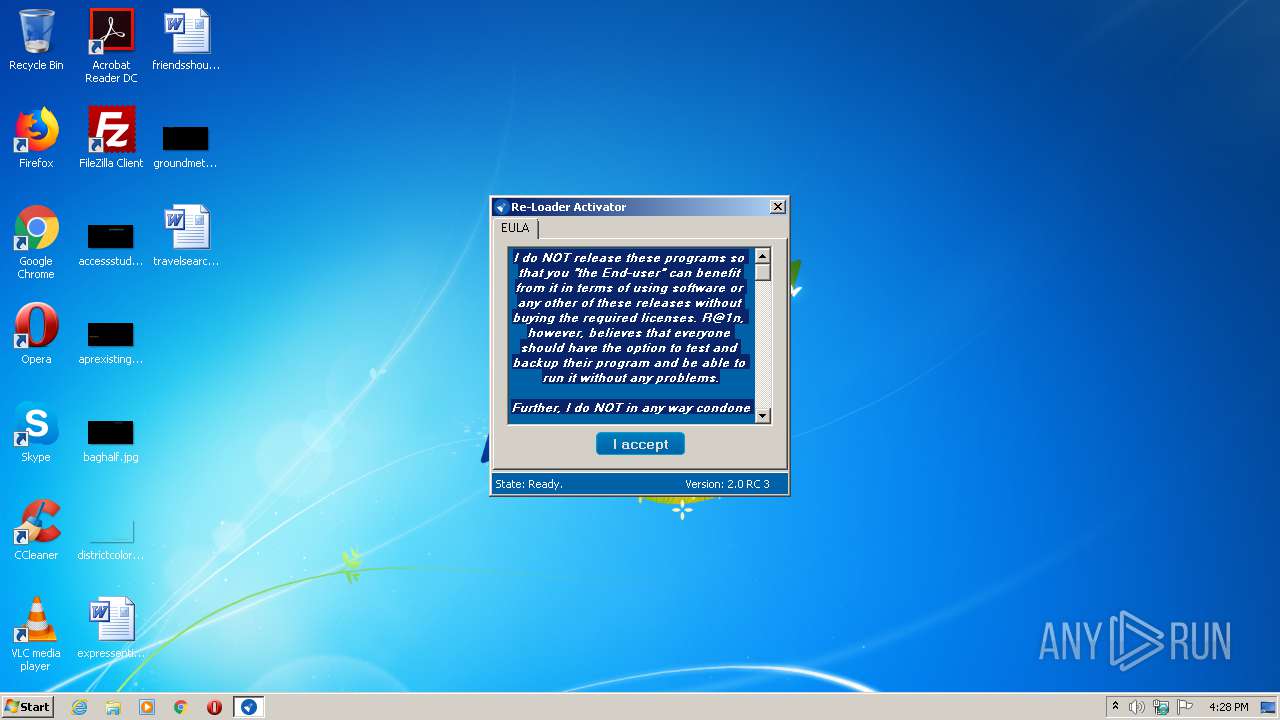
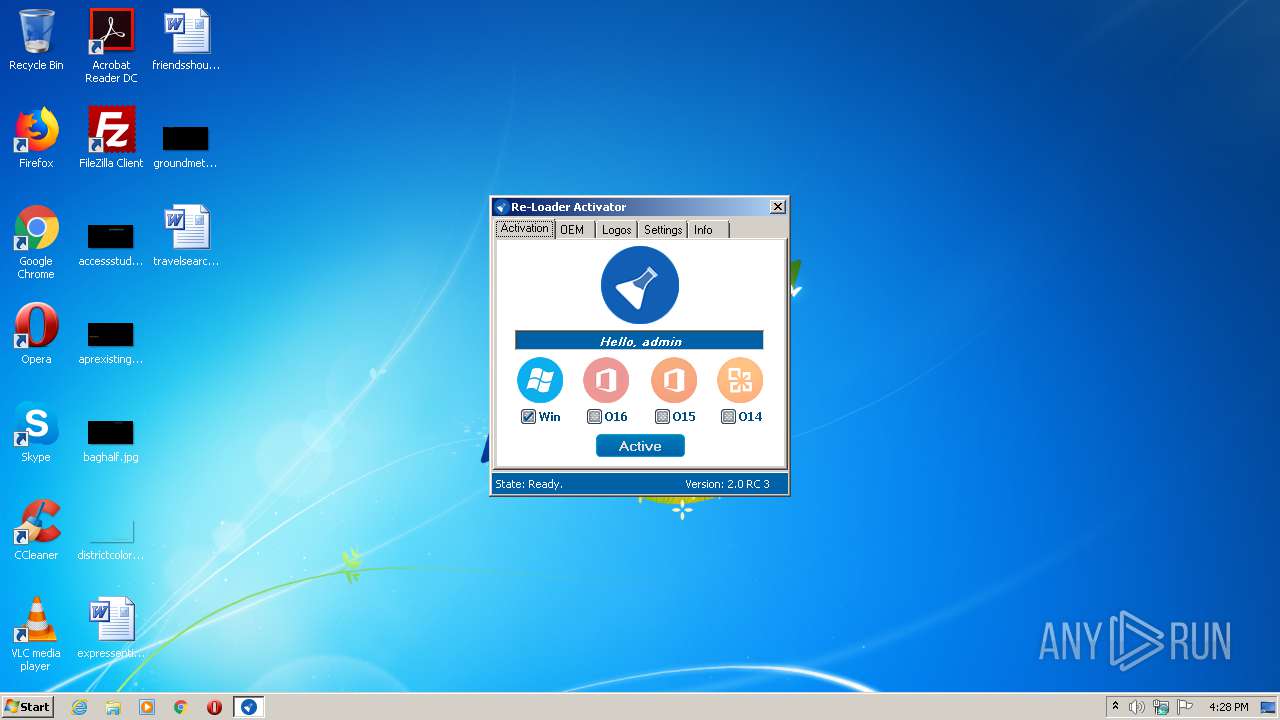
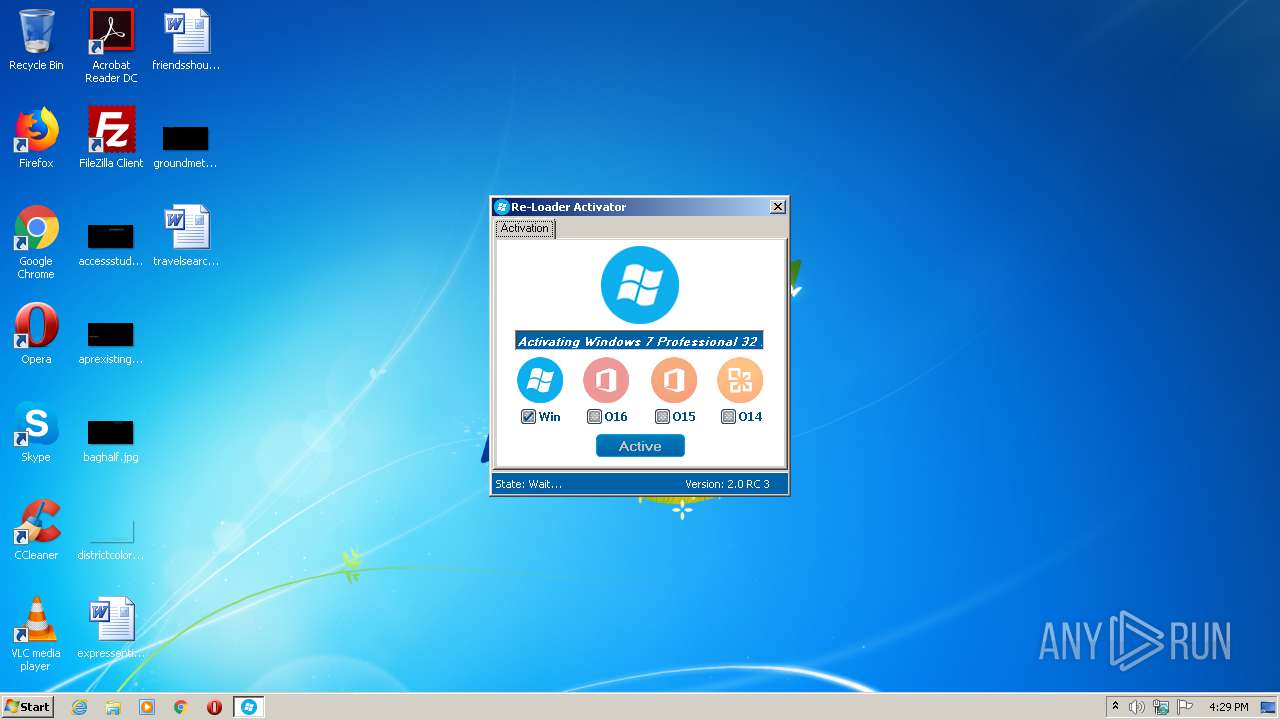
| File name: | Re-LoaderByR@1n.exe |
| Full analysis: | https://app.any.run/tasks/451e8c0b-2918-4fc5-98be-15cebdedf042 |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2020, 15:28:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | MS-DOS executable, MZ for MS-DOS |
| MD5: | 6ECDA49498C21201863980A28079B669 |
| SHA1: | 8F11D6A6B1FC3EEA545E45B410993C50AAE8C53E |
| SHA256: | 58C19F4E5C84201037CFBA23847CC9FE7D3B92C6523654343405D7E175854D67 |
| SSDEEP: | 24576:SQ1Pc1VxB0gOpnrER29UOYeZcz0xxb0V++gXgEjIIxF+XqUHFRDc13G9nwrfMB8h:SAk1V3GY29dYiczr8wCtUHM13Gxwgq |
MALICIOUS
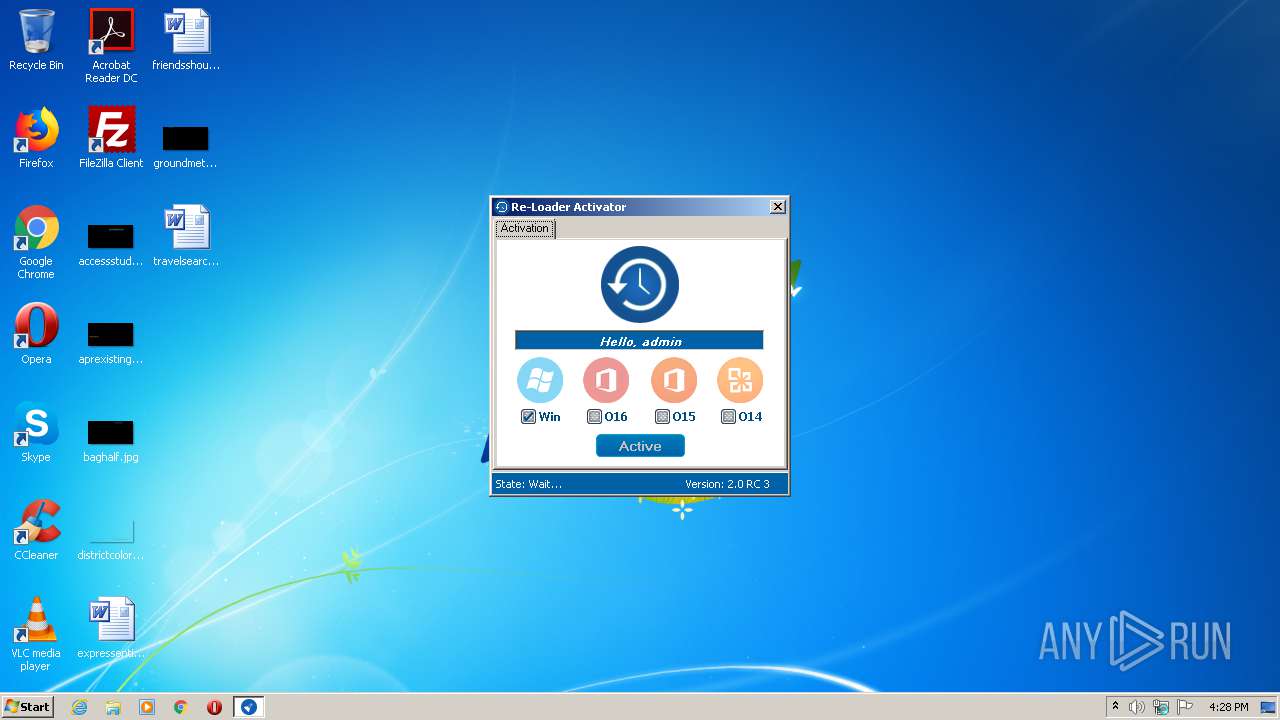
Application was dropped or rewritten from another process
- brset.exe (PID: 1640)
SUSPICIOUS
Executable content was dropped or overwritten
- Re-LoaderByR@1n.exe (PID: 2732)
Executed via COM
- DllHost.exe (PID: 3120)
Reads Environment values
- Re-LoaderByR@1n.exe (PID: 2732)
Low-level read access rights to disk partition
- brset.exe (PID: 1640)
- bootsect.exe (PID: 2676)
Executed as Windows Service
- vssvc.exe (PID: 1668)
INFO
Reads Microsoft Office registry keys
- Re-LoaderByR@1n.exe (PID: 2732)
Low-level read access rights to disk partition
- vssvc.exe (PID: 1668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:12:09 19:58:13+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 4096 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2e5e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.2.3 |
| ProductVersionNumber: | 2.0.2.3 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Activator |
| FileVersion: | 2.0.2.3 |
| InternalName: | Activator.exe |
| LegalCopyright: | Copyright © By R@1n 2015 |
| LegalTrademarks: | - |
| OriginalFileName: | Activator.exe |
| ProductName: | Re-Loader By R@1n |
| ProductVersion: | 2.0.2.3 |
| AssemblyVersion: | 2.0.2.3 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Dec-2010 18:58:13 |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Activator |
| FileVersion: | 2.0.2.3 |
| InternalName: | Activator.exe |
| LegalCopyright: | Copyright © By R@1n 2015 |
| LegalTrademarks: | - |
| OriginalFilename: | Activator.exe |
| ProductName: | Re-Loader By R@1n |
| ProductVersion: | 2.0.2.3 |
| Assembly Version: | 2.0.2.3 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0040 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0002 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0xB400 |
| OEM information: | 0xCD09 |
| Address of NE header: | 0x00000040 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 09-Dec-2010 18:58:13 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00000E64 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.26735 |
.rsrc | 0x00004000 | 0x00008FA8 | 0x00009000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.43592 |
.reloc | 0x0000E000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.49802 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00727 | 3463 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 3.8639 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.0782 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 3.60895 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.62308 | 62 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
53
Monitored processes
7
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1640 | "C:\Users\admin\AppData\Local\Temp\Re-Loader\OEM\brset.exe" /nt60 SYS /force | C:\Users\admin\AppData\Local\Temp\Re-Loader\OEM\brset.exe | — | Re-LoaderByR@1n.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Sector Manipulation Tool Exit code: 0 Version: 6.0.6001.18000 (longhorn_rtm.080118-1840) Modules
| |||||||||||||||
| 1668 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
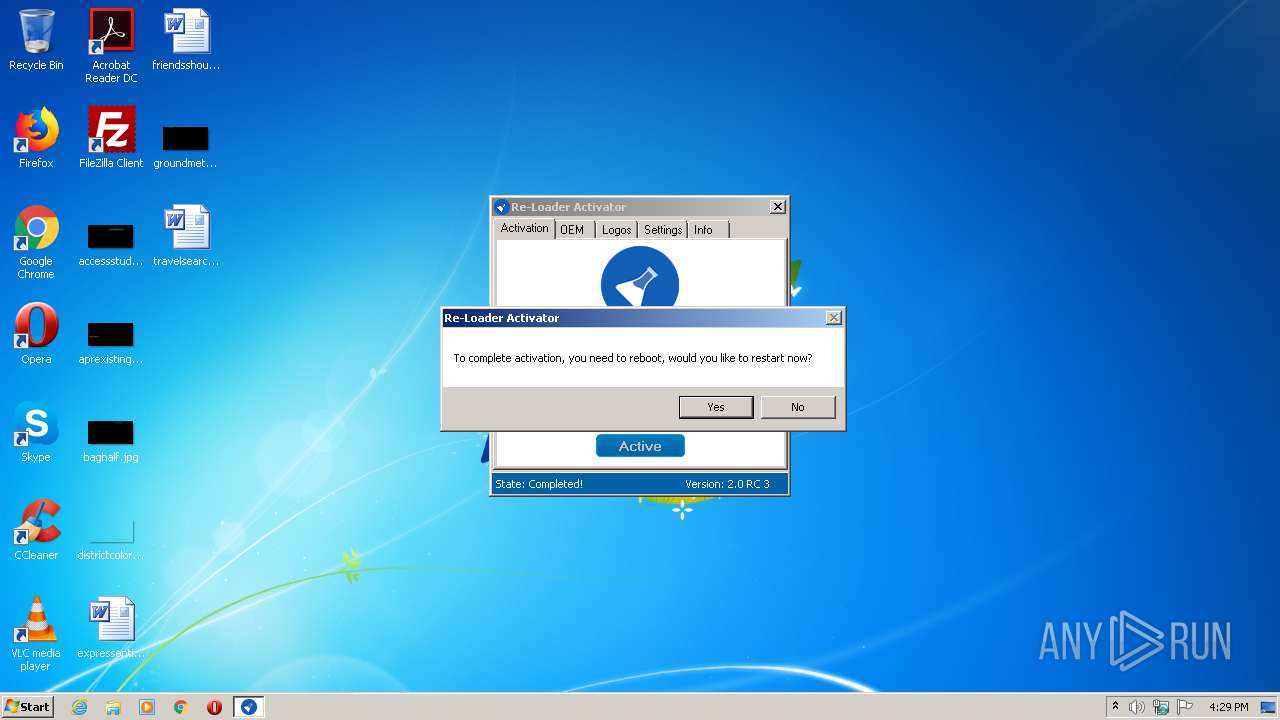
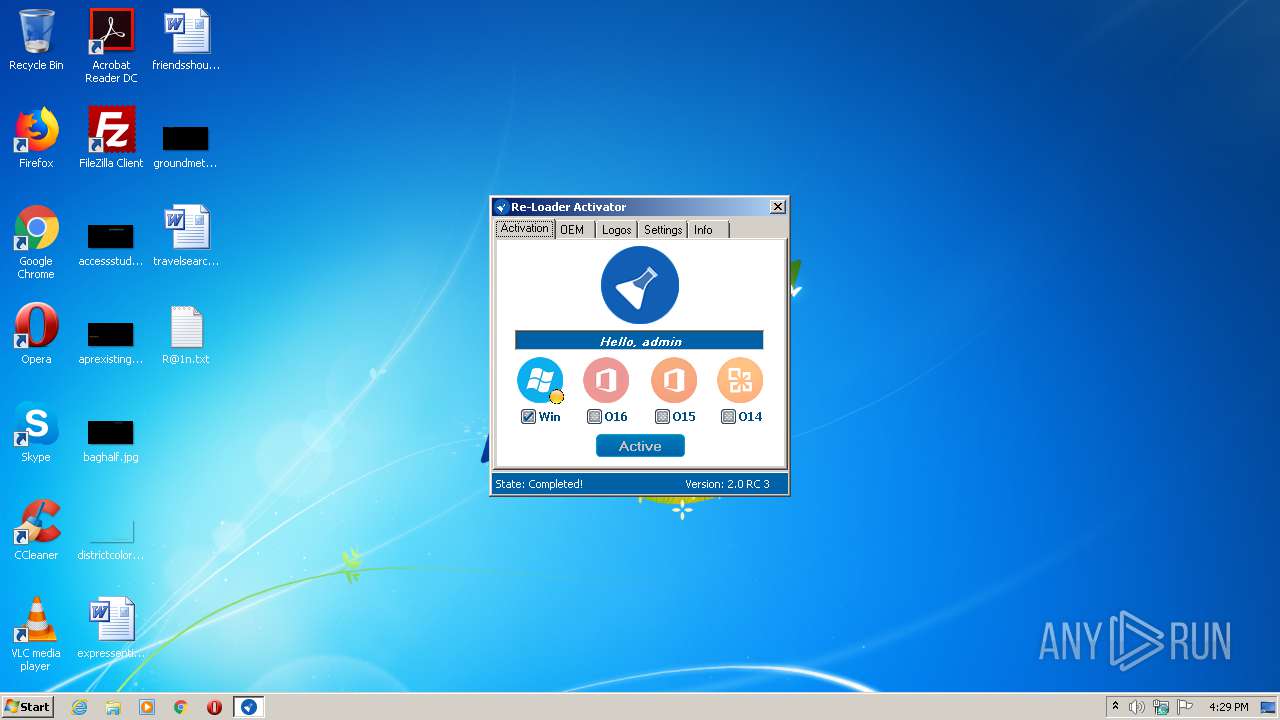
| 1764 | "C:\Windows\System32\shutdown.exe" /r /t 1 | C:\Windows\System32\shutdown.exe | — | Re-LoaderByR@1n.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1880 | "C:\Users\admin\AppData\Local\Temp\Re-LoaderByR@1n.exe" | C:\Users\admin\AppData\Local\Temp\Re-LoaderByR@1n.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Activator Exit code: 3221226540 Version: 2.0.2.3 Modules
| |||||||||||||||
| 2676 | "C:\Users\admin\AppData\Local\Temp\Re-Loader\OEM\bootsect.exe" /nt52 SYS /force | C:\Users\admin\AppData\Local\Temp\Re-Loader\OEM\bootsect.exe | — | Re-LoaderByR@1n.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Sector Manipulation Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2732 | "C:\Users\admin\AppData\Local\Temp\Re-LoaderByR@1n.exe" | C:\Users\admin\AppData\Local\Temp\Re-LoaderByR@1n.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Activator Exit code: 0 Version: 2.0.2.3 Modules
| |||||||||||||||
| 3120 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
244
Read events
106
Write events
138
Delete events
0
Modification events
| (PID) Process: | (2732) Re-LoaderByR@1n.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2732) Re-LoaderByR@1n.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3120) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 400000000000000046B4664B4E46D601300C0000A00F0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3120) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 37 | |||
| (PID) Process: | (3120) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000E061B54B4E46D601300C0000A00F0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3120) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000003AC4B74B4E46D601300C0000480F0000E80300000100000000000000000000004ECE0A9C0528314ABE69D188867295D60000000000000000 | |||
| (PID) Process: | (1668) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000B074C84B4E46D60184060000E40F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1668) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000B074C84B4E46D6018406000044090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1668) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000B074C84B4E46D60184060000280A0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1668) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000B074C84B4E46D6018406000004060000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
1
Suspicious files
3
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3120 | DllHost.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 1640 | brset.exe | \\?\Volume{e1a82db3-a9f0-11e7-b142-806e6f6e6963} | — | |
MD5:— | SHA256:— | |||
| 2732 | Re-LoaderByR@1n.exe | C:\Users\admin\AppData\Local\Temp\Re-Loader\OEM\SLIC\OVLXD | — | |
MD5:— | SHA256:— | |||
| 2732 | Re-LoaderByR@1n.exe | C:\Users\admin\AppData\Local\Temp\Re-Loader\OEM\bootsect.exe | — | |
MD5:— | SHA256:— | |||
| 2676 | bootsect.exe | \\?\Volume{e1a82db3-a9f0-11e7-b142-806e6f6e6963} | — | |
MD5:— | SHA256:— | |||
| 1668 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 3120 | DllHost.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{9c0ace4e-2805-4a31-be69-d188867295d6}_OnDiskSnapshotProp | binary | |
MD5:— | SHA256:— | |||
| 2732 | Re-LoaderByR@1n.exe | \\?\Volume{e1a82db3-a9f0-11e7-b142-806e6f6e6963}\OVLXD | binary | |
MD5:— | SHA256:— | |||
| 3120 | DllHost.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:— | SHA256:— | |||
| 2732 | Re-LoaderByR@1n.exe | C:\Users\admin\AppData\Local\Temp\Re-Loader\DEFAULT.XRM-MS | xml | |
MD5:18B1E45BF56F40C3C4BBE65831178216 | SHA256:D072A059D3ED3E75C98B85B41E4319E8D5CFAE0E0C239B62436A3AD34003AB4A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report