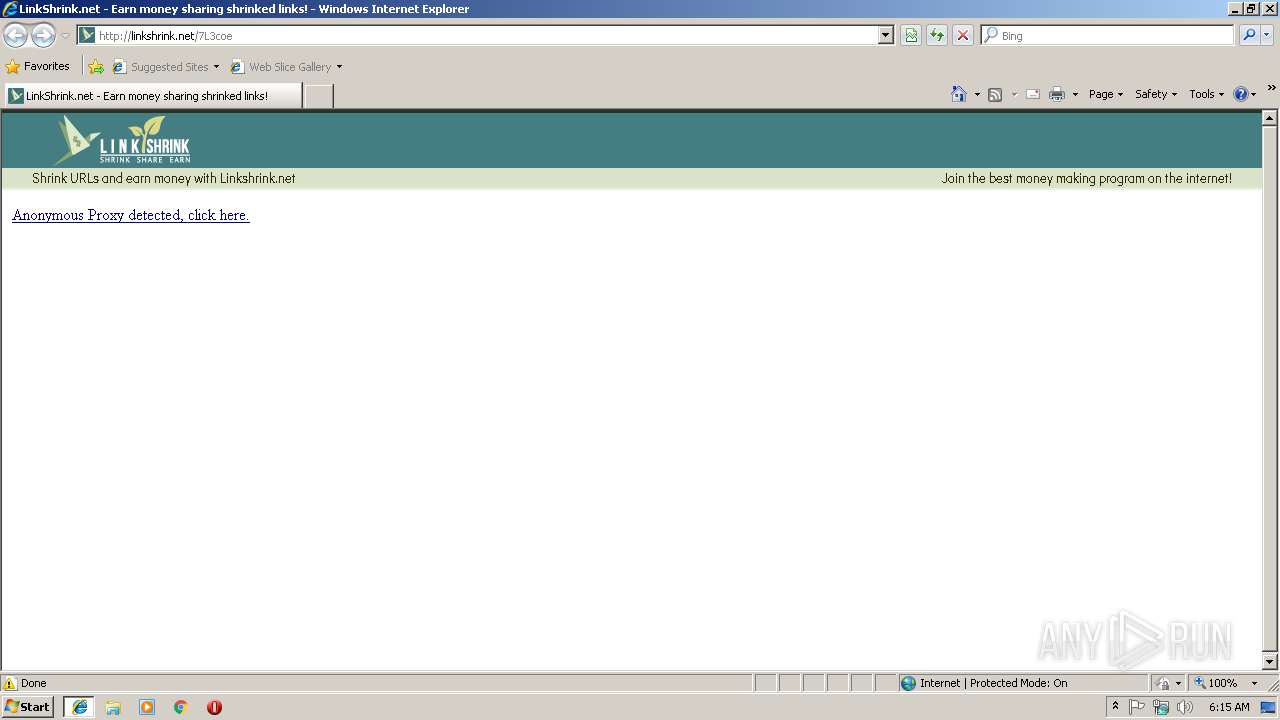
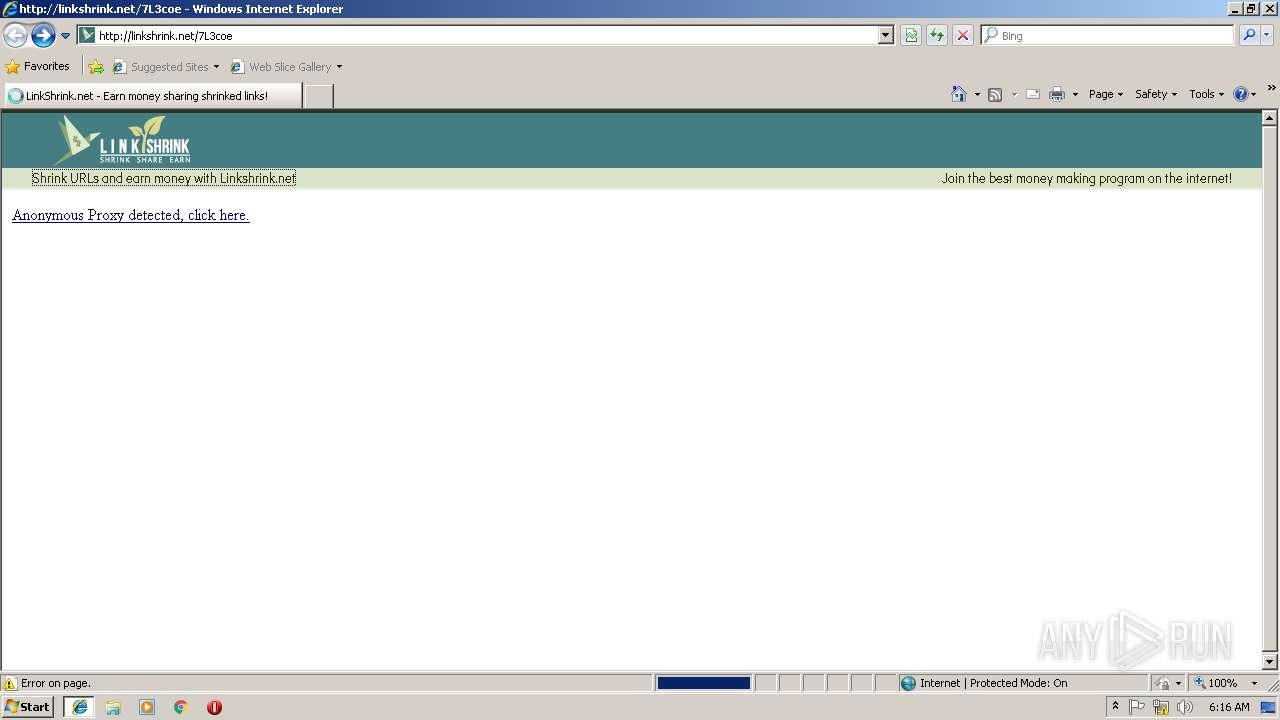
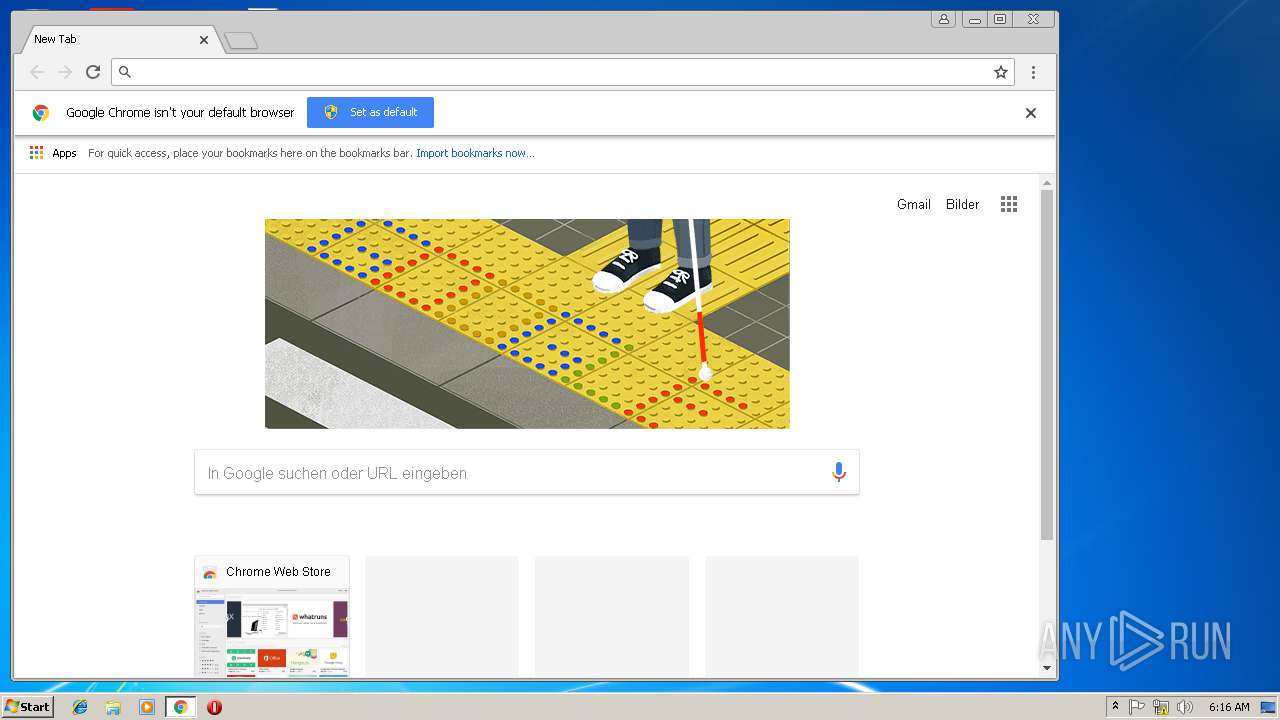
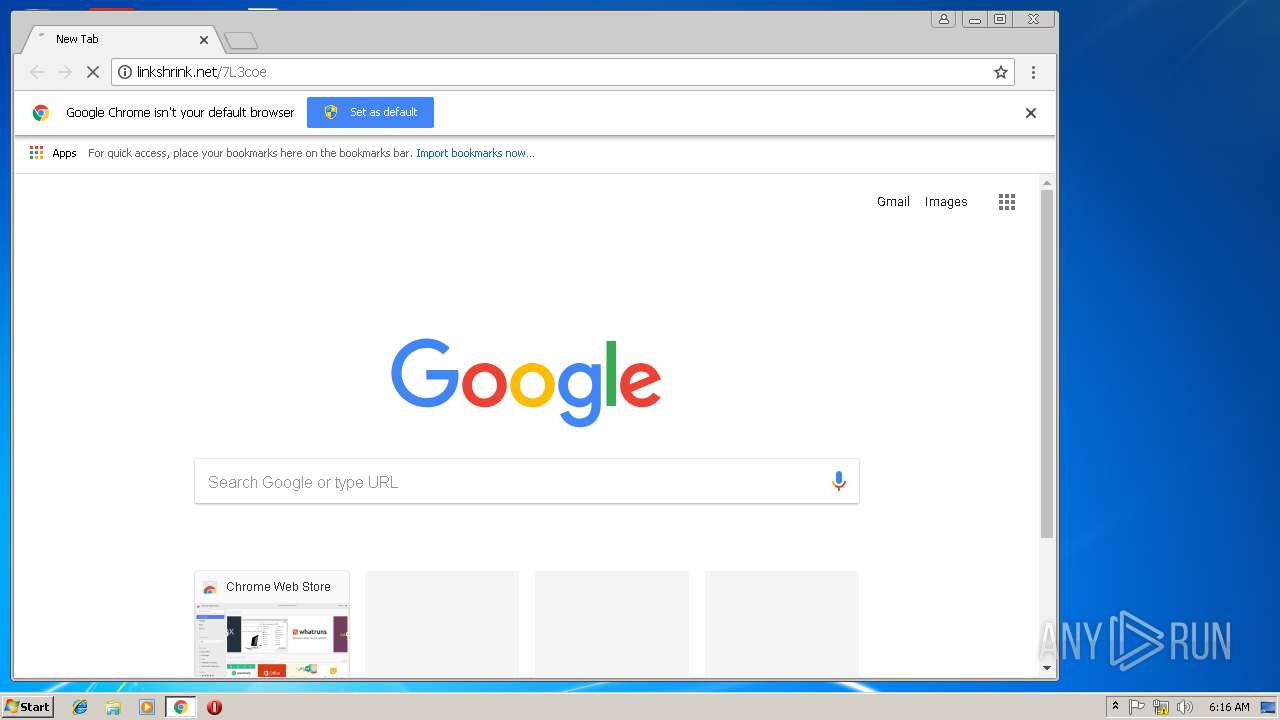
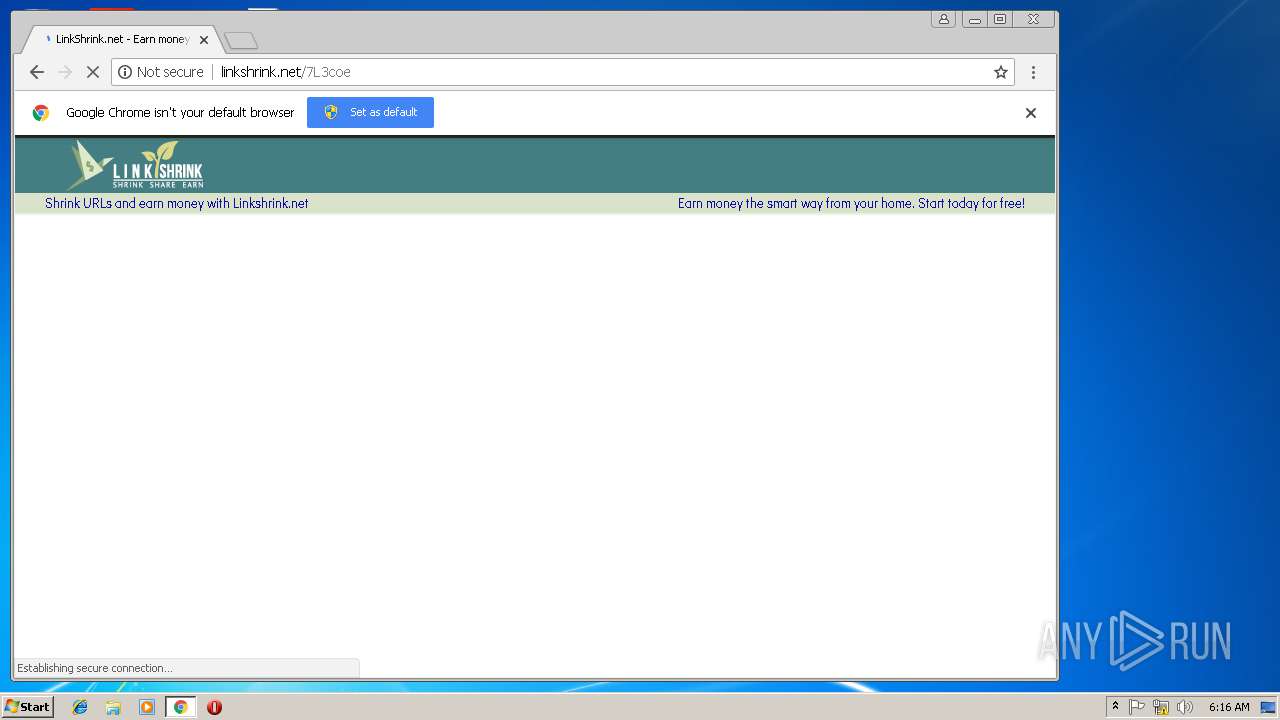
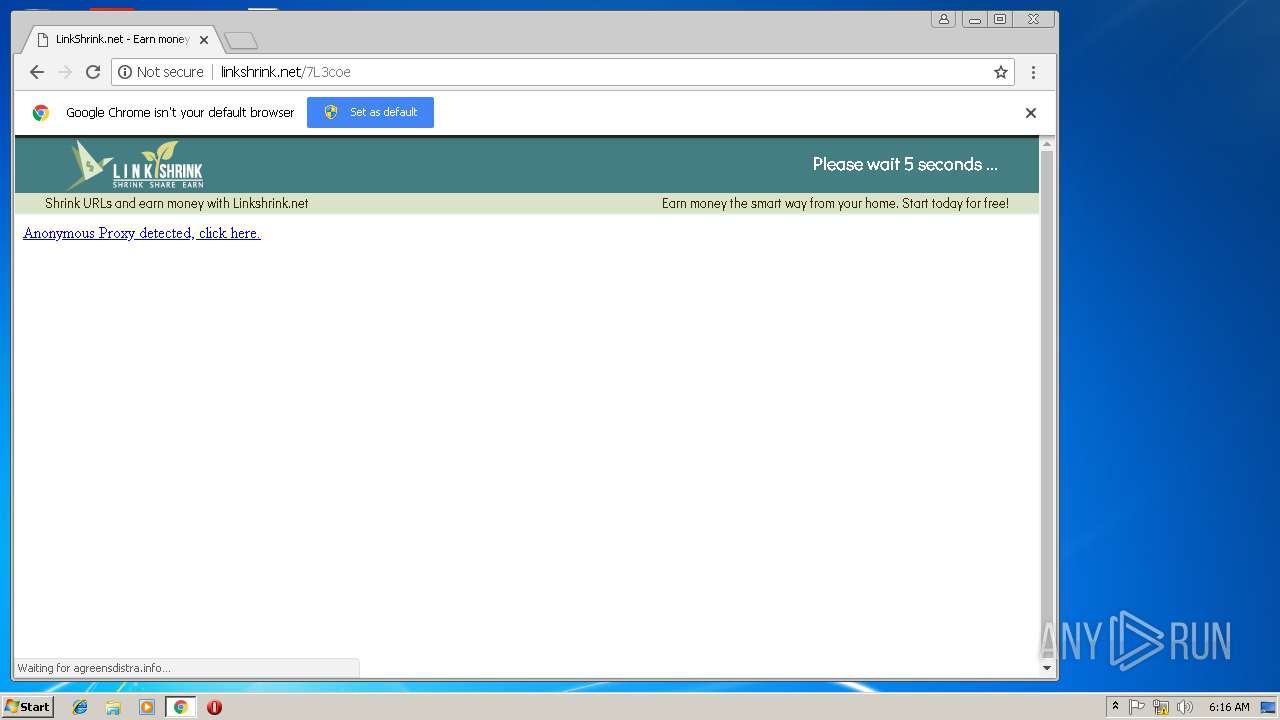
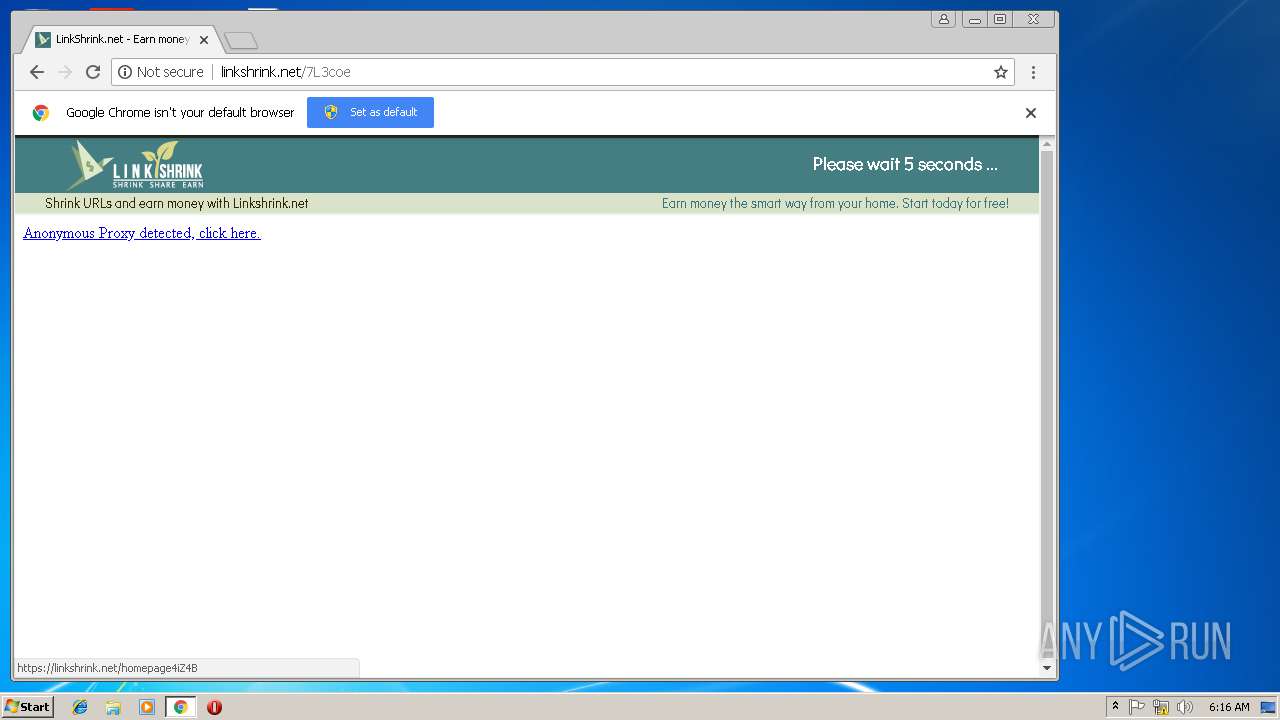
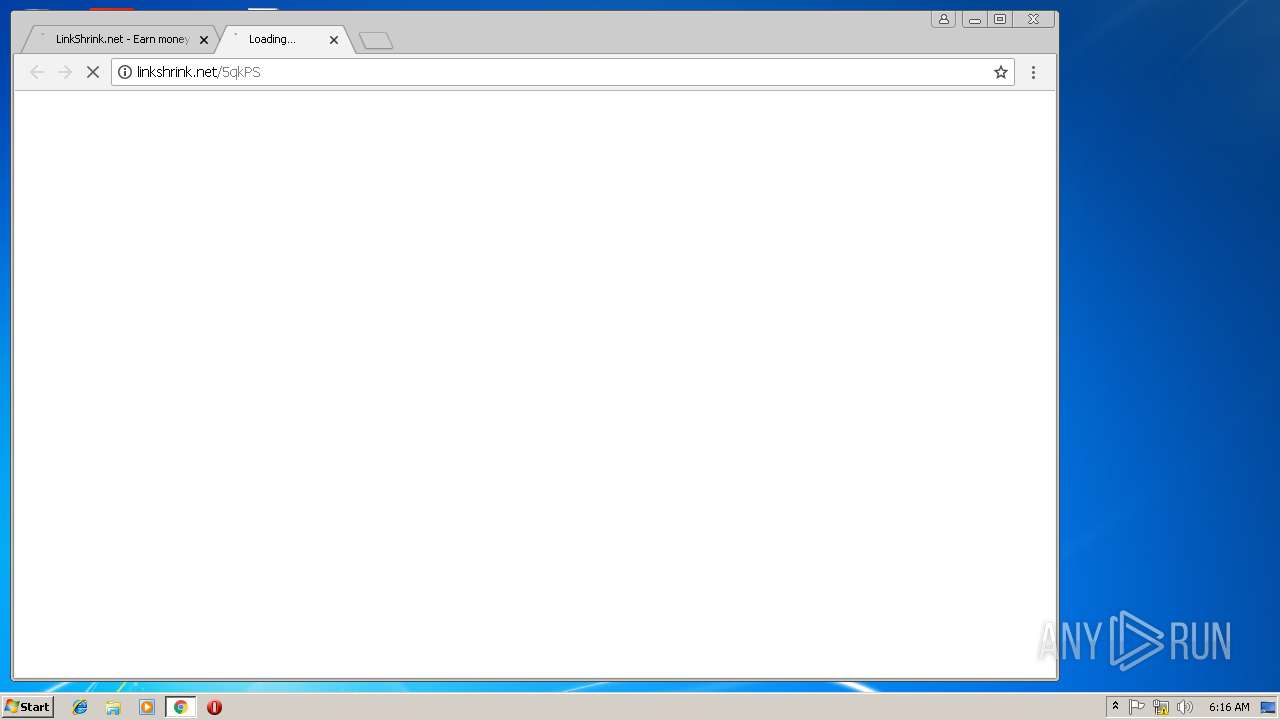
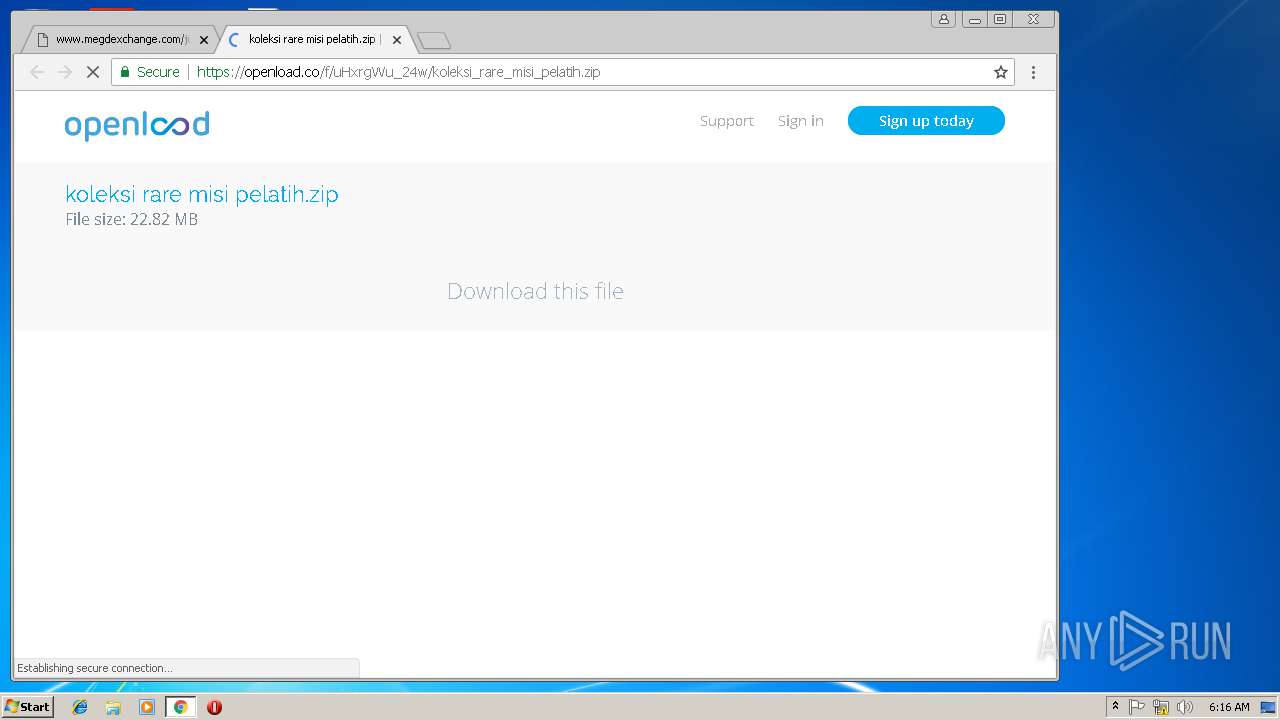
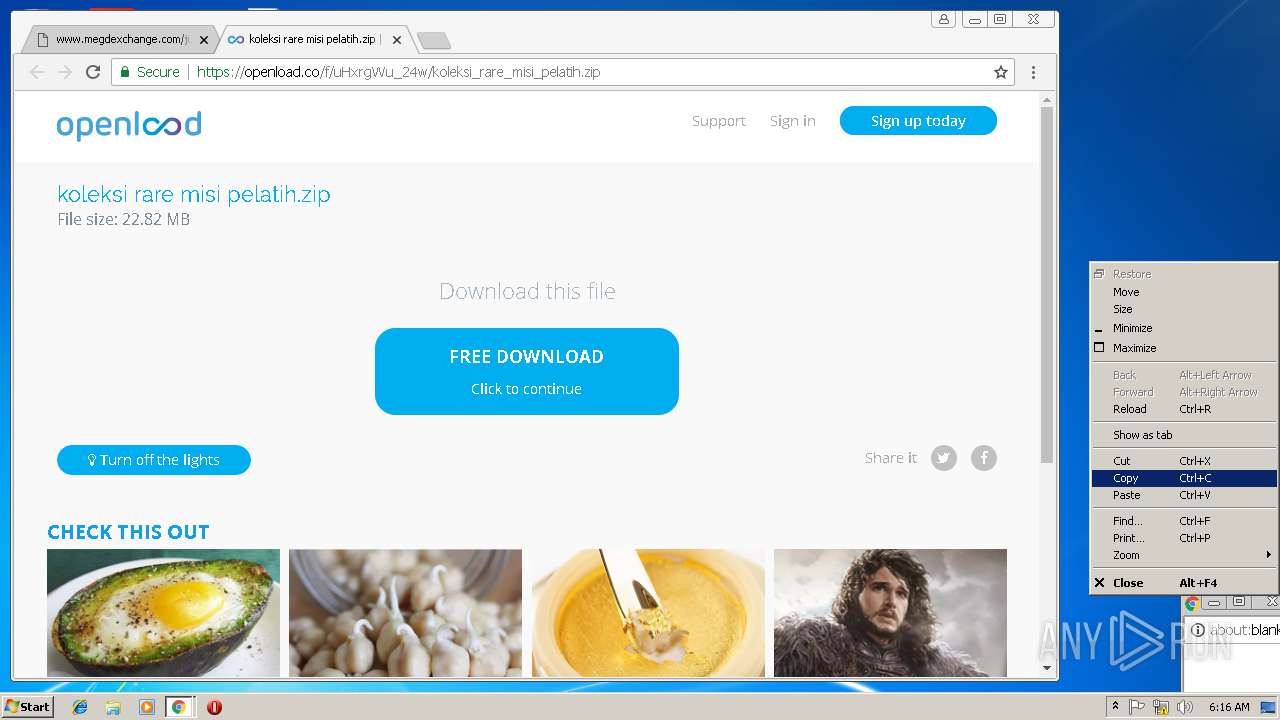
| URL: | http://linkshrink.net/7L3coe |
| Full analysis: | https://app.any.run/tasks/28169077-b02c-465b-807f-c09a92369c27 |
| Verdict: | Malicious activity |
| Analysis date: | March 18, 2019, 06:14:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 30502CD8B5B2FBA46D8863EEB1B3DD8F |
| SHA1: | 9FC0E01409BE45BDEABCEDA3C58E37B796B8BF65 |
| SHA256: | 58AD30406250BA695A0BB584349180559A29CD7F18A2B7C1CC55031AC5B701A8 |
| SSDEEP: | 3:N1KSMPKDRR:CS7RR |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
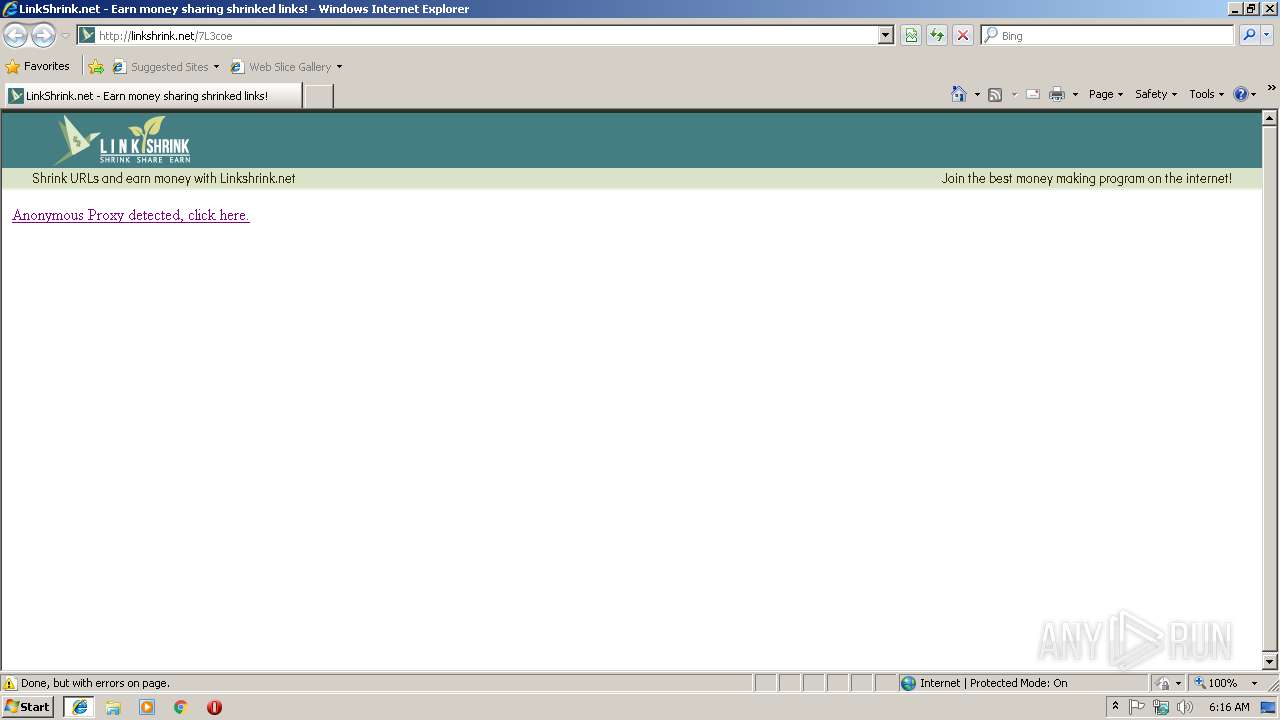
Changes internet zones settings
- iexplore.exe (PID: 2812)
Reads settings of System Certificates
- iexplore.exe (PID: 2812)
- iexplore.exe (PID: 3092)
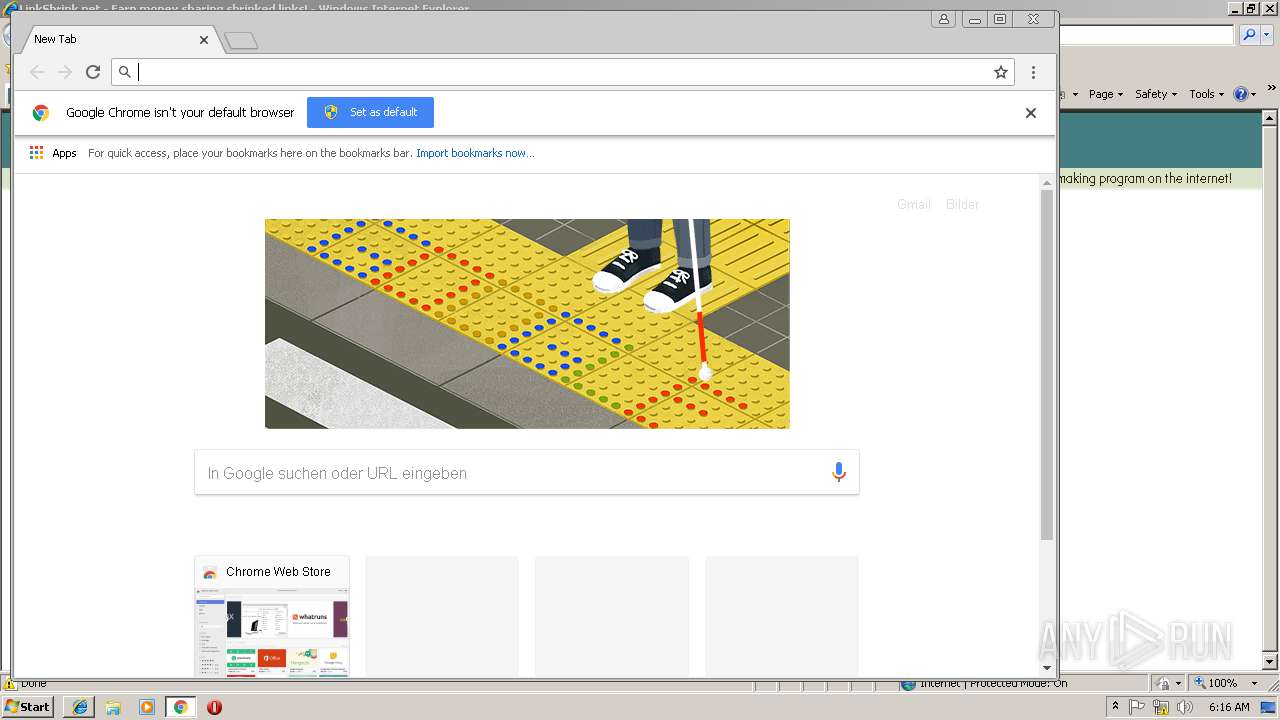
- chrome.exe (PID: 3712)
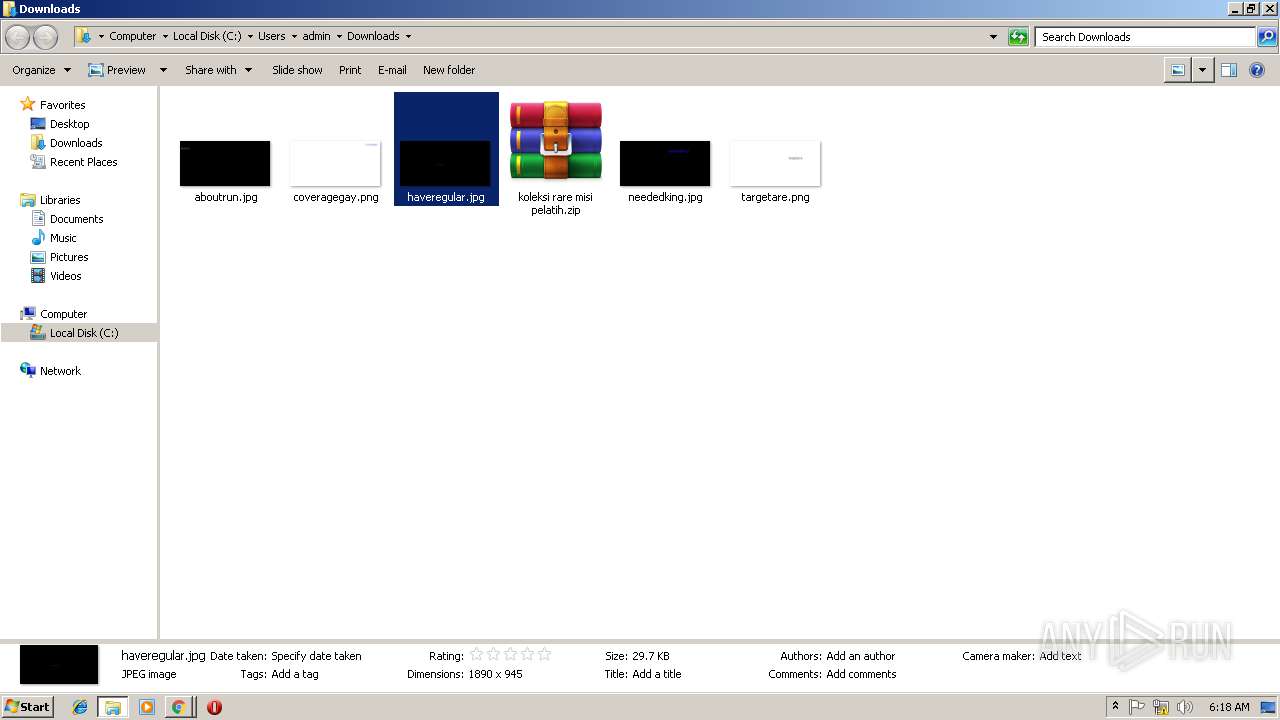
Creates files in the user directory
- iexplore.exe (PID: 3092)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 1488)
- iexplore.exe (PID: 2812)
- chrome.exe (PID: 3712)
Reads internet explorer settings
- iexplore.exe (PID: 3424)
- iexplore.exe (PID: 3092)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2812)
Reads Internet Cache Settings
- iexplore.exe (PID: 3092)
- iexplore.exe (PID: 2812)
- iexplore.exe (PID: 3424)
- chrome.exe (PID: 3712)
Changes settings of System certificates
- iexplore.exe (PID: 2812)
- chrome.exe (PID: 3712)
Application launched itself
- chrome.exe (PID: 3712)
- iexplore.exe (PID: 2812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
60
Monitored processes
22
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1488 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 2292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,15696185992708961327,5947440284735830169,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7A4D40447135A4EAFEC5727C54FB8BFC --mojo-platform-channel-handle=3392 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
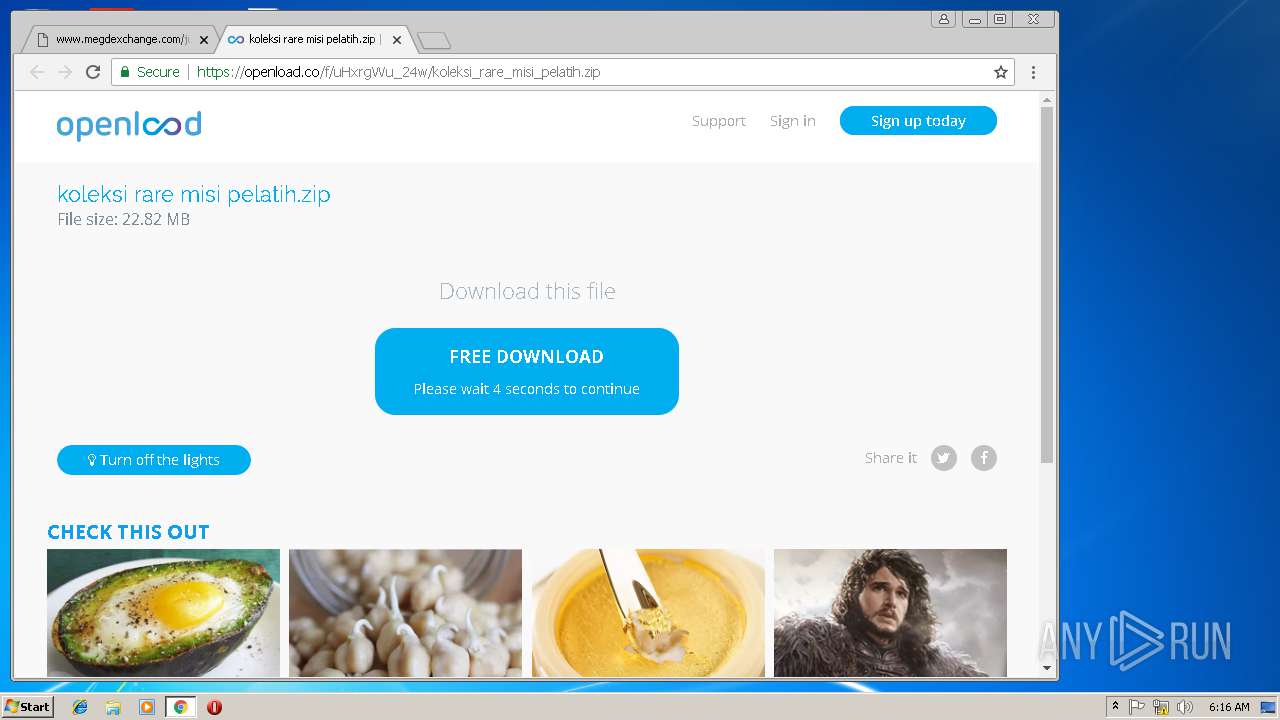
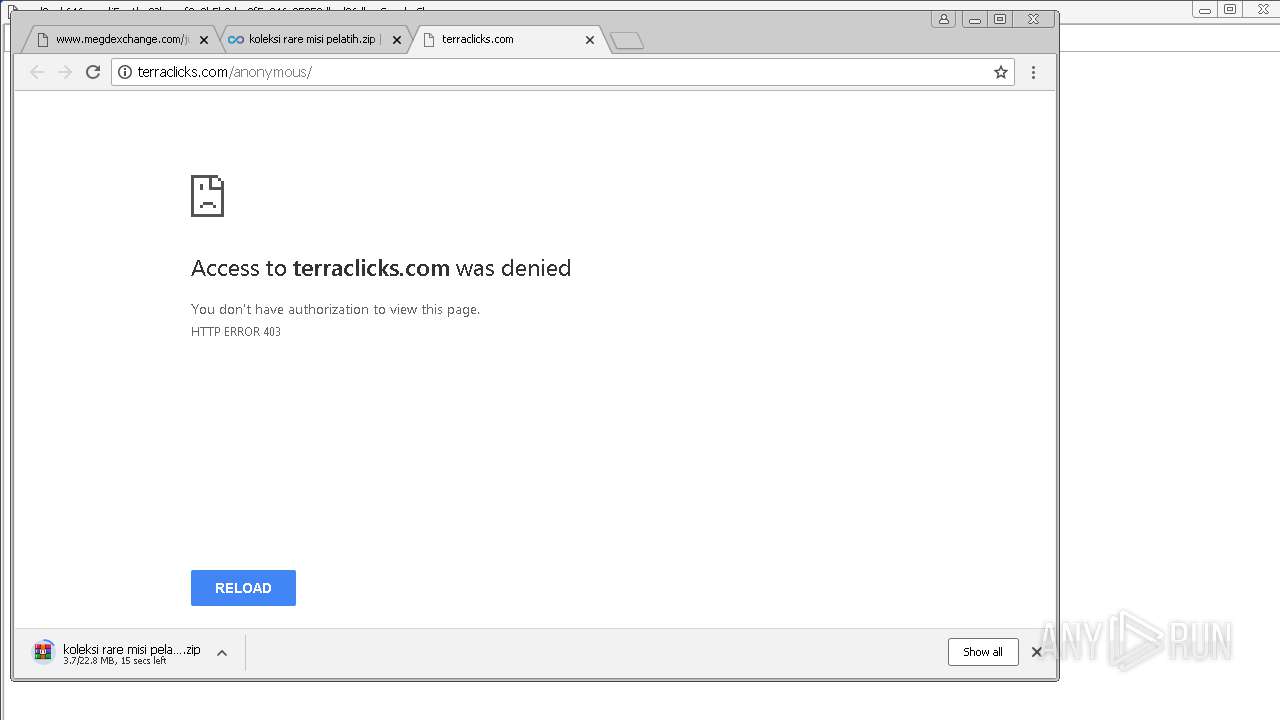
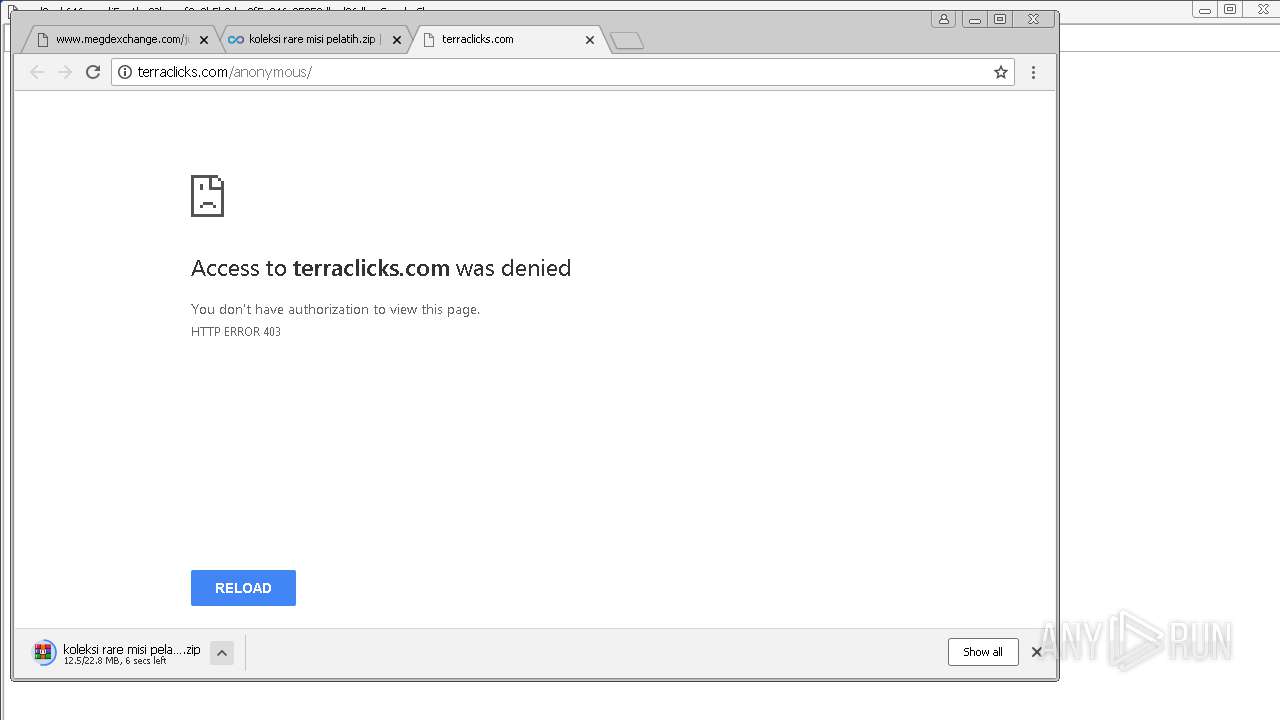
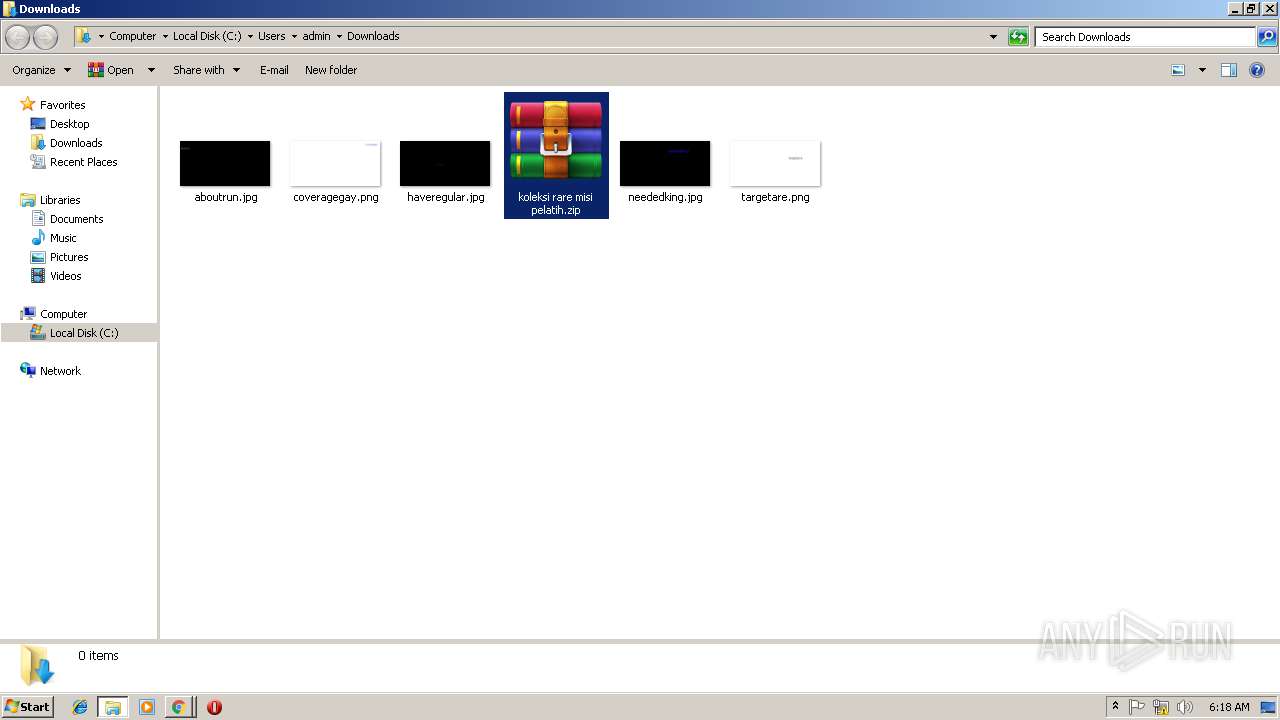
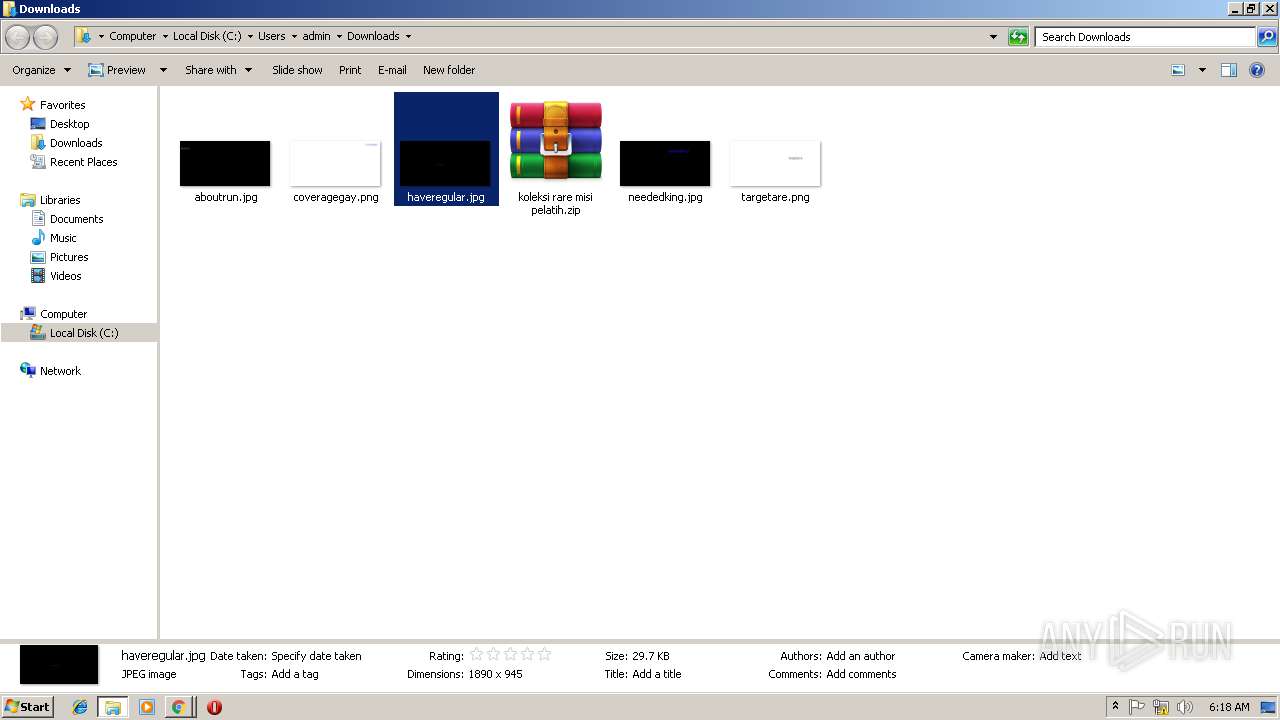
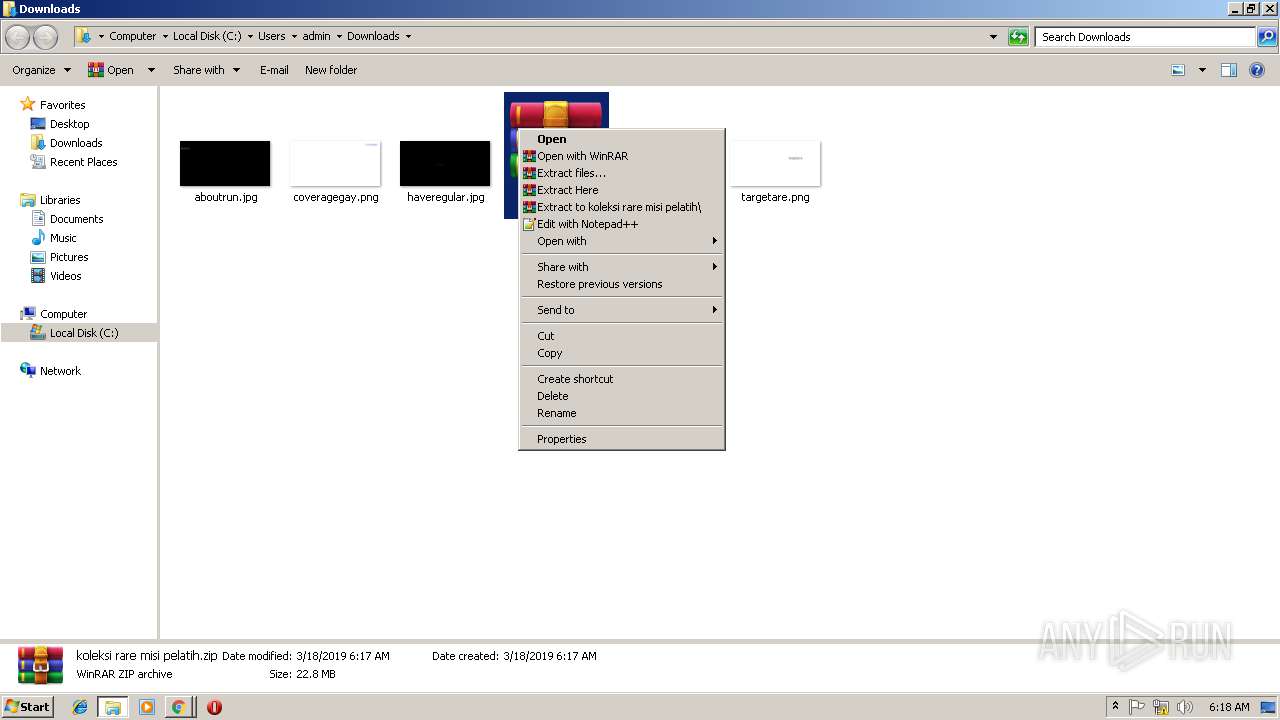
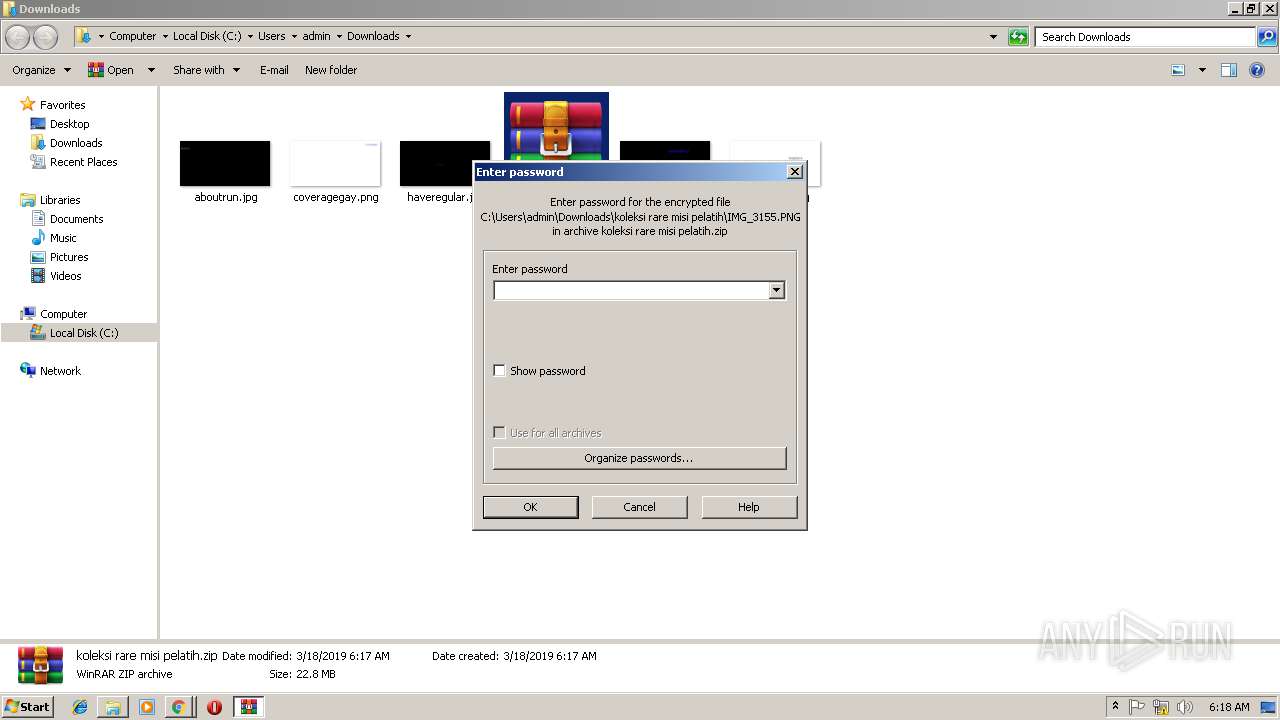
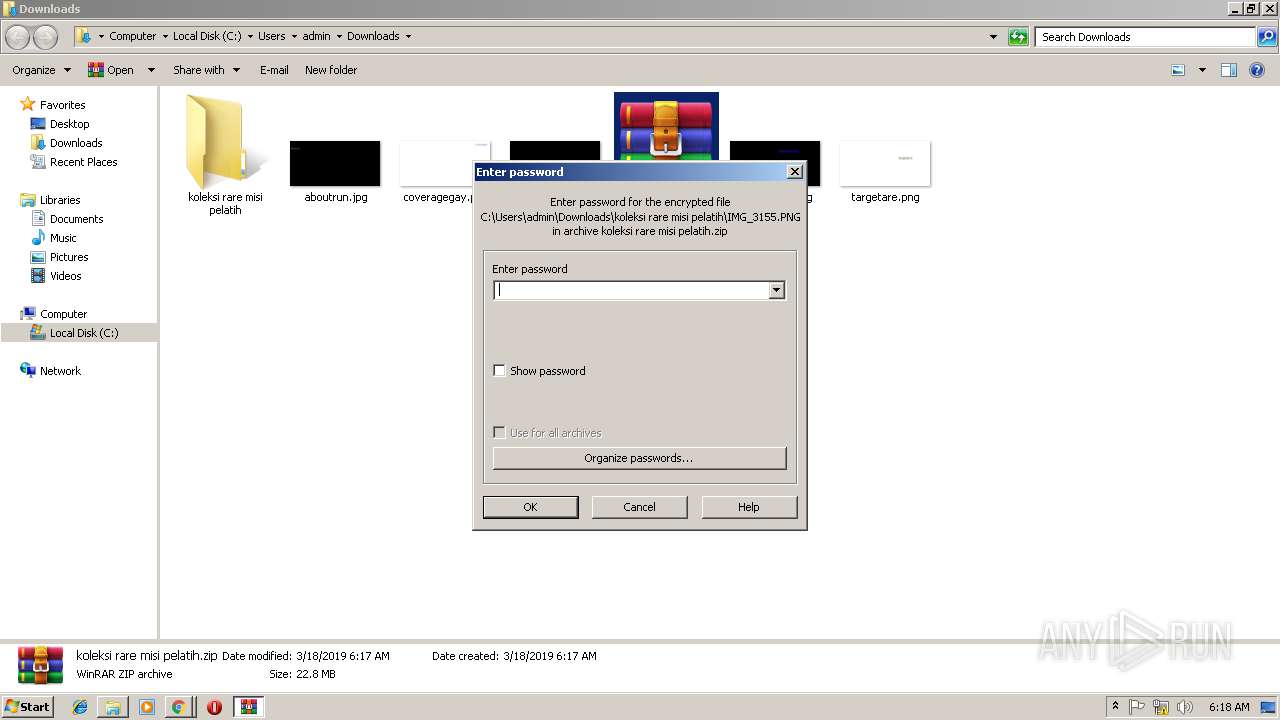
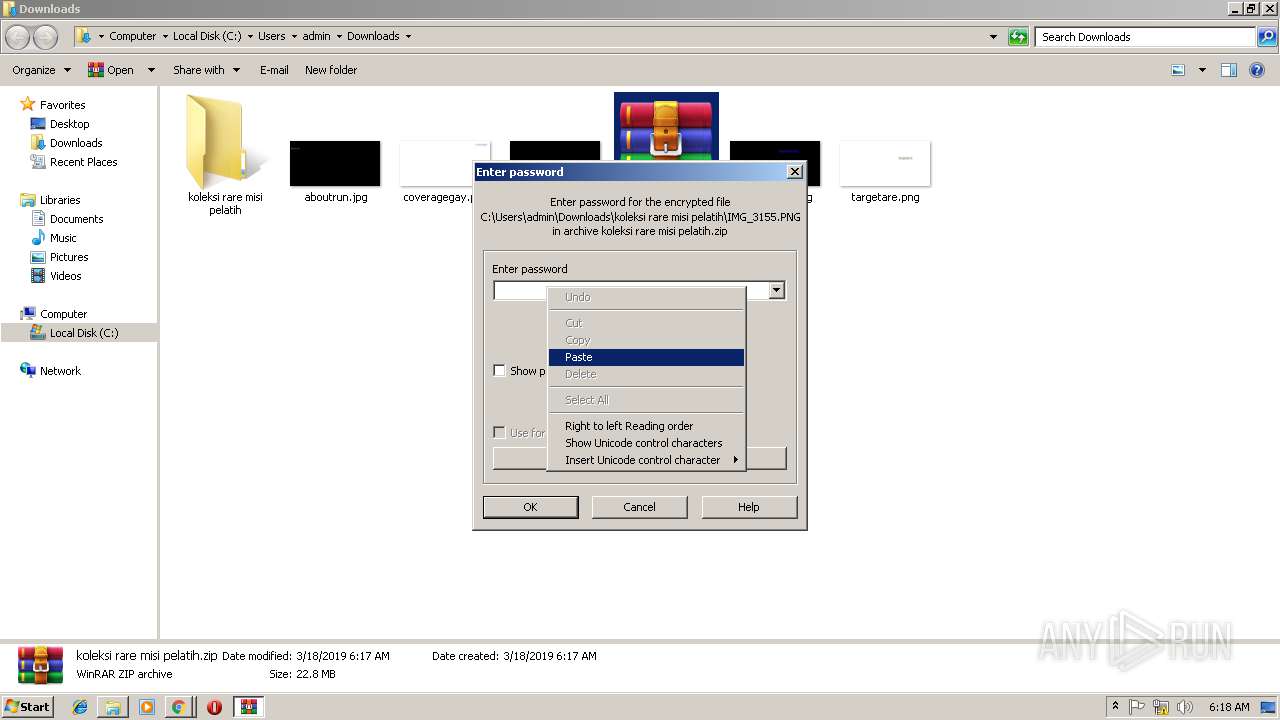
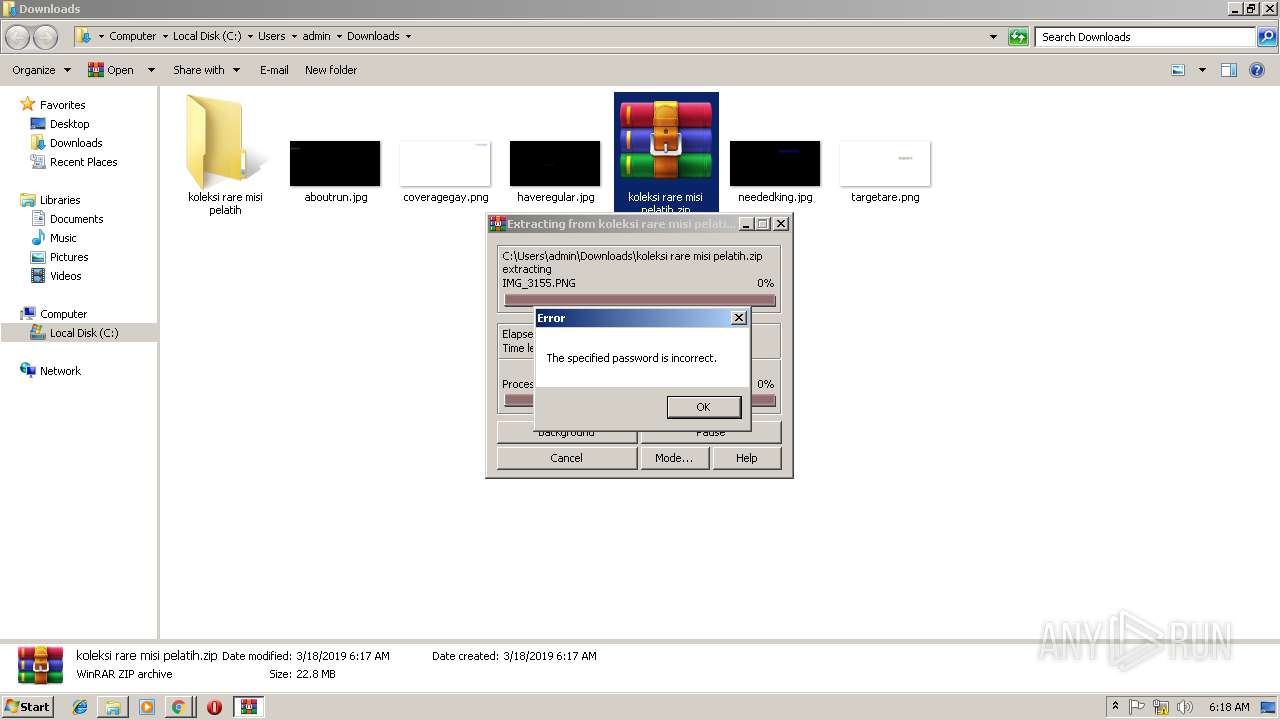
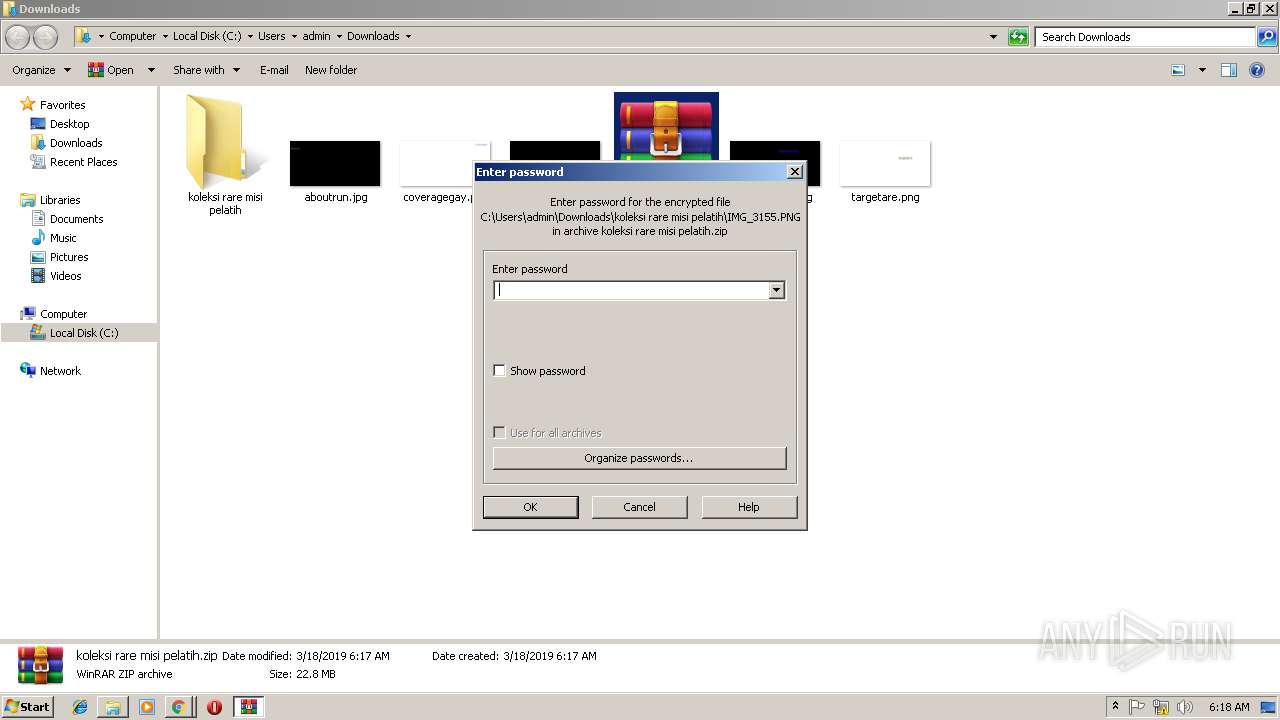
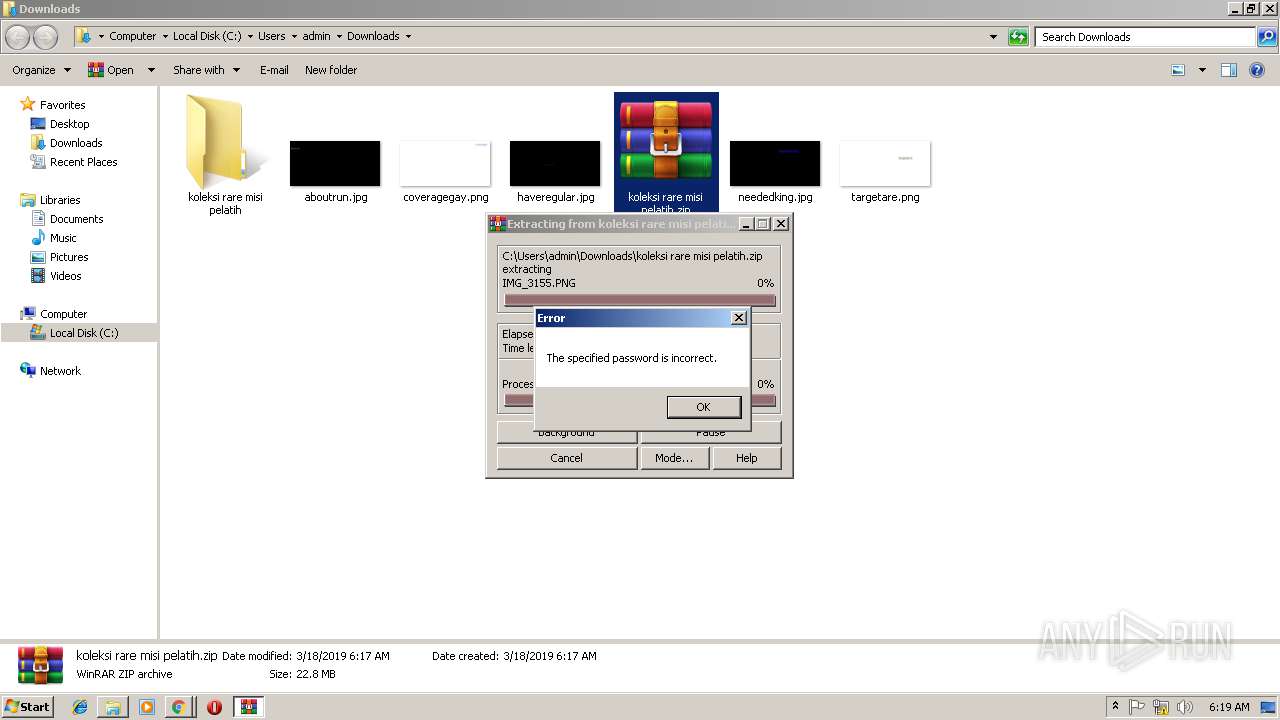
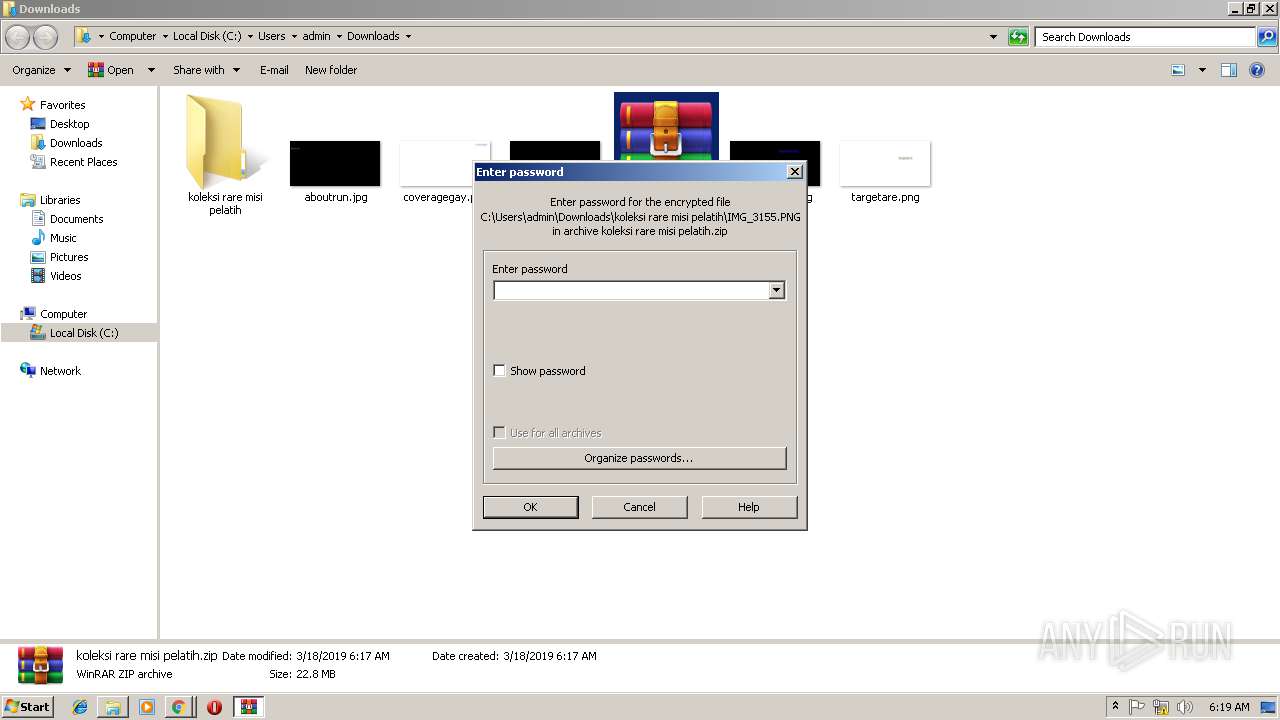
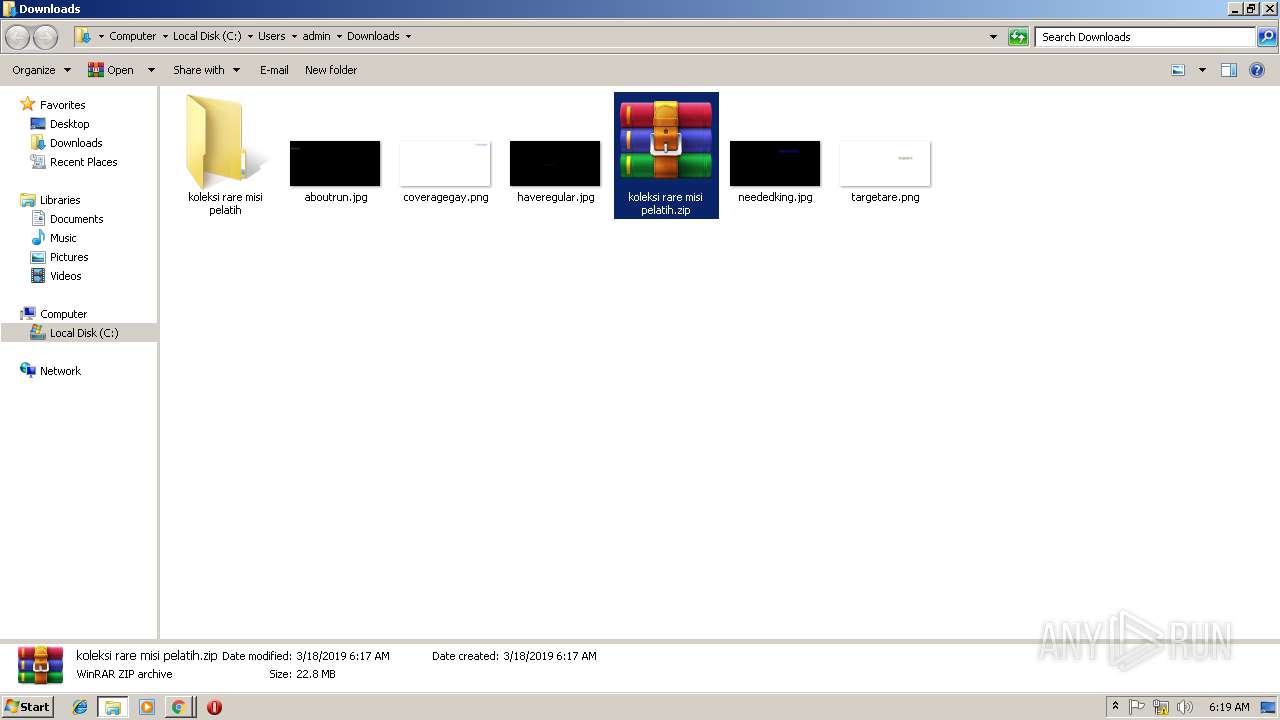
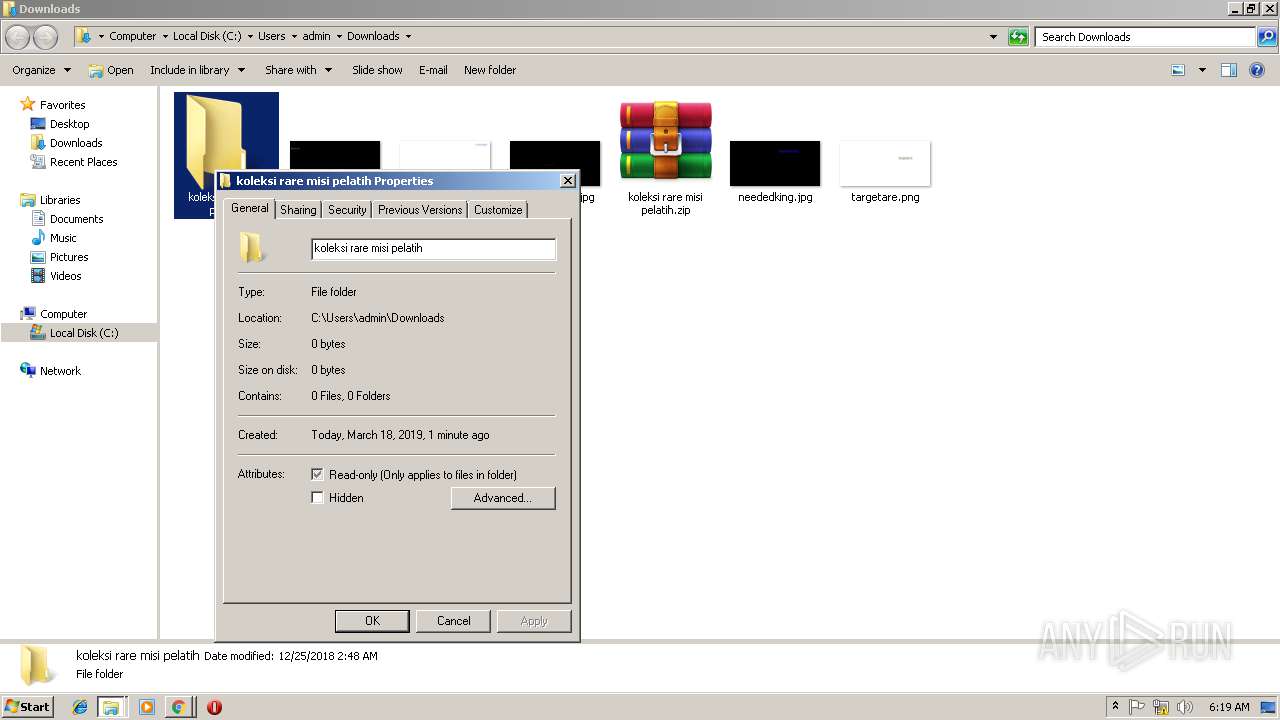
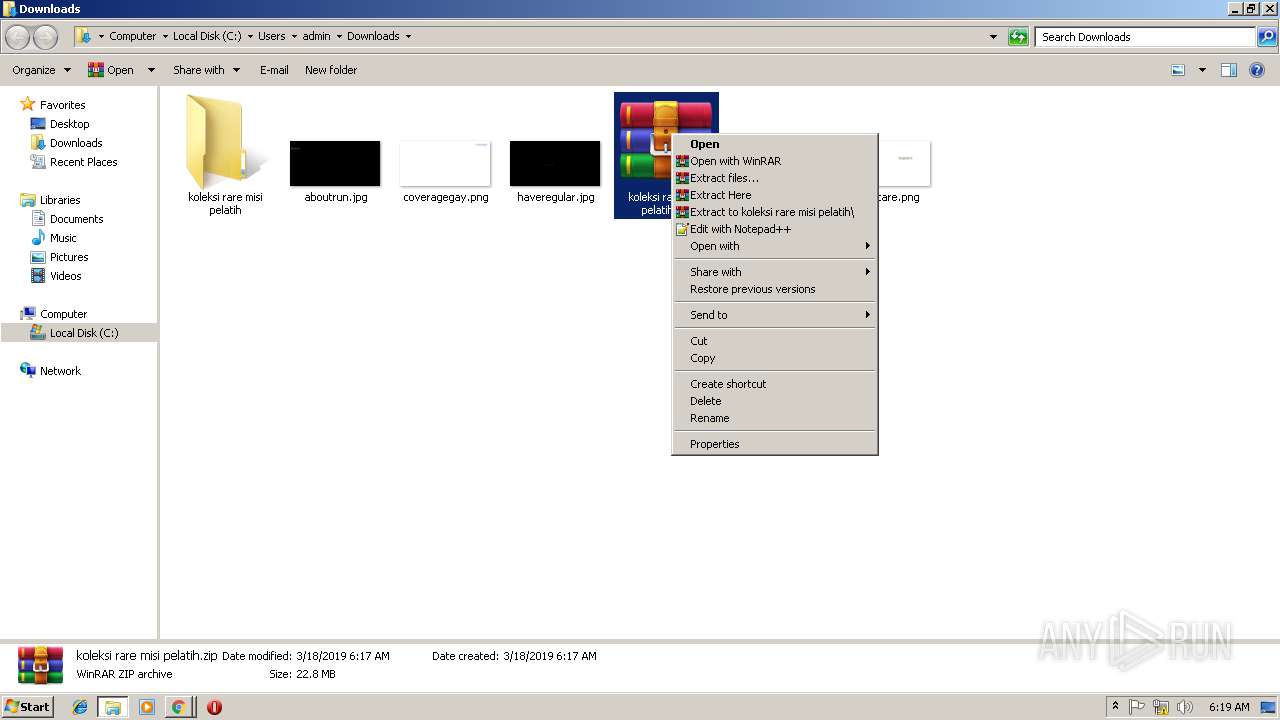
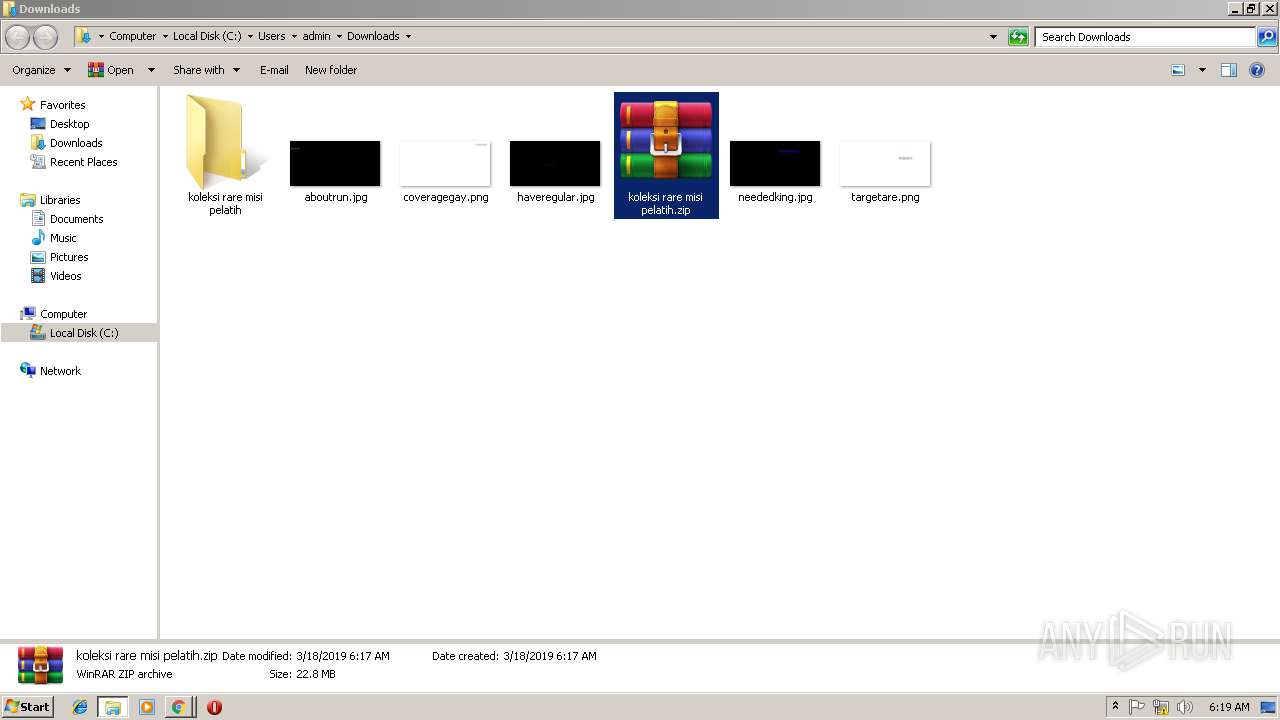
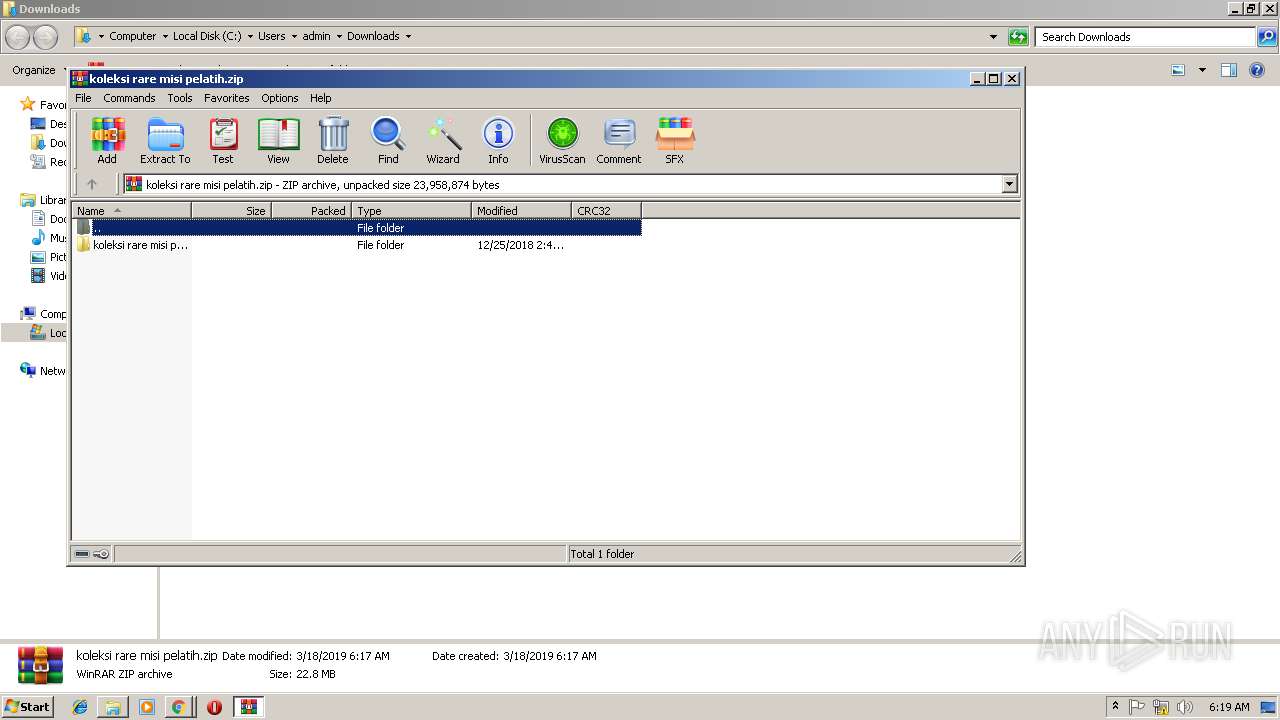
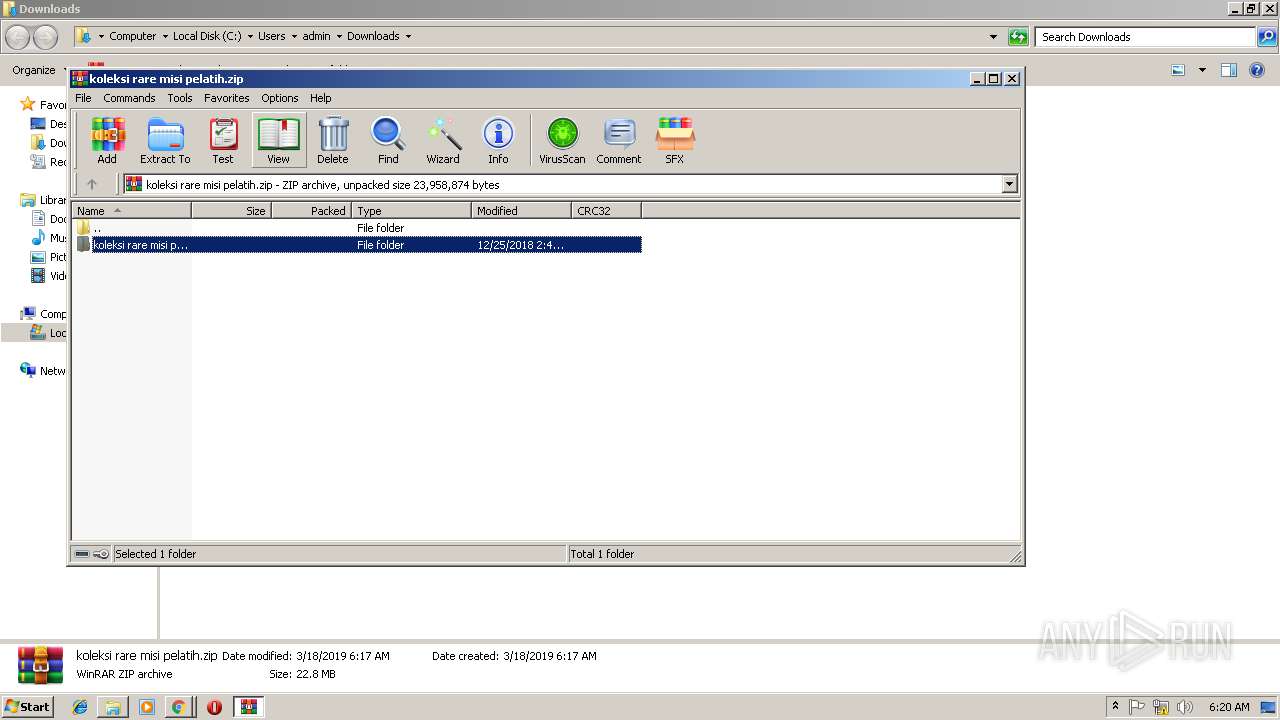
| 2568 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\koleksi rare misi pelatih.zip" C:\Users\admin\Downloads\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,15696185992708961327,5947440284735830169,131072 --enable-features=PasswordImport --service-pipe-token=C64B2B4B746BEFC881C6697B0FEF29C8 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=C64B2B4B746BEFC881C6697B0FEF29C8 --renderer-client-id=5 --mojo-platform-channel-handle=1900 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6ce700b0,0x6ce700c0,0x6ce700cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2812 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,15696185992708961327,5947440284735830169,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=396EDD7A4908D7BD4B5A6517E1429743 --mojo-platform-channel-handle=3228 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3036 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3728 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,15696185992708961327,5947440284735830169,131072 --enable-features=PasswordImport --service-pipe-token=A7576E83C57406079956DE3F7C44CC4D --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=A7576E83C57406079956DE3F7C44CC4D --renderer-client-id=3 --mojo-platform-channel-handle=2096 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
2 998
Read events
2 333
Write events
647
Delete events
18
Modification events
| (PID) Process: | (2812) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2812) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2812) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2812) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2812) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2812) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2812) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {30BD32AF-4945-11E9-BAD8-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2812) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2812) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2812) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E30703000100120006000F000E007102 | |||
Executable files
0
Suspicious files
87
Text files
221
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2812 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2812 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3092 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@linkshrink[2].txt | — | |
MD5:— | SHA256:— | |||
| 3092 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\7L3coe[1].txt | — | |
MD5:— | SHA256:— | |||
| 3092 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabAAAD.tmp | — | |
MD5:— | SHA256:— | |||
| 3092 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarAAAE.tmp | — | |
MD5:— | SHA256:— | |||
| 3092 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabAADE.tmp | — | |
MD5:— | SHA256:— | |||
| 3092 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarAADF.tmp | — | |
MD5:— | SHA256:— | |||
| 3092 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\css[1].txt | text | |
MD5:— | SHA256:— | |||
| 3092 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabAB8C.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
59
TCP/UDP connections
113
DNS requests
67
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3092 | iexplore.exe | GET | 204 | 18.204.49.173:80 | http://agreensdistra.info/MlU4N0cdaltEemtmYkUmXz56ZRFBGm1mAmcCeV8lcAd5Zx9eFB5DLlZoDg9wA2QOETdbMQUGYUEhWUMyQWgOBWFbO15YehQjBQZpA2UWAHYcZh5DN1MyBQZhbWgJAnIAbQAOcANsAQV1 | US | — | — | unknown |
3092 | iexplore.exe | GET | 204 | 18.204.49.173:80 | http://agreensdistra.info/ZnJISzlJTSs4BAQ1LCZjCjsHHX8/MSksDSAkGRleJRUNCGwLAW4/UAJPfnMOV0N+bUkPFnV6HxUGKT9MFU95bVAIFCd2HxBPeWUIVlx/ehdVVDw7WAFPeW1mW0N9fgteSnF8CF9Lenk | US | — | — | unknown |
3092 | iexplore.exe | GET | 204 | 18.204.49.173:80 | http://agreensdistra.info/eXVoZ21WSgsUUB0fLlQgPTg9JgYdICsfPy0nLi4vPDMLMy84Gk4TBB1IXl9aSEReQR0QEVVWSwoBCRMYCkheVEsQGw4IUF8DVVZDSEVGUFxXRk4THRgSVVZLJkhZUlhLTVBeWkhMUVdb | US | — | — | unknown |
3092 | iexplore.exe | GET | 204 | 18.204.49.173:80 | http://agreensdistra.info/MDVxajYfChIZC1F9NwJjW3srOHBbTTs8d2hiNjhOaGA4L3sDeyhMQllRTF0CCQZAXBBAXBVXBwgTAh5XREACVwcWXB8MWQ0TB1cHHgVfWhgDEwUaV1cIQExGREEdVwcFAENSDgkCQ1sDAQM | US | — | — | unknown |
3092 | iexplore.exe | GET | 204 | 18.204.49.173:80 | http://agreensdistra.info/VUU3a2h6elQYVTZ1WBwmEQRlDTkyBHQ+JmwHdik7BxZDOSkyHBEfATF4AVNfZHQBTRg8IQpaTiYxVh8dJngDWU48K1EEVWRzAl1OI3gGRVllawBaRmZjQxsJMngGTTdodAJeWm19DlxaZHAAUw | US | — | — | unknown |
3092 | iexplore.exe | GET | 301 | 104.27.175.178:80 | http://linkshrink.net/content/img/logov.png | US | — | — | suspicious |
3092 | iexplore.exe | GET | 204 | 18.204.49.173:80 | http://agreensdistra.info/V0lhVEh4dgIndTQOKz4eDyo0A3kaPjAGGRILGxYYBB80FRFnAEcgITN0V2x/ZnhXcjg+LVxlbiQ9ACA9JHRXZ24+Jwc7dXE/XGVmZnlPY3l5ekcgODYuXGVuCHRQYX1lcVltf2B5WGx8 | US | — | — | unknown |
3092 | iexplore.exe | GET | 204 | 18.204.49.173:80 | http://agreensdistra.info/Uk9vbzR9cAwcCQs1NRViPzgnKwQfNTgIUAMJFSFhBSgqPm0UJEkbXTZyWVcDY35ZSUQ7K1JeEiE7DhtBIXJeSV08KQBSEiRyXkEFYmFYXhphaRsfVTVyXklrb35aWgZqd1ZYA2J2VlY | US | — | — | unknown |
3092 | iexplore.exe | GET | 204 | 18.204.49.173:80 | http://agreensdistra.info/WktrcG11dAgDUAB5ITo/AgU8Jl4fJi0mVR8oIz4vDycuAycfBTNWGTMvVkdZY3haRksqIg9NXGJtGAQMLj4YTVtjbQIeCzV2TQZQa2VbXl10eE0EHTssVkFLKj8fHFBrfl5CVWJyXEJcb3pd | US | — | — | unknown |
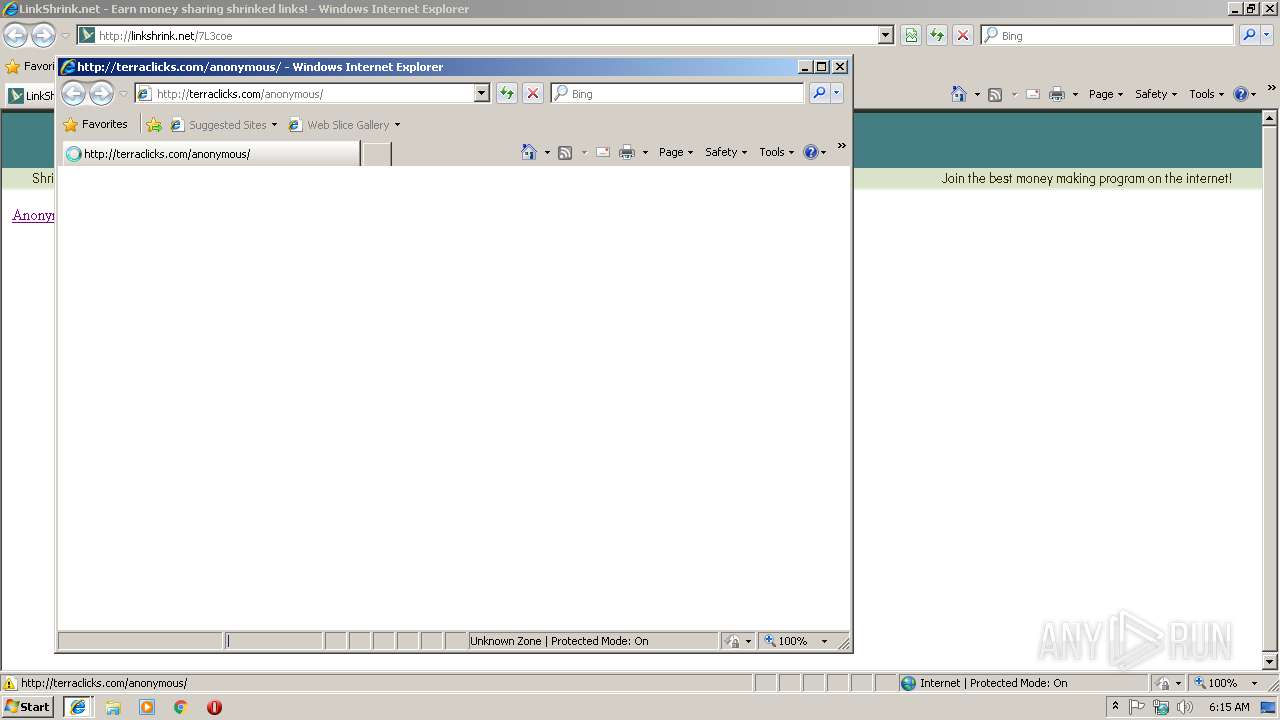
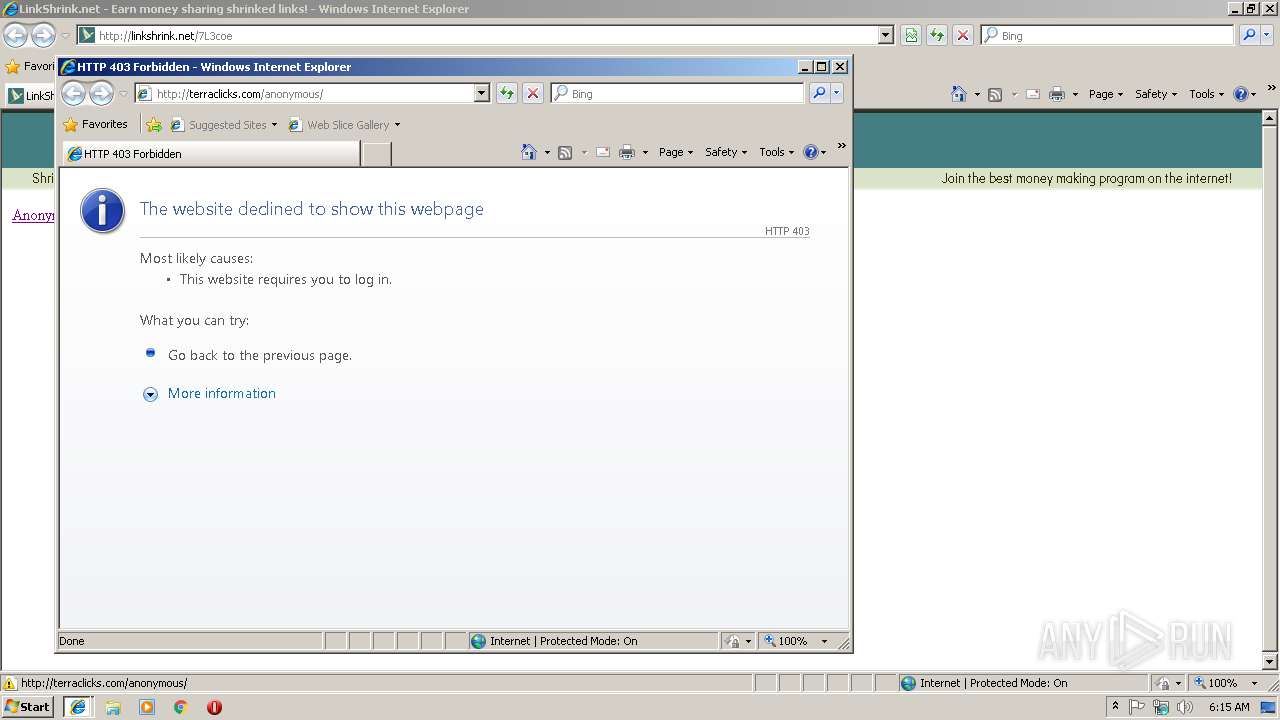
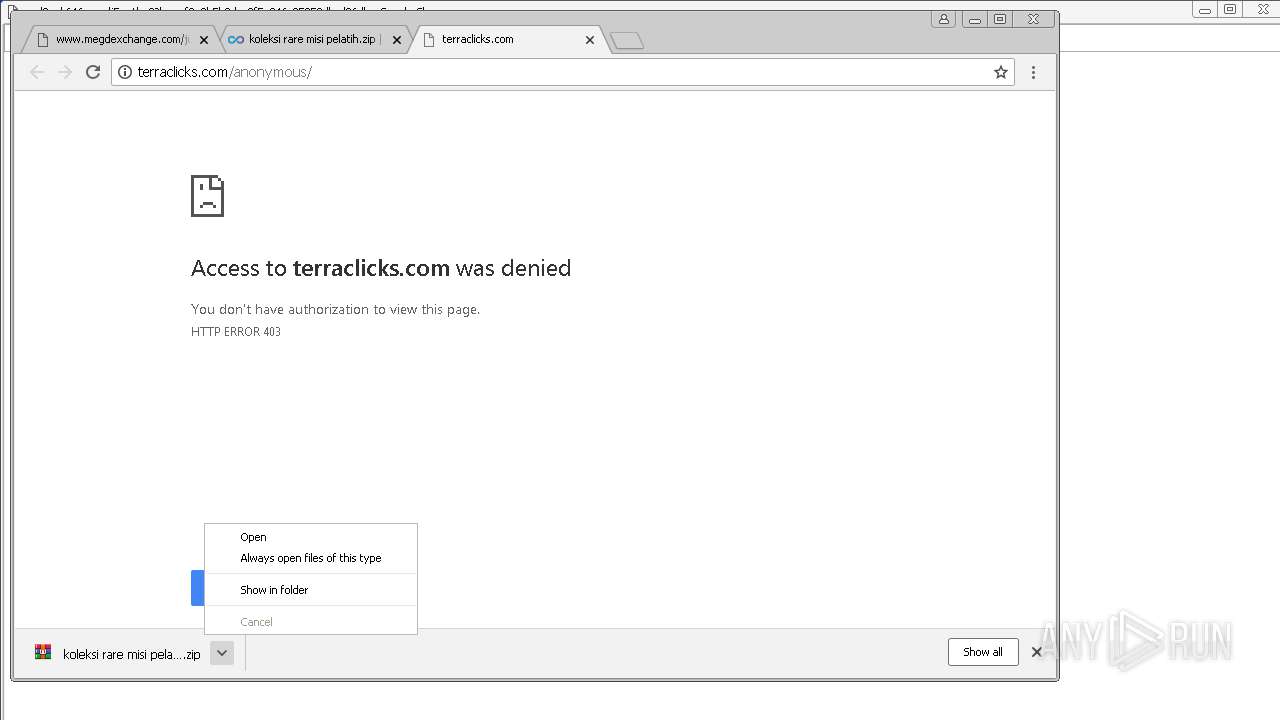
3424 | iexplore.exe | GET | 403 | 198.134.112.243:80 | http://terraclicks.com/anonymous/ | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2812 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3092 | iexplore.exe | 104.27.175.178:80 | linkshrink.net | Cloudflare Inc | US | shared |
3092 | iexplore.exe | 172.217.21.234:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3092 | iexplore.exe | 104.27.175.178:443 | linkshrink.net | Cloudflare Inc | US | shared |
3092 | iexplore.exe | 172.217.21.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3092 | iexplore.exe | 172.217.16.131:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3092 | iexplore.exe | 172.217.16.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
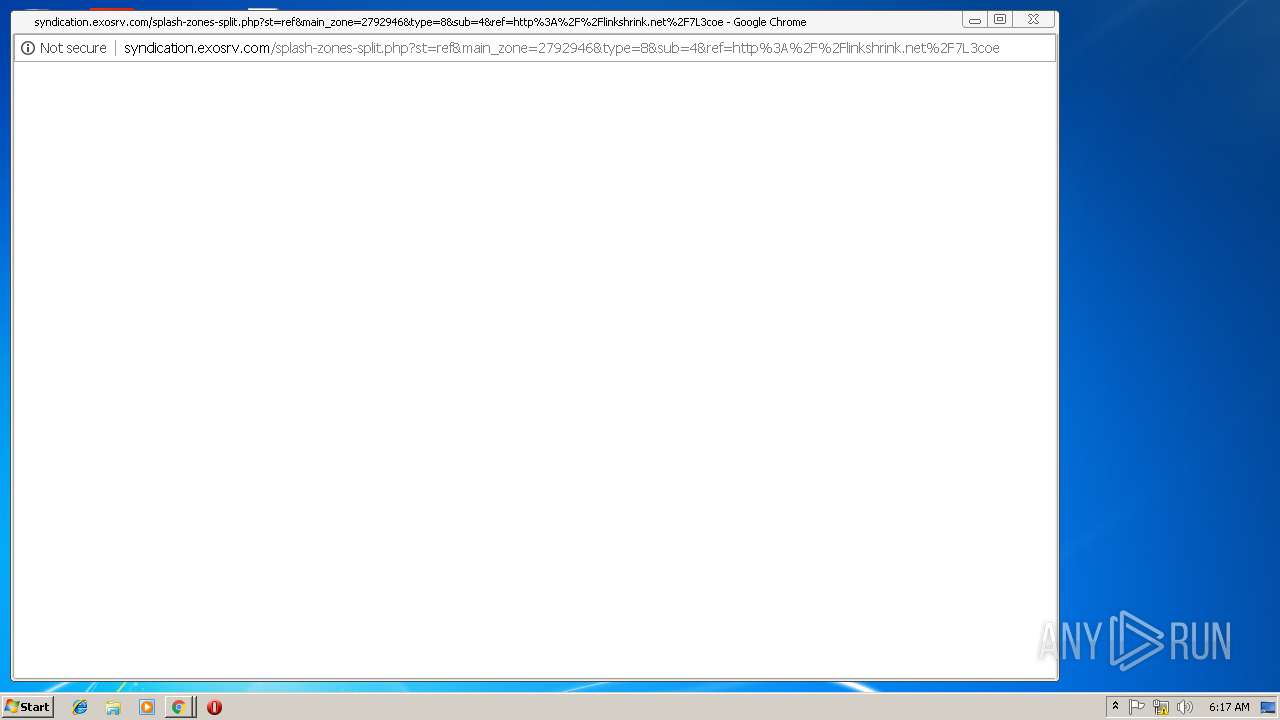
3092 | iexplore.exe | 198.134.112.244:443 | faxqaaawyb.com | Webair Internet Development Company Inc. | US | suspicious |
3092 | iexplore.exe | 54.230.9.212:443 | boudja.com | Amazon.com, Inc. | US | unknown |
3092 | iexplore.exe | 52.85.74.247:80 | x.ss2.us | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
linkshrink.net |
| suspicious |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
faxqaaawyb.com |
| malicious |
boudja.com |
| whitelisted |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
agreensdistra.info |
| unknown |
d63a3au5lqmtu.cloudfront.net |
| whitelisted |