| File name: | ab41f8d4dcef49ba87d3addf23e7c6d8 |
| Full analysis: | https://app.any.run/tasks/db85c1e3-1f47-4014-9e43-5e89b05add7b |
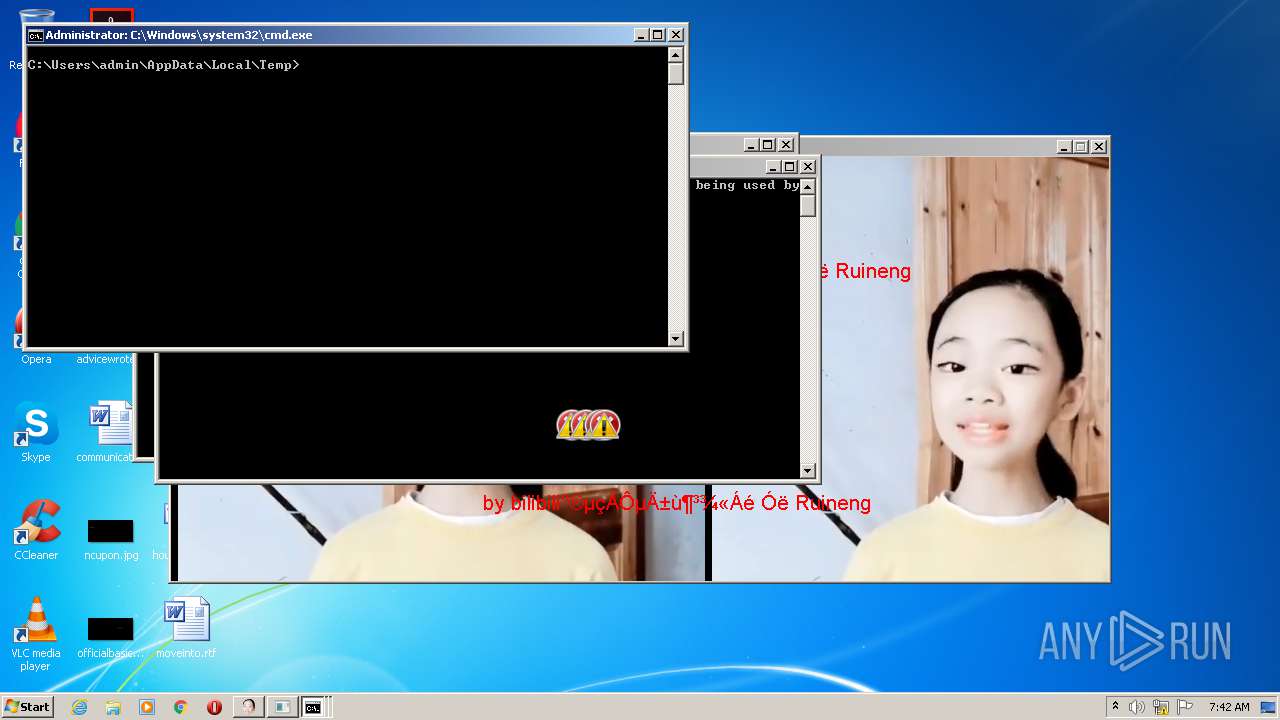
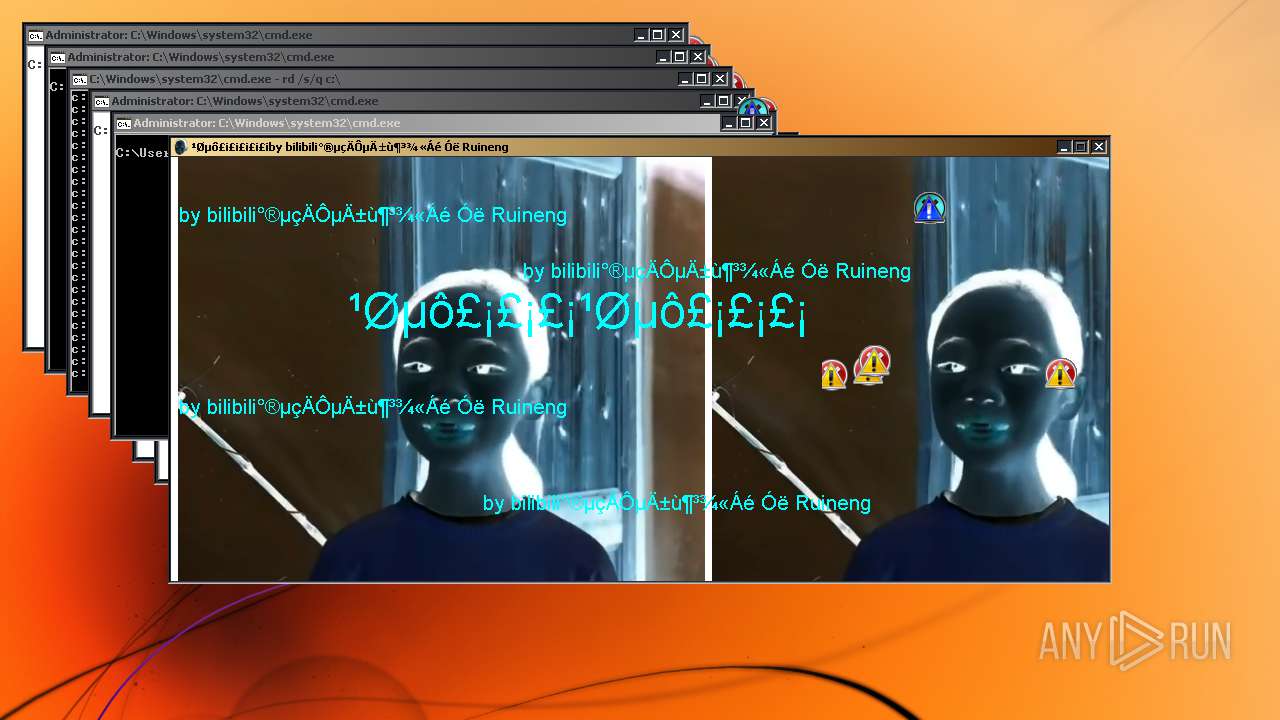
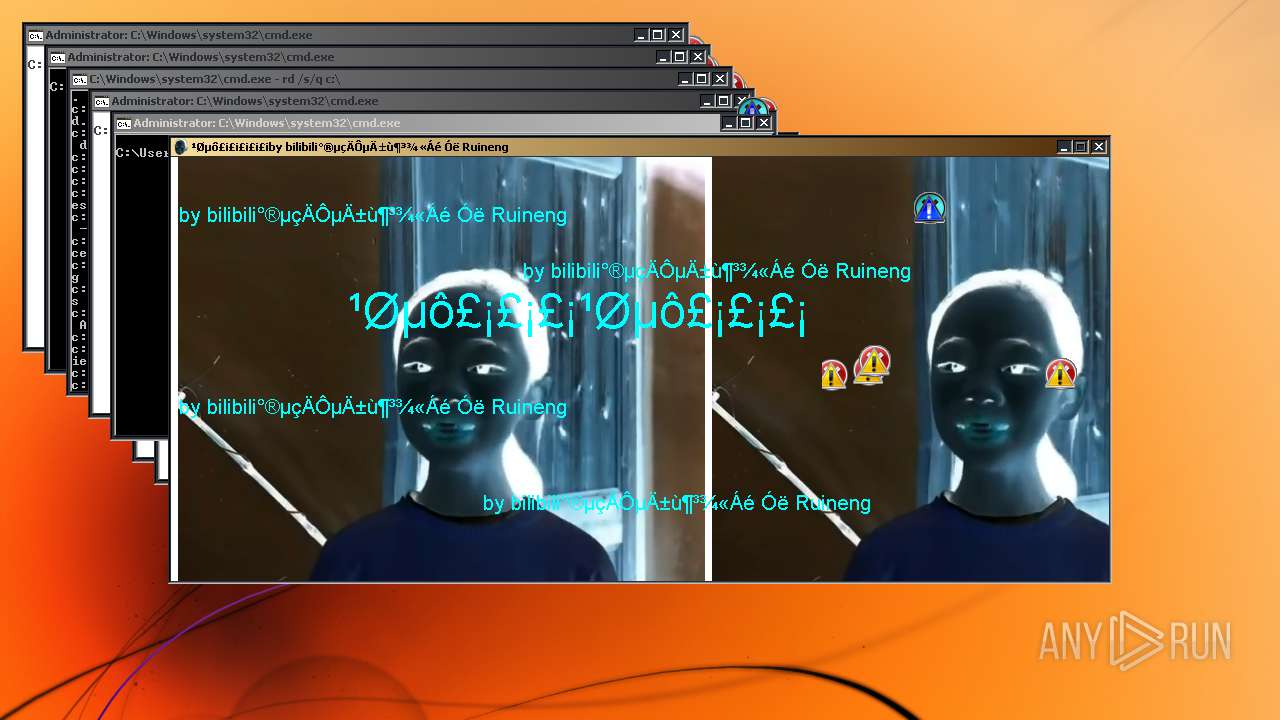
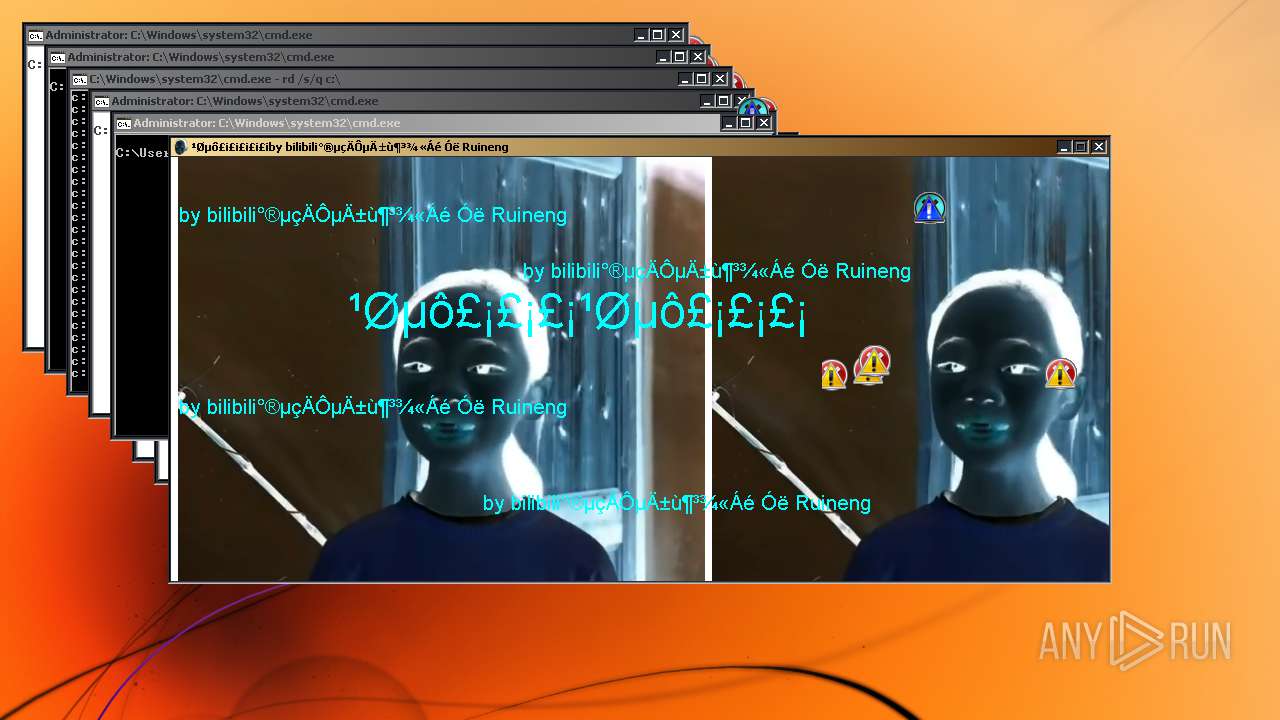
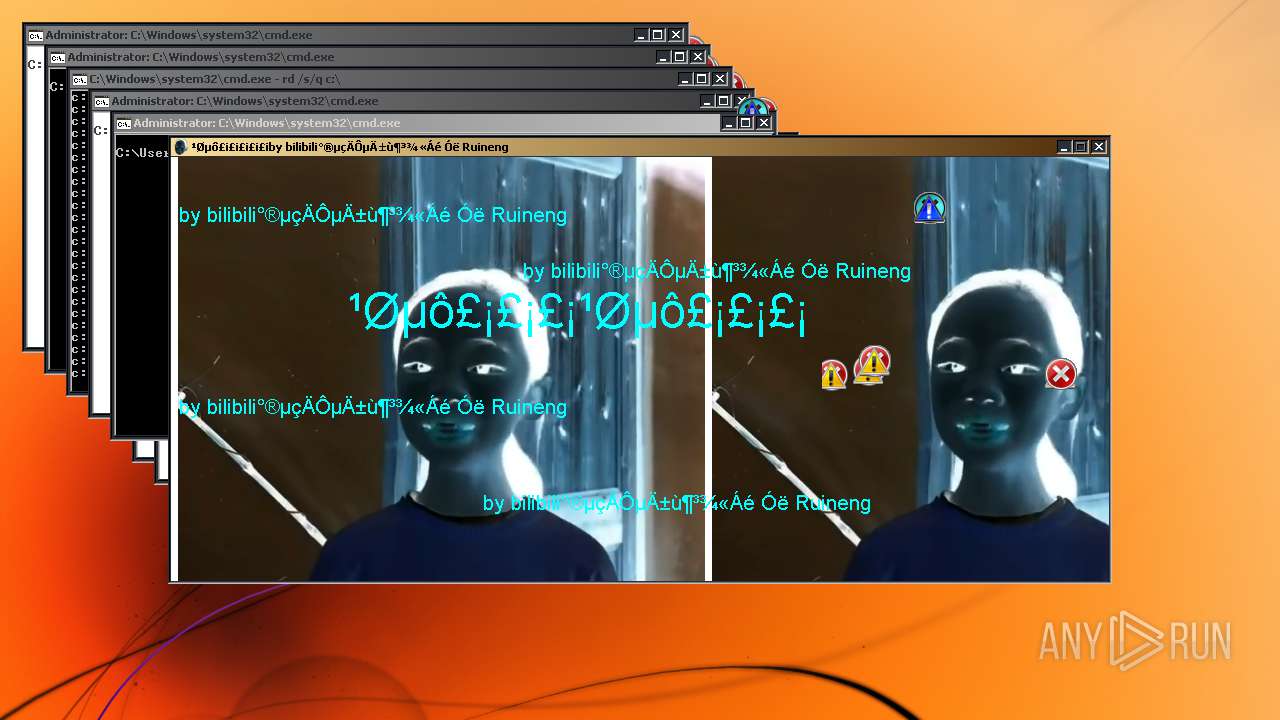
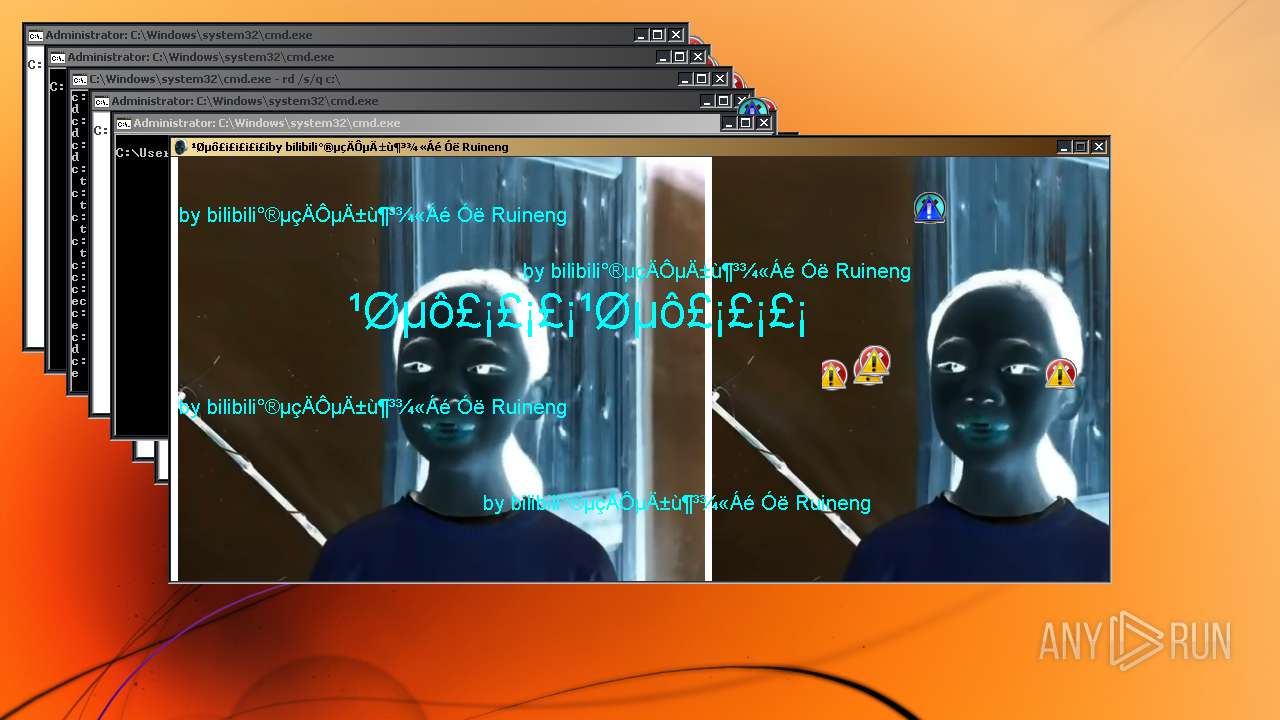
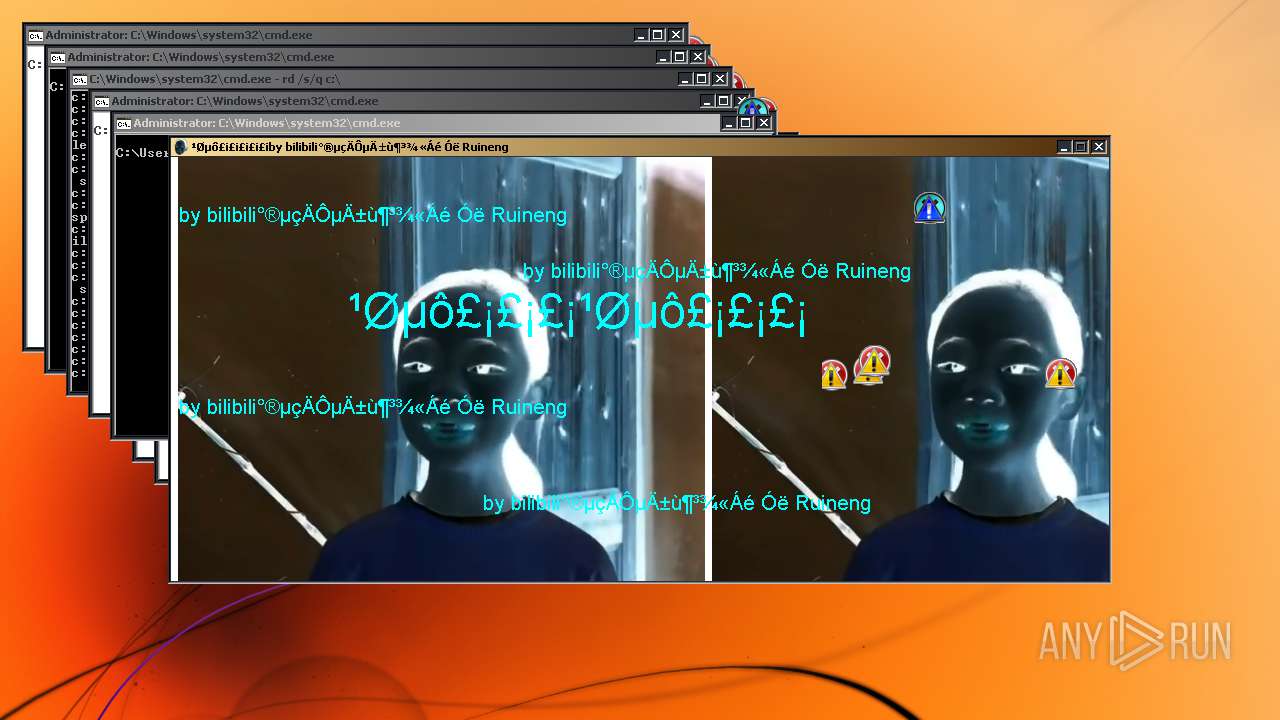
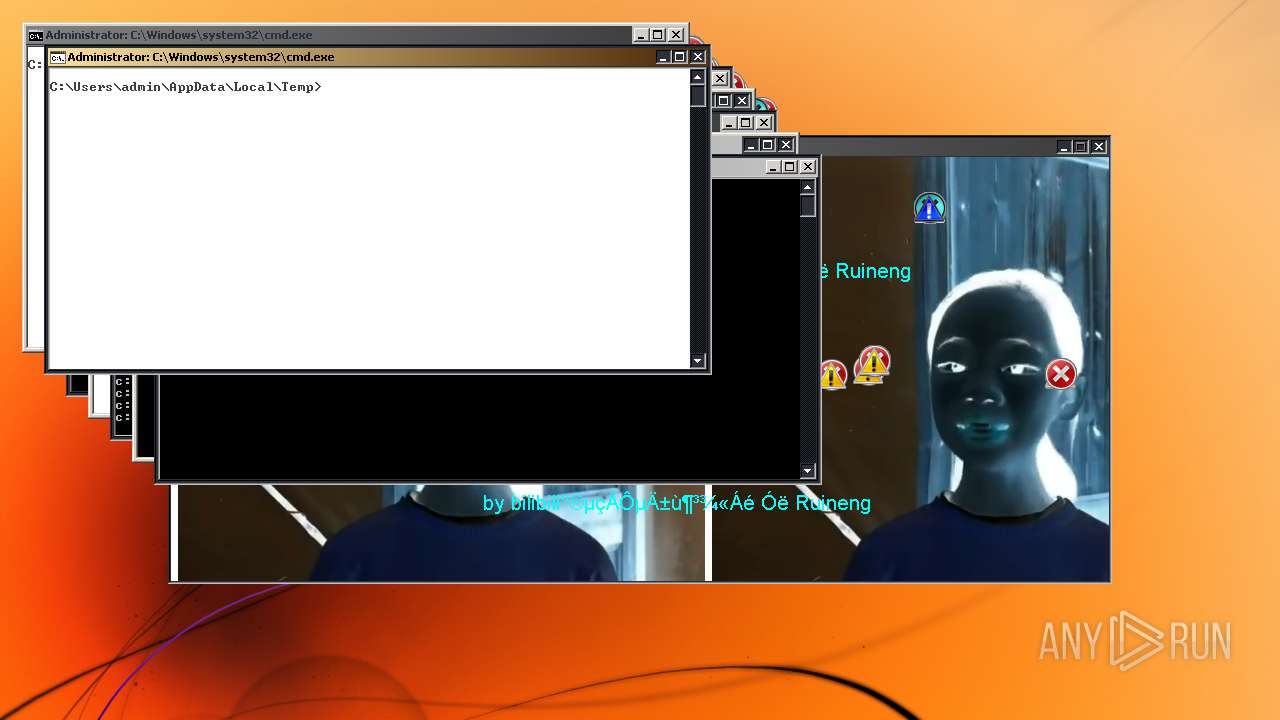
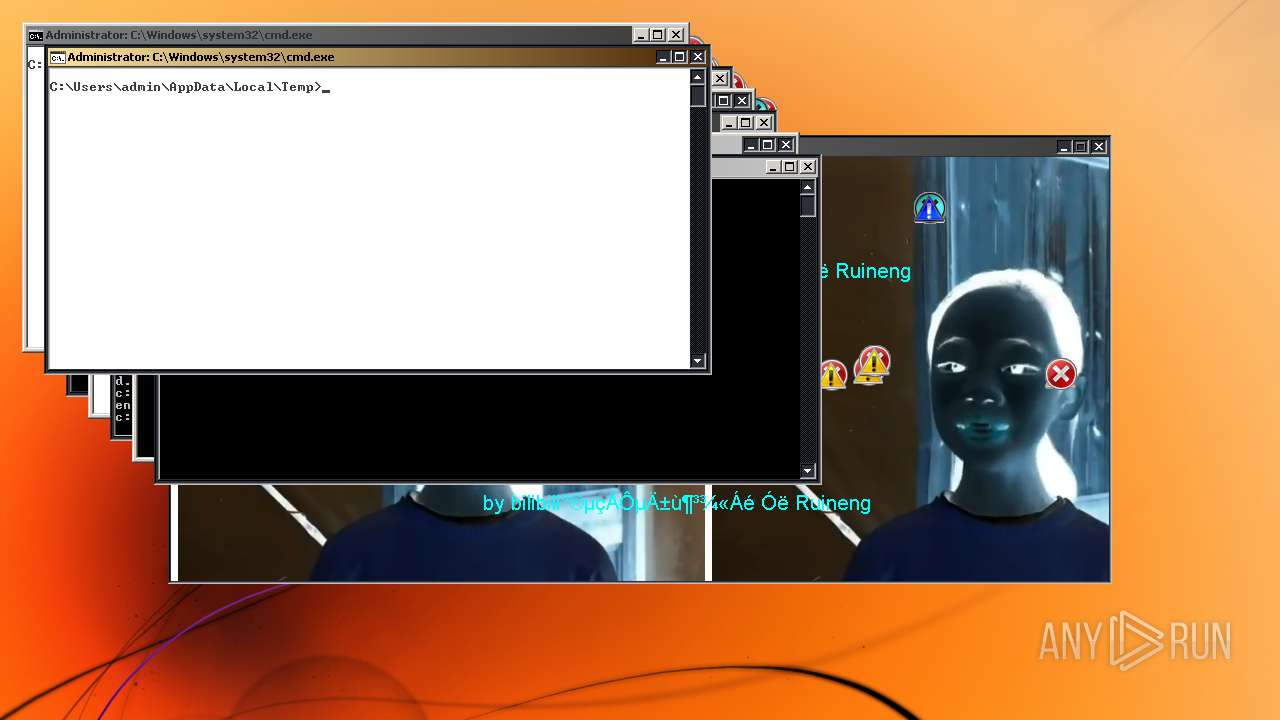
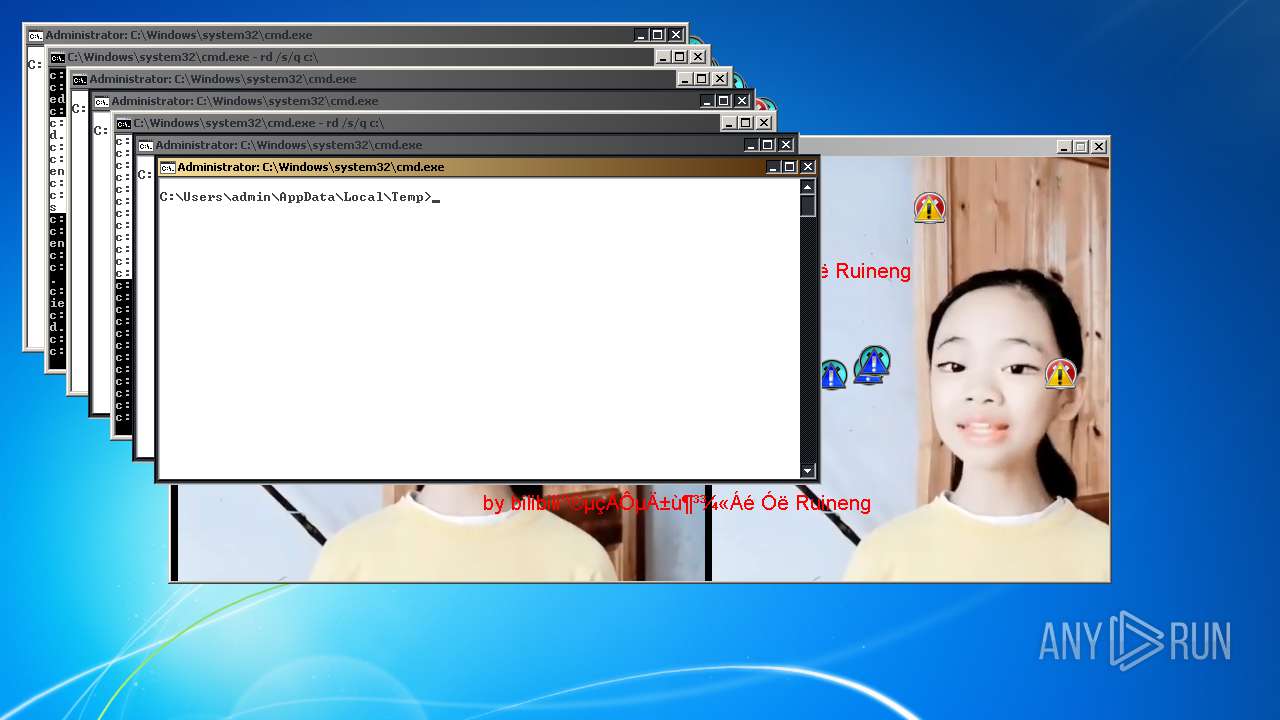
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 07:41:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | AB41F8D4DCEF49BA87D3ADDF23E7C6D8 |
| SHA1: | CA5E1C50B22C28ED9DE3AA985AC8C9B953E3F1E4 |
| SHA256: | 5929BB13747A0F1D6127F061F394C6005799A1B30B1429F66AB22BA1B0EF9167 |
| SSDEEP: | 98304:n5015501jNRRlmenpwdpQPSv6+4nO1FRSAwLvJLVBTwA5zCY7LNCkJXDg2:5OPOB5KvHKOoT5zJX02 |
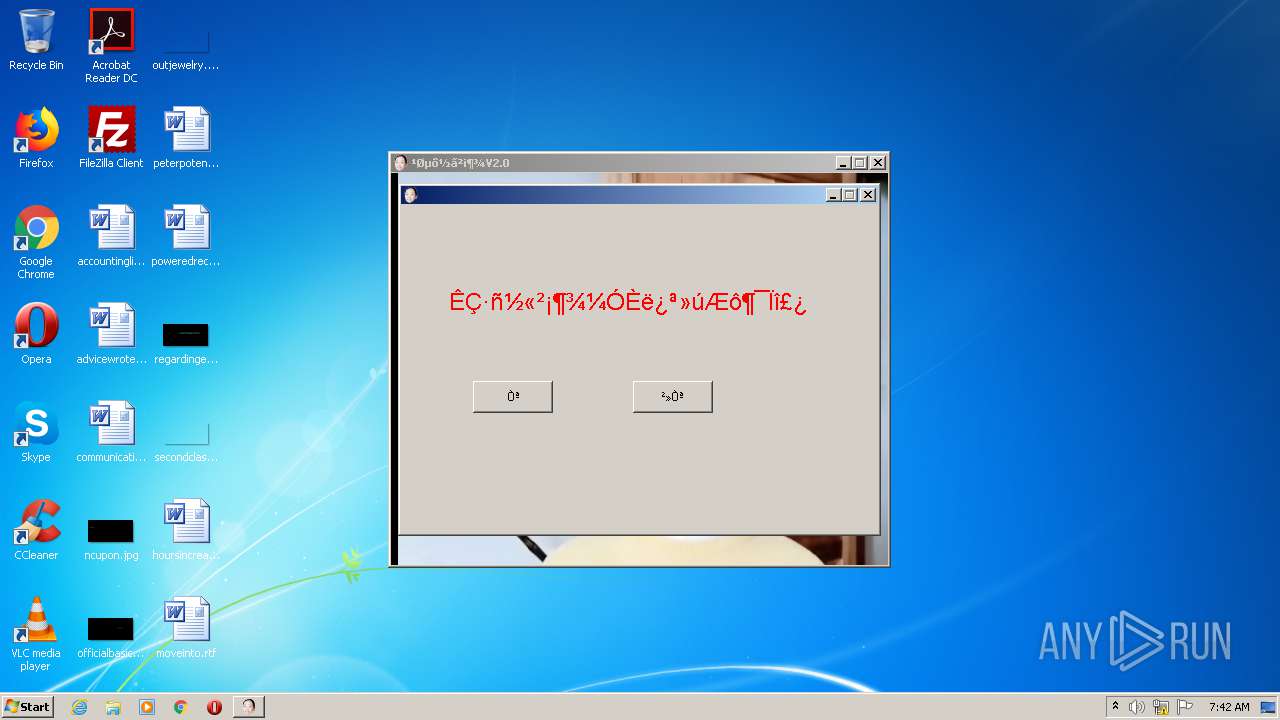
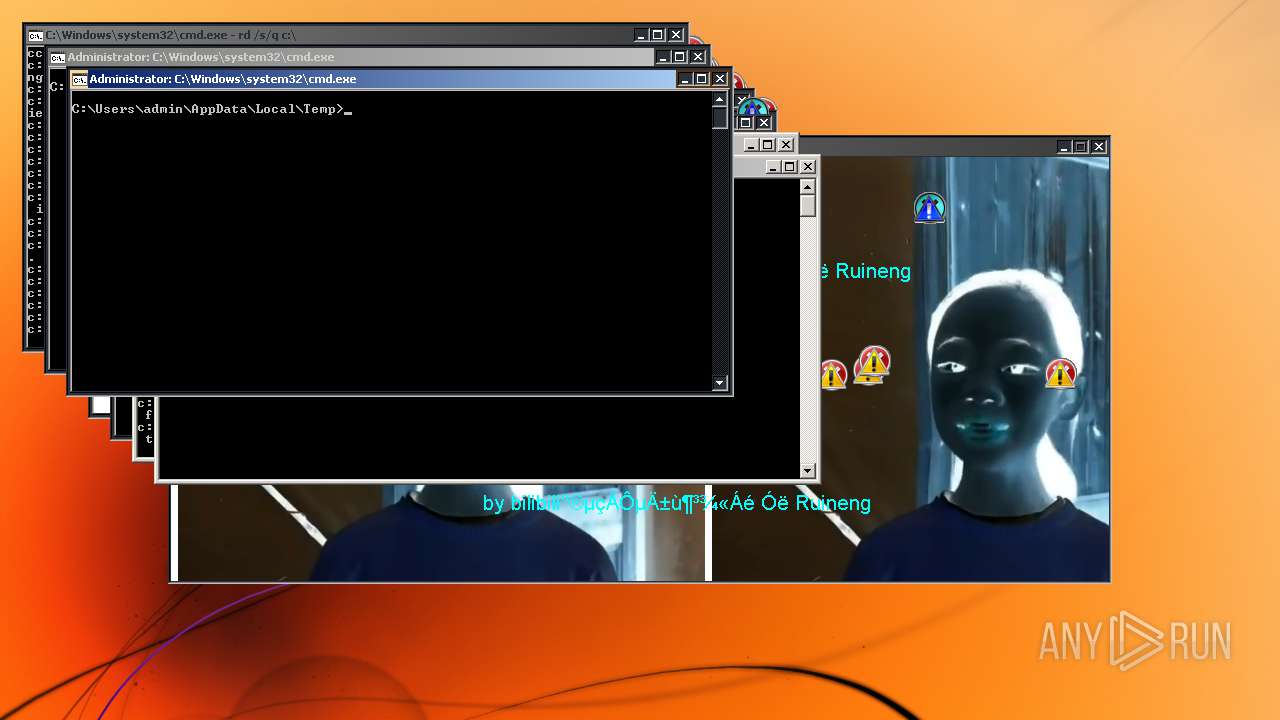
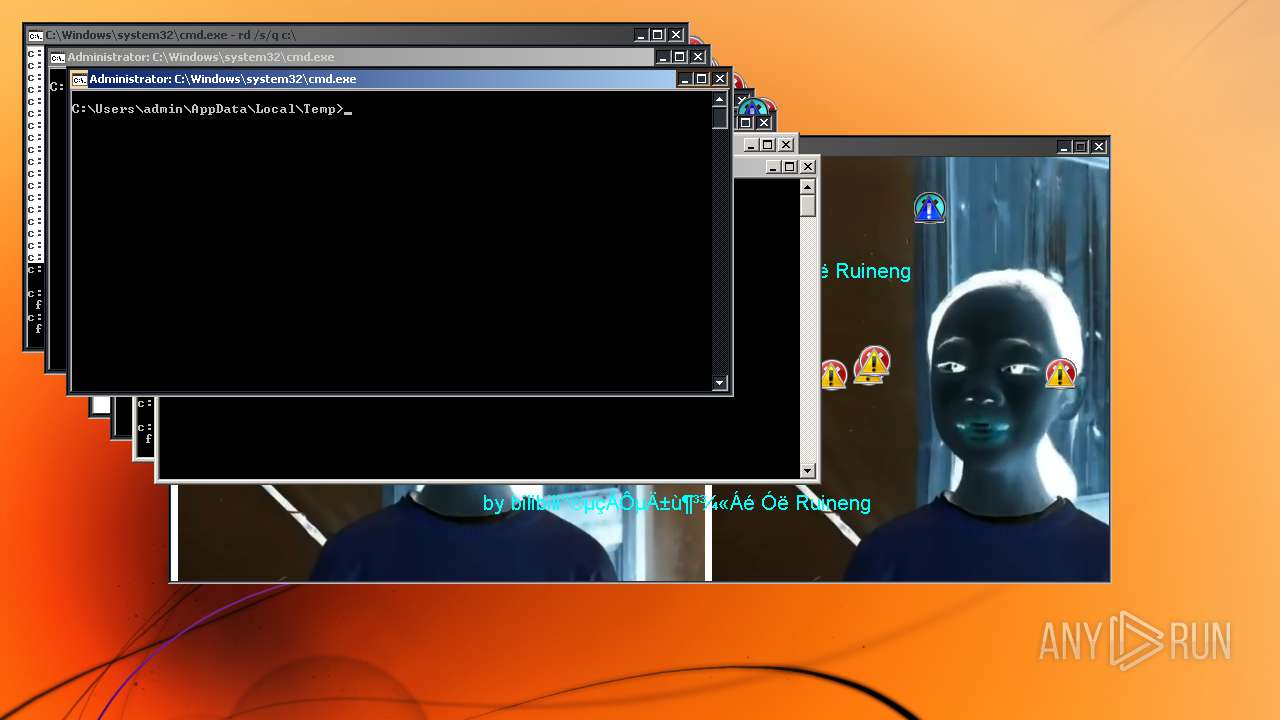
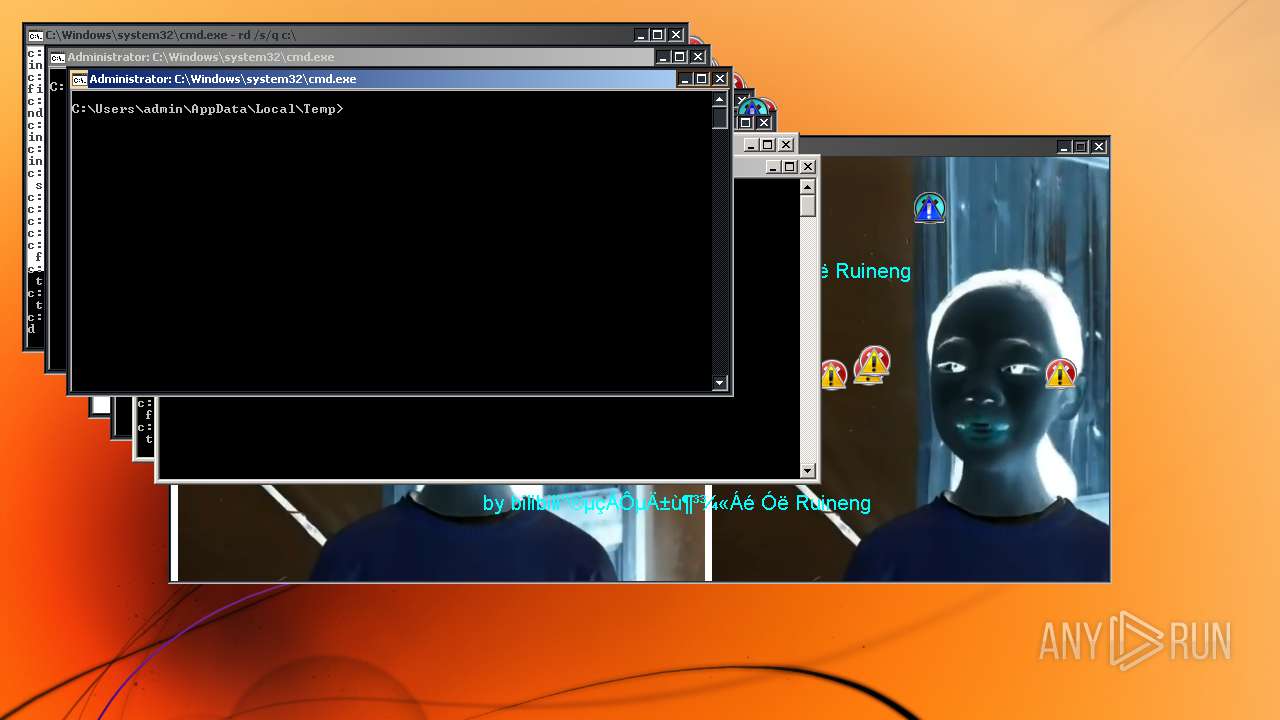
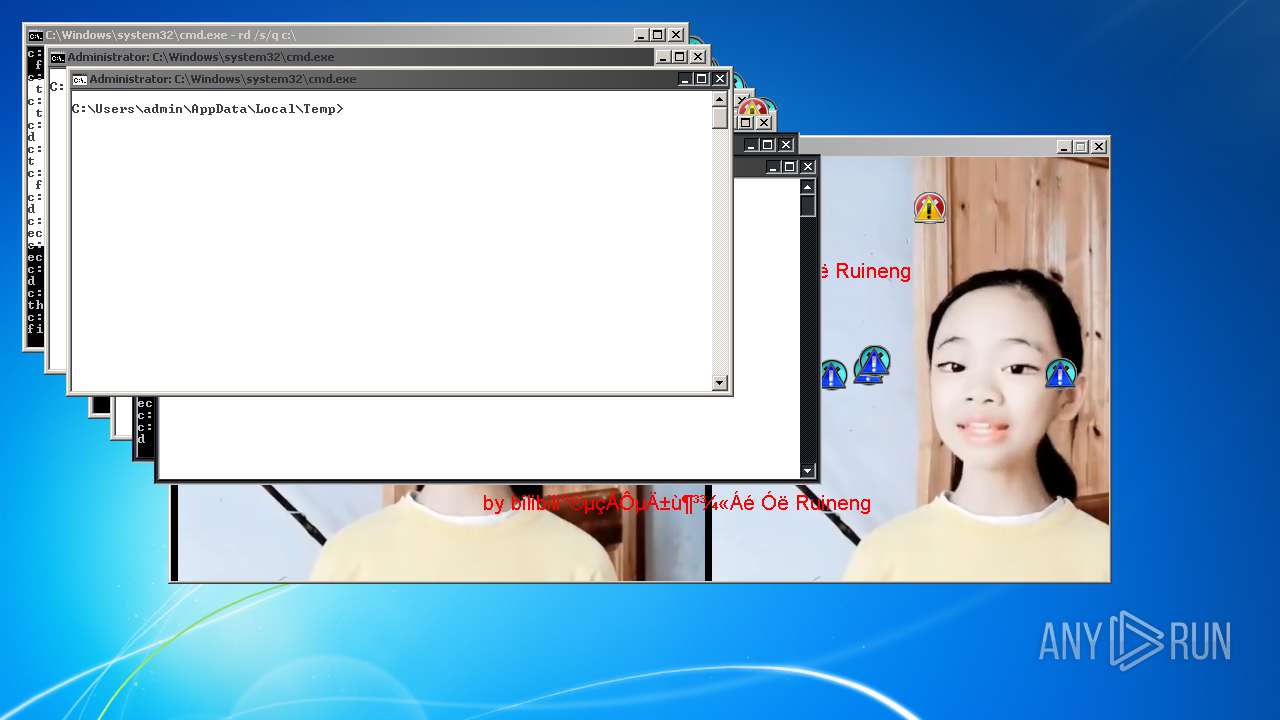
MALICIOUS
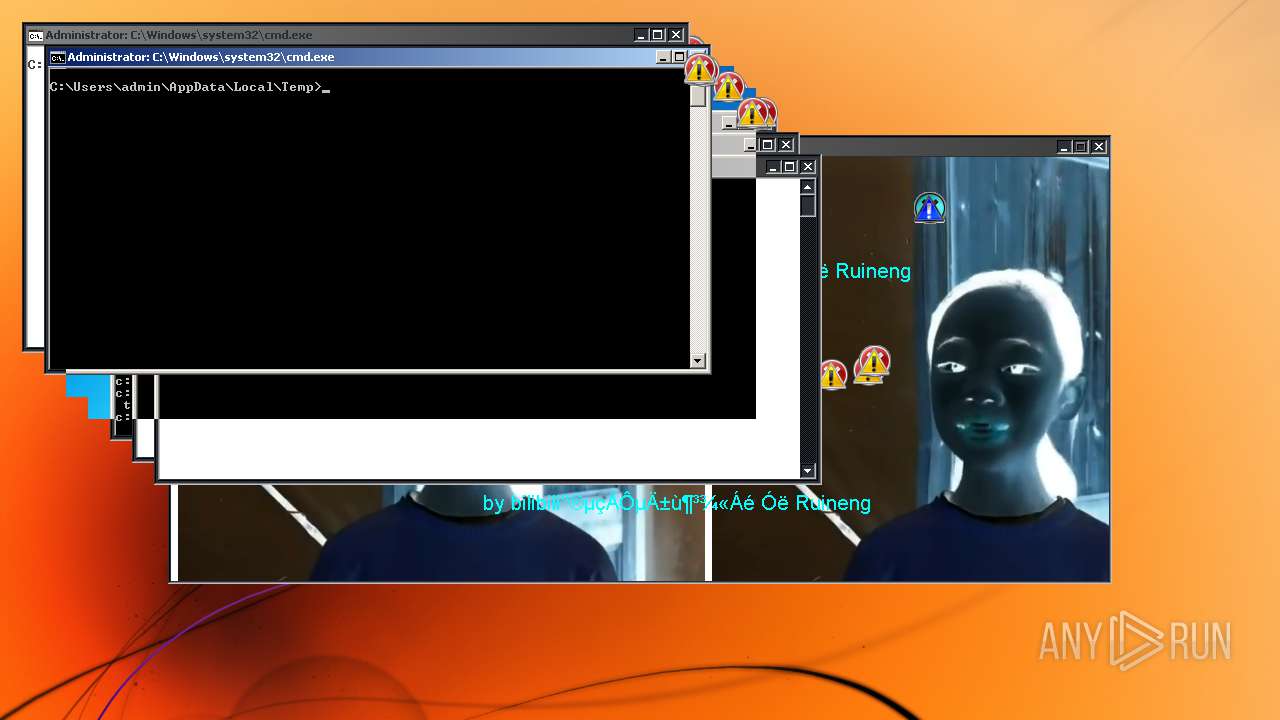
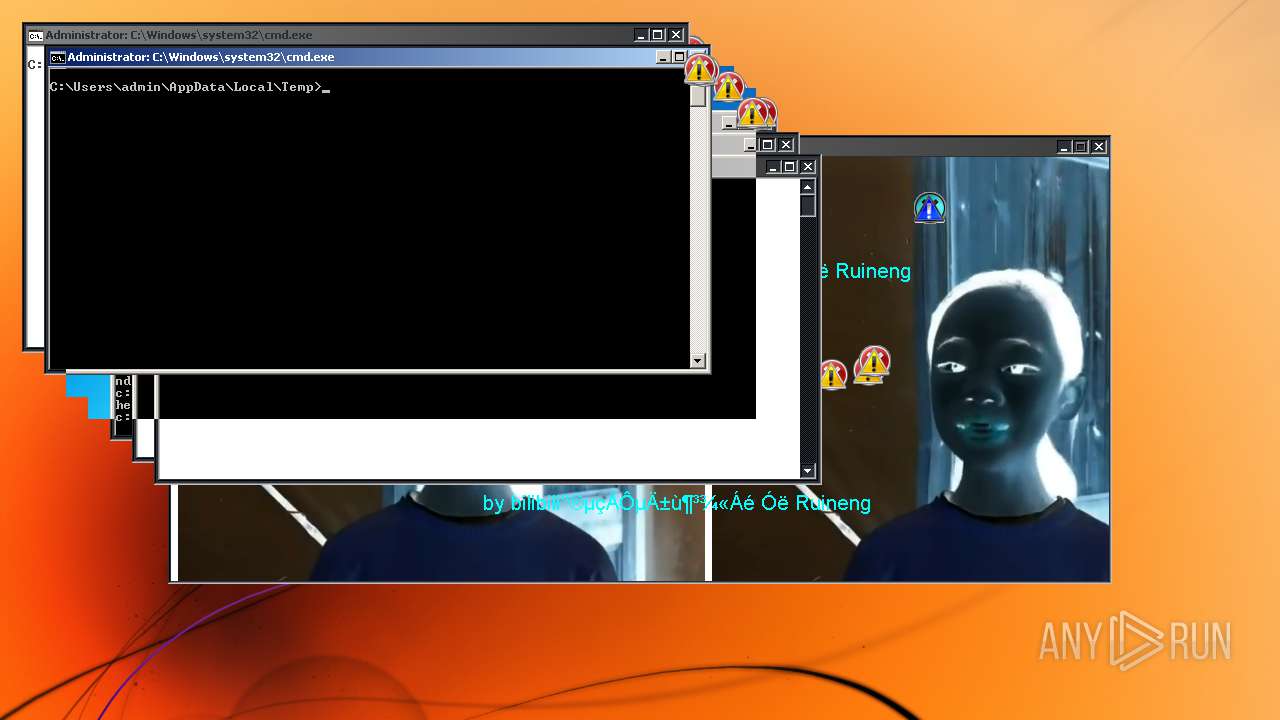
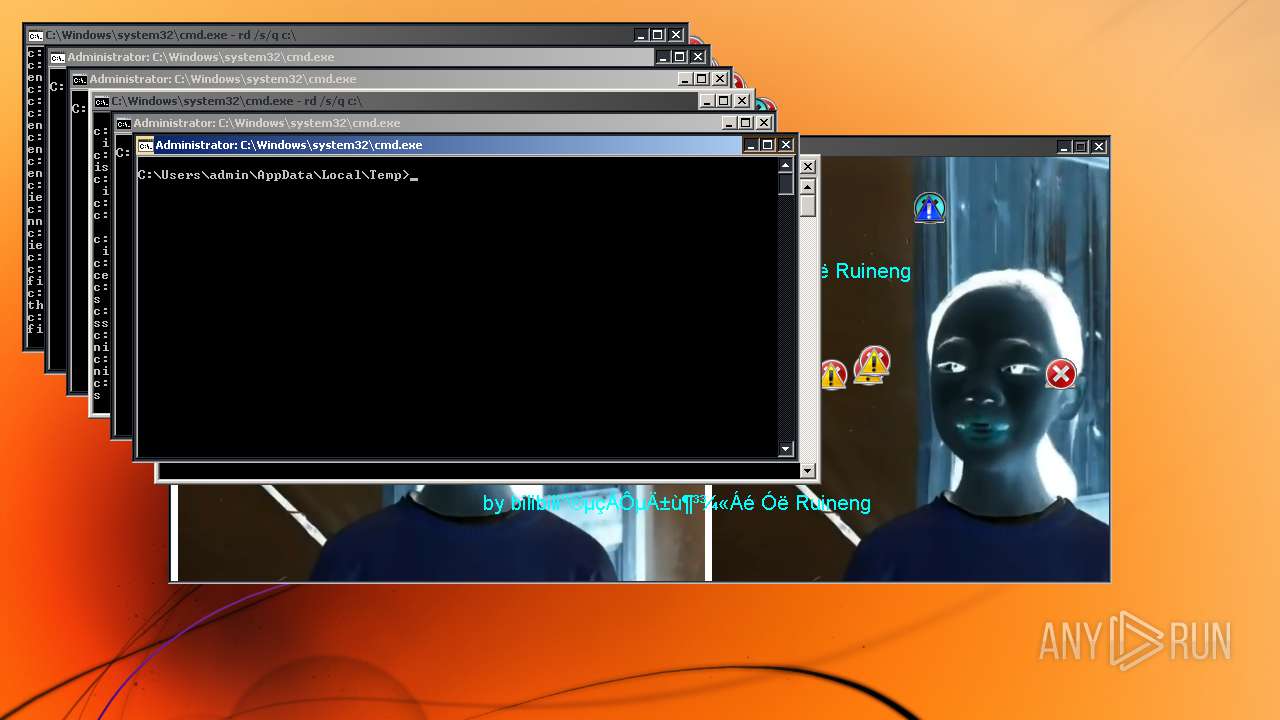
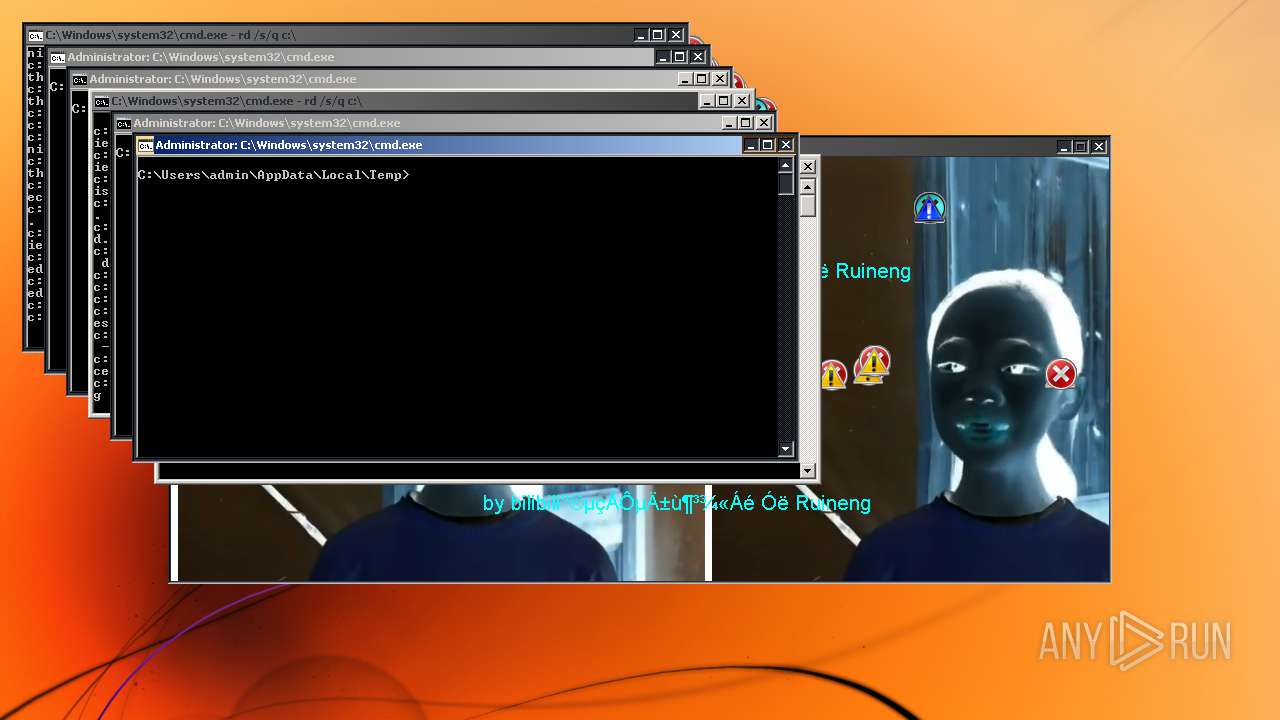
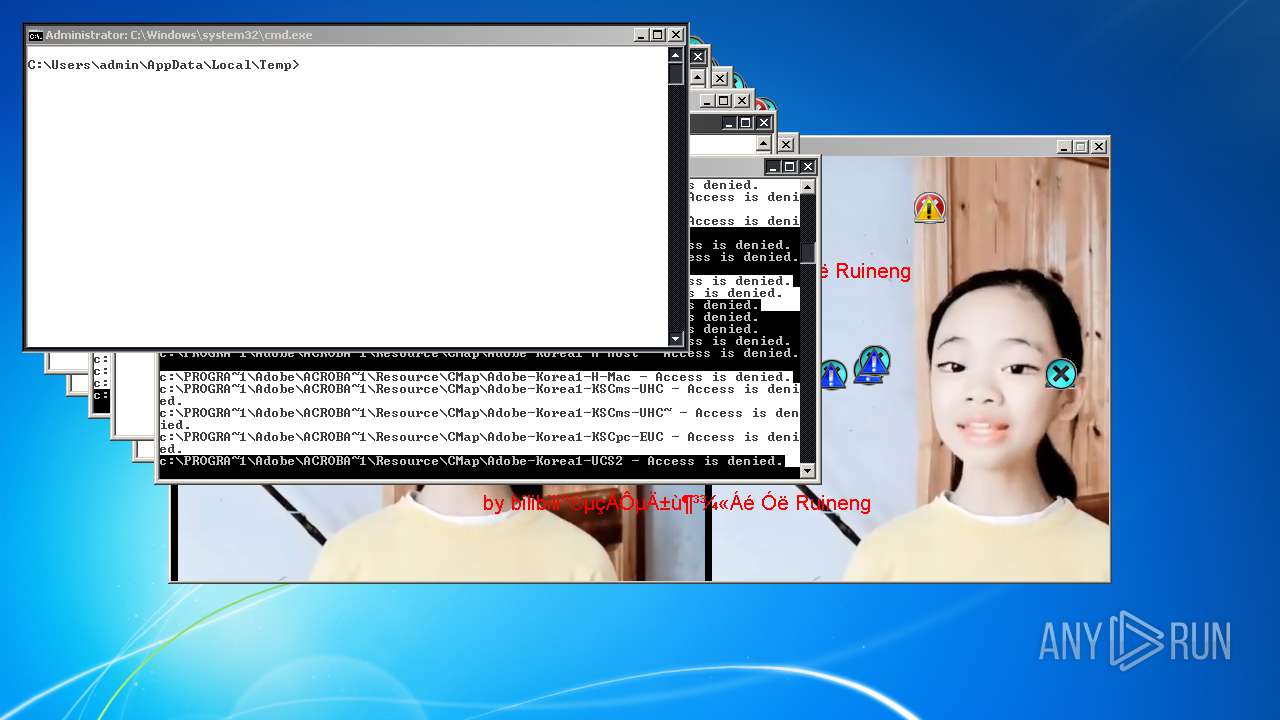
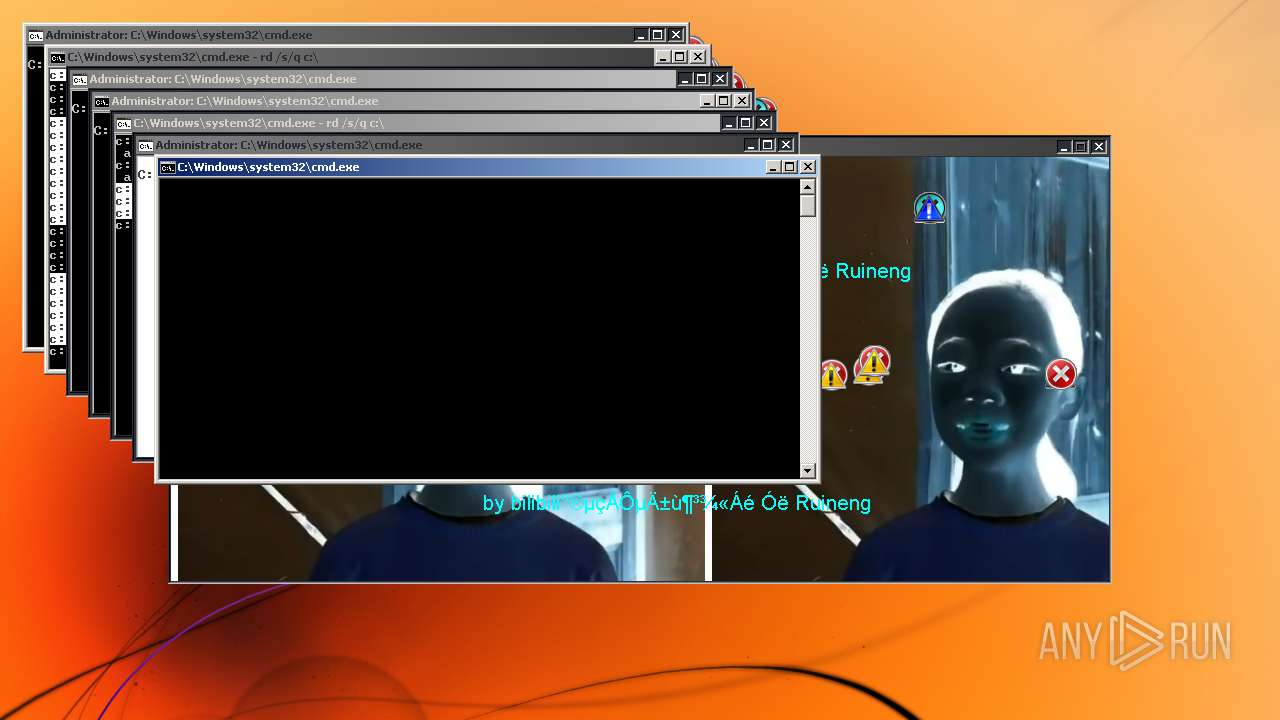
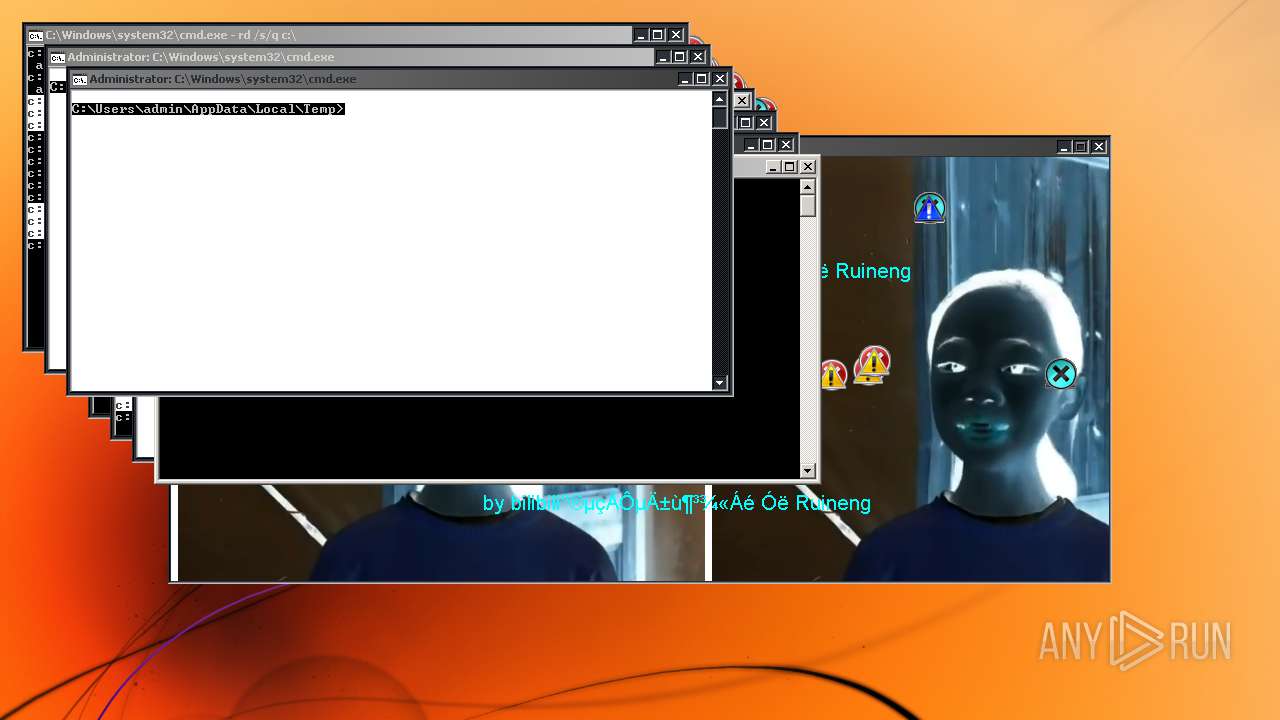
Drops executable file immediately after starts
- ab41f8d4dcef49ba87d3addf23e7c6d8.exe (PID: 2688)
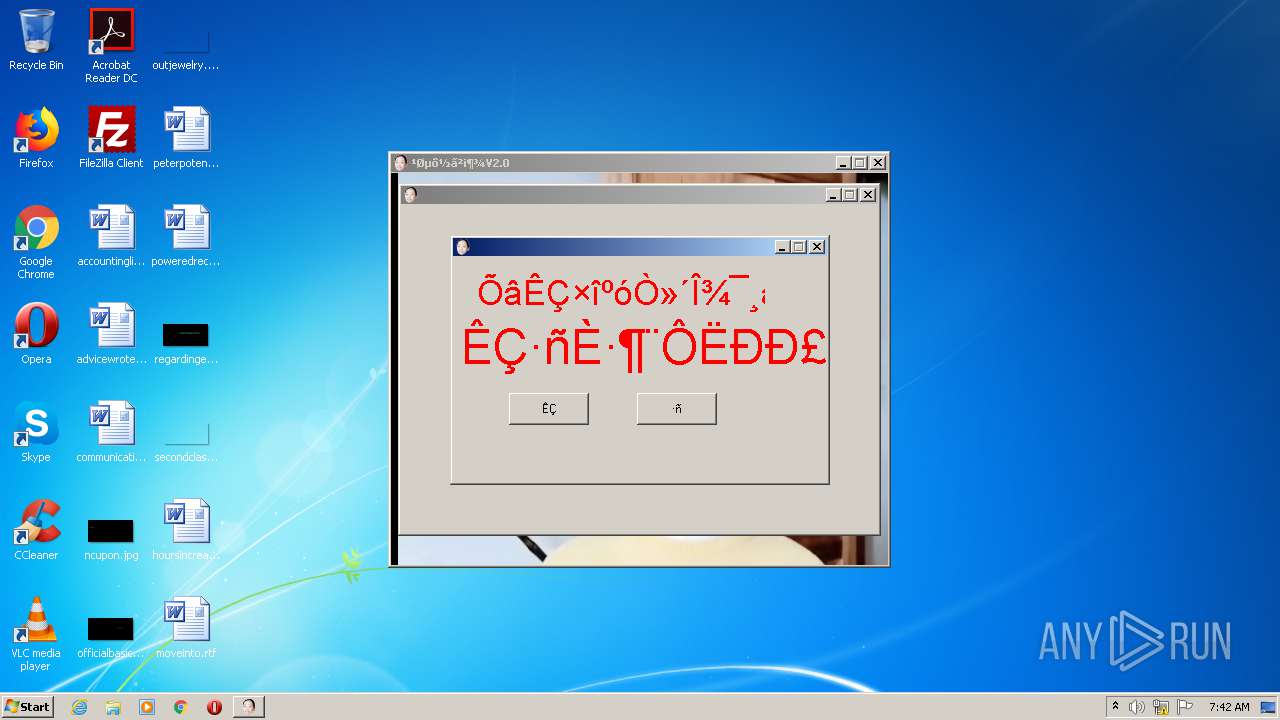
Disables the Run in Start menu
- ab41f8d4dcef49ba87d3addf23e7c6d8.exe (PID: 2688)
Disables registry editing tools (regedit)
- ab41f8d4dcef49ba87d3addf23e7c6d8.exe (PID: 2688)
Task Manager has been disabled (taskmgr)
- ab41f8d4dcef49ba87d3addf23e7c6d8.exe (PID: 2688)
Disables the Find in Start menu
- ab41f8d4dcef49ba87d3addf23e7c6d8.exe (PID: 2688)
Deletes the SafeBoot registry key
- ab41f8d4dcef49ba87d3addf23e7c6d8.exe (PID: 2688)
Disables the Shutdown in Start menu
- ab41f8d4dcef49ba87d3addf23e7c6d8.exe (PID: 2688)
Disables the LogOff in Start menu
- ab41f8d4dcef49ba87d3addf23e7c6d8.exe (PID: 2688)
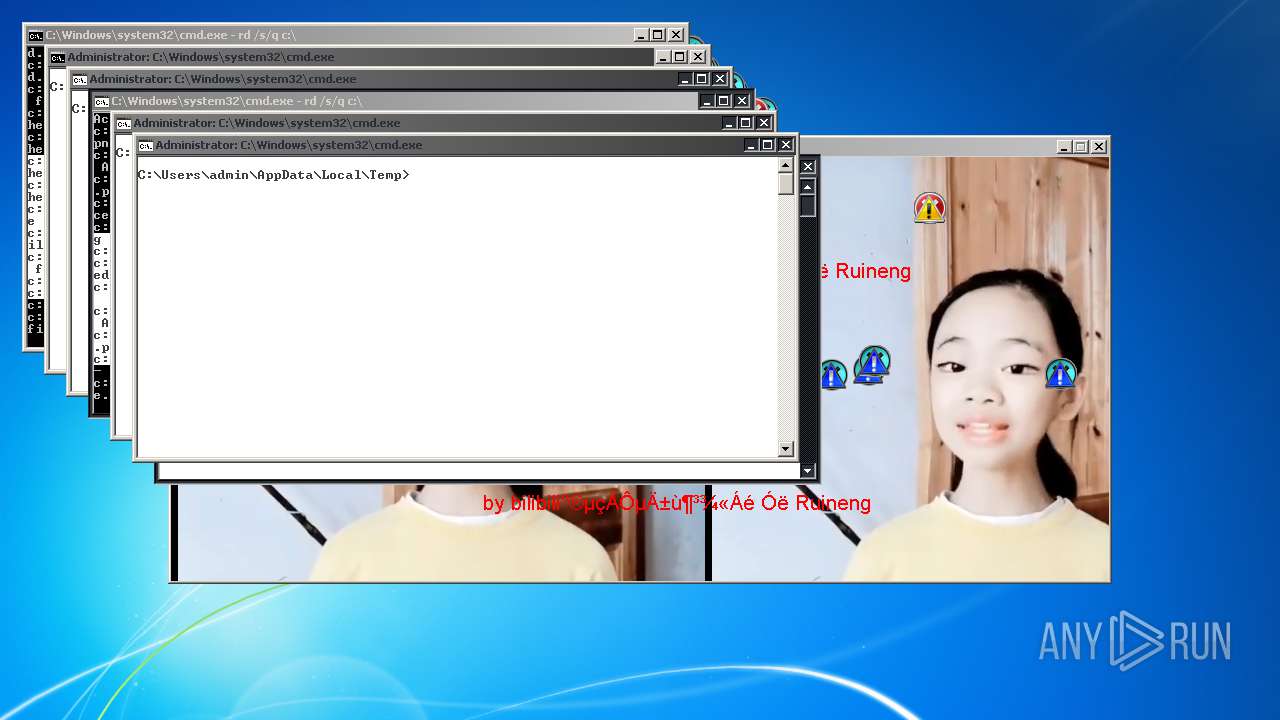
Changes appearance of the explorer extensions
- ab41f8d4dcef49ba87d3addf23e7c6d8.exe (PID: 2688)
Changes the autorun value in the registry
- ab41f8d4dcef49ba87d3addf23e7c6d8.exe (PID: 2688)
SUSPICIOUS
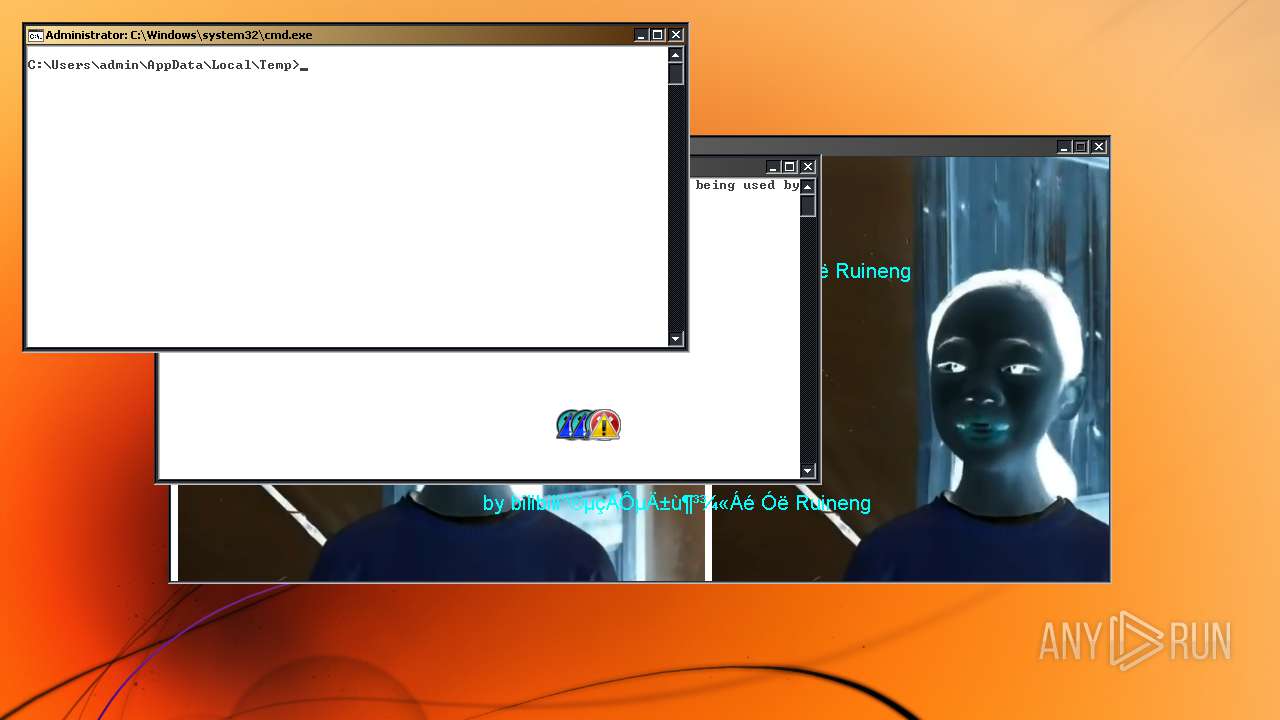
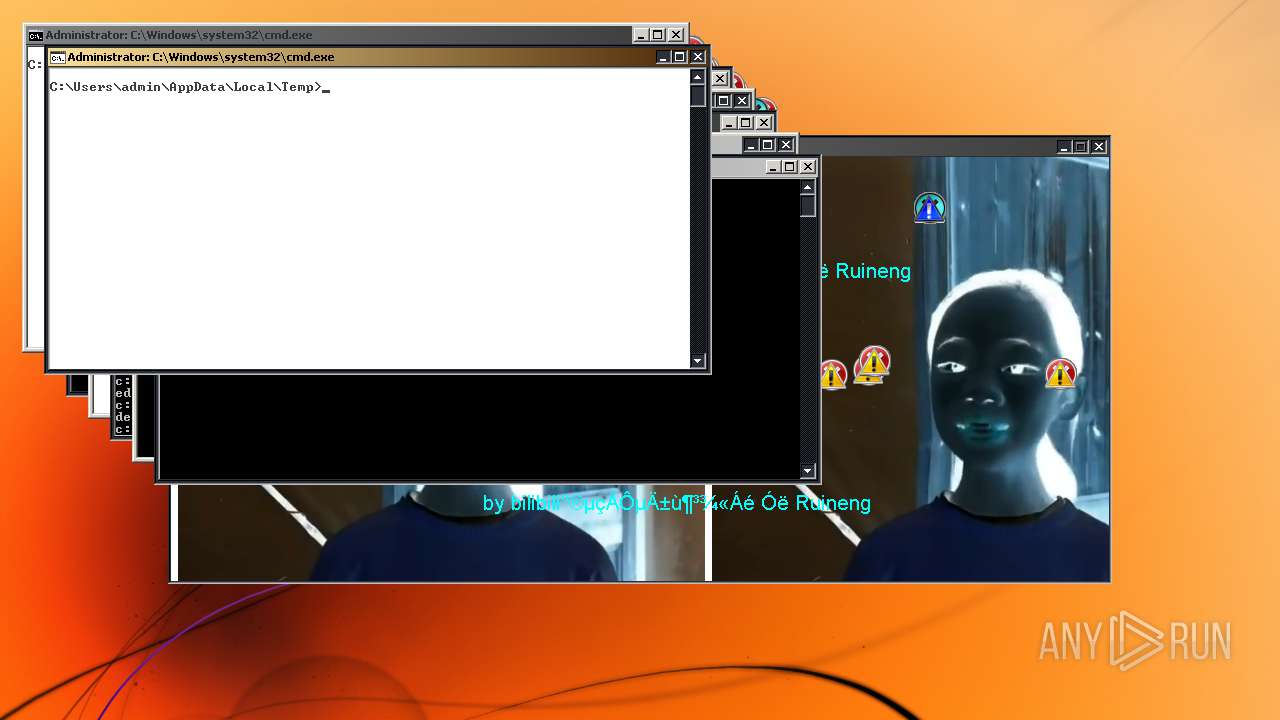
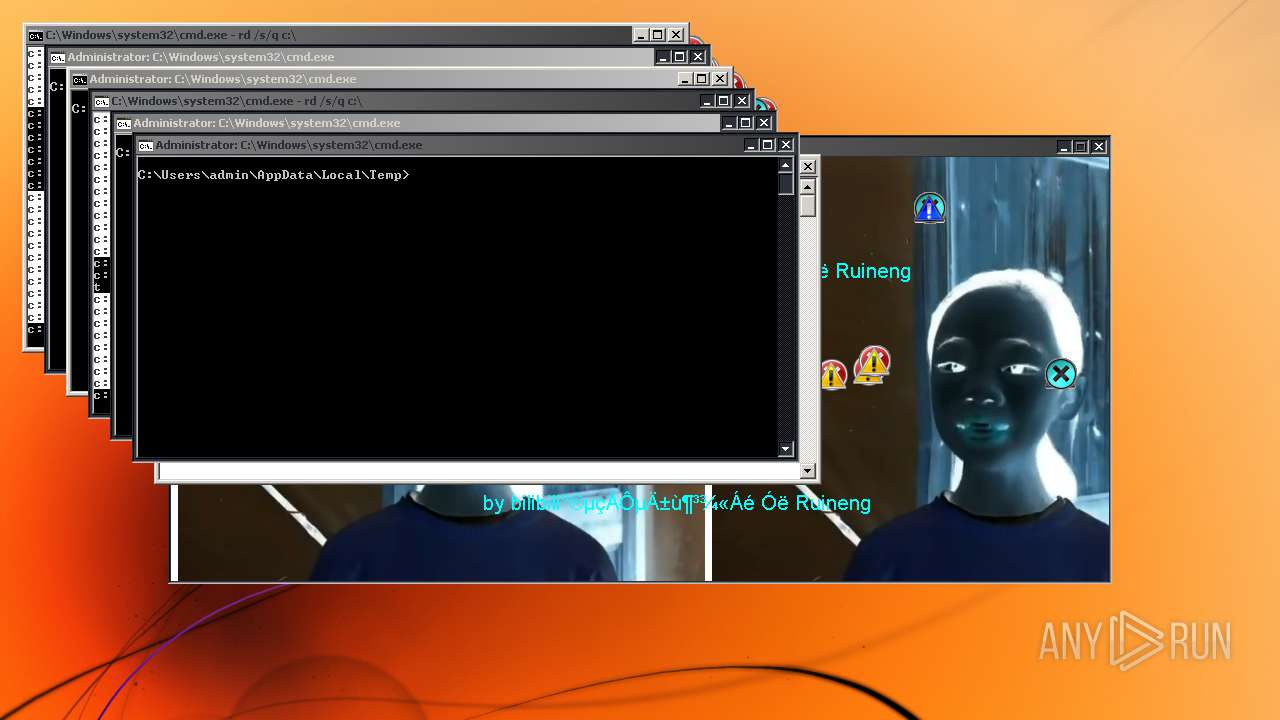
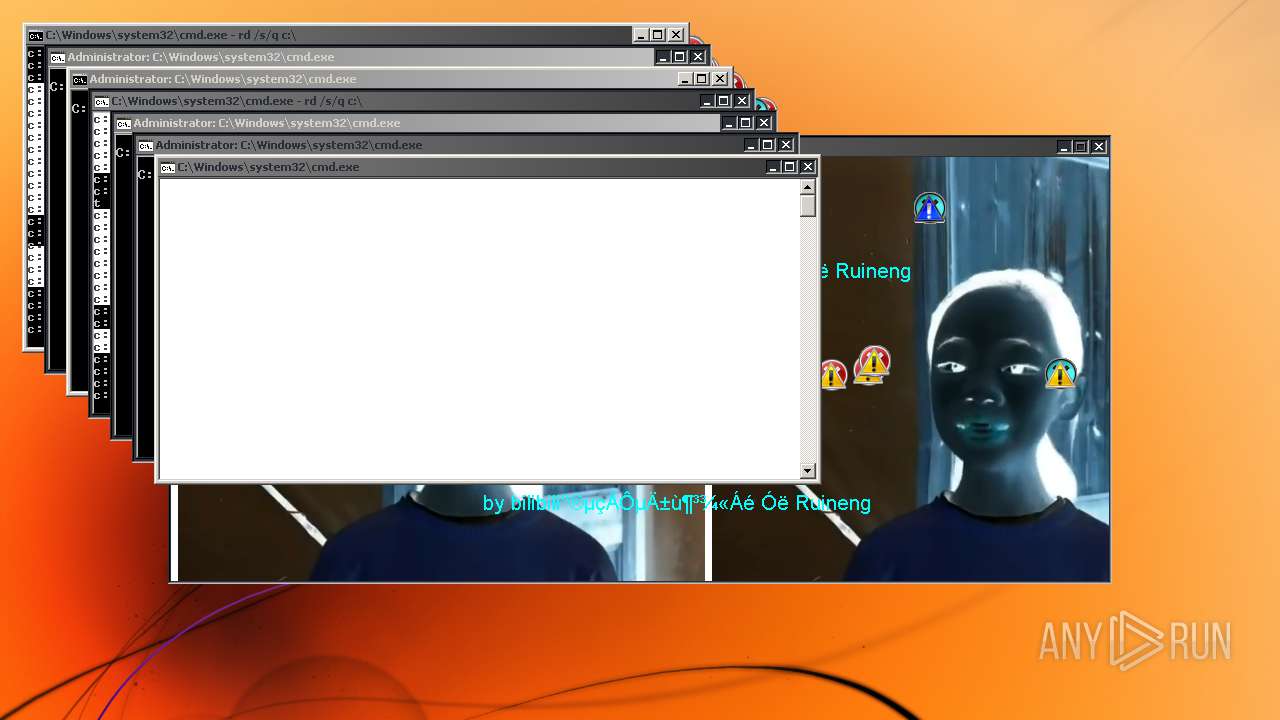
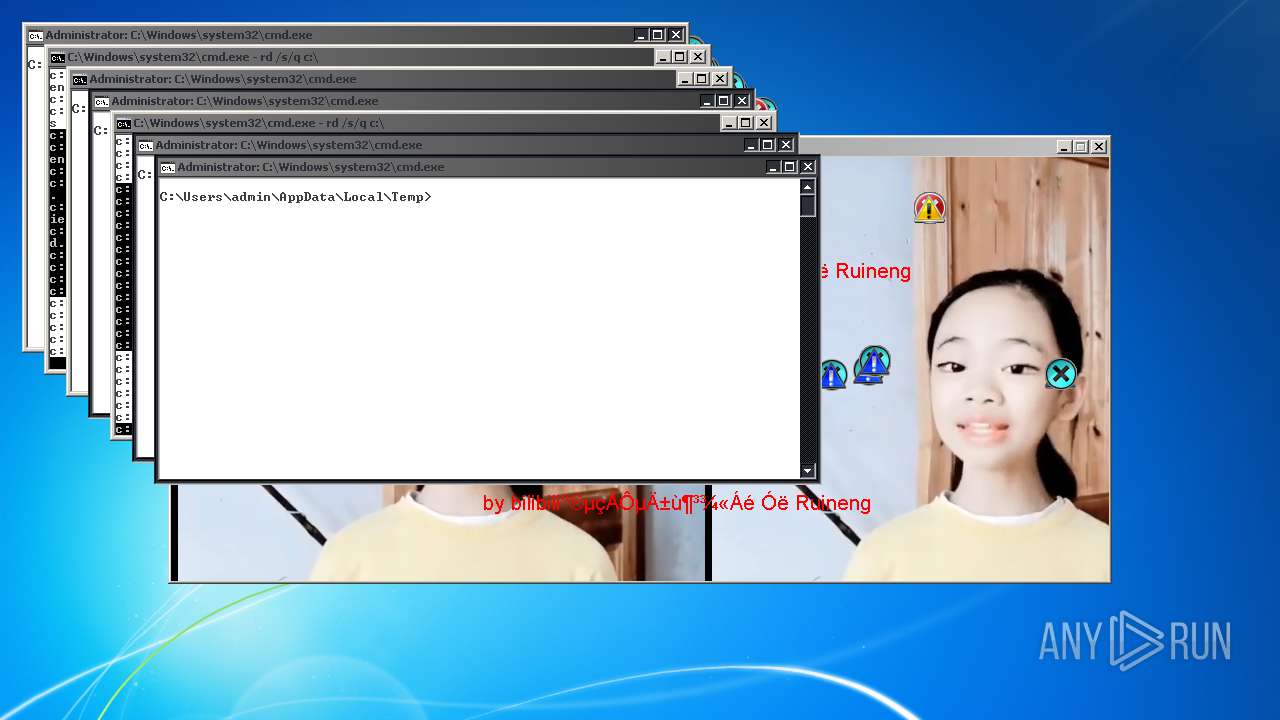
Uses TASKKILL.EXE to kill process
- ab41f8d4dcef49ba87d3addf23e7c6d8.exe (PID: 2688)
Drops a file with too old compile date
- ab41f8d4dcef49ba87d3addf23e7c6d8.exe (PID: 2688)
Executable content was dropped or overwritten
- ab41f8d4dcef49ba87d3addf23e7c6d8.exe (PID: 2688)
Executed as Windows Service
- SearchIndexer.exe (PID: 3652)
Creates files in the program directory
- SearchIndexer.exe (PID: 3652)
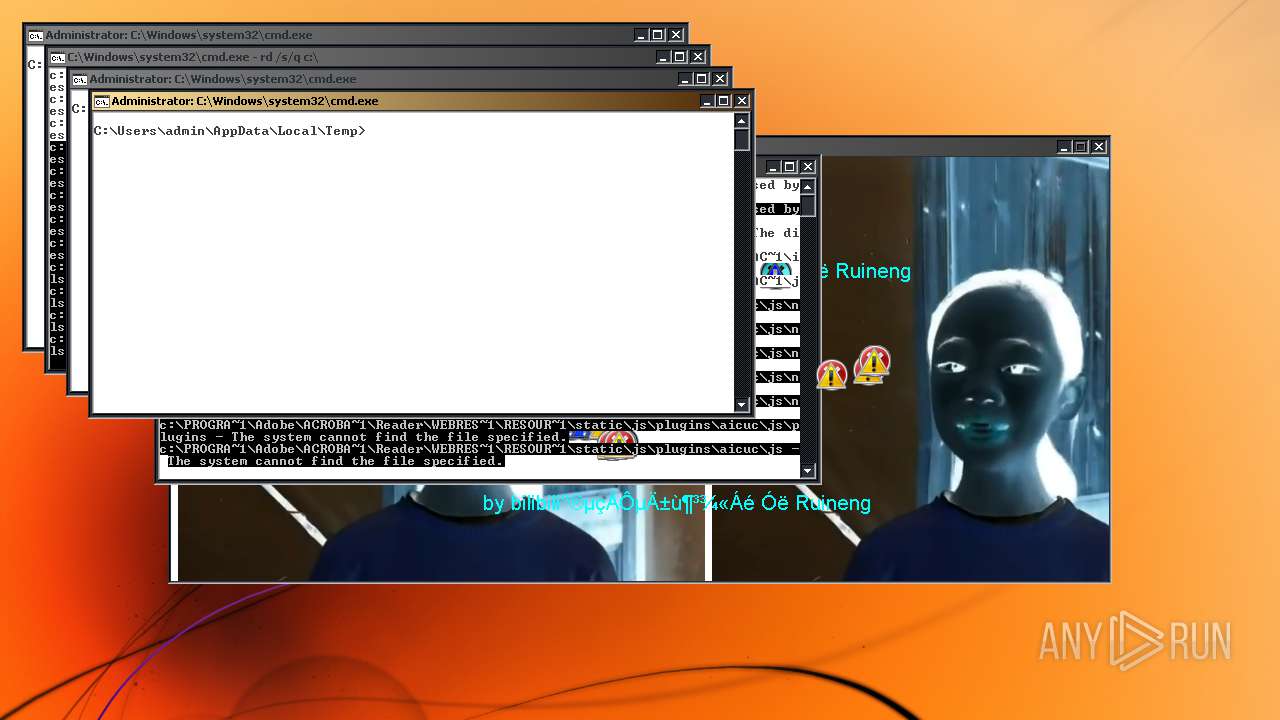
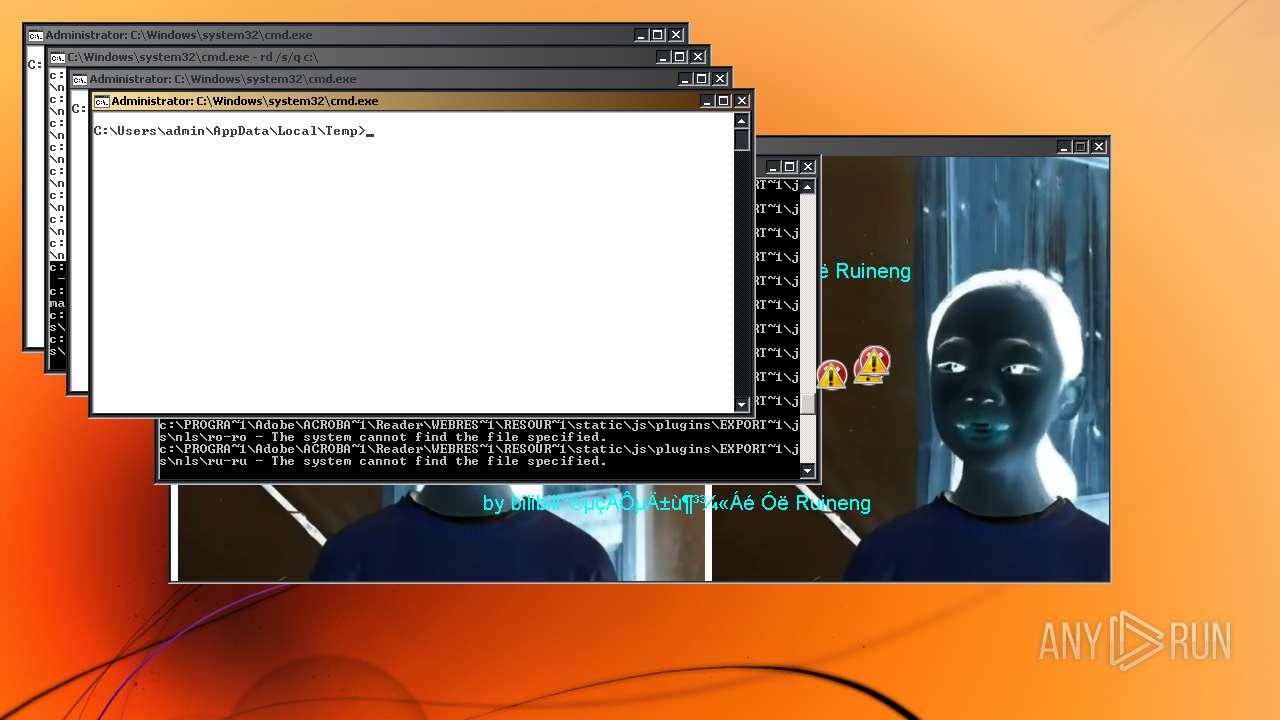
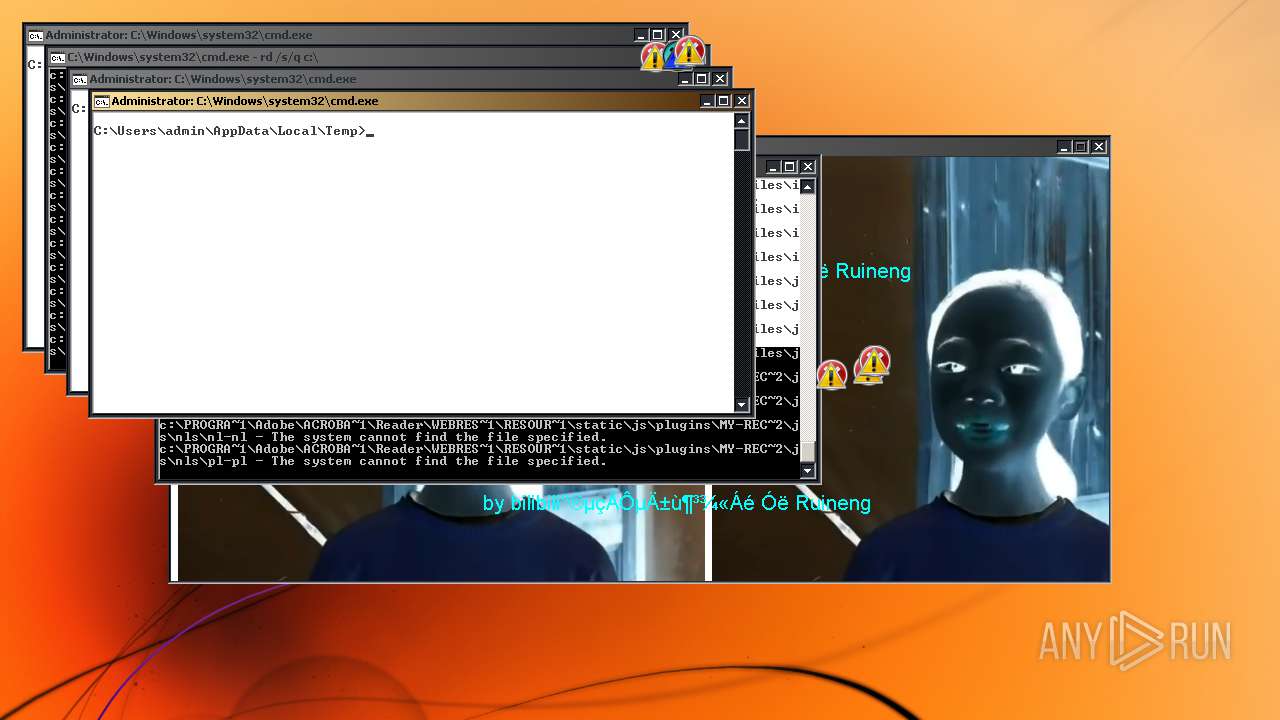
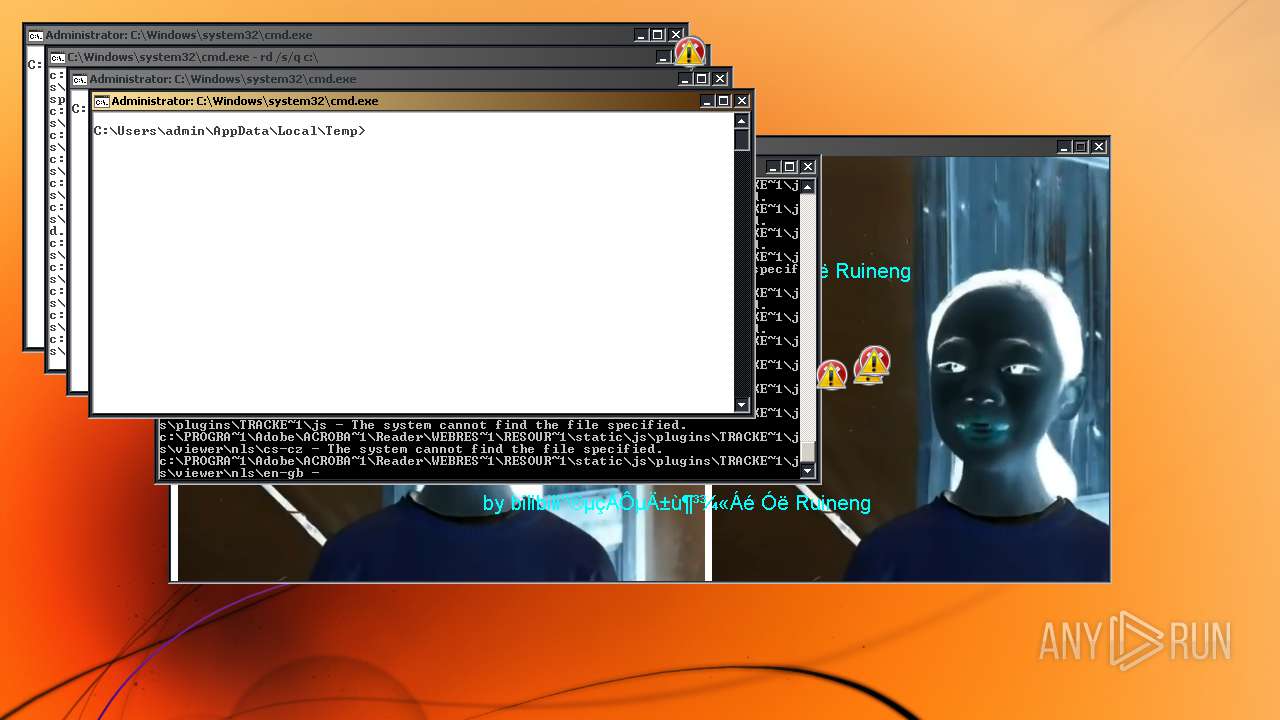
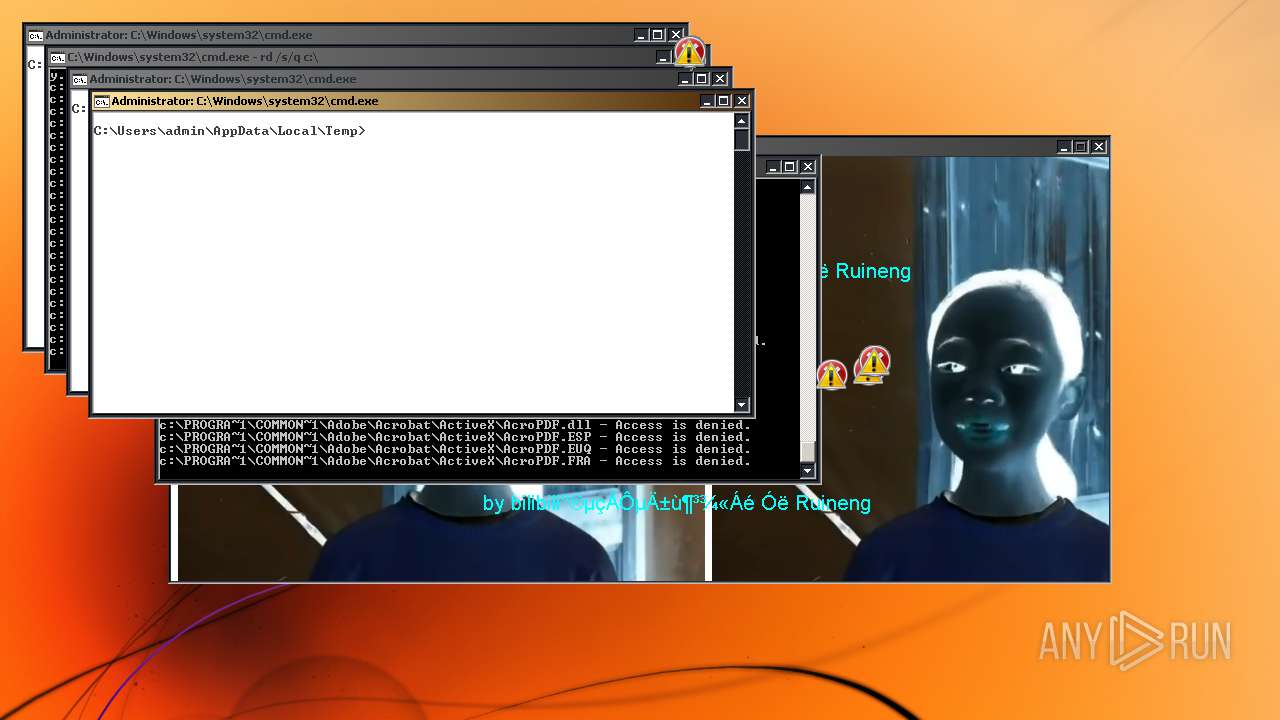
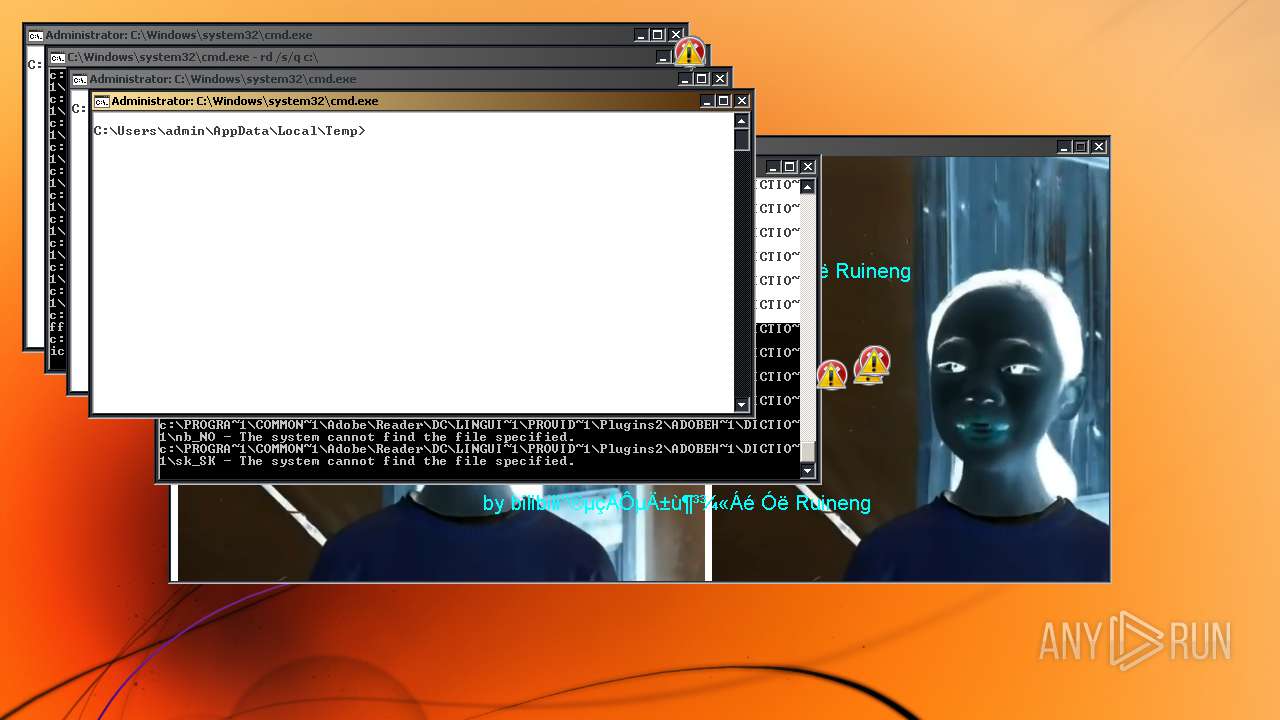
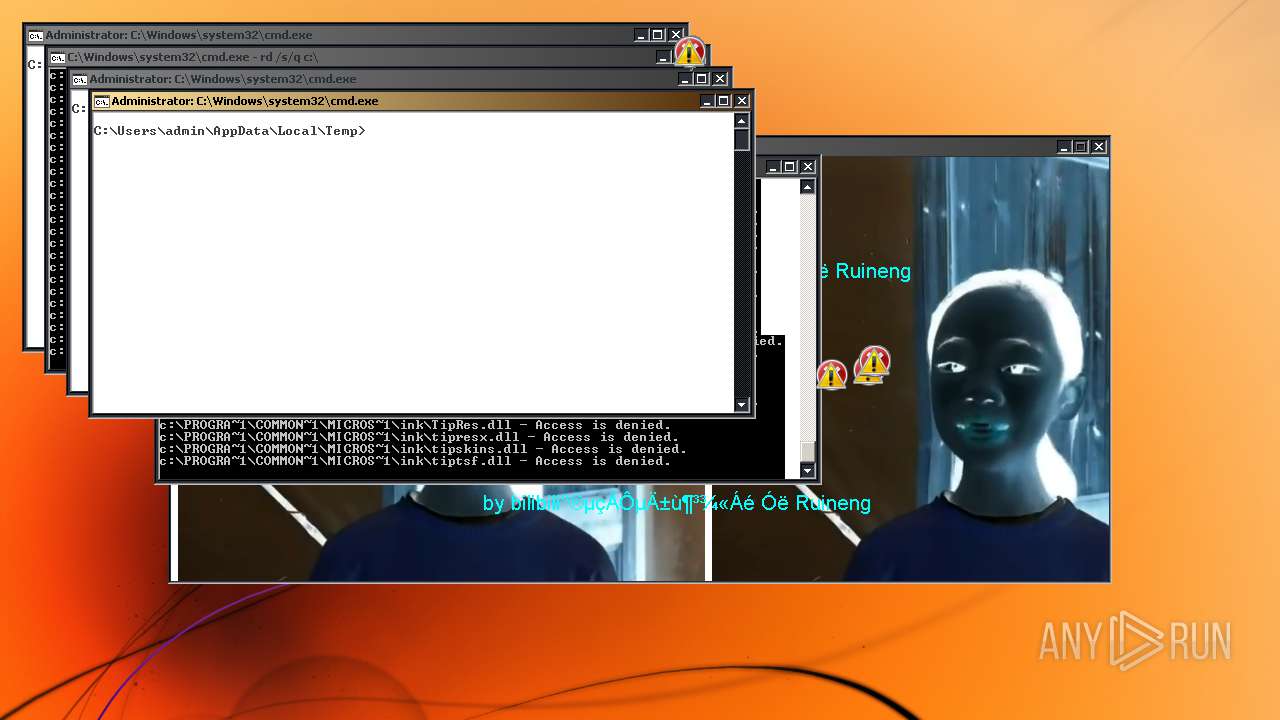
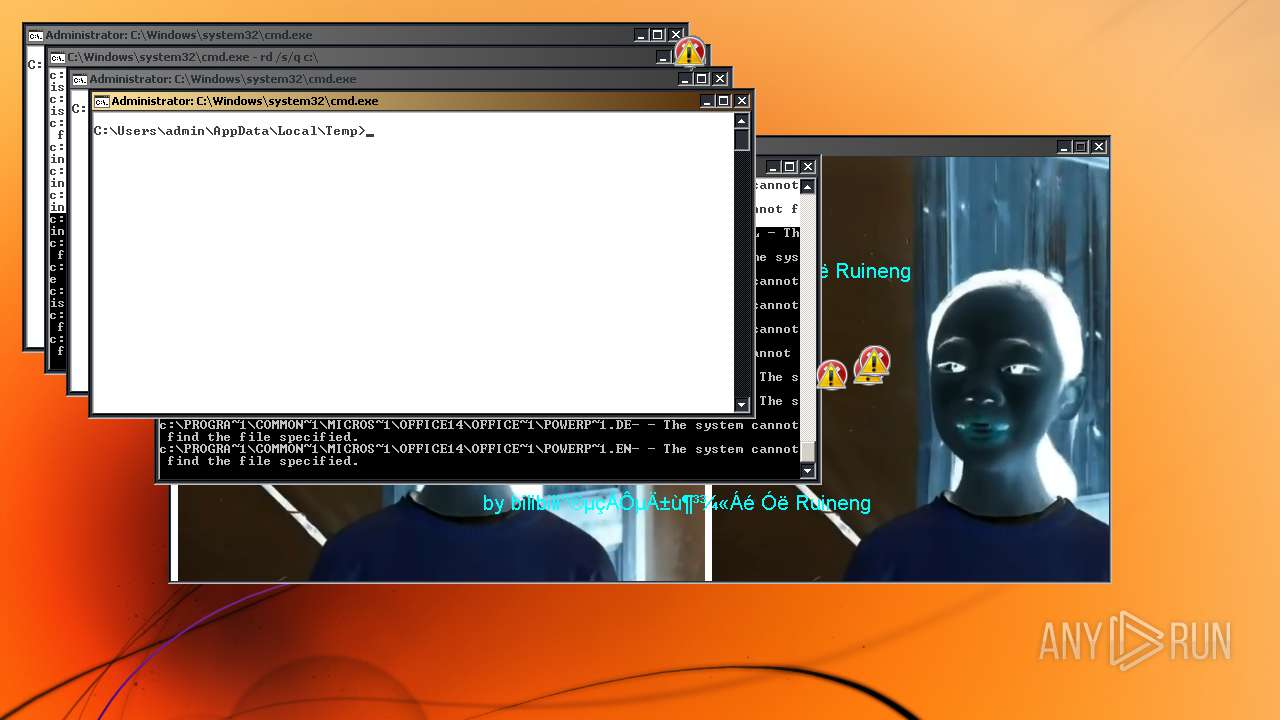
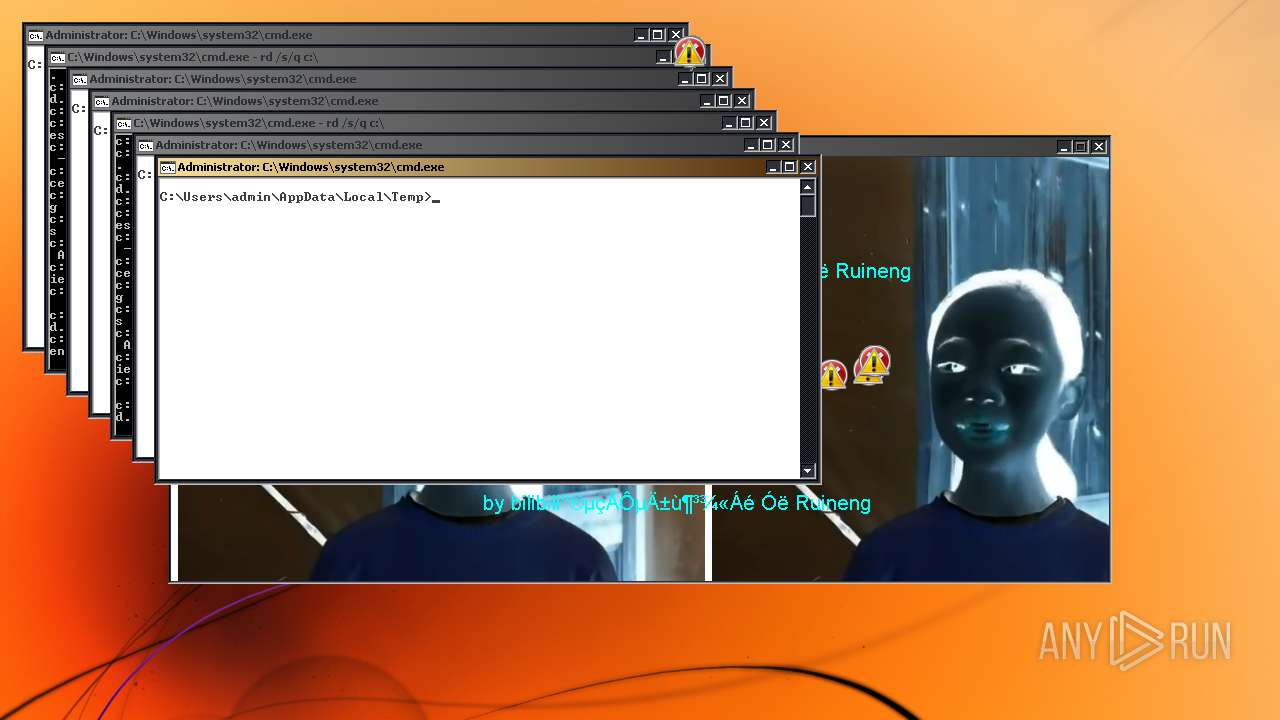
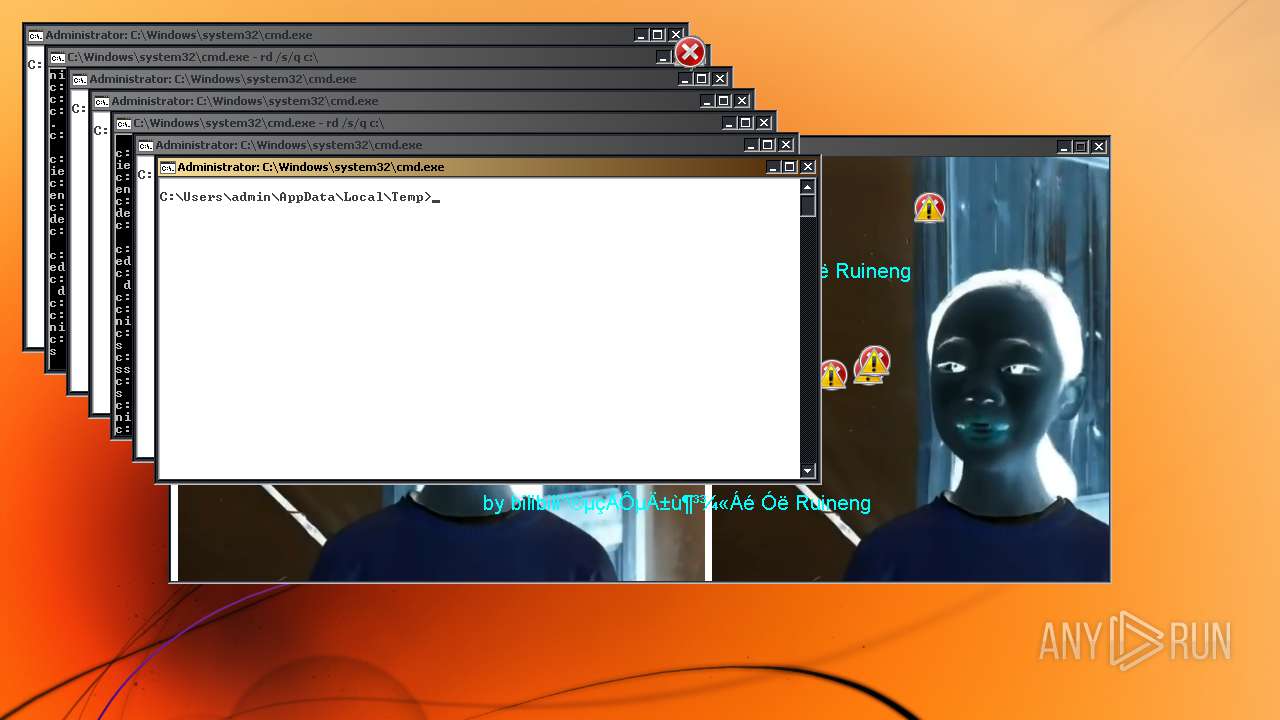
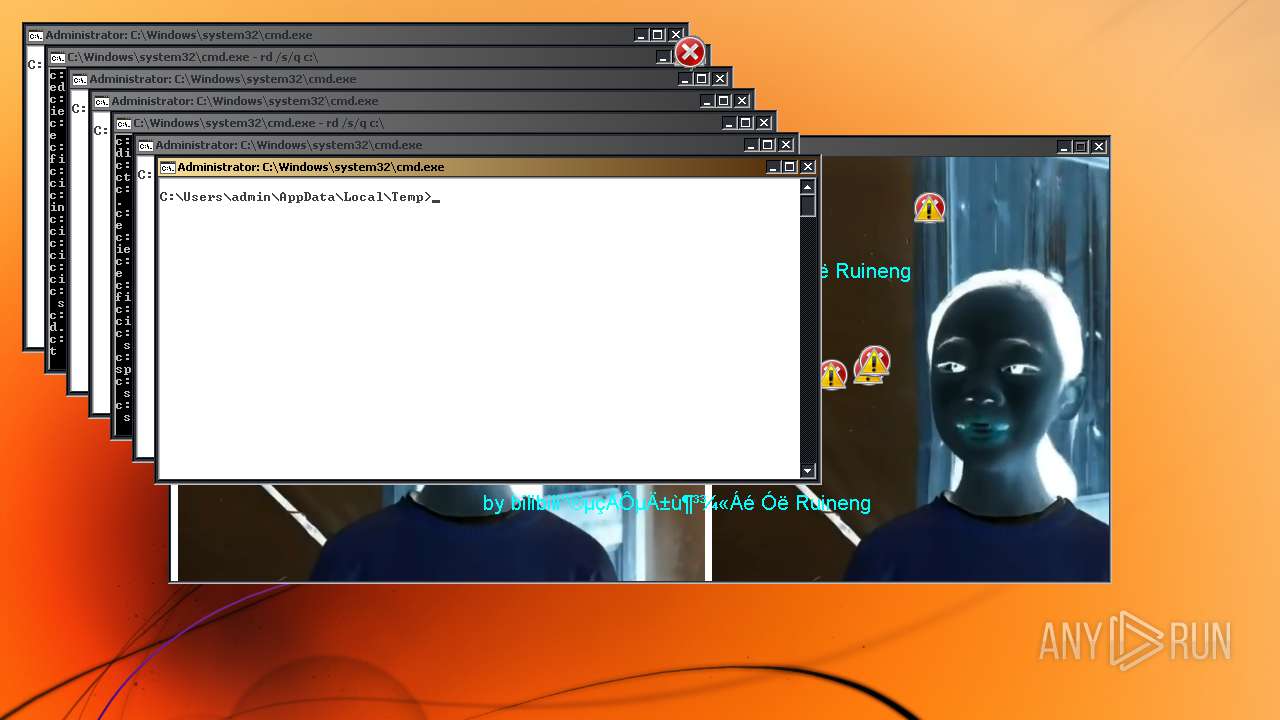
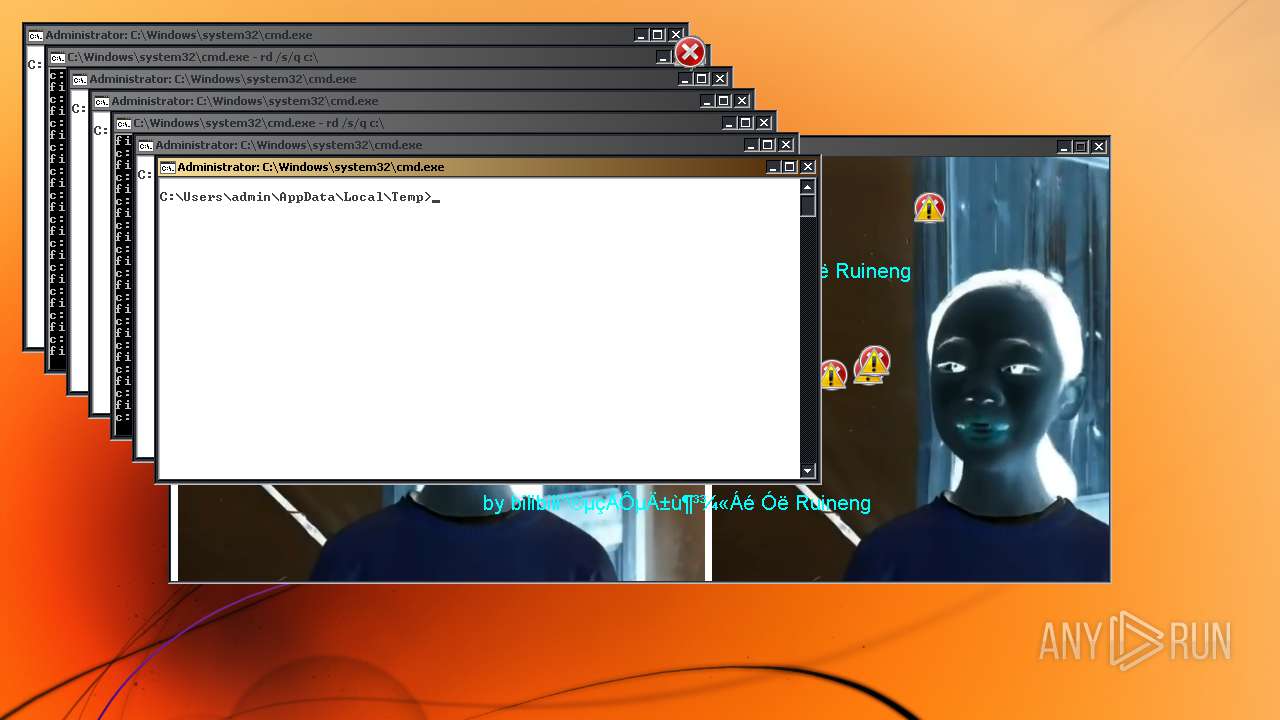
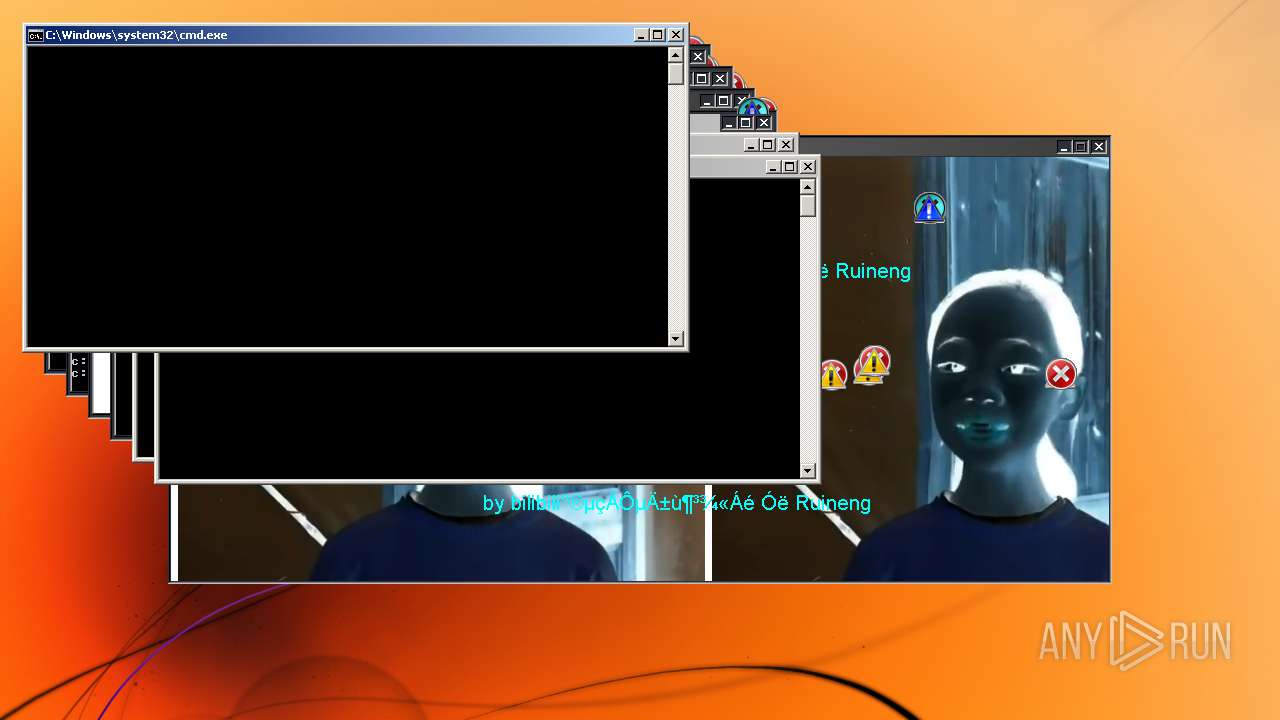
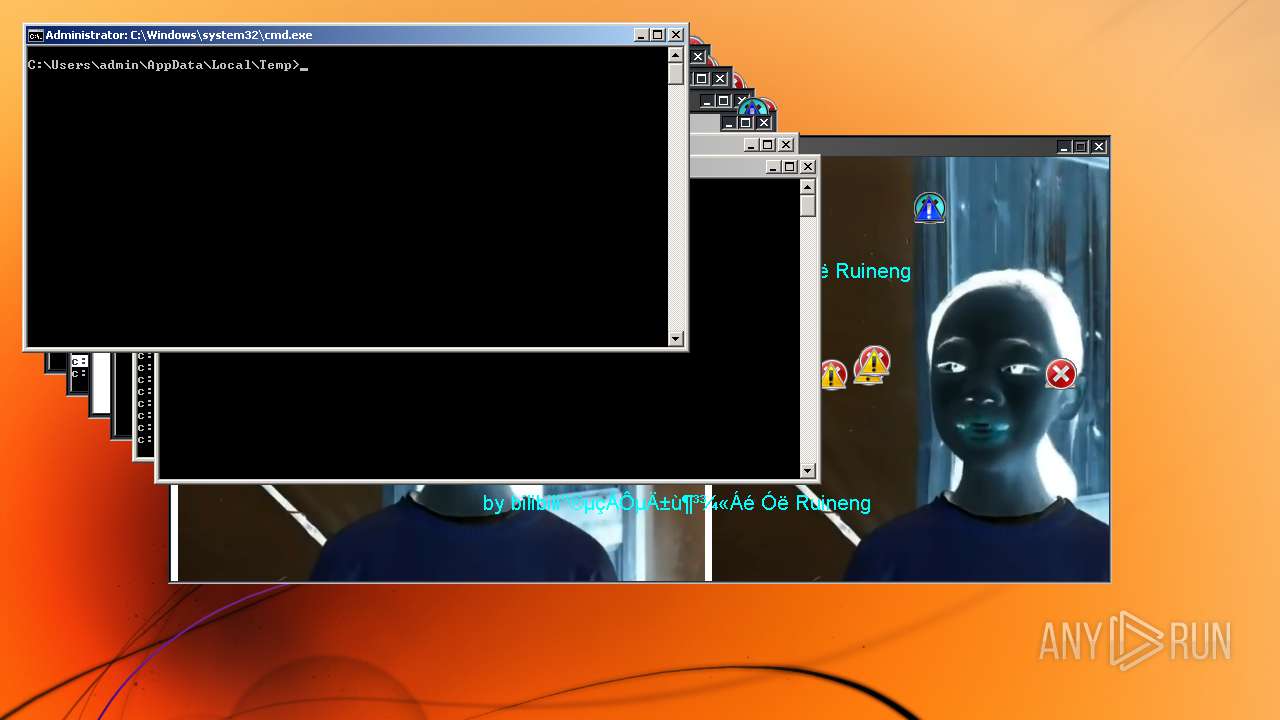
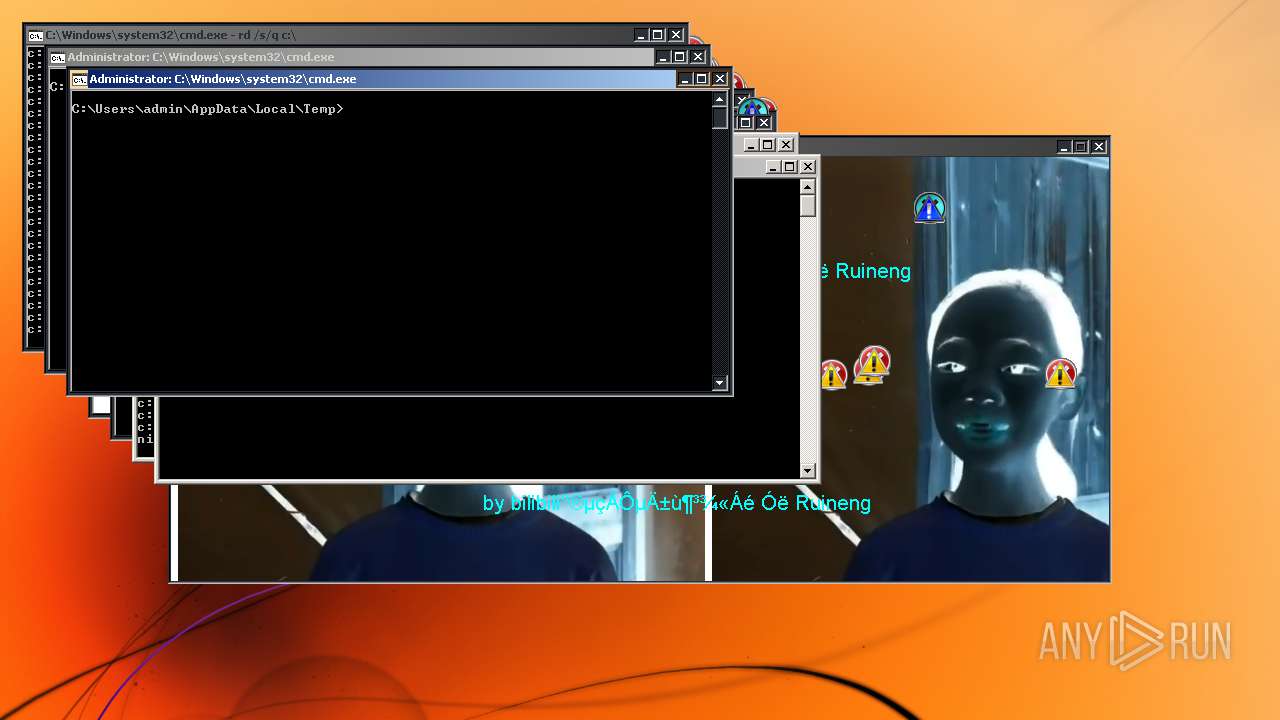
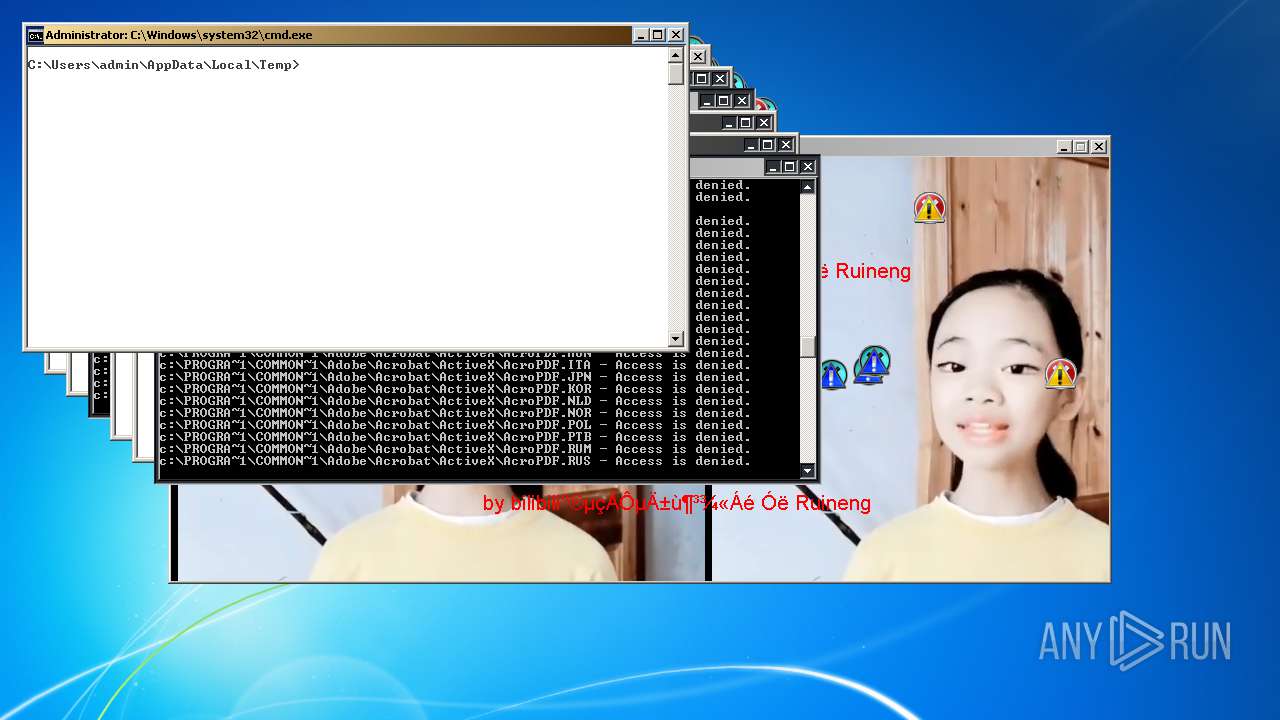
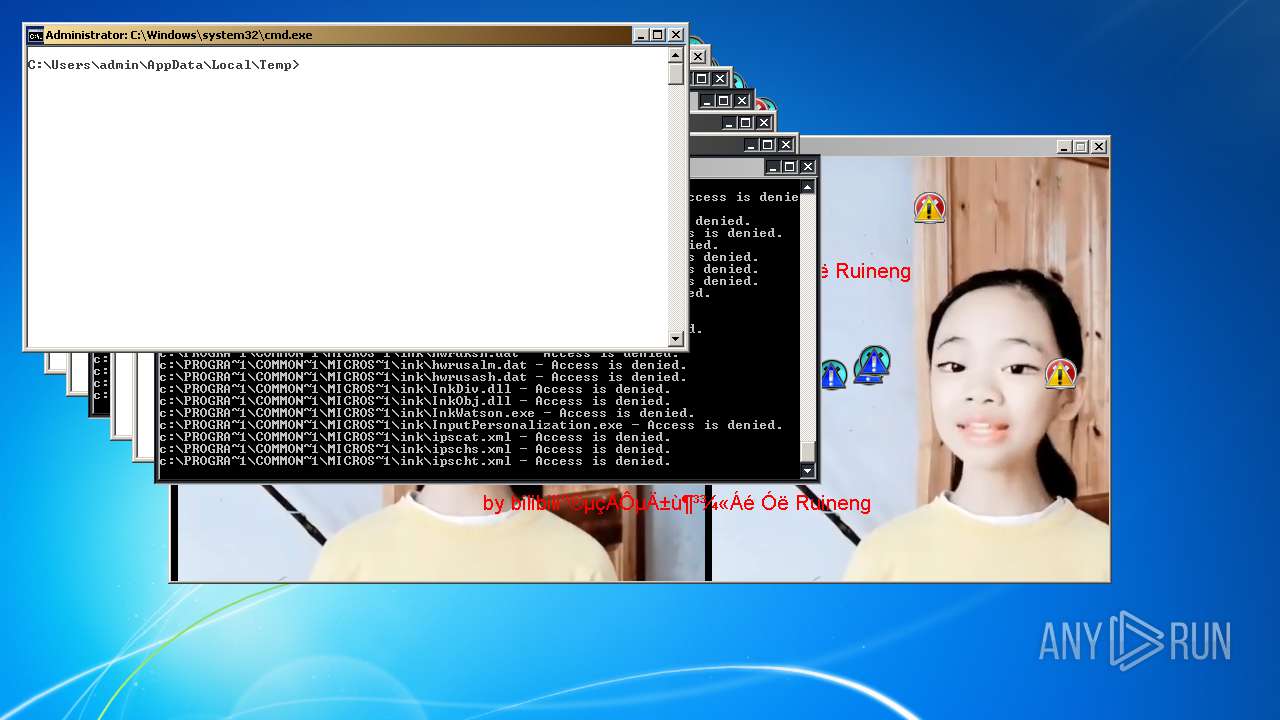
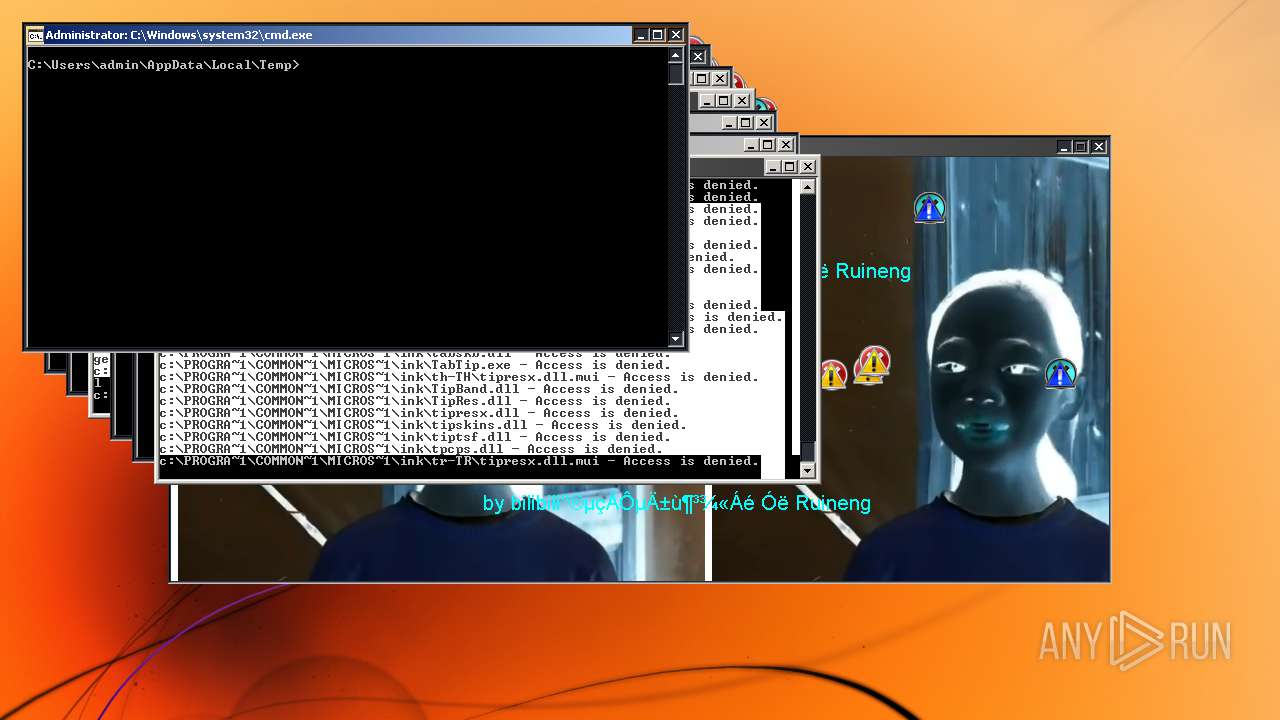
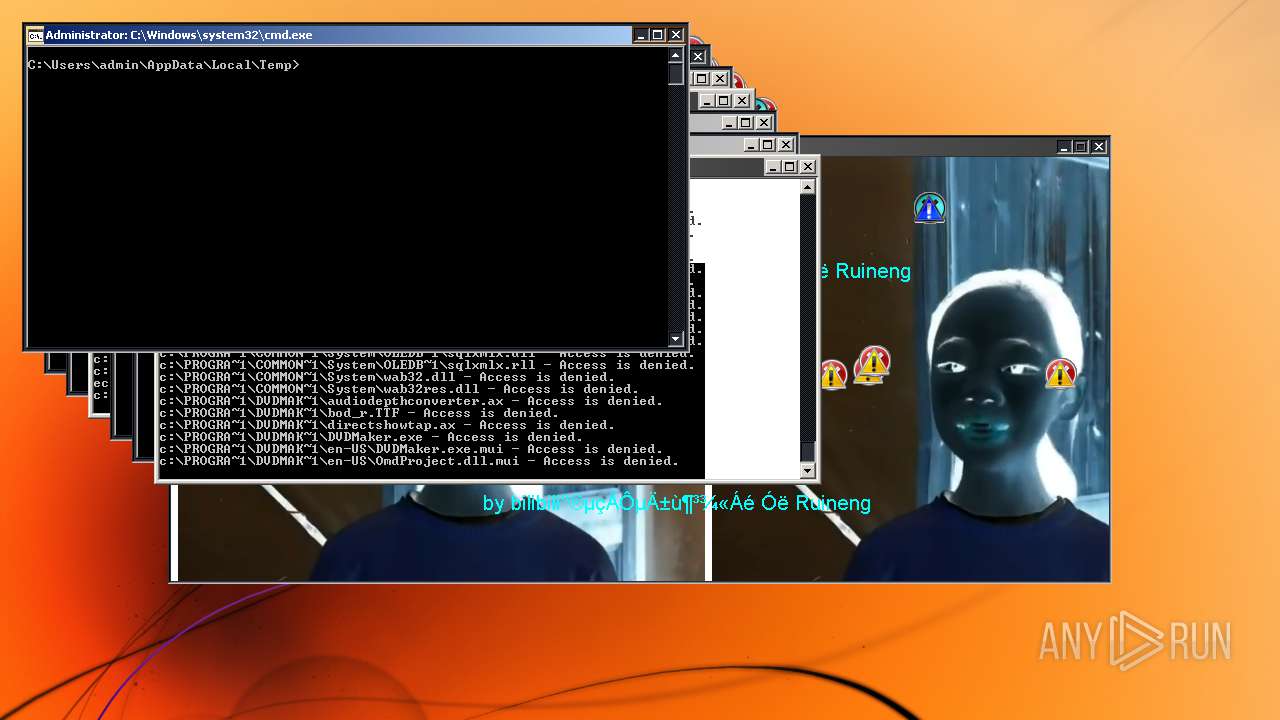
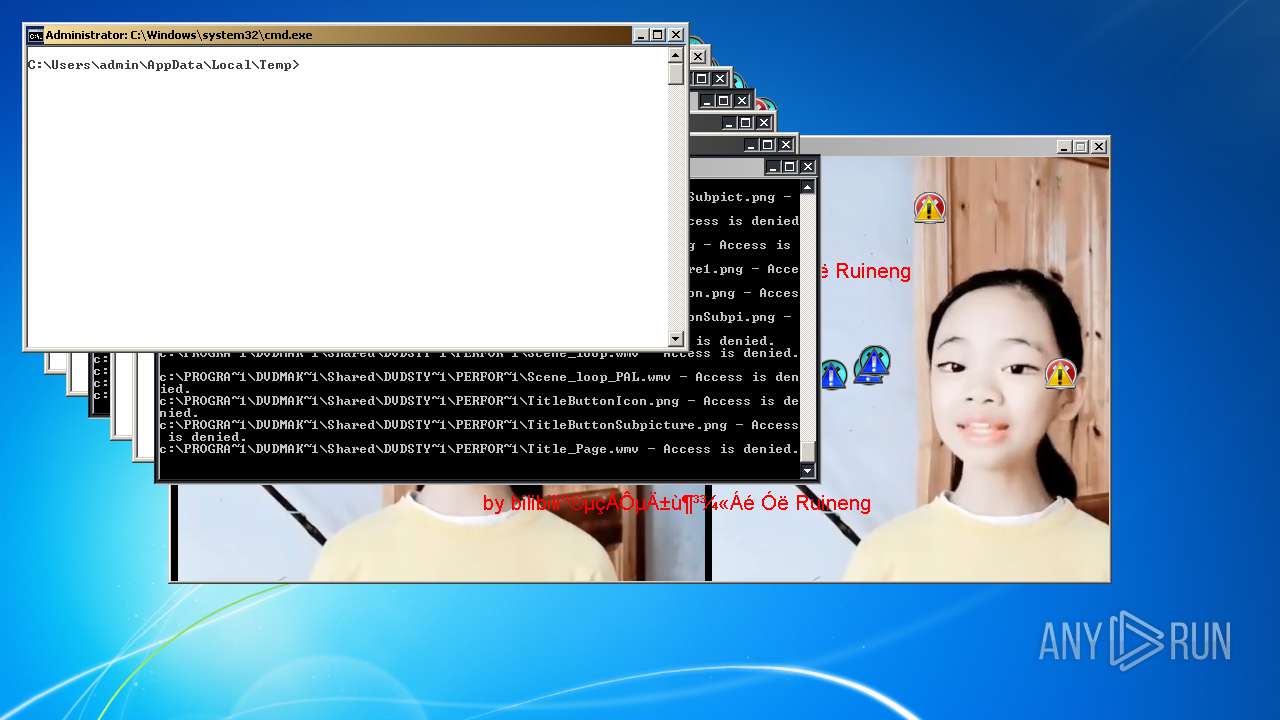
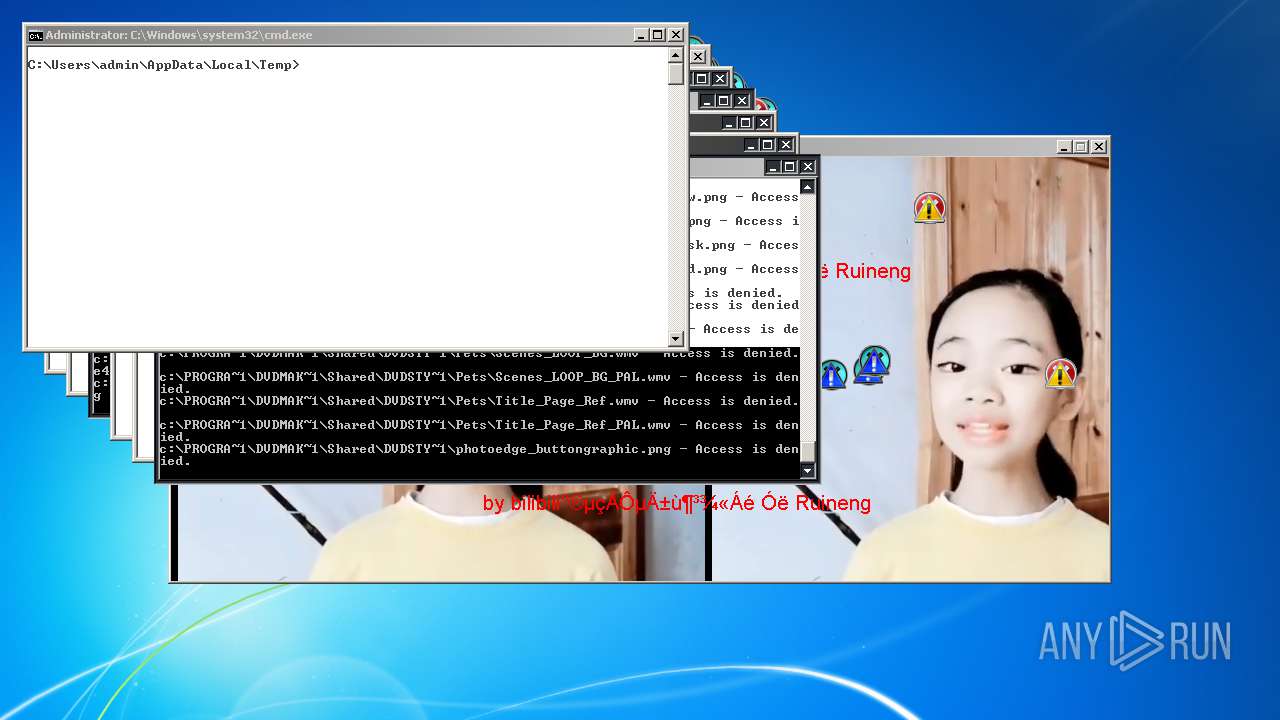
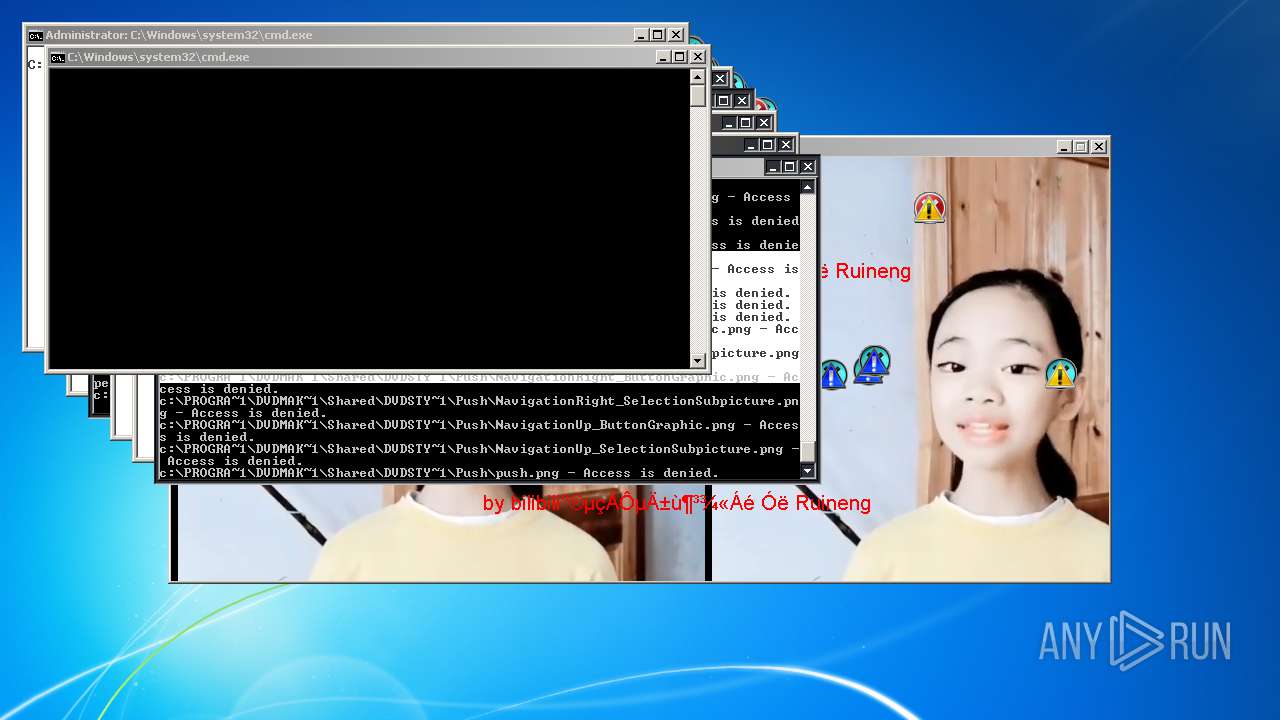
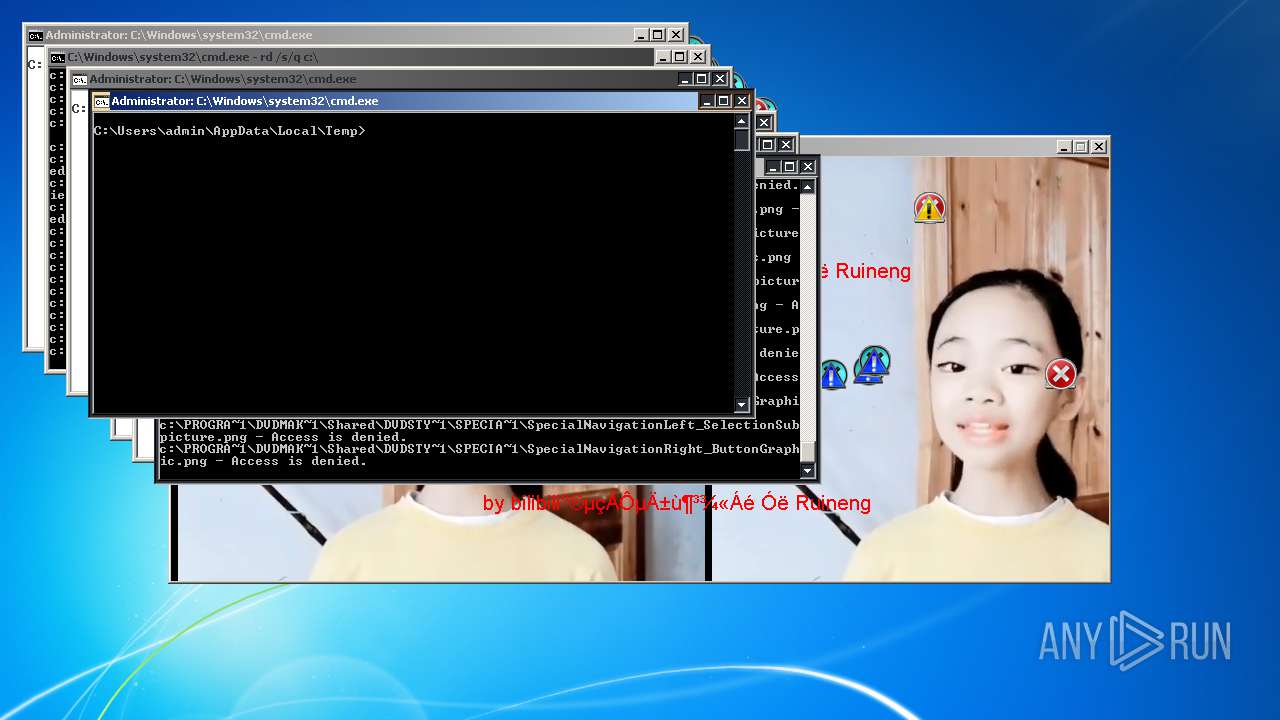
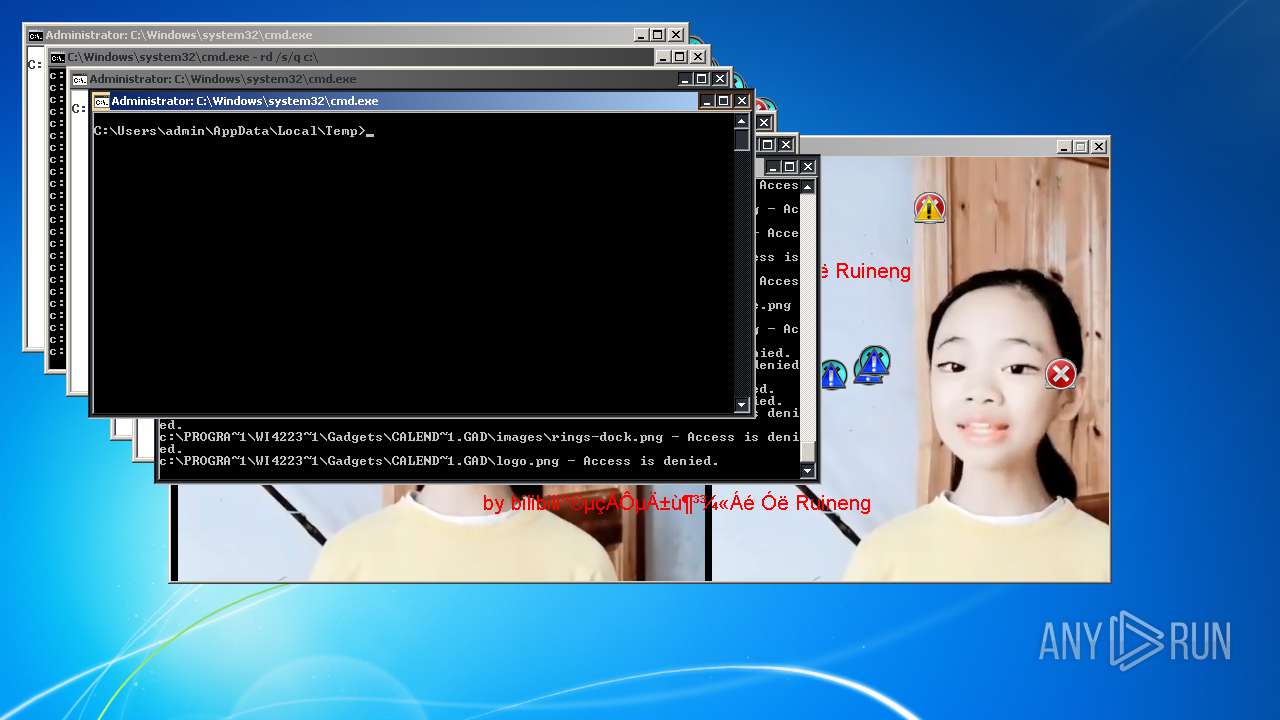
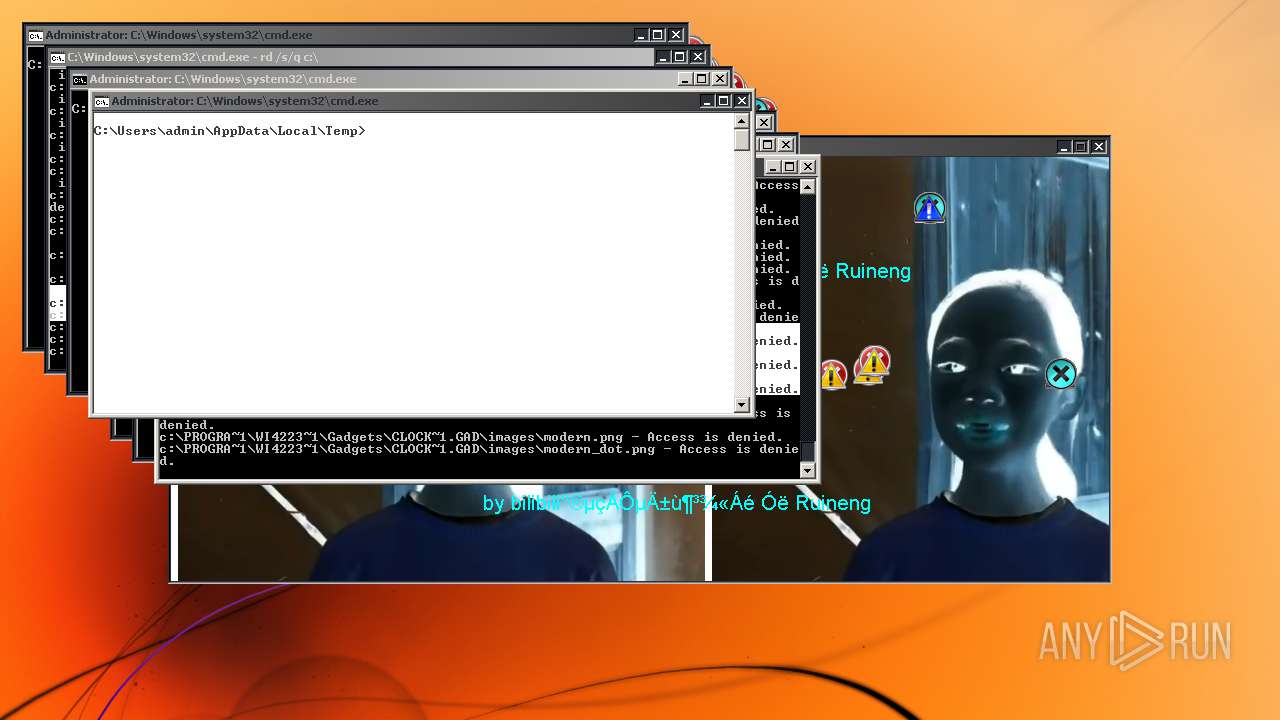
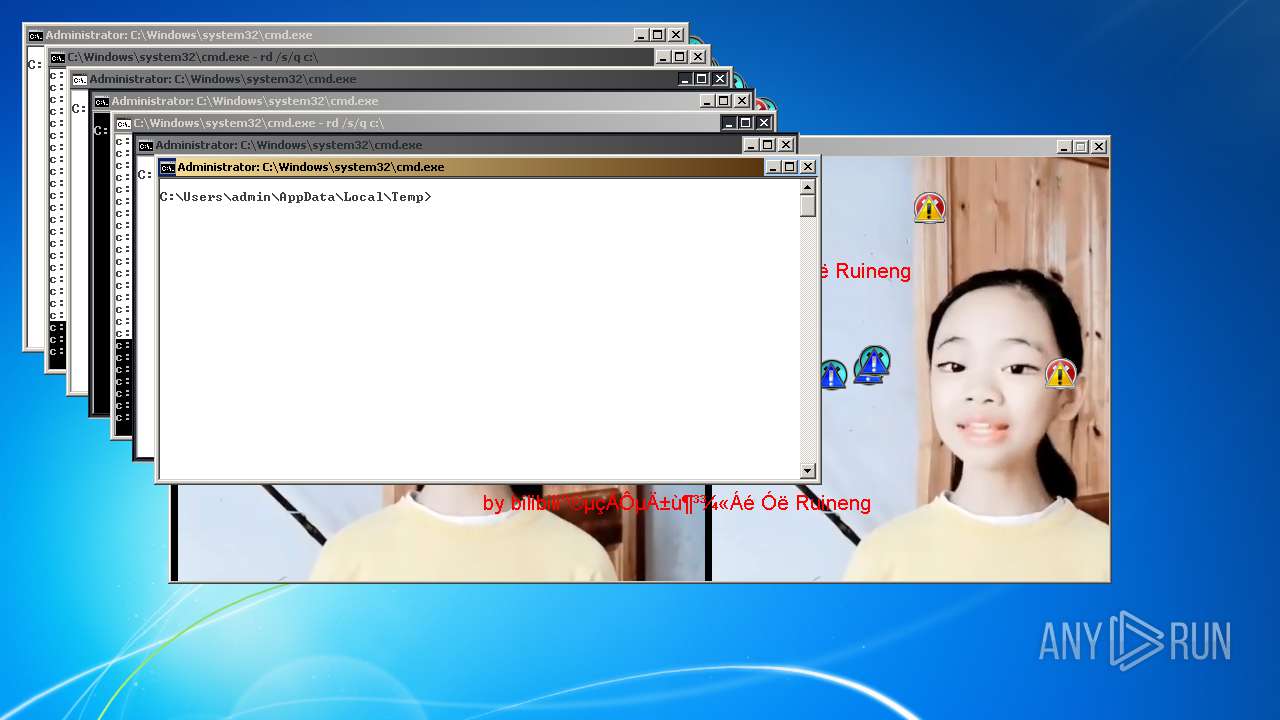
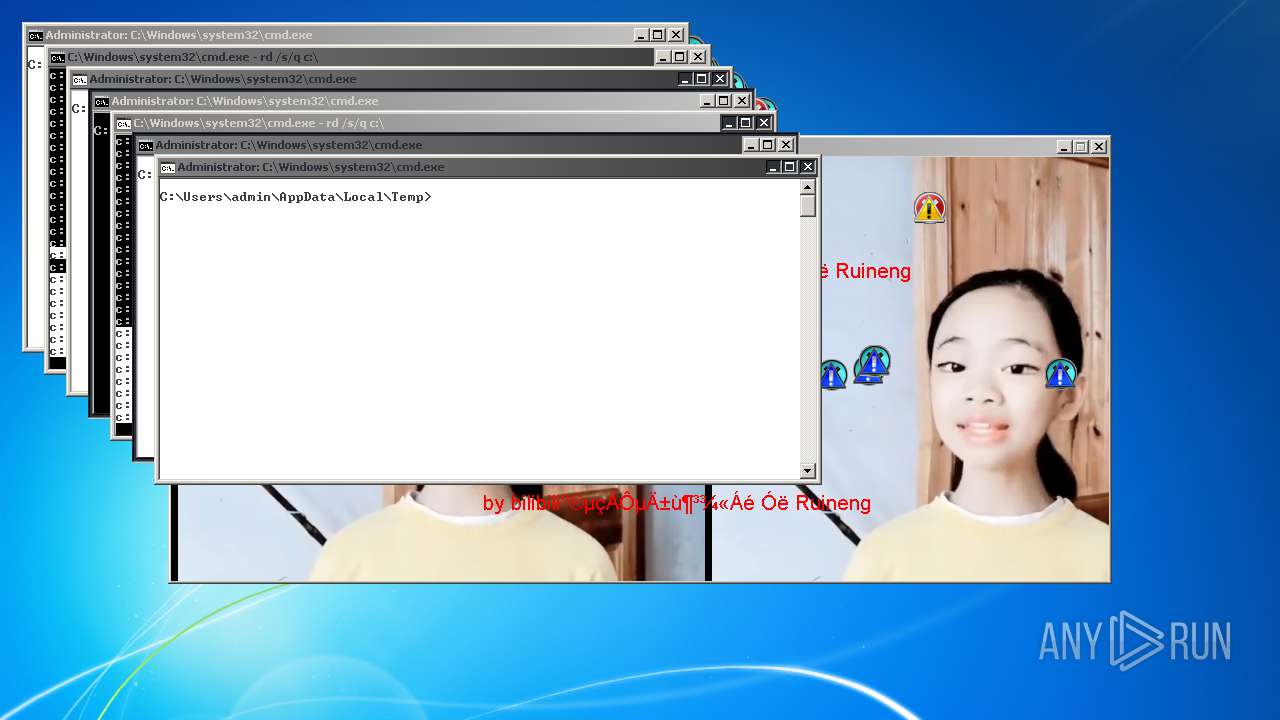
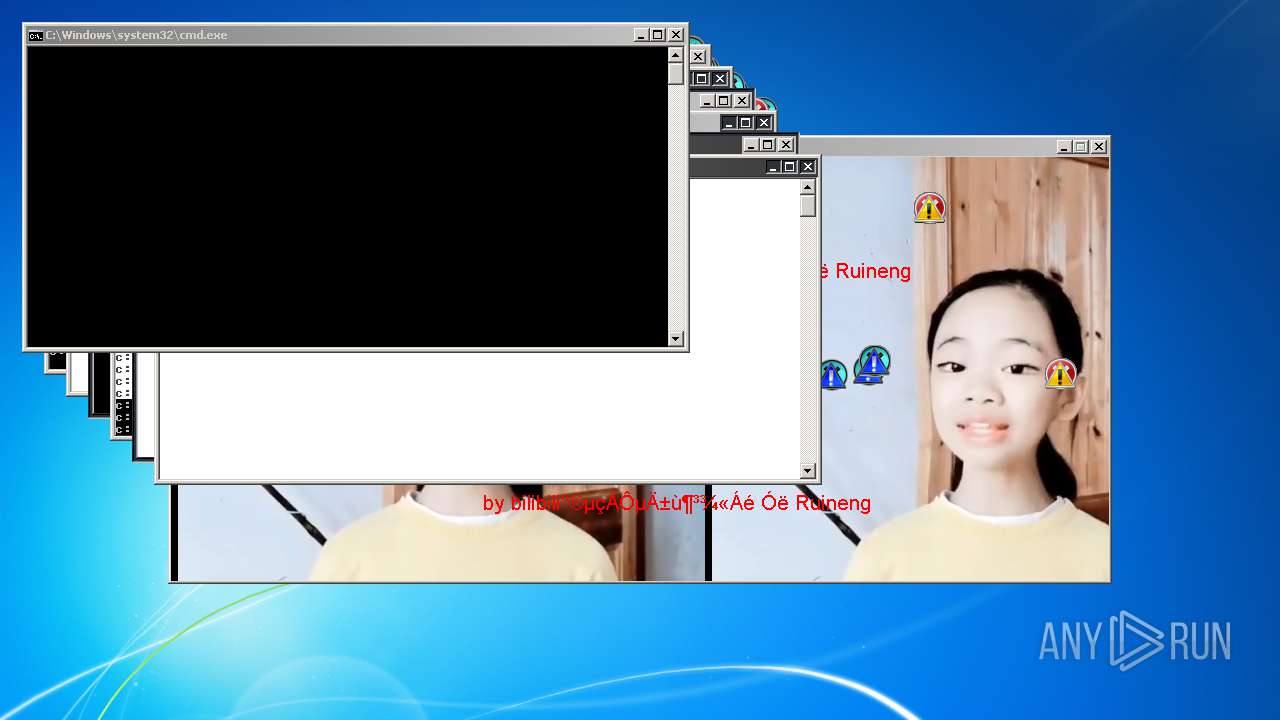
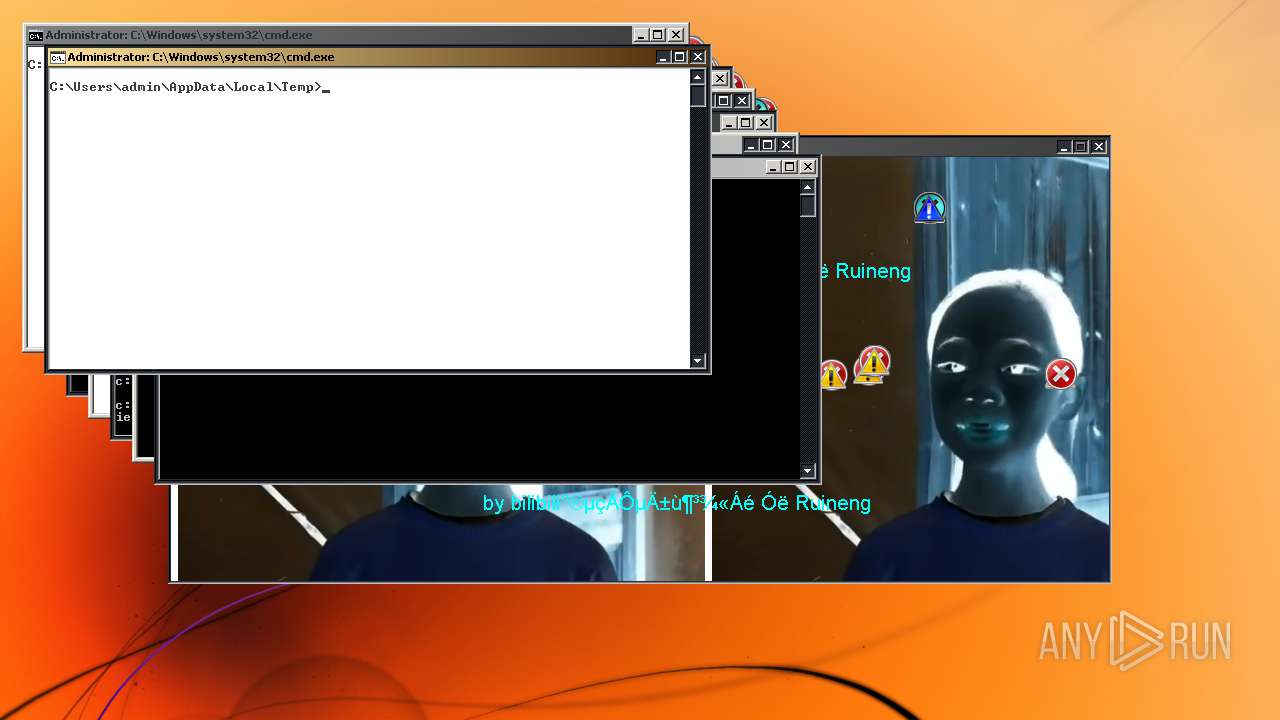
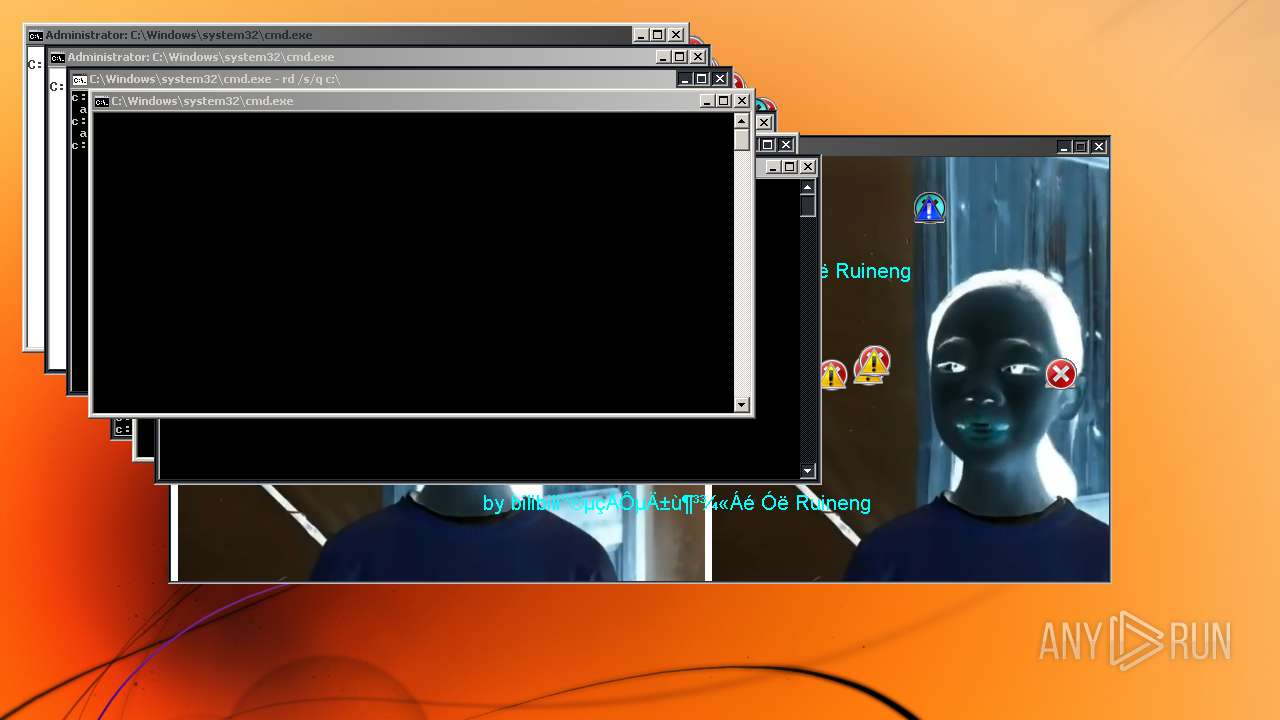
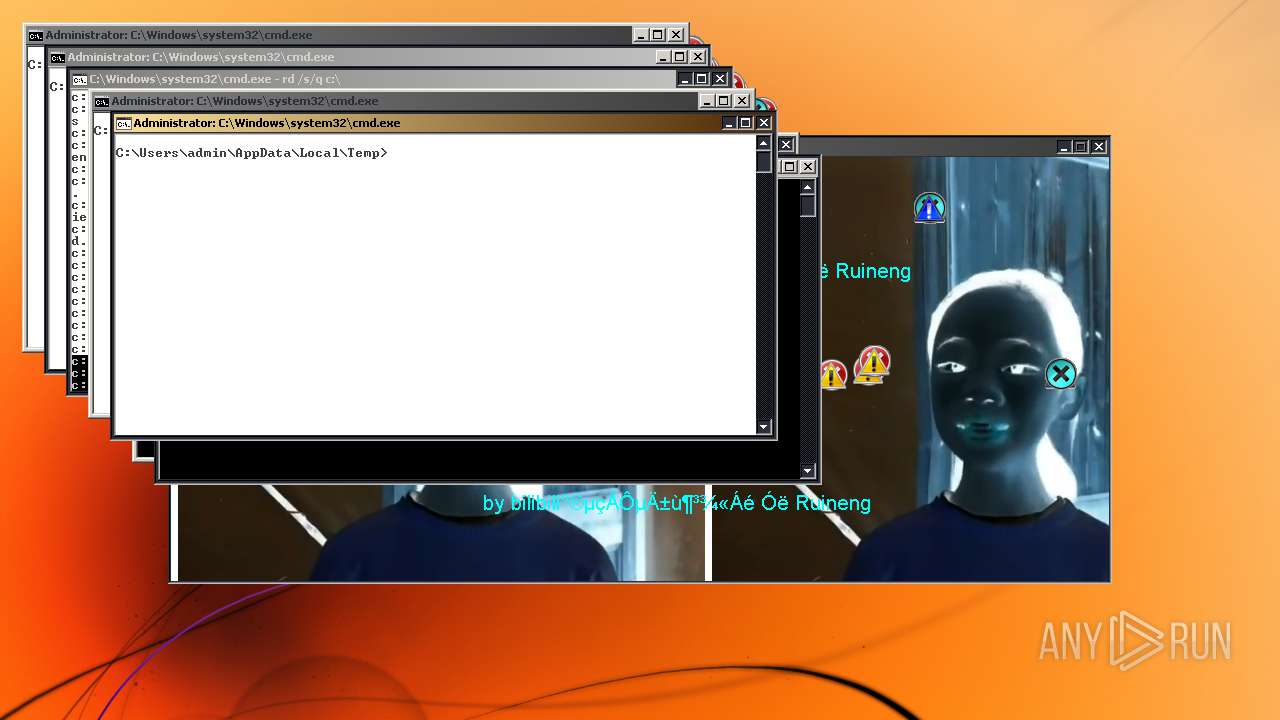
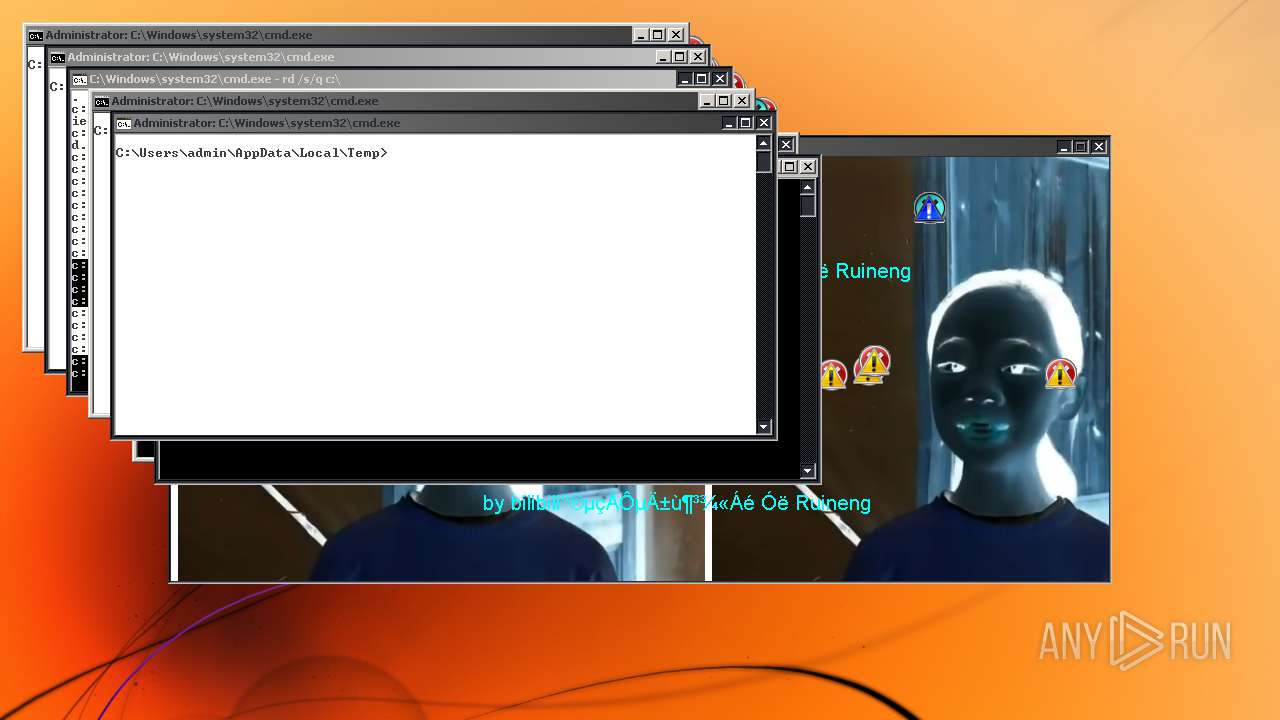
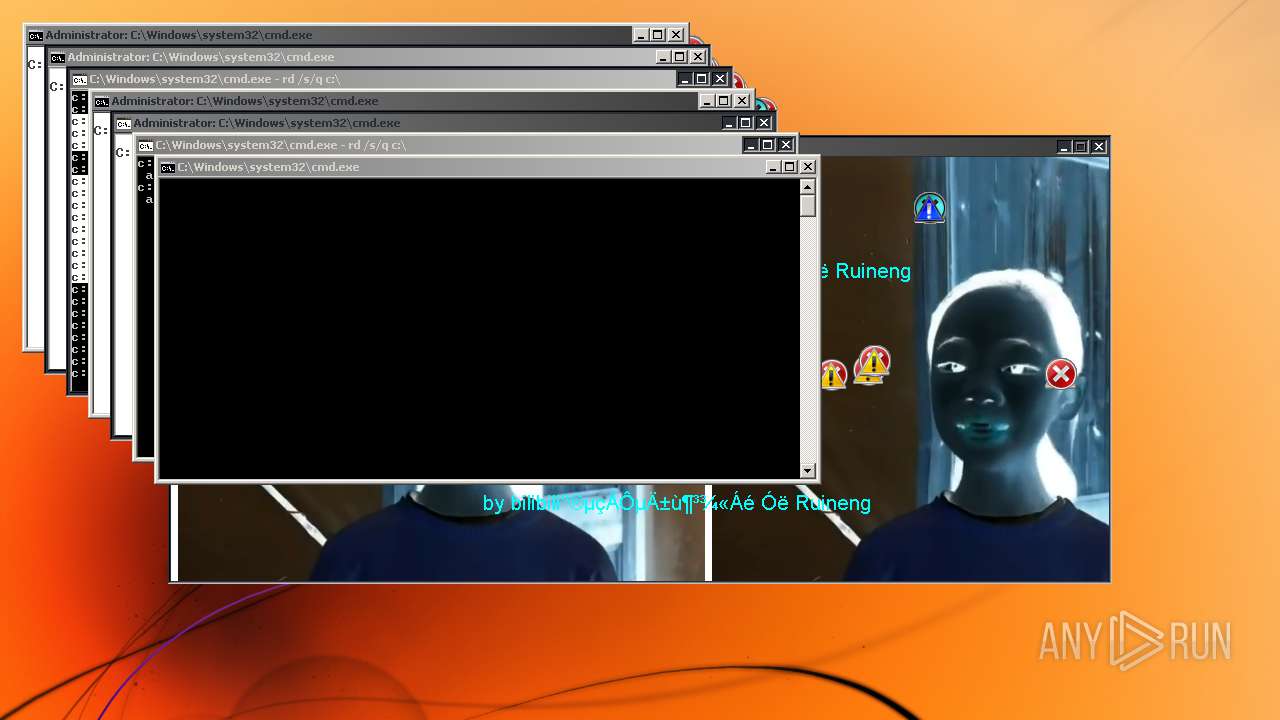
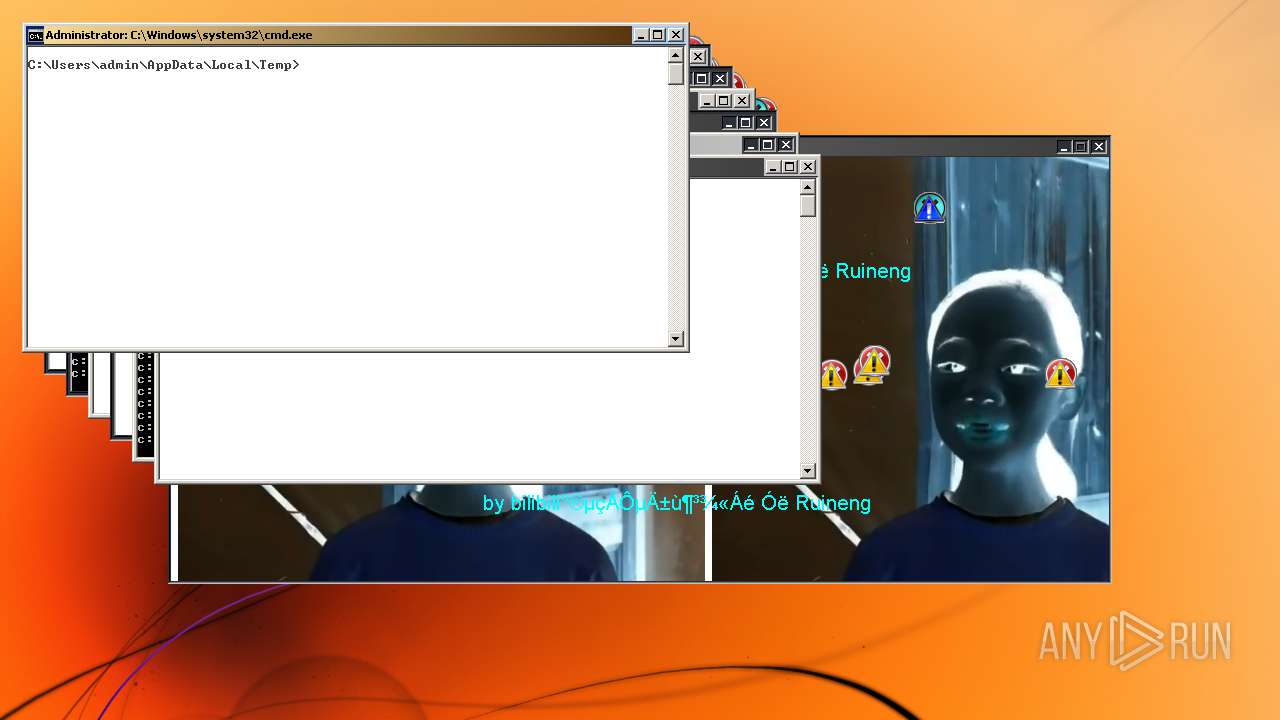
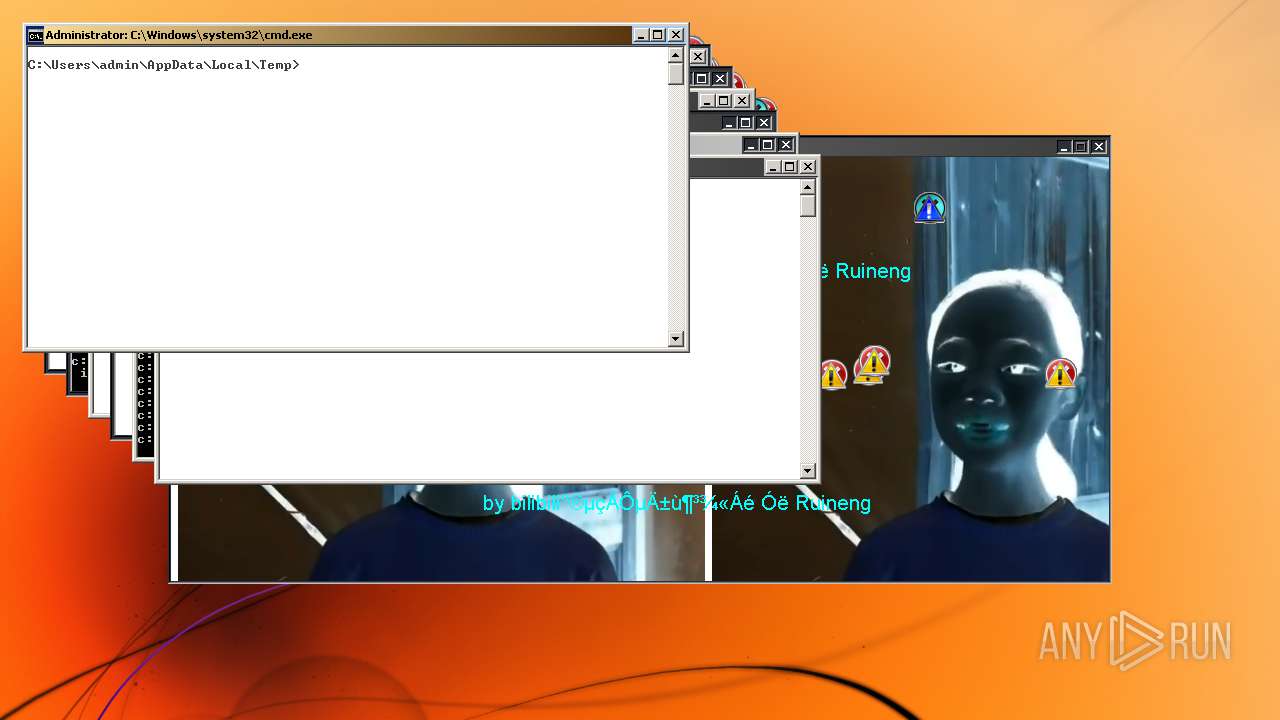
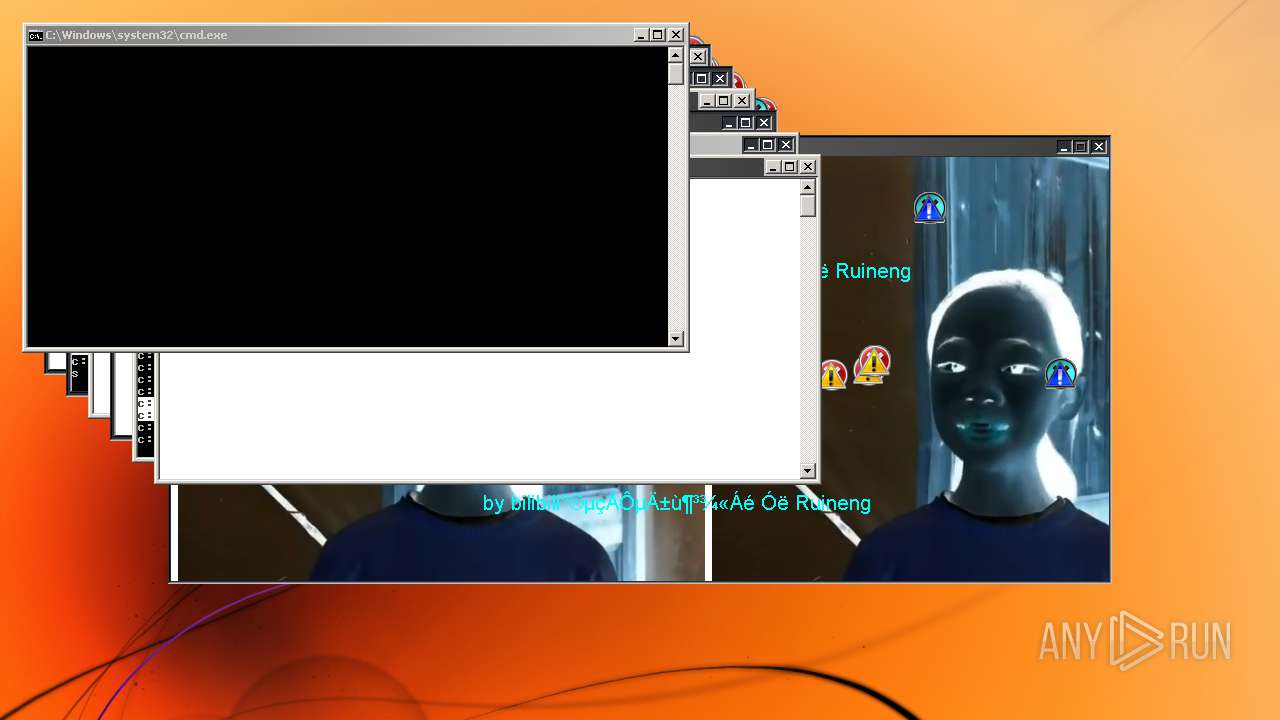
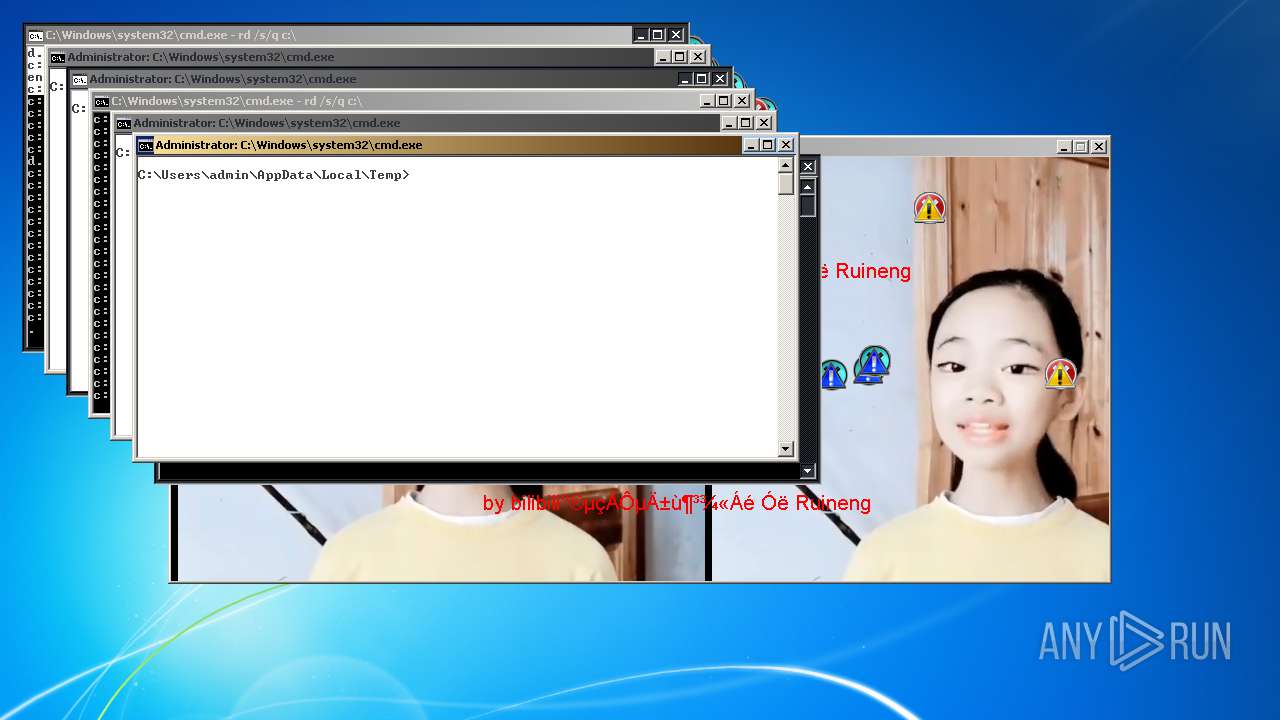
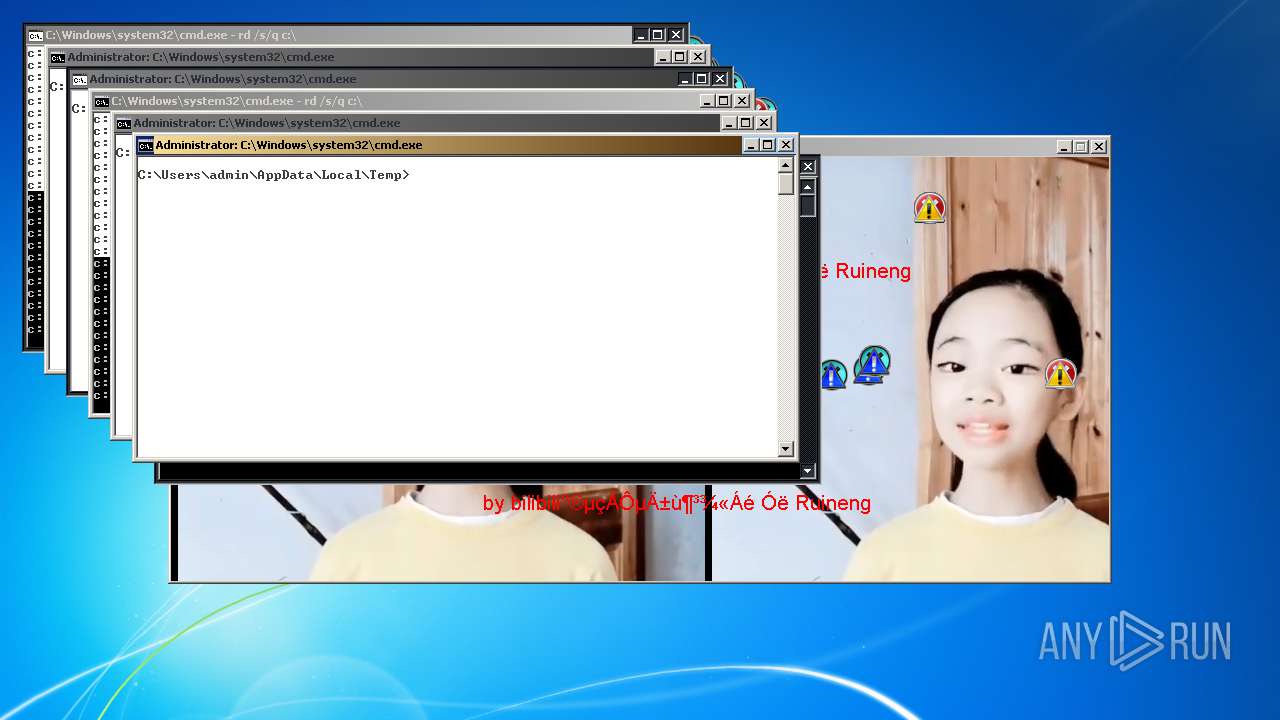
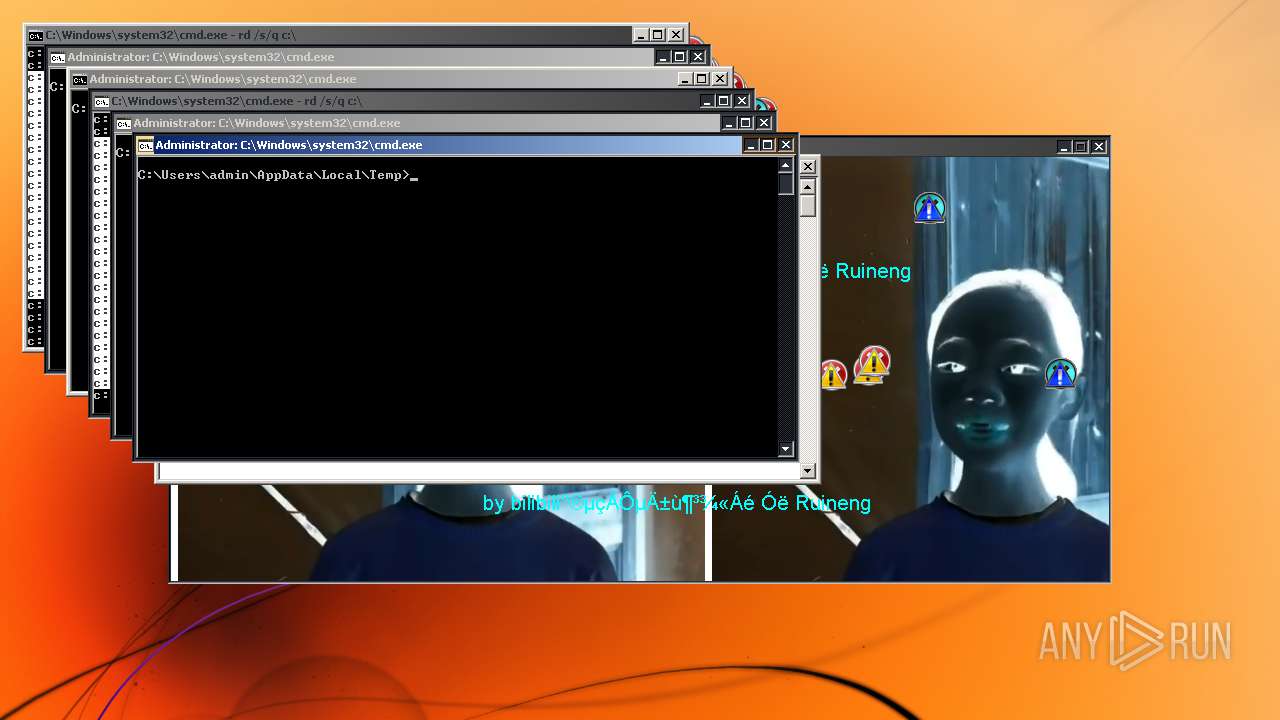
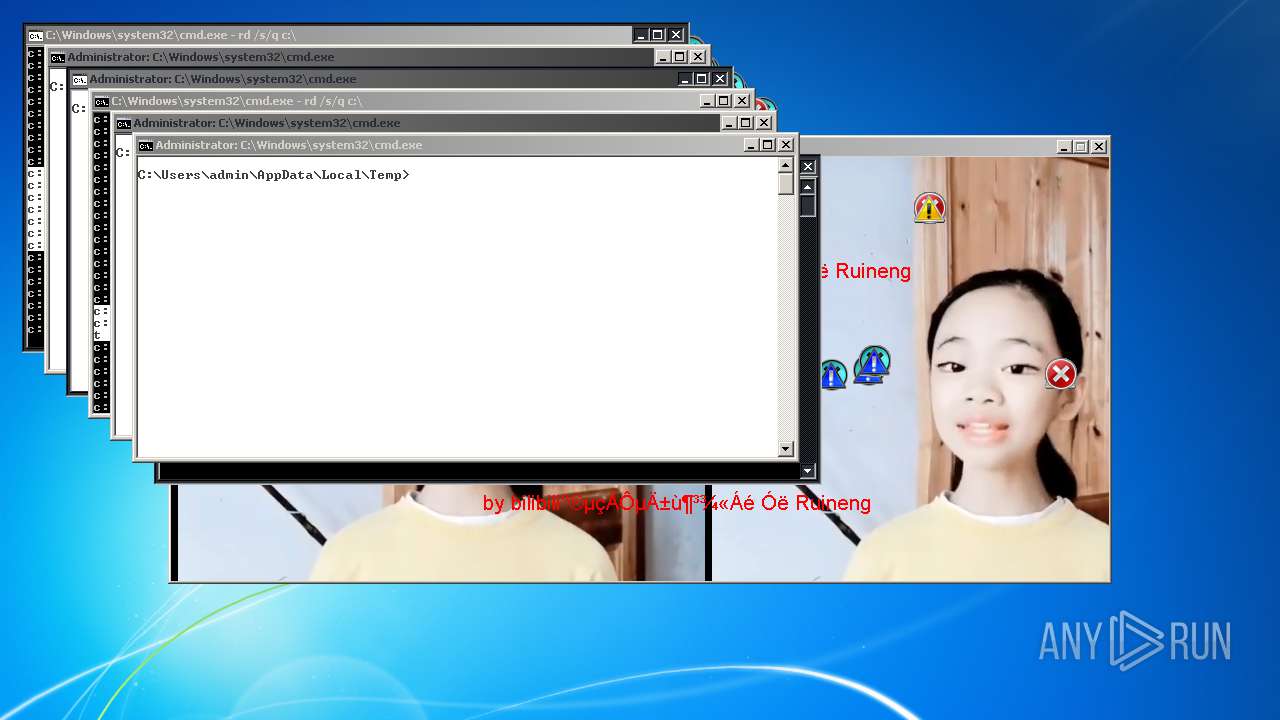
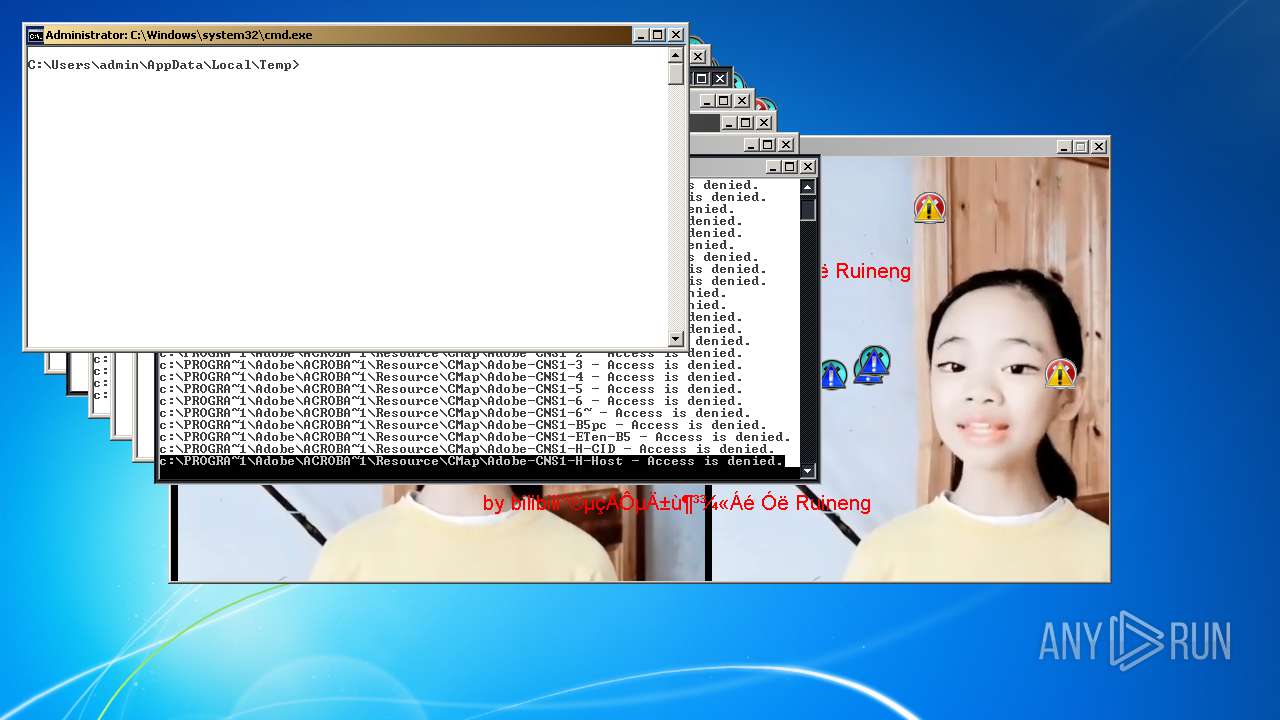
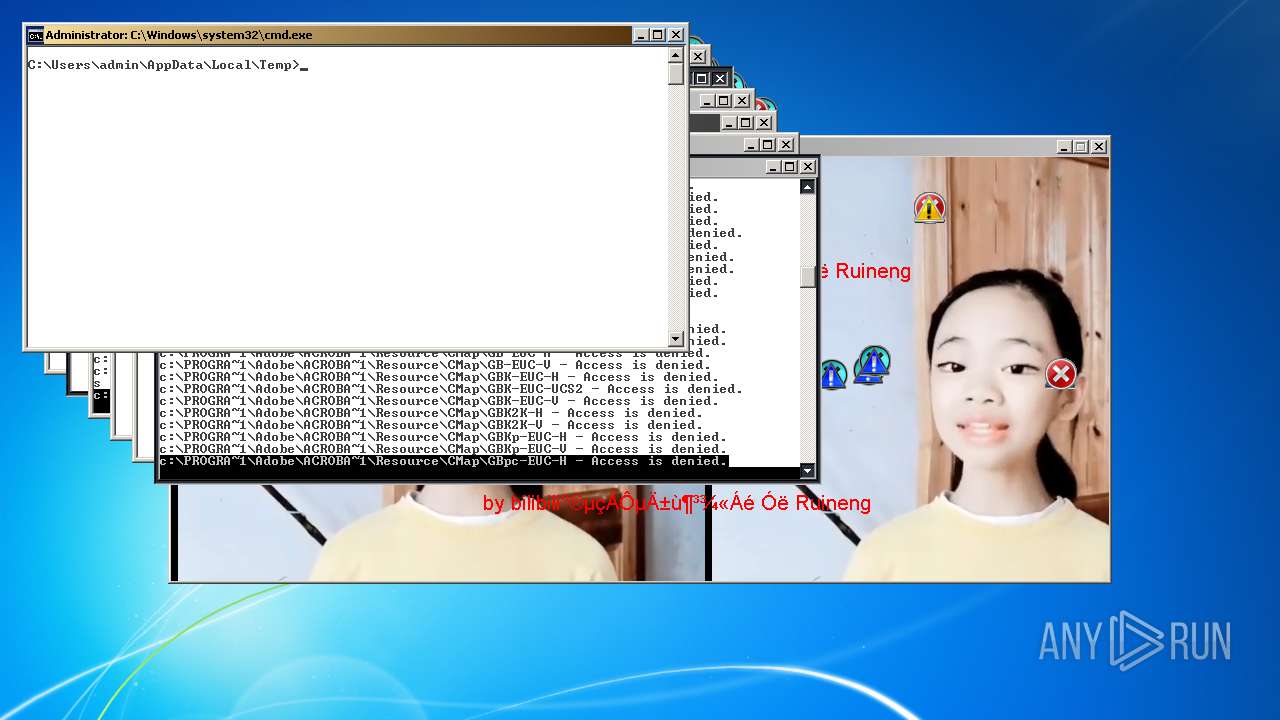
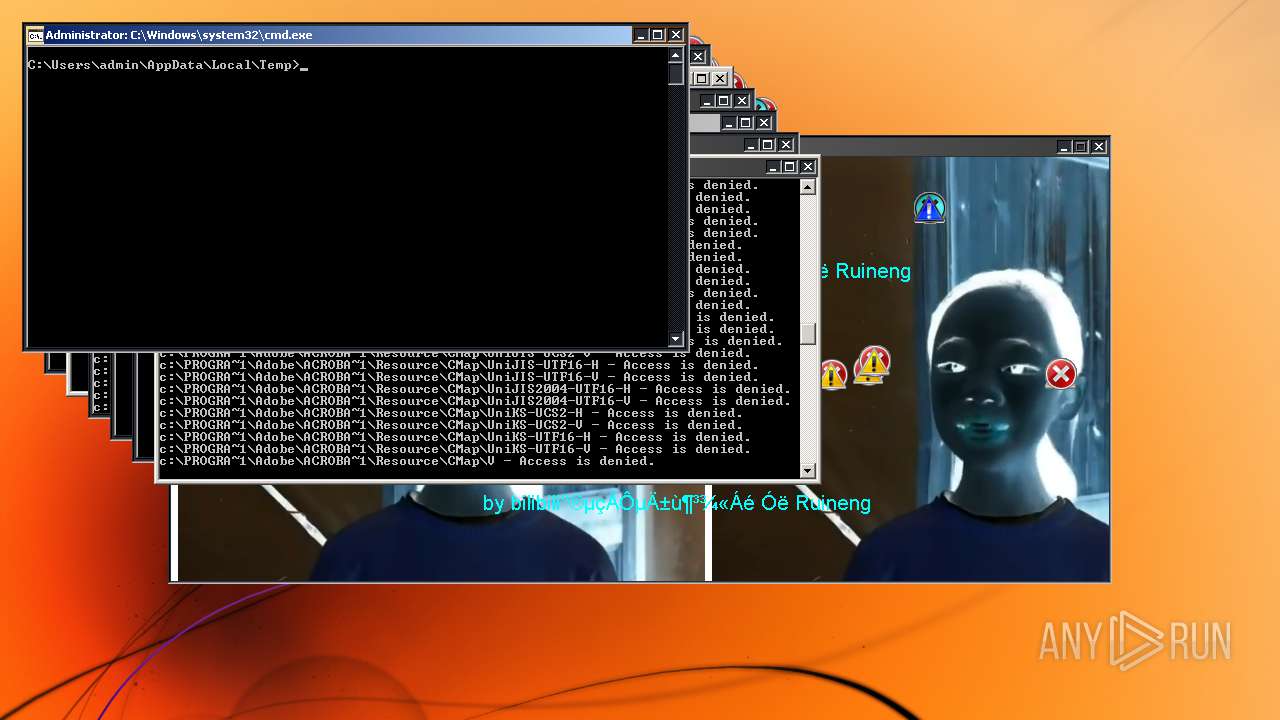
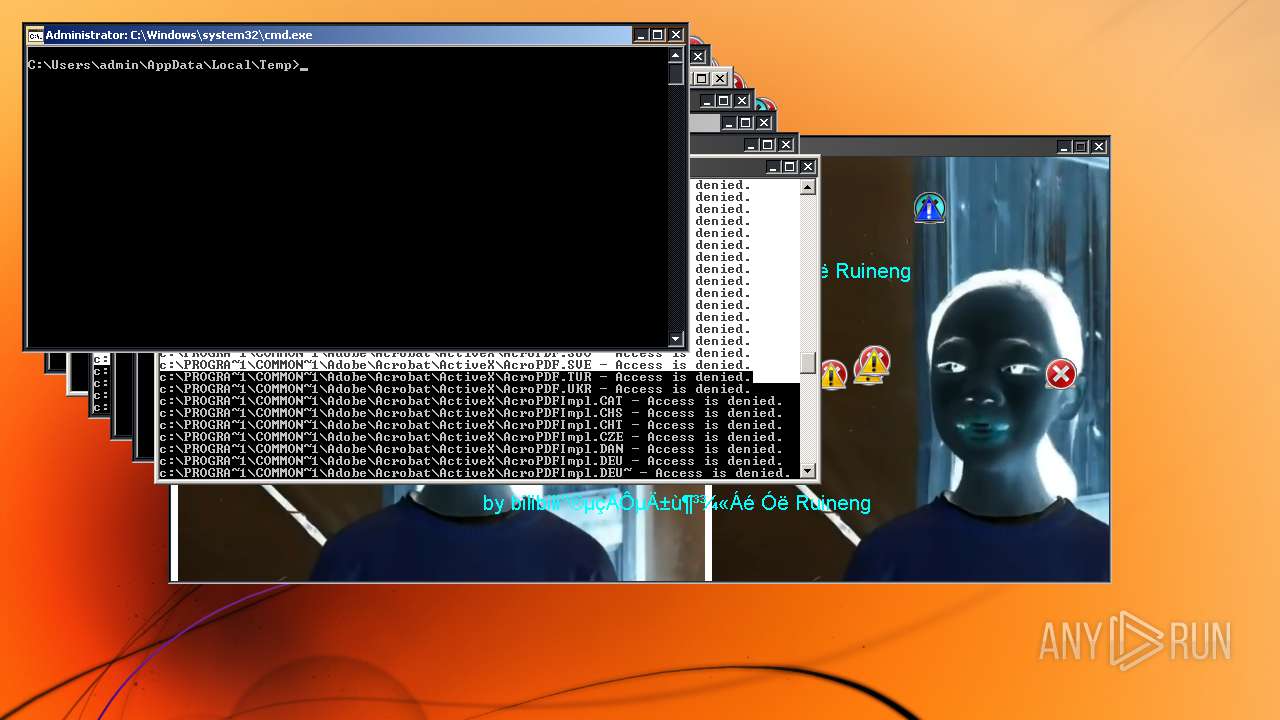
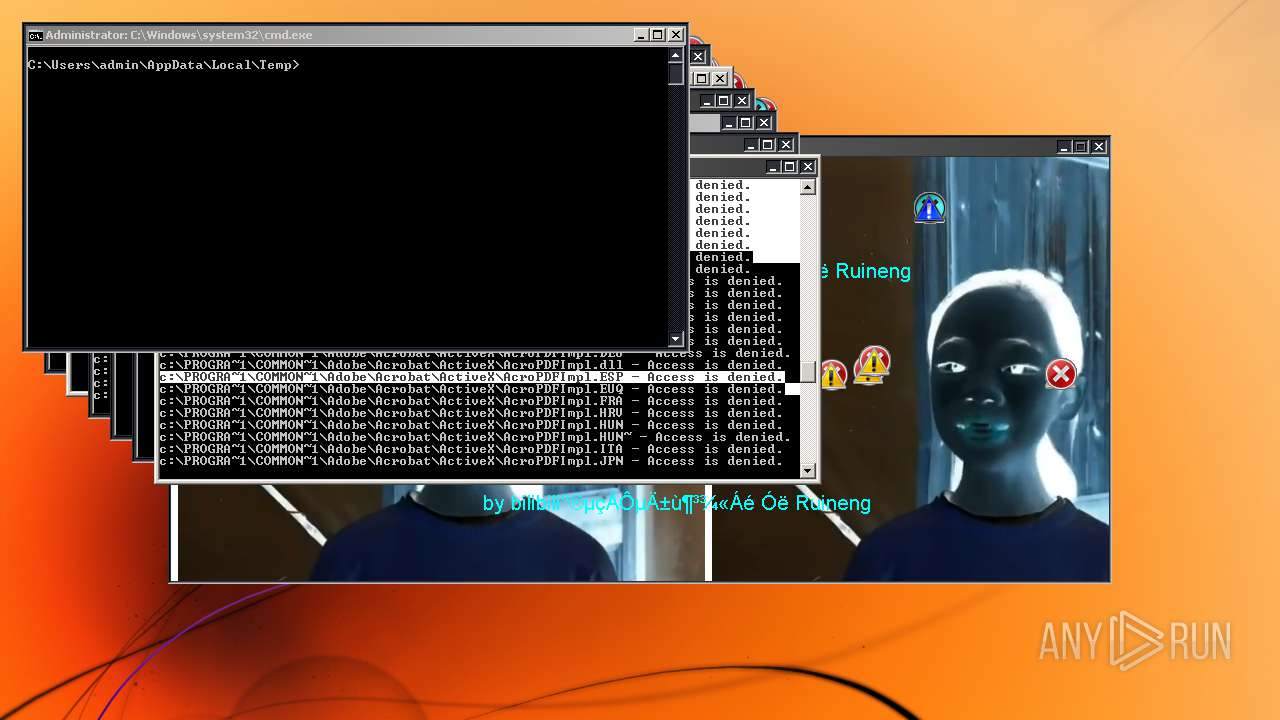
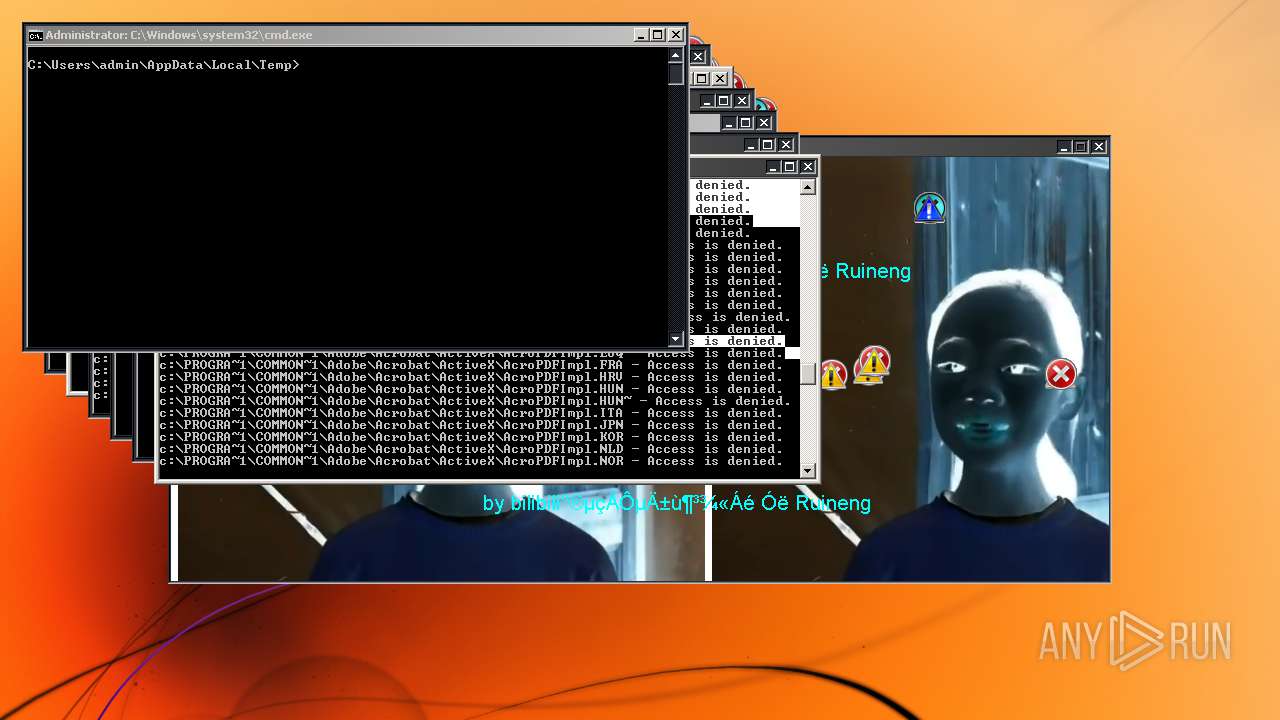
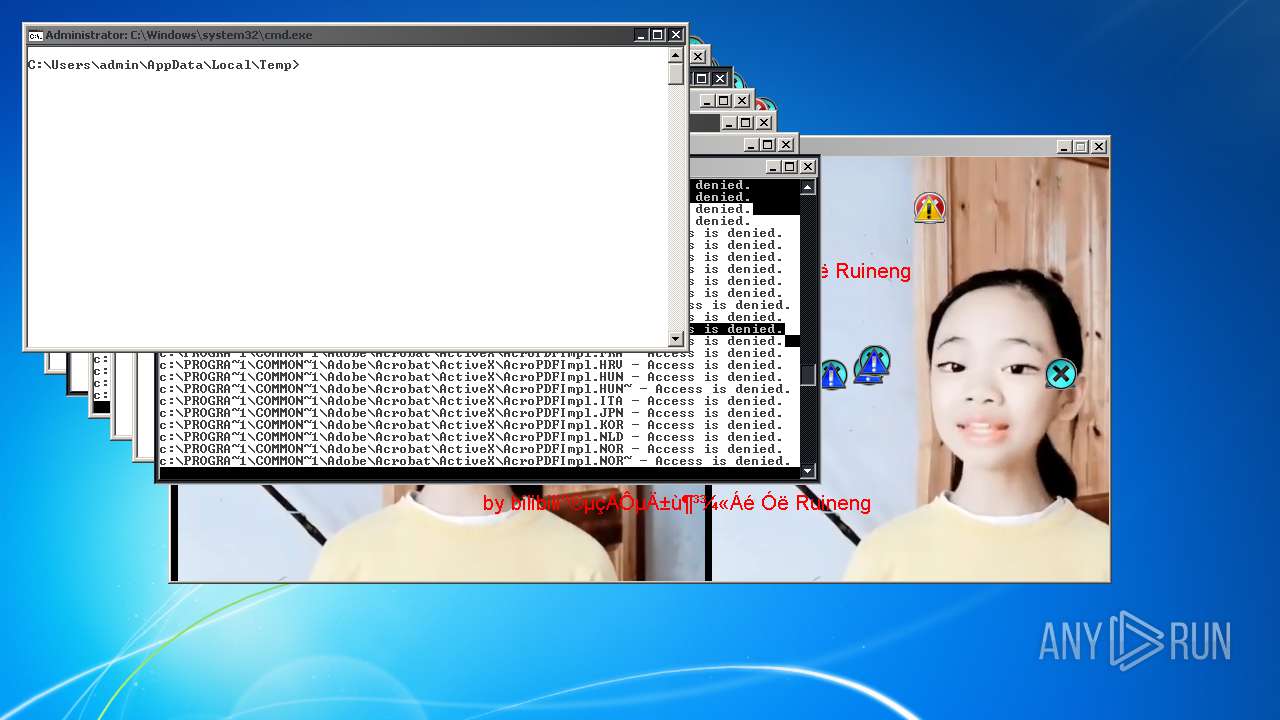
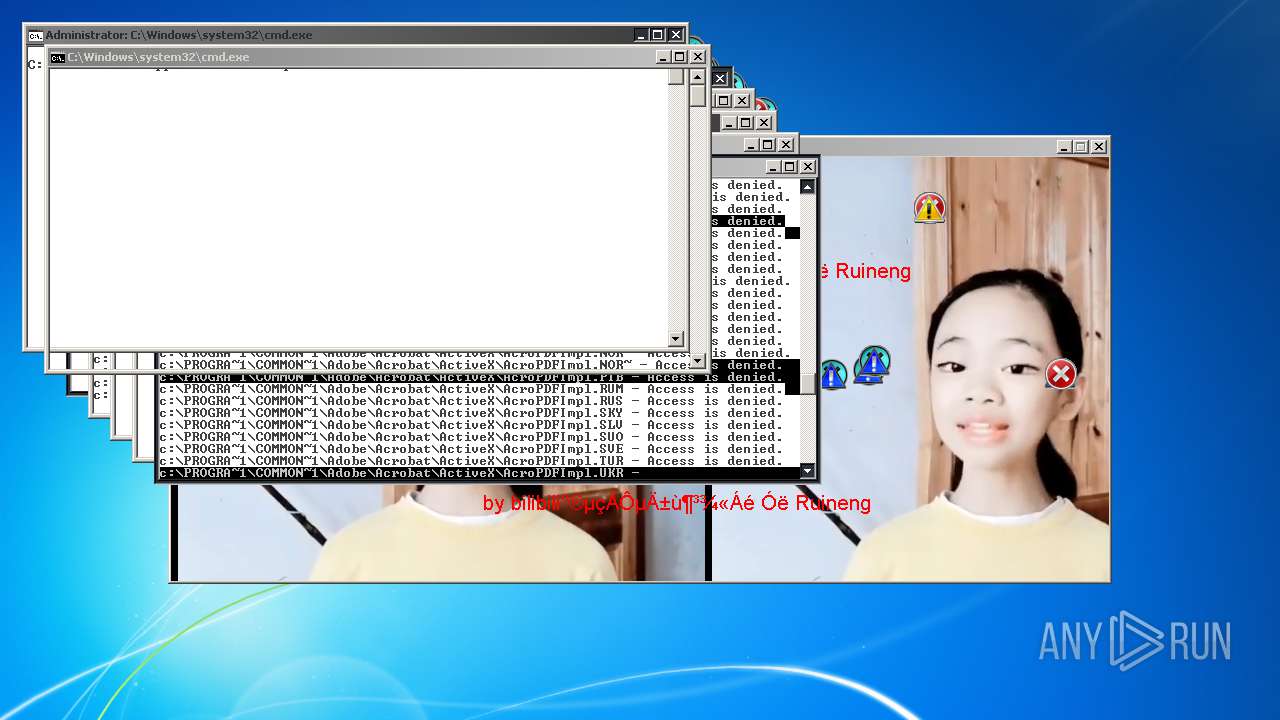
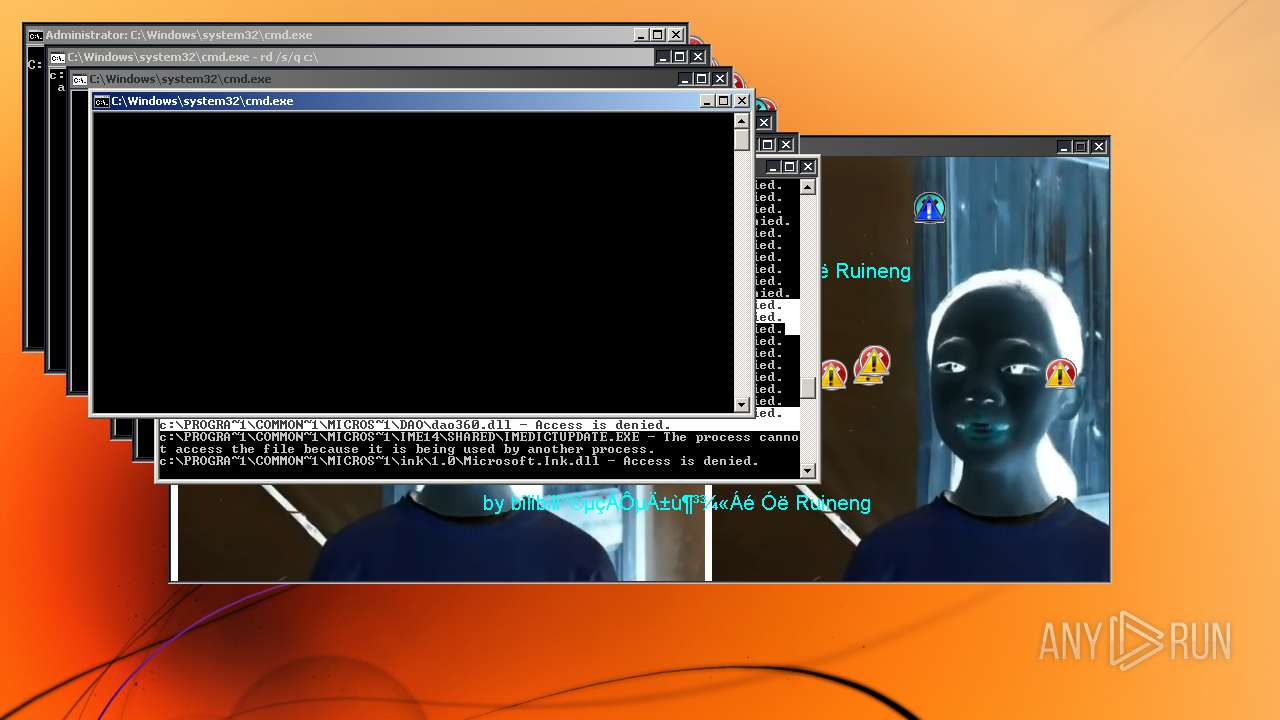
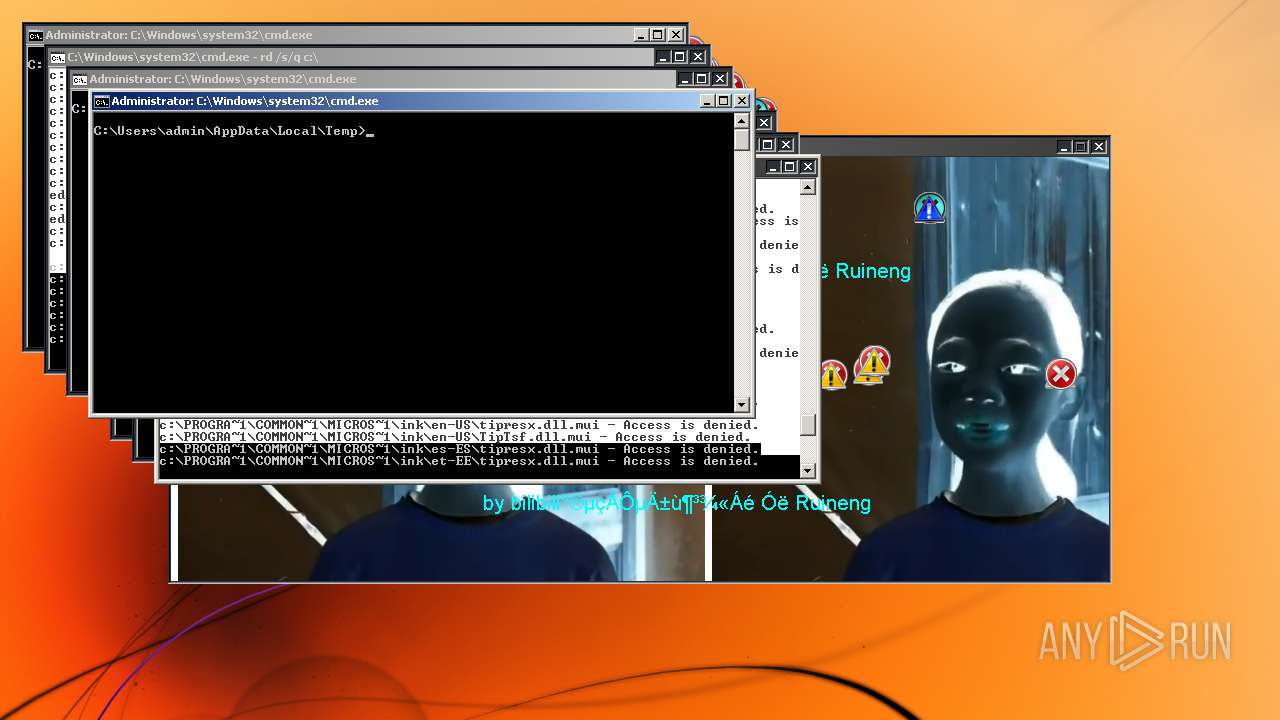
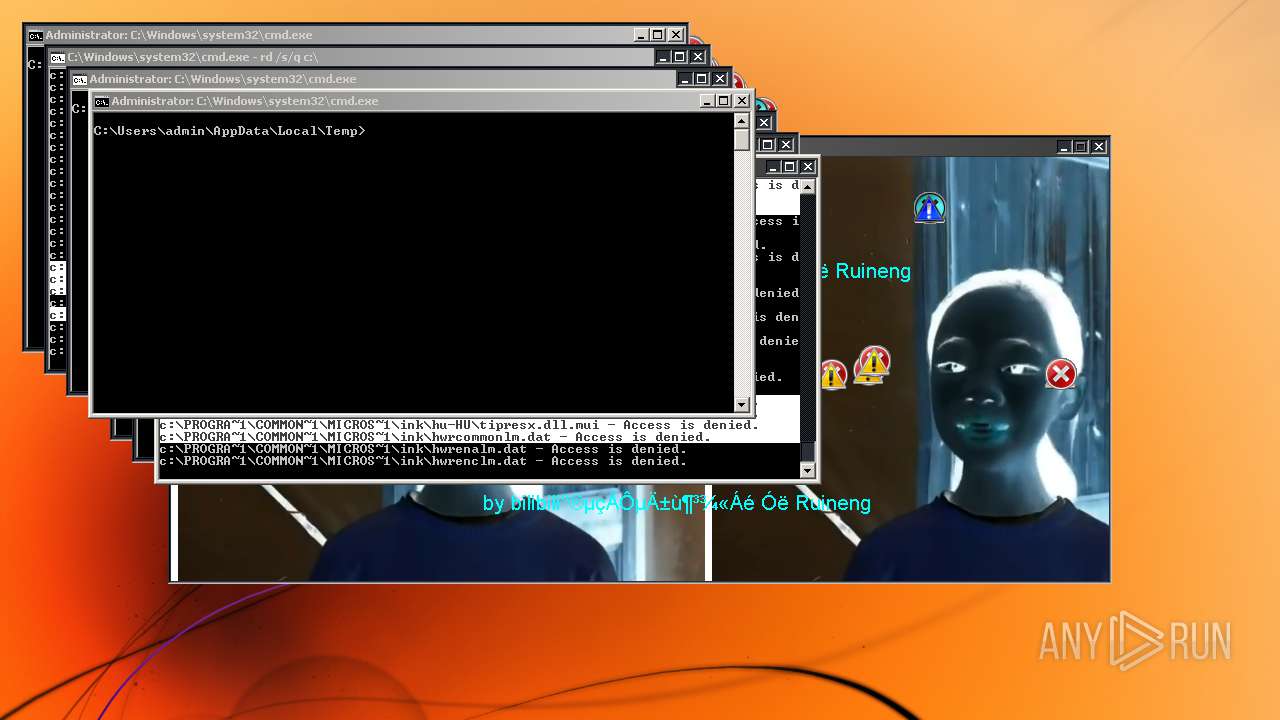
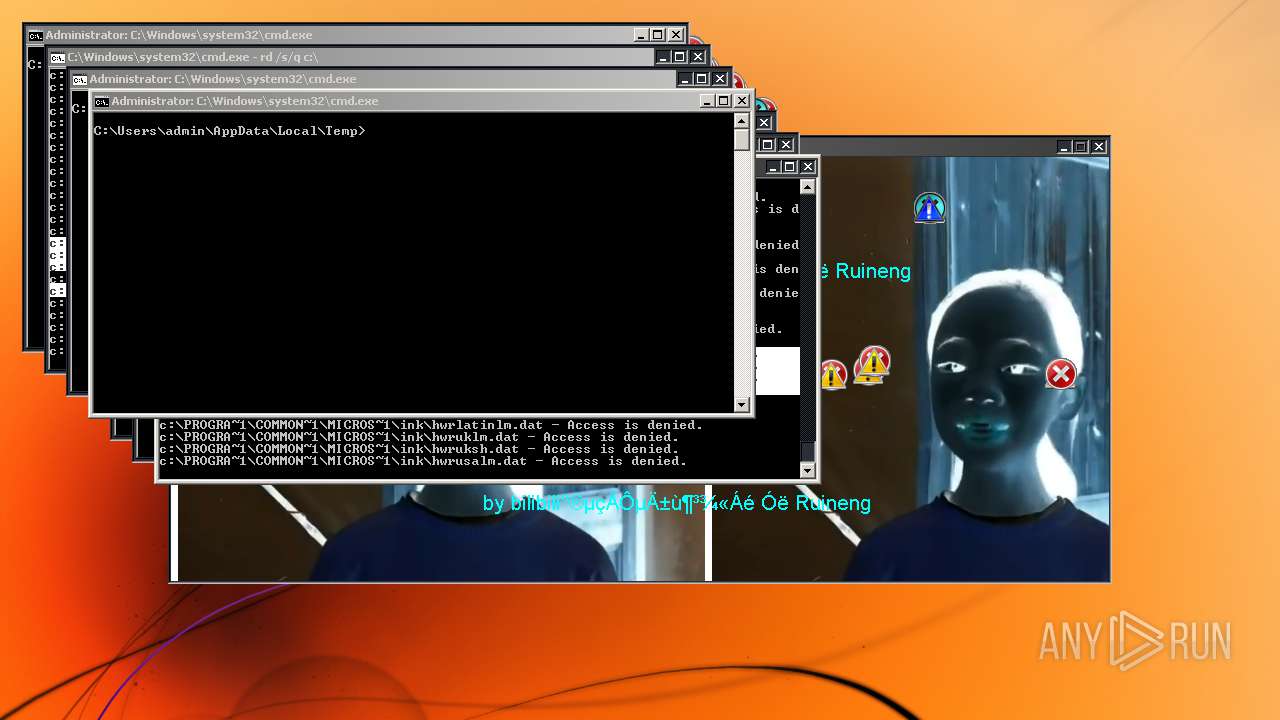
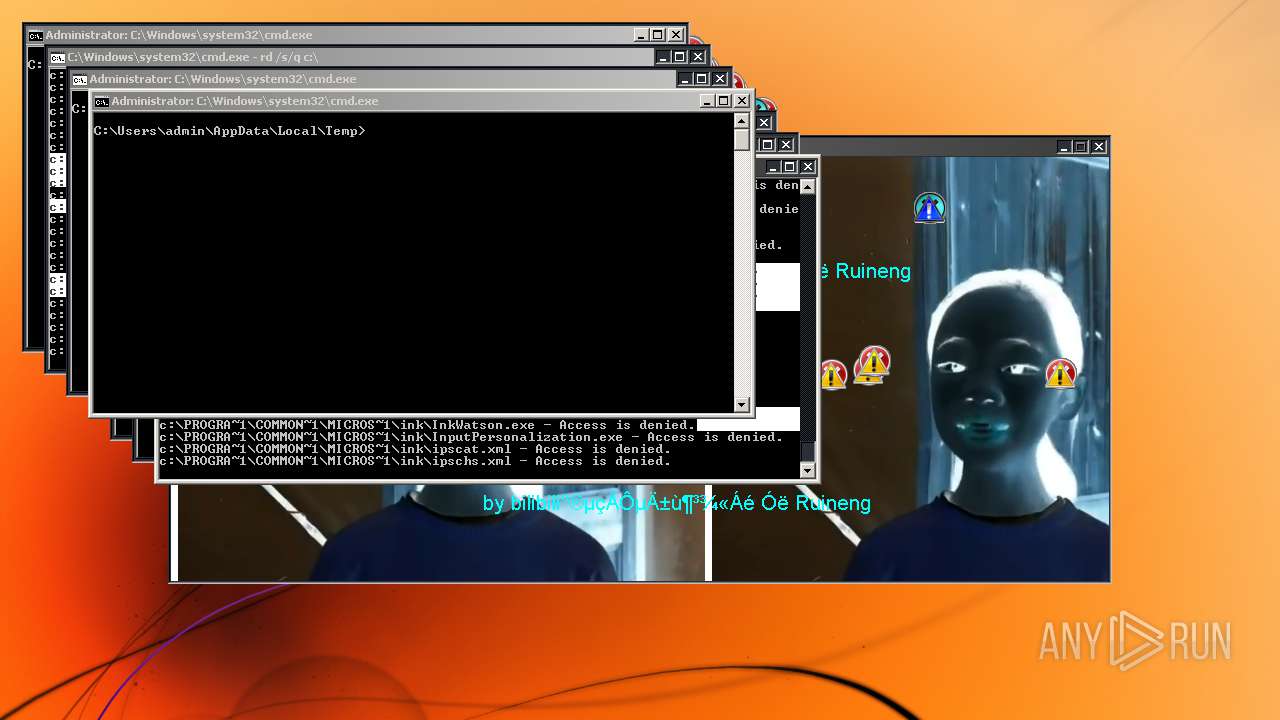
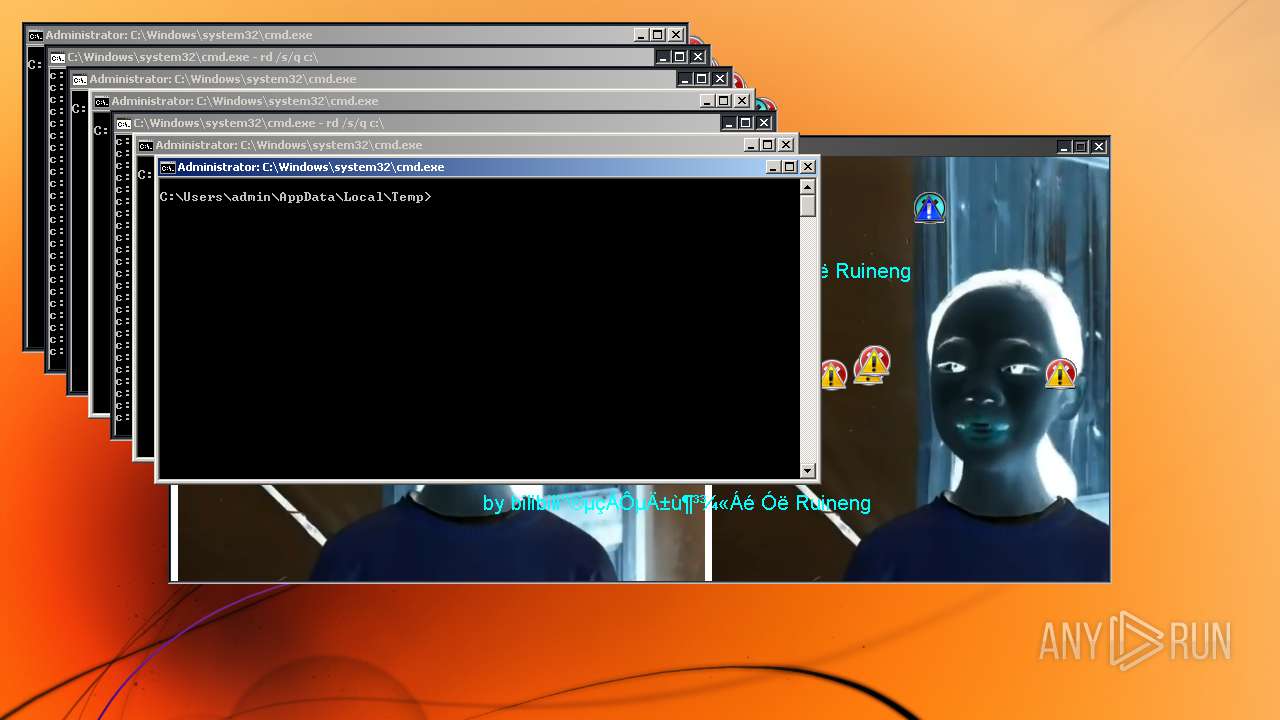
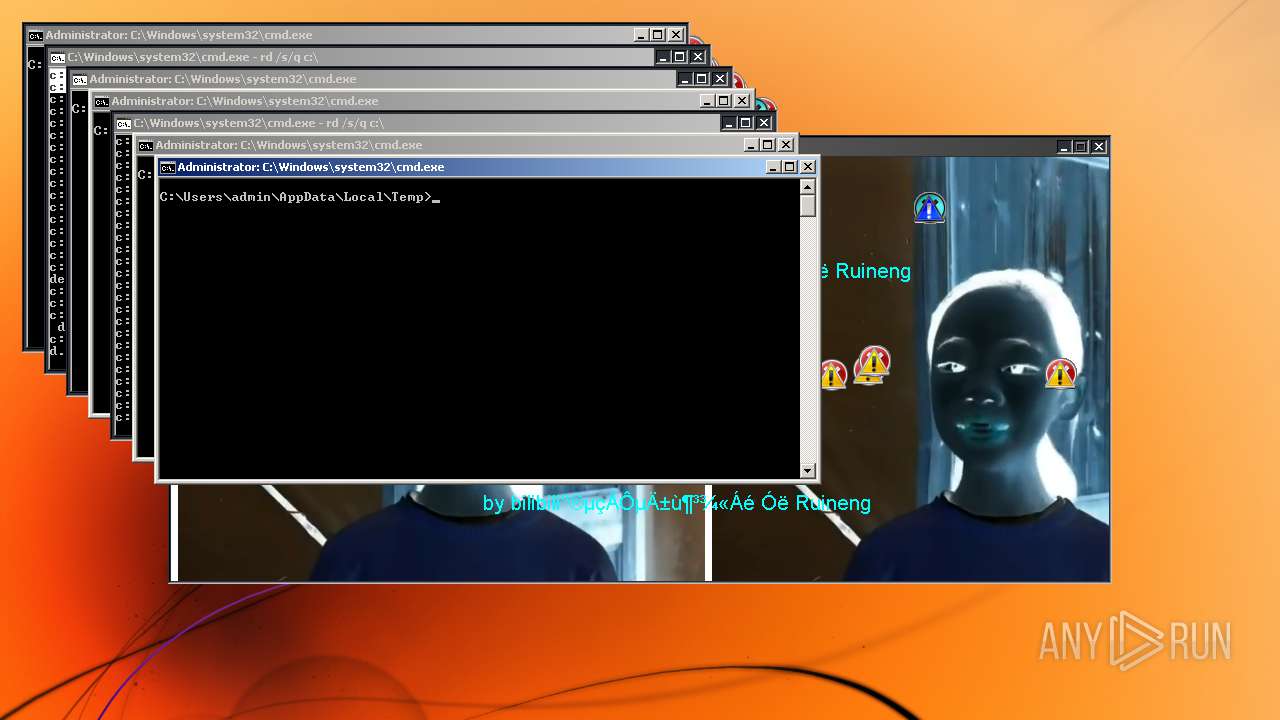
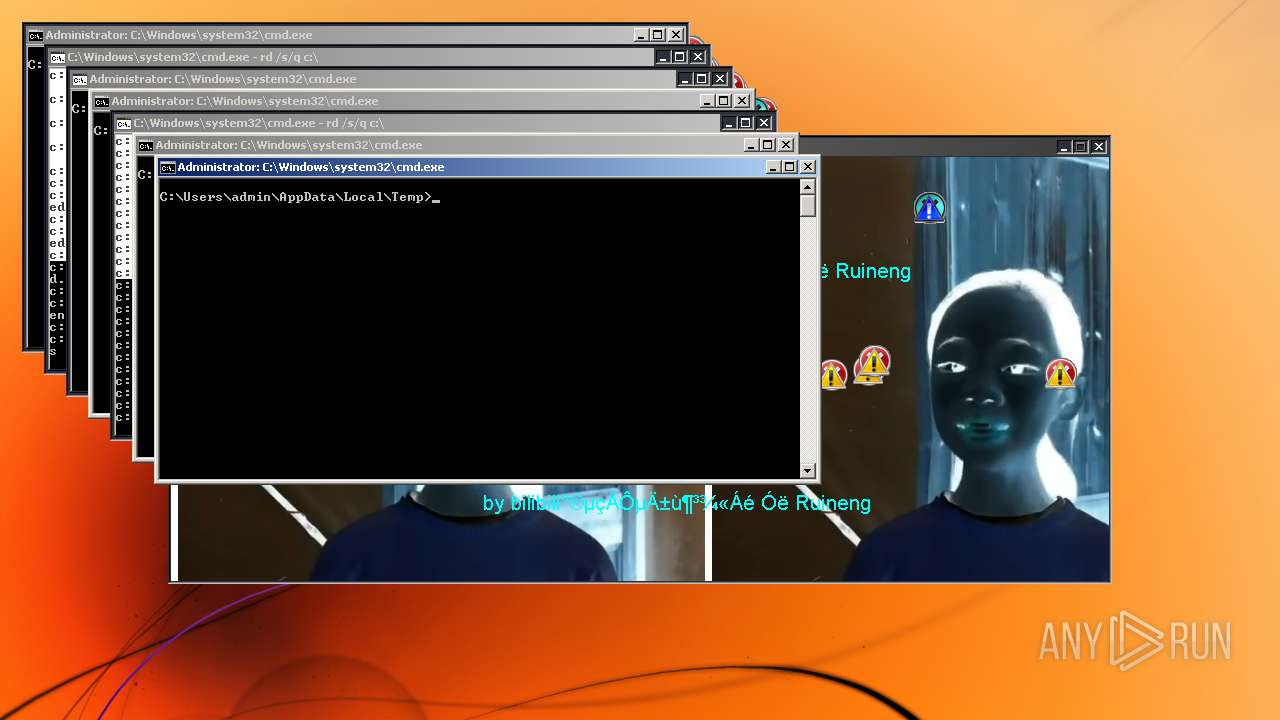
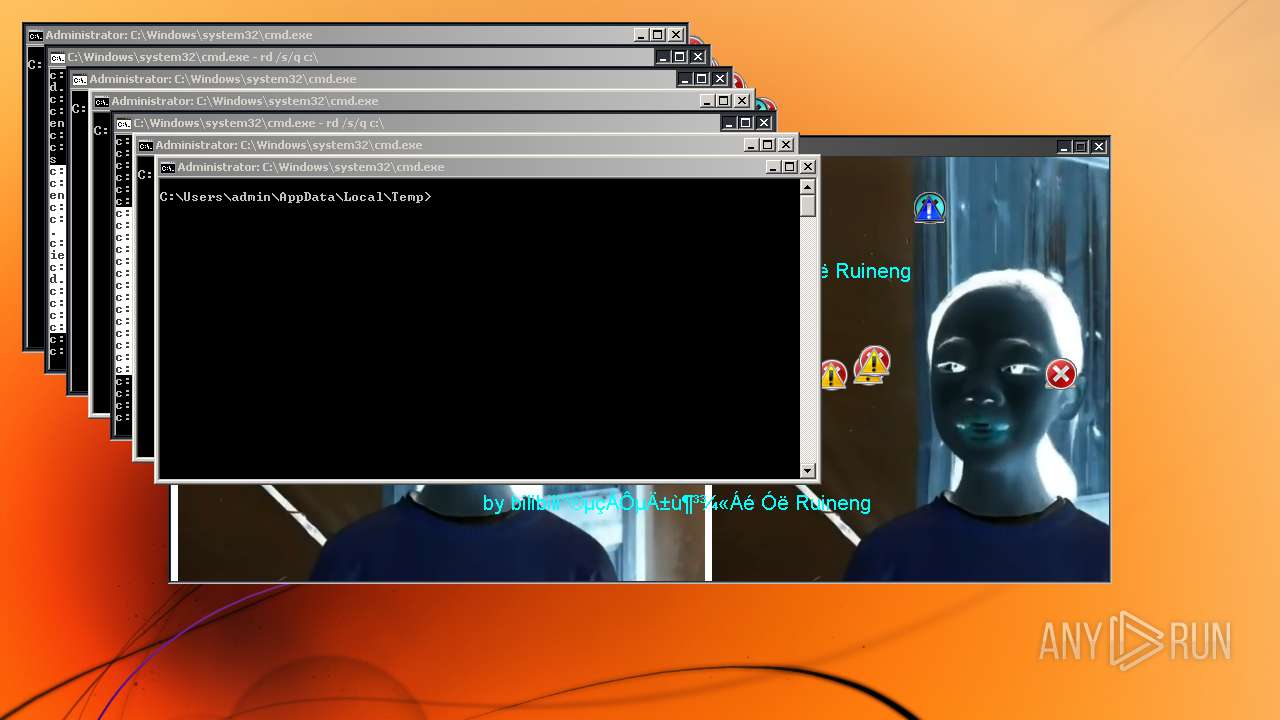
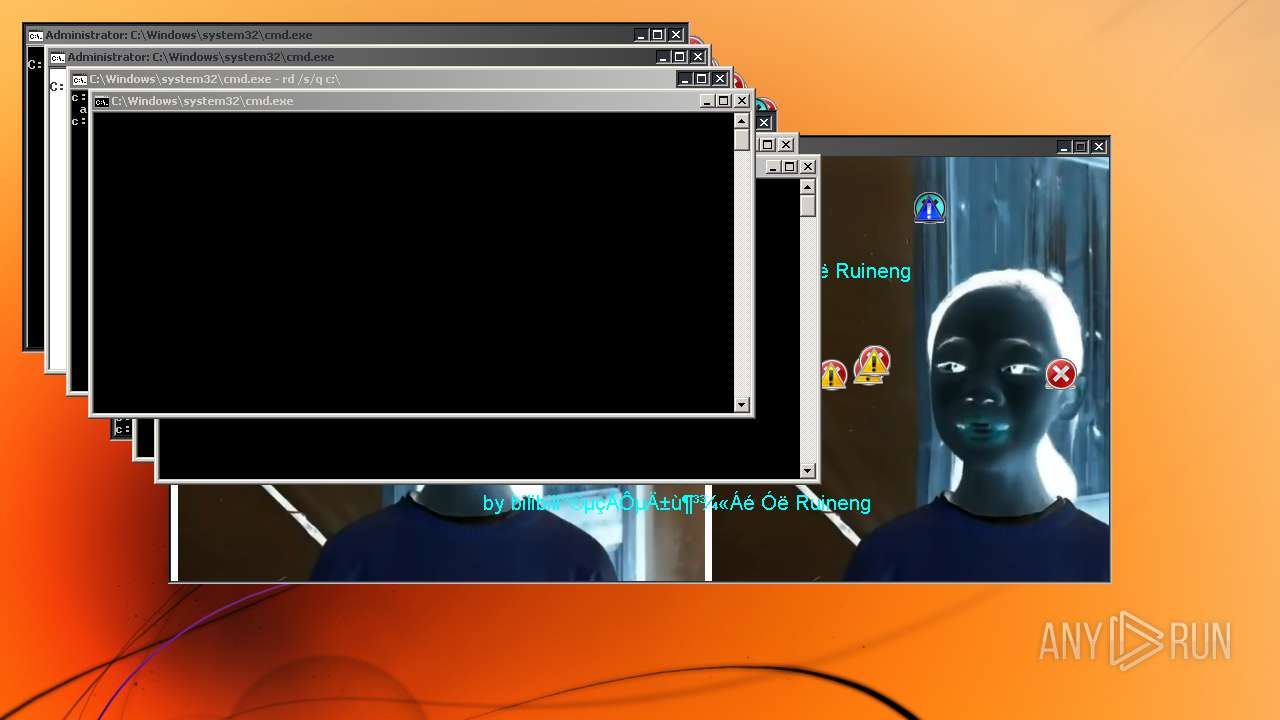
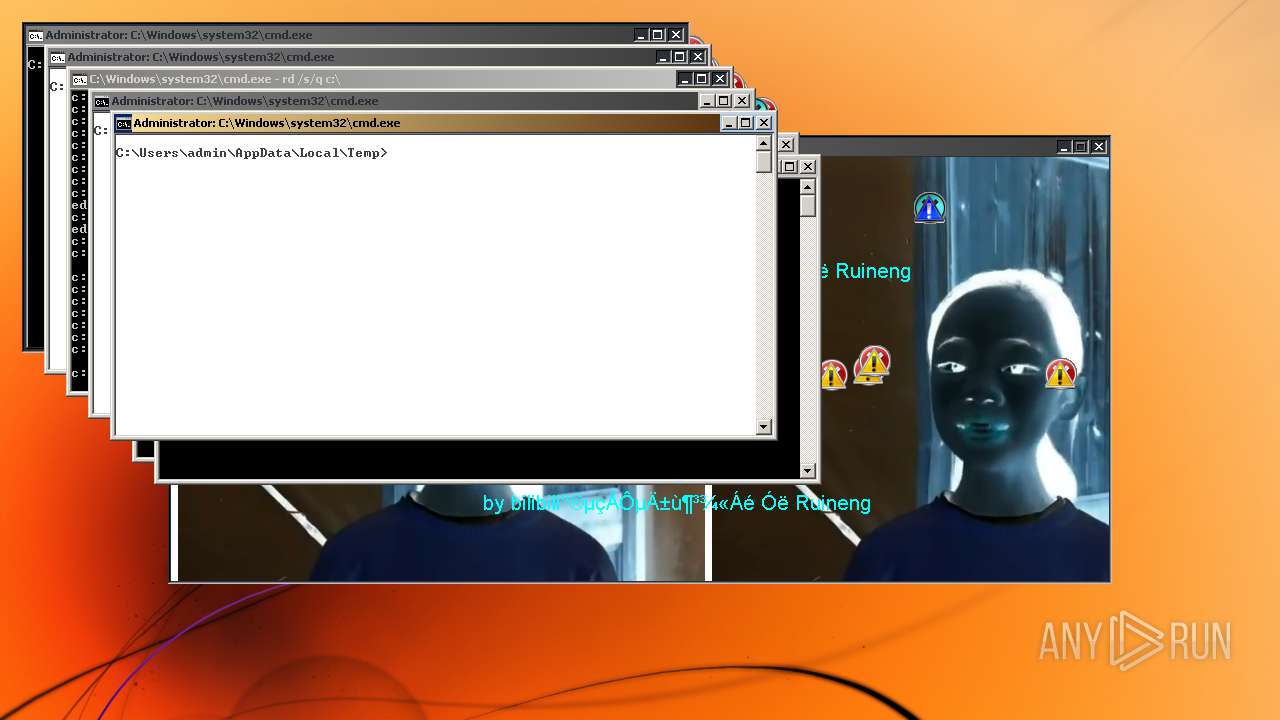
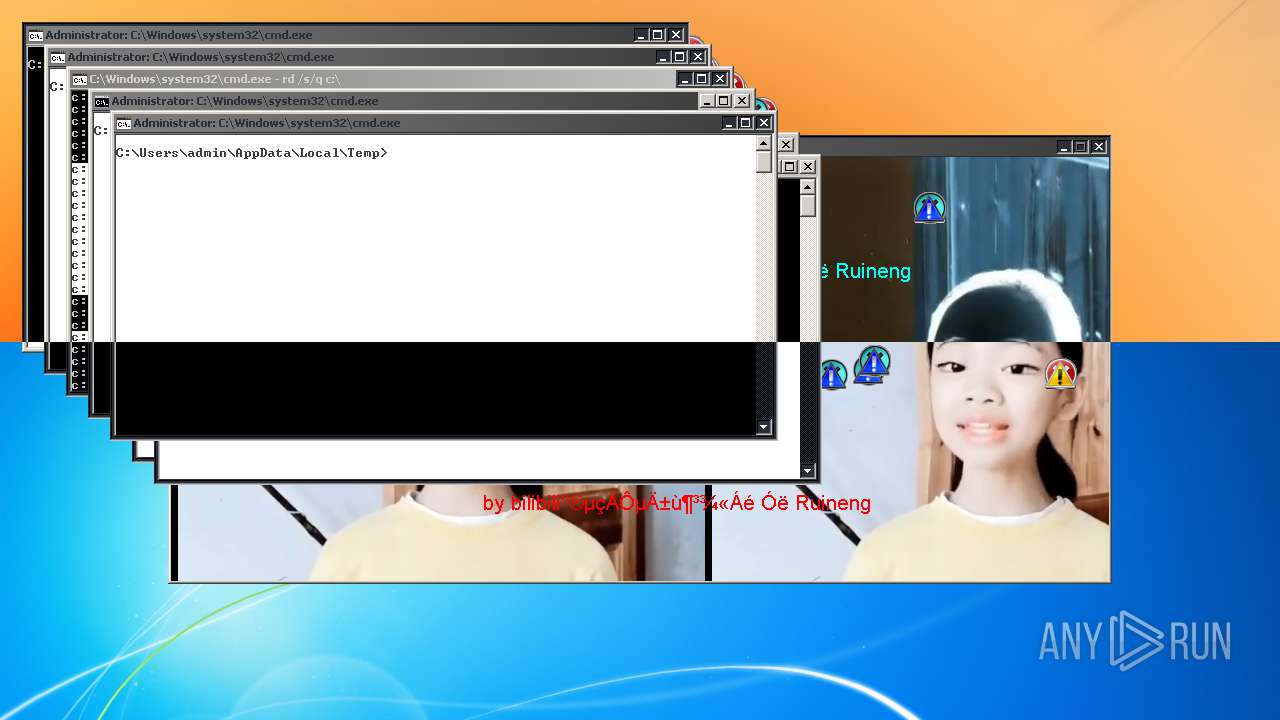
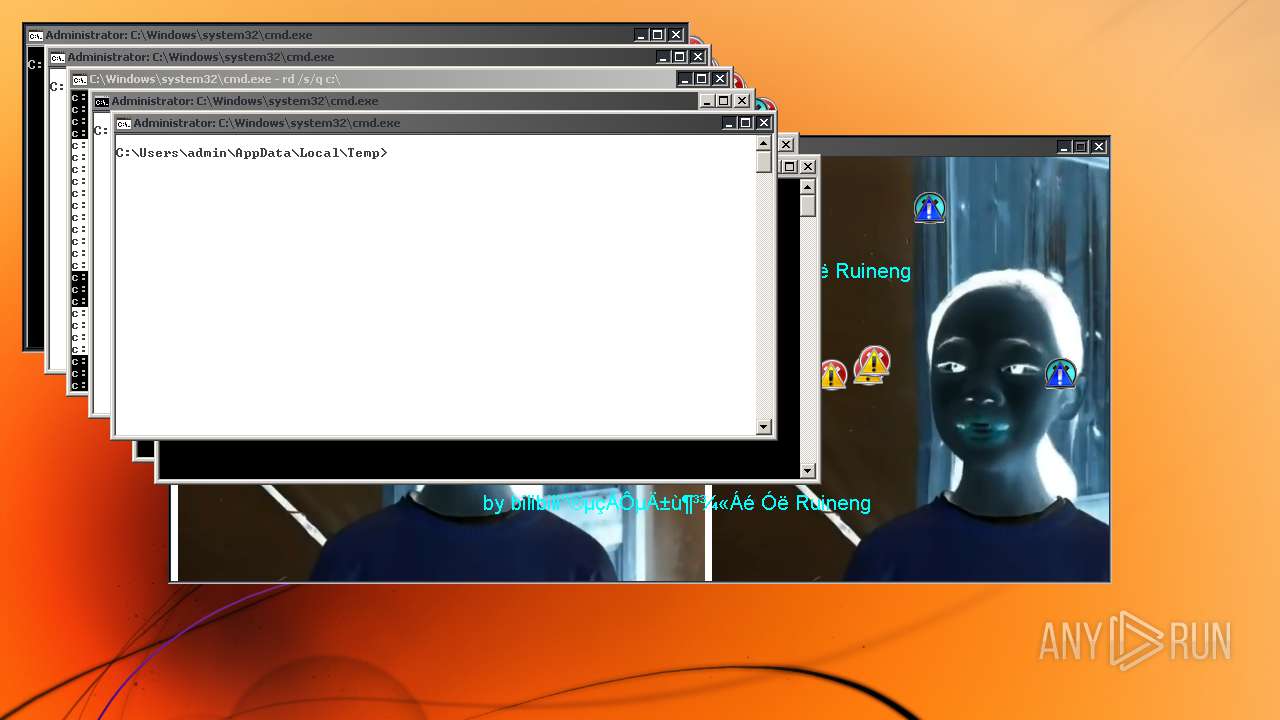
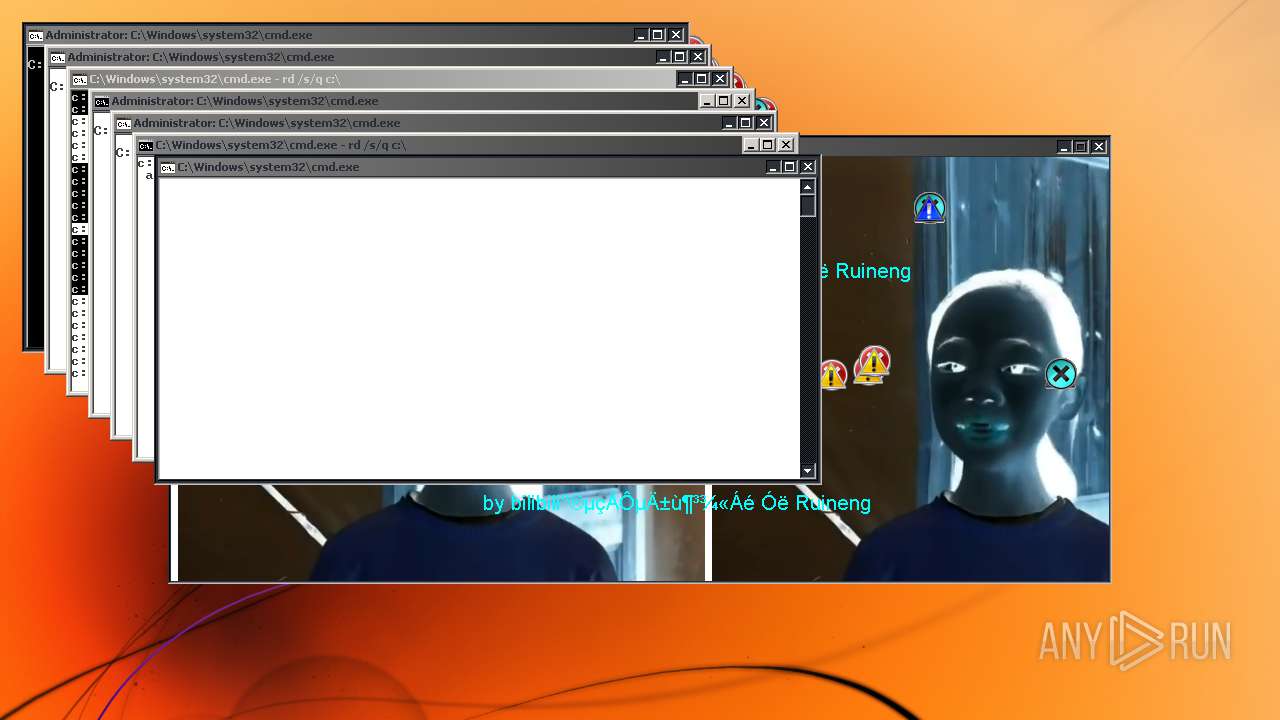
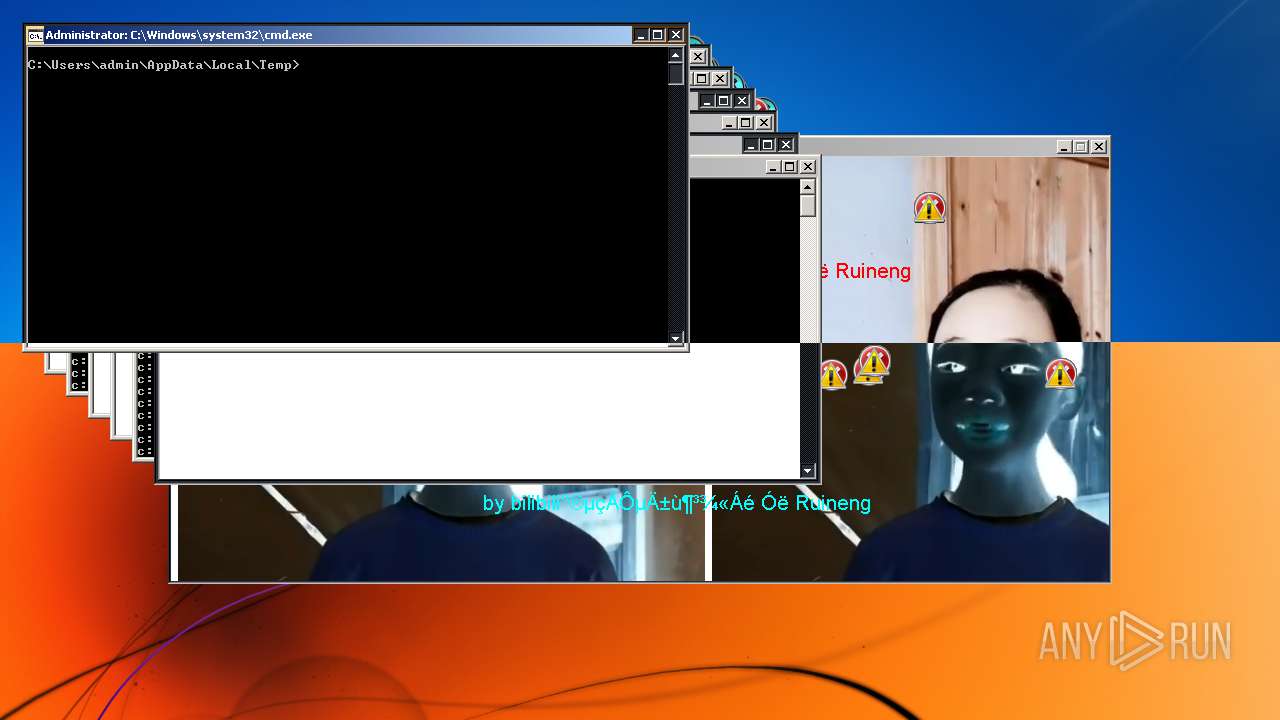
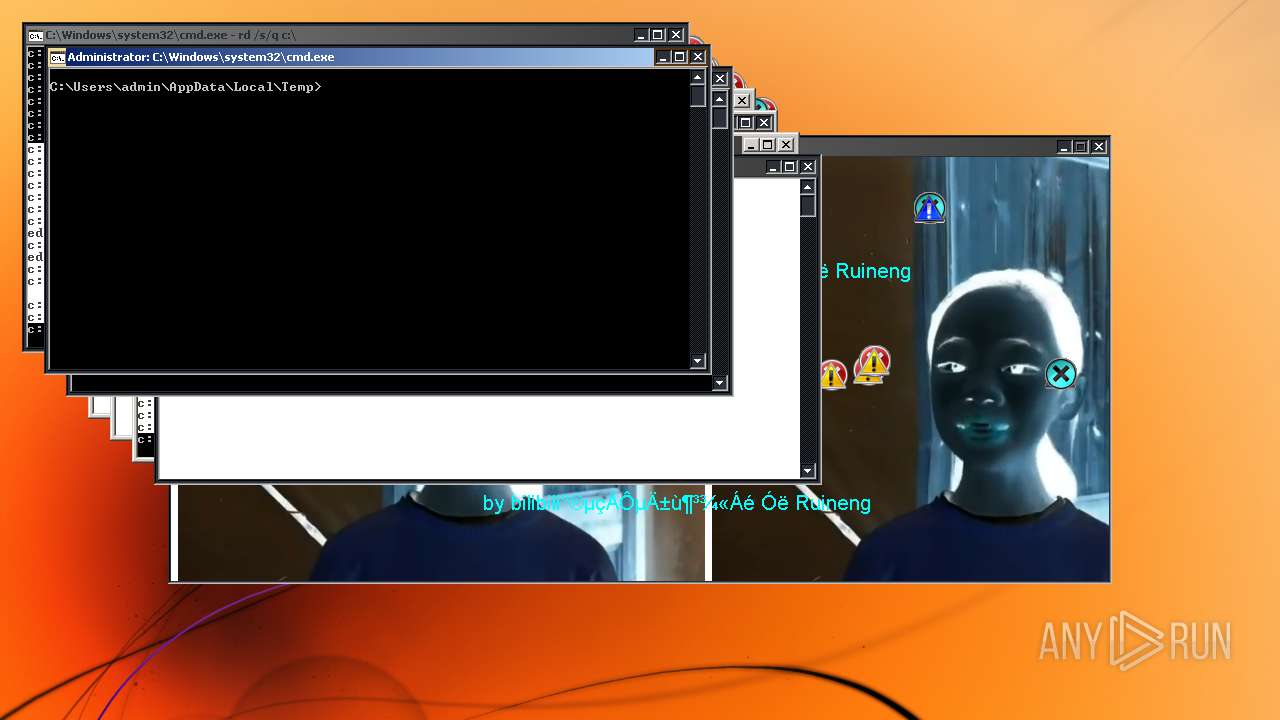
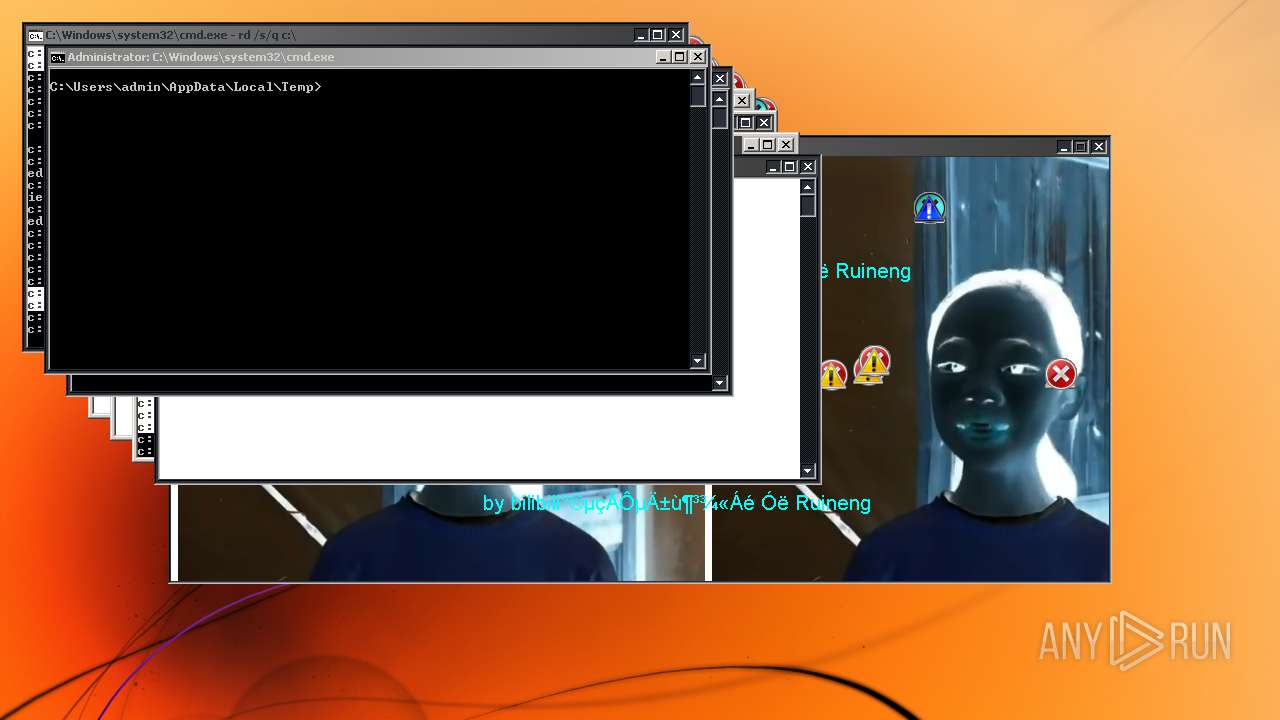
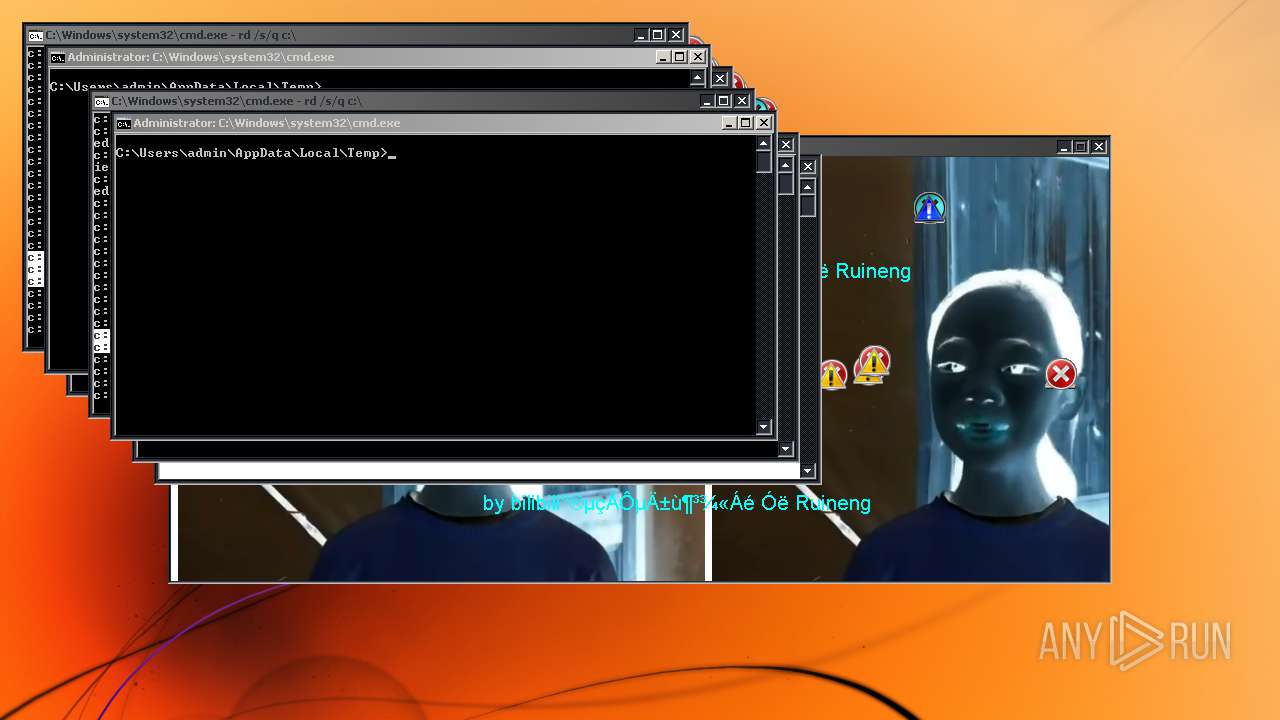
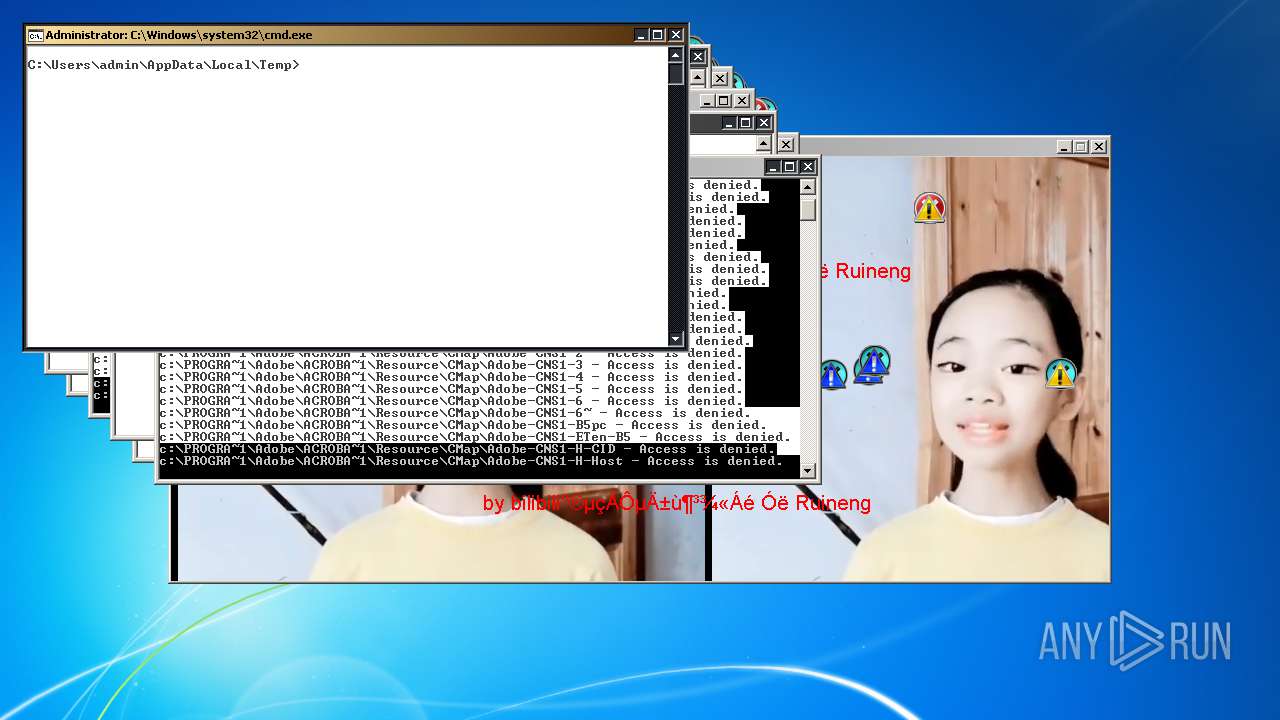
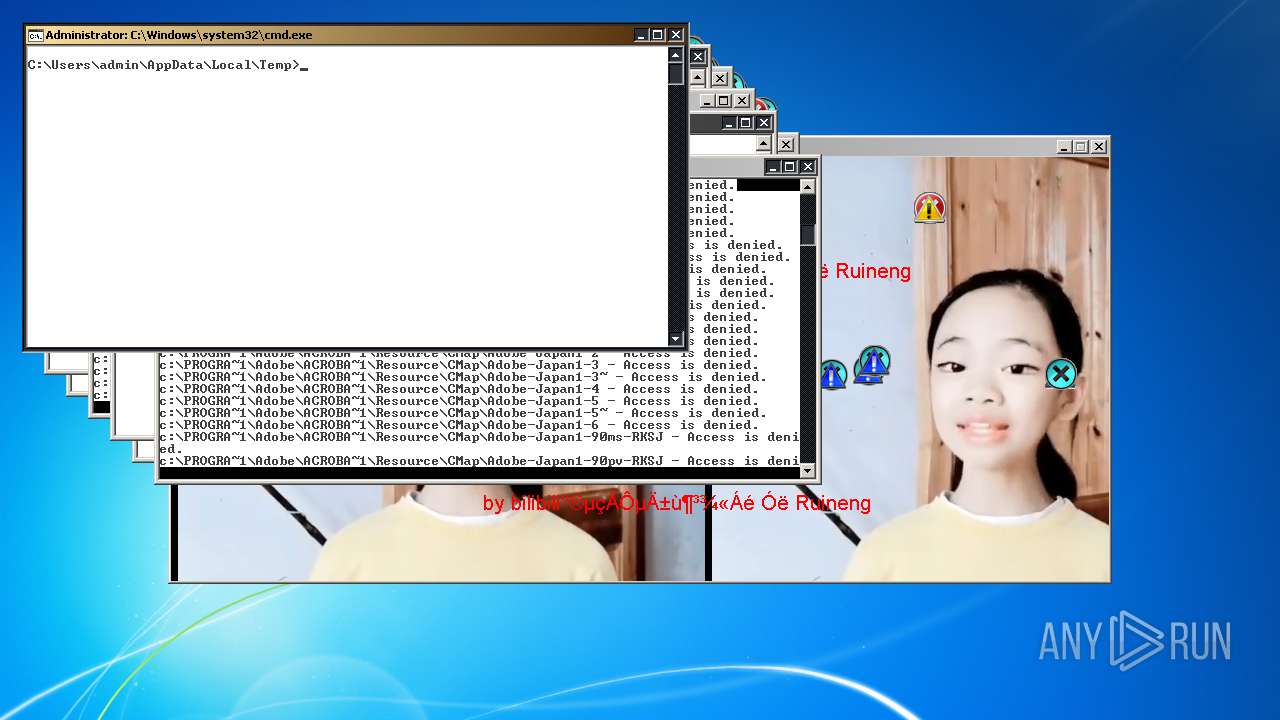
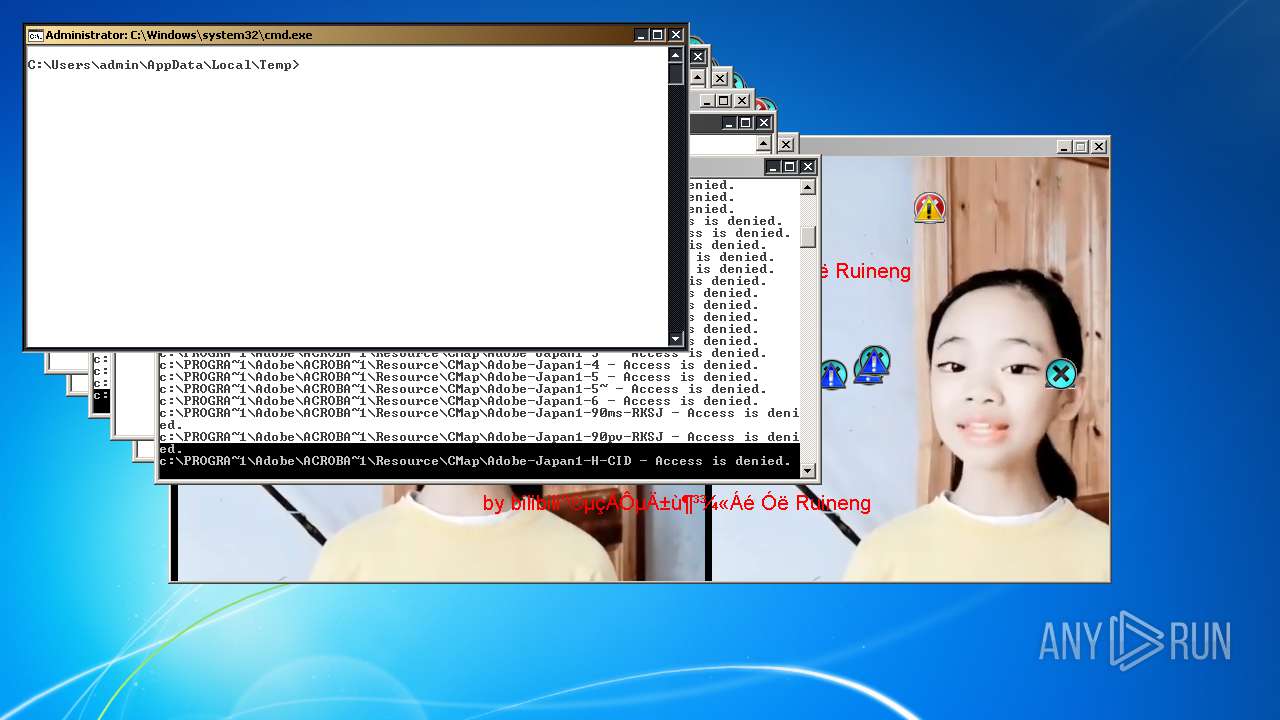
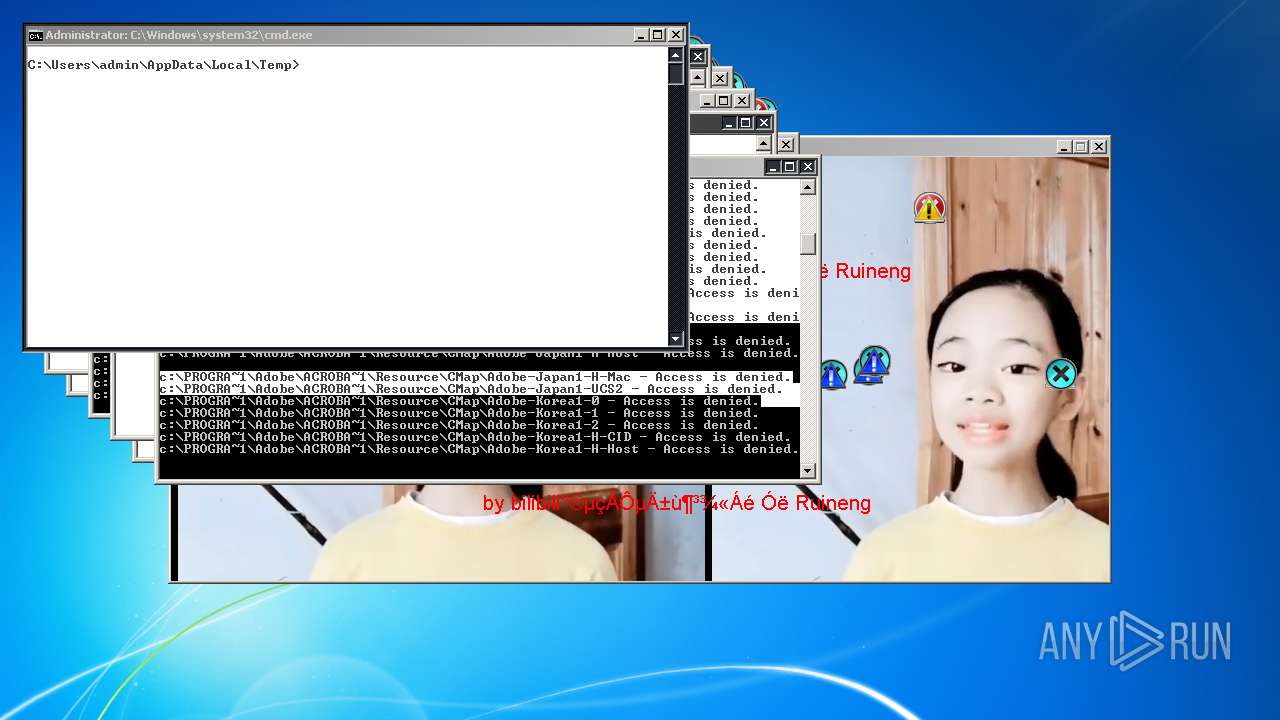
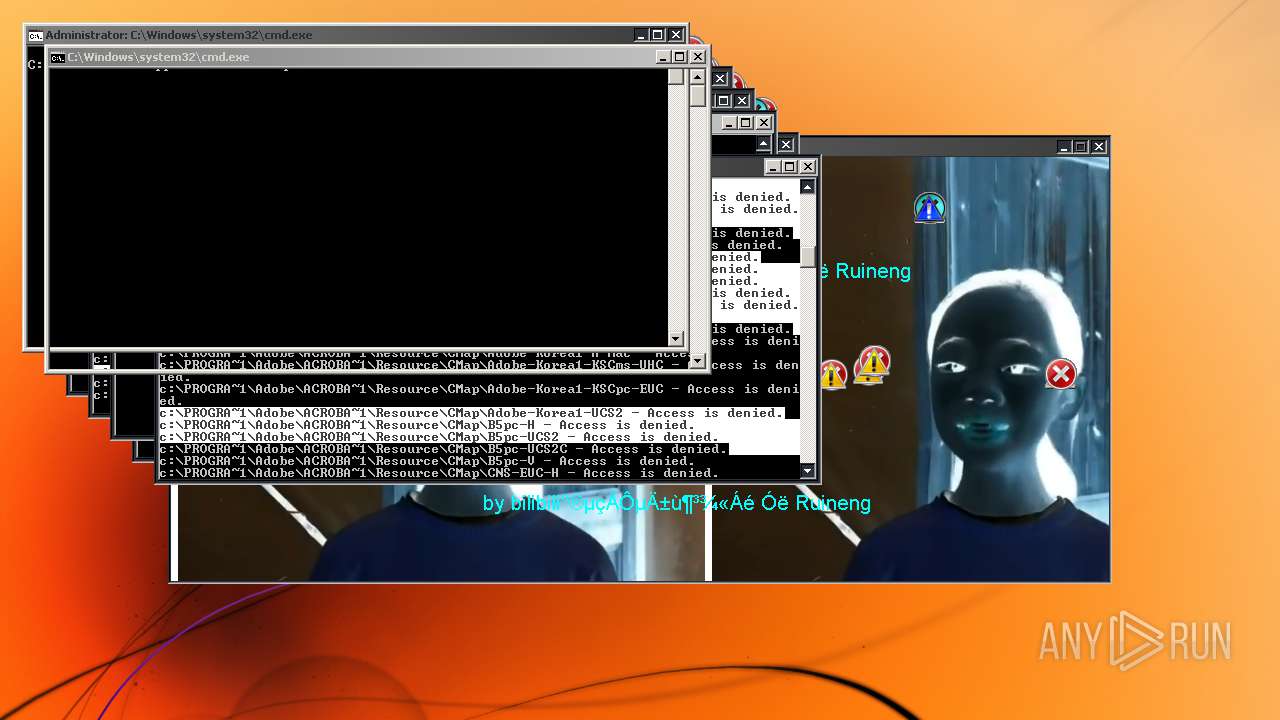
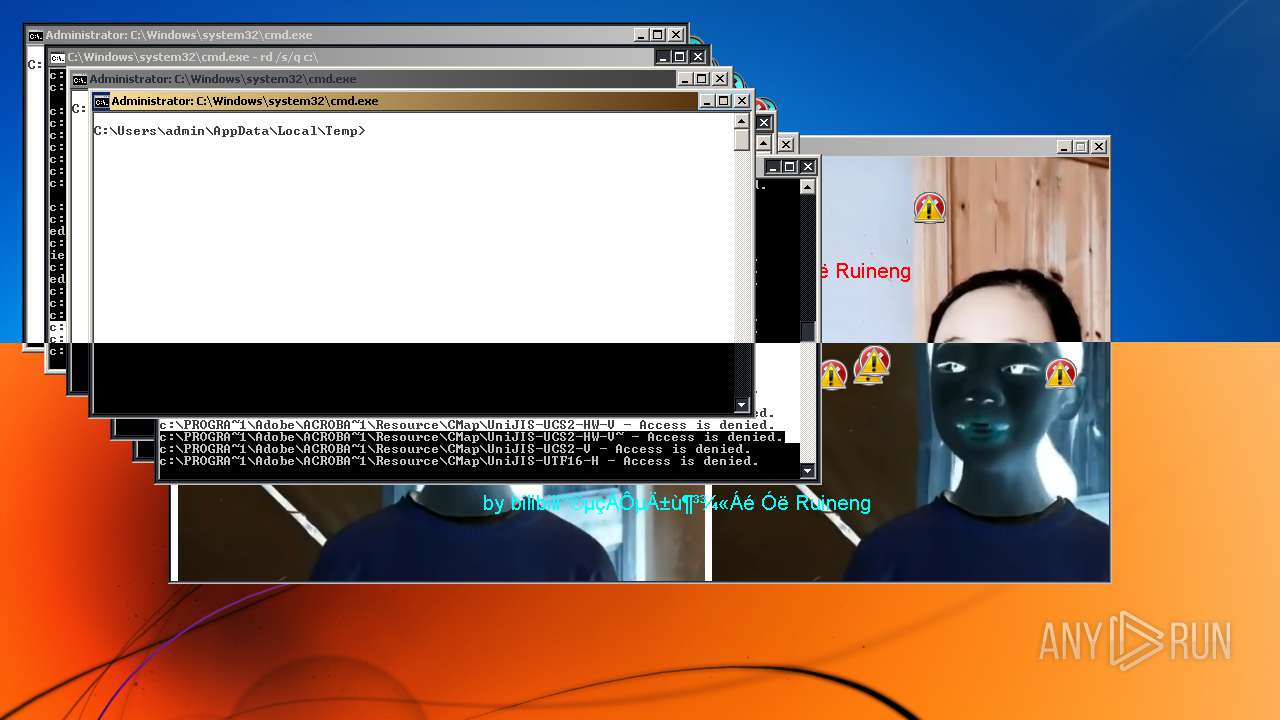
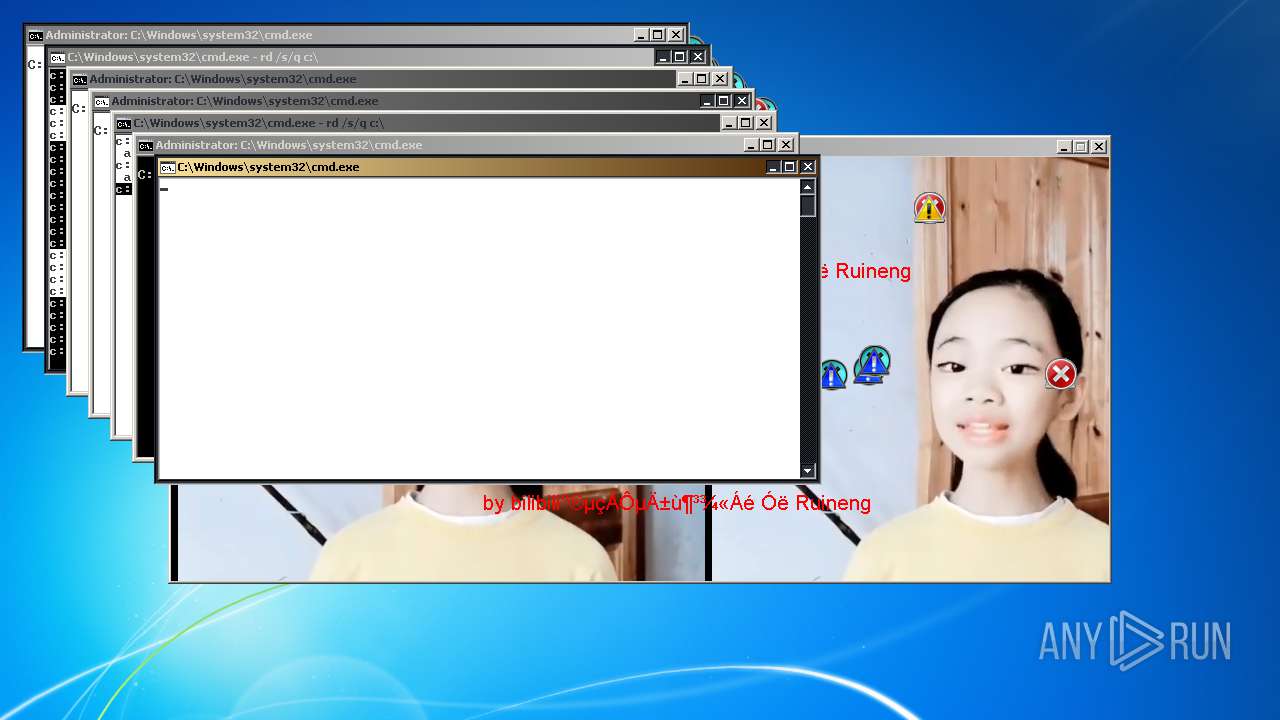
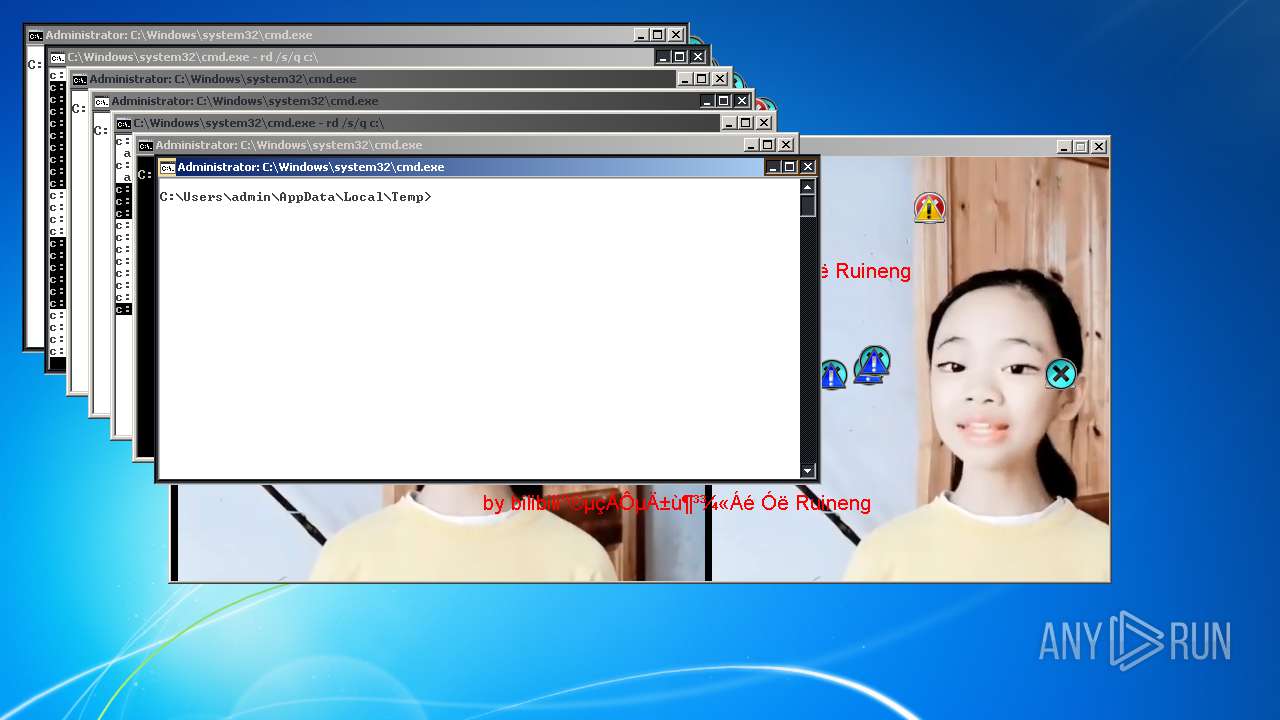
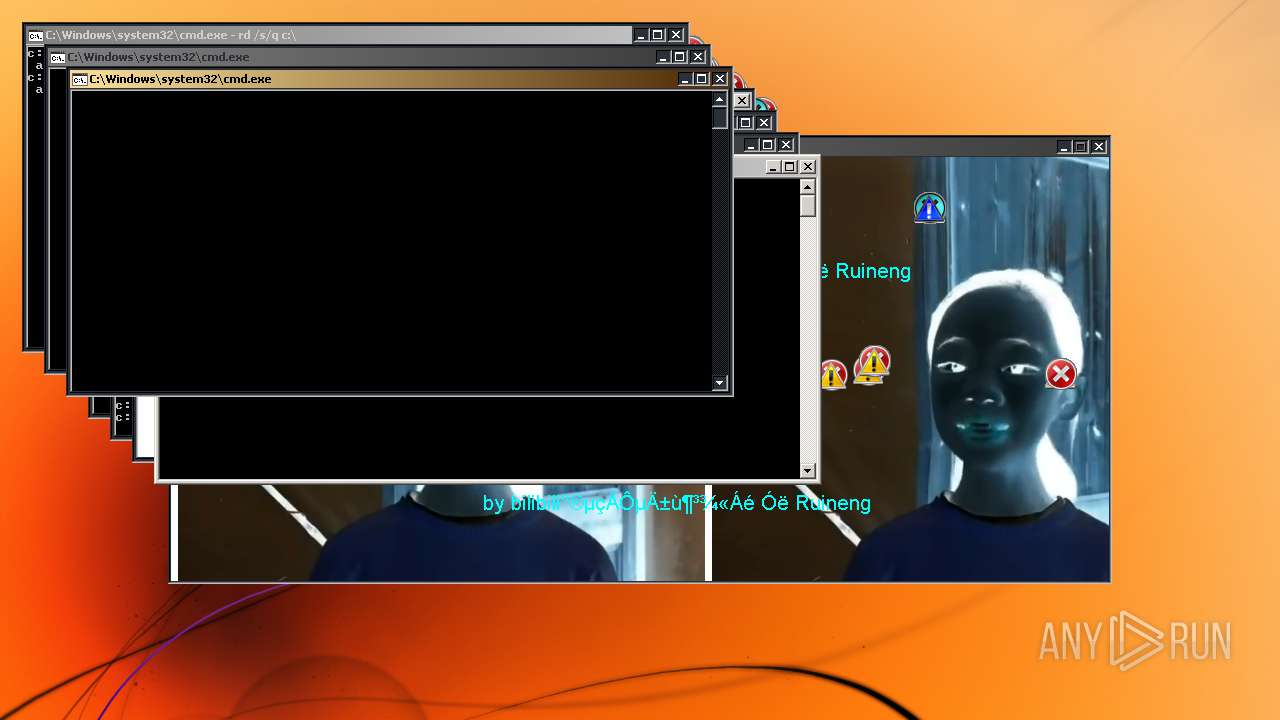
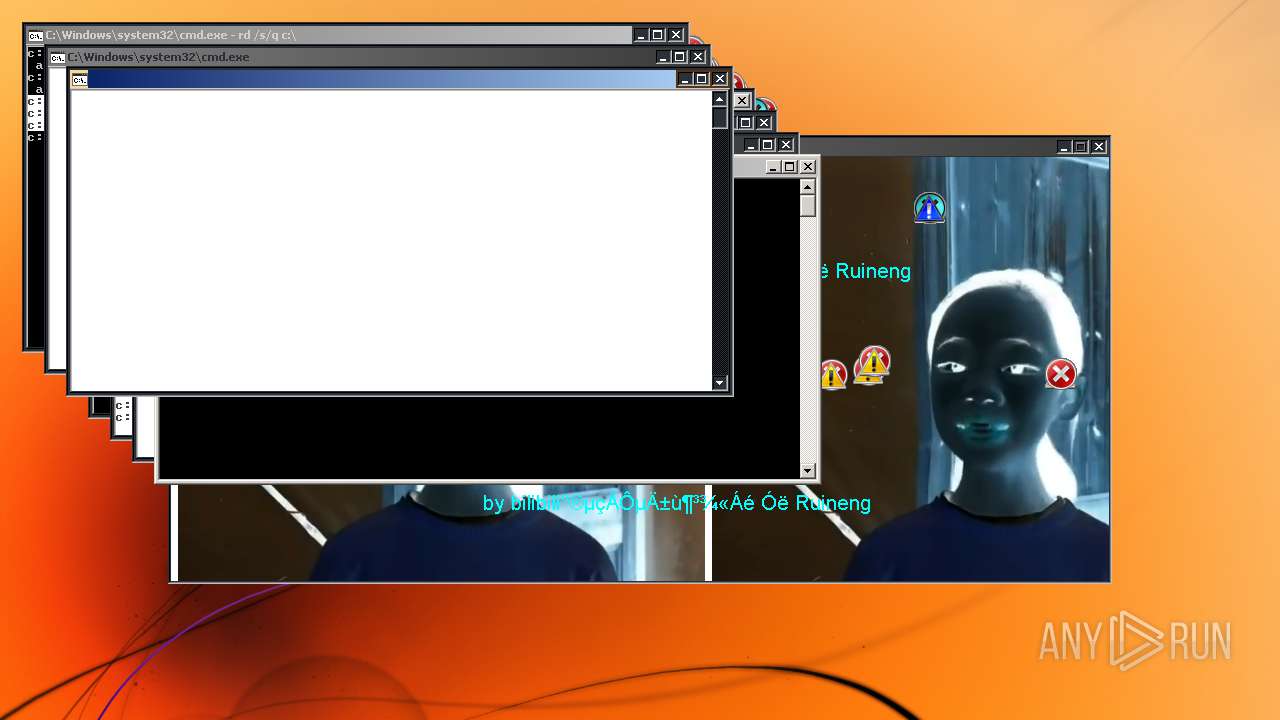
