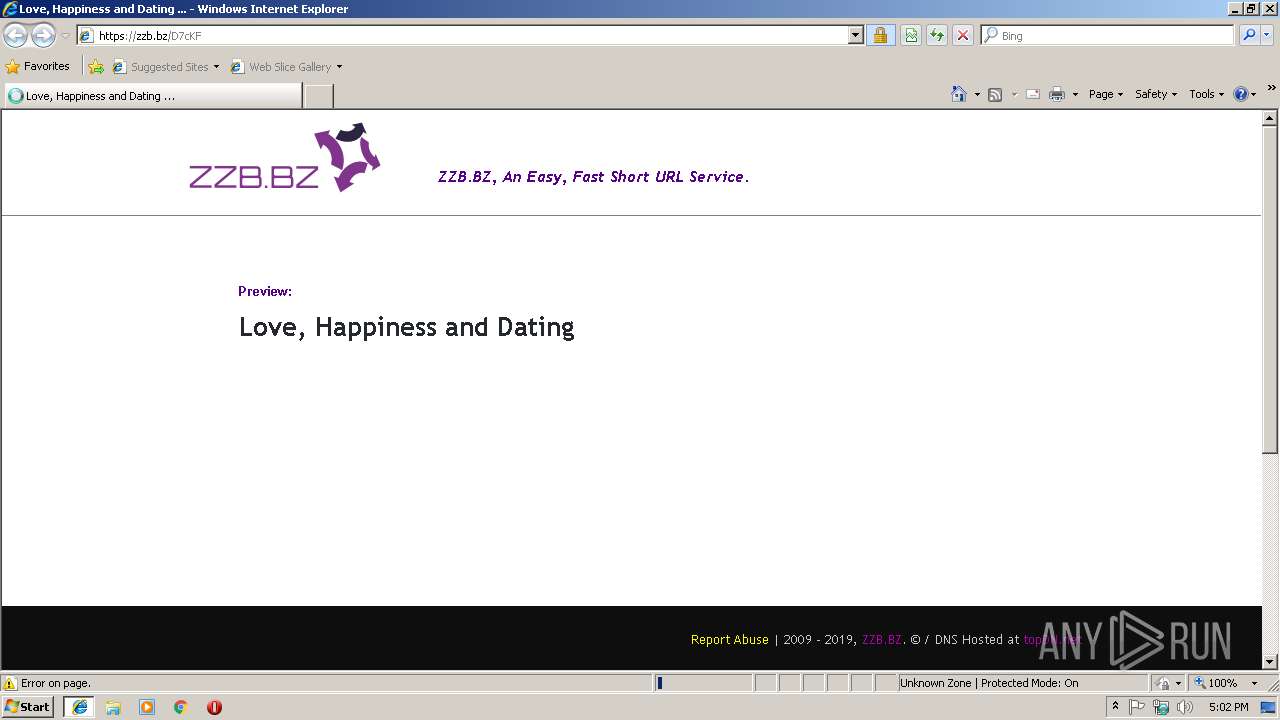
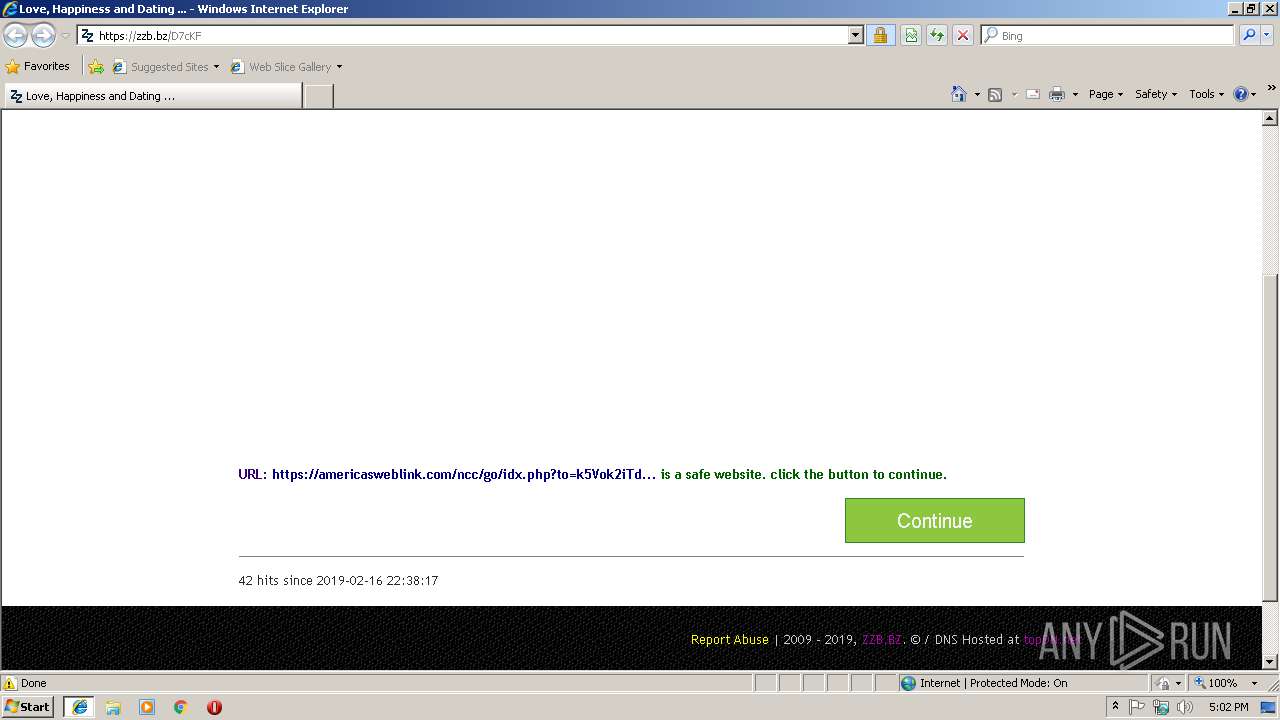
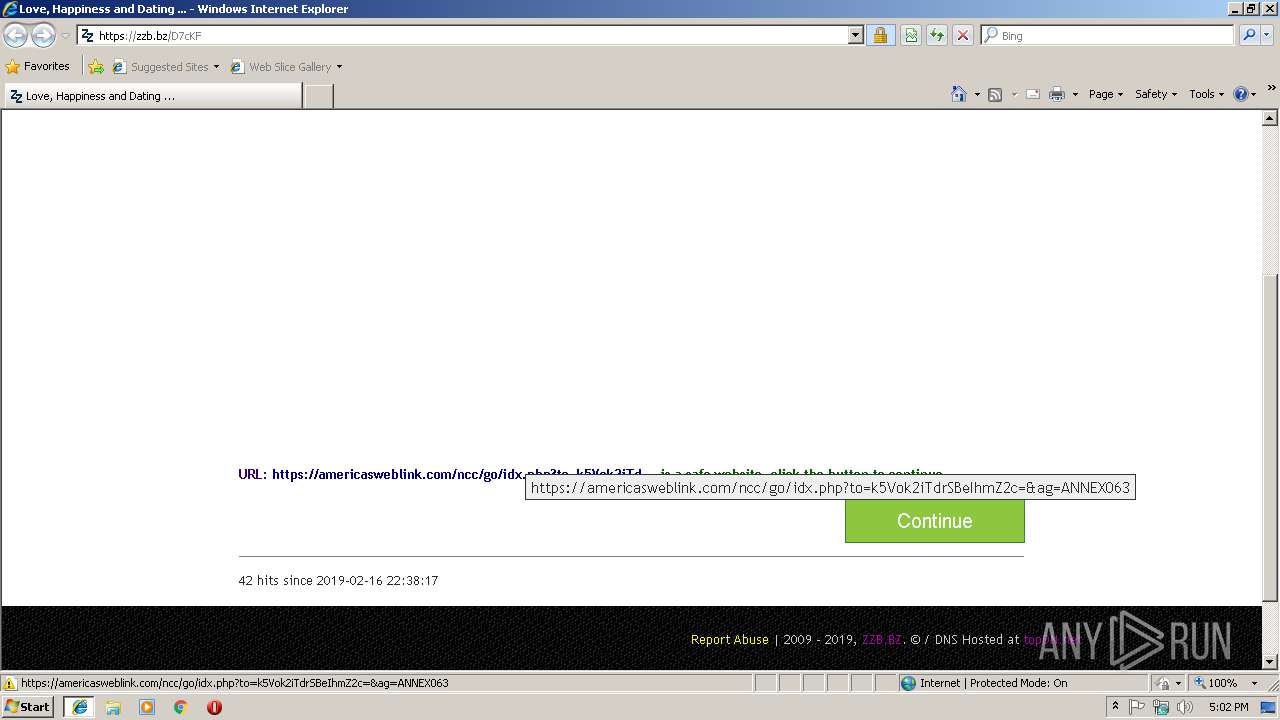
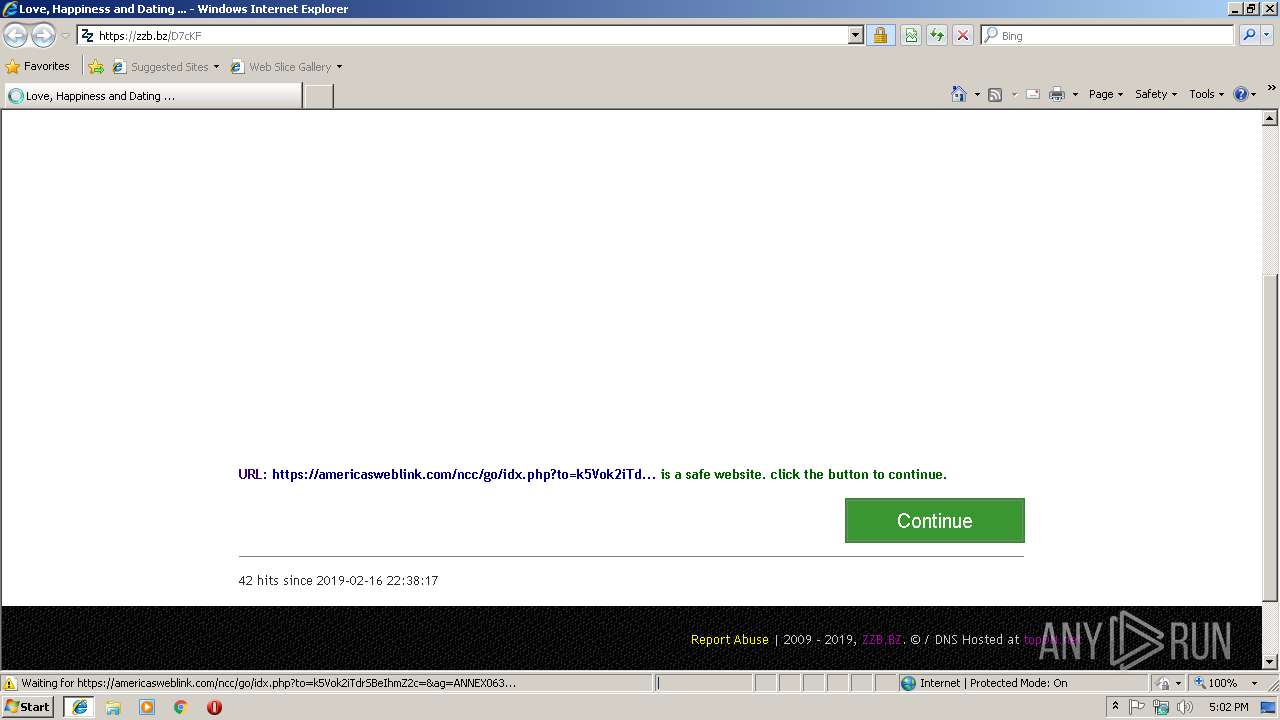
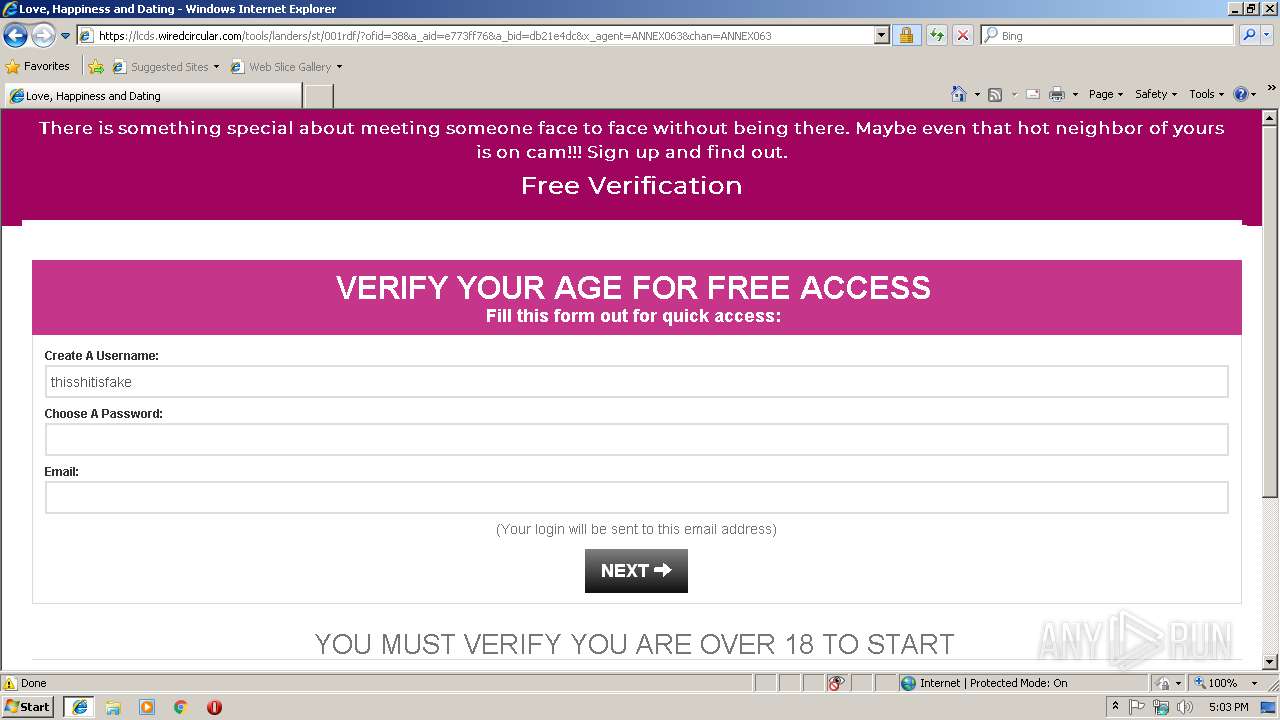
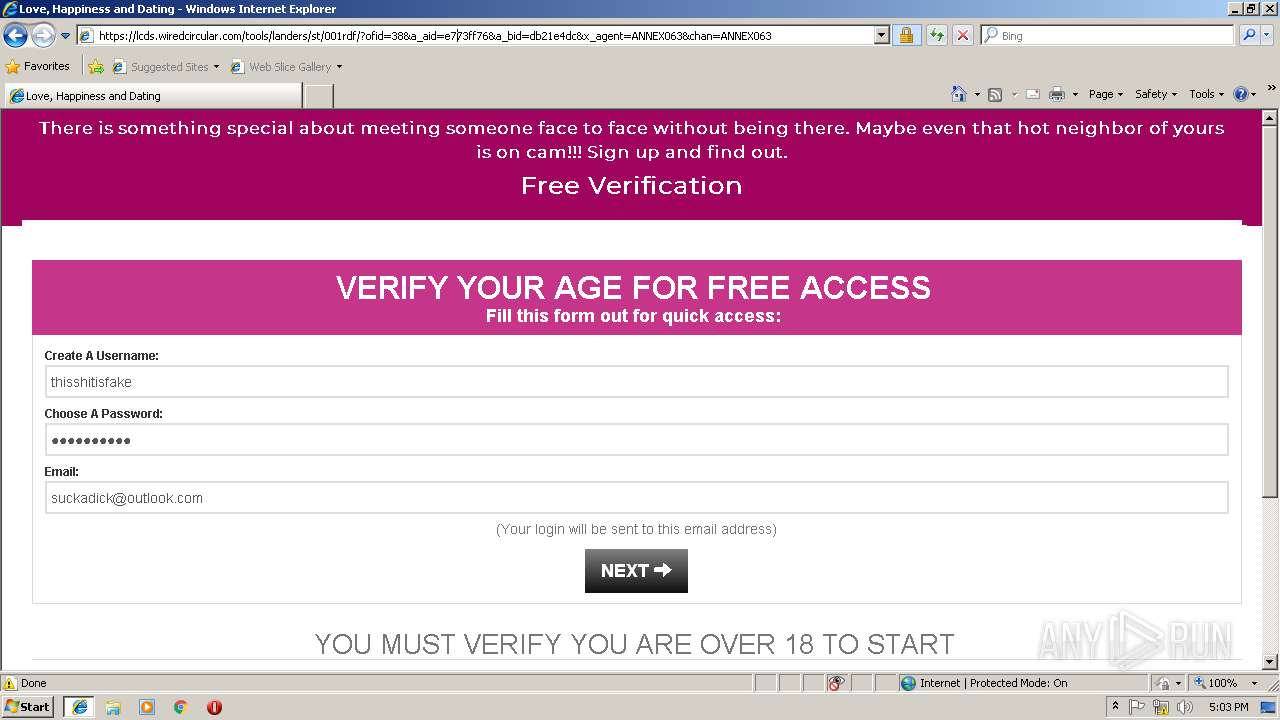
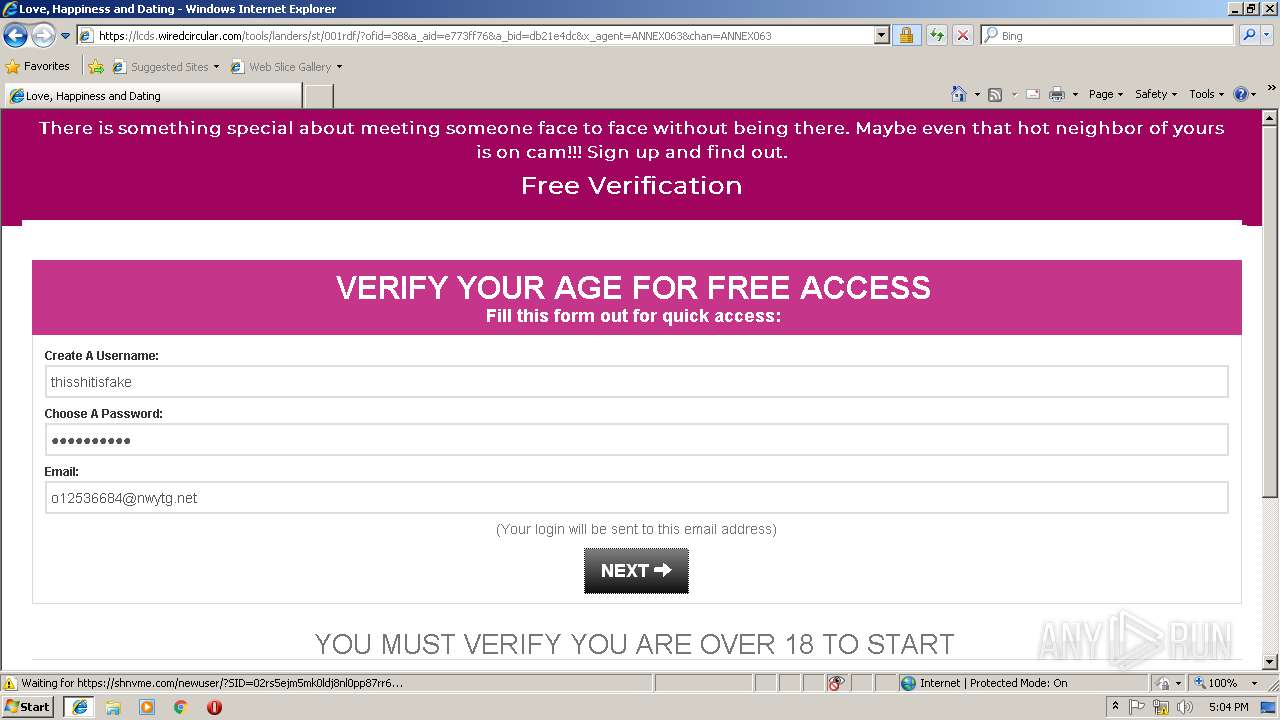
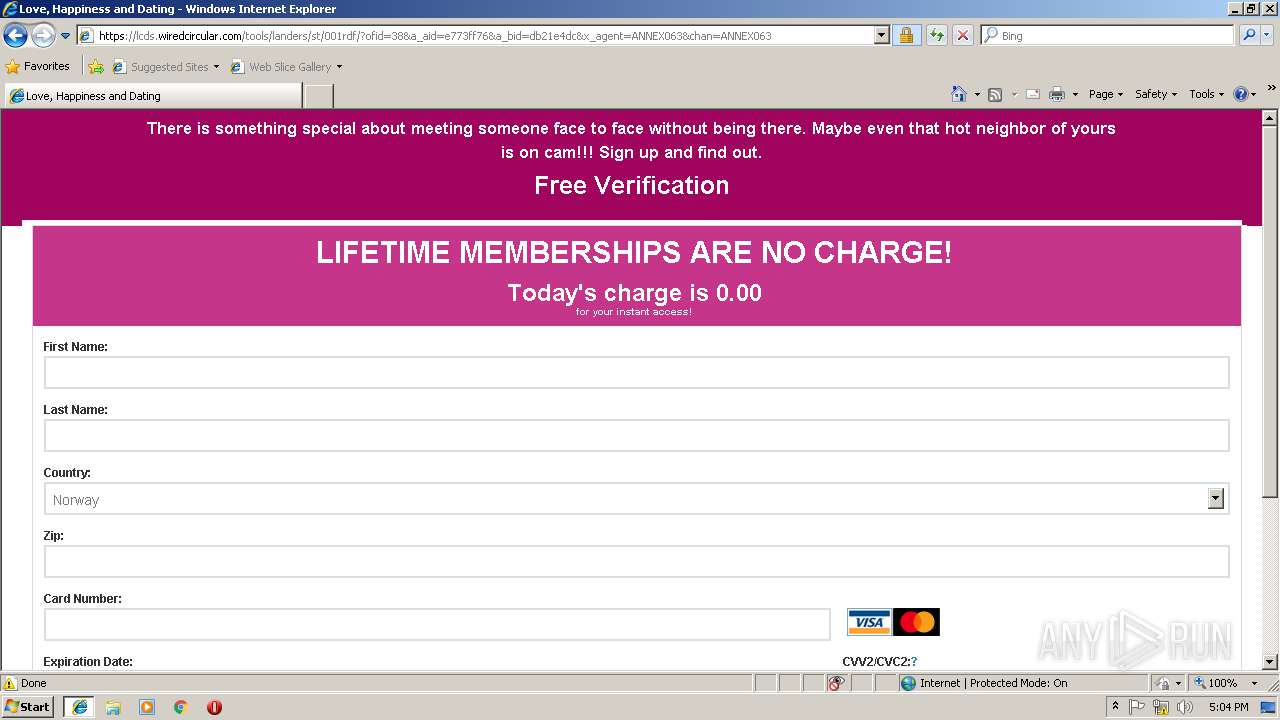
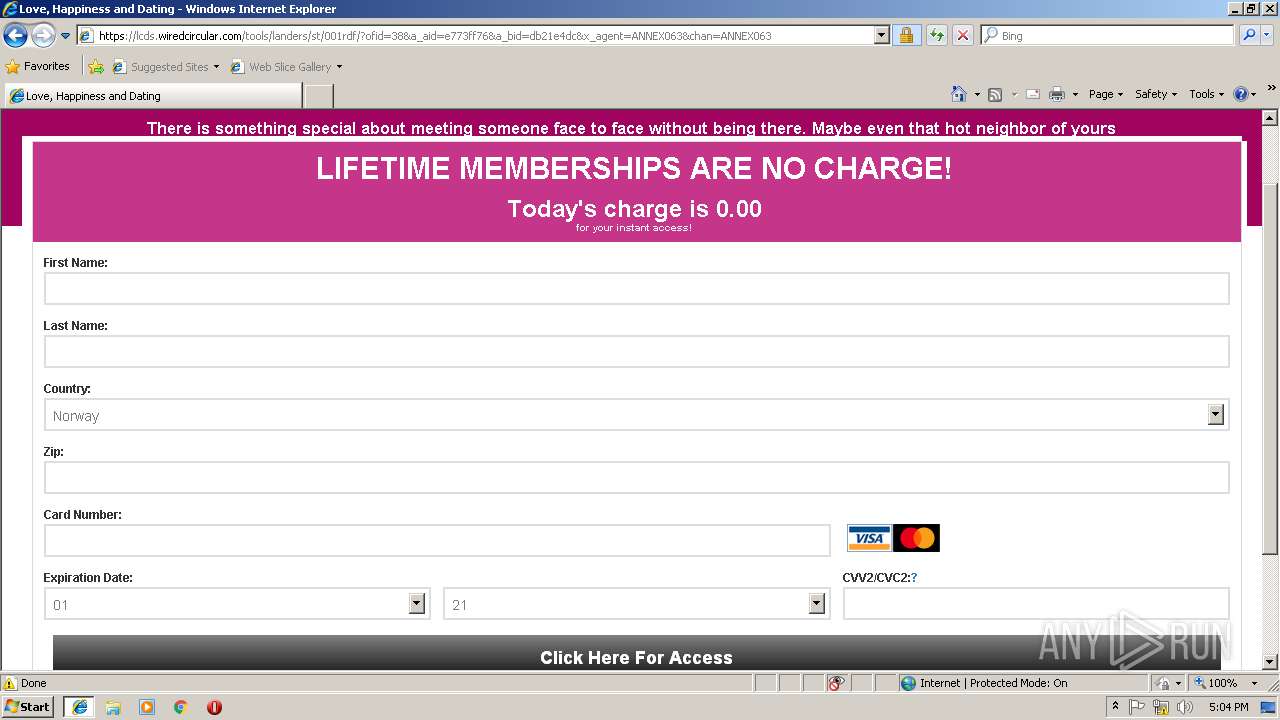
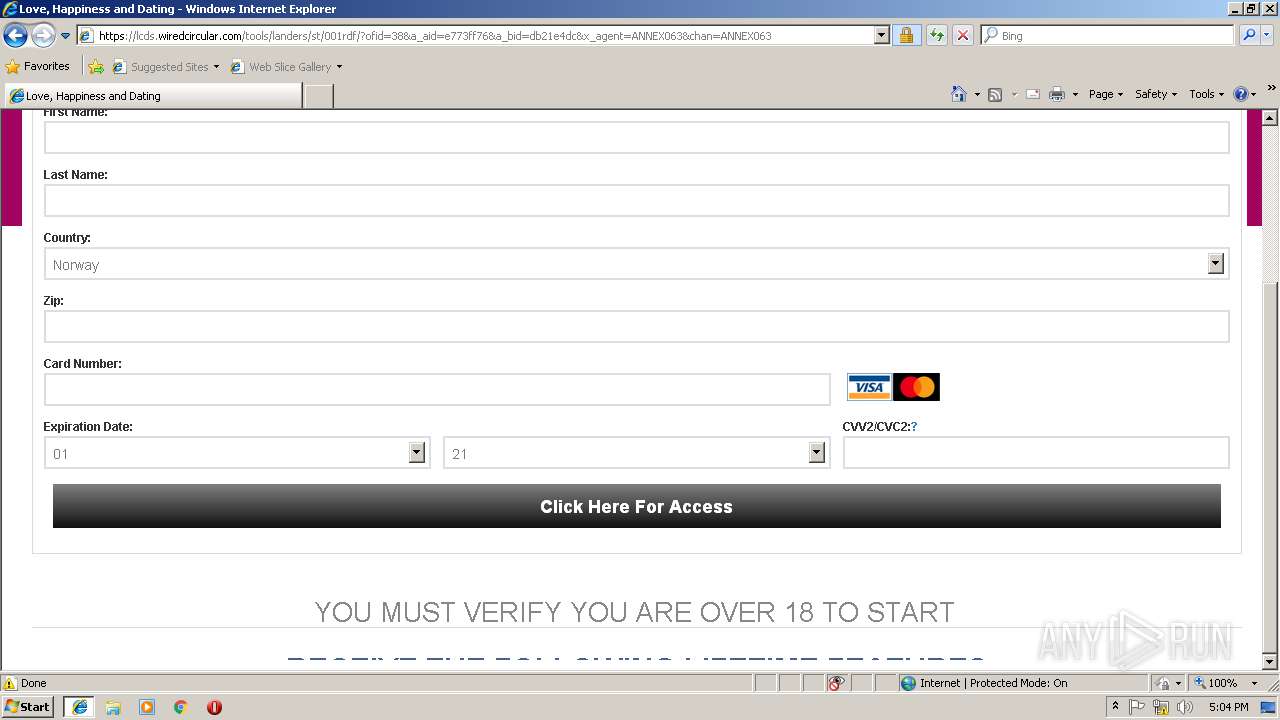
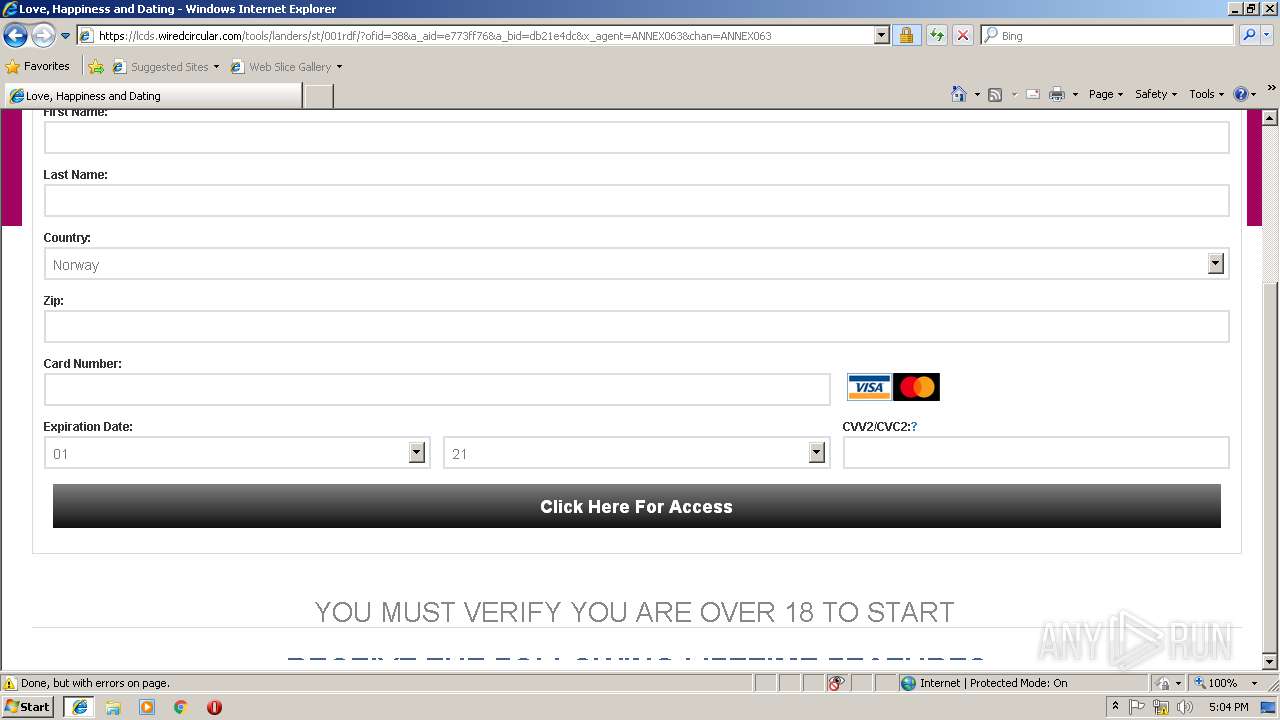
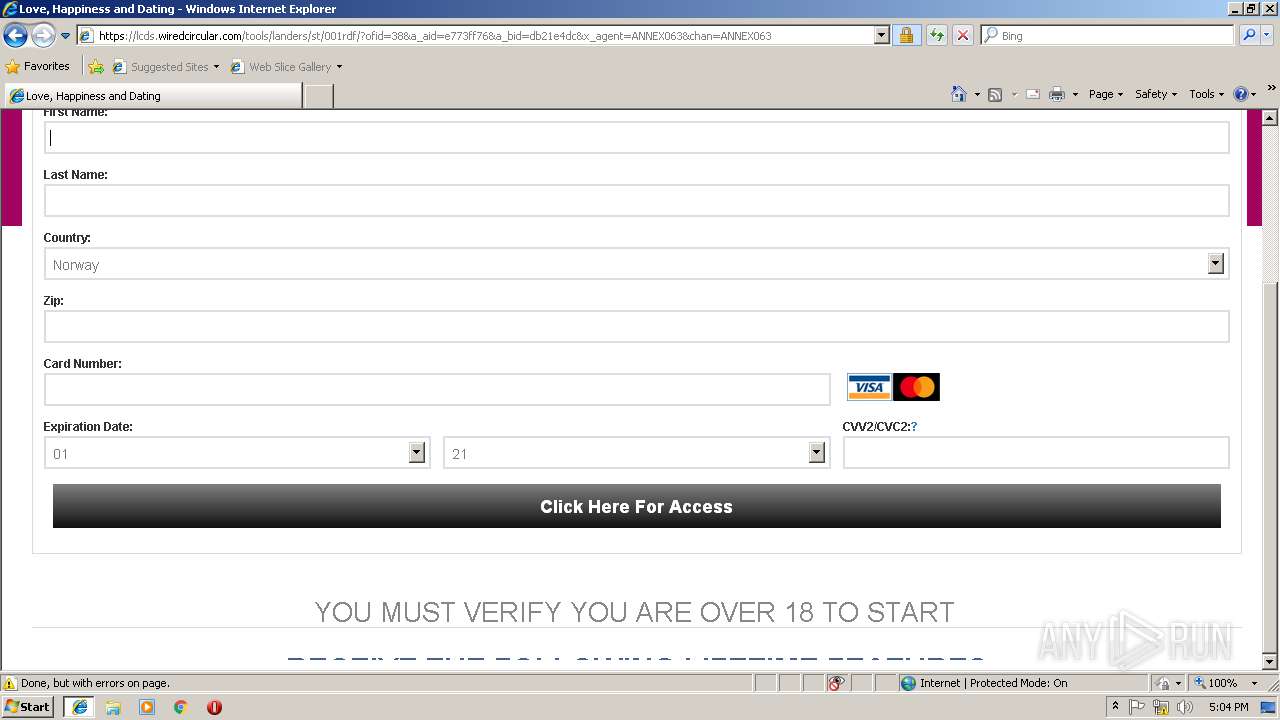
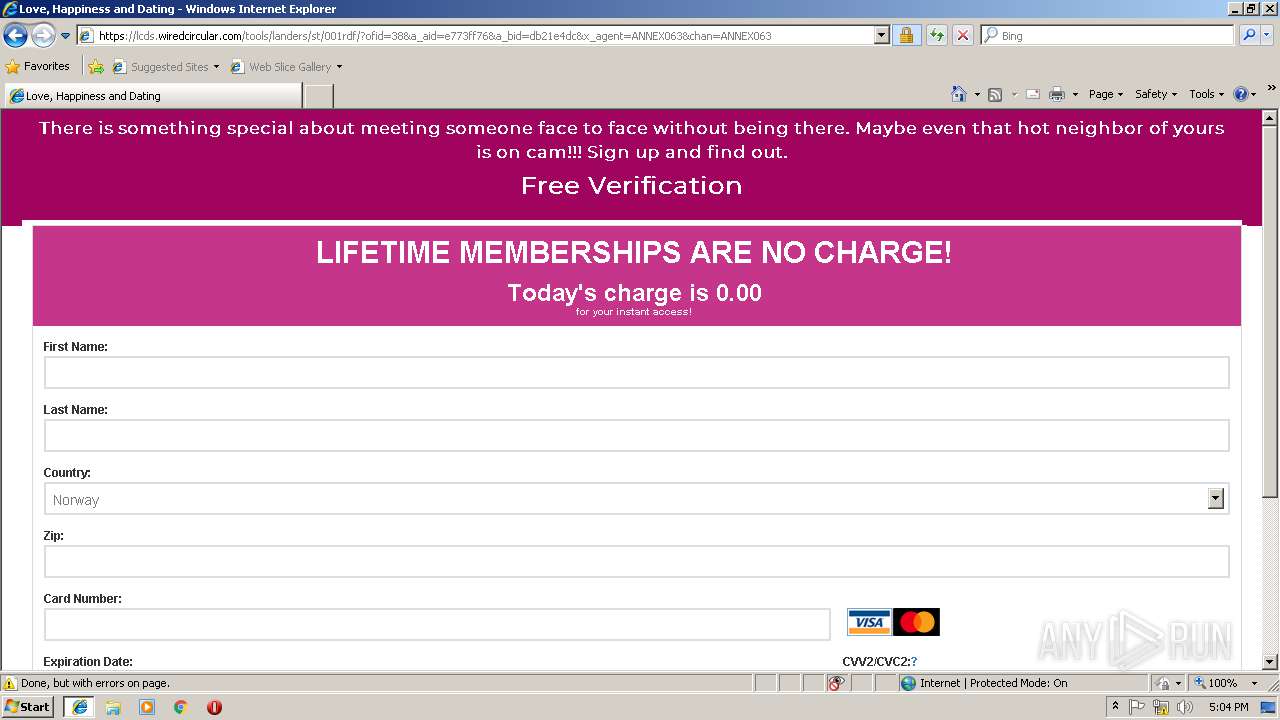
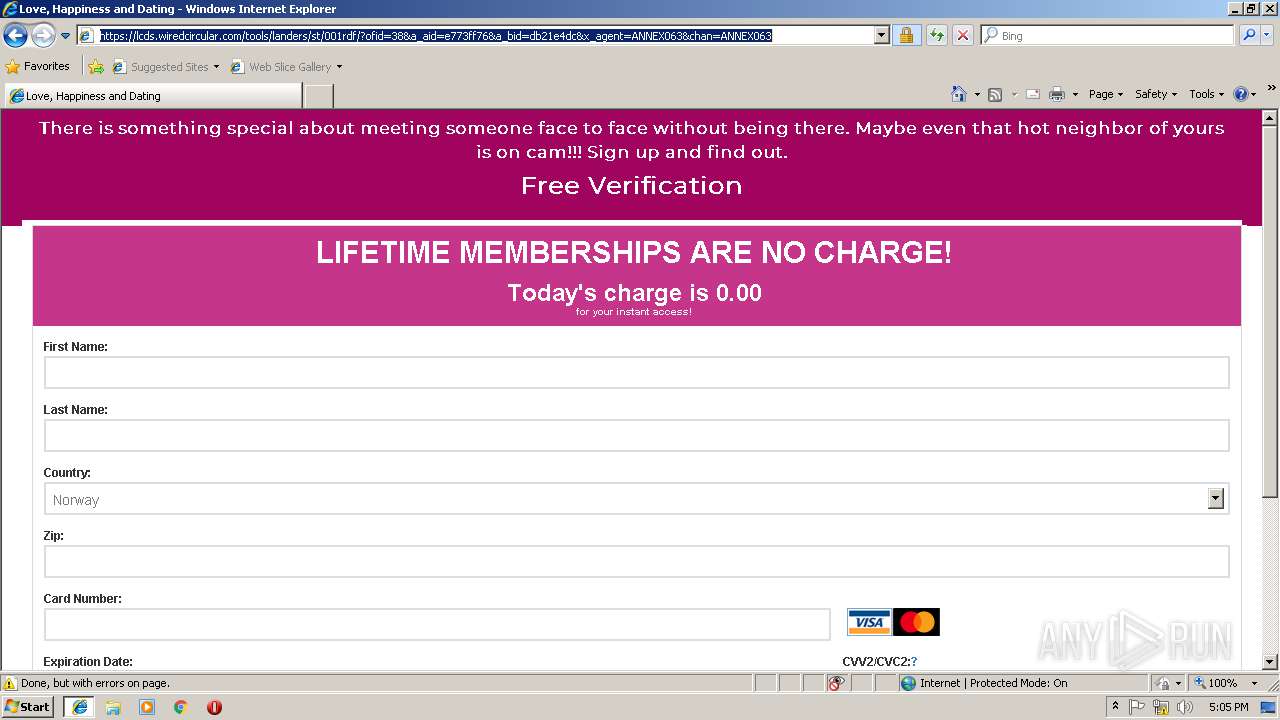
| URL: | https://zzb.bz/D7cKF |
| Full analysis: | https://app.any.run/tasks/21a3b2fb-d6fa-4b4e-9457-6c1bb2585c42 |
| Verdict: | No threats detected |
| Analysis date: | February 16, 2019, 17:02:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 91BC73A990CD7E001B23603E13C5C578 |
| SHA1: | 6A0C522E3C9FBF62545B6CF4866E200C5D4FD99B |
| SHA256: | 593D1F8A0A18B68A2C641D69B993DA2BE8820F691A93E76FA988A0124E98DA9C |
| SSDEEP: | 3:N85mvs:25mvs |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 2976)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3136)
Changes settings of System certificates
- iexplore.exe (PID: 2976)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2976)
Creates files in the user directory
- iexplore.exe (PID: 2976)
- iexplore.exe (PID: 3136)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2388)
Changes internet zones settings
- iexplore.exe (PID: 2976)
Reads Internet Cache Settings
- iexplore.exe (PID: 3136)
- iexplore.exe (PID: 2976)
Reads internet explorer settings
- iexplore.exe (PID: 3136)
Reads settings of System Certificates
- iexplore.exe (PID: 2976)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2388 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 2976 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3136 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2976 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
648
Read events
521
Write events
122
Delete events
5
Modification events
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {A8A859F7-320C-11E9-91D7-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070200060010001100020025004403 | |||
Executable files
0
Suspicious files
6
Text files
130
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2976 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2976 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3136 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\D7cKF[1].txt | — | |
MD5:— | SHA256:— | |||
| 3136 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@zzb[1].txt | text | |
MD5:56AC741C3F6AE09AFCCD9D9EE2BD8641 | SHA256:EB9322B663EA8B29CF9D727E90A646A91E19142C982FC842FA57BD2048813538 | |||
| 3136 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\D7cKF[1].htm | html | |
MD5:107316FF57869EC8526E68638BD551F5 | SHA256:0CB359AF40D570B7731312CC5D8BB2324400CCFB6AB9665609B103AAC1708DBD | |||
| 3136 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\U2ZG9DE0\style[1].css | text | |
MD5:B256006613FCE2F70FBC92B2B1697A68 | SHA256:F17FD4F6063BE18FA008BEA0261BEB0986B0CBF478FB54D69B4A318C958E228B | |||
| 3136 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\DOMStore\index.dat | dat | |
MD5:3D54B79D43C1013F6B6A706750527EBC | SHA256:A38AFD043DE2C726111B3B96599015F78119E677AD304064A4D4E67308ABFD00 | |||
| 3136 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\DOMStore\Z5U2EFM2\zzb[1].xml | text | |
MD5:9C3F566096DF48BDD6171F87AB8A87A2 | SHA256:4DFF996DF7DC8410BF003532935701161D9064451D1B7DCEFC08FA747065210E | |||
| 3136 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\001rdf[1].txt | — | |
MD5:— | SHA256:— | |||
| 3136 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\f[1].txt | text | |
MD5:D452EE4E43842C87FF9D5EBA53D773B7 | SHA256:99CEDAF93AC7EB63BE4B441B4A40DD115F1CAE18C88347C87BBD8E4D7AA63529 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
48
TCP/UDP connections
68
DNS requests
34
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
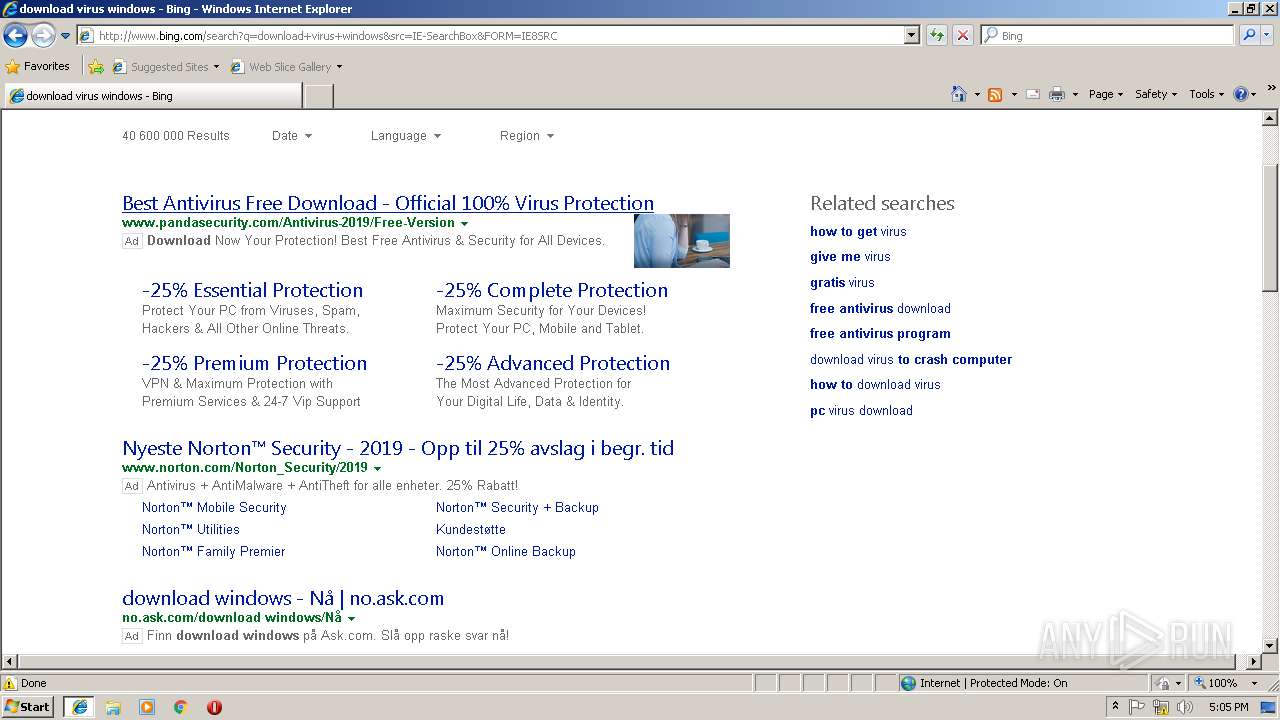
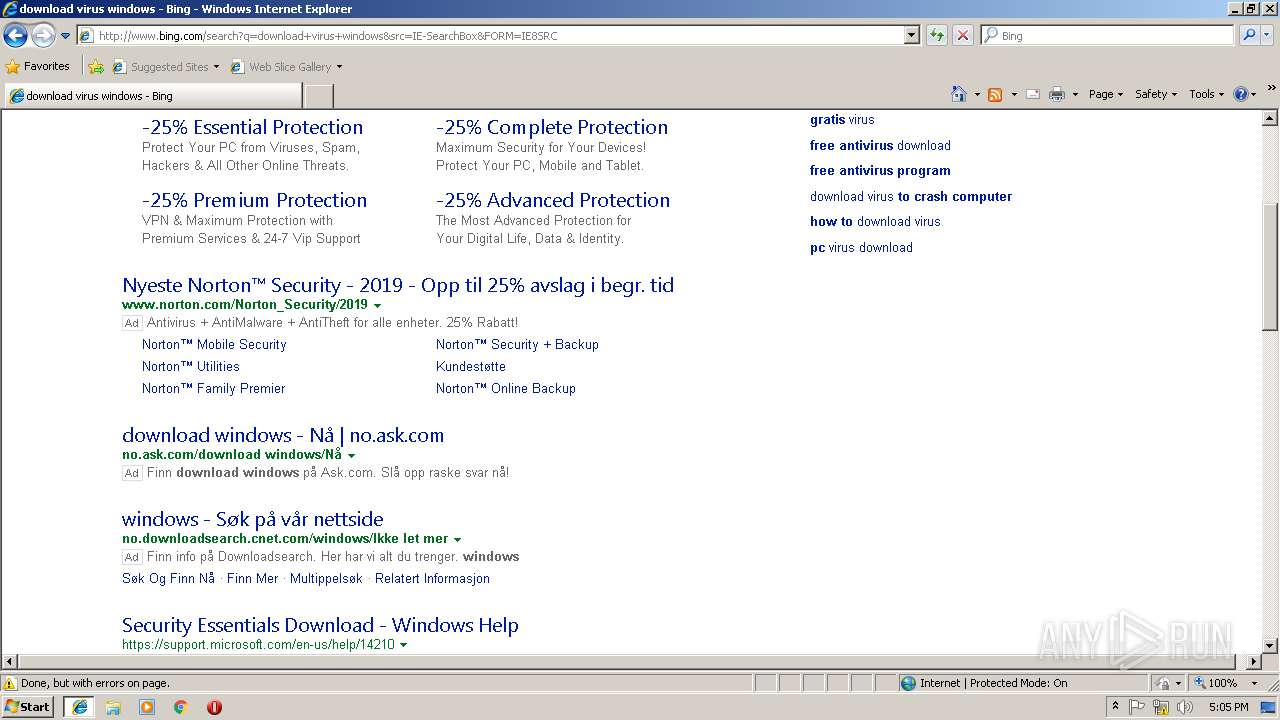
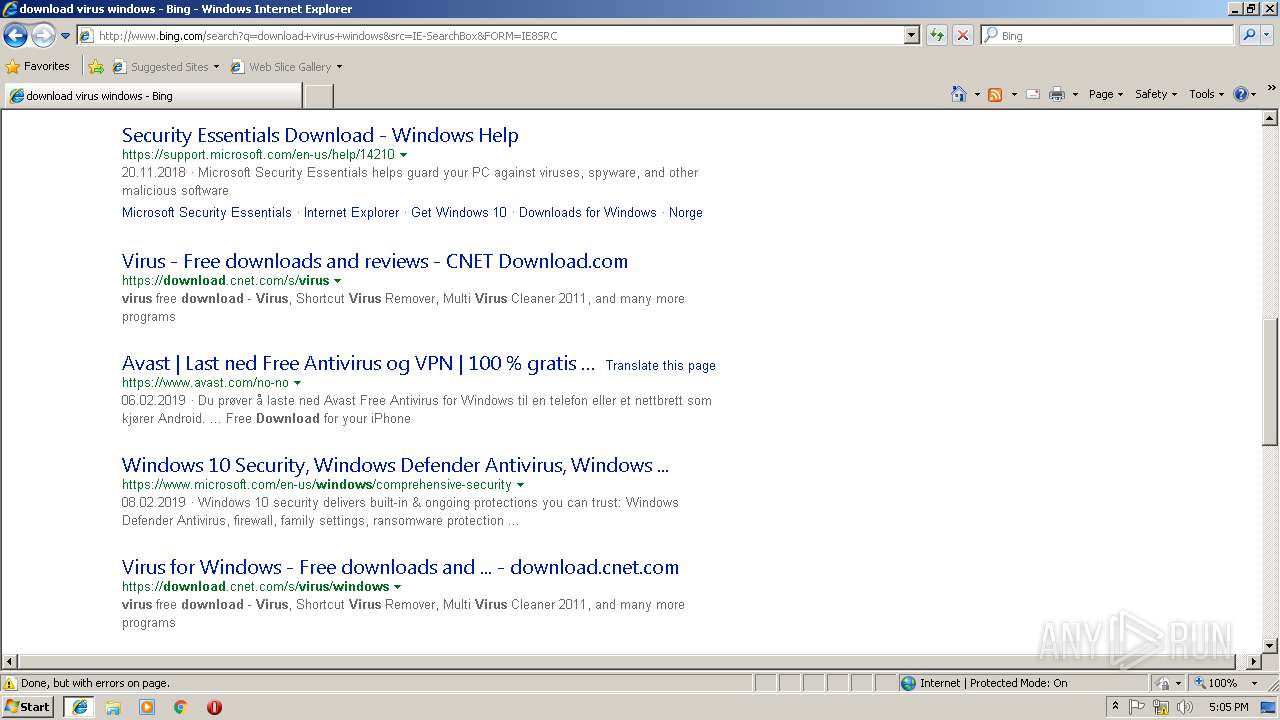
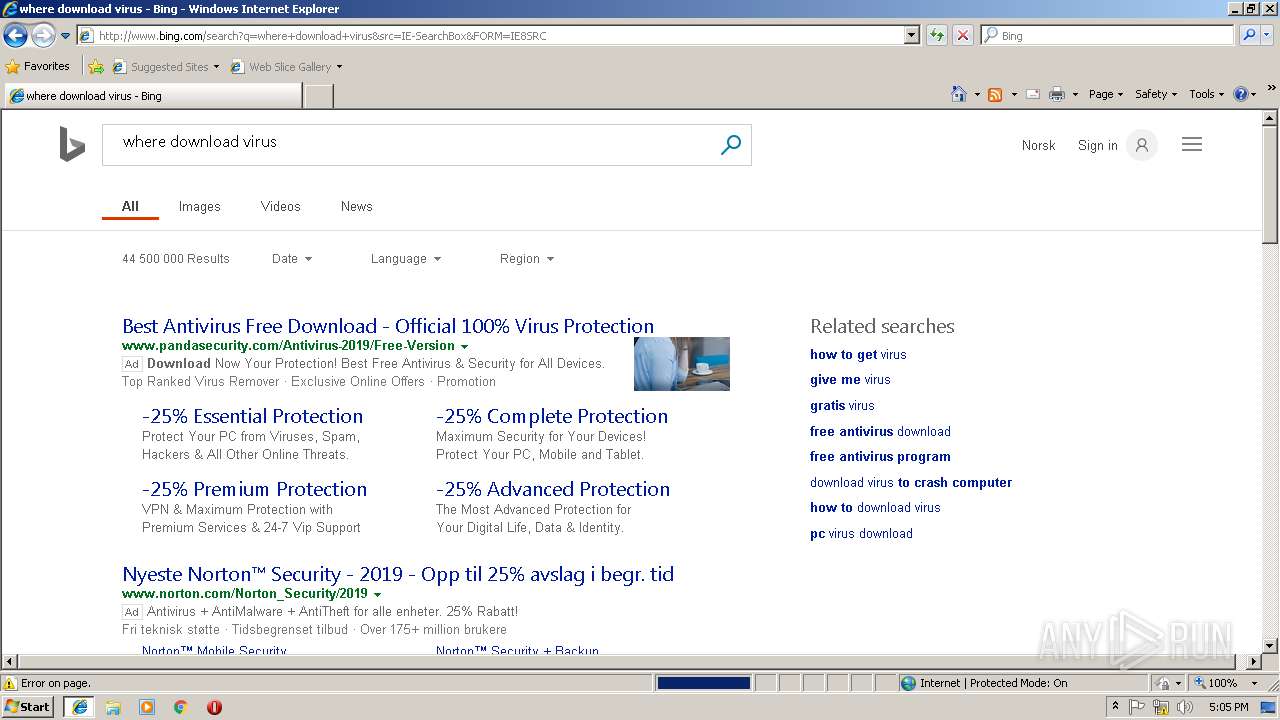
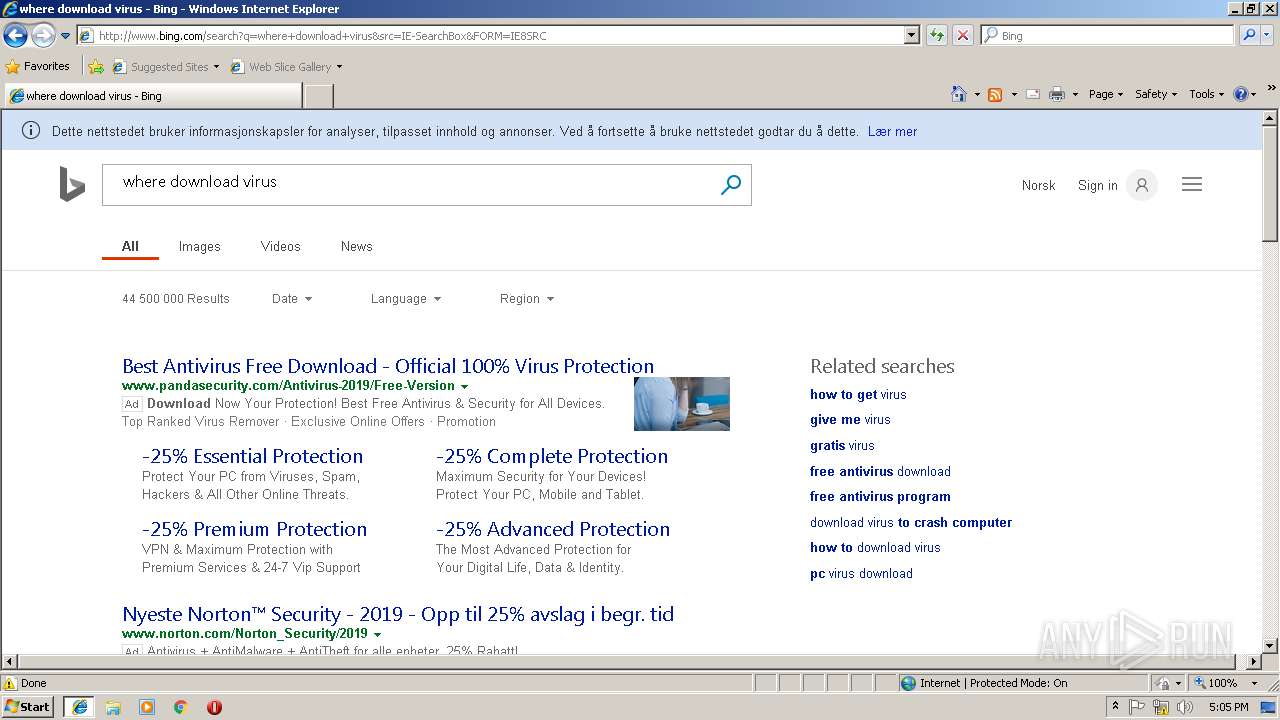
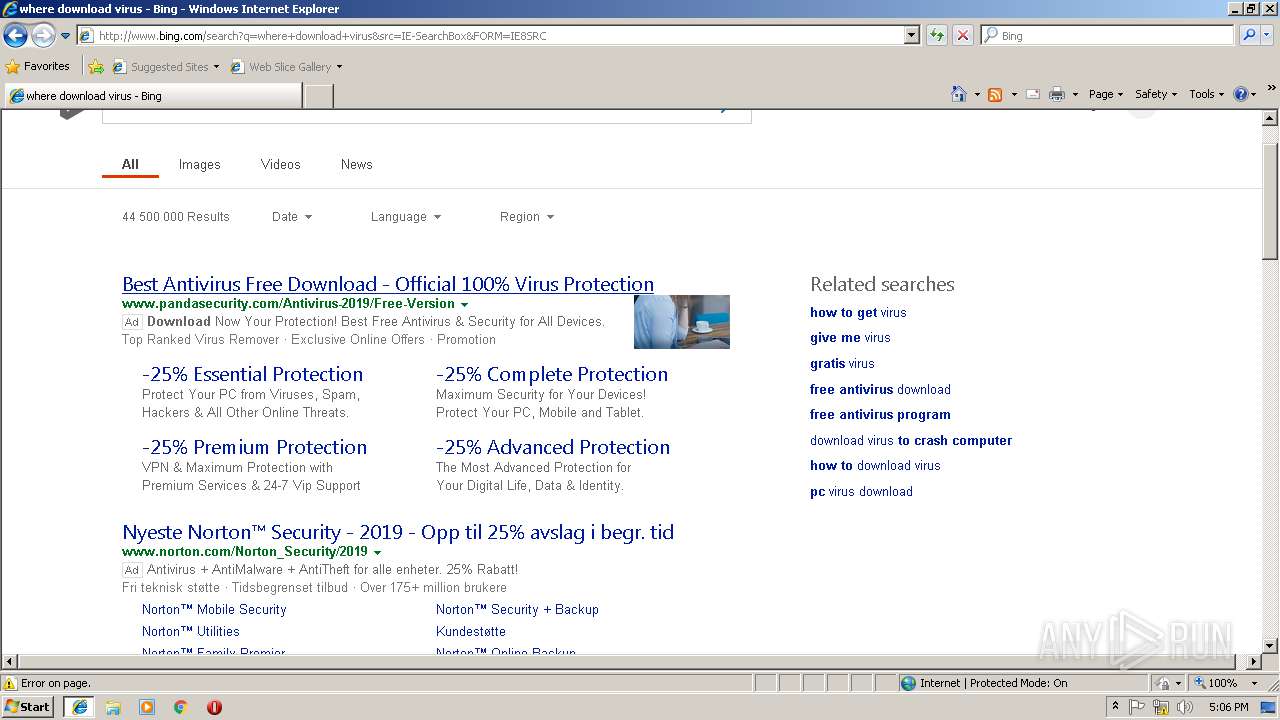
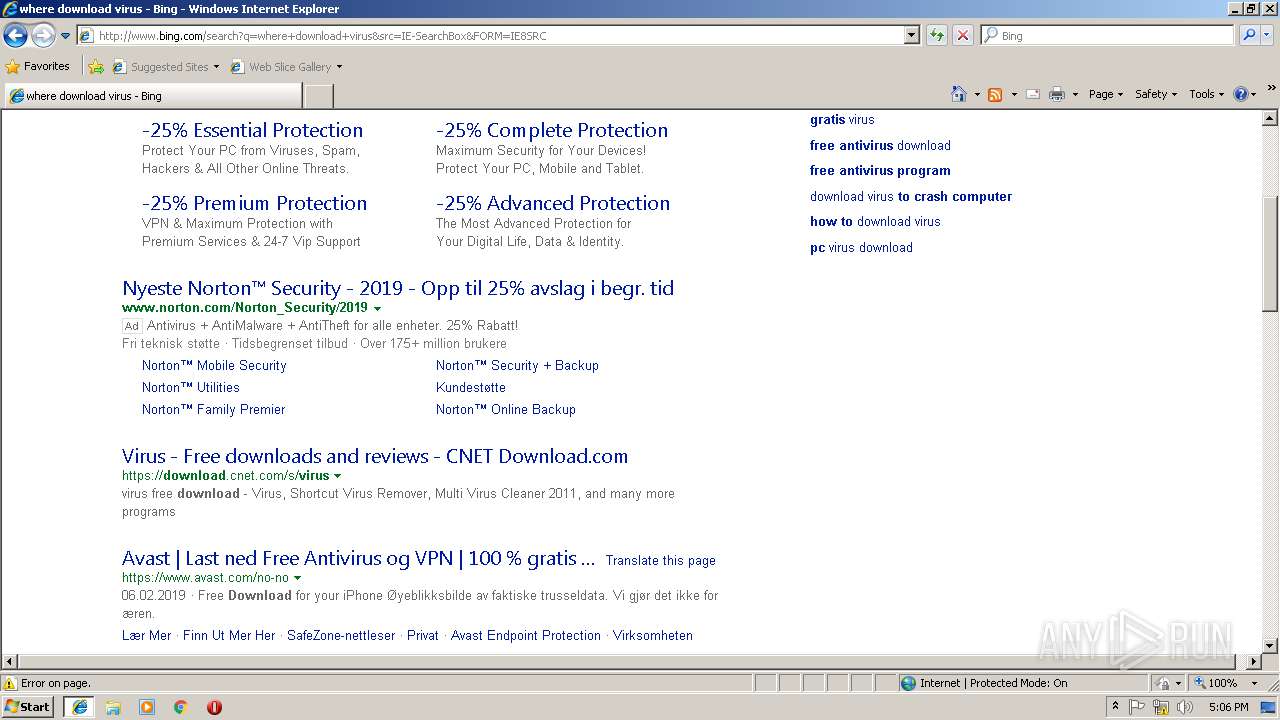
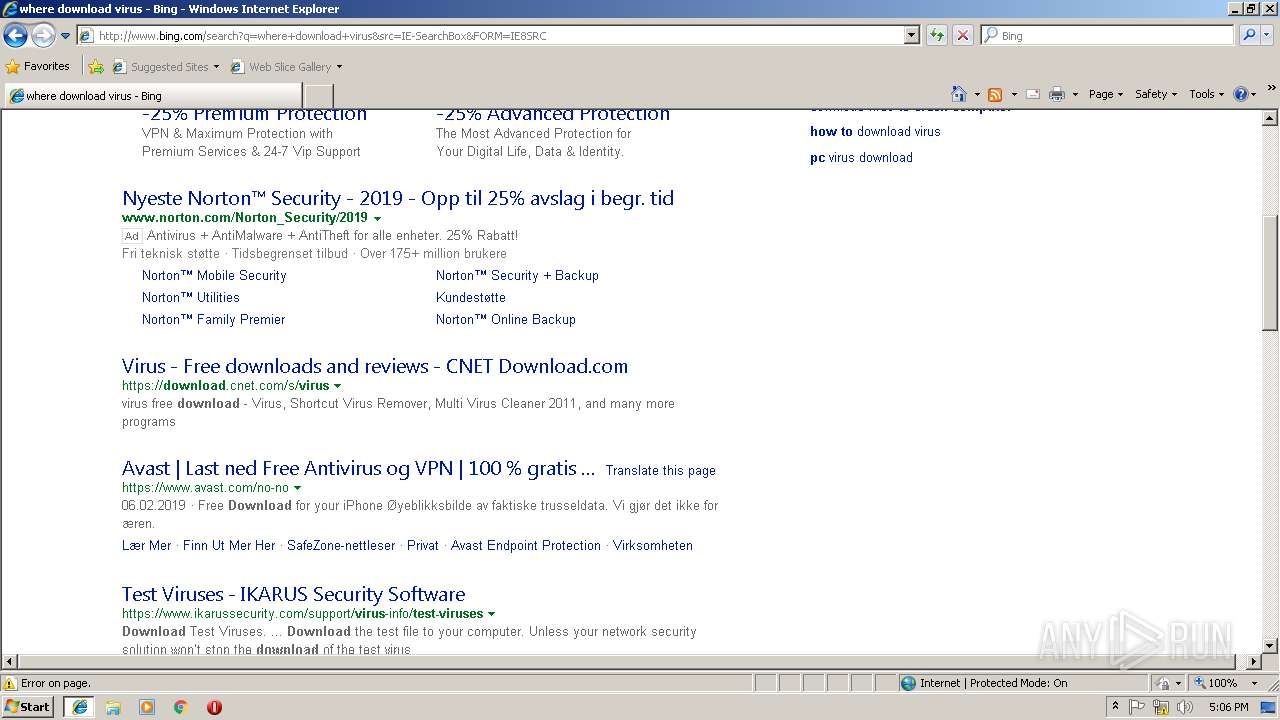
3136 | iexplore.exe | GET | 302 | 208.73.160.84:80 | http://208.73.160.84/ncc/accounts/go/11/20/ANNEX063 | US | — | — | unknown |
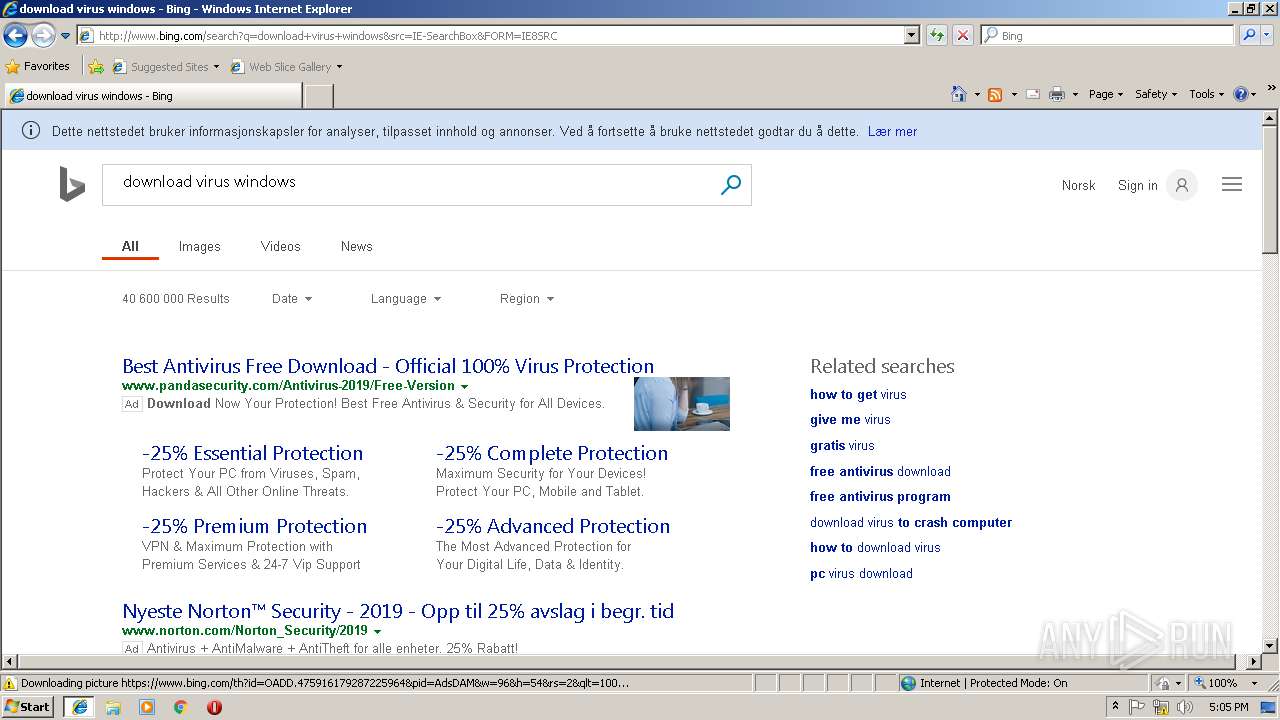
3136 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rb/14/cj,nj/1b7dfb88/cc8437ad.js?bu=DikuXGxwdGhgZKwBsAEuoAEu | US | text | 7.54 Kb | whitelisted |
3136 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/fd/ls/l?IG=8AFD60A0E99543BBB727BAF9505998EC&CID=376D4178A7666DB931D94C7DA64E6C3F&Type=Event.CPT&DATA={"pp":{"S":"L","FC":62,"BC":219,"SE":-1,"TC":-1,"H":250,"BP":265,"CT":281,"IL":4},"ad":[192,583,1260,560,1260,498,0]}&P=SERP&DA=Ch1b | US | image | 5.73 Kb | whitelisted |
3136 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/sa/simg/SharedSpriteDesktopRewards_022118.png | US | image | 5.73 Kb | whitelisted |
2976 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3136 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/2Y/2f/cj,nj/bf587ad6/f1d86b5a.js | US | text | 181 b | whitelisted |
3136 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rb/6k/cj,nj/f28dadef/aea7e831.js?bu=AcQF | US | text | 174 b | whitelisted |
3136 | iexplore.exe | GET | 200 | 204.79.197.222:80 | http://61185d9b78c8e0279f8488af63fffbd5.clo.footprintdns.com/apc/trans.gif | US | image | 43 b | suspicious |
3136 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rb/5m/cj,nj/3e6a7d75/9a358300.js?bu=EuoeiB-yHrUe4QTDHsUelB_HHs4e1h6AH_4e8x7nHfMc9hzqHQ | US | text | 4.95 Kb | whitelisted |
3136 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/5d/2s/cj,nj/bab57e12/ea8fe300.js | US | text | 2.75 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3136 | iexplore.exe | 172.105.206.132:443 | zzb.bz | — | US | suspicious |
3136 | iexplore.exe | 172.217.16.138:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3136 | iexplore.exe | 172.217.22.98:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
3136 | iexplore.exe | 172.217.18.162:443 | adservice.google.com | Google Inc. | US | whitelisted |
2976 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3136 | iexplore.exe | 172.217.23.136:443 | ssl.google-analytics.com | Google Inc. | US | whitelisted |
