| download: | /mestermc.exe |
| Full analysis: | https://app.any.run/tasks/df90b3bb-0e59-494e-9289-545c80ef94a7 |
| Verdict: | Malicious activity |
| Analysis date: | July 08, 2025, 20:29:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 11 sections |
| MD5: | DEB9C806AA00DE374FA78D5FFB02BA40 |
| SHA1: | 3FBDBB1B91E21475DD5A7E1DBA94A6EBAB771E71 |
| SHA256: | 58DE88C919C75751592A8ED36B280EC41837E30D0ECF9EFFBFB92232D584C42A |
| SSDEEP: | 98304:jLVIF8P3n1BLHxtD59KEKjSvkyklAI6YFKUvguJZYsdgQsbh1vNIw1aYOtj7fQEy:6YDo2 |
MALICIOUS
Script downloads file (POWERSHELL)
- powershell.exe (PID: 5808)
- powershell.exe (PID: 1508)
SUSPICIOUS
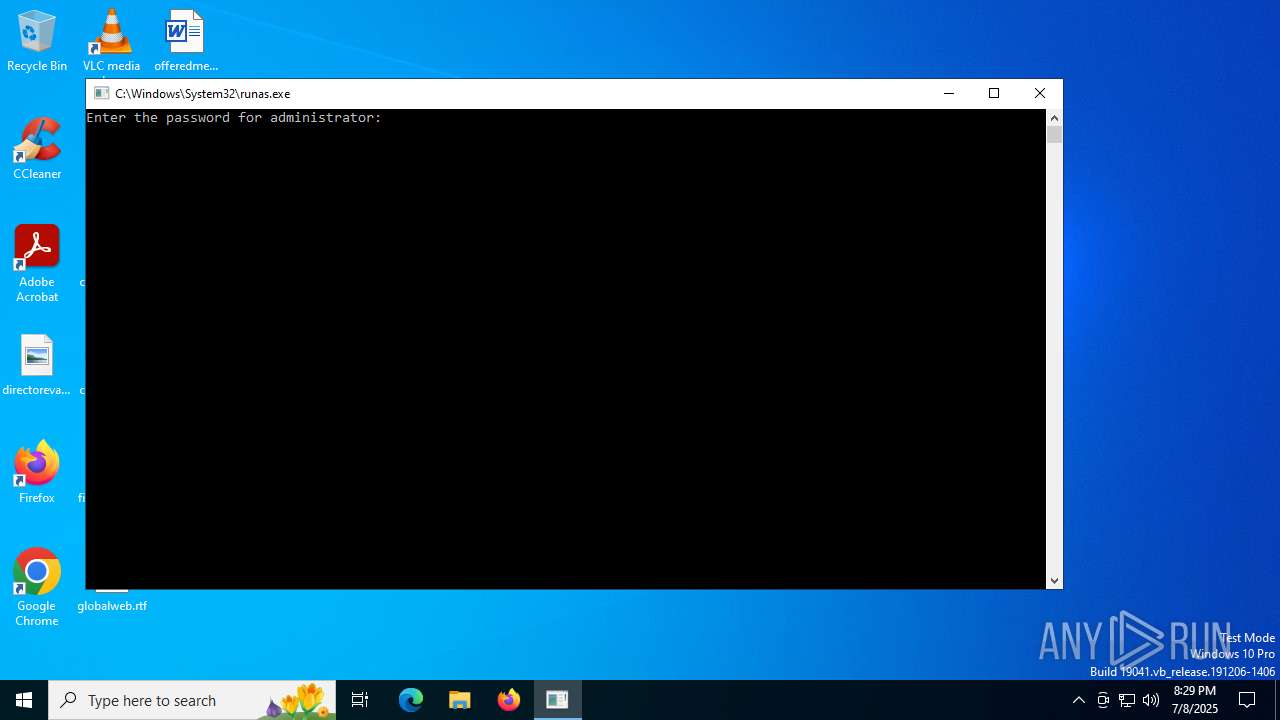
Starts another process probably with elevated privileges via RUNAS.EXE
- runas.exe (PID: 5368)
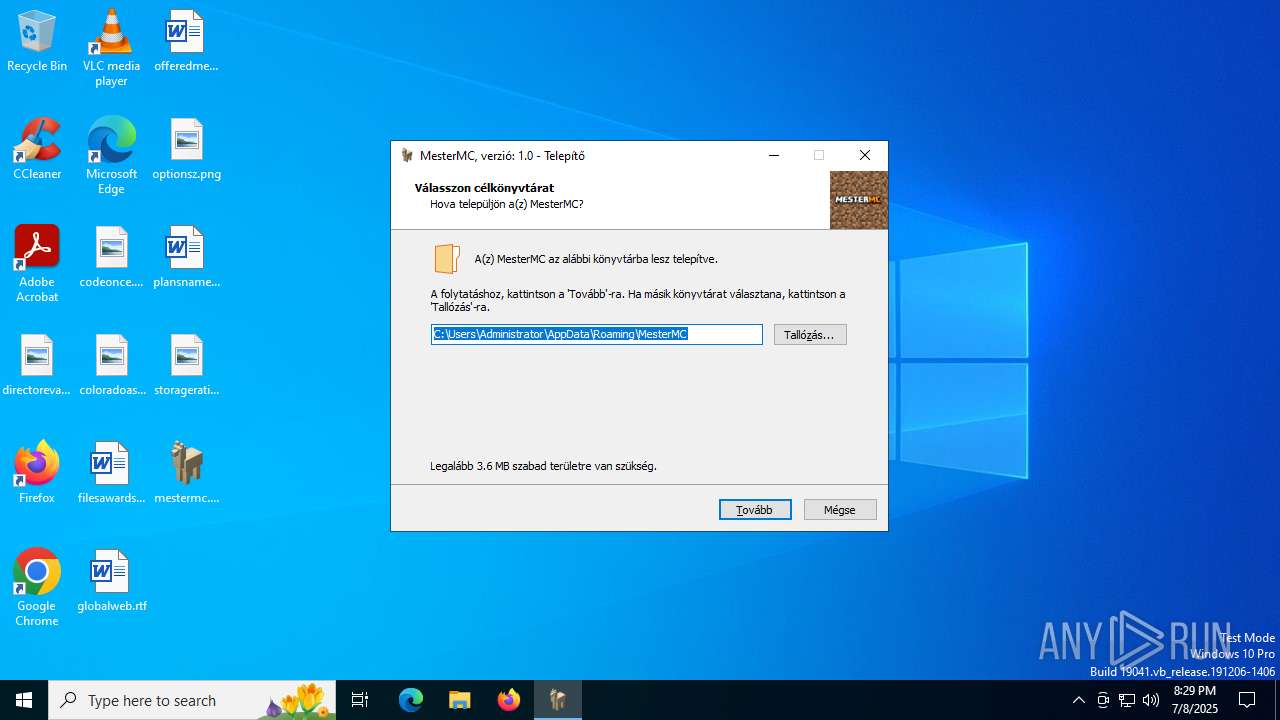
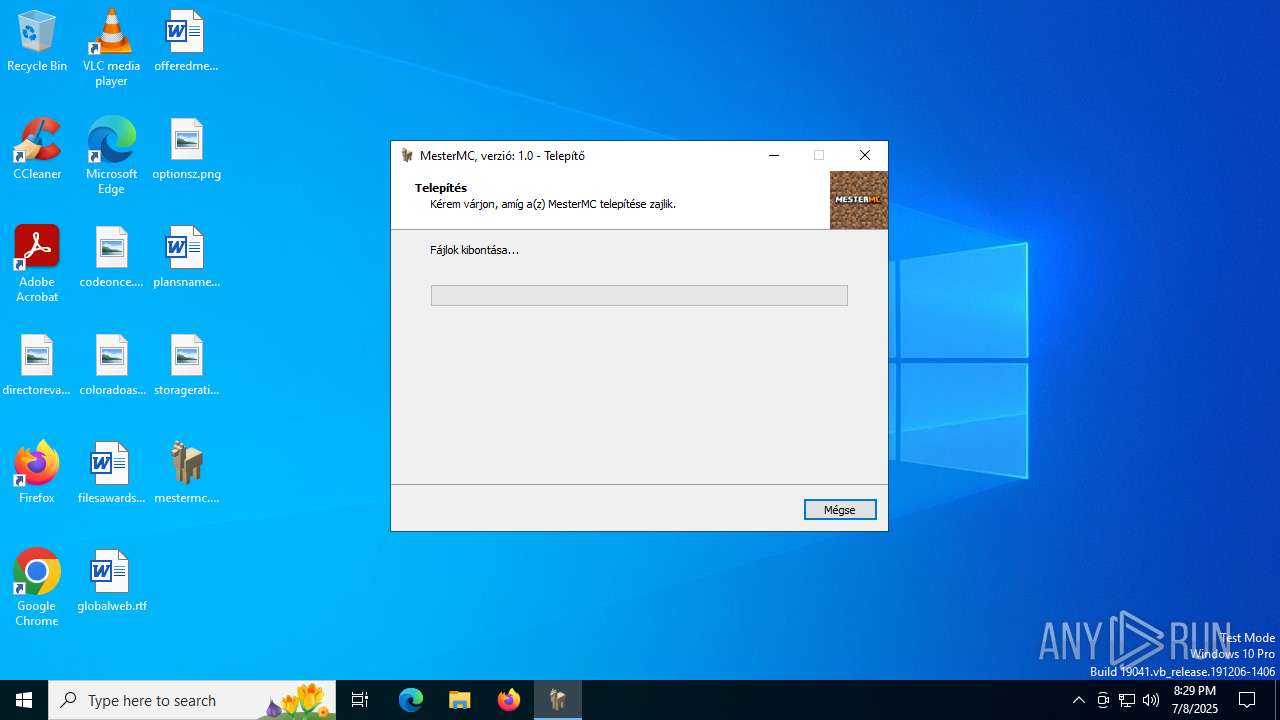
Executable content was dropped or overwritten
- mestermc.exe (PID: 3580)
- mestermc.tmp (PID: 2228)
- mestermc.exe (PID: 1480)
- mestermc.exe (PID: 3572)
- mestermc.exe (PID: 1096)
- mestermc.exe (PID: 3000)
- mestermc.tmp (PID: 3740)
- mestermc.tmp (PID: 4264)
Reads the Windows owner or organization settings
- mestermc.tmp (PID: 2228)
- mestermc.tmp (PID: 3740)
- mestermc.tmp (PID: 4264)
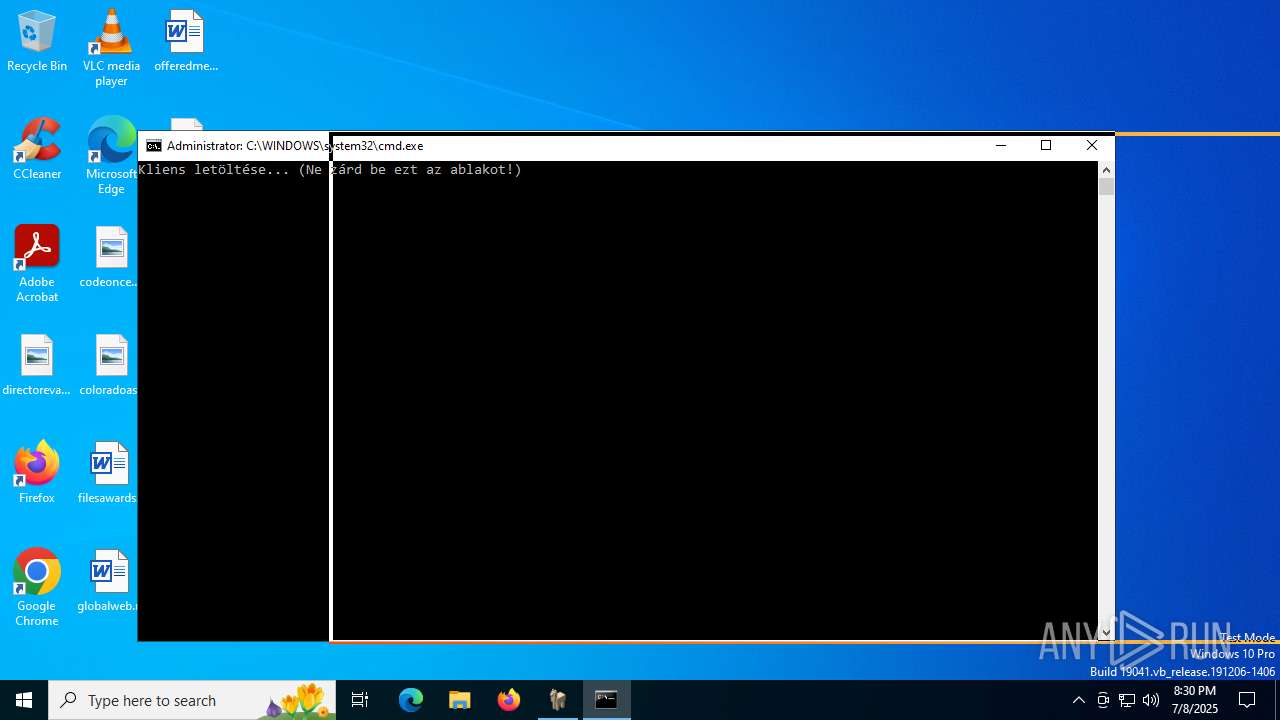
Starts CMD.EXE for commands execution
- mestermc.tmp (PID: 2228)
- mestermc.tmp (PID: 4264)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 864)
- cmd.exe (PID: 888)
Probably download files using WebClient
- cmd.exe (PID: 864)
- cmd.exe (PID: 888)
Reads security settings of Internet Explorer
- mestermc.tmp (PID: 7132)
- mestermc.tmp (PID: 2120)
Searches for installed software
- mestermc.tmp (PID: 3740)
- mestermc.tmp (PID: 4264)
INFO
Checks supported languages
- mestermc.exe (PID: 3580)
- mestermc.tmp (PID: 2228)
- SearchApp.exe (PID: 5328)
- mestermc.exe (PID: 1480)
- mestermc.tmp (PID: 7132)
- mestermc.exe (PID: 3572)
- mestermc.tmp (PID: 3740)
- mestermc.tmp (PID: 2120)
- mestermc.exe (PID: 1096)
- mestermc.exe (PID: 3000)
- mestermc.tmp (PID: 4264)
Reads the computer name
- mestermc.exe (PID: 3580)
- mestermc.tmp (PID: 2228)
- mestermc.tmp (PID: 7132)
- mestermc.exe (PID: 3572)
- mestermc.tmp (PID: 3740)
- mestermc.tmp (PID: 2120)
- mestermc.exe (PID: 3000)
- mestermc.tmp (PID: 4264)
Creates files in the program directory
- mestermc.tmp (PID: 2228)
Creates a software uninstall entry
- mestermc.tmp (PID: 2228)
- mestermc.tmp (PID: 4264)
Process checks computer location settings
- SearchApp.exe (PID: 5328)
- mestermc.tmp (PID: 7132)
- mestermc.tmp (PID: 2120)
Disables trace logs
- powershell.exe (PID: 5808)
- powershell.exe (PID: 1508)
Checks proxy server information
- powershell.exe (PID: 5808)
- slui.exe (PID: 6224)
- powershell.exe (PID: 1508)
Detects InnoSetup installer (YARA)
- mestermc.exe (PID: 3580)
- mestermc.tmp (PID: 2228)
- mestermc.exe (PID: 3000)
- mestermc.exe (PID: 1096)
- mestermc.tmp (PID: 2120)
- mestermc.tmp (PID: 4264)
Compiled with Borland Delphi (YARA)
- mestermc.exe (PID: 3580)
- mestermc.tmp (PID: 2228)
- mestermc.exe (PID: 1096)
- mestermc.tmp (PID: 2120)
- mestermc.exe (PID: 3000)
- mestermc.tmp (PID: 4264)
Manual execution by a user
- mestermc.exe (PID: 1480)
- mestermc.exe (PID: 1096)
Create files in a temporary directory
- mestermc.exe (PID: 1480)
- mestermc.exe (PID: 3572)
- mestermc.tmp (PID: 3740)
- mestermc.exe (PID: 1096)
- mestermc.exe (PID: 3000)
- mestermc.tmp (PID: 4264)
Reads the software policy settings
- SearchApp.exe (PID: 5328)
- slui.exe (PID: 6224)
Reads the machine GUID from the registry
- SearchApp.exe (PID: 5328)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (67.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (25.6) |
| .exe | | | Win32 Executable (generic) (2.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:03:13 06:55:45+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 704512 |
| InitializedDataSize: | 223232 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xacfe0 |
| OSVersion: | 6.1 |
| ImageVersion: | - |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
| FileDescription: | MesterMC Setup |
| FileVersion: | |
| LegalCopyright: | |
| OriginalFileName: | |
| ProductName: | MesterMC |
| ProductVersion: | 1.0 |
Total processes
165
Monitored processes
20
Malicious processes
2
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
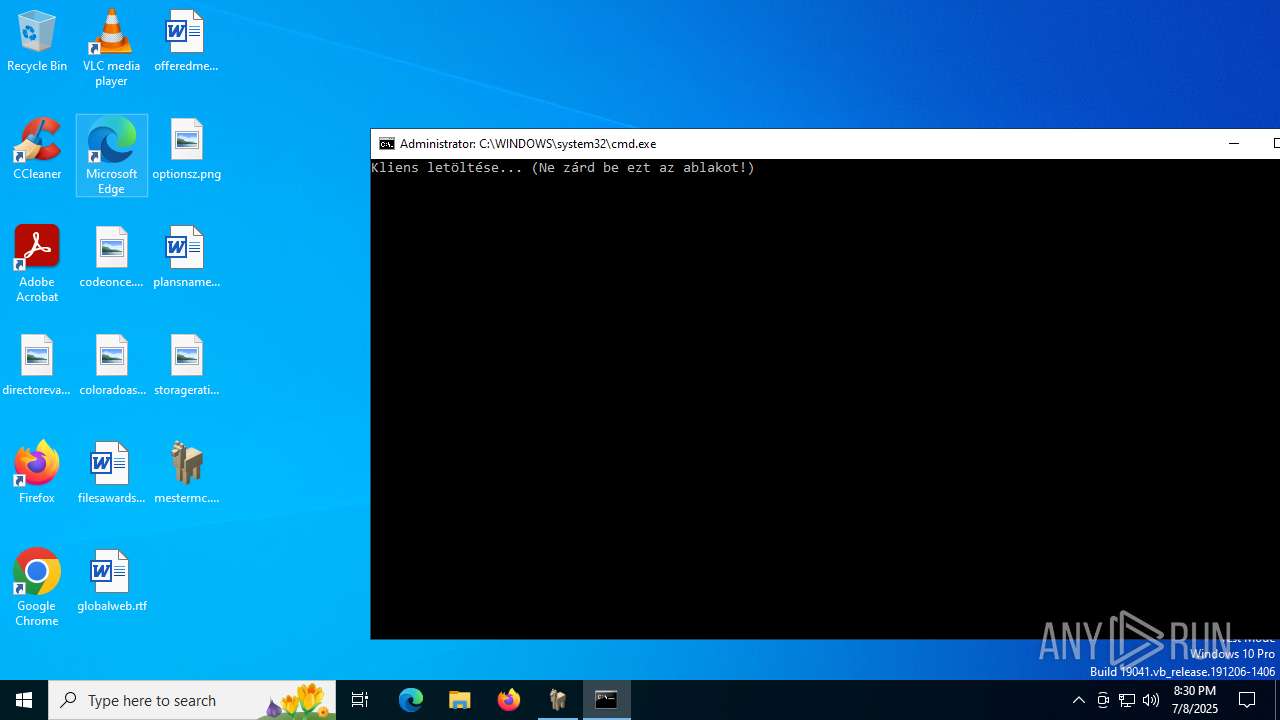
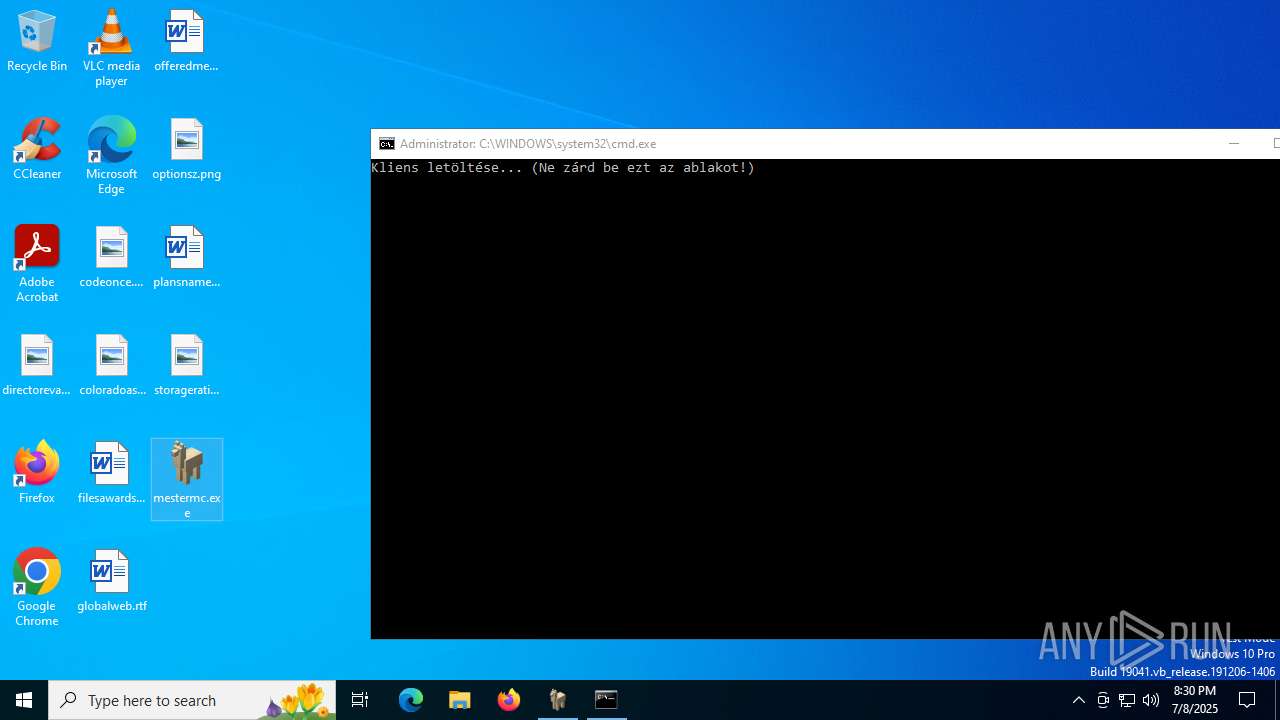
| 864 | "C:\WINDOWS\system32\cmd.exe" /C powershell -Command "Write-Host 'Kliens letöltése... (Ne zárd be ezt az ablakot!)'; $client = New-Object System.Net.WebClient; $client.DownloadFile('https://mestermc.b-cdn.net/MesterMC.jar', 'C:\Users\Administrator\AppData\Roaming\MesterMC\MesterMC.jar'); Write-Host 'Letöltés kész.'" | C:\Windows\SysWOW64\cmd.exe | — | mestermc.tmp | |||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 888 | "C:\WINDOWS\system32\cmd.exe" /C powershell -Command "Write-Host 'Kliens letöltése... (Ne zárd be ezt az ablakot!)'; $client = New-Object System.Net.WebClient; $client.DownloadFile('https://mestermc.b-cdn.net/MesterMC.jar', 'C:\Users\Administrator\AppData\Roaming\MesterMC\MesterMC.jar'); Write-Host 'Letöltés kész.'" | C:\Windows\SysWOW64\cmd.exe | — | mestermc.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
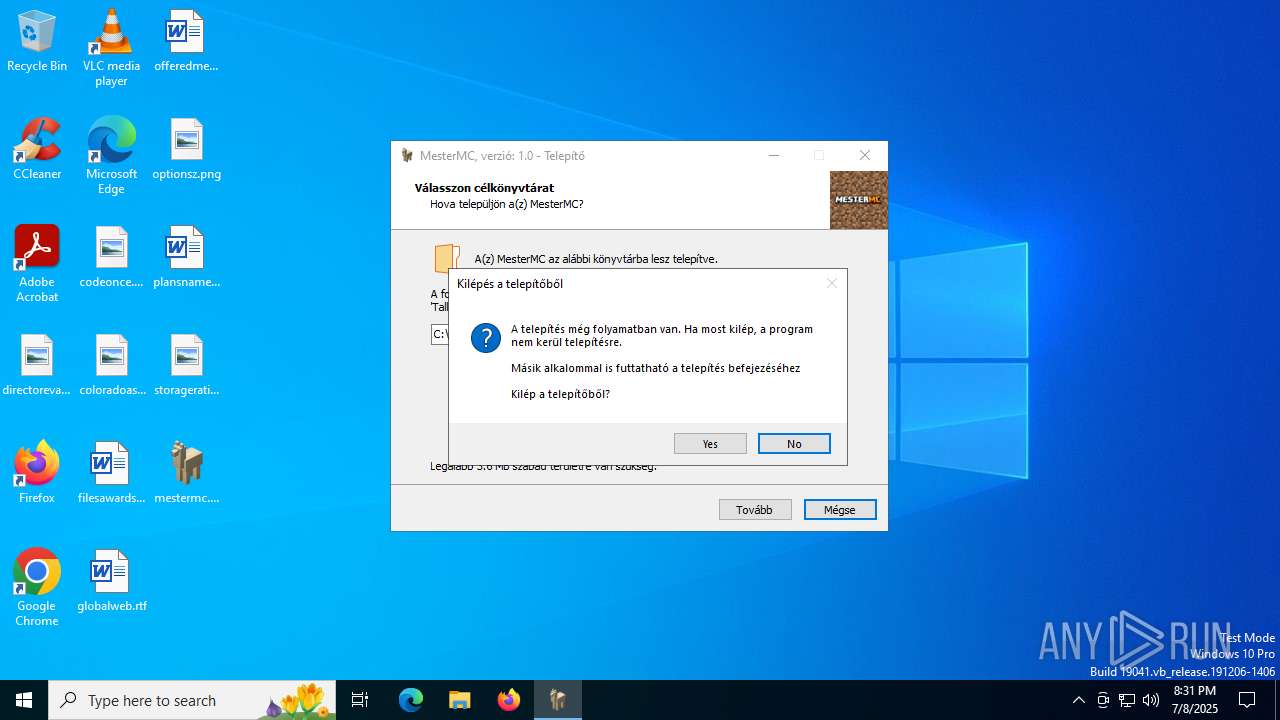
| 1096 | "C:\Users\admin\Desktop\mestermc.exe" | C:\Users\admin\Desktop\mestermc.exe | — | explorer.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: MesterMC Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1480 | "C:\Users\admin\Desktop\mestermc.exe" | C:\Users\admin\Desktop\mestermc.exe | — | explorer.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: MesterMC Setup Exit code: 2 Version: Modules
| |||||||||||||||
| 1508 | powershell -Command "Write-Host 'Kliens letöltése... (Ne zárd be ezt az ablakot!)'; $client = New-Object System.Net.WebClient; $client.DownloadFile('https://mestermc.b-cdn.net/MesterMC.jar', 'C:\Users\Administrator\AppData\Roaming\MesterMC\MesterMC.jar'); Write-Host 'Letöltés kész.'" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1944 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2120 | "C:\Users\admin\AppData\Local\Temp\is-76I6G.tmp\mestermc.tmp" /SL5="$F0344,957379,928768,C:\Users\admin\Desktop\mestermc.exe" | C:\Users\admin\AppData\Local\Temp\is-76I6G.tmp\mestermc.tmp | — | mestermc.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2228 | "C:\Users\ADMINI~1\AppData\Local\Temp\is-4D9B8.tmp\mestermc.tmp" /SL5="$6025A,957379,928768,C:\Users\admin\Desktop\mestermc.exe" | C:\Users\Administrator\AppData\Local\Temp\is-4D9B8.tmp\mestermc.tmp | — | mestermc.exe | |||||||||||
User: Administrator Company: Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3000 | "C:\Users\admin\Desktop\mestermc.exe" /SPAWNWND=$A0244 /NOTIFYWND=$F0344 | C:\Users\admin\Desktop\mestermc.exe | mestermc.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: MesterMC Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 3572 | "C:\Users\admin\Desktop\mestermc.exe" /SPAWNWND=$702D4 /NOTIFYWND=$70282 | C:\Users\admin\Desktop\mestermc.exe | mestermc.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: MesterMC Setup Exit code: 2 Version: Modules
| |||||||||||||||
Total events
17 721
Read events
17 555
Write events
160
Delete events
6
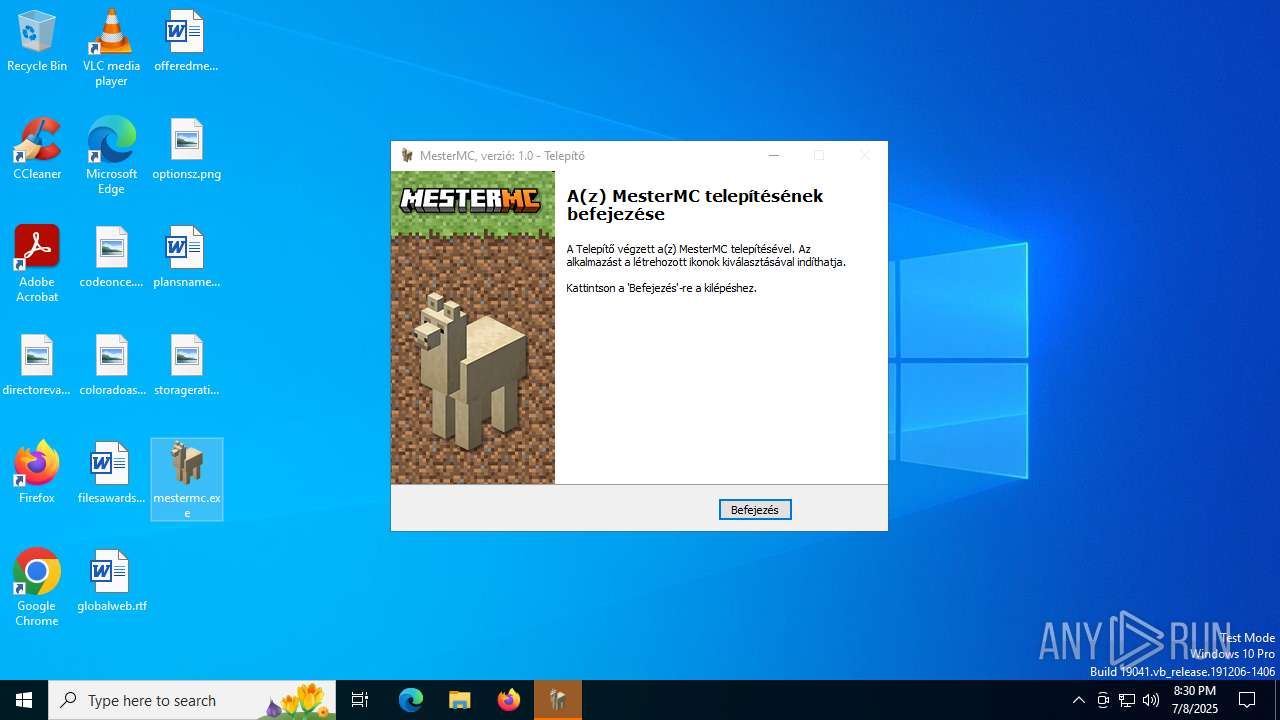
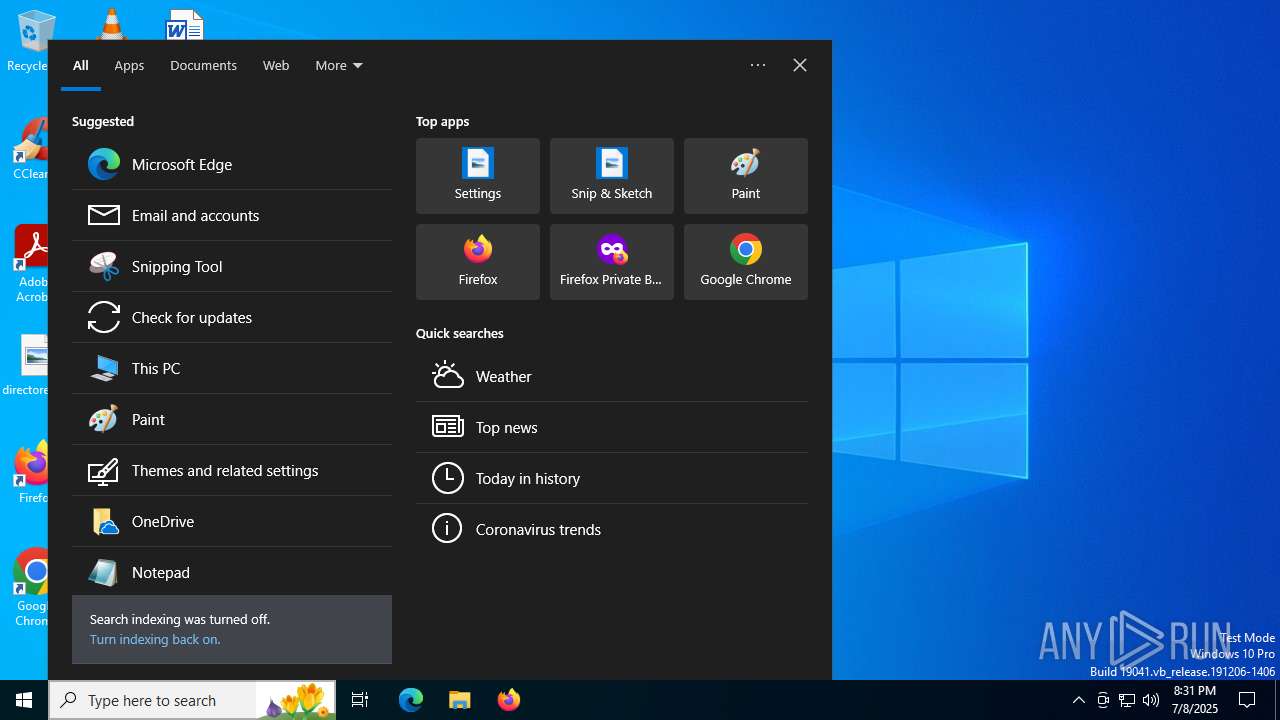
Modification events
| (PID) Process: | (2228) mestermc.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\MesterMC_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.4.2 | |||
| (PID) Process: | (2228) mestermc.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\MesterMC_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
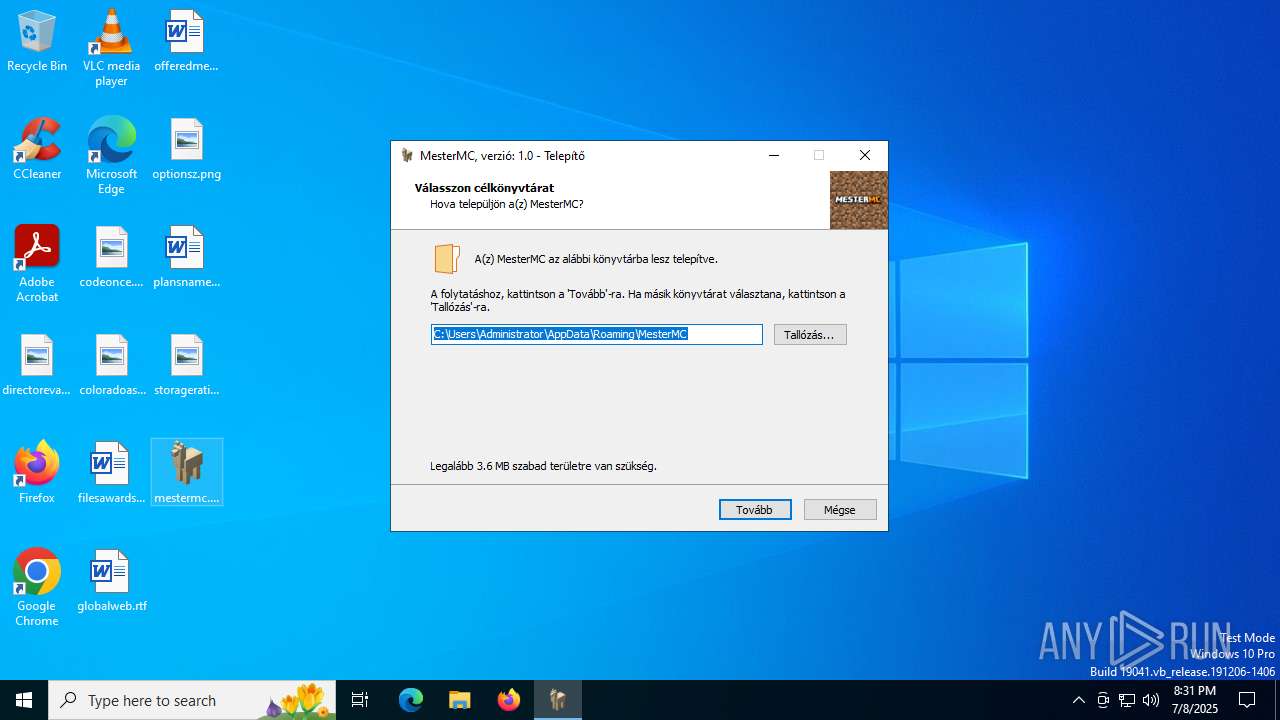
Value: C:\Users\Administrator\AppData\Roaming\MesterMC | |||
| (PID) Process: | (2228) mestermc.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\MesterMC_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Users\Administrator\AppData\Roaming\MesterMC\ | |||
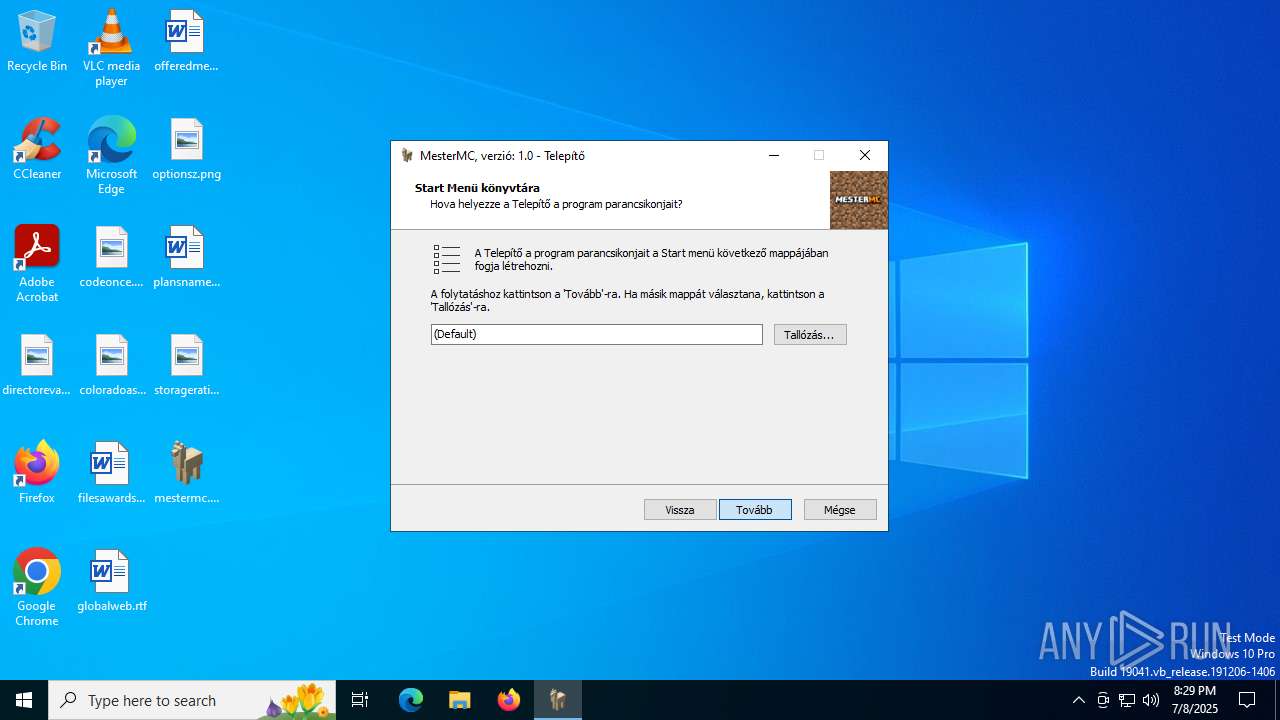
| (PID) Process: | (2228) mestermc.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\MesterMC_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: (Default) | |||
| (PID) Process: | (2228) mestermc.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\MesterMC_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: Administrator | |||
| (PID) Process: | (2228) mestermc.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\MesterMC_is1 |
| Operation: | write | Name: | Inno Setup: Selected Tasks |
Value: desktopicon,startmenuicon | |||
| (PID) Process: | (2228) mestermc.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\MesterMC_is1 |
| Operation: | write | Name: | Inno Setup: Deselected Tasks |
Value: | |||
| (PID) Process: | (2228) mestermc.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\MesterMC_is1 |
| Operation: | write | Name: | Inno Setup: Language |
Value: hu | |||
| (PID) Process: | (2228) mestermc.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\MesterMC_is1 |
| Operation: | write | Name: | DisplayName |
Value: MesterMC, verzió: 1.0 | |||
| (PID) Process: | (2228) mestermc.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\MesterMC_is1 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Users\Administrator\AppData\Roaming\MesterMC\unins000.exe" | |||
Executable files
12
Suspicious files
117
Text files
148
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5328 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\DeviceSearchCache\AppCache133964801997677929.txt~RF179470.TMP | — | |
MD5:— | SHA256:— | |||
| 2228 | mestermc.tmp | C:\Users\Administrator\AppData\Roaming\MesterMC\is-PL181.tmp | image | |
MD5:429549DA474E29DA8E4B2E5D67175327 | SHA256:4569A18F73F03359A5D19F07663EDE143D8A25571B4910C5FD426991391B2300 | |||
| 2228 | mestermc.tmp | C:\Users\Administrator\AppData\Roaming\MesterMC\mestermc.txt | text | |
MD5:F434C6B6CD10260C2BB5C7D3B9856765 | SHA256:C490ECC474F2D3F26708DD1767B85D13342FD3892B856400234019594CB58994 | |||
| 2228 | mestermc.tmp | C:\Users\Administrator\AppData\Roaming\MesterMC\is-ML0IP.tmp | text | |
MD5:F434C6B6CD10260C2BB5C7D3B9856765 | SHA256:C490ECC474F2D3F26708DD1767B85D13342FD3892B856400234019594CB58994 | |||
| 2228 | mestermc.tmp | C:\Users\Administrator\AppData\Roaming\MesterMC\is-926O5.tmp | executable | |
MD5:1CC6DD734E4559066F2DDA3033B86340 | SHA256:0DEEF53CB9EABEDBF4C62781CEB1EB28A2293437BF530D7B58FA97D929C648F3 | |||
| 5328 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\DeviceSearchCache\AppCache133964802297253930.txt~RF1809cf.TMP | — | |
MD5:— | SHA256:— | |||
| 2228 | mestermc.tmp | C:\Users\Administrator\AppData\Roaming\MesterMC\icon.ico | image | |
MD5:429549DA474E29DA8E4B2E5D67175327 | SHA256:4569A18F73F03359A5D19F07663EDE143D8A25571B4910C5FD426991391B2300 | |||
| 2228 | mestermc.tmp | C:\Users\Administrator\AppData\Roaming\MesterMC\unins000.dat | dat | |
MD5:897F60A6BE34C999F687051D97DD8B4C | SHA256:EACCB7253E31AF78EC42F177421B0832F1502A79F405220E51FBDE6E2F40CC56 | |||
| 5808 | powershell.exe | C:\Users\Administrator\AppData\Local\Temp\__PSScriptPolicyTest_ayoxsbq3.qy3.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2228 | mestermc.tmp | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\MesterMC.lnk | lnk | |
MD5:353E4326B373598FEF9C17003C705611 | SHA256:1E3BC916A558C5BFC379081E4269982FCFC0F010DD1F666981E18AC386332036 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
43
DNS requests
30
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5444 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3584 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3584 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4444 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5444 | svchost.exe | 20.190.159.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5444 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
mestermc.b-cdn.net |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |