| File name: | 1 |
| Full analysis: | https://app.any.run/tasks/140b50e2-d25f-4283-8609-247bceab80c8 |
| Verdict: | Malicious activity |
| Analysis date: | November 14, 2025, 00:05:43 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, 4 sections |
| MD5: | DF8F18FD4D9FBDF92E170C23480EC4EE |
| SHA1: | 60BC2BC6D6630C7AE7403EBB23656F6C3A81D759 |
| SHA256: | 58828A26B2BE6E7D9029BC9BF0C022A09DB72572C9D0F111E2EA65CEBE2FA85F |
| SSDEEP: | 6144:UZwpXu4UGF/PHCFNMulRmRBEZN2rm6EuFkRFBFkeXSlqbVIj3LtZo3:UZwpXUCHCzMq8Oqp1WoQ/kc3 |
MALICIOUS
ZEROACCESS mutex has been found
- 1.exe (PID: 7364)
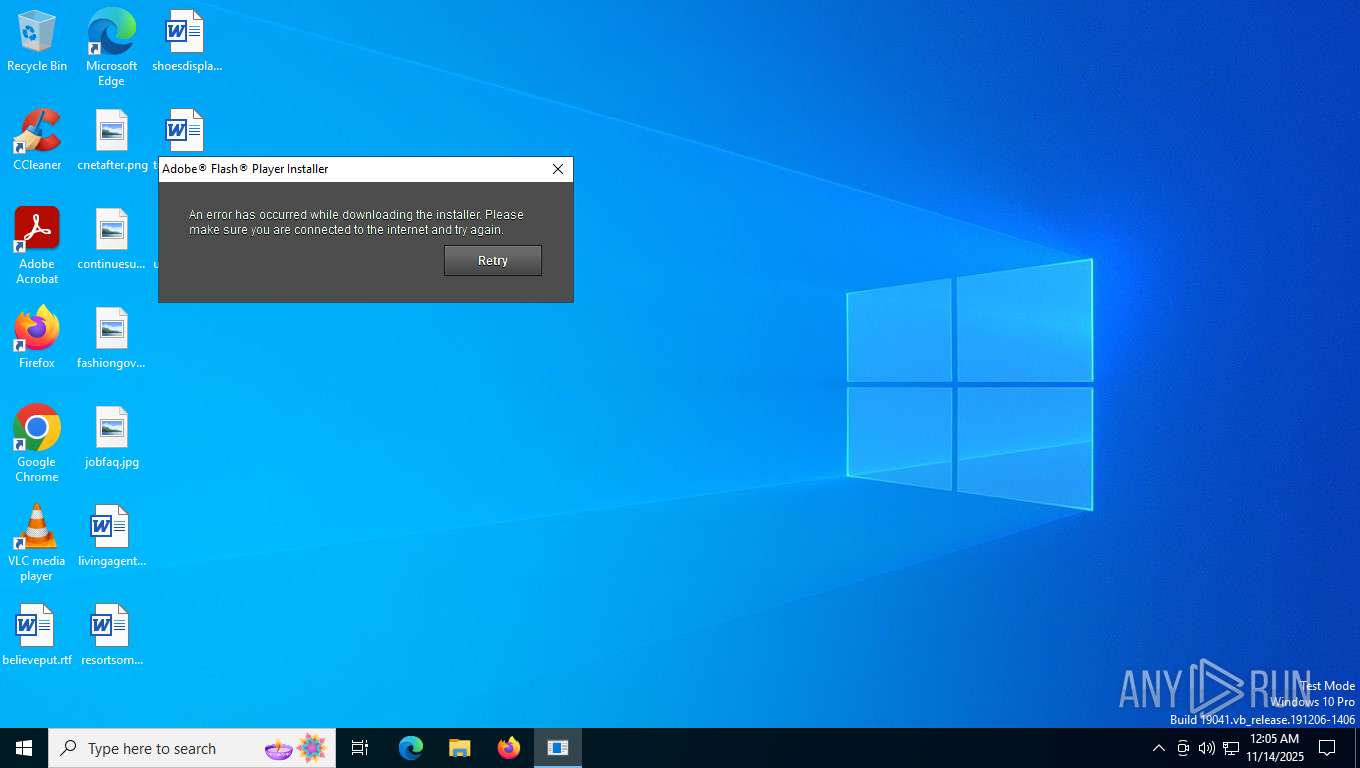
- InstallFlashPlayer.exe (PID: 7568)
ZEROACCESS has been detected
- 1.exe (PID: 7364)
ZEROACCESS has been detected (SURICATA)
- InstallFlashPlayer.exe (PID: 7568)
- 1.exe (PID: 7364)
Executing a file with an untrusted certificate
- InstallFlashPlayer.exe (PID: 7568)
SUSPICIOUS
Executable content was dropped or overwritten
- 1.exe (PID: 7364)
Creates/Modifies COM task schedule object
- 1.exe (PID: 7364)
There is functionality for taking screenshot (YARA)
- InstallFlashPlayer.exe (PID: 7568)
There is functionality for lookup Geolocation (YARA)
- InstallFlashPlayer.exe (PID: 7568)
Reads security settings of Internet Explorer
- InstallFlashPlayer.exe (PID: 7568)
- 1.exe (PID: 7364)
Starts CMD.EXE for commands execution
- 1.exe (PID: 7364)
INFO
Reads the machine GUID from the registry
- 1.exe (PID: 7364)
The sample compiled with english language support
- 1.exe (PID: 7364)
Checks supported languages
- InstallFlashPlayer.exe (PID: 7568)
- 1.exe (PID: 7364)
Reads the computer name
- InstallFlashPlayer.exe (PID: 7568)
- 1.exe (PID: 7364)
Checks proxy server information
- InstallFlashPlayer.exe (PID: 7568)
Process checks computer location settings
- 1.exe (PID: 7364)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
| .vxd | | | VXD Driver (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2004:03:30 18:48:45+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, 32-bit, No debug, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 98057 |
| InitializedDataSize: | 80896 |
| UninitializedDataSize: | 4096 |
| EntryPoint: | 0x2461 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Total processes
149
Monitored processes
5
Malicious processes
2
Suspicious processes
0
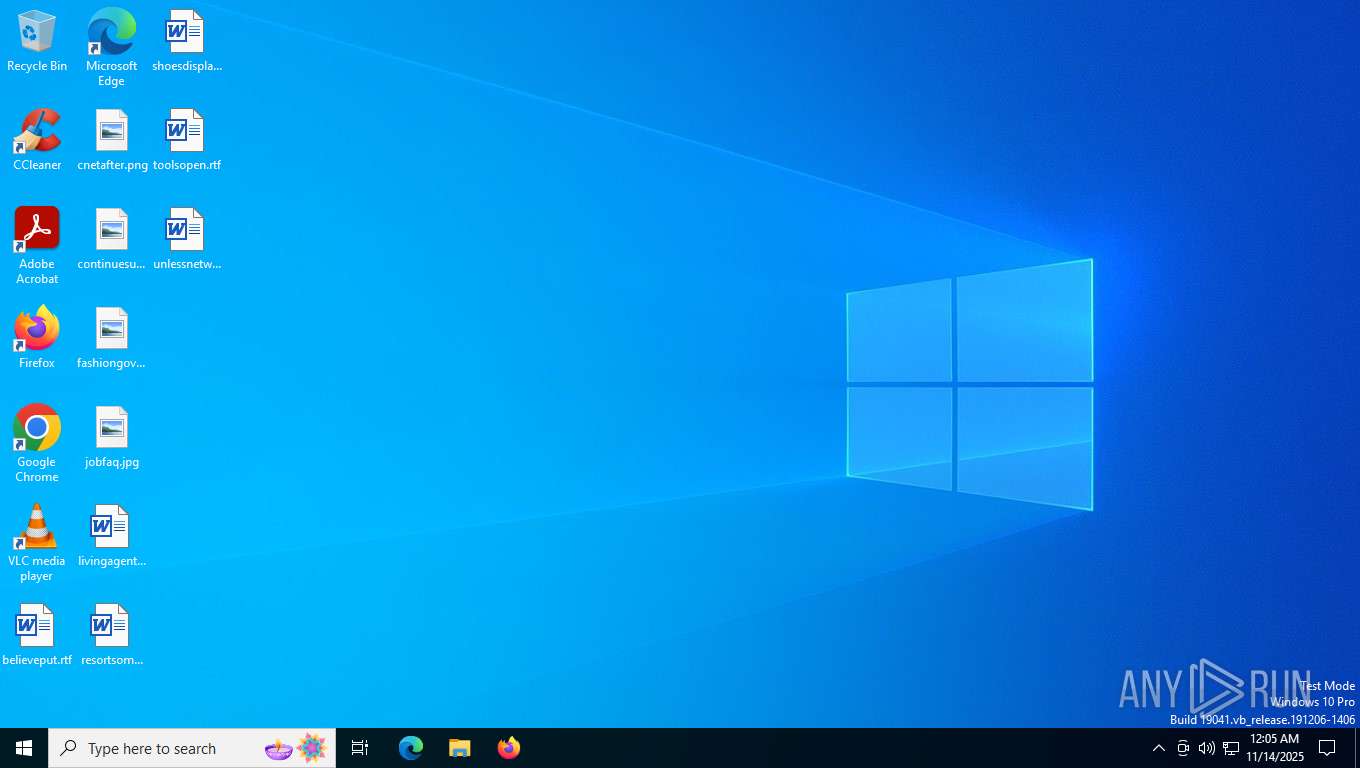
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3364 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7364 | "C:\Users\admin\AppData\Local\Temp\1.exe" | C:\Users\admin\AppData\Local\Temp\1.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7568 | "C:\Users\admin\AppData\Local\Temp\InstallFlashPlayer.exe" | C:\Users\admin\AppData\Local\Temp\InstallFlashPlayer.exe | 1.exe | ||||||||||||
User: admin Company: Adobe Systems, Inc. Integrity Level: HIGH Description: Adobe® Flash® Player Installer/Uninstaller 11.0 r1 Version: 11,0,1,152 Modules
| |||||||||||||||
| 7588 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\SysWOW64\cmd.exe | — | 1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 4294967295 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7600 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 248
Read events
5 234
Write events
14
Delete events
0
Modification events
| (PID) Process: | (7364) 1.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: 5C72166900000000 | |||
| (PID) Process: | (7568) InstallFlashPlayer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7568) InstallFlashPlayer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7568) InstallFlashPlayer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7364) 1.exe | Key: | HKEY_CLASSES_ROOT\CLSID\{fbeb8a05-beee-4442-804e-409d6c4515e9}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (7364) 1.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (7364) 1.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (7364) 1.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (7364) 1.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (7364) 1.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
3
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7364 | 1.exe | C:\$Recycle.Bin\S-1-5-21-1693682860-607145093-2874071422-1001\$81b8c3da9d80cef97346aaa39584b477\n | executable | |
MD5:9E0CD37B6D0809CF7D5FA5B521538D0D | SHA256:55D9748F0556576A8D522CF4B8DCFC9717436ADCC487D49B3320770432960DB2 | |||
| 7364 | 1.exe | C:\$Recycle.Bin\S-1-5-21-1693682860-607145093-2874071422-1001\$81b8c3da9d80cef97346aaa39584b477\@ | binary | |
MD5:A50C67D426770F6B5C15AFA547D3B9DC | SHA256:EDF43925D491F586BBF30DEBC261048132C210170D544F139F30FEF2C2720A54 | |||
| 7364 | 1.exe | C:\Users\admin\AppData\Local\Temp\InstallFlashPlayer.exe | executable | |
MD5:2FF9B590342C62748885D459D082295F | SHA256:672EC8DCEAFD429C1A09CFAFBC4951968953E2081E0D97243040DB16EDB24429 | |||
| 7364 | 1.exe | C:\Users\admin\AppData\Local\Temp\msimg32.dll | executable | |
MD5:4FC5991658F4773D17813B7CD1318F35 | SHA256:A8D271A7B85A876FBF18507E080113F1550857236DD3685803C6558FD2C8F2AA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
44
DNS requests
16
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2612 | SIHClient.exe | GET | 200 | 104.119.109.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
7568 | InstallFlashPlayer.exe | GET | 404 | 104.102.57.130:80 | http://fpdownload.macromedia.com/get/flashplayer/update/current/install/install_all_win_cab_64_ax_sgn.z | unknown | — | — | whitelisted |
744 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5596 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2612 | SIHClient.exe | GET | 200 | 104.119.109.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
2612 | SIHClient.exe | GET | 200 | 104.119.109.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | unknown | — | — | whitelisted |
2612 | SIHClient.exe | GET | 200 | 104.119.109.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
2612 | SIHClient.exe | GET | 200 | 104.119.109.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2348 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5596 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
744 | svchost.exe | 20.190.159.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 184.86.251.22:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
7364 | 1.exe | 194.165.17.3:53 | — | — | — | malicious |
7364 | 1.exe | 66.85.130.234:53 | — | — | — | malicious |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7568 | InstallFlashPlayer.exe | 104.102.57.130:80 | fpdownload.macromedia.com | AKAMAI-AS | DE | whitelisted |
7568 | InstallFlashPlayer.exe | 66.85.130.234:53 | — | — | — | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
j.maxmind.com |
| whitelisted |
fpdownload.macromedia.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7364 | 1.exe | A Network Trojan was detected | ET MALWARE ZeroAccess udp traffic detected |
7364 | 1.exe | A Network Trojan was detected | ET MALWARE ZeroAccess udp traffic detected |
7364 | 1.exe | A Network Trojan was detected | ET MALWARE ZeroAccess udp traffic detected |
7364 | 1.exe | A Network Trojan was detected | ET MALWARE ZeroAccess udp traffic detected |
7364 | 1.exe | A Network Trojan was detected | ET MALWARE ZeroAccess udp traffic detected |
7364 | 1.exe | A Network Trojan was detected | ET MALWARE ZeroAccess udp traffic detected |
7364 | 1.exe | A Network Trojan was detected | ET MALWARE ZeroAccess udp traffic detected |
7364 | 1.exe | A Network Trojan was detected | ET MALWARE ZeroAccess udp traffic detected |
7364 | 1.exe | A Network Trojan was detected | ET MALWARE ZeroAccess udp traffic detected |
7364 | 1.exe | A Network Trojan was detected | ET MALWARE ZeroAccess udp traffic detected |
Process | Message |
|---|---|
InstallFlashPlayer.exe | window key up
|