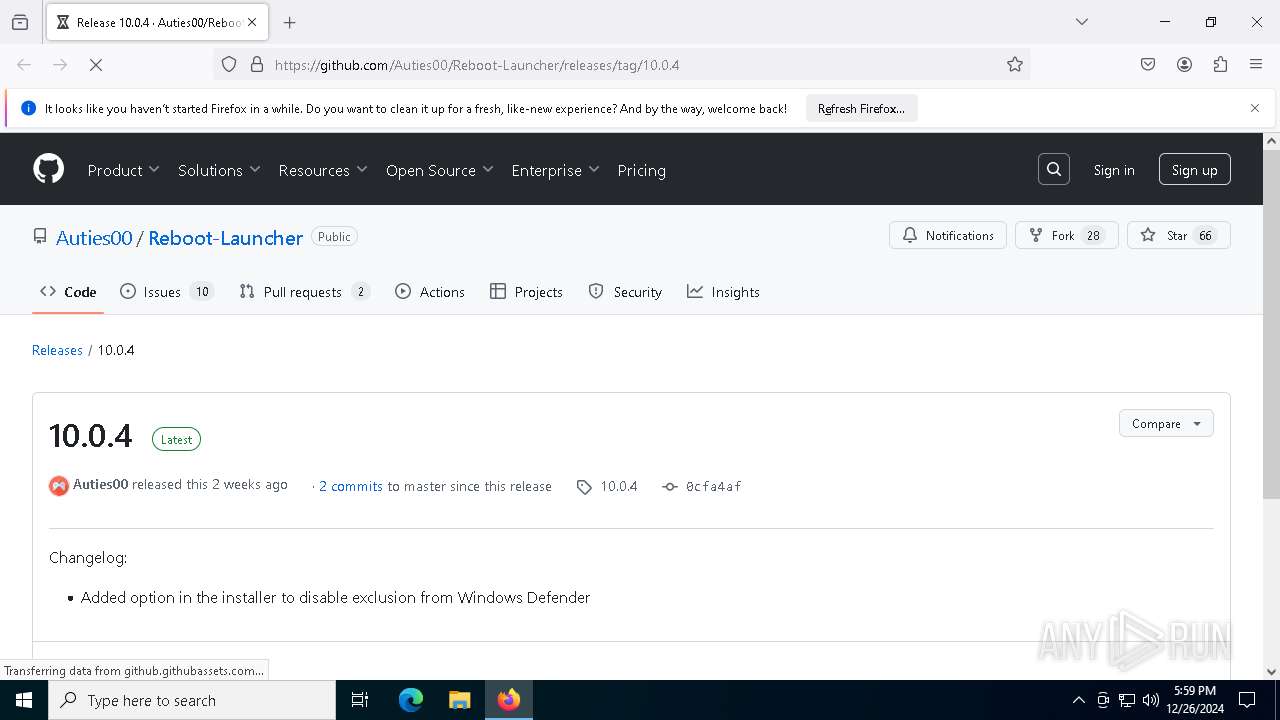
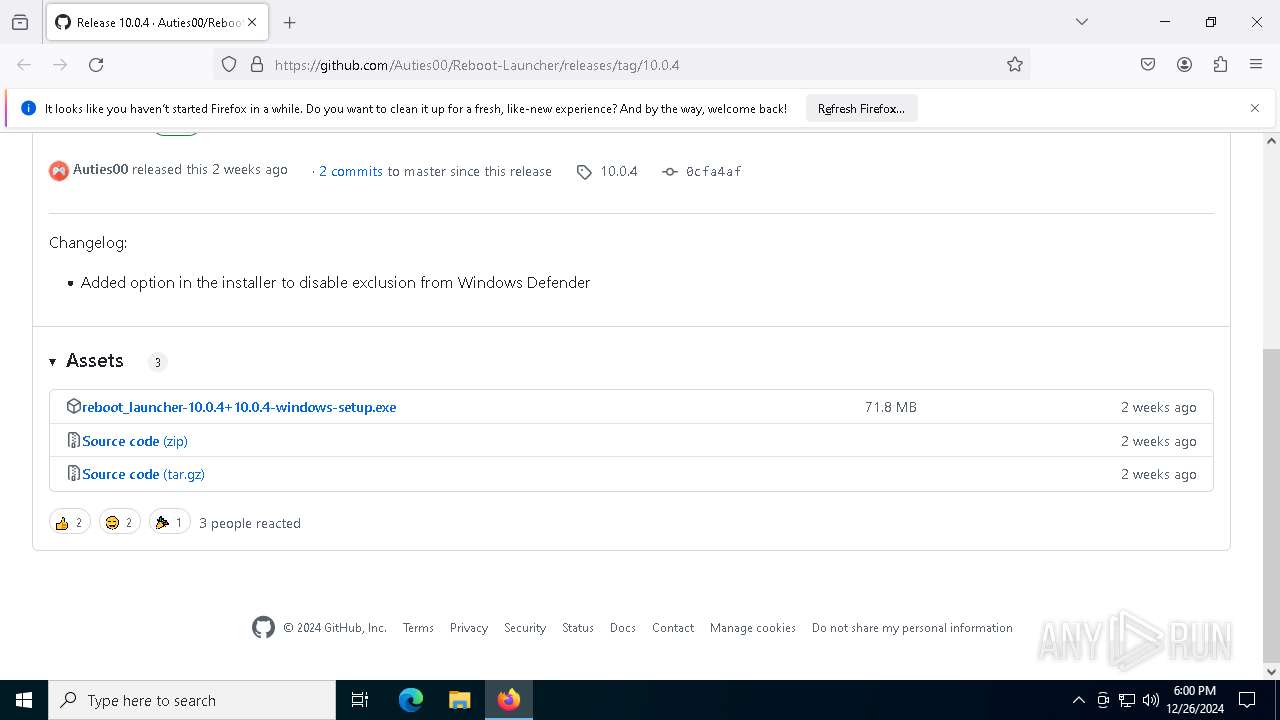
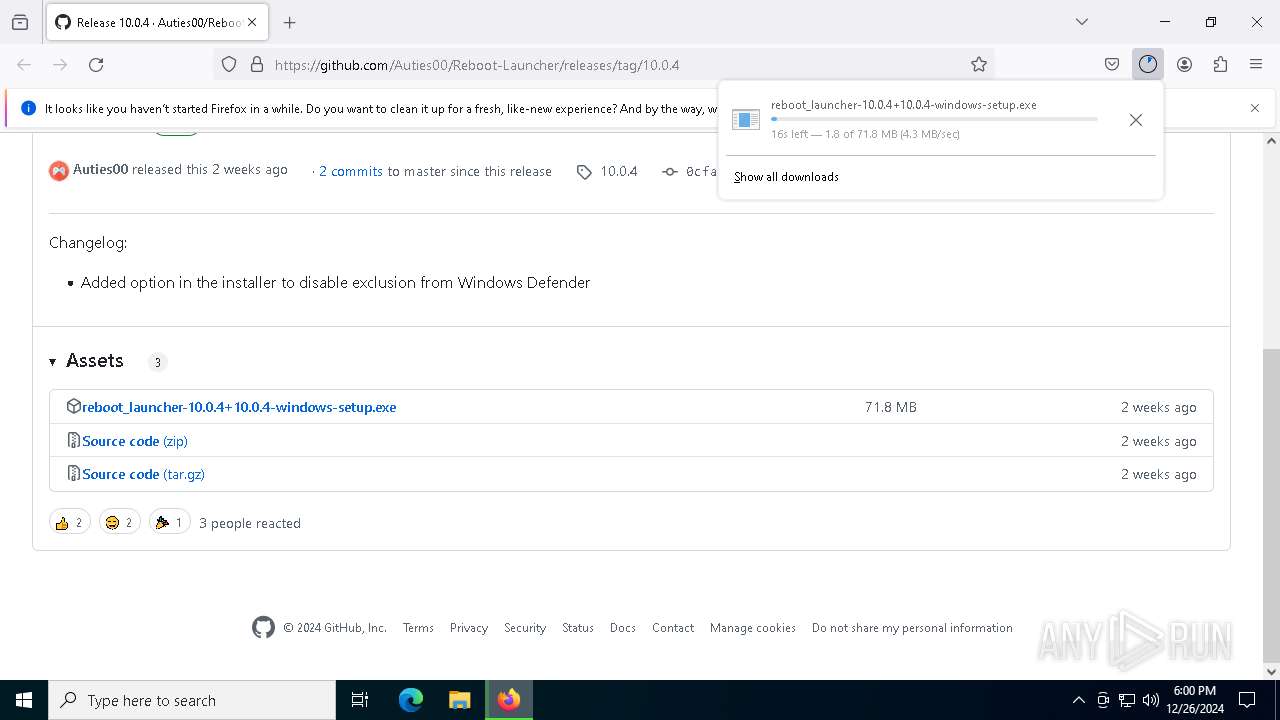
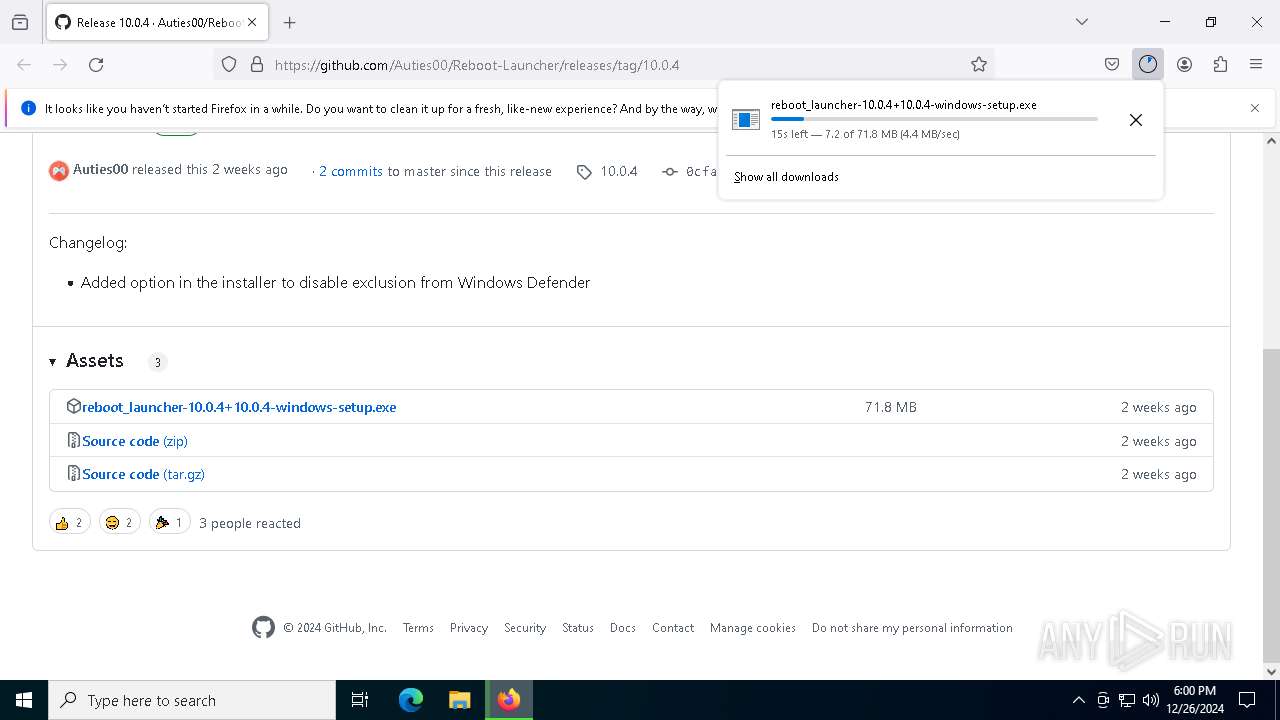
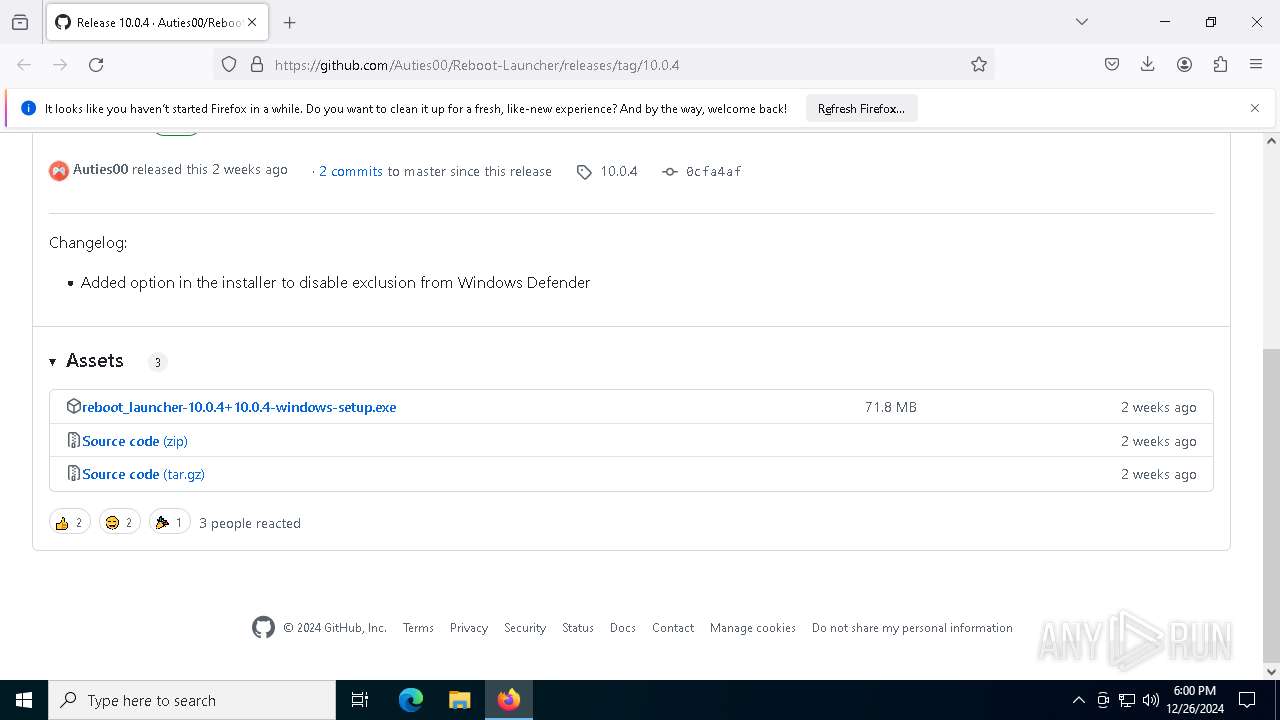
| URL: | https://github.com/Auties00/Reboot-Launcher/releases/tag/10.0.4 |
| Full analysis: | https://app.any.run/tasks/00ef5e4e-2d3b-4bce-b90f-f2e26e0c1a5e |
| Verdict: | Malicious activity |
| Analysis date: | December 26, 2024, 17:59:50 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | BC6D7C0A788B57DCCFD4570C5CE001A6 |
| SHA1: | 016297C62E8F7B266596ECC7E4CEF0F6AF6B9644 |
| SHA256: | 58EE94FCA180DC792B2CE55D7A46A2318D4FFFFB8F643B3A0F4DC2CD72467CE2 |
| SSDEEP: | 3:N8tEdfB9yRRL1E2qKKH:2udvoL1rxY |
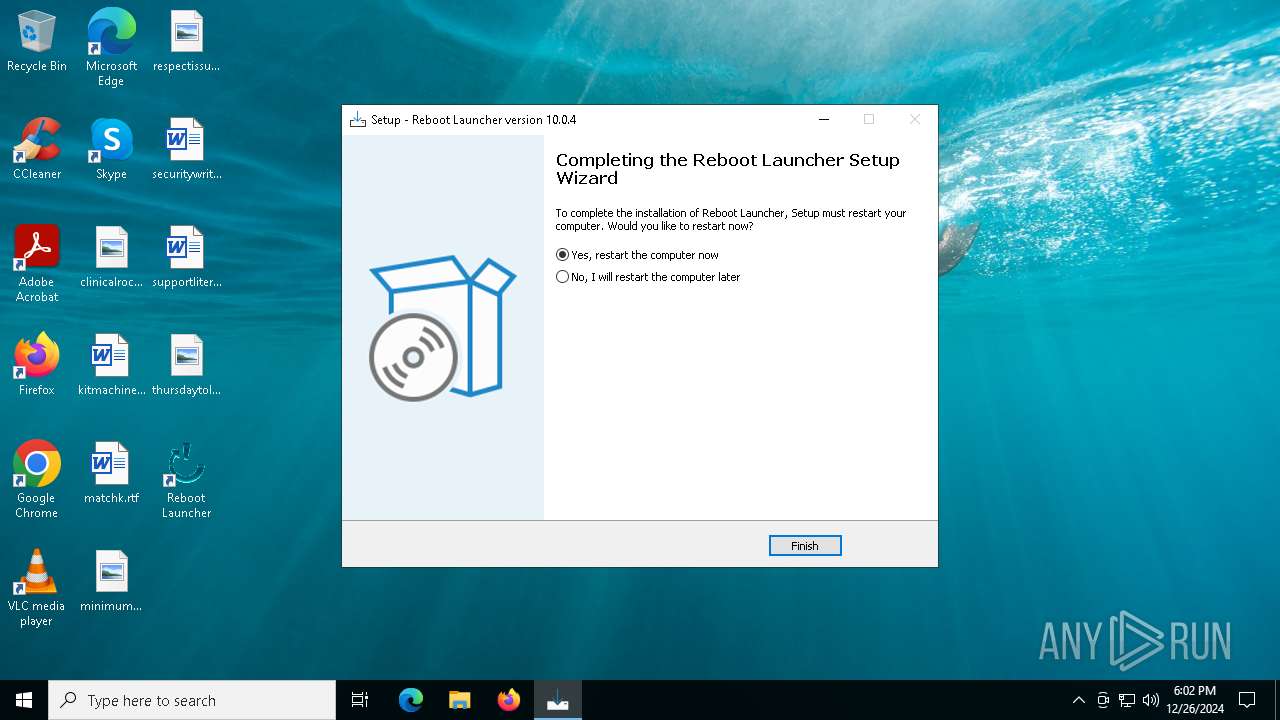
MALICIOUS
Changes the autorun value in the registry
- VC_redist.x64.exe (PID: 7228)
SUSPICIOUS
Reads security settings of Internet Explorer
- reboot_launcher-10.0.4+10.0.4-windows-setup.tmp (PID: 1296)
- VC_redist.x64.exe (PID: 4872)
- VC_redist.x64.exe (PID: 2132)
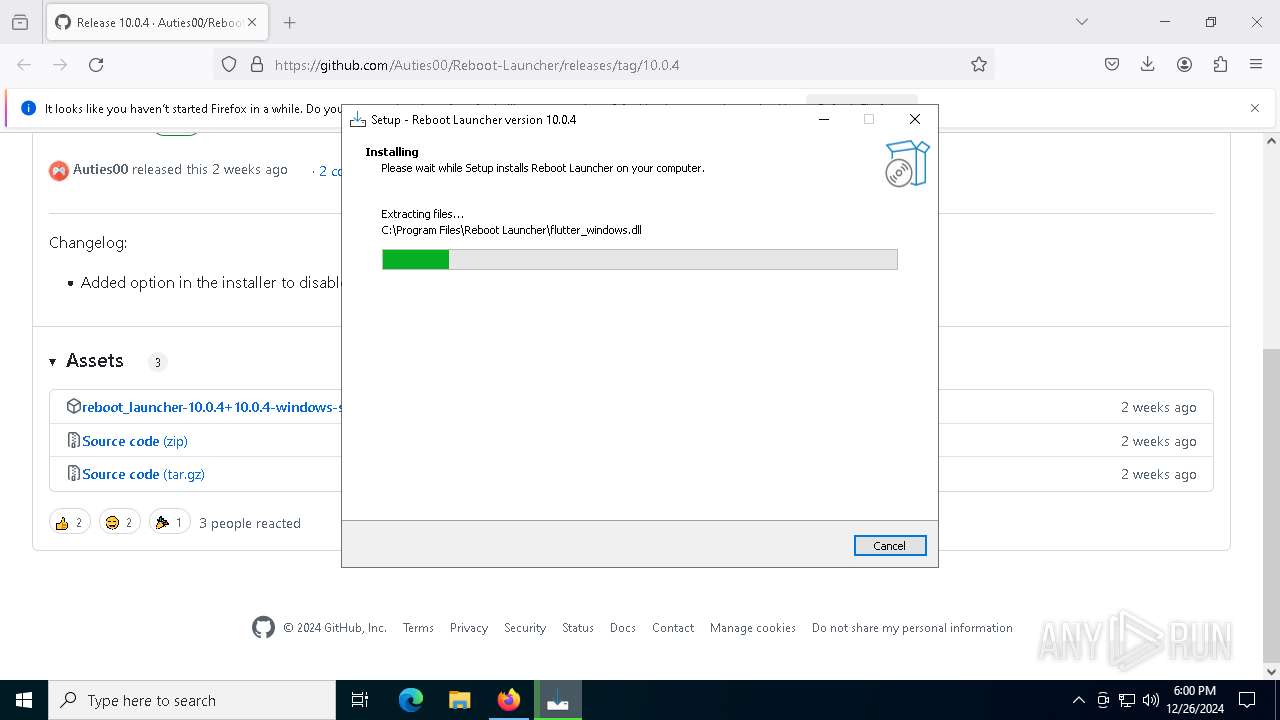
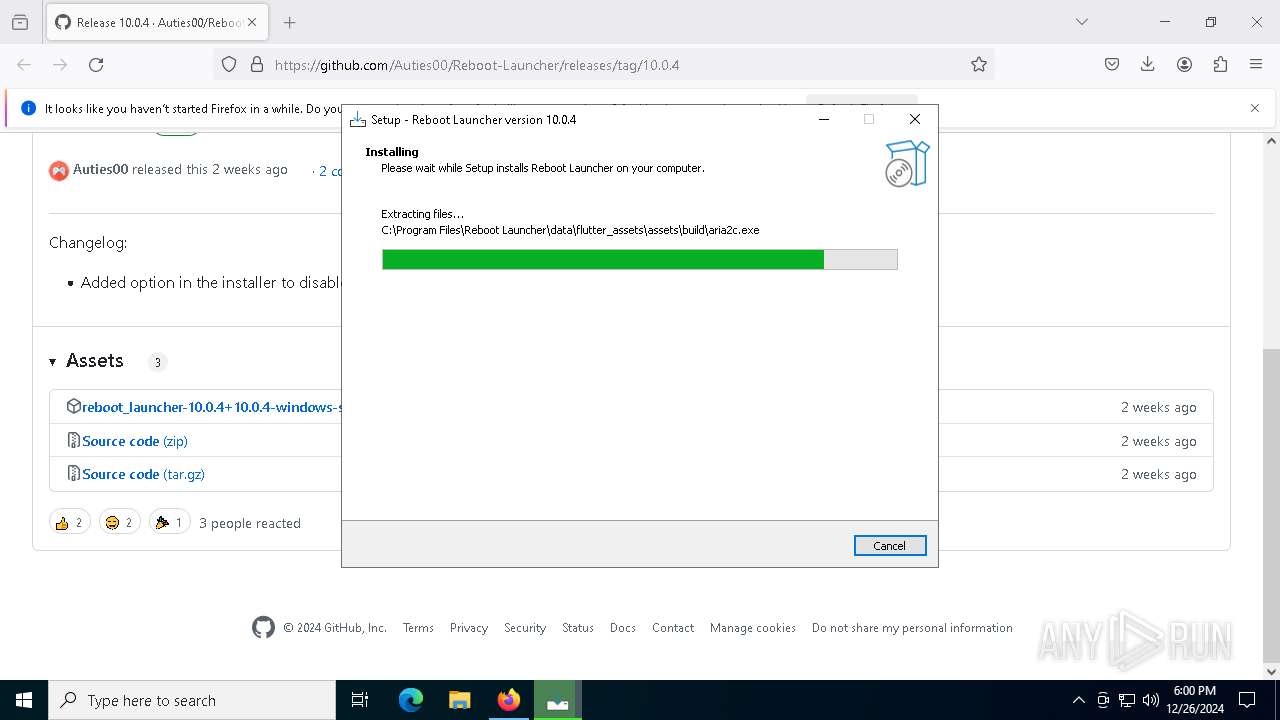
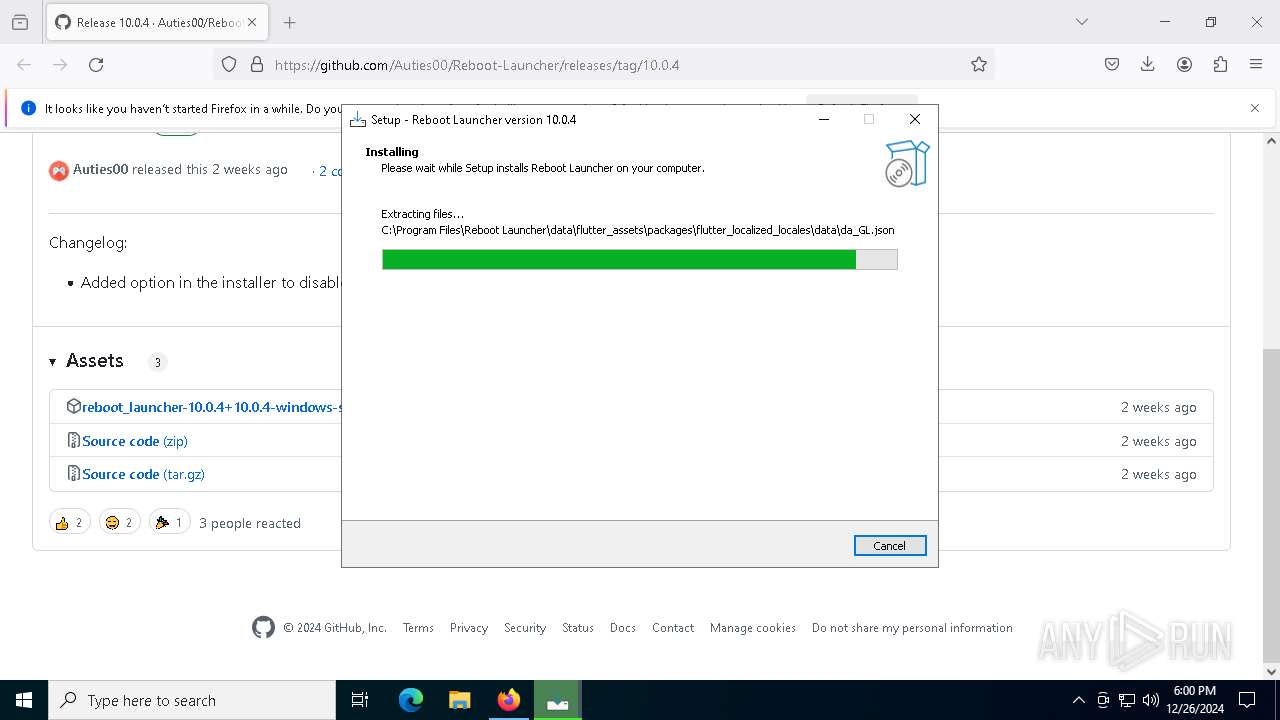
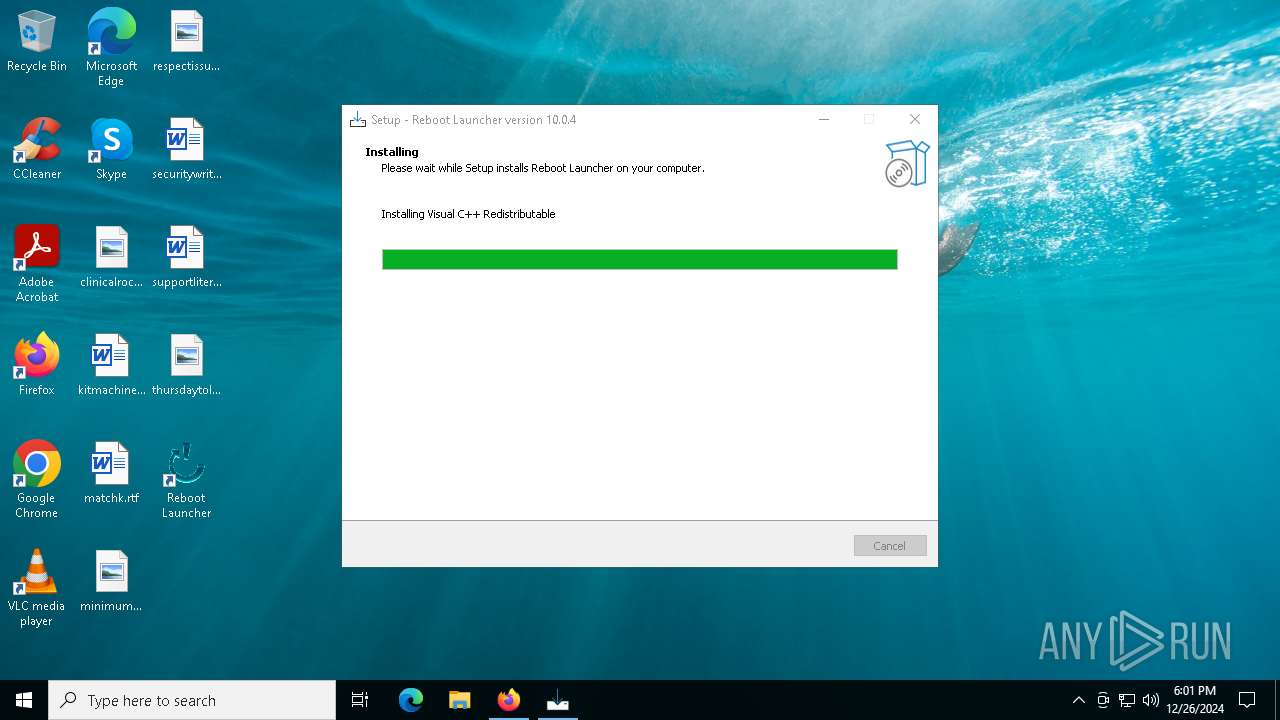
Executable content was dropped or overwritten
- reboot_launcher-10.0.4+10.0.4-windows-setup.exe (PID: 6012)
- reboot_launcher-10.0.4+10.0.4-windows-setup.tmp (PID: 5244)
- reboot_launcher-10.0.4+10.0.4-windows-setup.exe (PID: 4520)
- VC_redist.x64.exe (PID: 4872)
- VC_redist.x64.exe (PID: 8092)
- VC_redist.x64.exe (PID: 7228)
- VC_redist.x64.exe (PID: 2132)
- VC_redist.x64.exe (PID: 6700)
- reboot_launcher.exe (PID: 3288)
Reads the Windows owner or organization settings
- reboot_launcher-10.0.4+10.0.4-windows-setup.tmp (PID: 5244)
- msiexec.exe (PID: 2200)
Starts a Microsoft application from unusual location
- VC_redist.x64.exe (PID: 8092)
- VC_redist.x64.exe (PID: 4872)
- VC_redist.x64.exe (PID: 7228)
Drops 7-zip archiver for unpacking
- reboot_launcher-10.0.4+10.0.4-windows-setup.tmp (PID: 5244)
Process drops legitimate windows executable
- reboot_launcher-10.0.4+10.0.4-windows-setup.tmp (PID: 5244)
- VC_redist.x64.exe (PID: 8092)
- VC_redist.x64.exe (PID: 4872)
- VC_redist.x64.exe (PID: 7228)
- msiexec.exe (PID: 2200)
- VC_redist.x64.exe (PID: 6700)
Searches for installed software
- VC_redist.x64.exe (PID: 4872)
- dllhost.exe (PID: 7932)
- VC_redist.x64.exe (PID: 2132)
Starts itself from another location
- VC_redist.x64.exe (PID: 4872)
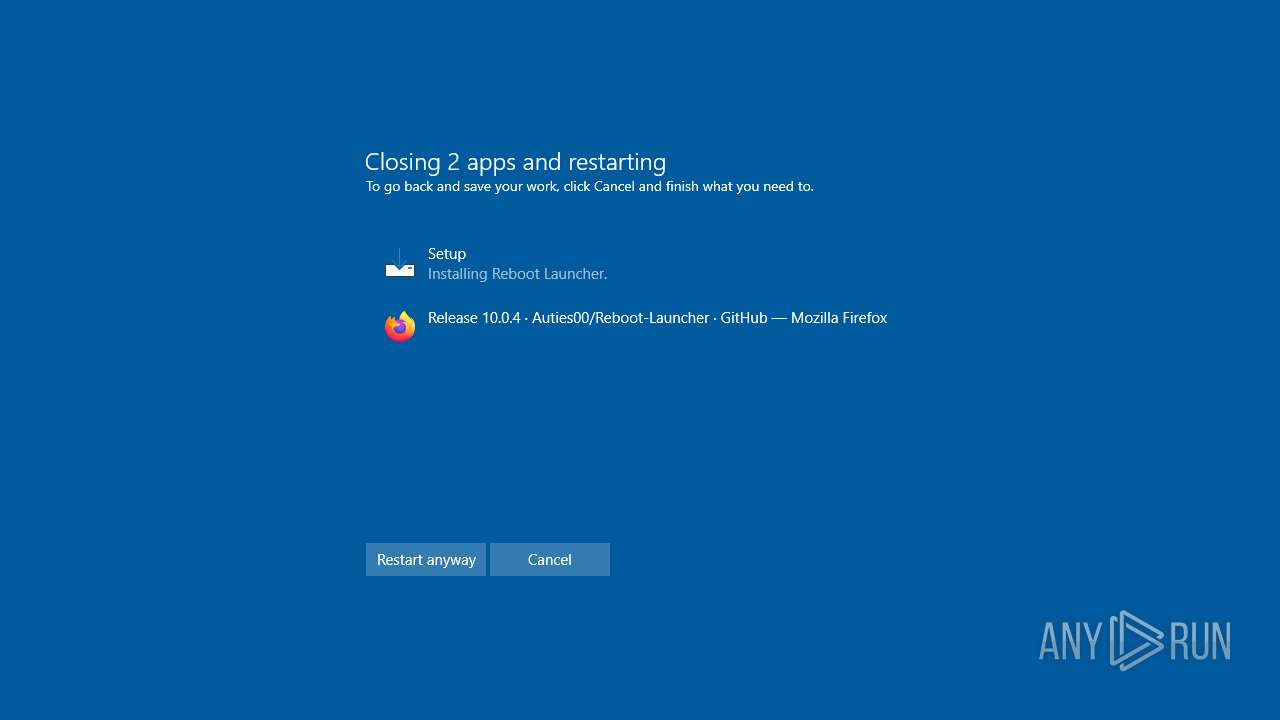
Executes as Windows Service
- VSSVC.exe (PID: 5652)
Checks Windows Trust Settings
- msiexec.exe (PID: 2200)
Creates a software uninstall entry
- VC_redist.x64.exe (PID: 7228)
The process checks if it is being run in the virtual environment
- msiexec.exe (PID: 2200)
The process drops C-runtime libraries
- msiexec.exe (PID: 2200)
Application launched itself
- VC_redist.x64.exe (PID: 6404)
- VC_redist.x64.exe (PID: 2132)
INFO
Application launched itself
- firefox.exe (PID: 5556)
- firefox.exe (PID: 5536)
The process uses the downloaded file
- firefox.exe (PID: 5536)
- VC_redist.x64.exe (PID: 4872)
Create files in a temporary directory
- reboot_launcher-10.0.4+10.0.4-windows-setup.exe (PID: 6012)
- reboot_launcher-10.0.4+10.0.4-windows-setup.exe (PID: 4520)
- reboot_launcher-10.0.4+10.0.4-windows-setup.tmp (PID: 5244)
Executable content was dropped or overwritten
- firefox.exe (PID: 5536)
- msiexec.exe (PID: 2200)
Reads the computer name
- reboot_launcher-10.0.4+10.0.4-windows-setup.tmp (PID: 1296)
- reboot_launcher-10.0.4+10.0.4-windows-setup.tmp (PID: 5244)
- VC_redist.x64.exe (PID: 4872)
- VC_redist.x64.exe (PID: 6700)
- VC_redist.x64.exe (PID: 2132)
- reboot_launcher.exe (PID: 3288)
Process checks computer location settings
- reboot_launcher-10.0.4+10.0.4-windows-setup.tmp (PID: 1296)
- VC_redist.x64.exe (PID: 4872)
- VC_redist.x64.exe (PID: 2132)
Checks supported languages
- reboot_launcher-10.0.4+10.0.4-windows-setup.exe (PID: 4520)
- reboot_launcher-10.0.4+10.0.4-windows-setup.tmp (PID: 5244)
- VC_redist.x64.exe (PID: 8092)
- reboot_launcher-10.0.4+10.0.4-windows-setup.exe (PID: 6012)
- reboot_launcher-10.0.4+10.0.4-windows-setup.tmp (PID: 1296)
- VC_redist.x64.exe (PID: 4872)
- VC_redist.x64.exe (PID: 7228)
- msiexec.exe (PID: 2200)
- VC_redist.x64.exe (PID: 2132)
- VC_redist.x64.exe (PID: 6404)
- reboot_launcher.exe (PID: 3288)
Creates files in the program directory
- reboot_launcher-10.0.4+10.0.4-windows-setup.tmp (PID: 5244)
- VC_redist.x64.exe (PID: 7228)
- reboot_launcher.exe (PID: 3288)
The sample compiled with english language support
- reboot_launcher-10.0.4+10.0.4-windows-setup.tmp (PID: 5244)
- VC_redist.x64.exe (PID: 8092)
- VC_redist.x64.exe (PID: 4872)
- VC_redist.x64.exe (PID: 7228)
- msiexec.exe (PID: 2200)
- VC_redist.x64.exe (PID: 2132)
- VC_redist.x64.exe (PID: 6700)
Manages system restore points
- SrTasks.exe (PID: 8156)
Reads the machine GUID from the registry
- VC_redist.x64.exe (PID: 7228)
- msiexec.exe (PID: 2200)
Reads the software policy settings
- msiexec.exe (PID: 2200)
Creates a software uninstall entry
- msiexec.exe (PID: 2200)
Sends debugging messages
- msiexec.exe (PID: 2200)
- reboot_launcher.exe (PID: 3288)
Reads Environment values
- reboot_launcher.exe (PID: 3288)
Reads product name
- reboot_launcher.exe (PID: 3288)
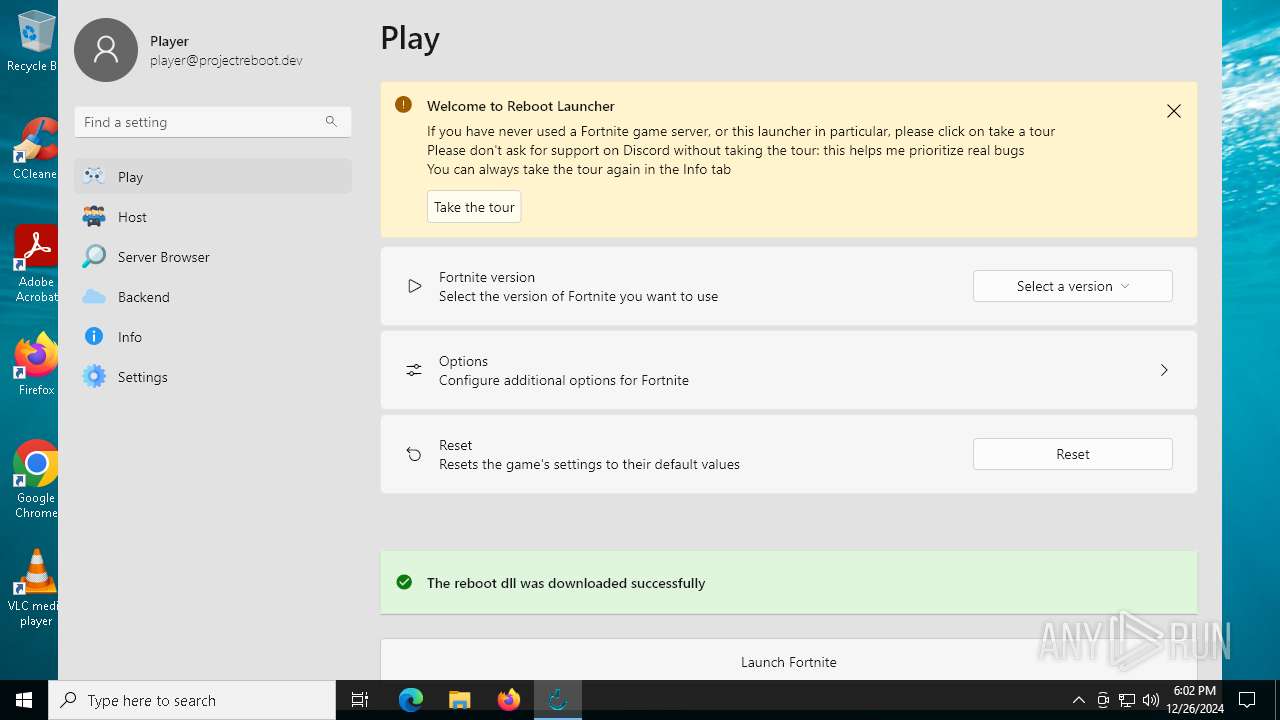
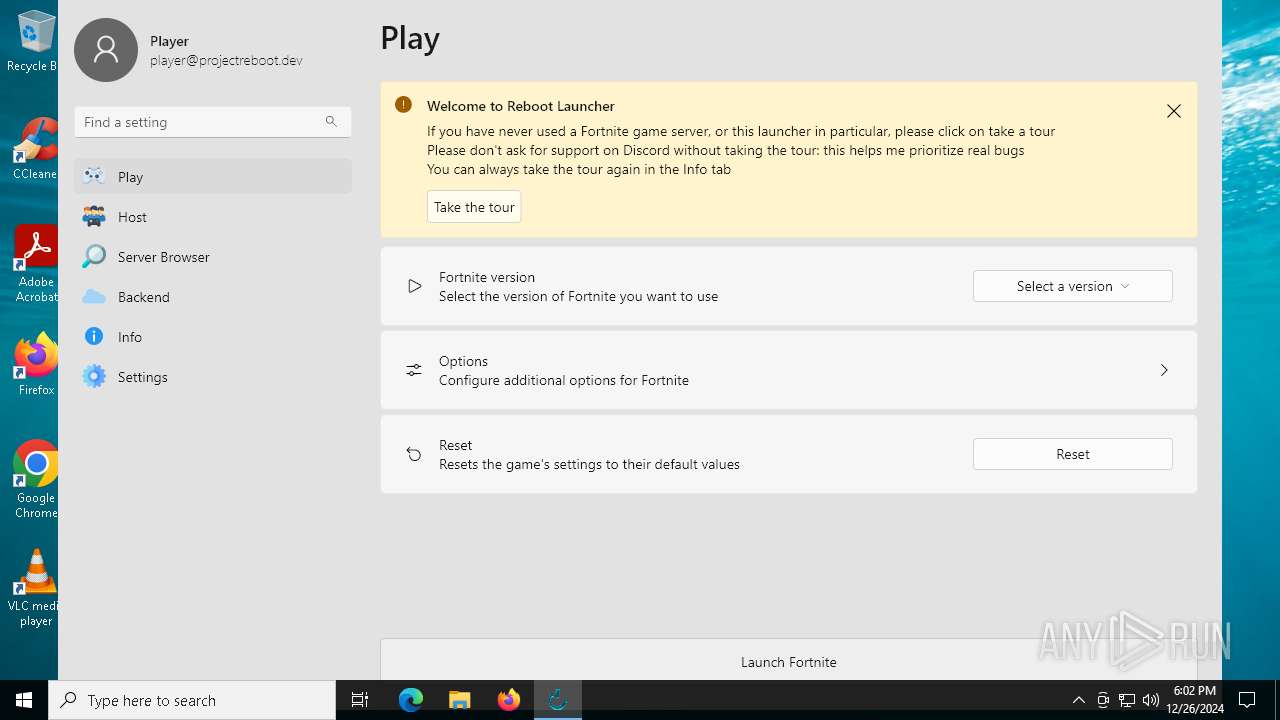
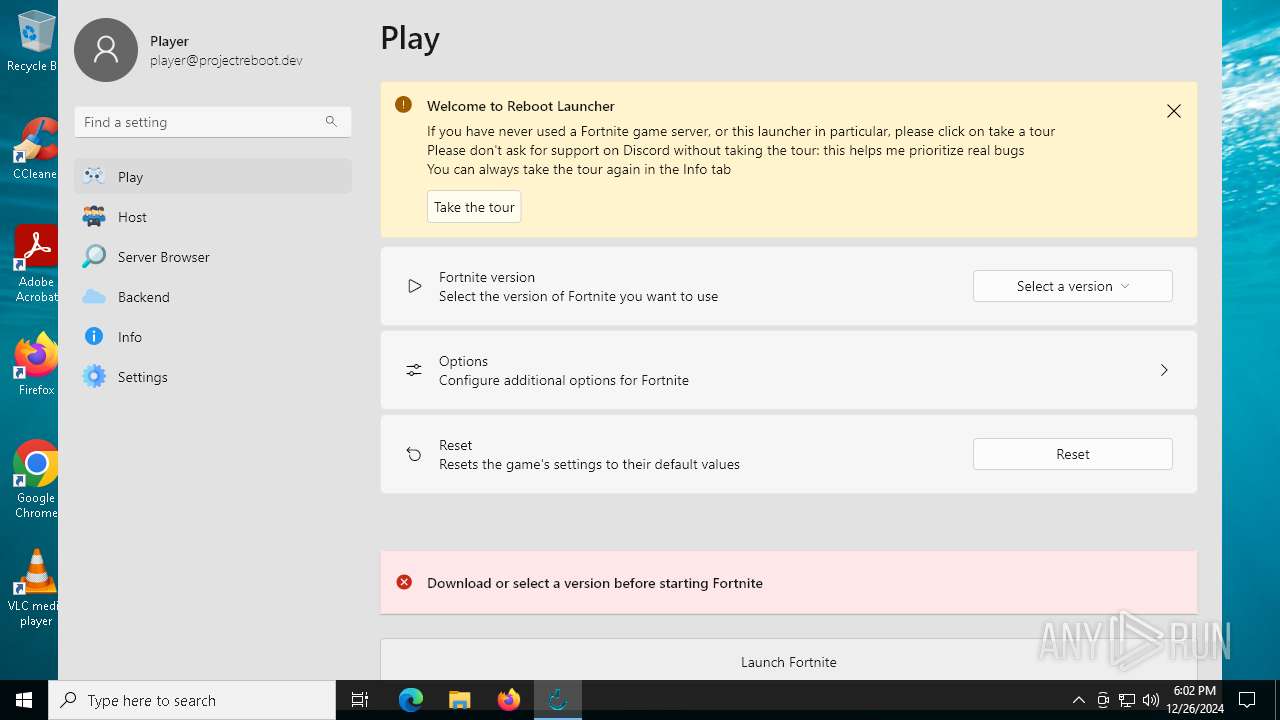
Manual execution by a user
- reboot_launcher.exe (PID: 3288)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
167
Monitored processes
30
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | helper 105 0x464 | C:\Users\admin\AppData\Local\Temp\is-6R6RR.tmp\_isetup\_setup64.tmp | — | reboot_launcher-10.0.4+10.0.4-windows-setup.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 776 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1296 | "C:\Users\admin\AppData\Local\Temp\is-R5KDF.tmp\reboot_launcher-10.0.4+10.0.4-windows-setup.tmp" /SL5="$5030A,74434244,832512,C:\Users\admin\Downloads\reboot_launcher-10.0.4+10.0.4-windows-setup.exe" | C:\Users\admin\AppData\Local\Temp\is-R5KDF.tmp\reboot_launcher-10.0.4+10.0.4-windows-setup.tmp | — | reboot_launcher-10.0.4+10.0.4-windows-setup.exe | |||||||||||
User: admin Company: Auties00 Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 1073807364 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2132 | "C:\ProgramData\Package Cache\{8bdfe669-9705-4184-9368-db9ce581e0e7}\VC_redist.x64.exe" -burn.clean.room="C:\ProgramData\Package Cache\{8bdfe669-9705-4184-9368-db9ce581e0e7}\VC_redist.x64.exe" -burn.filehandle.attached=644 -burn.filehandle.self=664 -uninstall -quiet -burn.related.upgrade -burn.ancestors={5af95fd8-a22e-458f-acee-c61bd787178e} -burn.filehandle.self=1344 -burn.embedded BurnPipe.{4C988497-5B65-4A0B-A1E5-97C050B45744} {B8C0AC37-DA2A-4CE1-8706-56A6EC6C5438} 7228 | C:\ProgramData\Package Cache\{8bdfe669-9705-4184-9368-db9ce581e0e7}\VC_redist.x64.exe | VC_redist.x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x64) - 14.36.32532 Exit code: 0 Version: 14.36.32532.0 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
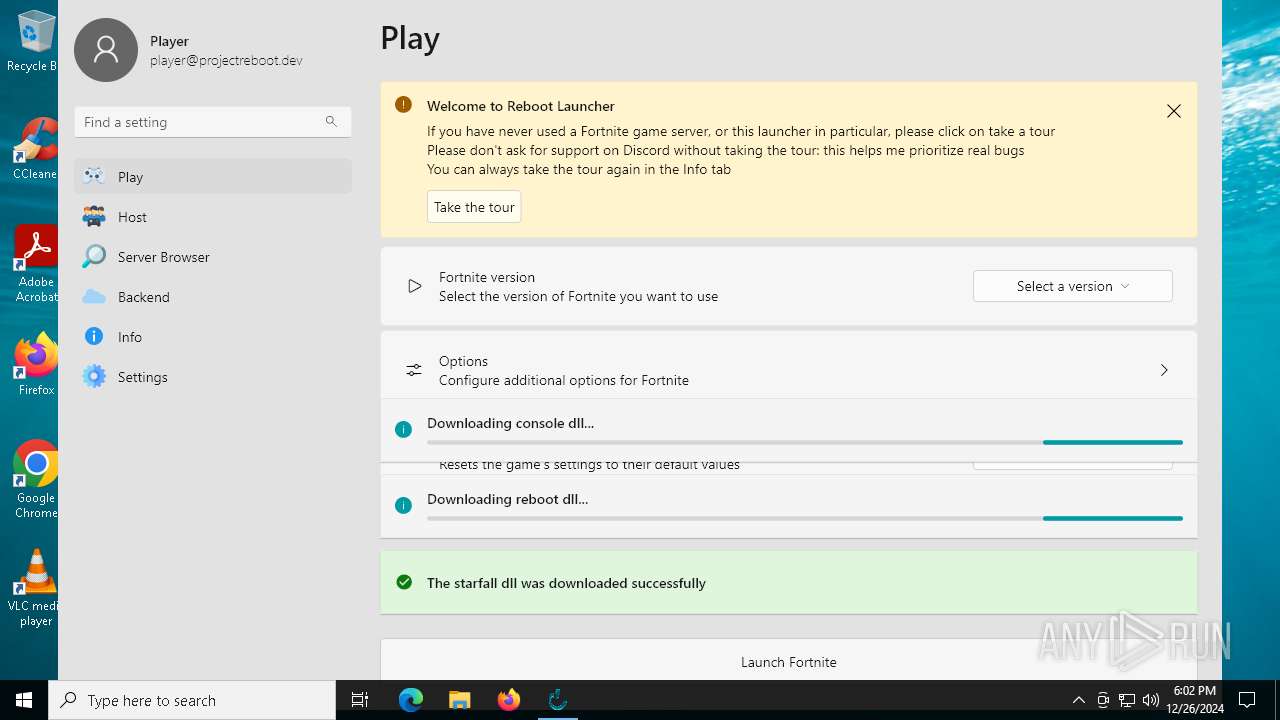
| 3288 | "C:\Program Files\Reboot Launcher\reboot_launcher.exe" | C:\Program Files\Reboot Launcher\reboot_launcher.exe | explorer.exe | ||||||||||||
User: admin Company: com.example Integrity Level: MEDIUM Description: reboot_launcher Version: 10.0.4 Modules
| |||||||||||||||
| 4520 | "C:\Users\admin\Downloads\reboot_launcher-10.0.4+10.0.4-windows-setup.exe" /SPAWNWND=$502EC /NOTIFYWND=$5030A | C:\Users\admin\Downloads\reboot_launcher-10.0.4+10.0.4-windows-setup.exe | reboot_launcher-10.0.4+10.0.4-windows-setup.tmp | ||||||||||||
User: admin Company: Auties00 Integrity Level: HIGH Description: Reboot Launcher Setup Exit code: 1073807364 Version: Modules
| |||||||||||||||
| 4872 | "C:\WINDOWS\Temp\{A18C5A54-BB49-41AE-BFC2-AE1069F63B36}\.cr\VC_redist.x64.exe" -burn.clean.room="C:\Users\admin\AppData\Local\Temp\is-6R6RR.tmp\VC_redist.x64.exe" -burn.filehandle.attached=784 -burn.filehandle.self=780 /quiet | C:\Windows\Temp\{A18C5A54-BB49-41AE-BFC2-AE1069F63B36}\.cr\VC_redist.x64.exe | VC_redist.x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x64) - 14.40.33810 Exit code: 3010 Version: 14.40.33810.0 Modules
| |||||||||||||||
| 5244 | "C:\Users\admin\AppData\Local\Temp\is-5F8KL.tmp\reboot_launcher-10.0.4+10.0.4-windows-setup.tmp" /SL5="$70306,74434244,832512,C:\Users\admin\Downloads\reboot_launcher-10.0.4+10.0.4-windows-setup.exe" /SPAWNWND=$502EC /NOTIFYWND=$5030A | C:\Users\admin\AppData\Local\Temp\is-5F8KL.tmp\reboot_launcher-10.0.4+10.0.4-windows-setup.tmp | reboot_launcher-10.0.4+10.0.4-windows-setup.exe | ||||||||||||
User: admin Company: Auties00 Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
30 220
Read events
29 206
Write events
646
Delete events
368
Modification events
| (PID) Process: | (5536) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (5536) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (5244) reboot_launcher-10.0.4+10.0.4-windows-setup.tmp | Key: | HKEY_CURRENT_USER\Environment |
| Operation: | write | Name: | OPENSSL_ia32cap |
Value: ~0x20000000 | |||
| (PID) Process: | (5244) reboot_launcher-10.0.4+10.0.4-windows-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\31868Auties00.RebootLauncher_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.2.2 | |||
| (PID) Process: | (5244) reboot_launcher-10.0.4+10.0.4-windows-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\31868Auties00.RebootLauncher_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\Reboot Launcher | |||
| (PID) Process: | (5244) reboot_launcher-10.0.4+10.0.4-windows-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\31868Auties00.RebootLauncher_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Reboot Launcher\ | |||
| (PID) Process: | (5244) reboot_launcher-10.0.4+10.0.4-windows-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\31868Auties00.RebootLauncher_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: (Default) | |||
| (PID) Process: | (5244) reboot_launcher-10.0.4+10.0.4-windows-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\31868Auties00.RebootLauncher_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (5244) reboot_launcher-10.0.4+10.0.4-windows-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\31868Auties00.RebootLauncher_is1 |
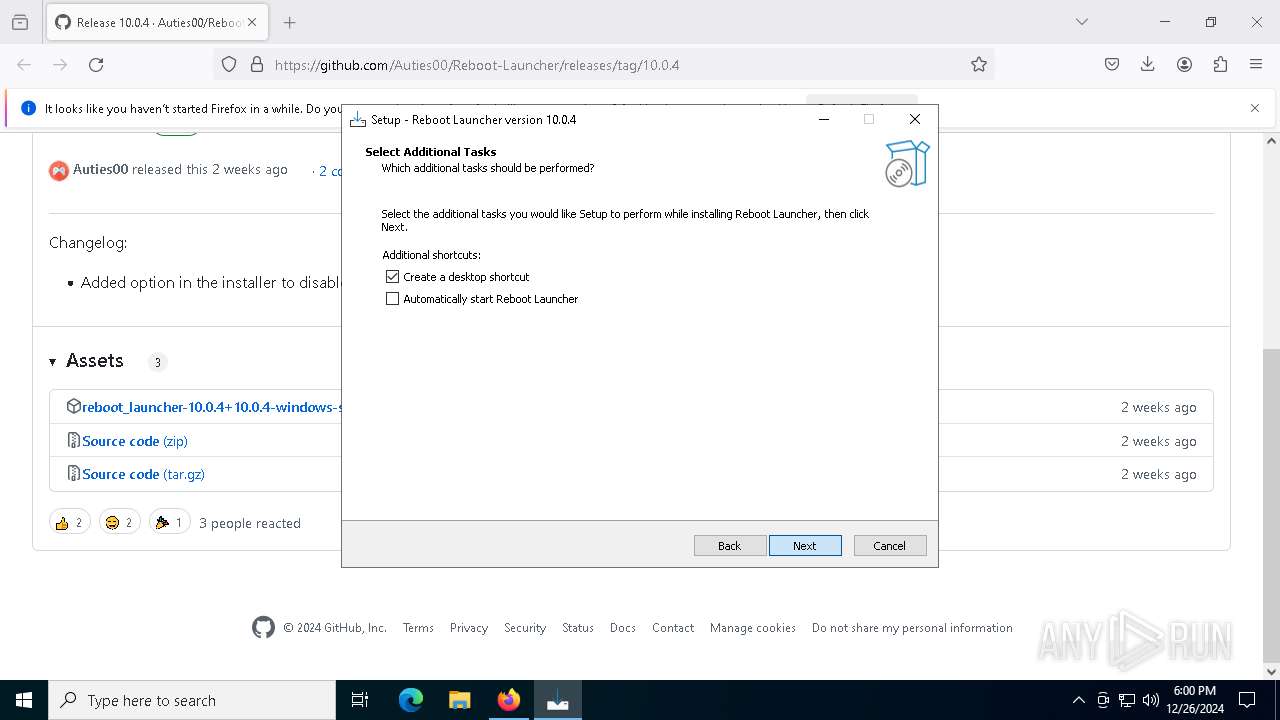
| Operation: | write | Name: | Inno Setup: Selected Tasks |
Value: desktopicon | |||
| (PID) Process: | (5244) reboot_launcher-10.0.4+10.0.4-windows-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\31868Auties00.RebootLauncher_is1 |
| Operation: | write | Name: | Inno Setup: Deselected Tasks |
Value: launchatstartup | |||
Executable files
112
Suspicious files
1 482
Text files
146
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5536 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 5536 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 5536 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
| 5536 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5536 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5536 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 5536 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 5536 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5536 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:26E9DAA5D9AF30BB63BA146BEFF57875 | SHA256:2634CD033FA088FFB2389A98EAC1C6606A6C928236B14806CF3AF83146C80F95 | |||
| 5536 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
118
DNS requests
132
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5536 | firefox.exe | POST | 200 | 2.16.202.121:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
5536 | firefox.exe | POST | 200 | 2.16.202.121:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
640 | svchost.exe | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5536 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
640 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5536 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
5536 | firefox.exe | POST | 200 | 2.16.241.15:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
5536 | firefox.exe | POST | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/ | unknown | — | — | whitelisted |
5536 | firefox.exe | POST | 200 | 142.250.186.99:80 | http://o.pki.goog/s/wr3/jLM | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
640 | svchost.exe | 2.16.164.72:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
640 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.23.209.148:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
5536 | firefox.exe | 140.82.121.3:443 | github.com | GITHUB | US | shared |
5536 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
5536 | firefox.exe | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
github.com |
| shared |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
content-signature-2.cdn.mozilla.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Misc activity | ET INFO Supabase Development Platform Related Domain in DNS Lookup |
2192 | svchost.exe | Misc activity | ET INFO Supabase Development Platform Related Domain in DNS Lookup |
3288 | reboot_launcher.exe | Misc activity | ET INFO Observed Online Application Hosting Domain (supabase .co in TLS SNI) |
3288 | reboot_launcher.exe | Misc activity | ET INFO Observed Online Application Hosting Domain (supabase .co in TLS SNI) |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
3288 | reboot_launcher.exe | Misc activity | ET INFO Observed Online Application Hosting Domain (supabase .co in TLS SNI) |
Process | Message |
|---|---|
msiexec.exe | Failed to release Service
|
reboot_launcher.exe | ****** SYSTEM_THEME_PLUGIN ******: Message Handle Registered |