analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
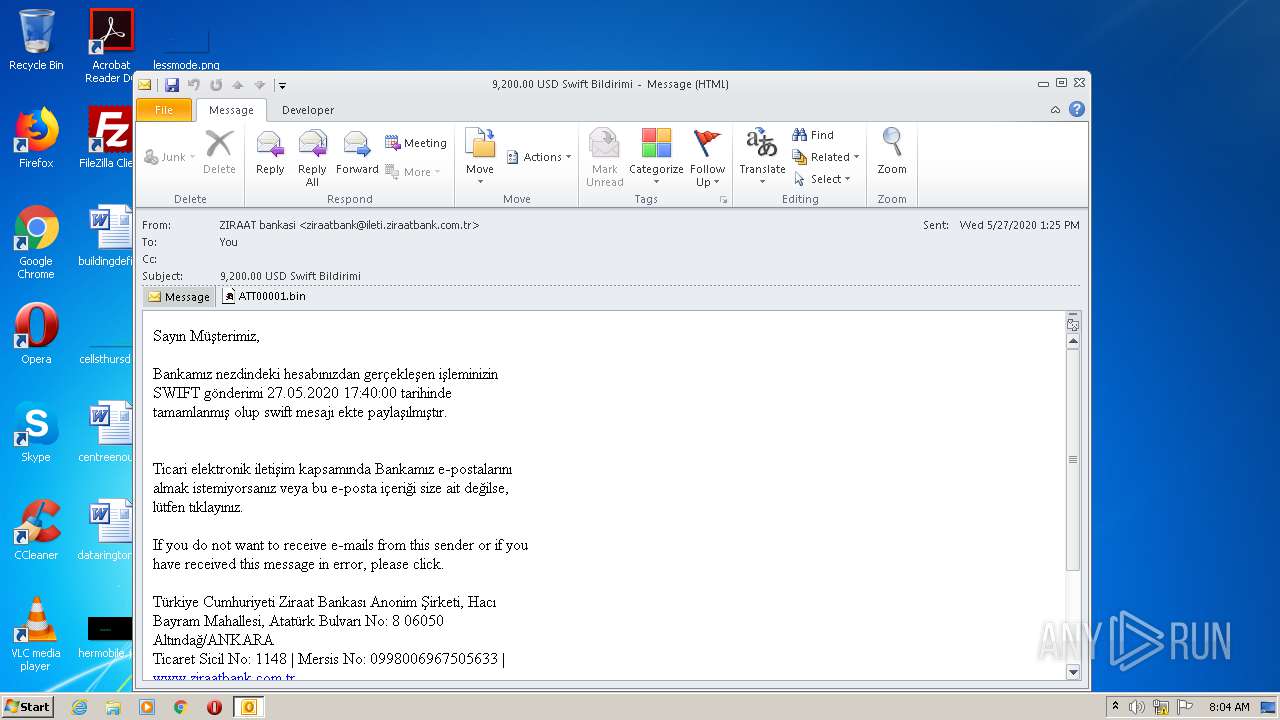
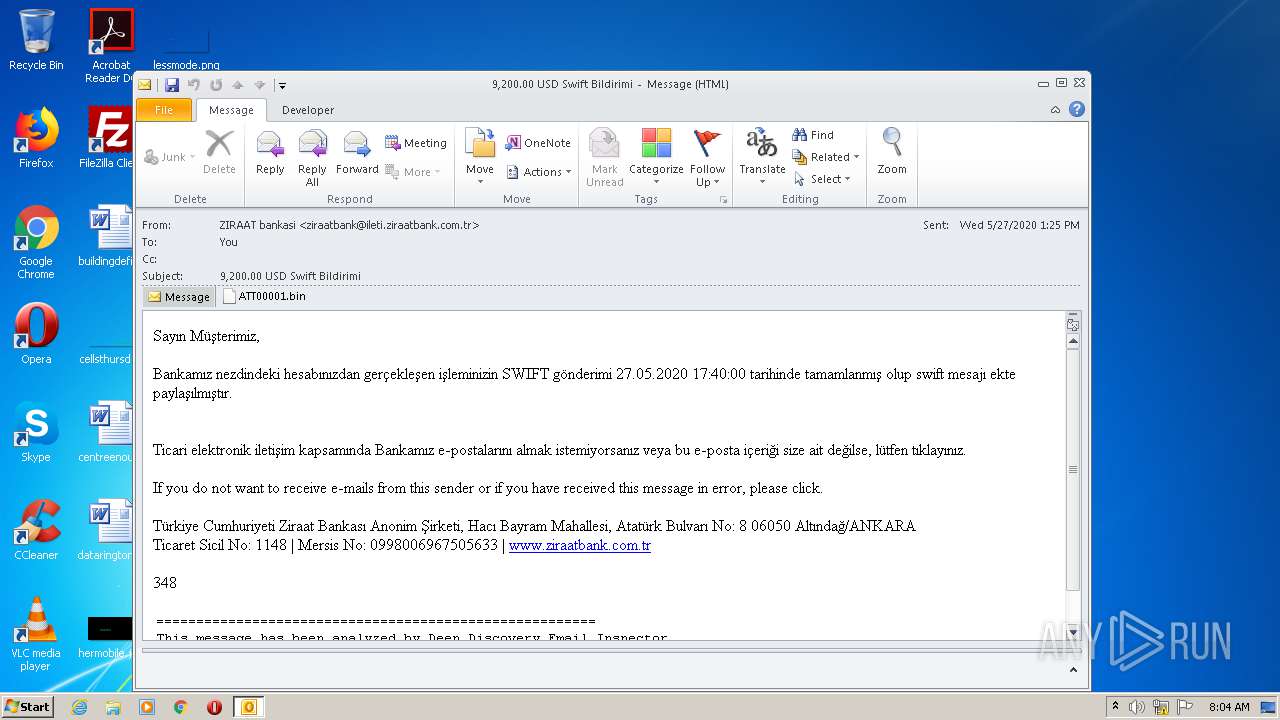
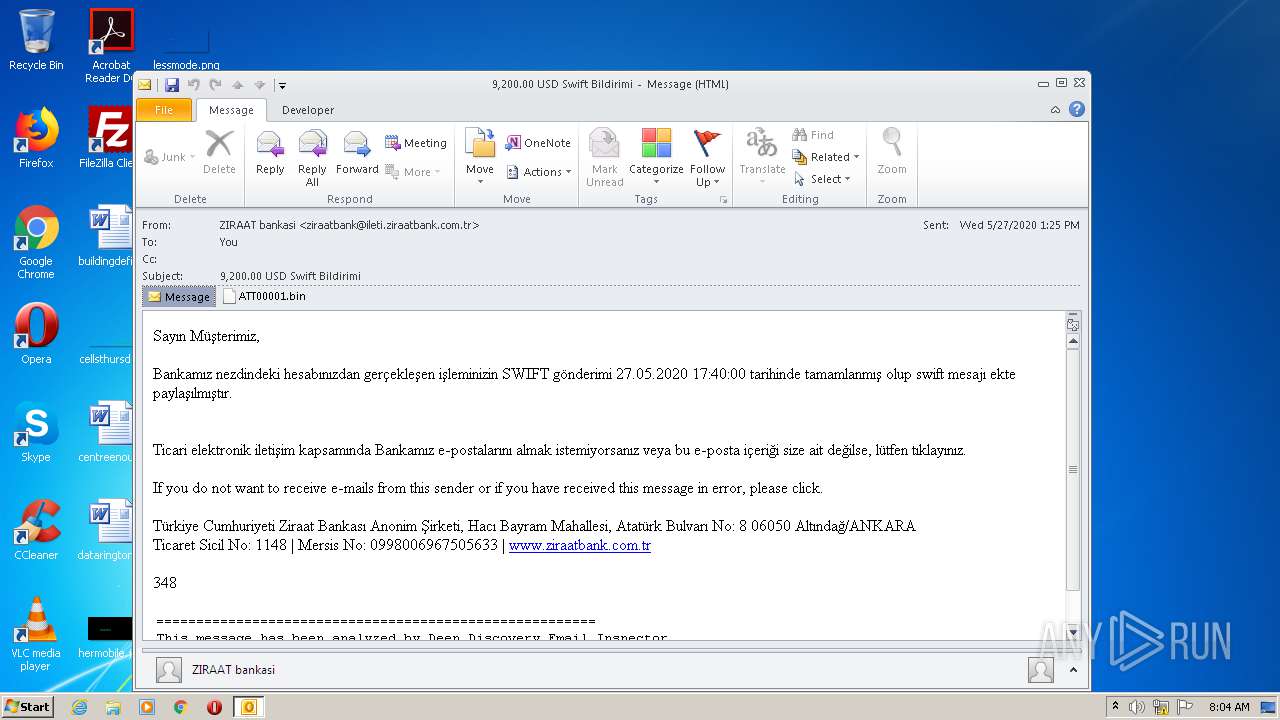
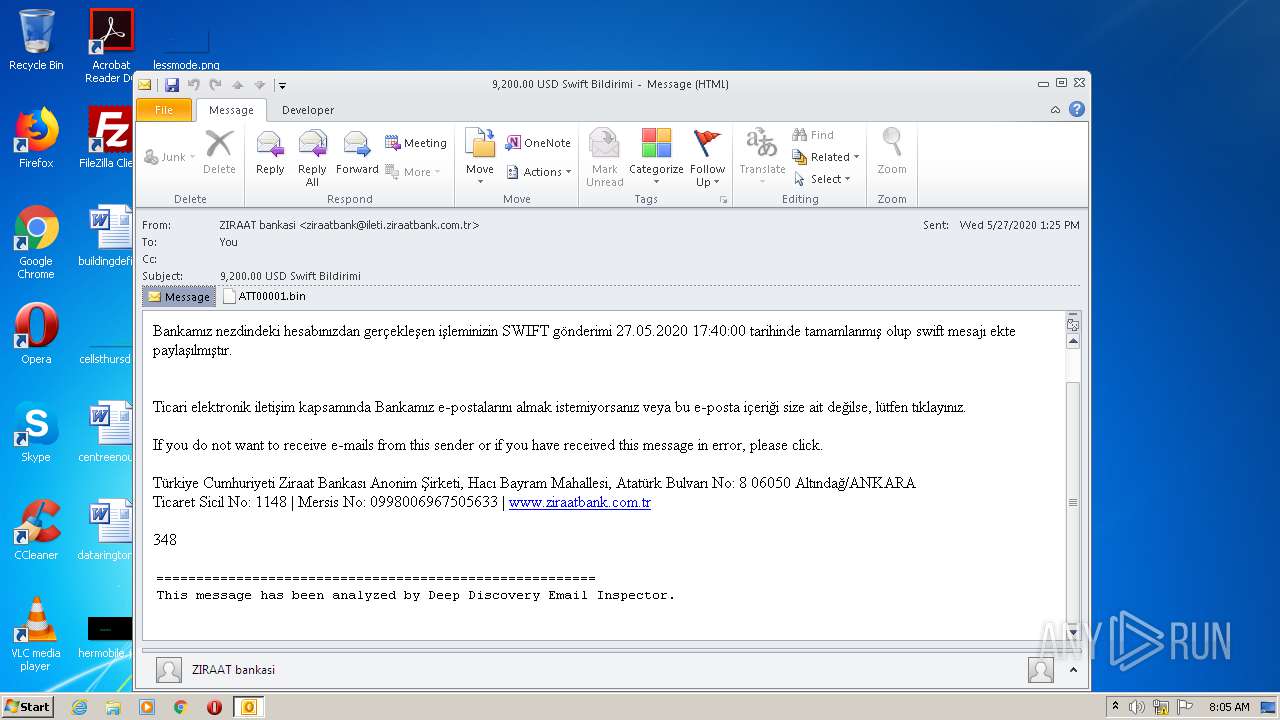
| File name: | 9200.00 USD Swift Bildirimi.msg |
| Full analysis: | https://app.any.run/tasks/3f93908b-cf89-4414-83d9-6a05c6755a8a |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 07:04:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 5F383951A5FAC3F2D36CED380D61D443 |
| SHA1: | 4B609E1F46B13D6DE75BC7A48DA34E6CD1E46AB1 |
| SHA256: | 58E602F10298A73E5752E3864580318D9B4CB8E16B1DD1F41165141C13EC7A9F |
| SSDEEP: | 24576:Zrw9ulmNu0wK453wRK0gChMjftdn9ciWArVP:Zg9uMU3kK1Cwt4ib |
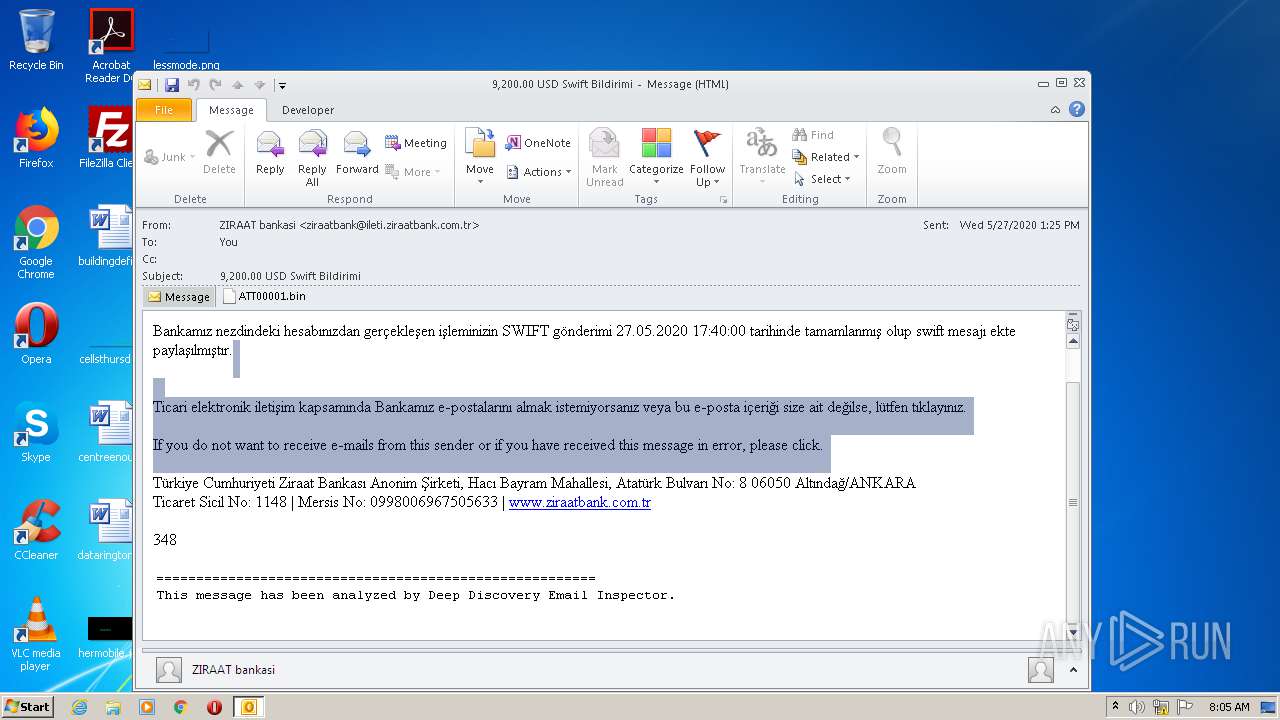
MALICIOUS
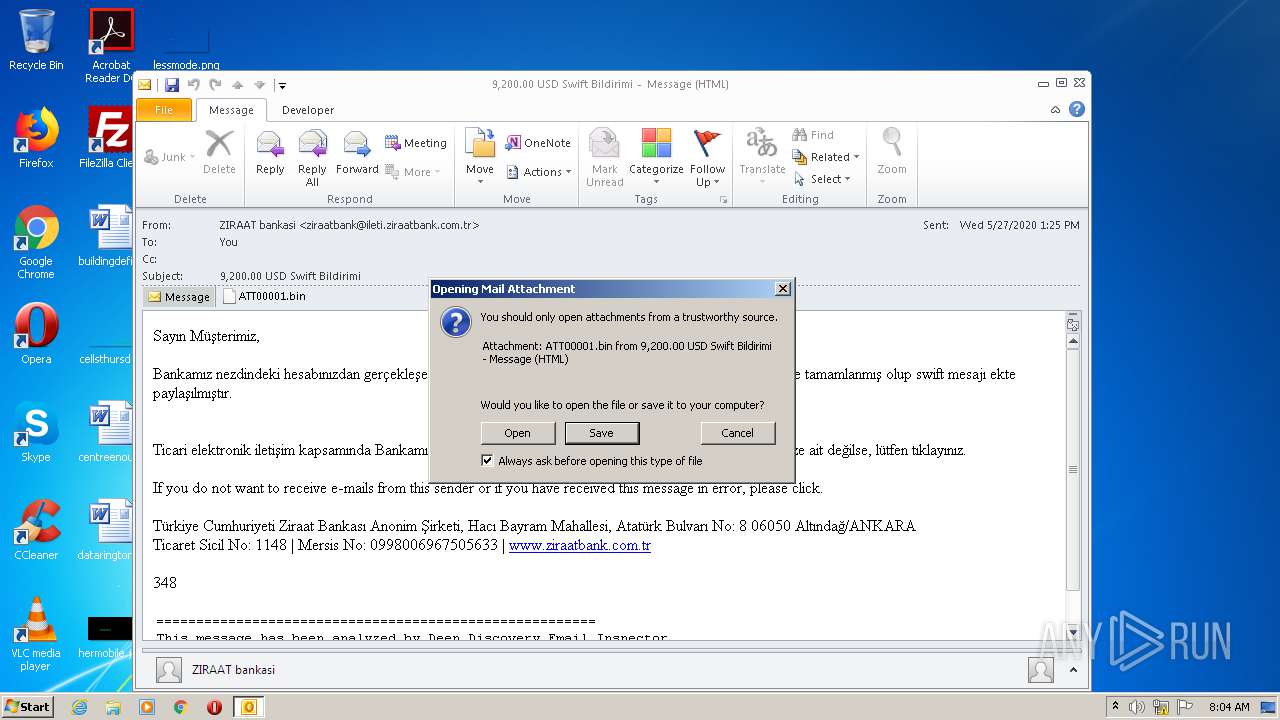
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2116)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- OUTLOOK.EXE (PID: 2116)
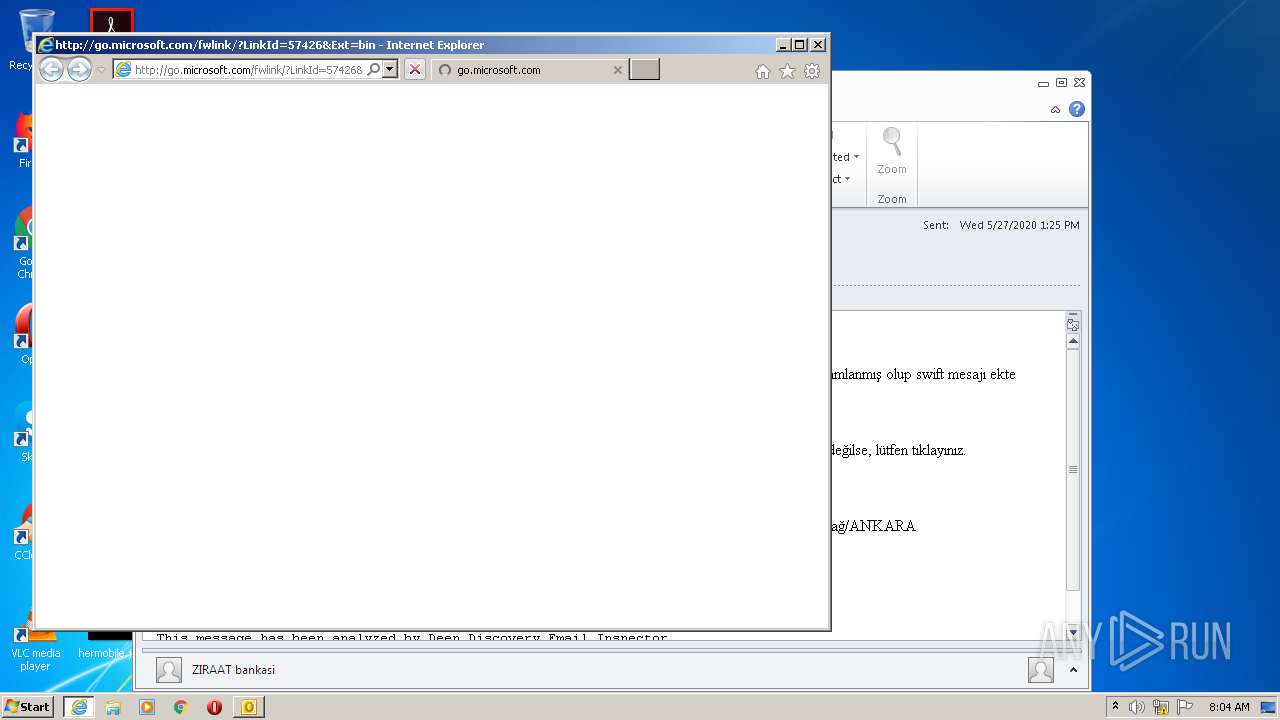
Starts Internet Explorer
- rundll32.exe (PID: 2736)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2116)
INFO
Reads settings of System Certificates
- iexplore.exe (PID: 3740)
- iexplore.exe (PID: 3524)
Changes internet zones settings
- iexplore.exe (PID: 3524)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2116)
- iexplore.exe (PID: 3740)
- iexplore.exe (PID: 3524)
Application launched itself
- iexplore.exe (PID: 3524)
Creates files in the user directory
- iexplore.exe (PID: 3740)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2116)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3740)
Reads internet explorer settings
- iexplore.exe (PID: 3740)
Changes settings of System certificates
- iexplore.exe (PID: 3524)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
39
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2116 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\9200.00 USD Swift Bildirimi.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Version: 14.0.6025.1000 | ||||
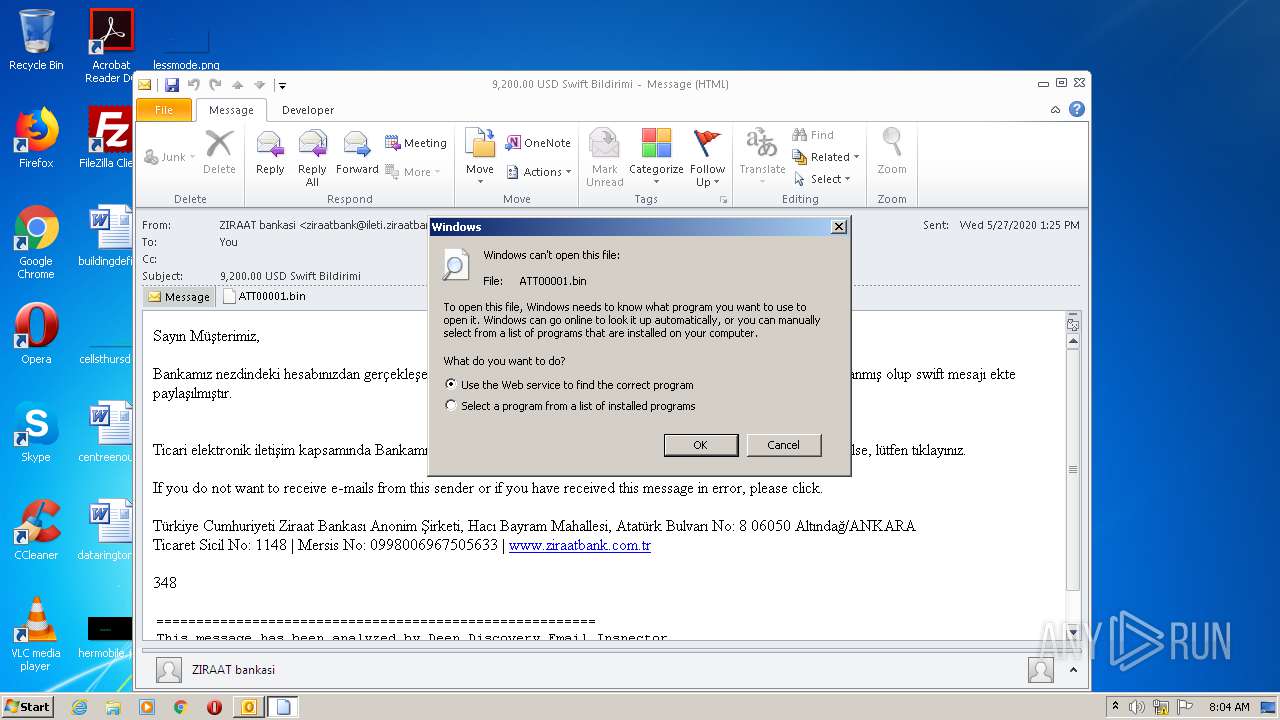
| 2736 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\J1NJQT5W\ATT00001.bin | C:\Windows\system32\rundll32.exe | — | OUTLOOK.EXE |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 3221225547 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
| 3524 | "C:\Program Files\Internet Explorer\iexplore.exe" http://go.microsoft.com/fwlink/?LinkId=57426&Ext=bin | C:\Program Files\Internet Explorer\iexplore.exe | rundll32.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) | ||||
| 3740 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3524 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) | ||||
Total events
2 475
Read events
1 837
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
13
Text files
33
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2116 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRADF4.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2116 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\J1NJQT5W\ATT00001 (2).bin\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3740 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab51D.tmp | — | |
MD5:— | SHA256:— | |||
| 3740 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar51E.tmp | — | |
MD5:— | SHA256:— | |||
| 3740 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\TT542MJ3.txt | — | |
MD5:— | SHA256:— | |||
| 3740 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\YE7QCHMI.txt | — | |
MD5:— | SHA256:— | |||
| 3740 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\VDC59QLB.txt | — | |
MD5:— | SHA256:— | |||
| 3740 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\11WGXQLK.txt | — | |
MD5:— | SHA256:— | |||
| 2116 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:8849F2213A6F66B465C3AC7B83174F3E | SHA256:9E88E1209289188341EFF114D28B1526BFCA6B0870A32DF60C7FA864FAD04616 | |||
| 2116 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:B9647AEAE29B64E54C19CCC3AA09202B | SHA256:CCCAD2FD01CBA45AFE35D0AE1CDF16452CDFF09032DCA28E9D3360FCC4BBF439 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
17
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3740 | iexplore.exe | GET | 301 | 2.16.186.27:80 | http://shell.windows.com/fileassoc/fileassoc.asp?Ext=bin | unknown | — | — | whitelisted |
3740 | iexplore.exe | GET | 302 | 104.108.39.131:80 | http://go.microsoft.com/fwlink/?LinkId=57426&Ext=bin | NL | — | — | whitelisted |
3740 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
1052 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEA7yTSbUNi7CXXtef0luXqk%3D | US | der | 279 b | whitelisted |
1052 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3524 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3740 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3740 | iexplore.exe | 2.16.186.27:80 | shell.windows.com | Akamai International B.V. | — | whitelisted |
1052 | svchost.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3524 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2116 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3524 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3740 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3740 | iexplore.exe | 104.108.39.131:80 | go.microsoft.com | Akamai Technologies, Inc. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
shell.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |