScreenConnect.ClientService.exe (PID: 188)
- ScreenConnect.ClientService.exe (PID: 4076)
- ScreenConnect.WindowsClient.exe (PID: 2280)
- ScreenConnect.WindowsClient.exe (PID: 2008)
Reads the machine GUID from the registry
- Support.Client.exe (PID: 1488)
- dfsvc.exe (PID: 7664)
- ScreenConnect.WindowsClient.exe (PID: 3364)
- ScreenConnect.ClientService.exe (PID: 188)
- ScreenConnect.ClientService.exe (PID: 4076)
- ScreenConnect.WindowsClient.exe (PID: 2008)
- ScreenConnect.WindowsClient.exe (PID: 2280)
Checks proxy server information
- dfsvc.exe (PID: 7664)
- WerFault.exe (PID: 1856)
Disables trace logs
- dfsvc.exe (PID: 7664)
Application launched itself
- msedge.exe (PID: 6420)
Creates files or folders in the user directory
- dfsvc.exe (PID: 7664)
- ScreenConnect.WindowsClient.exe (PID: 3364)
- ScreenConnect.ClientService.exe (PID: 4076)
- WerFault.exe (PID: 1856)
Reads the software policy settings
- dfsvc.exe (PID: 7664)
- WerFault.exe (PID: 1856)
Process checks whether UAC notifications are on
- dfsvc.exe (PID: 7664)
Create files in a temporary directory
- dfsvc.exe (PID: 7664)
Process checks computer location settings
- dfsvc.exe (PID: 7664)
- ScreenConnect.WindowsClient.exe (PID: 3364)
Sends debugging messages
- dfsvc.exe (PID: 7664)
Reads CPU info
- ScreenConnect.WindowsClient.exe (PID: 2280)
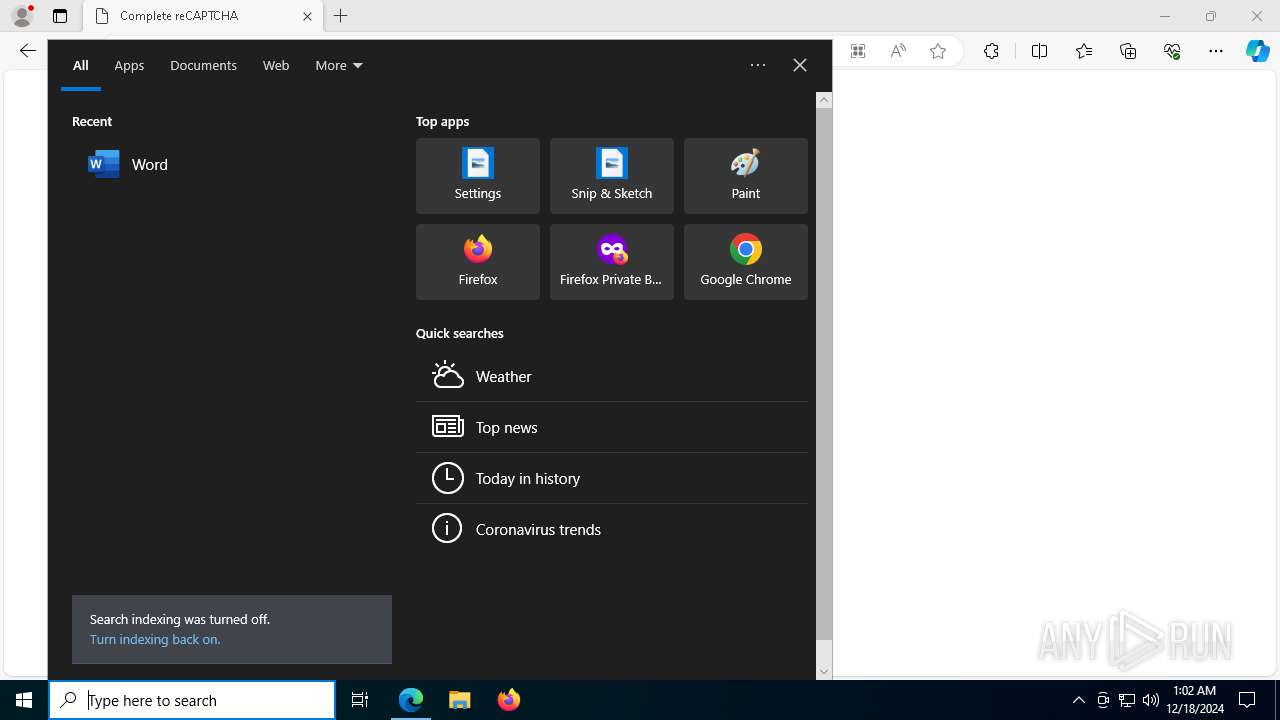
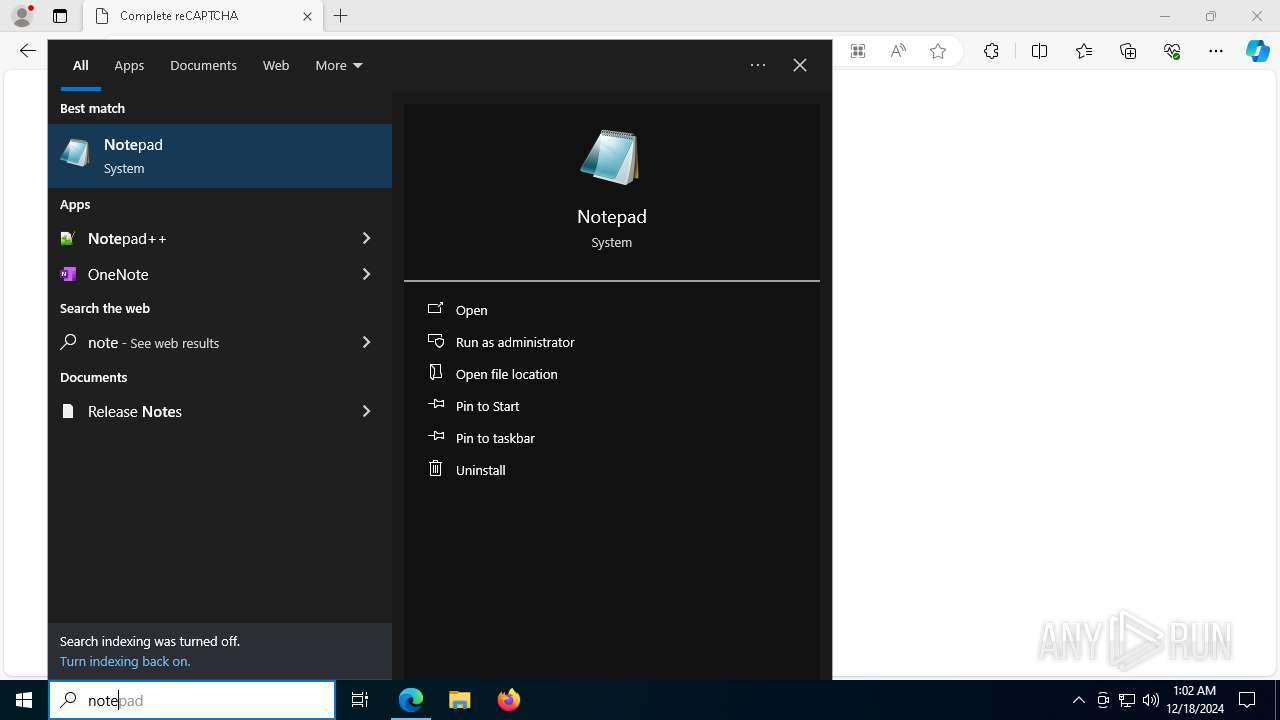
Manual execution by a user
- notepad.exe (PID: 7948)
The sample compiled with english language support
- msedge.exe (PID: 5544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
216
Monitored processes
76
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6204 --field-trial-handle=2316,i,8084750194685327235,2991910020201298893,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 188 | "C:\Users\admin\AppData\Local\Apps\2.0\TJ9COWPE.7PK\RVKW6JBA.Q6M\scre..tion_25b0fbb6ef7eb094_0018.0002_dfa92e60aa8309cf\ScreenConnect.ClientService.exe" "?e=Support&y=Guest&h=0bd0.adrsxpjm0rga0n.de&p=8041&s=71e4dd28-010d-4763-bae4-587cc6789e21&k=BgIAAACkAABSU0ExAAgAAAEAAQBdRYPv%2fs%2bijGK1u%2flkqPsG%2bdG7F%2f4ax8QNSH9Yo6i7A6UZdAY2kZfgAMhSjF%2fKrmKc4KX%2fDk9ZtiCRIRrmQh3eoku1a3oxQ2phk099M%2brHxm%2fsY2PWCCL%2fy3eISyDDs8dYSd7NyaWC%2bZQBDk%2bCMboNgHDqg5TZ2DZSQbH4e9PpCOhBmemQ0OLPi7s6np%2fBxp4rKNbDymsYFM0a6KINC%2bdchq29F%2bXHGl%2fK%2fQmGvHtdIpX8%2bO%2fTtZQDOLPXW57J20w3ypOH%2bHf7phXvddrwOTzrArQoTCReWUatoySRLumG3cOPSFHex5FRYf45W%2bMRD4DXmWP56lW1jk7oCGLWlFHE&r=&i=Untitled%20Session" "1" | C:\Users\admin\AppData\Local\Apps\2.0\TJ9COWPE.7PK\RVKW6JBA.Q6M\scre..tion_25b0fbb6ef7eb094_0018.0002_dfa92e60aa8309cf\ScreenConnect.ClientService.exe | ScreenConnect.WindowsClient.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 24.2.10.8991 Modules
| |||||||||||||||
| 836 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7224 --field-trial-handle=2316,i,8084750194685327235,2991910020201298893,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1228 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --no-appcompat-clear --mojo-platform-channel-handle=6992 --field-trial-handle=2316,i,8084750194685327235,2991910020201298893,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1328 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1428 --field-trial-handle=2316,i,8084750194685327235,2991910020201298893,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1356 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7208 --field-trial-handle=2316,i,8084750194685327235,2991910020201298893,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1488 | "C:\Users\admin\Downloads\Support.Client.exe" | C:\Users\admin\Downloads\Support.Client.exe | msedge.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 1604 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3828 --field-trial-handle=2316,i,8084750194685327235,2991910020201298893,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1620 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=8260 --field-trial-handle=2316,i,8084750194685327235,2991910020201298893,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1856 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 1488 -s 320 | C:\Windows\SysWOW64\WerFault.exe | Support.Client.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
21 345
Read events
21 112
Write events
203
Delete events
30
Modification events
| (PID) Process: | (6420) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6420) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6420) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6420) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6420) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 7C4B713A17882F00 | |||
| (PID) Process: | (6420) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 811D7A3A17882F00 | |||
| (PID) Process: | (6420) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328346 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C62578EB-54B0-459A-A013-ADCC9B6A4490} | |||
| (PID) Process: | (6420) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328346 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {5CA753FE-9AA5-482E-A9E3-68D33BC72948} | |||
| (PID) Process: | (6420) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328346 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {04D10D0A-6238-48A9-A7F0-C2DFF0129DD1} | |||
| (PID) Process: | (6420) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328346 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {227A580D-20E9-481D-954F-D3CE3A5A9968} | |||
Executable files
25
Suspicious files
568
Text files
137
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6420 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135334.TMP | — | |
MD5:— | SHA256:— | |||
| 6420 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6420 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135334.TMP | — | |
MD5:— | SHA256:— | |||
| 6420 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6420 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135334.TMP | — | |
MD5:— | SHA256:— | |||
| 6420 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6420 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135344.TMP | — | |
MD5:— | SHA256:— | |||
| 6420 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6420 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135353.TMP | — | |
MD5:— | SHA256:— | |||
| 6420 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
51
TCP/UDP connections
121
DNS requests
127
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1688 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8000 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8000 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8140 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1734853259&P2=404&P3=2&P4=jE2ejB9eHfHrjgMnpu5JXe9Jg9YRVcf%2b1ocJmV5hb5lndywaJVwrBdv88nNWWZV6O5McXrzg6tkwt0mYJ7paYg%3d%3d | unknown | — | — | whitelisted |
8140 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1734853259&P2=404&P3=2&P4=jE2ejB9eHfHrjgMnpu5JXe9Jg9YRVcf%2b1ocJmV5hb5lndywaJVwrBdv88nNWWZV6O5McXrzg6tkwt0mYJ7paYg%3d%3d | unknown | — | — | whitelisted |
8140 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1734853259&P2=404&P3=2&P4=jE2ejB9eHfHrjgMnpu5JXe9Jg9YRVcf%2b1ocJmV5hb5lndywaJVwrBdv88nNWWZV6O5McXrzg6tkwt0mYJ7paYg%3d%3d | unknown | — | — | whitelisted |
1688 | svchost.exe | GET | 200 | 2.16.164.106:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
8140 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/659eb513-f907-4672-9f89-efb5d63fc871?P1=1735023475&P2=404&P3=2&P4=C0d%2bAhvZCljaMFzod01jfP9nUde8ccIWOF9wwXGQCKv5DPd08NtxHtqG4RMta09CVBR0zioI89MxWwHPkKFU0A%3d%3d | unknown | — | — | whitelisted |
8140 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/659eb513-f907-4672-9f89-efb5d63fc871?P1=1735023475&P2=404&P3=2&P4=C0d%2bAhvZCljaMFzod01jfP9nUde8ccIWOF9wwXGQCKv5DPd08NtxHtqG4RMta09CVBR0zioI89MxWwHPkKFU0A%3d%3d | unknown | — | — | whitelisted |
8140 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/659eb513-f907-4672-9f89-efb5d63fc871?P1=1735023475&P2=404&P3=2&P4=C0d%2bAhvZCljaMFzod01jfP9nUde8ccIWOF9wwXGQCKv5DPd08NtxHtqG4RMta09CVBR0zioI89MxWwHPkKFU0A%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1688 | svchost.exe | 2.16.164.106:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5064 | SearchApp.exe | 2.23.209.187:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
1688 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5968 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6732 | msedge.exe | 188.114.96.3:443 | link.sbstck.com | — | — | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
link.sbstck.com |
| malicious |
business.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
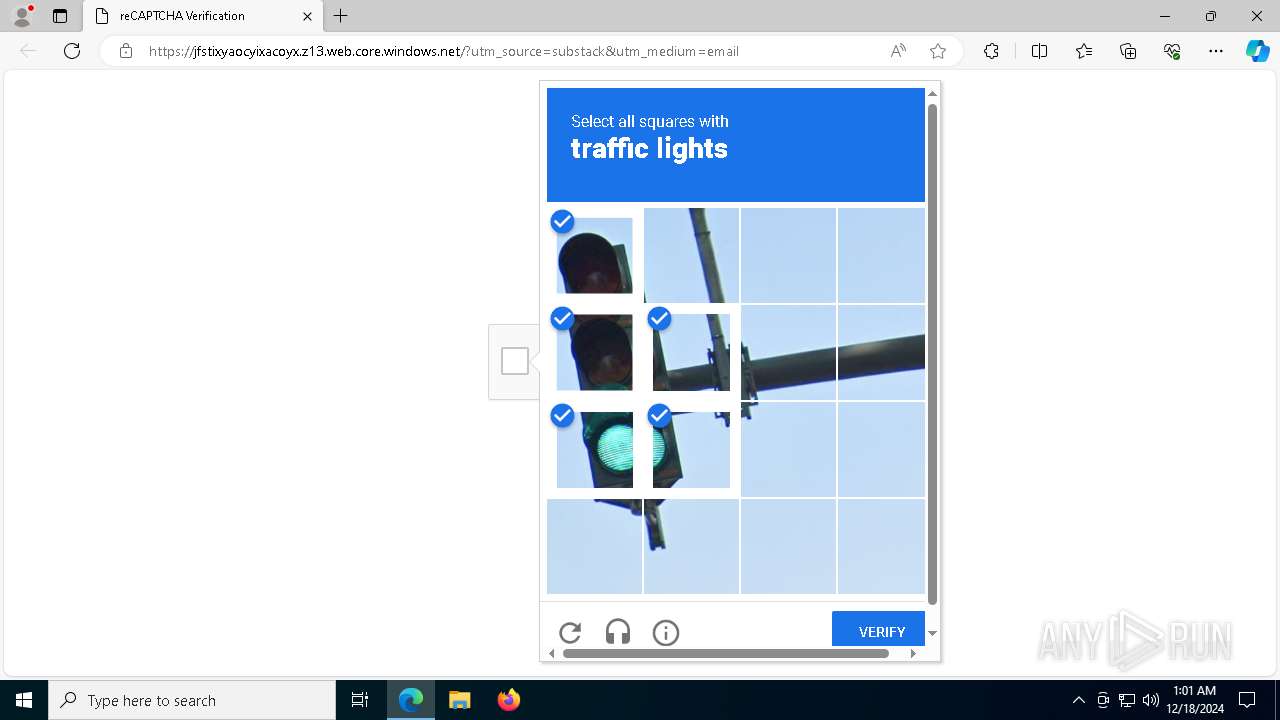
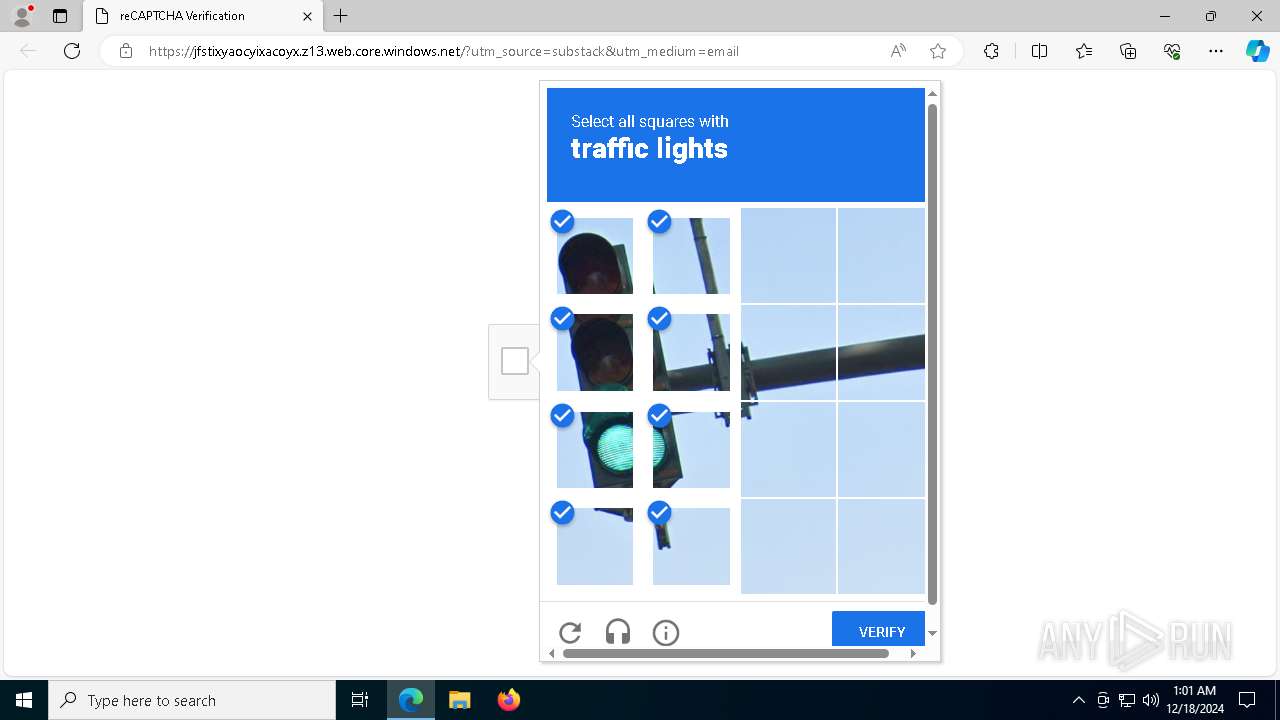
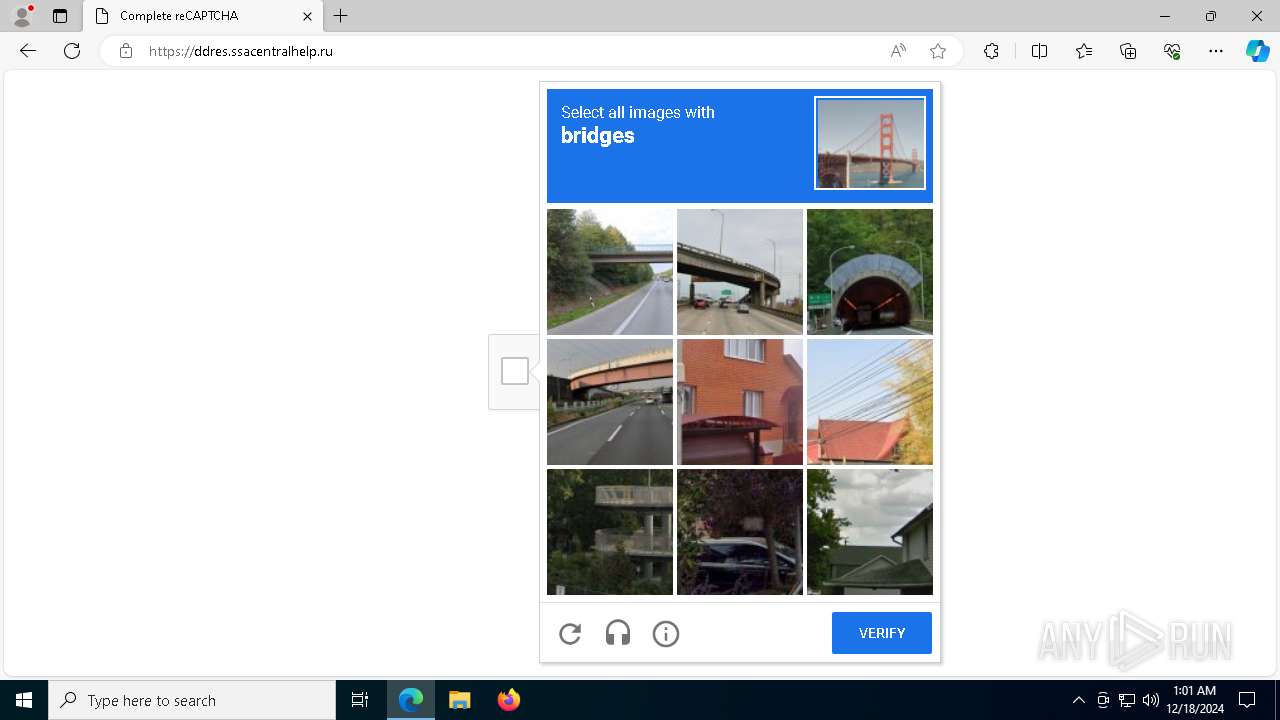
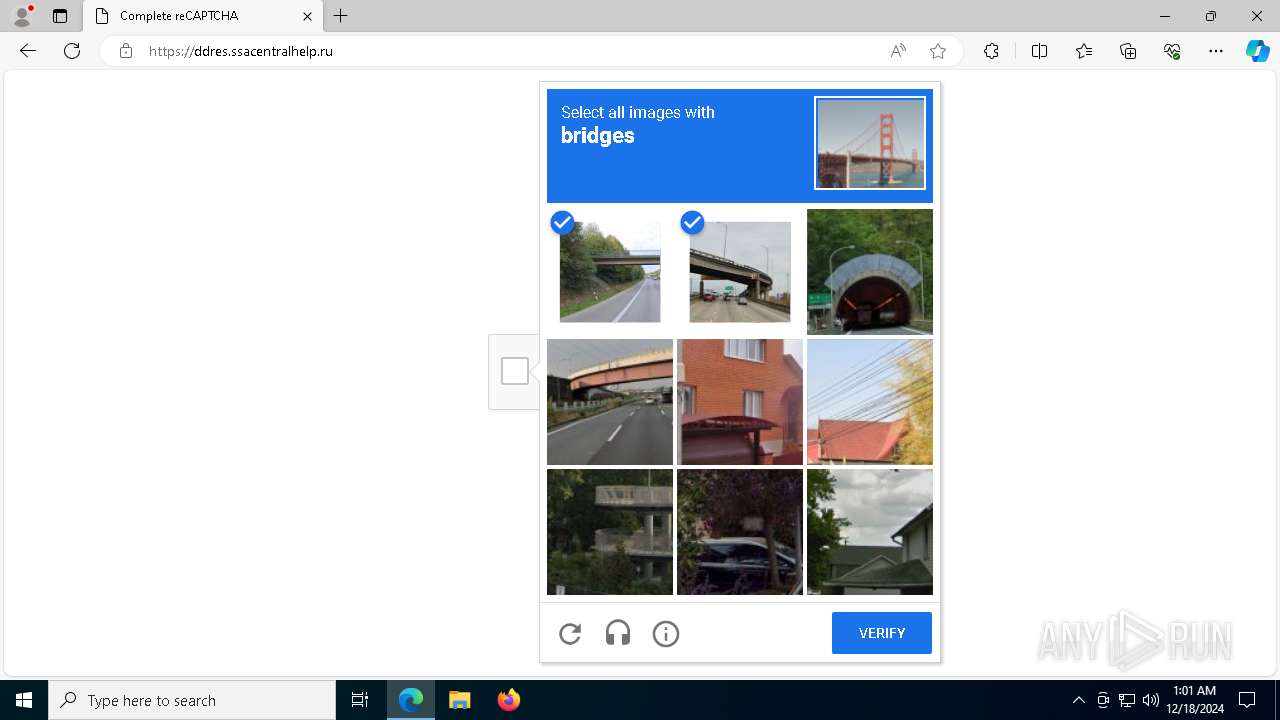
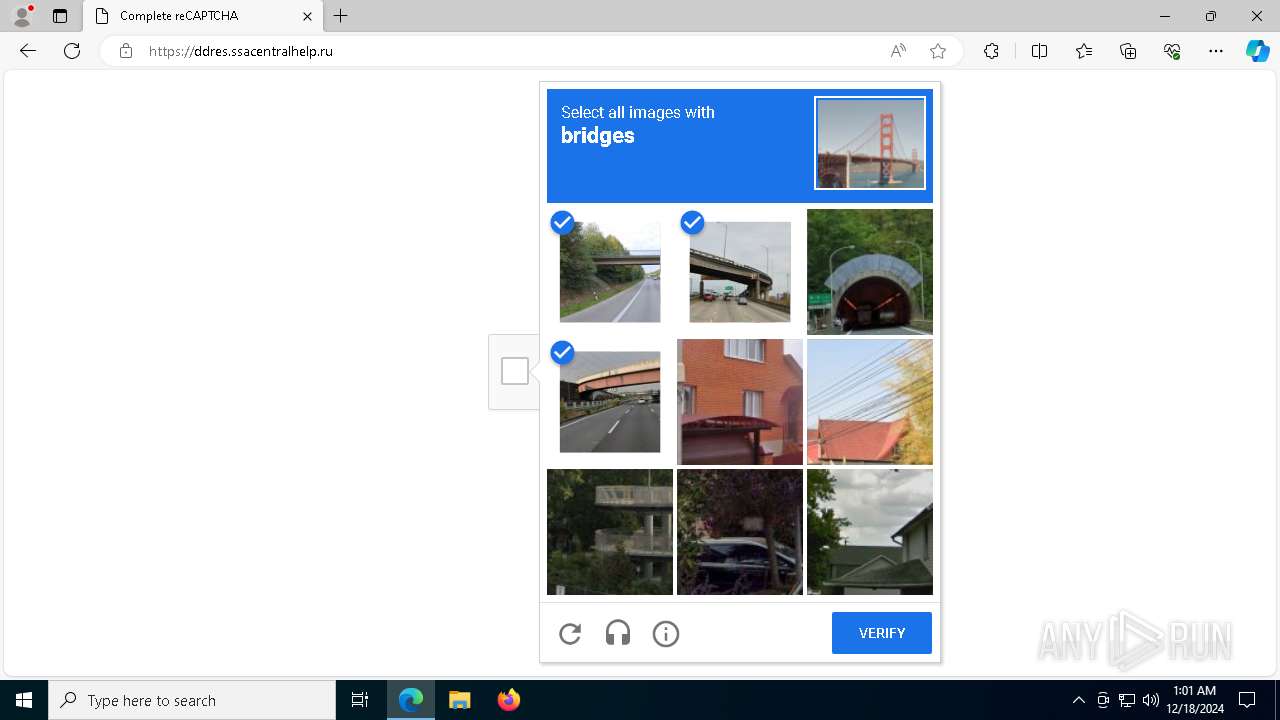
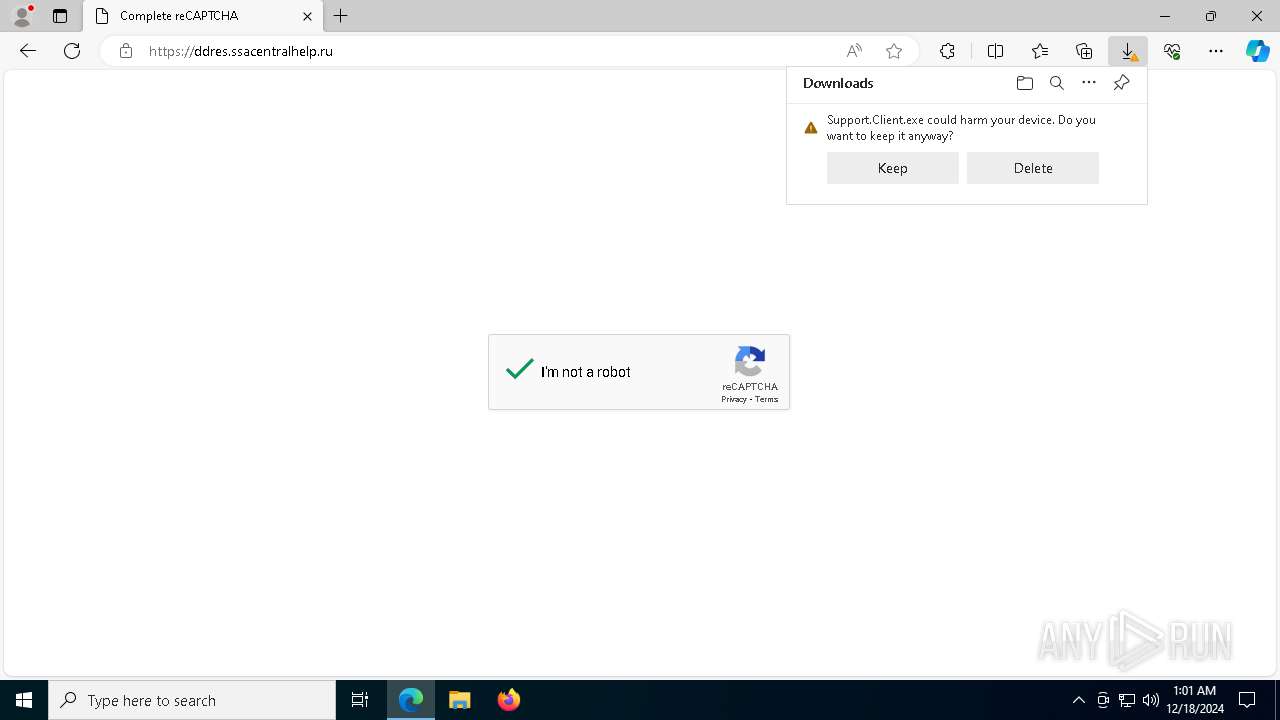
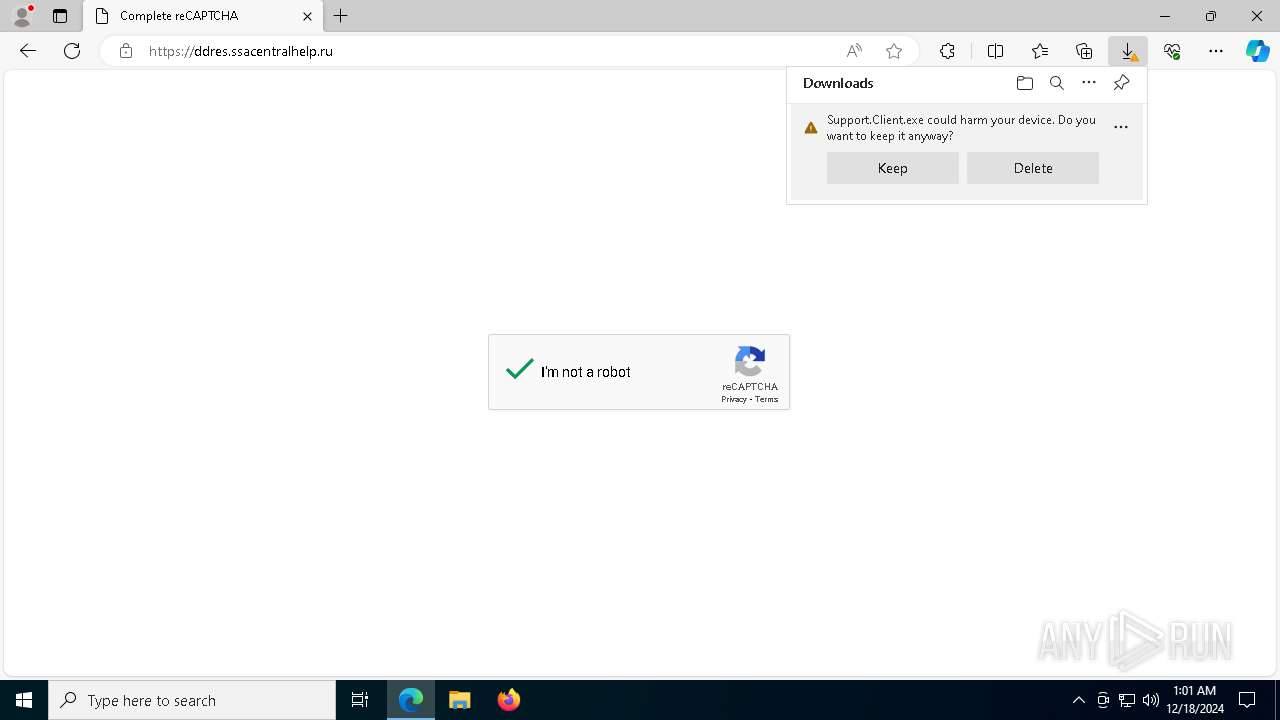
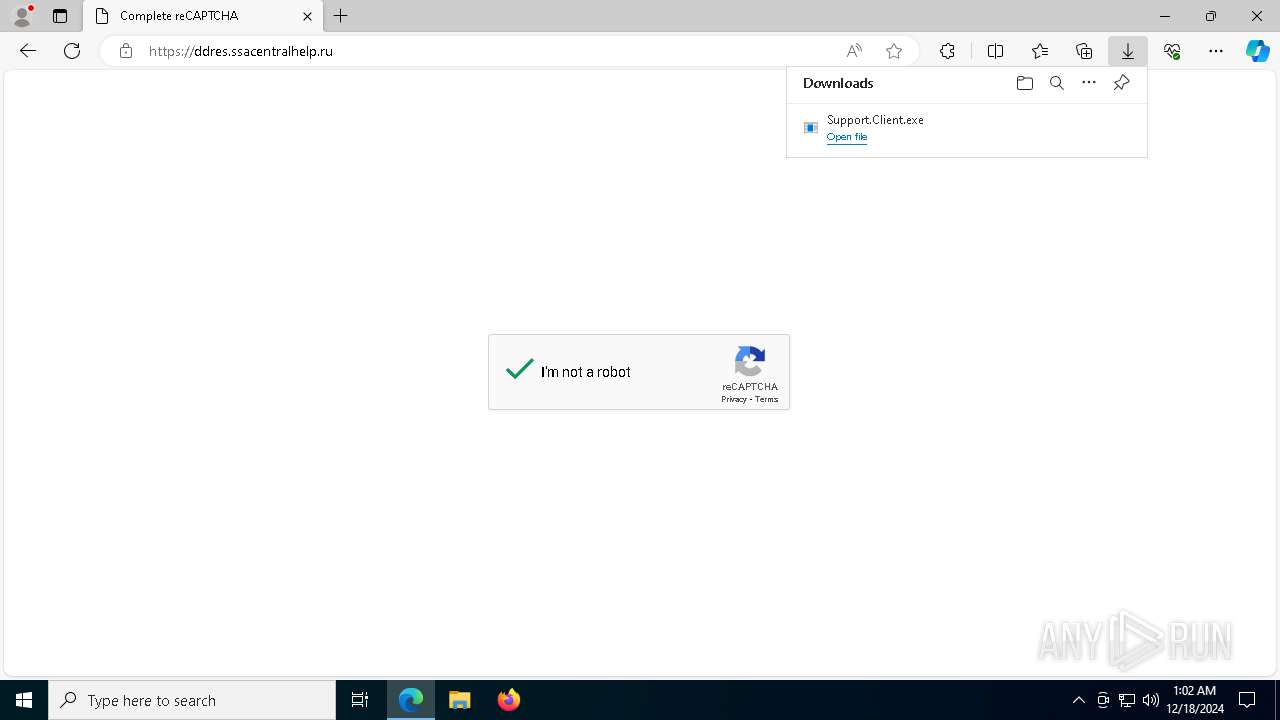
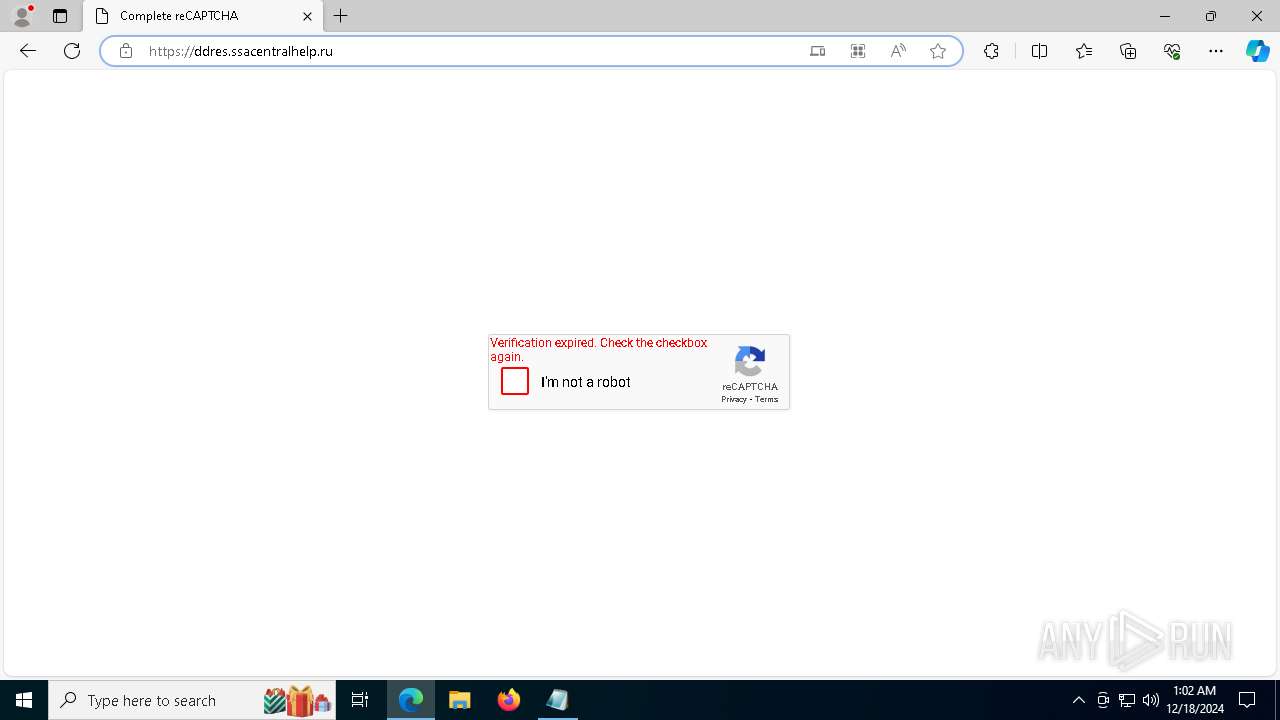
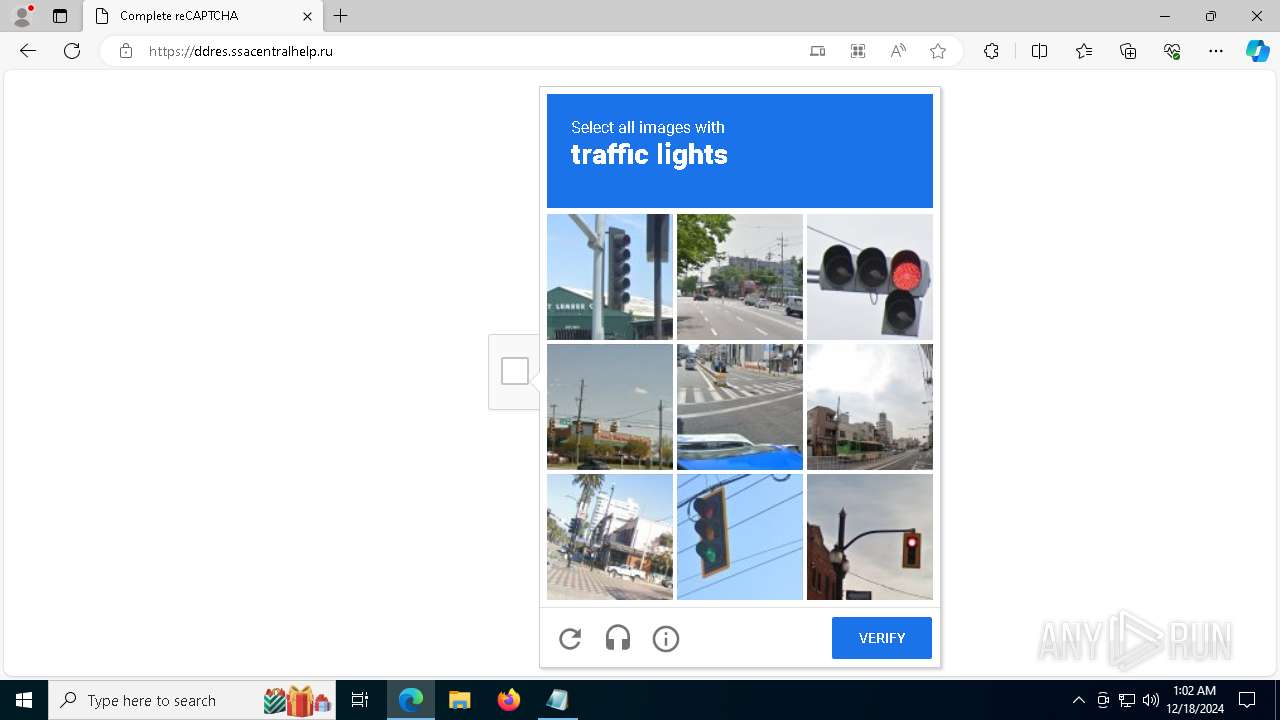
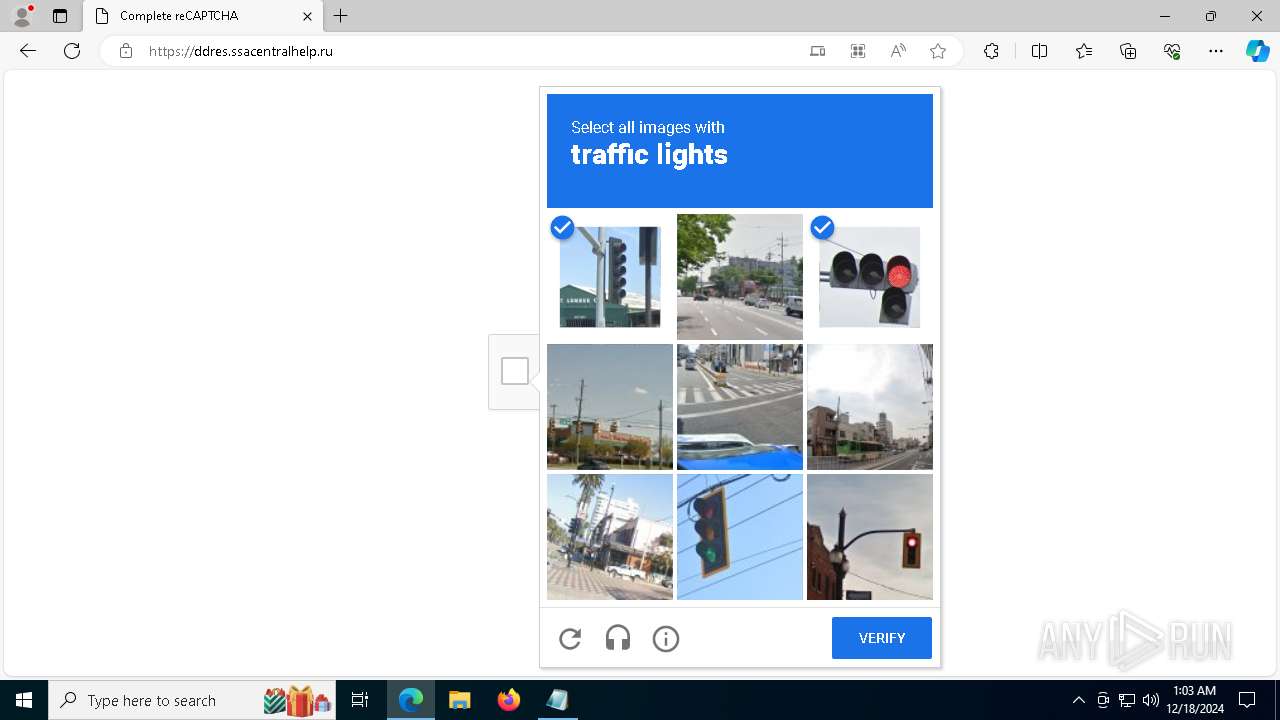
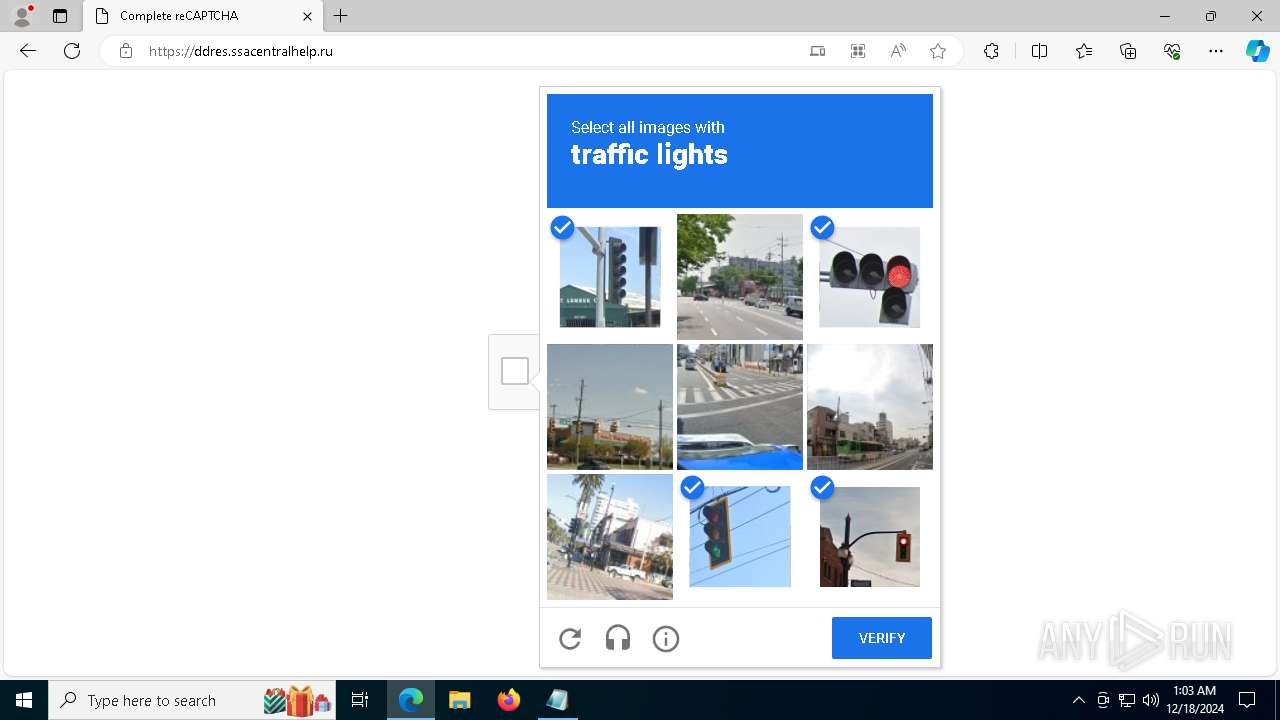
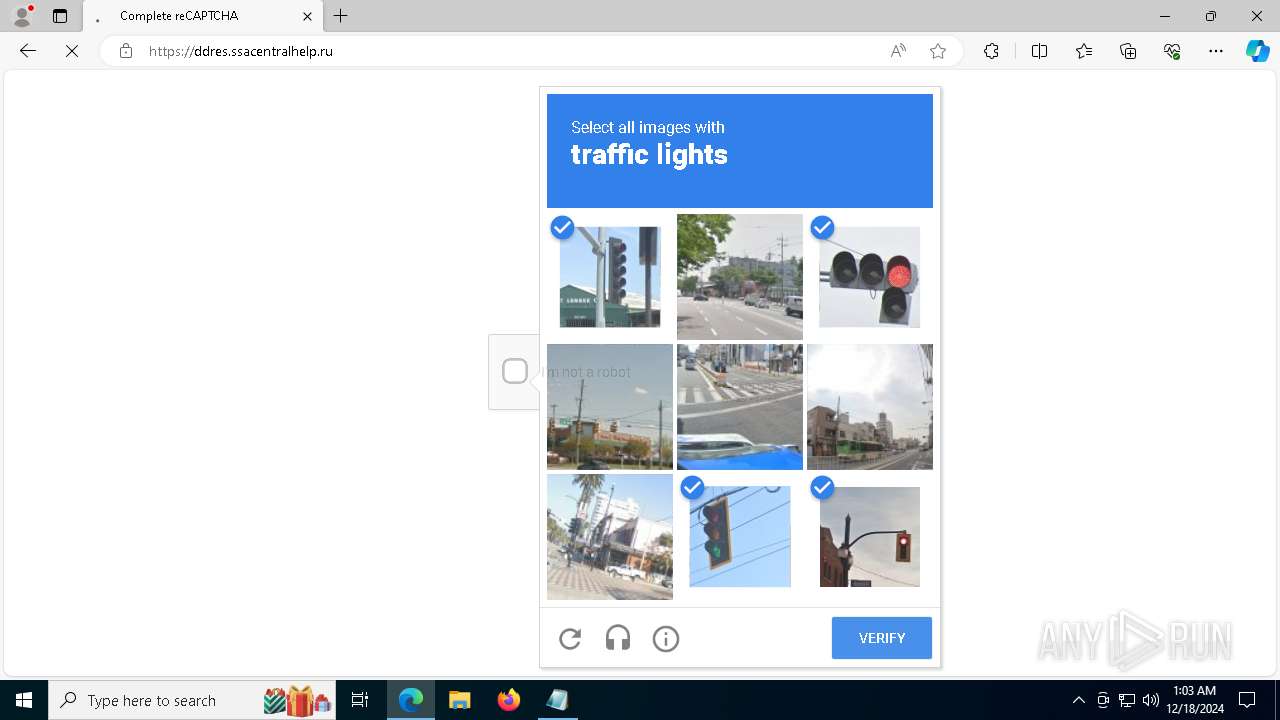
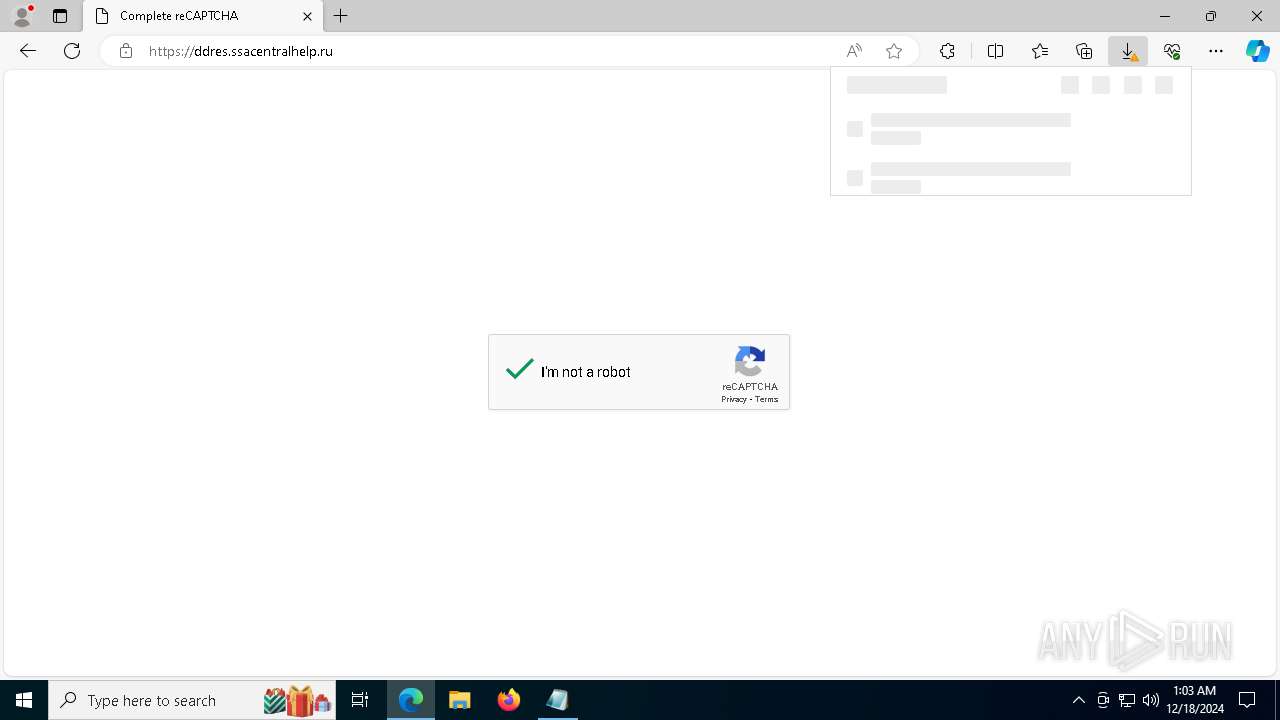
6732 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain ( .ssacentralhelp .ru) |
6732 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain ( .ssacentralhelp .ru) |
6732 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain ( .ssacentralhelp .ru) |
6732 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain ( .ssacentralhelp .ru) |
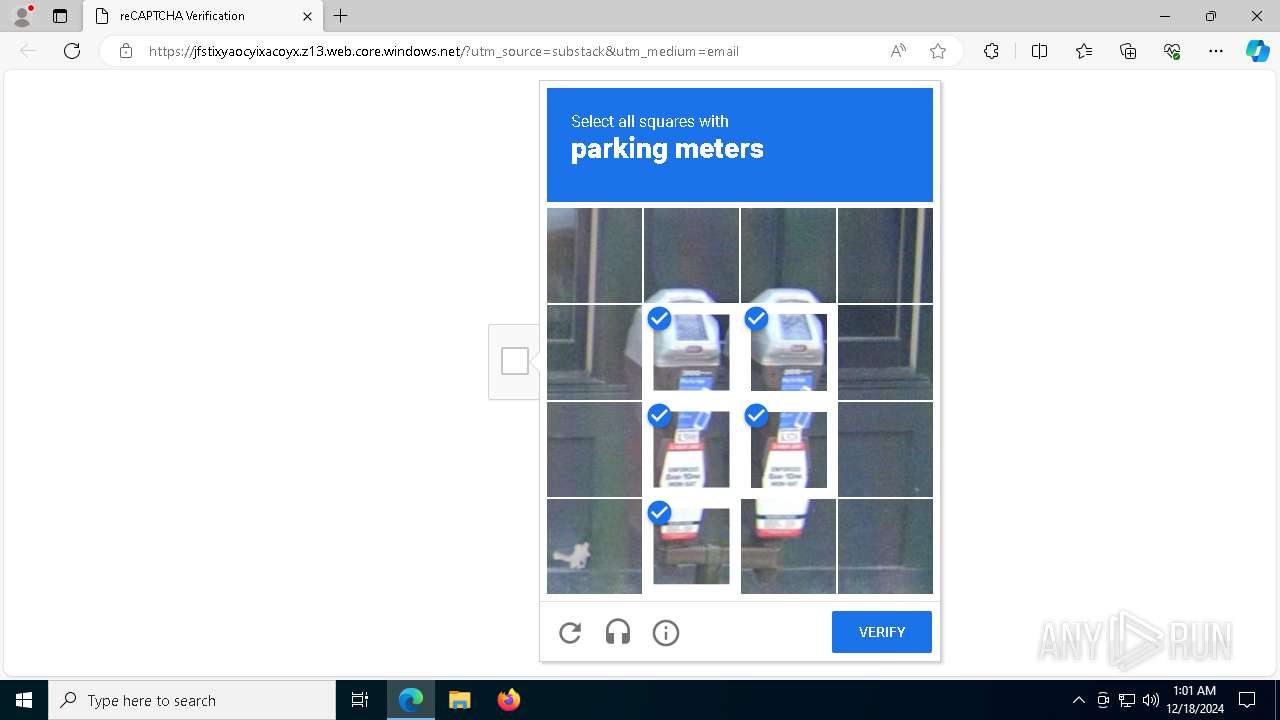
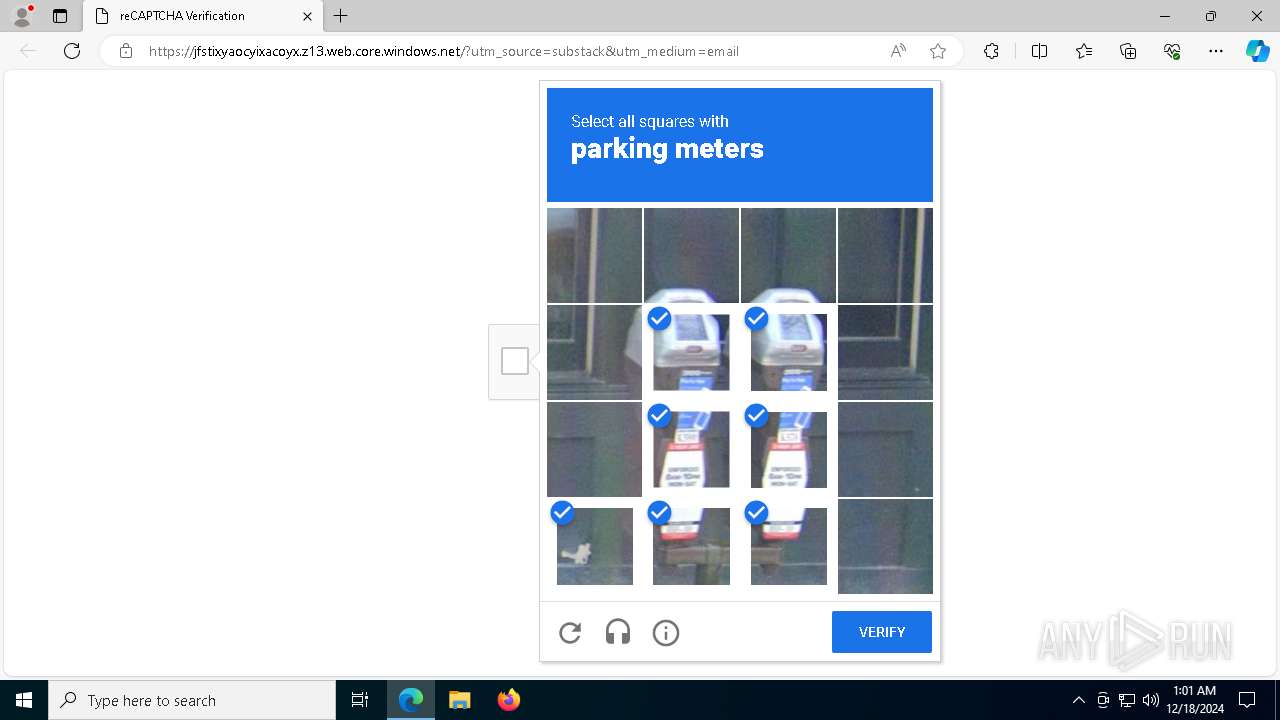
6732 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
6732 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
6732 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6732 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
4076 | ScreenConnect.ClientService.exe | Potential Corporate Privacy Violation | REMOTE [ANY.RUN] ScreenConnect Server Response |
Process | Message |
|---|---|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741772
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\win32\isoreg_direct.cpp, line 1127
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|