2976 | iexplore.exe | 172.105.206.132:443 | zzb.bz | — | US | suspicious |
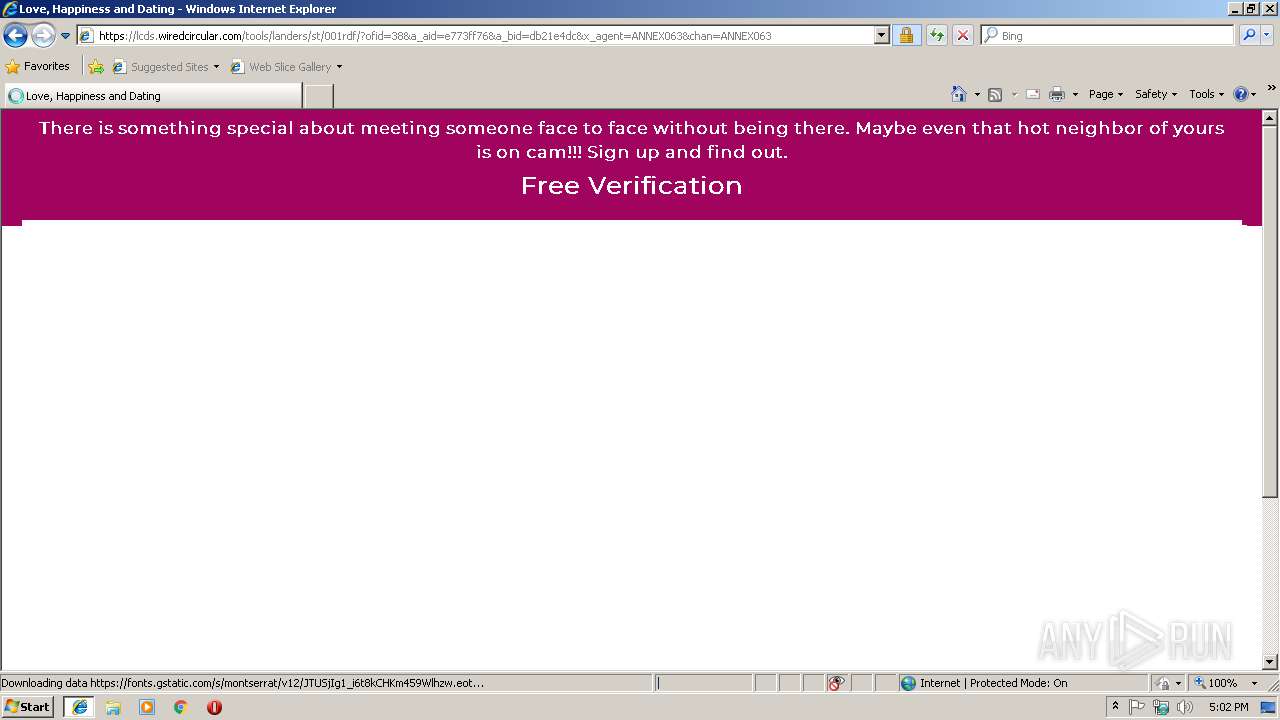
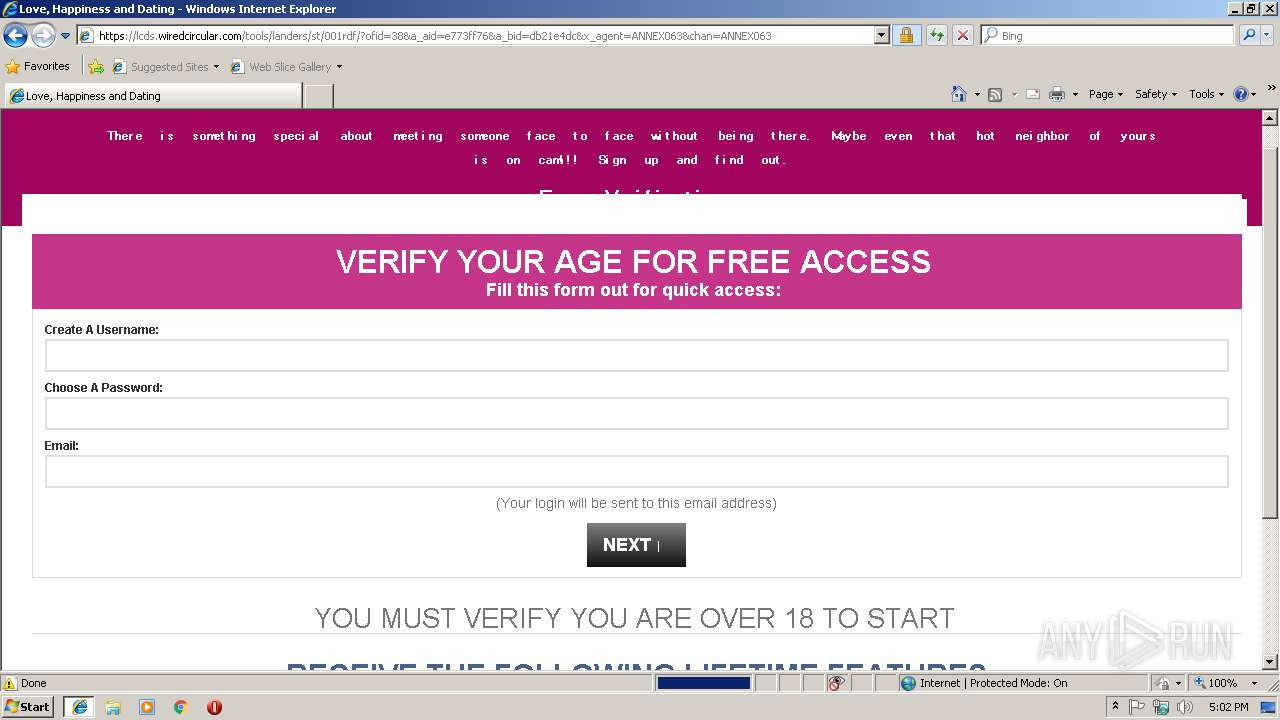
3136 | iexplore.exe | 104.28.1.202:443 | americasweblink.com | Cloudflare Inc | US | shared |
3136 | iexplore.exe | 208.73.160.84:80 | — | FSX HOLDINGS, LLC | US | unknown |
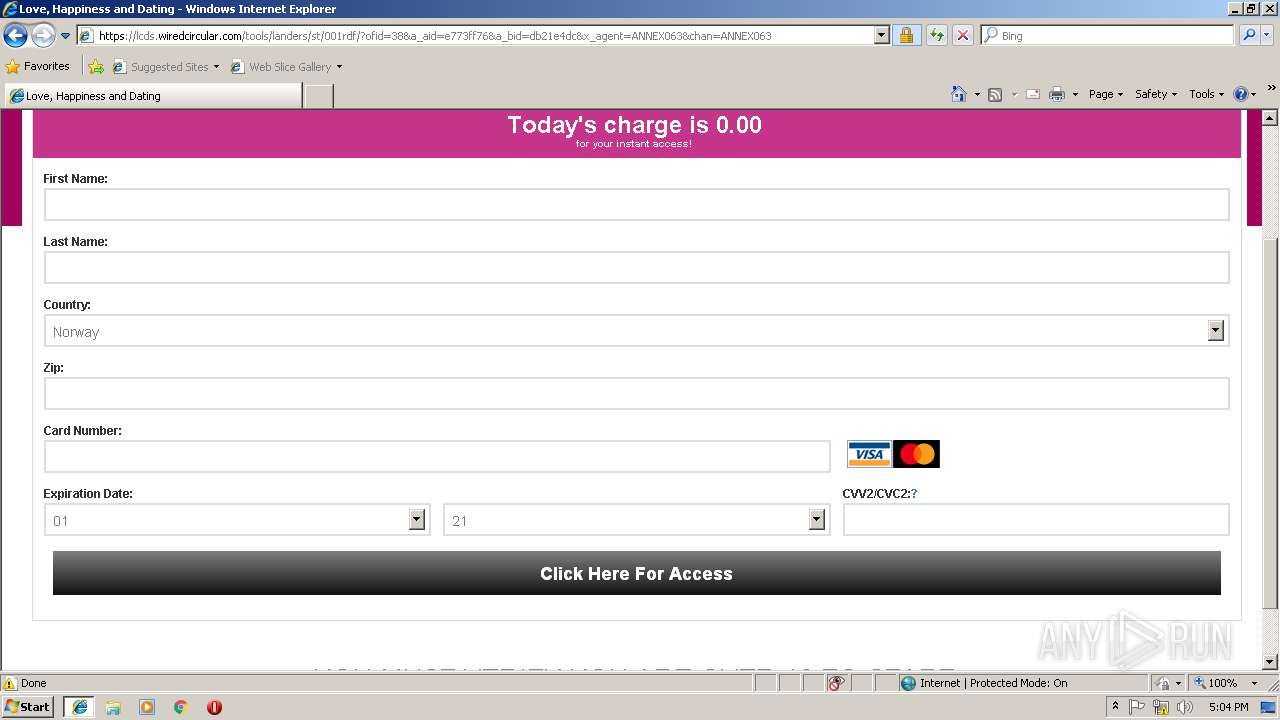
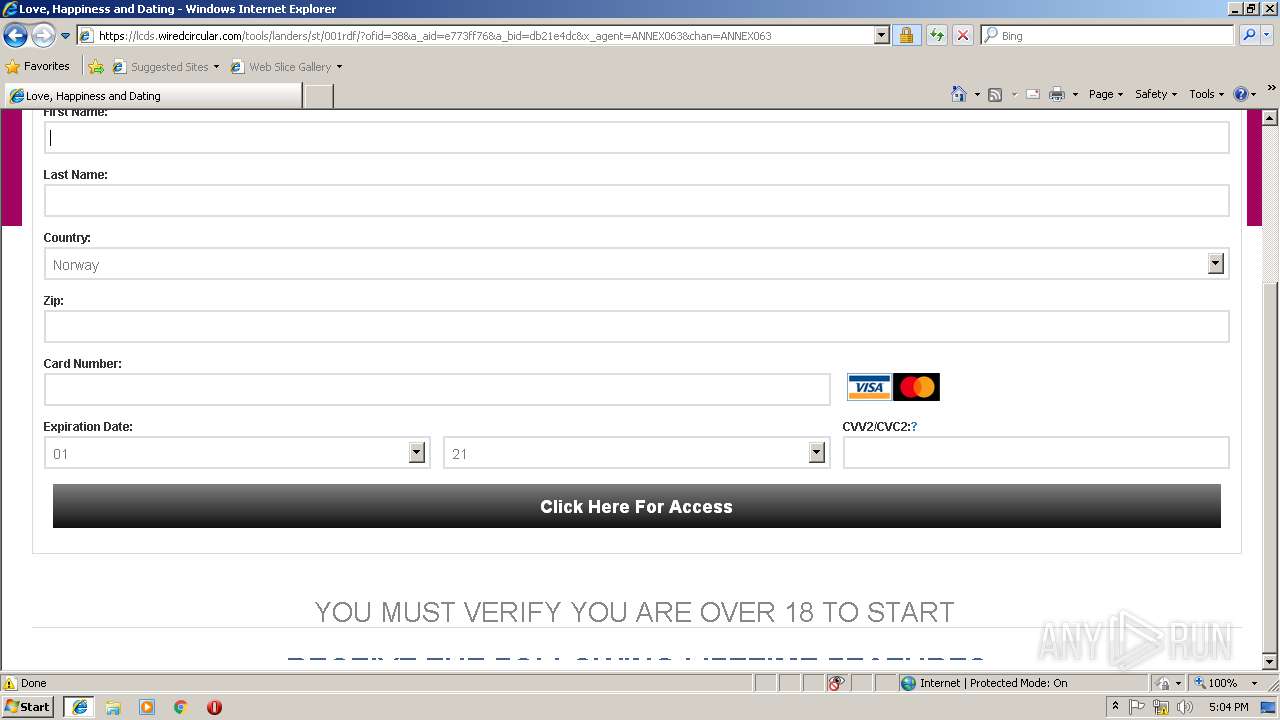
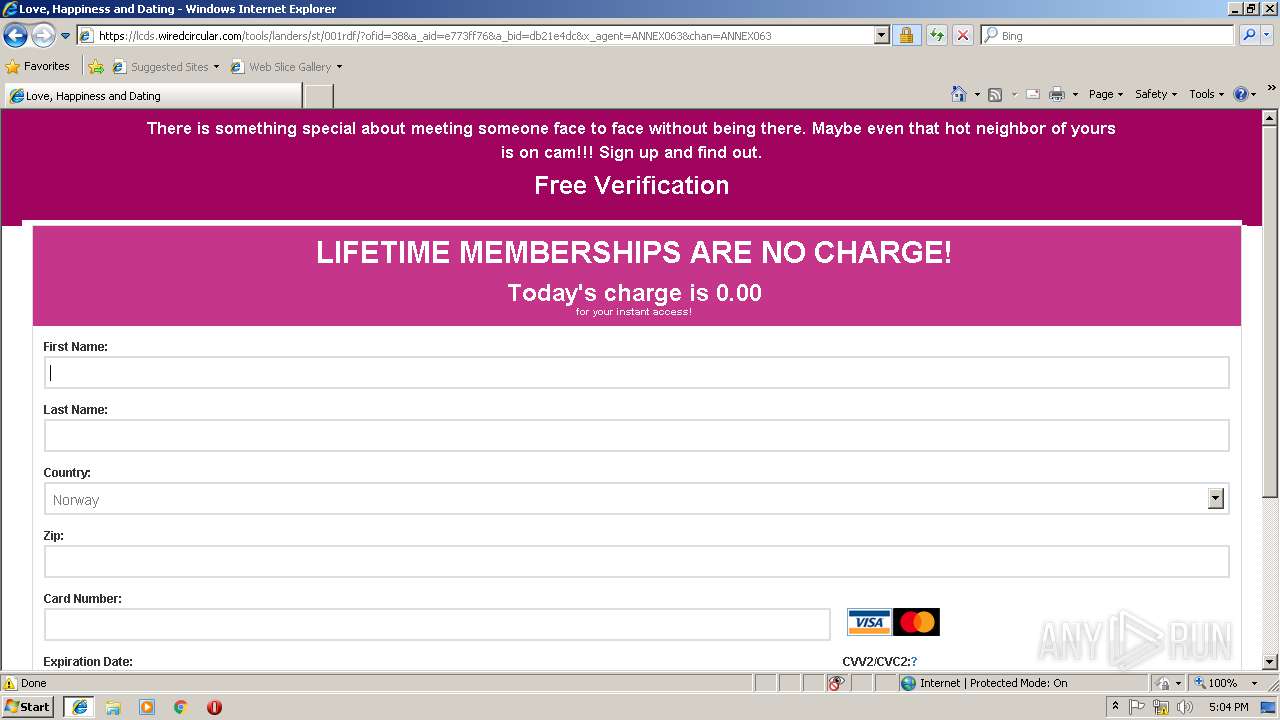
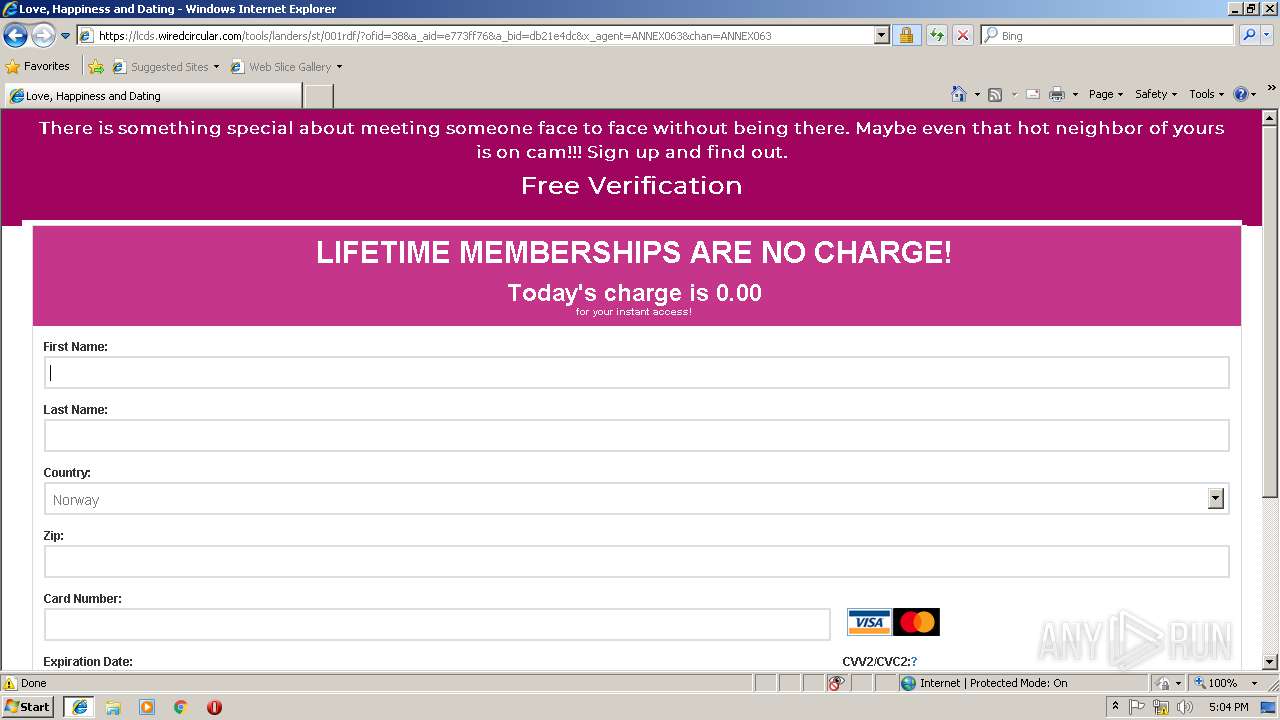
3136 | iexplore.exe | 104.25.174.24:443 | lcds.wiredcircular.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
zzb.bz |
| suspicious |
www.bing.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
adservice.google.com |
| whitelisted |
adservice.google.no |
| whitelisted |
ssl.google-analytics.com |
| whitelisted |
americasweblink.com |
| suspicious |
lcds.wiredcircular.com |
| unknown |
fonts.googleapis.com |
| whitelisted |