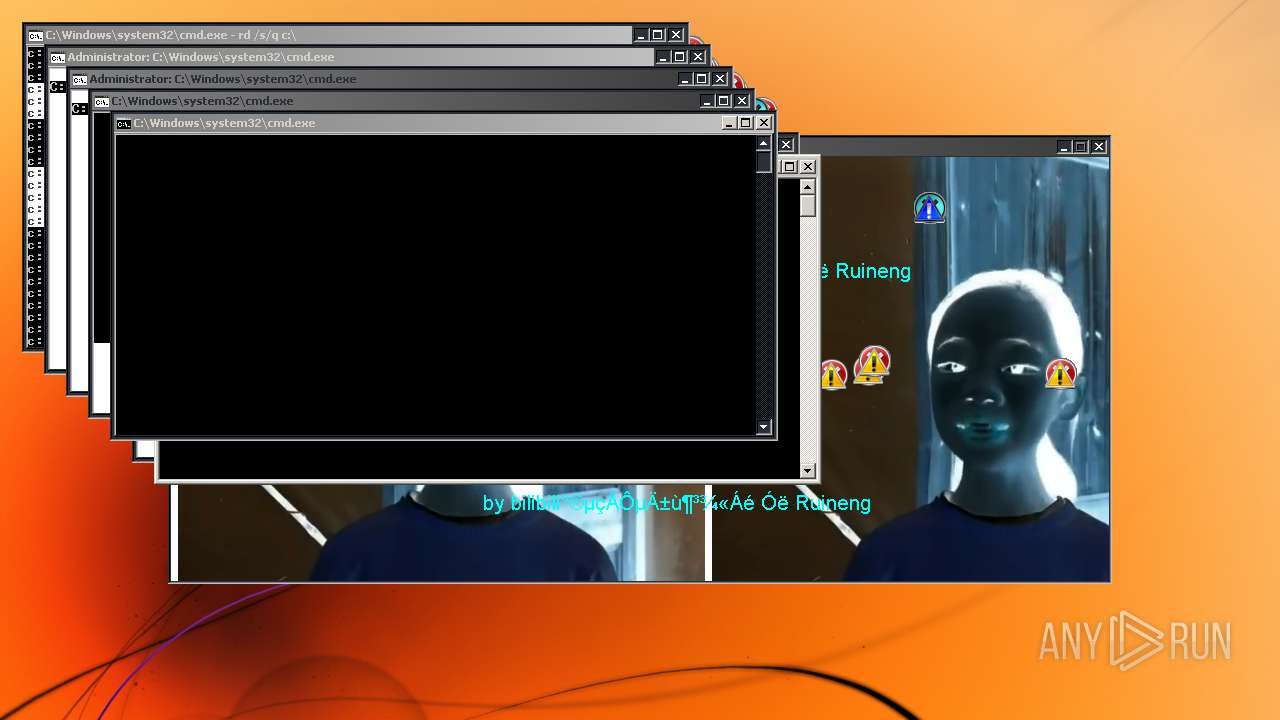
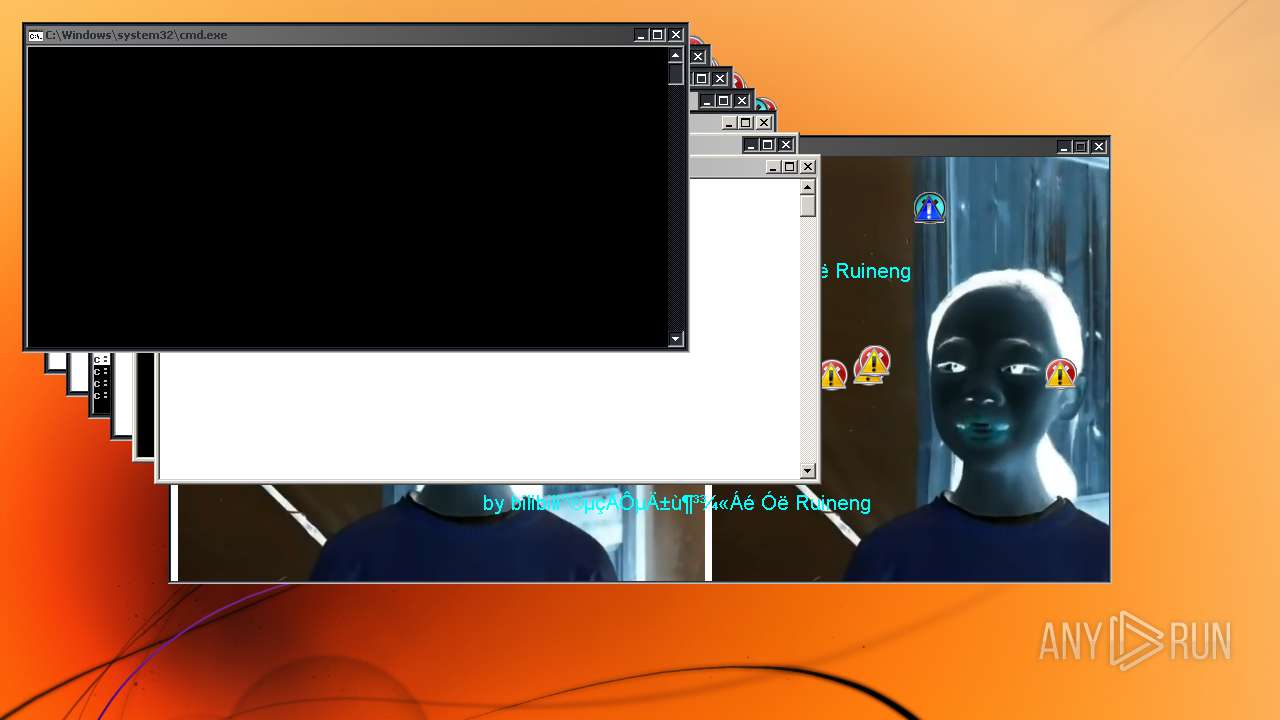
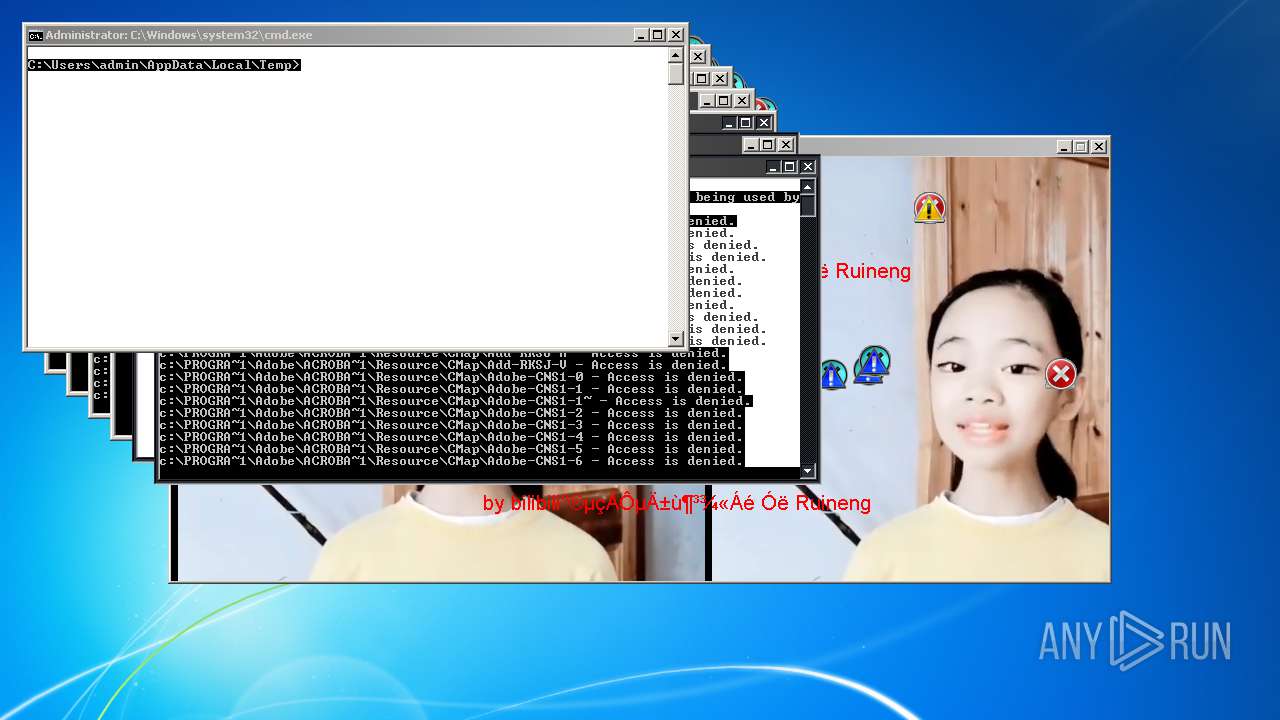
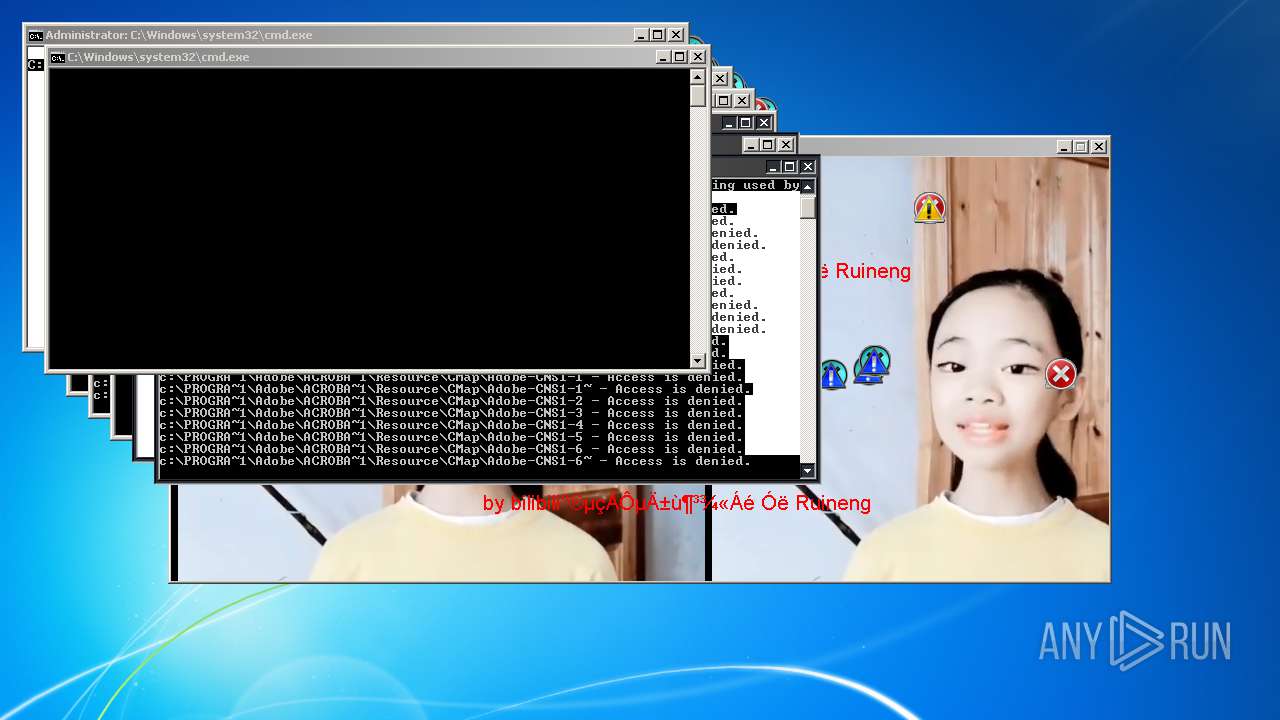
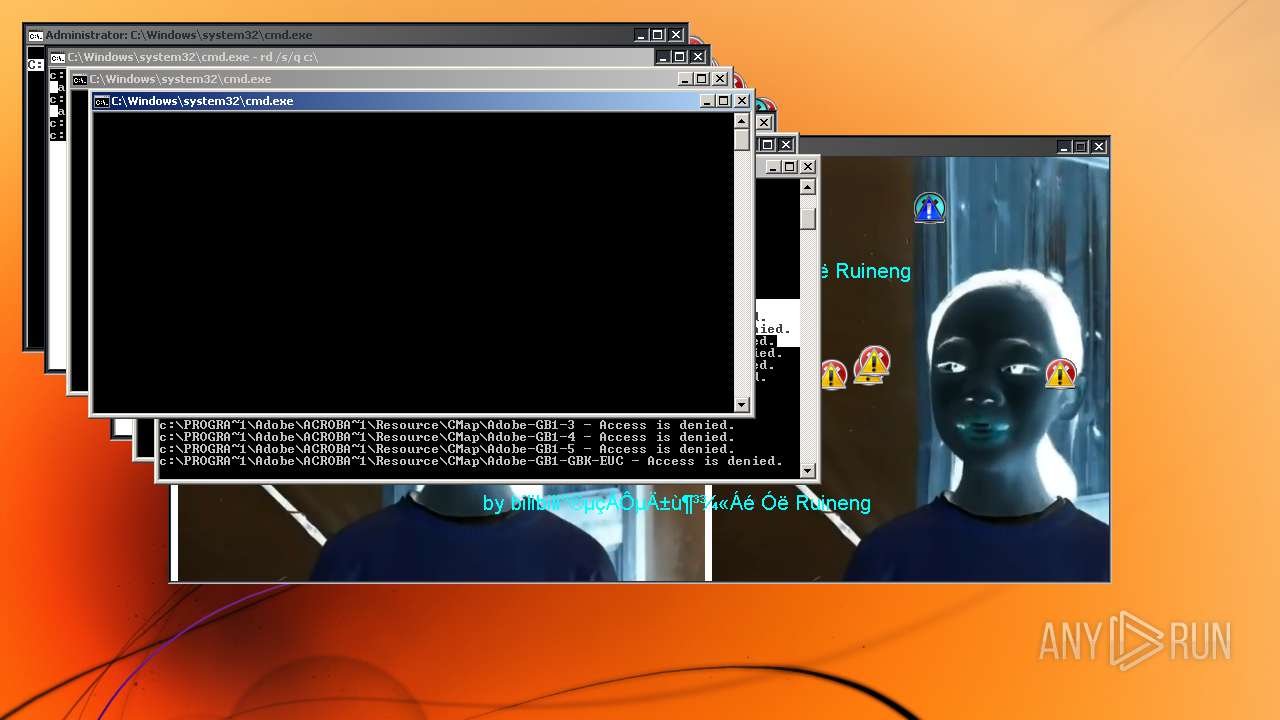
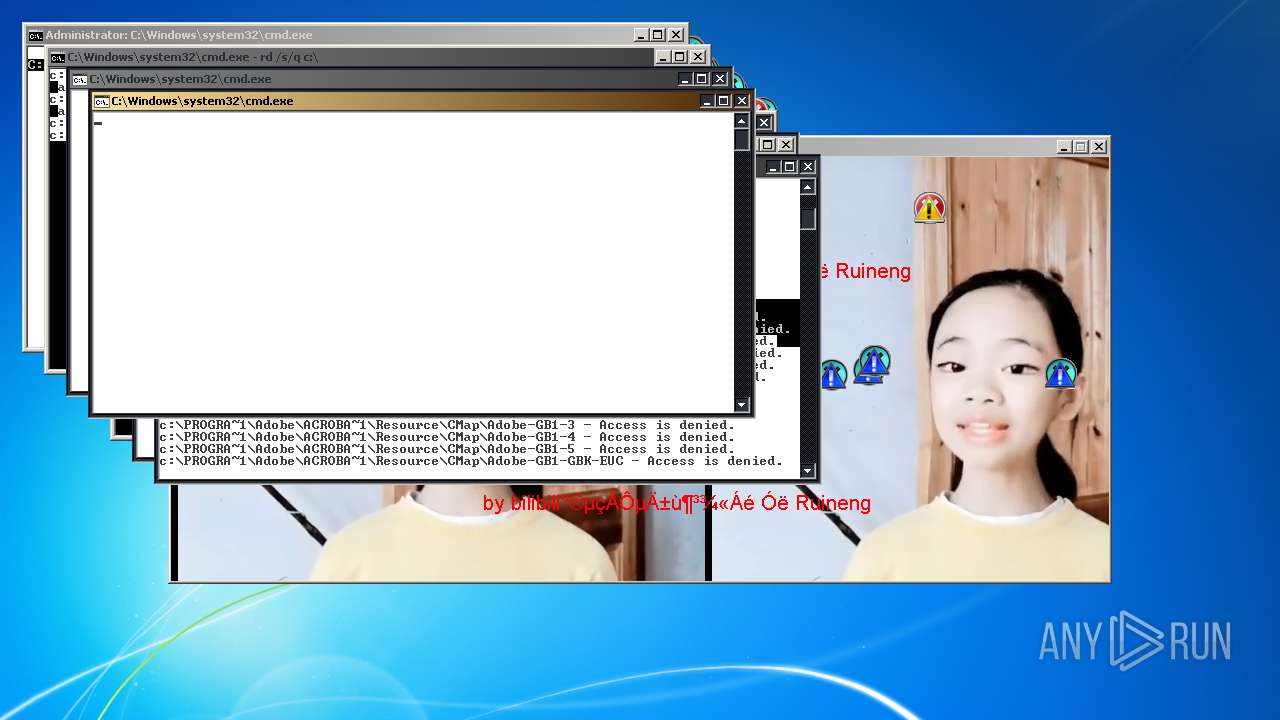
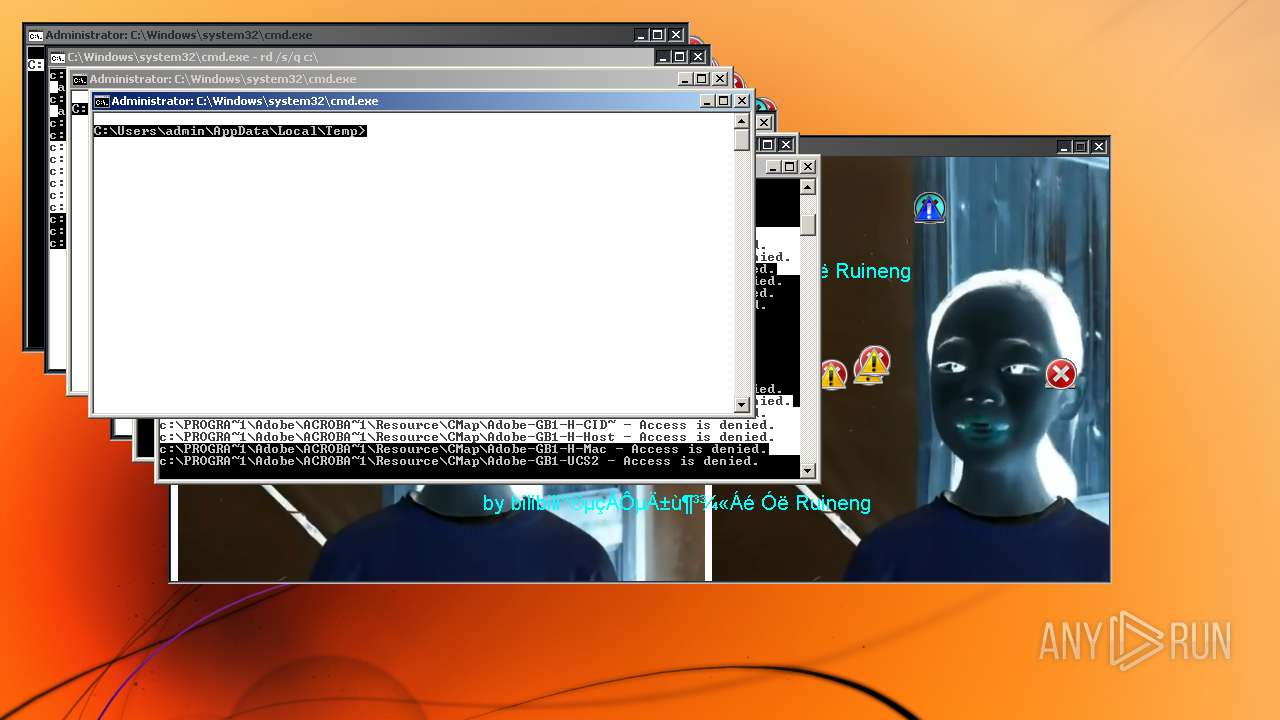
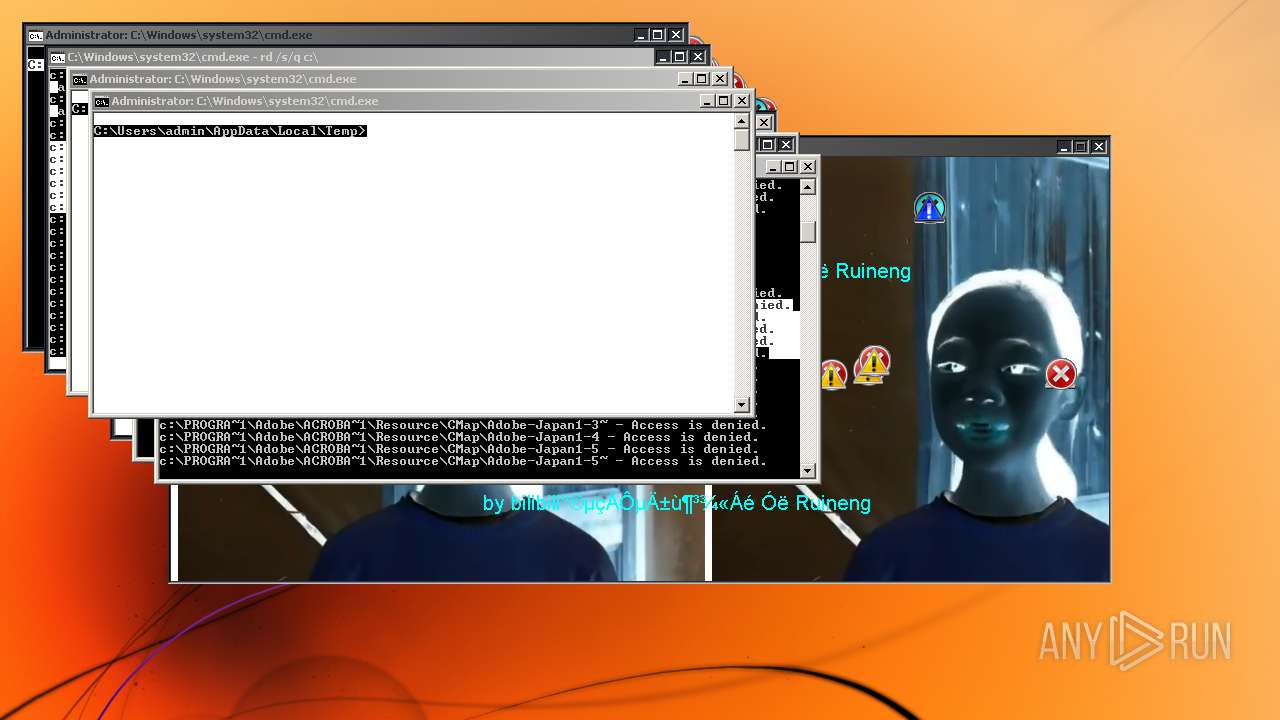
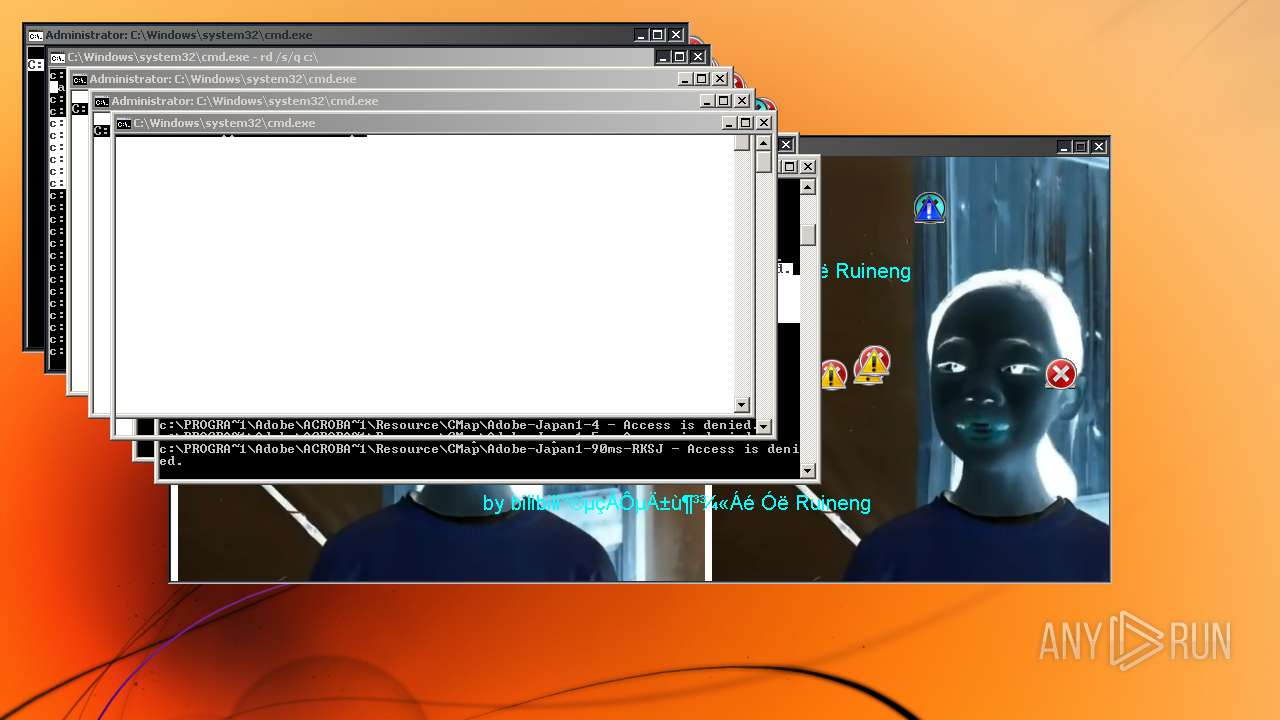
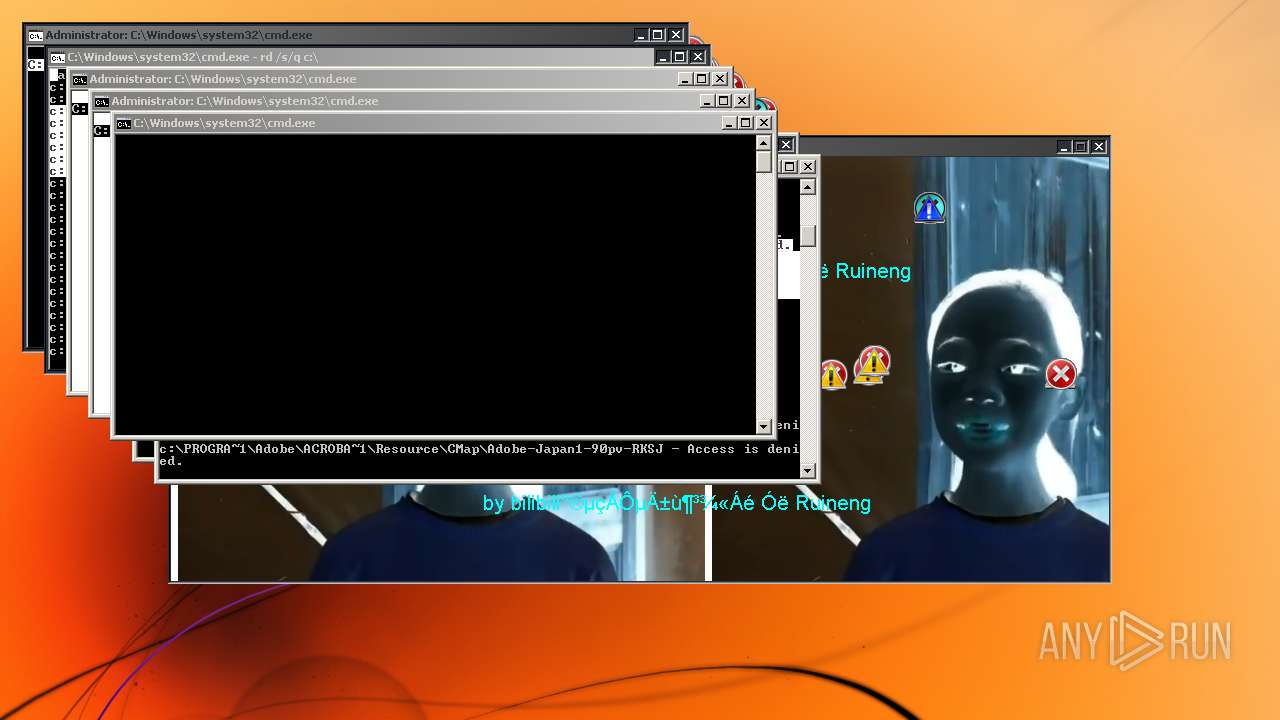
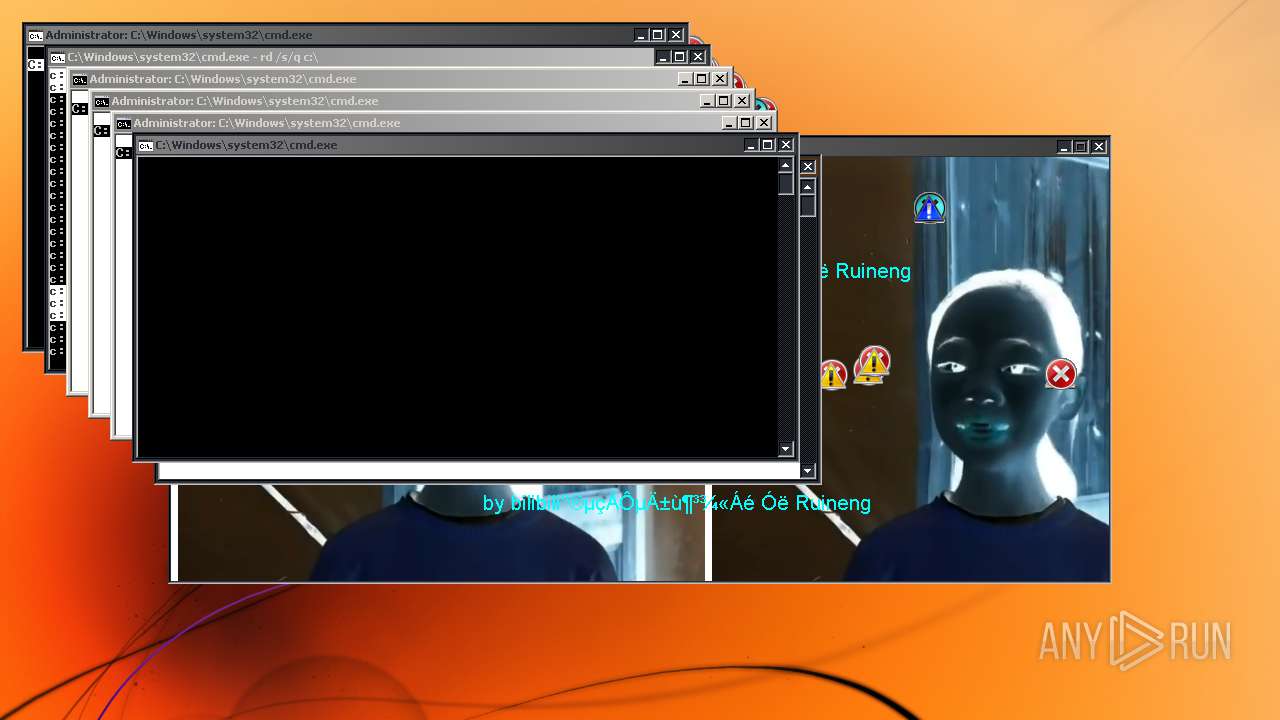
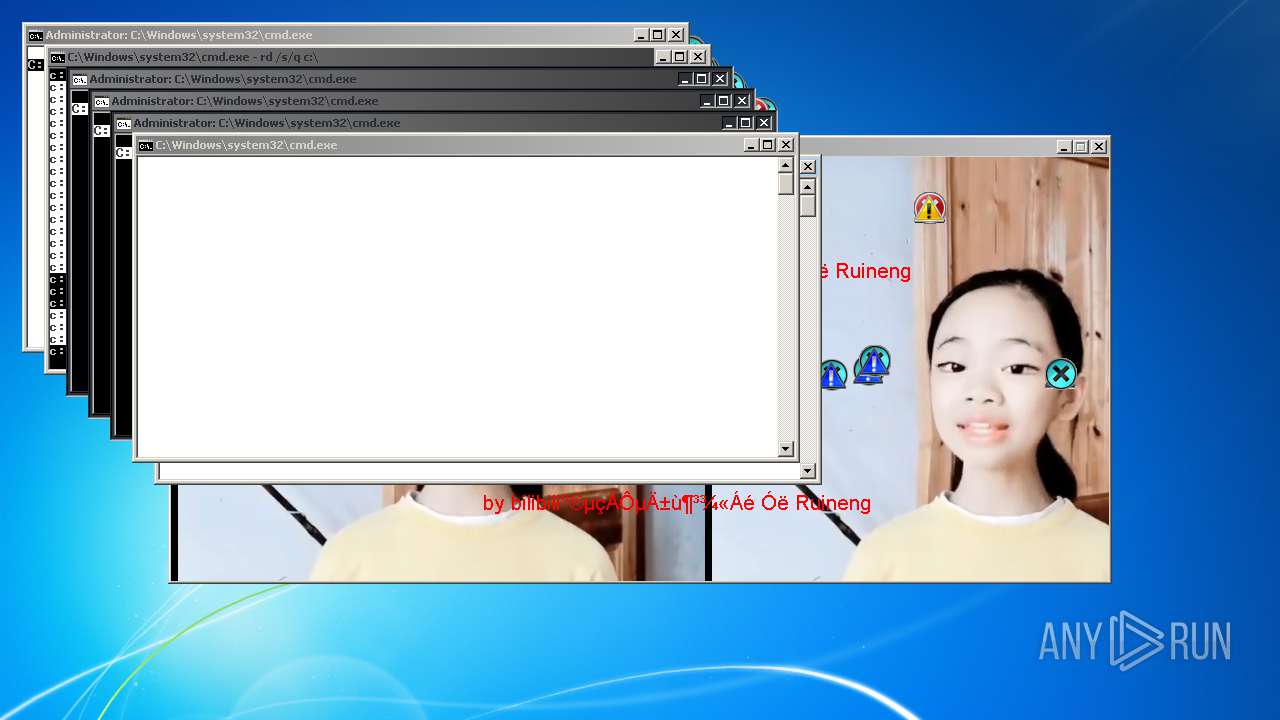
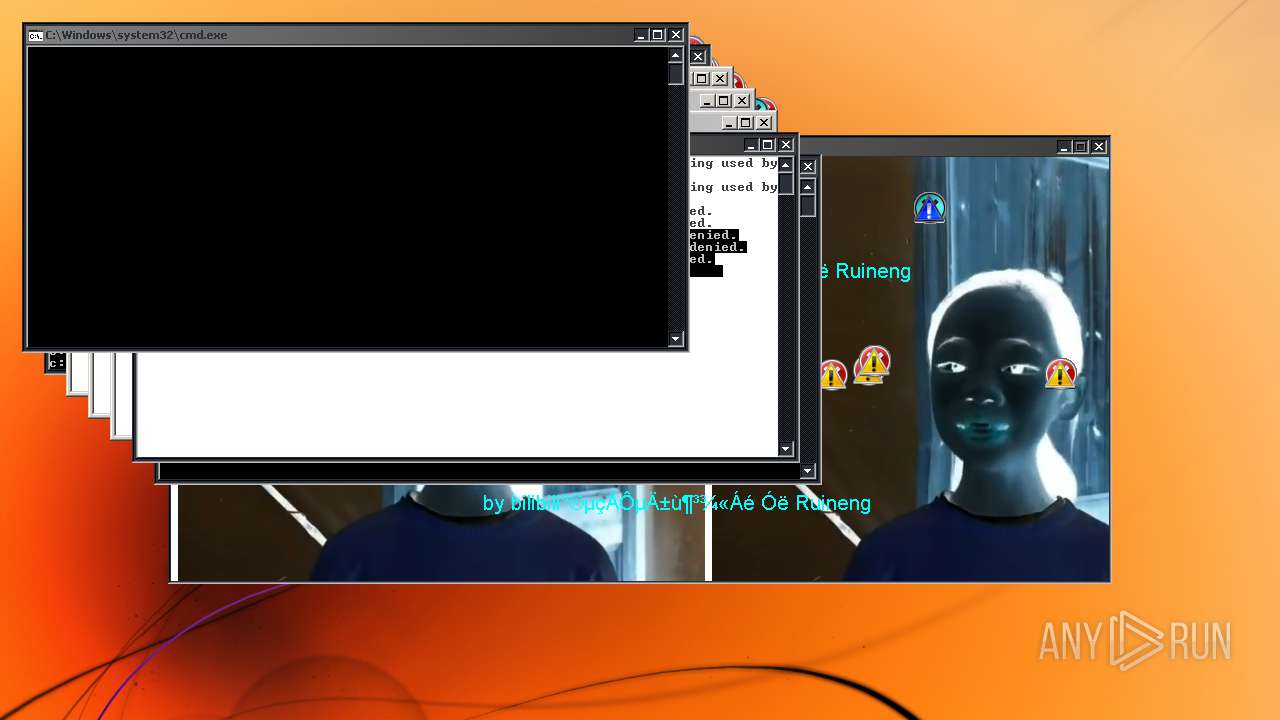
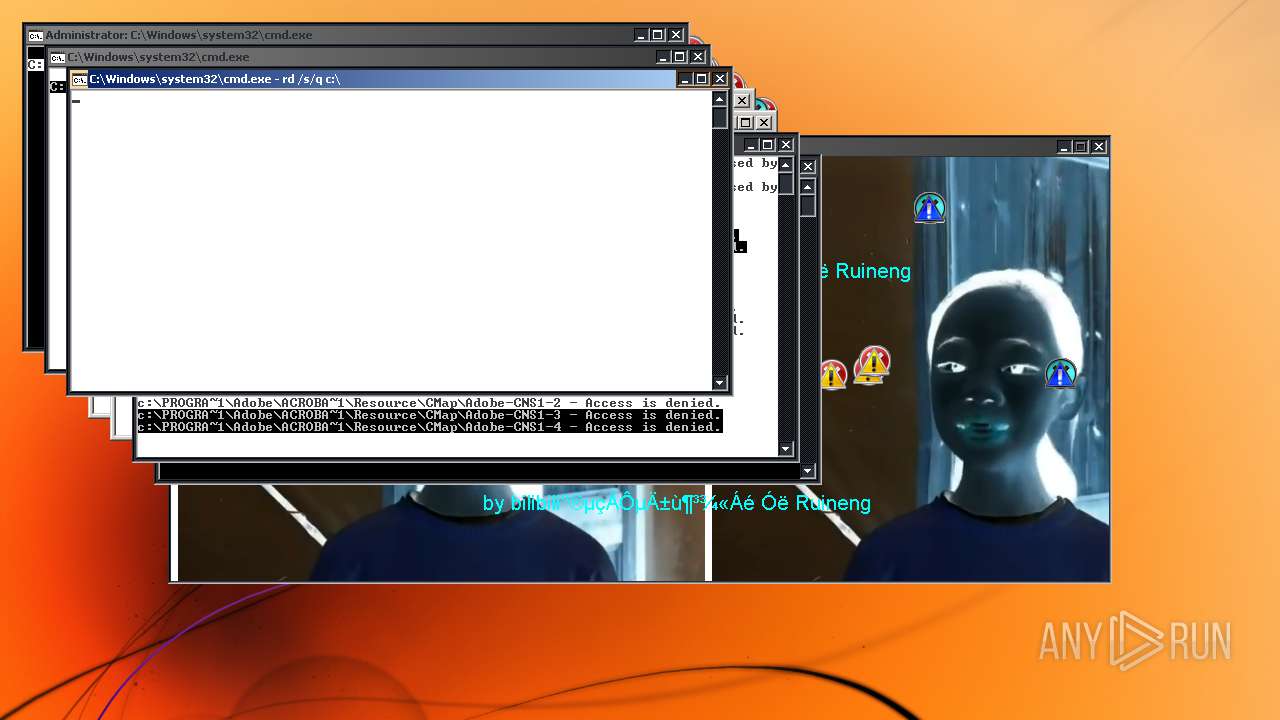
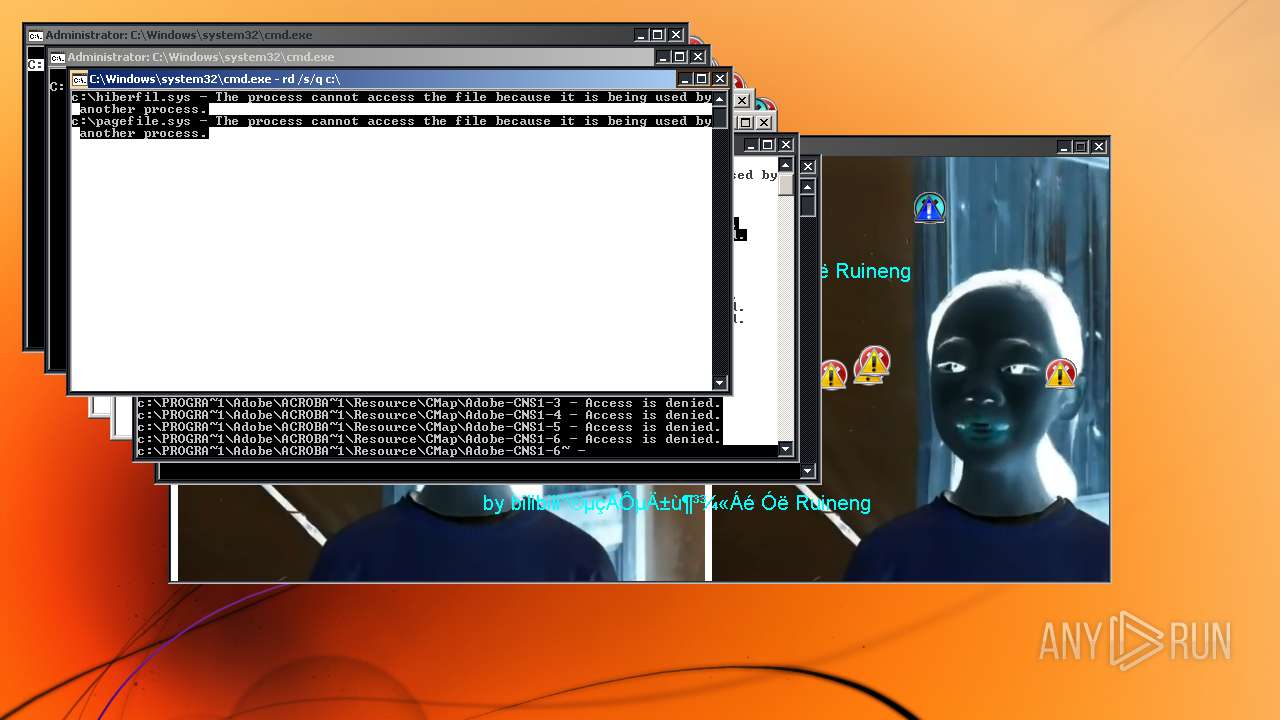
Removes files from Windows directory
- cmd.exe (PID: 2360)
- cmd.exe (PID: 3796)
- cmd.exe (PID: 3116)
- cmd.exe (PID: 3244)
- cmd.exe (PID: 3072)
- cmd.exe (PID: 1176)
- cmd.exe (PID: 1660)
- cmd.exe (PID: 3452)
- cmd.exe (PID: 3276)
- cmd.exe (PID: 404)
- cmd.exe (PID: 3000)
- cmd.exe (PID: 3436)
- cmd.exe (PID: 2724)
- cmd.exe (PID: 3940)
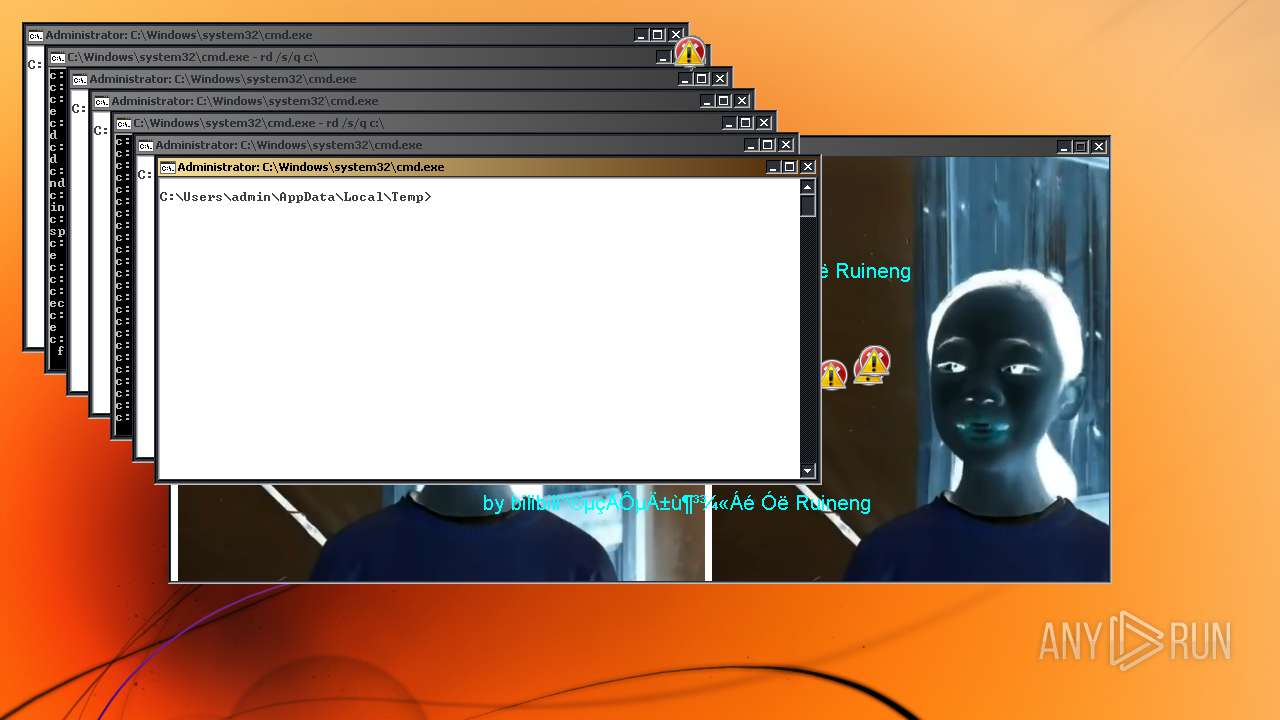
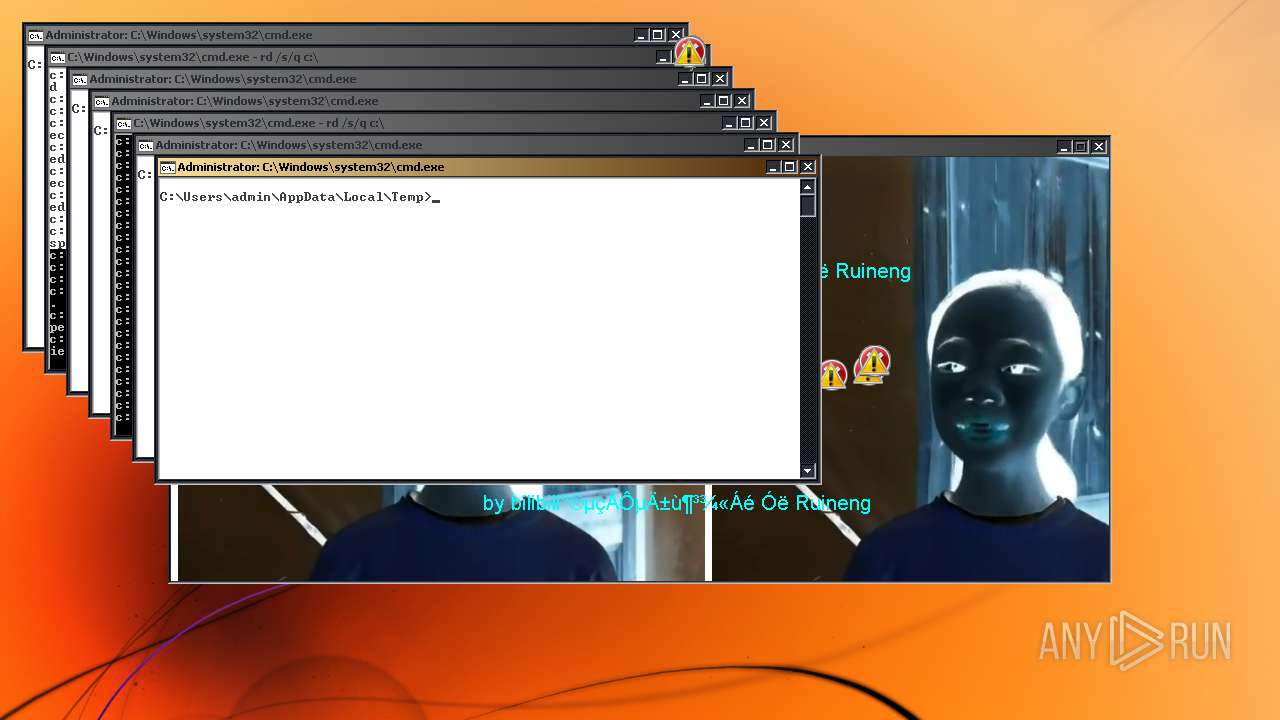
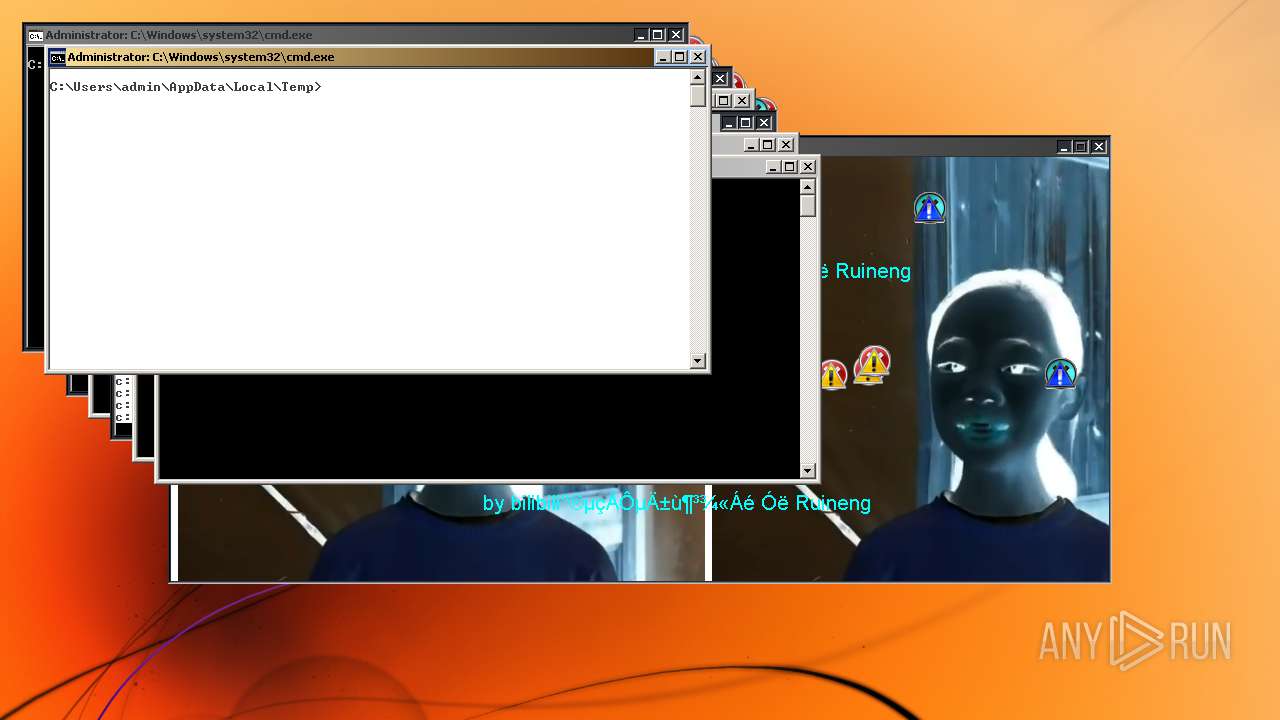
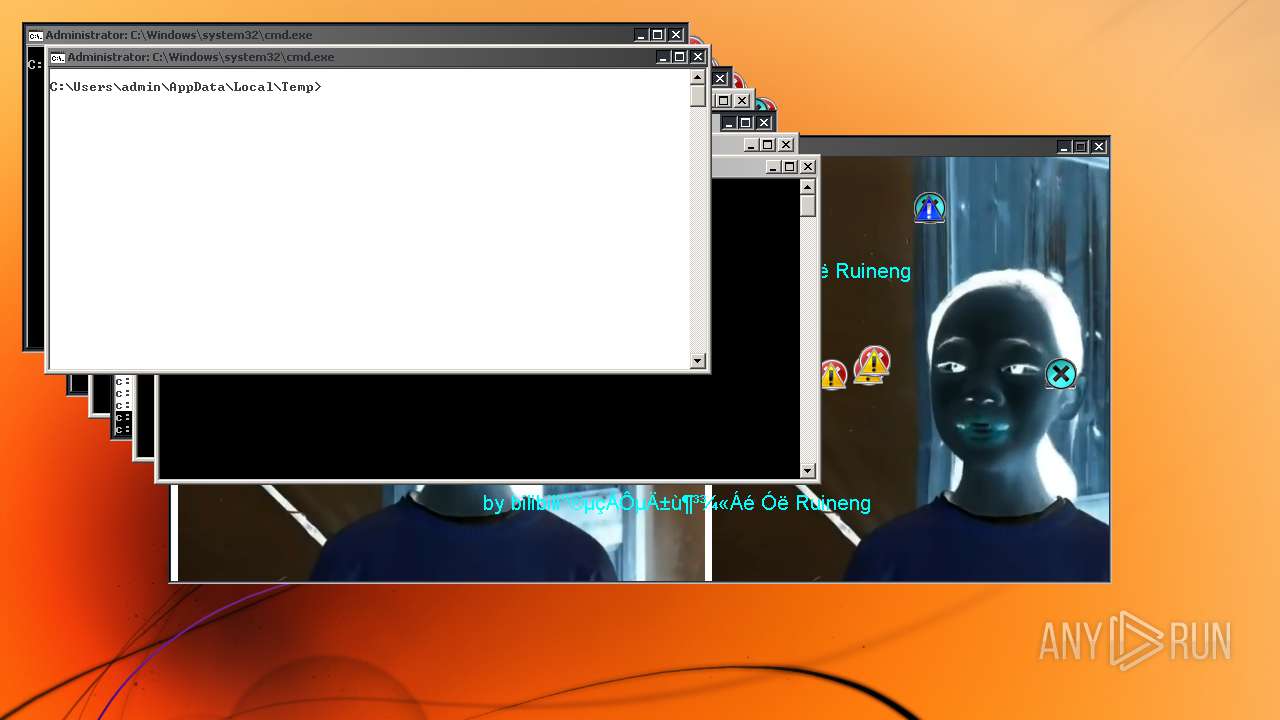
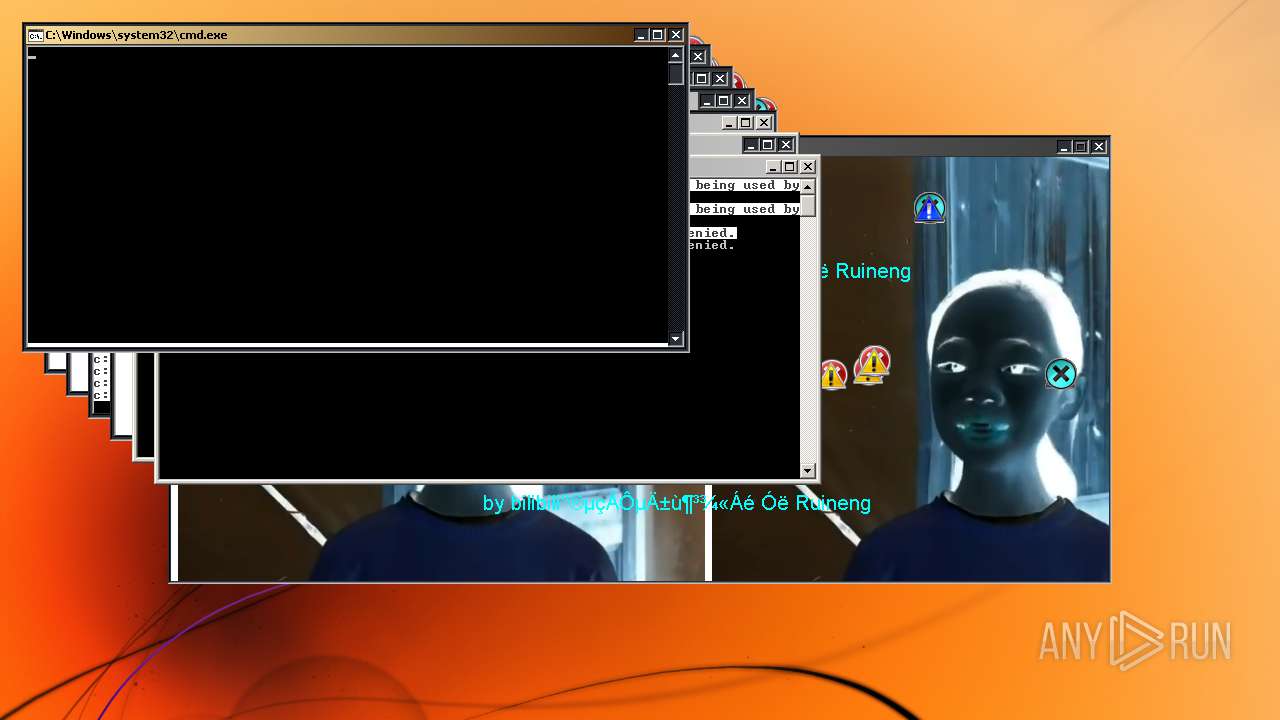
Starts CMD.EXE for commands execution
- ab41f8d4dcef49ba87d3addf23e7c6d8.exe (PID: 2688)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1972:12:25 06:33:23+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 5.6 |
| CodeSize: | 20480 |
| InitializedDataSize: | 3416064 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3861 |
| OSVersion: | 4 |
| ImageVersion: | 2 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.2.0 |
| ProductVersionNumber: | 2.0.2.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
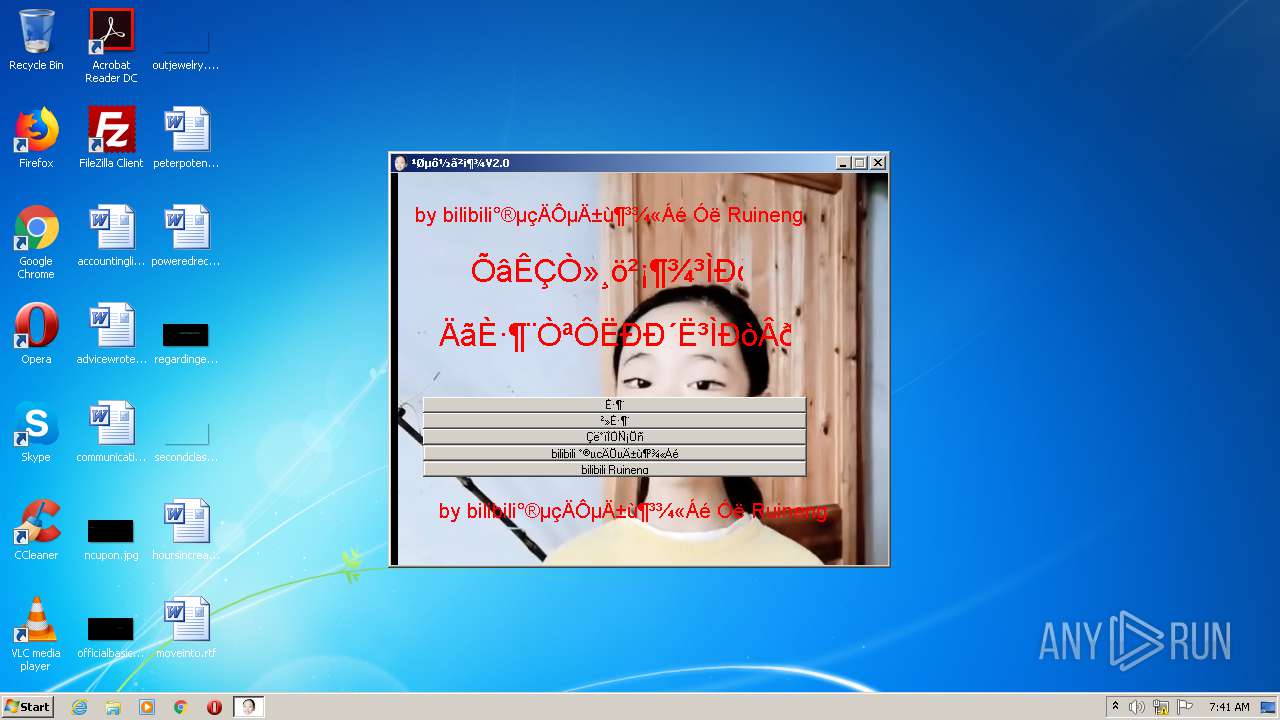
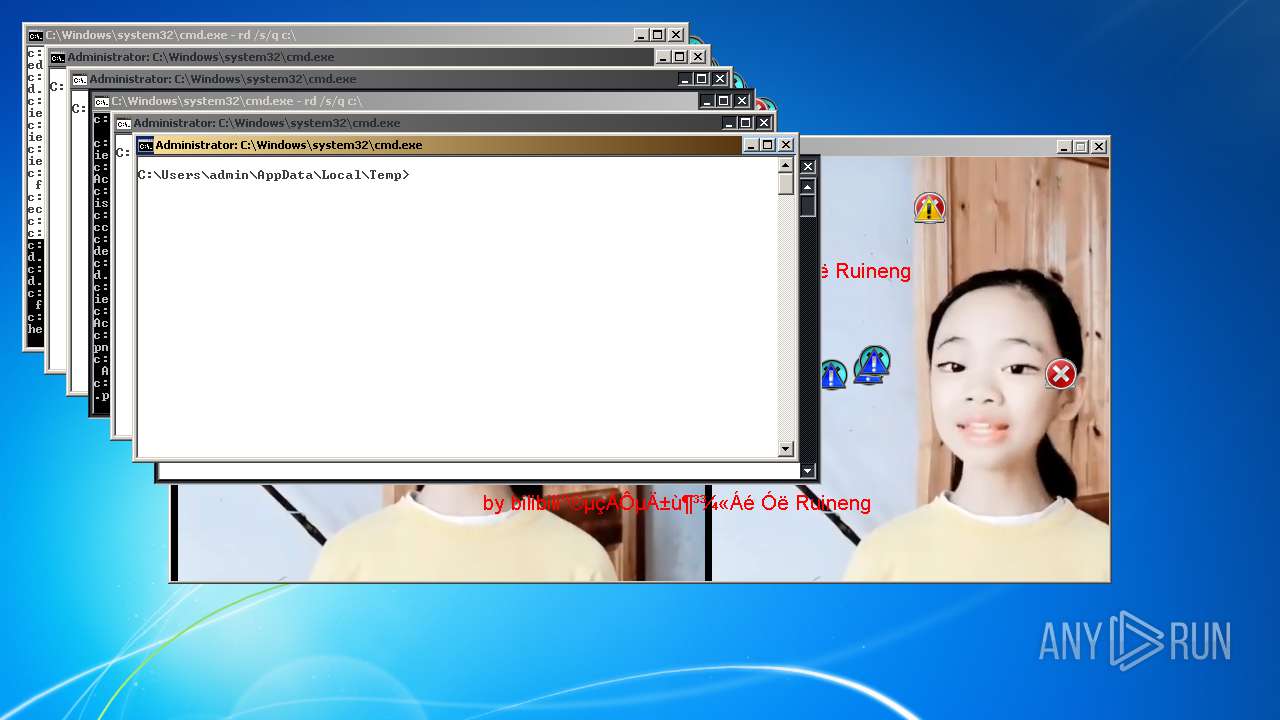
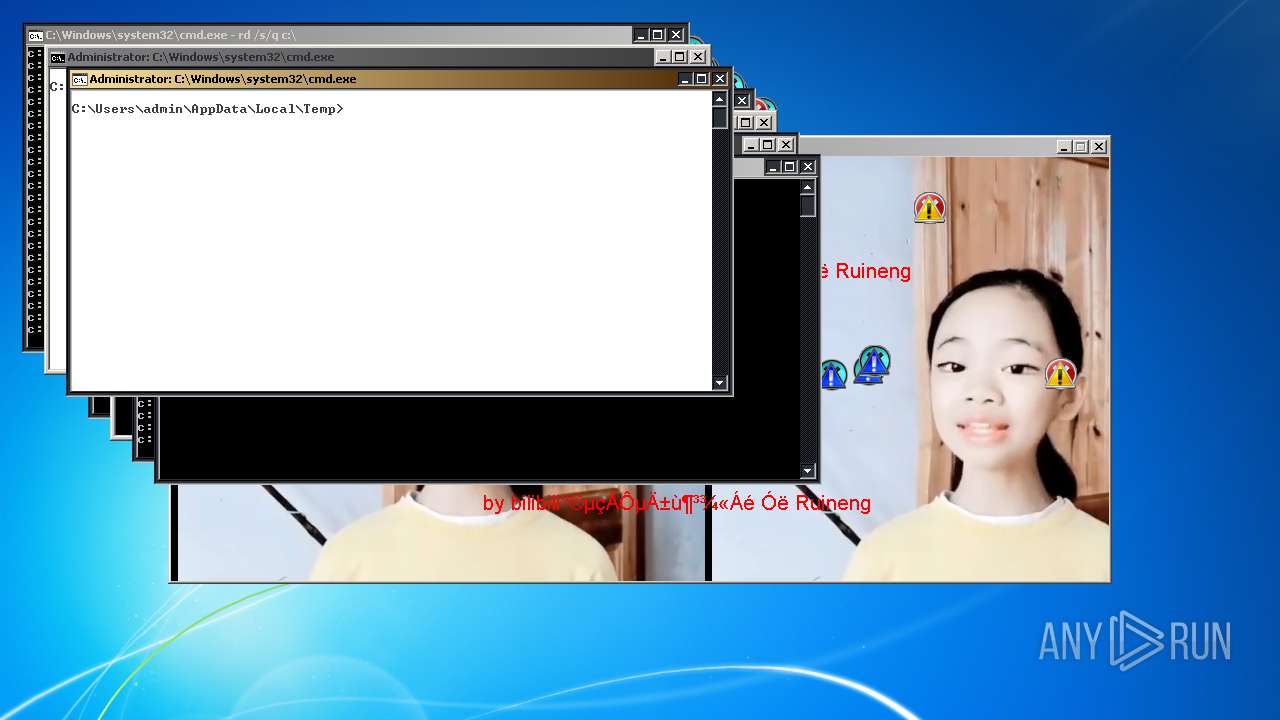
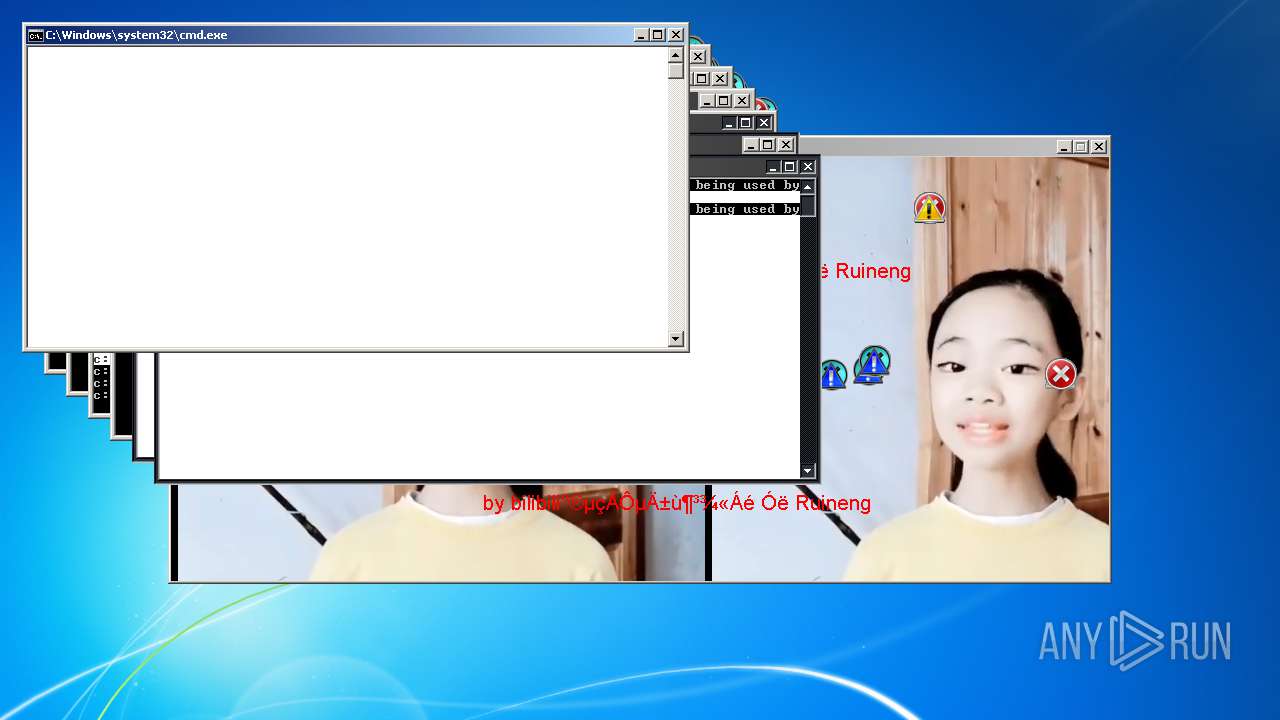
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 2.0.2.0 |
| FileDescription: | update |
| ProductName: | 易语言程序 |
| ProductVersion: | 2.0.2.0 |
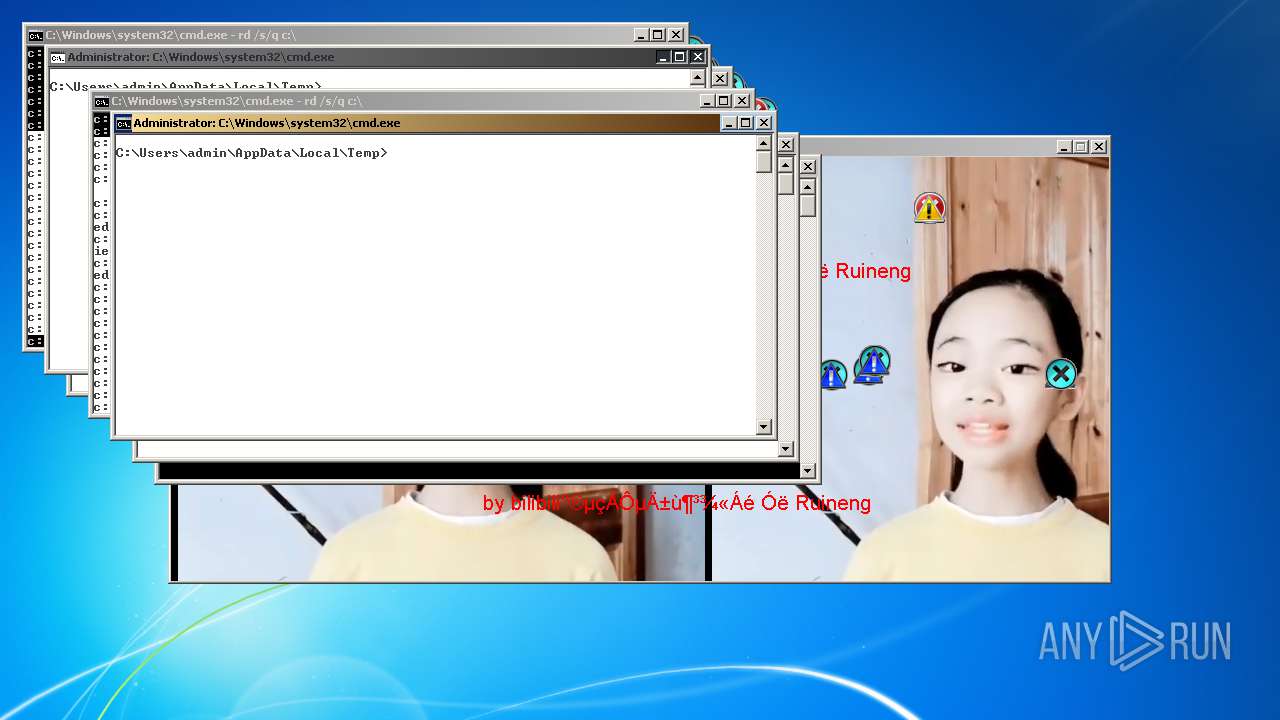
| CompanyName: | bilibili爱电脑的冰冻精灵 与Ruineng |
| LegalCopyright: | bilibili爱电脑的冰冻精灵 与Ruineng 版权所有 |
| Comments: | update |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Dec-1972 05:33:23 |
| Detected languages: |
|
| FileVersion: | 2.0.2.0 |
| FileDescription: | update |
| ProductName: | 易语言程序 |
| ProductVersion: | 2.0.2.0 |
| CompanyName: | bilibili爱电脑的冰冻精灵 与Ruineng |
| LegalCopyright: | bilibili爱电脑的冰冻精灵 与Ruineng 版权所有 |
| Comments: | update |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 25-Dec-1972 05:33:23 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00004DCC | 0x00005000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.52193 |
.rdata | 0x00006000 | 0x00000A4A | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.55983 |
.data | 0x00009000 | 0x00322000 | 0x00322000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.26754 |
.rsrc | 0x0032B000 | 0x0001C0A4 | 0x0001D000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.64036 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.02094 | 697 | Latin 1 / Western European | Chinese - PRC | RT_MANIFEST |
2 | 7.88997 | 22498 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 7.98163 | 55659 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
4 | 4.80503 | 296 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
5 | 4.95962 | 744 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
6 | 4.45093 | 1640 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
7 | 5.25144 | 1384 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
8 | 6.14018 | 2216 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
9 | 5.97829 | 3752 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
10 | 5.49114 | 1128 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
Imports
KERNEL32.dll |
USER32.dll |
Total processes
261
Monitored processes
112
Malicious processes
16
Suspicious processes
0
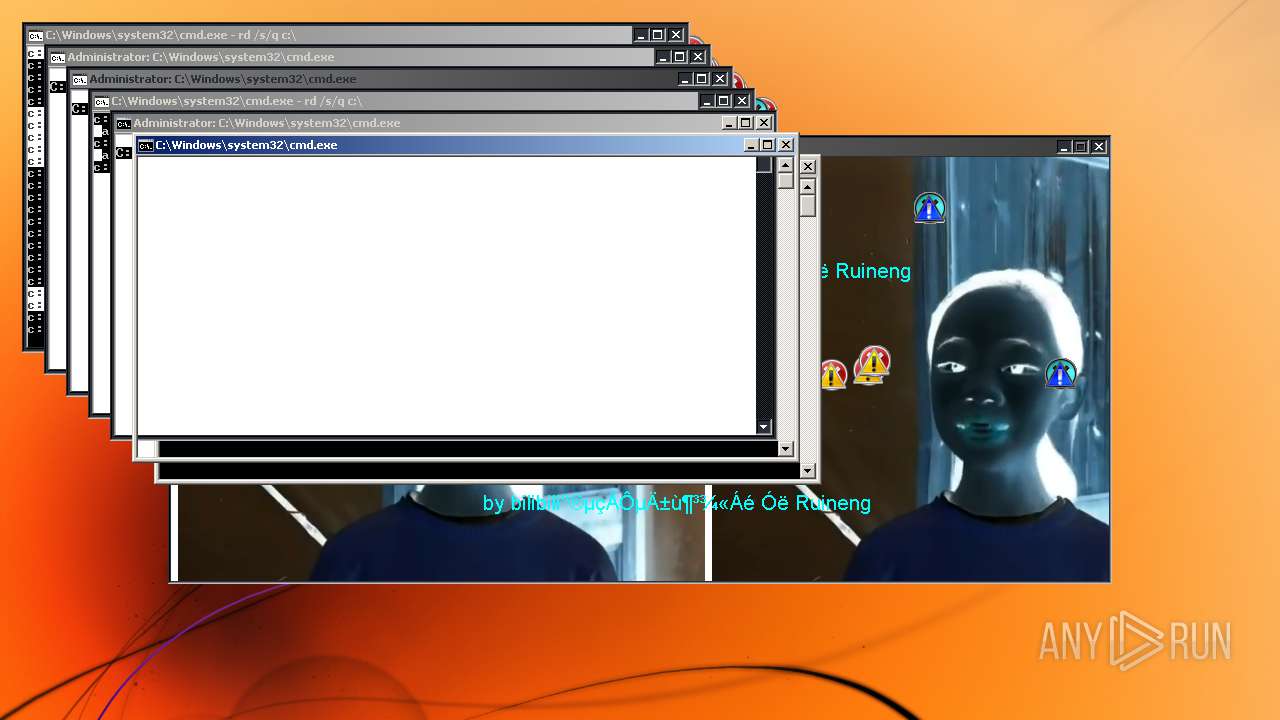
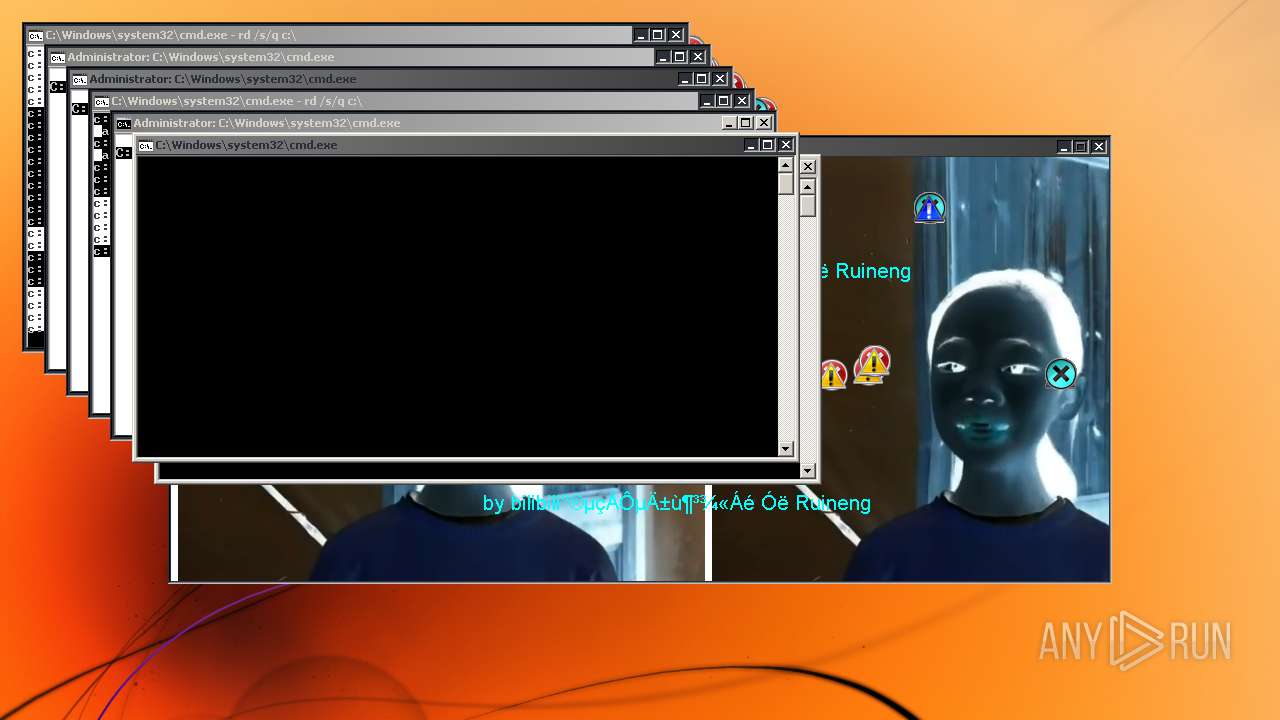
Behavior graph
Click at the process to see the details
Process information
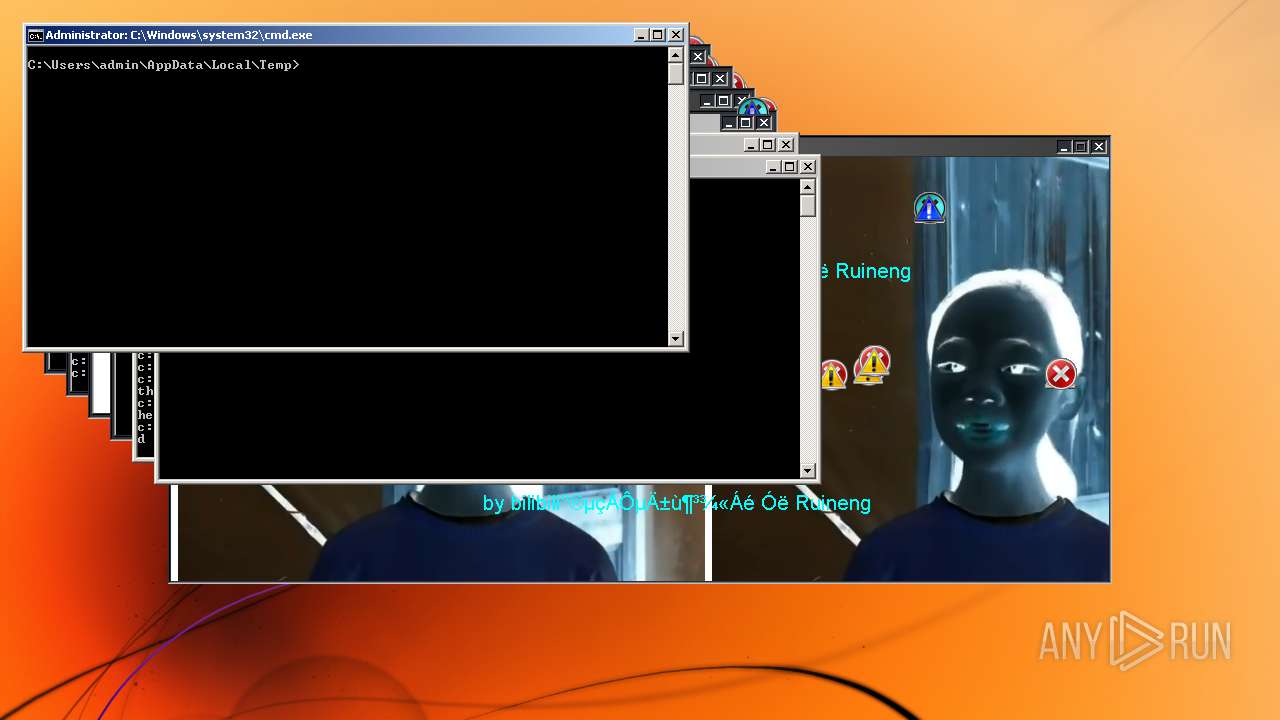
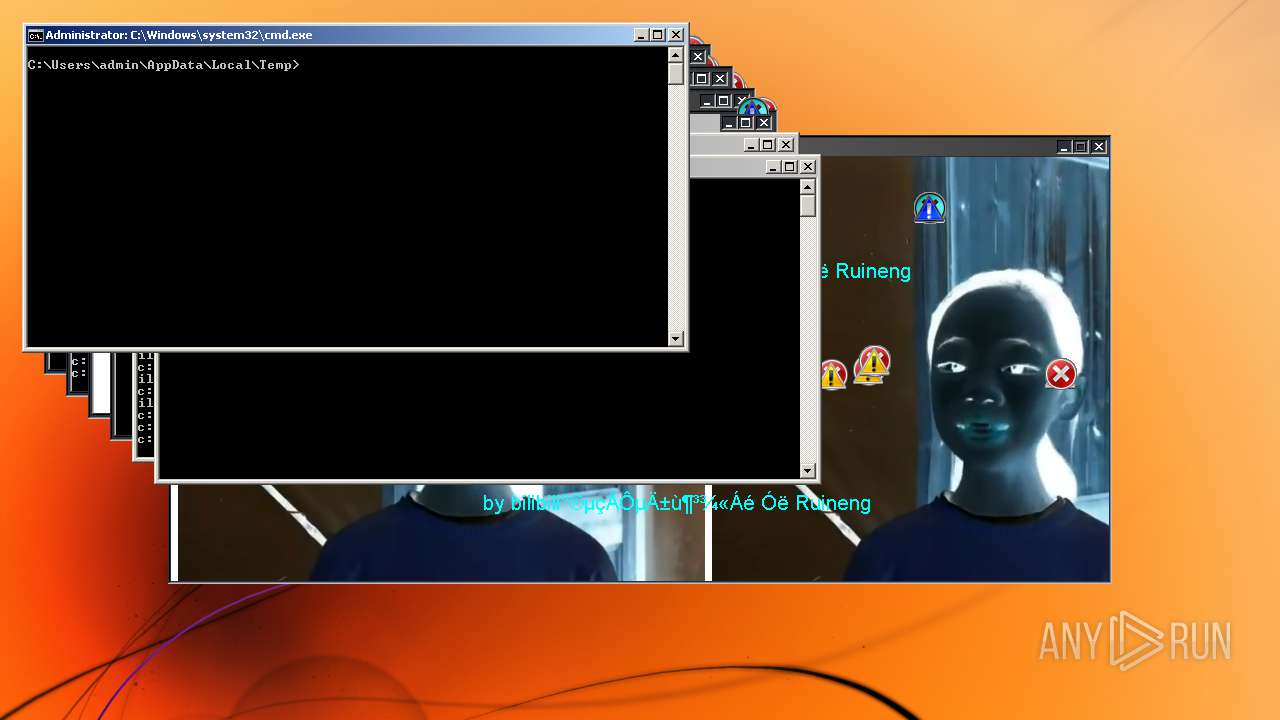
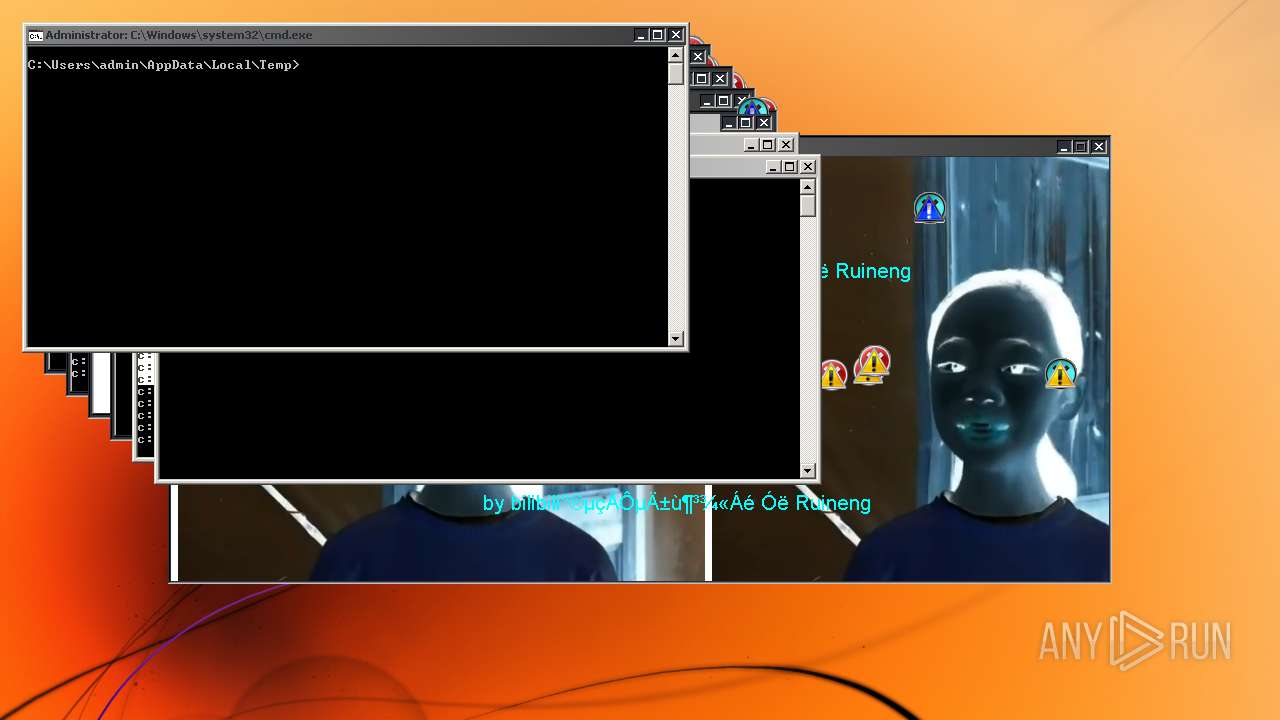
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
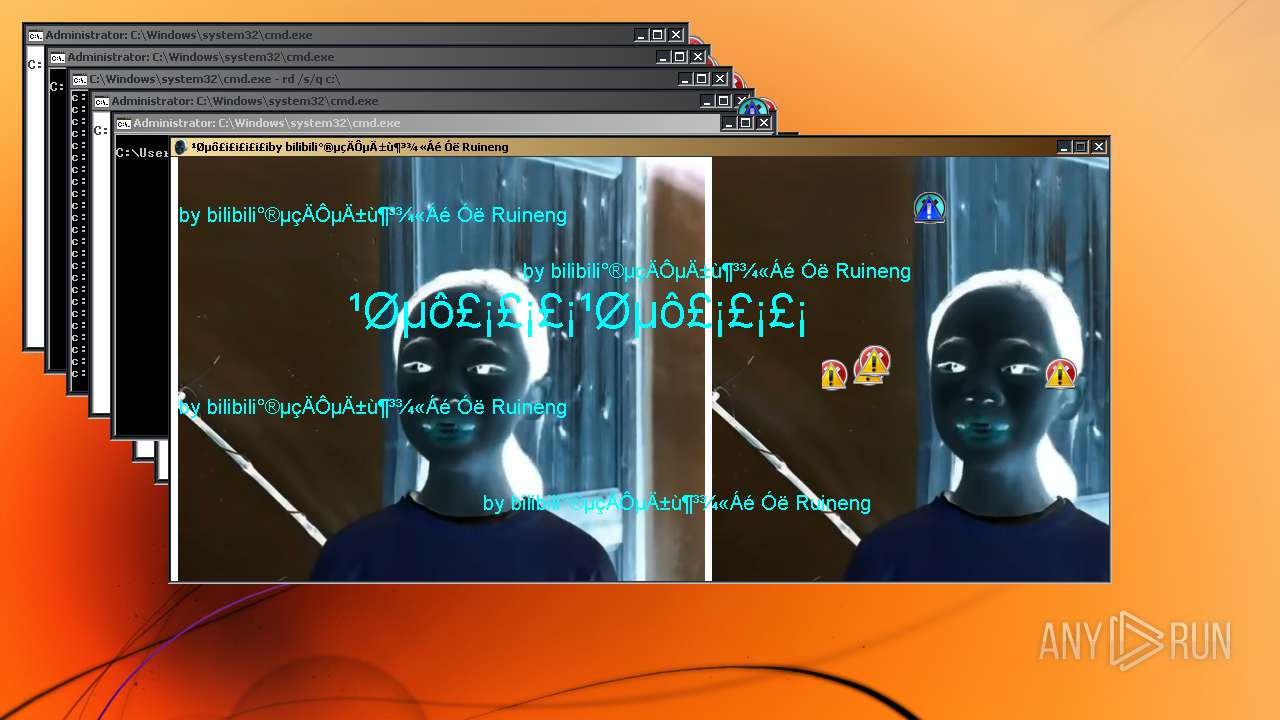
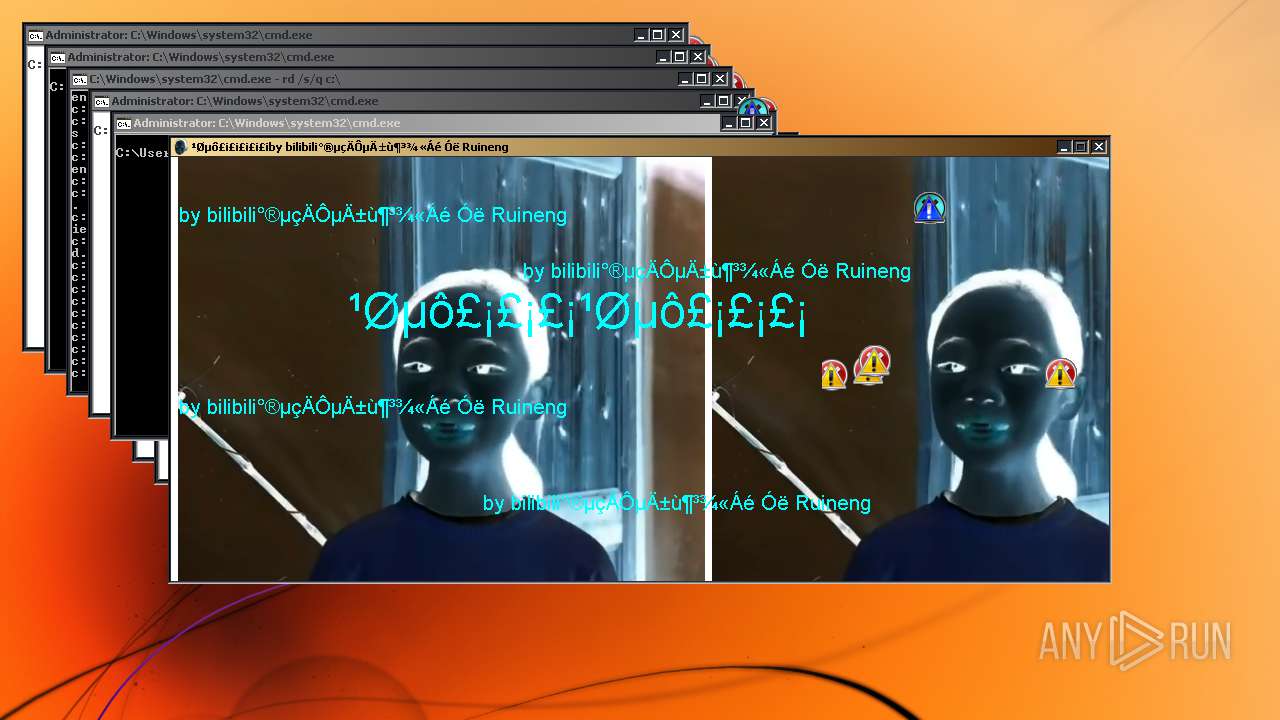
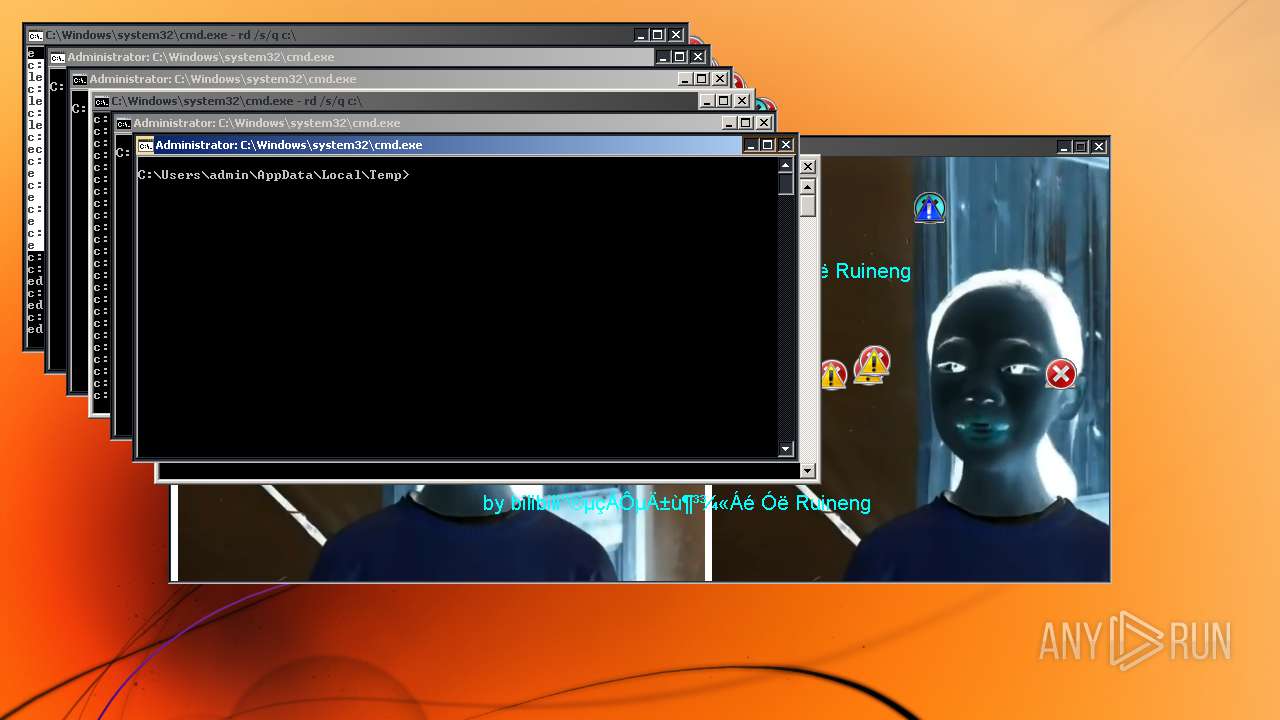
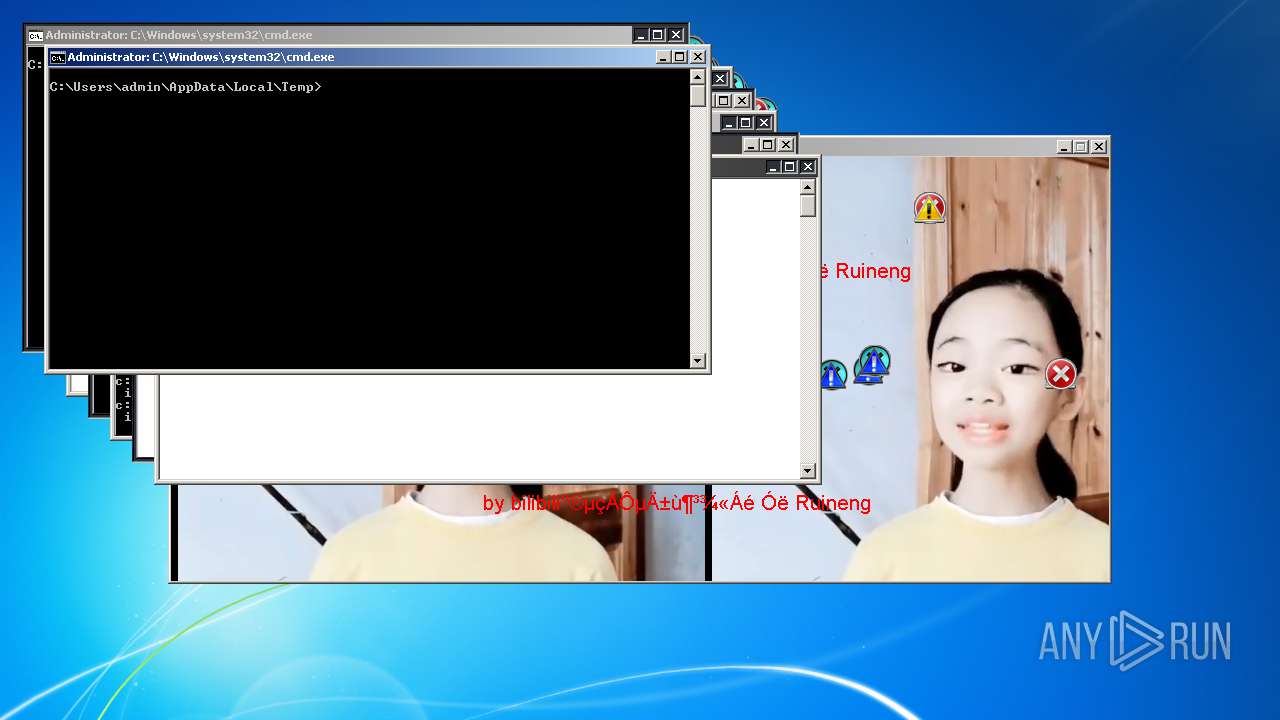
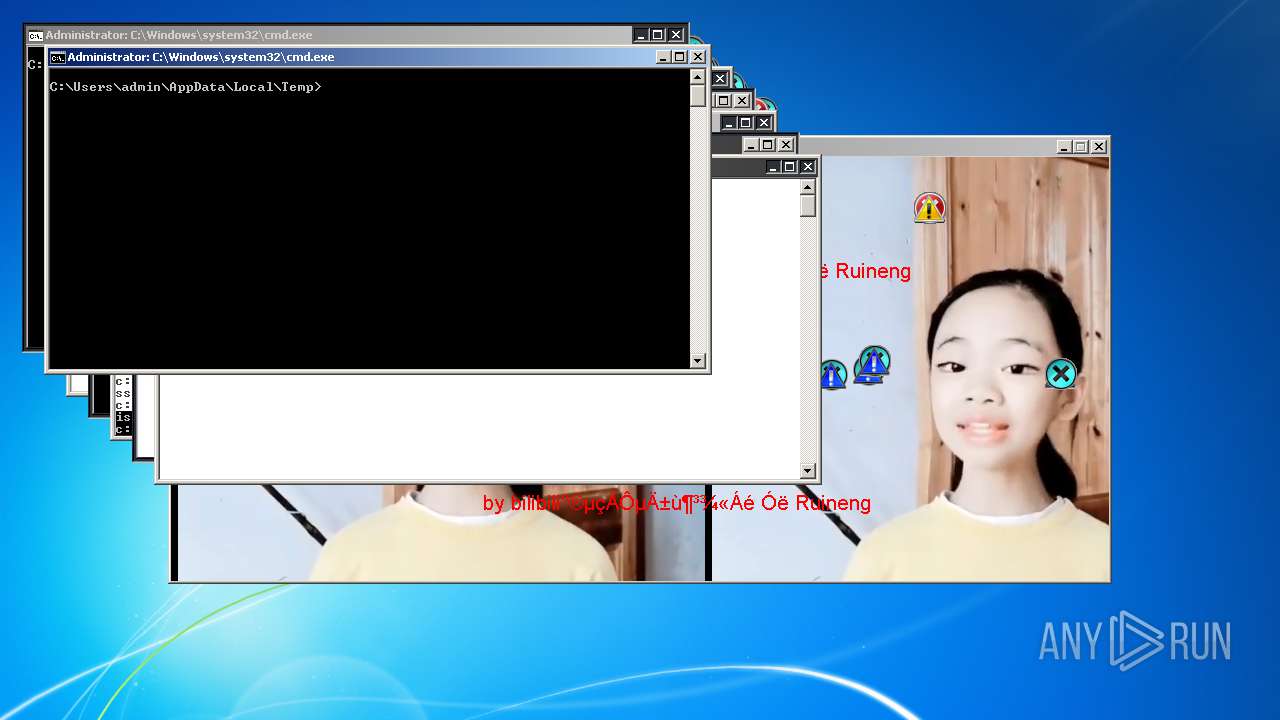
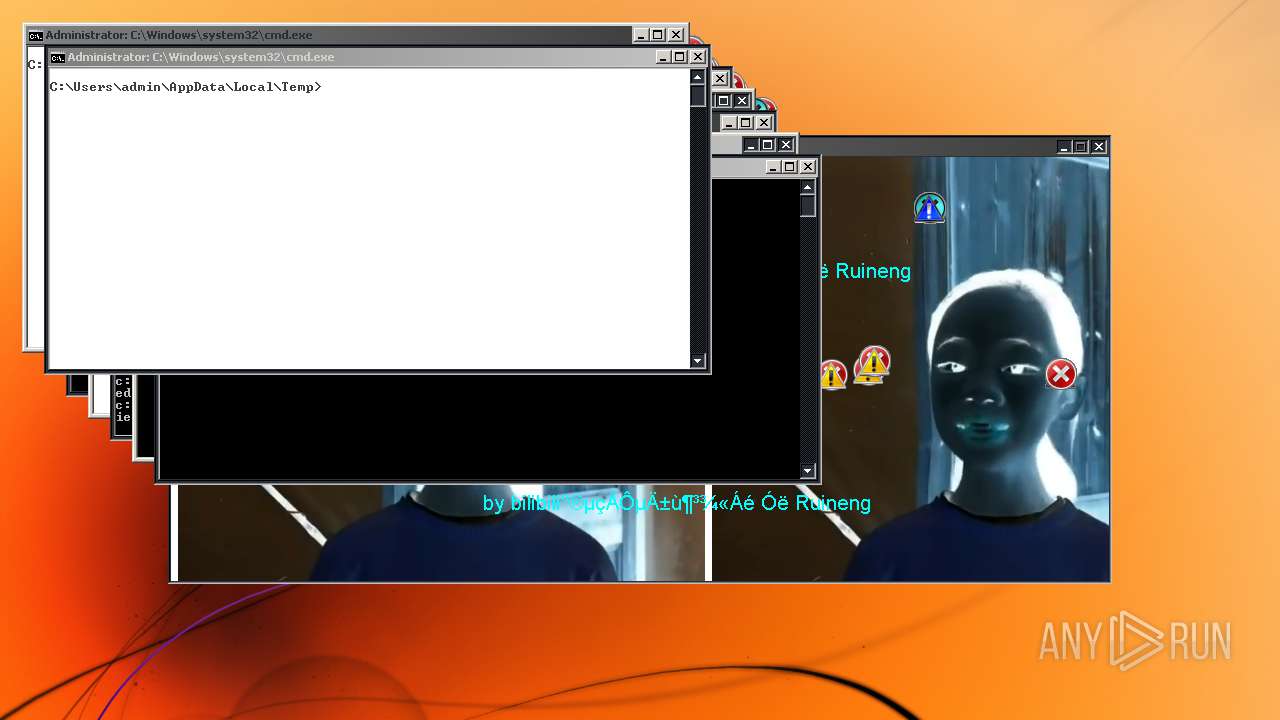
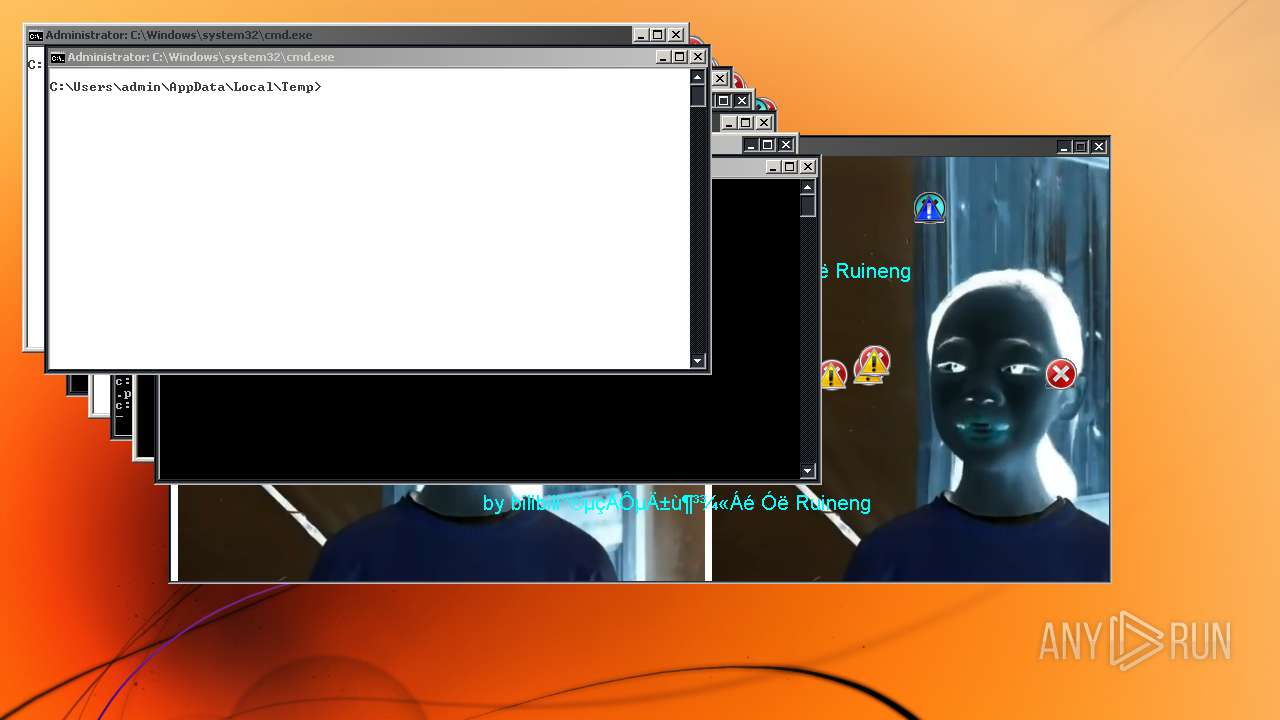
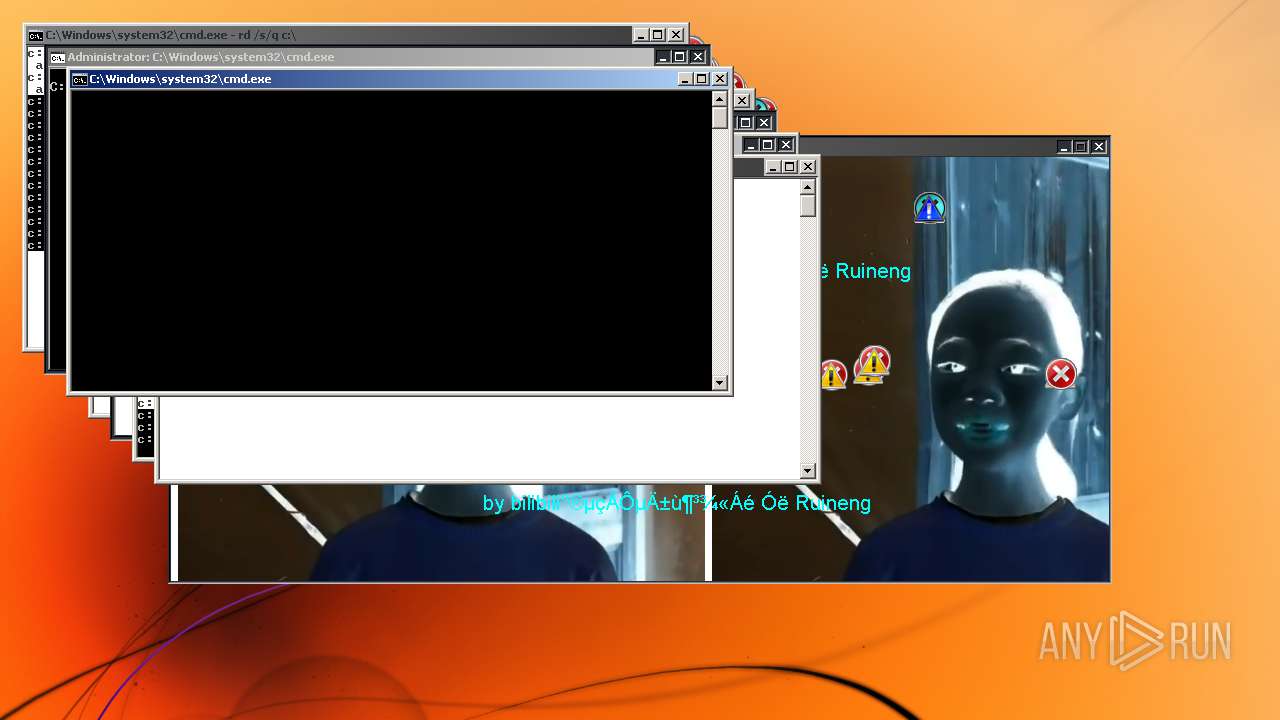
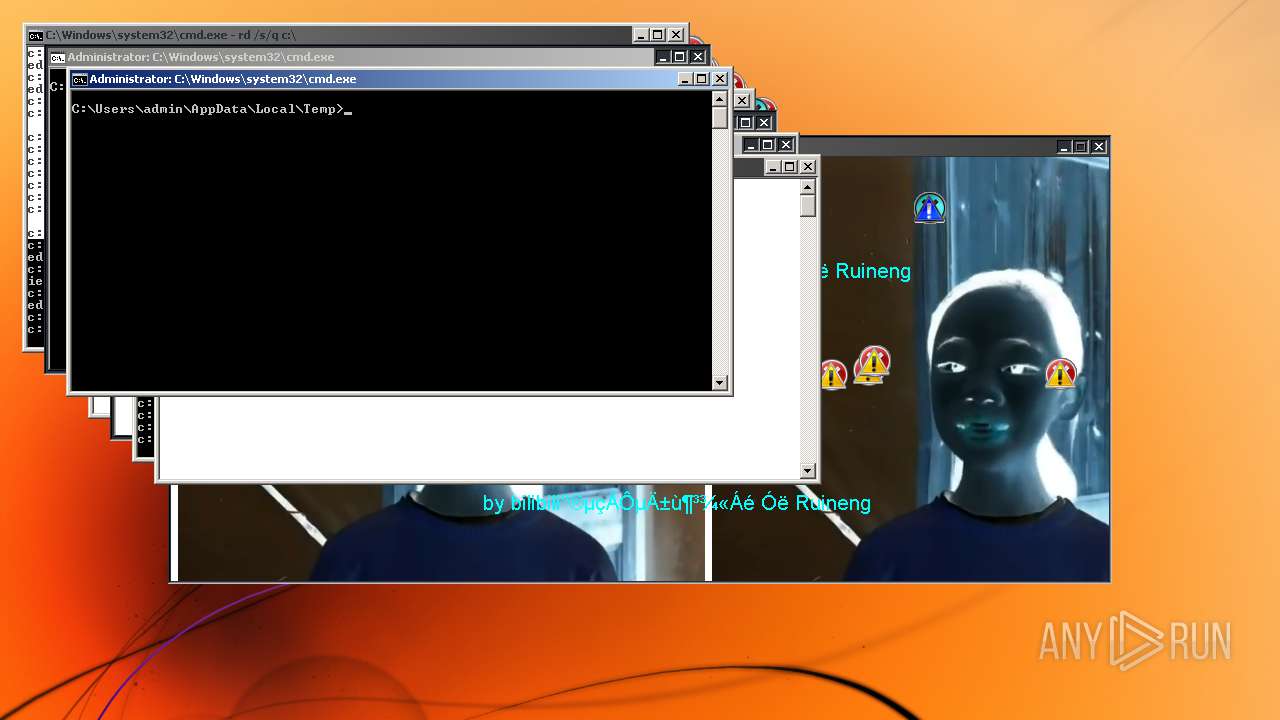
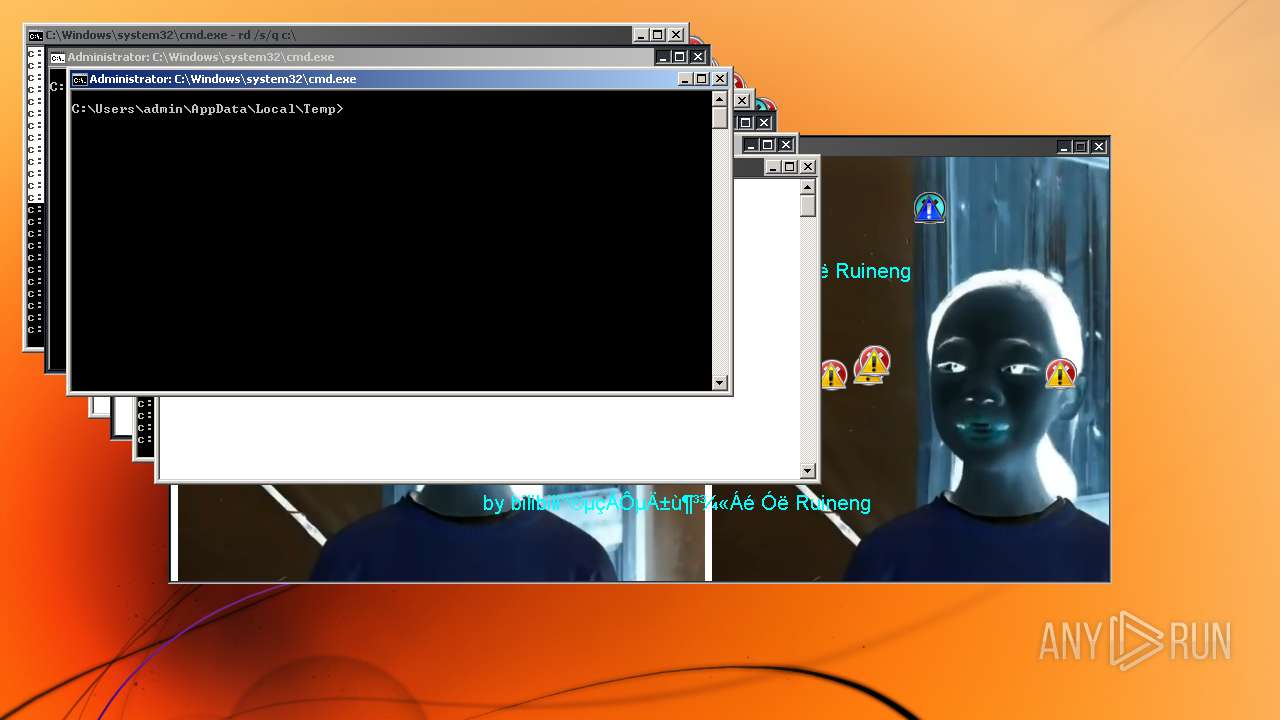
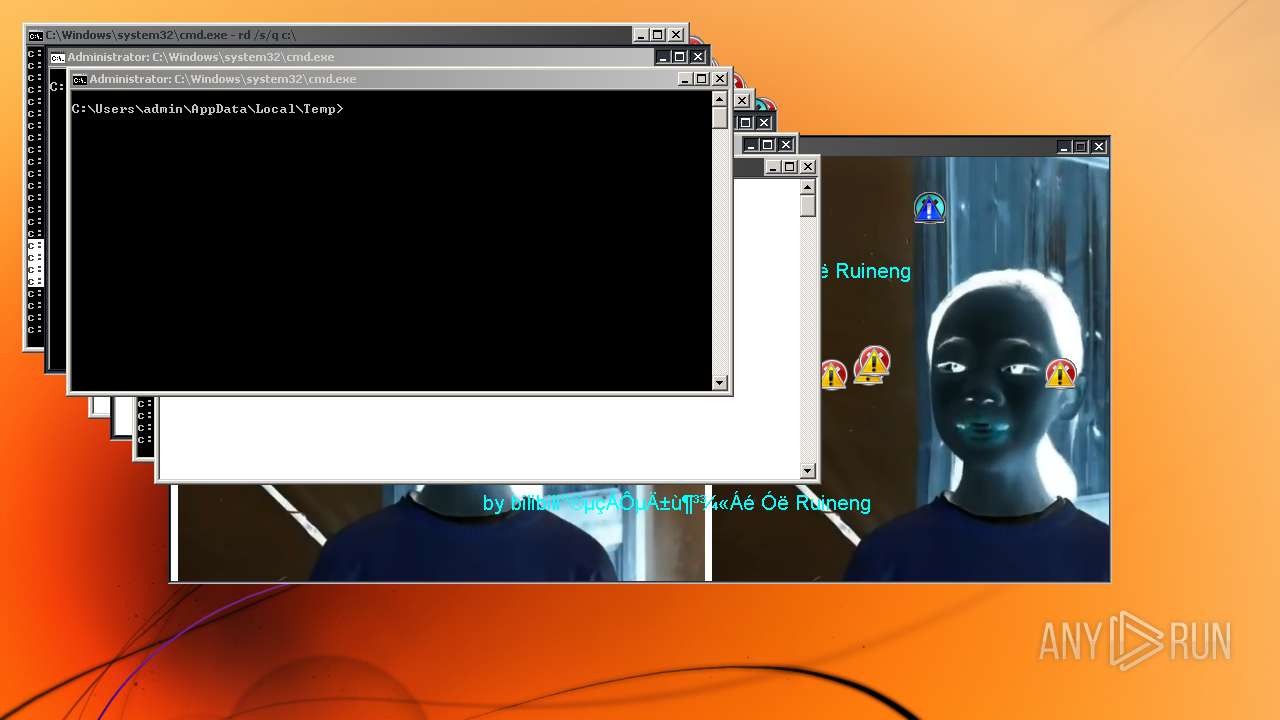
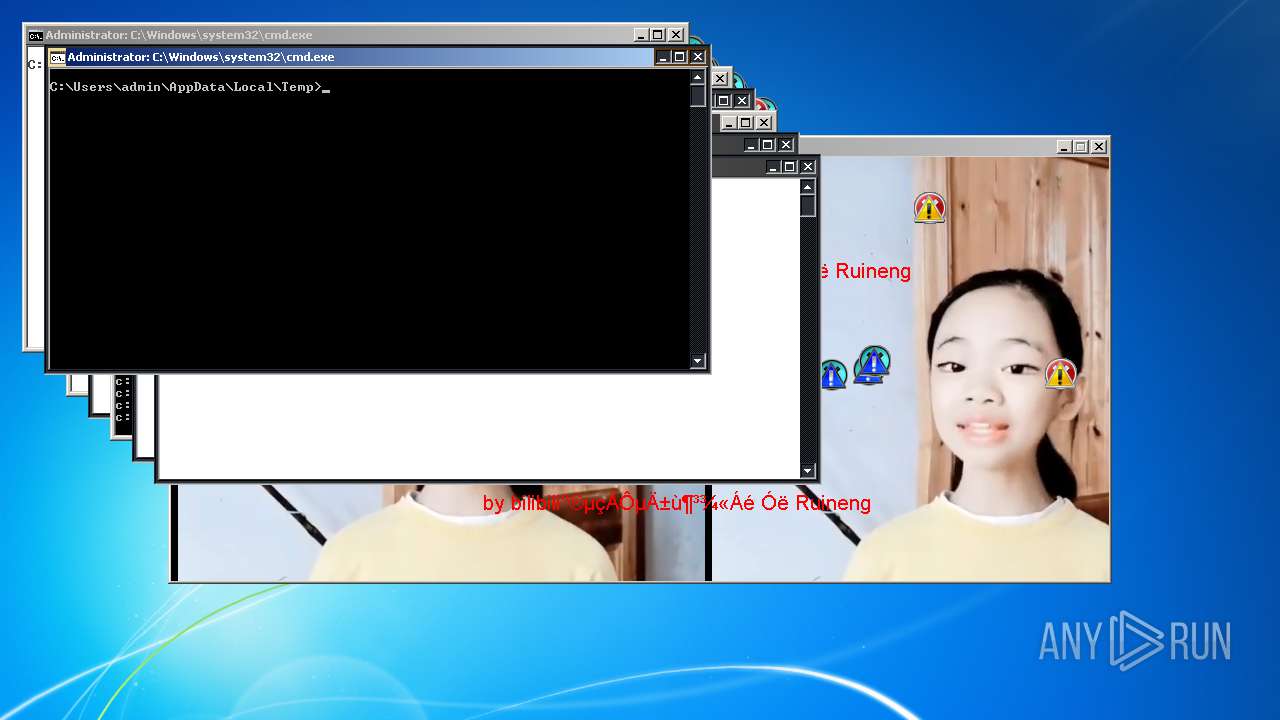
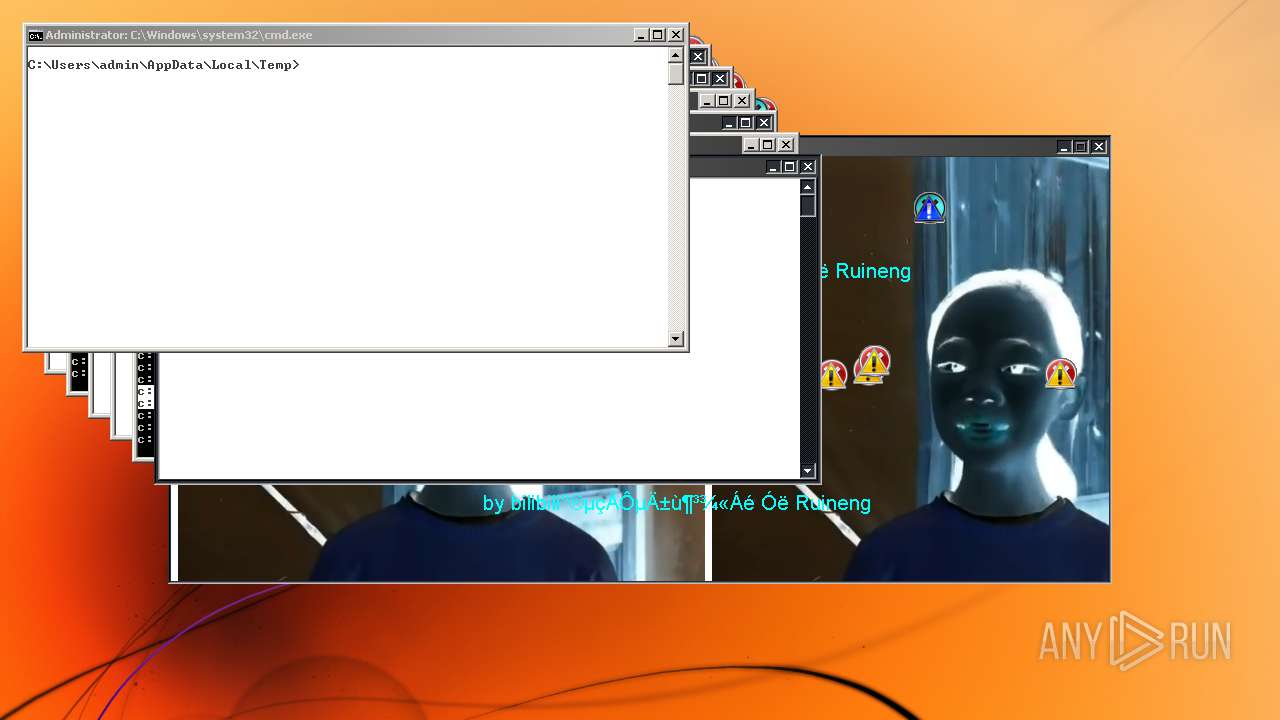
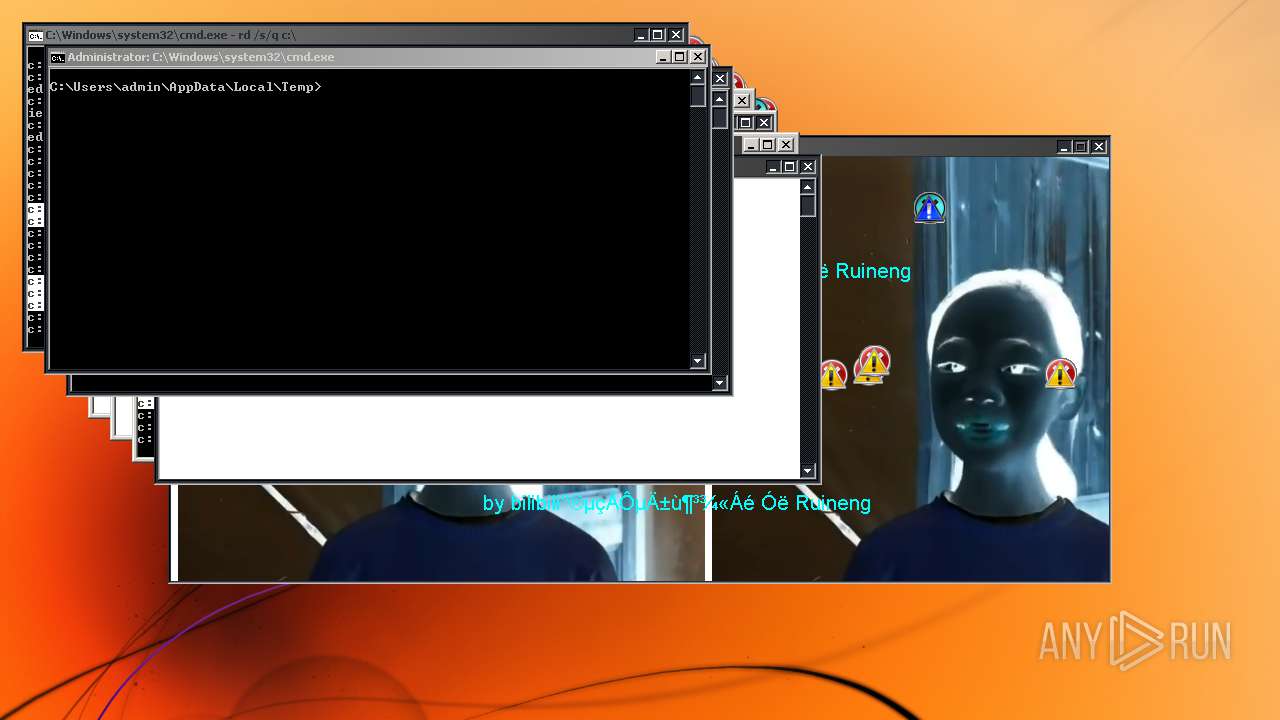
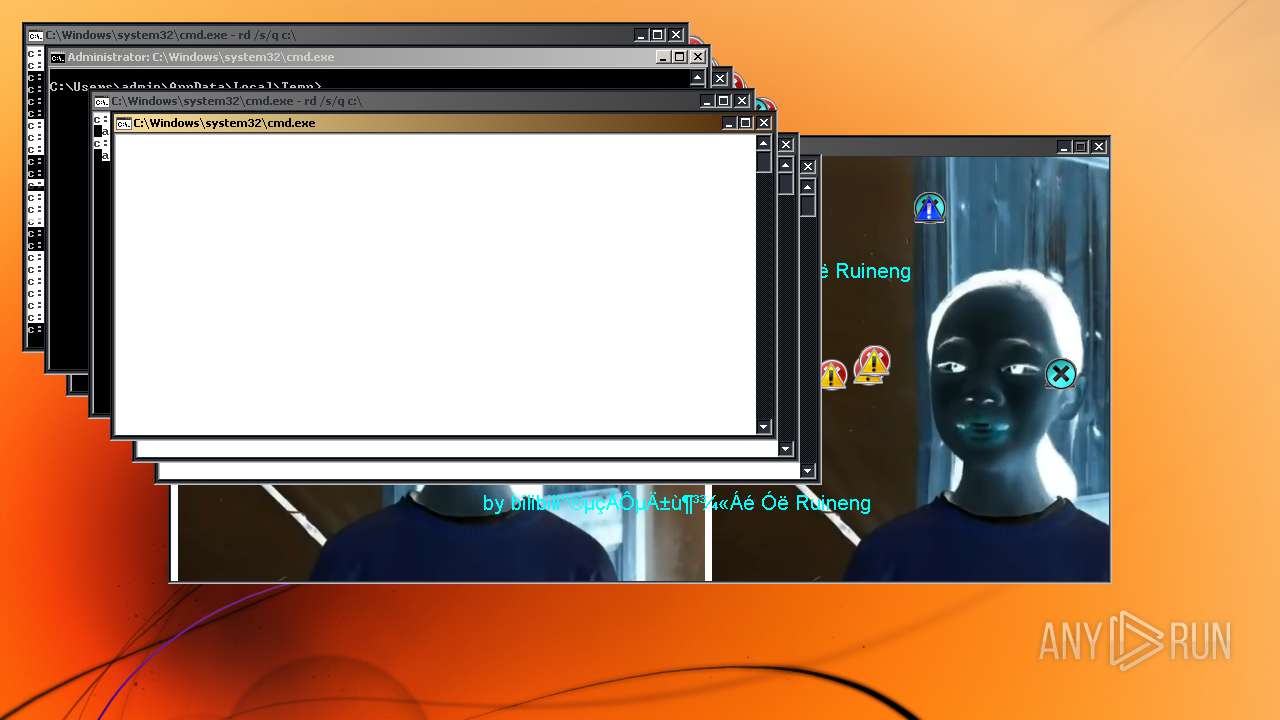
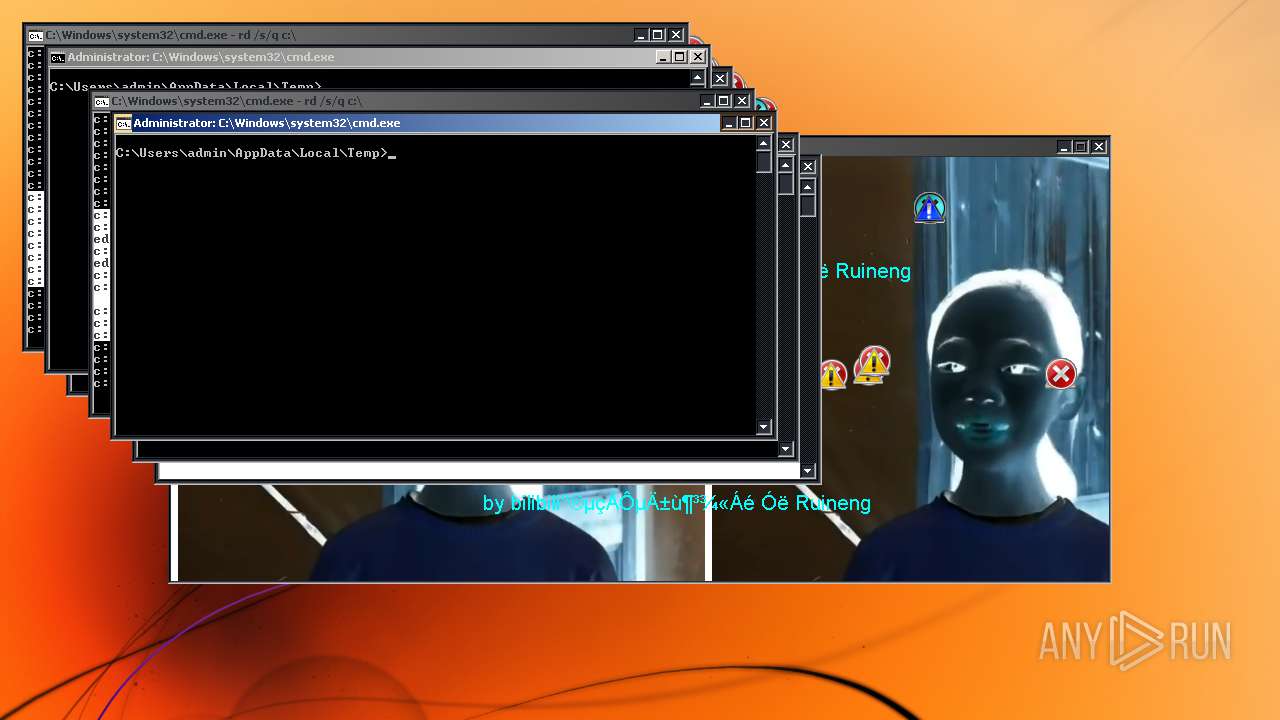
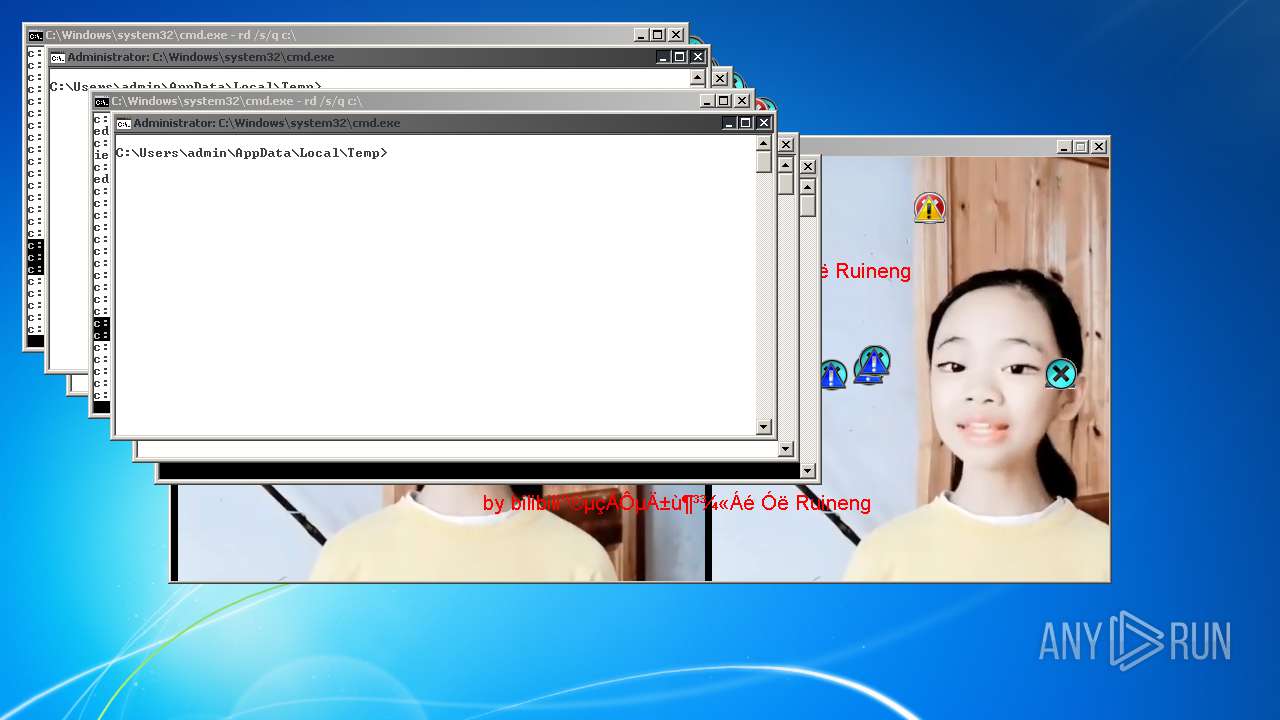
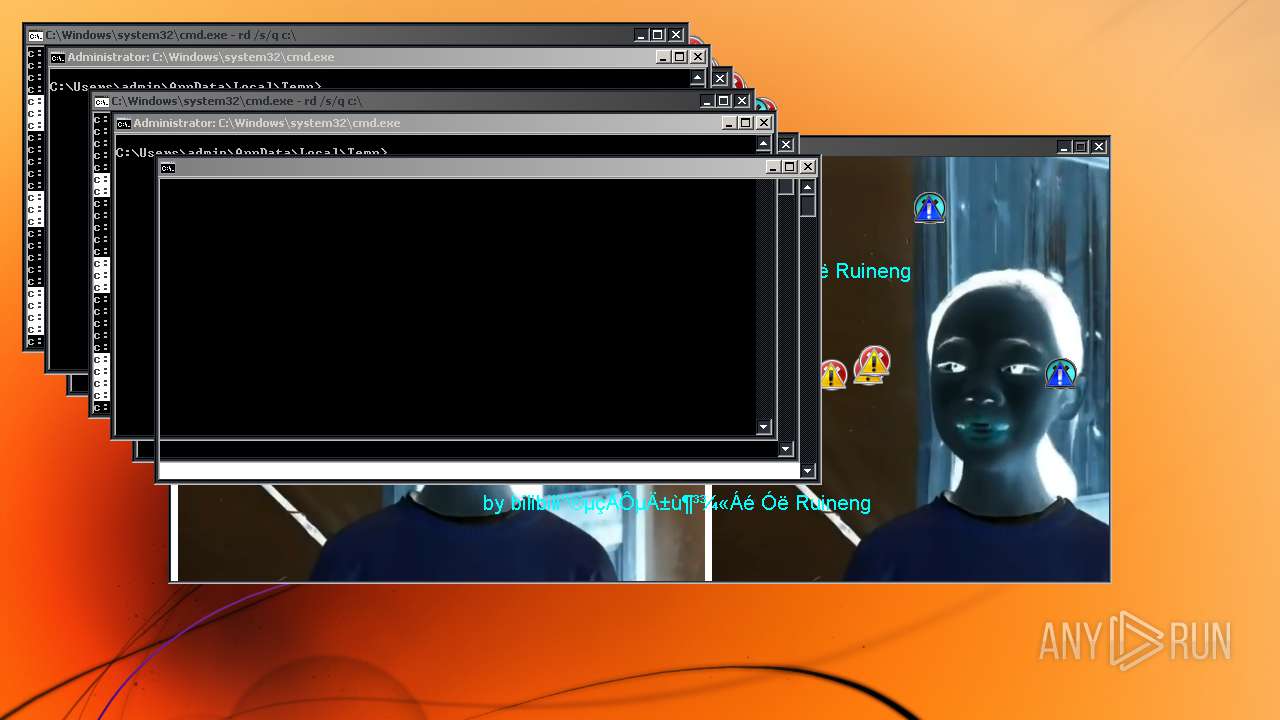
| 332 | cmd /k rd/s/q d:\ | C:\Windows\system32\cmd.exe | — | ab41f8d4dcef49ba87d3addf23e7c6d8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 340 | cmd /k rd/s/q c:\ | C:\Windows\system32\cmd.exe | — | ab41f8d4dcef49ba87d3addf23e7c6d8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 384 | cmd /k rd/s/q d:\ | C:\Windows\system32\cmd.exe | — | ab41f8d4dcef49ba87d3addf23e7c6d8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 404 | cmd /k rd/s/q c:\ | C:\Windows\system32\cmd.exe | — | ab41f8d4dcef49ba87d3addf23e7c6d8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 560 | cmd /k rd/s/q e:\ | C:\Windows\system32\cmd.exe | — | ab41f8d4dcef49ba87d3addf23e7c6d8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 688 | cmd /k rd/s/q c:\ | C:\Windows\system32\cmd.exe | — | ab41f8d4dcef49ba87d3addf23e7c6d8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 720 | cmd /k rd/s/q c:\ | C:\Windows\system32\cmd.exe | — | ab41f8d4dcef49ba87d3addf23e7c6d8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 824 | "C:\Users\admin\AppData\Local\Temp\ab41f8d4dcef49ba87d3addf23e7c6d8.exe" | C:\Users\admin\AppData\Local\Temp\ab41f8d4dcef49ba87d3addf23e7c6d8.exe | — | explorer.exe | |||||||||||
User: admin Company: bilibili爱电脑的冰冻精灵 与Ruineng Integrity Level: MEDIUM Description: update Exit code: 3221226540 Version: 2.0.2.0 Modules
| |||||||||||||||
| 852 | cmd /k rd/s/q d:\ | C:\Windows\system32\cmd.exe | — | ab41f8d4dcef49ba87d3addf23e7c6d8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 888 | cmd /k rd/s/q e:\ | C:\Windows\system32\cmd.exe | — | ab41f8d4dcef49ba87d3addf23e7c6d8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
3 120
Read events
1 461
Write events
1 454
Delete events
205
Modification events
| (PID) Process: | (2688) ab41f8d4dcef49ba87d3addf23e7c6d8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | name |
Value: C:\Users\admin\AppData\Local\Temp\ab41f8d4dcef49ba87d3addf23e7c6d8.exe | |||
| (PID) Process: | (2688) ab41f8d4dcef49ba87d3addf23e7c6d8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.txt |
| Operation: | write | Name: | (default) |
Value: jpegfile | |||
| (PID) Process: | (2688) ab41f8d4dcef49ba87d3addf23e7c6d8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.inf |
| Operation: | write | Name: | (default) |
Value: jpegfile | |||
| (PID) Process: | (2688) ab41f8d4dcef49ba87d3addf23e7c6d8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.exe |
| Operation: | write | Name: | (default) |
Value: jpegfile | |||
| (PID) Process: | (2688) ab41f8d4dcef49ba87d3addf23e7c6d8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.zip |
| Operation: | write | Name: | (default) |
Value: jpegfile | |||
| (PID) Process: | (2688) ab41f8d4dcef49ba87d3addf23e7c6d8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.lnk |
| Operation: | write | Name: | (default) |
Value: jpegfile | |||
| (PID) Process: | (2688) ab41f8d4dcef49ba87d3addf23e7c6d8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Advanced\Folder\Hidden\SHOWALL |
| Operation: | write | Name: | CheckedValue |
Value: 0 | |||
| (PID) Process: | (2688) ab41f8d4dcef49ba87d3addf23e7c6d8.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 1 | |||
| (PID) Process: | (2688) ab41f8d4dcef49ba87d3addf23e7c6d8.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoControlPanel |
Value: 1 | |||
| (PID) Process: | (2688) ab41f8d4dcef49ba87d3addf23e7c6d8.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | Disableregistrytools |
Value: 1 | |||
Executable files
7
Suspicious files
17
Text files
2
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3652 | SearchIndexer.exe | C:\ProgramData\Microsoft\Search\Data\Applications\Windows\MSStmp.log | — | |
MD5:— | SHA256:— | |||
| 3652 | SearchIndexer.exe | C:\ProgramData\Microsoft\Search\Data\Applications\Windows\MSS.log | — | |
MD5:— | SHA256:— | |||
| 3652 | SearchIndexer.exe | C:\ProgramData\Microsoft\Search\Data\Applications\Windows\Windows.edb | — | |
MD5:— | SHA256:— | |||
| 2688 | ab41f8d4dcef49ba87d3addf23e7c6d8.exe | C:\Users\admin\AppData\Local\Temp\E_N60005\EThread.fne | executable | |
MD5:206396257B97BD275A90CE6C2C0C37FD | SHA256:64EEF86745D7AE0168FEC357099E2E952CE74EE19576D06CC8C8C65F210CC22C | |||
| 3652 | SearchIndexer.exe | C:\ProgramData\Microsoft\Search\Data\Applications\Windows\Projects\SystemIndex\PropMap\CiPT0000.002 | binary | |
MD5:— | SHA256:— | |||
| 3652 | SearchIndexer.exe | C:\ProgramData\Microsoft\Search\Data\Applications\Windows\Projects\SystemIndex\PropMap\CiPT0000.001 | binary | |
MD5:— | SHA256:— | |||
| 3652 | SearchIndexer.exe | C:\ProgramData\Microsoft\Windows\Caches\{6AF0698E-D558-4F6E-9B3C-3716689AF493}.2.ver0x0000000000000001.db | binary | |
MD5:— | SHA256:— | |||
| 3652 | SearchIndexer.exe | C:\programdata\microsoft\search\data\applications\windows\projects\systemindex\indexer\cifiles\00010001.dir | — | |
MD5:— | SHA256:— | |||
| 3652 | SearchIndexer.exe | C:\ProgramData\Microsoft\Search\Data\Applications\Windows\Projects\SystemIndex\Indexer\CiFiles\00010001.ci | — | |
MD5:— | SHA256:— | |||
| 3652 | SearchIndexer.exe | C:\ProgramData\Microsoft\Search\Data\Applications\Windows\Projects\SystemIndex\Indexer\CiFiles\00010001.wid | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report