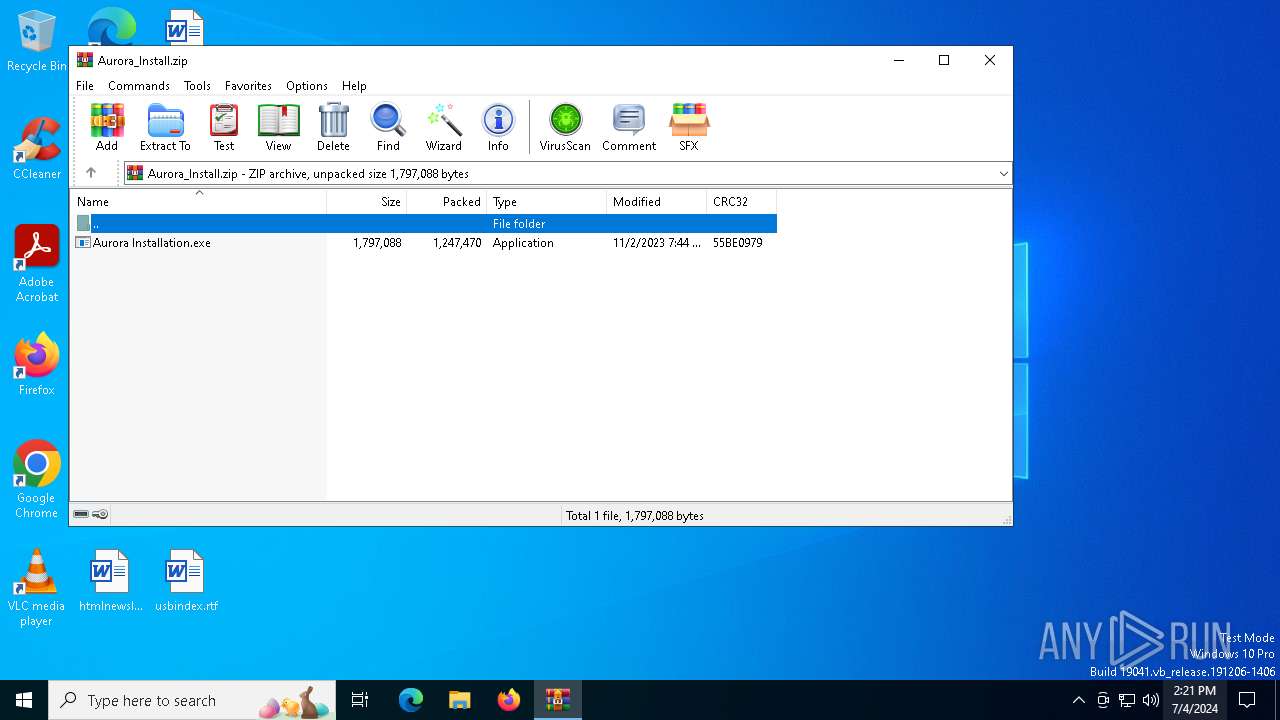
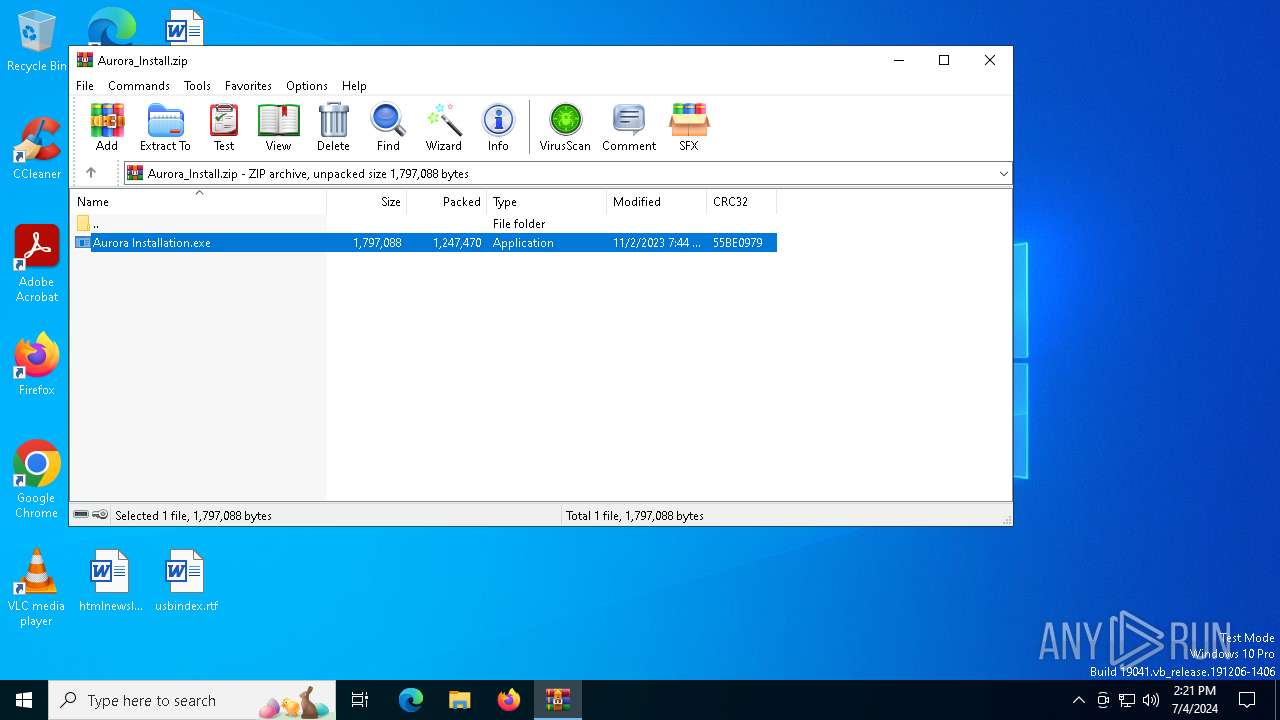
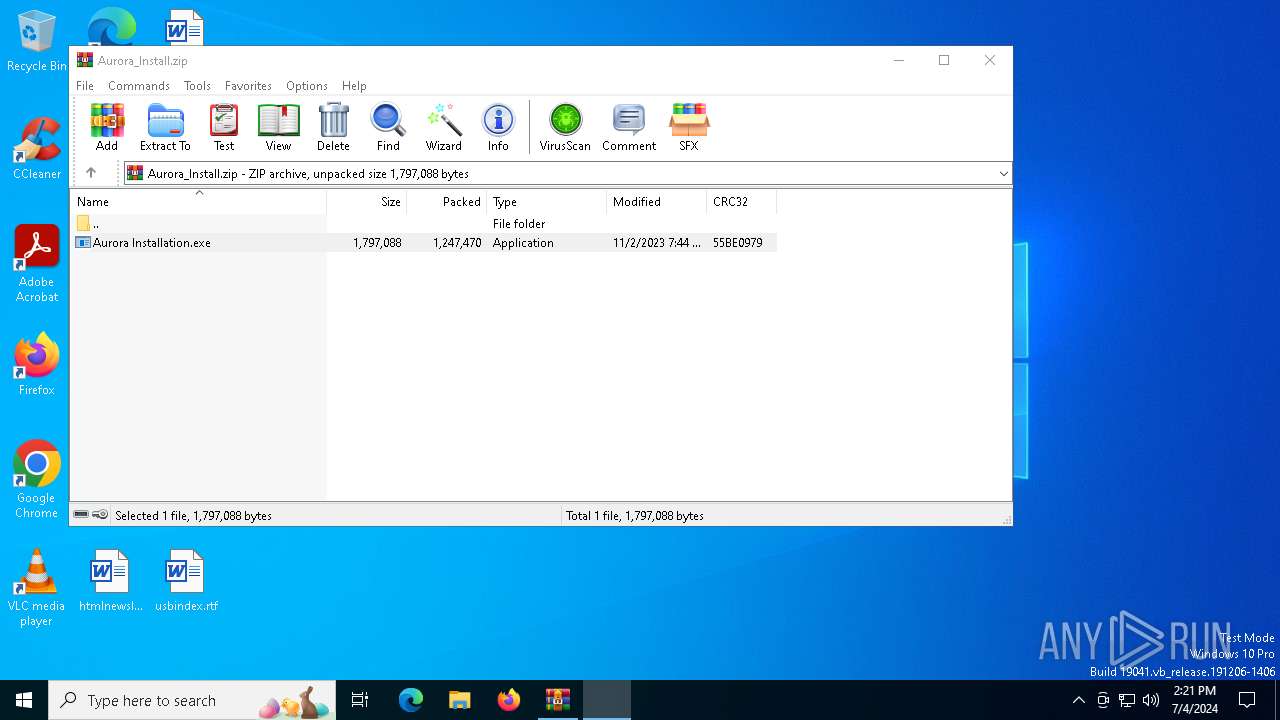
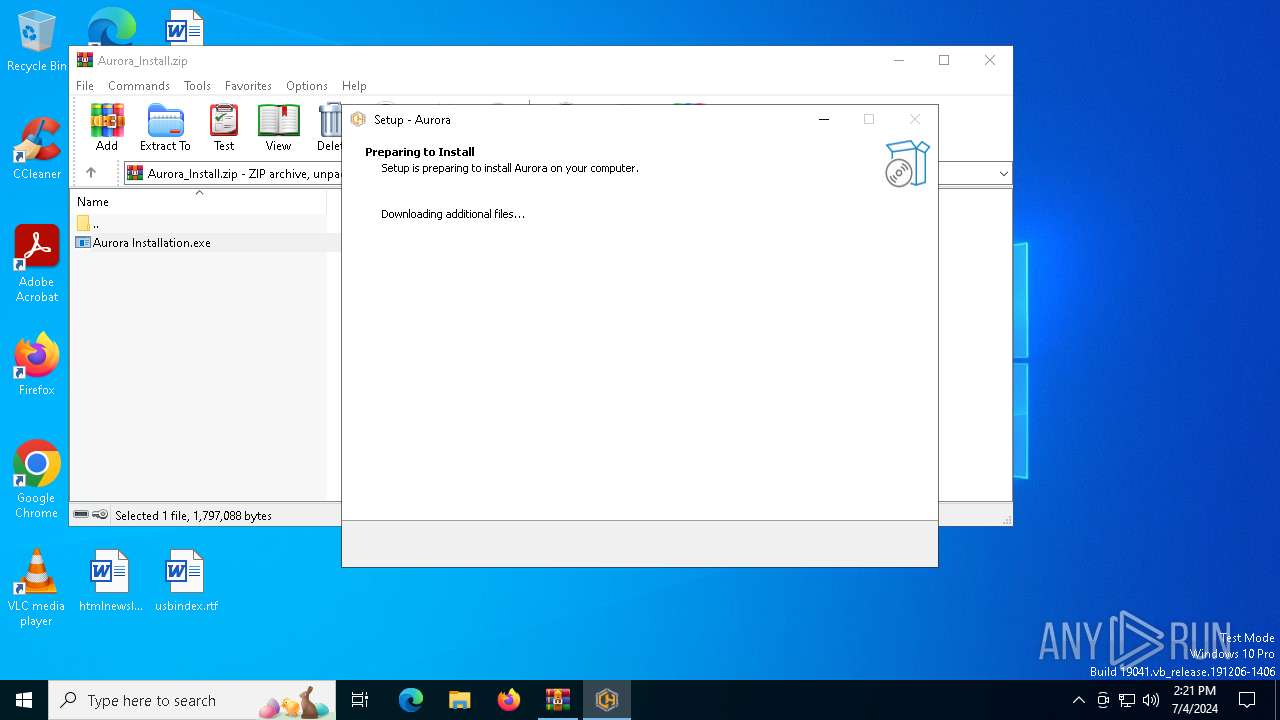
| File name: | Aurora_Install.zip |
| Full analysis: | https://app.any.run/tasks/ee9258f8-b28d-45e9-9a05-53f5bacb5923 |
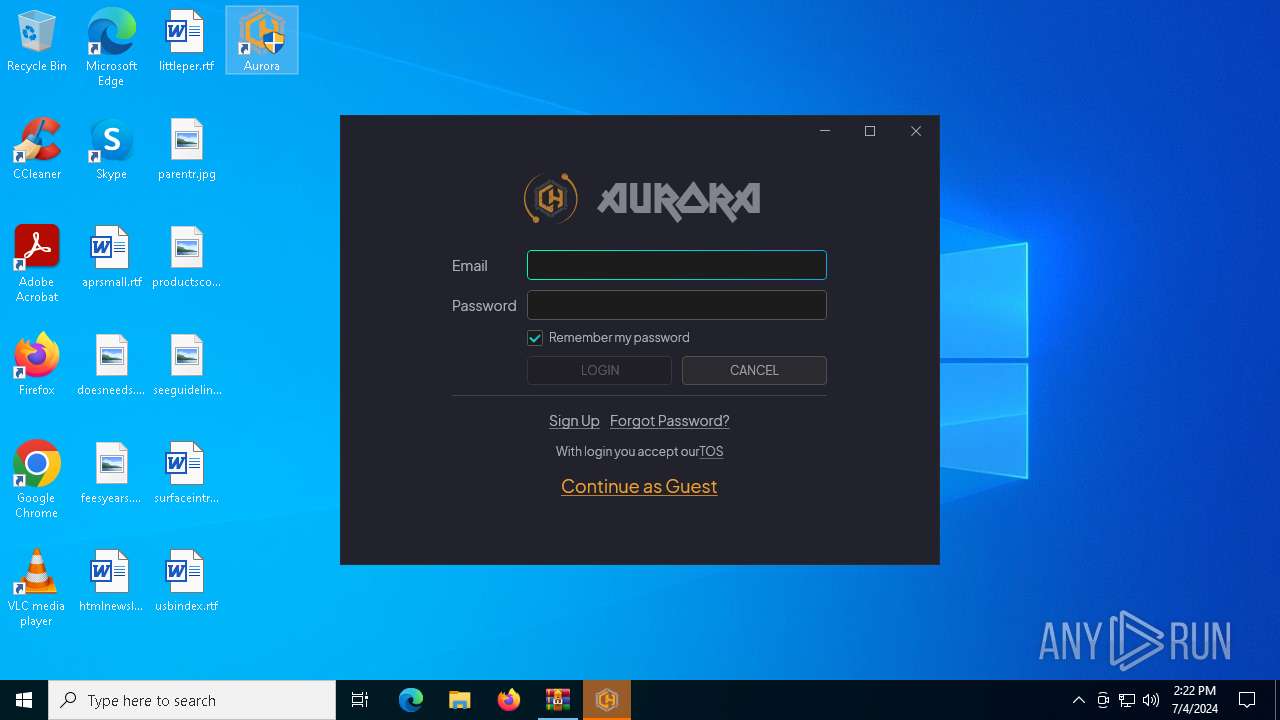
| Verdict: | Malicious activity |
| Analysis date: | July 04, 2024, 14:21:00 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | C90E775B0FB4E589D10267141EEE994B |
| SHA1: | A0C27EFBF30587FDF2E13BDB3FA2915AC9A39EBB |
| SHA256: | 592FD8B1513102016C6FFB1C0ABE2833B8BDCDC75D0FE9B43A35D8CED5C63C63 |
| SSDEEP: | 49152:p6uDPZsvQnlPZ05QUsqO1sLENQtWGlTCaFfK/OF3aWO304X+fkiM8ZRcbESzOp1G:p6uy4lPZ0qrqMs4iheaFy/O1ap3NOfkZ |
MALICIOUS
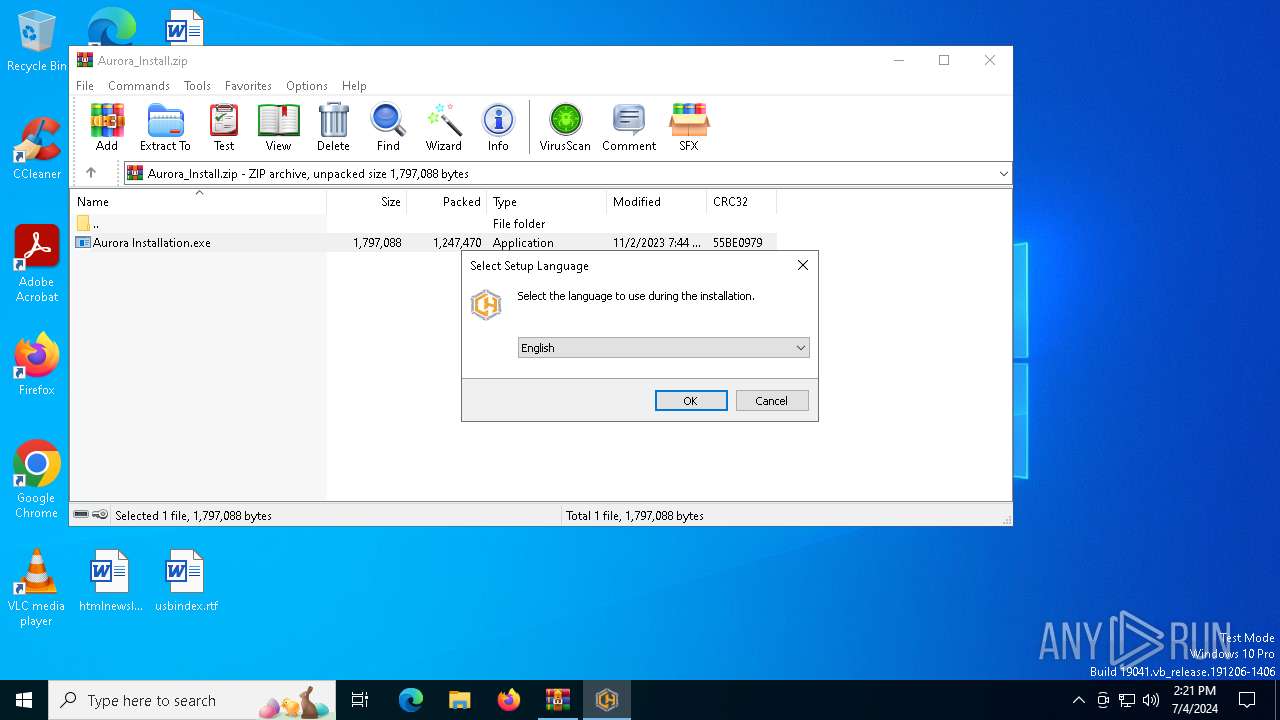
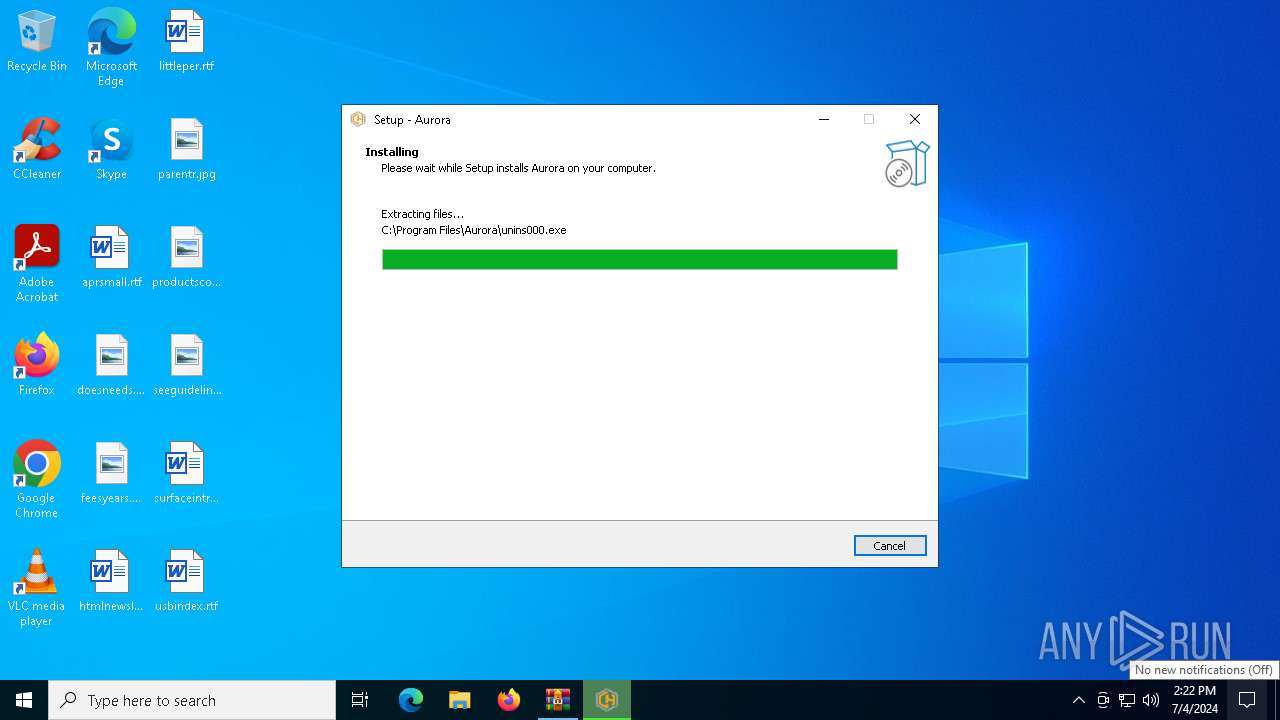
Drops the executable file immediately after the start
- Aurora Installation.exe (PID: 3836)
- Aurora Installation.exe (PID: 992)
- WinRAR.exe (PID: 5396)
- Aurora Installation.tmp (PID: 3832)
SUSPICIOUS
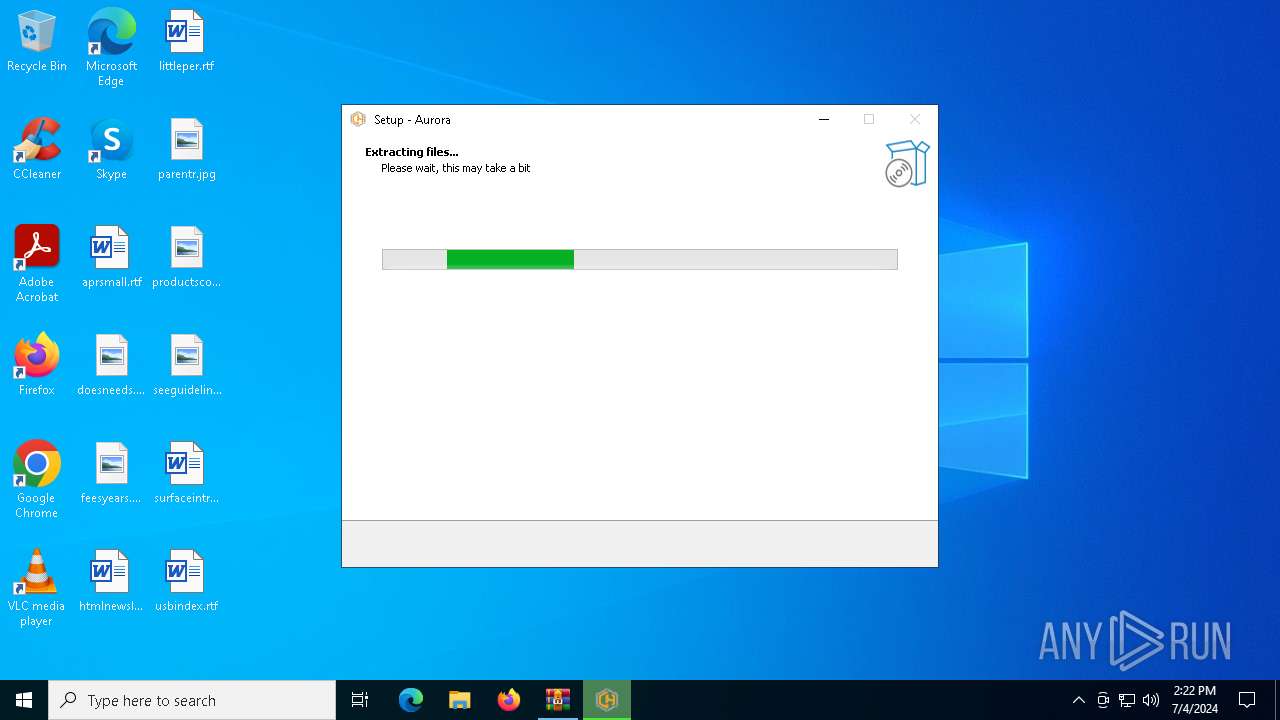
Executable content was dropped or overwritten
- Aurora Installation.exe (PID: 3836)
- Aurora Installation.exe (PID: 992)
- Aurora Installation.tmp (PID: 3832)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5396)
- Aurora Installation.tmp (PID: 1956)
- Aurora Installation.tmp (PID: 3832)
- Aurora.exe (PID: 4628)
- Aurora.exe (PID: 5992)
Reads the date of Windows installation
- Aurora Installation.tmp (PID: 1956)
- Aurora.exe (PID: 4628)
- Aurora.exe (PID: 5992)
Reads the Windows owner or organization settings
- Aurora Installation.tmp (PID: 3832)
Process drops legitimate windows executable
- Aurora Installation.tmp (PID: 3832)
The process drops C-runtime libraries
- Aurora Installation.tmp (PID: 3832)
The process creates files with name similar to system file names
- Aurora Installation.tmp (PID: 3832)
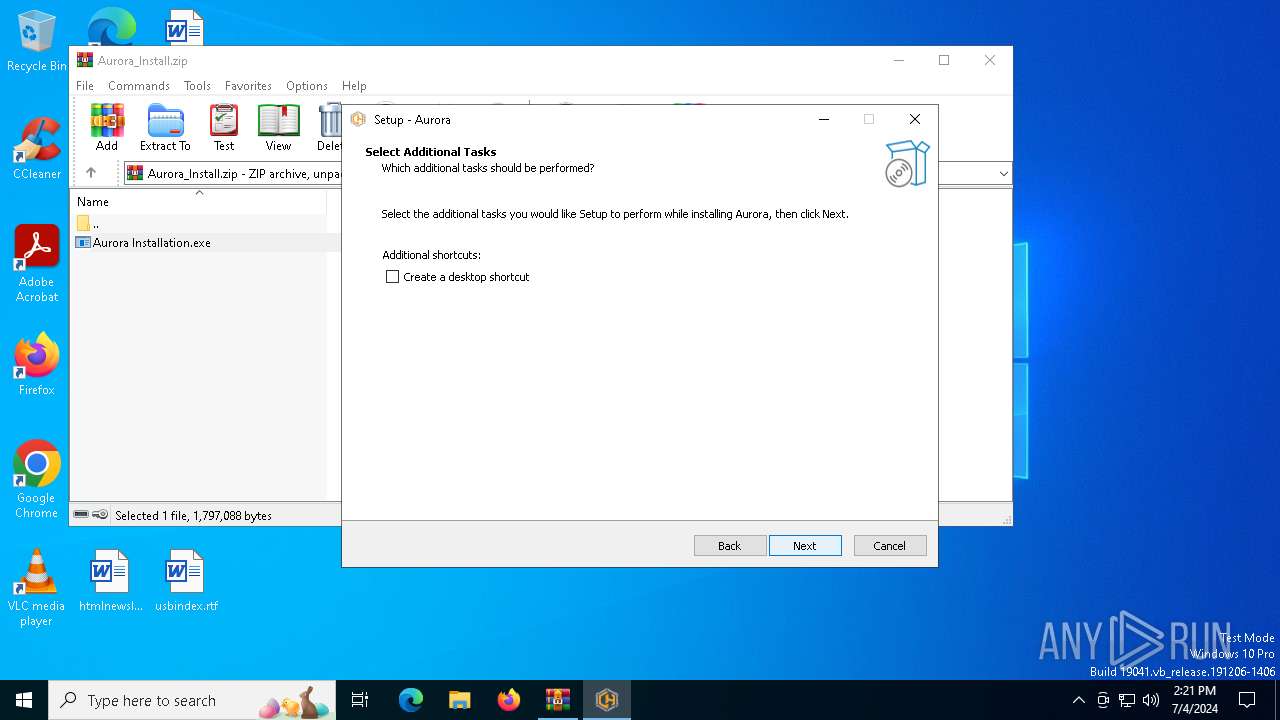
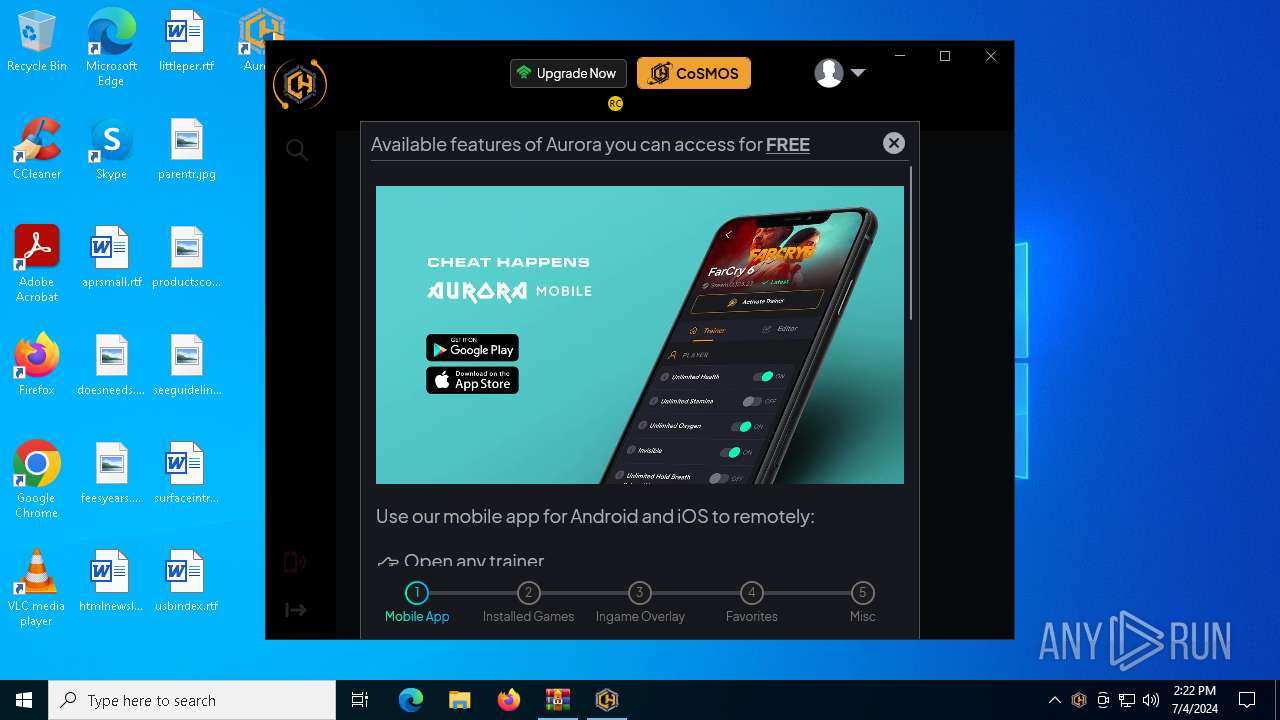
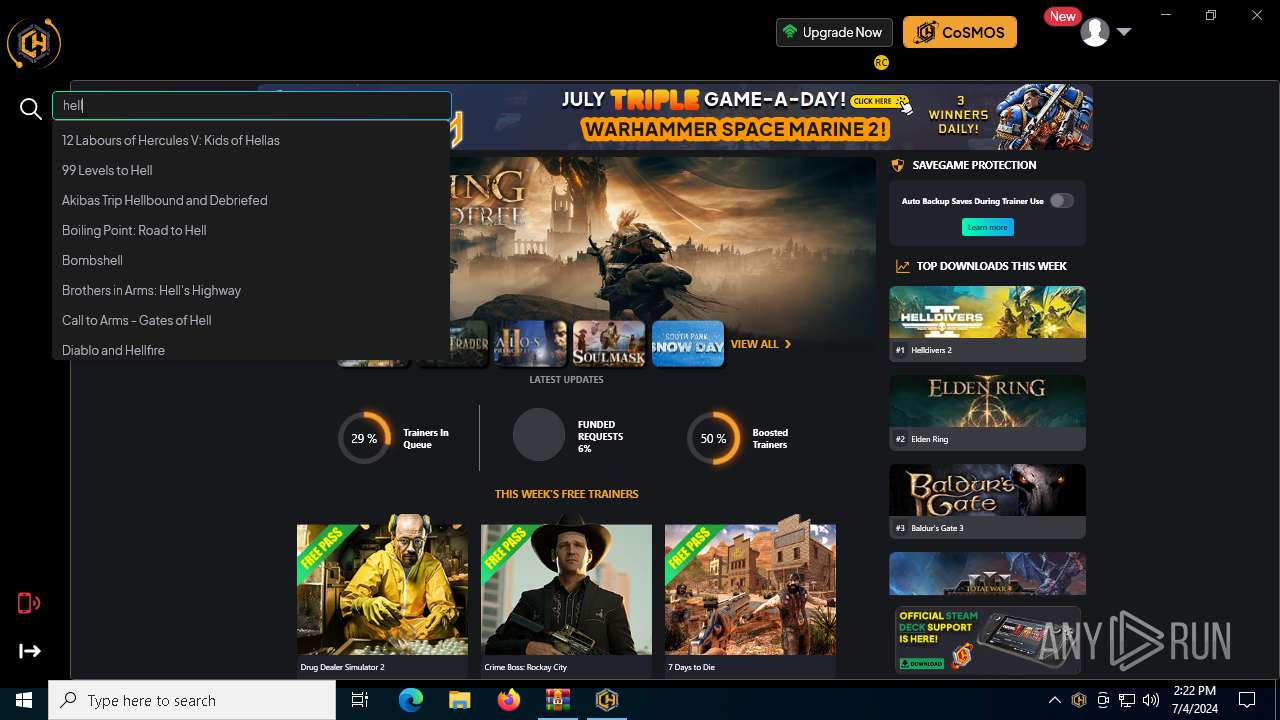
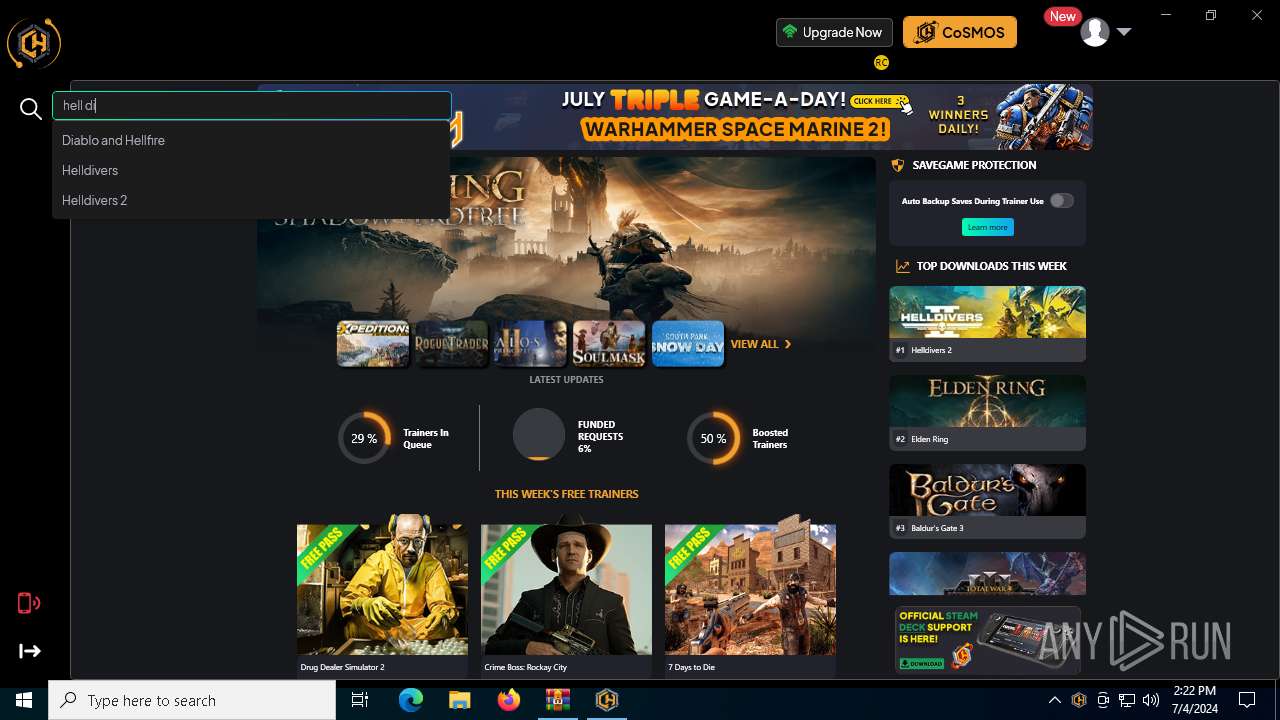
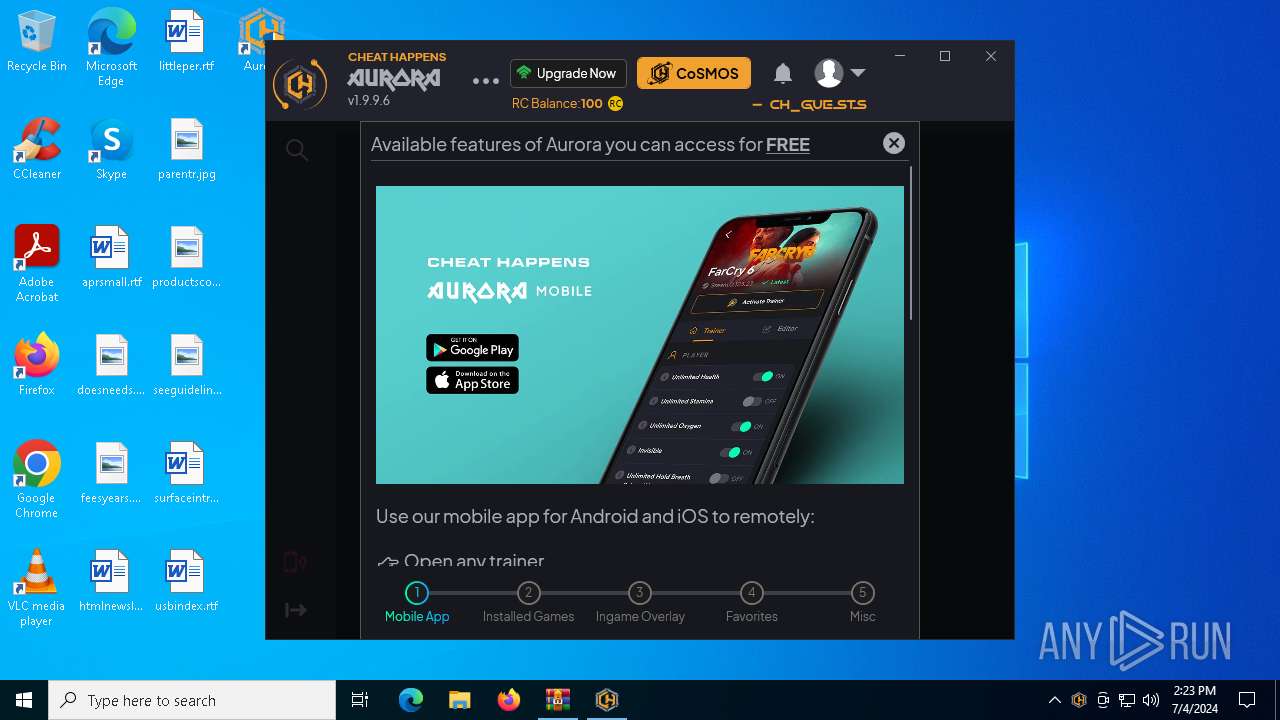
Searches for installed software
- Aurora.exe (PID: 4628)
- Aurora.exe (PID: 5992)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5396)
Process checks computer location settings
- Aurora Installation.tmp (PID: 1956)
- Aurora.exe (PID: 4628)
- Aurora.exe (PID: 5992)
Checks supported languages
- Aurora Installation.exe (PID: 992)
- Aurora Installation.tmp (PID: 1956)
- Aurora.exe (PID: 4628)
- Aurora Installation.exe (PID: 3836)
- Aurora.exe (PID: 4632)
- Aurora.exe (PID: 5992)
- Aurora Installation.tmp (PID: 3832)
Create files in a temporary directory
- Aurora Installation.exe (PID: 3836)
- Aurora Installation.tmp (PID: 3832)
- Aurora Installation.exe (PID: 992)
Reads the computer name
- Aurora Installation.tmp (PID: 1956)
- Aurora Installation.tmp (PID: 3832)
- Aurora.exe (PID: 4632)
- Aurora.exe (PID: 5992)
- Aurora.exe (PID: 4628)
Checks proxy server information
- Aurora Installation.tmp (PID: 3832)
- slui.exe (PID: 4836)
- Aurora.exe (PID: 4628)
- Aurora.exe (PID: 5992)
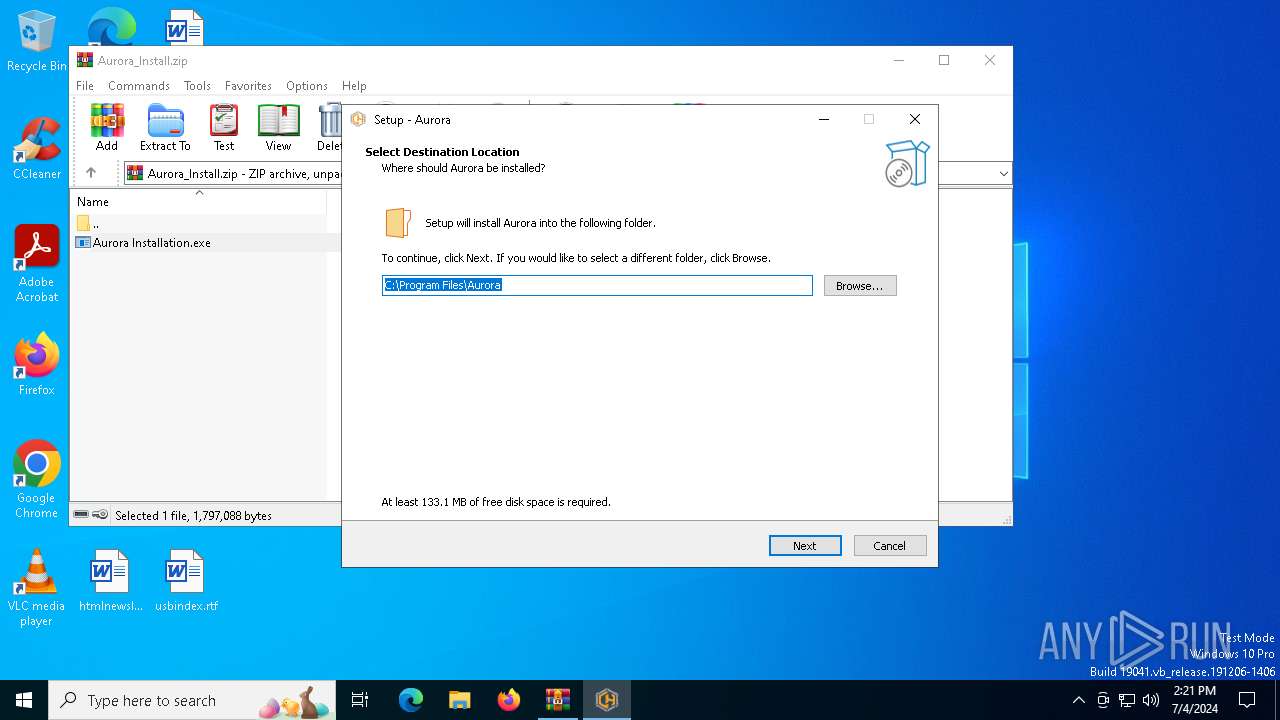
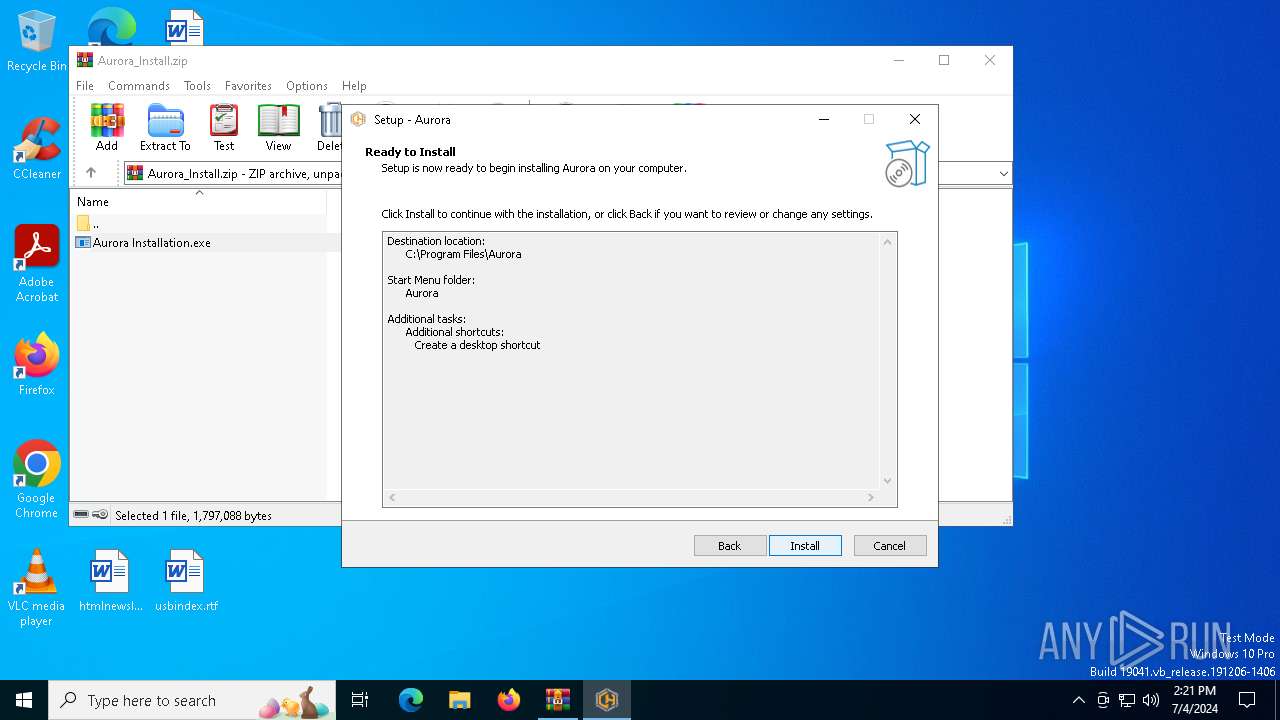
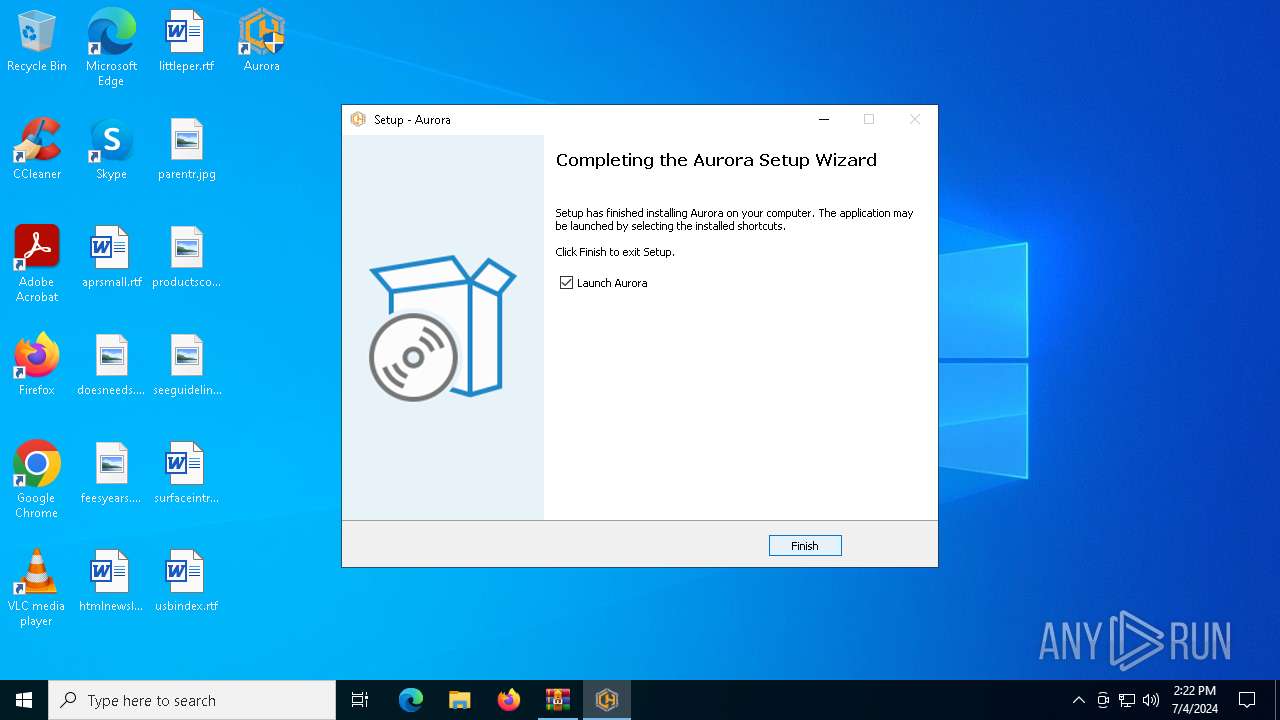
Creates files in the program directory
- Aurora Installation.tmp (PID: 3832)
- Aurora.exe (PID: 4628)
Creates a software uninstall entry
- Aurora Installation.tmp (PID: 3832)
Reads the software policy settings
- Aurora Installation.tmp (PID: 3832)
- slui.exe (PID: 7028)
- Aurora.exe (PID: 4628)
- slui.exe (PID: 4836)
- Aurora.exe (PID: 5992)
Manual execution by a user
- Aurora.exe (PID: 3164)
- Aurora.exe (PID: 4632)
- Aurora.exe (PID: 5992)
- Aurora.exe (PID: 6616)
Creates files or folders in the user directory
- Aurora.exe (PID: 4628)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2023:11:02 19:44:38 |
| ZipCRC: | 0x55be0979 |
| ZipCompressedSize: | 1247470 |
| ZipUncompressedSize: | 1797088 |
| ZipFileName: | Aurora Installation.exe |
Total processes
161
Monitored processes
14
