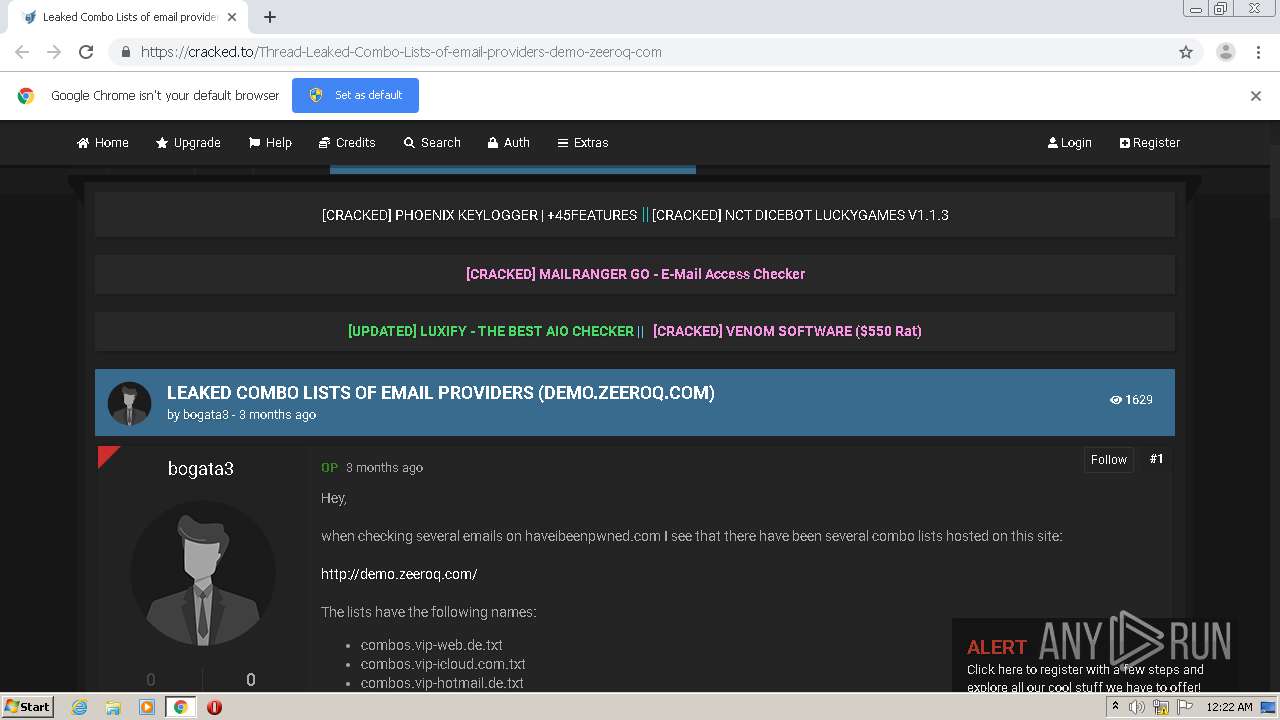
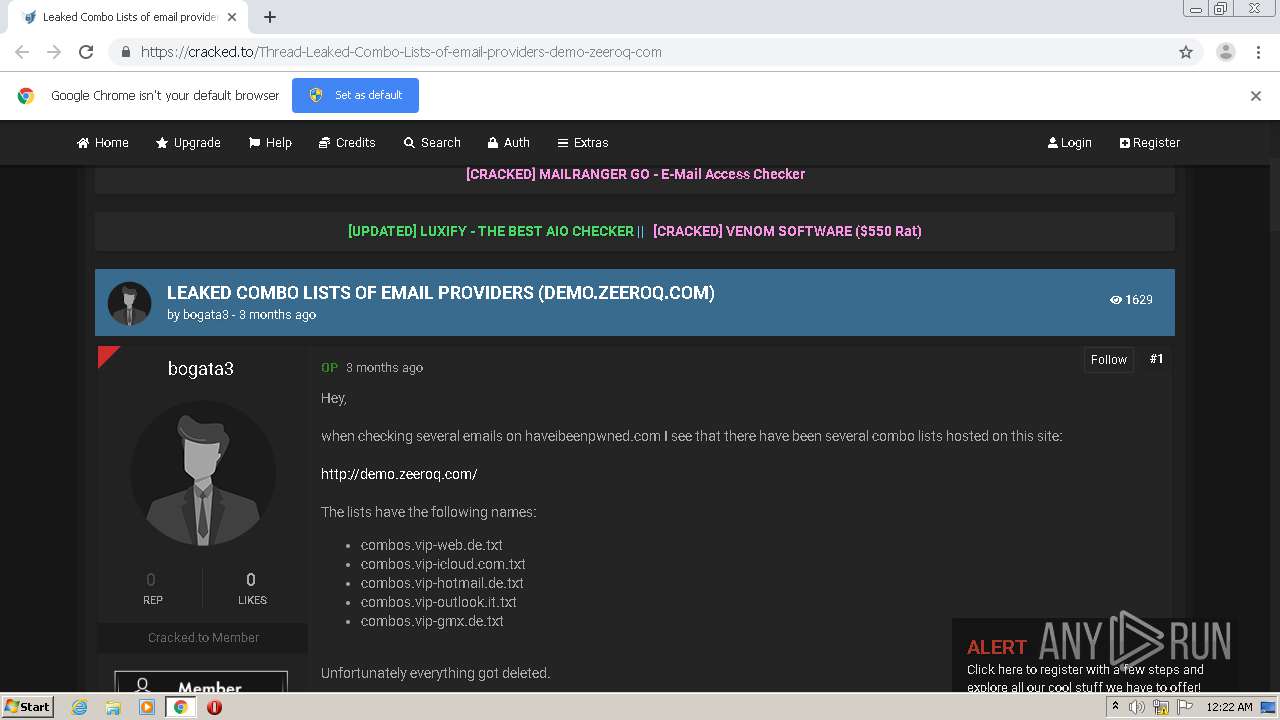
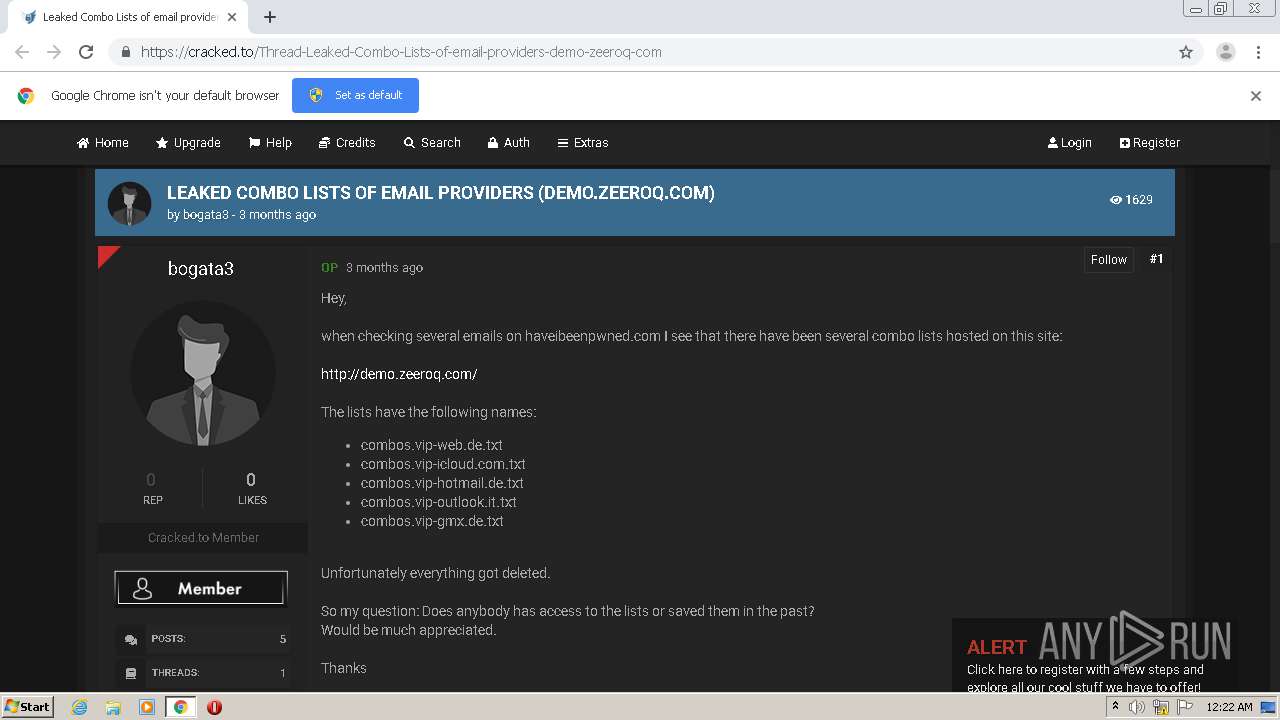
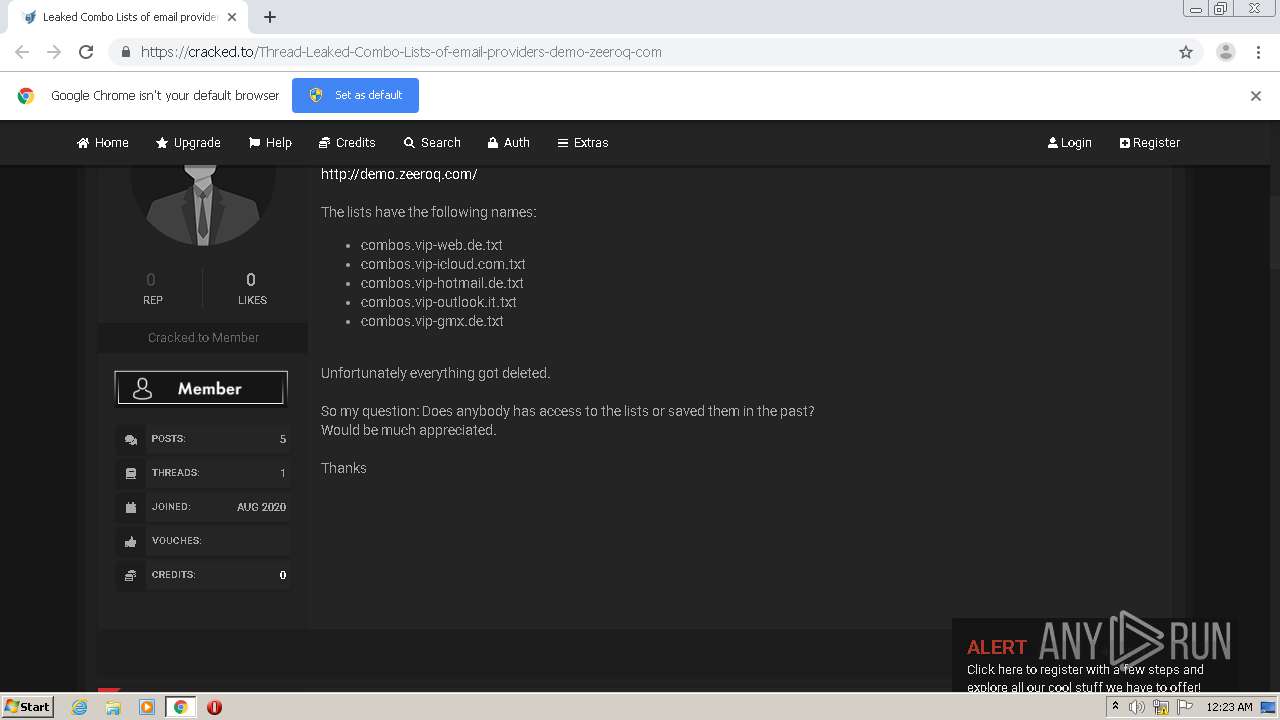
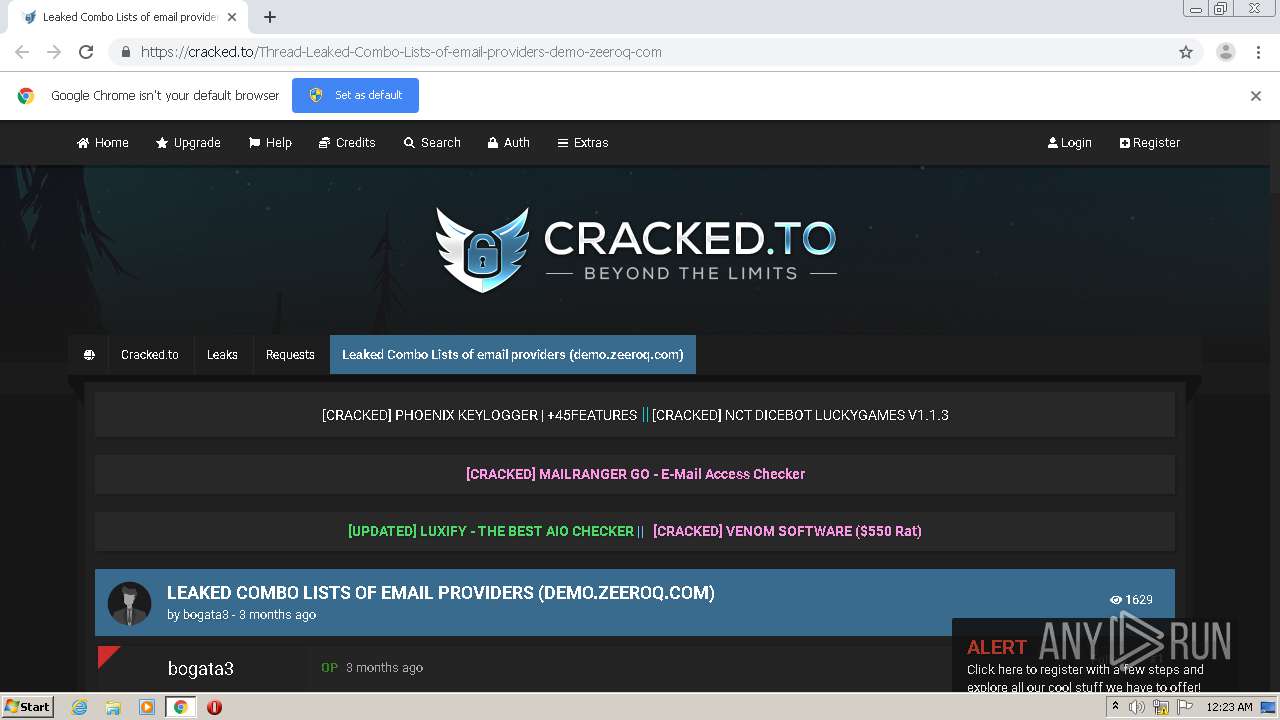
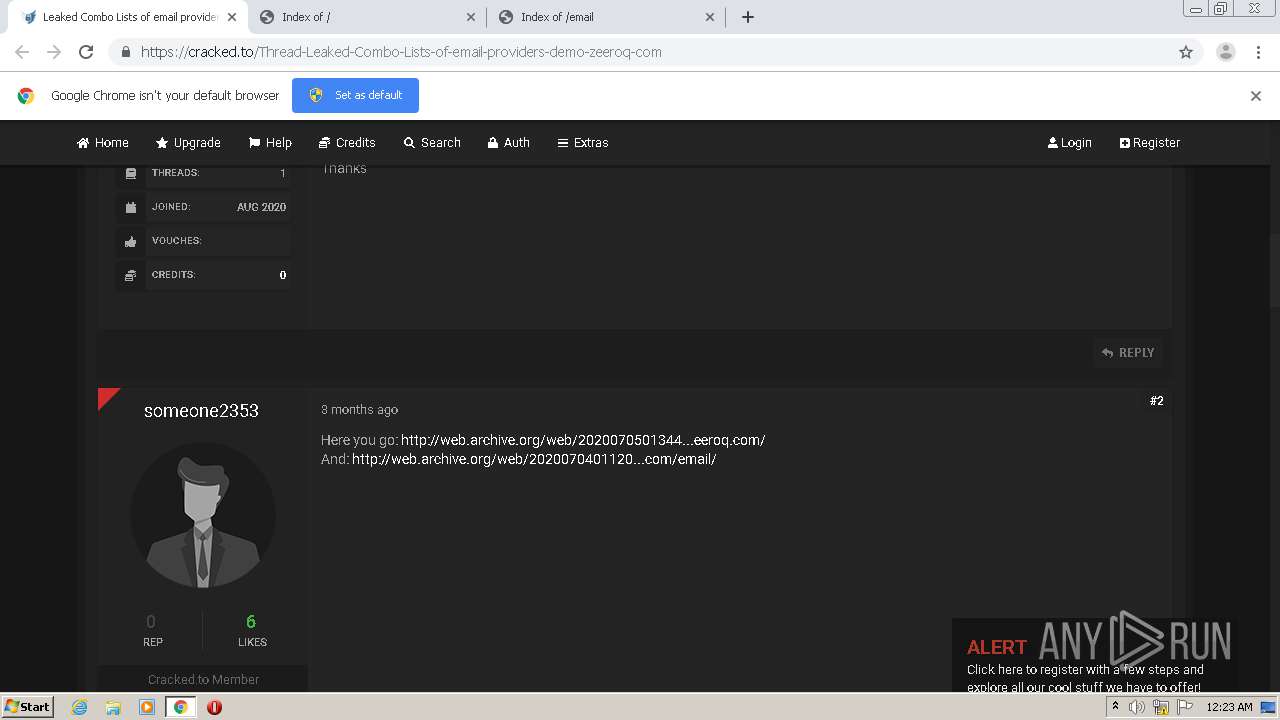
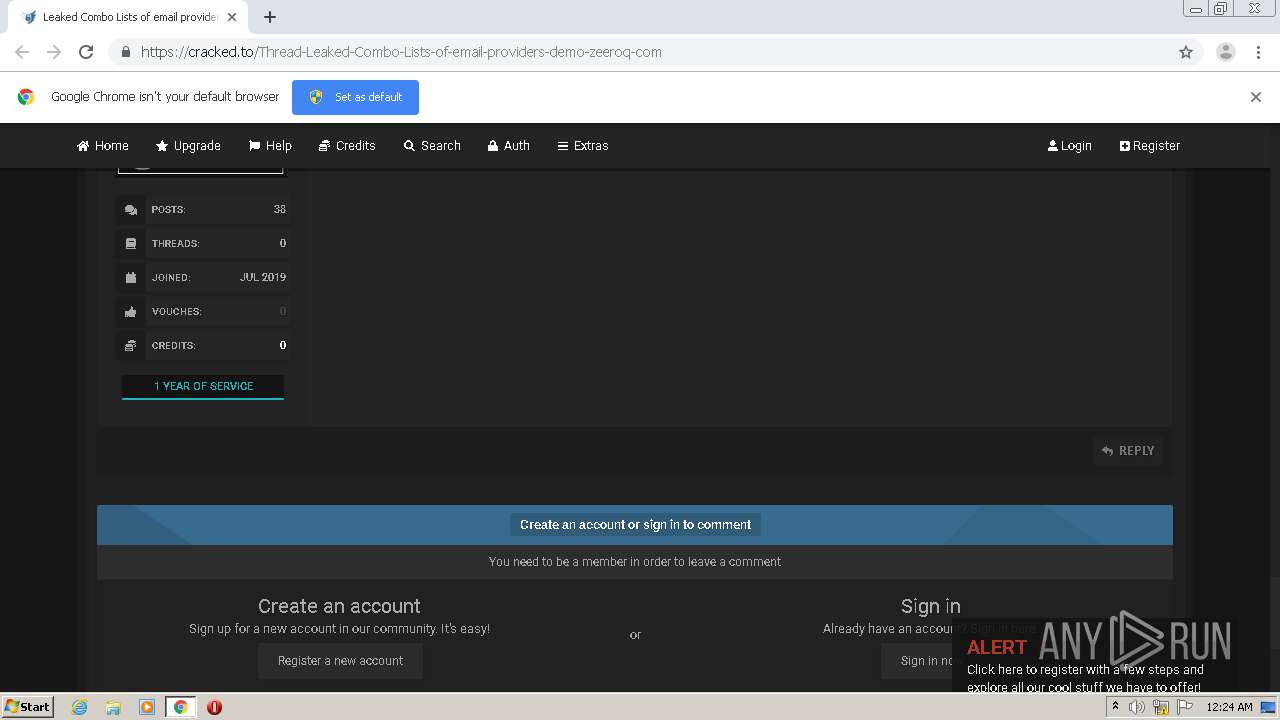
| URL: | https://www.google.com/url?sa=t&rct=j&q=&esrc=s&source=web&cd=&cad=rja&uact=8&ved=2ahUKEwjMien2spftAhUW4HMBHUNCDvoQFjACegQIAxAC&url=https%3A%2F%2Fcracked.to%2FThread-Leaked-Combo-Lists-of-email-providers-demo-zeeroq-com&usg=AOvVaw1kB22rTiz6j6g4Ml-M436S |
| Full analysis: | https://app.any.run/tasks/1cfde754-1edf-4f55-8121-8d7d7e2fd6c9 |
| Verdict: | Malicious activity |
| Analysis date: | November 23, 2020, 00:22:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CA9334EF61AB60818B1FD4C48EF16E17 |
| SHA1: | 4278A3ED9E6A89225B2DF94F622572EBDBF5DBF9 |
| SHA256: | 58939D234ADAF0E58EE7682058DAF66438FB62384130228284A889BCB1CC73BB |
| SSDEEP: | 6:2OLI2sq+wp1w4pNoXWRZh6R3zQvj9s8iAt3rSE46:2V2JnNoXAhoWNvp |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads settings of System Certificates
- chrome.exe (PID: 2040)
Reads the hosts file
- chrome.exe (PID: 2040)
- chrome.exe (PID: 2152)
Creates files in the user directory
- chrome.exe (PID: 2152)
Application launched itself
- chrome.exe (PID: 2152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
16
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2016 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,15220806301515651852,17211955527374645769,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10237289239948223285 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3572 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,15220806301515651852,17211955527374645769,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6418171916126332208 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3636 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1052,15220806301515651852,17211955527374645769,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=17696619685057486824 --mojo-platform-channel-handle=1548 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://www.google.com/url?sa=t&rct=j&q=&esrc=s&source=web&cd=&cad=rja&uact=8&ved=2ahUKEwjMien2spftAhUW4HMBHUNCDvoQFjACegQIAxAC&url=https%3A%2F%2Fcracked.to%2FThread-Leaked-Combo-Lists-of-email-providers-demo-zeeroq-com&usg=AOvVaw1kB22rTiz6j6g4Ml-M436S" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1052,15220806301515651852,17211955527374645769,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=15405559369405096235 --mojo-platform-channel-handle=1128 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,15220806301515651852,17211955527374645769,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11849490705233320693 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3216 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,15220806301515651852,17211955527374645769,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3234962758992956941 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2172 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,15220806301515651852,17211955527374645769,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=286154480276977031 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2708 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x71aea9d0,0x71aea9e0,0x71aea9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
614
Read events
550
Write events
61
Delete events
3
Modification events
| (PID) Process: | (960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2152-13250564564214250 |
Value: 259 | |||
| (PID) Process: | (2152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2152) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
65
Text files
85
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FBB00D4-868.pma | — | |
MD5:— | SHA256:— | |||
| 2152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0d63dadb-89ca-4d3e-bbc6-ee7e9bbfd7cf.tmp | — | |
MD5:— | SHA256:— | |||
| 2152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF13f30e.TMP | text | |
MD5:— | SHA256:— | |||
| 2152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF13f30e.TMP | text | |
MD5:— | SHA256:— | |||
| 2152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF13f4e3.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
60
TCP/UDP connections
40
DNS requests
24
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
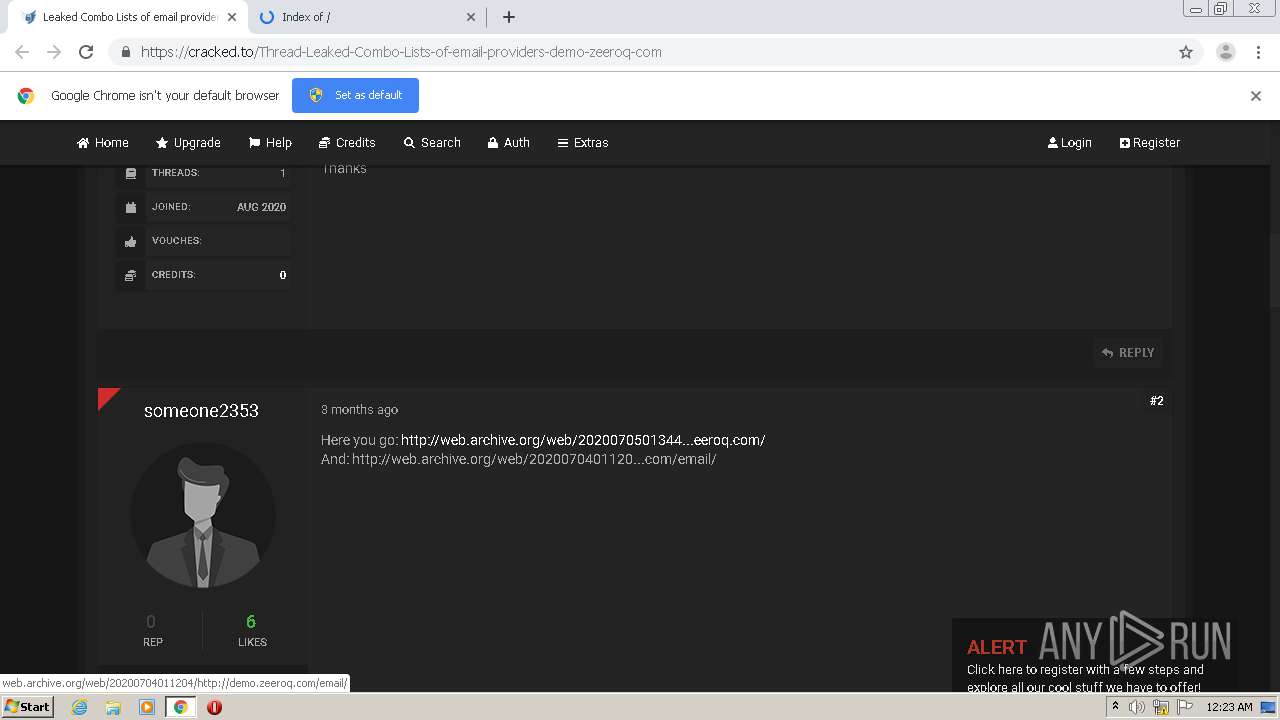
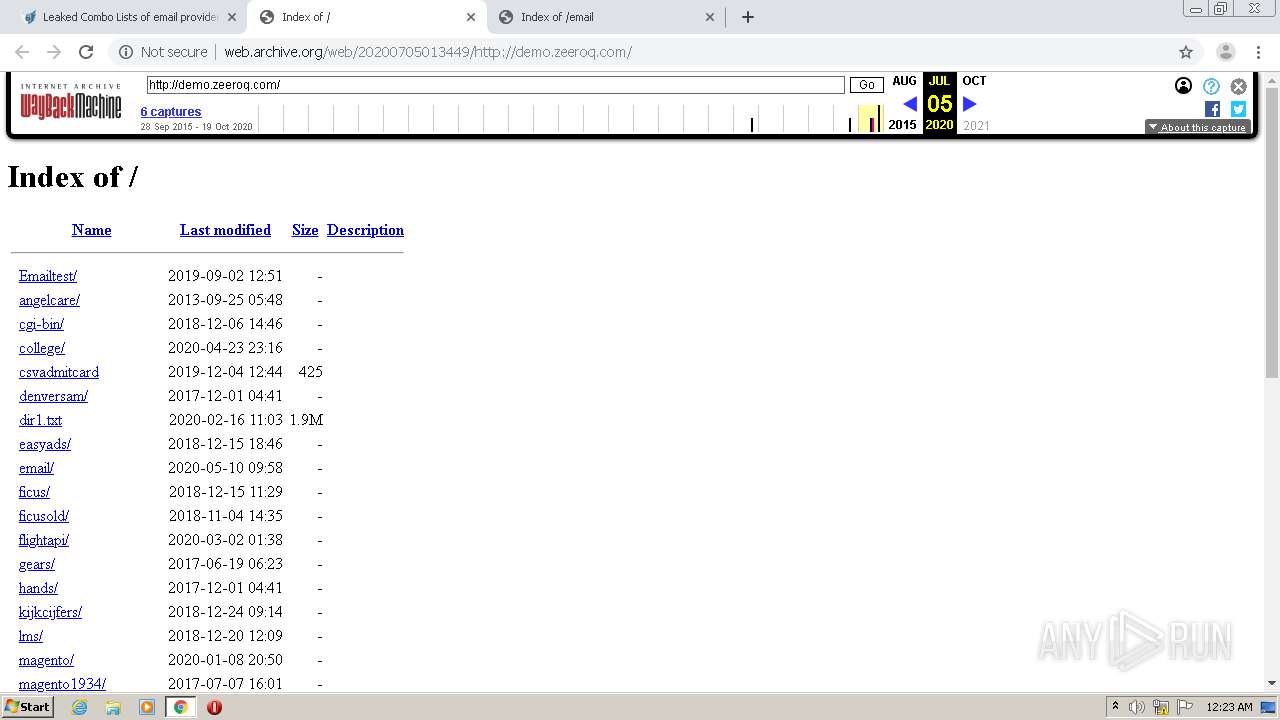
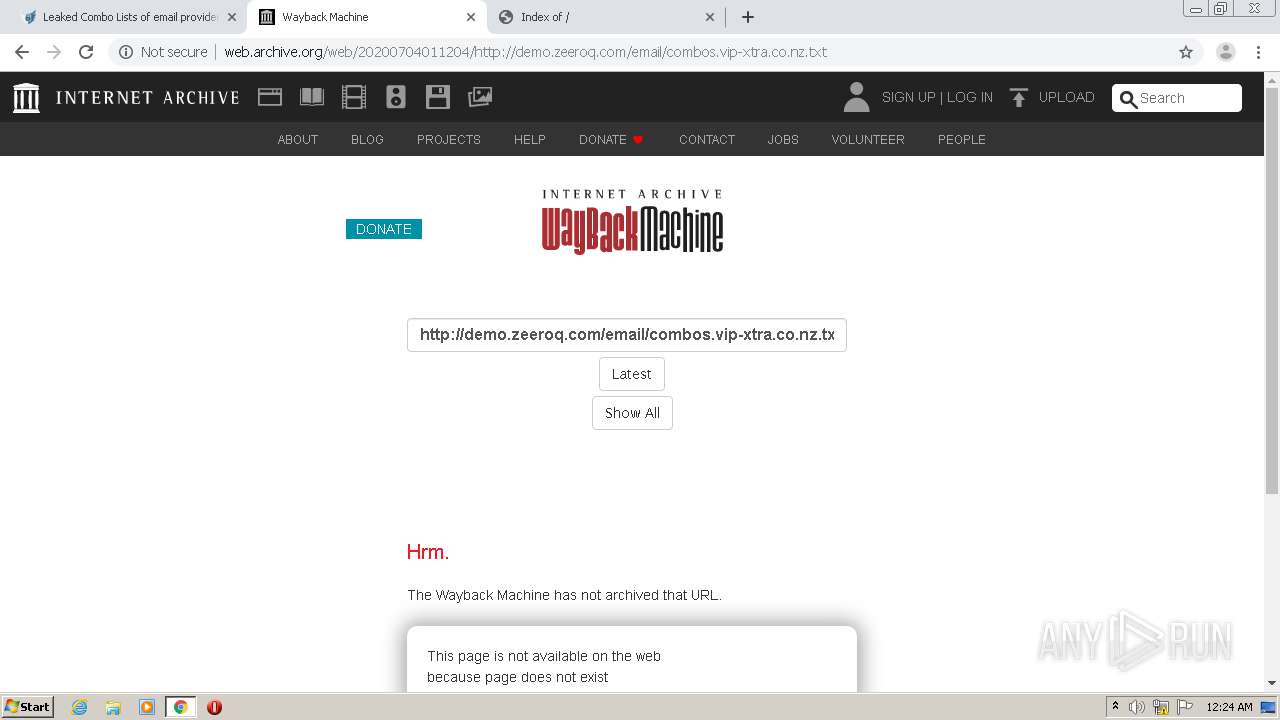
2040 | chrome.exe | HEAD | 404 | 207.241.226.190:80 | http://web.archive.org/web/20200705013449/http://web.archive.org/screenshot/http://demo.zeeroq.com/ | US | — | — | whitelisted |
2040 | chrome.exe | GET | 200 | 207.241.226.190:80 | http://web.archive.org/__wb/sparkline?output=json&url=http%3A%2F%2Fdemo.zeeroq.com%2F&collection=web | US | text | 165 b | whitelisted |
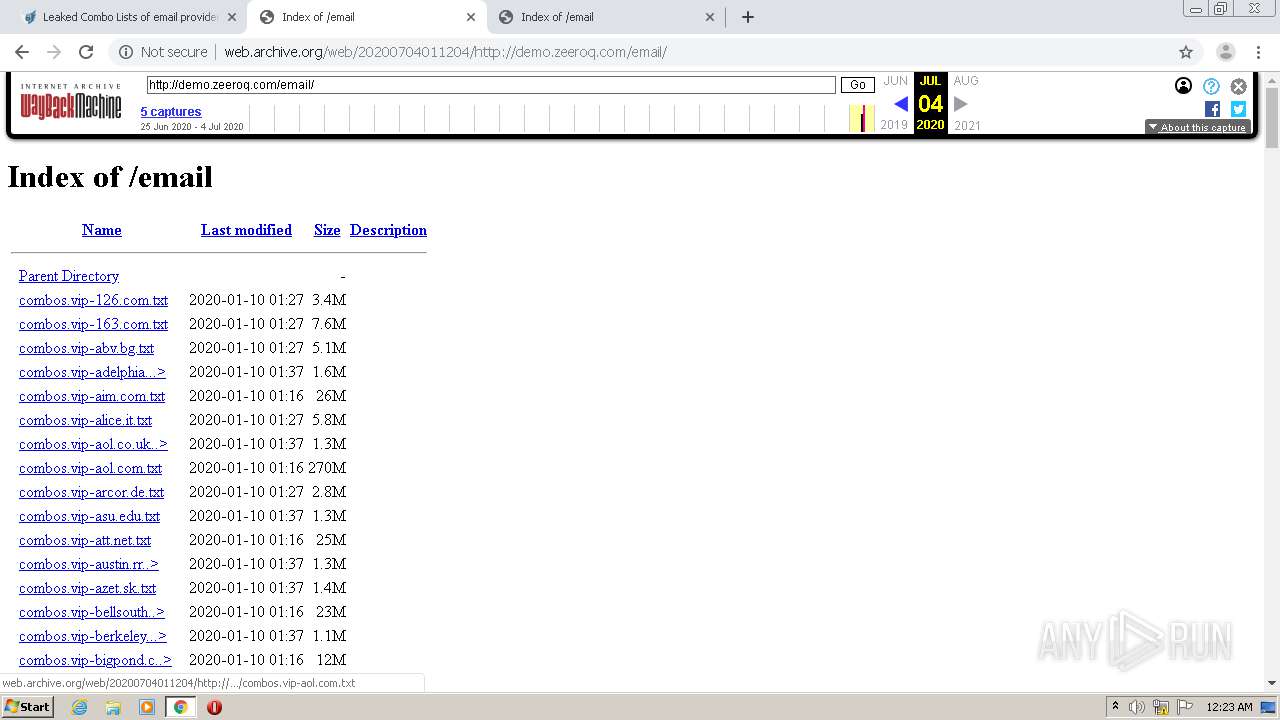
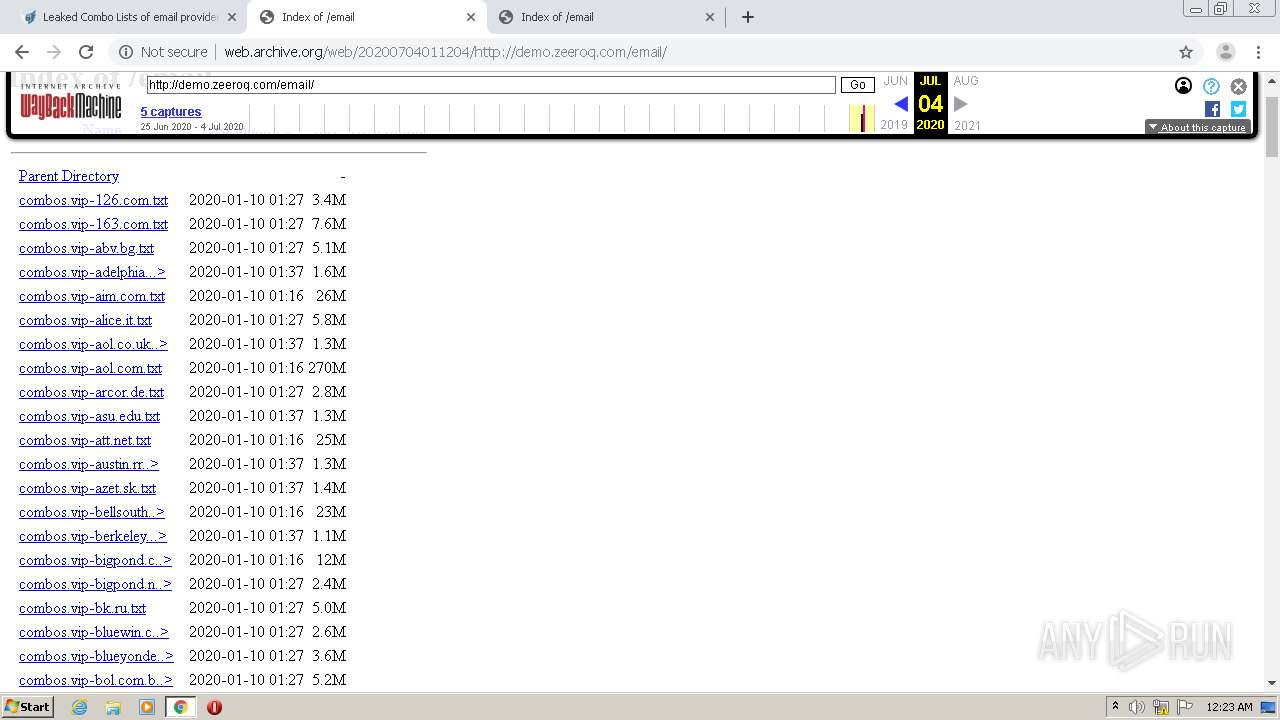
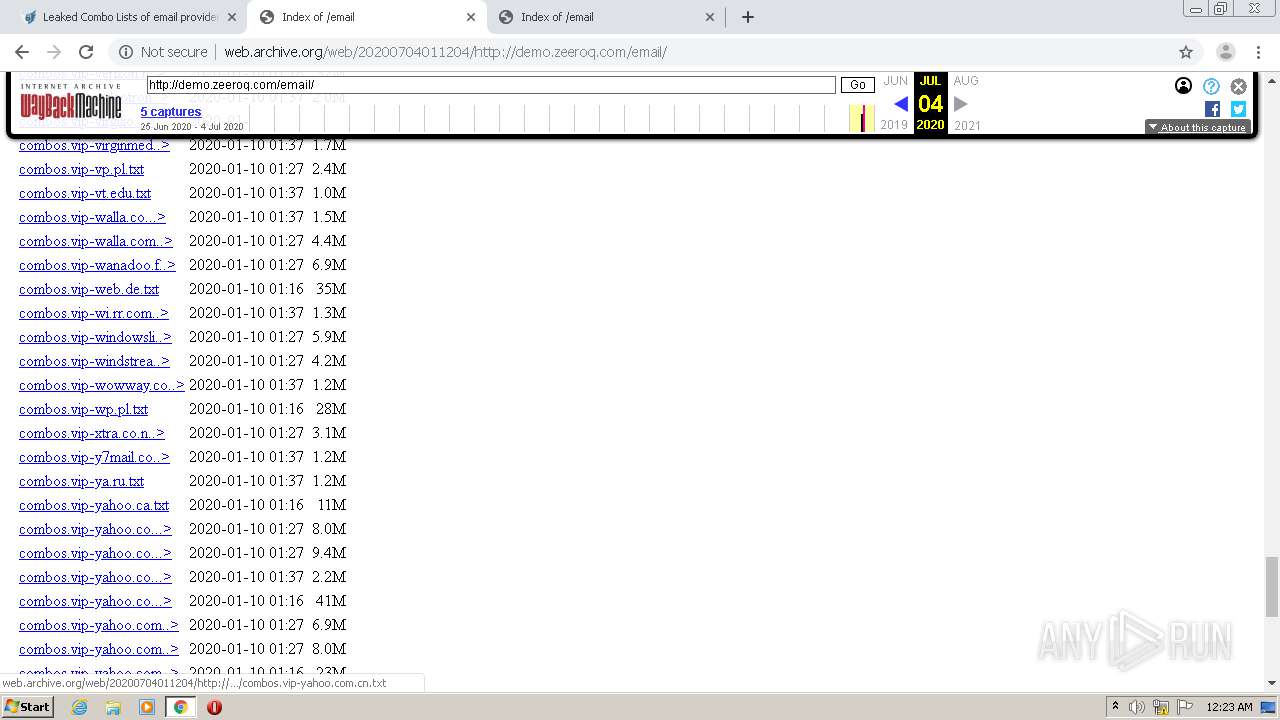
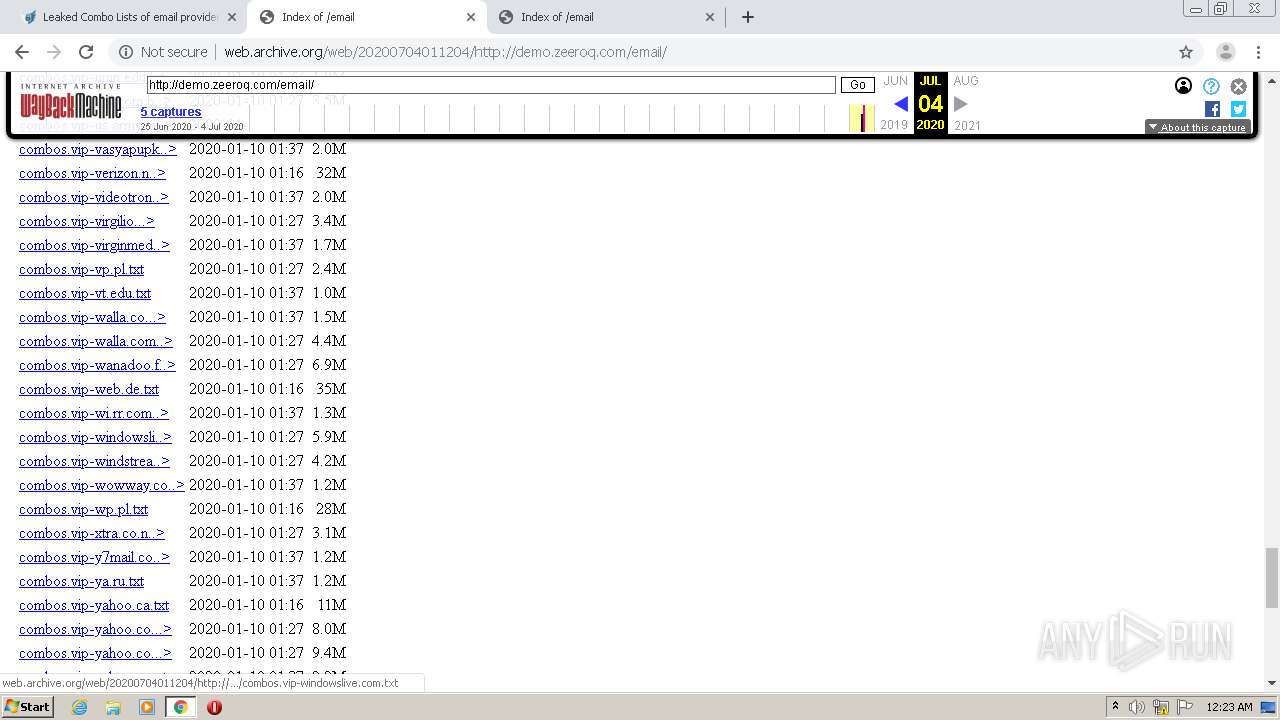
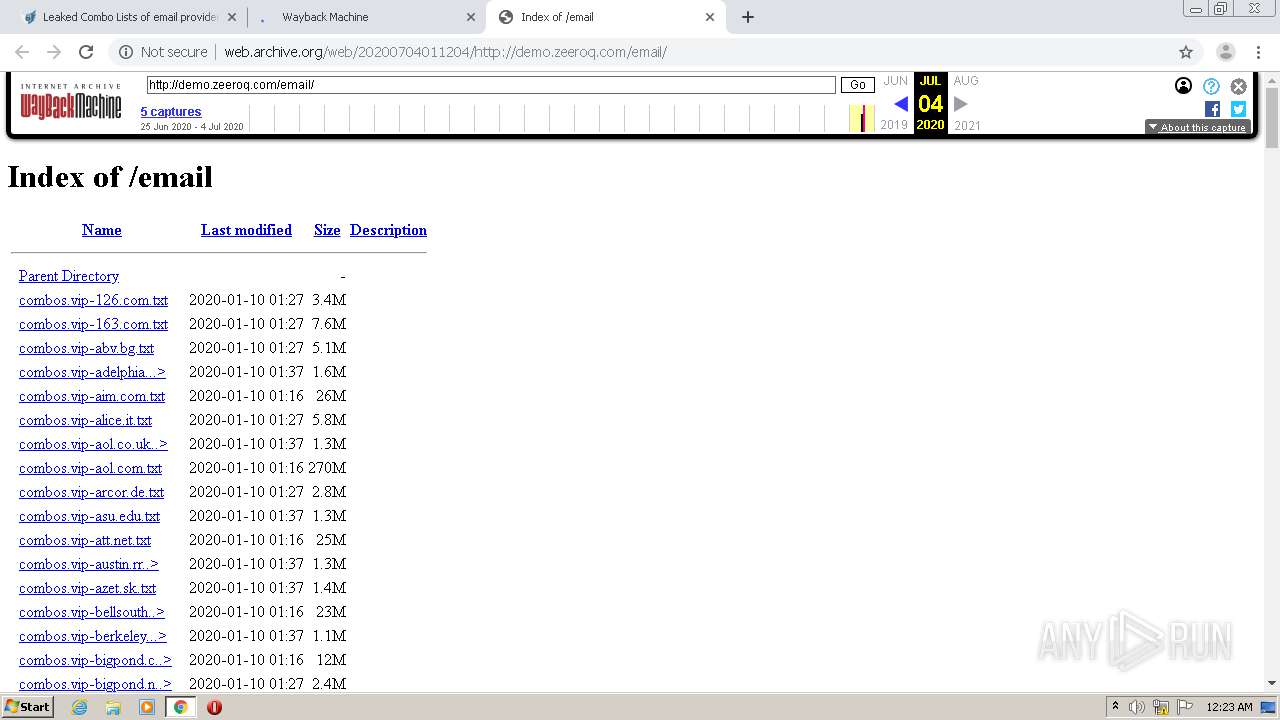
2040 | chrome.exe | GET | 200 | 207.241.226.190:80 | http://web.archive.org/web/20200704011204/http://demo.zeeroq.com/email/ | US | html | 8.15 Kb | whitelisted |
2040 | chrome.exe | GET | 200 | 207.241.226.190:80 | http://web.archive.org/_static/js/playback.bundle.js?v=SOX25l-I | US | text | 10.6 Kb | whitelisted |
2040 | chrome.exe | GET | 200 | 207.241.226.190:80 | http://web.archive.org/_static/css/banner-styles.css?v=bsmaklHF | US | text | 2.89 Kb | whitelisted |
2040 | chrome.exe | GET | 200 | 207.241.224.2:80 | http://archive.org/includes/analytics.js?v=cf34f82 | US | text | 4.79 Kb | whitelisted |
2040 | chrome.exe | GET | 200 | 207.241.226.190:80 | http://web.archive.org/_static/js/playback.bundle.js?v=VsAvnOBw | US | text | 10.6 Kb | whitelisted |
2040 | chrome.exe | GET | 200 | 207.241.226.190:80 | http://web.archive.org/web/20200705013449/http://demo.zeeroq.com/ | US | html | 5.21 Kb | whitelisted |
2040 | chrome.exe | GET | 200 | 207.241.226.190:80 | http://web.archive.org/_static/css/banner-styles.css?v=bsmaklHF | US | text | 2.89 Kb | whitelisted |
2040 | chrome.exe | GET | 200 | 207.241.226.190:80 | http://web.archive.org/_static/images/loading.gif | US | image | 913 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2040 | chrome.exe | 172.217.21.194:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
2040 | chrome.exe | 172.217.23.163:443 | www.google.co.uk | Google Inc. | US | whitelisted |
2040 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
2040 | chrome.exe | 74.125.198.105:443 | www.google.com | Google Inc. | US | whitelisted |
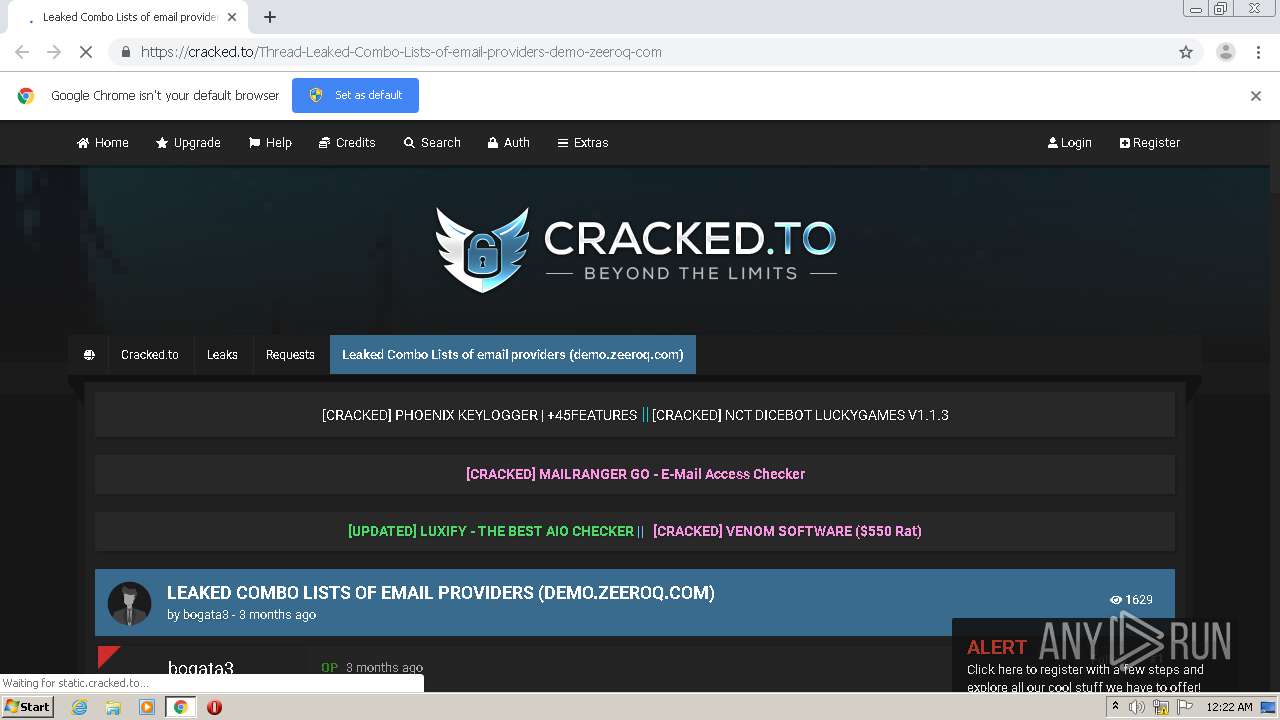
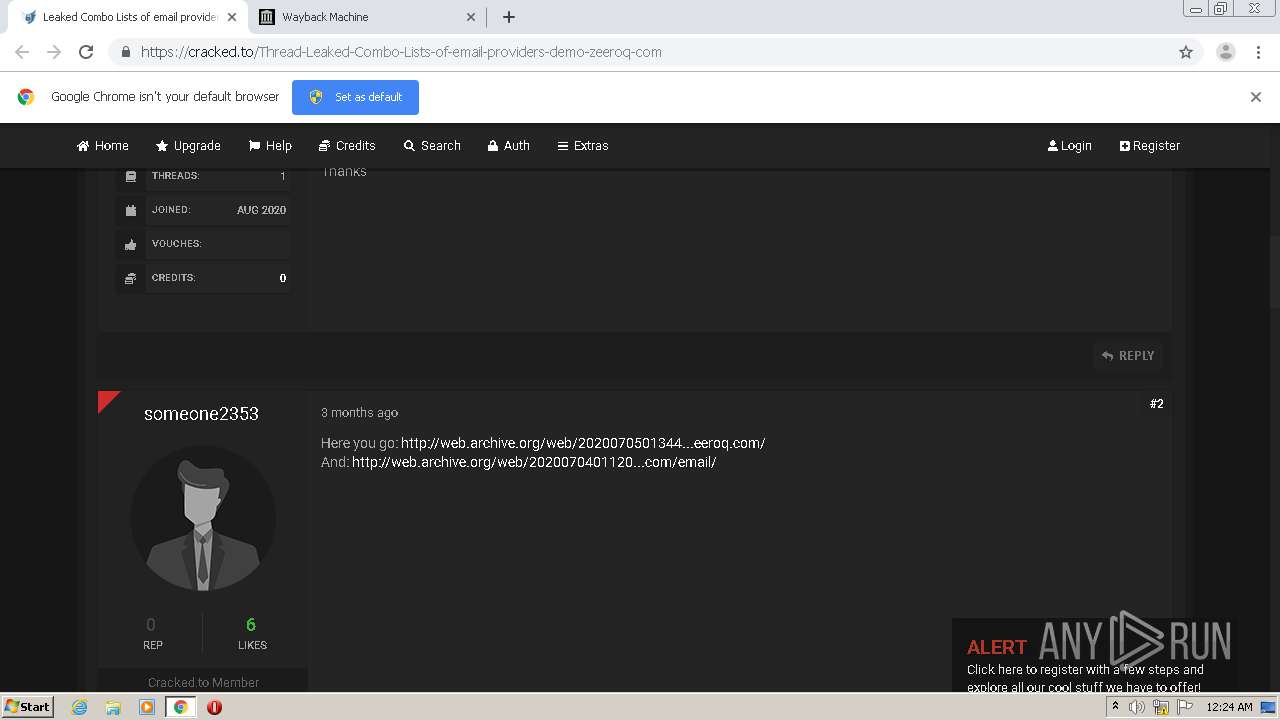
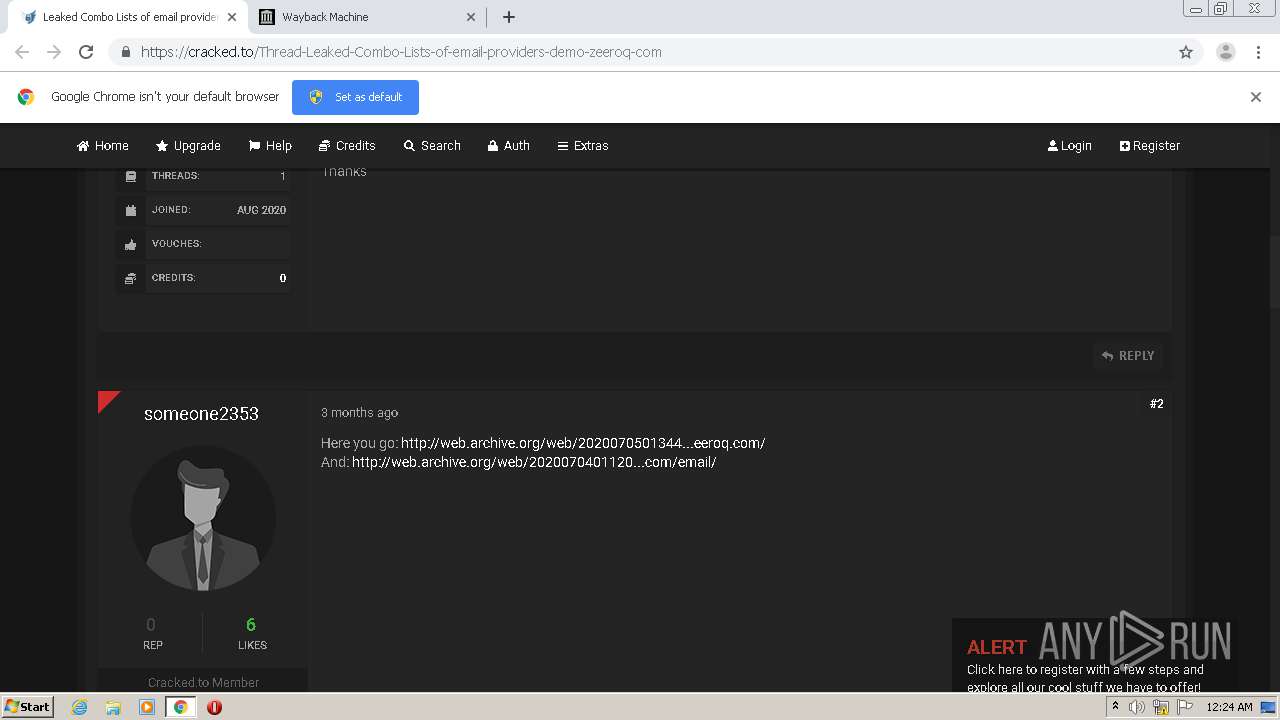
2040 | chrome.exe | 185.100.87.106:443 | cracked.to | Flokinet Ltd | RO | suspicious |
2040 | chrome.exe | 142.250.74.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2040 | chrome.exe | 104.16.18.94:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | unknown |
2040 | chrome.exe | 216.58.207.72:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2040 | chrome.exe | 104.26.0.64:443 | shoppy.gg | Cloudflare Inc | US | shared |
2040 | chrome.exe | 207.241.226.190:80 | web.archive.org | Internet Archive | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
accounts.google.com |
| shared |
cracked.to |
| whitelisted |
static.cracked.to |
| suspicious |
fonts.googleapis.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
shoppy.gg |
| malicious |
cdn.sellix.io |
| unknown |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1044 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |