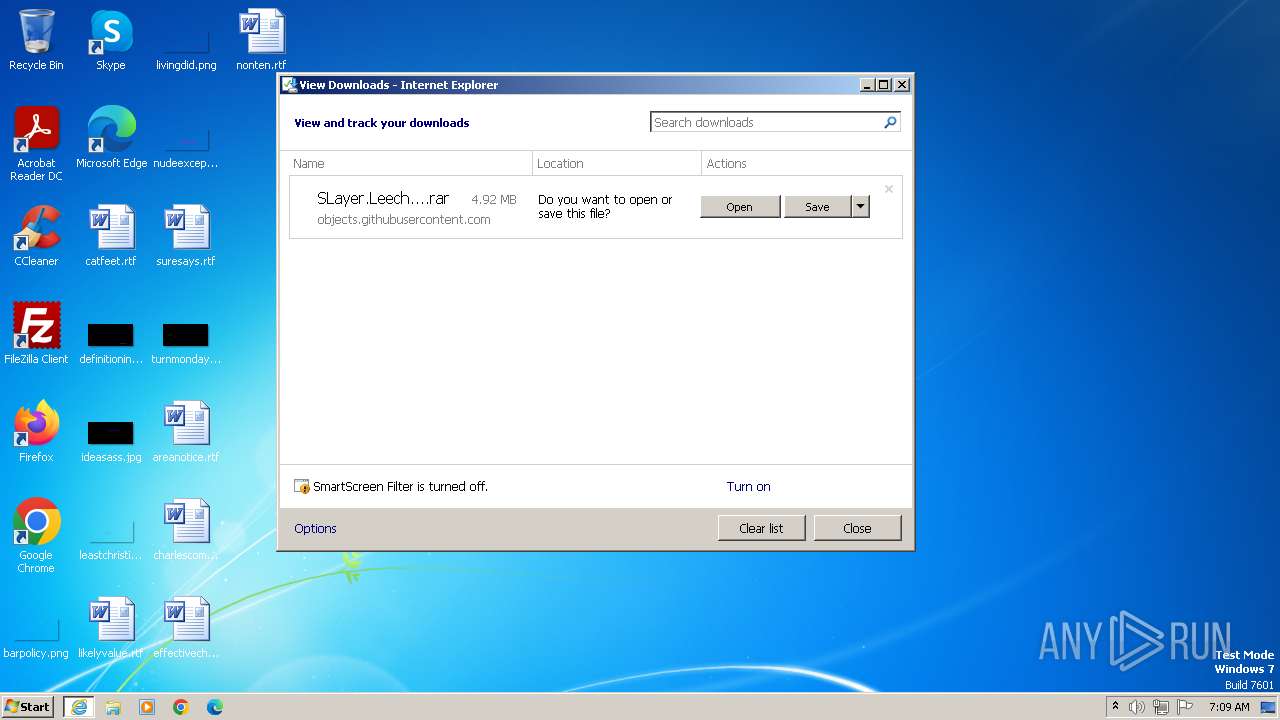
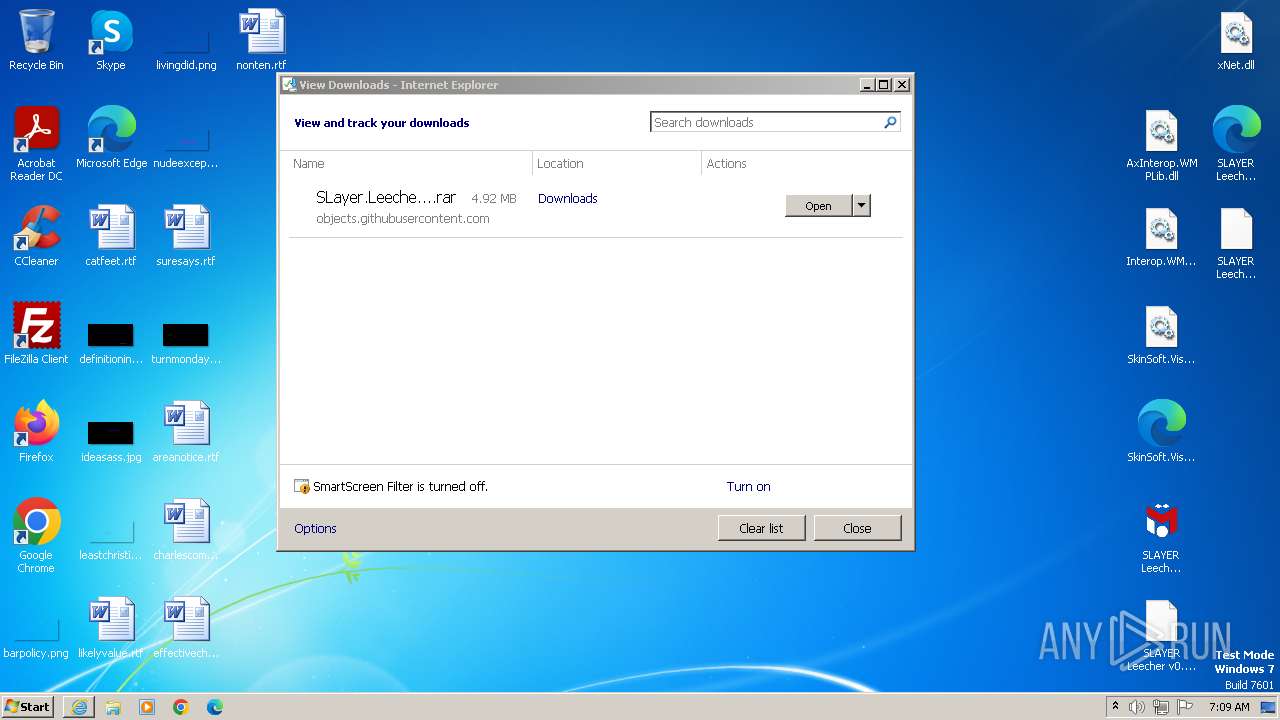
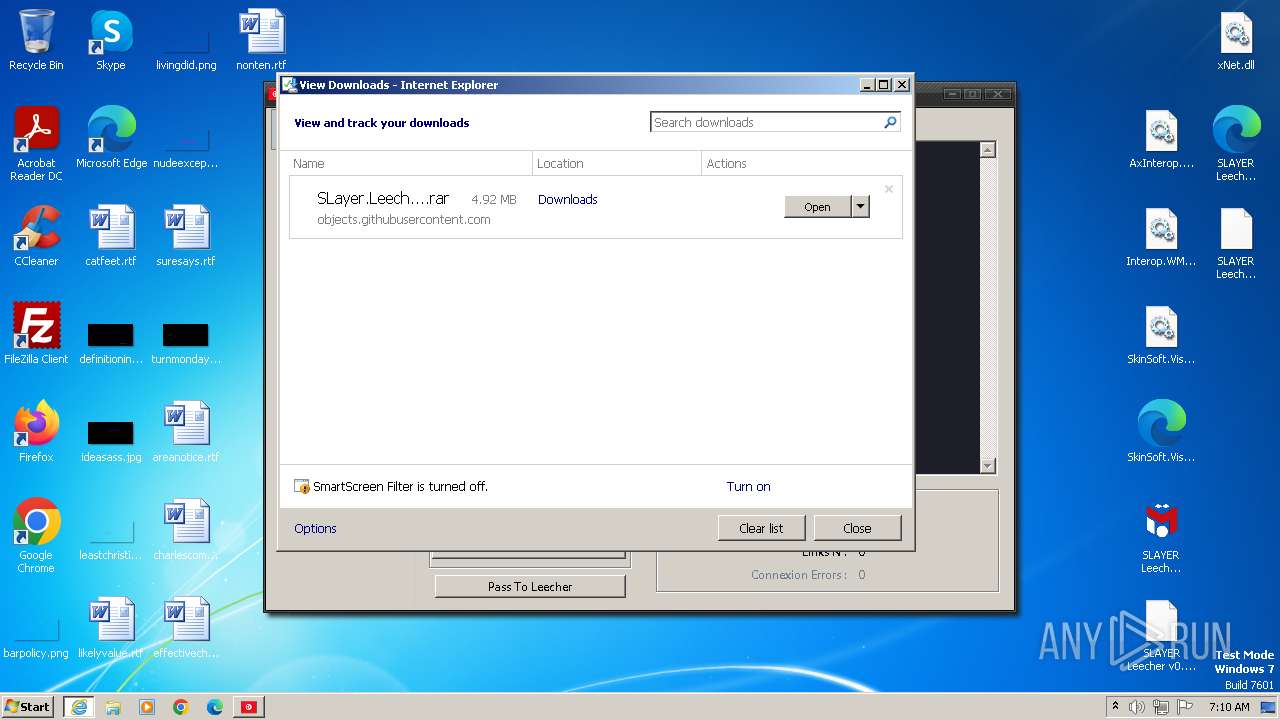
| URL: | https://github.com/X-SLAYER/SLAYER-LEECHER/releases/download/v0.7/SLayer.Leecher.v0.7.rar |
| Full analysis: | https://app.any.run/tasks/3a894ff6-3754-42ea-824e-e17c3eb267f6 |
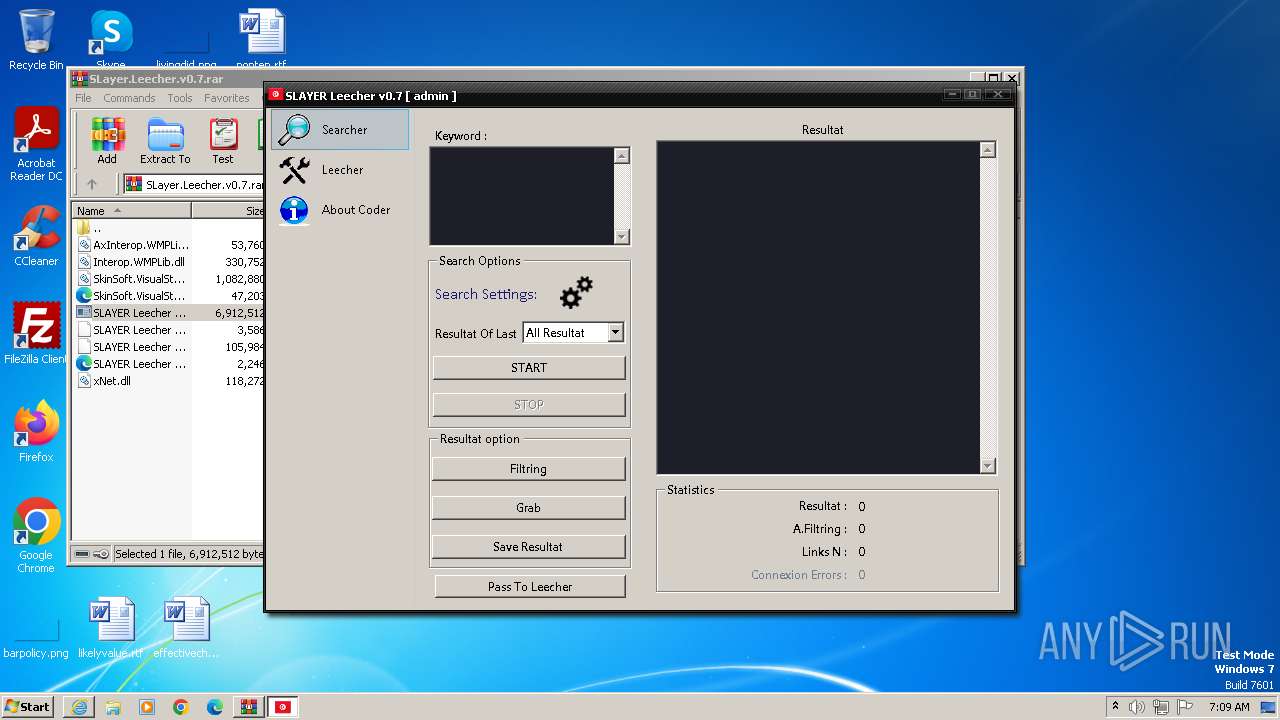
| Verdict: | Malicious activity |
| Analysis date: | October 29, 2023, 07:09:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| SHA1: | 351F46E109EC69876243D584D2D1BABDC56C48D9 |
| SHA256: | 5913264F4132C5D5EBEB8752F30AD2A061CEC79C8A2397A4C9C401BFED99336C |
| SSDEEP: | 3:N8tEdO6LxIpl2XAJArkCYKO1yLp8AXLYan:2uwwxUWAJArWK1LbLYan |
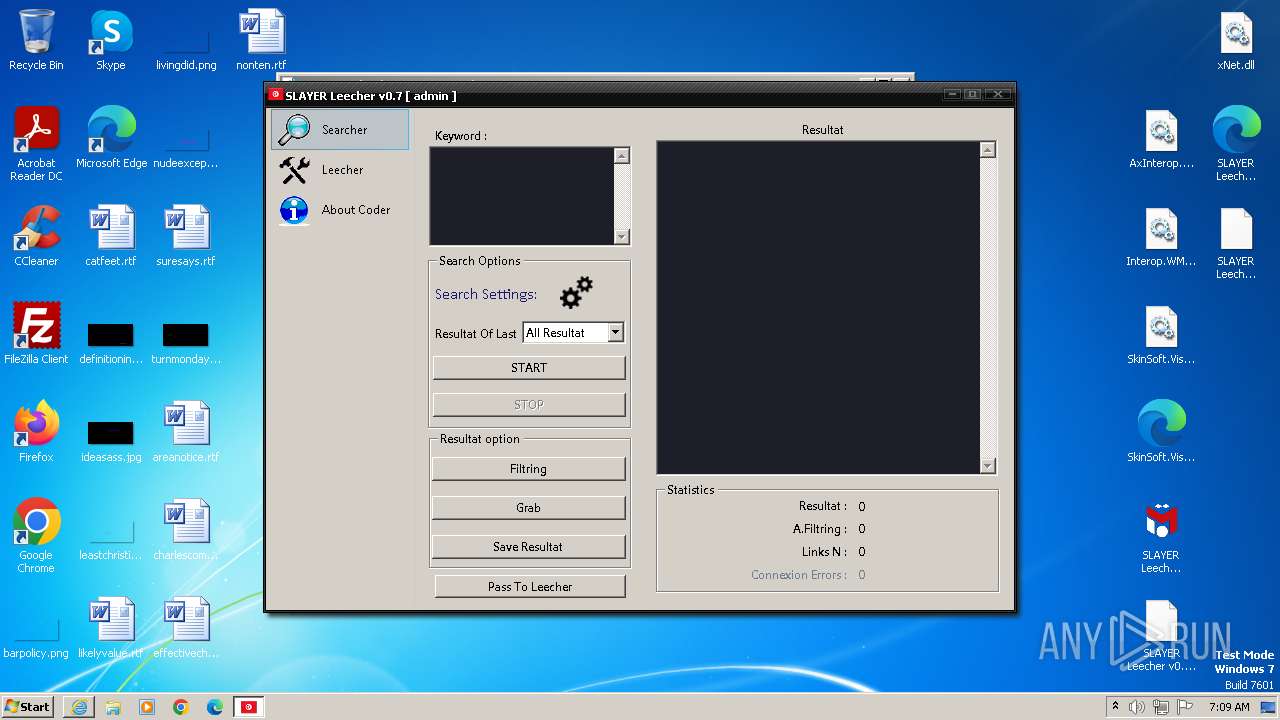
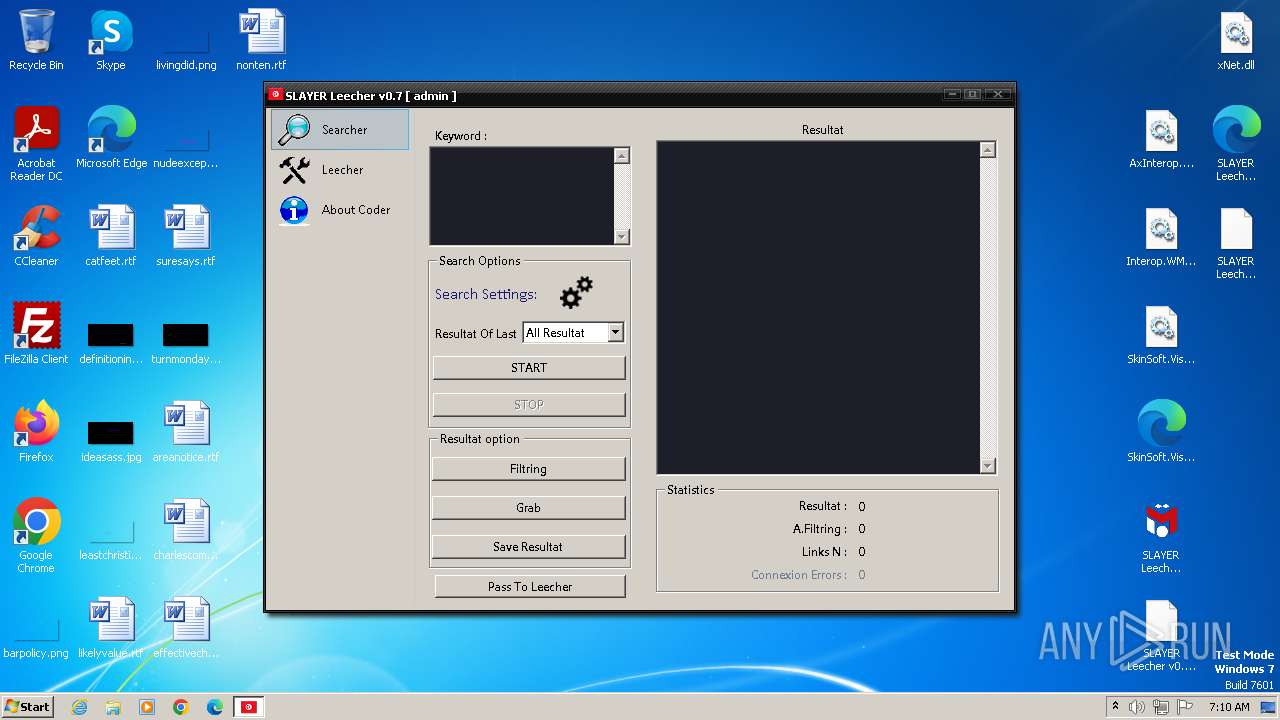
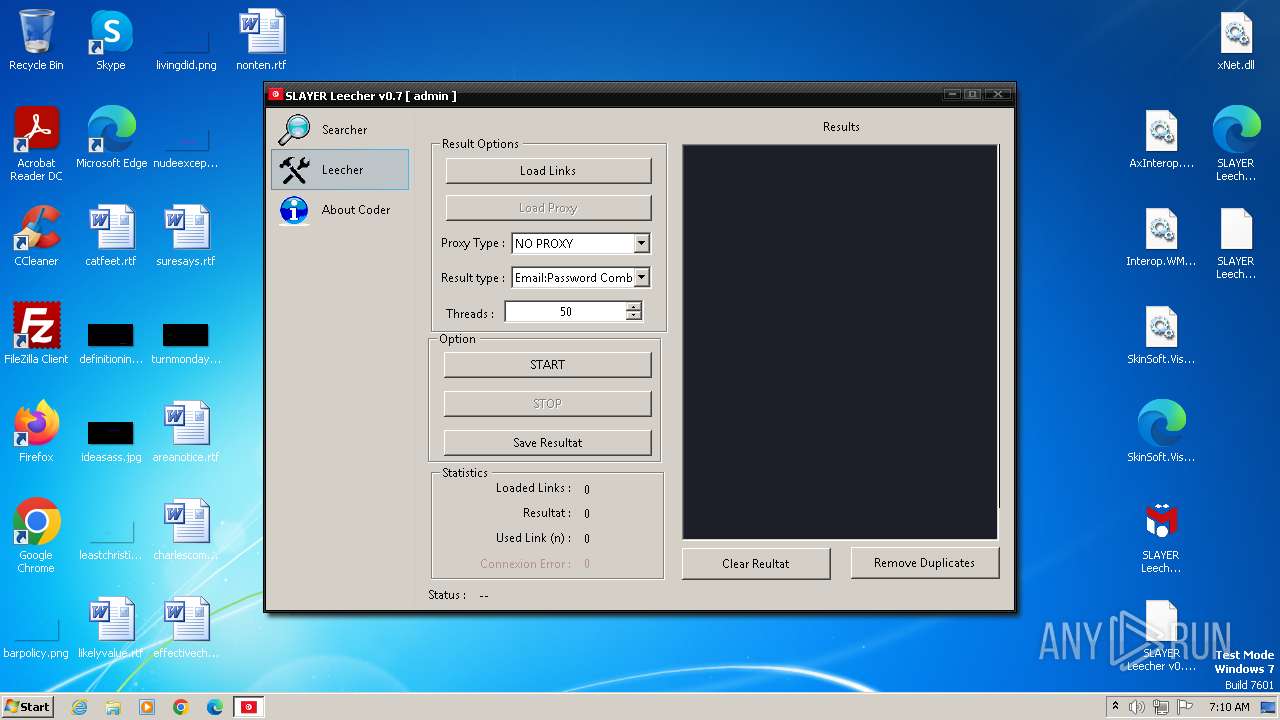
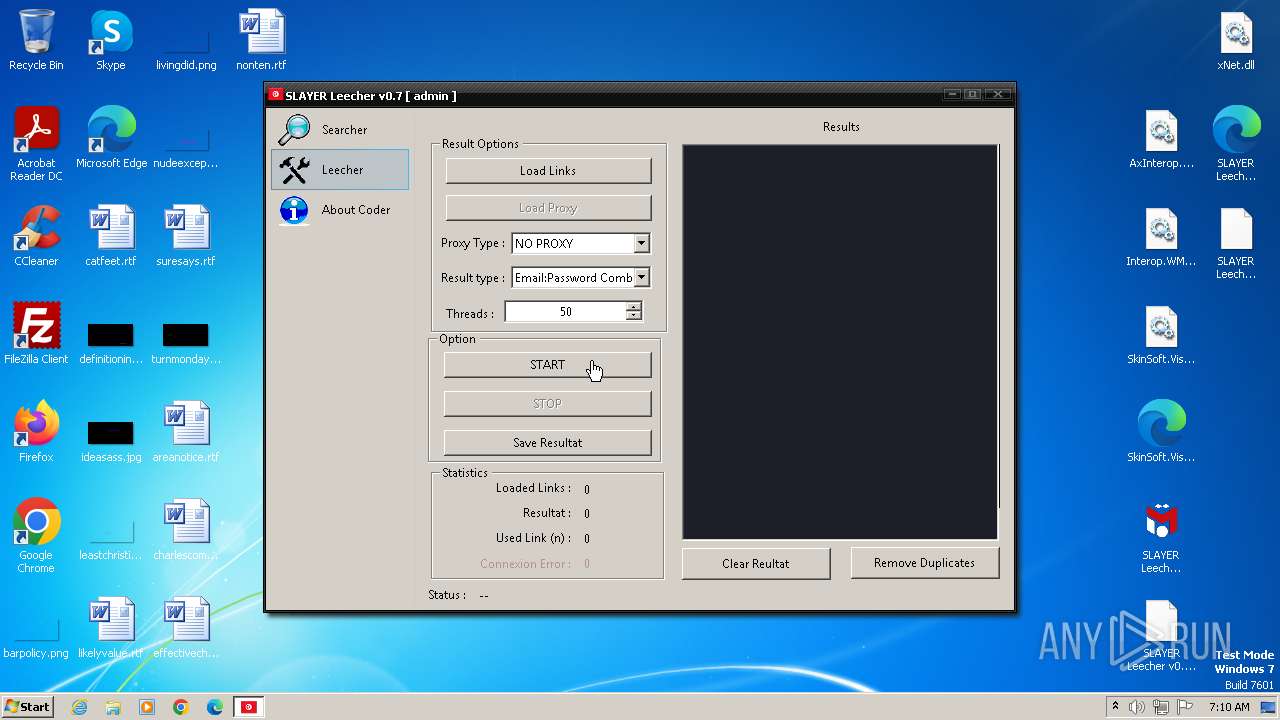
MALICIOUS
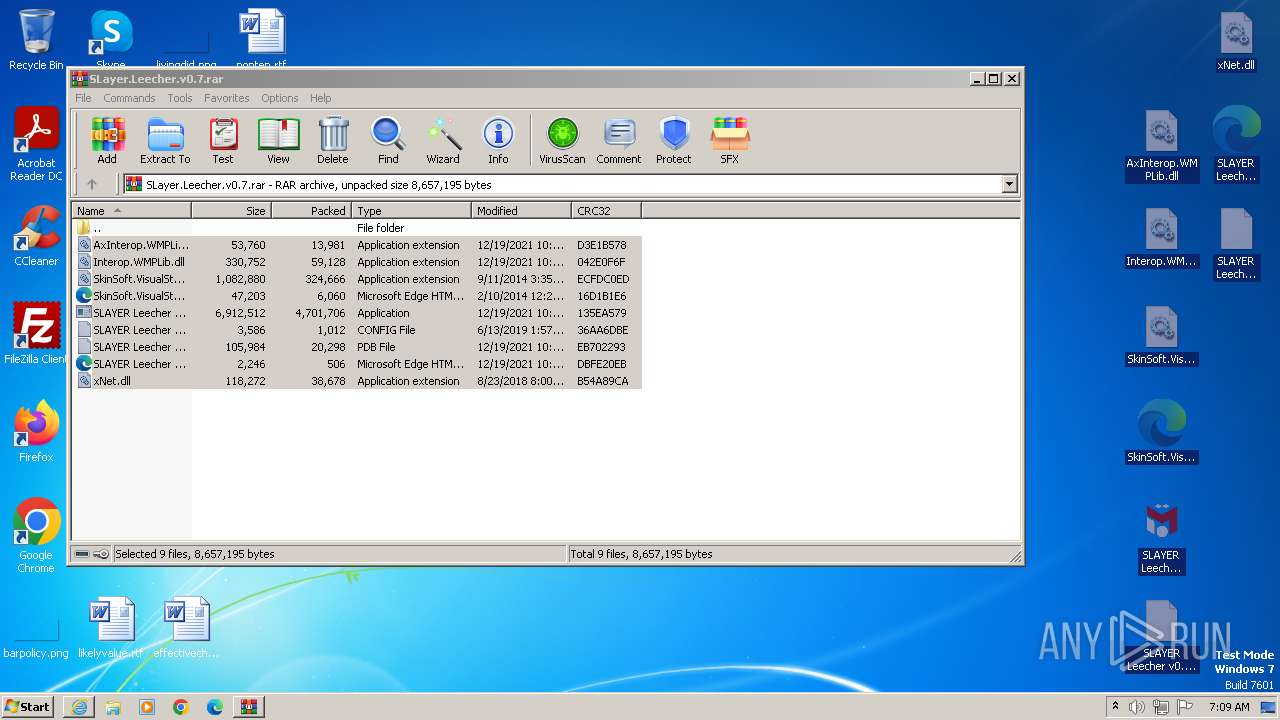
Application was dropped or rewritten from another process
- SLAYER Leecher v0.7.exe (PID: 2184)
- SLAYER Leecher v0.7.exe (PID: 2200)
Drops the executable file immediately after the start
- SLAYER Leecher v0.7.exe (PID: 2184)
Loads dropped or rewritten executable
- SLAYER Leecher v0.7.exe (PID: 2200)
SUSPICIOUS
Reads the Internet Settings
- SLAYER Leecher v0.7.exe (PID: 2184)
- SLAYER Leecher v0.7.exe (PID: 2200)
Reads Internet Explorer settings
- SLAYER Leecher v0.7.exe (PID: 2200)
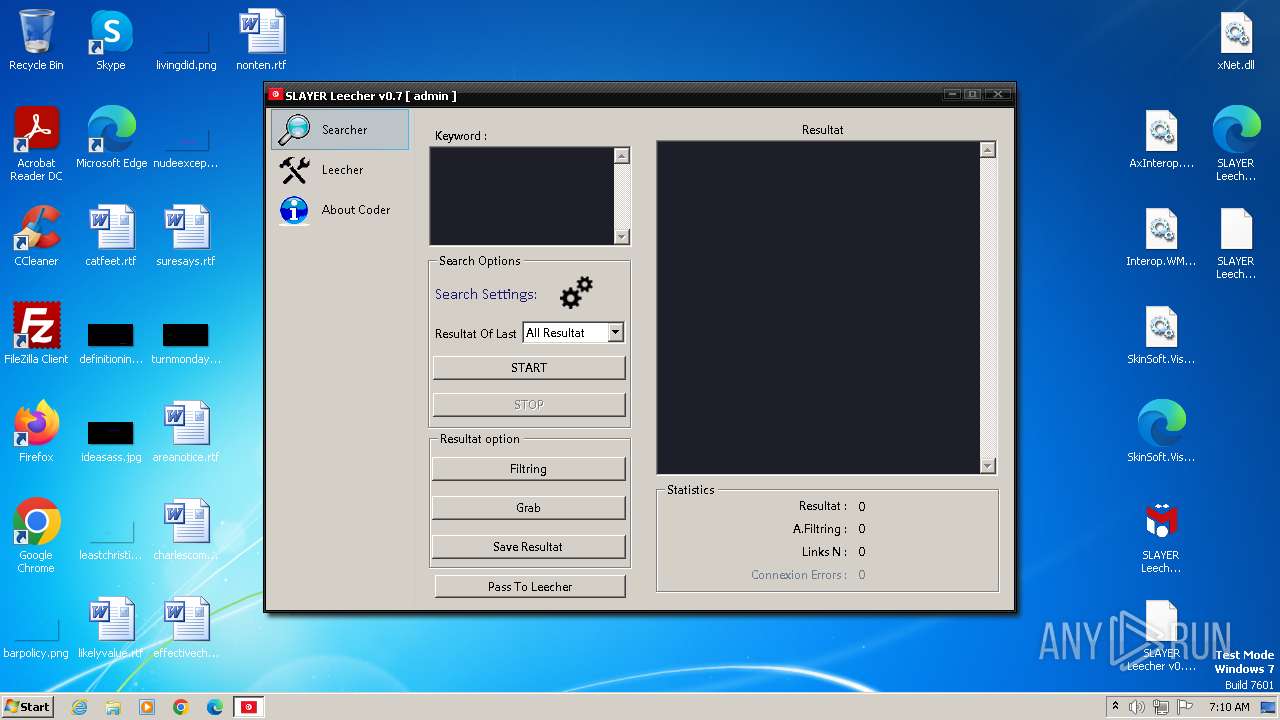
INFO
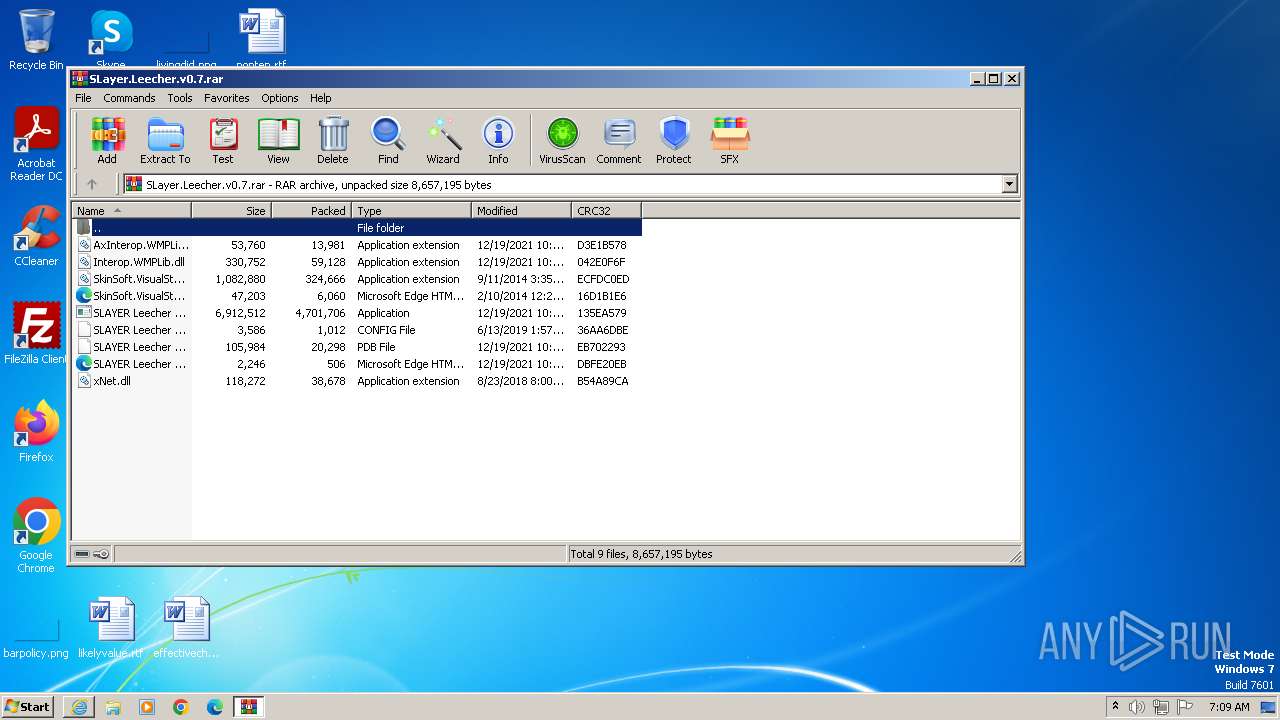
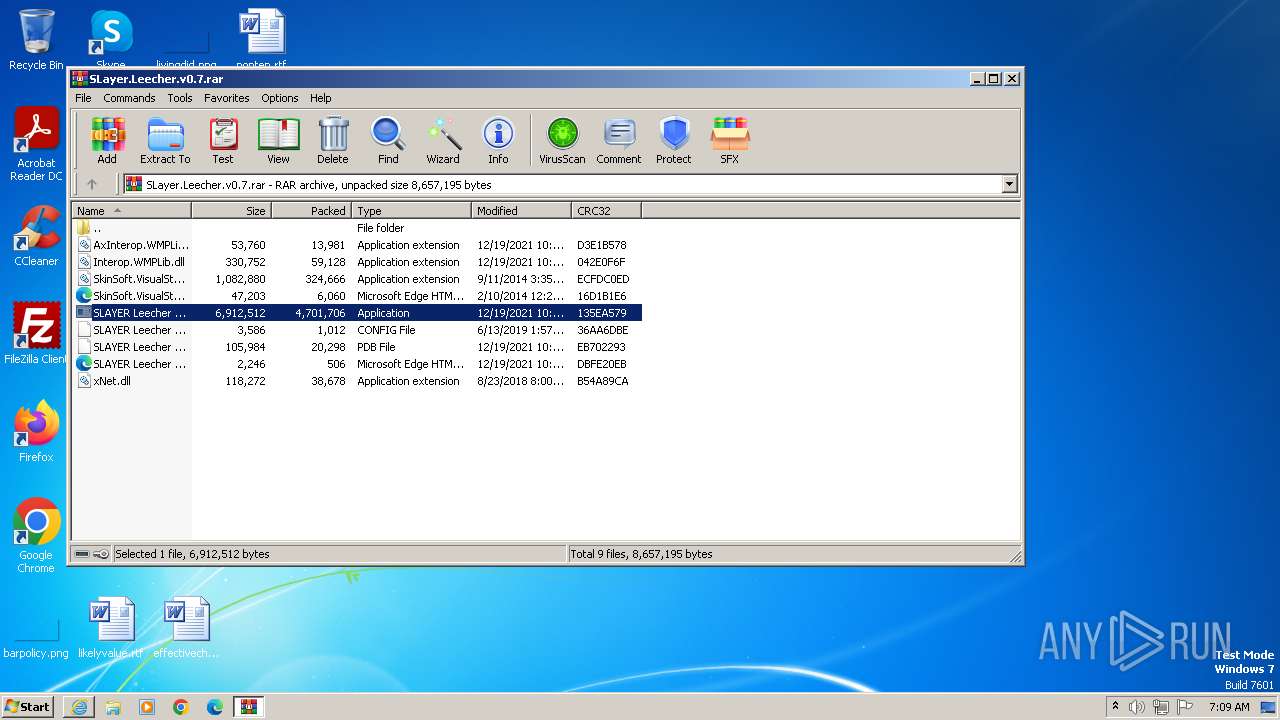
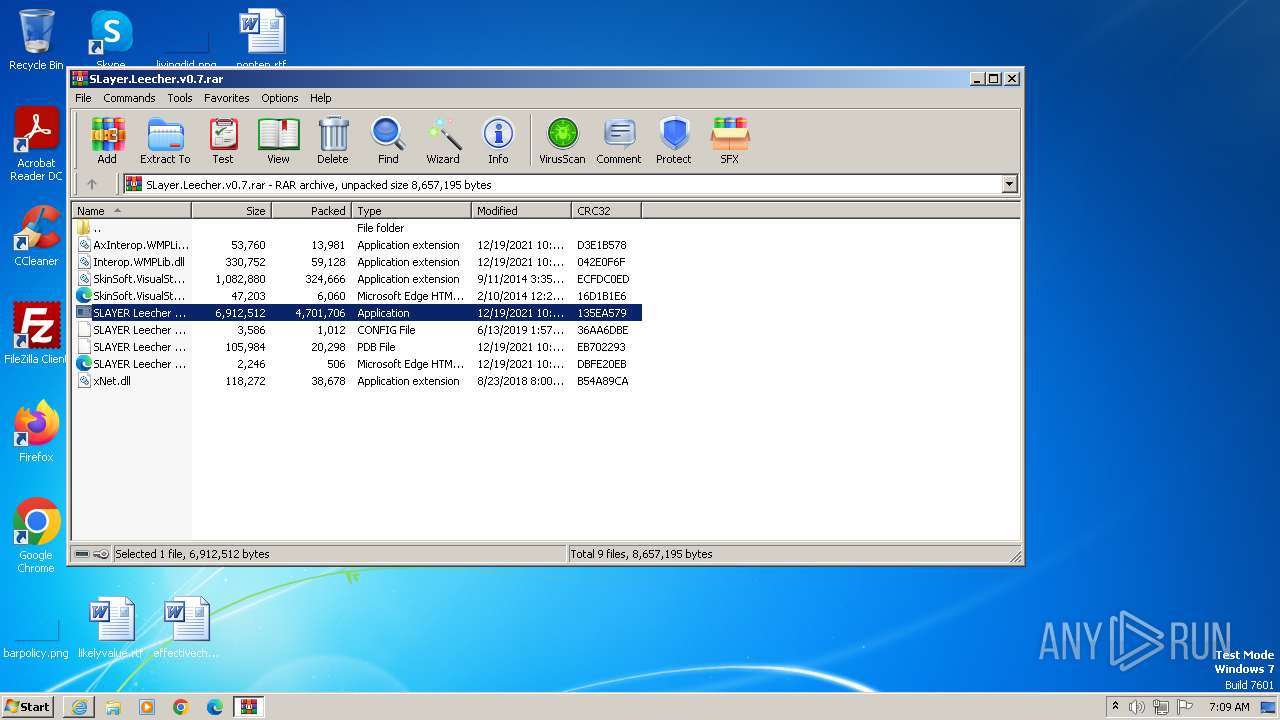
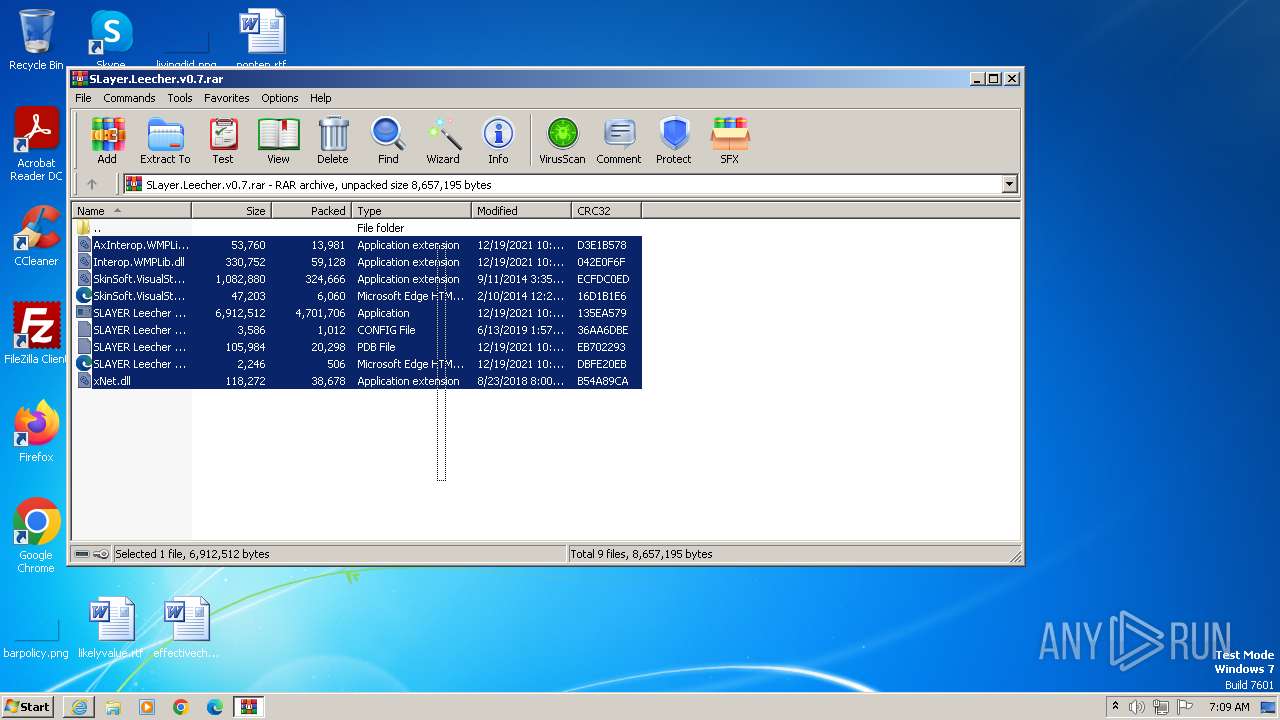
The process uses the downloaded file
- WinRAR.exe (PID: 2812)
- iexplore.exe (PID: 1764)
Application launched itself
- iexplore.exe (PID: 1764)
Reads the computer name
- SLAYER Leecher v0.7.exe (PID: 2184)
- SLAYER Leecher v0.7.exe (PID: 2200)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 2812)
Reads the machine GUID from the registry
- SLAYER Leecher v0.7.exe (PID: 2184)
- SLAYER Leecher v0.7.exe (PID: 2200)
Creates files or folders in the user directory
- SLAYER Leecher v0.7.exe (PID: 2184)
Checks supported languages
- SLAYER Leecher v0.7.exe (PID: 2184)
- SLAYER Leecher v0.7.exe (PID: 2200)
Manual execution by a user
- SLAYER Leecher v0.7.exe (PID: 2200)
Loads dropped or rewritten executable
- SLAYER Leecher v0.7.exe (PID: 2184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
42
Monitored processes
6
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
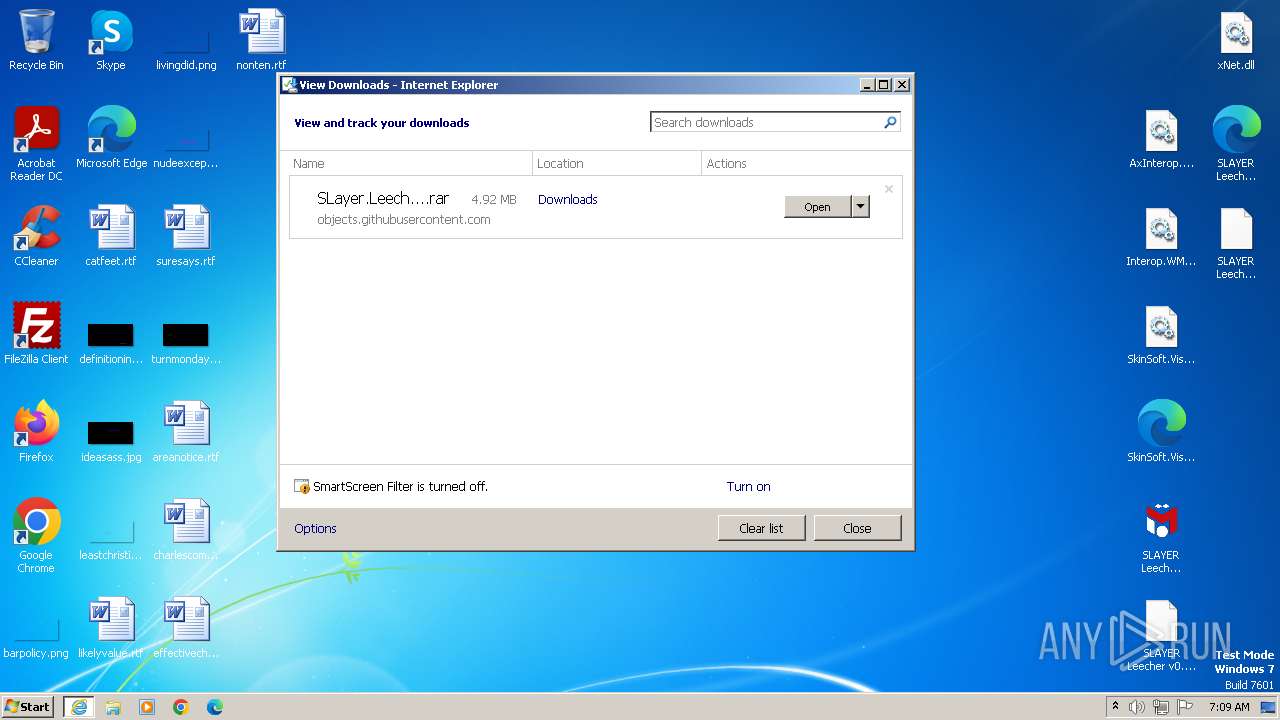
| 1764 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://github.com/X-SLAYER/SLAYER-LEECHER/releases/download/v0.7/SLayer.Leecher.v0.7.rar" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1908 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe6_ Global\UsGthrCtrlFltPipeMssGthrPipe6 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
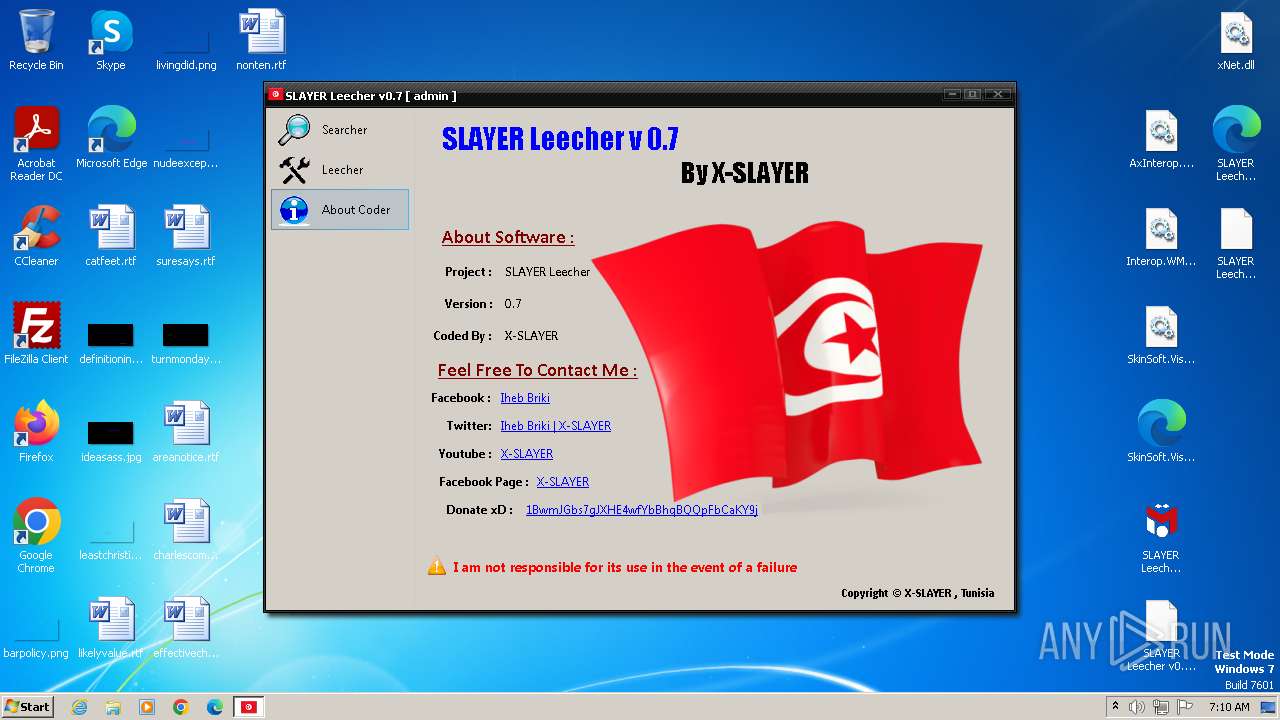
| 2184 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2812.36559\SLAYER Leecher v0.7.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2812.36559\SLAYER Leecher v0.7.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Iheb Briki Integrity Level: MEDIUM Description: SLAYER Leecher Exit code: 0 Version: 0.4.1 Modules
| |||||||||||||||
| 2200 | "C:\Users\admin\Desktop\SLAYER Leecher v0.7.exe" | C:\Users\admin\Desktop\SLAYER Leecher v0.7.exe | — | explorer.exe | |||||||||||
User: admin Company: Iheb Briki Integrity Level: MEDIUM Description: SLAYER Leecher Exit code: 0 Version: 0.4.1 Modules
| |||||||||||||||
| 2812 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\SLayer.Leecher.v0.7.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3148 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1764 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
12 105
Read events
12 024
Write events
80
Delete events
1
Modification events
| (PID) Process: | (1764) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (1764) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (1764) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (1764) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1764) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1764) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1764) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1764) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1764) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1764) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
11
Suspicious files
15
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3148 | iexplore.exe | C:\Users\admin\Downloads\SLayer.Leecher.v0.7.rar.jpahtjk.partial | — | |
MD5:— | SHA256:— | |||
| 1764 | iexplore.exe | C:\Users\admin\Downloads\SLayer.Leecher.v0.7.rar | — | |
MD5:— | SHA256:— | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:3F17B17012D32DBD0393D65322FDB694 | SHA256:509E4EDB4FB466EC3DD72FB5CA5ABFD66F2006CFA65FAF890BF9D46C7F1FA2B7 | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_ADE4E4D3A3BCBCA5C39C54D362D88565 | binary | |
MD5:44D2131EA969A322CF5FDF8C82E1DC56 | SHA256:AD235CB9E573731D5871542AD397645B771E0D1AD5C1AED69730F66B74E4B6B3 | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_ADE4E4D3A3BCBCA5C39C54D362D88565 | binary | |
MD5:4C903CE9BAE7C93EFF3A5A1BAC4E141B | SHA256:65D7BBAA91B300CCD87F9CE6E0102771A62DBD129E21C8C913F7443DBB6035BC | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\50CD3D75D026C82E2E718570BD6F44D0_D222662A57BAA60D2F5EA0D2CC7B2F1C | binary | |
MD5:978B6BD839025BC6981DF8C8F1DD898A | SHA256:E10855A3633487C385F4D1648D86340565303D3250617CDF1225E3BB934529CE | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\50CD3D75D026C82E2E718570BD6F44D0_D222662A57BAA60D2F5EA0D2CC7B2F1C | binary | |
MD5:45B80C69293663EED18B30C6FDE9148D | SHA256:D77F2E2EA8E19C9CC0AB81365F8D43C9511C1B7066B4046201A310B3E21B896C | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:6F3BC8F44A80D6DB76AC0ECE143A422D | SHA256:DCD322FE92F08400BC2A5136BCB230DEE7232B27A130B91670E4AB0F0C0C9651 | |||
| 1764 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF41EBDBD5CAB04A25.TMP | binary | |
MD5:B42D321266B60561F8353FEB992A1F91 | SHA256:ED96A3084E9DB6576C1FED3ADDAFBA3E1AF1E6C86F68C180EF2E4BF55E45CF05 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
9
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3148 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAfy81yHqHeveu%2FpR5k1Jb0%3D | US | der | 471 b | unknown |
3148 | iexplore.exe | GET | 200 | 67.27.234.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?ab121734c4c30a79 | US | compressed | 4.66 Kb | unknown |
3148 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | binary | 471 b | unknown |
3148 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrHR6YzPN2BNbByL0VoiTIBBMAOAQUCrwIKReMpTlteg7OM8cus%2B37w3oCEAzQqL7GMs%2FmReygqbCE%2Bxw%3D | US | binary | 312 b | unknown |
3148 | iexplore.exe | GET | 200 | 67.27.234.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?26be22f8eec632ad | US | compressed | 4.66 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2656 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3148 | iexplore.exe | 67.27.234.126:80 | ctldl.windowsupdate.com | LEVEL3 | US | unknown |
3148 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3148 | iexplore.exe | 185.199.109.133:443 | objects.githubusercontent.com | FASTLY | US | unknown |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
objects.githubusercontent.com |
| shared |