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 992 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5396.17919\Aurora Installation.exe" /SPAWNWND=$801E2 /NOTIFYWND=$902CE | C:\Users\admin\AppData\Local\Temp\Rar$EXa5396.17919\Aurora Installation.exe | Aurora Installation.tmp | ||||||||||||
User: admin Company: Cheat Happens Integrity Level: HIGH Description: Aurora Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1956 | "C:\Users\admin\AppData\Local\Temp\is-D0U7N.tmp\Aurora Installation.tmp" /SL5="$902CE,841216,841216,C:\Users\admin\AppData\Local\Temp\Rar$EXa5396.17919\Aurora Installation.exe" | C:\Users\admin\AppData\Local\Temp\is-D0U7N.tmp\Aurora Installation.tmp | — | Aurora Installation.exe | |||||||||||
User: admin Company: Cheat Happens Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3164 | "C:\Program Files\Aurora\Aurora.exe" | C:\Program Files\Aurora\Aurora.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.9.9.6 Modules
| |||||||||||||||
| 3832 | "C:\Users\admin\AppData\Local\Temp\is-TN3DV.tmp\Aurora Installation.tmp" /SL5="$60346,841216,841216,C:\Users\admin\AppData\Local\Temp\Rar$EXa5396.17919\Aurora Installation.exe" /SPAWNWND=$801E2 /NOTIFYWND=$902CE | C:\Users\admin\AppData\Local\Temp\is-TN3DV.tmp\Aurora Installation.tmp | Aurora Installation.exe | ||||||||||||
User: admin Company: Cheat Happens Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3836 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5396.17919\Aurora Installation.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa5396.17919\Aurora Installation.exe | WinRAR.exe | ||||||||||||
User: admin Company: Cheat Happens Integrity Level: MEDIUM Description: Aurora Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 4628 | "C:\Program Files\Aurora\Aurora.exe" | C:\Program Files\Aurora\Aurora.exe | Aurora Installation.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 4294967295 Version: 1.9.9.6 Modules
| |||||||||||||||
| 4632 | "C:\Program Files\Aurora\Aurora.exe" | C:\Program Files\Aurora\Aurora.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.9.9.6 Modules
| |||||||||||||||
| 4836 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5396 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Aurora_Install.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 5992 | "C:\Program Files\Aurora\Aurora.exe" | C:\Program Files\Aurora\Aurora.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 4294967295 Version: 1.9.9.6 Modules
| |||||||||||||||
Total events
45 923
Read events
45 829
Write events
90
Delete events
4
Modification events
| (PID) Process: | (5396) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (5396) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (5396) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (5396) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Aurora_Install.zip | |||
| (PID) Process: | (5396) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5396) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5396) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5396) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5396) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (5396) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
287
Suspicious files
61
Text files
13
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3832 | Aurora Installation.tmp | C:\Users\admin\AppData\Local\Temp\is-K12IP.tmp\is-IM4H2.tmp | — | |
MD5:— | SHA256:— | |||
| 3832 | Aurora Installation.tmp | C:\Users\admin\AppData\Local\Temp\is-K12IP.tmp\Aurora.zip | — | |
MD5:— | SHA256:— | |||
| 3832 | Aurora Installation.tmp | C:\Program Files\Aurora\audio\please wait.mp3 | mp3 | |
MD5:DE40712B34492EBA152848BB395C3A7D | SHA256:807E5A10308B26164860A2C87603A42C3A413A4C0E4493CBFF9F7095623449BC | |||
| 3832 | Aurora Installation.tmp | C:\Program Files\Aurora\audio\savegame protection enabled.mp3 | mp3 | |
MD5:4B1AD88857BA46DA24845019802352F5 | SHA256:C46D48D6B145C0EB803DF97FB8D52E0FF3026FD41699E76FB988185844ED2AA7 | |||
| 3832 | Aurora Installation.tmp | C:\Program Files\Aurora\audio\trainer activated.mp3 | mp3 | |
MD5:22B2BE5858786122337589D024221D98 | SHA256:C4A76483E47289BB48B8F255FDA68A3CAF1E6E782D2C0B84D02CC1E34C0C211B | |||
| 3832 | Aurora Installation.tmp | C:\Program Files\Aurora\audio\a new trainer update is available.mp3 | mp3 | |
MD5:B694CAFE2380784861D147E46B3F1651 | SHA256:A604DAA41820EDEA760C16B46A229290840D57015DAA706AE4D4AE5A74863478 | |||
| 3832 | Aurora Installation.tmp | C:\Program Files\Aurora\Assembler.dll | executable | |
MD5:EB4CE9252CB6B53A35A7B2343E103A5B | SHA256:54E7081252F7004608C6F8FC91CA7B8D054A97461CD6893E1BBB33F067B7625D | |||
| 3832 | Aurora Installation.tmp | C:\Program Files\Aurora\audio\savegame protected.mp3 | mp3 | |
MD5:FA59E566B86A0EAC2E7931D2F48FBB5F | SHA256:D2363FCEDAF02EDC7442C0E666830CE4A207136E6E7D9E47BA0F3D75FAA19862 | |||
| 3832 | Aurora Installation.tmp | C:\Program Files\Aurora\audio\failed.mp3 | mp3 | |
MD5:2C0D142262BEE0FA849DA0EF912AE6FE | SHA256:4C2C444BC8AFF4766B35F9D50015365716BEBD8EFE4F838FE51844046C6FCAE3 | |||
| 3832 | Aurora Installation.tmp | C:\Program Files\Aurora\audio\female\a new trainer update is available.mp3 | mp3 | |
MD5:3794F1B3A6B7E7BF29E3AC8CFA6F4441 | SHA256:AAF0A3125B9B581B5D182AD699ACAA0181248767CD4E10F979C95E88B314AFBB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
89
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2064 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
648 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
2064 | svchost.exe | GET | 200 | 2.16.164.106:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
2764 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
7088 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
3688 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
3040 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | unknown |
7088 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3580 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1888 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2064 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2064 | svchost.exe | 2.16.164.106:80 | crl.microsoft.com | Akamai International B.V. | NL | unknown |
2064 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
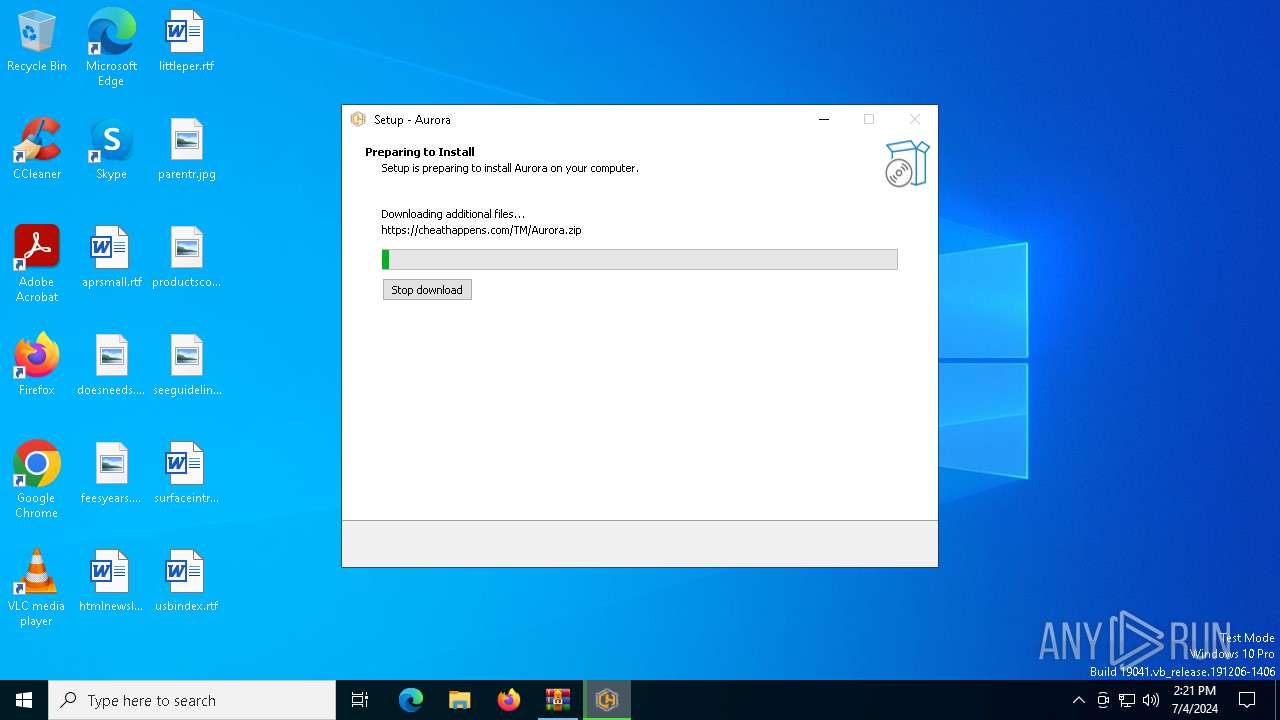
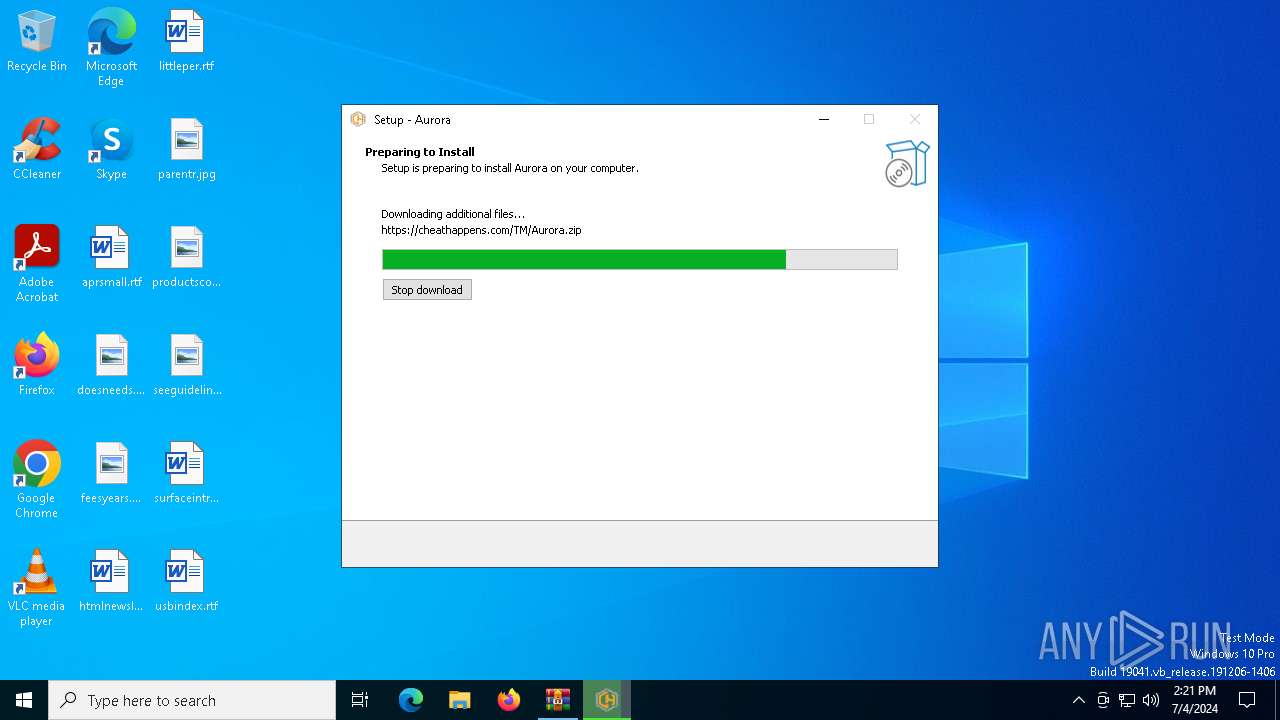
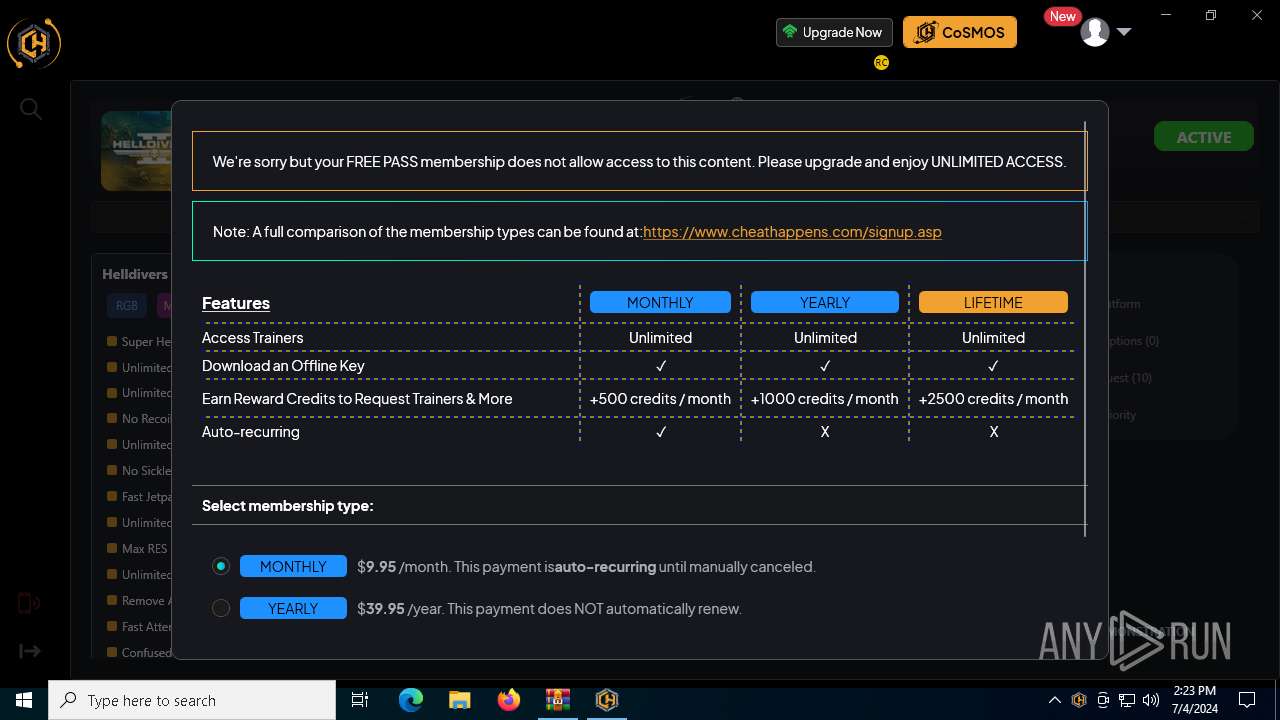
3832 | Aurora Installation.tmp | 95.101.111.132:443 | cheathappens.com | TELXIUS TELXIUS Cable | NL | unknown |
3832 | Aurora Installation.tmp | 2.16.100.40:443 | www.cheathappens.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
cheathappens.com |
| whitelisted |
www.cheathappens.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Aurora.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|