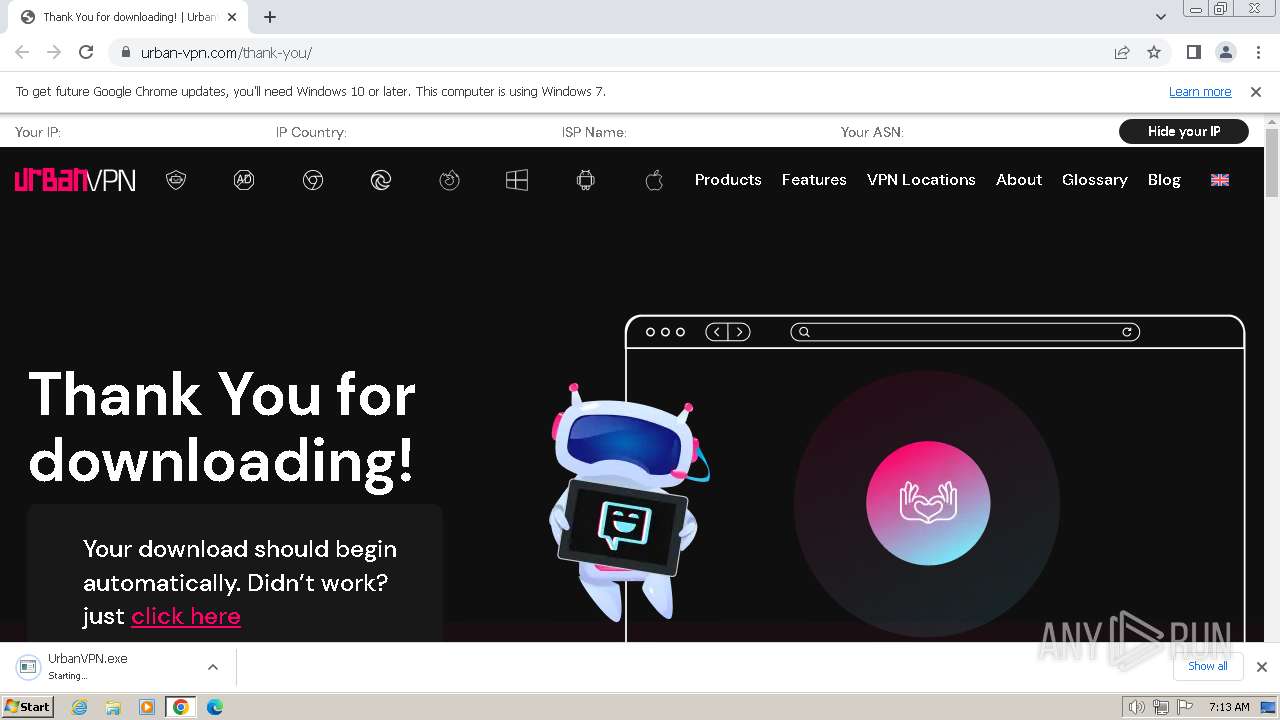
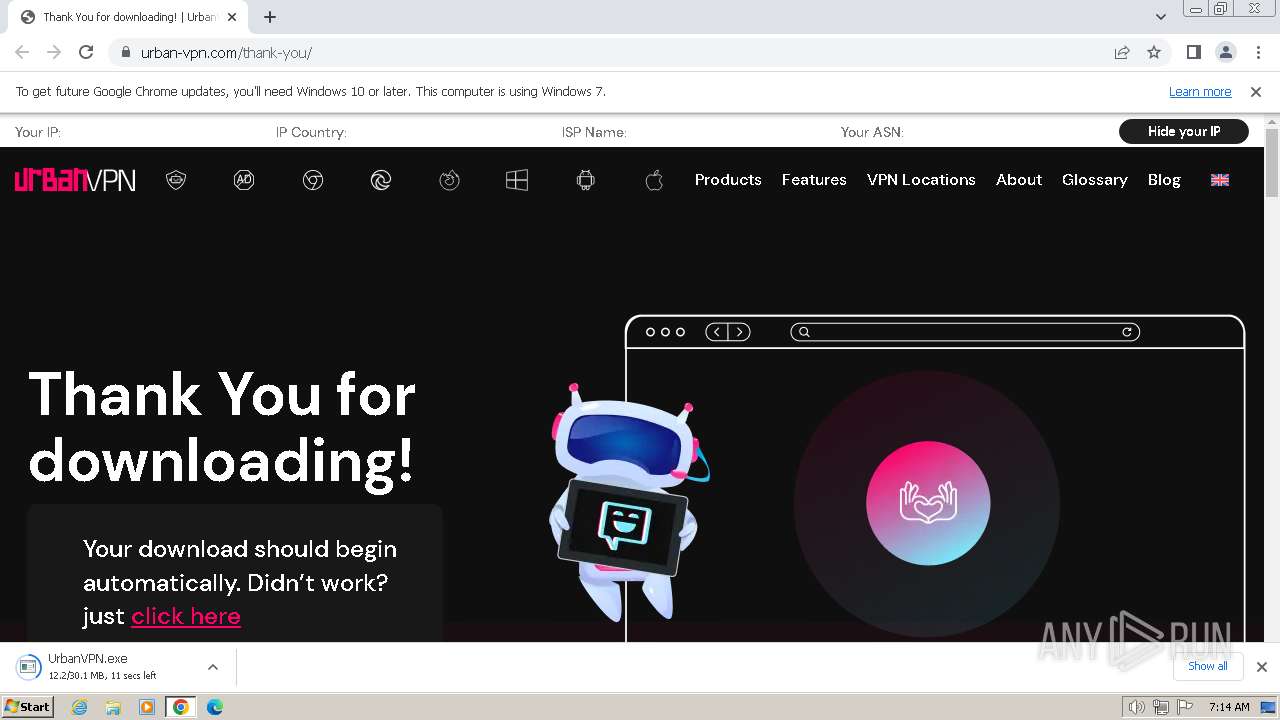
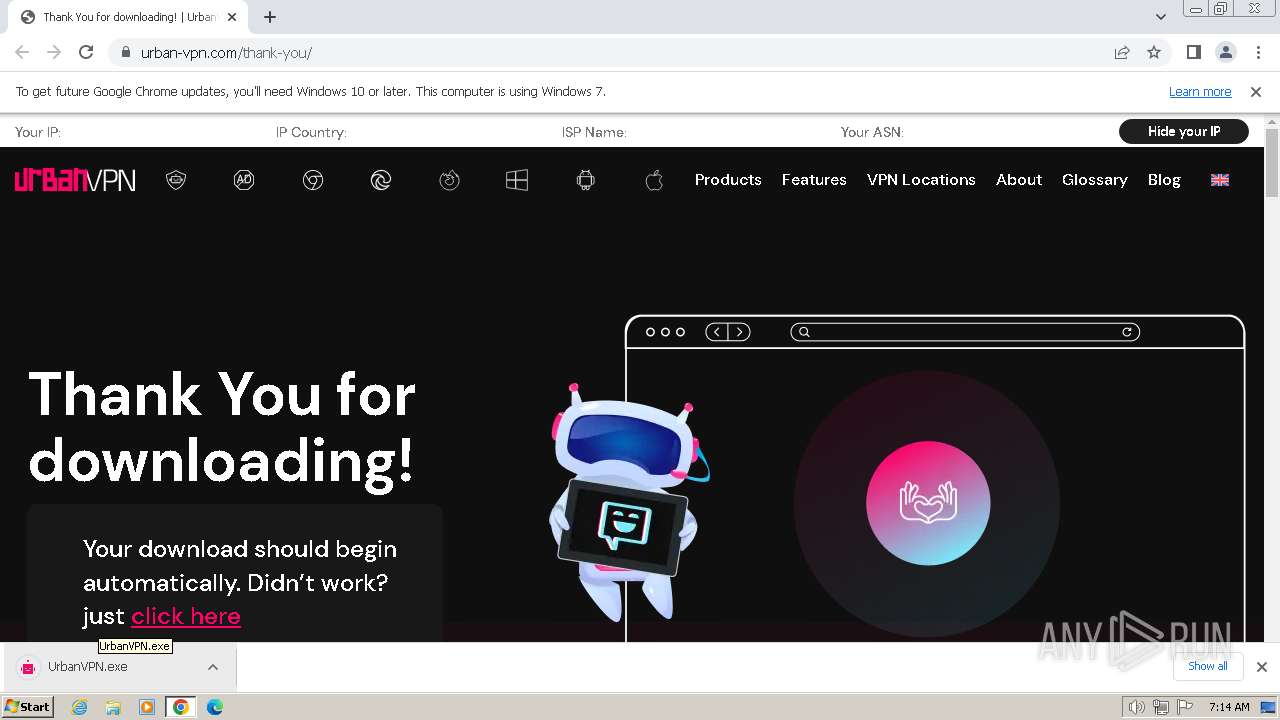
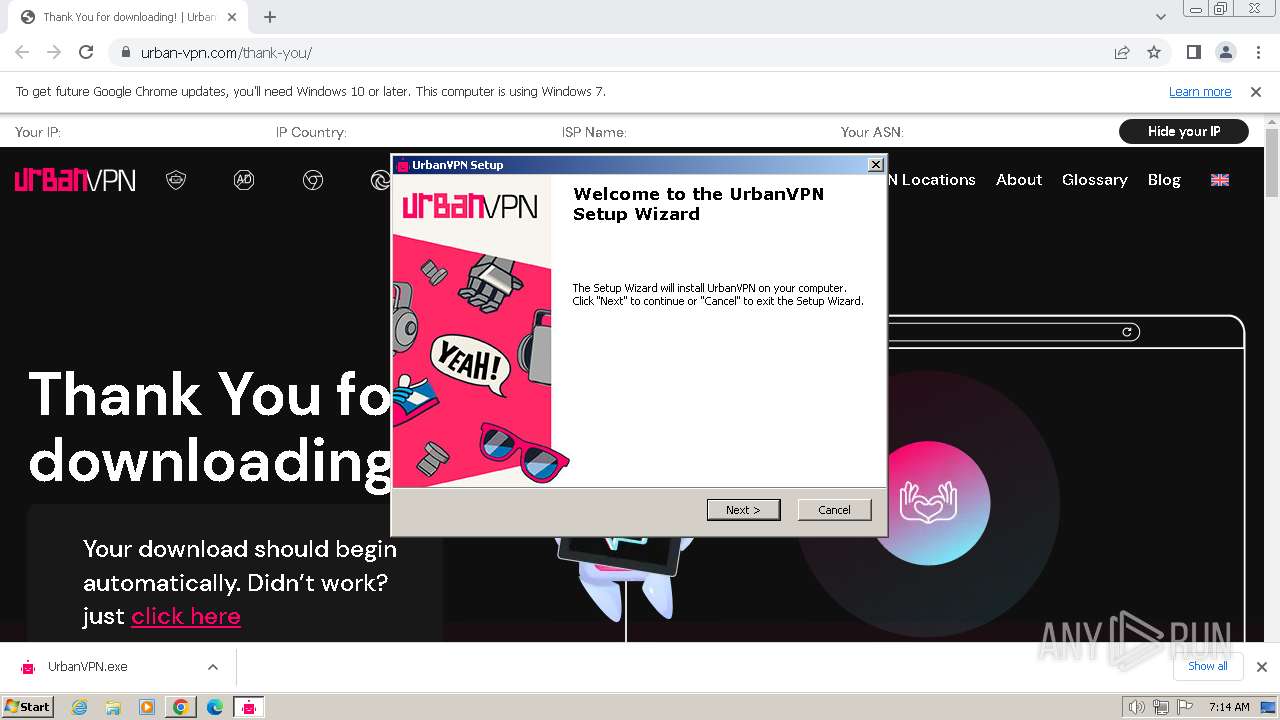
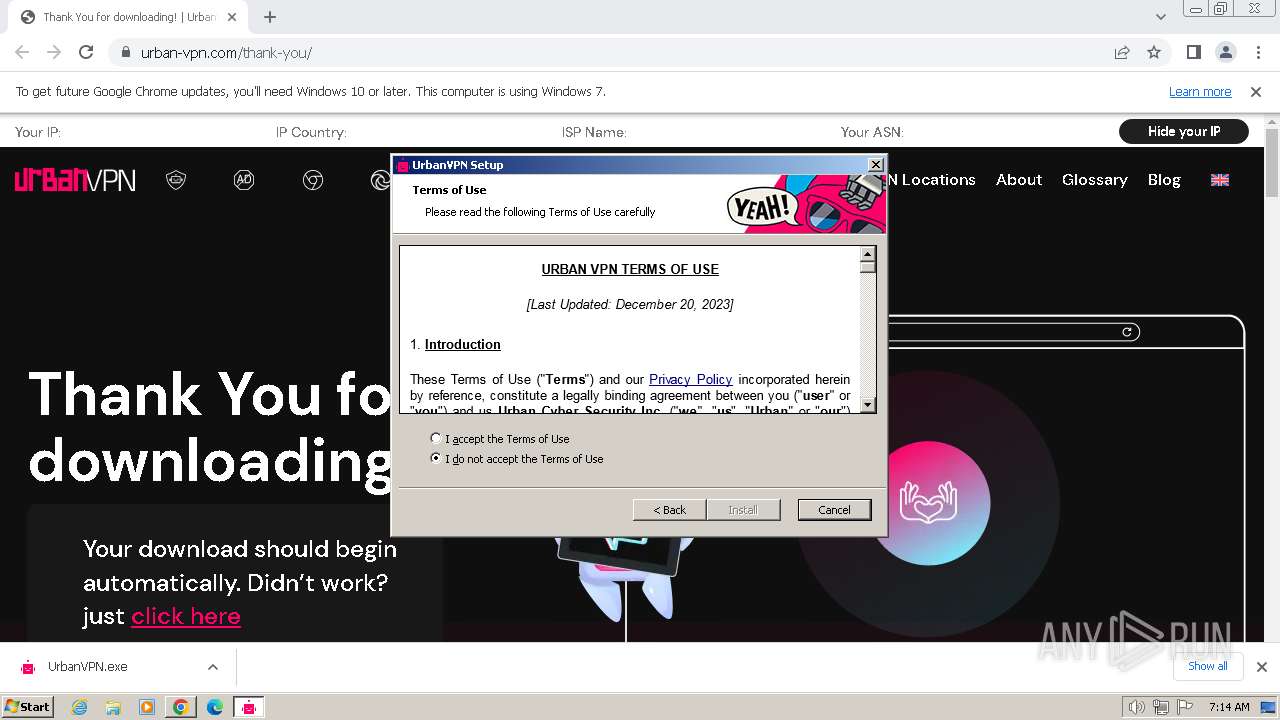
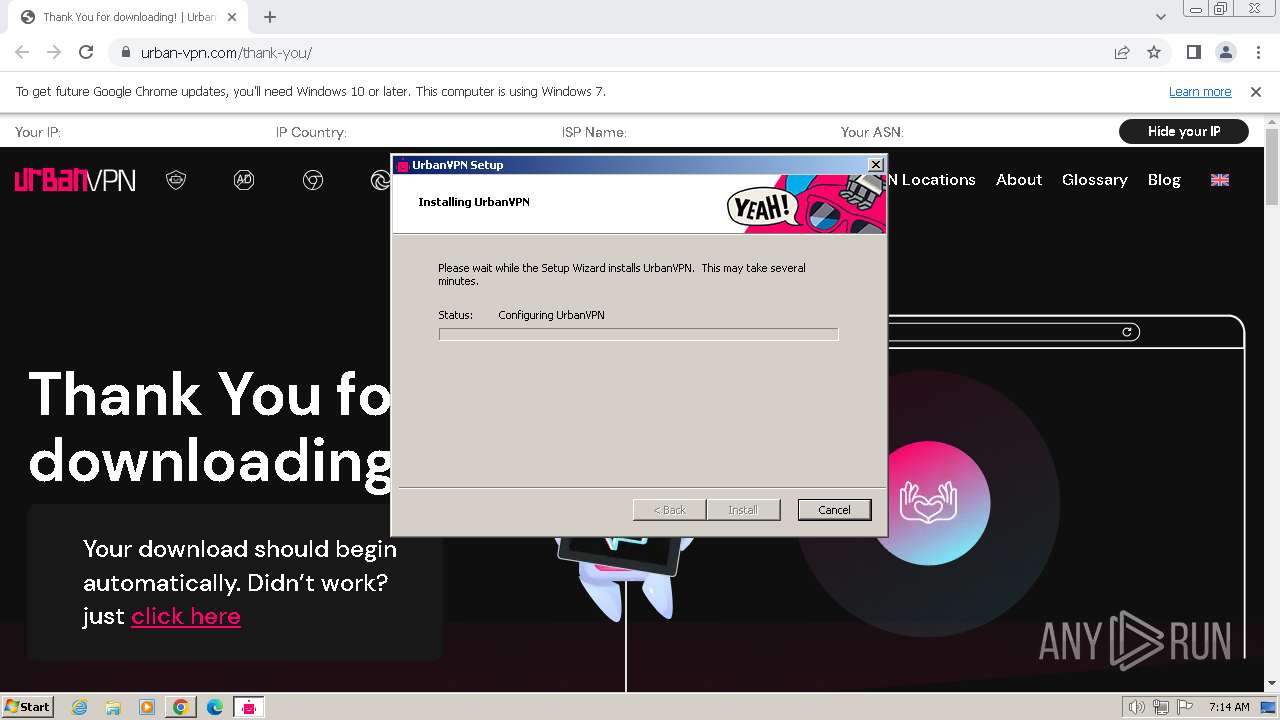
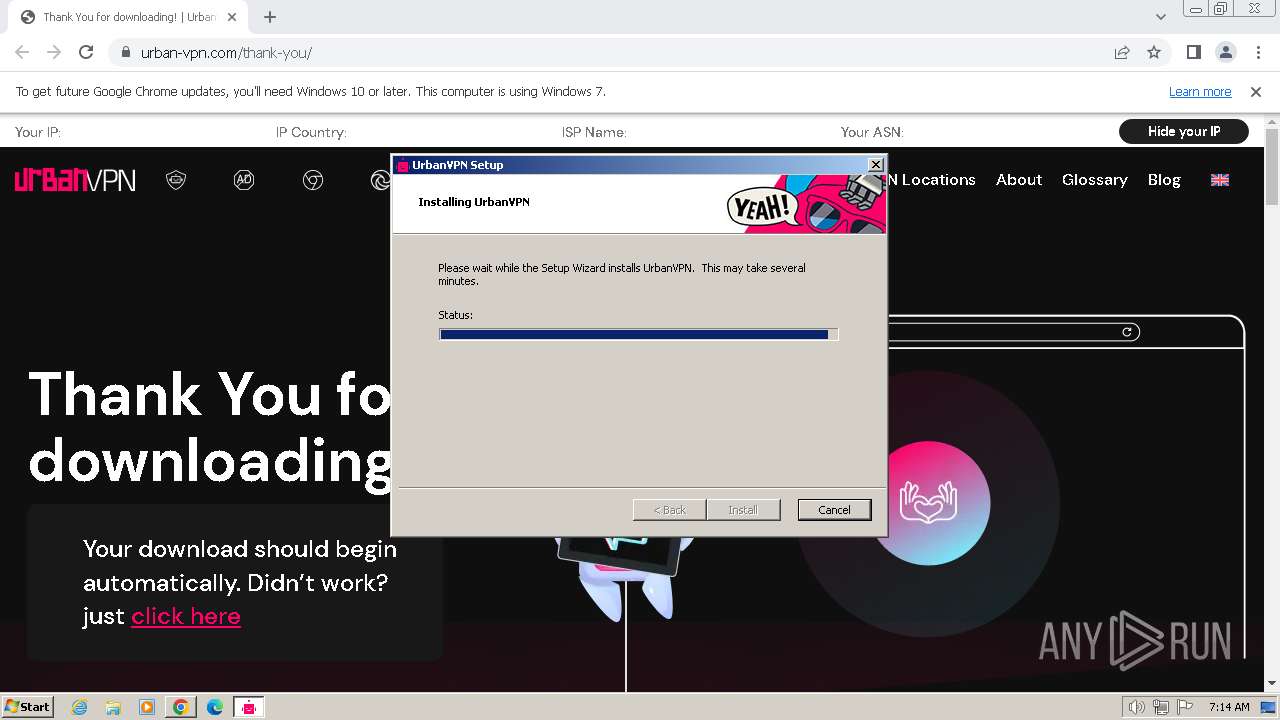
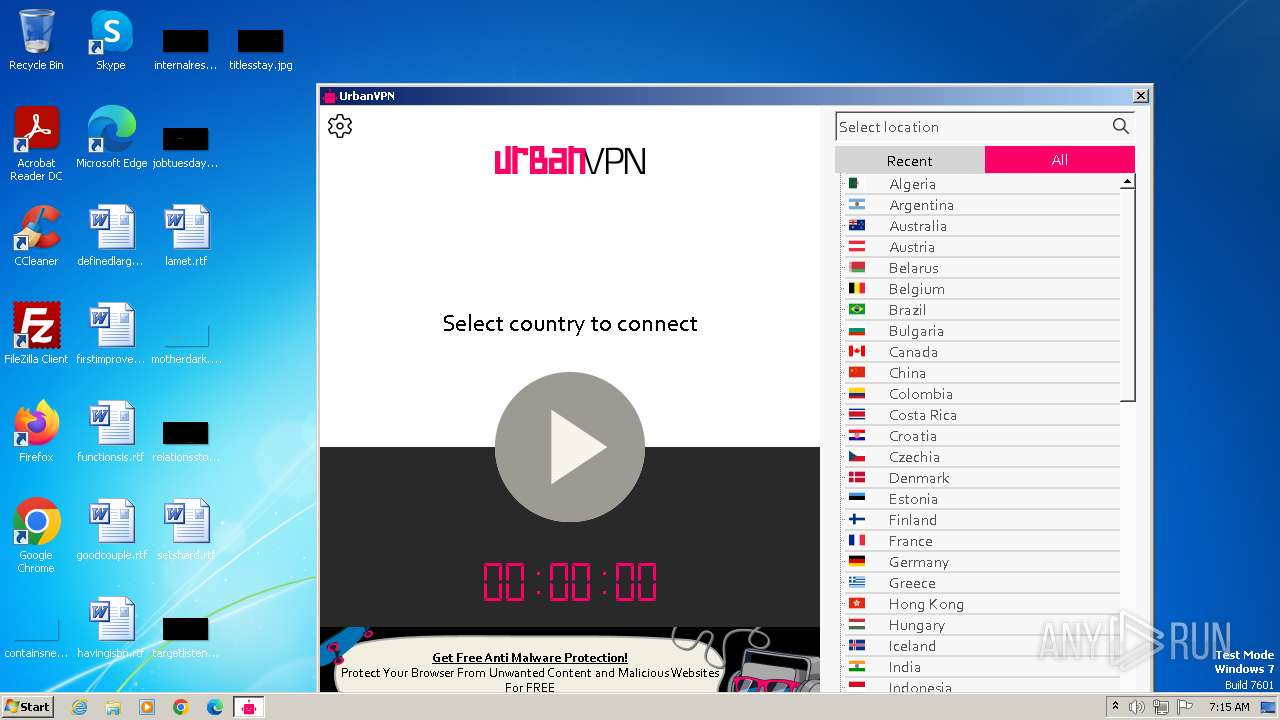
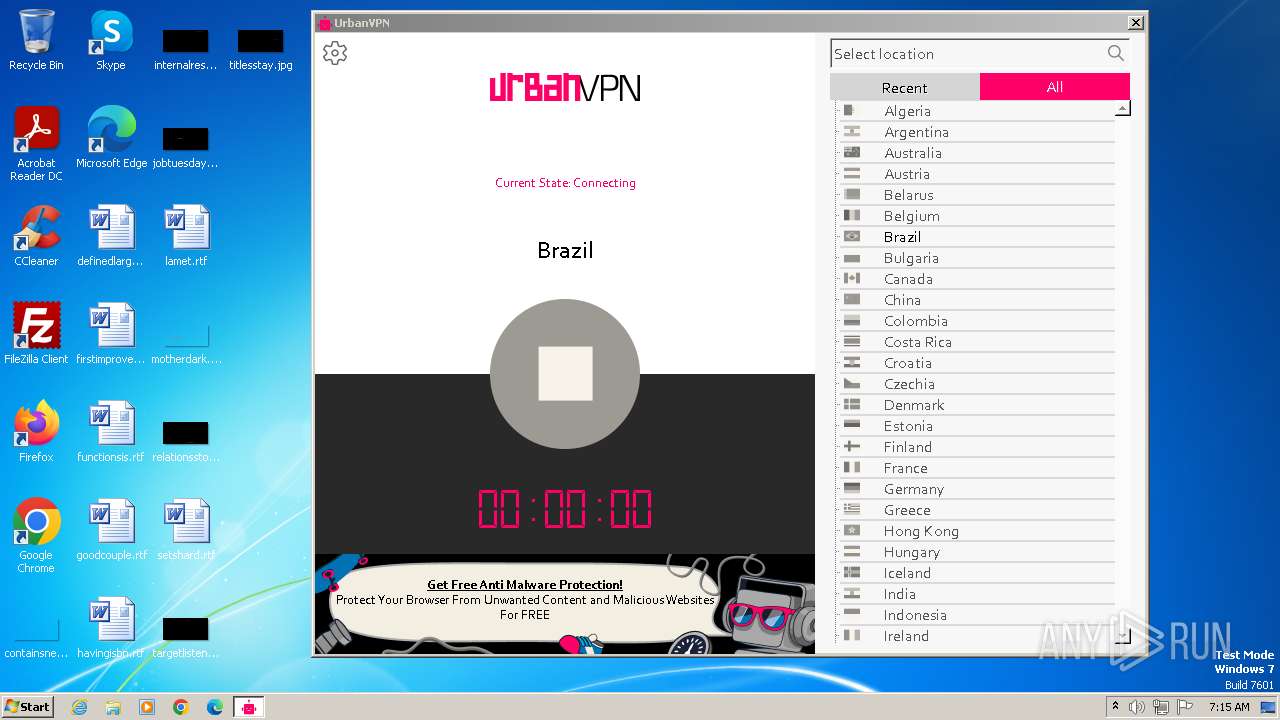
| URL: | https://www.urban-vpn.com/thank-you/ |
| Full analysis: | https://app.any.run/tasks/9842ea3b-29ac-4154-beb5-49d8edfe7a9b |
| Verdict: | Malicious activity |
| Analysis date: | January 09, 2024, 07:13:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E61314DA51165150D1CDDB97ADBC546B |
| SHA1: | F0232E1B9CD69796B0CE44073E985CFB7A6394F1 |
| SHA256: | 58EC7210ACF7D407255EE0CBCFF87782A3517B6D3252985BE2F75F7BB2D62FB9 |
| SSDEEP: | 3:N8DSLEUKNiOcn:2OLEW |
MALICIOUS
The DLL Hijacking
- msiexec.exe (PID: 2832)
Creates a writable file in the system directory
- drvinst.exe (PID: 996)
- drvinst.exe (PID: 3432)
SUSPICIOUS
Reads security settings of Internet Explorer
- UrbanVPN.exe (PID: 1220)
- UrbanVPN.exe (PID: 3128)
- tapinstall.exe (PID: 316)
- UrbanVPNUpdater.exe (PID: 3000)
Reads settings of System Certificates
- UrbanVPN.exe (PID: 1220)
- UrbanVPN.exe (PID: 3128)
- tapinstall.exe (PID: 316)
- rundll32.exe (PID: 1232)
- UrbanVPNUpdater.exe (PID: 3000)
- urbanvpn-gui.exe (PID: 3032)
Checks Windows Trust Settings
- UrbanVPN.exe (PID: 1220)
- UrbanVPN.exe (PID: 3128)
- msiexec.exe (PID: 2860)
- tapinstall.exe (PID: 316)
- drvinst.exe (PID: 996)
- drvinst.exe (PID: 3432)
- UrbanVPNUpdater.exe (PID: 3000)
Reads the Windows owner or organization settings
- UrbanVPN.exe (PID: 1220)
- UrbanVPN.exe (PID: 3128)
Checks for Java to be installed
- msiexec.exe (PID: 2832)
Reads the Internet Settings
- UrbanVPN.exe (PID: 1220)
- MSI280.tmp (PID: 1932)
- UrbanVPNUpdater.exe (PID: 3000)
- urbanvpn-gui.exe (PID: 3032)
Reads Microsoft Outlook installation path
- UrbanVPN.exe (PID: 1220)
Reads Internet Explorer settings
- UrbanVPN.exe (PID: 1220)
The process creates files with name similar to system file names
- MSID215.tmp (PID: 4028)
- msiexec.exe (PID: 2860)
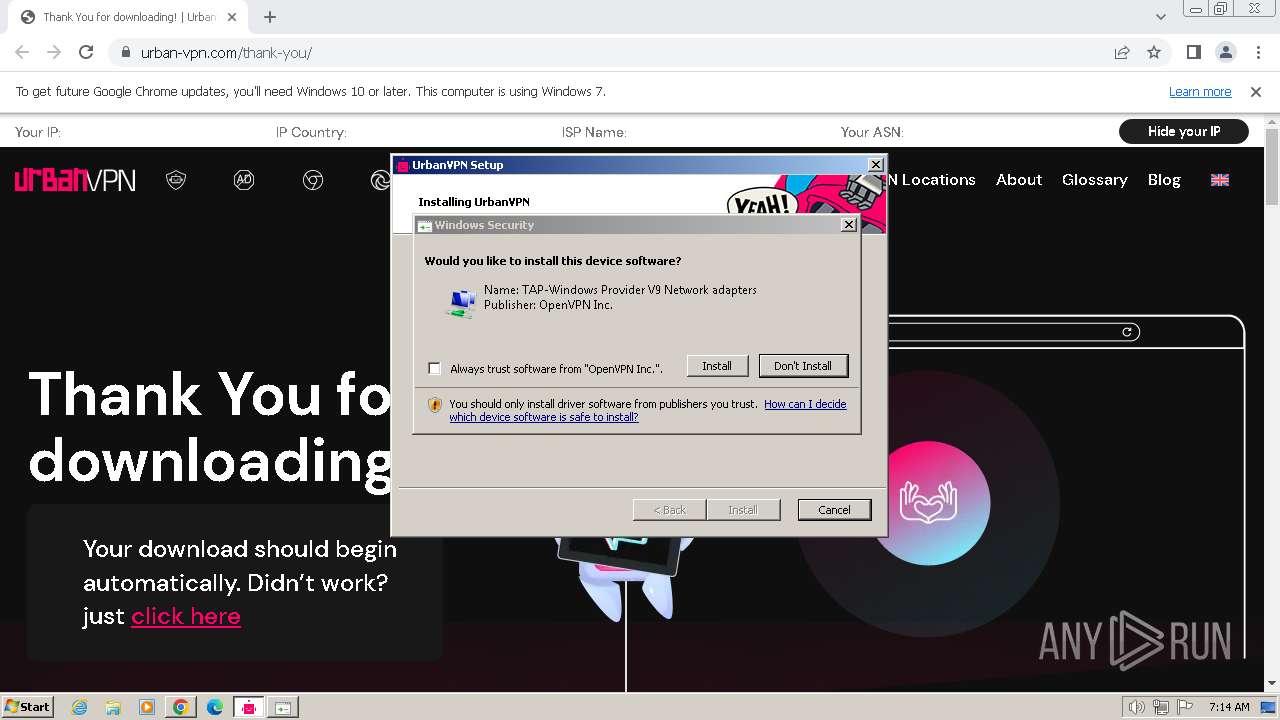
Drops a system driver (possible attempt to evade defenses)
- MSID215.tmp (PID: 4028)
- tapinstall.exe (PID: 316)
- drvinst.exe (PID: 996)
- drvinst.exe (PID: 3432)
Starts application with an unusual extension
- MSID215.tmp (PID: 4028)
Creates files in the driver directory
- drvinst.exe (PID: 996)
- drvinst.exe (PID: 3432)
INFO
Drops the executable file immediately after the start
- chrome.exe (PID: 2036)
- UrbanVPN.exe (PID: 1220)
- msiexec.exe (PID: 2860)
- MSID215.tmp (PID: 4028)
- tapinstall.exe (PID: 316)
- drvinst.exe (PID: 996)
- drvinst.exe (PID: 3432)
Checks supported languages
- UrbanVPN.exe (PID: 1220)
- msiexec.exe (PID: 2860)
- msiexec.exe (PID: 2832)
- UrbanVPN.exe (PID: 3128)
- msiexec.exe (PID: 3652)
- MSID215.tmp (PID: 4028)
- nsD32D.tmp (PID: 1072)
- tapinstall.exe (PID: 1936)
- nsD418.tmp (PID: 632)
- tapinstall.exe (PID: 316)
- drvinst.exe (PID: 996)
- drvinst.exe (PID: 3432)
- MSI280.tmp (PID: 1932)
- msiexec.exe (PID: 2816)
- urbanvpn-gui.exe (PID: 3032)
- UrbanVPNUpdater.exe (PID: 3508)
- urbanvpnserv.exe (PID: 1232)
- UrbanVPNUpdater.exe (PID: 3000)
- urbanvpn.exe (PID: 1196)
- urbanvpn.exe (PID: 3132)
- wmpnscfg.exe (PID: 1388)
- wmpnscfg.exe (PID: 1880)
- wmpnscfg.exe (PID: 2560)
- wmpnscfg.exe (PID: 2736)
- urbanvpn.exe (PID: 2436)
- wmpnscfg.exe (PID: 2580)
- wmpnscfg.exe (PID: 3148)
- wmpnscfg.exe (PID: 3840)
- wmpnscfg.exe (PID: 3208)
- urbanvpn.exe (PID: 568)
- wmpnscfg.exe (PID: 3408)
- wmpnscfg.exe (PID: 3344)
Reads the computer name
- UrbanVPN.exe (PID: 1220)
- msiexec.exe (PID: 2860)
- msiexec.exe (PID: 2832)
- UrbanVPN.exe (PID: 3128)
- msiexec.exe (PID: 3652)
- MSID215.tmp (PID: 4028)
- tapinstall.exe (PID: 1936)
- tapinstall.exe (PID: 316)
- drvinst.exe (PID: 996)
- drvinst.exe (PID: 3432)
- MSI280.tmp (PID: 1932)
- UrbanVPNUpdater.exe (PID: 3000)
- msiexec.exe (PID: 2816)
- UrbanVPNUpdater.exe (PID: 3508)
- urbanvpnserv.exe (PID: 1232)
- urbanvpn.exe (PID: 3132)
- urbanvpn-gui.exe (PID: 3032)
- wmpnscfg.exe (PID: 2580)
- wmpnscfg.exe (PID: 1880)
- wmpnscfg.exe (PID: 2736)
- wmpnscfg.exe (PID: 2560)
- wmpnscfg.exe (PID: 1388)
- urbanvpn.exe (PID: 2436)
- wmpnscfg.exe (PID: 3208)
- urbanvpn.exe (PID: 568)
- wmpnscfg.exe (PID: 3840)
- wmpnscfg.exe (PID: 3408)
- wmpnscfg.exe (PID: 3344)
- wmpnscfg.exe (PID: 3148)
The process uses the downloaded file
- chrome.exe (PID: 2052)
- chrome.exe (PID: 2036)
- UrbanVPN.exe (PID: 1220)
Reads the machine GUID from the registry
- UrbanVPN.exe (PID: 1220)
- msiexec.exe (PID: 2860)
- msiexec.exe (PID: 2832)
- msiexec.exe (PID: 3652)
- UrbanVPN.exe (PID: 3128)
- tapinstall.exe (PID: 316)
- drvinst.exe (PID: 996)
- drvinst.exe (PID: 3432)
- MSI280.tmp (PID: 1932)
- msiexec.exe (PID: 2816)
- urbanvpnserv.exe (PID: 1232)
- urbanvpn-gui.exe (PID: 3032)
- UrbanVPNUpdater.exe (PID: 3000)
- urbanvpn.exe (PID: 2436)
- urbanvpn.exe (PID: 3132)
- urbanvpn.exe (PID: 568)
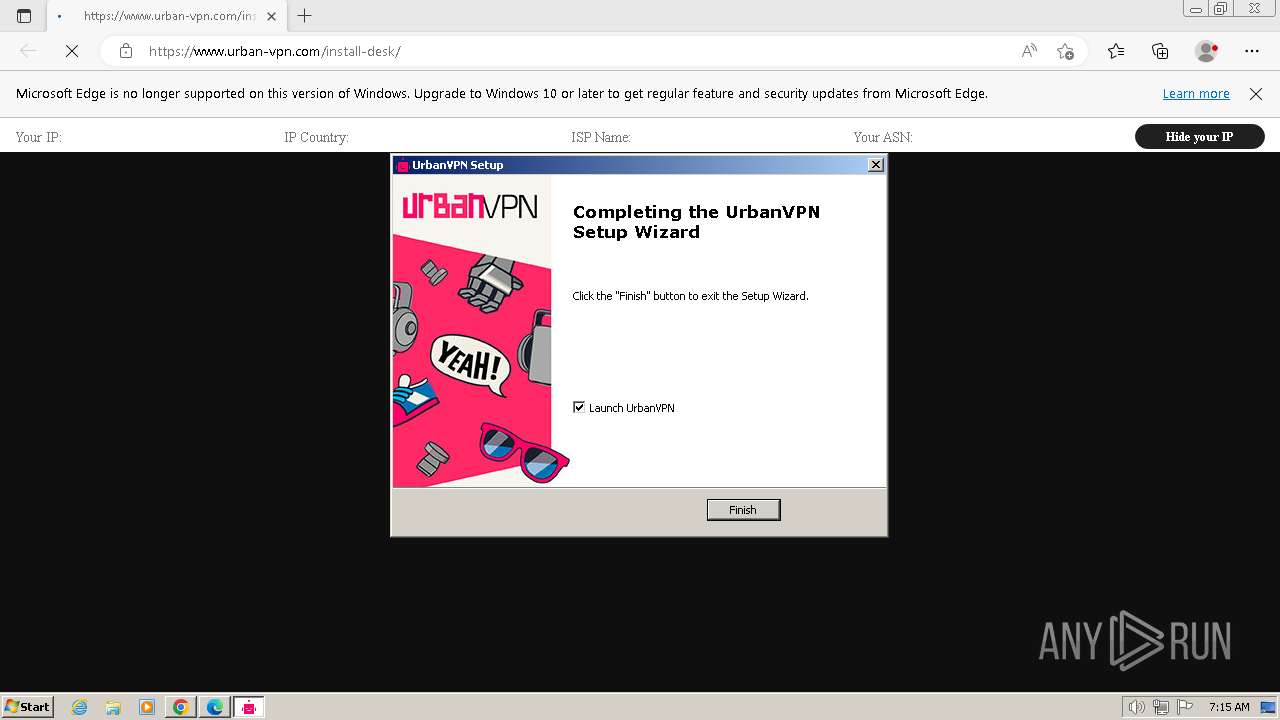
Application launched itself
- chrome.exe (PID: 2036)
- UrbanVPN.exe (PID: 1220)
- msiexec.exe (PID: 2860)
- msedge.exe (PID: 3024)
- msedge.exe (PID: 3036)
- msedge.exe (PID: 3024)
Creates files or folders in the user directory
- UrbanVPN.exe (PID: 1220)
- urbanvpn-gui.exe (PID: 3032)
- UrbanVPNUpdater.exe (PID: 3000)
Create files in a temporary directory
- UrbanVPN.exe (PID: 1220)
- msiexec.exe (PID: 2832)
- msiexec.exe (PID: 3652)
- msiexec.exe (PID: 2860)
- MSID215.tmp (PID: 4028)
- tapinstall.exe (PID: 316)
- MSI280.tmp (PID: 1932)
Reads Environment values
- UrbanVPN.exe (PID: 1220)
- msiexec.exe (PID: 2832)
- UrbanVPN.exe (PID: 3128)
- msiexec.exe (PID: 3652)
- drvinst.exe (PID: 3432)
- urbanvpnserv.exe (PID: 1232)
- UrbanVPNUpdater.exe (PID: 3000)
Reads Microsoft Office registry keys
- msiexec.exe (PID: 2832)
Process checks Powershell version
- msiexec.exe (PID: 2832)
Checks proxy server information
- UrbanVPN.exe (PID: 1220)
- UrbanVPNUpdater.exe (PID: 3000)
Starts application with an unusual extension
- msiexec.exe (PID: 2860)
Process checks are UAC notifies on
- msiexec.exe (PID: 3652)
Executes as Windows Service
- VSSVC.exe (PID: 3008)
- urbanvpnserv.exe (PID: 1232)
Malware-specific behavior (creating "System.dll" in Temp)
- MSID215.tmp (PID: 4028)
Creates files in the program directory
- MSID215.tmp (PID: 4028)
- UrbanVPNUpdater.exe (PID: 3000)
- urbanvpn-gui.exe (PID: 3032)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 1232)
Connects to unusual port
- msiexec.exe (PID: 3652)
- urbanvpnserv.exe (PID: 1232)
Manual execution by a user
- msedge.exe (PID: 3036)
- UrbanVPNUpdater.exe (PID: 3000)
- wmpnscfg.exe (PID: 1388)
- wmpnscfg.exe (PID: 2736)
- wmpnscfg.exe (PID: 1880)
- wmpnscfg.exe (PID: 2560)
- wmpnscfg.exe (PID: 2580)
- wmpnscfg.exe (PID: 3148)
- wmpnscfg.exe (PID: 3208)
- wmpnscfg.exe (PID: 3408)
- wmpnscfg.exe (PID: 3344)
- wmpnscfg.exe (PID: 3840)
Checks transactions between databases Windows and Oracle
- msiexec.exe (PID: 2816)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
130
Monitored processes
80
Malicious processes
12
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1100 --field-trial-handle=1152,i,3474016441220328974,16667434146352012409,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 316 | "C:\Program Files\TAP-Windows\bin\tapinstall.exe" install "C:\Program Files\TAP-Windows\driver\OemVista.inf" tap0901 | C:\Program Files\TAP-Windows\bin\tapinstall.exe | — | nsD418.tmp | |||||||||||
User: admin Company: Windows (R) Win 7 DDK provider Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 10.0.10011.16384 Modules
| |||||||||||||||
| 452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3260 --field-trial-handle=1152,i,3474016441220328974,16667434146352012409,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 568 | urbanvpn --log "C:\Users\admin\UrbanVPN\log\SG.Asia.Singapore R4.log" --config "SG.Asia.Singapore R4.ovpn" --setenv IV_GUI_VER "UrbanVPN GUI" --service bd800000ac0 0 --auth-retry interact --management 127.0.0.1 25429 stdin --management-query-passwords --management-hold --remap-usr1 SIGTERM --connect-timeout 60 --msg-channel 720 | C:\Program Files\UrbanVPN\bin\urbanvpn.exe | urbanvpnserv.exe | ||||||||||||
User: admin Company: Urban Cyber Security Inc. Integrity Level: MEDIUM Description: UrbanVPN Daemon Exit code: 0 Version: 2.3.0.0 Modules
| |||||||||||||||
| 572 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1528 --field-trial-handle=1212,i,3674429292416181108,622997450965654025,131072 /prefetch:3 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 632 | "C:\Users\admin\AppData\Local\Temp\nszD261.tmp\nsD418.tmp" "C:\Program Files\TAP-Windows\bin\tapinstall.exe" install "C:\Program Files\TAP-Windows\driver\OemVista.inf" tap0901 | C:\Users\admin\AppData\Local\Temp\nszD261.tmp\nsD418.tmp | — | MSID215.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 996 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{4be6b375-be4a-0b2d-2a87-f65259221e0c}\oemvista.inf" "0" "6d14a44ff" "000005D4" "WinSta0\Default" "000005E4" "208" "c:\program files\tap-windows\driver" | C:\Windows\System32\drvinst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3936 --field-trial-handle=1212,i,3674429292416181108,622997450965654025,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1040 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --mojo-platform-channel-handle=3280 --field-trial-handle=1368,i,16709067344812636628,13281050157642075143,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1312 --field-trial-handle=1152,i,3474016441220328974,16667434146352012409,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
63 979
Read events
63 446
Write events
467
Delete events
66
Modification events
| (PID) Process: | (2036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (2036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2036) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (2036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
106
Suspicious files
277
Text files
147
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFdffec.TMP | — | |
MD5:— | SHA256:— | |||
| 2036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RFe0115.TMP | text | |
MD5:C383FD120B14BB0E98E99C1BCC9B43F6 | SHA256:56A3A5EACBD28BEE1CF8C1D0052321A5C27EE858BEF7B2FA1DE20806A0823CC1 | |||
| 2036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFe001b.TMP | text | |
MD5:ADB669AB4CD1C63883C64FB0DBA2C7DA | SHA256:18BFF89047EC5B122573D089B3DC7A7DD14A5A7A515B2D8141584B41E723253F | |||
| 2036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | text | |
MD5:4755704EAEB72509F8E78594142D80D6 | SHA256:52D45B3A4947B8B5B8C48F83F83BA6758CFB7C4434FC574124378F5B01E15999 | |||
| 2036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFe06b2.TMP | — | |
MD5:— | SHA256:— | |||
| 2036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RFe0d69.TMP | — | |
MD5:— | SHA256:— | |||
| 2036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
205
DNS requests
122
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3652 | msiexec.exe | POST | 200 | 148.72.165.78:40000 | http://analytics.urban-vpn.com:40000/tickets | US | — | — | unknown |
3652 | msiexec.exe | POST | 200 | 148.72.165.78:40000 | http://analytics.urban-vpn.com:40000/tickets | US | — | — | unknown |
3652 | msiexec.exe | POST | 200 | 148.72.165.78:40000 | http://analytics.urban-vpn.com:40000/tickets | US | — | — | unknown |
3652 | msiexec.exe | POST | 200 | 148.72.165.78:40004 | http://analytics.urban-vpn.com:40004/tickets | US | — | — | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acndjwmqxwtdgbrvzyvmjueryz3a_3012/jflookgnkcckhobaglndicnbbgbonegd_3012_all_adibosofcauewnjjfrmlhf522neq.crx3 | US | — | — | unknown |
1232 | urbanvpnserv.exe | HEAD | 200 | 212.102.56.178:80 | http://ping.urban-vpn.com/ | DE | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acndjwmqxwtdgbrvzyvmjueryz3a_3012/jflookgnkcckhobaglndicnbbgbonegd_3012_all_adibosofcauewnjjfrmlhf522neq.crx3 | US | binary | 6.60 Kb | unknown |
3000 | UrbanVPNUpdater.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | US | binary | 471 b | unknown |
3000 | UrbanVPNUpdater.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e46bda77852c59f5 | GB | compressed | 4.66 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acndjwmqxwtdgbrvzyvmjueryz3a_3012/jflookgnkcckhobaglndicnbbgbonegd_3012_all_adibosofcauewnjjfrmlhf522neq.crx3 | US | binary | 14.6 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2036 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1044 | chrome.exe | 108.177.15.84:443 | accounts.google.com | GOOGLE | US | unknown |
1044 | chrome.exe | 18.66.248.89:443 | www.urban-vpn.com | AMAZON-02 | US | unknown |
1044 | chrome.exe | 142.250.185.168:443 | www.googletagmanager.com | GOOGLE | US | unknown |
1044 | chrome.exe | 157.240.0.6:443 | connect.facebook.net | FACEBOOK | US | unknown |
1044 | chrome.exe | 18.66.248.25:443 | assets.urban-vpn.com | AMAZON-02 | US | unknown |
1044 | chrome.exe | 108.157.4.119:443 | install.urban-vpn.com | AMAZON-02 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
www.urban-vpn.com |
| unknown |
www.googletagmanager.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
assets.urban-vpn.com |
| unknown |
install.urban-vpn.com |
| unknown |
www.google-analytics.com |
| whitelisted |
bat.bing.com |
| whitelisted |
37165035.adoric-om.com |
| unknown |
analytics.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1232 | urbanvpnserv.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
1232 | urbanvpnserv.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
1232 | urbanvpnserv.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
1232 | urbanvpnserv.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
1232 | urbanvpnserv.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
1232 | urbanvpnserv.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
1232 | urbanvpnserv.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
1232 | urbanvpnserv.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
Process | Message |
|---|---|
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
UrbanVPNUpdater.exe | Logger::SetLogFile( C:\ProgramData\UrbanVPN\updates\updater.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
UrbanVPNUpdater.exe | Logger::SetLogFile( C:\ProgramData\UrbanVPN\updates\updater.log ) while OLD path is: |
urbanvpn-gui.exe | First instance of UrbanVPN was started.
|
msedge.exe | [0109/071633.836:ERROR:process_info.cc(617)] range at 0x0, size 0x18 fully unreadable
|
msedge.exe | [0109/071633.891:ERROR:process_info.cc(617)] range at 0x0, size 0x18 fully unreadable
|
msedge.exe | [0109/071643.706:ERROR:filesystem_win.cc(130)] GetFileAttributes C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad\attachments\f9635780-27b3-4d58-8bbd-b9589f431453: The system cannot find the file specified. (0x2)
|
msedge.exe | [0109/071643.706:ERROR:filesystem_win.cc(130)] GetFileAttributes C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad\attachments\f9635780-27b3-4d58-8bbd-b9589f431453: The system cannot find the file specified. (0x2)
|