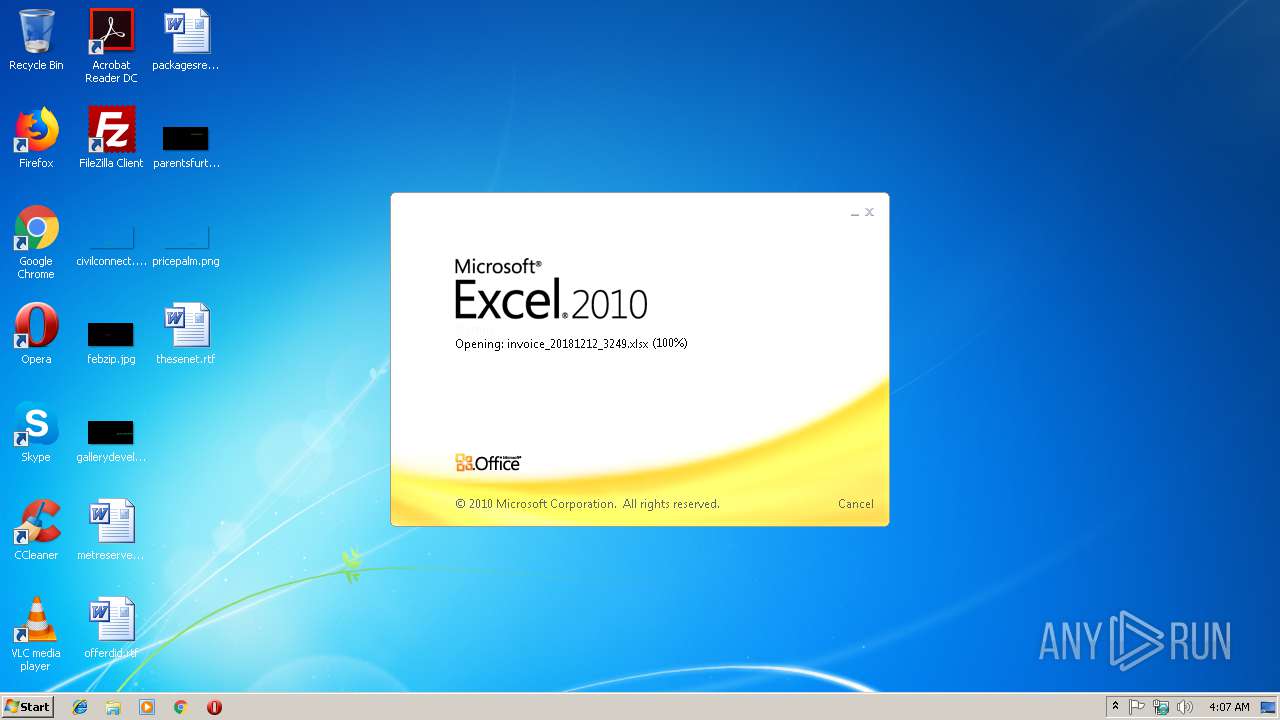
| File name: | invoice_20181212_3249.xlsx |
| Full analysis: | https://app.any.run/tasks/42ddca60-7ba2-4547-a8f0-648fe0f87303 |
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2018, 04:06:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.spreadsheetml.sheet |
| File info: | Microsoft Excel 2007+ |
| MD5: | 71E1B8D3E971ACDBF7FFDDEBFE66F499 |
| SHA1: | 0B9FF8C681FD39D7301458853F52523E2F3C9E4D |
| SHA256: | 58BB4C631DF7648CBFCAEFBD6FD1BFEA20D5EBFDB35B13041F1E0128C48DD627 |
| SSDEEP: | 192:YCoedIkThvI7kVJHRjIYIoLQTGZtAxItN8KWCJs411AMziw5:FLddm7apBIg268PCJ9A3s |
MALICIOUS
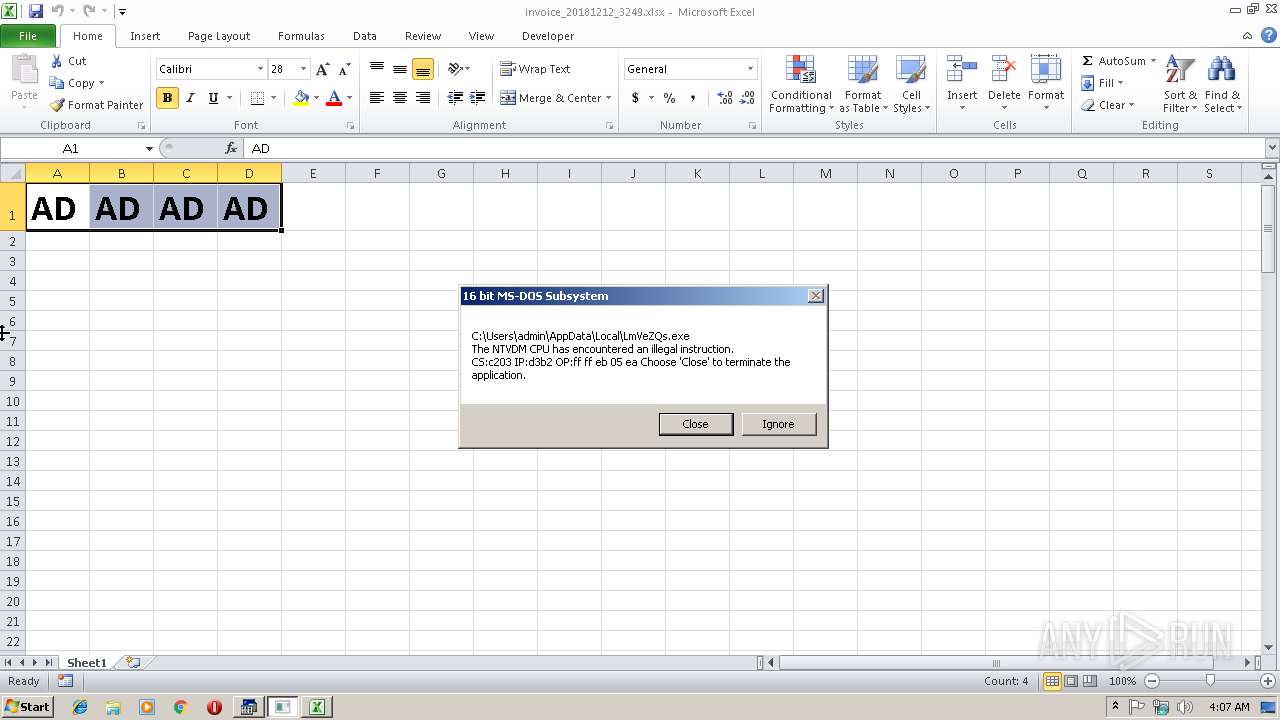
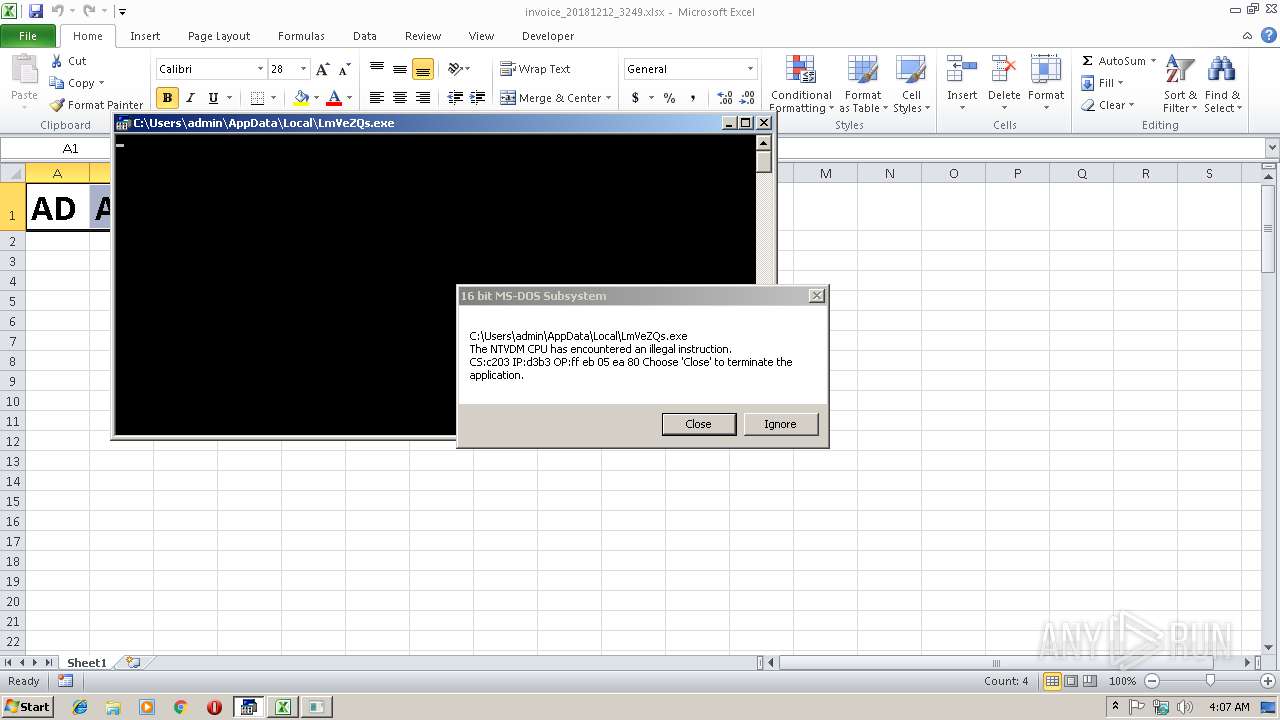
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 3264)
Suspicious connection from the Equation Editor
- EQNEDT32.EXE (PID: 3264)
SUSPICIOUS
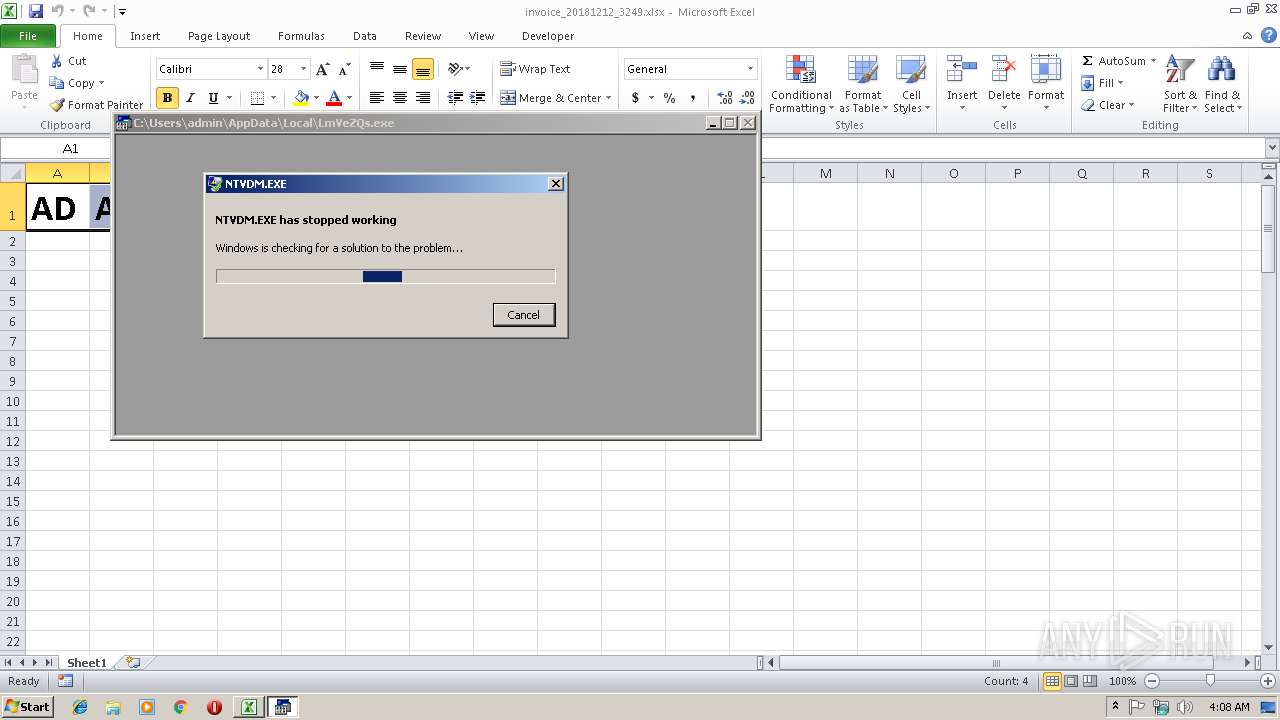
Executes application which crashes
- EQNEDT32.EXE (PID: 3264)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 3392)
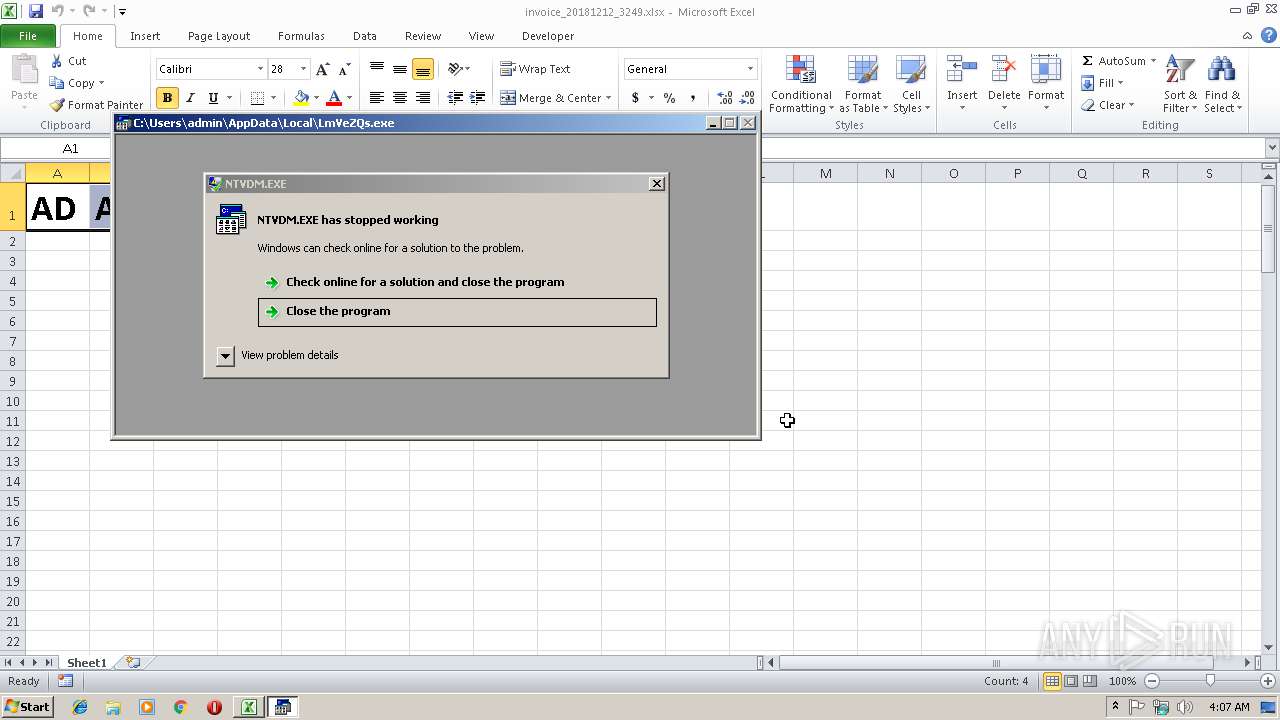
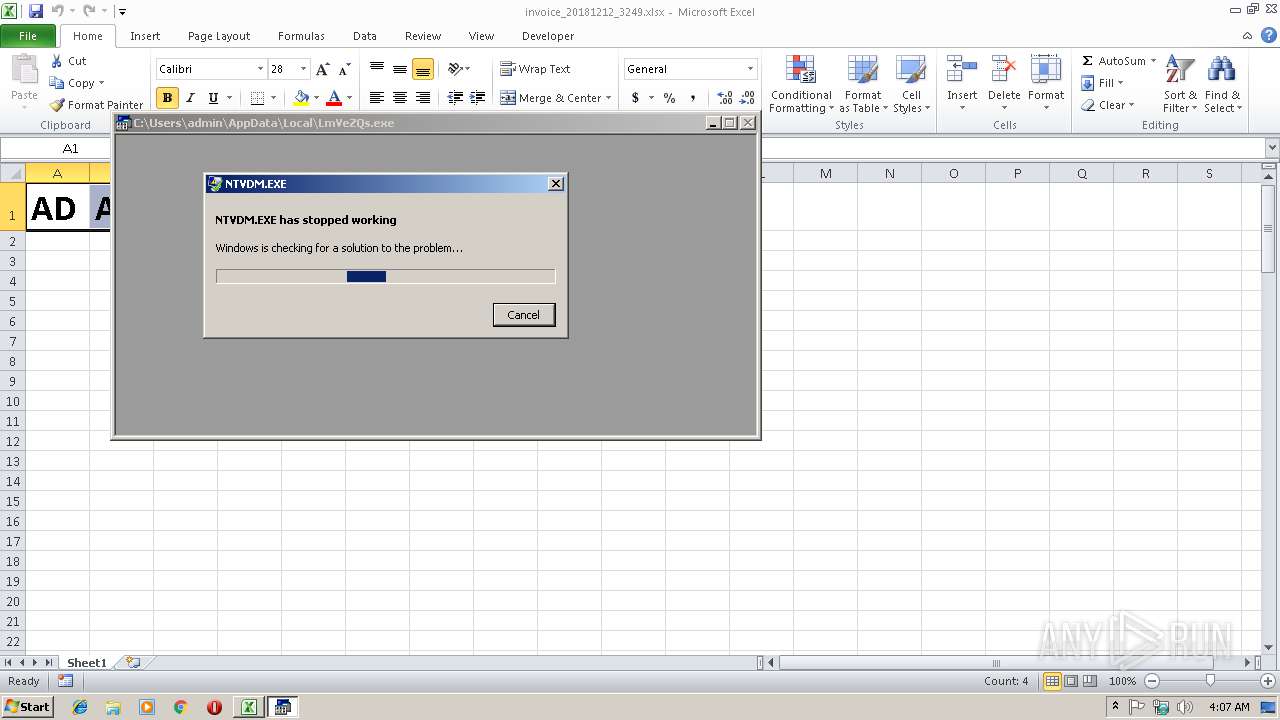
Application was crashed
- ntvdm.exe (PID: 2992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xlsx | | | Excel Microsoft Office Open XML Format document (61.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (31.5) |
| .zip | | | ZIP compressed archive (7.2) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0002 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:12:12 13:27:24 |
| ZipCRC: | 0xa97f1e42 |
| ZipCompressedSize: | 386 |
| ZipUncompressedSize: | 1505 |
| ZipFileName: | [Content_Types].xml |
XMP
| Creator: | wolek |
|---|
XML
| LastModifiedBy: | wolek |
|---|---|
| CreateDate: | 2018:12:12 13:22:29Z |
| ModifyDate: | 2018:12:12 13:24:05Z |
| Application: | Microsoft Excel |
| DocSecurity: | None |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | Sheet1 |
| Company: | - |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 15.03 |
Total processes
35
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2992 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | EQNEDT32.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 3221225477 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3264 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 3392 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
560
Read events
516
Write events
37
Delete events
7
Modification events
| (PID) Process: | (3392) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | 0h |
Value: 30682000400D0000010000000000000000000000 | |||
| (PID) Process: | (3392) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3392) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3392) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 400D0000B2ECF47C6293D40100000000 | |||
| (PID) Process: | (3392) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | 0h |
Value: 30682000400D0000010000000000000000000000 | |||
| (PID) Process: | (3392) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3392) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3392) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3392) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3392) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\13AADA |
| Operation: | write | Name: | 13AADA |
Value: 04000000400D00003C00000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C0069006E0076006F006900630065005F00320030003100380031003200310032005F0033003200340039002E0078006C0073007800000000002200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C00010000000000000070C9497E6293D401DAAA1300DAAA130000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3392 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRA480.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2992 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsB190.tmp | — | |
MD5:— | SHA256:— | |||
| 2992 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsB191.tmp | — | |
MD5:— | SHA256:— | |||
| 3264 | EQNEDT32.EXE | C:\Users\admin\AppData\Local\LmVeZQs.exe | text | |
MD5:— | SHA256:— | |||
| 3264 | EQNEDT32.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\download[1].php | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2480 | WerFault.exe | GET | — | 40.70.13.248:80 | http://watson.microsoft.com/StageOne/ntvdm_exe/6_1_7600_16385/4a5bc158/StackHash_2264/0_0_0_0/00000000/c0000005/0000ffff.htm?LCID=1033&OS=6.1.7601.2.00010100.1.0.48.17514&SM=DELL&SPN=DELL&BV=DELL&MID=3ADE2C42-4AB9-49B7-B142-BE9AEEA69063 | US | — | — | whitelisted |
3264 | EQNEDT32.EXE | GET | 200 | 101.99.84.159:80 | http://mpstationery.com/livestream/canciani/download.php?file=NjM0MzYzODI0OV9fX19wb3FlaC5leGU= | MY | text | 58 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3264 | EQNEDT32.EXE | 101.99.84.159:80 | mpstationery.com | — | MY | suspicious |
2480 | WerFault.exe | 40.70.13.248:80 | watson.microsoft.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mpstationery.com |
| malicious |
watson.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2480 | WerFault.exe | Potential Corporate Privacy Violation | ET POLICY Application Crash Report Sent to Microsoft |