| File name: | Acrobyte SMS Verification Bypass.zip |
| Full analysis: | https://app.any.run/tasks/90a13ff4-74fe-49ec-a212-ecbc9260cc70 |
| Verdict: | Malicious activity |
| Analysis date: | May 14, 2021, 11:09:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | E1D51D7CAE936DF2968B9EAFFFF4B4A5 |
| SHA1: | EC1B14999CA1FE9DBD578533788FA3BD85A1F657 |
| SHA256: | 58FA34ADA1C771FCDA6BAF9E4FE7968A99B4BD06A0F090CB88C9352CC2926C48 |
| SSDEEP: | 196608:HgK00sVRifdZIs8oG38OvE0p7GDgZCdjrjgk/B0vtoEJR12B:MVRkB/GsEp7G6mrp/6R1M |
MALICIOUS
Writes to a start menu file
- libGLESV2.bin (PID: 3500)
- Acrobyte SMS Verification Bypass.exe (PID: 1440)
Application was dropped or rewritten from another process
- Runtime Broker.exe (PID: 2704)
Drops executable file immediately after starts
- Acrobyte SMS Verification Bypass.exe (PID: 1440)
SUSPICIOUS
Executable content was dropped or overwritten
- Acrobyte SMS Verification Bypass.exe (PID: 1440)
- libGLESV2.bin (PID: 3500)
Starts application with an unusual extension
- Acrobyte SMS Verification Bypass.exe (PID: 1440)
Creates files in the user directory
- libGLESV2.bin (PID: 3500)
Drops a file that was compiled in debug mode
- libGLESV2.bin (PID: 3500)
Creates files in the program directory
- Acrobyte SMS Verification Bypass.exe (PID: 1440)
Drops a file with a compile date too recent
- Acrobyte SMS Verification Bypass.exe (PID: 1440)
INFO
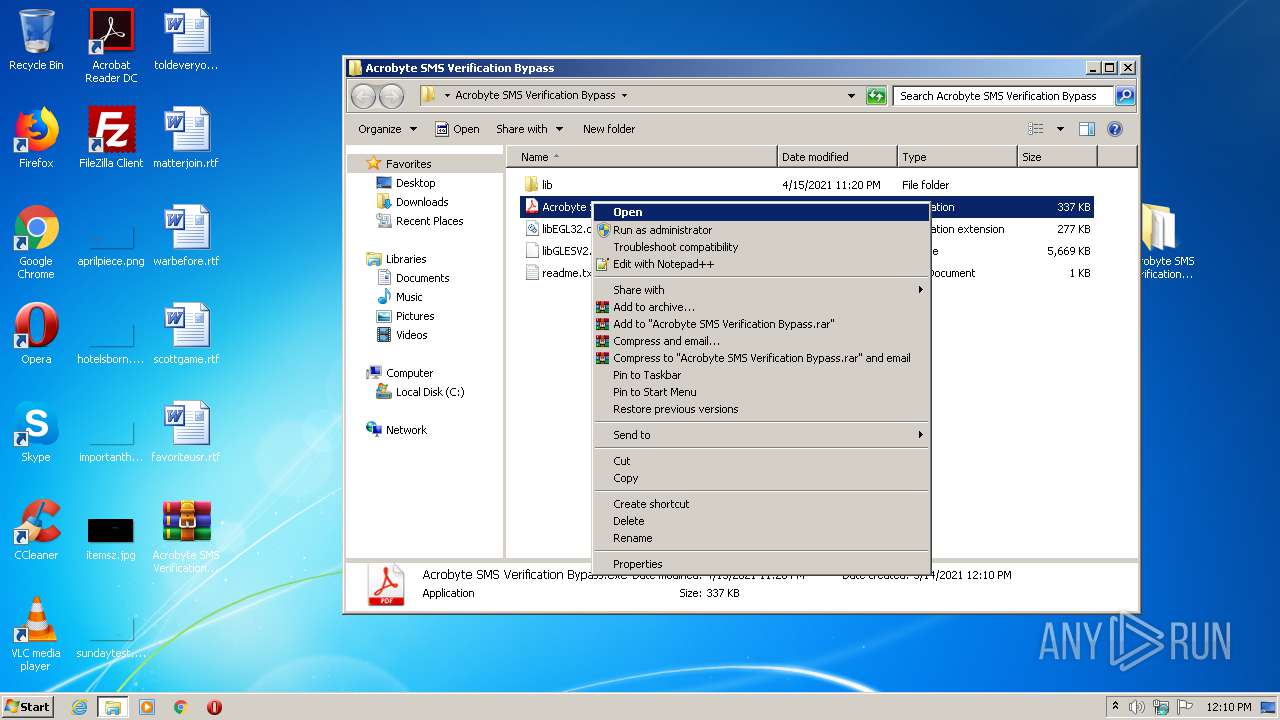
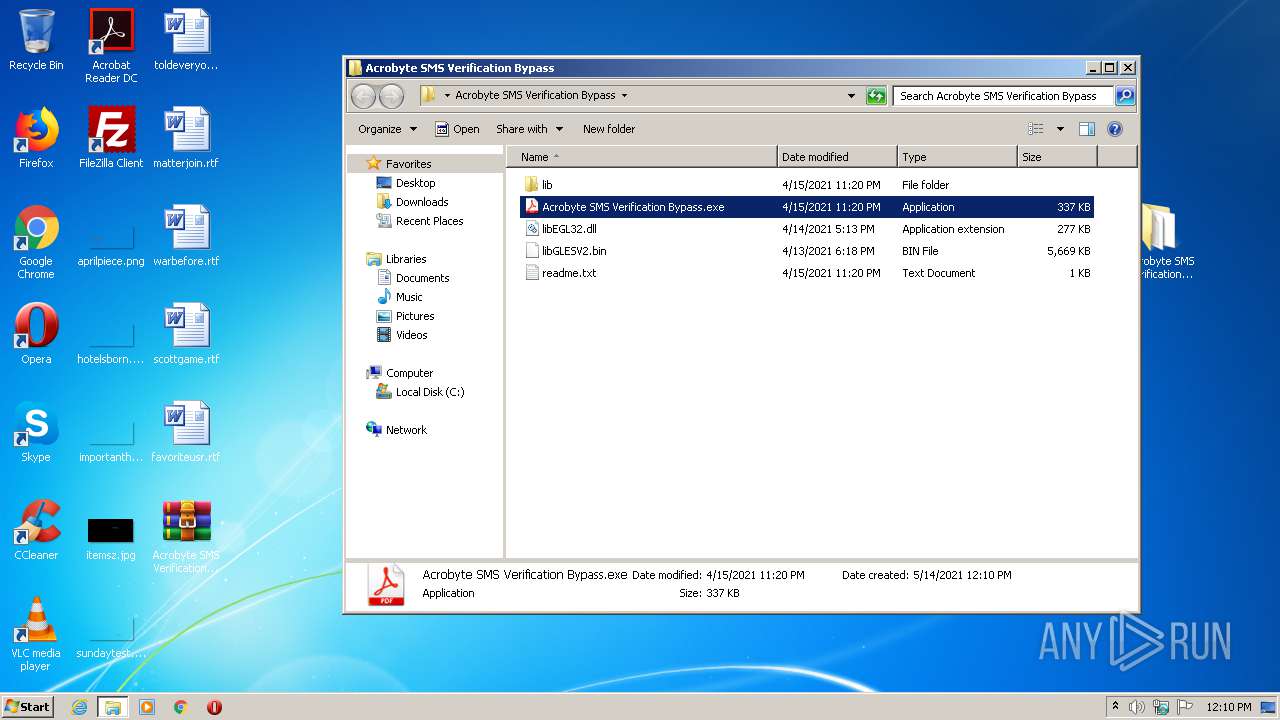
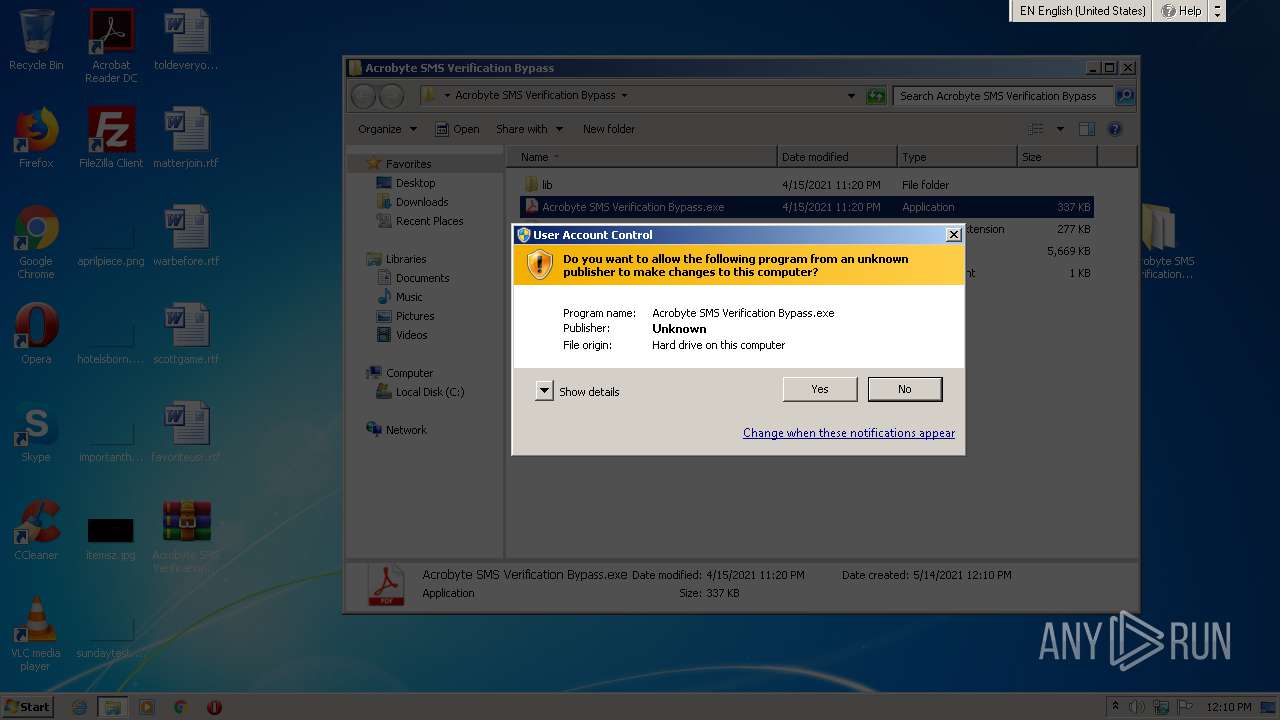
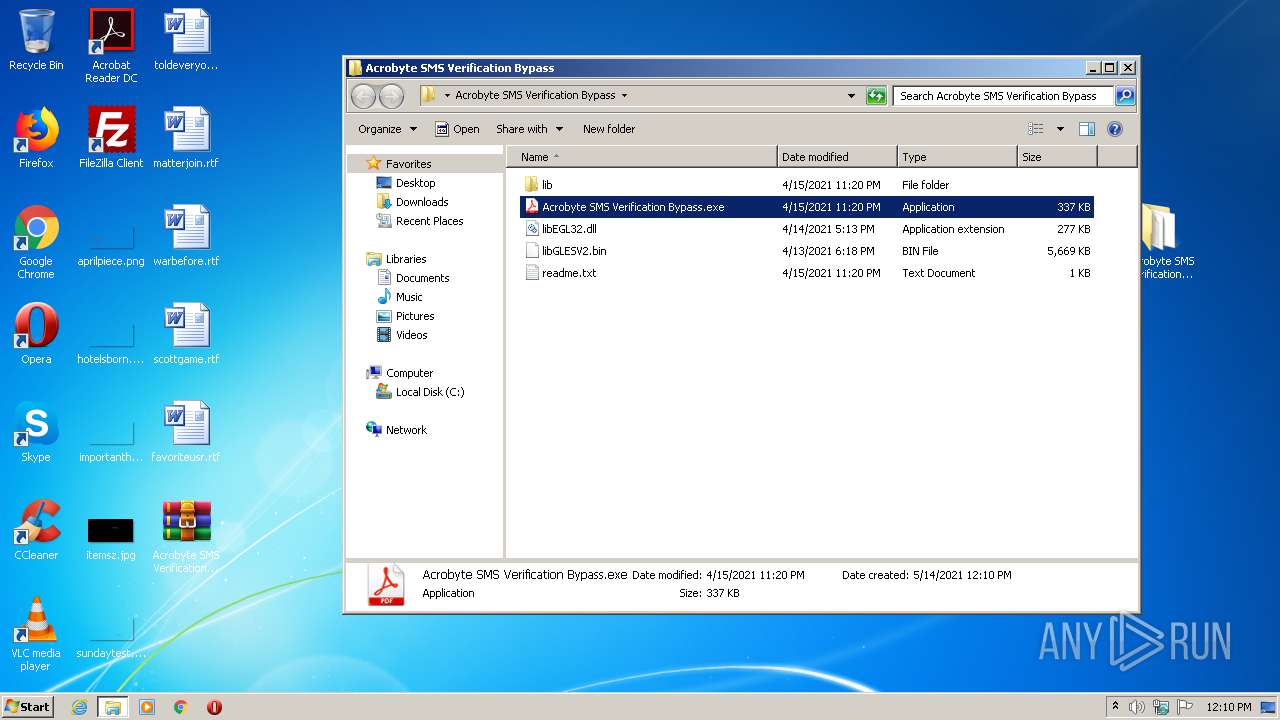
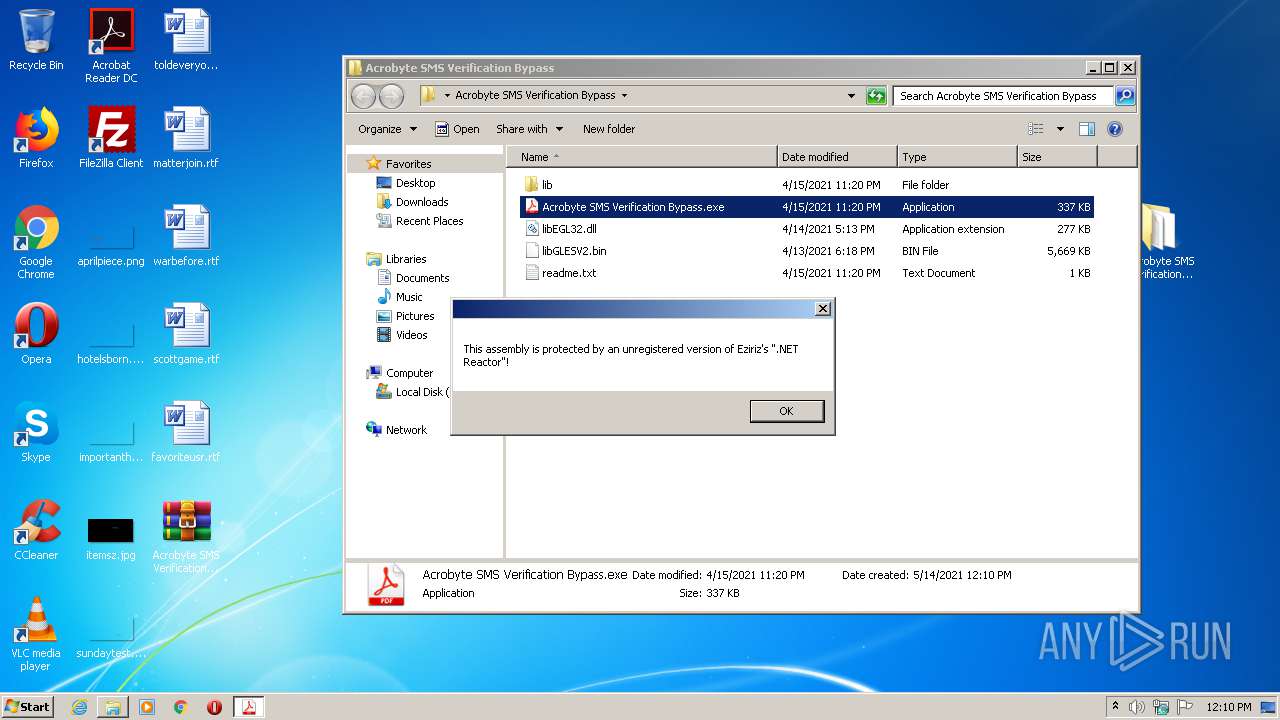
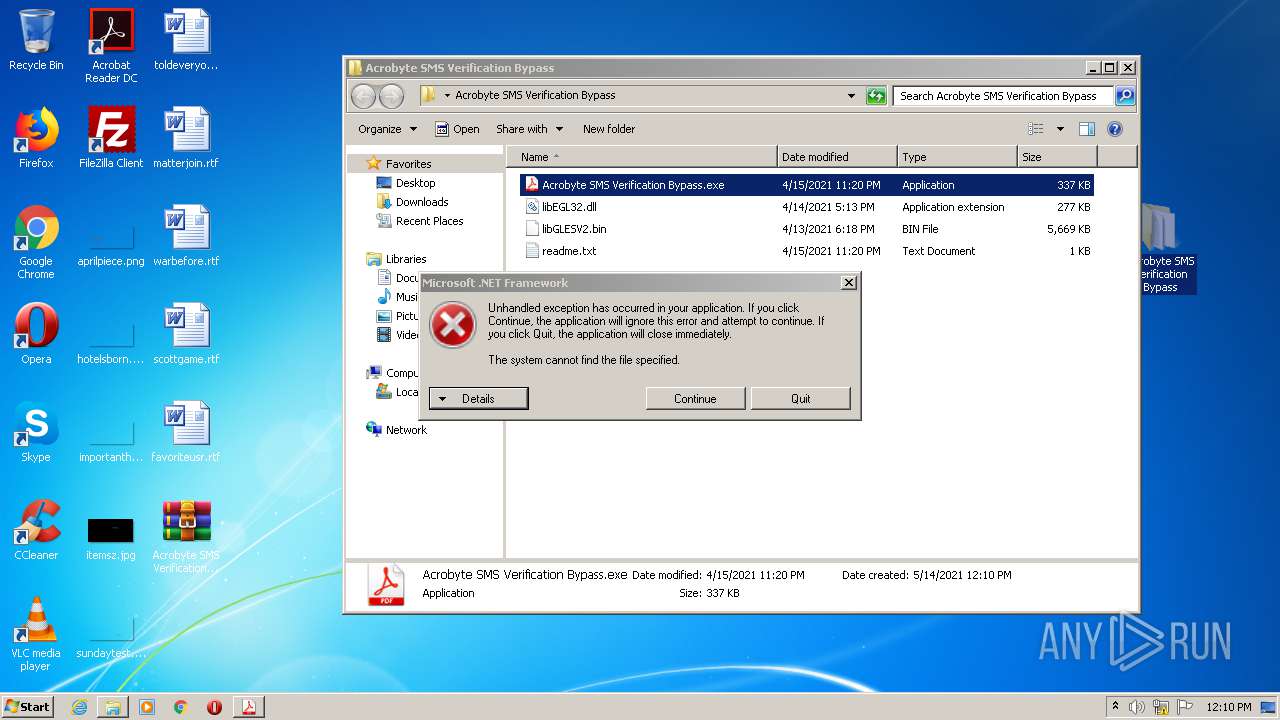
Manual execution by user
- Acrobyte SMS Verification Bypass.exe (PID: 1440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
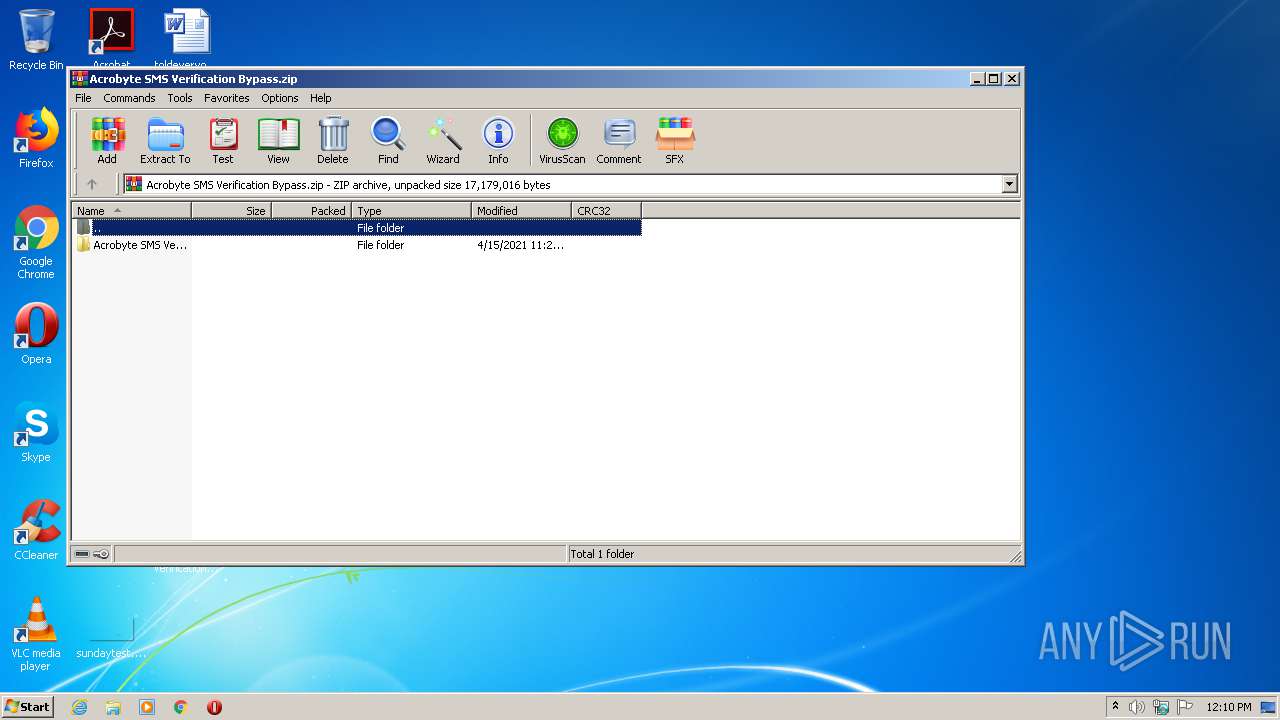
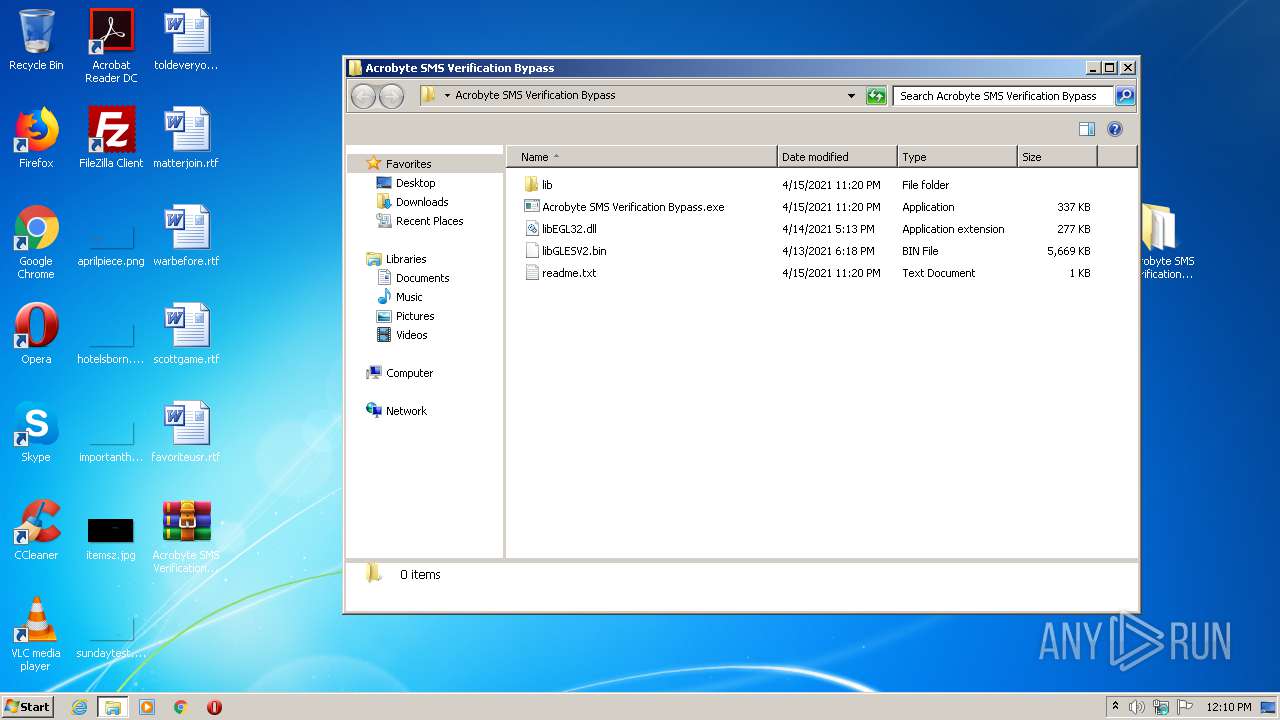
| ZipFileName: | Acrobyte SMS Verification Bypass/ |
|---|---|
| ZipUncompressedSize: | - |
| ZipCompressedSize: | - |
| ZipCRC: | 0x00000000 |
| ZipModifyDate: | 2021:04:15 19:20:24 |
| ZipCompression: | None |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 10 |
Total processes
47
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
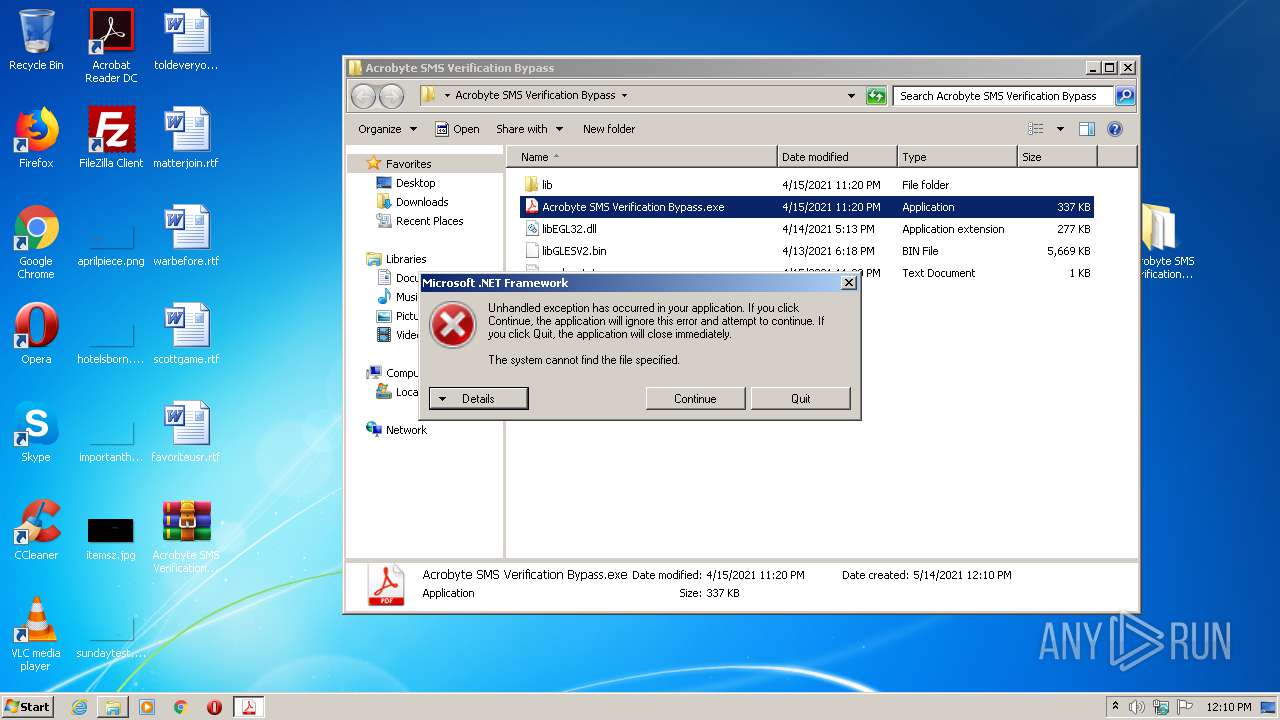
| 1440 | "C:\Users\admin\Desktop\Acrobyte SMS Verification Bypass\Acrobyte SMS Verification Bypass.exe" | C:\Users\admin\Desktop\Acrobyte SMS Verification Bypass\Acrobyte SMS Verification Bypass.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2704 | "C:\\ProgramData\\Windows Portable Clipboard\\Runtime Broker.exe" | C:\ProgramData\Windows Portable Clipboard\Runtime Broker.exe | — | Acrobyte SMS Verification Bypass.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Runtime Broker Exit code: 0 Version: 10.0.19041.1 Modules
| |||||||||||||||
| 3500 | "libGLESV2.bin" | C:\Users\admin\Desktop\Acrobyte SMS Verification Bypass\libGLESV2.bin | Acrobyte SMS Verification Bypass.exe | ||||||||||||
User: admin Company: Acrobyte Hacks Integrity Level: HIGH Description: Acrobyte SMS Verification Bypass Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
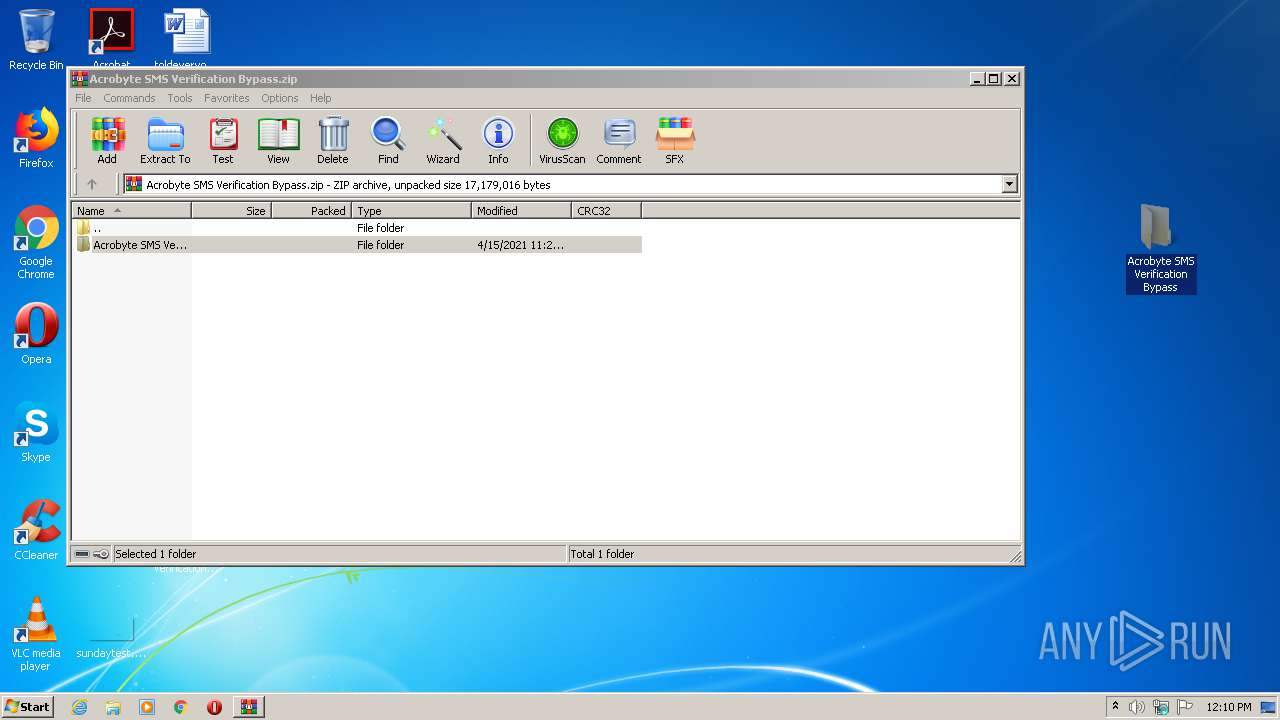
| 3704 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Acrobyte SMS Verification Bypass.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
558
Read events
528
Write events
30
Delete events
0
Modification events
| (PID) Process: | (3704) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3704) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3704) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3704) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (3704) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Acrobyte SMS Verification Bypass.zip | |||
| (PID) Process: | (3704) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3704) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3704) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3704) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3704) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
24
Suspicious files
0
Text files
3
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3704 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3704.45921\Acrobyte SMS Verification Bypass\Acrobyte SMS Verification Bypass.exe | — | |
MD5:— | SHA256:— | |||
| 3704 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3704.45921\Acrobyte SMS Verification Bypass\lib\btc.exe.manifest | — | |
MD5:— | SHA256:— | |||
| 3704 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3704.45921\Acrobyte SMS Verification Bypass\lib\bz2.pyd | — | |
MD5:— | SHA256:— | |||
| 3704 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3704.45921\Acrobyte SMS Verification Bypass\lib\Microsoft.VC90.CRT.manifest | — | |
MD5:— | SHA256:— | |||
| 3704 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3704.45921\Acrobyte SMS Verification Bypass\lib\msvcm90.dll | — | |
MD5:— | SHA256:— | |||
| 3704 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3704.45921\Acrobyte SMS Verification Bypass\lib\msvcp90.dll | — | |
MD5:— | SHA256:— | |||
| 3704 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3704.45921\Acrobyte SMS Verification Bypass\lib\msvcr90.dll | — | |
MD5:— | SHA256:— | |||
| 3704 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3704.45921\Acrobyte SMS Verification Bypass\lib\perfmon.pyd | — | |
MD5:— | SHA256:— | |||
| 3704 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3704.45921\Acrobyte SMS Verification Bypass\lib\pyconfig.h | — | |
MD5:— | SHA256:— | |||
| 3704 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3704.45921\Acrobyte SMS Verification Bypass\lib\pyexpat.pyd | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report