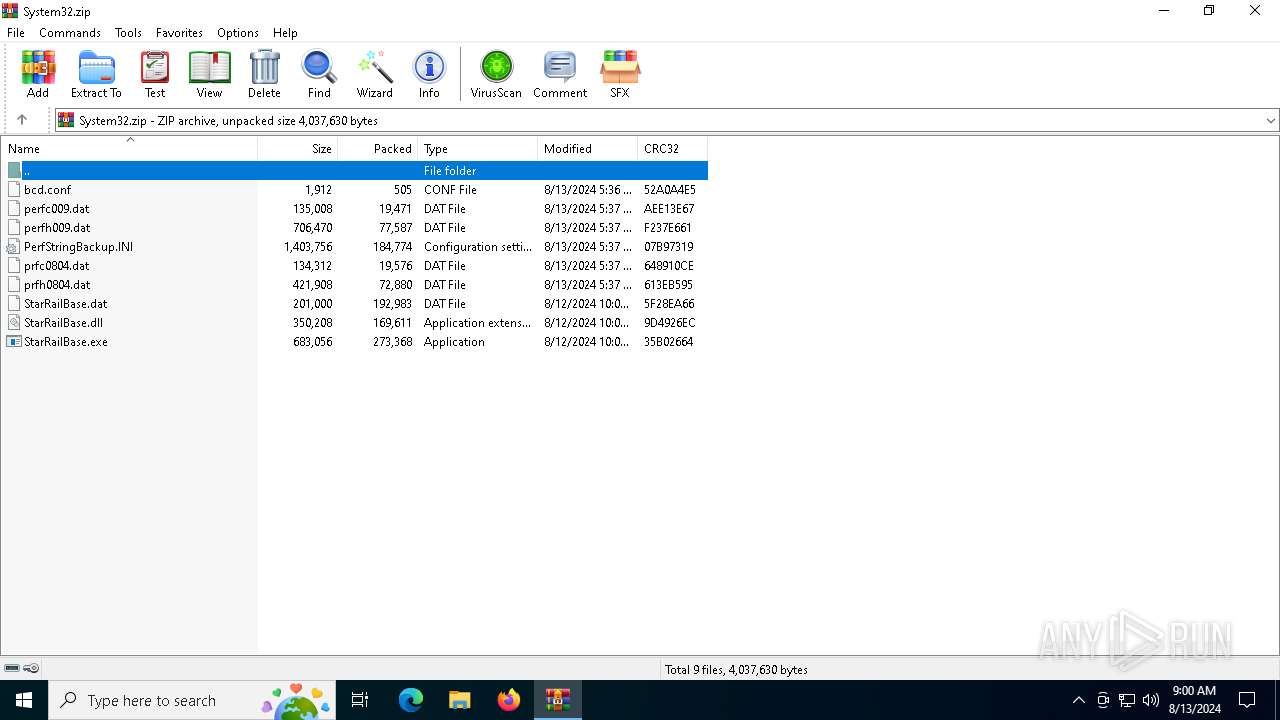
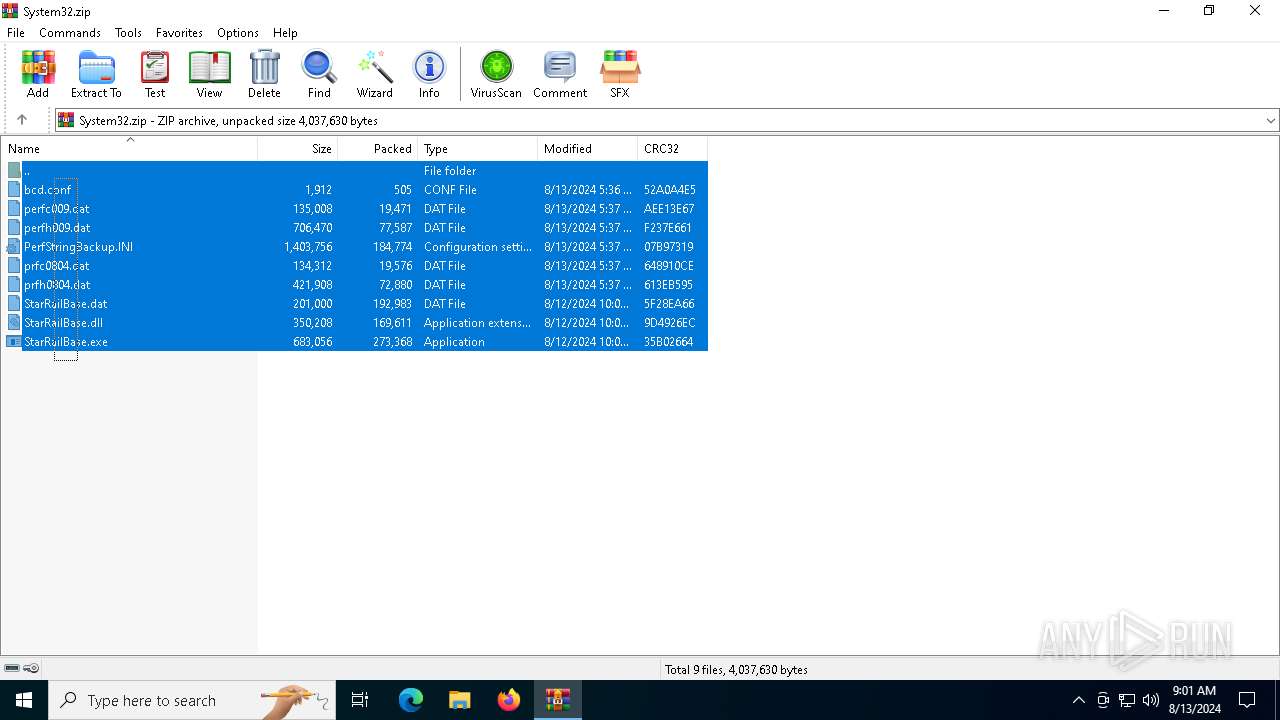
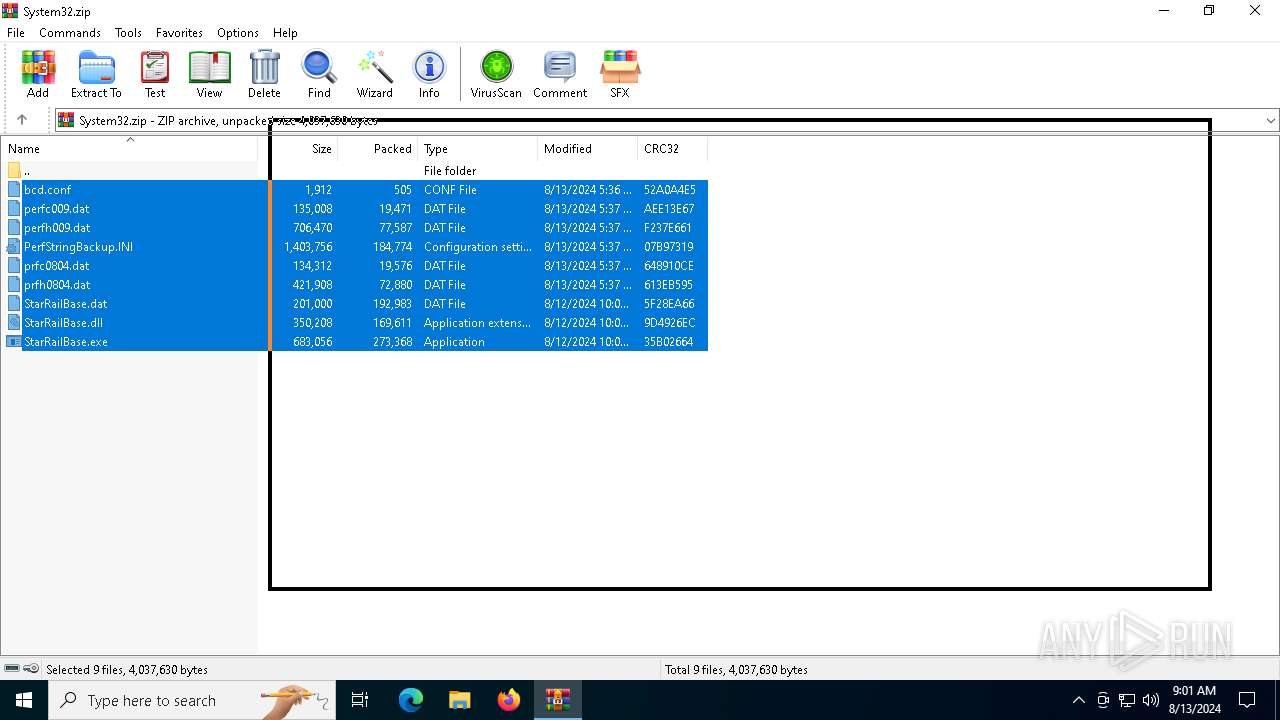
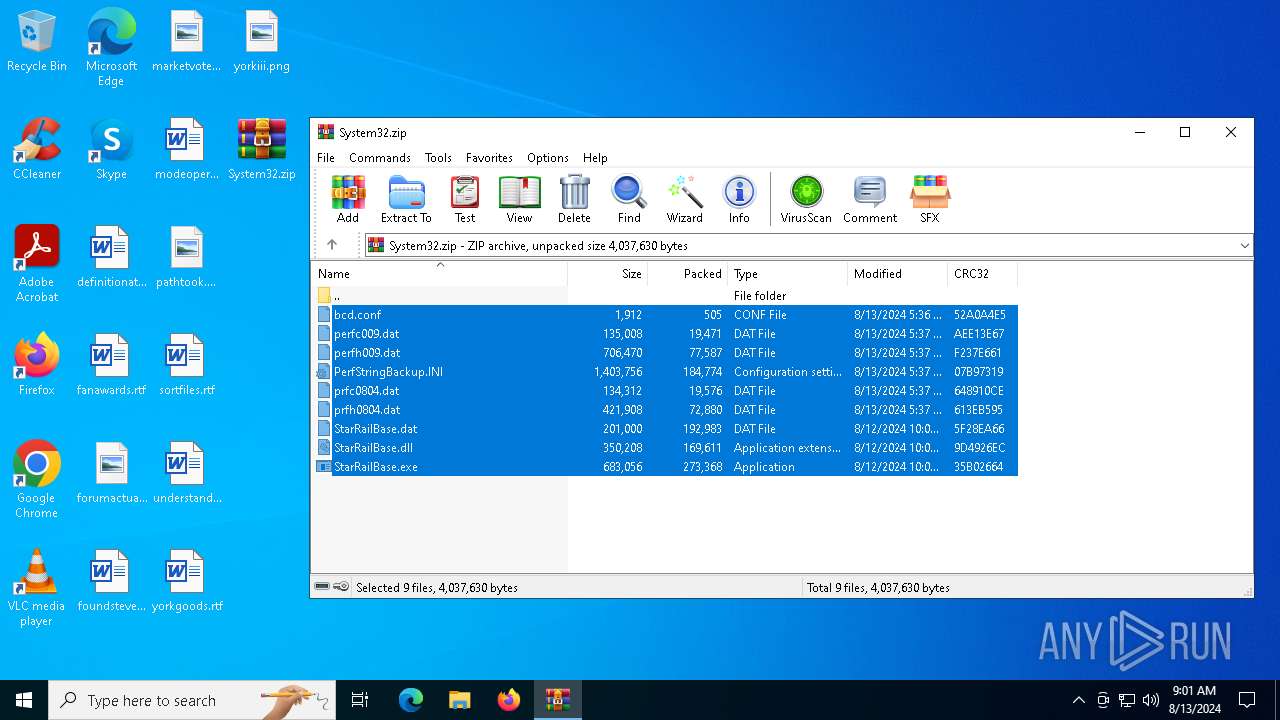
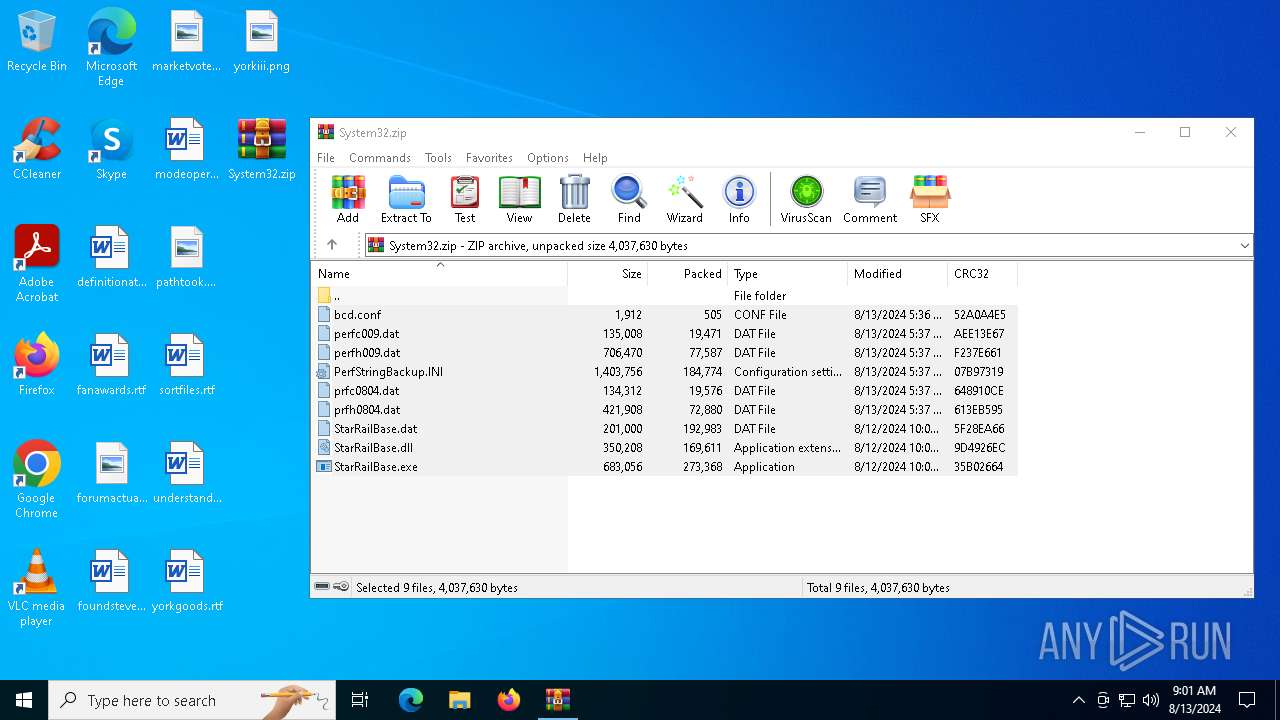
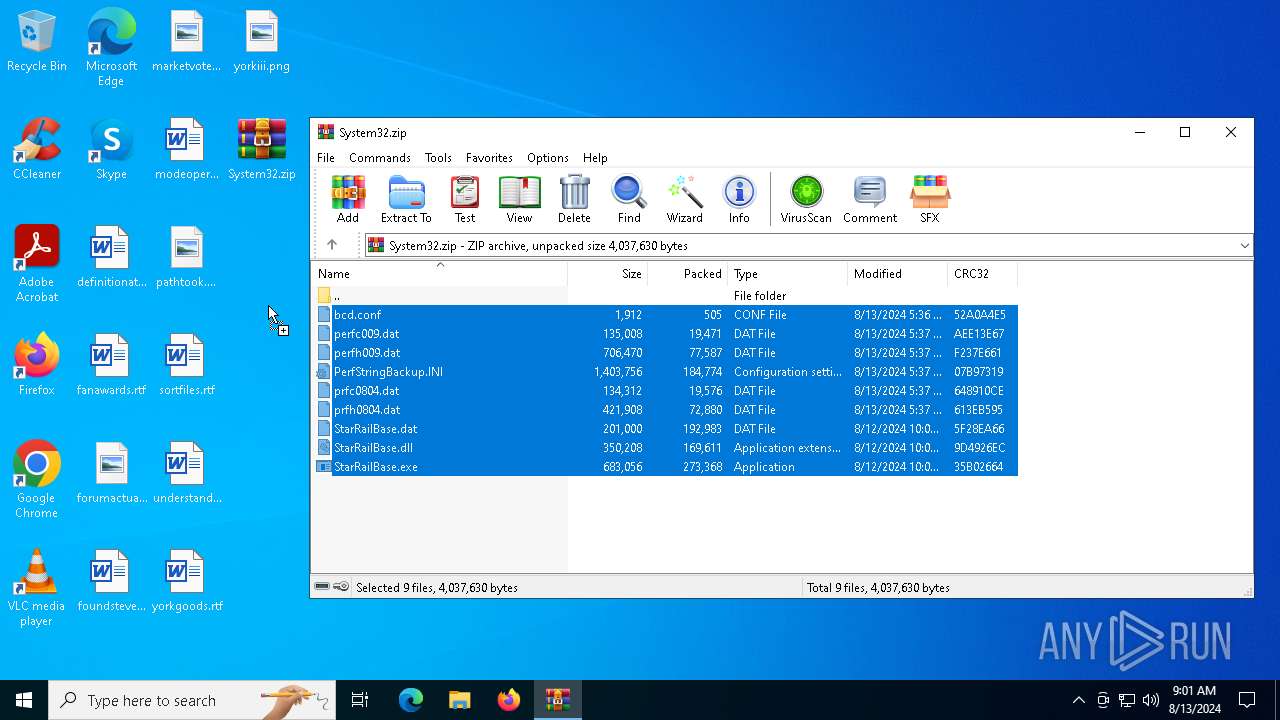
| File name: | System32.zip |
| Full analysis: | https://app.any.run/tasks/137e0533-d5bd-4b72-bc20-7217dc7144a6 |
| Verdict: | Malicious activity |
| Analysis date: | August 13, 2024, 09:00:41 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 81501582E60A1DAD472F180E85F1730E |
| SHA1: | BC5E2341C7357D60802D1B87A1DE6F377D7E04EB |
| SHA256: | 58B77BCEEC85D1E91B996443CDB42E6D2CDF5186543EE85F3B2850D57CEB5EBB |
| SSDEEP: | 49152:lZ4c5j08e6AgVBDlAqSuw6psEMXz7LrDHt4JRKNHMVM7LY4FCm84JPxrhxefoUaE:lic5pAaBDlAgdfYfXzC+HMwRhPRhxefl |
MALICIOUS
Runs injected code in another process
- StarRailBase.exe (PID: 2960)
Application was injected by another process
- svchost.exe (PID: 1316)
SUSPICIOUS
The process executes via Task Scheduler
- StarRailBase.exe (PID: 2960)
- svchost.exe (PID: 6188)
Executable content was dropped or overwritten
- svchost.exe (PID: 5372)
INFO
Reads the computer name
- StarRailBase.exe (PID: 6192)
- StarRailBase.exe (PID: 2960)
Checks supported languages
- StarRailBase.exe (PID: 6192)
- StarRailBase.exe (PID: 2960)
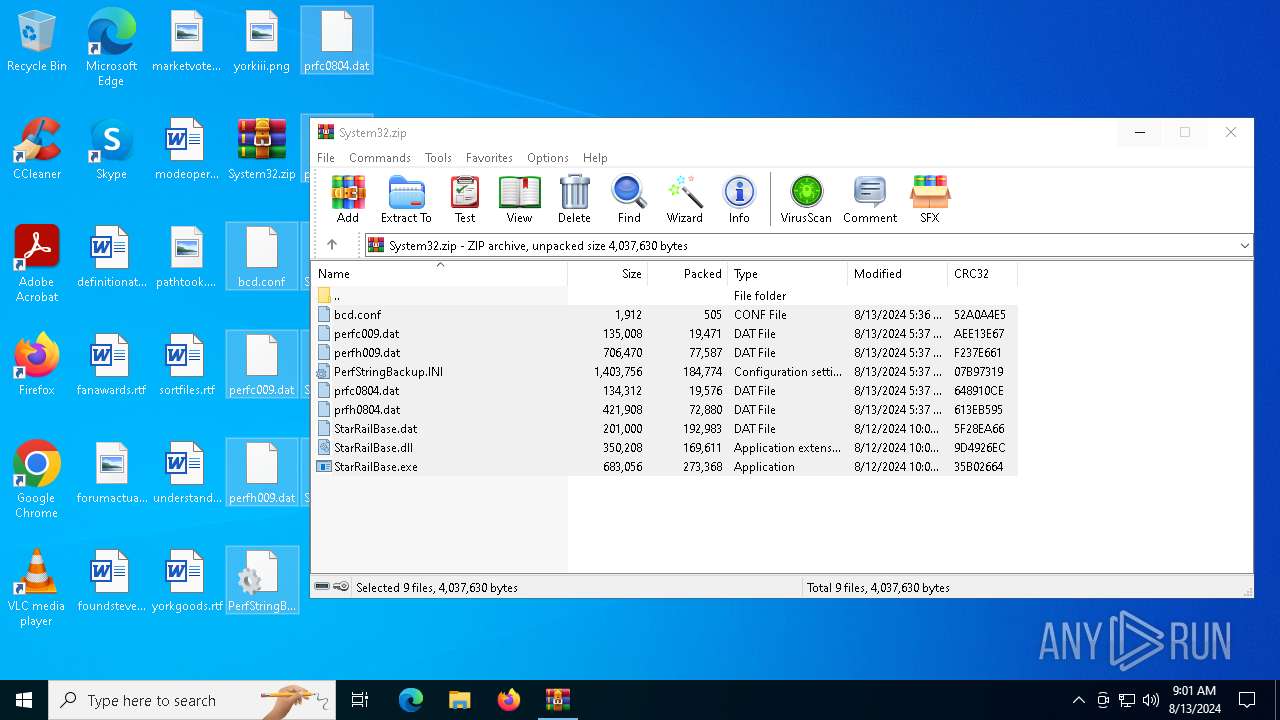
Manual execution by a user
- StarRailBase.exe (PID: 5172)
- StarRailBase.exe (PID: 6192)
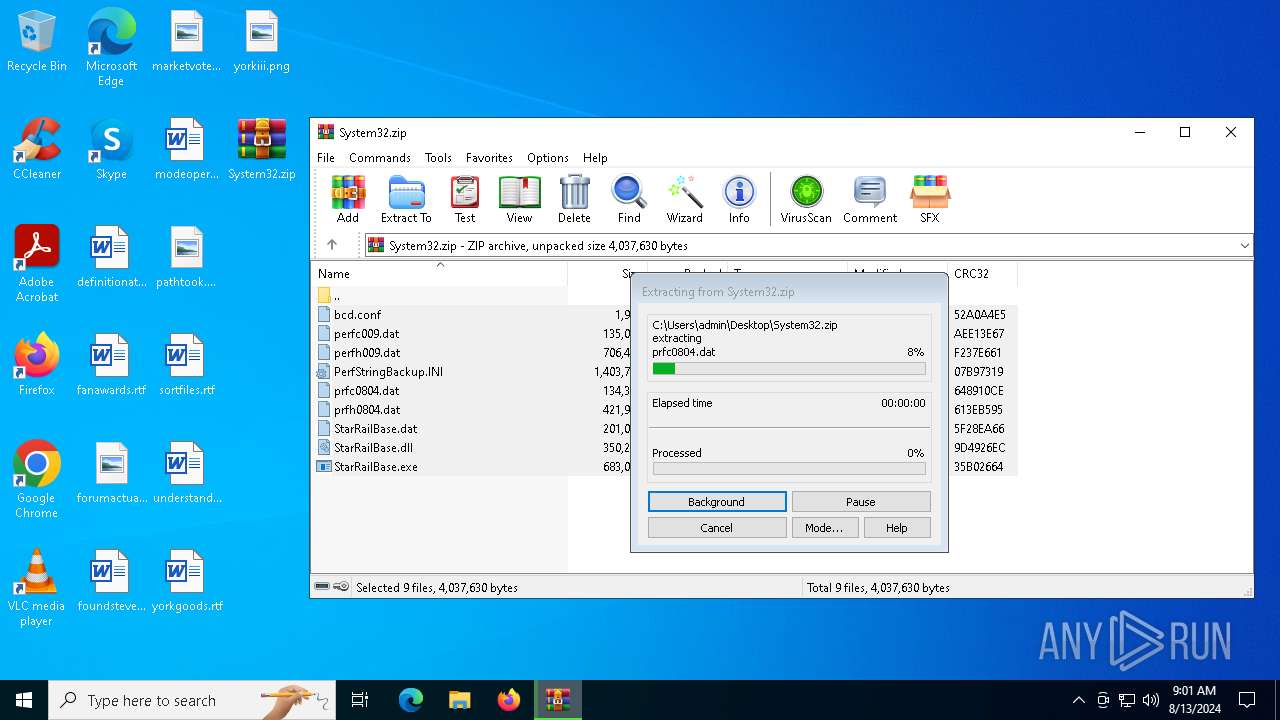
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6540)
Reads security settings of Internet Explorer
- svchost.exe (PID: 5372)
UPX packer has been detected
- dllhost.exe (PID: 6760)
- svchost.exe (PID: 6188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:08:13 13:36:18 |
| ZipCRC: | 0x52a0a4e5 |
| ZipCompressedSize: | 505 |
| ZipUncompressedSize: | 1912 |
| ZipFileName: | bcd.conf |
Total processes
143
Monitored processes
8
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1316 | C:\WINDOWS\system32\svchost.exe -k netsvcs -p -s Schedule | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2960 | "C:\WINDOWS\system32\StarRailBase.exe" -svc | C:\Windows\System32\StarRailBase.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: 上海米哈游网络科技股份有限公司 Integrity Level: SYSTEM Description: Star Rail Exit code: 0 Version: 2019.4.34.1463972 Modules
| |||||||||||||||
| 5172 | "C:\Users\admin\Desktop\StarRailBase.exe" | C:\Users\admin\Desktop\StarRailBase.exe | — | explorer.exe | |||||||||||
User: admin Company: 上海米哈游网络科技股份有限公司 Integrity Level: MEDIUM Description: Star Rail Exit code: 3221226540 Version: 2019.4.34.1463972 Modules
| |||||||||||||||
| 5372 | C:\WINDOWS\system32\svchost.exe -Install | C:\Windows\System32\svchost.exe | StarRailBase.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Host Process for Windows Services Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6188 | C:\WINDOWS\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6192 | "C:\Users\admin\Desktop\StarRailBase.exe" | C:\Users\admin\Desktop\StarRailBase.exe | explorer.exe | ||||||||||||
User: admin Company: 上海米哈游网络科技股份有限公司 Integrity Level: HIGH Description: Star Rail Exit code: 0 Version: 2019.4.34.1463972 Modules
| |||||||||||||||
| 6540 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\System32.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6760 | C:\WINDOWS\system32\dllhost.exe /Processid:{F8284233-48F4-4680-ADDD-F8284233} | C:\Windows\System32\dllhost.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: COM Surrogate Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 336
Read events
7 149
Write events
107
Delete events
80
Modification events
| (PID) Process: | (1316) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tasks\{4671B5C1-A383-4428-A45A-8D348E4CB873} |
| Operation: | write | Name: | DynamicInfo |
Value: 030000009F7DFD23AAB7D8014AA7034A5FEDDA0100000000000000006D74554C5FEDDA01 | |||
| (PID) Process: | (1316) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tasks\{C2AF3602-9179-4BAE-85B3-74A4EF5CF51F} |
| Operation: | write | Name: | DynamicInfo |
Value: 03000000BDCB09F80A59DA0143BF164A5FEDDA0100000000000000000102884E5FEDDA01 | |||
| (PID) Process: | (6540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\System32.zip | |||
| (PID) Process: | (6540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
4
Suspicious files
7
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6540 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6540.48839\perfc009.dat | binary | |
MD5:B9110FA37E4201AEA490E485659A3264 | SHA256:6E896FF7EEE8D9EDE7606DD1EF7C20CF8AA2B211B7BFB0A03057861DFD50A646 | |||
| 5372 | svchost.exe | C:\Windows\System32\StarRailBase.dat | binary | |
MD5:D95A5AB222BB990F0526EB7CBAC469D6 | SHA256:F514C1554837F67CC92AFE952DB86202F25B3AF47F7B70B1AE9CA0B09F0D4686 | |||
| 6540 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6540.48839\StarRailBase.exe | executable | |
MD5:09CBEBE3306F81DBB1498E2C214B897D | SHA256:2AA3366883B707C1FEA777156417F4BE0B5C90F209FDA1AFAC1C8544ACAB702C | |||
| 6540 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6540.48839\StarRailBase.dat | binary | |
MD5:D95A5AB222BB990F0526EB7CBAC469D6 | SHA256:F514C1554837F67CC92AFE952DB86202F25B3AF47F7B70B1AE9CA0B09F0D4686 | |||
| 1316 | svchost.exe | C:\Windows\System32\Tasks\Microsoft\Windows\WindowsUpdate\RUXIM\PLUGScheduler | xml | |
MD5:1E0FD17505DF7FDD52708C59FCD5284C | SHA256:B374CE865F05A467798DE01B77F9AEEA861325CF274390D4C06753E77CDA564D | |||
| 6540 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6540.48839\prfh0804.dat | binary | |
MD5:1F60142B2EC52E25A1E997AC3FB12E83 | SHA256:0A6A8B5FB743DD8B414C035B29850943A45BE1659CF4AE8CF4C26CA84F8F2CAA | |||
| 6540 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6540.48839\perfh009.dat | binary | |
MD5:E13FD884C7657275D86A0CC09772A20A | SHA256:B2E14C98949C6011B5E95C0FEA32167A5D44A0432F5EB9CF0ED2F9FCC0CF099F | |||
| 6540 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6540.48839\prfc0804.dat | binary | |
MD5:8F59C94B33DF4A34B0D9F6EB2A958D1C | SHA256:7FCD2C036A50462AD3C7C05DB6862D6EE8F138160B5847D5C492485E72B1676B | |||
| 6540 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6540.48839\PerfStringBackup.INI | binary | |
MD5:587BE8DB8A4326FA40E6085C71106F4C | SHA256:D7310CDACA1DFEA5817171B2883A0017C7F6CE10B9C49327C34C85F8B6E9F283 | |||
| 5372 | svchost.exe | C:\Windows\System32\StarRailBase.exe | executable | |
MD5:09CBEBE3306F81DBB1498E2C214B897D | SHA256:2AA3366883B707C1FEA777156417F4BE0B5C90F209FDA1AFAC1C8544ACAB702C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
49
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5552 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5552 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7004 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
7060 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
1108 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6080 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5336 | SearchApp.exe | 13.107.21.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3260 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5552 | svchost.exe | 20.190.144.136:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | KR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |